| File name: | CornerstoneFoundationRepair.zip |
| Full analysis: | https://app.any.run/tasks/7d4ff7e6-e1e2-4ee2-97d4-30a25f99cd5c |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 16:17:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 76B444D76A6DE07CD06AC33128864F27 |
| SHA1: | D369C892EF73E26EFB242B48DDBED63E393CACDE |
| SHA256: | 2AB8E35D0F586119F5F4A34319D10D472AD45501712D1AC1BE13B4C0DC0308F6 |
| SSDEEP: | 768:dzRPPRComRu4WnznZN5ubs4aIkVI3NHckihcr6yvE+dYo:dzBMpRW5IaIkV4oyEWd |
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 2508)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2508)
SUSPICIOUS
Creates files in the Windows directory
- WINWORD.EXE (PID: 2508)
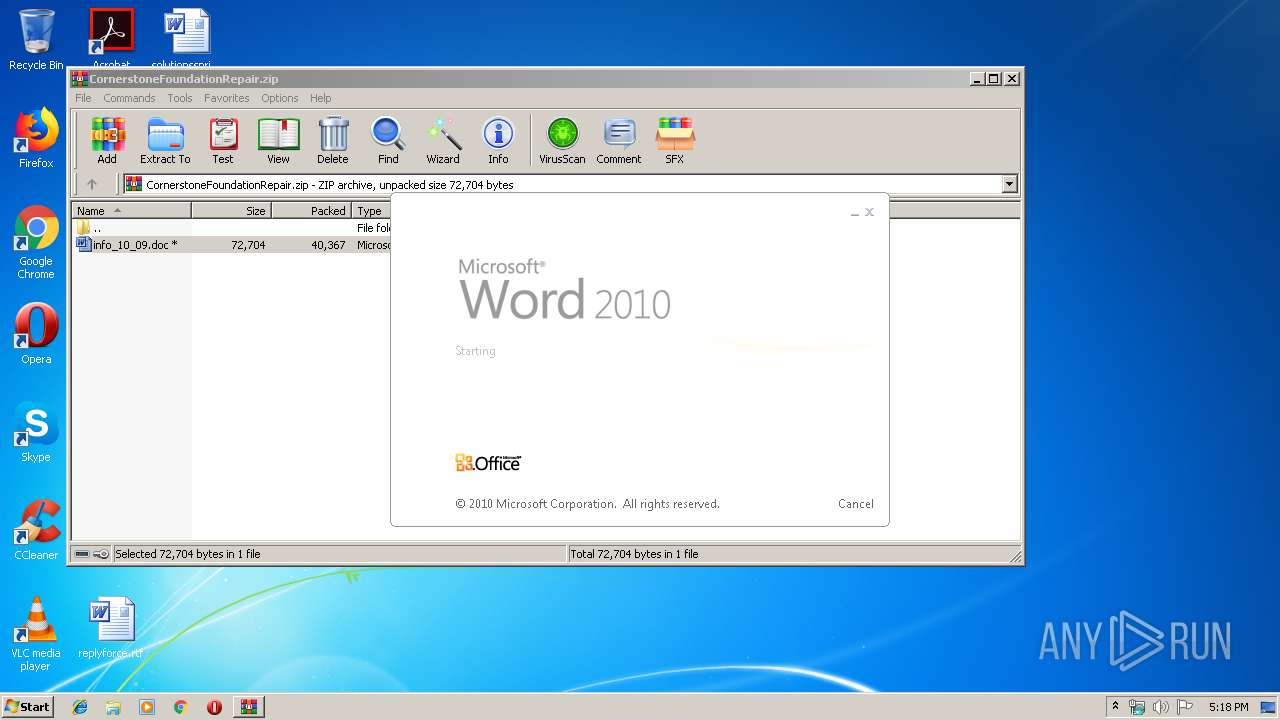
Starts Microsoft Office Application
- WinRAR.exe (PID: 3044)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2508)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
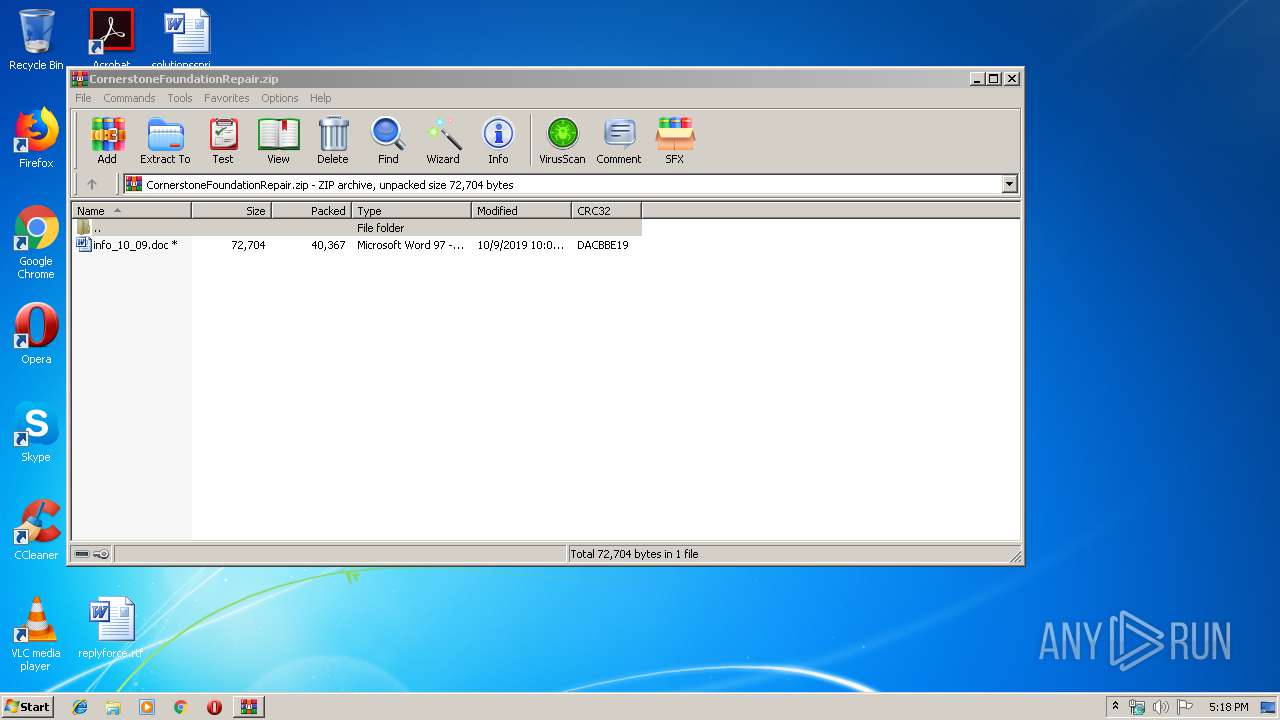
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 12:08:25 |
| ZipCRC: | 0xdacbbe19 |
| ZipCompressedSize: | 40367 |
| ZipUncompressedSize: | 72704 |
| ZipFileName: | info_10_09.doc |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2508 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3044.38768\info_10_09.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CornerstoneFoundationRepair.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3604 | "C:\Windows\System32\WScript.exe" "C:\Windows\Temp\ndllnnelcc.js" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
1 725
Read events
1 271
Write events
440
Delete events
14
Modification events
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CornerstoneFoundationRepair.zip | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2508) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ou; |
Value: 6F753B00CC090000010000000000000000000000 | |||
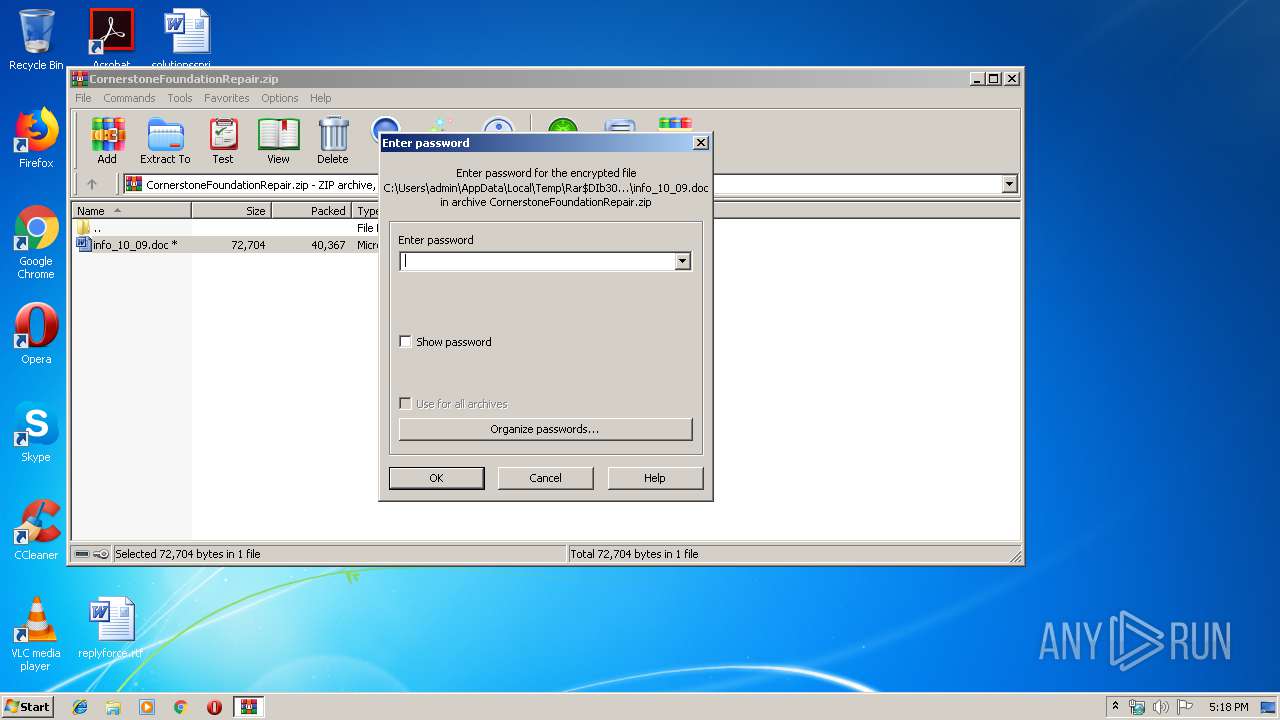
| (PID) Process: | (3044) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR39CF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Cab5ECB.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Tar5ECC.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Cab5EED.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Tar5EEE.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Cab5F6C.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\Local\Temp\Tar5F6D.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3604 | WScript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 3044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3044.38768\info_10_09.doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3604 | WScript.exe | GET | 200 | 67.26.83.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3604 | WScript.exe | GET | 200 | 67.26.83.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | WScript.exe | 104.64.21.50:443 | www.trendmicro.com | Akamai Technologies, Inc. | US | unknown |
3604 | WScript.exe | 95.101.177.126:443 | docs.microsoft.com | Akamai Technologies, Inc. | — | whitelisted |
— | — | 67.26.83.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.microsoft.com |
| whitelisted |
www.trendmicro.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |