| download: | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe |
| Full analysis: | https://app.any.run/tasks/3ce6a5b5-e194-476d-9a7e-9c4c27c8eca5 |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2020, 14:19:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7AFBCADE075C4938D415B32A1F39AAF8 |
| SHA1: | 4375A9AAA122FD916429F412DB02998959E7181C |
| SHA256: | 2A9281186883EB2E2D6AB777CF846019FAD39AFF1D95FACDF4915FD9B686D300 |
| SSDEEP: | 196608:eFMTtaLqlUgN7AktVweDO8emQmG5eWWi/zio/i:zaD2O84wWrX/ |
MALICIOUS
Loads dropped or rewritten executable
- TenioDL.exe (PID: 404)
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- QMEmulatorService.exe (PID: 3840)
- AppMarket.exe (PID: 2524)
- TBSWebRenderer.exe (PID: 2788)
- GameDownload.exe (PID: 3756)
Application was dropped or rewritten from another process
- TenioDL.exe (PID: 404)
- QMEmulatorService.exe (PID: 3840)
- AppMarket.exe (PID: 2092)
- Tinst.exe (PID: 1688)
- AppMarket.exe (PID: 2524)
- TBSWebRenderer.exe (PID: 2788)
- GameDownload.exe (PID: 3756)
- TenioDL.exe (PID: 3504)
Adds new firewall rule via NETSH.EXE
- Tinst.exe (PID: 1688)
Actions looks like stealing of personal data
- AppMarket.exe (PID: 2524)
Changes settings of System certificates
- AppMarket.exe (PID: 2524)
- GameDownload.exe (PID: 3756)
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
SUSPICIOUS
Creates files in the user directory
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- TenioDL.exe (PID: 404)
- Tinst.exe (PID: 1688)
- AppMarket.exe (PID: 2524)
Low-level read access rights to disk partition
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- QMEmulatorService.exe (PID: 3840)
- AppMarket.exe (PID: 2524)
- GameDownload.exe (PID: 3756)
Connects to unusual port
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- TenioDL.exe (PID: 404)
- GameDownload.exe (PID: 3756)
Uses ICACLS.EXE to modify access control list
- TenioDL.exe (PID: 404)
Executable content was dropped or overwritten
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- Market.exe (PID: 2748)
- Tinst.exe (PID: 1688)
- GameDownload.exe (PID: 3756)
Reads Internet Cache Settings
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- GameDownload.exe (PID: 3756)
Executed as Windows Service
- QMEmulatorService.exe (PID: 3840)
Creates files in the program directory
- QMEmulatorService.exe (PID: 3840)
- Tinst.exe (PID: 1688)
- AppMarket.exe (PID: 2524)
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
Uses NETSH.EXE for network configuration
- Tinst.exe (PID: 1688)
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
Creates files in the Windows directory
- QMEmulatorService.exe (PID: 3840)
Modifies the open verb of a shell class
- Tinst.exe (PID: 1688)
Creates a software uninstall entry
- Tinst.exe (PID: 1688)
Adds / modifies Windows certificates
- AppMarket.exe (PID: 2524)
- GameDownload.exe (PID: 3756)
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
INFO
Reads the hosts file
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- AppMarket.exe (PID: 2524)
- GameDownload.exe (PID: 3756)
Reads settings of System Certificates
- GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe (PID: 1268)
- AppMarket.exe (PID: 2524)
- GameDownload.exe (PID: 3756)
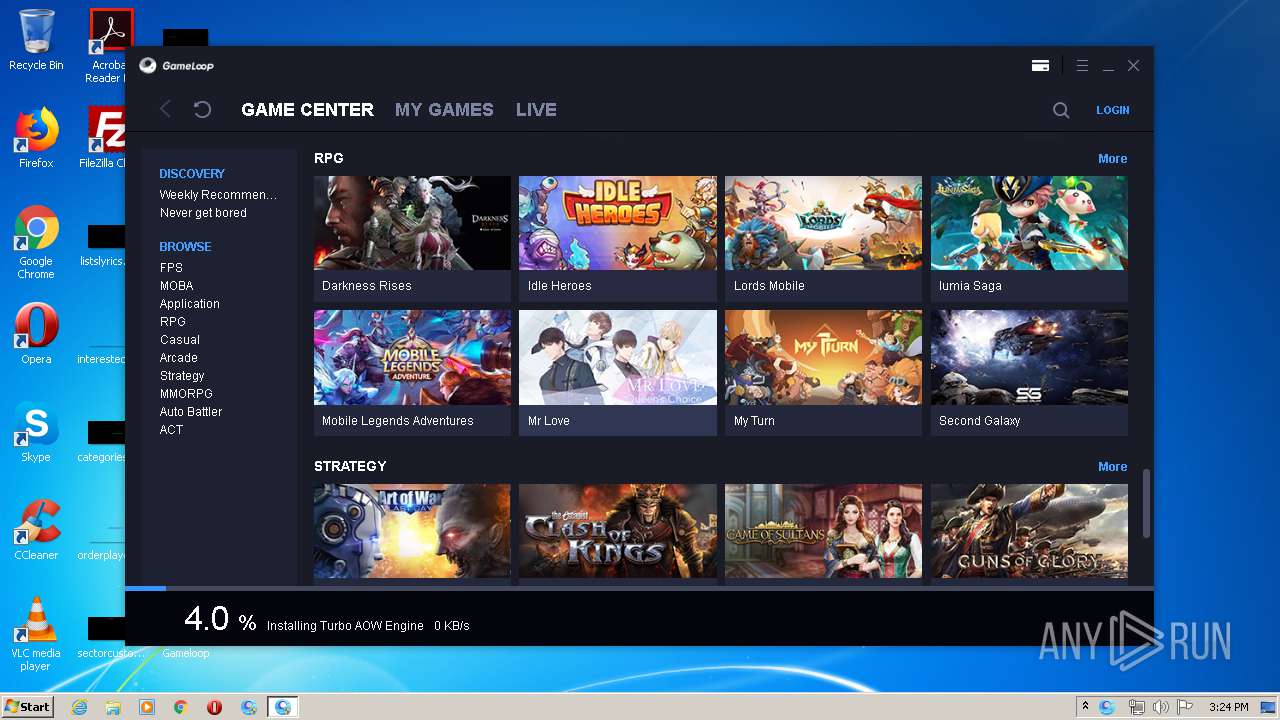
Manual execution by user
- AppMarket.exe (PID: 2092)
- AppMarket.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:28 08:55:03+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1301504 |
| InitializedDataSize: | 9174528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b534 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.8746.123 |
| ProductVersionNumber: | 1.0.8746.123 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
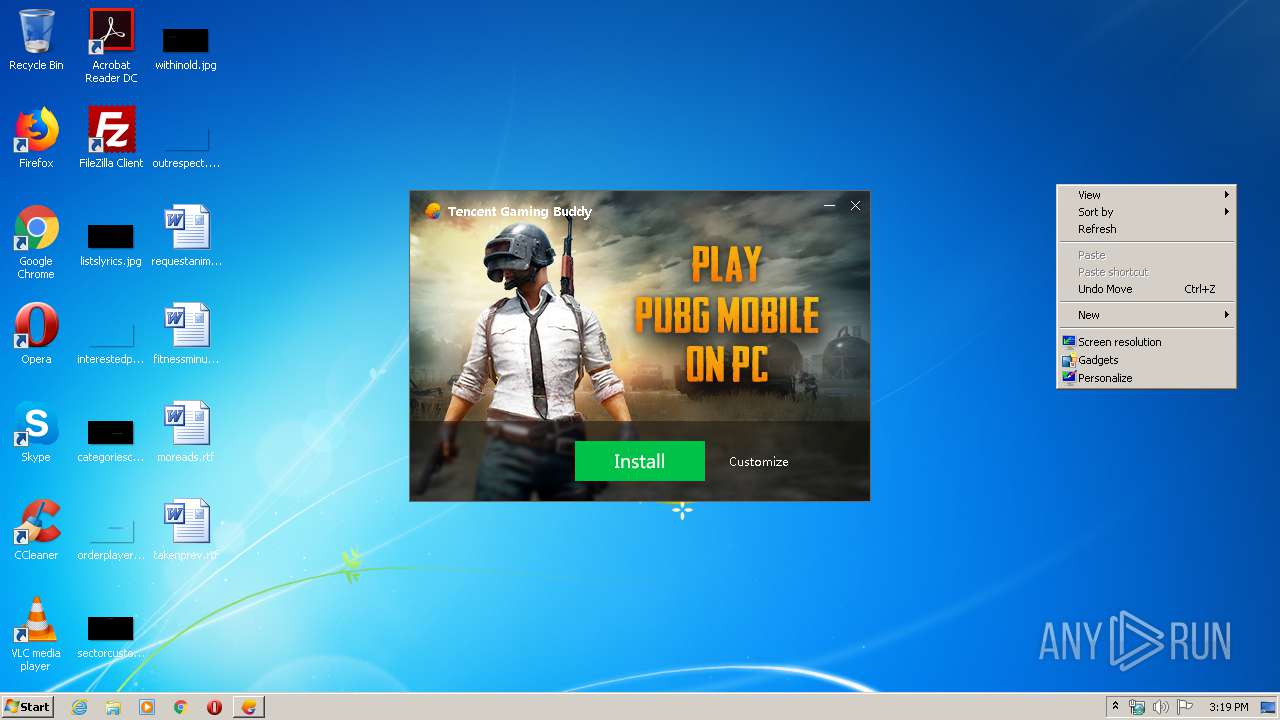
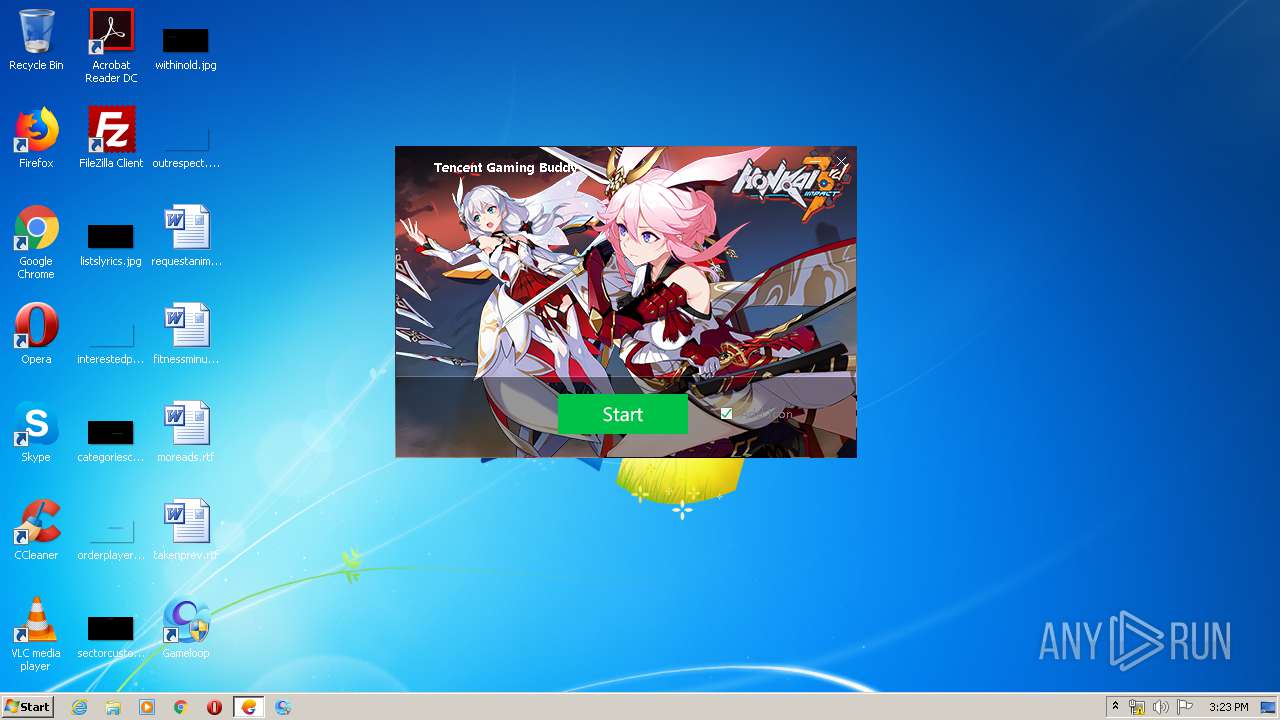
| CompanyName: | Tencent |
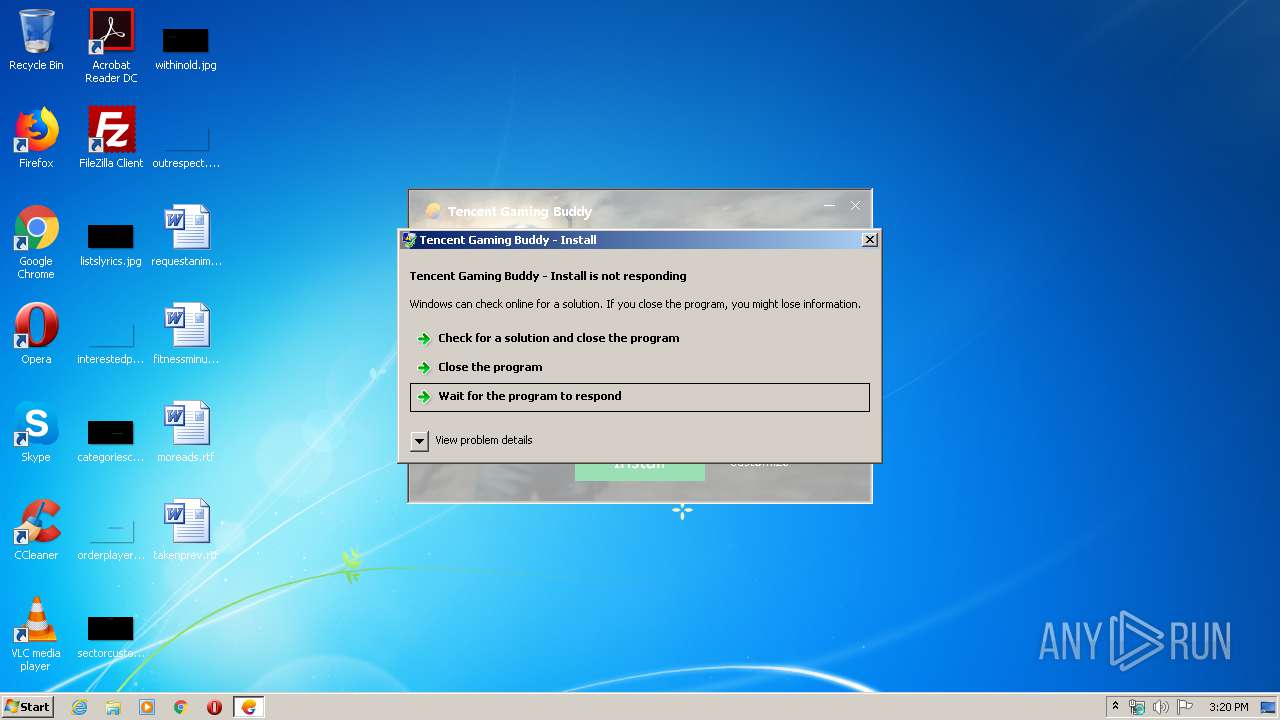
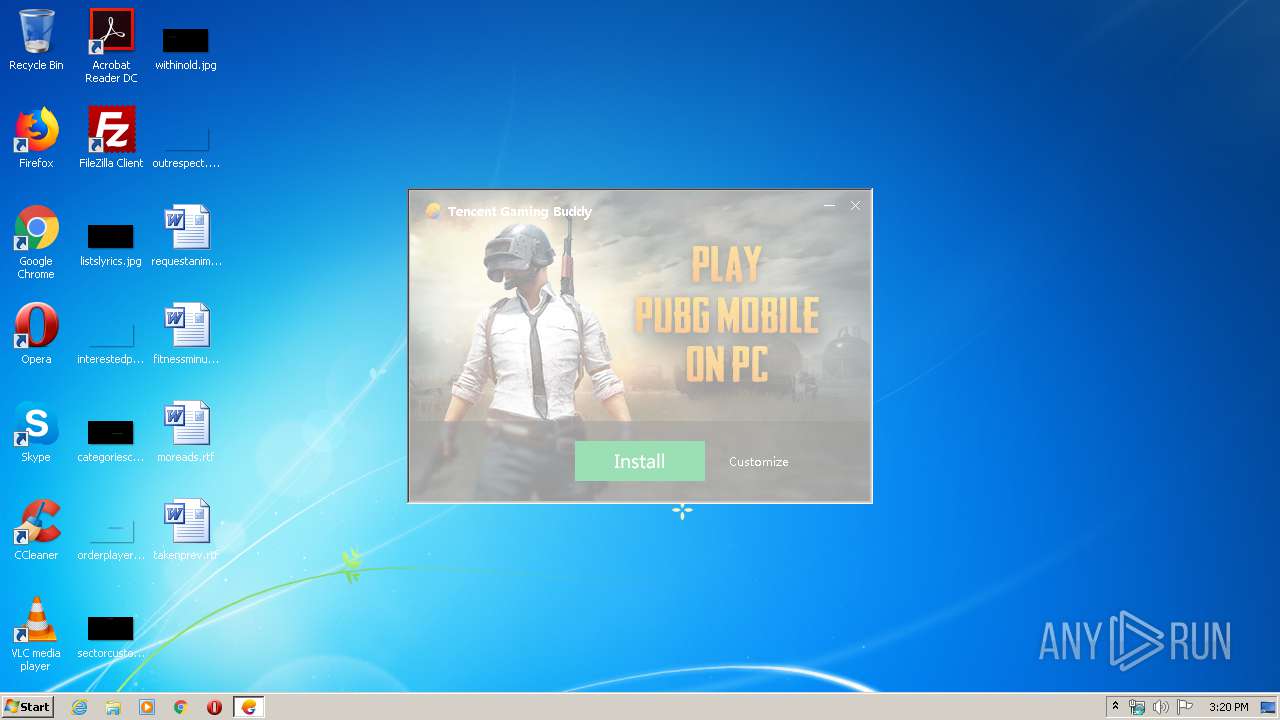
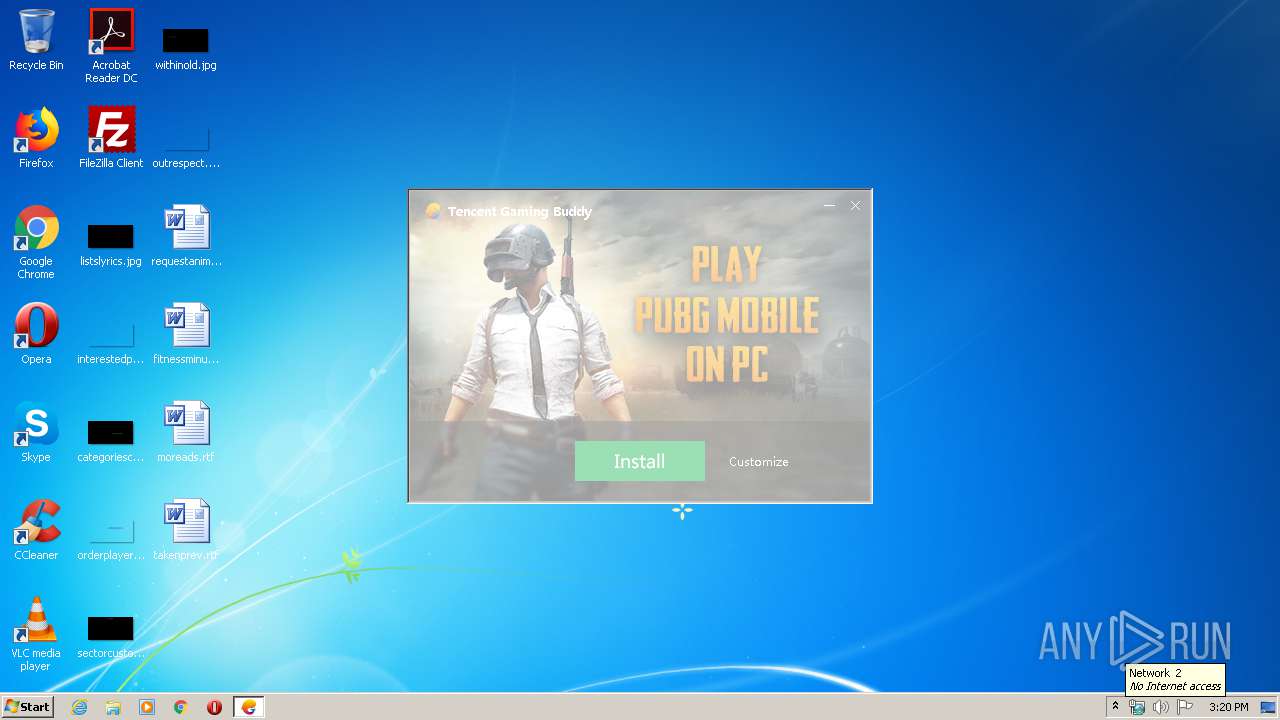
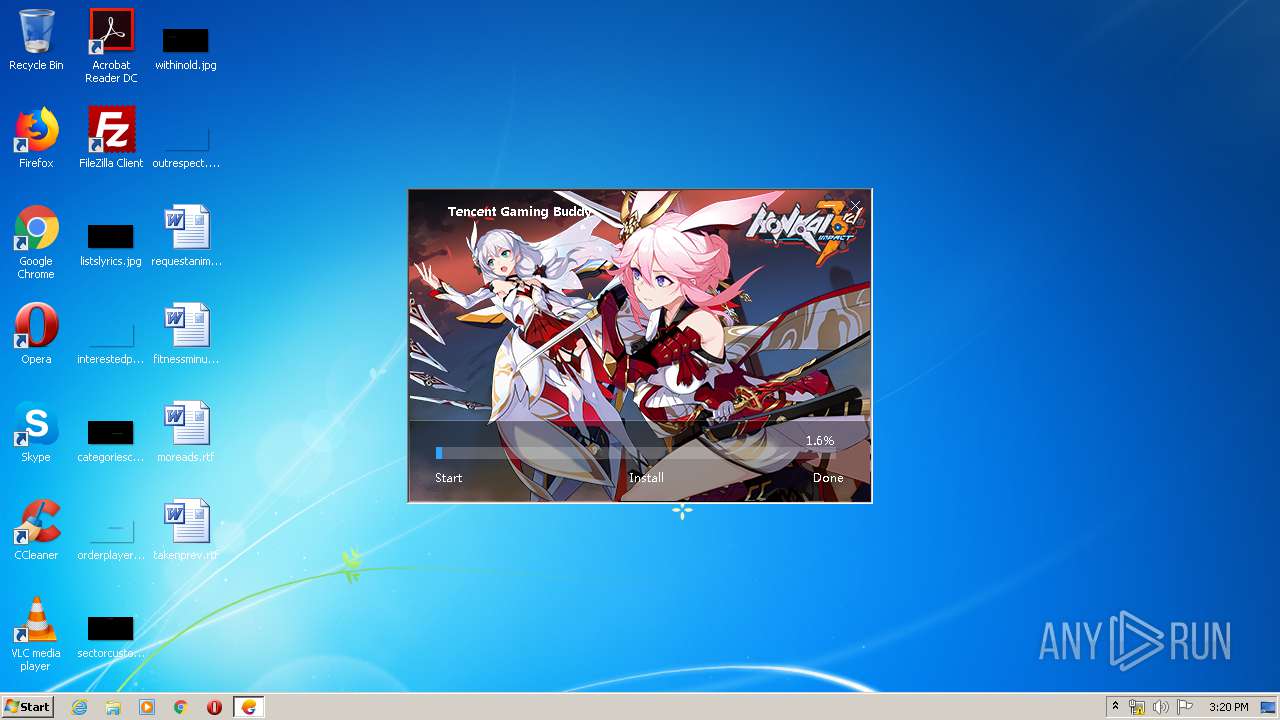
| FileDescription: | Tencent Gaming Buddy - Install |
| FileVersion: | 1.0.8746.123 |
| InternalName: | GameDownload |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFileName: | GameDownload.exe |
| ProductName: | Tencent Gaming Buddy |
| ProductVersion: | 1,0,8746,123 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Mar-2019 07:55:03 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Tencent |
| FileDescription: | Tencent Gaming Buddy - Install |
| FileVersion: | 1.0.8746.123 |
| InternalName: | GameDownload |
| LegalCopyright: | Copyright © 2017 Tencent. All Rights Reserved. |
| OriginalFilename: | GameDownload.exe |
| ProductName: | Tencent Gaming Buddy |
| ProductVersion: | 1,0,8746,123 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 28-Mar-2019 07:55:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0013DBAB | 0x0013DC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53525 |
.rdata | 0x0013F000 | 0x0005A05C | 0x0005A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02497 |
.data | 0x0019A000 | 0x000060A4 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.71512 |
.gfids | 0x001A1000 | 0x000003F4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.05647 |
.tls | 0x001A2000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.QMGuid | 0x001A3000 | 0x00000014 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001A4000 | 0x0084CF60 | 0x0084D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.26883 |
.reloc | 0x009F1000 | 0x00012090 | 0x00012200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65418 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.39184 | 67624 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.60059 | 38056 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 4.58985 | 16936 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 4.94036 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 4.94677 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.86818 | 122 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 1.18167 | 46 | UNKNOWN | Chinese - PRC | RT_STRING |
9 | 2.54353 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 0.38158 | 34 | UNKNOWN | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
curl_easy_cleanup | 1 | 0x00065B20 |
curl_easy_duphandle | 2 | 0x00065B40 |
curl_easy_escape | 3 | 0x000900D0 |
curl_easy_getinfo | 4 | 0x00065D20 |
curl_easy_init | 5 | 0x00065D40 |
curl_easy_pause | 6 | 0x00065D80 |
curl_easy_perform | 7 | 0x00065EA0 |
curl_easy_recv | 8 | 0x00065F90 |
curl_easy_reset | 9 | 0x00065FE0 |
curl_easy_send | 10 | 0x00066090 |
Total processes
73
Monitored processes
20
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Users\admin\AppData\Roaming\Tencent\TxGameAssistant\GameDownload\TenioDL.exe | C:\Users\admin\AppData\Roaming\Tencent\TxGameAssistant\GameDownload\TenioDL.exe | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯游戏云加速下载引擎(旋风Inside) Exit code: 0 Version: 2, 0, 15, 26 Modules
| |||||||||||||||
| 988 | "C:\Windows\system32\Netsh.exe" advfirewall firewall delete rule name="腾讯手游助手下载器" | C:\Windows\system32\Netsh.exe | — | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Users\admin\AppData\Local\Temp\GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe" | C:\Users\admin\AppData\Local\Temp\GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | explorer.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Tencent Gaming Buddy - Install Exit code: 0 Version: 1.0.8746.123 Modules
| |||||||||||||||
| 1688 | "C:\Temp\TxGameDownload\Component\AppMarket\Setup\Tinst.exe" | C:\Temp\TxGameDownload\Component\AppMarket\Setup\Tinst.exe | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TMarketInst Exit code: 0 Version: 3.11.325.100 Modules
| |||||||||||||||
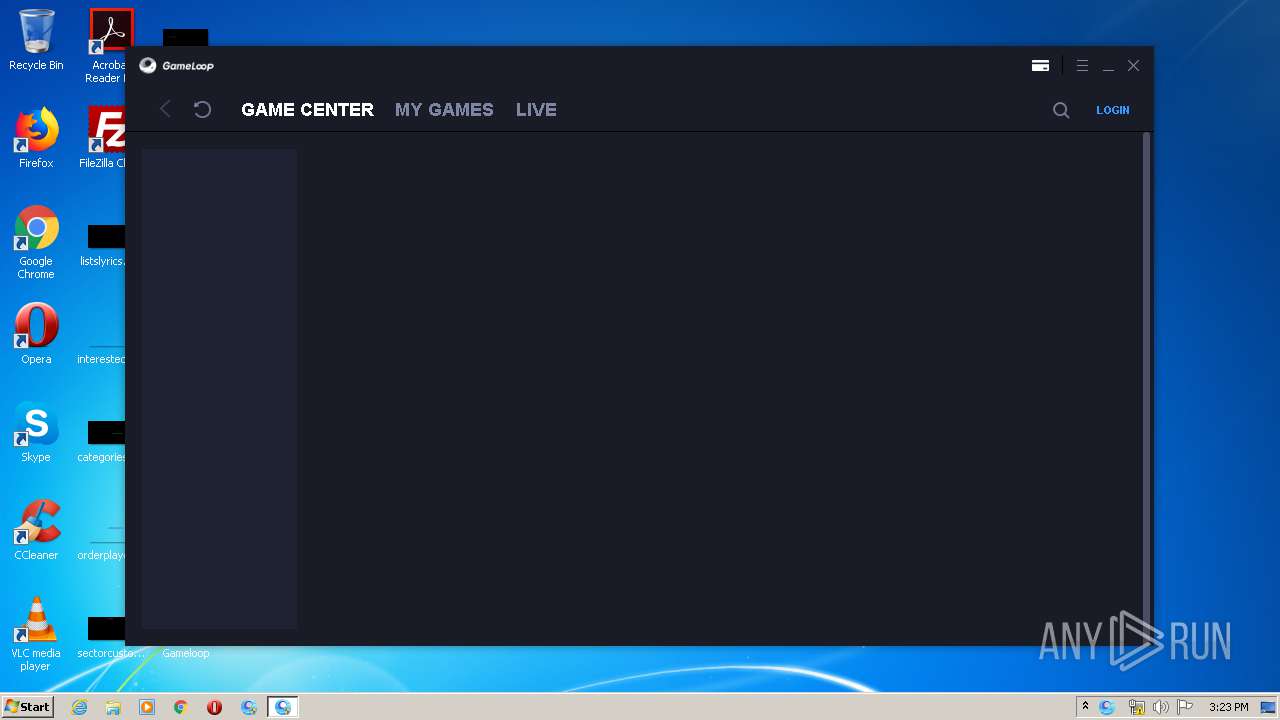
| 2092 | "C:\Program Files\txgameassistant\appmarket\AppMarket.exe" -from AppMarketDesktopLink | C:\Program Files\txgameassistant\appmarket\AppMarket.exe | — | explorer.exe | |||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: Gameloop Exit code: 3221226540 Version: 3.11.325.100 Modules
| |||||||||||||||
| 2228 | "C:\Windows\System32\icacls.exe" C:\Users\admin\AppData\Roaming\Tencent\Config\ /t /setintegritylevel low | C:\Windows\System32\icacls.exe | — | TenioDL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Windows\system32\Netsh.exe" advfirewall firewall delete rule name="腾讯手游助手下载器组件" | C:\Windows\system32\Netsh.exe | — | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="bugreport" dir=in program="c:\program files\txgameassistant\appmarket\bugreport.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2524 | "C:\Program Files\txgameassistant\appmarket\AppMarket.exe" -from AppMarketDesktopLink | C:\Program Files\txgameassistant\appmarket\AppMarket.exe | explorer.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Gameloop Exit code: 0 Version: 3.11.325.100 Modules
| |||||||||||||||
| 2748 | "C:\Temp\TxGameDownload\Component\AppMarket\Market.exe" | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 607
Read events
533
Write events
2 072
Delete events
2
Modification events
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tencent\MobileGamePC |
| Operation: | write | Name: | SupplyId |
Value: 100505 | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | sf |
Value: C:\Temp\TxGameDownload\MobileGamePCShared | |||
| (PID) Process: | (404) TenioDL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (404) TenioDL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (404) TenioDL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\metnsd\clsid |
| Operation: | write | Name: | SequenceID |
Value: 304281E2762D3740A2D4513ED26C0D69 | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | UserLanguage |
Value: en | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1268) GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
234
Suspicious files
120
Text files
1 839
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | C:\test.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | TenioDL.exe | C:\Users\admin\AppData\Local\Temp\etilqs_P0ZUg0egpmvCIRi | — | |
MD5:— | SHA256:— | |||
| 404 | TenioDL.exe | C:\Users\admin\AppData\Local\Temp\etilqs_EIV9W6OMbBNeGVB | — | |
MD5:— | SHA256:— | |||
| 404 | TenioDL.exe | C:\Users\admin\AppData\Roaming\Tencent\TenioDL\1502\cache\download.db-journal | — | |
MD5:— | SHA256:— | |||
| 404 | TenioDL.exe | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe.ttd | — | |
MD5:— | SHA256:— | |||
| 1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | C:\Users\admin\AppData\Local\Temp\Cab704.tmp | — | |
MD5:— | SHA256:— | |||
| 1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | C:\Users\admin\AppData\Local\Temp\Tar715.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | TenioDL.exe | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe | — | |
MD5:— | SHA256:— | |||
| 1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | binary | |
MD5:3320387453E9A7BE985C3C12E61E0330 | SHA256:8DC8FAEBB6C00FAE815977FB6F264420CE6F99CE36B57A4F4BB0D28CC6558944 | |||
| 1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | der | |
MD5:2B03E9023854D8BDAA8C0831C73C2D6F | SHA256:179FC22C1381D944B9158DA1E9907A40C59DC938955EF372E2AC55522E7905FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
128
DNS requests
41
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
404 | TenioDL.exe | GET | — | 2.16.186.10:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
404 | TenioDL.exe | GET | — | 2.16.186.10:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
404 | TenioDL.exe | GET | — | 2.16.186.40:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
404 | TenioDL.exe | GET | — | 2.16.186.10:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | GET | 200 | 203.205.253.183:80 | http://syzs.qq.com/downloads/xml/compoment.xml | CN | xml | 20.1 Kb | suspicious |
404 | TenioDL.exe | GET | — | 2.16.186.10:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
404 | TenioDL.exe | GET | — | 2.16.186.40:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
404 | TenioDL.exe | GET | — | 2.16.186.10:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | — | — | whitelisted |
404 | TenioDL.exe | GET | 206 | 2.16.186.40:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.325.100.dat | unknown | binary | 1.00 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | 111.161.108.243:8000 | p2pupgrade.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | 58.251.106.185:443 | master.etl.desktop.qq.com | China Unicom Guangdong IP network | CN | malicious |
404 | TenioDL.exe | 163.177.93.178:8000 | stun.qqlive.qq.com | China Unicom Shenzen network | CN | unknown |
404 | TenioDL.exe | 220.194.108.75:8000 | ps2.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
404 | TenioDL.exe | 220.194.106.243:14309 | config.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
404 | TenioDL.exe | 111.161.108.243:8000 | p2pupgrade.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | 203.205.253.140:80 | syzs.qq.com | — | CN | suspicious |
— | — | 183.61.39.228:8000 | — | China Telecom (Group) | CN | unknown |
404 | TenioDL.exe | 101.89.238.216:8443 | ga.gamedl.qq.com | China Telecom (Group) | CN | unknown |
404 | TenioDL.exe | 220.194.108.43:443 | downloadtpt.gamedl.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
p2pupgrade.gamedl.qq.com |
| unknown |
masterconn.qq.com |
| whitelisted |
master.etl.desktop.qq.com |
| whitelisted |
masterconn2.qq.com |
| unknown |
stat.gamedl.qq.com |
| unknown |
config.gamedl.qq.com |
| whitelisted |
stun.qqlive.qq.com |
| suspicious |
ps2.gamedl.qq.com |
| unknown |
p2pupdate.gamedl.qq.com |
| unknown |
syzs.qq.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
404 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
404 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
404 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
404 | TenioDL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
404 | TenioDL.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
1268 | GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2524 | AppMarket.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
2524 | AppMarket.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
2524 | AppMarket.exe | Potential Corporate Privacy Violation | ET POLICY QQ Browser WUP Request - qbpcstatf.stat |
2524 | AppMarket.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | [Downloader] DriverType C: = 3
|
GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | [Downloader] DriverType C: = 3
|
GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | [Downloader] DriverType C: = 3
|
GameDownload_gamedownload_i18n_hw-by6_100505_1.0.8746.123.exe | [Downloader] GetLogicalDrives 4
|
AppMarket.exe | [0402/152348:INFO:exception_record.cc(518)] [QB]Process ID: 2524 Type: 1
|
TBSWebRenderer.exe | [0402/152349:INFO:exception_record.cc(518)] [QB]Process ID: 2788 Type: 2
|
GameDownload.exe | [Downloader] GetLogicalDrives 4
|
GameDownload.exe | [Downloader] DriverType C: = 3
|
GameDownload.exe | [Downloader] GetLogicalDrives 4
|
GameDownload.exe | [Downloader] DriverType C: = 3
|