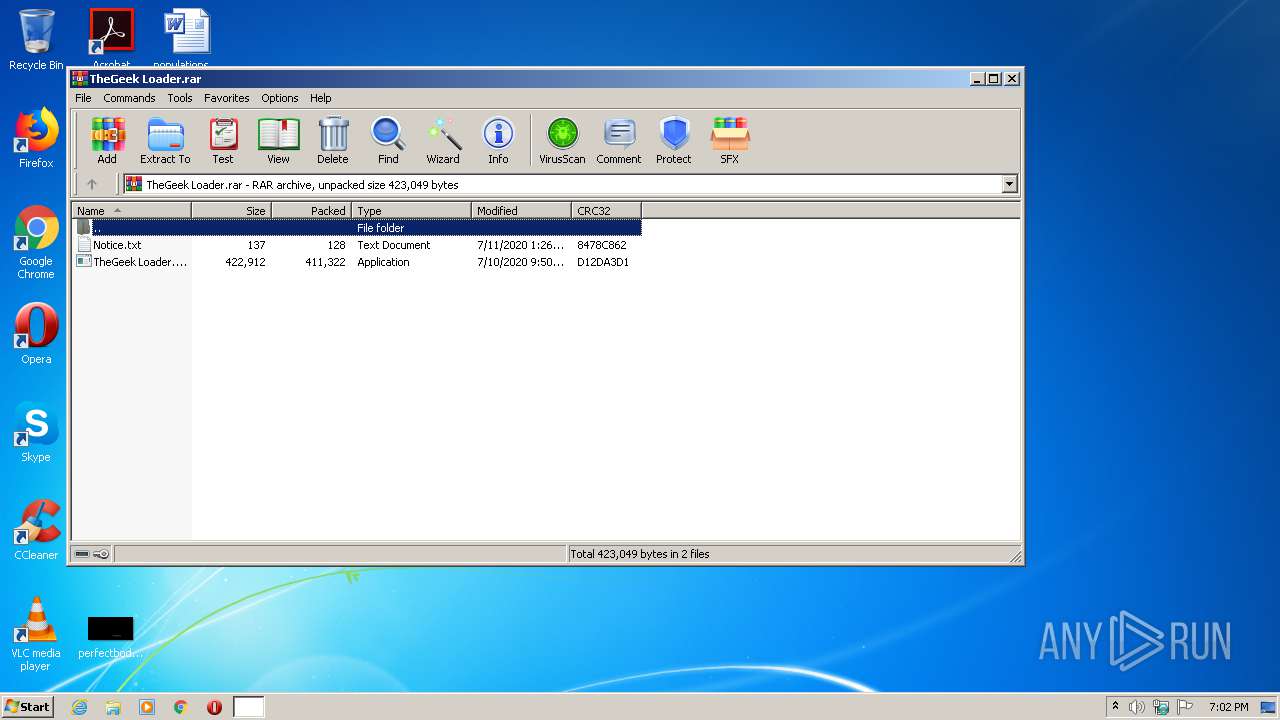
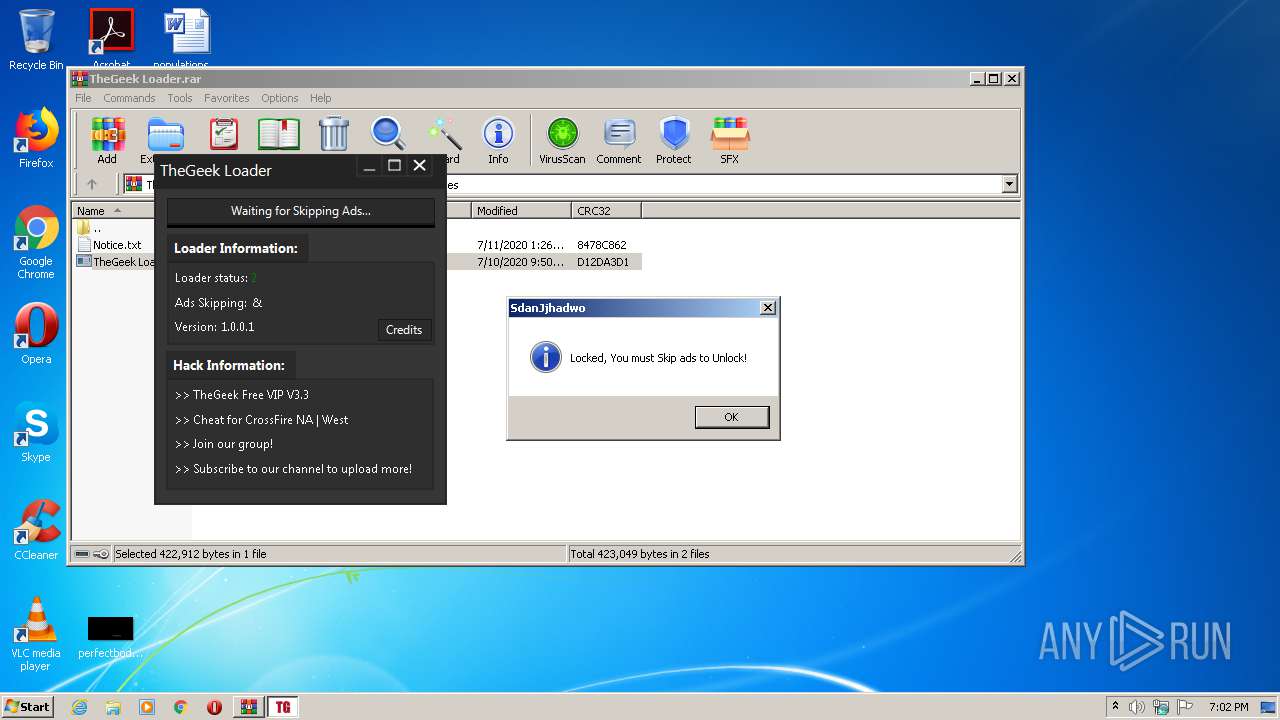
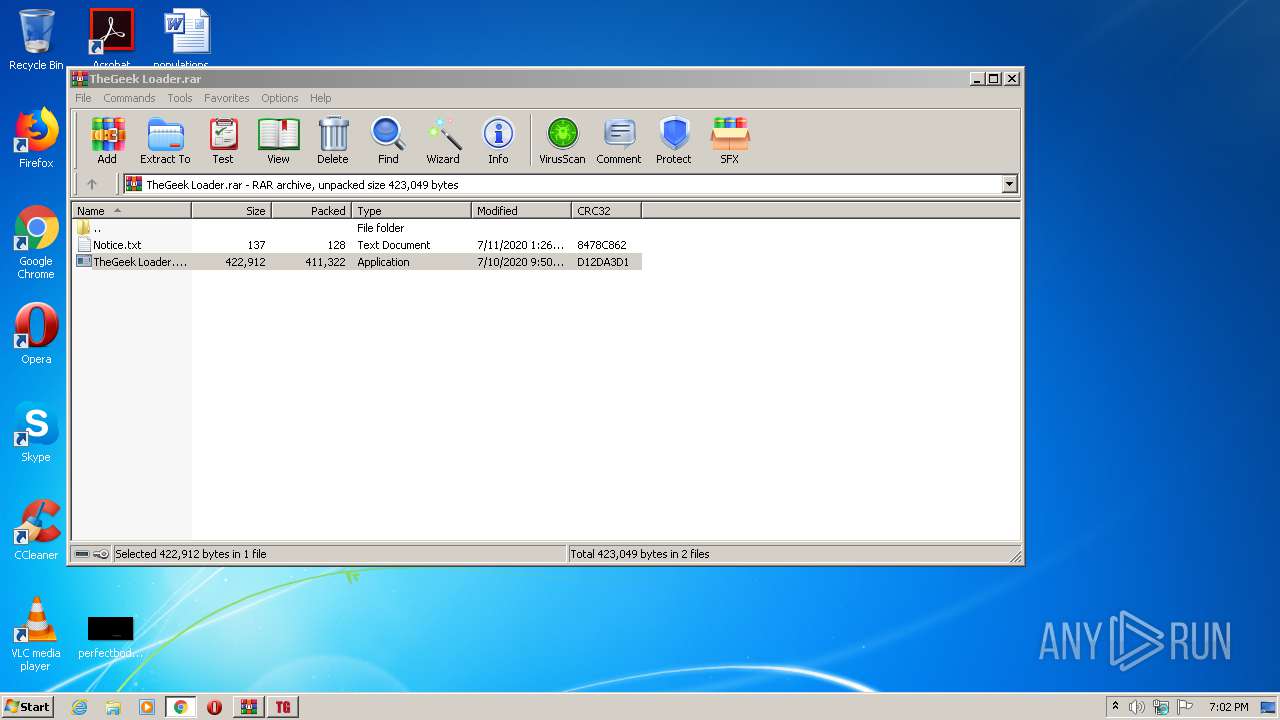
| File name: | TheGeek Loader.rar |
| Full analysis: | https://app.any.run/tasks/e3714035-c6ab-4534-9452-f1ffd7eddaca |
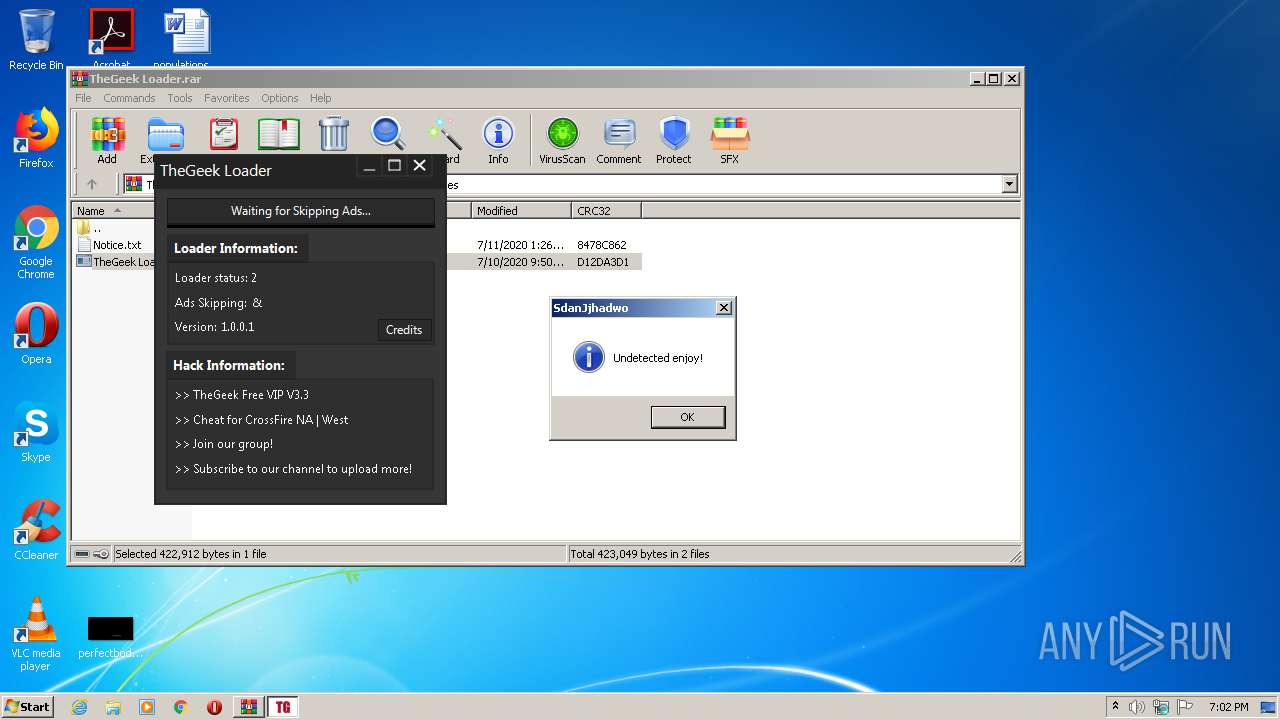
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:01:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8918A3B959CF08F7B363AF5AF3F8E962 |
| SHA1: | 4618336F448F76A4EFF07C4E12BCA3E23BE6342D |
| SHA256: | 2A72F187C79E411D730C2FEE513D2C1942E2E9A7A582164B3E8738D3F7481E15 |
| SSDEEP: | 12288:m5trCjAwpRr5S+BPQ5JRih02gIEn0v+8I6b/e:SrCdp7qr8uIgq/e |
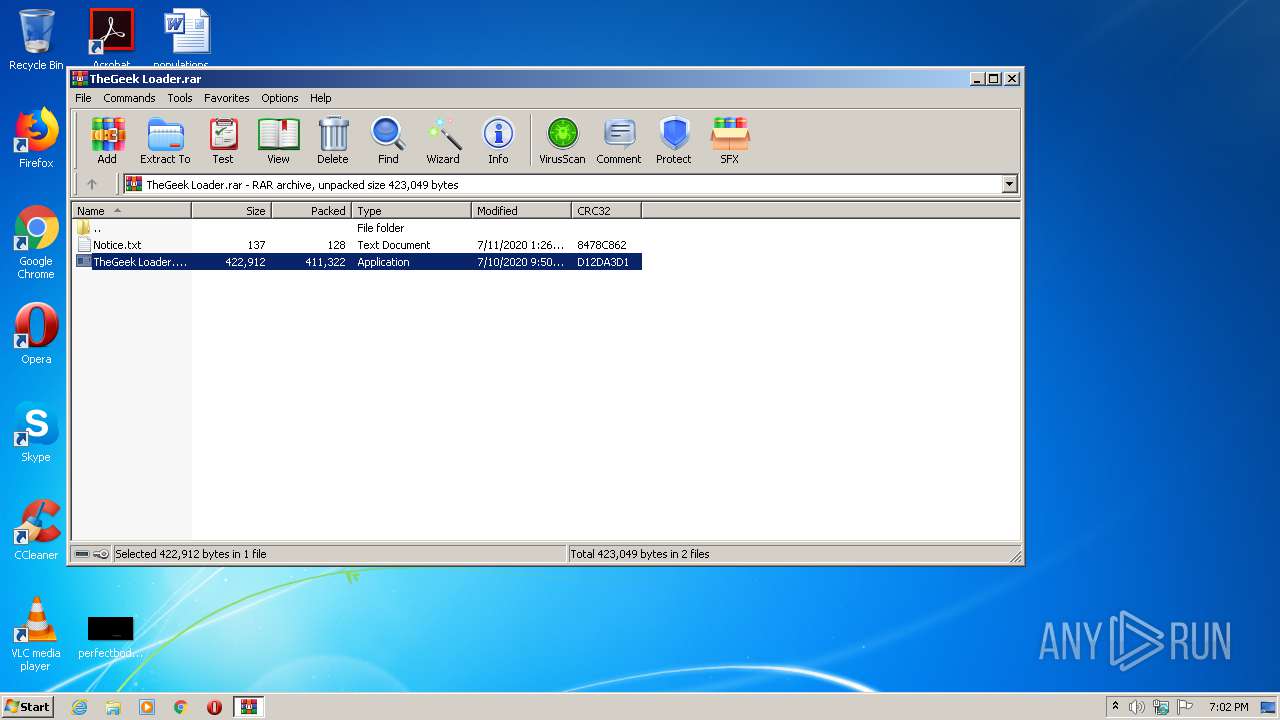
MALICIOUS
Application was dropped or rewritten from another process
- TheGeek Loader.exe (PID: 3024)
- TheGeek Loader.exe (PID: 3500)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3220)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3236)
INFO
Reads the hosts file
- chrome.exe (PID: 3220)
- chrome.exe (PID: 1360)
Modifies the open verb of a shell class
- chrome.exe (PID: 3220)
Application launched itself
- chrome.exe (PID: 3220)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3220)
Reads settings of System Certificates
- chrome.exe (PID: 1360)
Adds / modifies Windows certificates
- chrome.exe (PID: 1360)
Changes settings of System certificates
- chrome.exe (PID: 1360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
81
Monitored processes
41
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17192792162443604380 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16365373415373937906 --mojo-platform-channel-handle=5168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15781783031326093979 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8914093469898498227 --mojo-platform-channel-handle=2916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13431401466795807832 --mojo-platform-channel-handle=5132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4267631179565180497 --mojo-platform-channel-handle=1652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4545976663857000309 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6047415991507339242 --mojo-platform-channel-handle=5176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15571749925161689397 --mojo-platform-channel-handle=3272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4058870911151446087,9497555936381666836,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4500188678709446285 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 899
Read events
1 617
Write events
2 272
Delete events
10
Modification events
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\TheGeek Loader.rar | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3236) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
1
Suspicious files
275
Text files
315
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B5037-C94.pma | — | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c913d90a-e917-4f67-9577-a7294a7a6659.tmp | — | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3236.26849\TheGeek Loader.exe | executable | |
MD5:— | SHA256:— | |||
| 3236 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3236.26849\Notice.txt | text | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2817ac.TMP | text | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2817da.TMP | text | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF281809.TMP | text | |
MD5:— | SHA256:— | |||
| 3220 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
150
DNS requests
83
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1360 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
1360 | chrome.exe | GET | 200 | 173.194.163.105:80 | http://r3---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=196.244.192.14&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1594576557&mv=u&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
1360 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
1360 | chrome.exe | GET | 200 | 74.125.110.170:80 | http://r5---sn-5go7yner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=196.244.192.14&mm=28&mn=sn-5go7yner&ms=nvh&mt=1594576557&mv=u&mvi=5&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
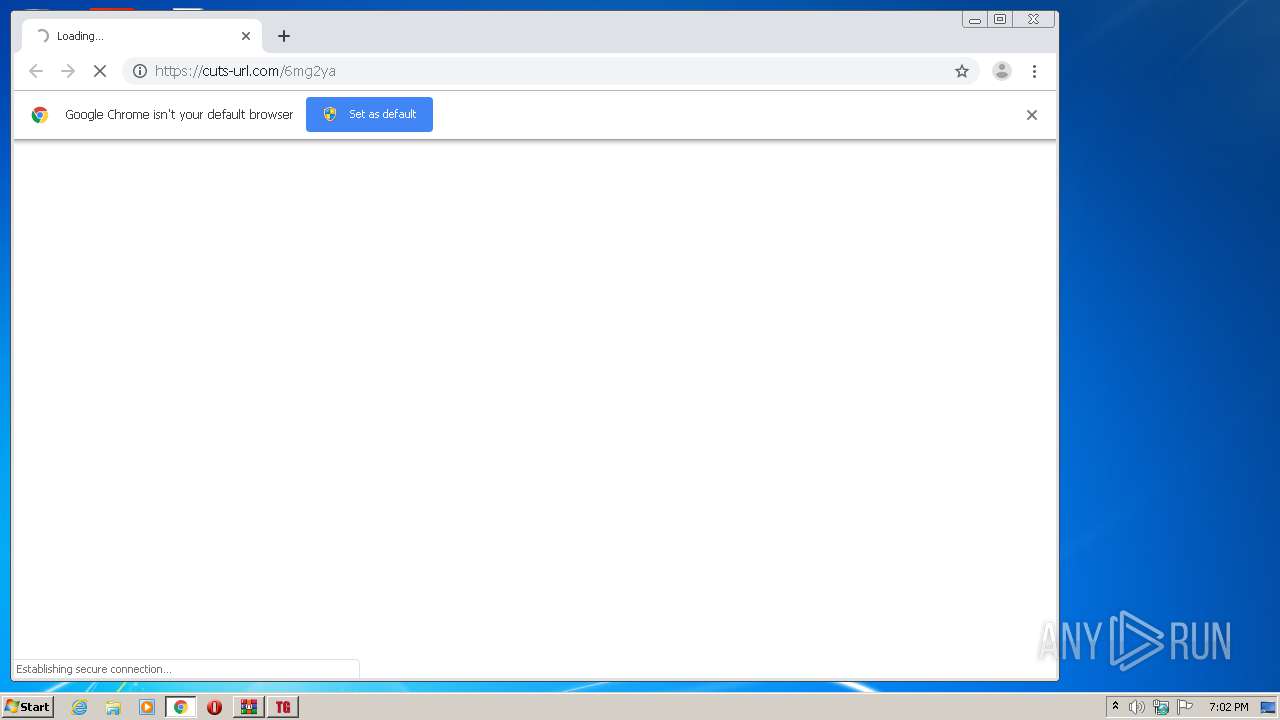
3500 | TheGeek Loader.exe | GET | 200 | 204.12.192.242:80 | http://tgramo.guncheats.com/sandbox/status.txt | US | binary | 1 b | suspicious |
3500 | TheGeek Loader.exe | GET | 200 | 204.12.192.242:80 | http://tgramo.guncheats.com/version.txt | US | text | 7 b | suspicious |
1360 | chrome.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.rapidssl.com/RapidSSLRSACA2018.crt | US | der | 1.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3500 | TheGeek Loader.exe | 204.12.192.242:80 | tgramo.guncheats.com | WholeSale Internet, Inc. | US | suspicious |
1360 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
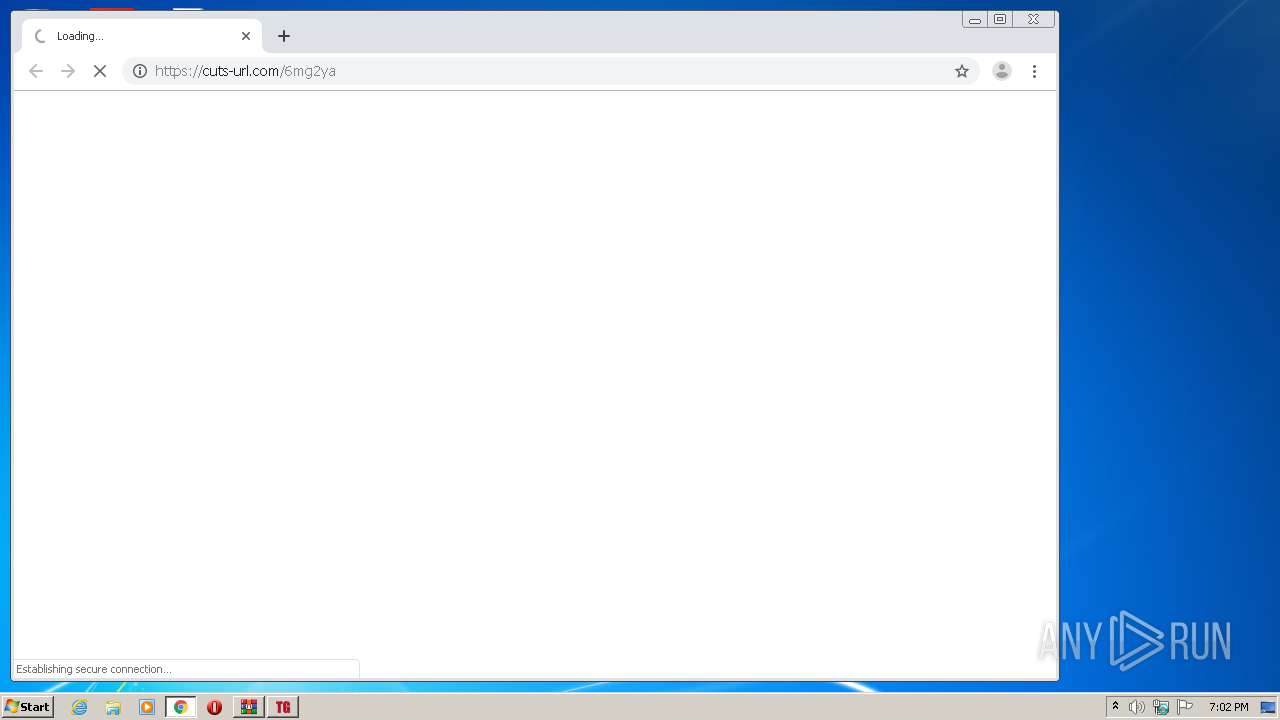
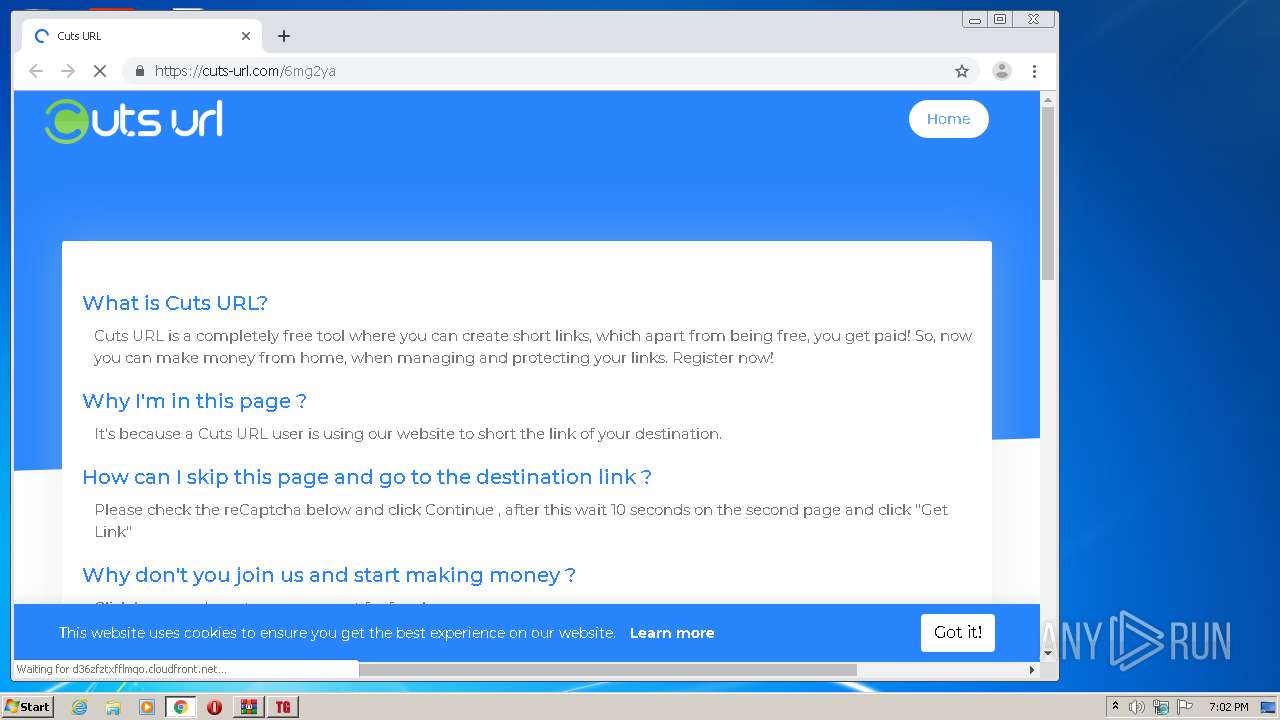
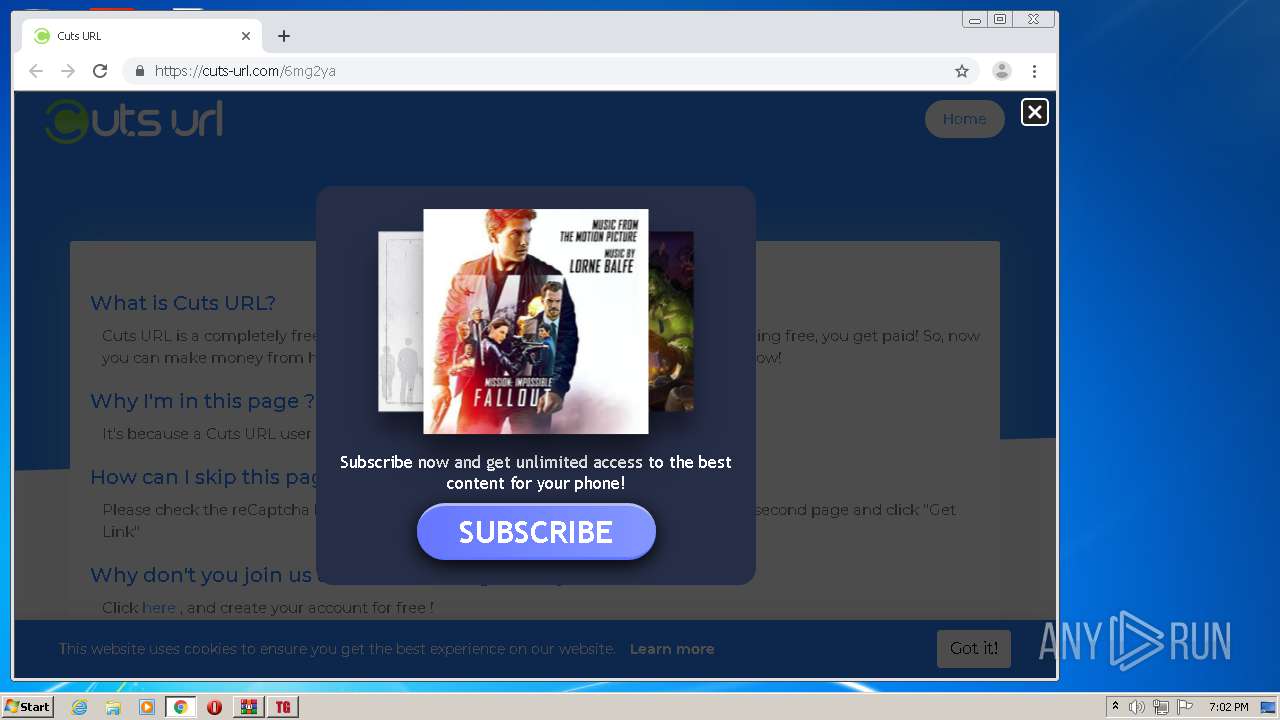
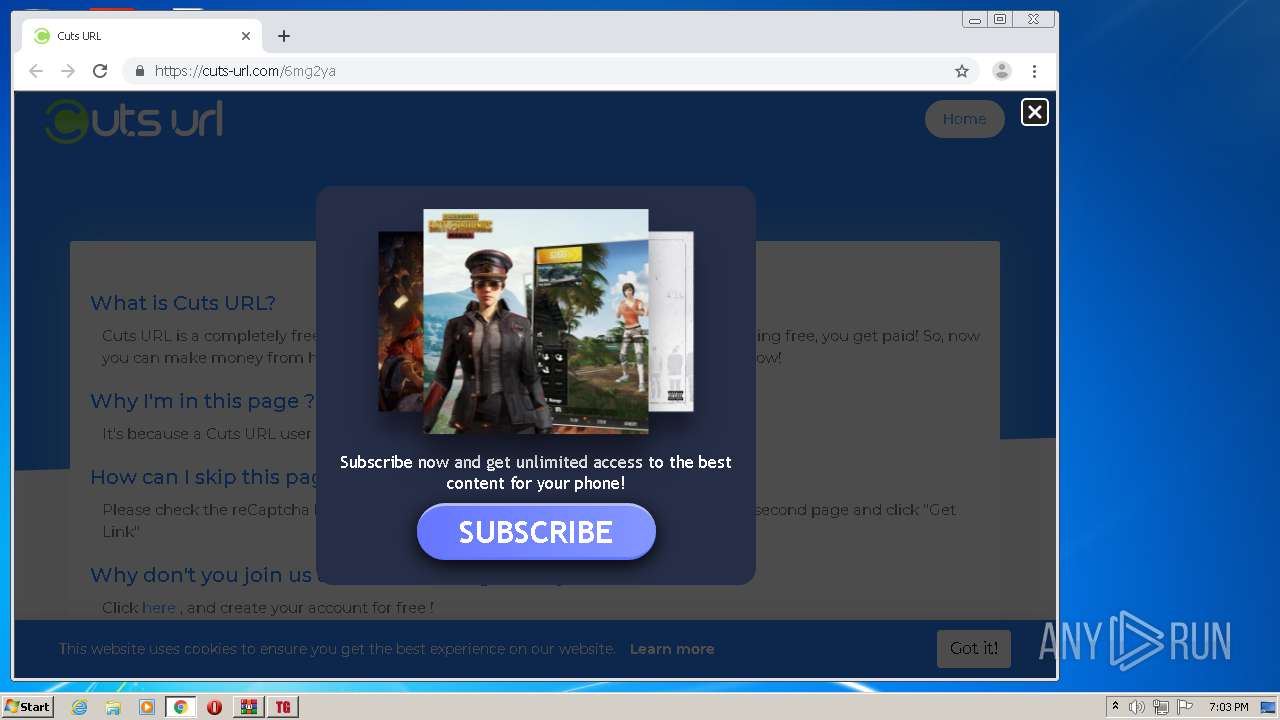
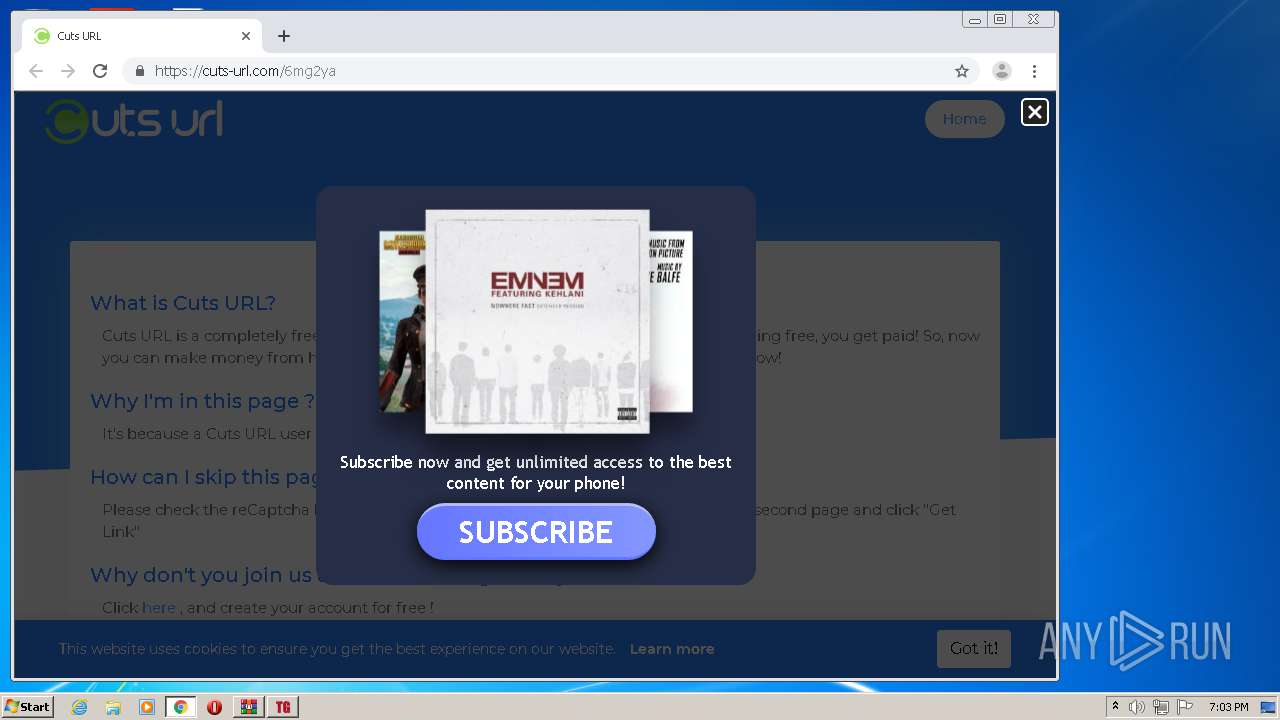
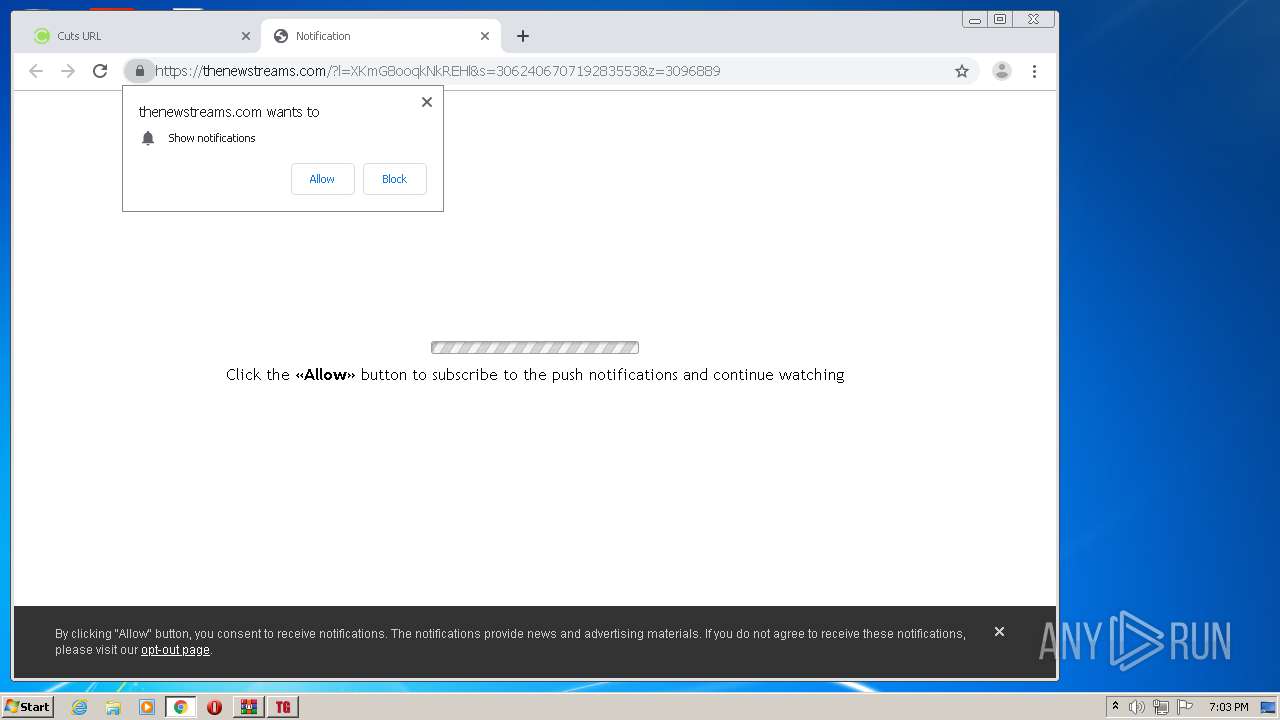
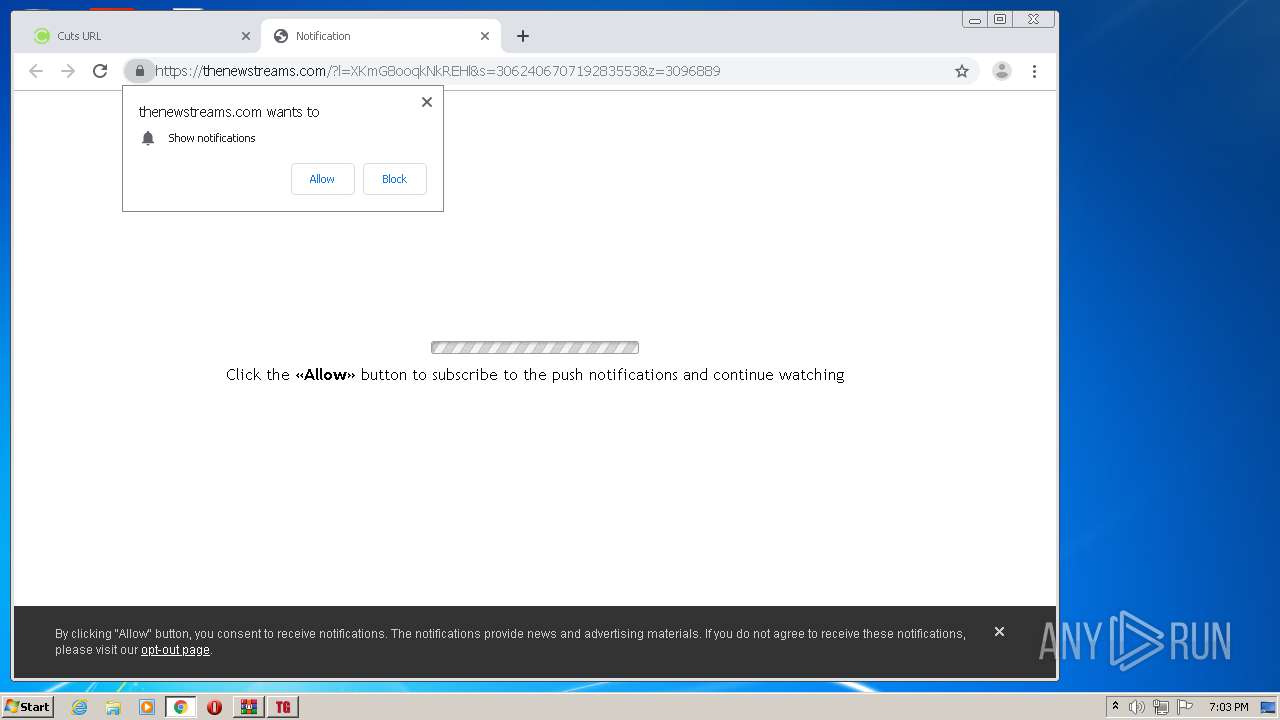
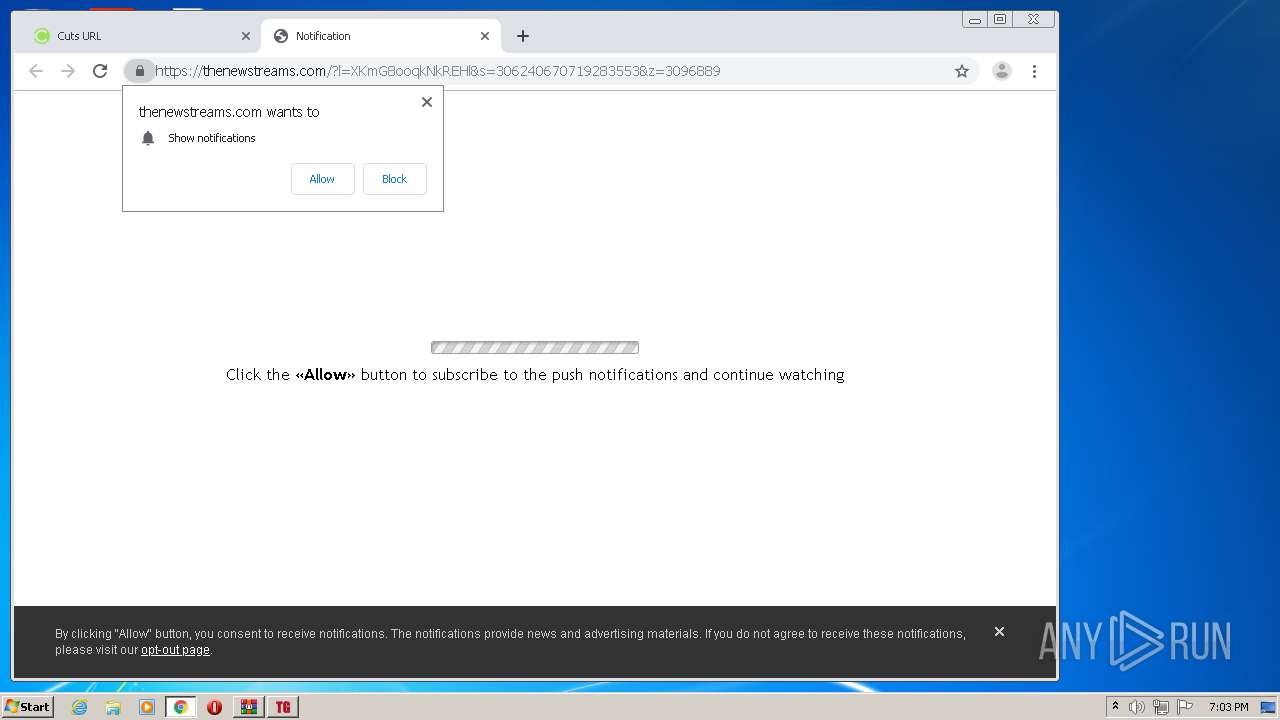
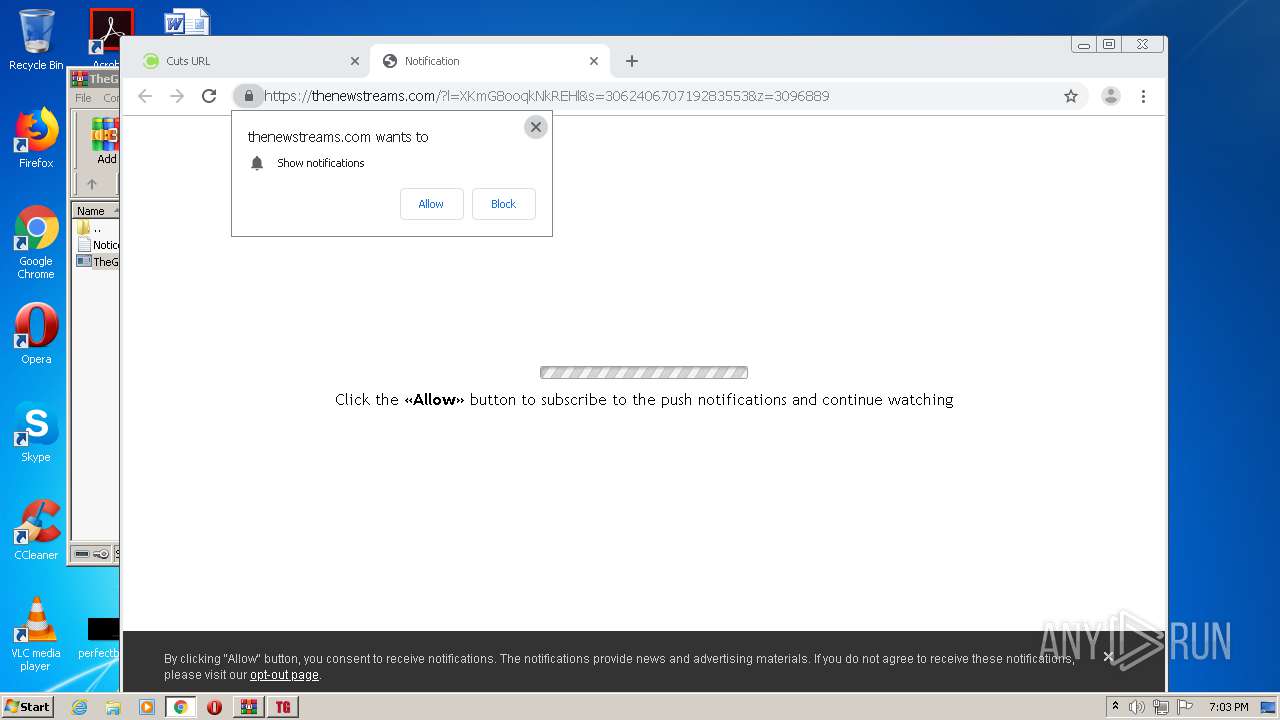
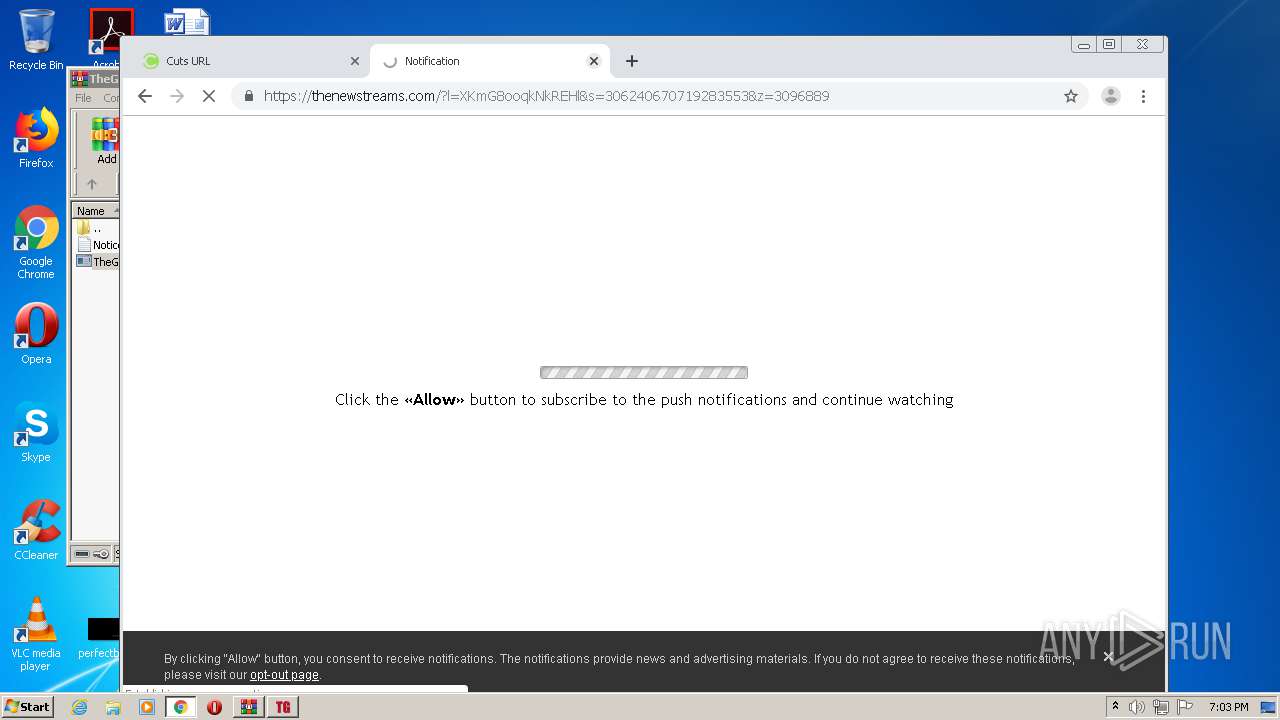
1360 | chrome.exe | 35.208.223.29:443 | cuts-url.com | — | US | unknown |
1360 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1360 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
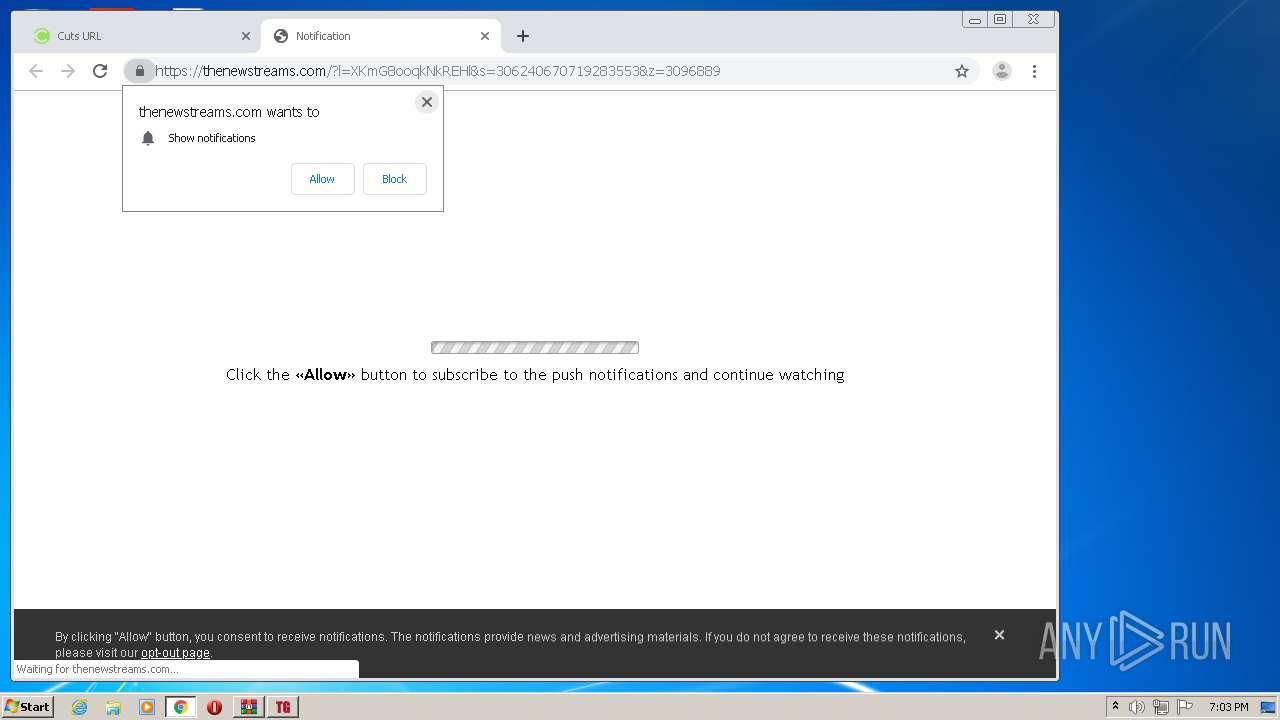
1360 | chrome.exe | 139.45.196.132:443 | propu.sh | — | US | suspicious |
1360 | chrome.exe | 139.45.196.96:443 | native.propellerclick.com | — | US | unknown |
1360 | chrome.exe | 172.217.21.193:443 | lh6.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tgramo.guncheats.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
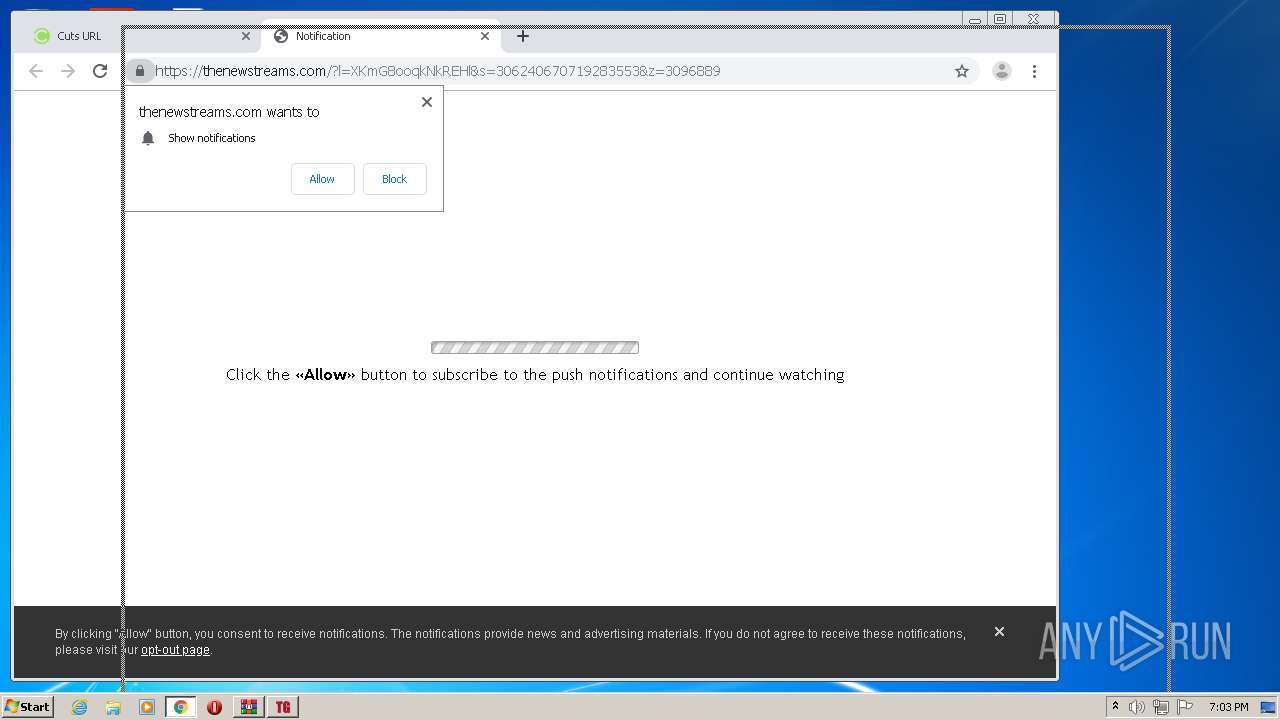
cuts-url.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.linearicons.com |
| shared |
www.googletagmanager.com |
| whitelisted |
onemboaran.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report