| File name: | Activator WF X10.xx.exe |
| Full analysis: | https://app.any.run/tasks/58e457f8-9fe8-4bc9-837b-3c4130a335fe |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 14:03:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FDB94075CD45B5828C5645B65DF42BB2 |
| SHA1: | EE080FA3BBF0513179627B4D1F1DACA35461D032 |
| SHA256: | 2ABC20764B812903F81D1787F8C47165713582E587A8F099DDACFC041937410C |
| SSDEEP: | 12288:LtLXhYSnzes1xJl62pgfmeUlHWDZQpT0js:L/YSzes1/kme4QZy0js |
MALICIOUS
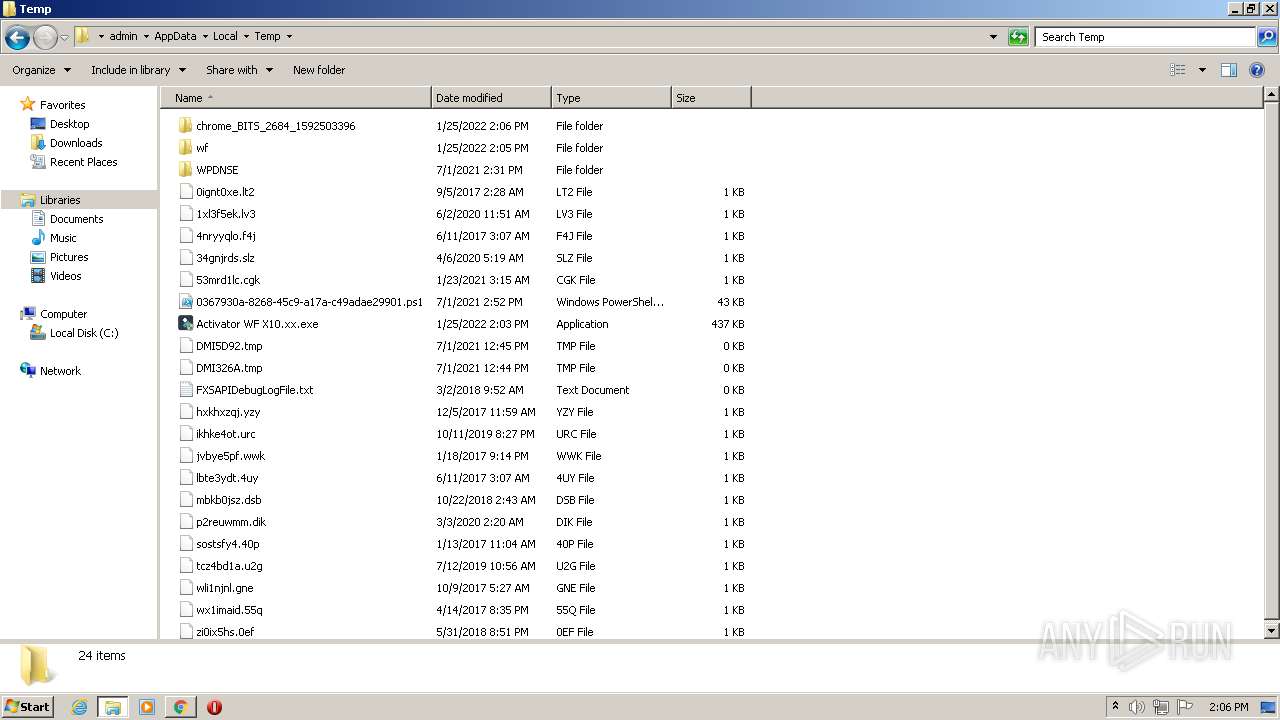
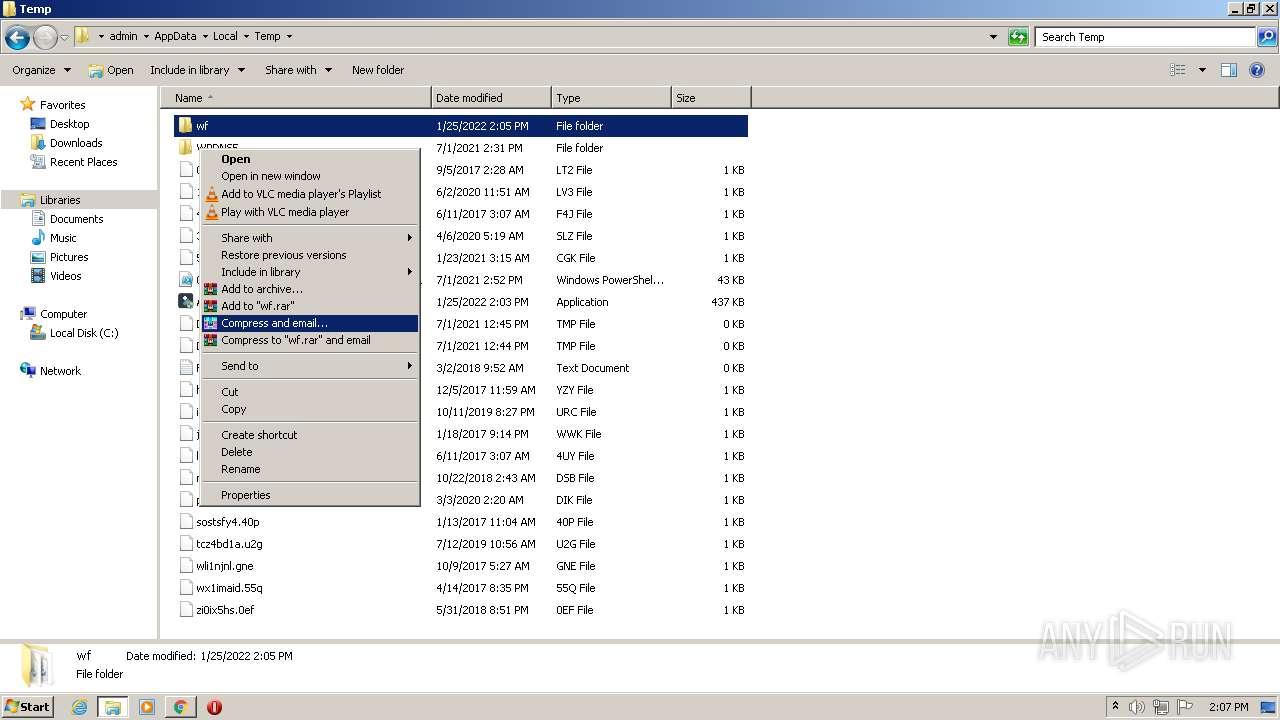
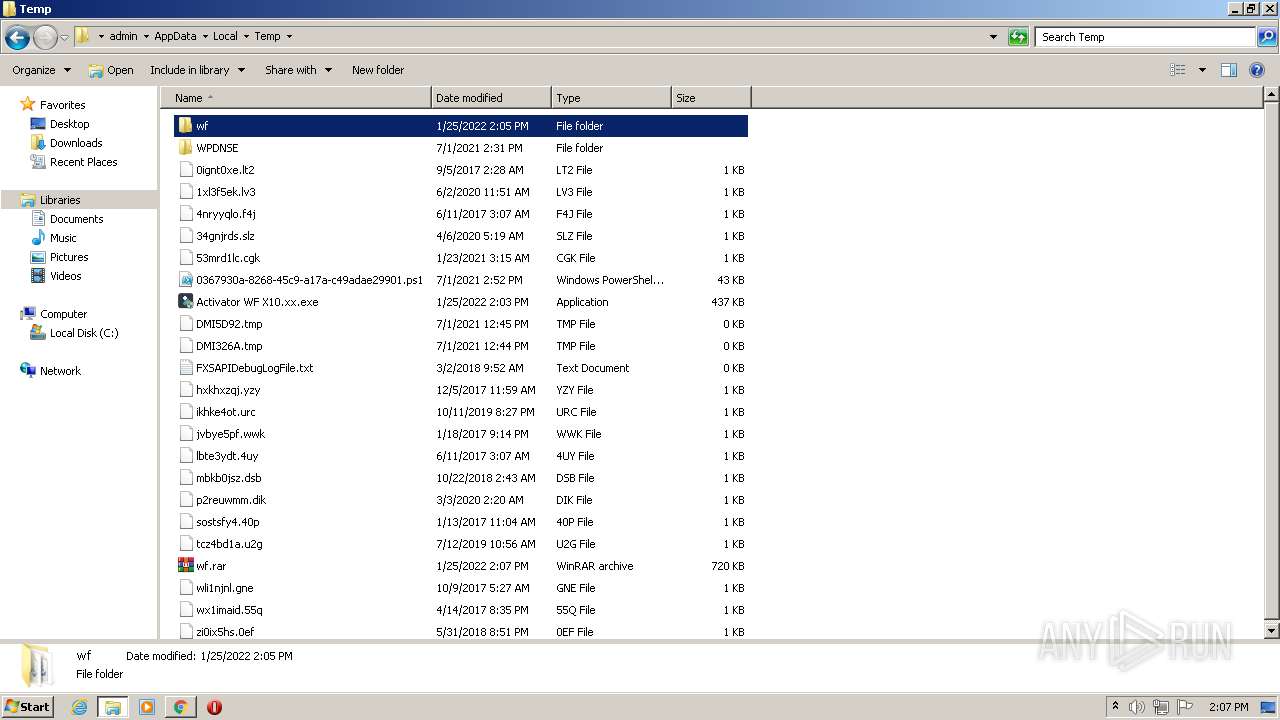
Drops executable file immediately after starts
- Activator WF X10.xx.exe (PID: 3368)
- chrome.exe (PID: 3228)
Writes to the hosts file
- cmd.exe (PID: 2652)
SUSPICIOUS
Checks supported languages
- Activator WF X10.xx.exe (PID: 3368)
- cmd.exe (PID: 2652)
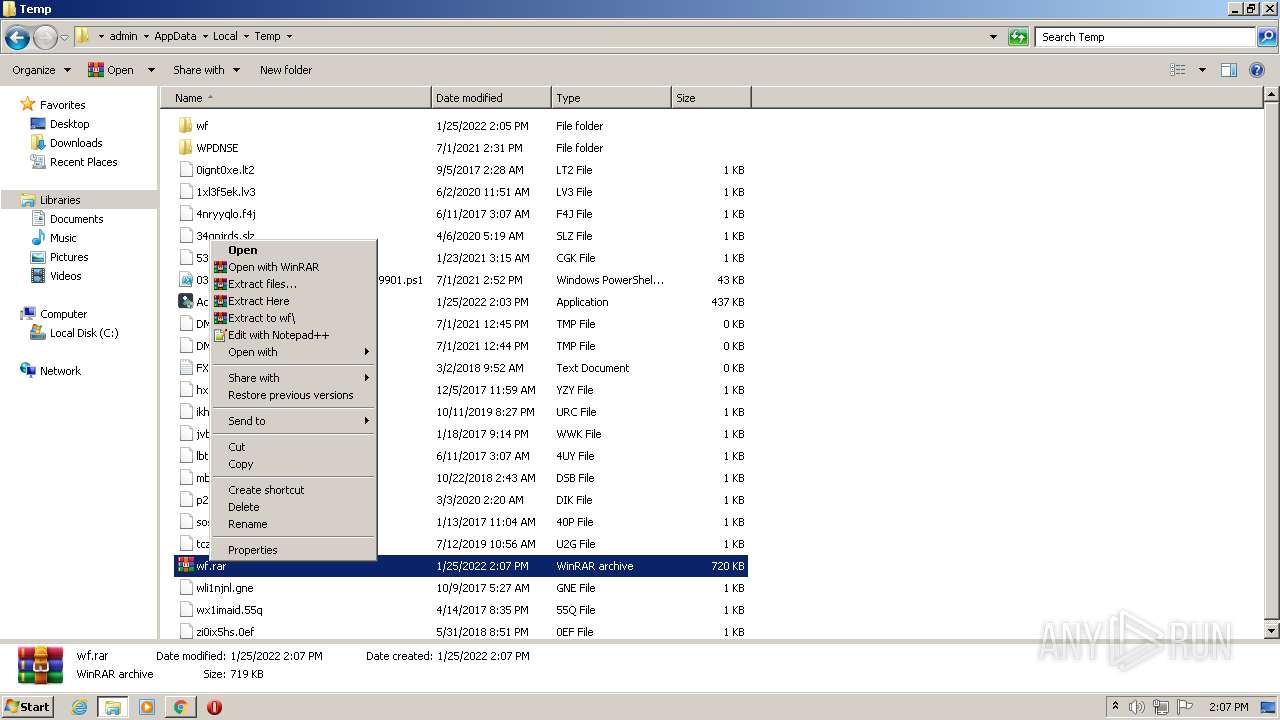
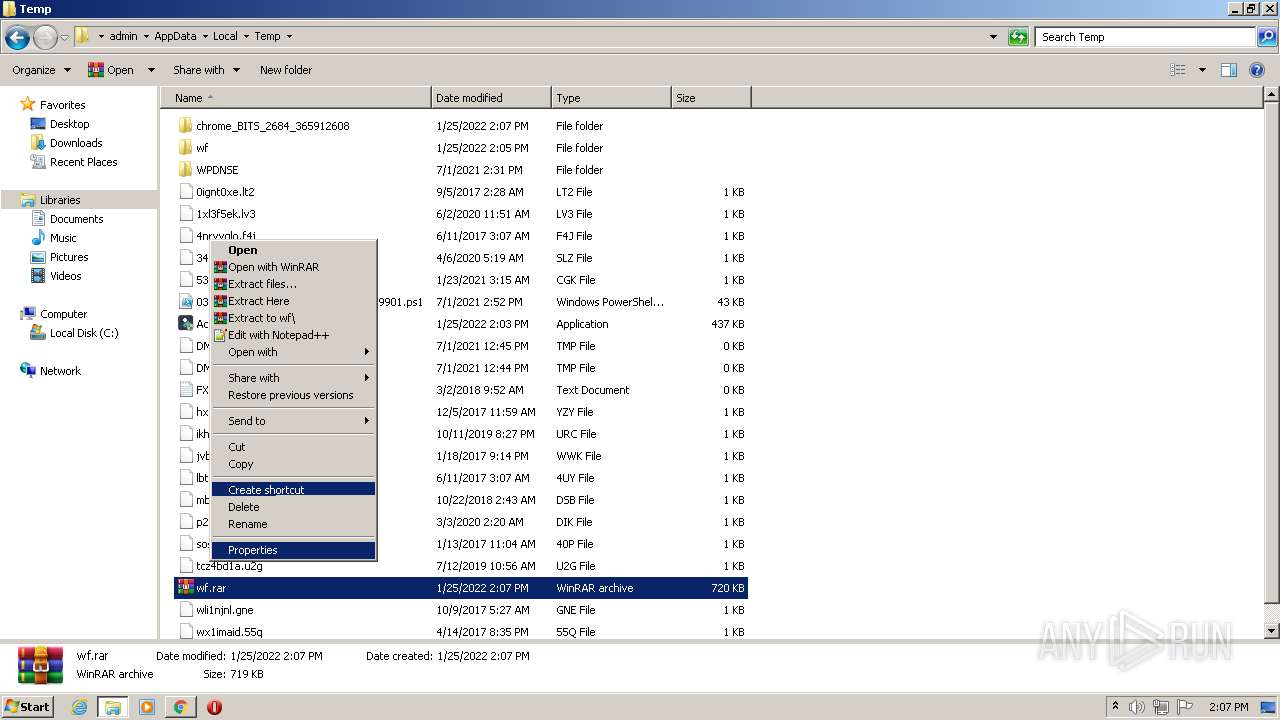
- WinRAR.exe (PID: 3284)
Creates files in the Windows directory
- Activator WF X10.xx.exe (PID: 3368)
Executable content was dropped or overwritten
- Activator WF X10.xx.exe (PID: 3368)
- chrome.exe (PID: 3228)
Reads the computer name
- Activator WF X10.xx.exe (PID: 3368)
- WinRAR.exe (PID: 3284)
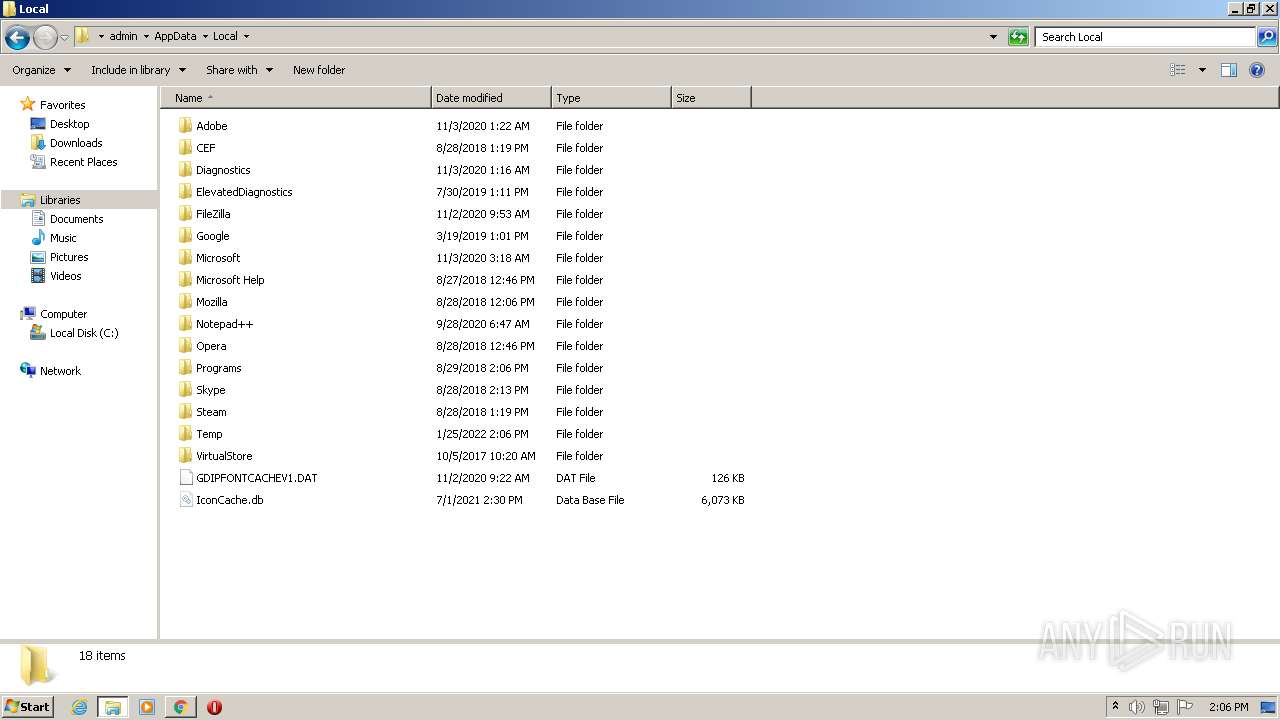
Creates files in the user directory
- Activator WF X10.xx.exe (PID: 3368)
Drops a file that was compiled in debug mode
- Activator WF X10.xx.exe (PID: 3368)
- chrome.exe (PID: 3228)
Starts CMD.EXE for commands execution
- Activator WF X10.xx.exe (PID: 3368)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2684)
INFO
Reads the hosts file
- cmd.exe (PID: 2652)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 852)
Checks supported languages
- xcopy.exe (PID: 2868)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 1536)
- explorer.exe (PID: 3912)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 852)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 968)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 832)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 776)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 848)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 1220)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 1480)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 876)
- chrome.exe (PID: 2720)
- explorer.exe (PID: 356)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2724)
Manual execution by user
- chrome.exe (PID: 2684)
- explorer.exe (PID: 3912)
- explorer.exe (PID: 356)
- WinRAR.exe (PID: 3284)
Reads the computer name
- chrome.exe (PID: 2684)
- explorer.exe (PID: 3912)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 852)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3476)
- explorer.exe (PID: 356)
Application launched itself
- chrome.exe (PID: 2684)
Reads settings of System Certificates
- chrome.exe (PID: 852)
Reads the date of Windows installation
- chrome.exe (PID: 2296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| LegalCopyright: | FireZzZ |
|---|---|
| FileVersion: | X10.xx |
| FileDescription: | Activator WF X10.xx Installation |
| CompanyName: | FireZzZ |
| Comments: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x19b64 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 20992 |
| CodeSize: | 101376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | FireZzZ |
| FileDescription: | Activator WF X10.xx Installation |
| FileVersion: | X10.xx |
| LegalCopyright: | FireZzZ |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00018BC8 | 0x00018C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48382 |
DATA | 0x0001A000 | 0x0000071C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.28887 |
BSS | 0x0001B000 | 0x0000088D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001C000 | 0x00001756 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85156 |
.tls | 0x0001E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00020000 | 0x00001364 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.672 |
.rsrc | 0x00022000 | 0x00001A90 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.62796 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.75657 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.19786 | 248 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.94375 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
122
Monitored processes
74
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3892 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,17144472976039855030,15109437266933575196,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
15 064
Read events
14 915
Write events
141
Delete events
8
Modification events
| (PID) Process: | (3368) Activator WF X10.xx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3368) Activator WF X10.xx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3368) Activator WF X10.xx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3368) Activator WF X10.xx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3368) Activator WF X10.xx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 101 | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
5
Suspicious files
221
Text files
194
Unknown types
14
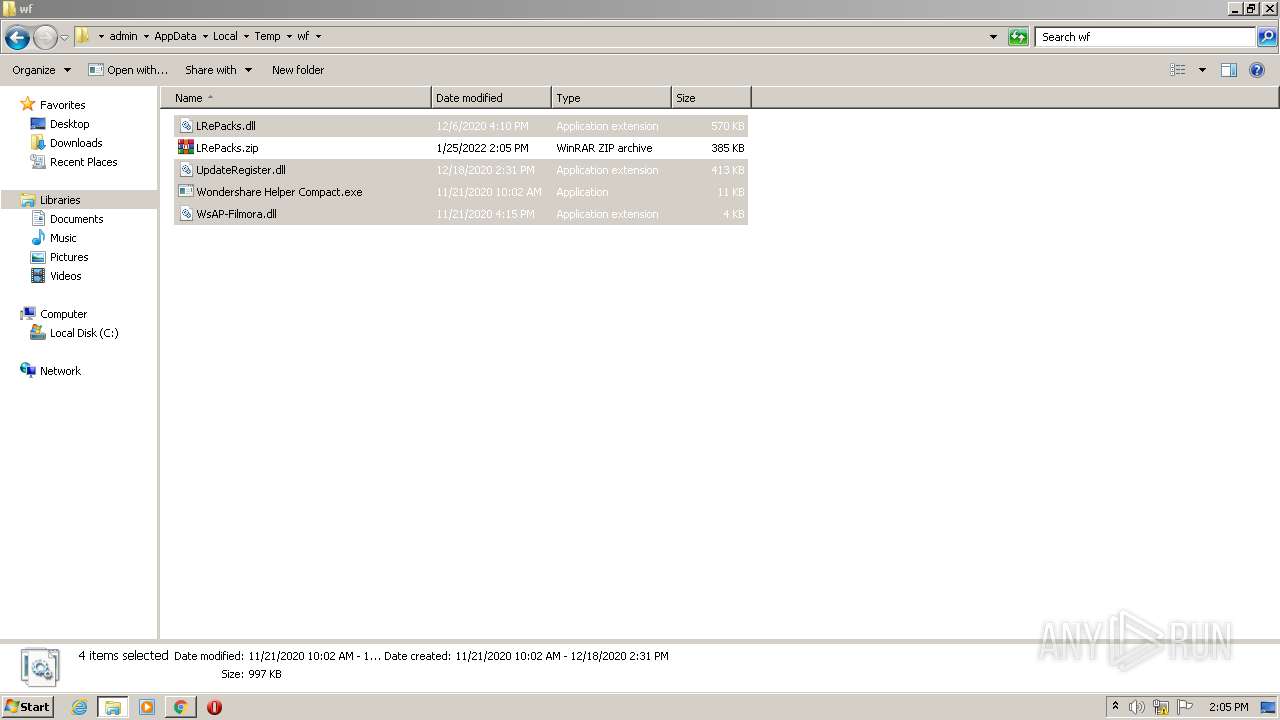
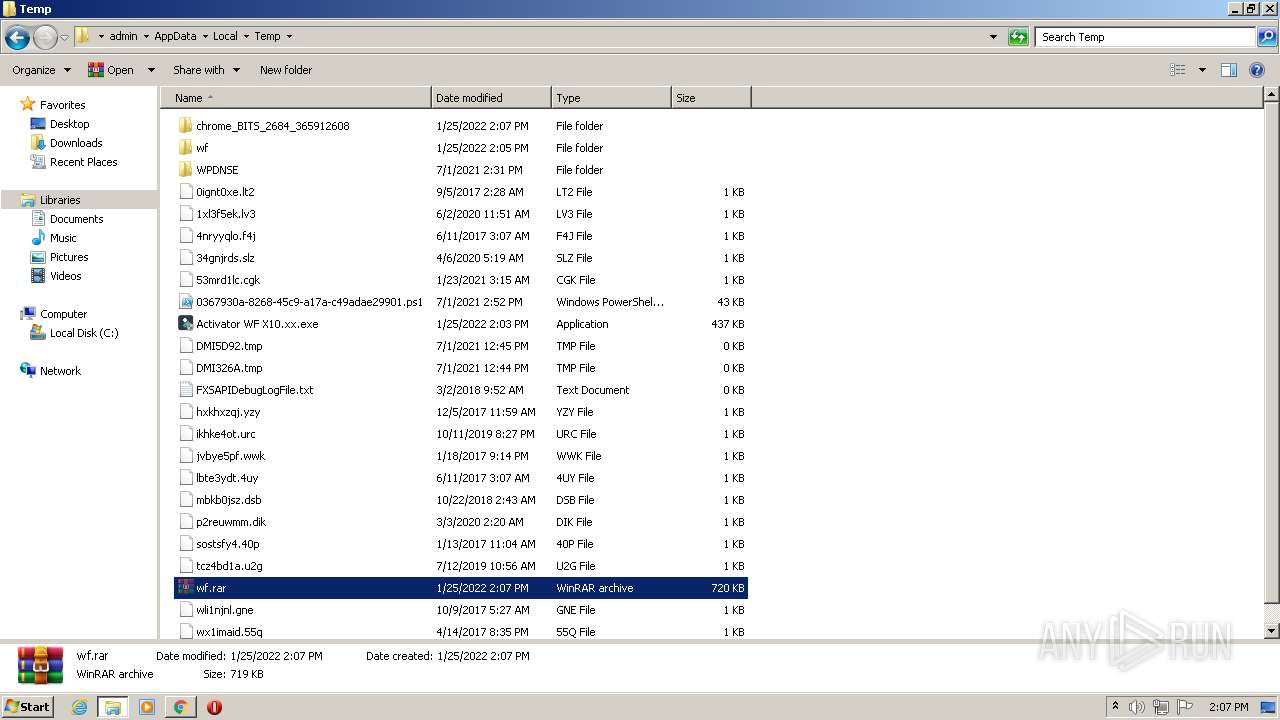
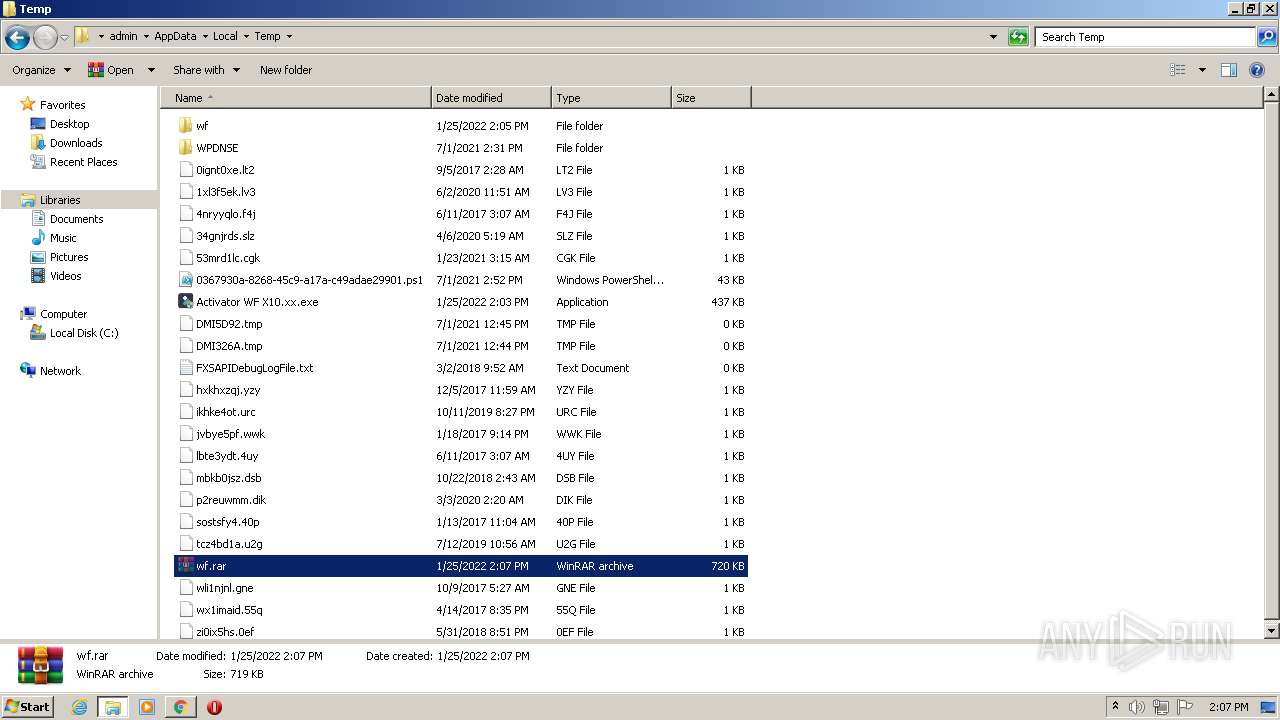
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61F0038E-A7C.pma | — | |
MD5:— | SHA256:— | |||
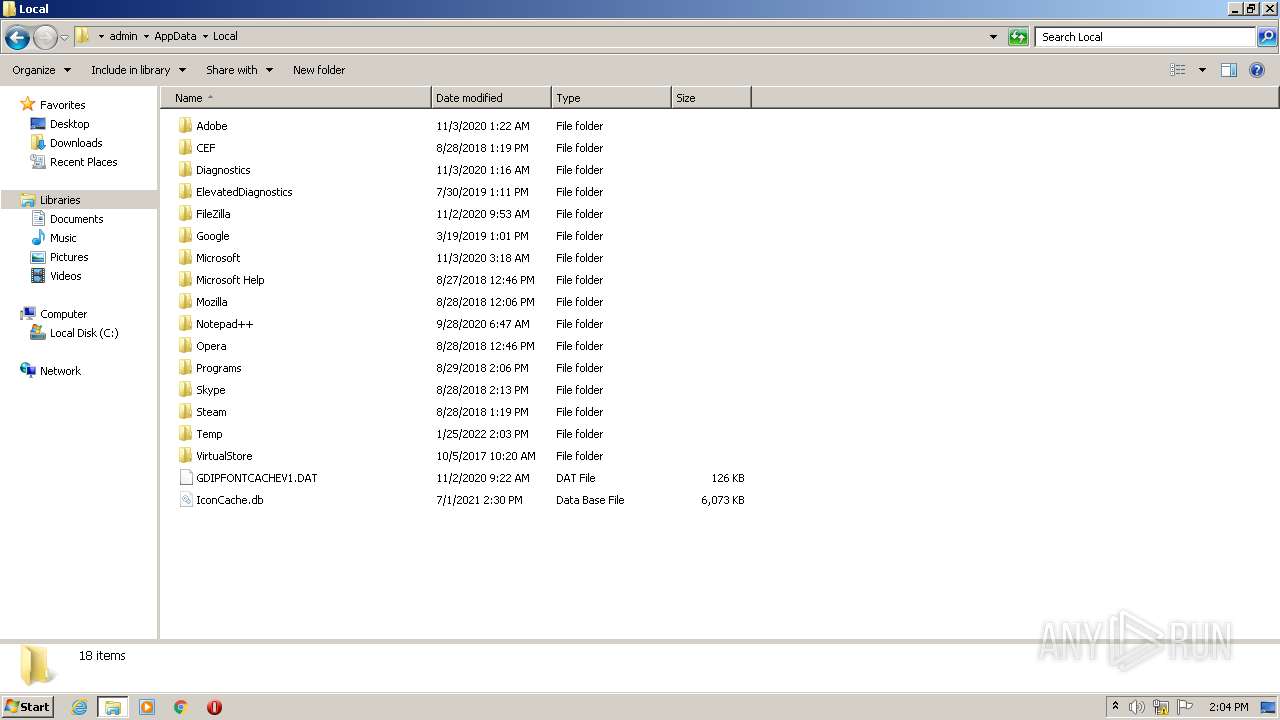
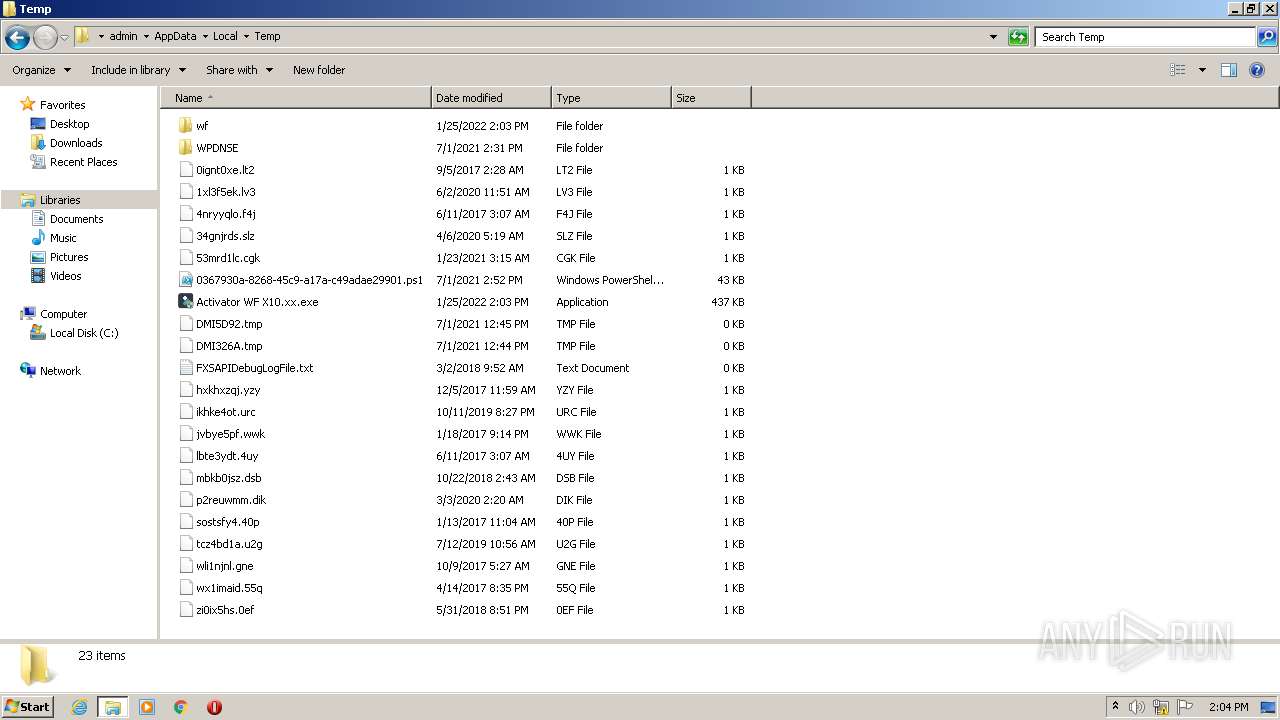
| 3368 | Activator WF X10.xx.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:8708699D2C73BED30A0A08D80F96D6D7 | SHA256:A32E0A83001D2C5D41649063217923DAC167809CAB50EC5784078E41C9EC0F0F | |||
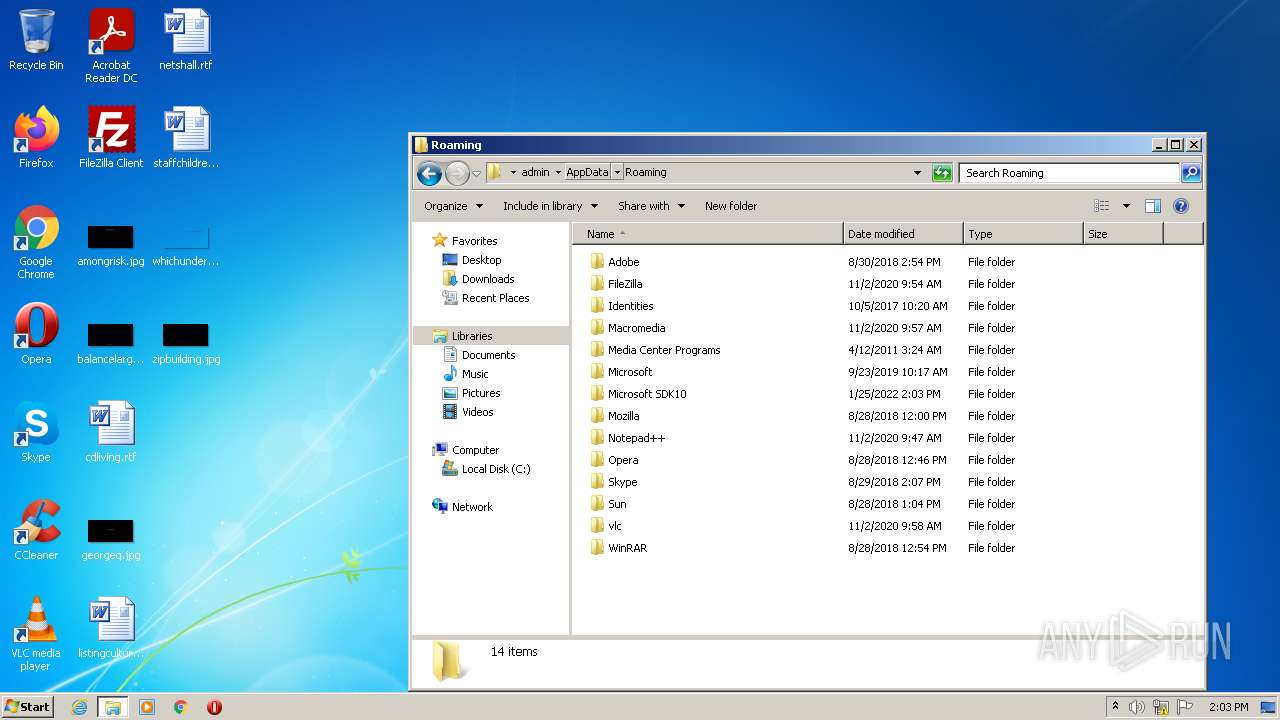
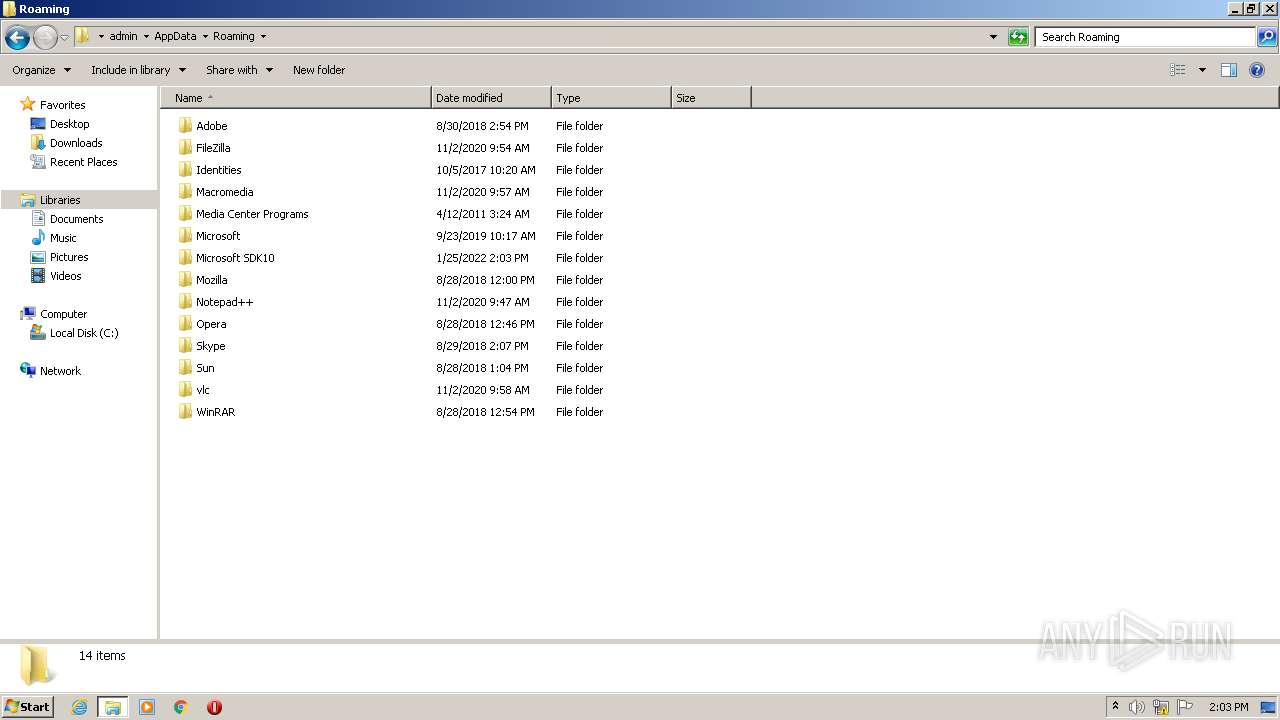
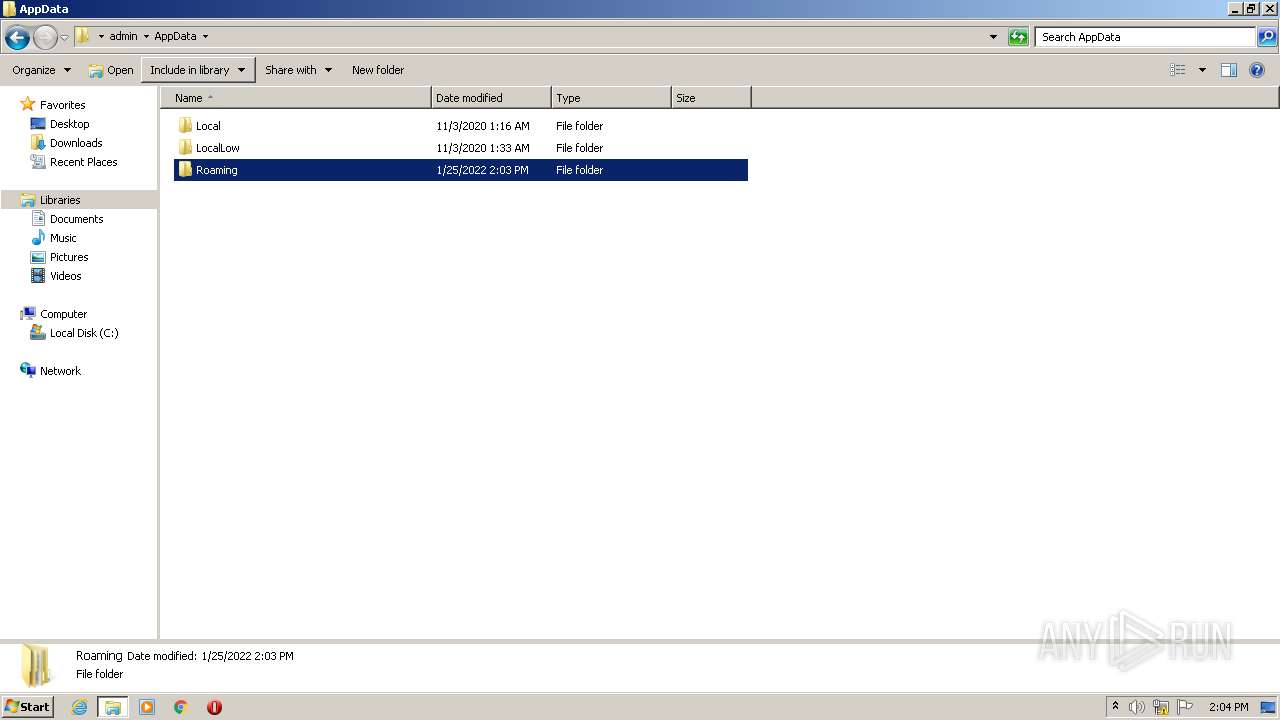
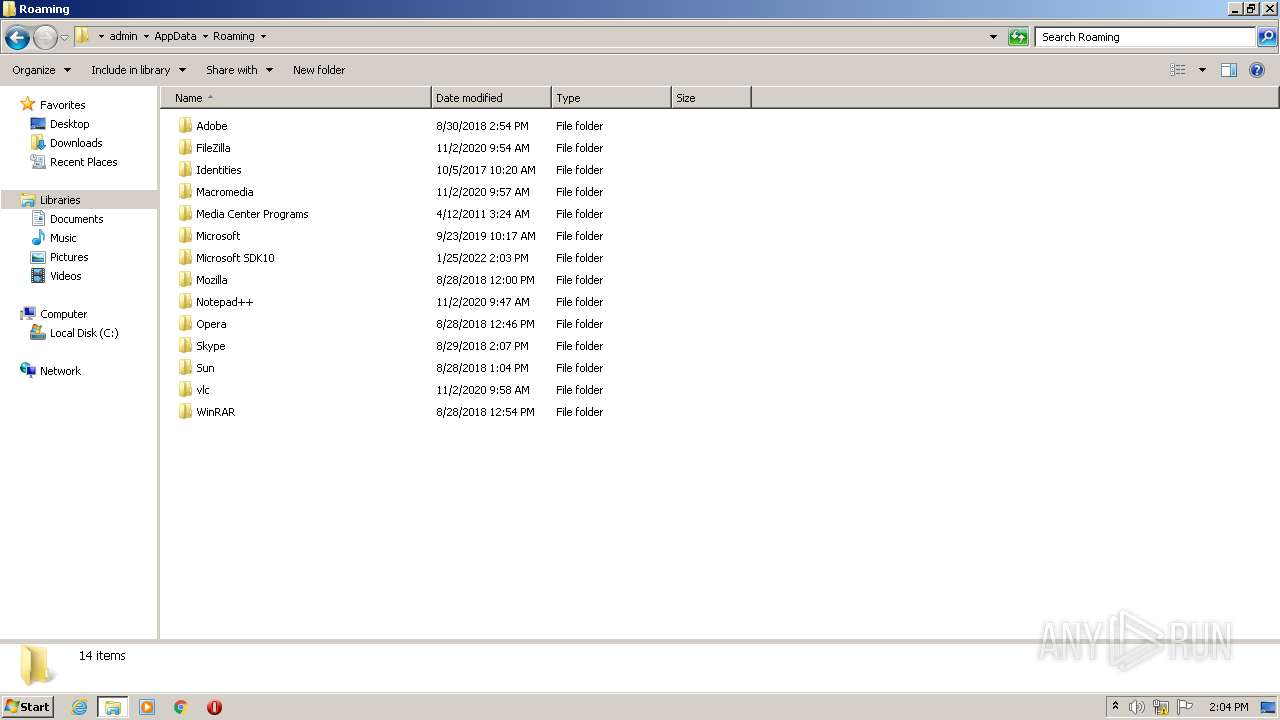
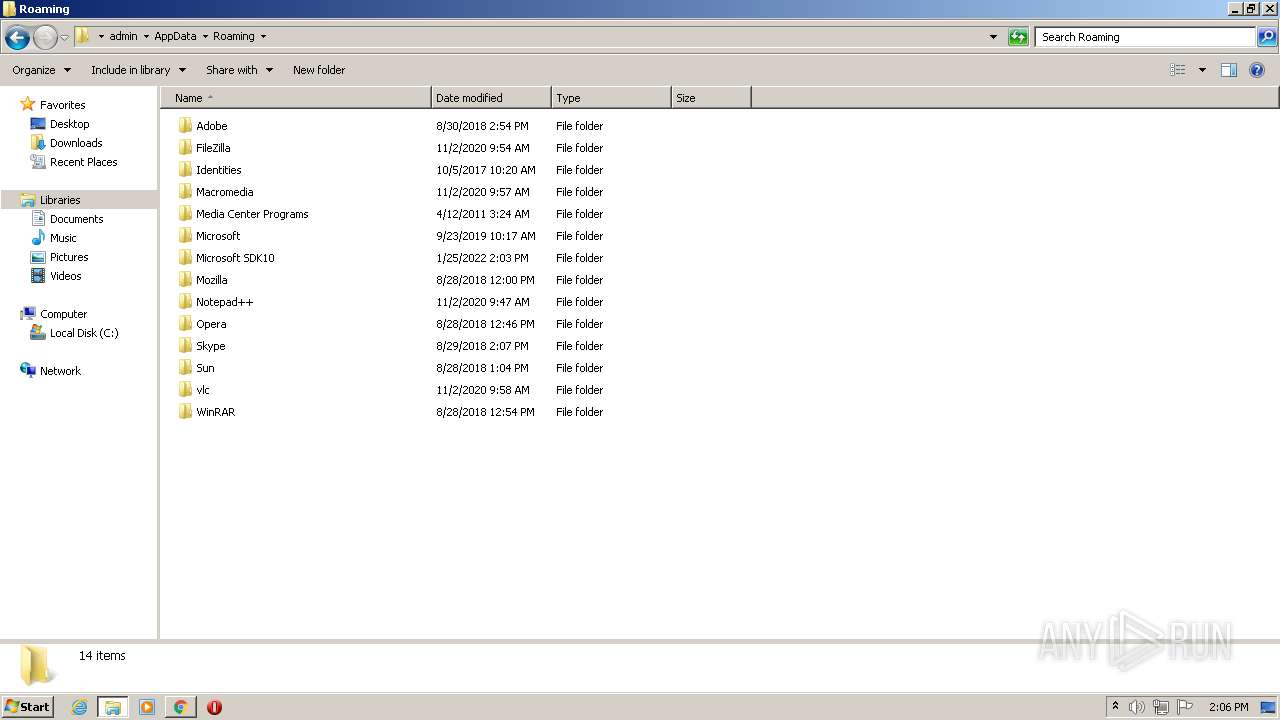
| 3368 | Activator WF X10.xx.exe | C:\Users\admin\AppData\Roaming\Microsoft SDK10\activator.bat | text | |
MD5:27EE4E33289FB4E71F21EB61F62FE12C | SHA256:AF2DB13C34AB1176D65A92DB07E2BBAD9977DCAE53910FAABAF0D2E8249A661D | |||
| 1536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3368 | Activator WF X10.xx.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:2ACB5D066BF5608429BF7B1190551B60 | SHA256:A626DC5002999D5491C563D17A993D9B4A18F401514D87C6430E0E4031F223E4 | |||
| 3368 | Activator WF X10.xx.exe | C:\Windows\s.txt | text | |
MD5:FA19C41E099F85AE05AFADEE6BADF787 | SHA256:51042A4B41B948EC0117C5E139A253B14511B7029A31B7D39F411073BC770D76 | |||
| 2652 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:C7A752A70E0F841D32E1CA3E668B5147 | SHA256:AEDA66023850EE3D7E16E9F16D23F9637C803533A4DD01A10EAACAF446D8E75B | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
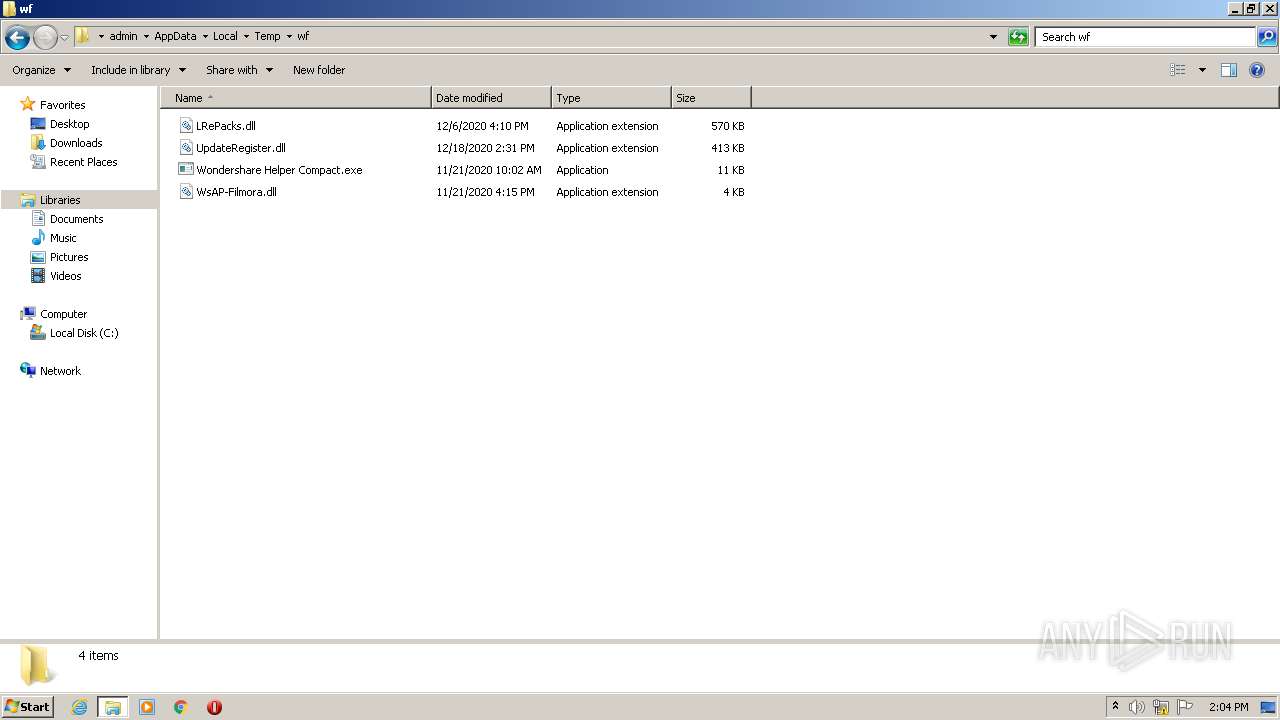
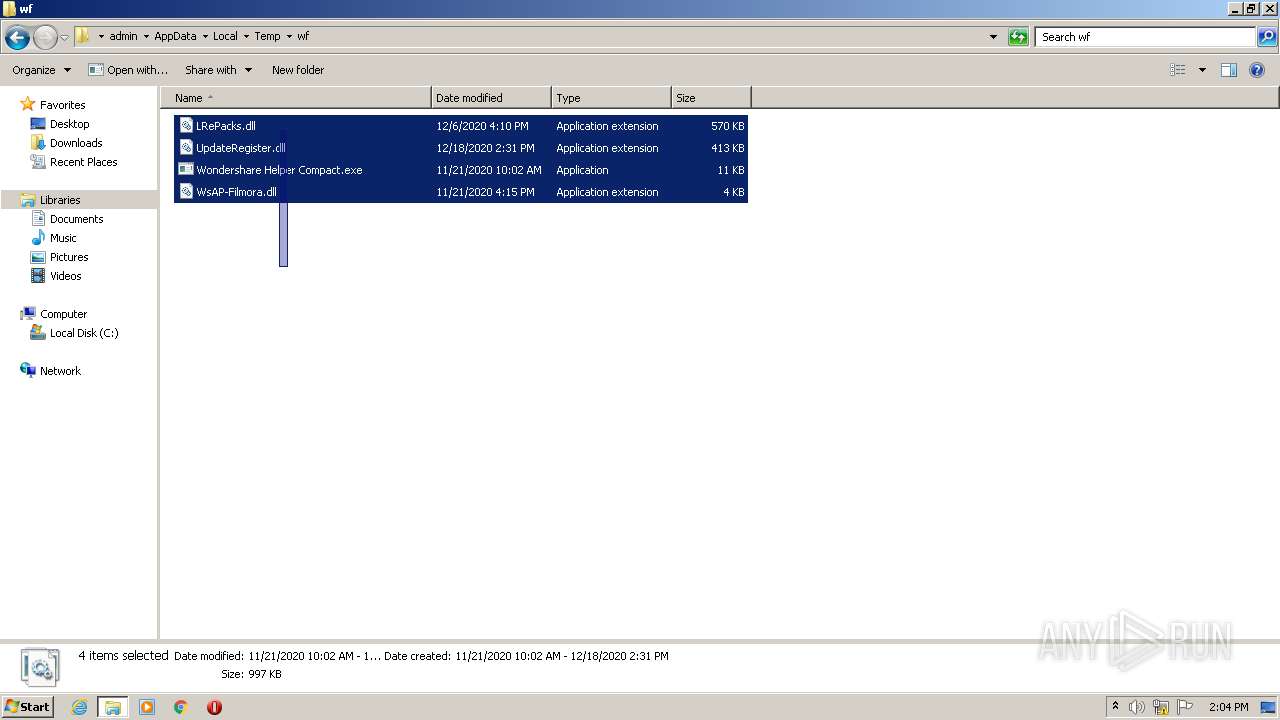
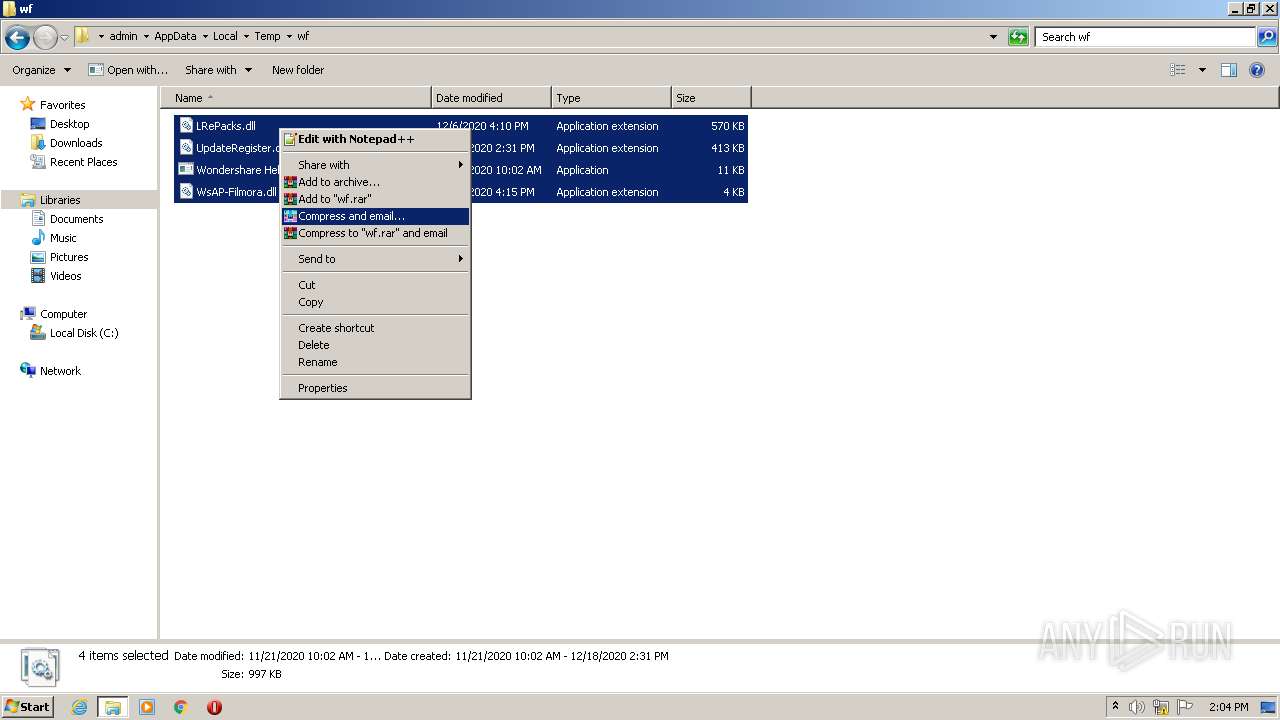
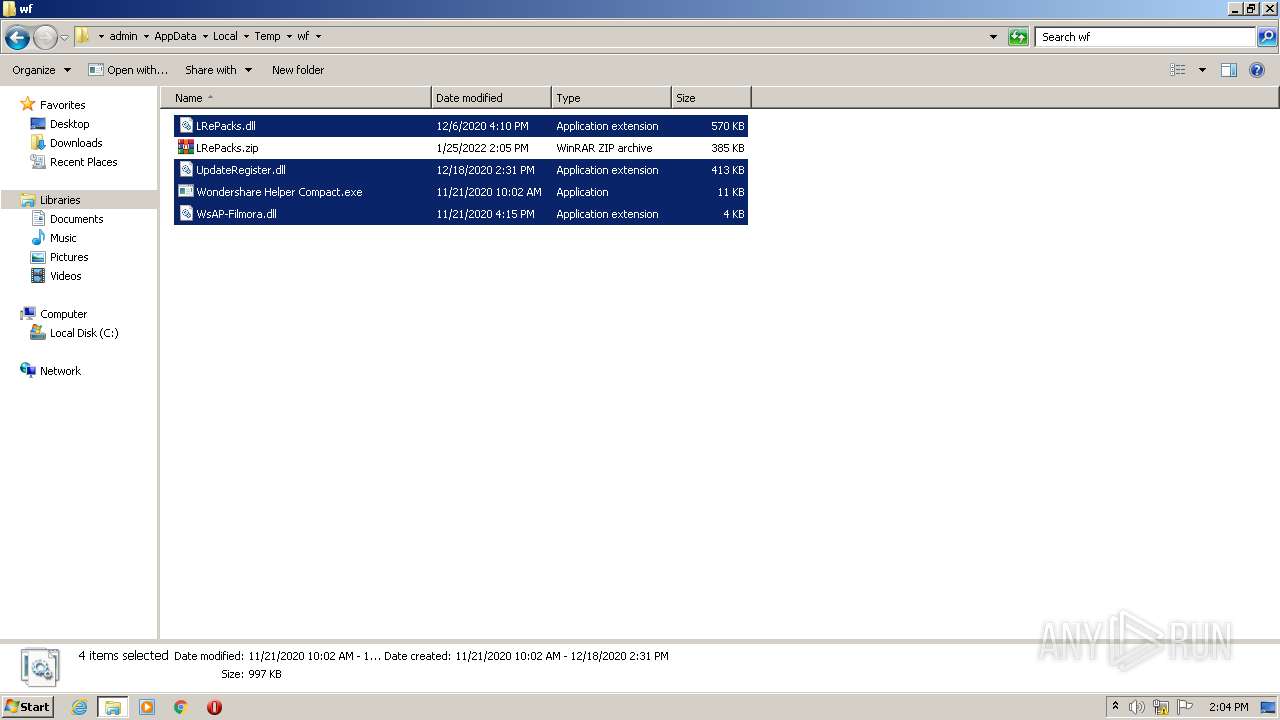
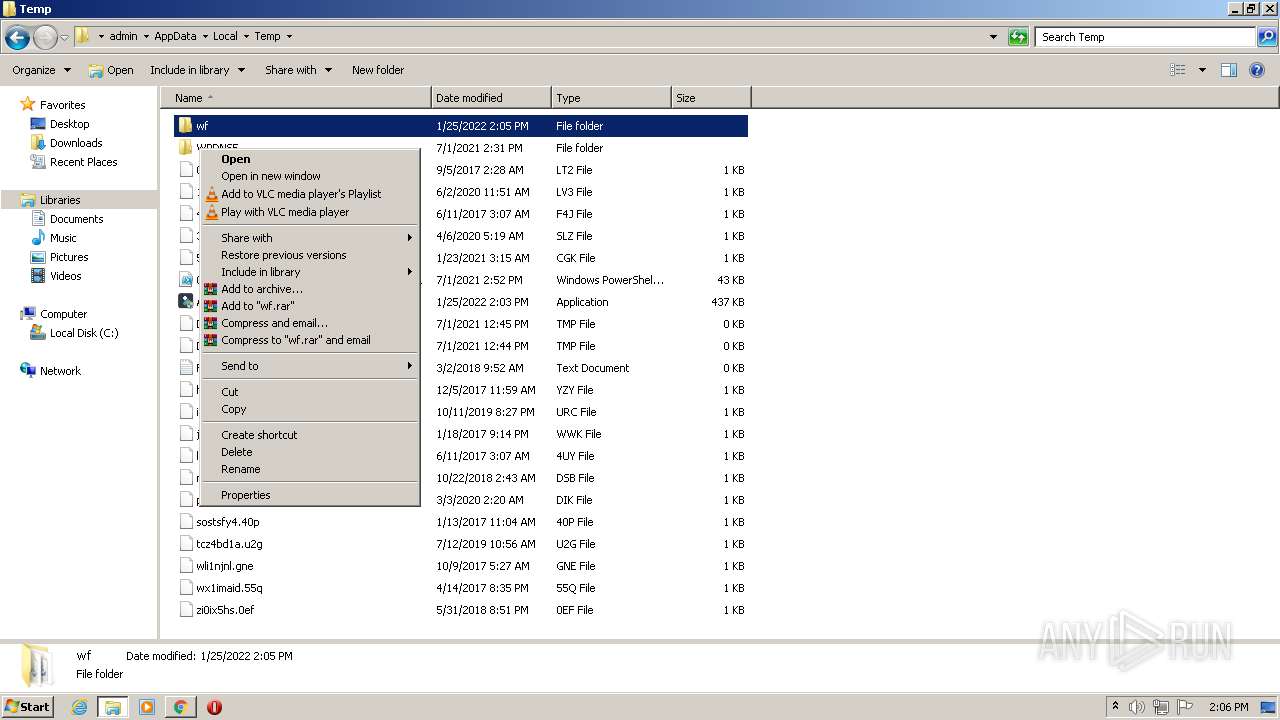
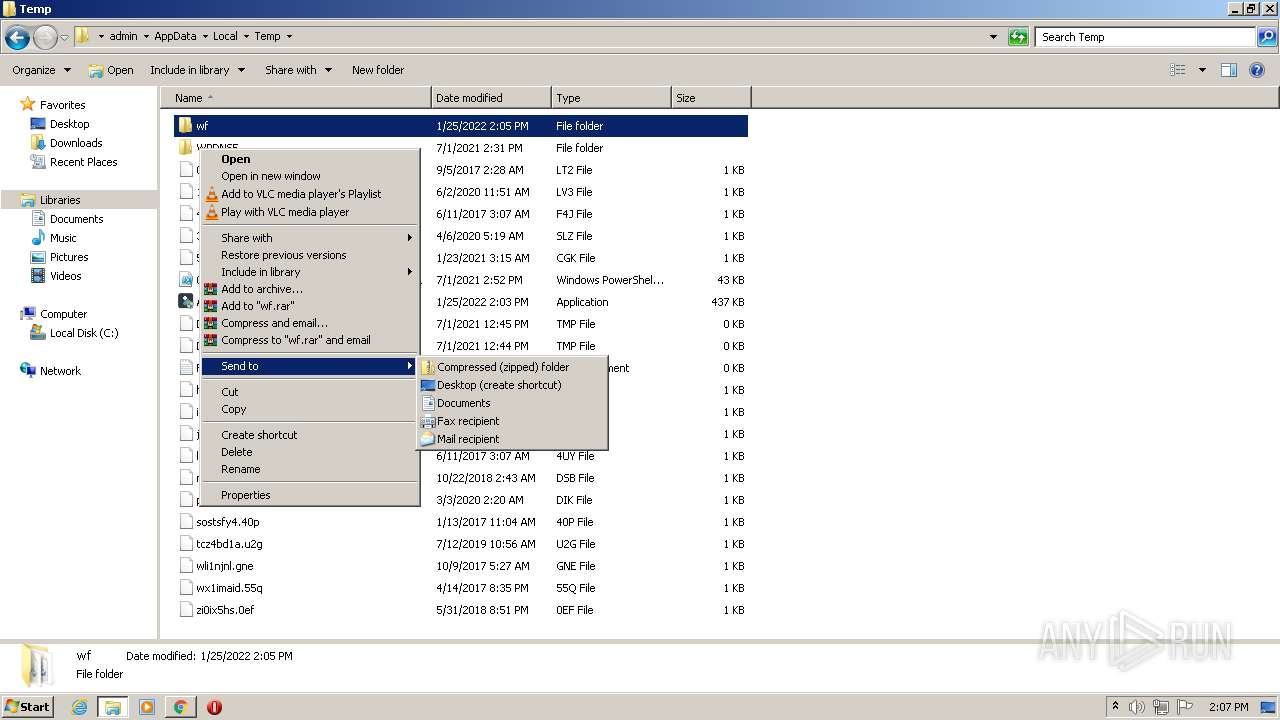
| 3368 | Activator WF X10.xx.exe | C:\Users\admin\AppData\Local\Temp\wf\Wondershare Helper Compact.exe | executable | |
MD5:45FBD7B4A57994922D58541202713336 | SHA256:0C3169530C3209FA9AA5DCAD6C28CB6B7DDEF63DBA8C784AC603D9293FD3A053 | |||
| 3368 | Activator WF X10.xx.exe | C:\Users\admin\AppData\Local\Temp\wf\UpdateRegister.dll | executable | |
MD5:126E54A44EF54E8F1DE799646CC1478F | SHA256:AAF6EA616C4A572C70E4915490717BF4FAD023331AB95DB8A769E4D8DDF777D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
56
DNS requests
34
Threats
2
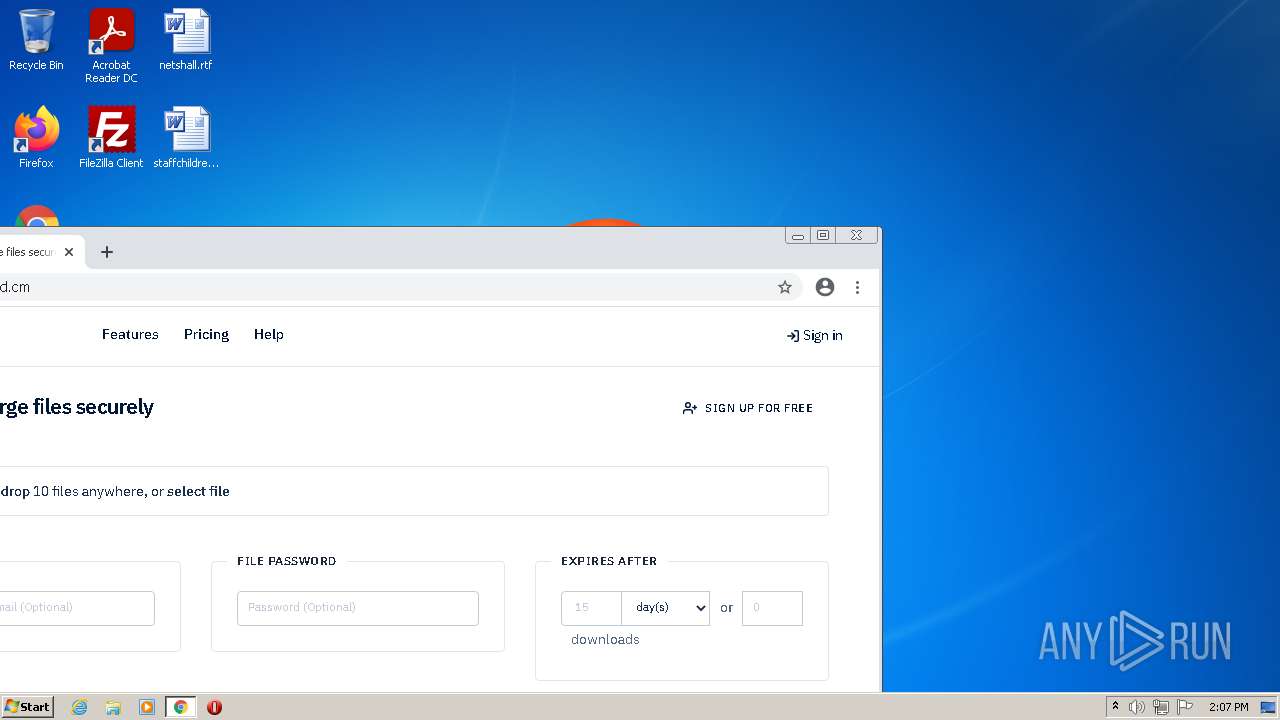
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | — | — | whitelisted |
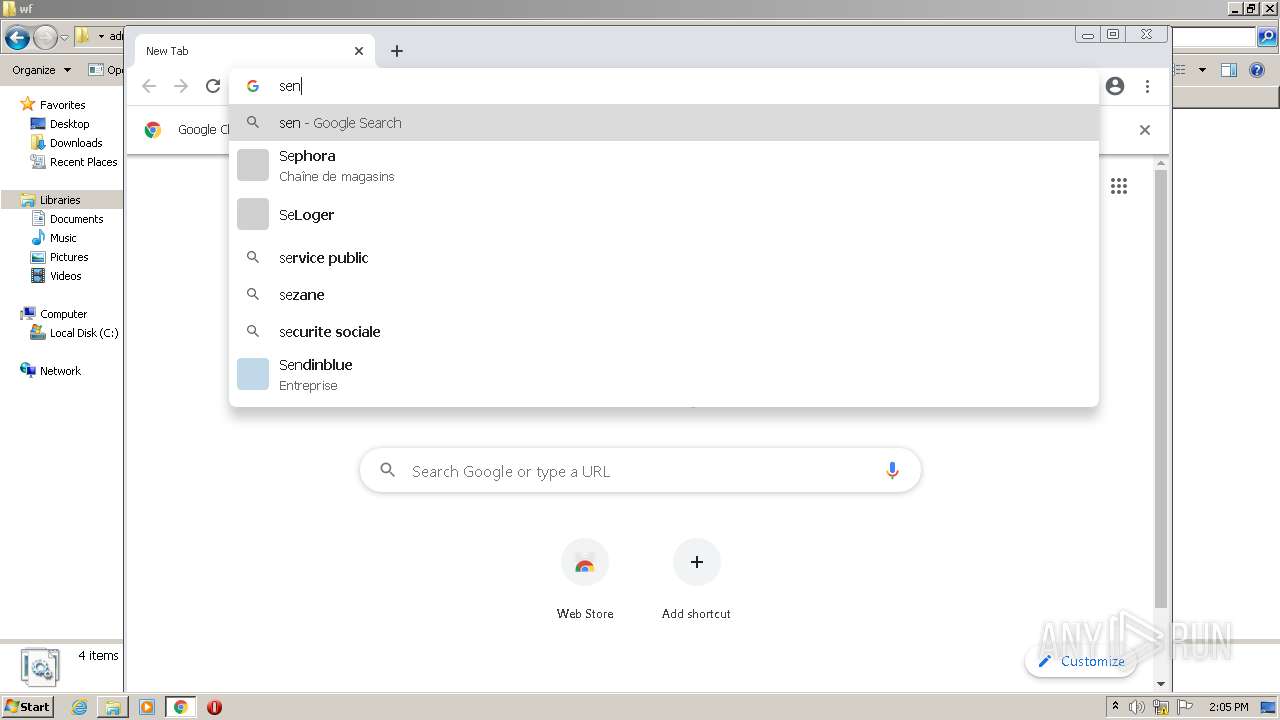
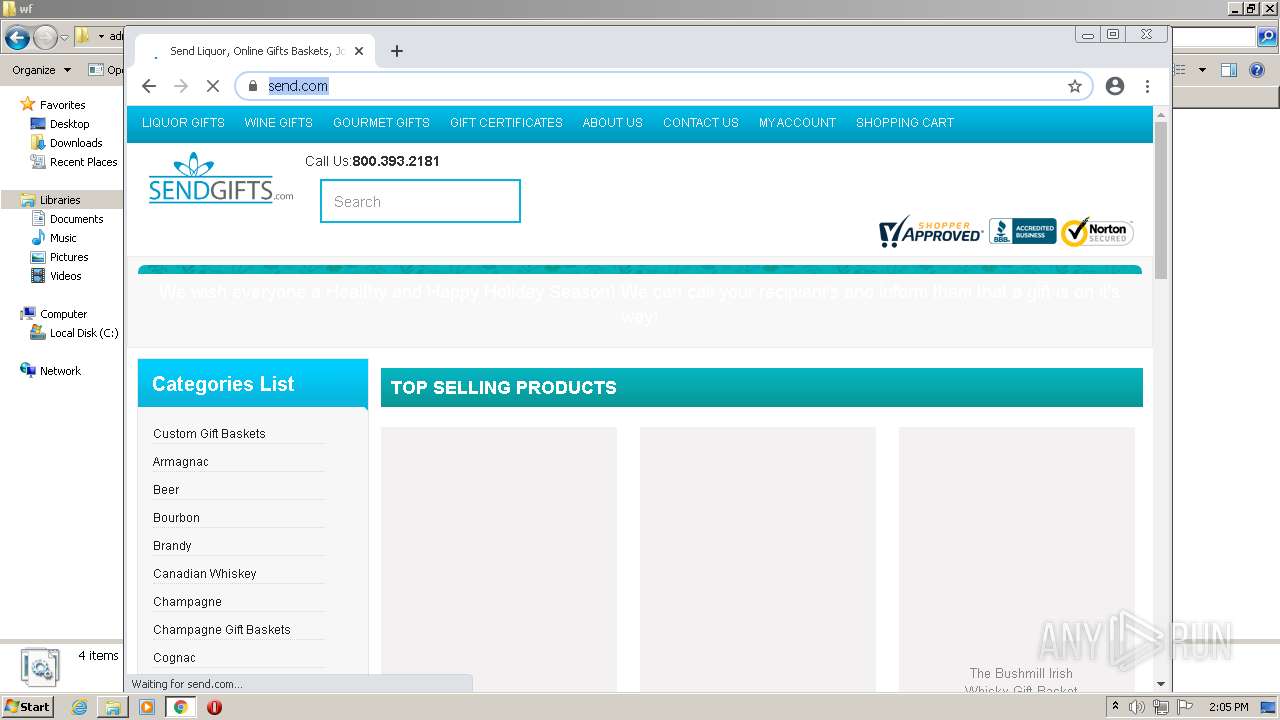
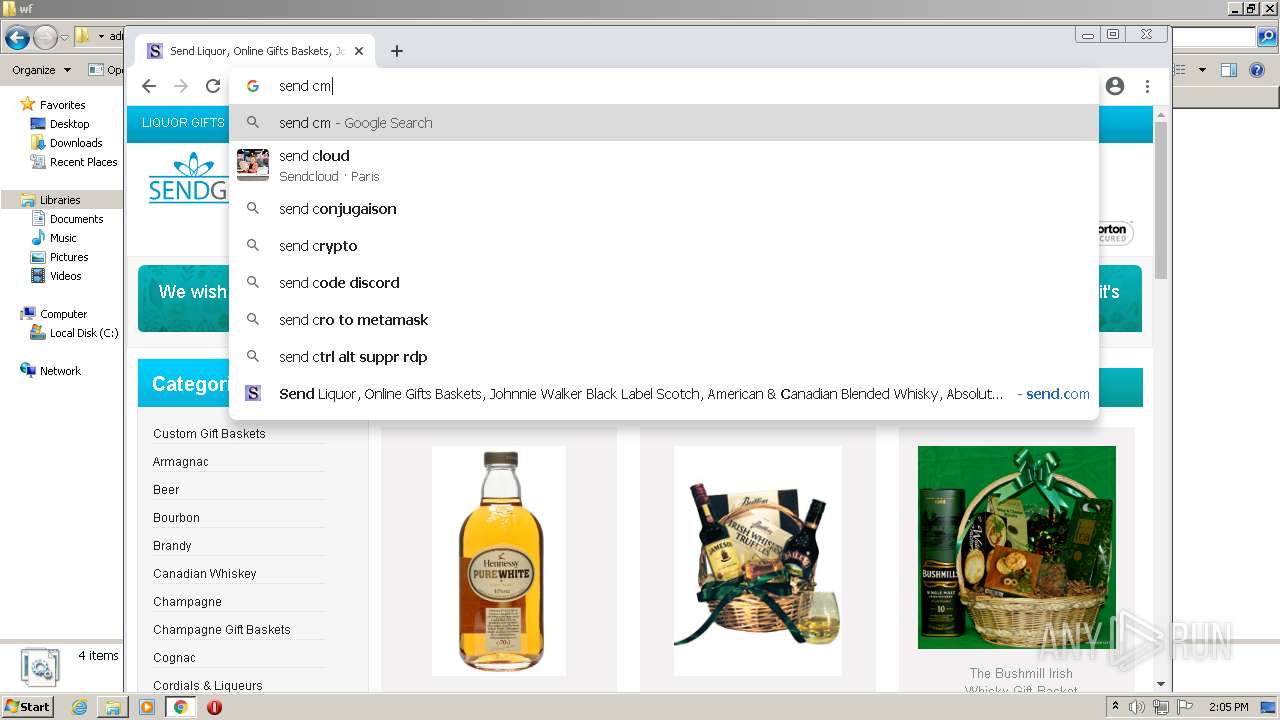
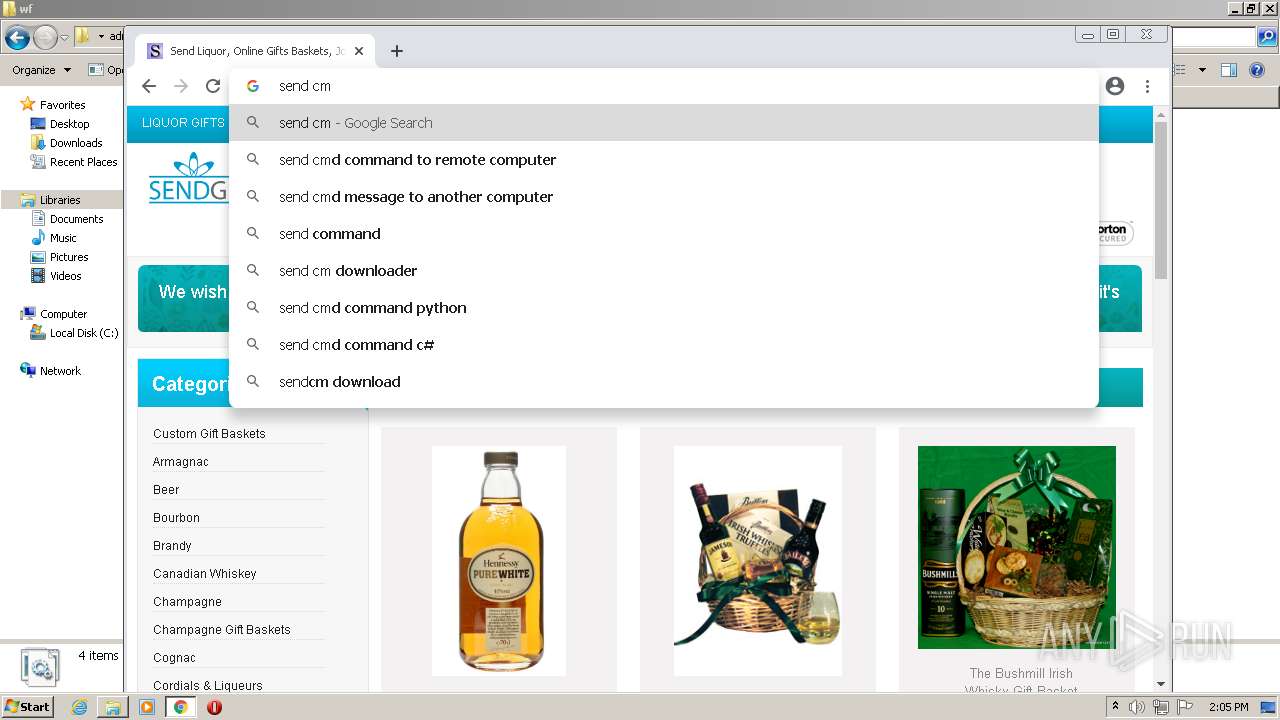
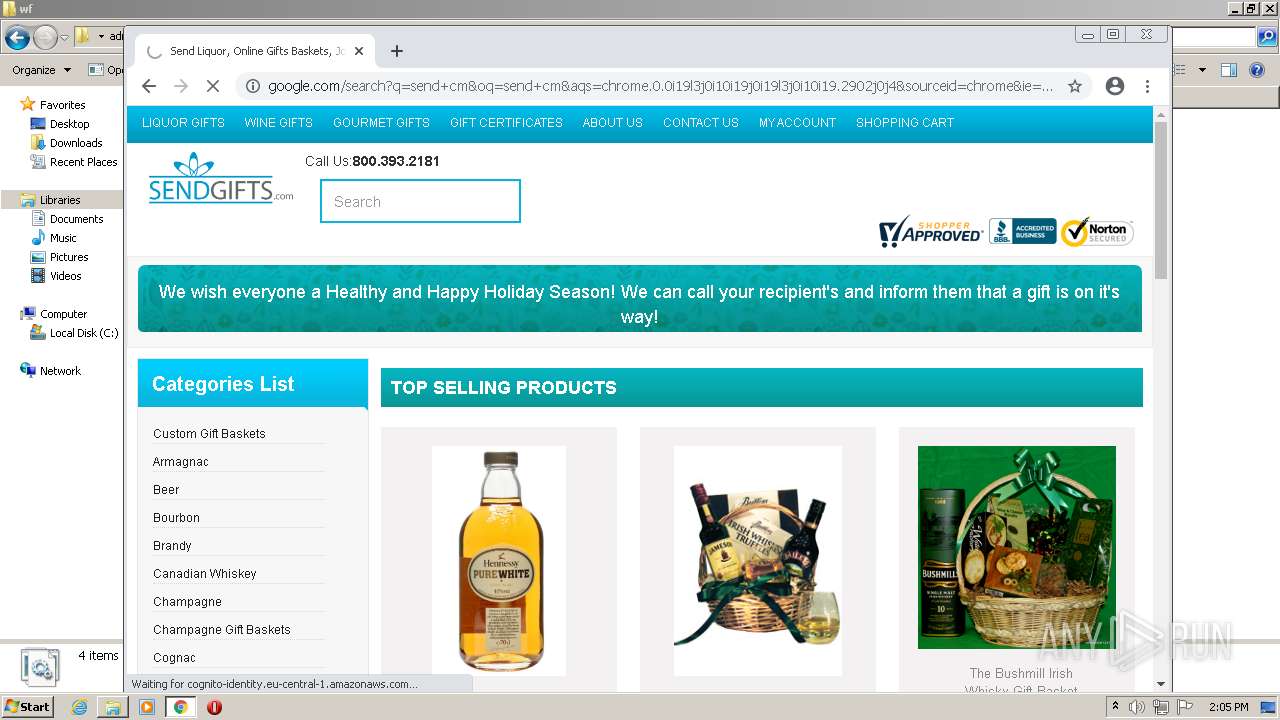
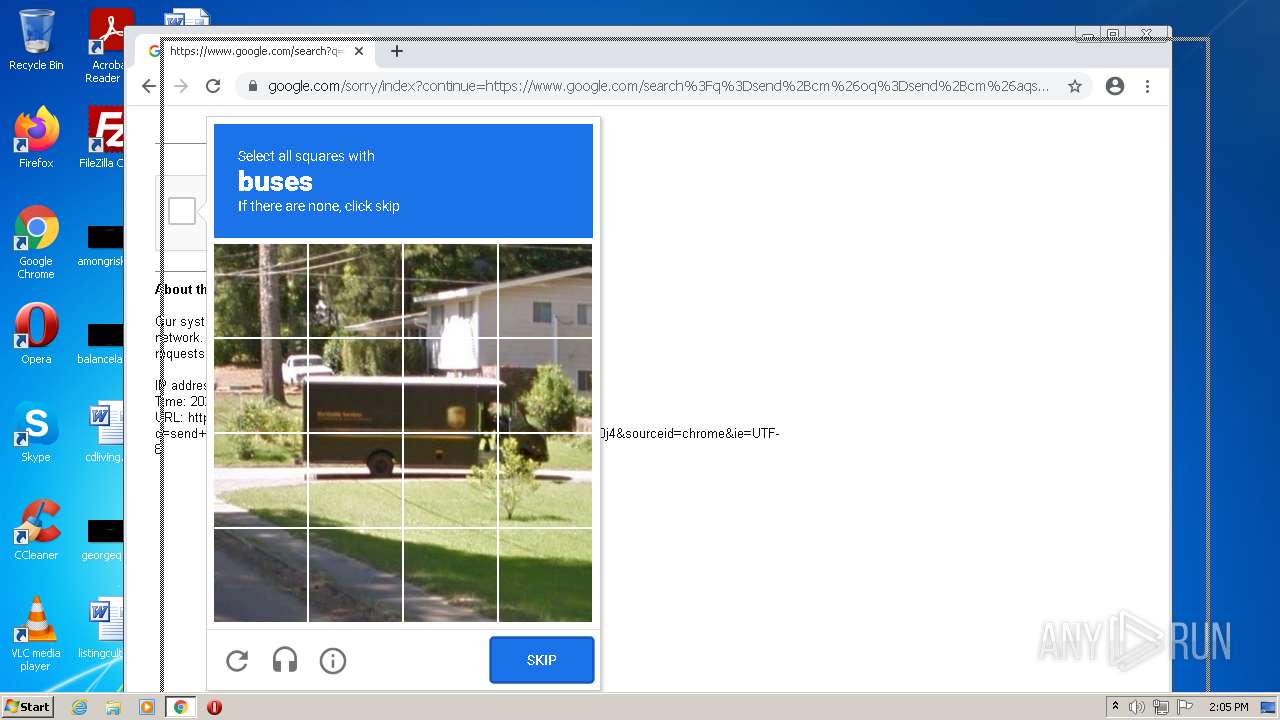
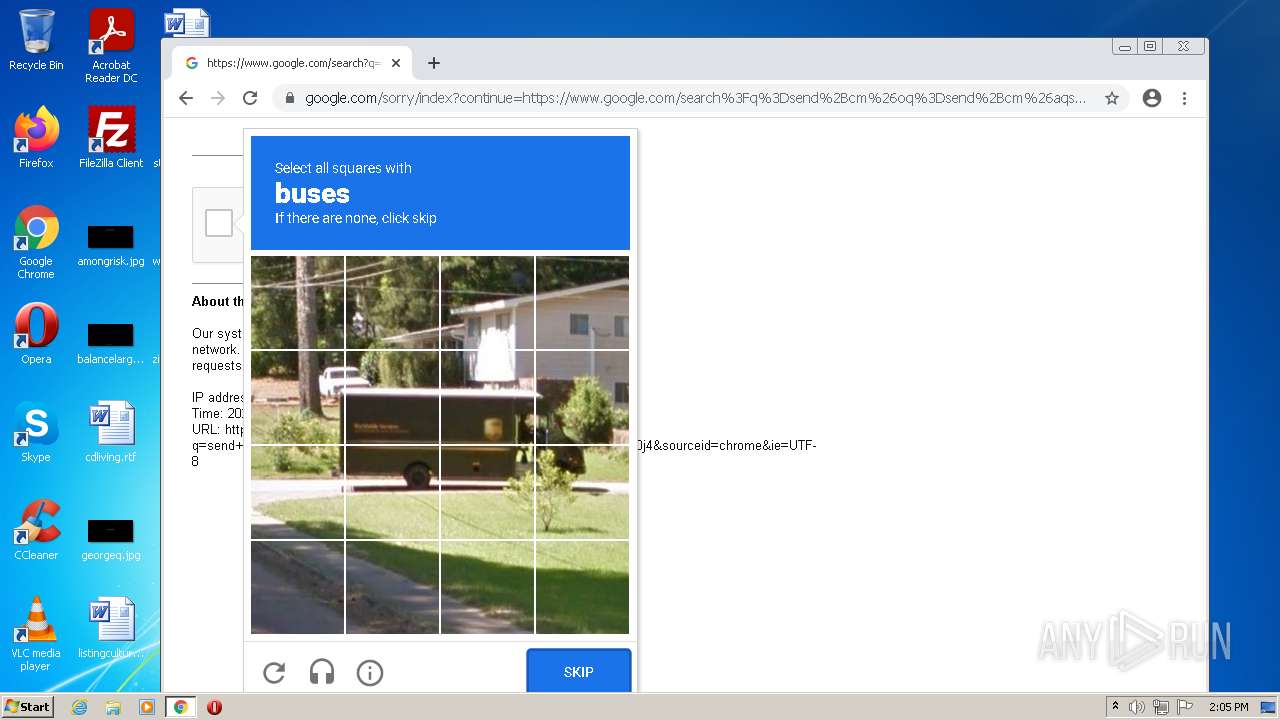
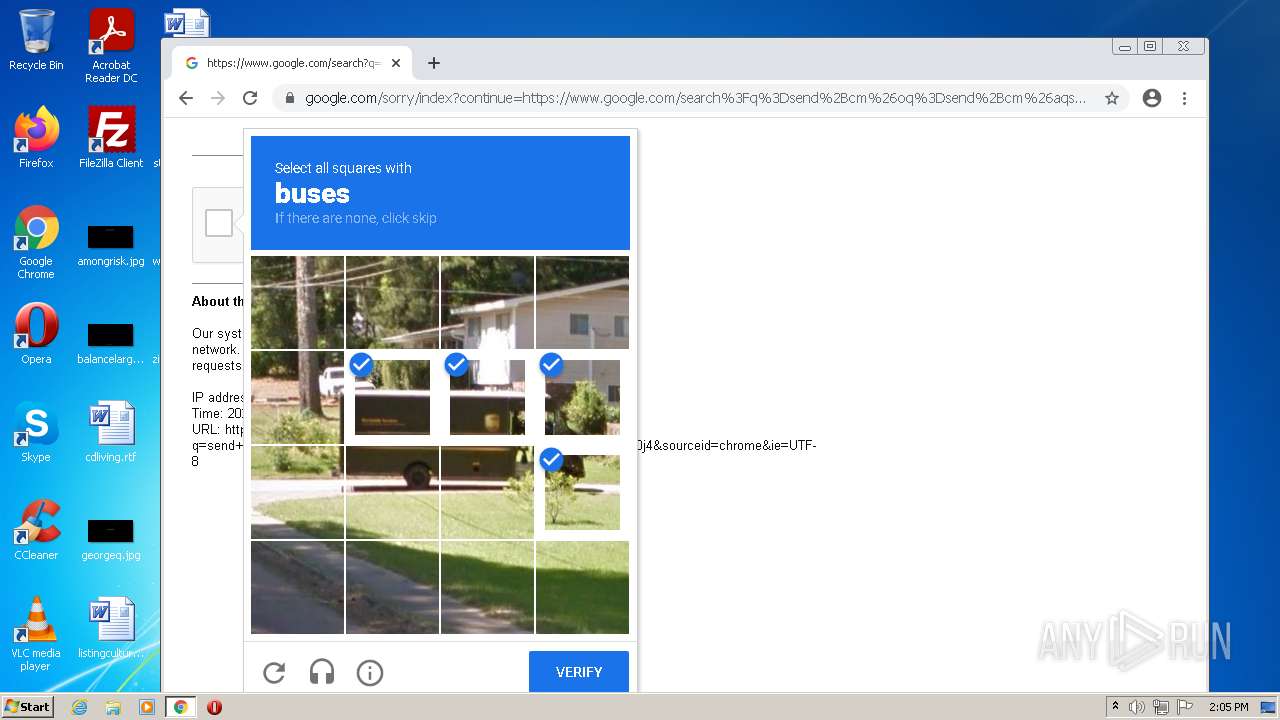
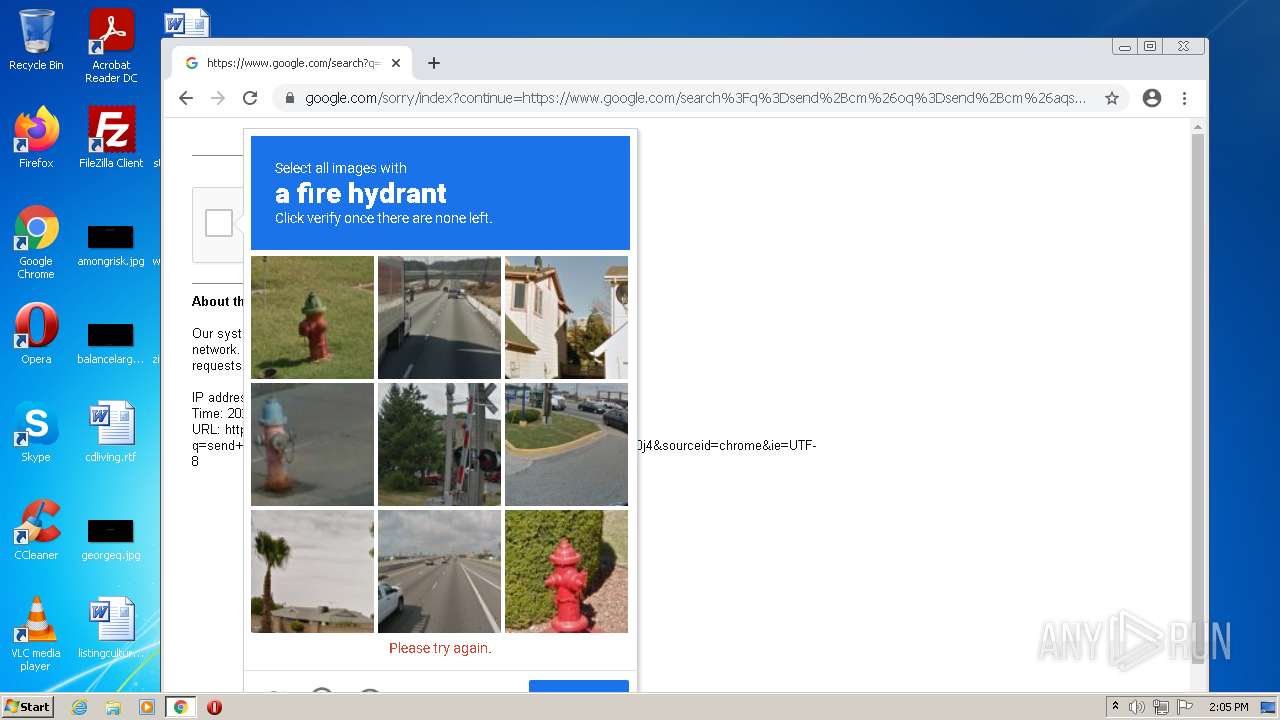
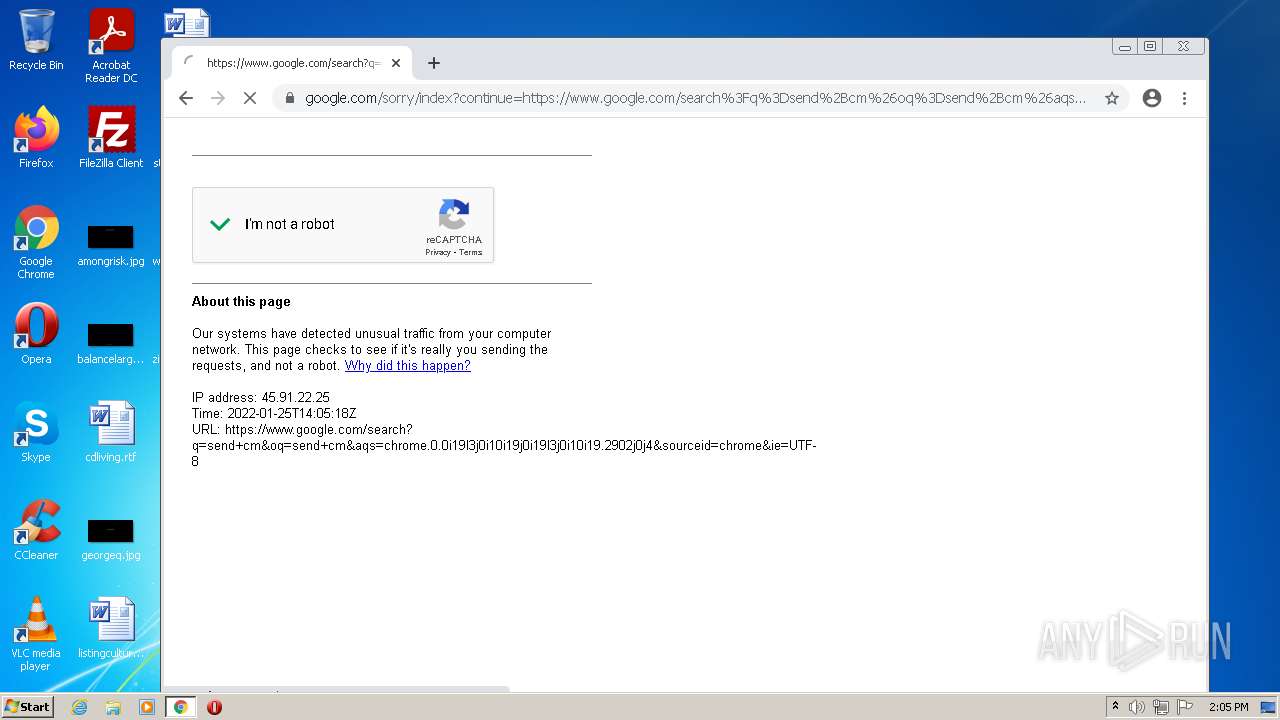
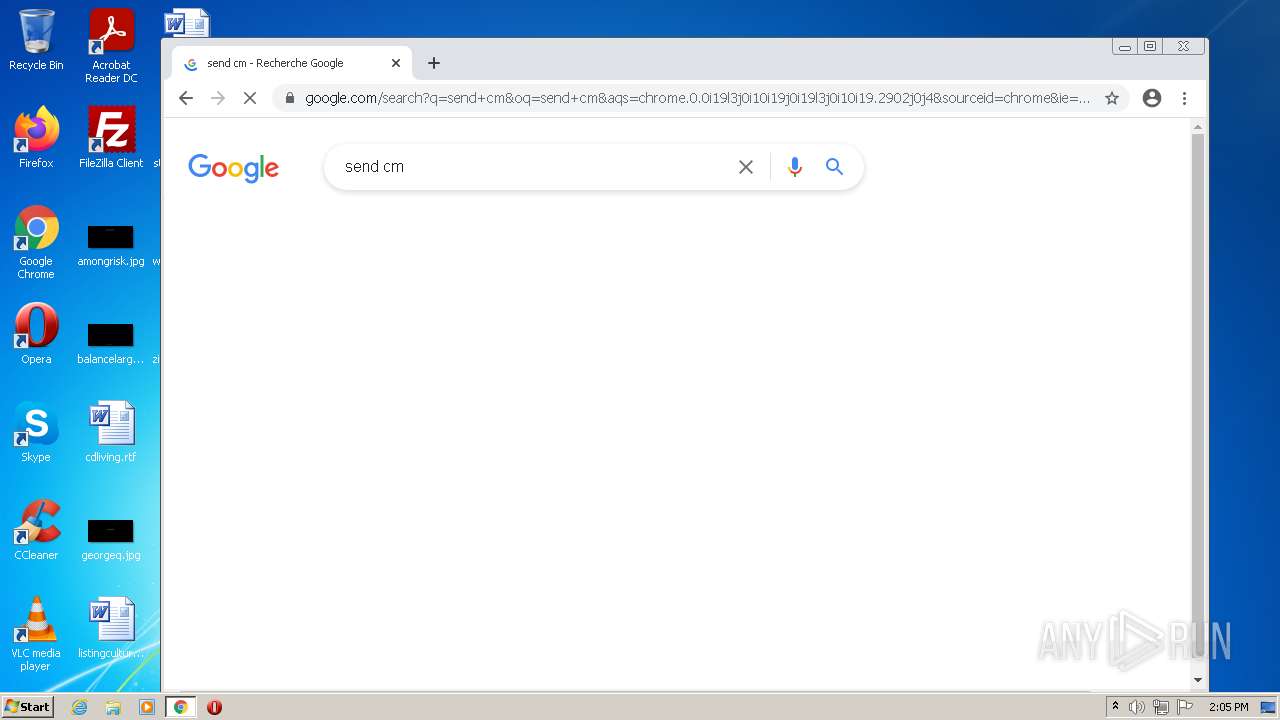
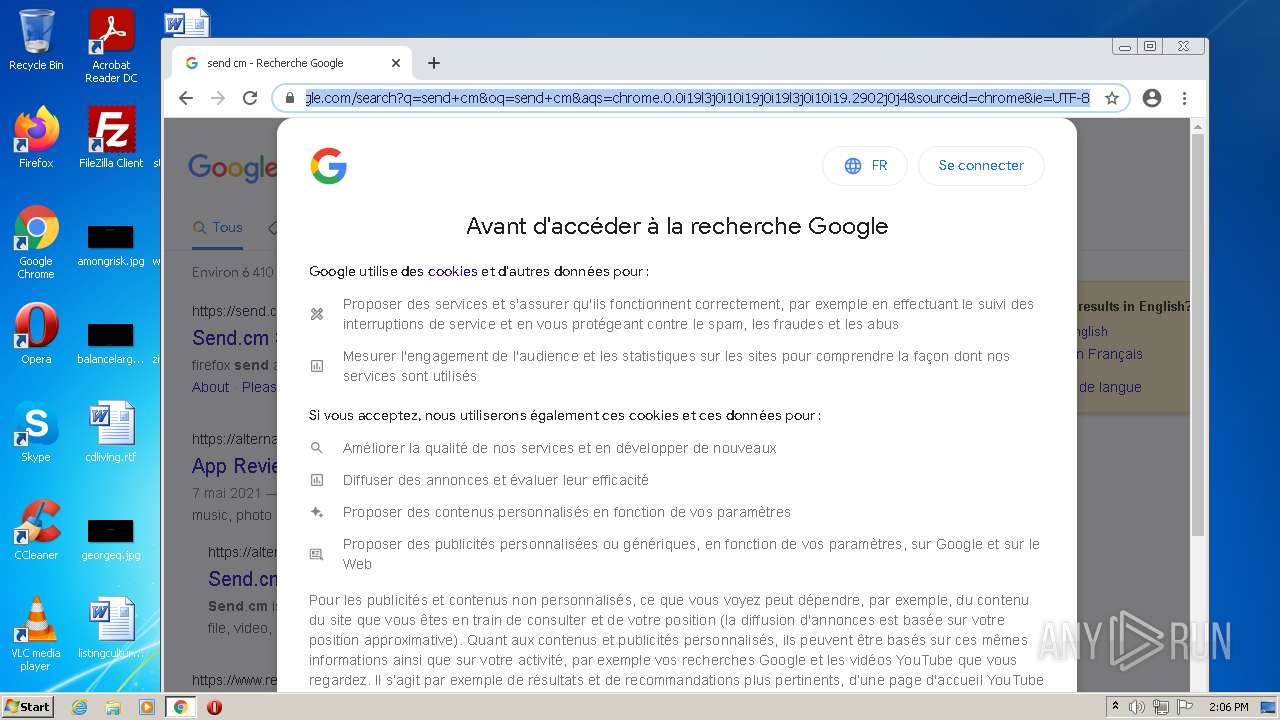
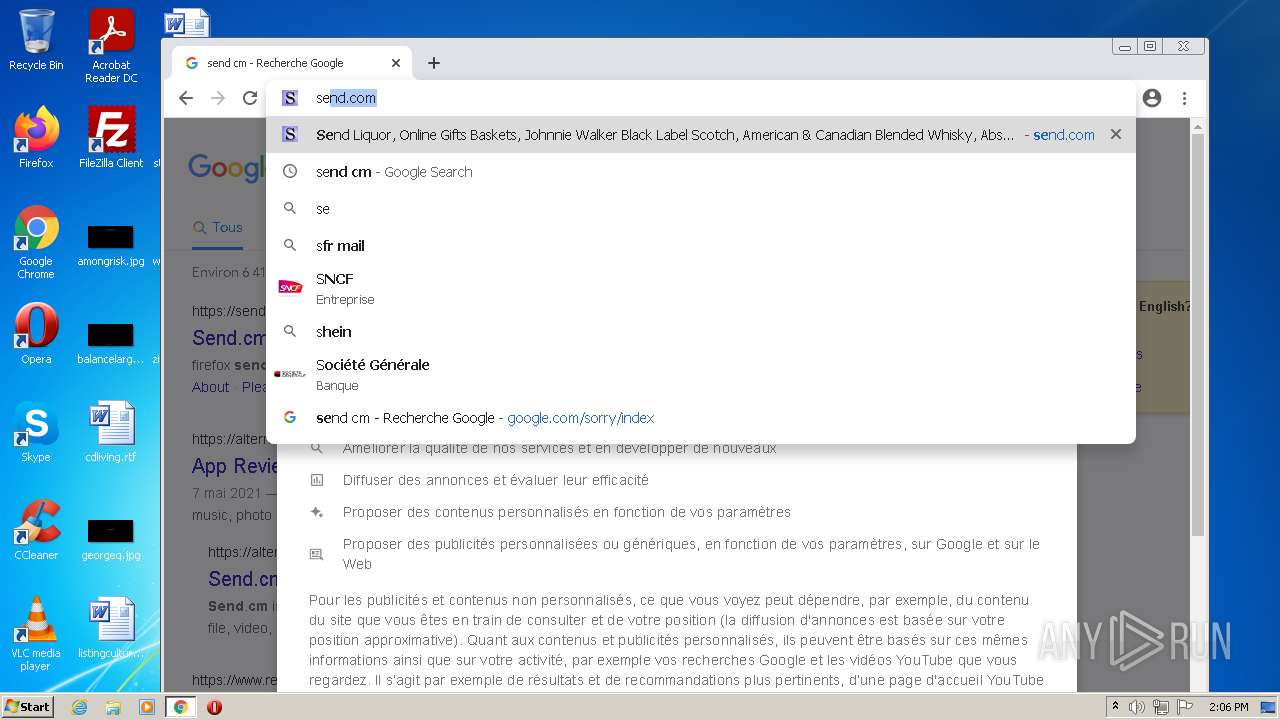
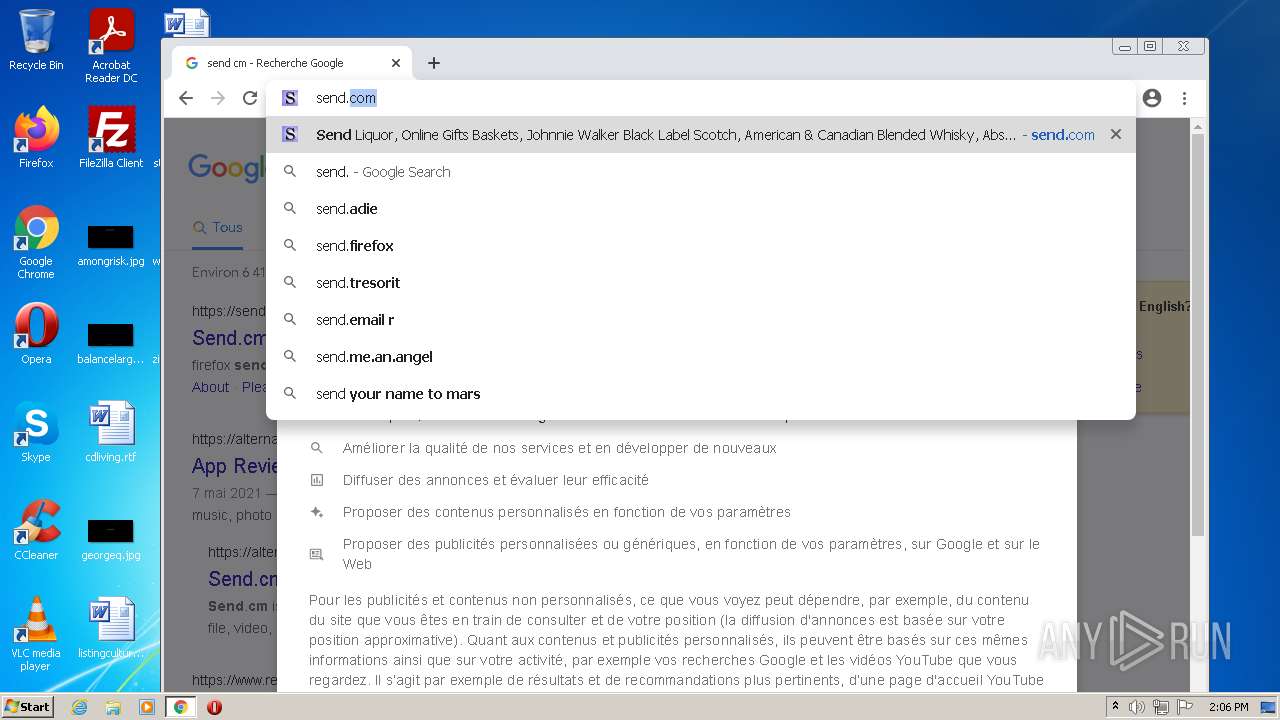
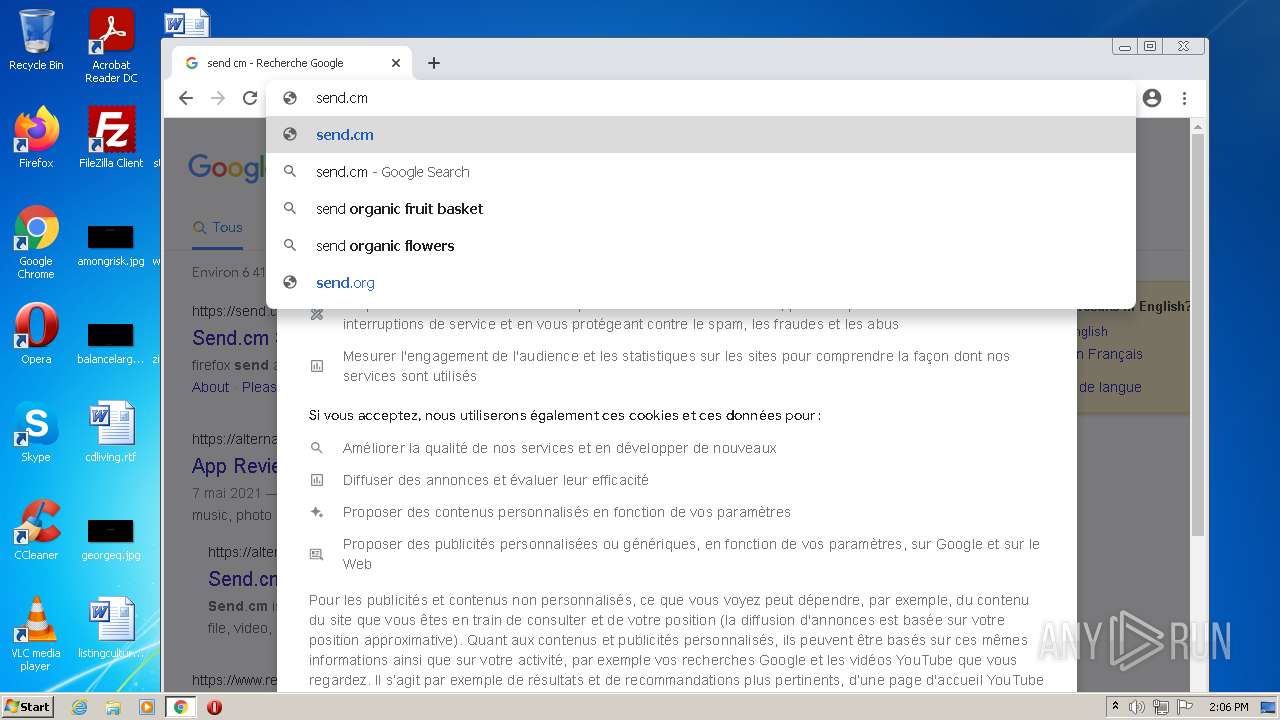
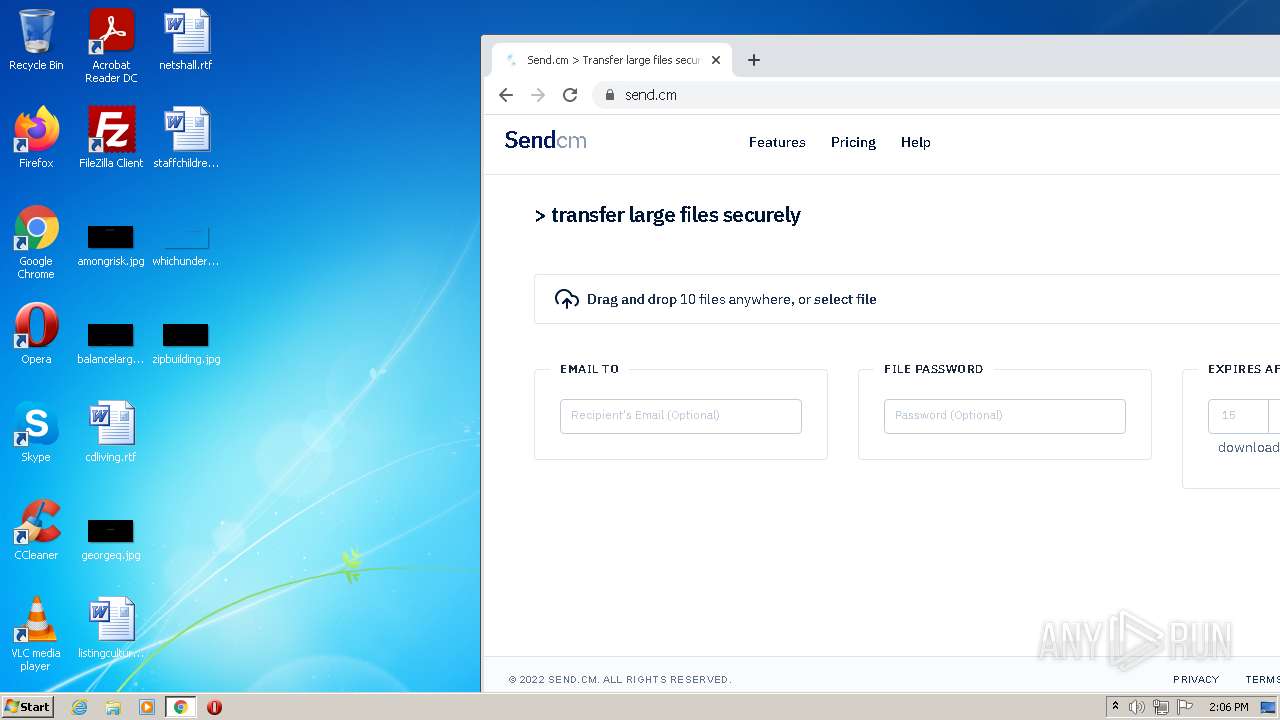
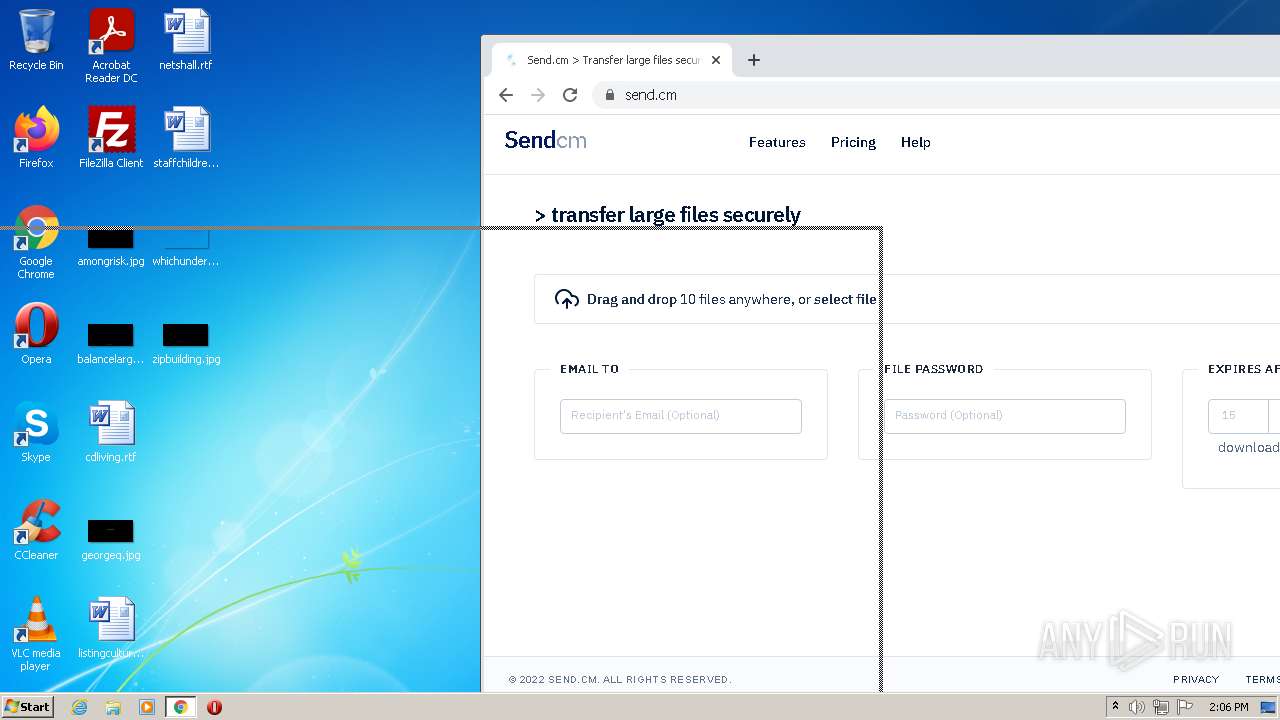
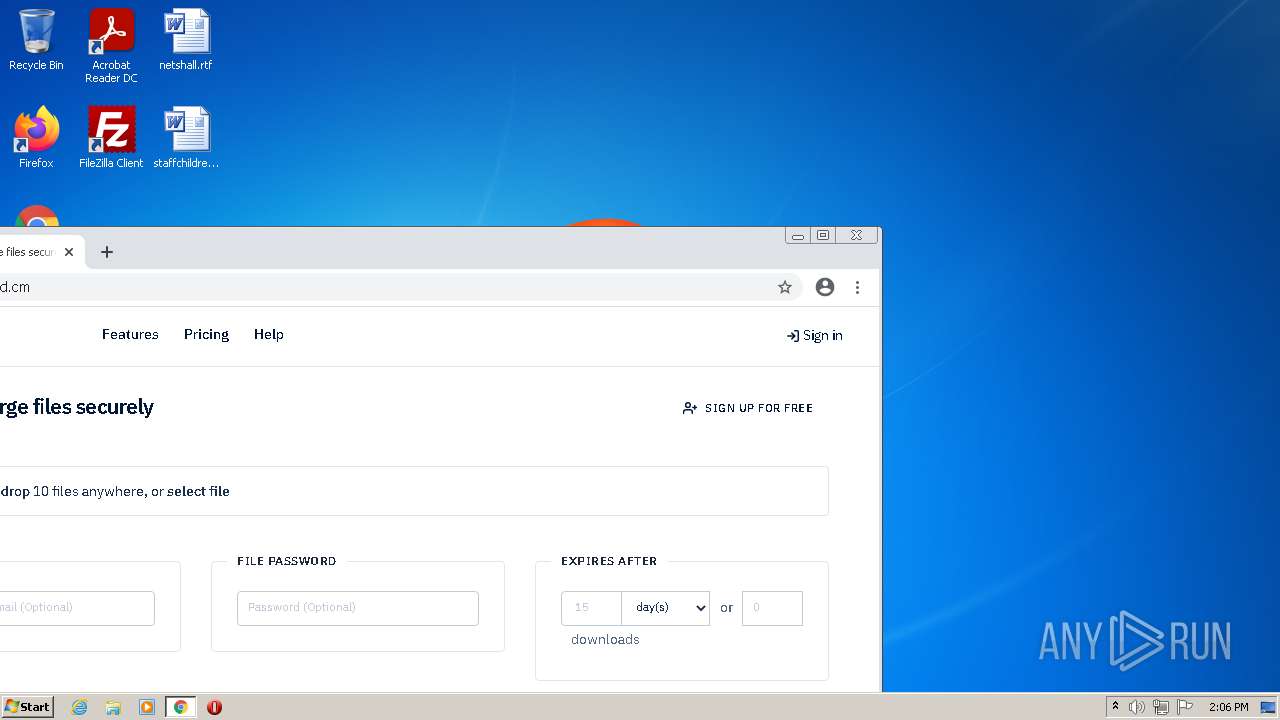
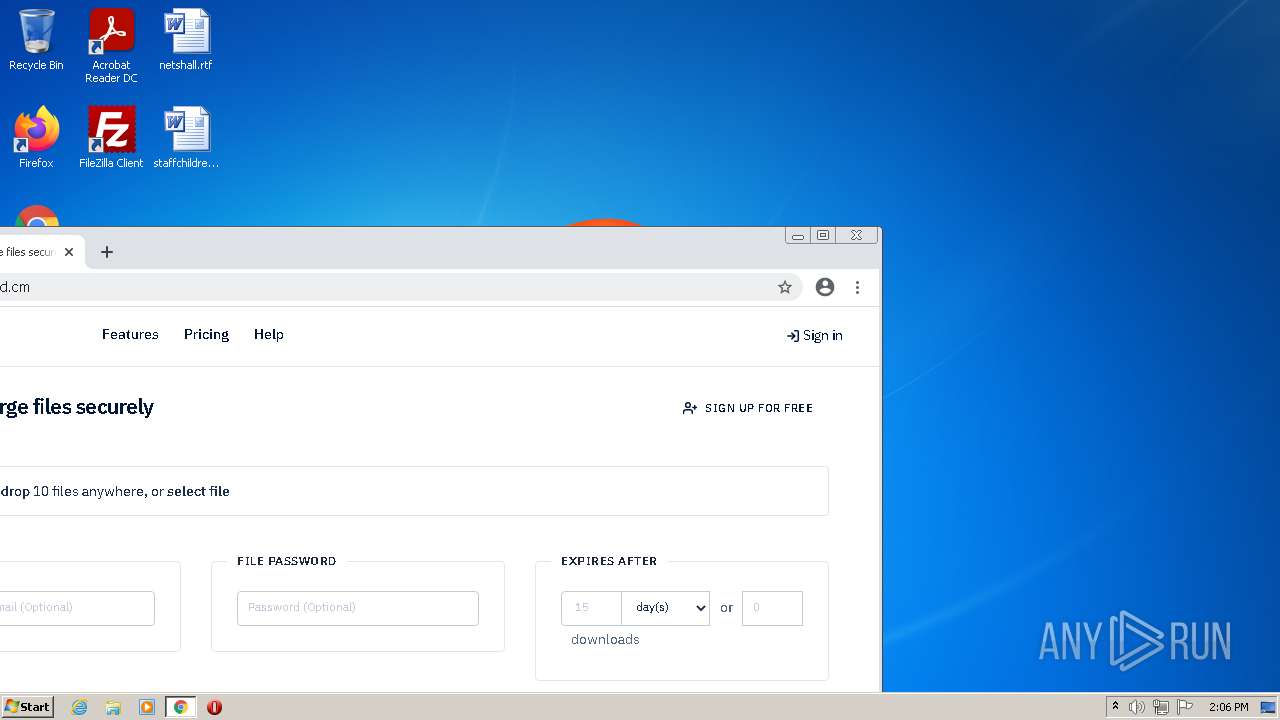
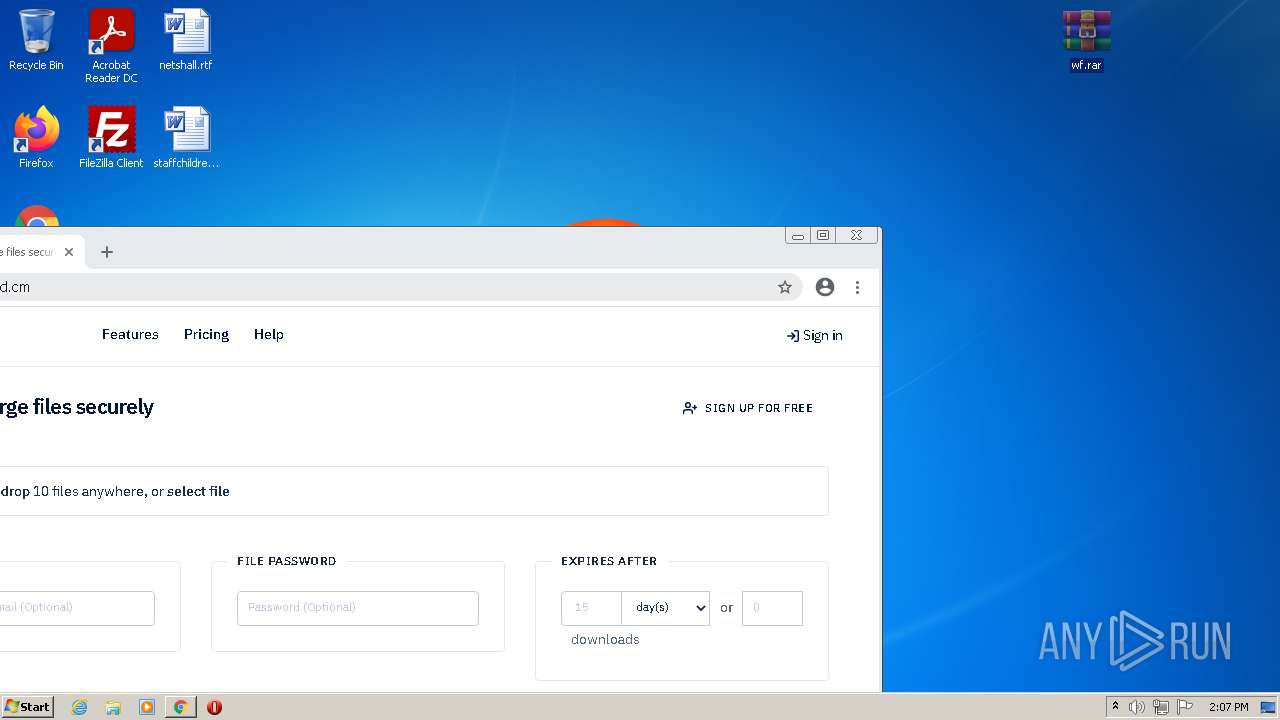
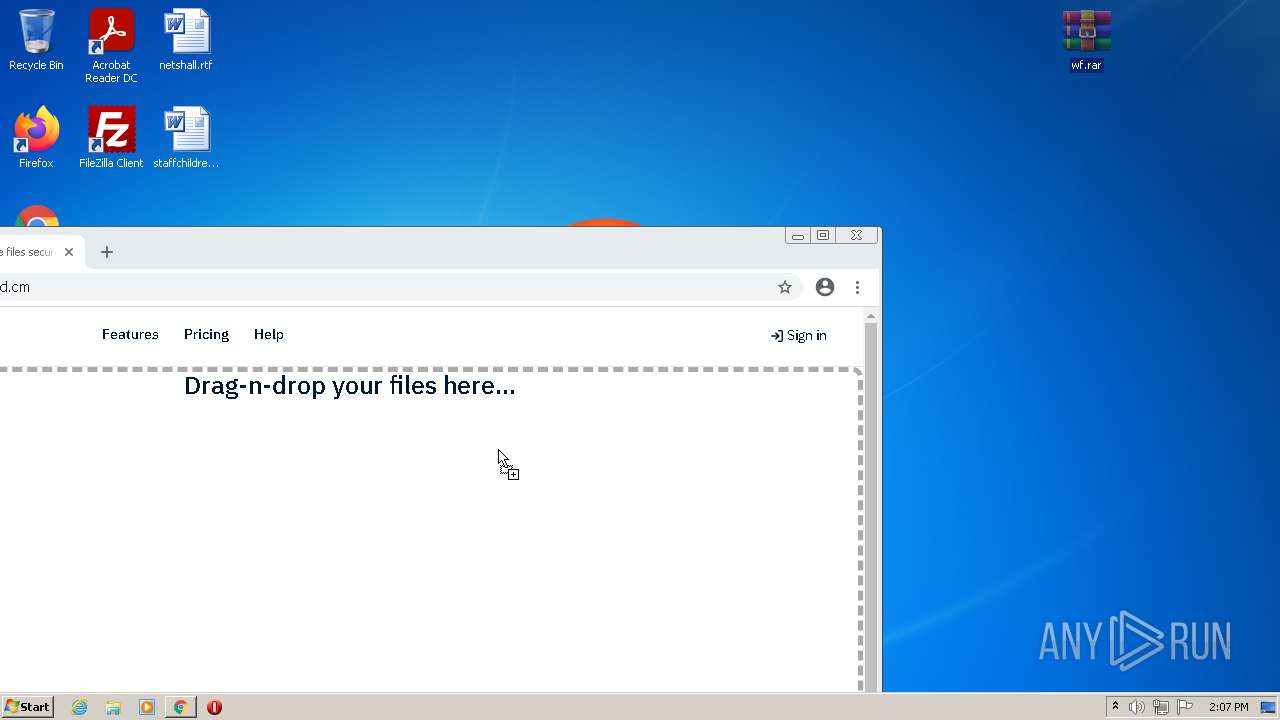
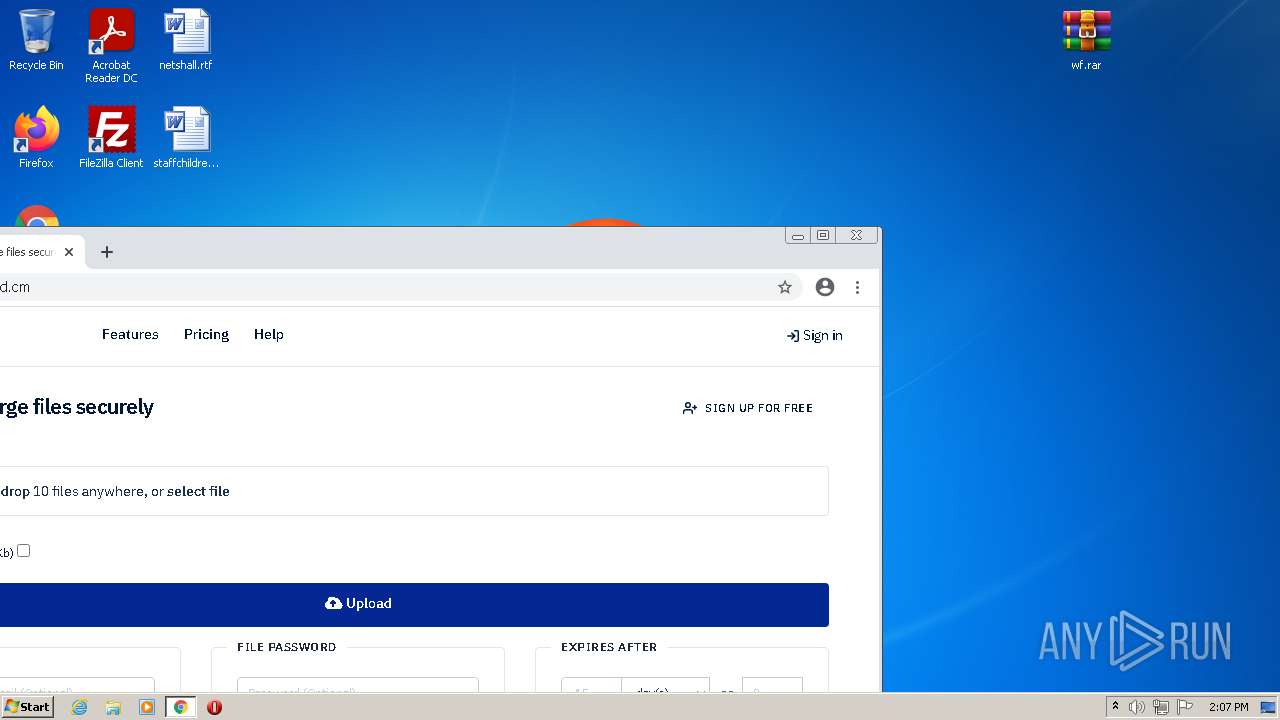
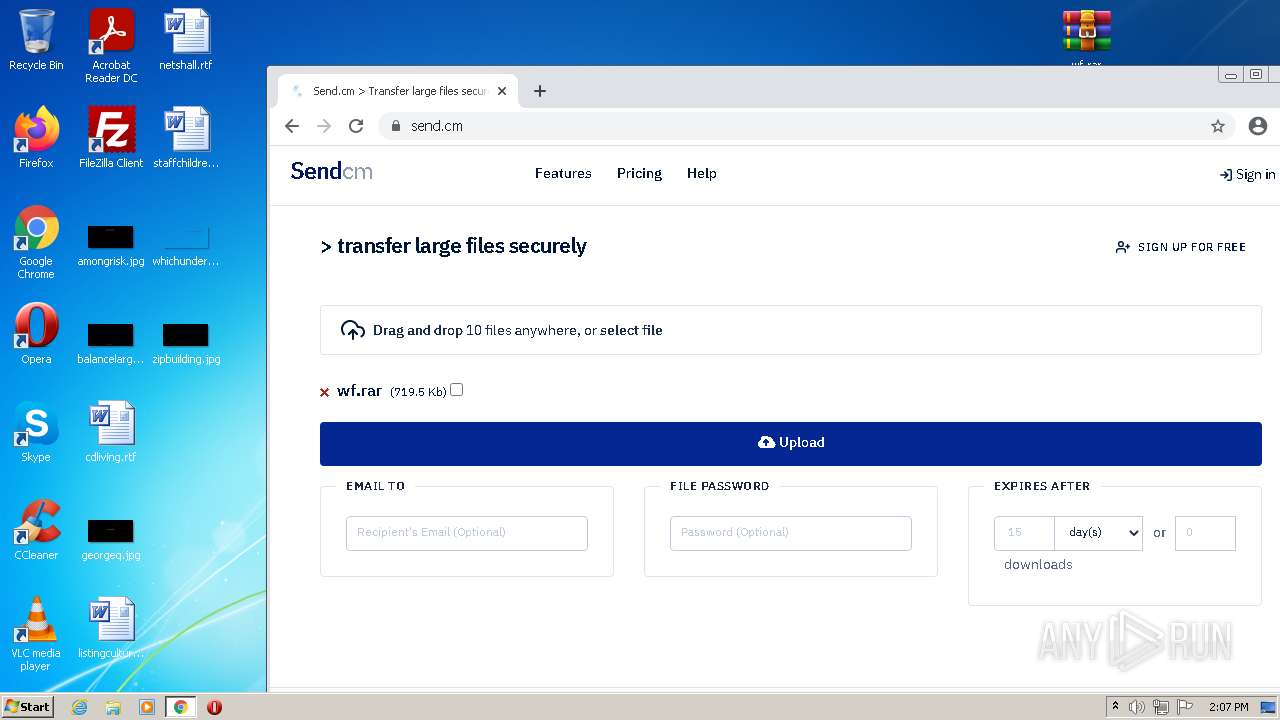
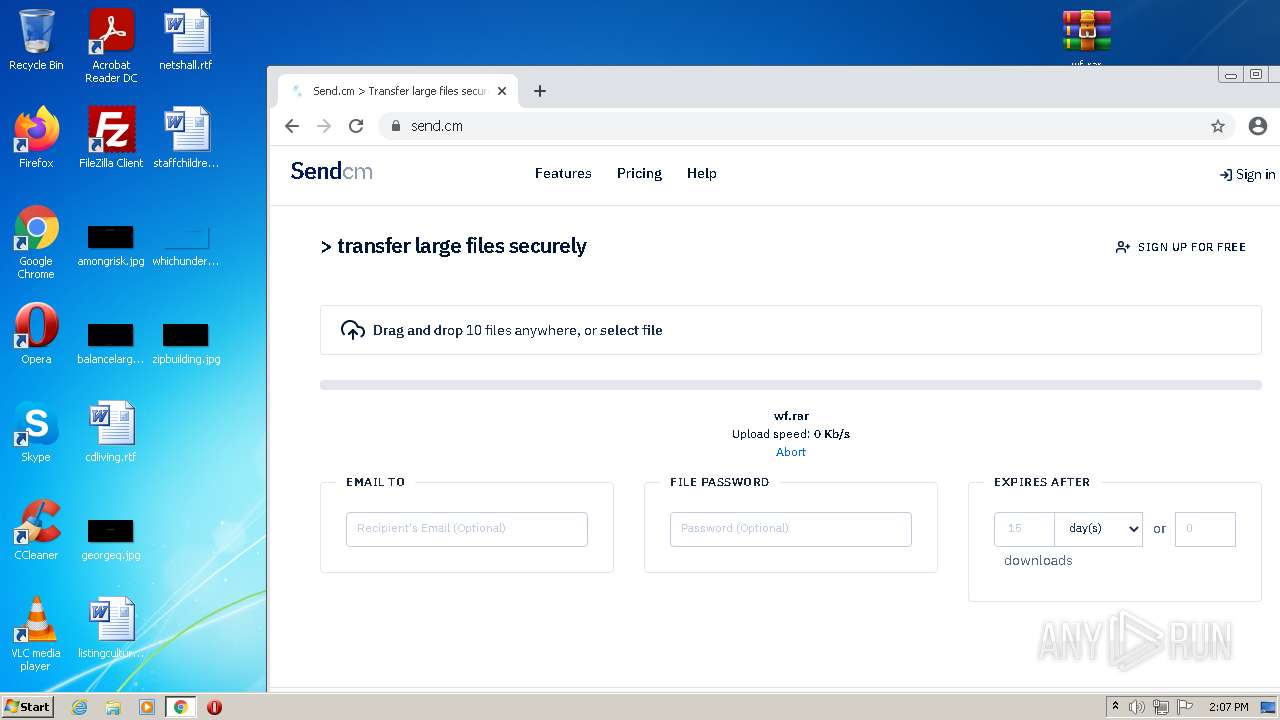
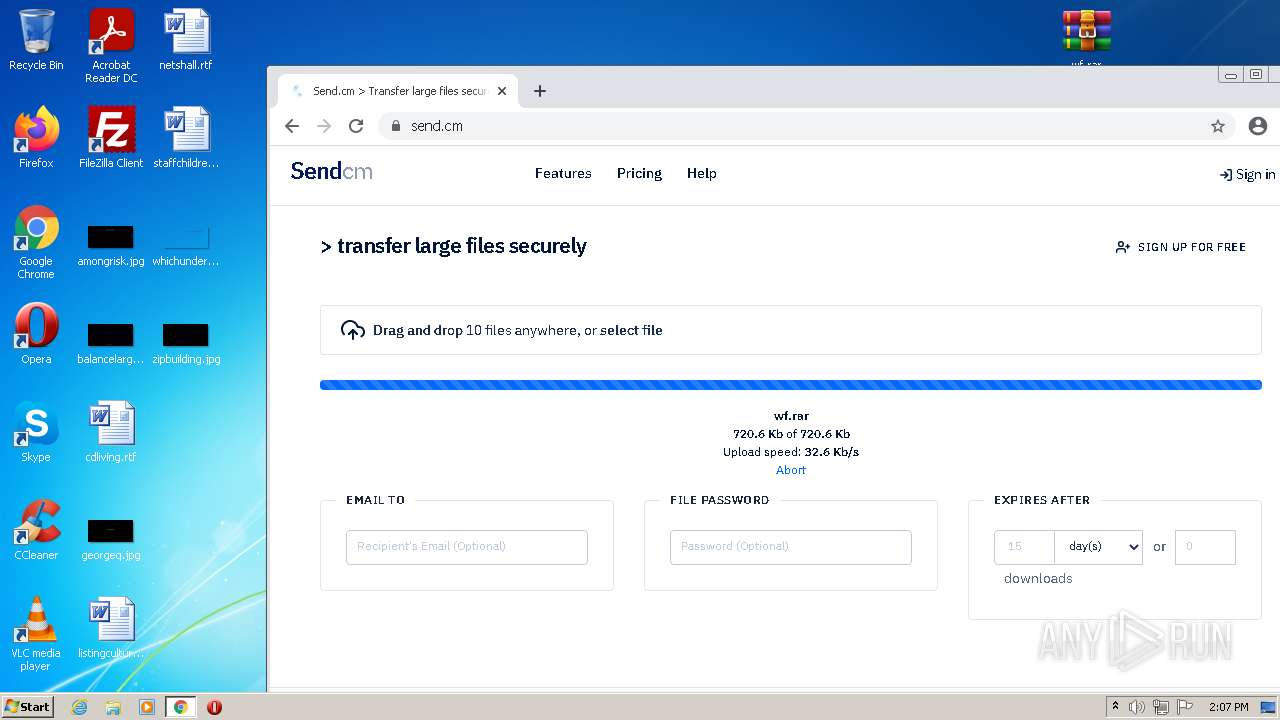
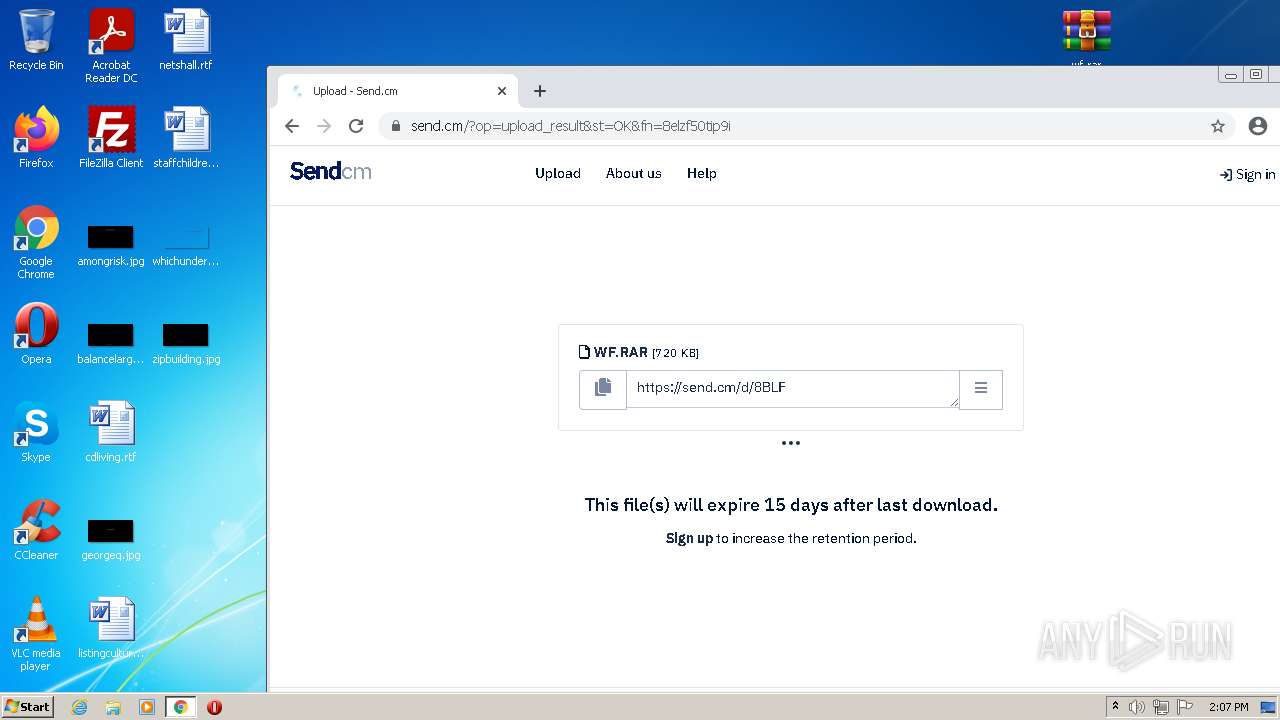
852 | chrome.exe | GET | 301 | 172.67.68.194:80 | http://send.cm/ | US | — | — | suspicious |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | binary | 9.74 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | binary | 5.66 Kb | whitelisted |
924 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/etfhywtptnfps2qeuyx6p57rsa_47/khaoiebndkojlmppeemjhbpbandiljpe_47_win_eiam27nsc3cmgynazgpf5duaty.crx3 | US | crx | 5.45 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | abr | 141 b | whitelisted |
852 | chrome.exe | GET | 302 | 50.242.12.196:80 | http://send.com/ | US | binary | 1.32 Kb | unknown |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | crx | 9.06 Kb | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/etfhywtptnfps2qeuyx6p57rsa_47/khaoiebndkojlmppeemjhbpbandiljpe_47_win_eiam27nsc3cmgynazgpf5duaty.crx3 | US | abr | 141 b | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 180 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
852 | chrome.exe | 142.250.186.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
852 | chrome.exe | 142.250.185.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 142.250.186.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
852 | chrome.exe | 142.250.186.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.67.36.56:443 | www.shopperapproved.com | — | US | unknown |
852 | chrome.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
852 | chrome.exe | 143.204.215.5:443 | static.sooqr.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
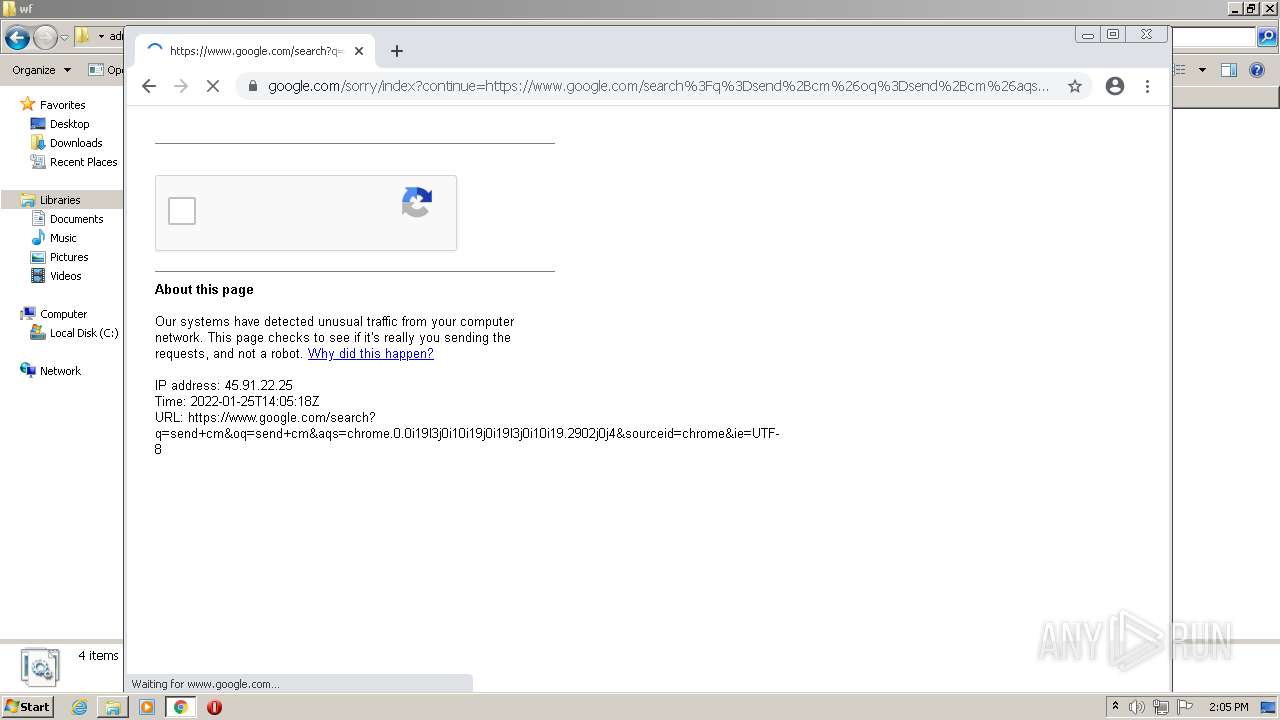
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP gzip decompression failed |
852 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP gzip decompression failed |