| File name: | SYS Informer.exe |
| Full analysis: | https://app.any.run/tasks/ed0fbcbe-797a-4311-9f98-53eb0c405d47 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2024, 07:13:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B6FB6E5F34744834E5B8771FA236A0DC |
| SHA1: | 155B34AA9BA383201A37A8B43943C6CA249AD4DC |
| SHA256: | 2A9AE75D674E77136545EA9BB4301AFDC408A21EF0FF0F68146FE4327EDCA990 |
| SSDEEP: | 49152:SI/RR5H2v4xEQ1aBB6BDBXBkBPBB2BBBBBBBBBBBBBBj9bUBBBBBBuBBBBBkBBzl:SI1HsEw6eYGGGGe |
MALICIOUS
Drops the executable file immediately after the start
- SYS Informer.exe (PID: 6328)
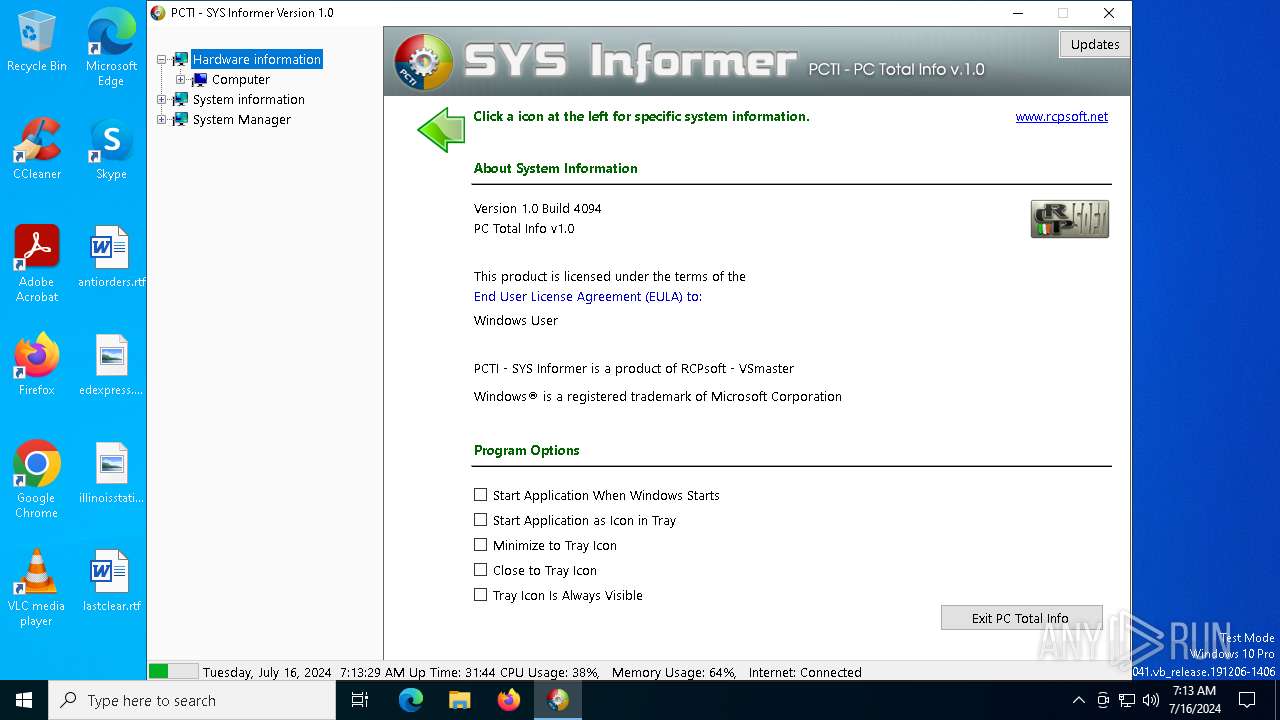
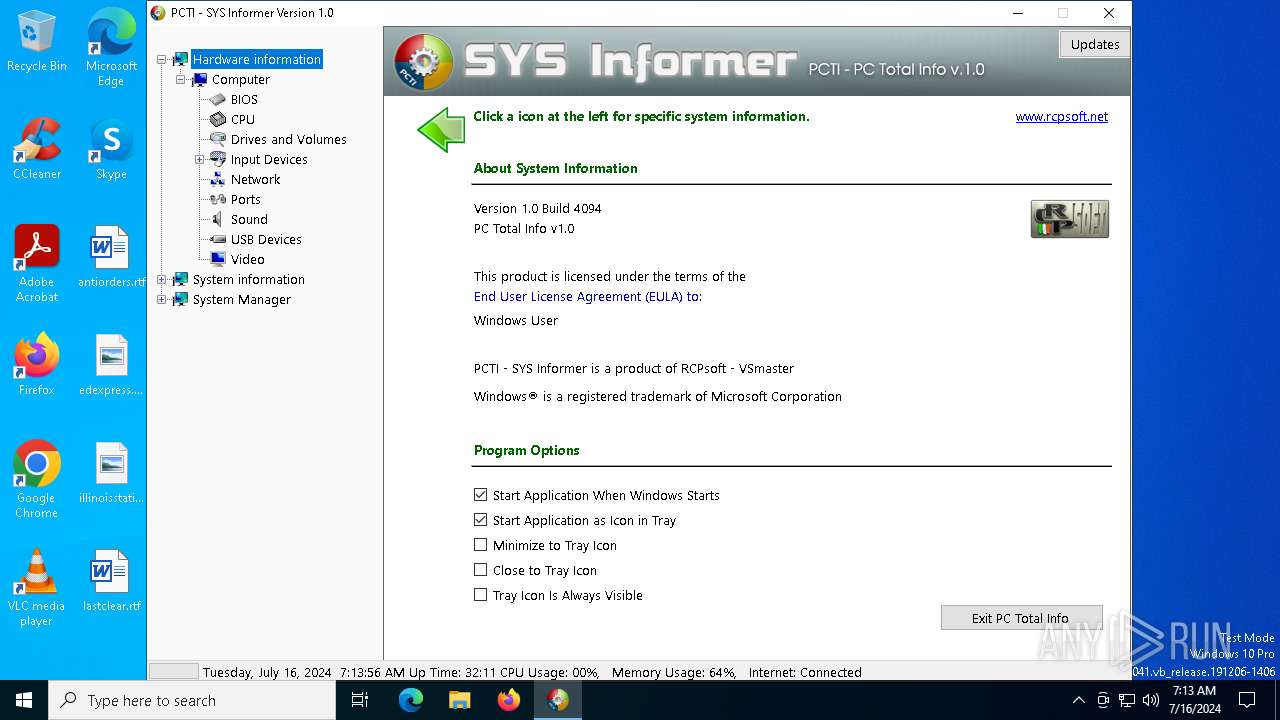
Changes the autorun value in the registry
- SYS Informer.exe (PID: 6328)
SUSPICIOUS
Executes as Windows Service
- WmiApSrv.exe (PID: 7132)
The process checks if it is being run in the virtual environment
- SYS Informer.exe (PID: 6328)
Reads security settings of Internet Explorer
- SYS Informer.exe (PID: 6328)
Reads the Windows owner or organization settings
- SYS Informer.exe (PID: 6328)
Reads Internet Explorer settings
- SYS Informer.exe (PID: 6328)
INFO
Reads the machine GUID from the registry
- SYS Informer.exe (PID: 6328)
Checks supported languages
- SYS Informer.exe (PID: 6328)
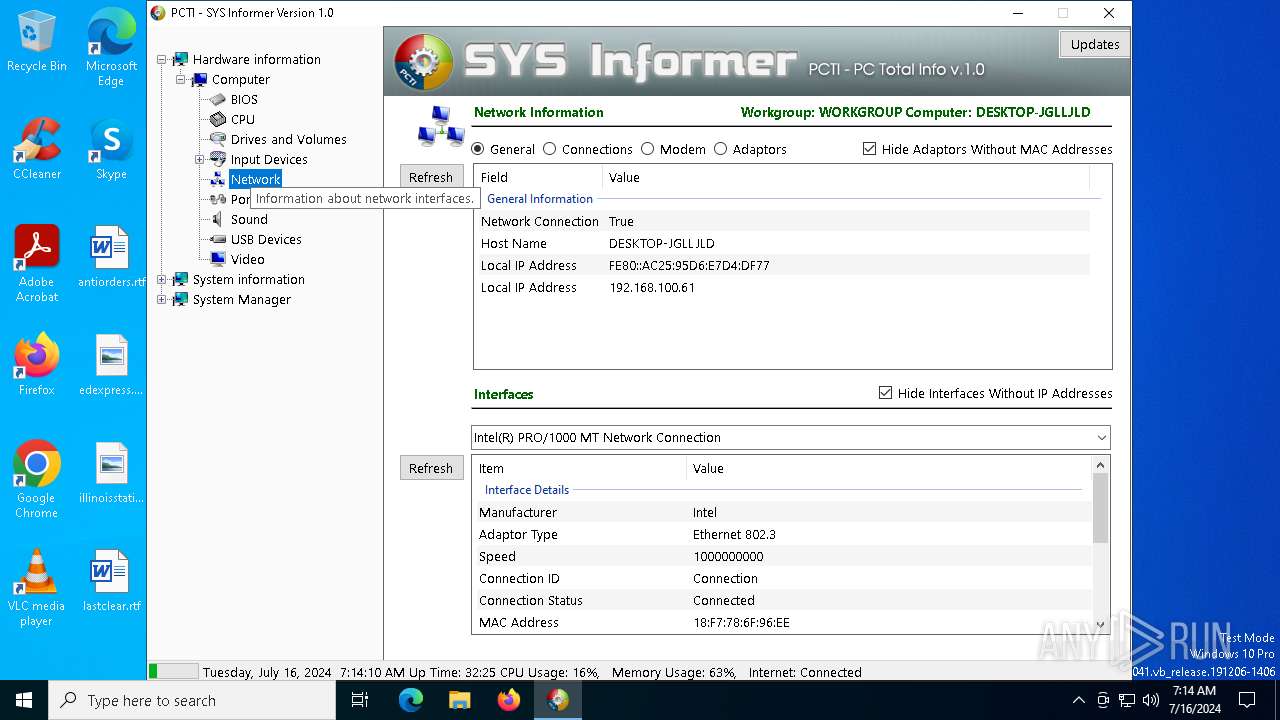
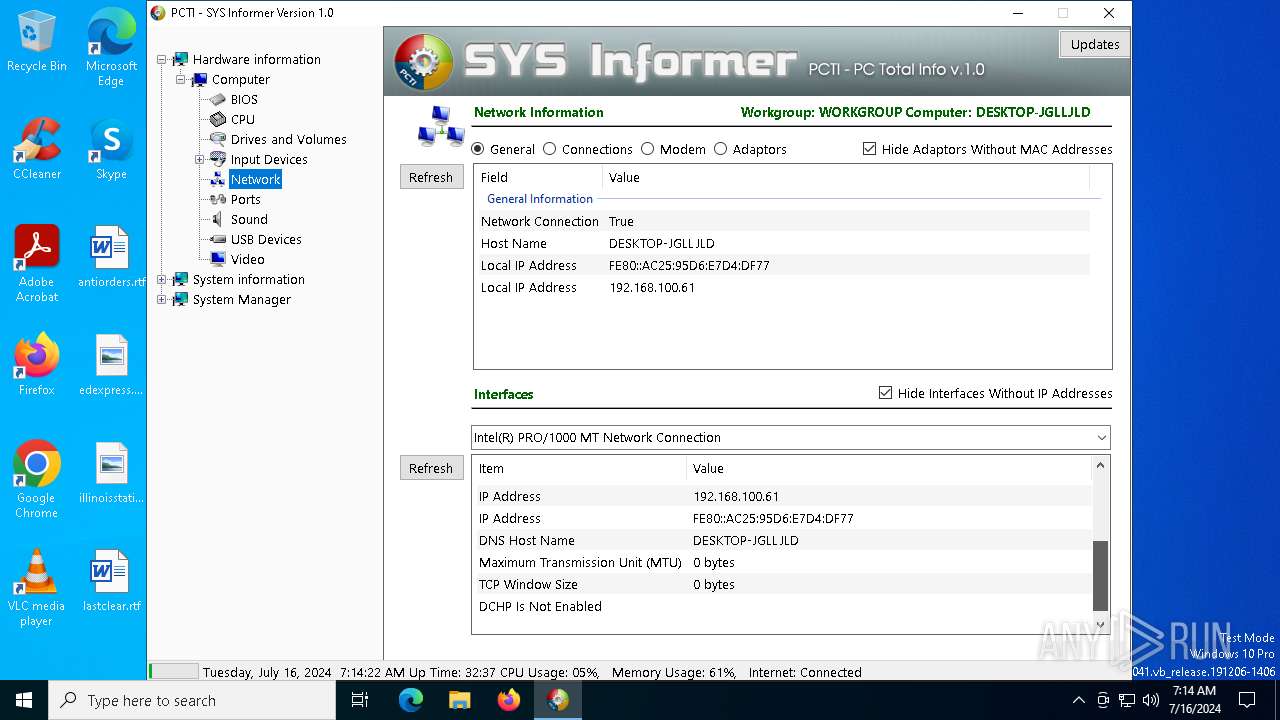
Reads the computer name
- SYS Informer.exe (PID: 6328)
Reads Environment values
- SYS Informer.exe (PID: 6328)
Reads the time zone
- SYS Informer.exe (PID: 6328)
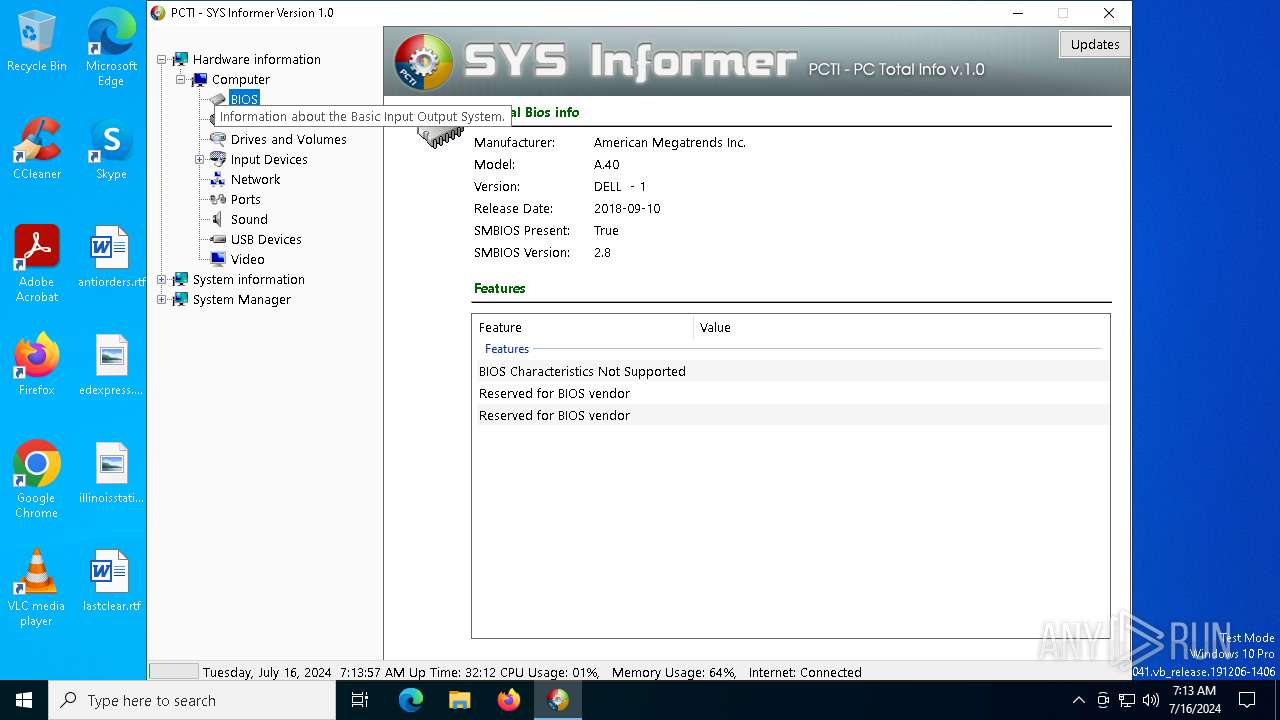
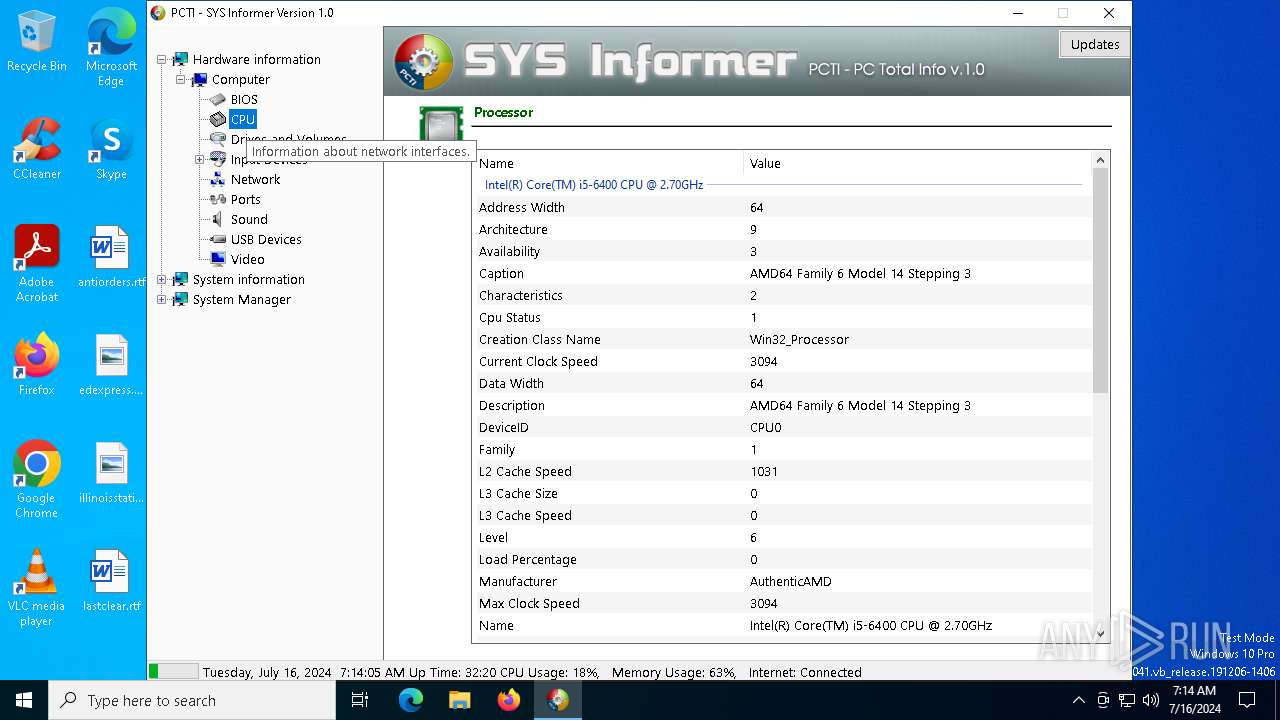
Reads CPU info
- SYS Informer.exe (PID: 6328)
Checks proxy server information
- SYS Informer.exe (PID: 6328)
Creates files or folders in the user directory
- SYS Informer.exe (PID: 6328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:03:18 06:17:50+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3563008 |
| InitializedDataSize: | 373248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x367cee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
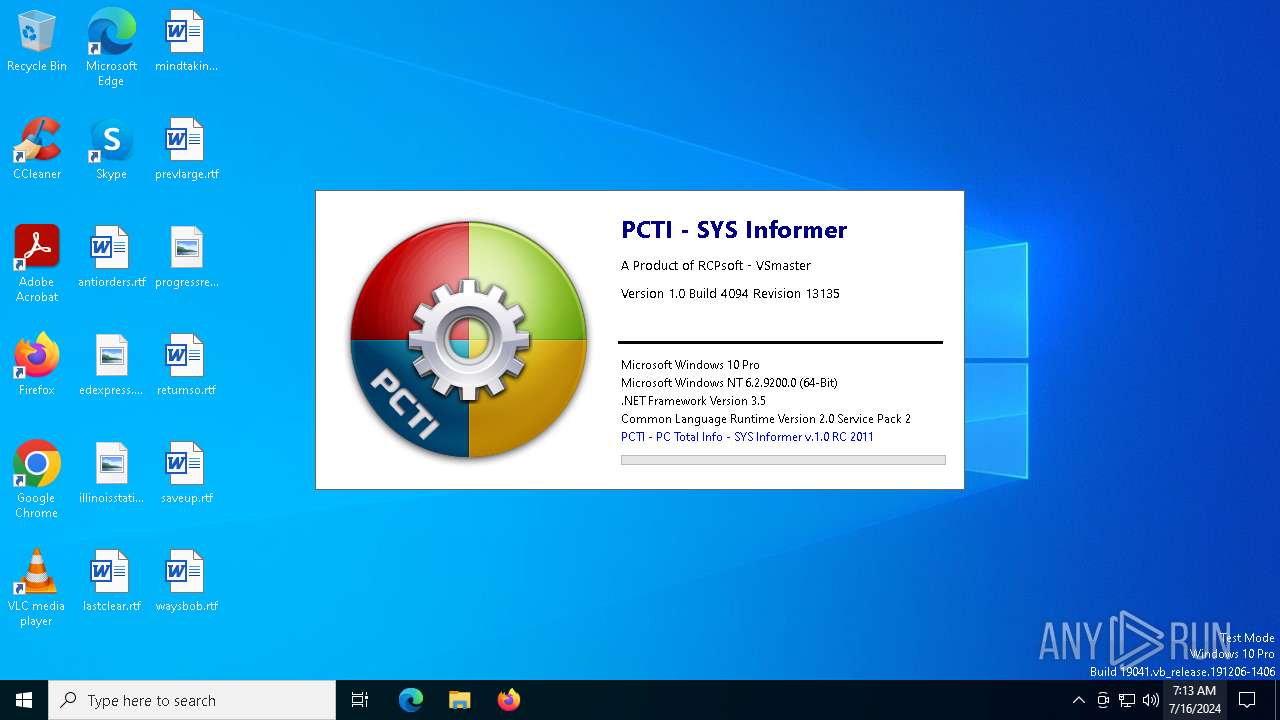
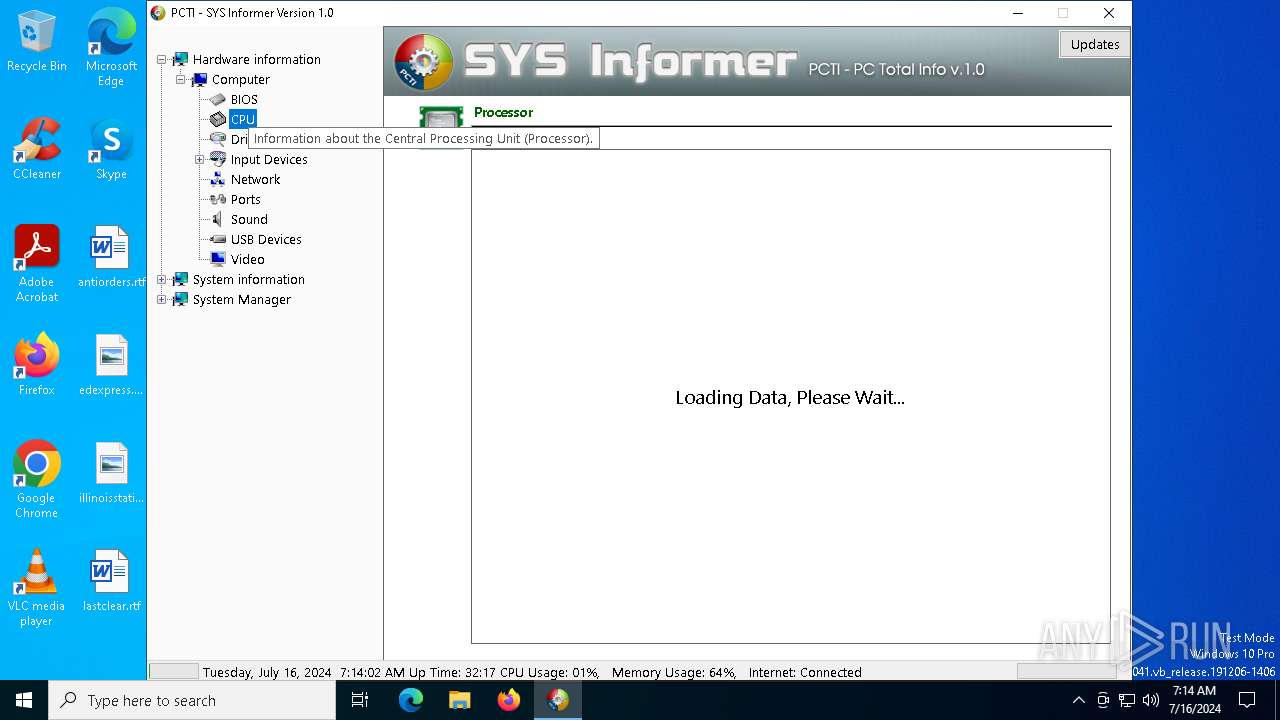
| Comments: | PC Total Info v1.0 |
| CompanyName: | RCPsoft - VSmaster |
| FileDescription: | PCTI - SYS Informer |
| FileVersion: | 1.0.0.0 |
| InternalName: | SYS Informer.exe |
| LegalCopyright: | |
| OriginalFileName: | SYS Informer.exe |
| ProductName: | PC Total Info- SYS Informer |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.4094.13135 |
Total processes
138
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6172 | "C:\Users\admin\AppData\Local\Temp\SYS Informer.exe" | C:\Users\admin\AppData\Local\Temp\SYS Informer.exe | — | explorer.exe | |||||||||||
User: admin Company: RCPsoft - VSmaster Integrity Level: MEDIUM Description: PCTI - SYS Informer Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6328 | "C:\Users\admin\AppData\Local\Temp\SYS Informer.exe" | C:\Users\admin\AppData\Local\Temp\SYS Informer.exe | explorer.exe | ||||||||||||
User: admin Company: RCPsoft - VSmaster Integrity Level: HIGH Description: PCTI - SYS Informer Version: 1.0.0.0 Modules
| |||||||||||||||
| 7132 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 002
Read events
3 990
Write events
12
Delete events
0
Modification events
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\.NET Memory Cache 4.0\Linkage |
| Operation: | write | Name: | Export |
Value: .NET Memory Cache 4.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\MSDTC Bridge 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: MSDTC Bridge 4.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelEndpoint 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelEndpoint 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelOperation 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelOperation 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\ServiceModelService 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: ServiceModelService 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SMSvcHost 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: SMSvcHost 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SMSvcHost 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: SMSvcHost 4.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Windows Workflow Foundation 3.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: Windows Workflow Foundation 3.0.0.0 | |||
| (PID) Process: | (6328) SYS Informer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Windows Workflow Foundation 4.0.0.0\Linkage |
| Operation: | write | Name: | Export |
Value: Windows Workflow Foundation 4.0.0.0 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6328 | SYS Informer.exe | C:\Users\admin\AppData\Local\RCPsoft_-_VSmaster\SYS_Informer.exe_Url_ud2gu4bul4ych25kjypfrikxt051mq1y\1.0.4094.13135\ertn_icn.newcfg | xml | |
MD5:B77919E8211B5BF8286B40A70A230E48 | SHA256:BD893CC382AE8197595BB1D877C6A82DE66E84C64CA60D42B8FD47CE0AA498B5 | |||
| 6328 | SYS Informer.exe | C:\Users\admin\AppData\Local\RCPsoft_-_VSmaster\SYS_Informer.exe_Url_ud2gu4bul4ych25kjypfrikxt051mq1y\1.0.4094.13135\ibyesq00.newcfg | xml | |
MD5:E0ABCDE56C209F3CA8EBB2A089B3390B | SHA256:E3111B3DC553484E3A8FC8FC9BCC2C8370E478EE0107600121661C0AD5EF3BE9 | |||
| 6328 | SYS Informer.exe | C:\Users\admin\AppData\Local\RCPsoft_-_VSmaster\SYS_Informer.exe_Url_ud2gu4bul4ych25kjypfrikxt051mq1y\1.0.4094.13135\user.config | xml | |
MD5:B77919E8211B5BF8286B40A70A230E48 | SHA256:BD893CC382AE8197595BB1D877C6A82DE66E84C64CA60D42B8FD47CE0AA498B5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
45
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3828 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4372 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1824 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6180 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6180 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3580 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4656 | SearchApp.exe | 2.23.209.167:443 | www.bing.com | Akamai International B.V. | GB | unknown |
2020 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3828 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3828 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4372 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |