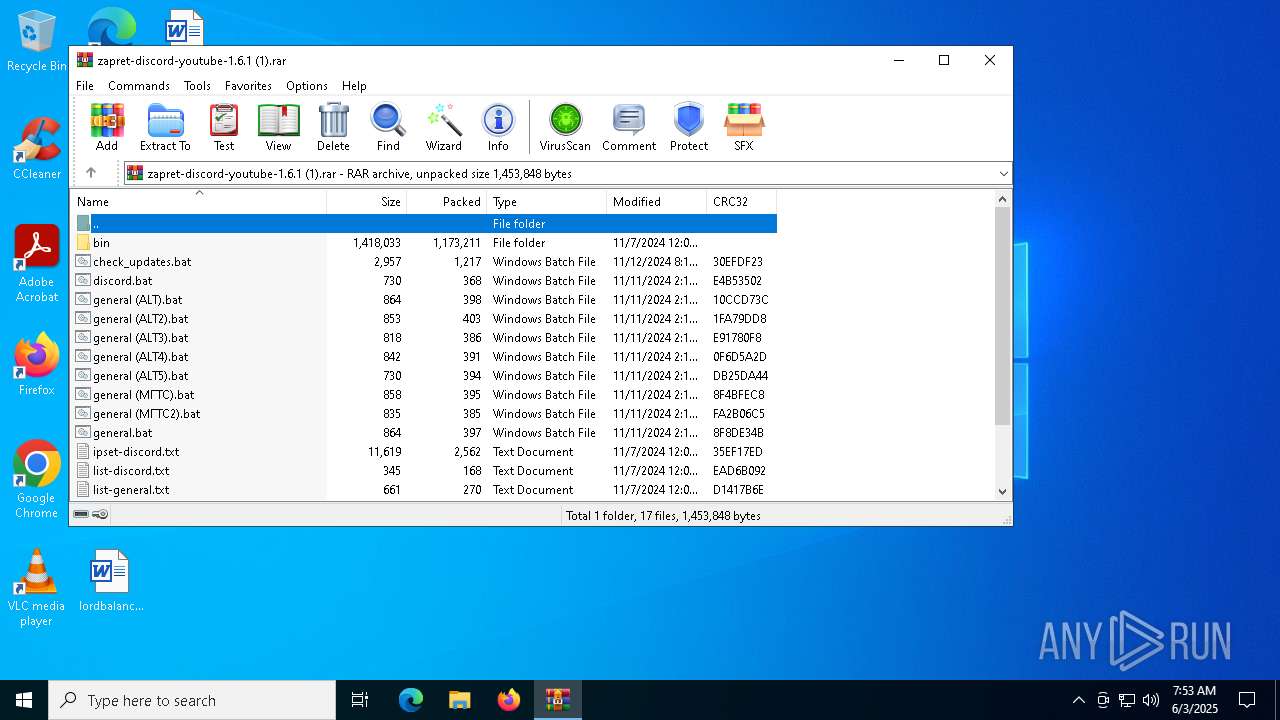
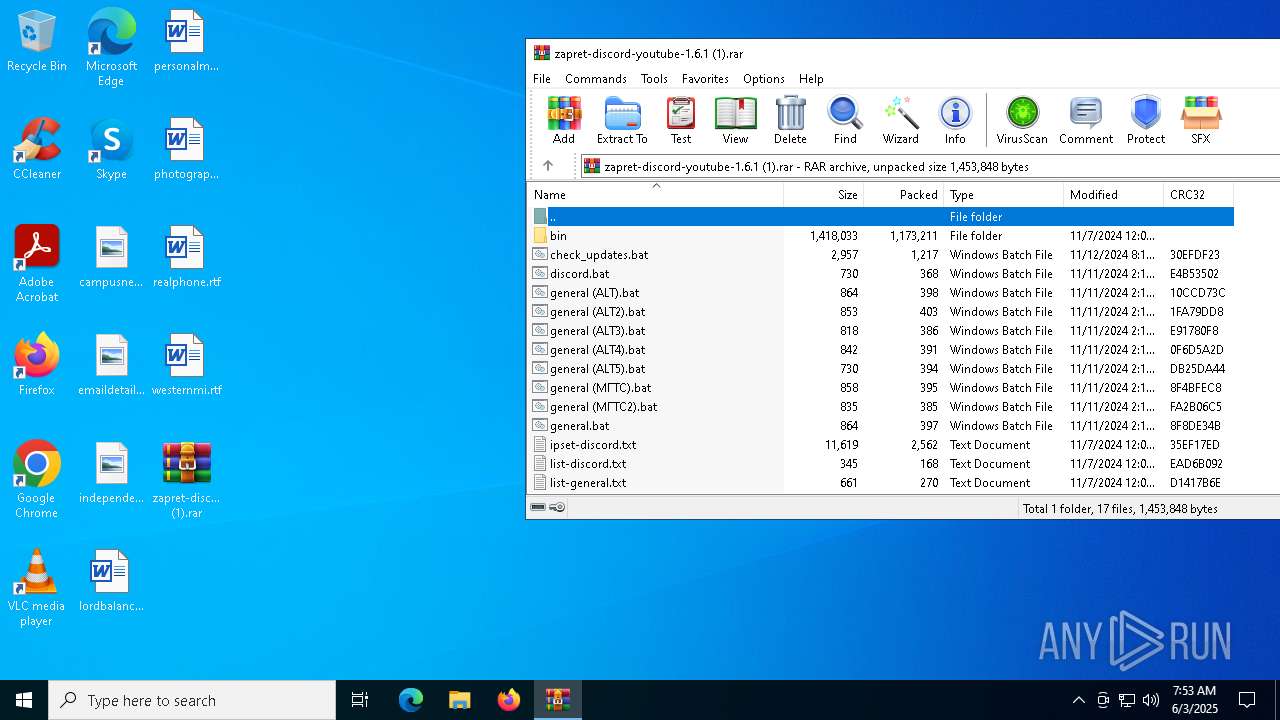
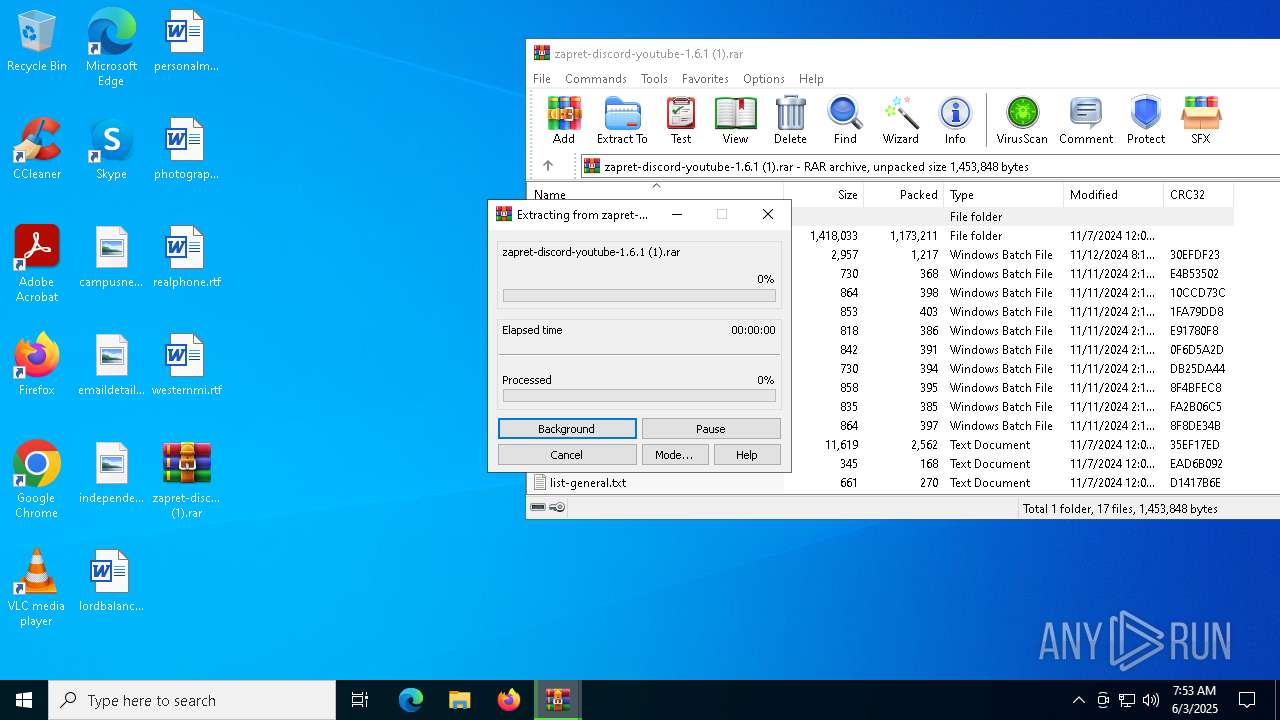
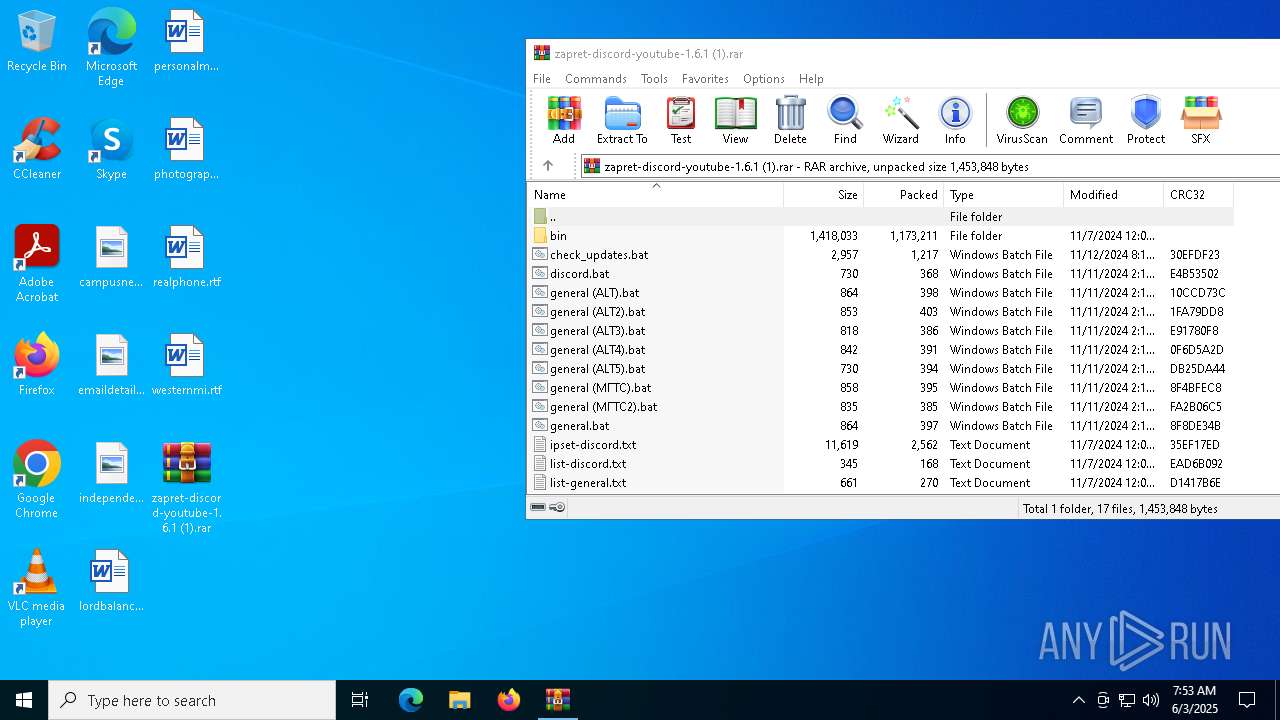
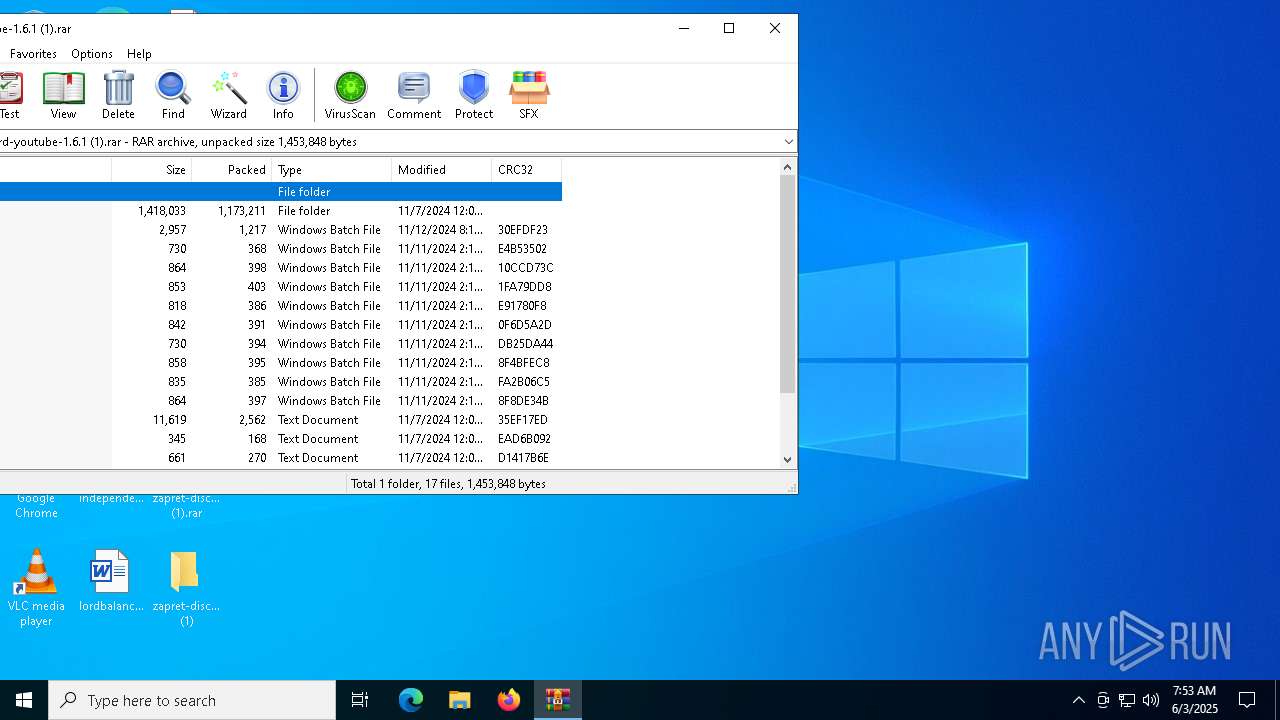
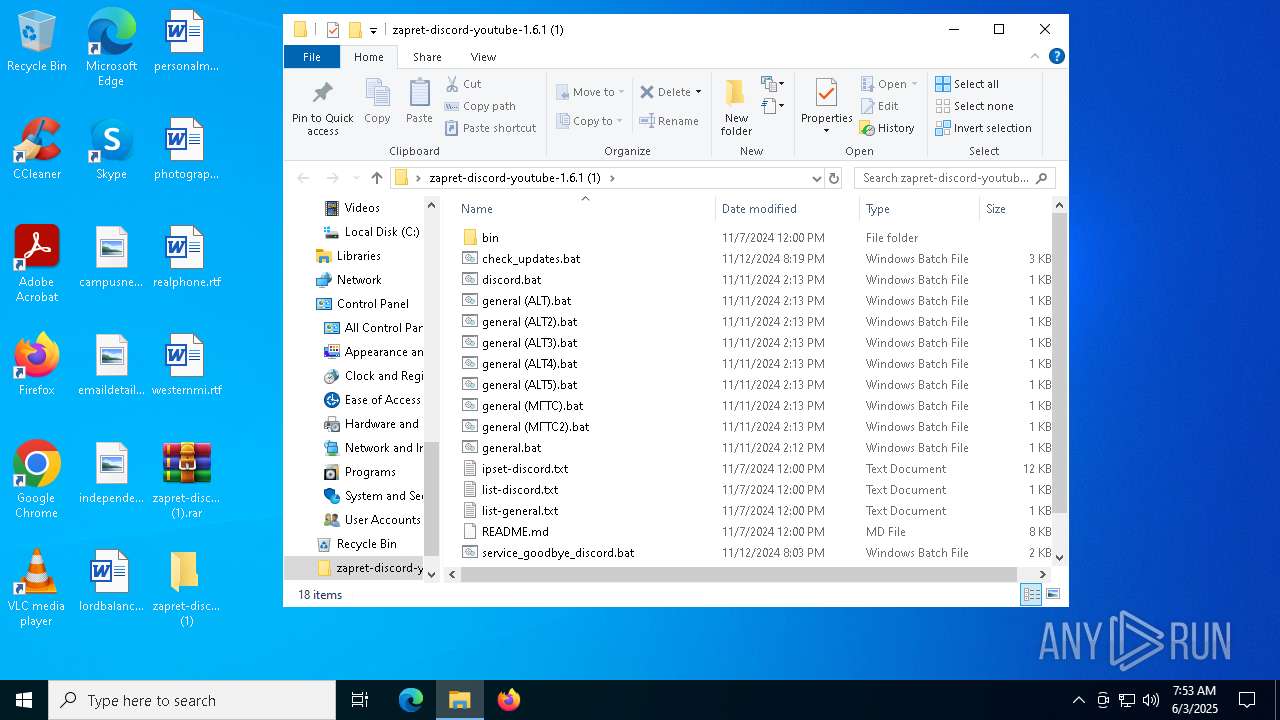
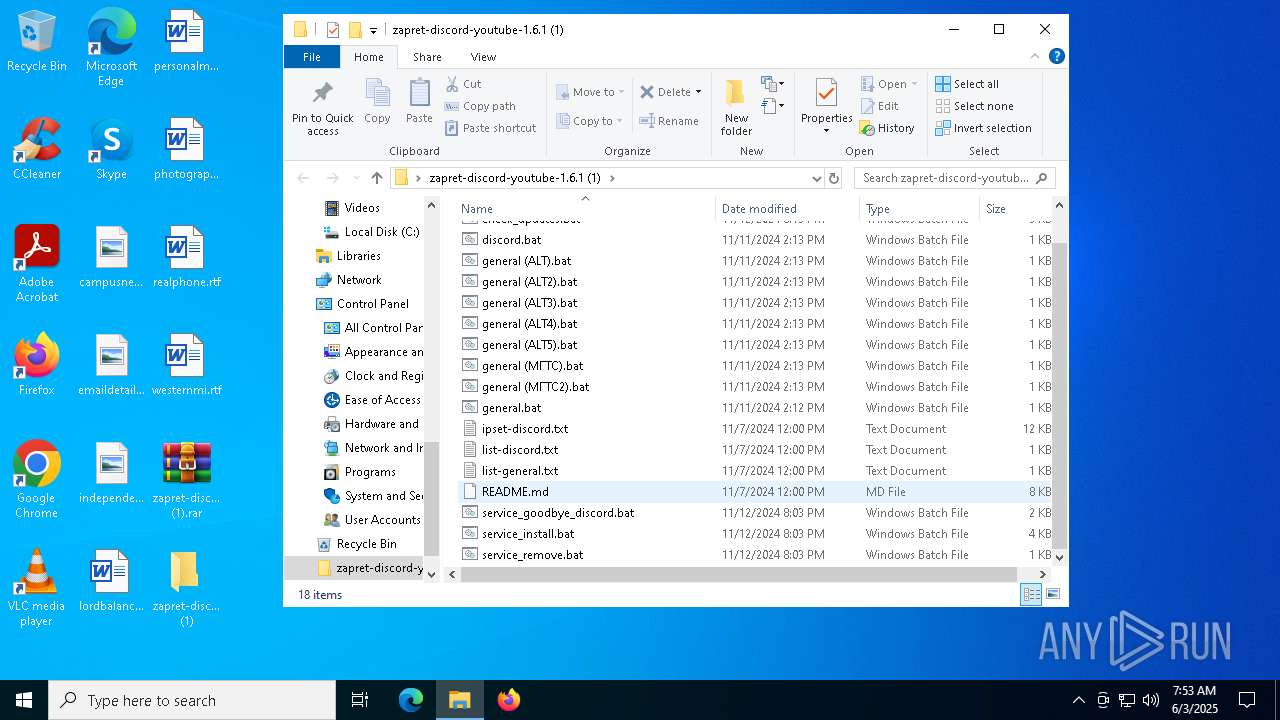
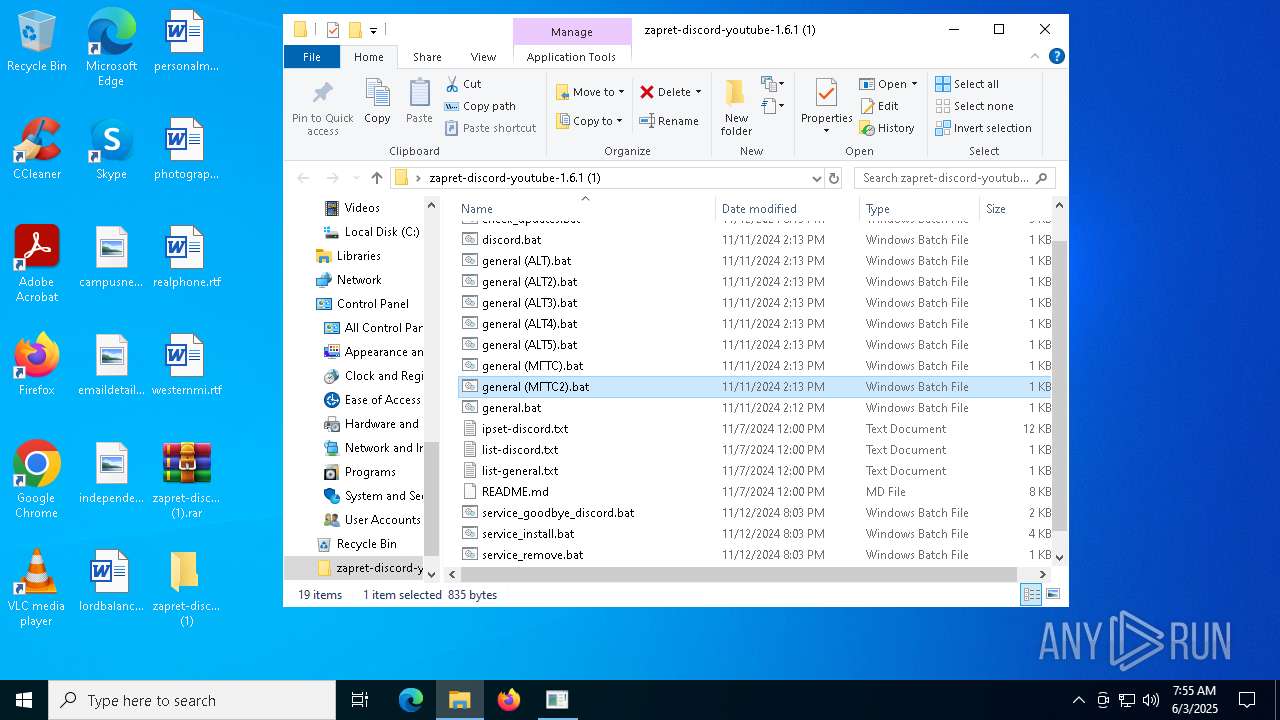
| File name: | zapret-discord-youtube-1.6.1 (1).rar |
| Full analysis: | https://app.any.run/tasks/6c85b1e9-c4b2-4560-9e26-ab5144700445 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2025, 07:53:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | DB6DDF779FEDE5B17A289880EB2CE217 |
| SHA1: | DF3ACA68FB4D28116FD17C286907DE4709E50F2A |
| SHA256: | 2AAC3961D99AB14BEE7BC9D4CC3ABDA083050BE23456BF15C4BAA2B580CF9B70 |
| SSDEEP: | 49152:nD2pC3Q/k0bvTtqsyTDWaxsJ/tfjnlcNw7hqnFTII6w8b+IWx8n/cYZrECWSBVcx:Dx3Q/k0dYT6axYhzIZnFkI6fHRcYZr/C |
MALICIOUS
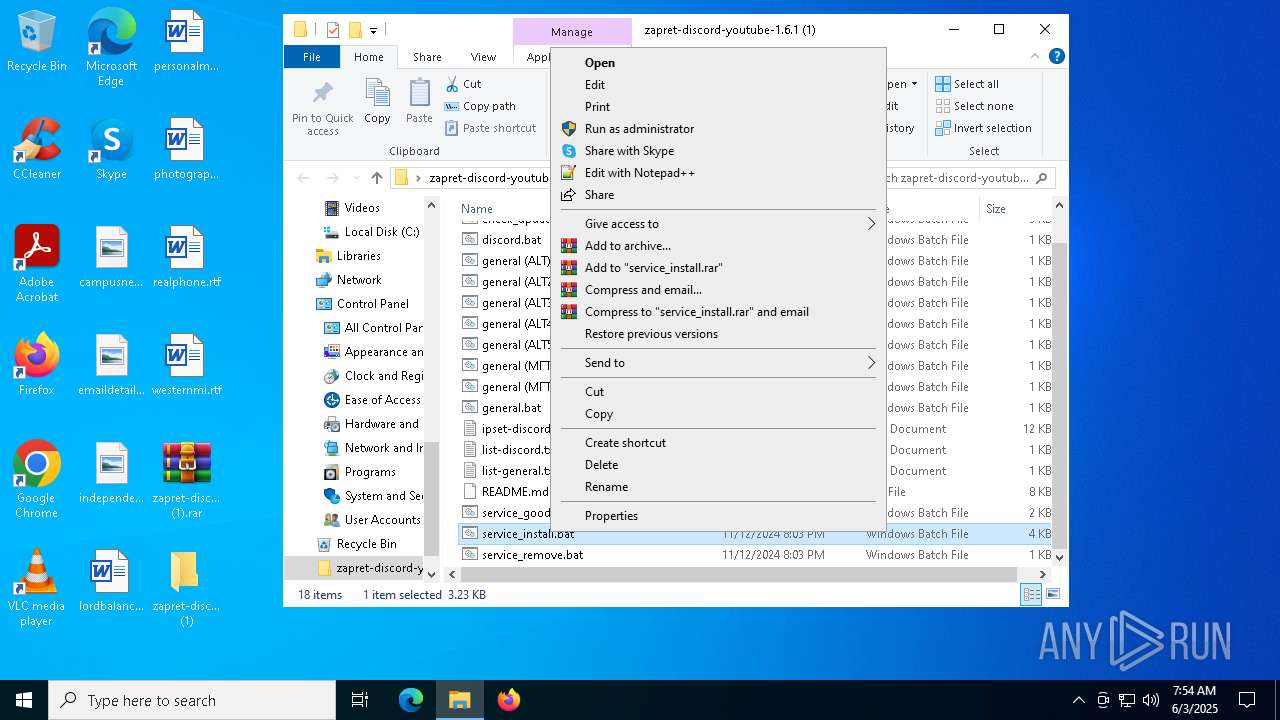
Generic archive extractor
- WinRAR.exe (PID: 4652)
Detects Cygwin installation
- WinRAR.exe (PID: 4628)
Malicious driver has been detected
- WinRAR.exe (PID: 4628)
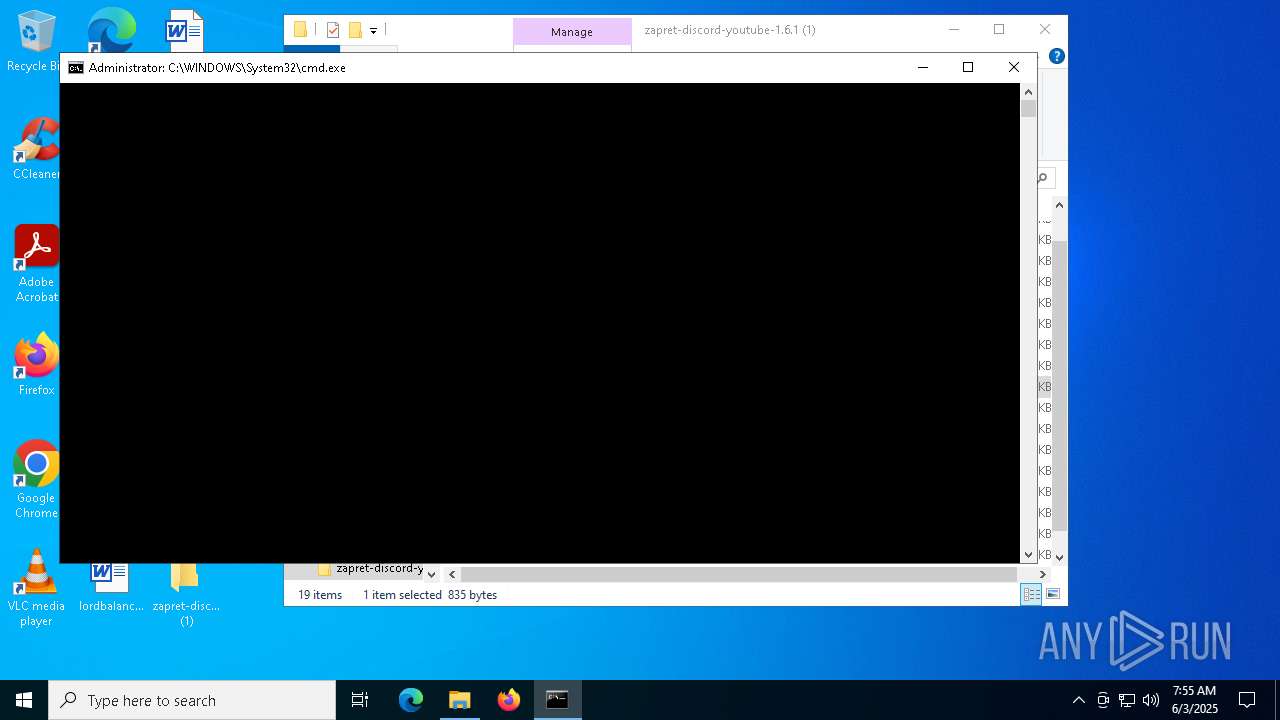
Starts NET.EXE for service management
- cmd.exe (PID: 3896)
- net.exe (PID: 5360)
- cmd.exe (PID: 5508)
- net.exe (PID: 772)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5360)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 856)
- cmd.exe (PID: 5156)
Starts process via Powershell
- powershell.exe (PID: 864)
- powershell.exe (PID: 3884)
Starts application with an unusual extension
- cmd.exe (PID: 5360)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 856)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 6872)
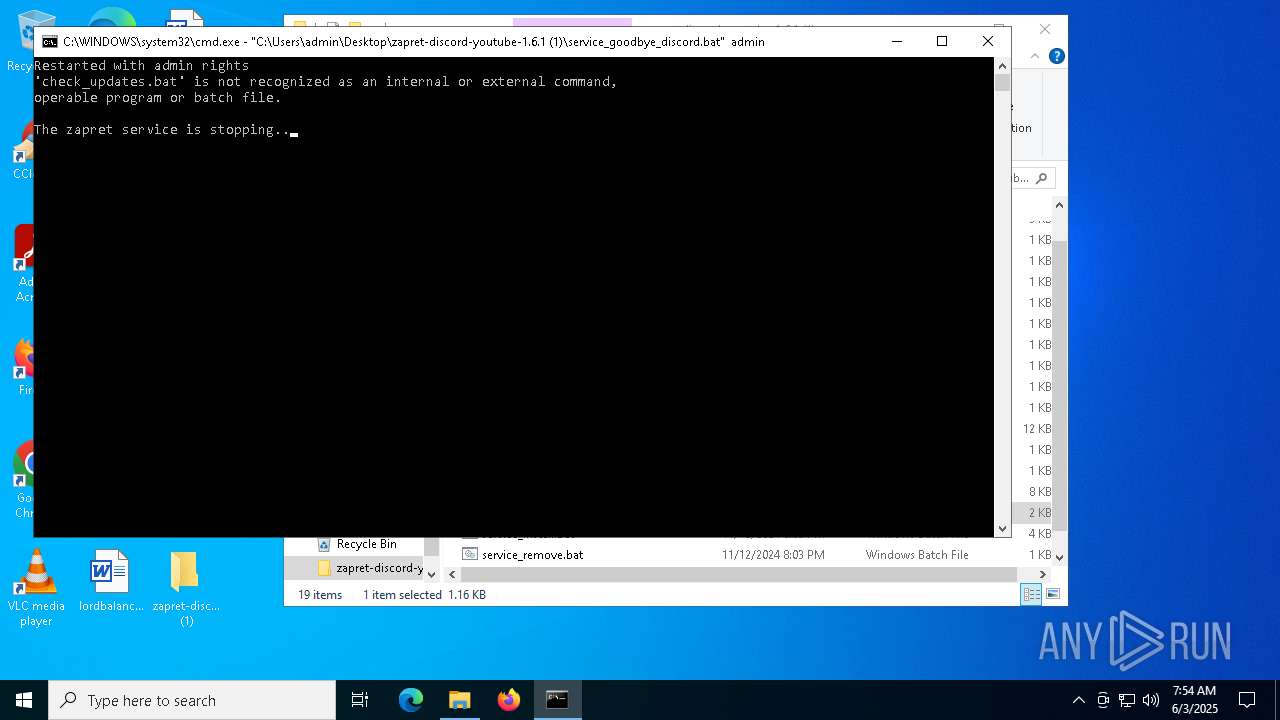
Starts CMD.EXE for commands execution
- powershell.exe (PID: 864)
- cmd.exe (PID: 3896)
- powershell.exe (PID: 3884)
- cmd.exe (PID: 6872)
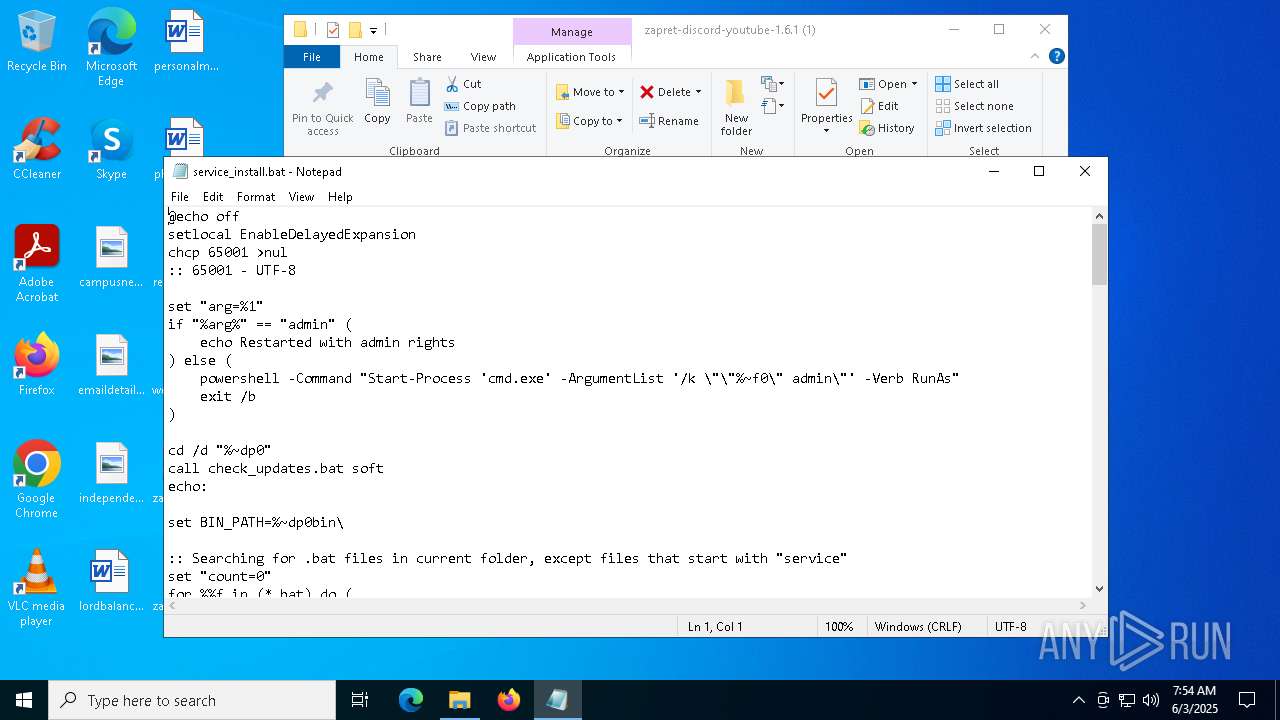
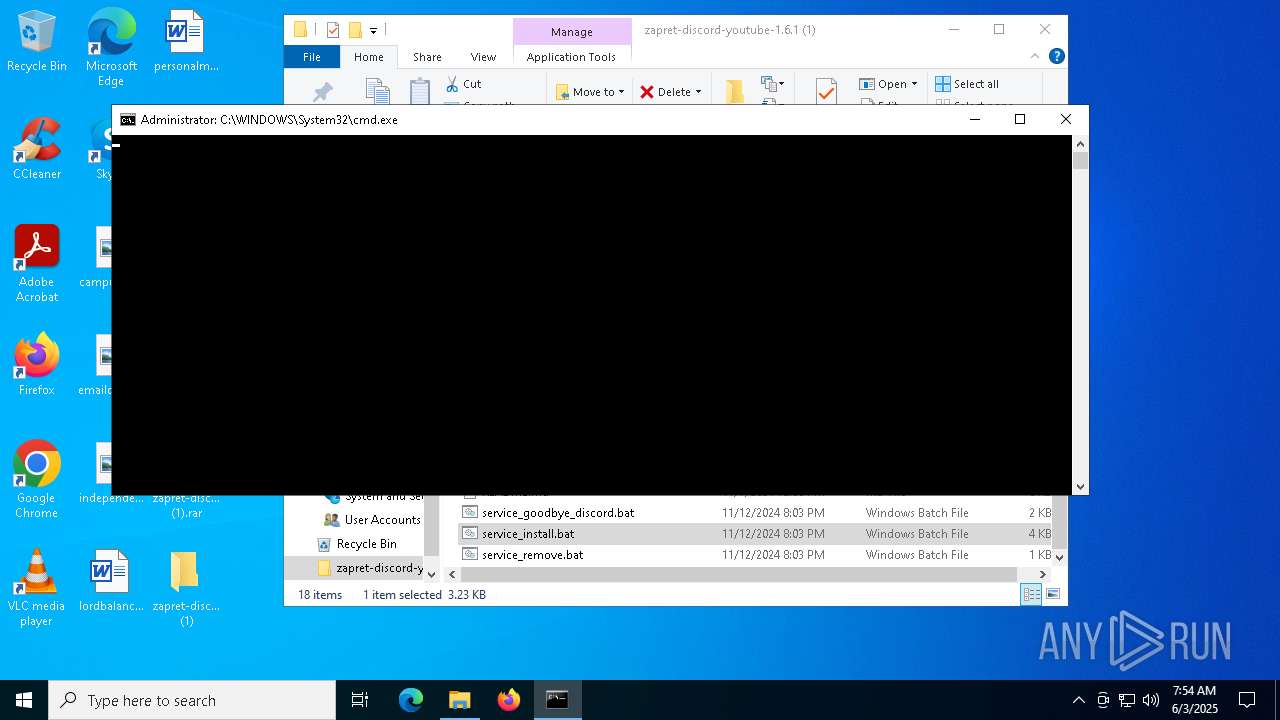
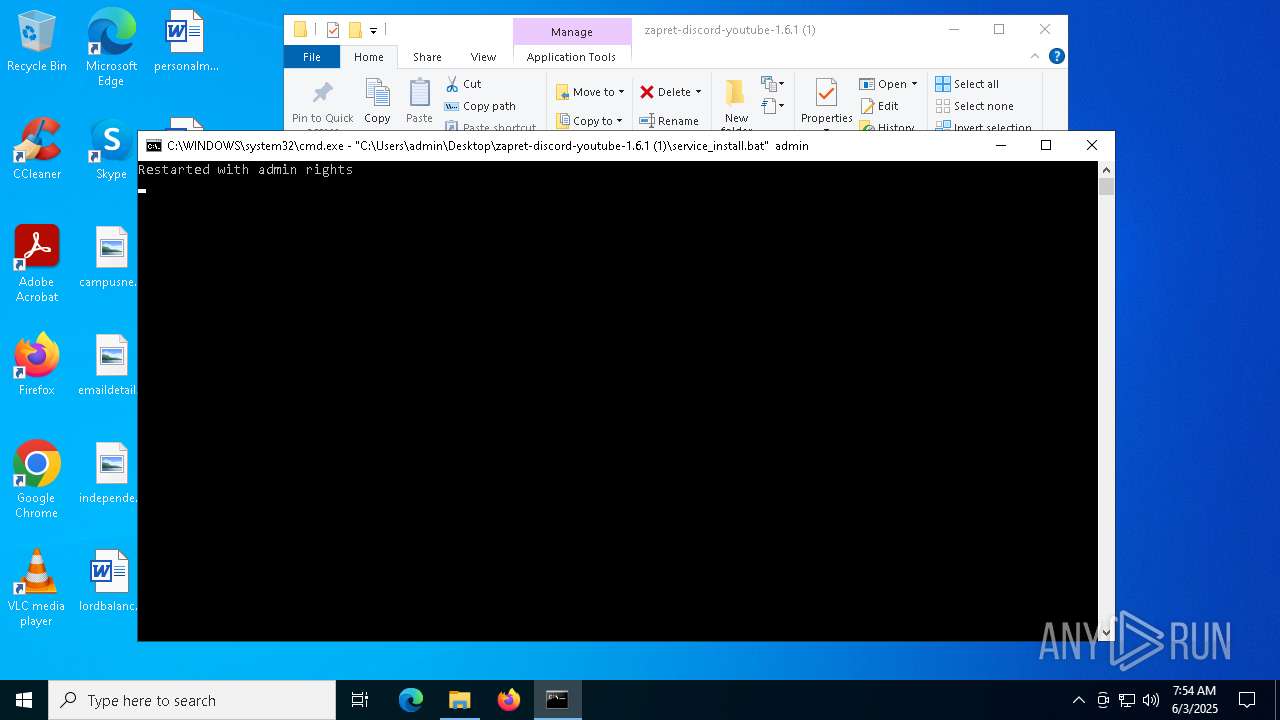
Executing commands from a ".bat" file
- powershell.exe (PID: 864)
- cmd.exe (PID: 3896)
- powershell.exe (PID: 3884)
Application launched itself
- cmd.exe (PID: 3896)
- cmd.exe (PID: 6872)
Hides command output
- cmd.exe (PID: 1228)
- cmd.exe (PID: 6676)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3896)
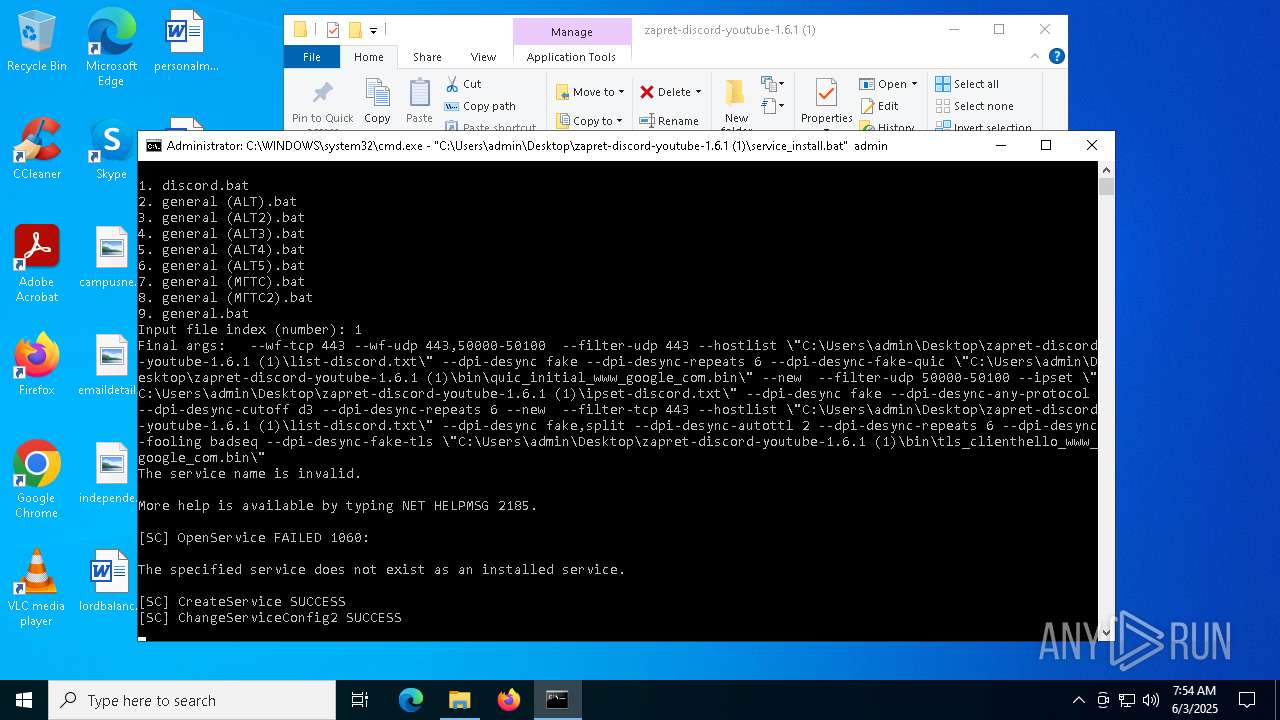
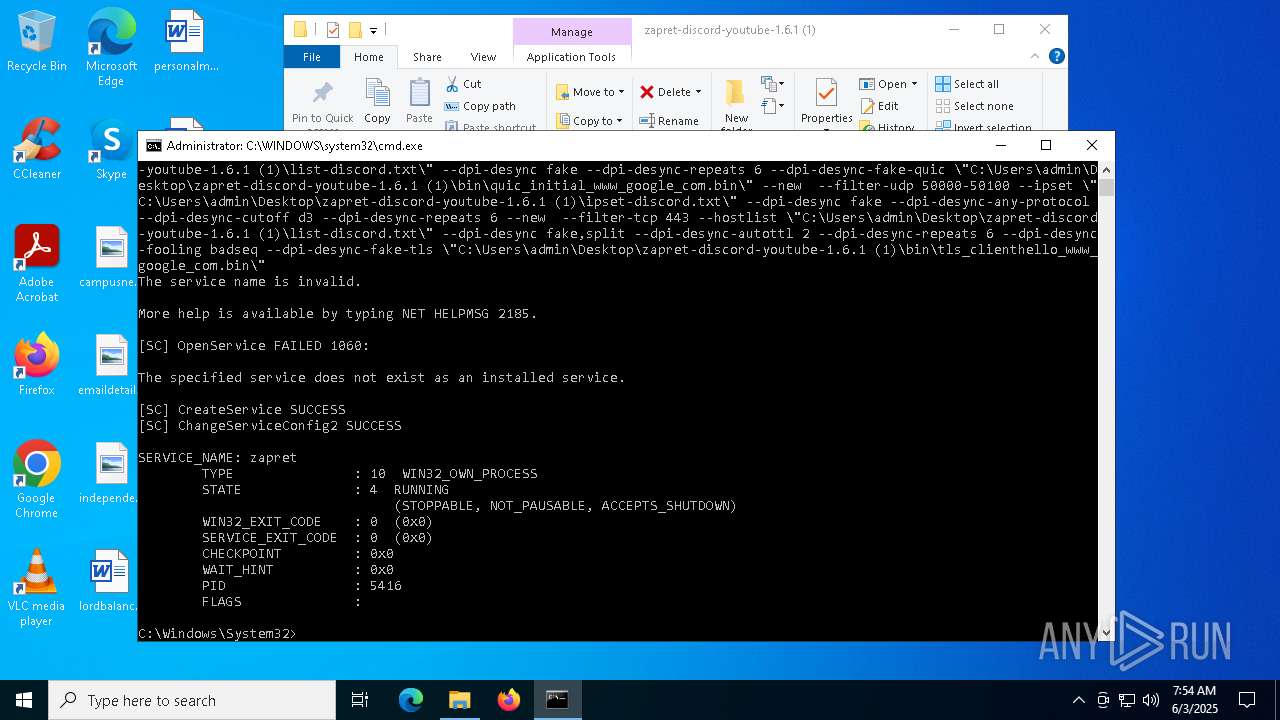
Windows service management via SC.EXE
- sc.exe (PID: 3996)
- sc.exe (PID: 5984)
- sc.exe (PID: 6872)
- sc.exe (PID: 6620)
- sc.exe (PID: 2908)
- sc.exe (PID: 6676)
Executes as Windows Service
- winws.exe (PID: 5416)
Creates a new Windows service
- sc.exe (PID: 1616)
- sc.exe (PID: 5256)
Starts SC.EXE for service management
- cmd.exe (PID: 3896)
- cmd.exe (PID: 5508)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 4628)
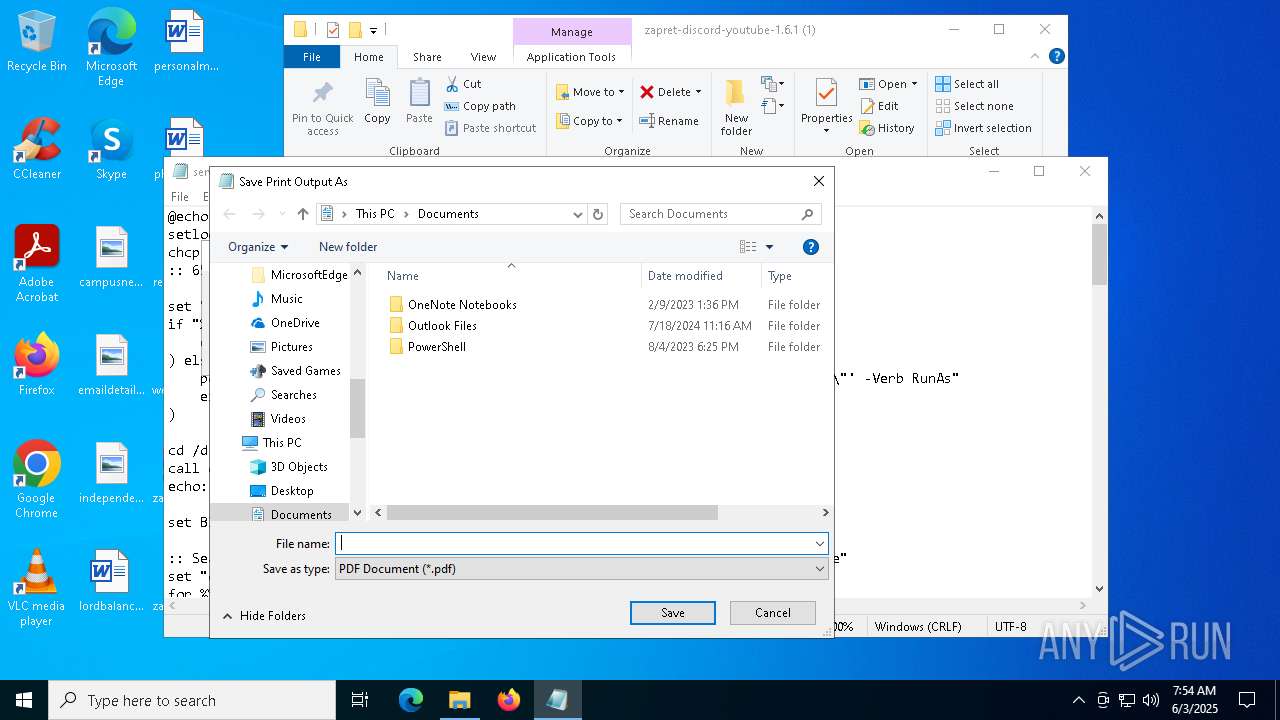
Sets XML DOM element text (SCRIPT)
- notepad.exe (PID: 4336)
INFO
Checks supported languages
- chcp.com (PID: 4756)
- chcp.com (PID: 732)
- chcp.com (PID: 5416)
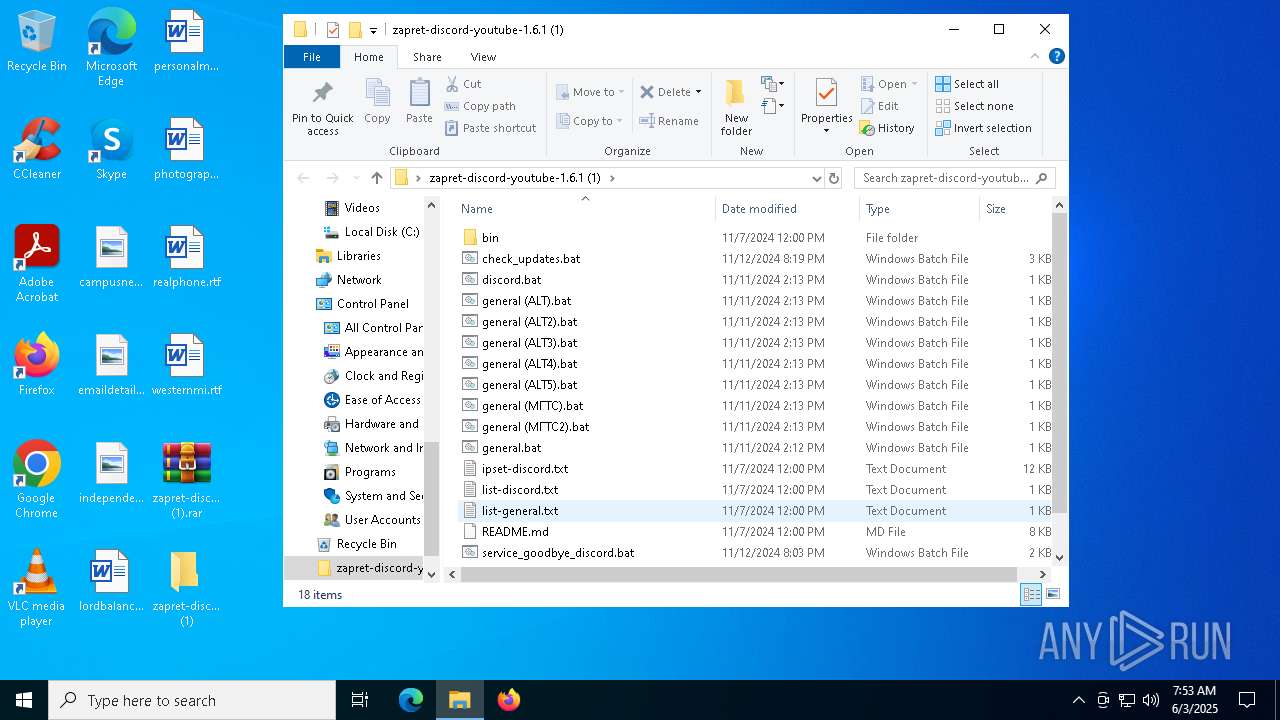
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4628)
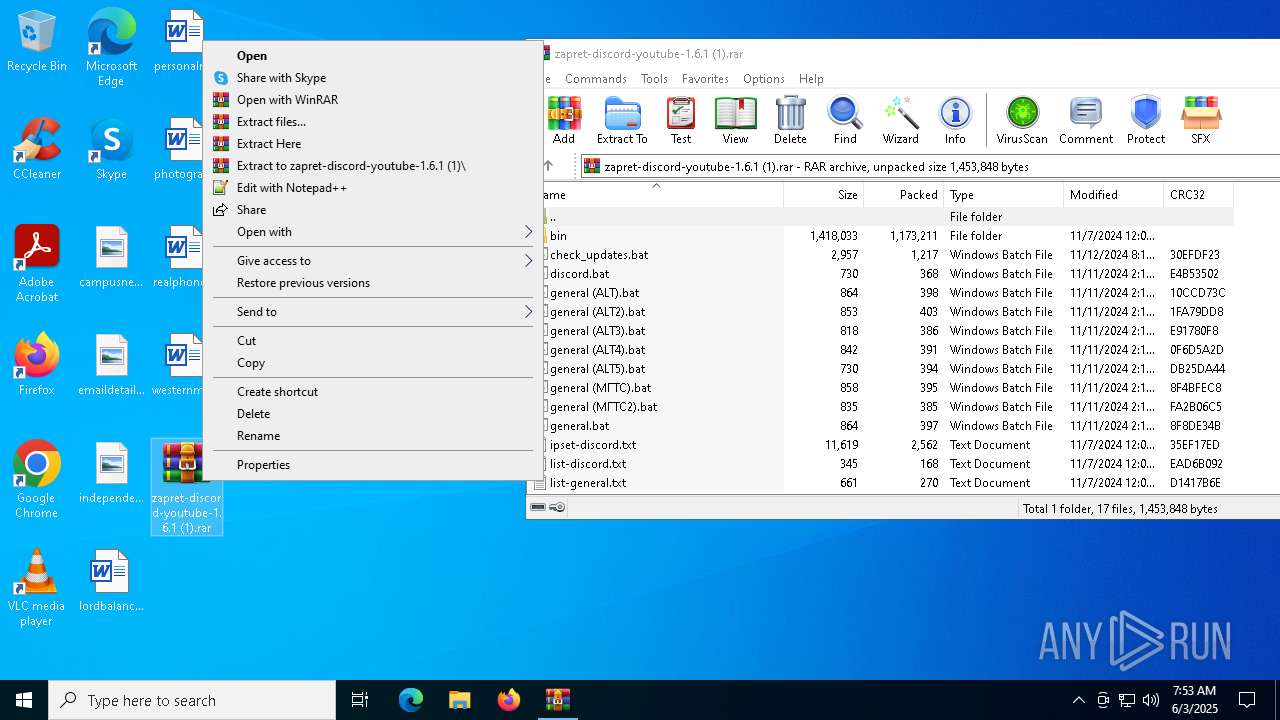
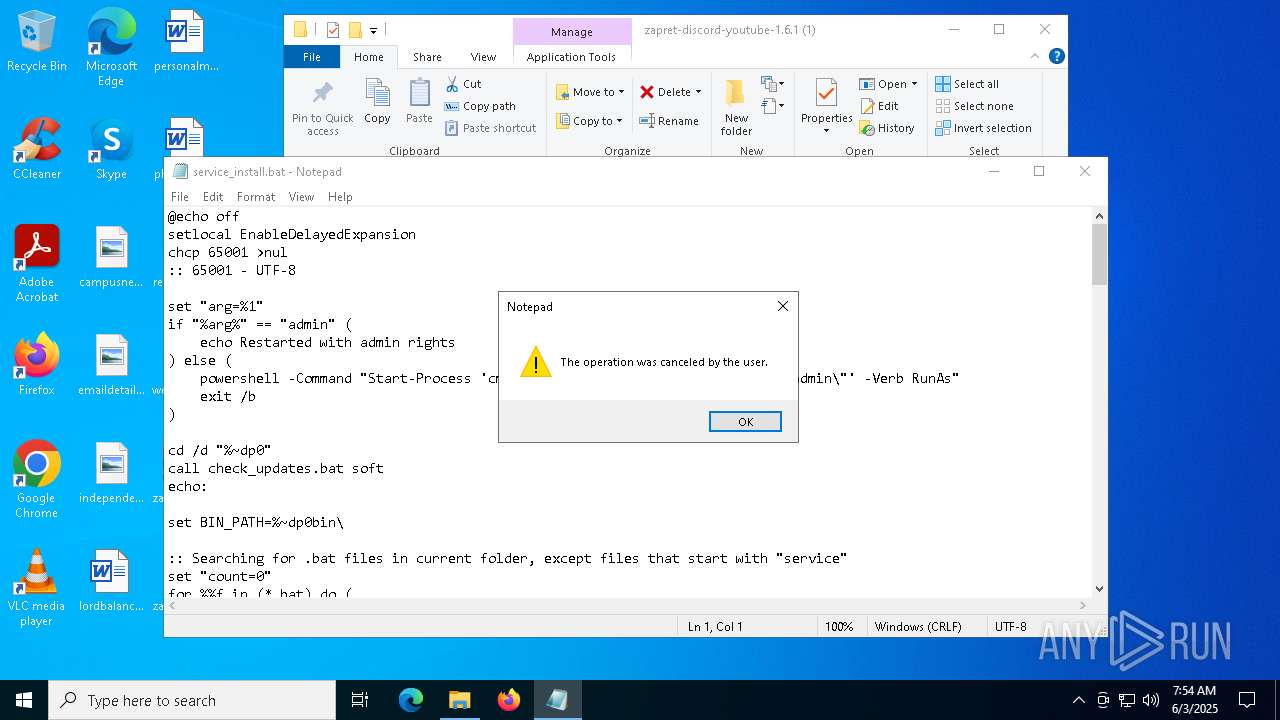
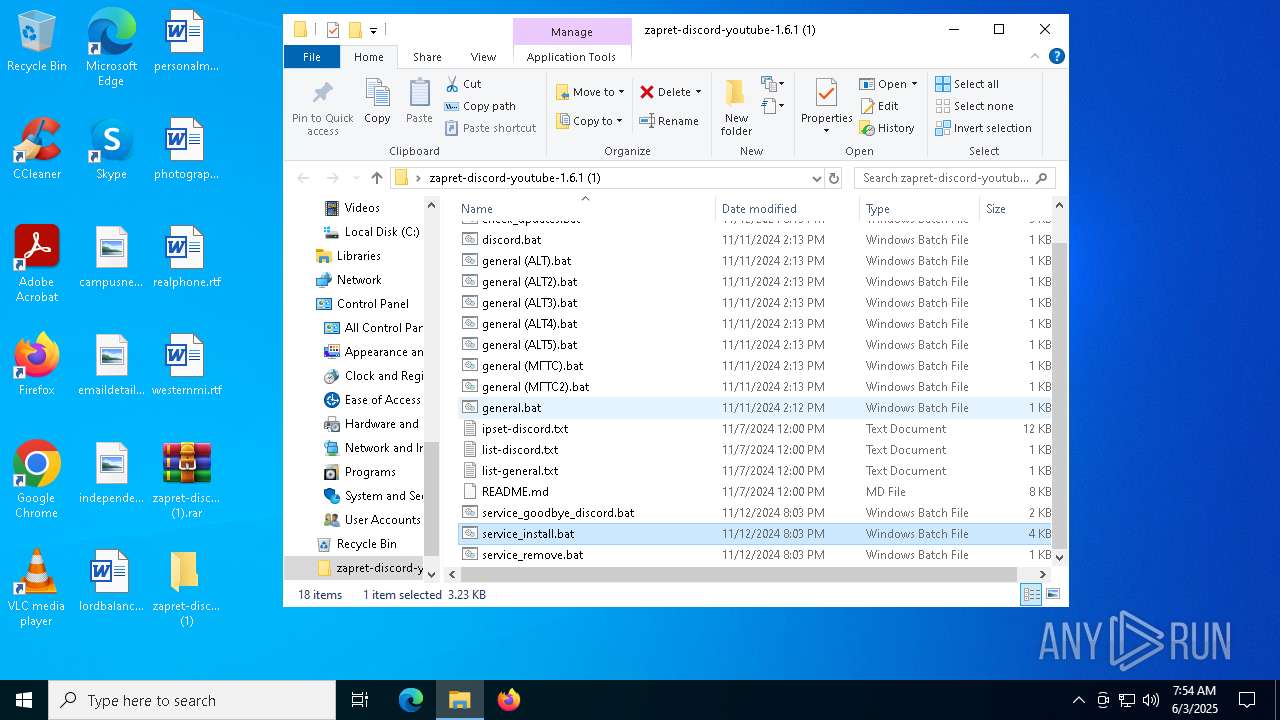
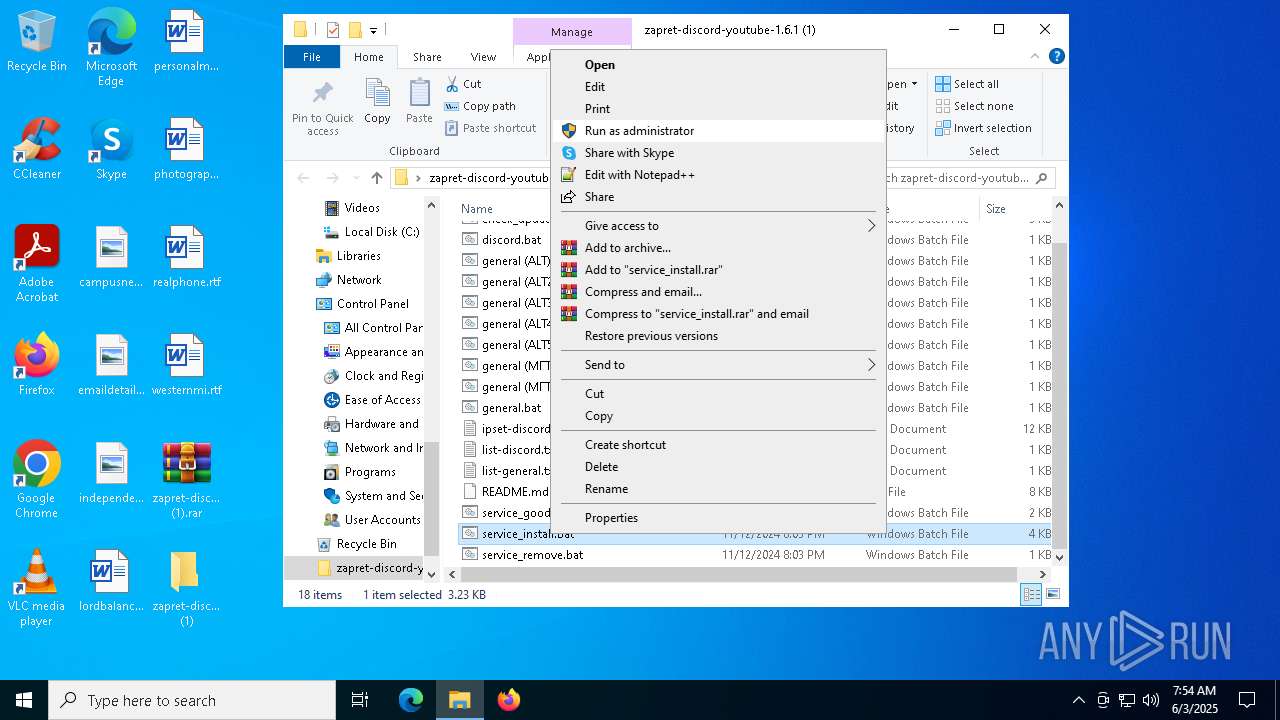
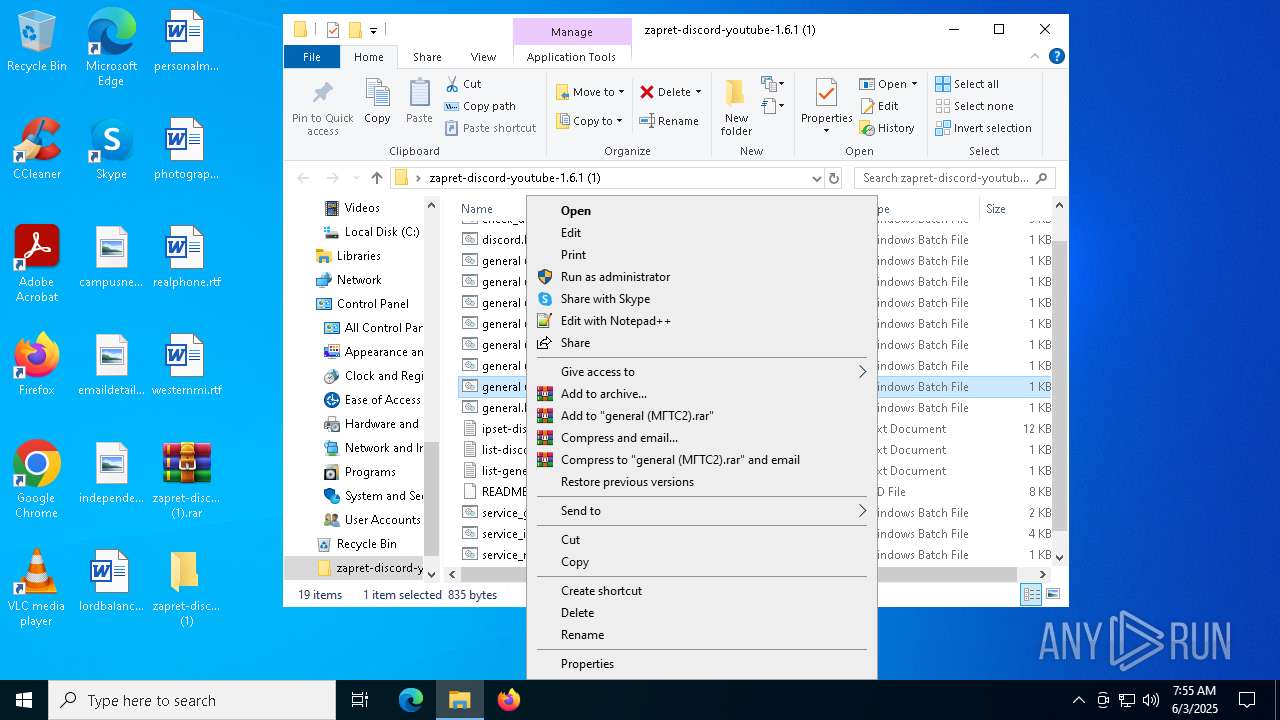
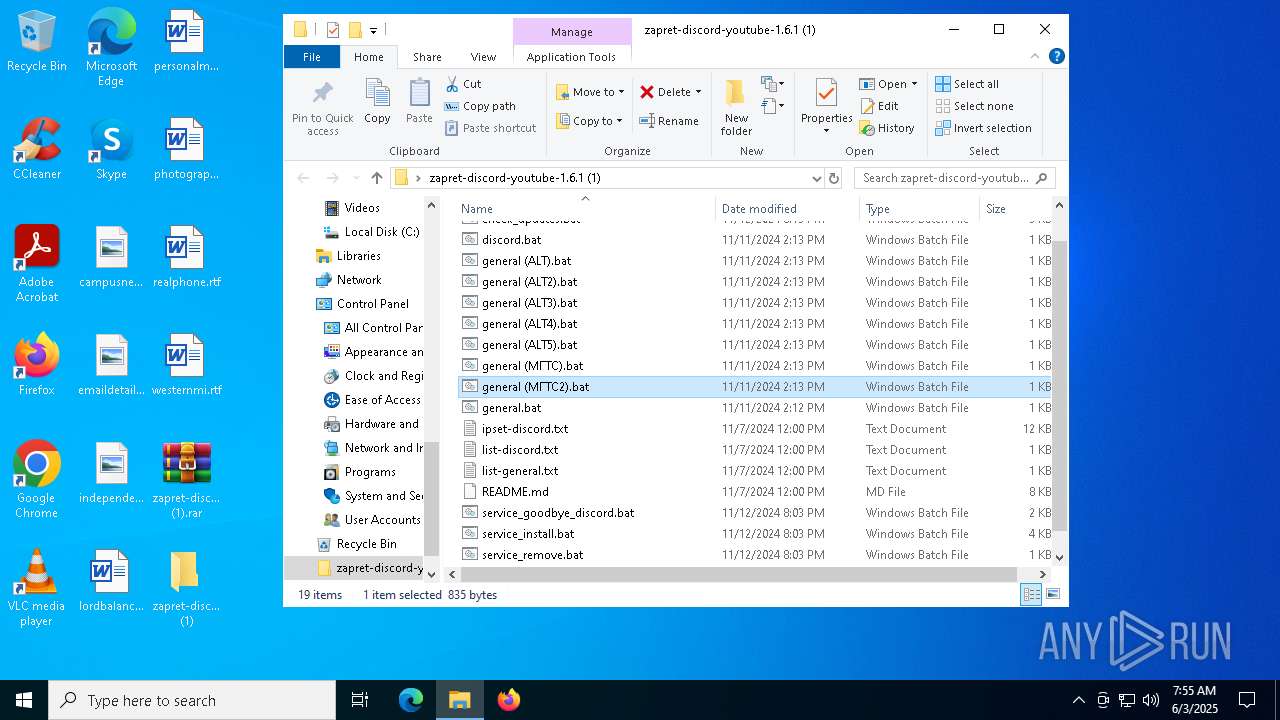
Manual execution by a user
- WinRAR.exe (PID: 4628)
- cmd.exe (PID: 856)
- cmd.exe (PID: 6872)
- notepad.exe (PID: 4336)
- cmd.exe (PID: 5360)
The sample compiled with english language support
- WinRAR.exe (PID: 4628)
Changes the display of characters in the console
- cmd.exe (PID: 3896)
- cmd.exe (PID: 856)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 5360)
Checks proxy server information
- powershell.exe (PID: 5064)
Disables trace logs
- powershell.exe (PID: 5064)
UPX packer has been detected
- winws.exe (PID: 5416)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2826 |
| UncompressedSize: | 7925 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | README.md |
Total processes
212
Monitored processes
78
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | net stop zapret | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
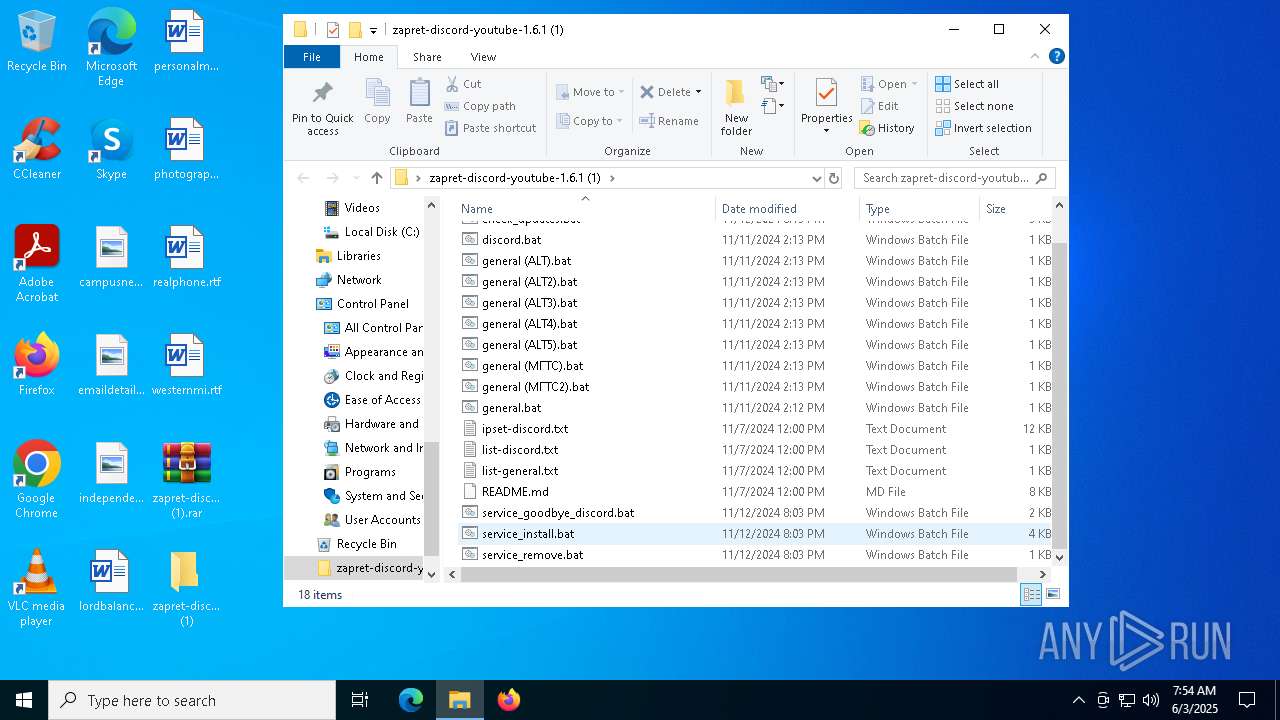
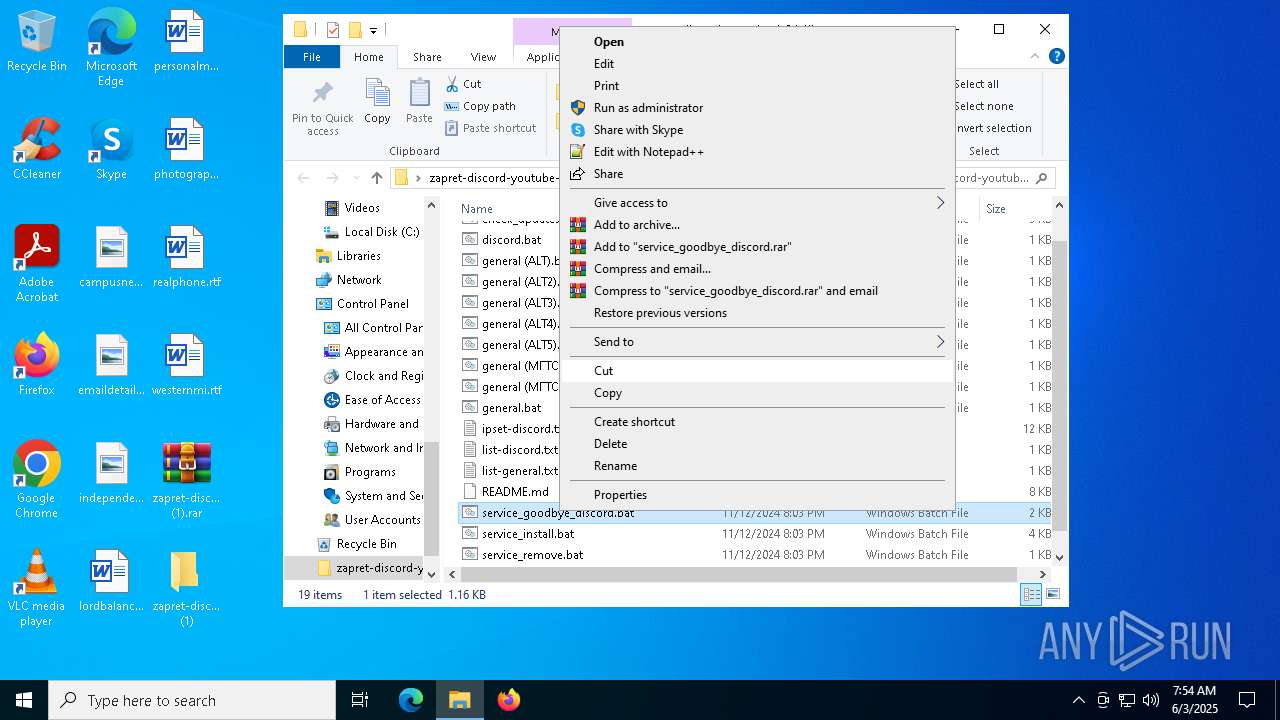
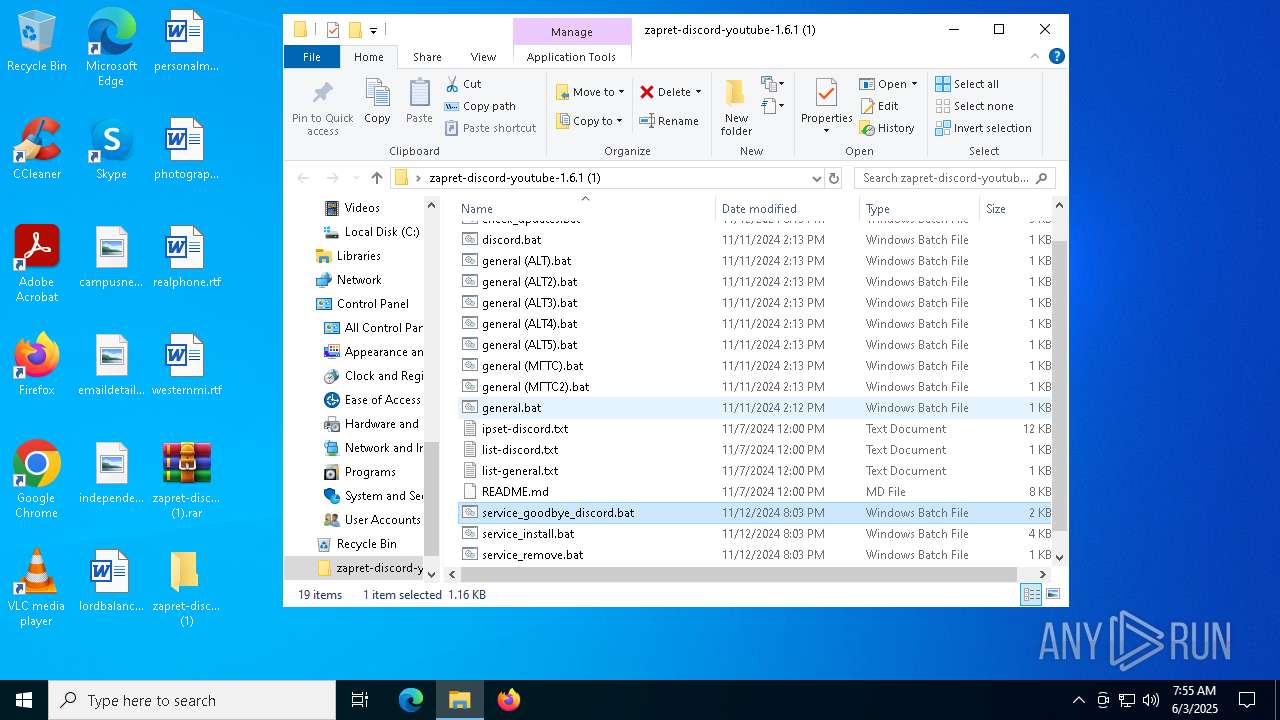
| 856 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\service_goodbye_discord.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | powershell -Command "Start-Process 'cmd.exe' -ArgumentList '/k \"\"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\service_install.bat\" admin\"' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\cmd.exe /c powershell -command "(Invoke-WebRequest -Uri https://raw.githubusercontent.com/Flowseal/zapret-discord-youtube/refs/heads/main/.service/version.txt -Headers @{\"Cache-Control\"=\"no-cache\"} -TimeoutSec 5).Content" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | findstr /i "winws.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | sc create zapret binPath= "\"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\bin\winws.exe\" --wf-tcp 443 --wf-udp 443,50000-50100 --filter-udp 443 --hostlist \"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\list-discord.txt\" --dpi-desync fake --dpi-desync-repeats 6 --dpi-desync-fake-quic \"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\bin\quic_initial_www_google_com.bin\" --new --filter-udp 50000-50100 --ipset \"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\ipset-discord.txt\" --dpi-desync fake --dpi-desync-any-protocol --dpi-desync-cutoff d3 --dpi-desync-repeats 6 --new --filter-tcp 443 --hostlist \"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\list-discord.txt\" --dpi-desync fake,split --dpi-desync-autottl 2 --dpi-desync-repeats 6 --dpi-desync-fooling badseq --dpi-desync-fake-tls \"C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\bin\tls_clienthello_www_google_com.bin\"" DisplayName= "zapret" start= auto | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 492
Read events
27 430
Write events
61
Delete events
1
Modification events
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1).rar | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
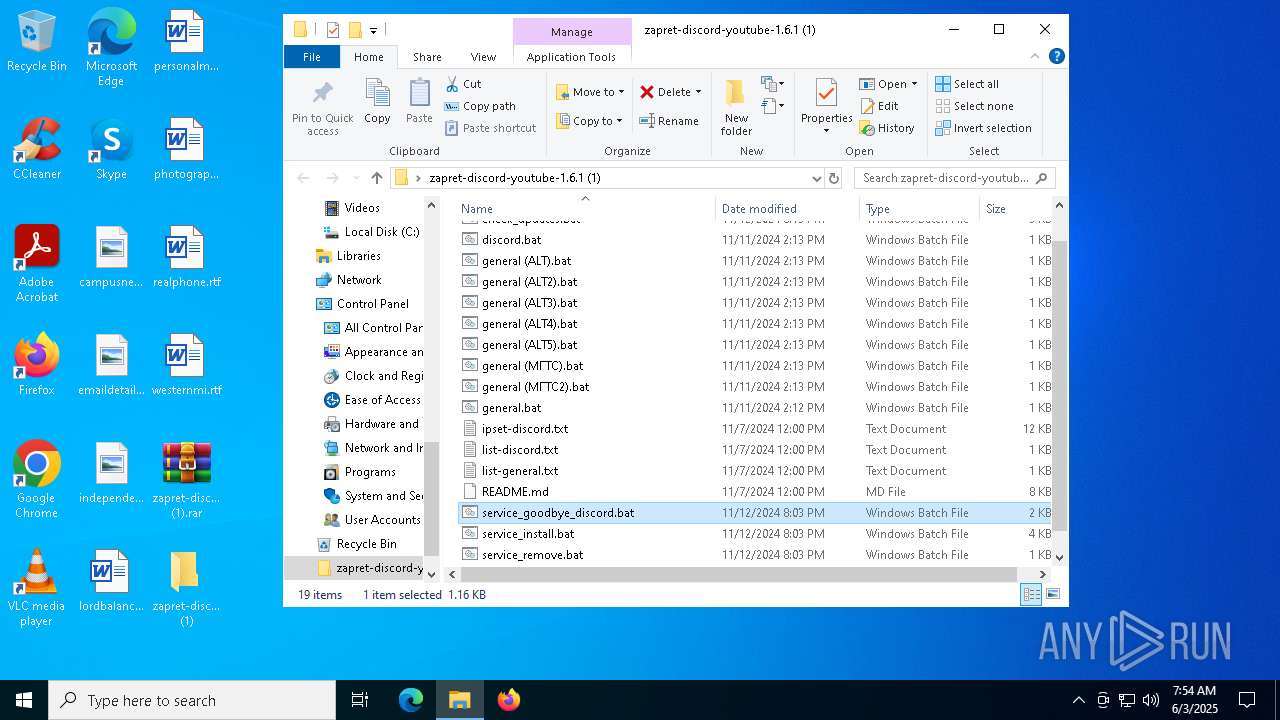
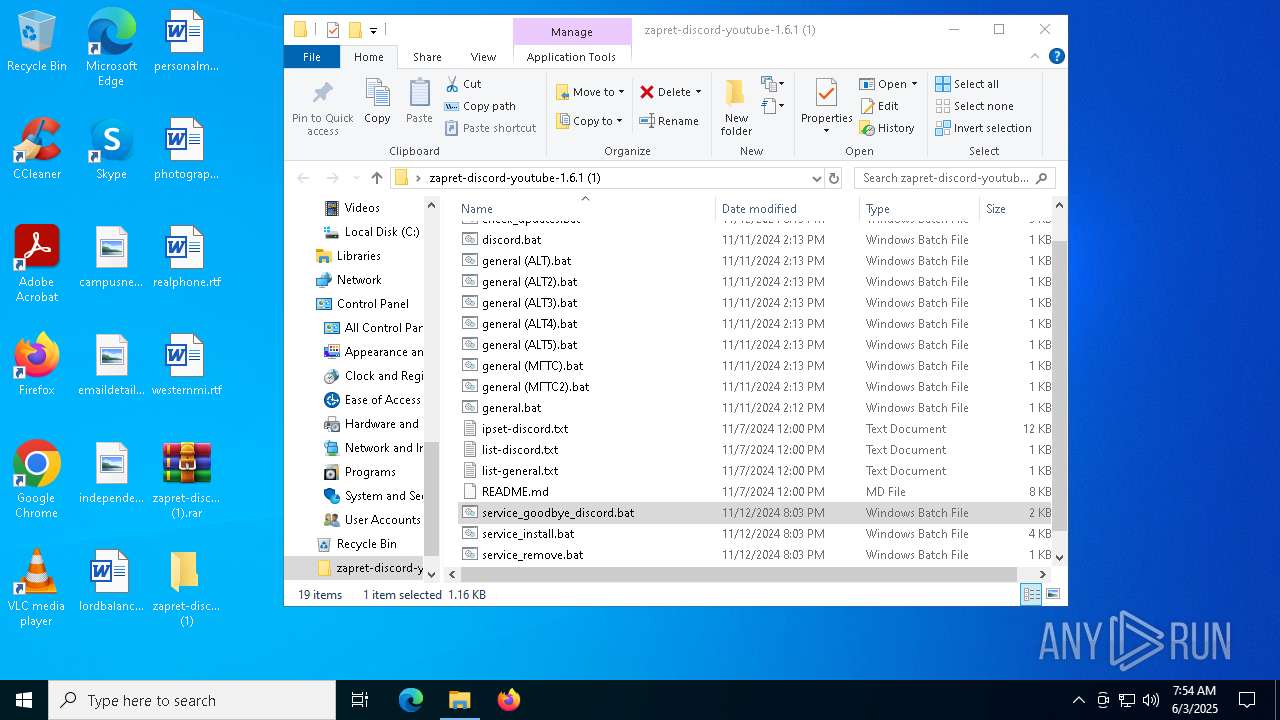
Executable files
4
Suspicious files
3
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
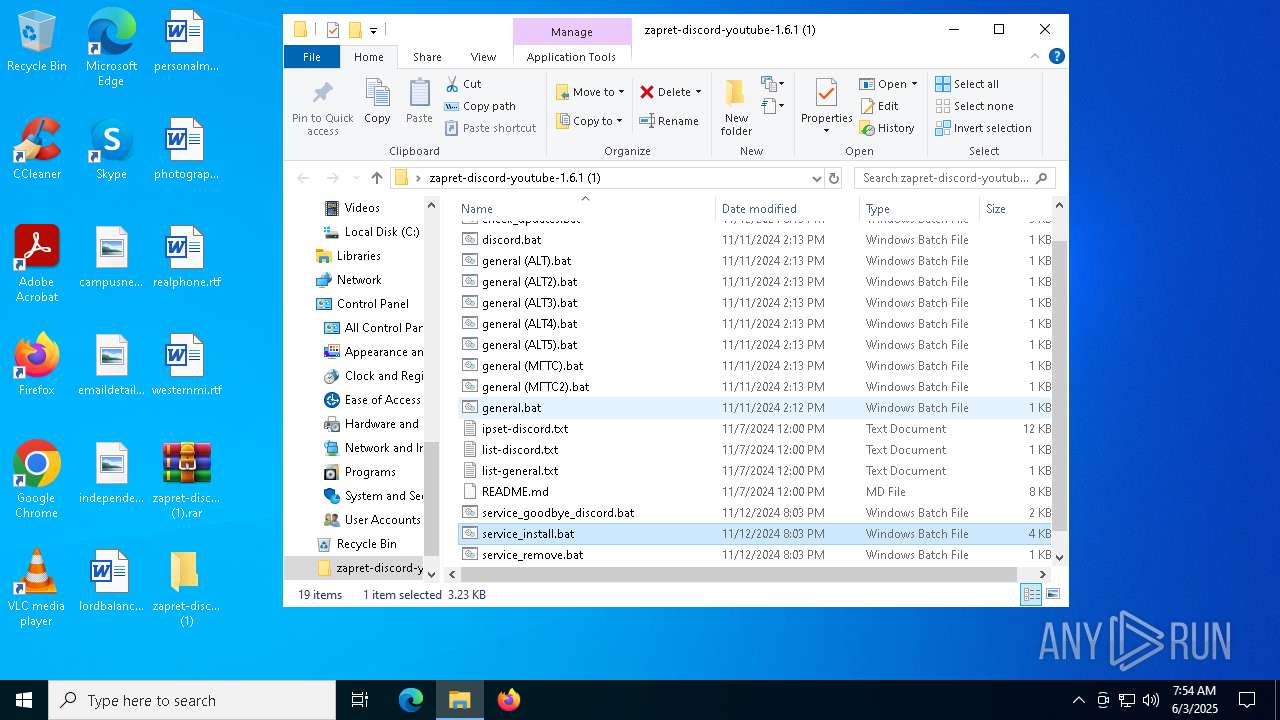
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\README.md | html | |
MD5:1C1C8E2DA620A9988B305ECD13E8E8FF | SHA256:A3D9D6C4BA590F5B8790BCDB68258425FD268534588A7B74E4EF926336FD653B | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\service_install.bat | text | |
MD5:55D22378709DC7EA40E84CADCED29E4A | SHA256:A77AC7ABD0ADCB995C701019BFE2D67133D6D0F94D90754046A13ADE40ADF693 | |||
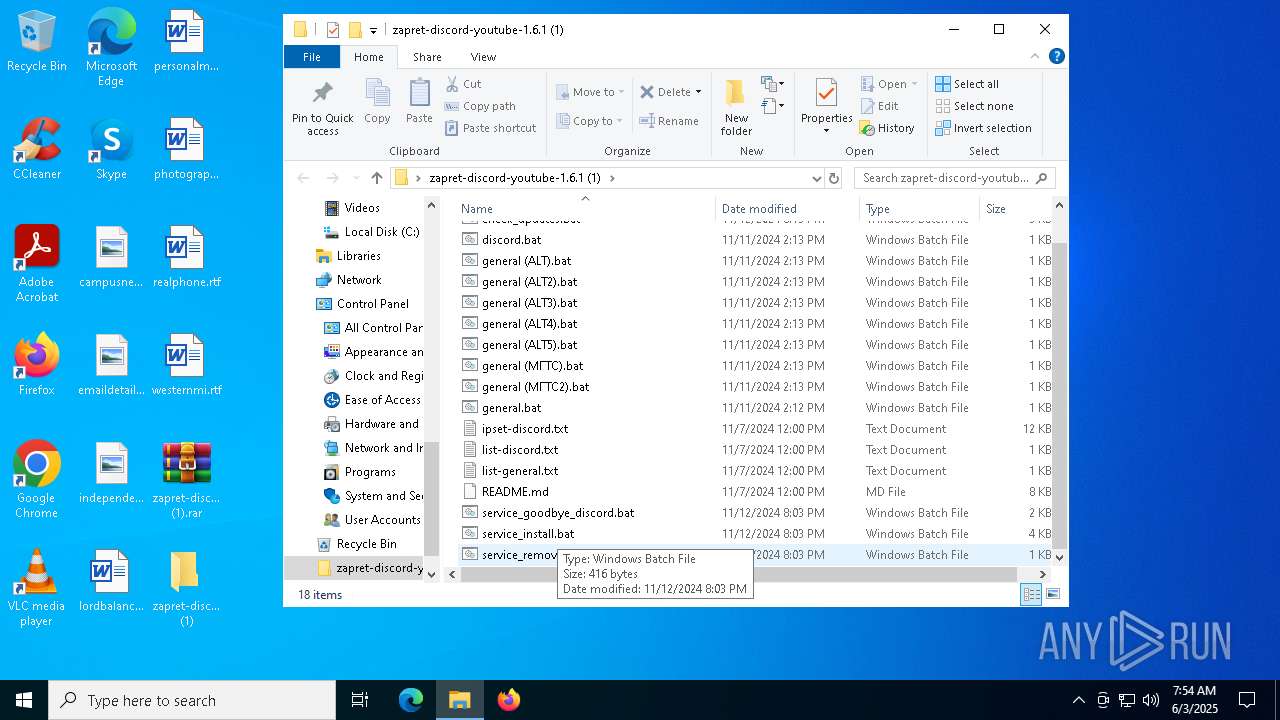
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\service_remove.bat | text | |
MD5:F7AD12616404A382B1689C9E3937C9E5 | SHA256:9D8F0B7105D86DE09B9408515F30B2BC2BB935430F4E73196021368906B7F128 | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\bin\tls_clienthello_www_google_com.bin | binary | |
MD5:7AB7AD857C5B8794FBDF1091B494DC94 | SHA256:E5938780152169F720383F80EABB309E9477369B83B5EC40CC137C397F862CDE | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\check_updates.bat | text | |
MD5:C0AF479B986A7E2095929A68136CD97C | SHA256:438ADFB9F66429E1B6B0474FE0CDBD397098D58C4B80FF2C74237C6F9B99DF23 | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\service_goodbye_discord.bat | text | |
MD5:8B043F2A0EC87328DC40542B9739988F | SHA256:263102816588BD719FC628A75C8B73185110050564EA21A62B360F3AE545022B | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\bin\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\general (ALT3).bat | text | |
MD5:6E0FD8729815F1941C5FD4016C888EC5 | SHA256:198FDA8A2FC02A4A501F13B67D1232DFCB3157075D3AB76494D17C64742E82D3 | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\general (ALT4).bat | text | |
MD5:D731B6B9E4E68B70CAB7721FD84AF920 | SHA256:8CA143406A8D2007CF6E123DA7D7DD8898BF230DAEA1A6D79DE5A104D323E82B | |||
| 4628 | WinRAR.exe | C:\Users\admin\Desktop\zapret-discord-youtube-1.6.1 (1)\discord.bat | text | |
MD5:C01056F88C8646CAB2D85A31F44F1186 | SHA256:21ADF614F58D39396C49BF10AE3F6187905F328E24D7363372D299F821D18CF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4628 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5796 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6592 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |