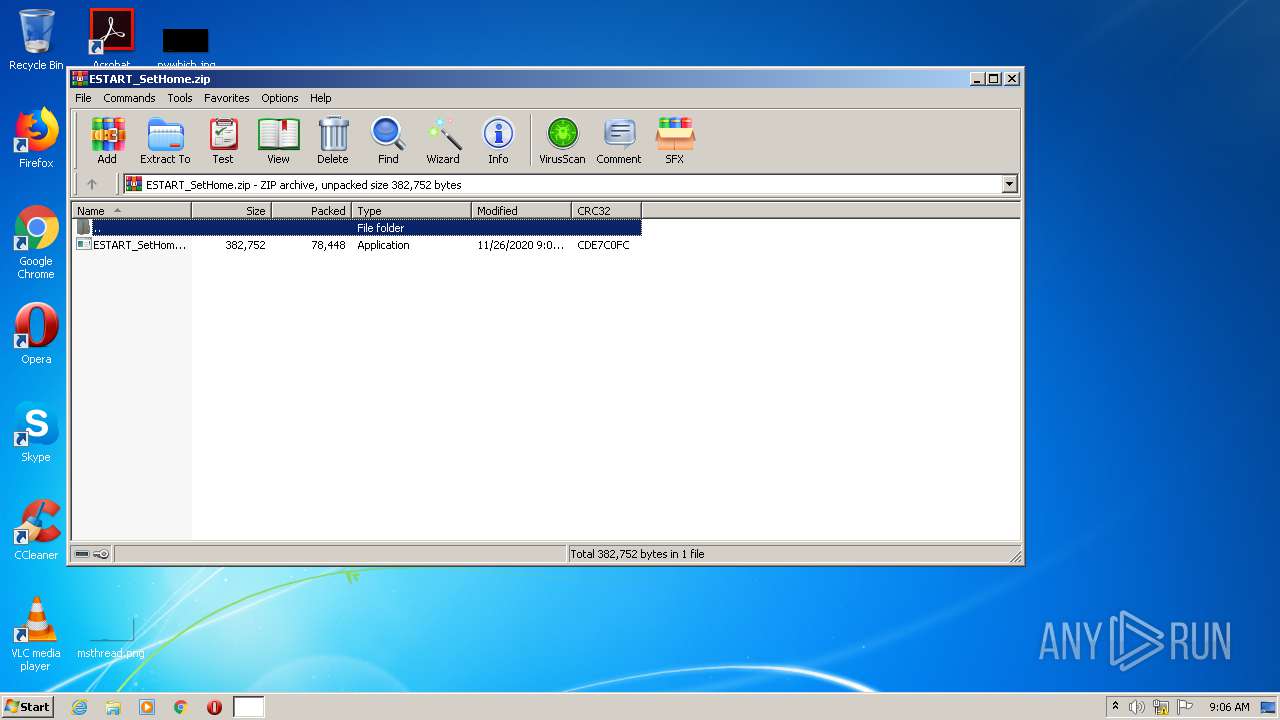
| File name: | ESTART_SetHome.zip |
| Full analysis: | https://app.any.run/tasks/6ff100d3-467c-43aa-a9c8-6301ea5b8412 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2020, 09:05:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9578F0161ED9F3F57C95B8613AA4B980 |
| SHA1: | 82699DEE3049E552AC6BBEFB09F7BFF70EED300D |
| SHA256: | 2AB0CAE175B5832FDEADF78961A073A492AC1AA192746EE38BAEBA6FEAACCD9F |
| SSDEEP: | 1536:XFEI8RZDnWBAErJX6Q+6TJiSgMdjLfQ8E5HtXF0eGu9ZVWdCw:XFEI8vgAElFbTJpjfcHt10eRZsow |
MALICIOUS
Application was dropped or rewritten from another process
- ESTART_SetHome.exe (PID: 4024)
Actions looks like stealing of personal data
- ESTART_SetHome.exe (PID: 4024)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1488)
- ESTART_SetHome.exe (PID: 4024)
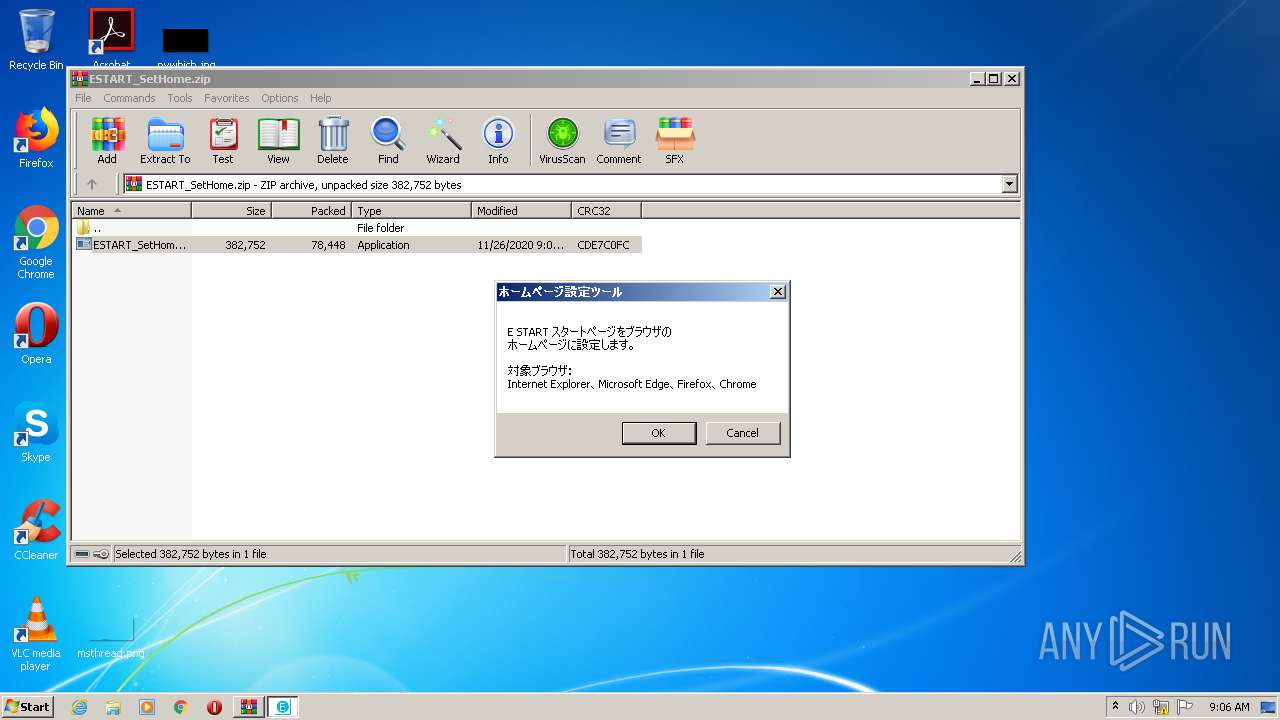
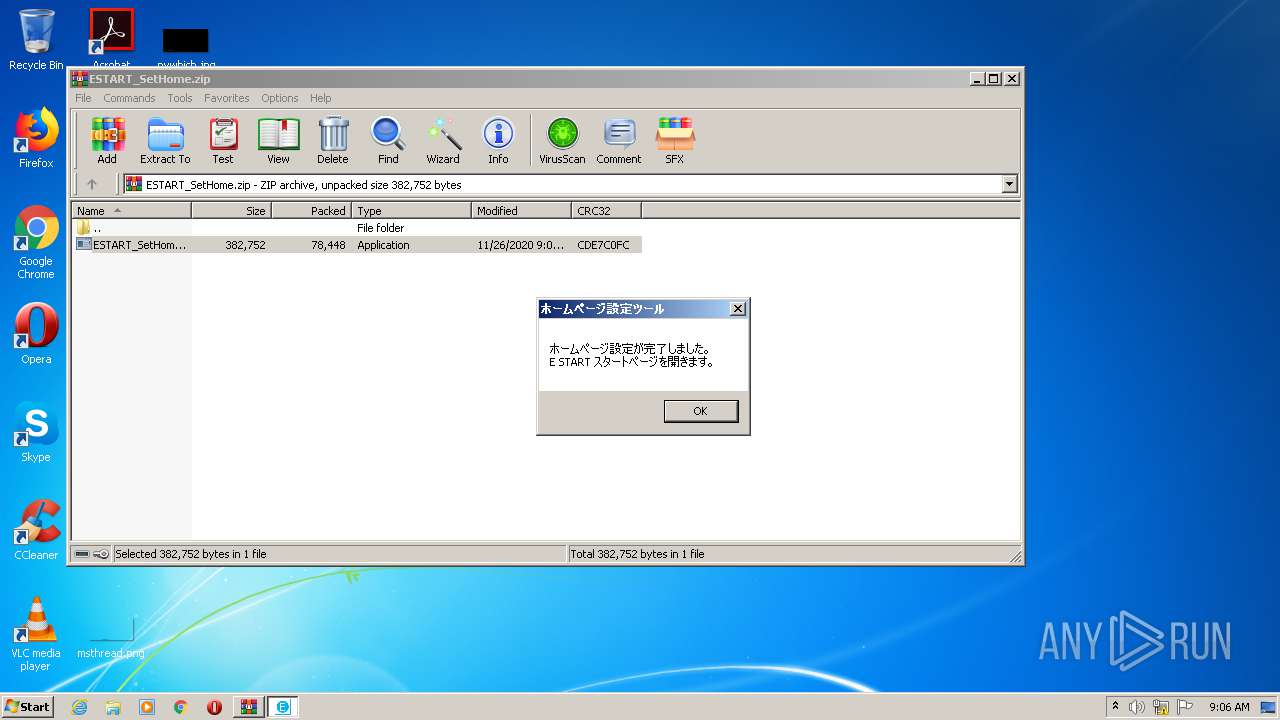
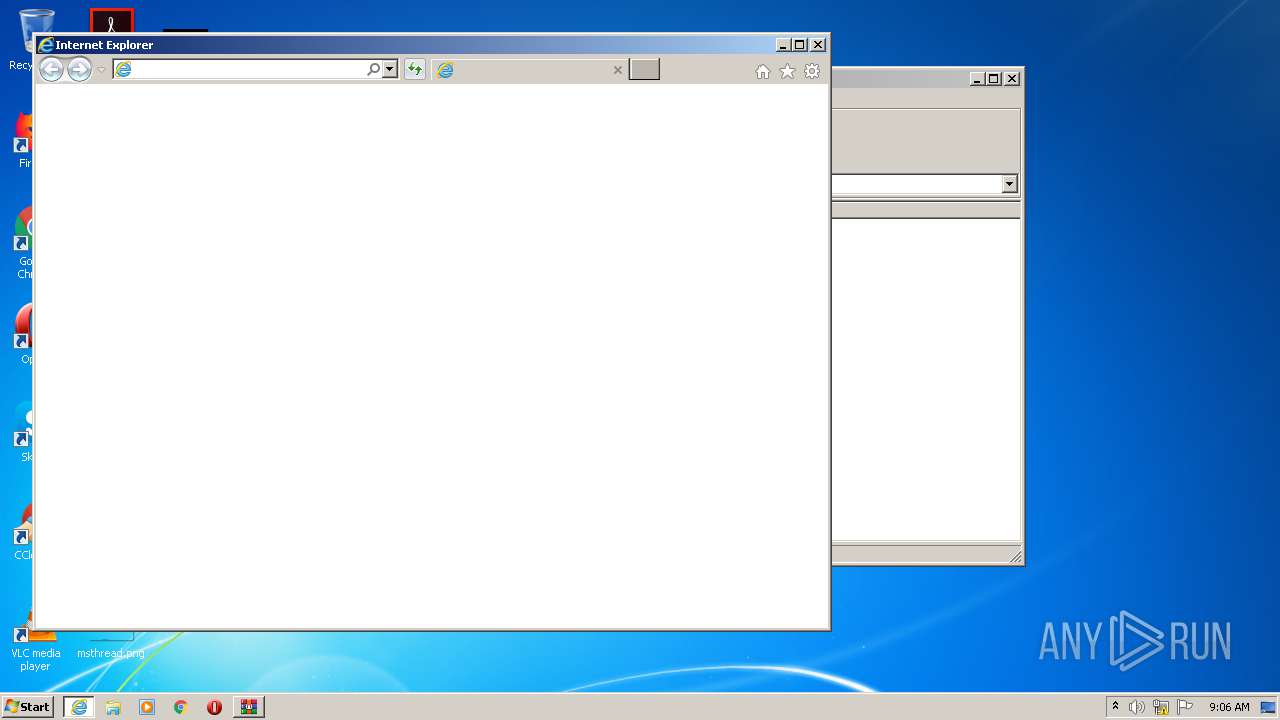
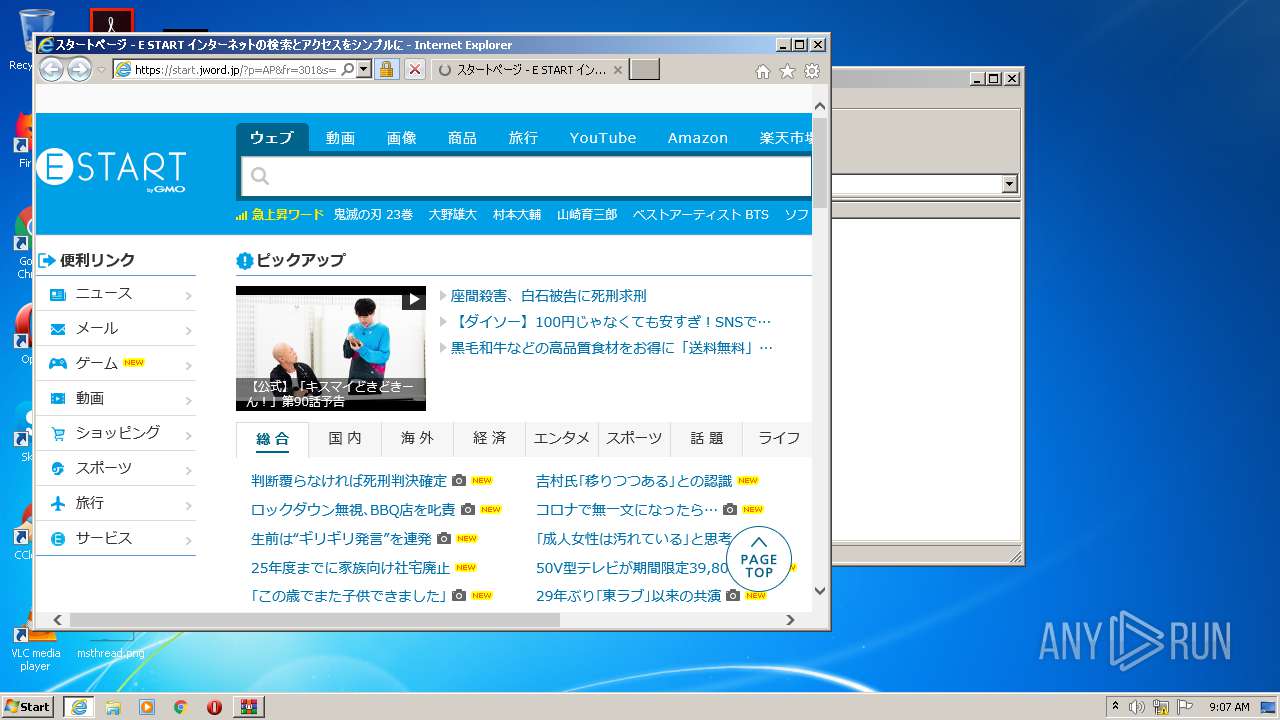
Starts Internet Explorer
- ESTART_SetHome.exe (PID: 4024)
Changes the started page of IE
- ESTART_SetHome.exe (PID: 4024)
Creates files in the user directory
- ESTART_SetHome.exe (PID: 4024)
INFO
Application launched itself
- iexplore.exe (PID: 3572)
Changes internet zones settings
- iexplore.exe (PID: 3572)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3924)
Reads settings of System Certificates
- iexplore.exe (PID: 3572)
Creates files in the user directory
- iexplore.exe (PID: 3924)
- iexplore.exe (PID: 3572)
Reads internet explorer settings
- iexplore.exe (PID: 3924)
Changes settings of System certificates
- iexplore.exe (PID: 3572)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:26 09:08:17 |
| ZipCRC: | 0xcde7c0fc |
| ZipCompressedSize: | 78448 |
| ZipUncompressedSize: | 382752 |
| ZipFileName: | ESTART_SetHome.exe |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ESTART_SetHome.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Internet Explorer\iexplore.exe" http://start.jword.jp/?p=AP&fr=301&s=insfin | C:\Program Files\Internet Explorer\iexplore.exe | ESTART_SetHome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3924 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3572 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1488.42963\ESTART_SetHome.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1488.42963\ESTART_SetHome.exe | WinRAR.exe | ||||||||||||
User: admin Company: JWord Inc. Integrity Level: MEDIUM Description: Set E-START to HomePage Exit code: 0 Version: 1.0.4.3 Modules
| |||||||||||||||
Total events
1 148
Read events
1 001
Write events
142
Delete events
5
Modification events
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ESTART_SetHome.zip | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1488) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
189
Text files
199
Unknown types
95
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFB27.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFB28.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PNI5EBDY.txt | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EKMTNRMN.txt | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 4024 | ESTART_SetHome.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 4024 | ESTART_SetHome.exe | C:\Users\admin\Favorites\ƒXƒ^[ƒgƒy[ƒW - E START ƒCƒ“ƒ^[ƒlƒbƒg‚ÌŒŸõ‚ƃAƒNƒZƒX‚ðƒVƒ“ƒvƒ‹‚É.url | text | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PMQ0HE7G.txt | text | |
MD5:— | SHA256:— | |||
| 4024 | ESTART_SetHome.exe | C:\Users\admin\AppData\Roaming\JWord\ESTART_SetHome.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
104
TCP/UDP connections
214
DNS requests
78
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | ESTART_SetHome.exe | GET | 200 | 150.95.46.29:80 | http://search.jword.jp/go.phtml?type=cnt&fm=&agent=&partner=AP&bypass=2&url=&lang=euc&name=estart_inst_AP_301&rnd=b27 | JP | — | — | unknown |
3924 | iexplore.exe | GET | 200 | 65.9.70.113:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEApeE0KTF%2BNB06LEXAKo%2Buk%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 65.9.70.133:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | der | 608 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 65.9.70.113:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEASdO6z8KpBwJOe3KTXCFF8%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDa2MTpyZrzlQgAAAAAYth4 | US | der | 472 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 65.9.70.113:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEASdO6z8KpBwJOe3KTXCFF8%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCKcuDfDBqJ0QIAAAAAgFWT | US | der | 472 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | ESTART_SetHome.exe | 18.176.69.127:80 | rd.jword.jp | Massachusetts Institute of Technology | US | unknown |
4024 | ESTART_SetHome.exe | 150.95.46.29:80 | search.jword.jp | GMO Internet,Inc | JP | unknown |
3924 | iexplore.exe | 52.69.114.168:80 | start.jword.jp | Amazon.com, Inc. | JP | unknown |
3924 | iexplore.exe | 52.69.114.168:443 | start.jword.jp | Amazon.com, Inc. | JP | unknown |
3924 | iexplore.exe | 65.9.70.225:80 | o.ss2.us | AT&T Services, Inc. | US | unknown |
3572 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3924 | iexplore.exe | 65.9.70.105:80 | ocsp.rootg2.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
3924 | iexplore.exe | 65.9.70.133:80 | crl.rootg2.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
3924 | iexplore.exe | 65.9.70.113:80 | ocsp.sca1b.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
3924 | iexplore.exe | 65.9.70.194:80 | ocsp.rootg2.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rd.jword.jp |
| suspicious |
start.jword.jp |
| unknown |
search.jword.jp |
| unknown |
o.ss2.us |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
crl.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |