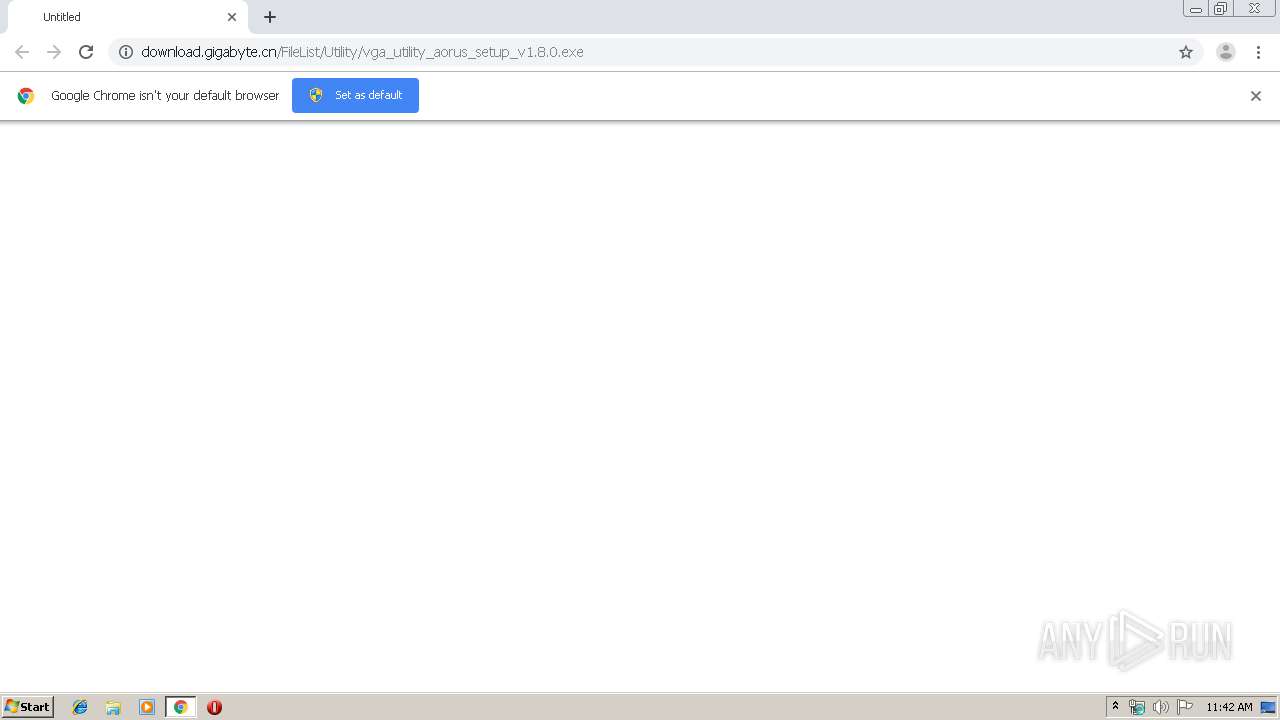
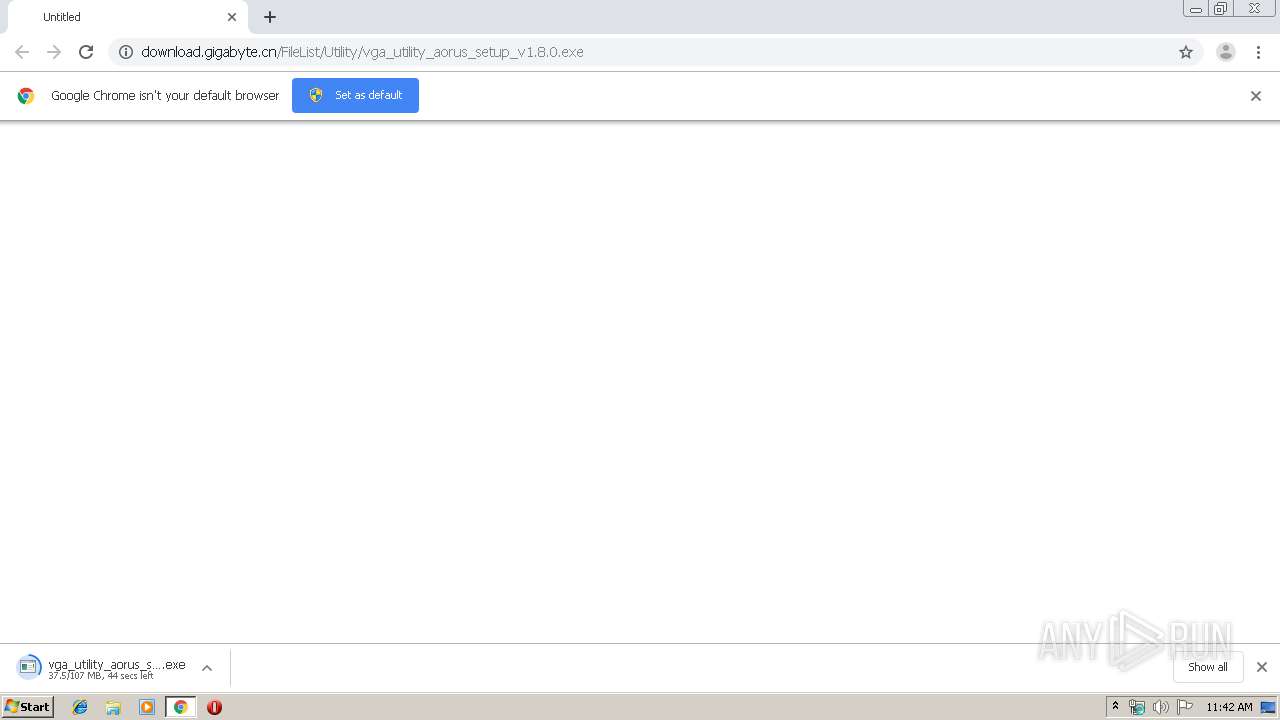
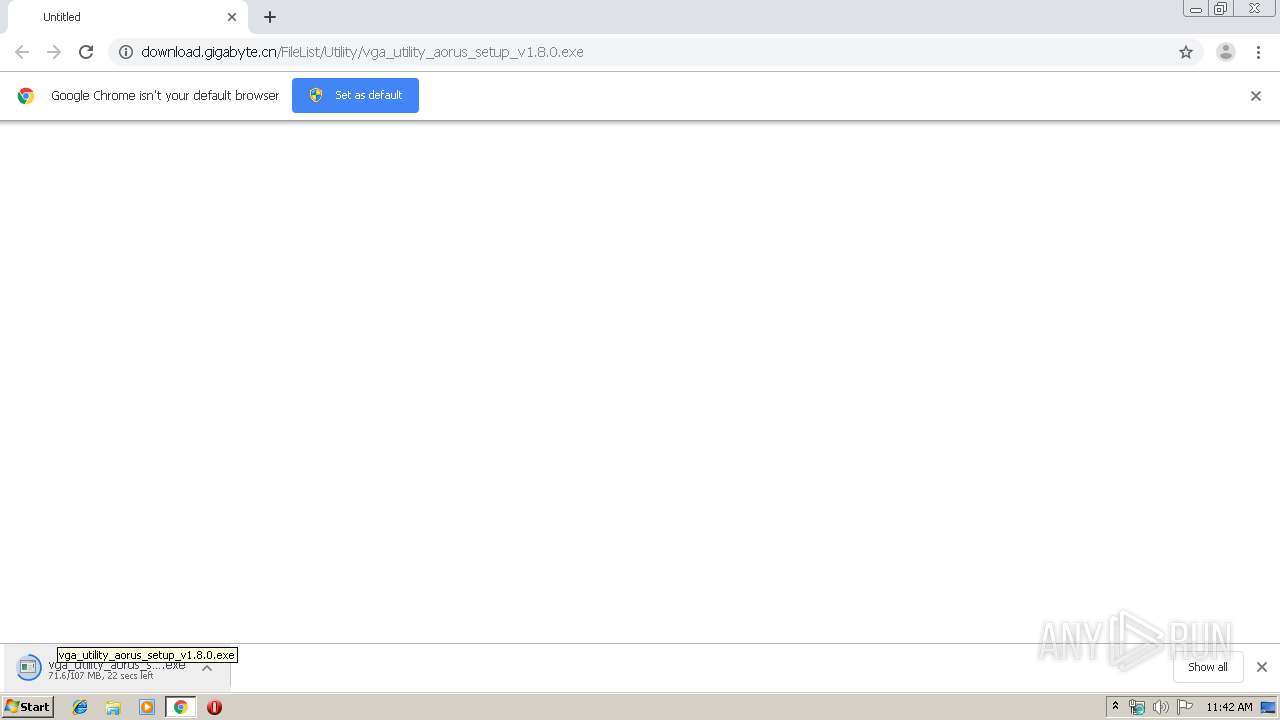
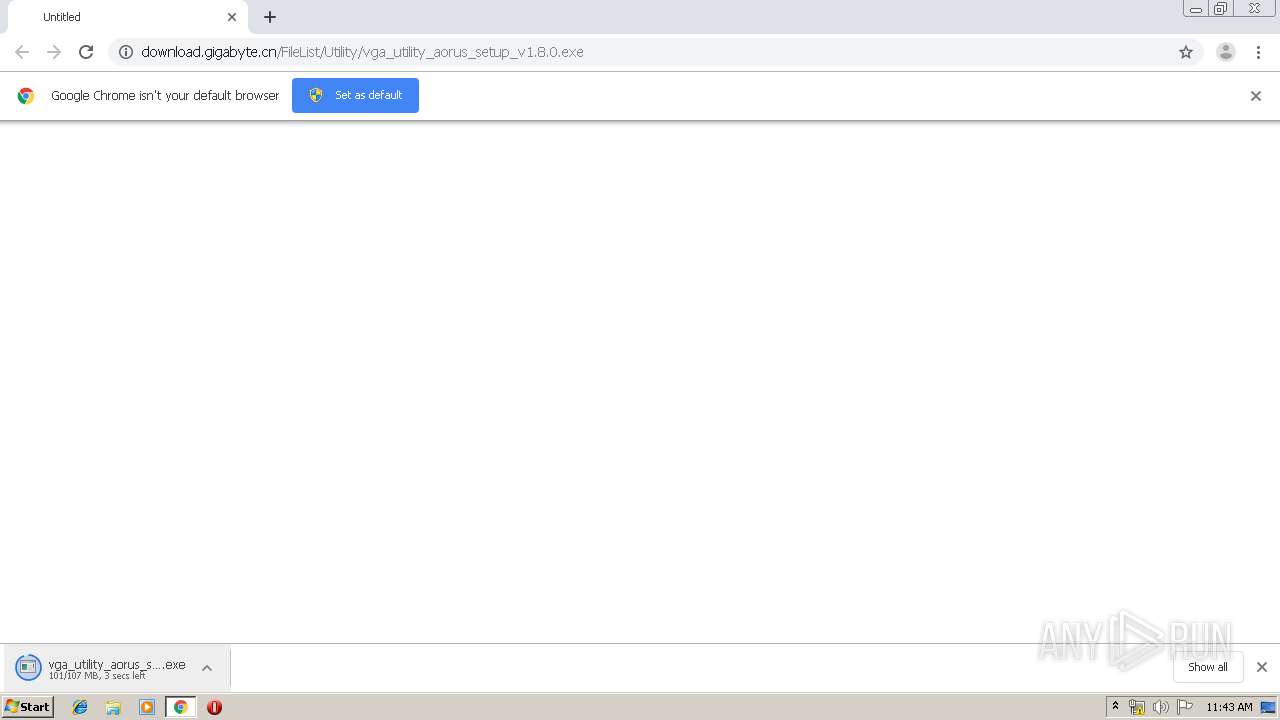
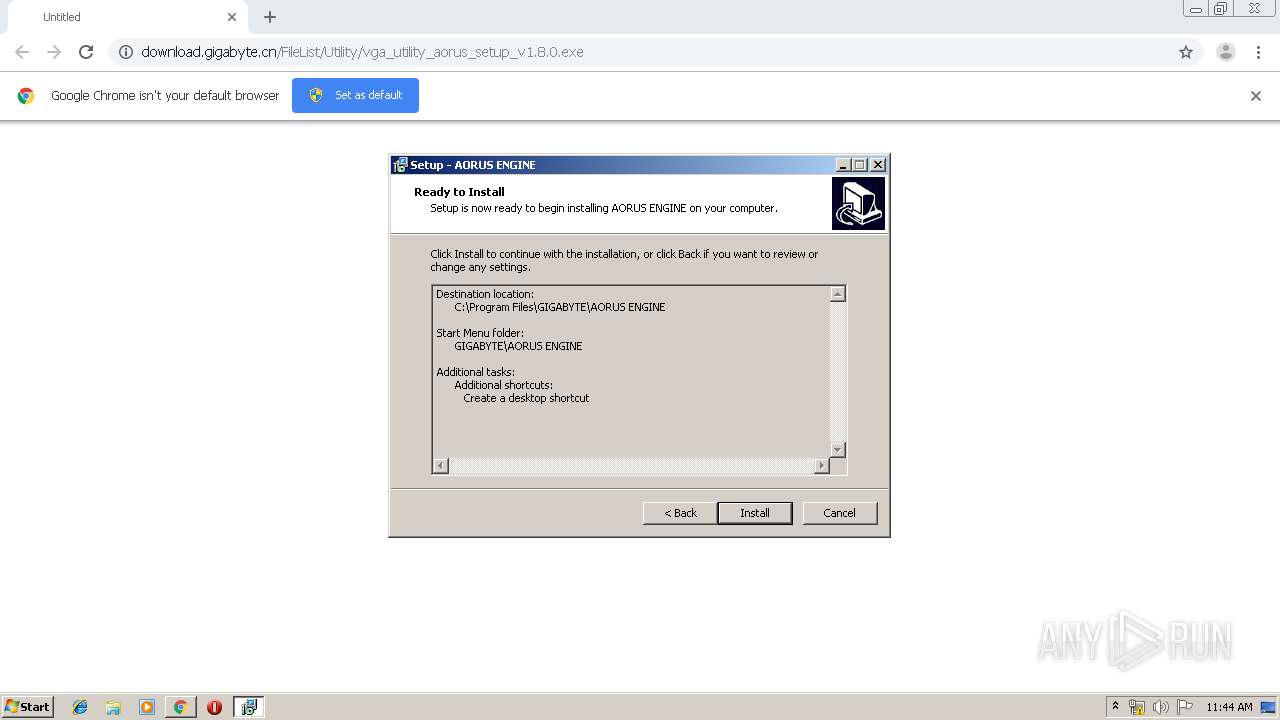
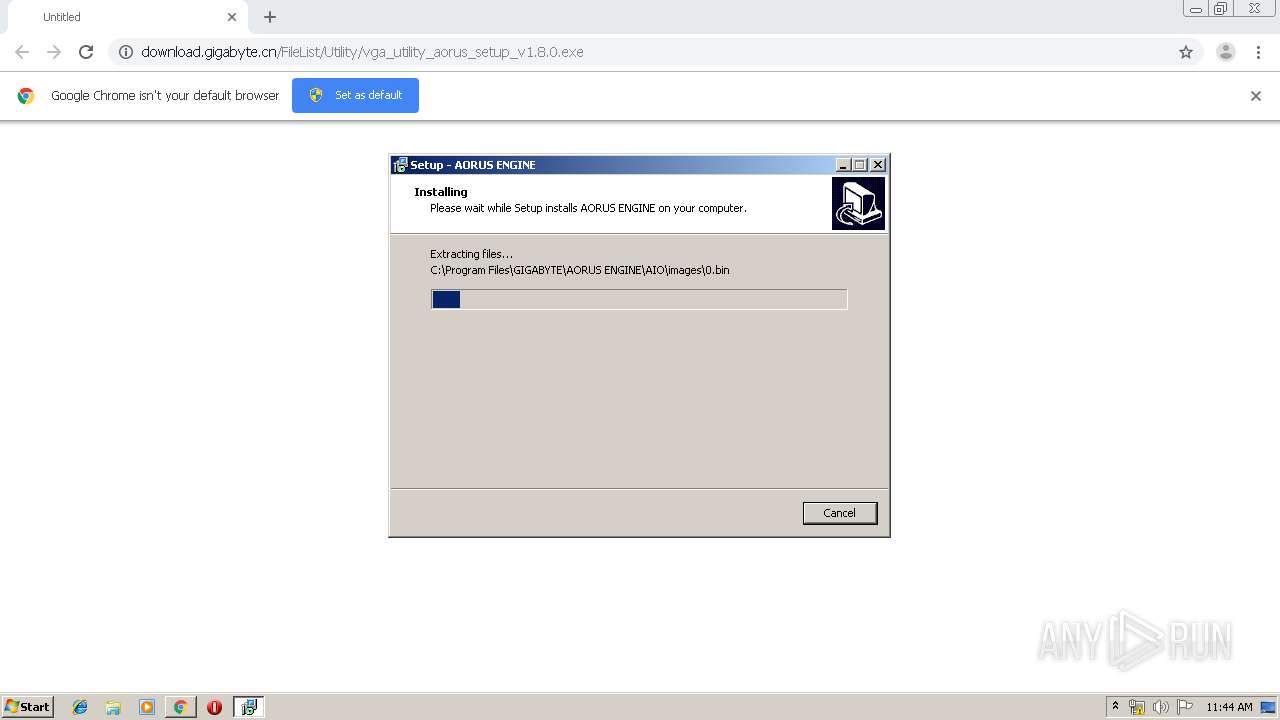
| URL: | http://download.gigabyte.cn/FileList/Utility/vga_utility_aorus_setup_v1.8.0.exe |
| Full analysis: | https://app.any.run/tasks/04ab9b03-0408-48c6-a424-93d66e2a0291 |
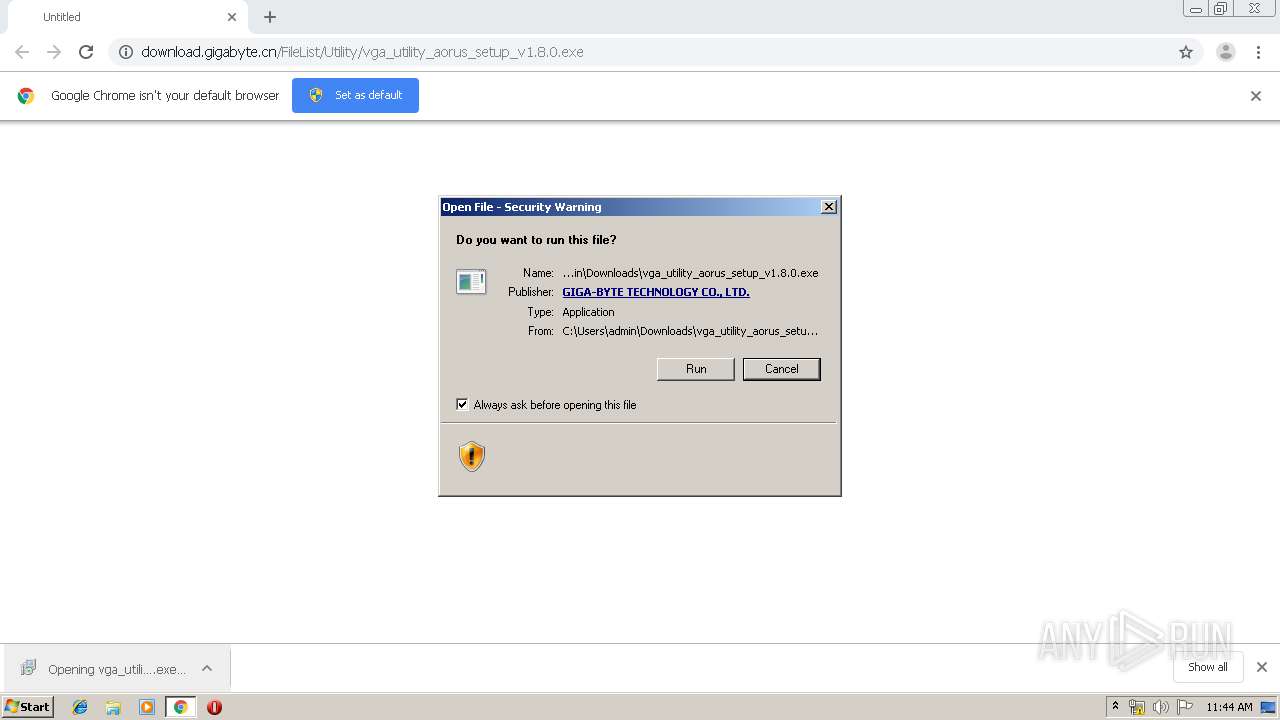
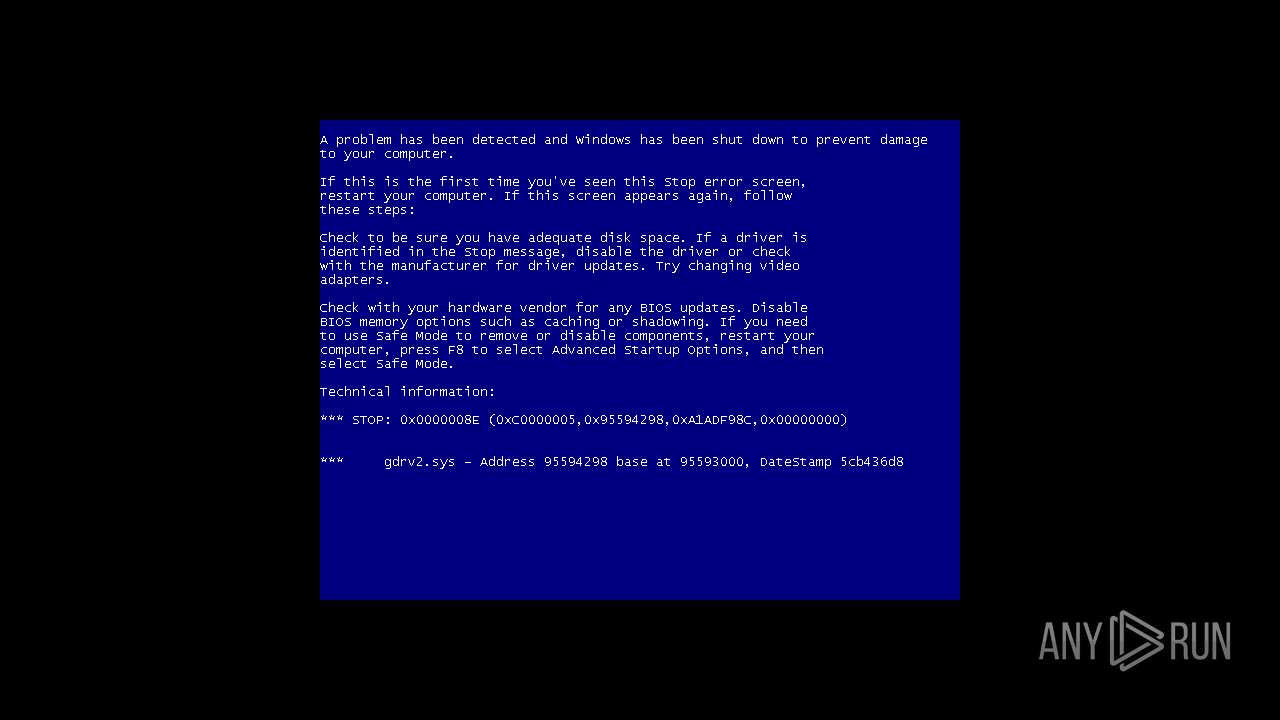
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 11:41:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA3AF3A075C21C53E6784D64652429B4 |
| SHA1: | 799BB4B2BC06CDA6882BA97435252323454F464F |
| SHA256: | 2AAB29838199E03FB3CA6C44FA0DDCB21A51EE12E32F718B4F3588B5EACA2D9C |
| SSDEEP: | 3:N1KaKEl6P4LBFH7RIMRcSAW6W+Ypfn:Ca56P4LBF+QcZ9WRn |
MALICIOUS
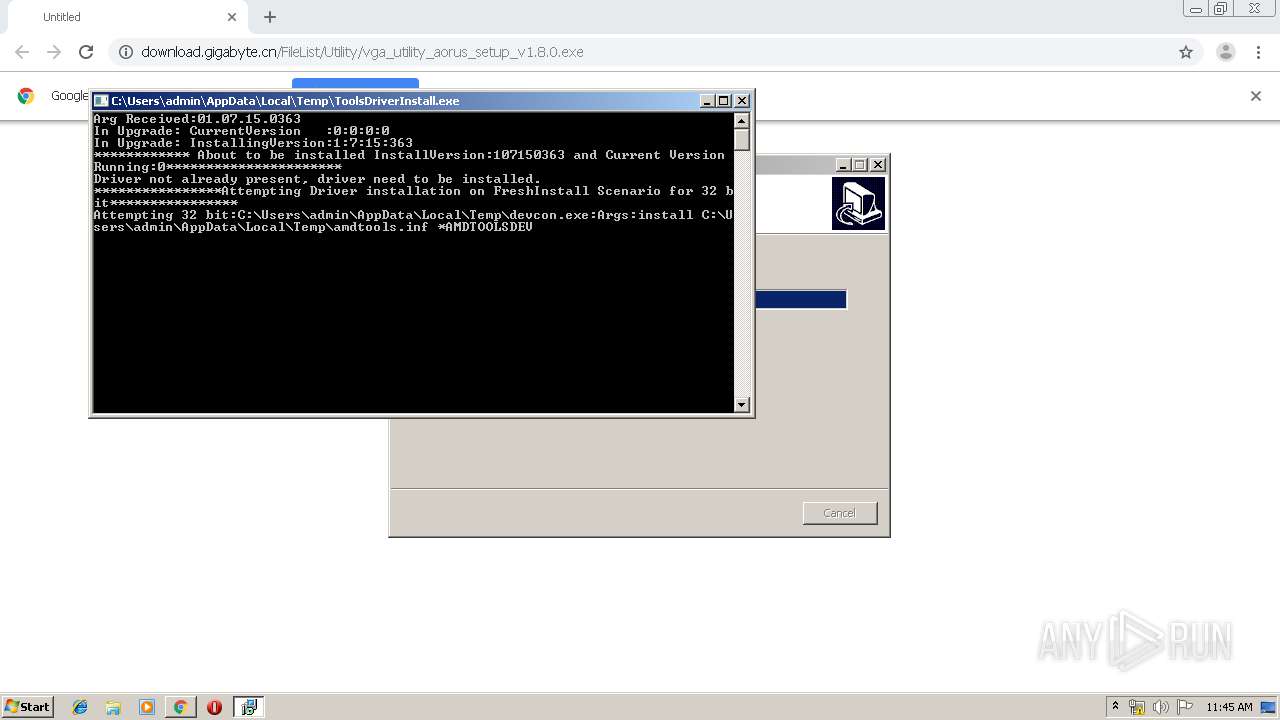
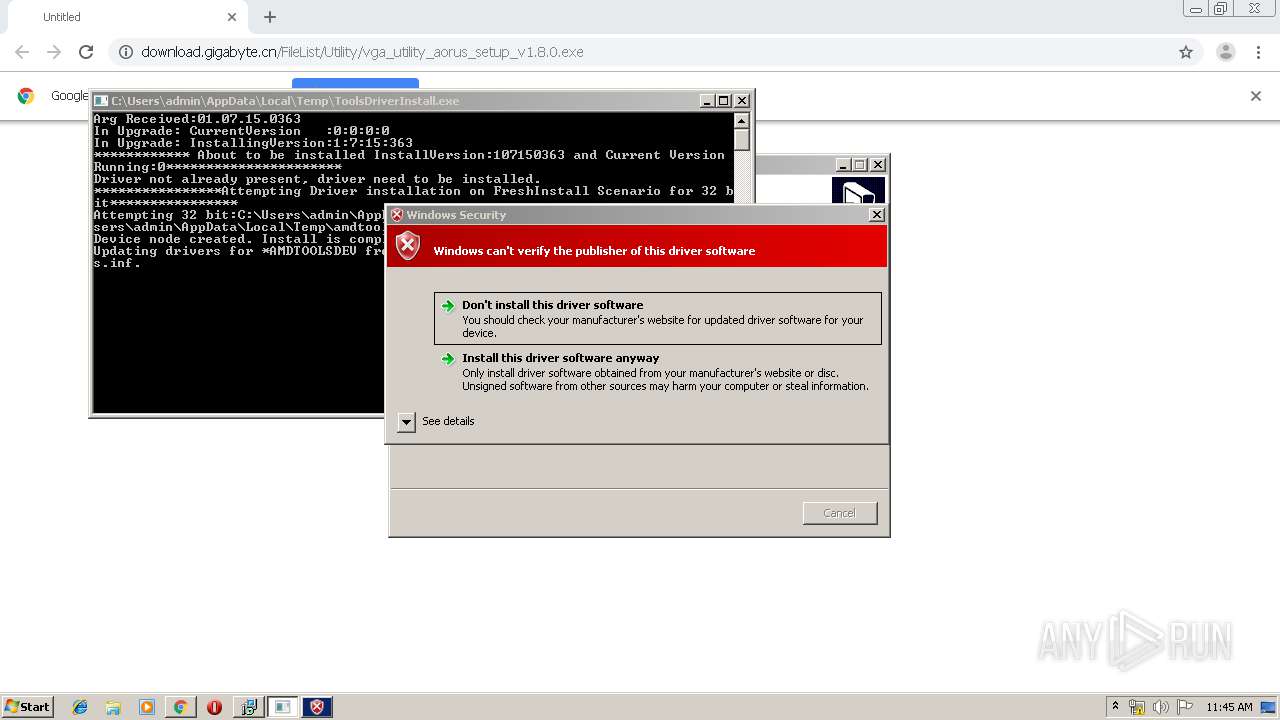
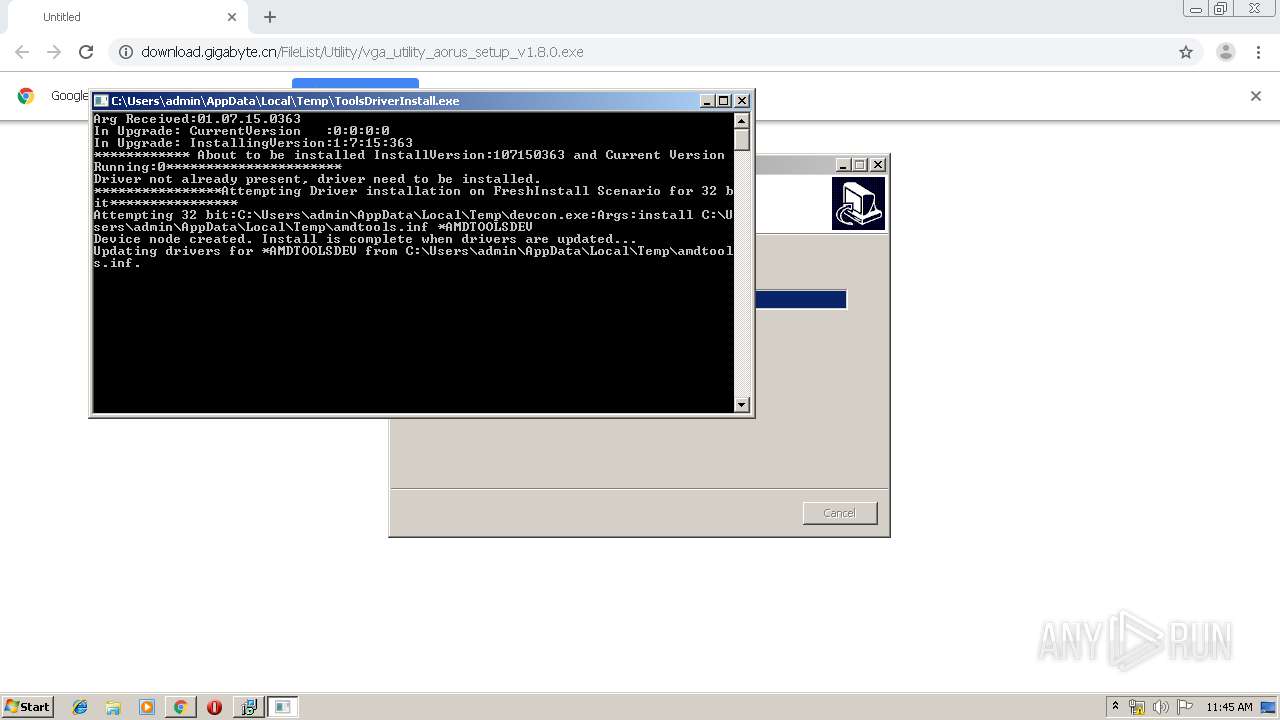
Application was dropped or rewritten from another process
- vga_utility_aorus_setup_v1.8.0.exe (PID: 640)
- vga_utility_aorus_setup_v1.8.0.exe (PID: 4076)
- vcredist_x64.exe (PID: 3632)
- vcredist_x64.exe (PID: 1268)
- vcredist_x86.exe (PID: 2296)
- installAMD.exe (PID: 2668)
- insttool.exe (PID: 1784)
- ToolsDriverInstall.exe (PID: 3828)
- devcon.exe (PID: 3028)
- vcredist_x86.exe (PID: 3584)
- devcon.exe (PID: 2548)
- autorun.exe (PID: 792)
- N2080_FW_Upgrade_Tool_V004.exe (PID: 1532)
- AORUS.exe (PID: 1908)
- FWUpgrade.exe (PID: 3856)
- Launcher.exe (PID: 2628)
- Gv.exe (PID: 1732)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 2296)
Loads dropped or rewritten executable
- vcredist_x64.exe (PID: 3632)
- vcredist_x86.exe (PID: 3584)
- FWUpgrade.exe (PID: 3856)
- AORUS.exe (PID: 1908)
- Gv.exe (PID: 1732)
Uses Task Scheduler to run other applications
- autorun.exe (PID: 792)
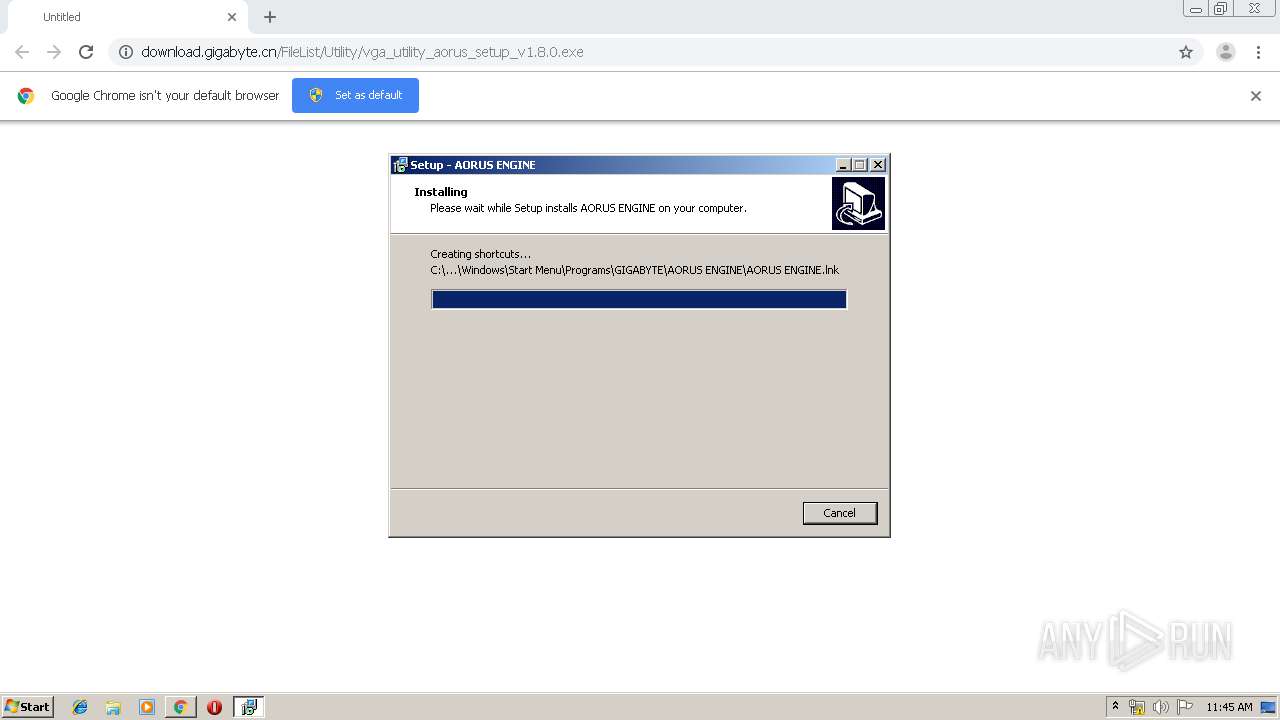
Writes to a start menu file
- autorun.exe (PID: 792)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1788)
SUSPICIOUS
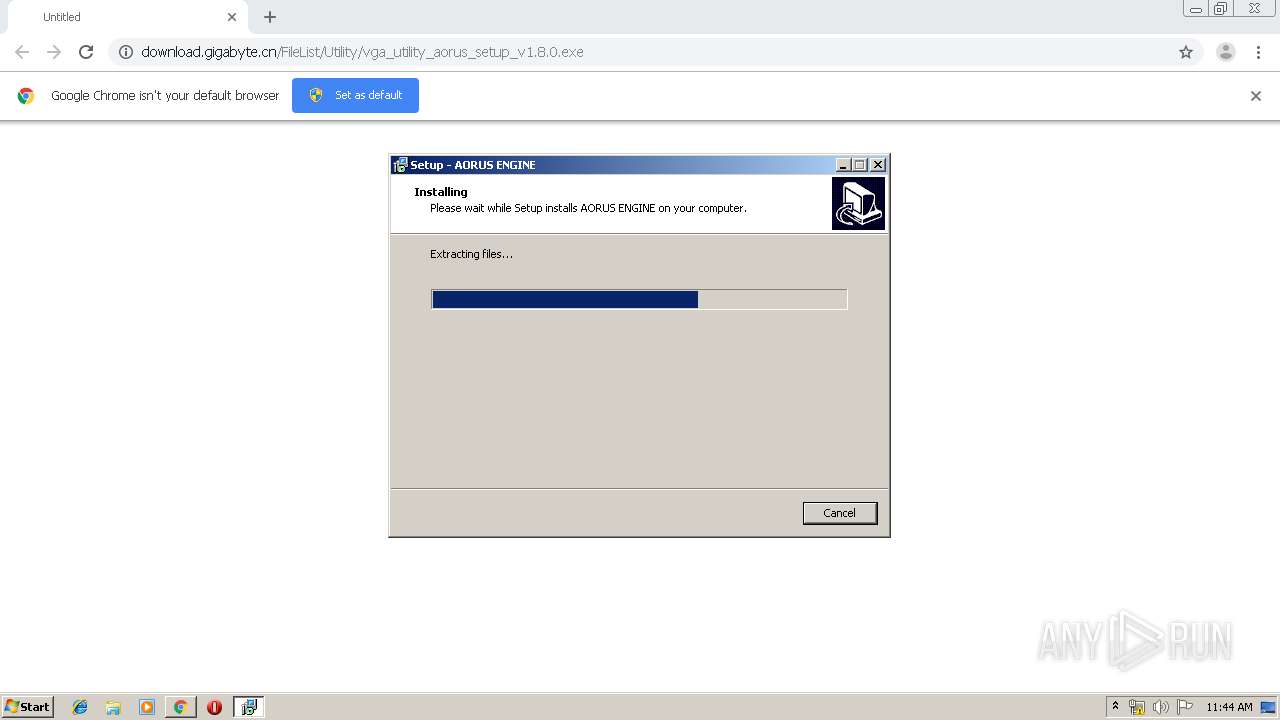
Executable content was dropped or overwritten
- chrome.exe (PID: 2344)
- vga_utility_aorus_setup_v1.8.0.exe (PID: 640)
- vga_utility_aorus_setup_v1.8.0.exe (PID: 4076)
- vcredist_x86.exe (PID: 3584)
- vcredist_x86.exe (PID: 2296)
- msiexec.exe (PID: 2240)
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
- insttool.exe (PID: 1784)
- devcon.exe (PID: 3028)
- DrvInst.exe (PID: 2424)
- DrvInst.exe (PID: 4060)
- N2080_FW_Upgrade_Tool_V004.exe (PID: 1532)
- AORUS.exe (PID: 1908)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2004)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 2848)
Reads the Windows organization settings
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Reads Windows owner or organization settings
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Starts CMD.EXE for commands execution
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Searches for installed software
- vcredist_x64.exe (PID: 3632)
- vcredist_x86.exe (PID: 2296)
- vcredist_x86.exe (PID: 3584)
Application launched itself
- vcredist_x86.exe (PID: 2296)
Executed as Windows Service
- vssvc.exe (PID: 3900)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 2296)
Creates files in the program directory
- vcredist_x86.exe (PID: 2296)
Creates files in the Windows directory
- msiexec.exe (PID: 2240)
- DrvInst.exe (PID: 2424)
- AORUS.exe (PID: 1908)
- DrvInst.exe (PID: 4060)
Executed via COM
- DrvInst.exe (PID: 2424)
- DrvInst.exe (PID: 4060)
- rundll32.exe (PID: 2884)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2344)
Removes files from Windows directory
- DrvInst.exe (PID: 2424)
- DrvInst.exe (PID: 4060)
Creates files in the driver directory
- DrvInst.exe (PID: 2424)
- DrvInst.exe (PID: 4060)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2424)
Creates or modifies windows services
- DrvInst.exe (PID: 4060)
Creates files in the user directory
- autorun.exe (PID: 792)
INFO
Application launched itself
- chrome.exe (PID: 2344)
Reads the hosts file
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2344)
Application was dropped or rewritten from another process
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 3468)
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Creates files in the user directory
- chrome.exe (PID: 2344)
Reads Internet Cache Settings
- chrome.exe (PID: 2344)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3900)
Creates files in the program directory
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Dropped object may contain Bitcoin addresses
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Creates a software uninstall entry
- msiexec.exe (PID: 2240)
- vga_utility_aorus_setup_v1.8.0.tmp (PID: 1636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
65
Malicious processes
8
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13817098721703345053 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Users\admin\Downloads\vga_utility_aorus_setup_v1.8.0.exe" | C:\Users\admin\Downloads\vga_utility_aorus_setup_v1.8.0.exe | chrome.exe | ||||||||||||
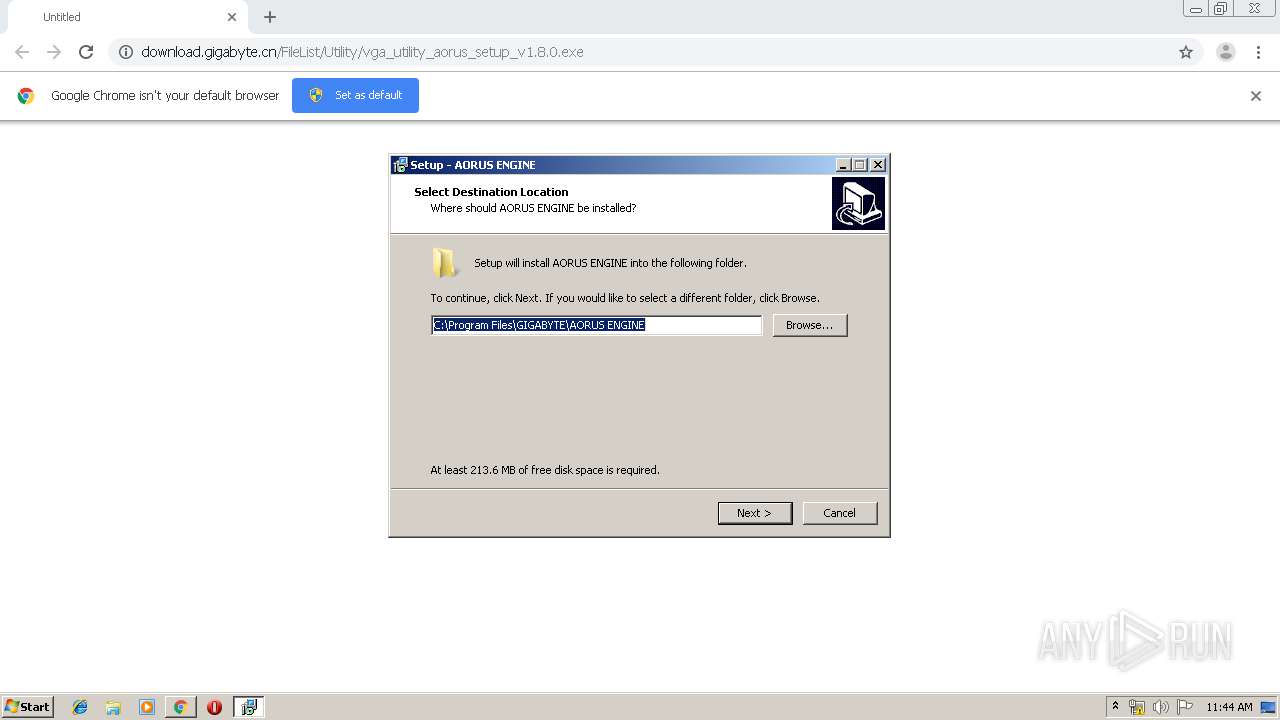
User: admin Company: GIGABYTE Technology Co.,Inc. Integrity Level: MEDIUM Description: GIGABYTE AORUS ENGINE Software. Exit code: 0 Version: 1.8.0.0 Modules
| |||||||||||||||
| 716 | taskkill /f /im FurMark_XTREME_Edition_x32.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 792 | "C:\Program Files\GIGABYTE\AORUS ENGINE\autorun.exe" /c | C:\Program Files\GIGABYTE\AORUS ENGINE\autorun.exe | vga_utility_aorus_setup_v1.8.0.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1082283399599336296 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8703407933147754130 --mojo-platform-channel-handle=4024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\GIGABYTE\AORUS ENGINE\vcredist_x64.exe" /quiet | C:\Program Files\GIGABYTE\AORUS ENGINE\vcredist_x64.exe | — | vga_utility_aorus_setup_v1.8.0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x64) - 11.0.61030 Exit code: 2180251649 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14150017854240913890 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2412 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15807759753557044284 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 422
Read events
2 715
Write events
673
Delete events
34
Modification events
| (PID) Process: | (1296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2344-13223648533518375 |
Value: 259 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
157
Suspicious files
46
Text files
456
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\537ba5e0-5eb3-4f64-83ea-1918ad176171.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39aa25.TMP | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1324 | chrome.exe | GET | — | 163.171.144.39:80 | http://download.gigabyte.cn/FileList/Utility/vga_utility_aorus_setup_v1.8.0.exe | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1324 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1324 | chrome.exe | 163.171.144.39:80 | download.gigabyte.cn | — | US | malicious |
1324 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
1324 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1324 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1324 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
download.gigabyte.cn |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1324 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |