| File name: | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe |
| Full analysis: | https://app.any.run/tasks/88592a08-f62a-404c-9586-22a4f913225a |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2021, 09:37:18 |
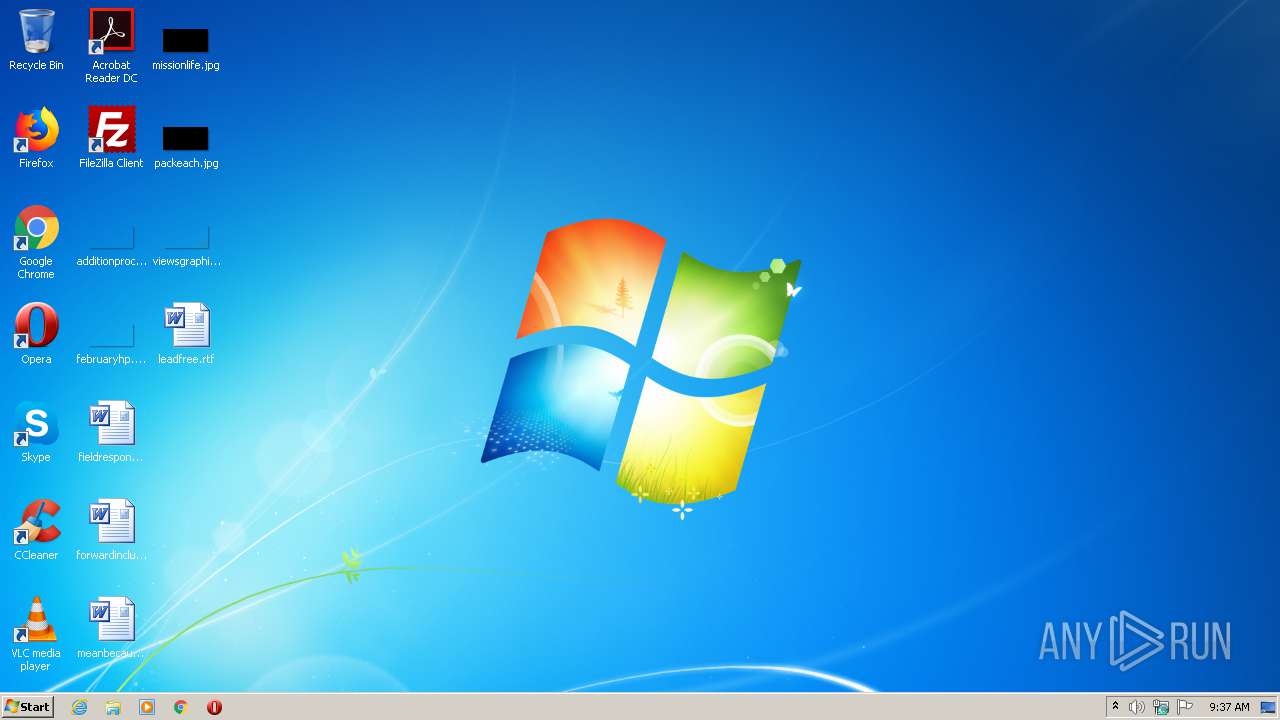
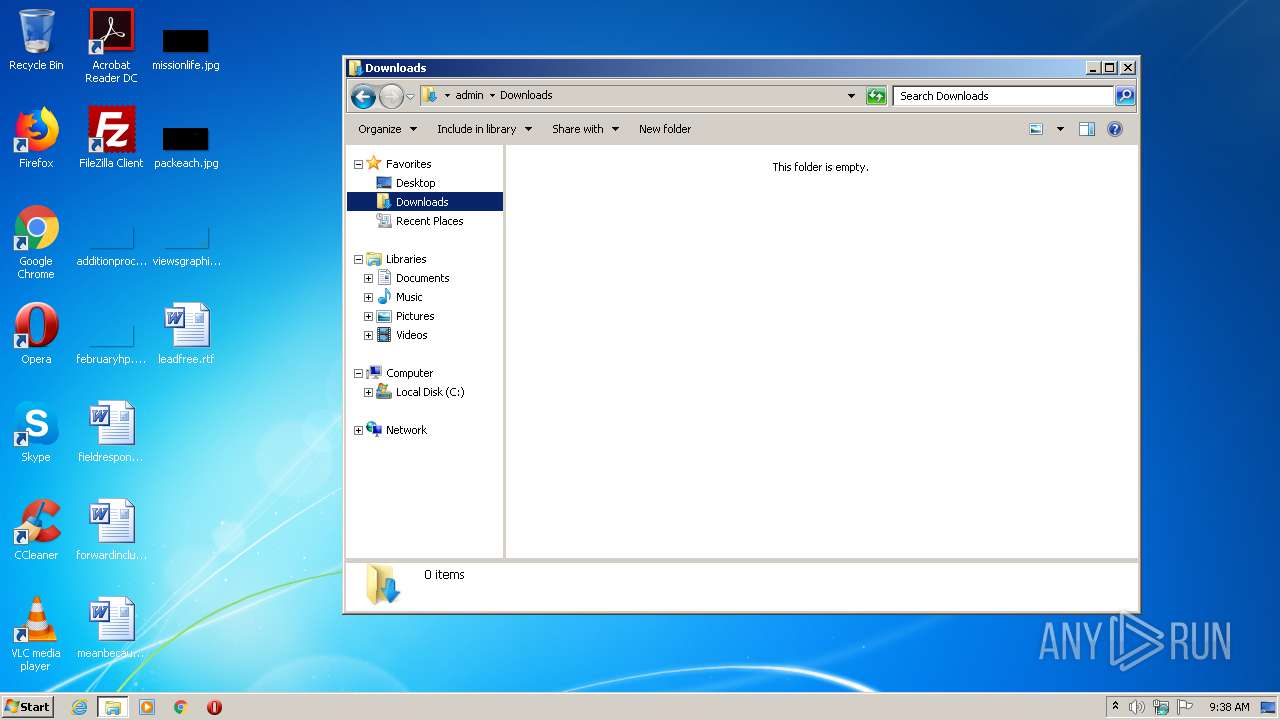
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FDB94075CD45B5828C5645B65DF42BB2 |
| SHA1: | EE080FA3BBF0513179627B4D1F1DACA35461D032 |
| SHA256: | 2ABC20764B812903F81D1787F8C47165713582E587A8F099DDACFC041937410C |
| SSDEEP: | 12288:LtLXhYSnzes1xJl62pgfmeUlHWDZQpT0js:L/YSzes1/kme4QZy0js |
MALICIOUS
Writes to the hosts file
- cmd.exe (PID: 1268)
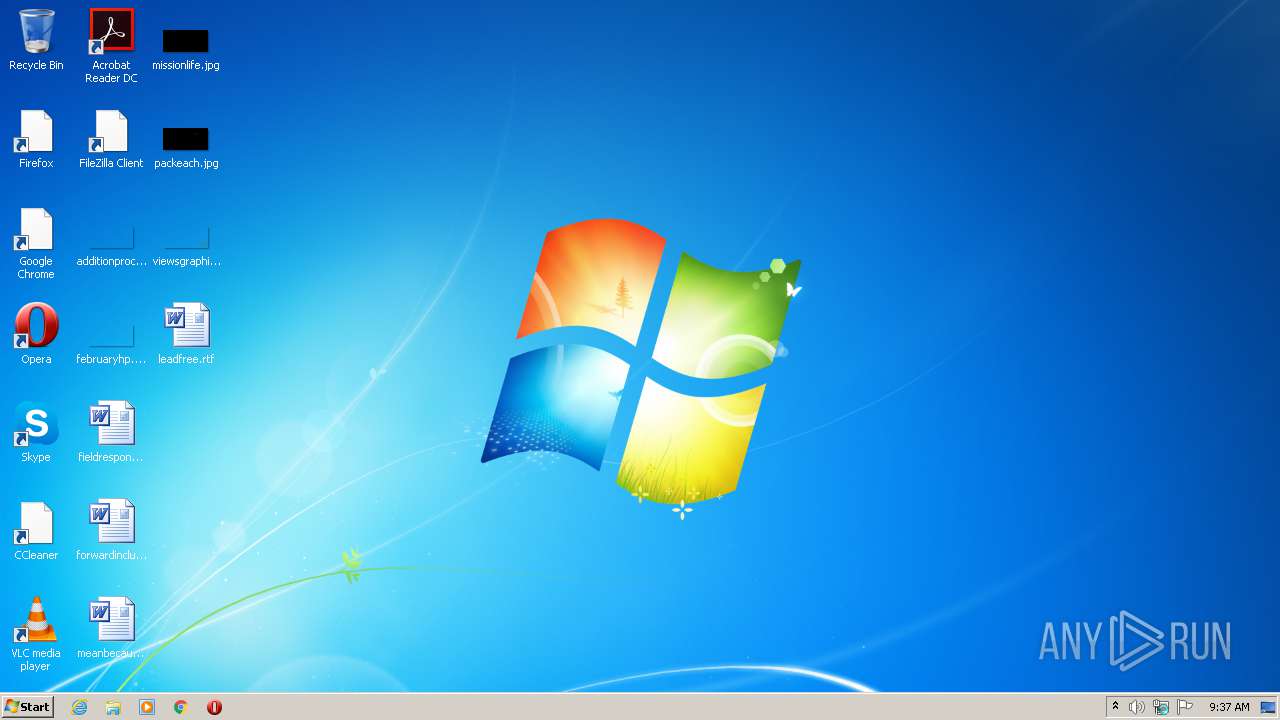
Drops executable file immediately after starts
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
SUSPICIOUS
Creates files in the Windows directory
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
Creates files in the user directory
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
Drops a file that was compiled in debug mode
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
Executable content was dropped or overwritten
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
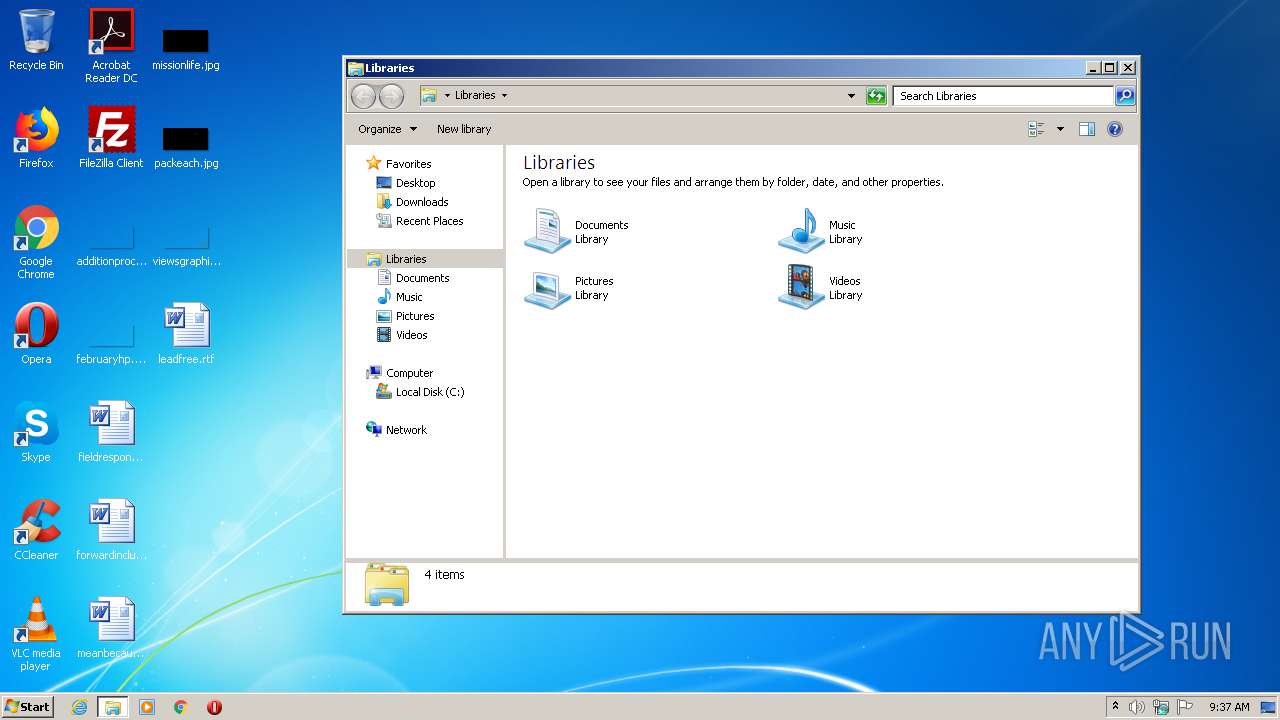
Starts CMD.EXE for commands execution
- Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe (PID: 2376)
INFO
Reads the hosts file
- cmd.exe (PID: 1268)
Manual execution by user
- explorer.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 101376 |
| InitializedDataSize: | 20992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19b64 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | FireZzZ |
| FileDescription: | Activator WF X10.xx Installation |
| FileVersion: | X10.xx |
| LegalCopyright: | FireZzZ |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | FireZzZ |
| FileDescription: | Activator WF X10.xx Installation |
| FileVersion: | X10.xx |
| LegalCopyright: | FireZzZ |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00018BC8 | 0x00018C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48382 |
DATA | 0x0001A000 | 0x0000071C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.28887 |
BSS | 0x0001B000 | 0x0000088D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001C000 | 0x00001756 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85156 |
.tls | 0x0001E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00020000 | 0x00001364 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.672 |
.rsrc | 0x00022000 | 0x00001A90 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.62796 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.75657 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.19786 | 248 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.94375 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
48
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1268 | cmd /c ""C:\Users\admin\AppData\Roaming\Microsoft SDK10\activator.bat" " | C:\Windows\system32\cmd.exe | — | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe" | C:\Users\admin\AppData\Local\Temp\Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | explorer.exe | ||||||||||||
User: admin Company: FireZzZ Integrity Level: HIGH Description: Activator WF X10.xx Installation Exit code: 0 Version: X10.xx Modules
| |||||||||||||||
| 2456 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | xcopy "C:\Users\admin\AppData\Local\Temp\wf" "C:\Program Files\Wondershare\Wondershare Filmora" /H /Y /C | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\AppData\Local\Temp\Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe" | C:\Users\admin\AppData\Local\Temp\Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | — | explorer.exe | |||||||||||
User: admin Company: FireZzZ Integrity Level: MEDIUM Description: Activator WF X10.xx Installation Exit code: 3221226540 Version: X10.xx Modules
| |||||||||||||||
Total events
383
Read events
378
Write events
5
Delete events
0
Modification events
| (PID) Process: | (2376) Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2376) Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2376) Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 74 | |||
Executable files
4
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 1268 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\wf\UpdateRegister.dll | executable | |
MD5:126E54A44EF54E8F1DE799646CC1478F | SHA256:AAF6EA616C4A572C70E4915490717BF4FAD023331AB95DB8A769E4D8DDF777D4 | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Windows\s.txt | text | |
MD5:FA19C41E099F85AE05AFADEE6BADF787 | SHA256:51042A4B41B948EC0117C5E139A253B14511B7029A31B7D39F411073BC770D76 | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Roaming\Microsoft SDK10\activator.bat | text | |
MD5:27EE4E33289FB4E71F21EB61F62FE12C | SHA256:AF2DB13C34AB1176D65A92DB07E2BBAD9977DCAE53910FAABAF0D2E8249A661D | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:8708699D2C73BED30A0A08D80F96D6D7 | SHA256:A32E0A83001D2C5D41649063217923DAC167809CAB50EC5784078E41C9EC0F0F | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\wf\Wondershare Helper Compact.exe | executable | |
MD5:45FBD7B4A57994922D58541202713336 | SHA256:0C3169530C3209FA9AA5DCAD6C28CB6B7DDEF63DBA8C784AC603D9293FD3A053 | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\wf\WsAP-Filmora.dll | executable | |
MD5:6EBFE13A53D8577F1B7AFDBF8756ED35 | SHA256:963CBD39A125BC1507701E3766633105CF1E4CCE64FC3EC14CD5AAC28C27B593 | |||
| 2376 | Activator W-Filmora X 10.xx By Bhakkar IT Ustaad .exe | C:\Users\admin\AppData\Local\Temp\wf\LRePacks.dll | executable | |
MD5:0C9DA69BADE89063D5B0E7F6039EDEF9 | SHA256:B9DE47144F56545A06FDEEA47D6CFCFC4A142B0DF99FFFBECA2C1297CEF71C68 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report