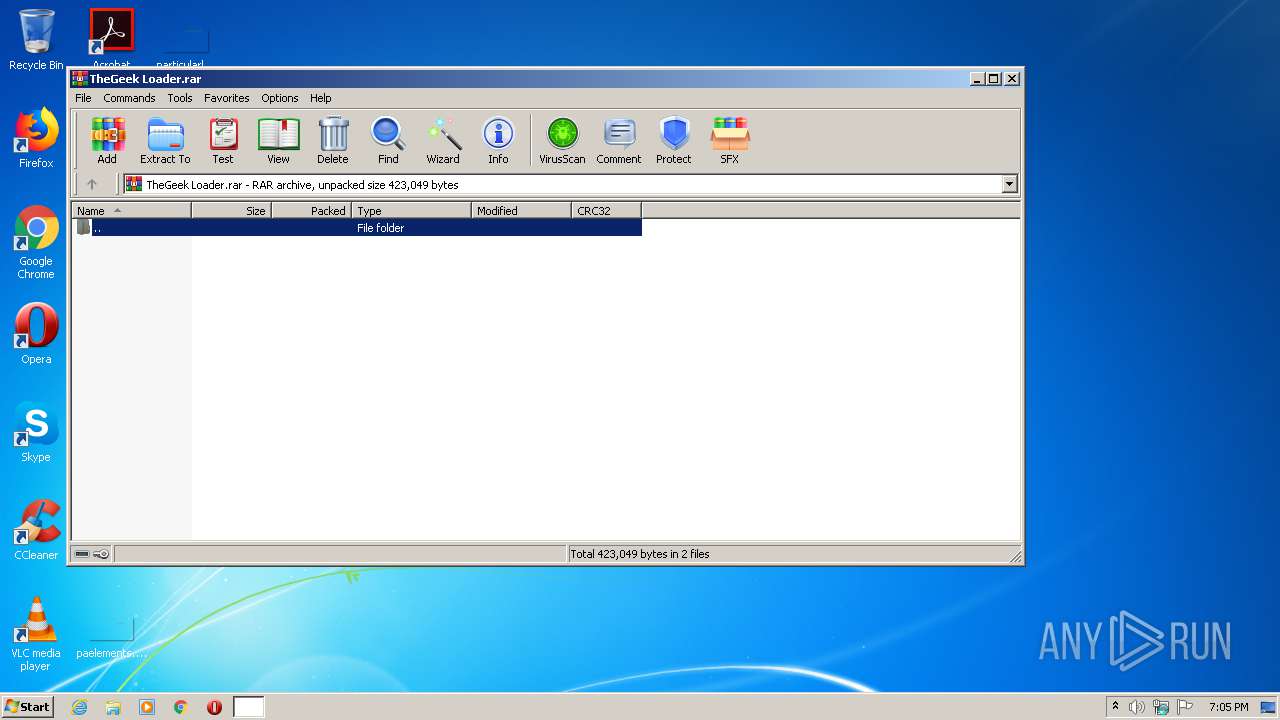
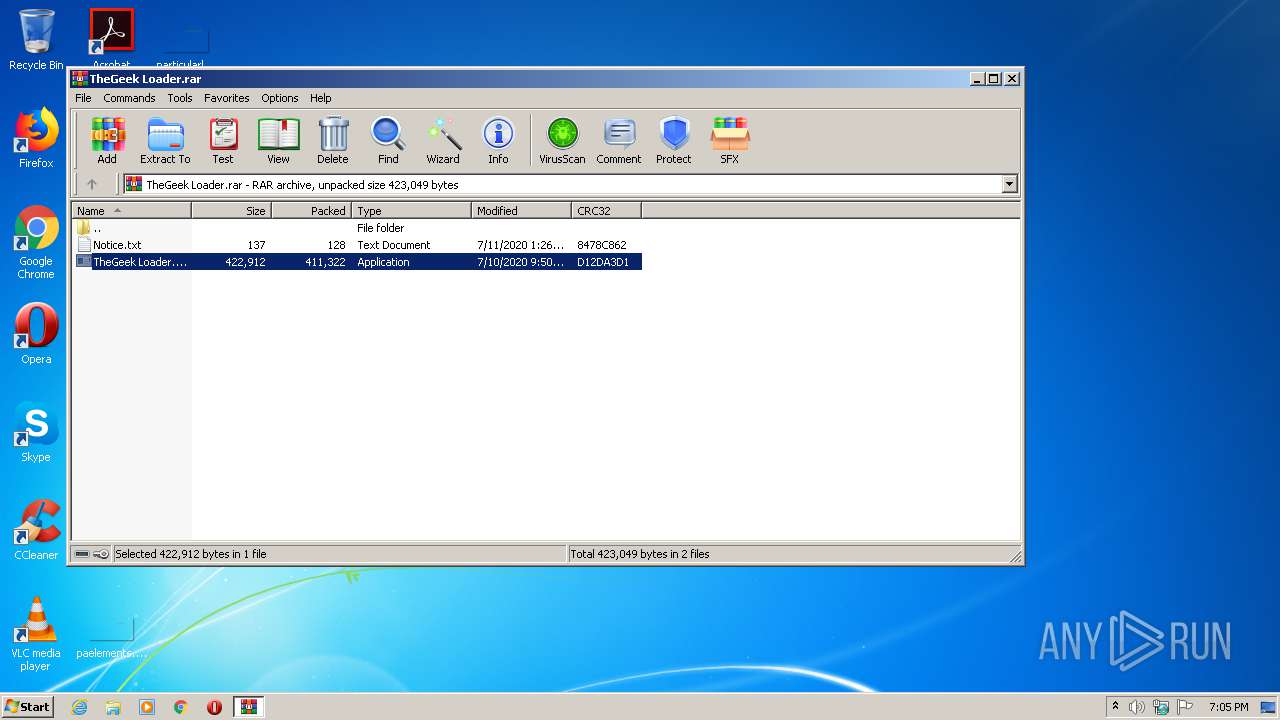
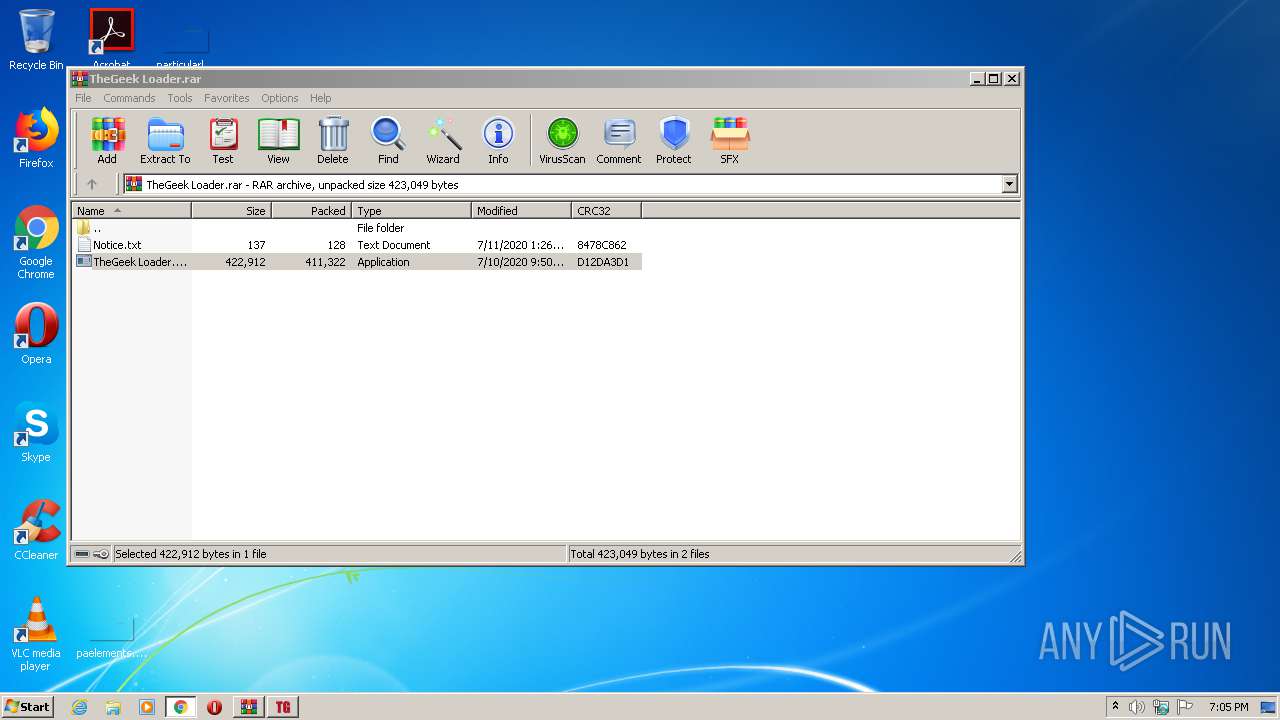
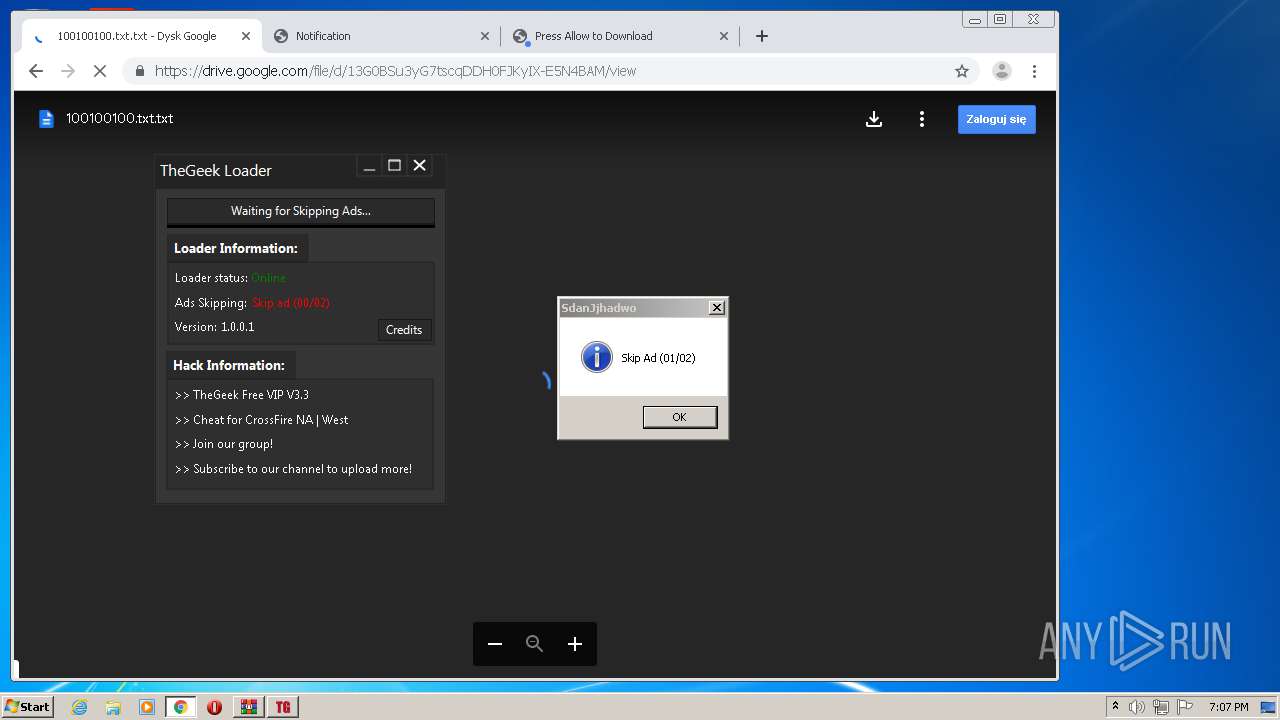
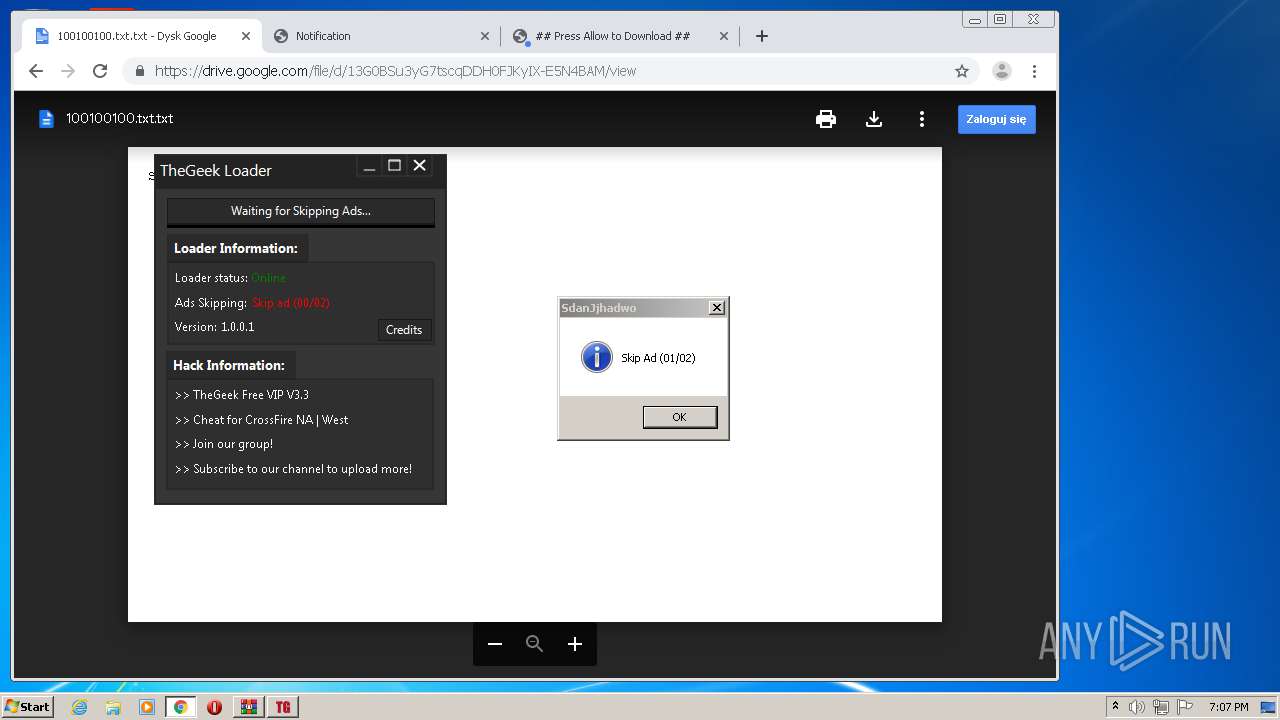
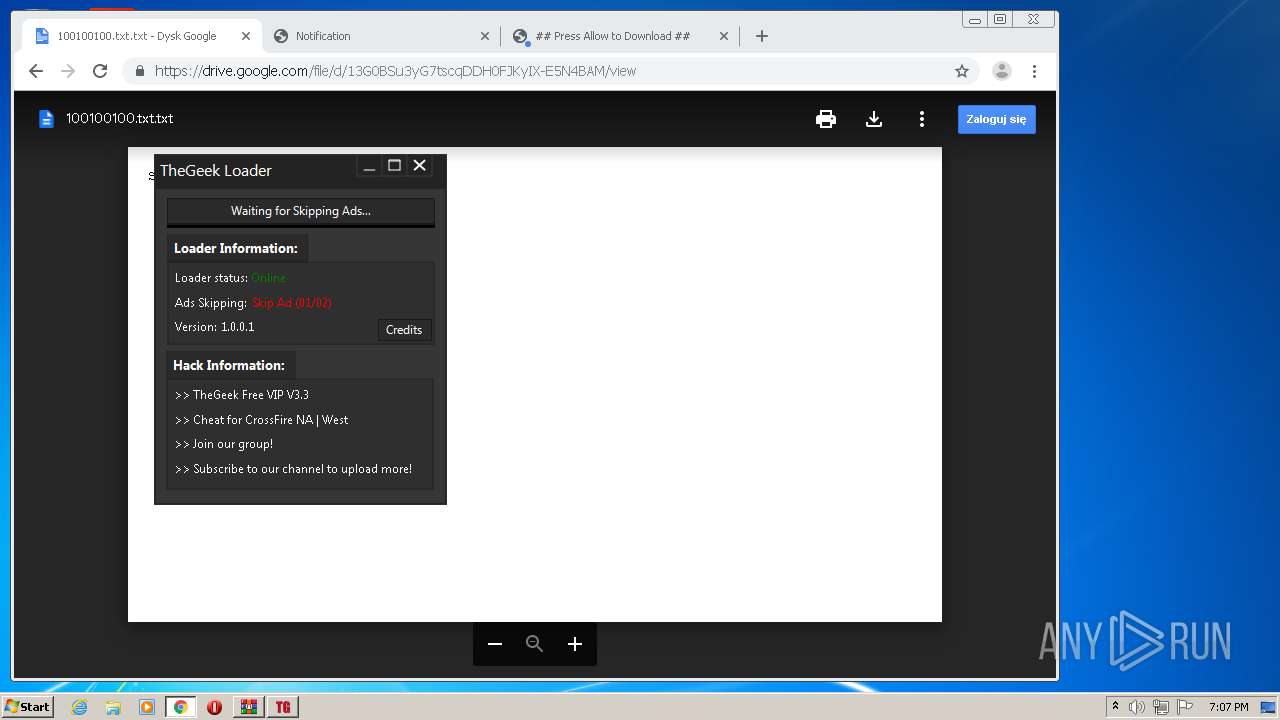
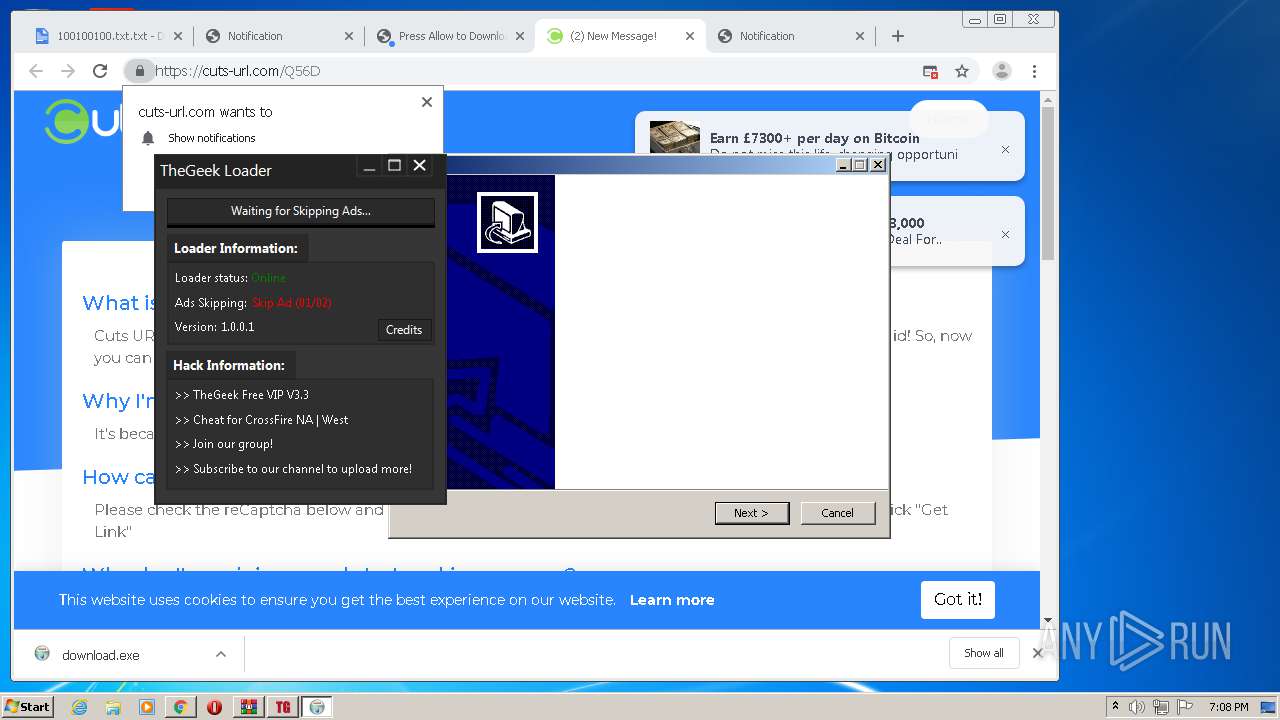
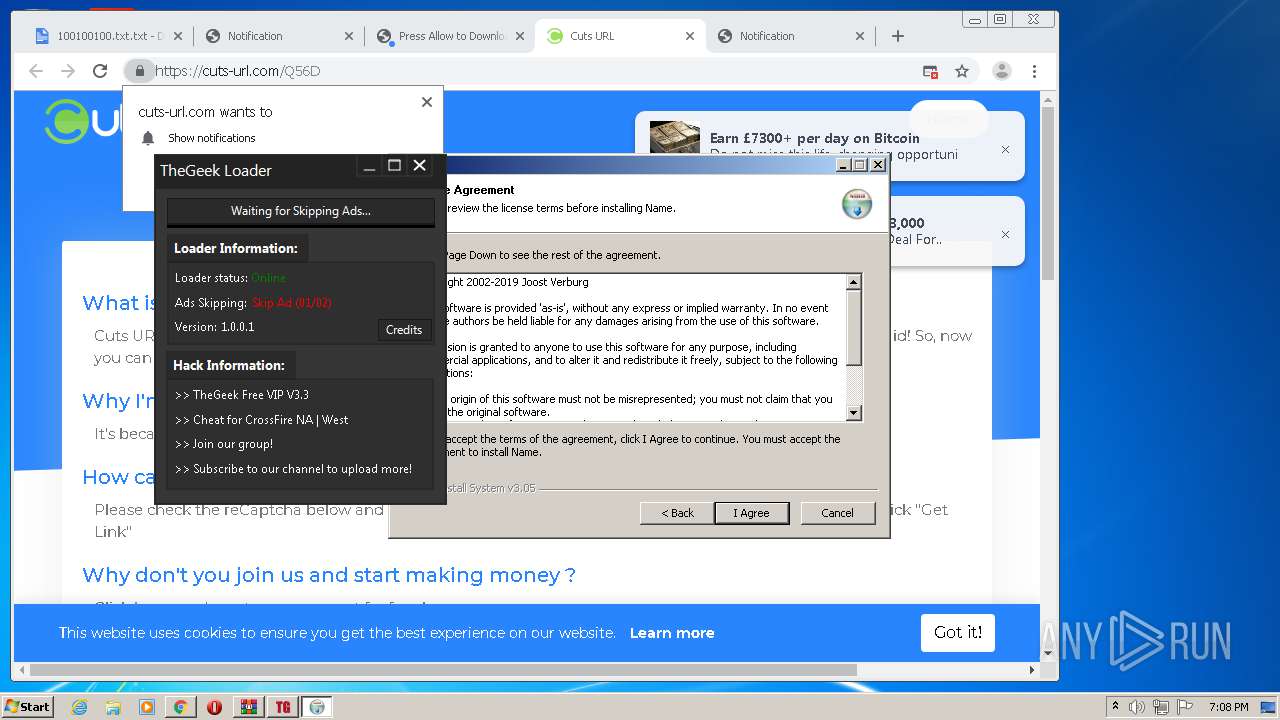
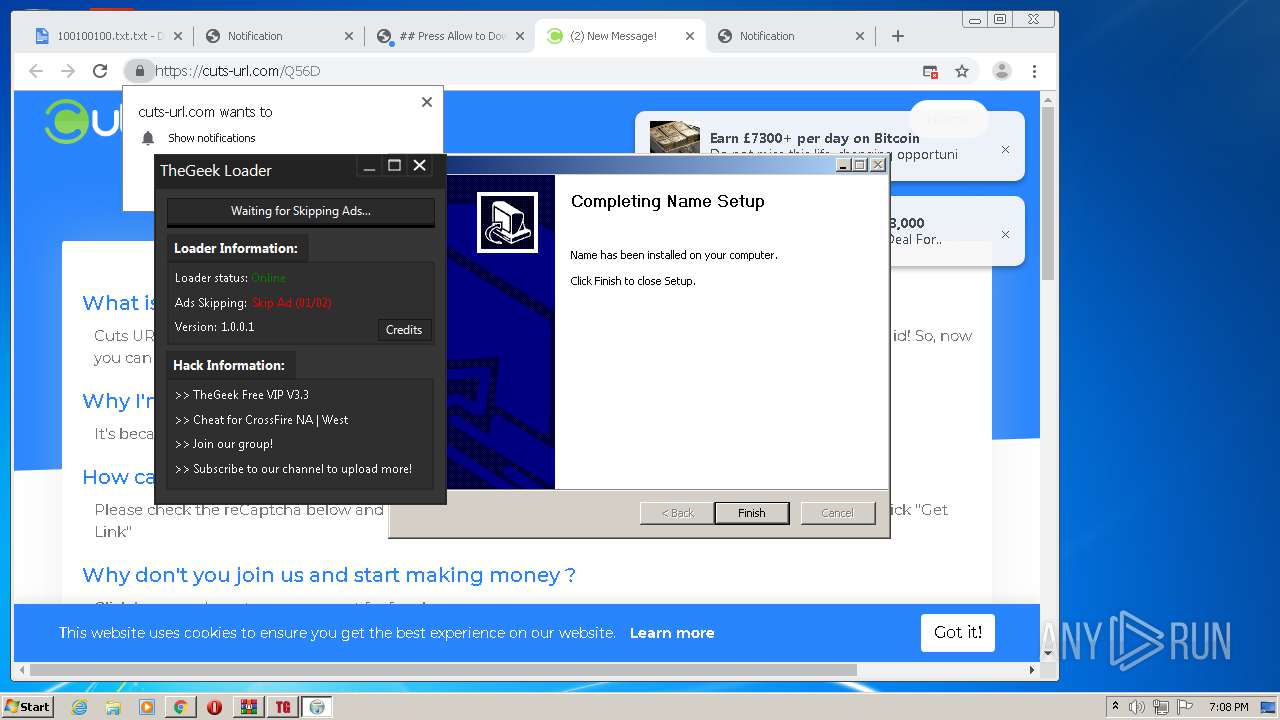
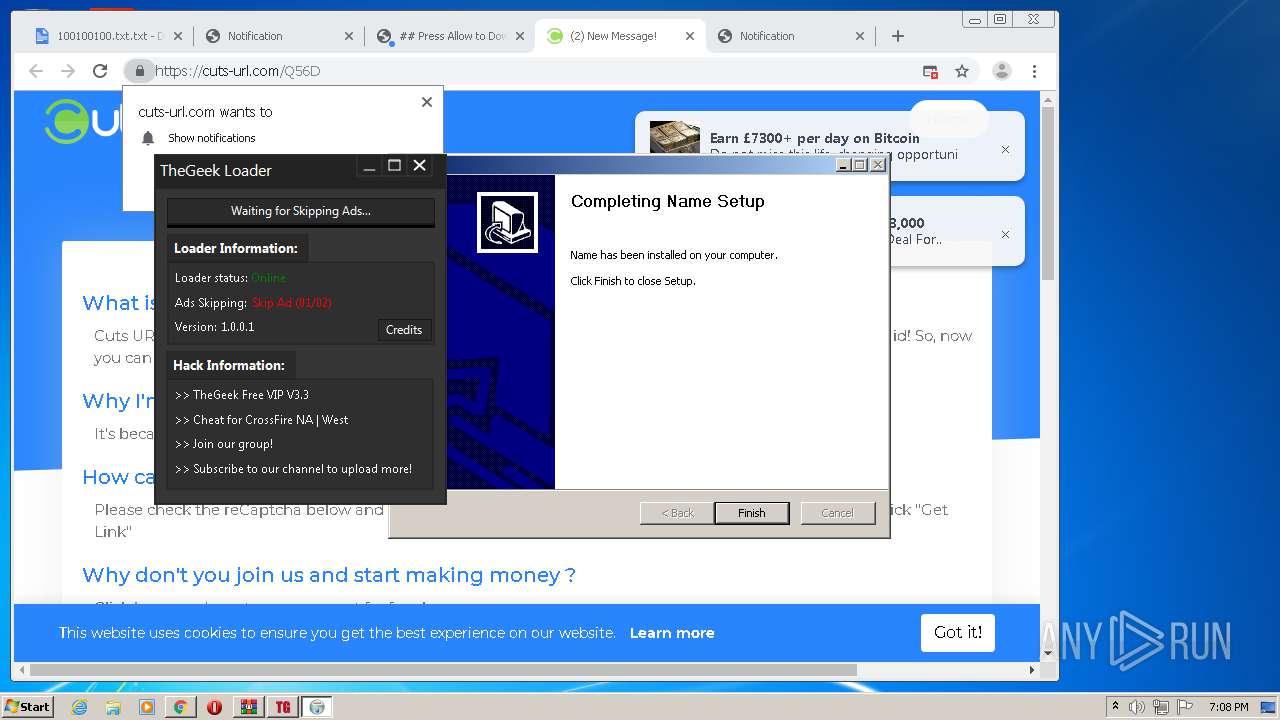
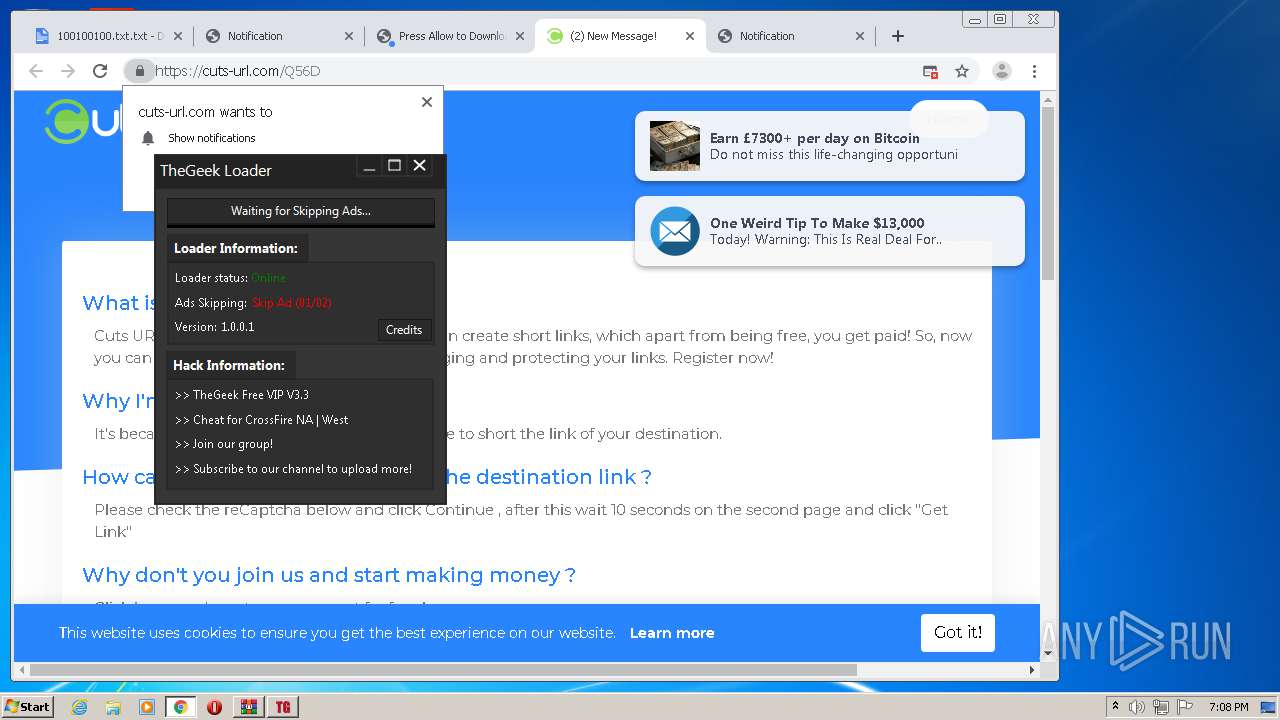
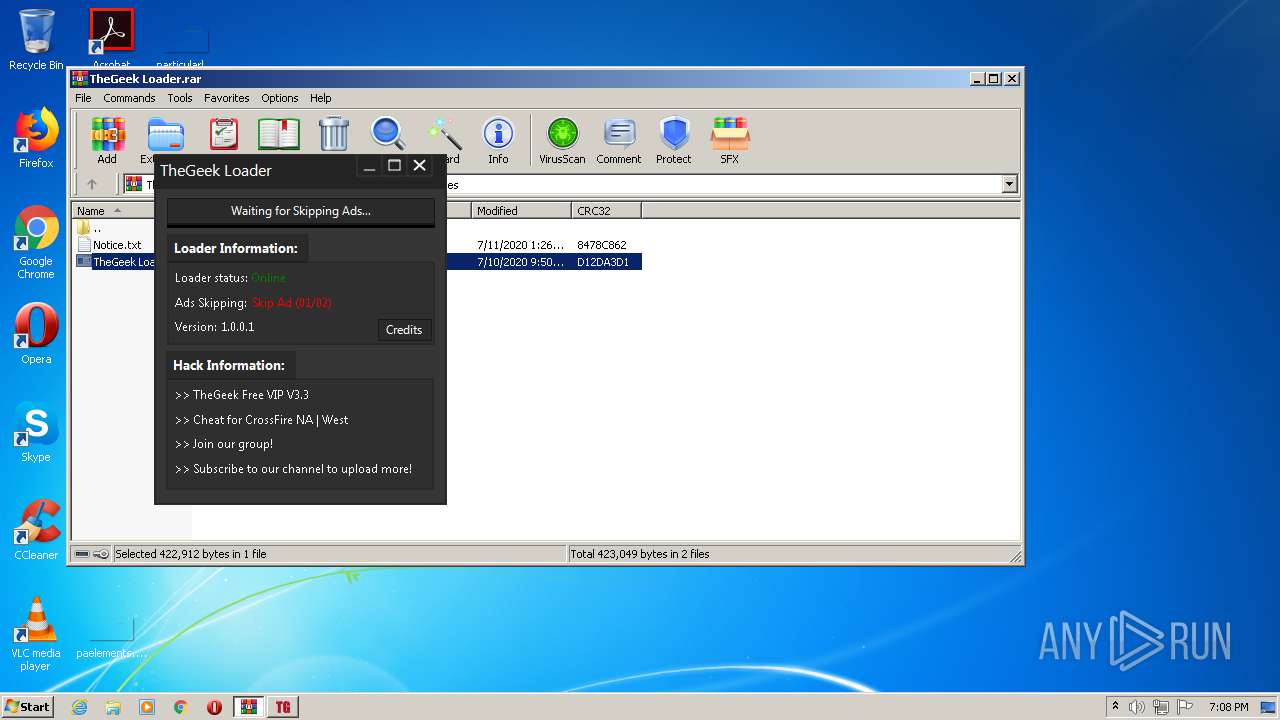
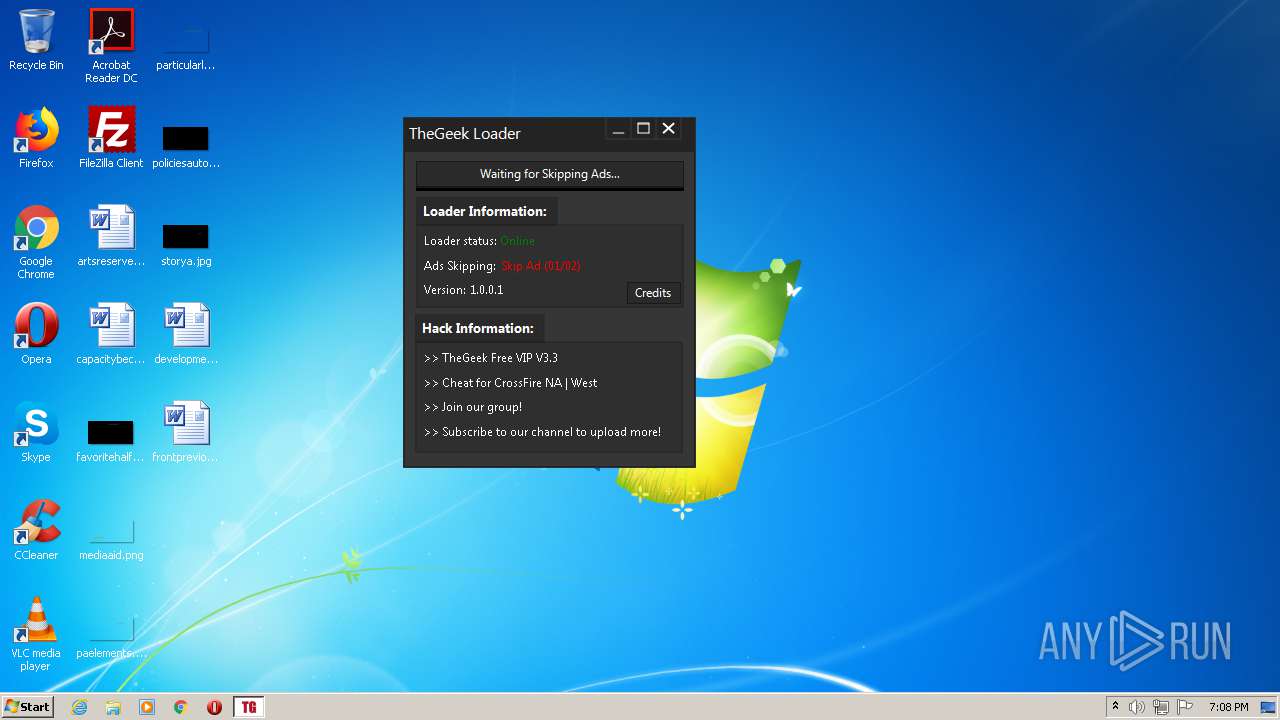
| File name: | TheGeek Loader.rar |
| Full analysis: | https://app.any.run/tasks/03180d19-49b1-480c-b5b4-77f0c887db3a |
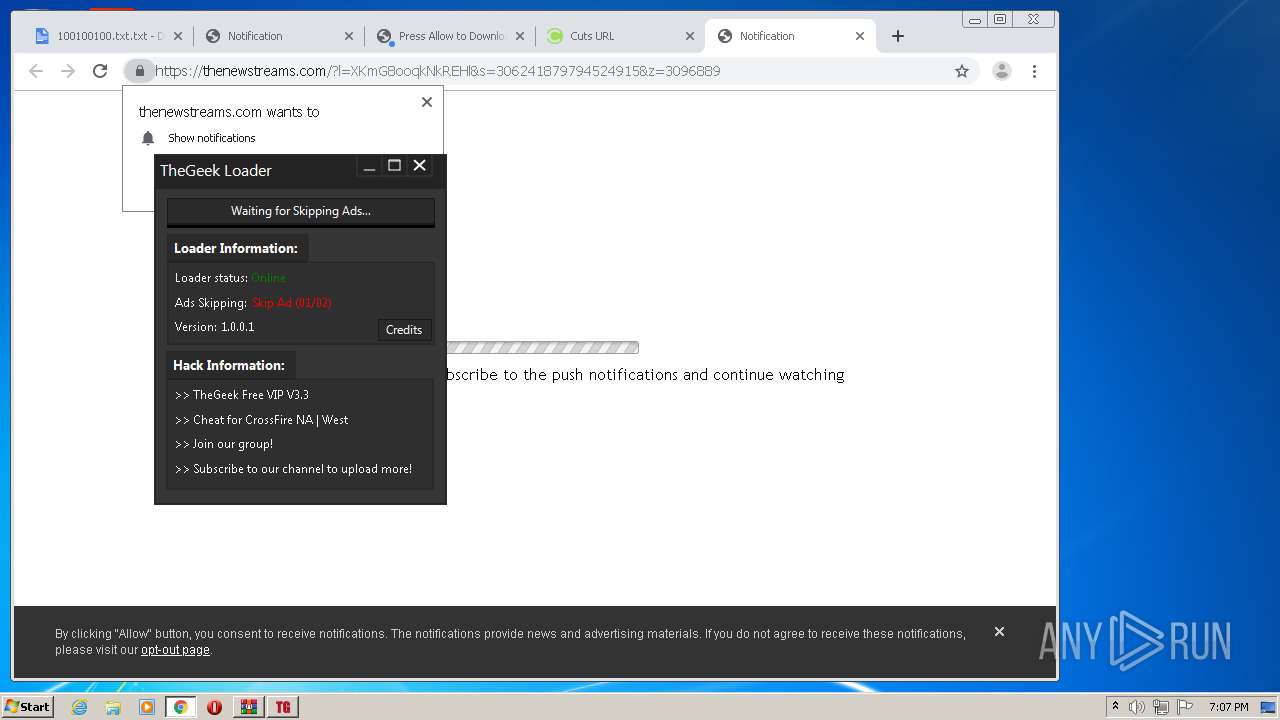
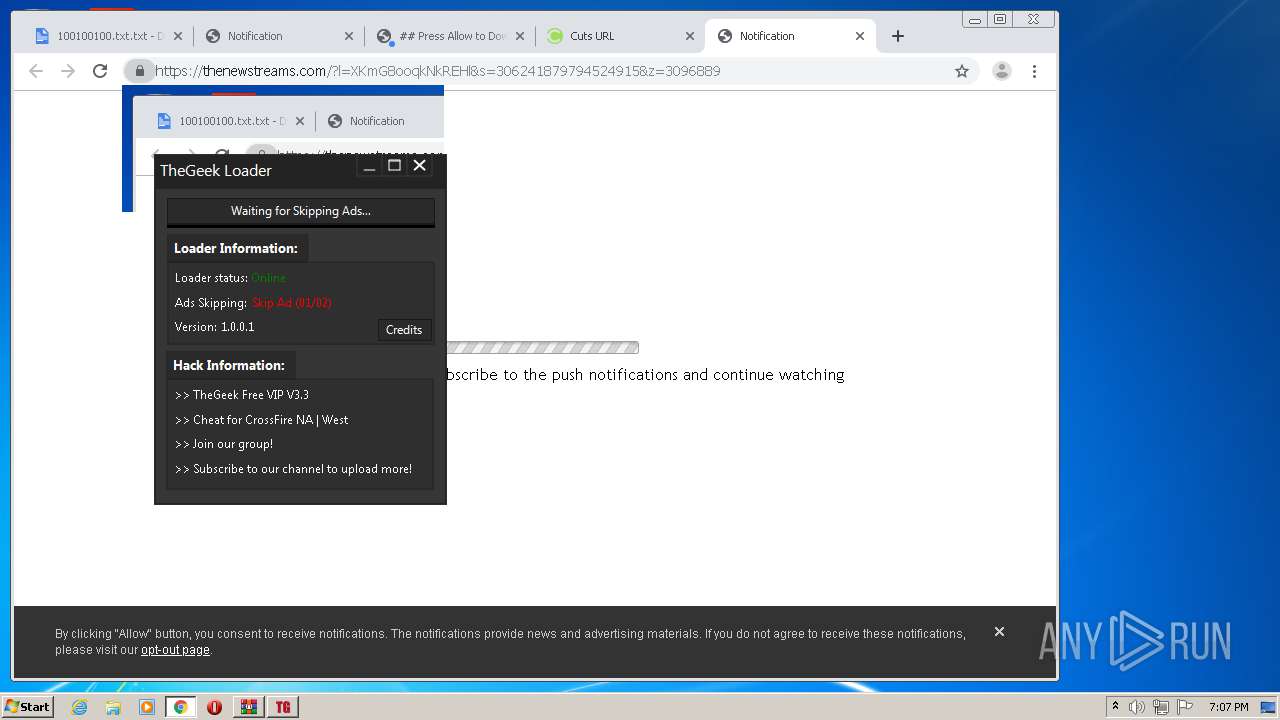
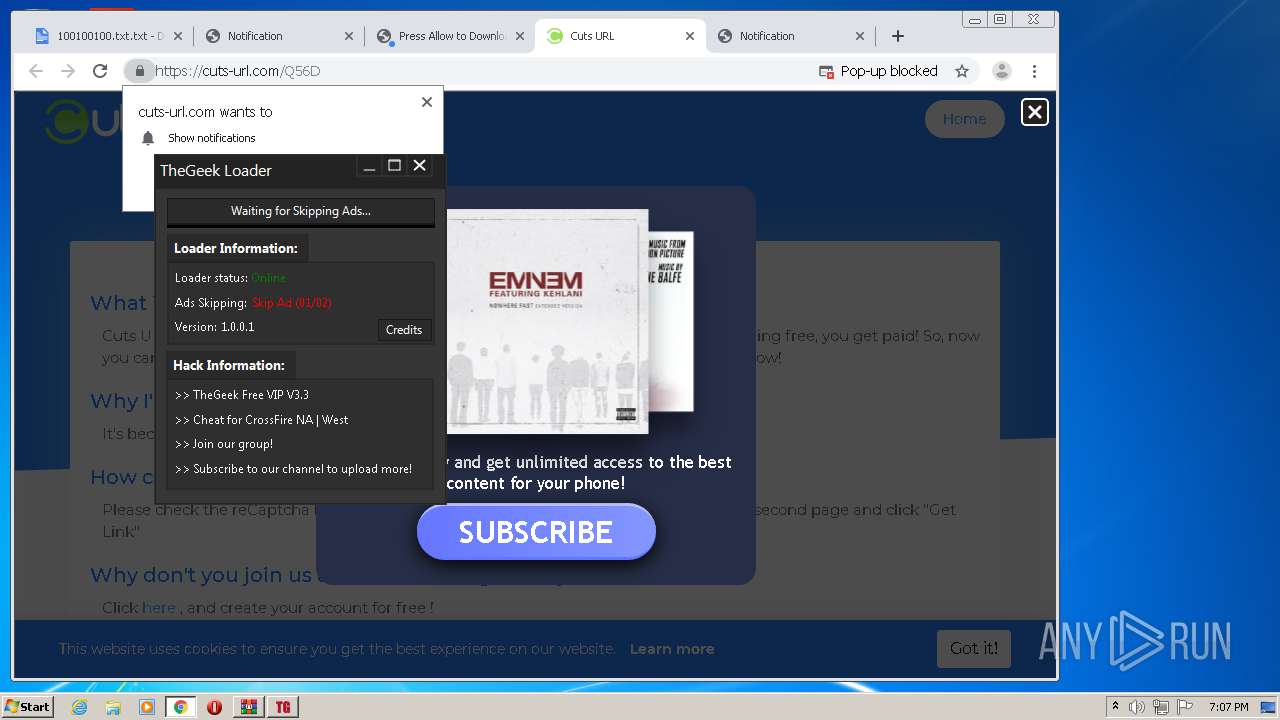
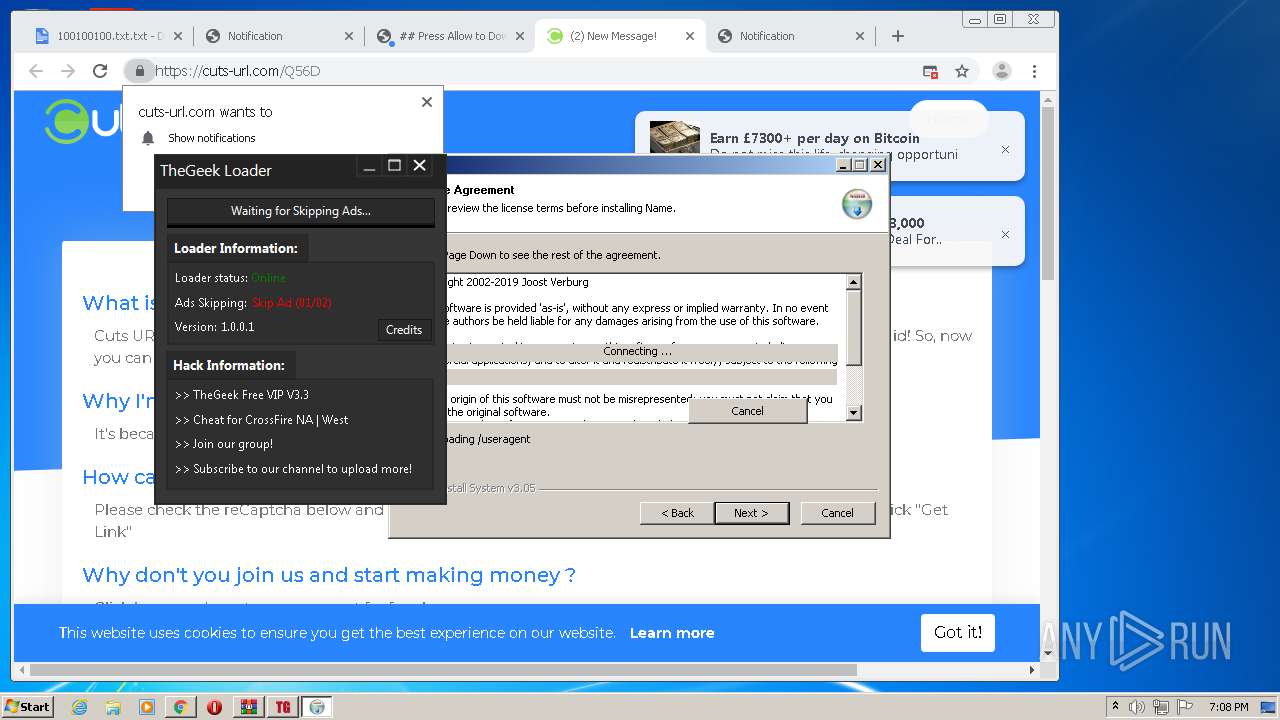
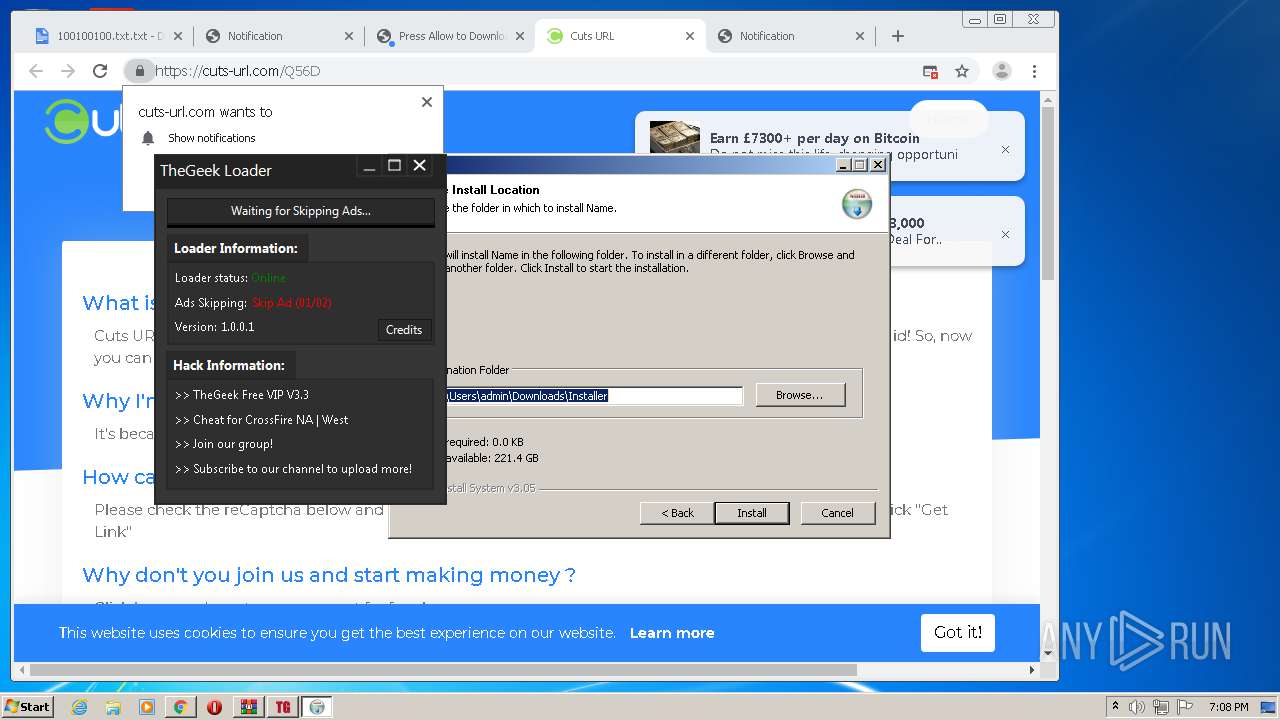
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:04:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8918A3B959CF08F7B363AF5AF3F8E962 |
| SHA1: | 4618336F448F76A4EFF07C4E12BCA3E23BE6342D |
| SHA256: | 2A72F187C79E411D730C2FEE513D2C1942E2E9A7A582164B3E8738D3F7481E15 |
| SSDEEP: | 12288:m5trCjAwpRr5S+BPQ5JRih02gIEn0v+8I6b/e:SrCdp7qr8uIgq/e |
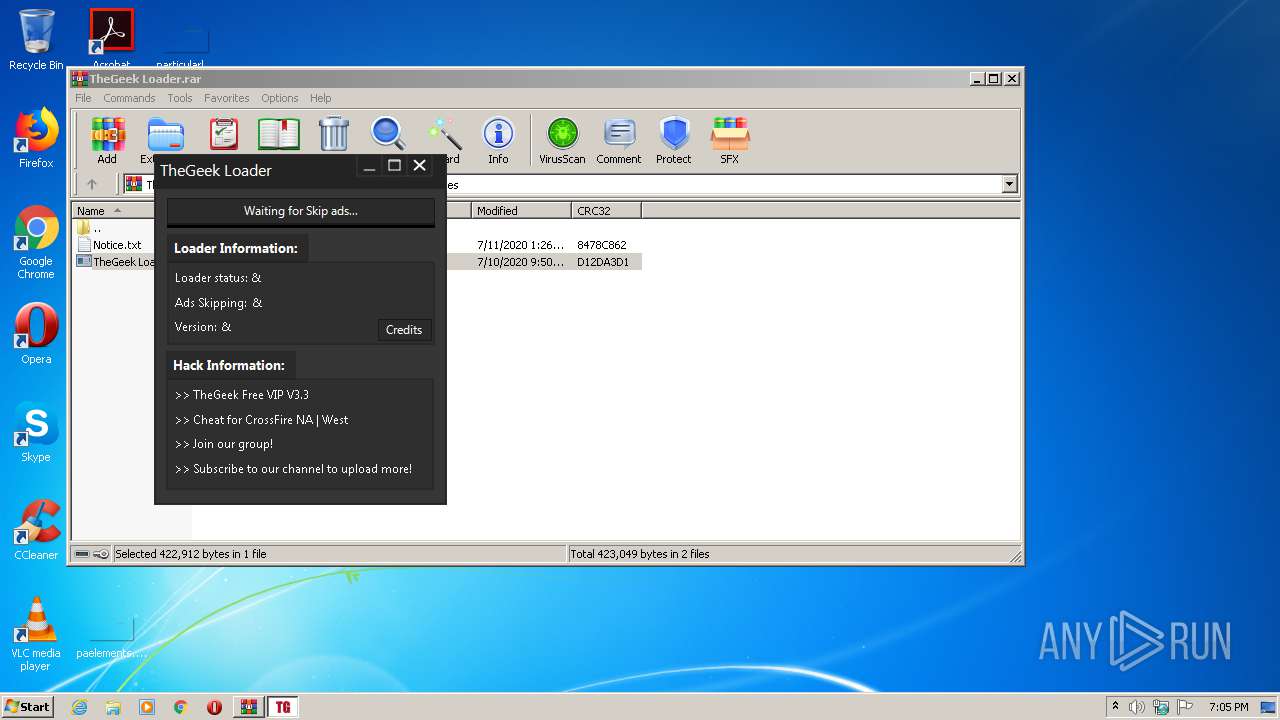
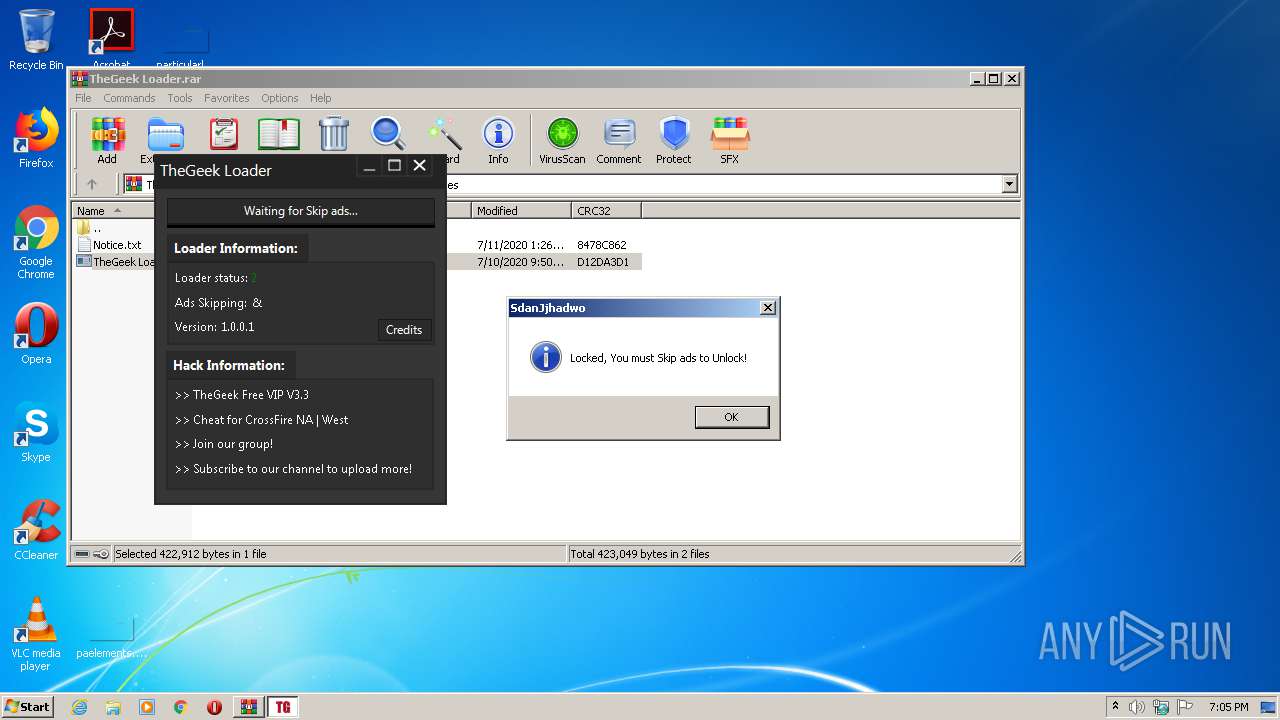
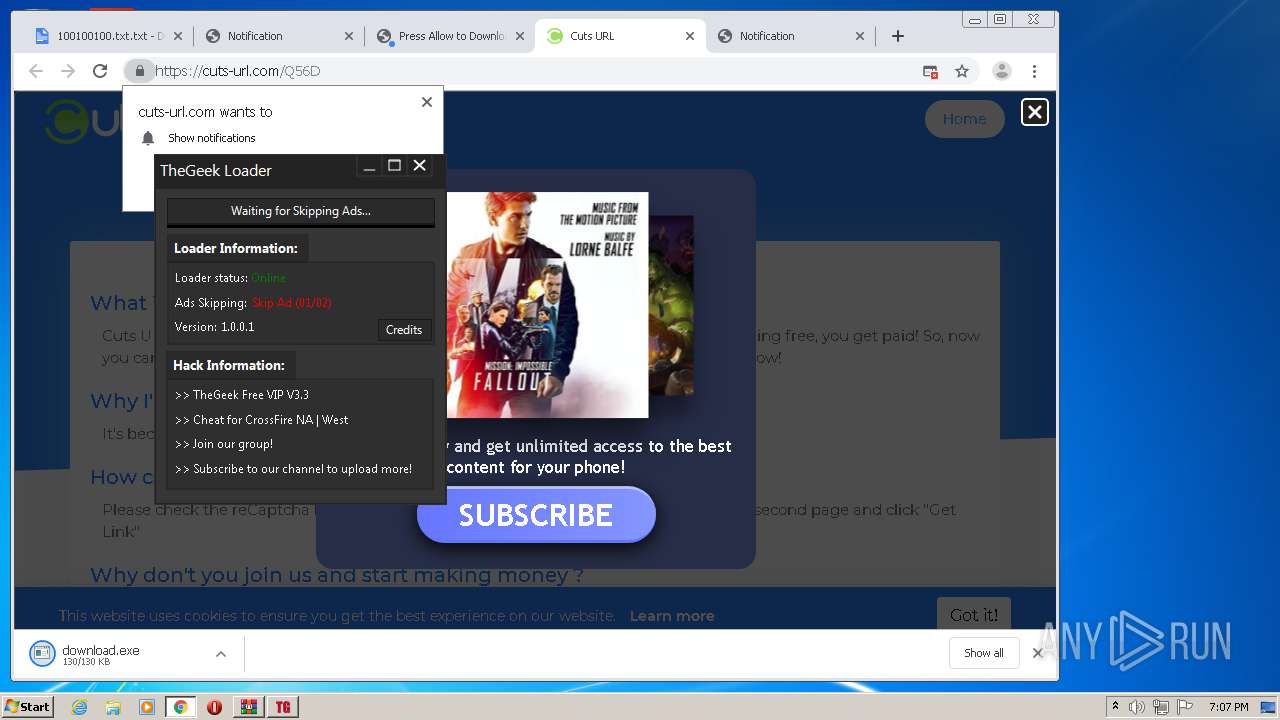
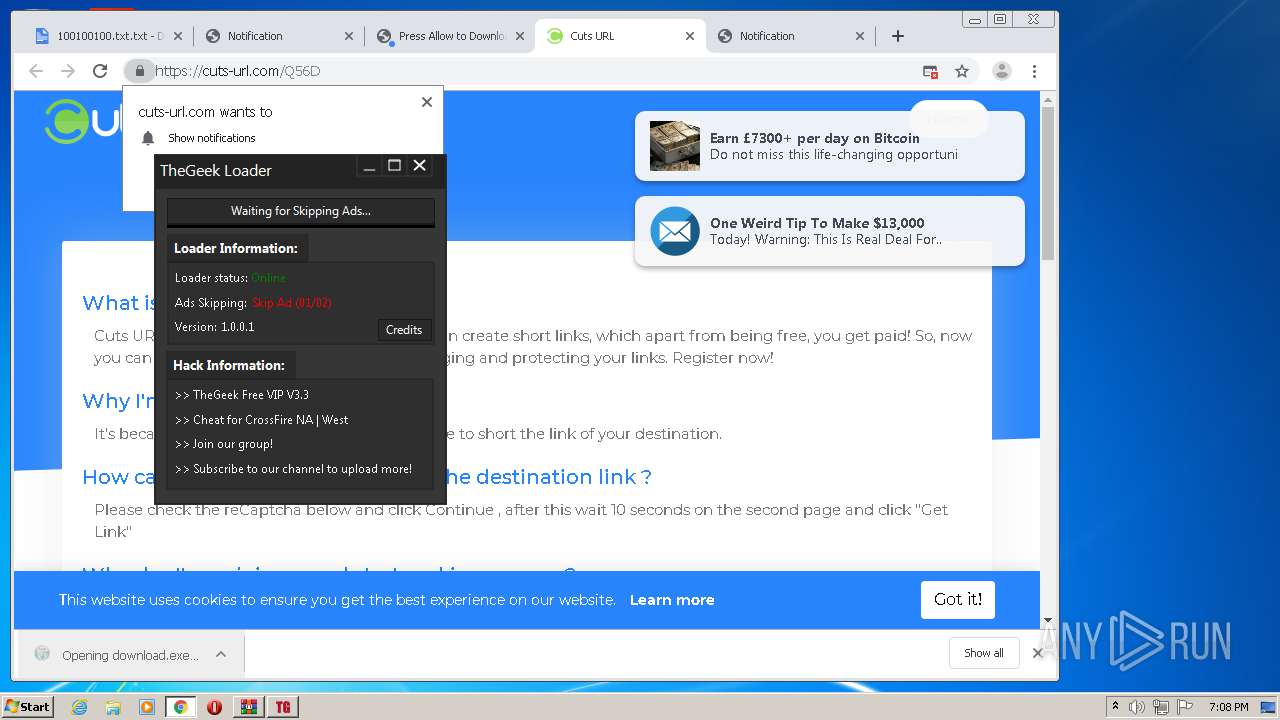
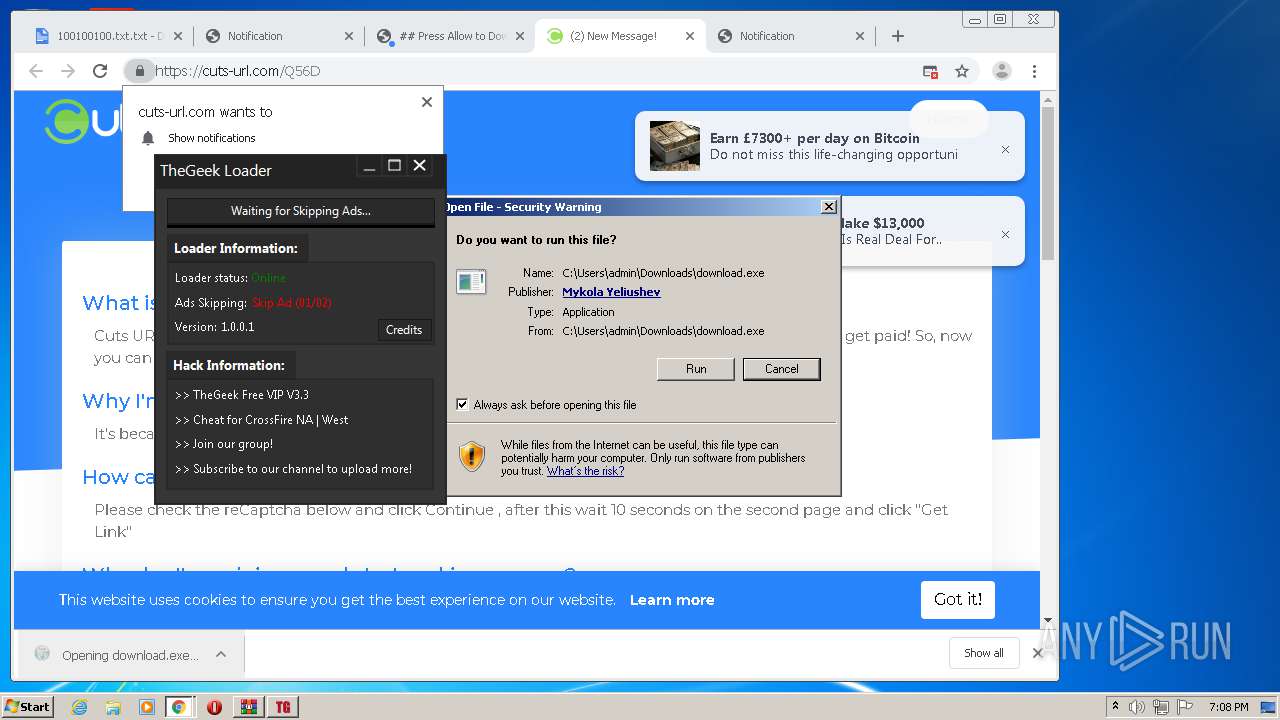
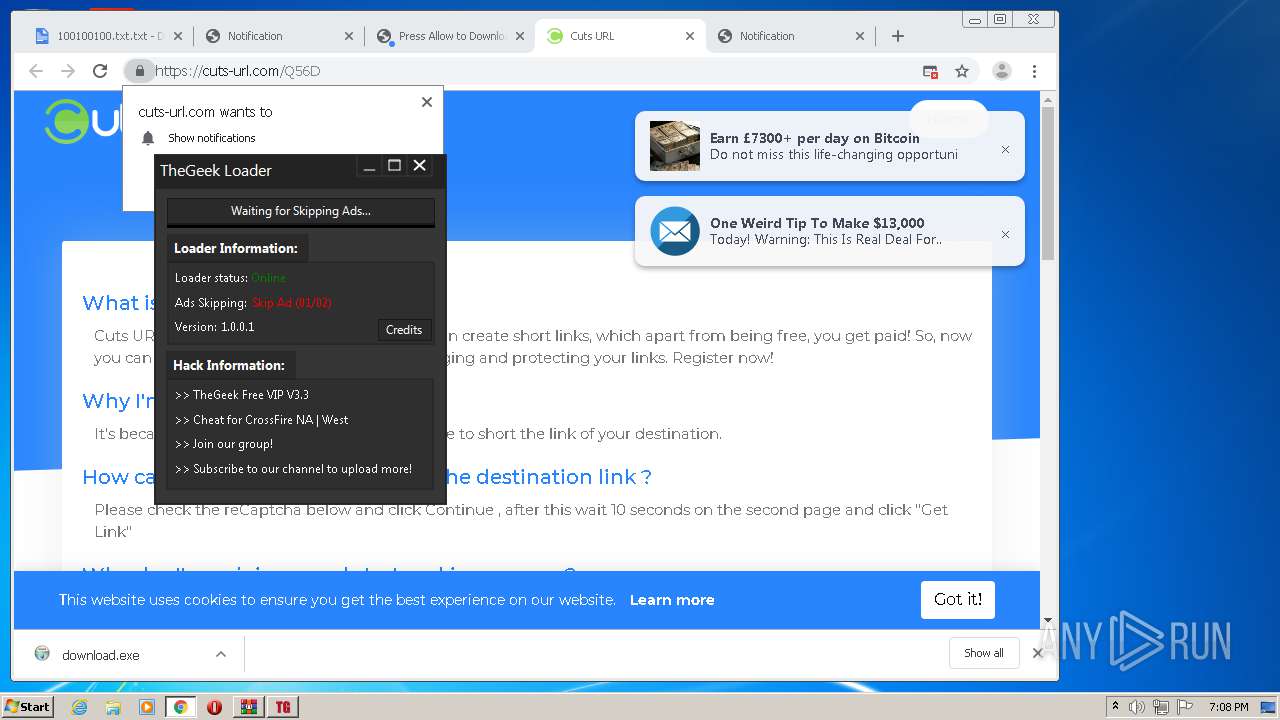
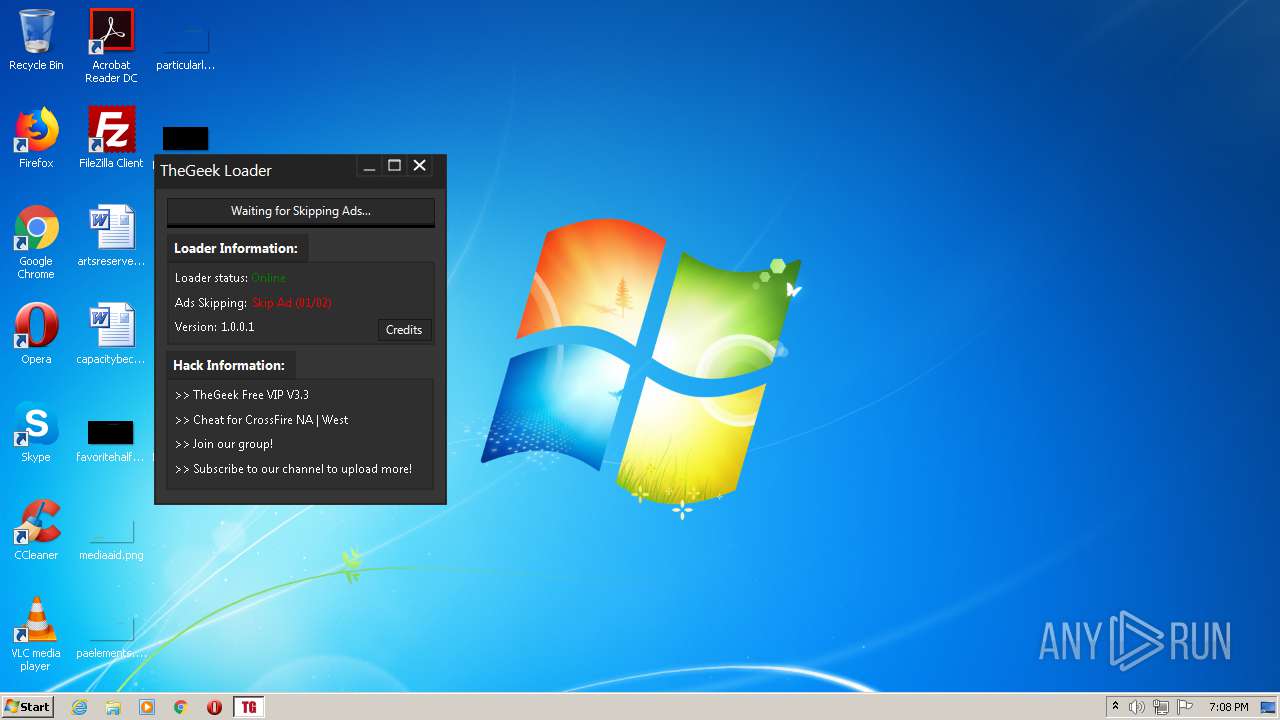
MALICIOUS
Application was dropped or rewritten from another process
- TheGeek Loader.exe (PID: 1540)
- TheGeek Loader.exe (PID: 3068)
- download.exe (PID: 3344)
Changes settings of System certificates
- download.exe (PID: 3344)
Loads dropped or rewritten executable
- download.exe (PID: 3344)
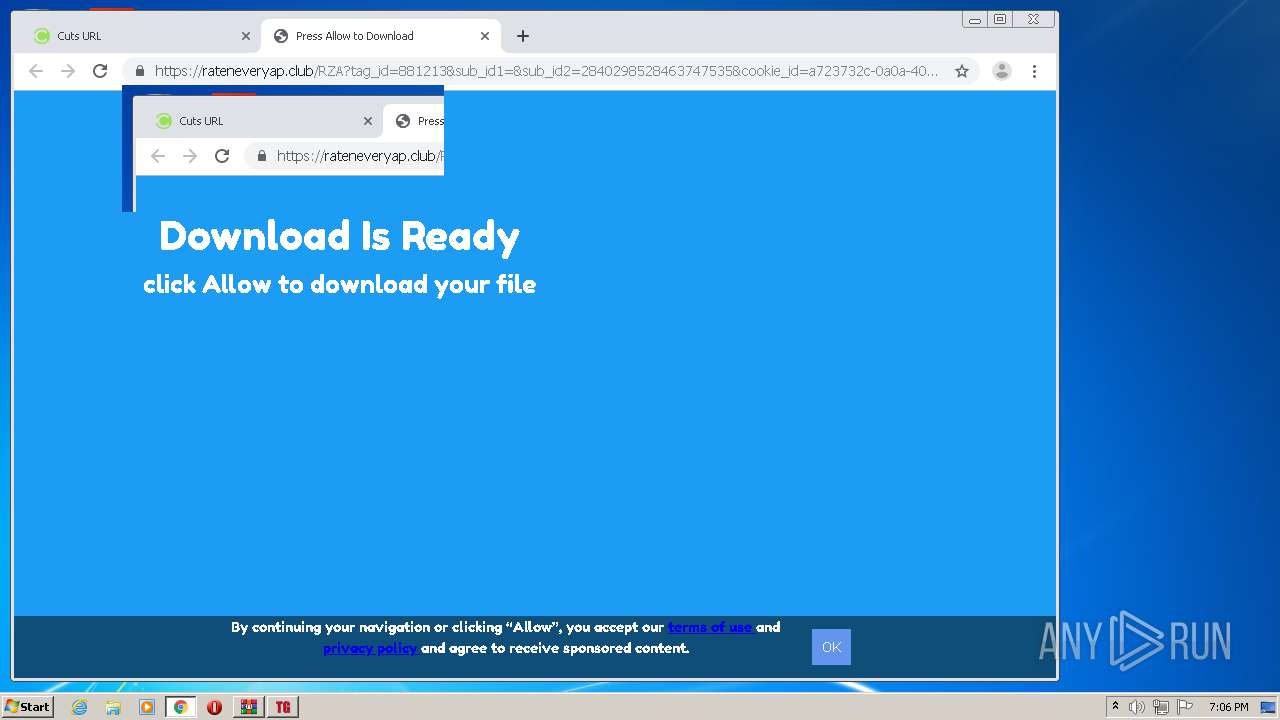
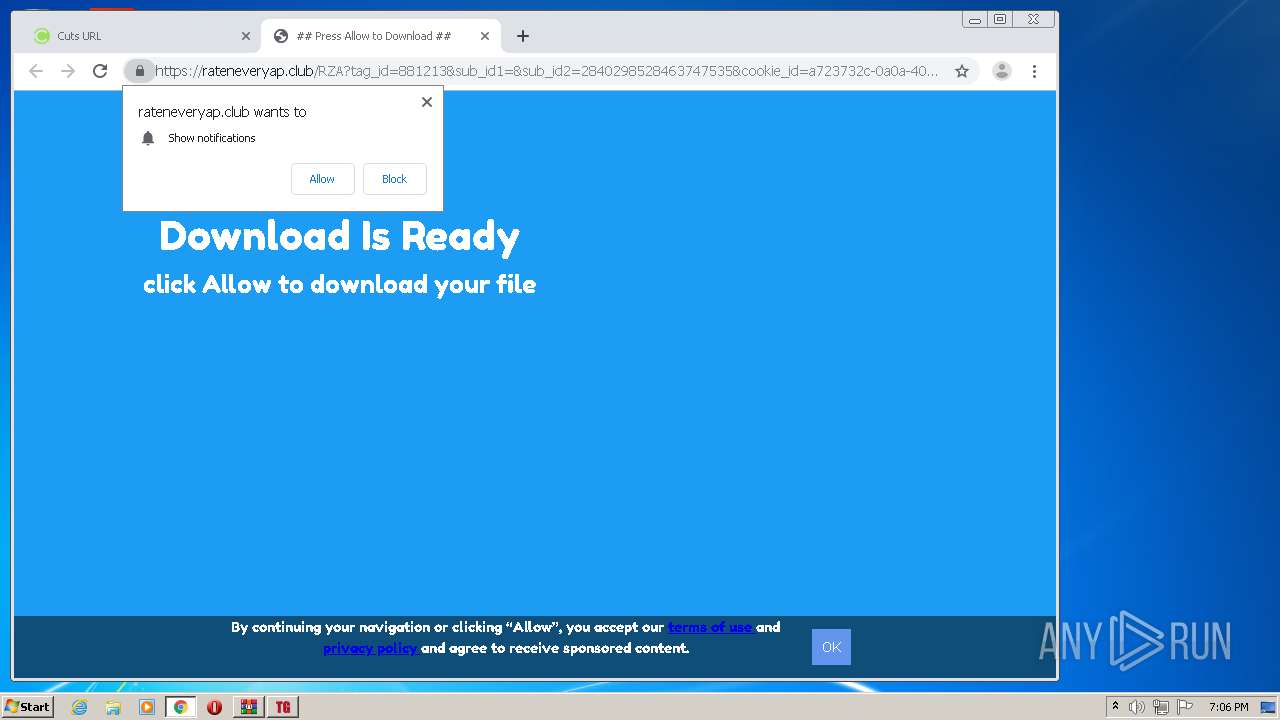
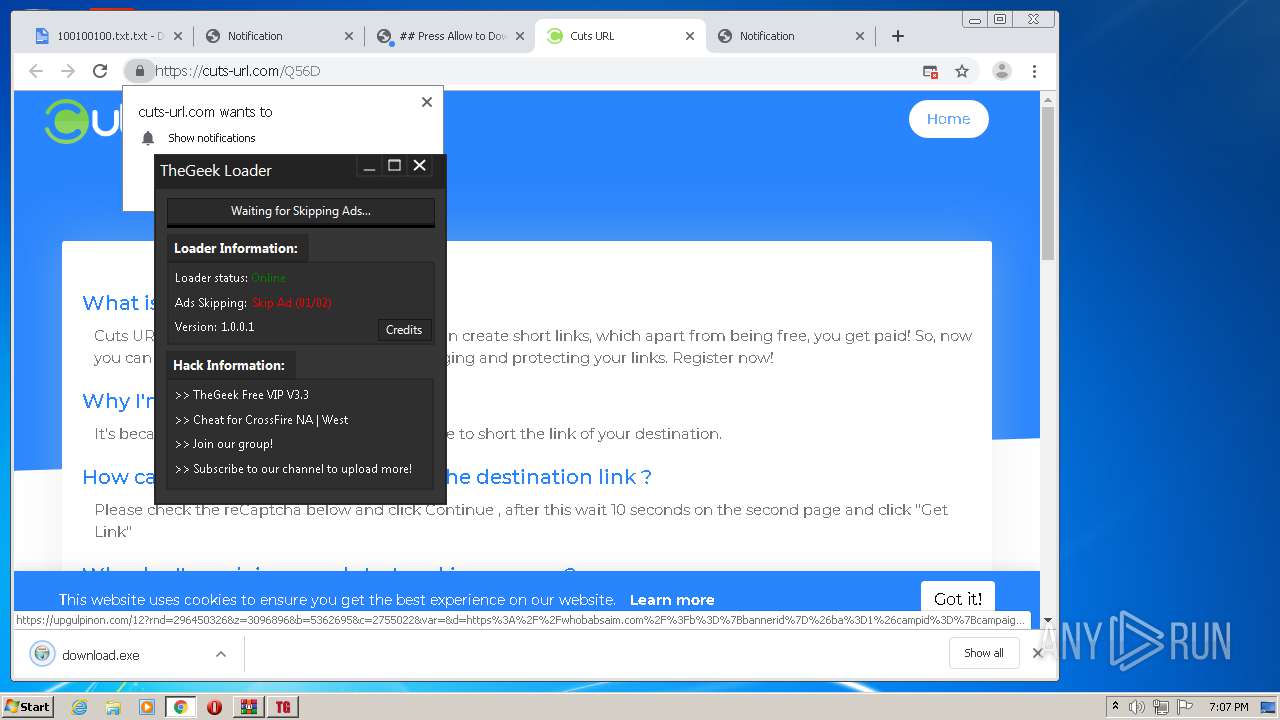
SUSPICIOUS
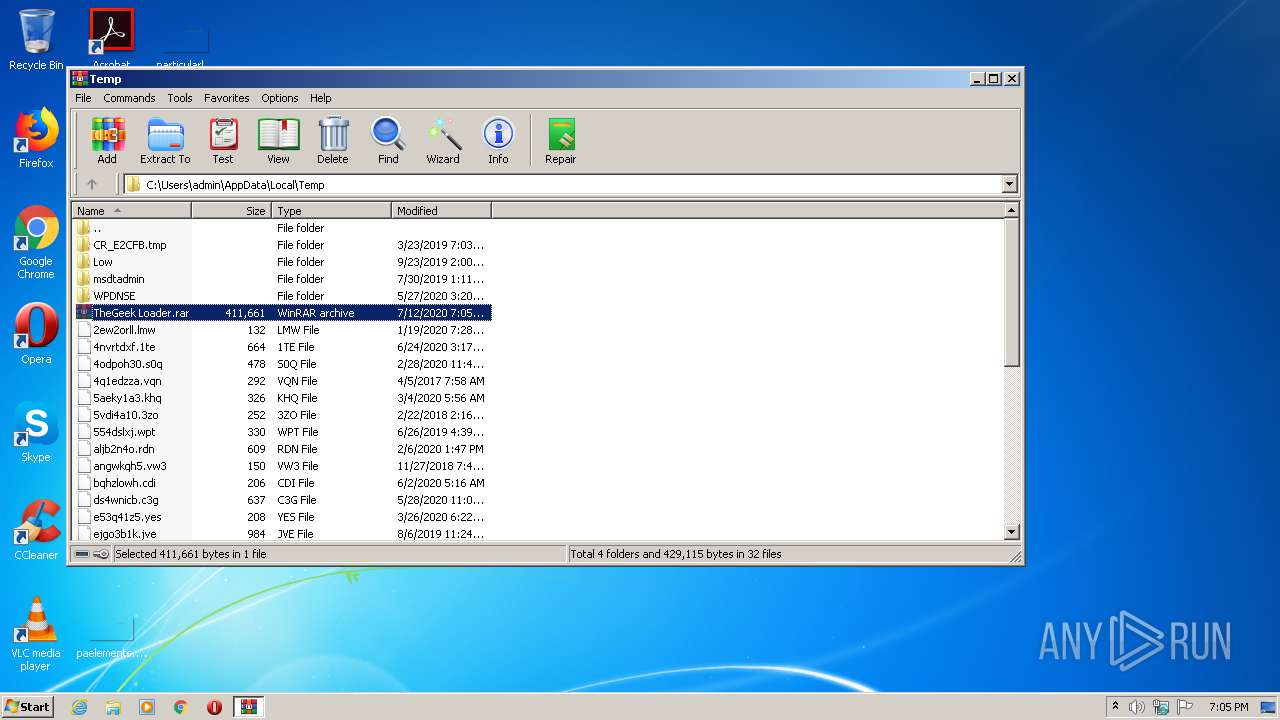
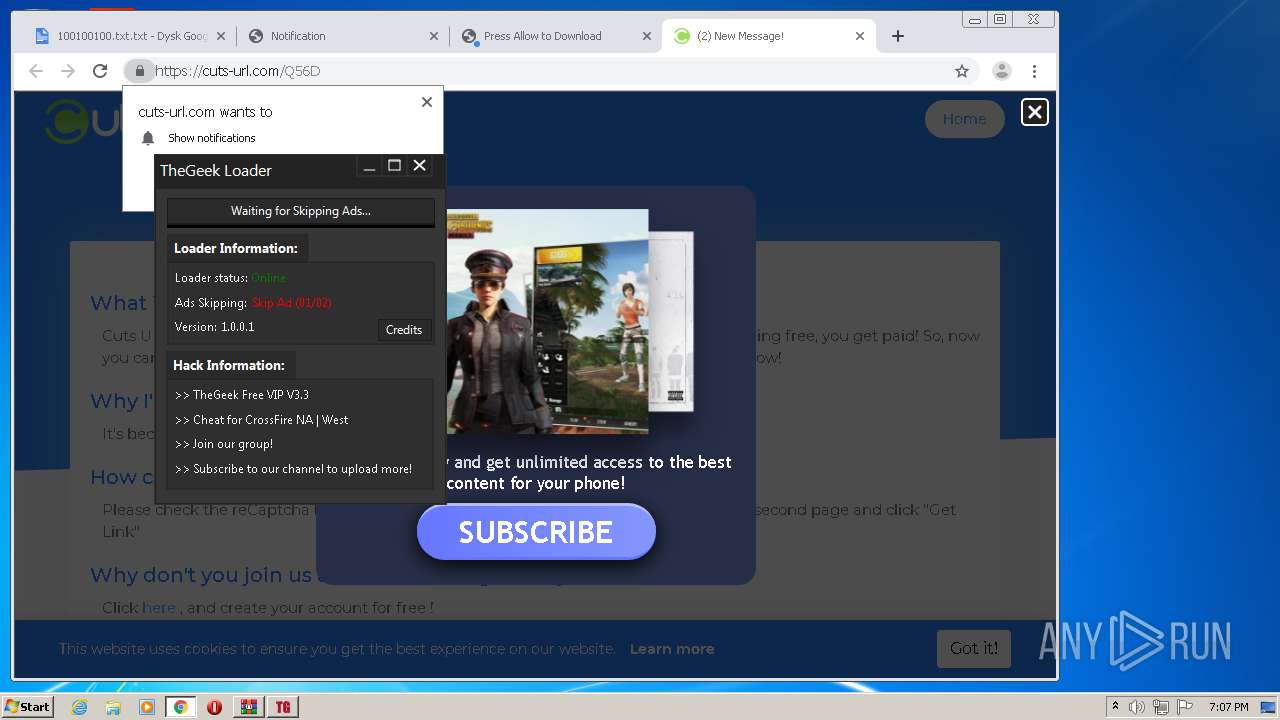
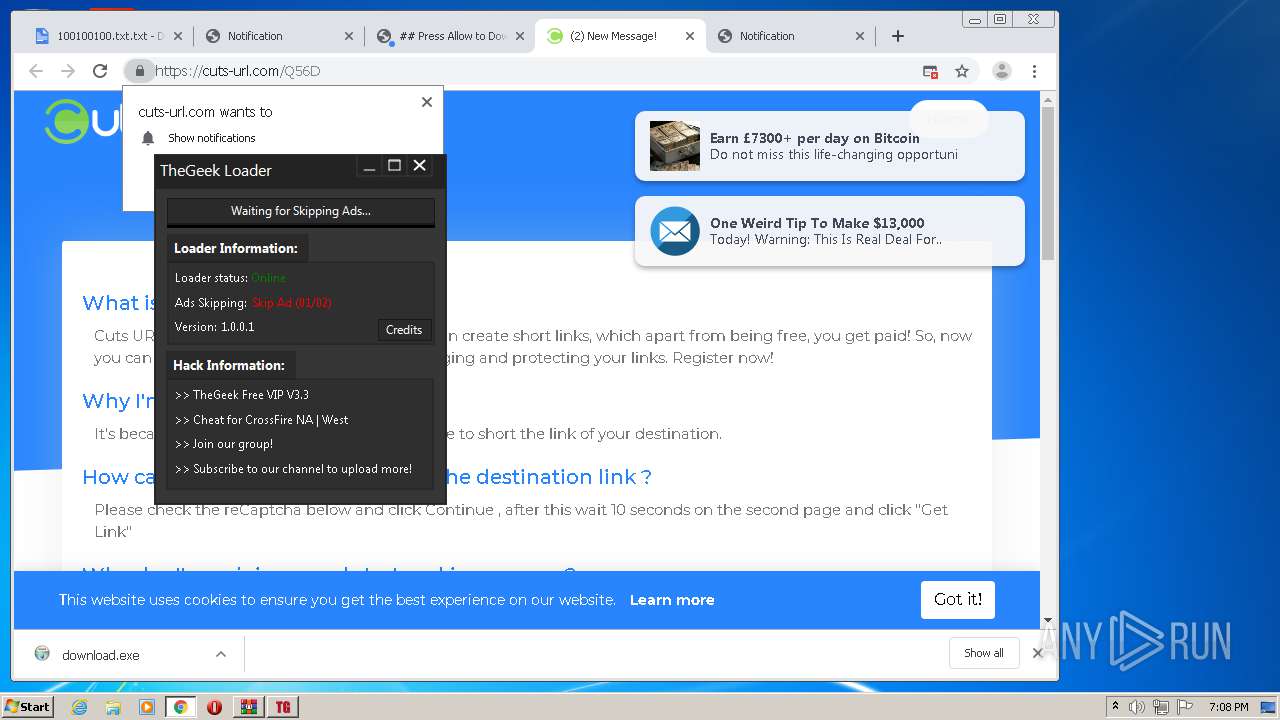
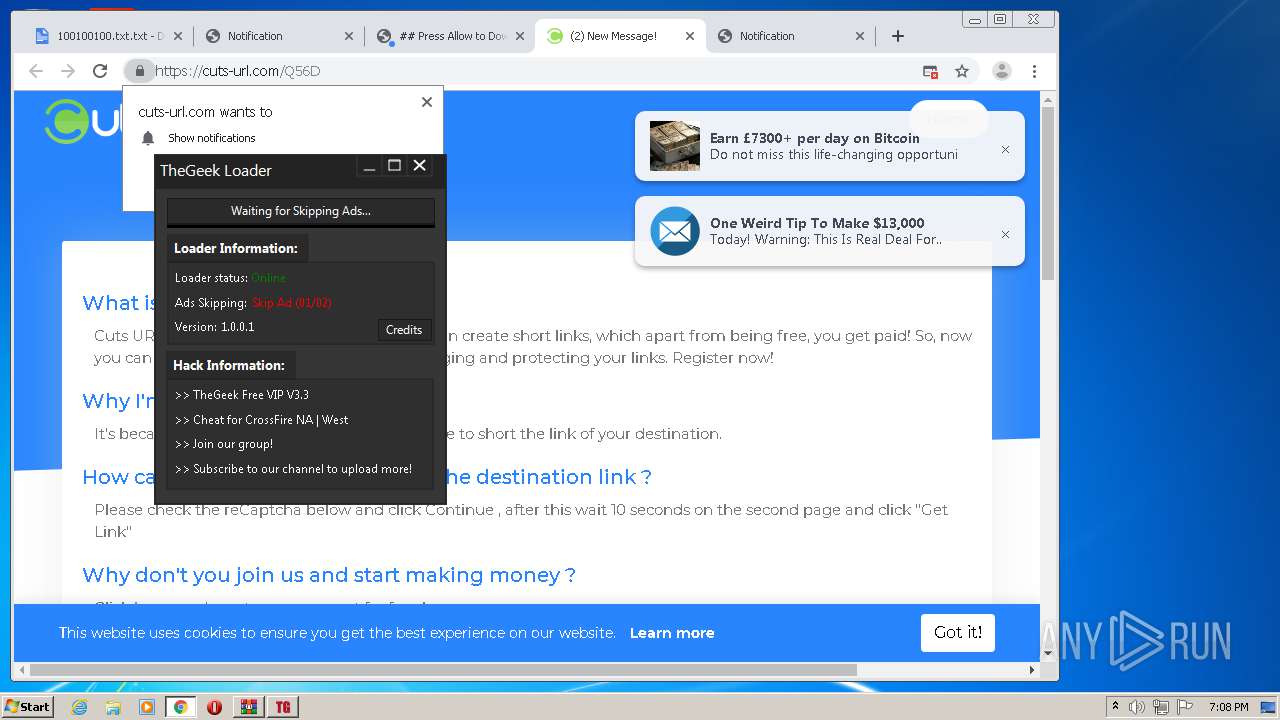
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1352)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1308)
- download.exe (PID: 3344)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1308)
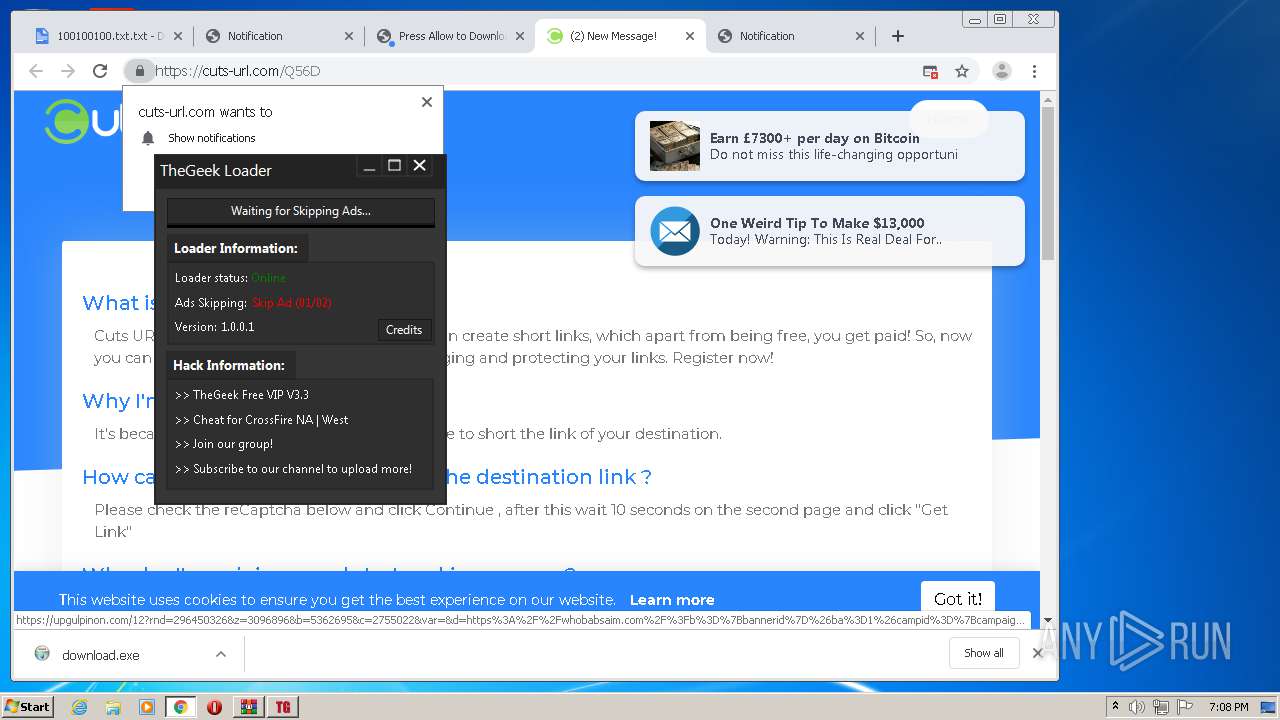
Reads Internet Cache Settings
- download.exe (PID: 3344)
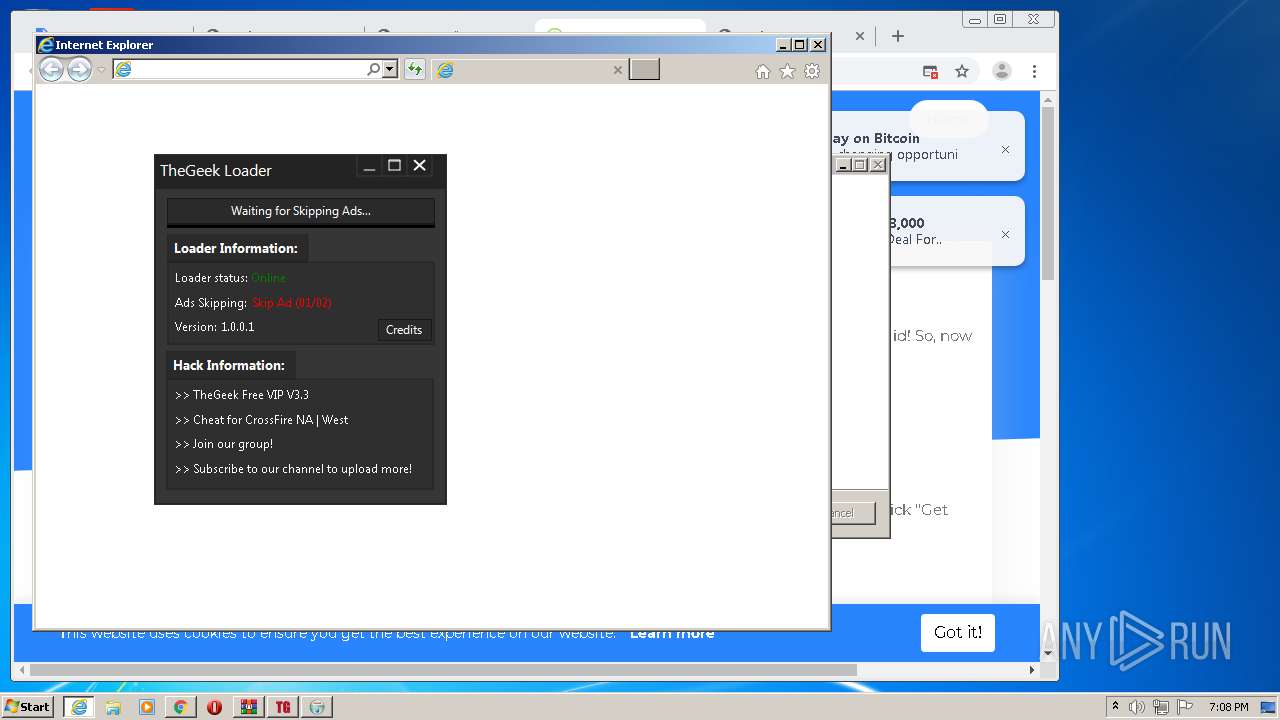
Starts Internet Explorer
- download.exe (PID: 3344)
Adds / modifies Windows certificates
- download.exe (PID: 3344)
Creates files in the user directory
- download.exe (PID: 3344)
INFO
Reads the hosts file
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1308)
Application launched itself
- chrome.exe (PID: 1728)
- chrome.exe (PID: 1308)
- iexplore.exe (PID: 2444)
Reads Internet Cache Settings
- chrome.exe (PID: 1308)
- iexplore.exe (PID: 2660)
- iexplore.exe (PID: 2444)
Changes settings of System certificates
- chrome.exe (PID: 1308)
- chrome.exe (PID: 2796)
Adds / modifies Windows certificates
- chrome.exe (PID: 1308)
- chrome.exe (PID: 2796)
Reads settings of System Certificates
- chrome.exe (PID: 1308)
- iexplore.exe (PID: 2660)
- chrome.exe (PID: 2796)
Reads internet explorer settings
- iexplore.exe (PID: 2660)
Changes internet zones settings
- iexplore.exe (PID: 2444)
Creates files in the user directory
- iexplore.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
98
Monitored processes
57
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=772984201805810685 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7908708870916226793 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5661586720379001823 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5797261043465289696 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a93a9d0,0x6a93a9e0,0x6a93a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4937375413193092089 --mojo-platform-channel-handle=3236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9013534470350058450 --mojo-platform-channel-handle=4140 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10909824129495364431 --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,11735540510584326241,4110026622411019352,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1157681945351682300 --mojo-platform-channel-handle=5048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a93a9d0,0x6a93a9e0,0x6a93a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 009
Read events
2 531
Write events
2 469
Delete events
9
Modification events
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\TheGeek Loader.rar | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
11
Suspicious files
187
Text files
374
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0B50EE-51C.pma | — | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\58ff7b4f-6a80-4927-b46b-d3f7ac33e611.tmp | — | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFfc402.TMP | text | |
MD5:— | SHA256:— | |||
| 1352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.44861\Notice.txt | text | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFfc4fc.TMP | text | |
MD5:— | SHA256:— | |||
| 1308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1352.44861\TheGeek Loader.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
146
DNS requests
75
Threats
1
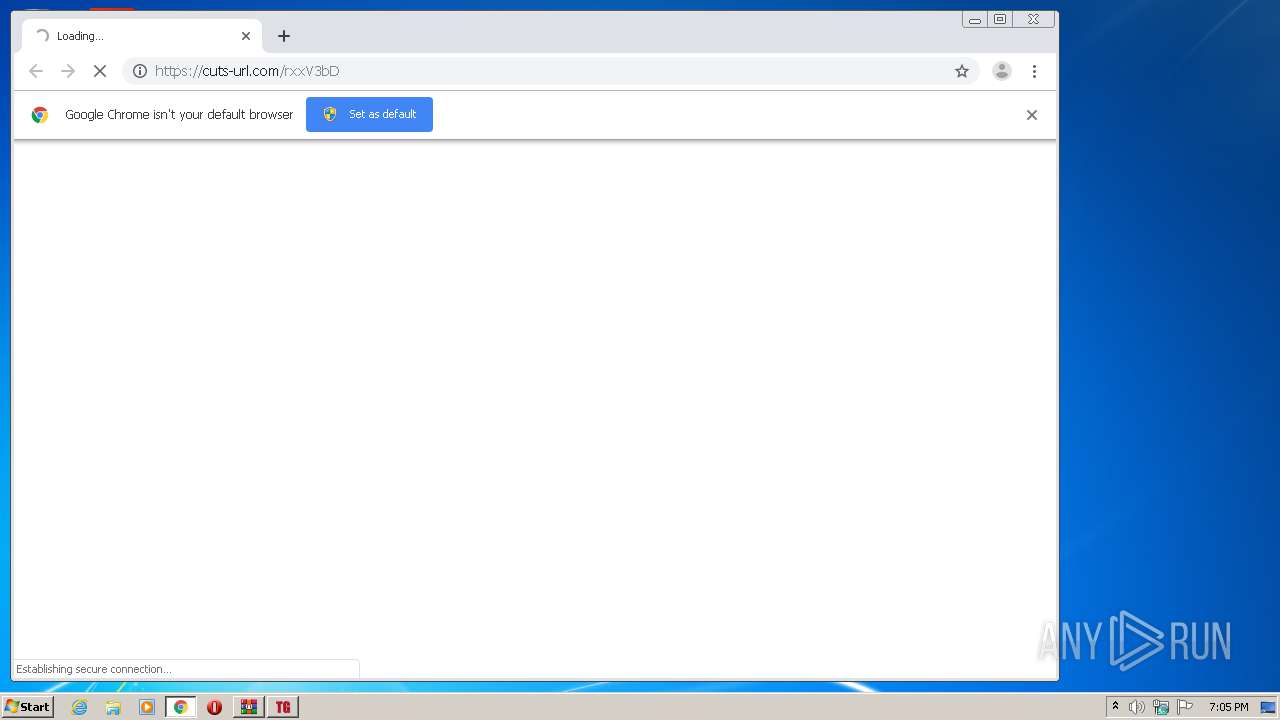
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
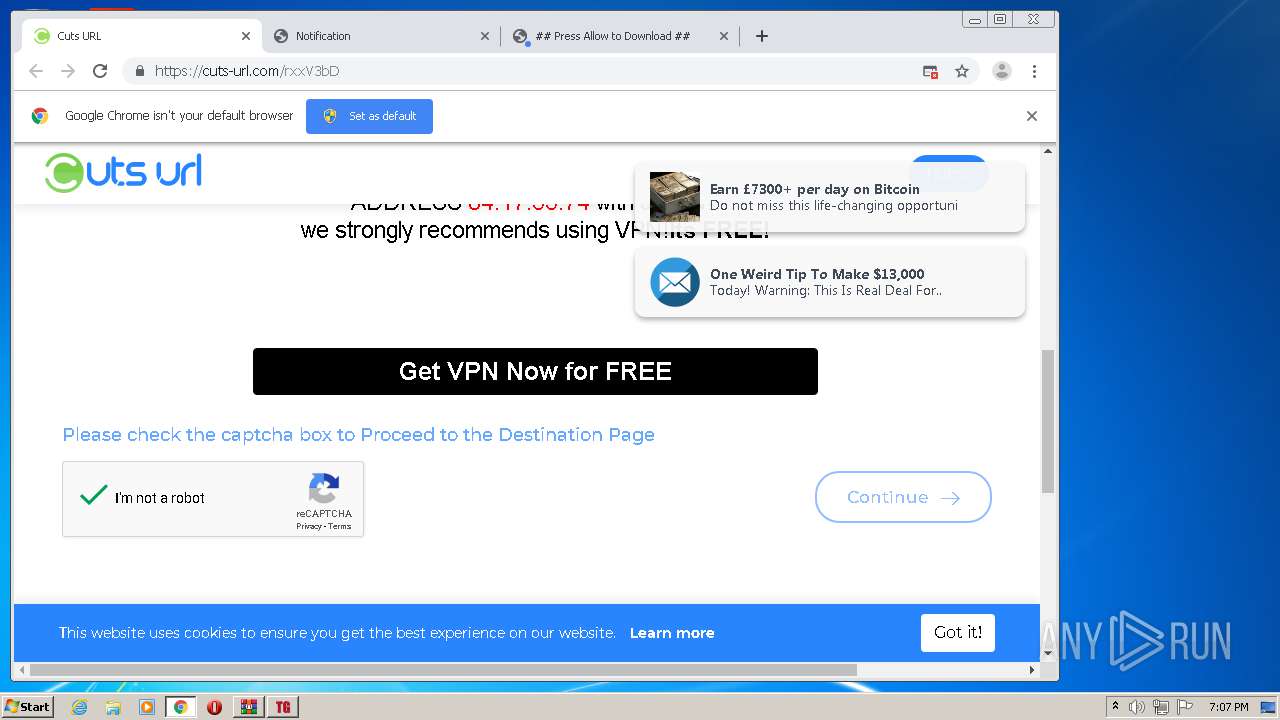
2796 | chrome.exe | GET | 200 | 185.48.9.15:80 | http://r4---sn-x2pm-3uf6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=84.17.55.74&mm=28&mn=sn-x2pm-3uf6&ms=nvh&mt=1594577054&mv=m&mvi=4&pl=23&shardbypass=yes | PL | crx | 823 Kb | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3344 | download.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD9bz4kmMJbHQgAAAAAR%2FAz | US | der | 472 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDCBDbuX62tRAgAAAABvB68%3D | US | der | 471 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDCBDbuX62tRAgAAAABvB68%3D | US | der | 471 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEH4Q2QH3rAPNCAAAAABH744%3D | US | der | 471 b | whitelisted |
2796 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEH4Q2QH3rAPNCAAAAABH744%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
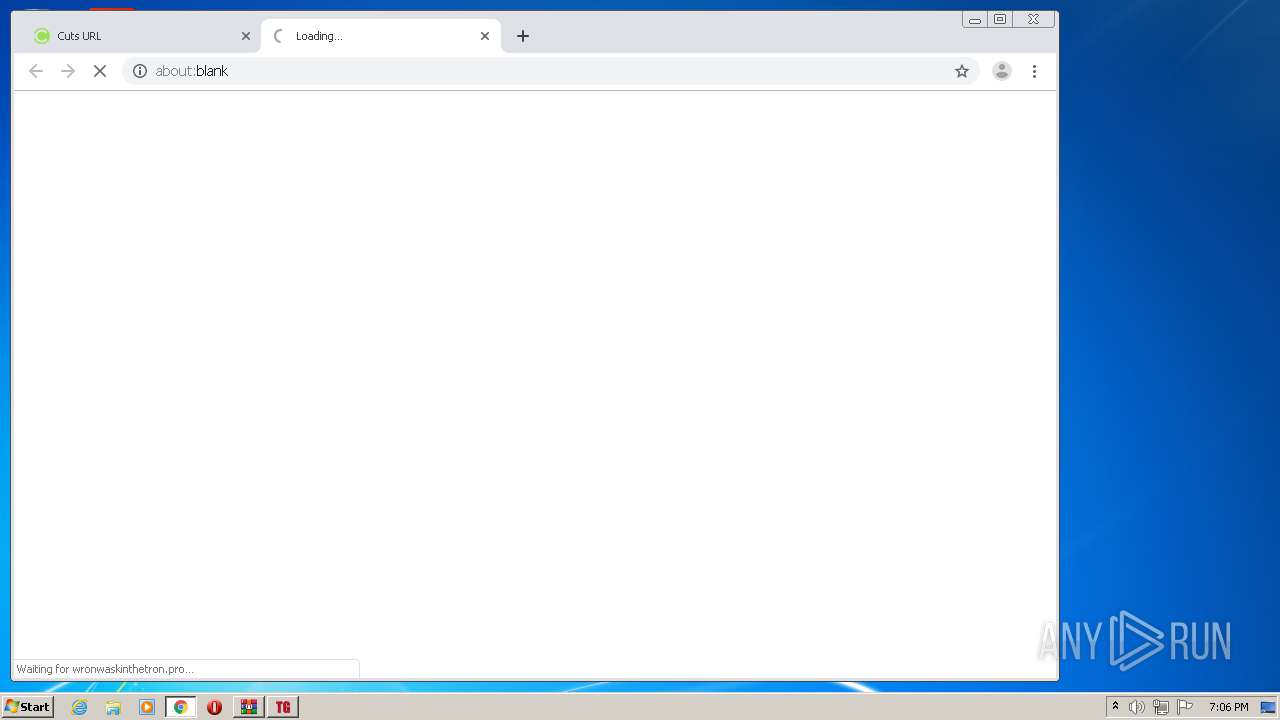
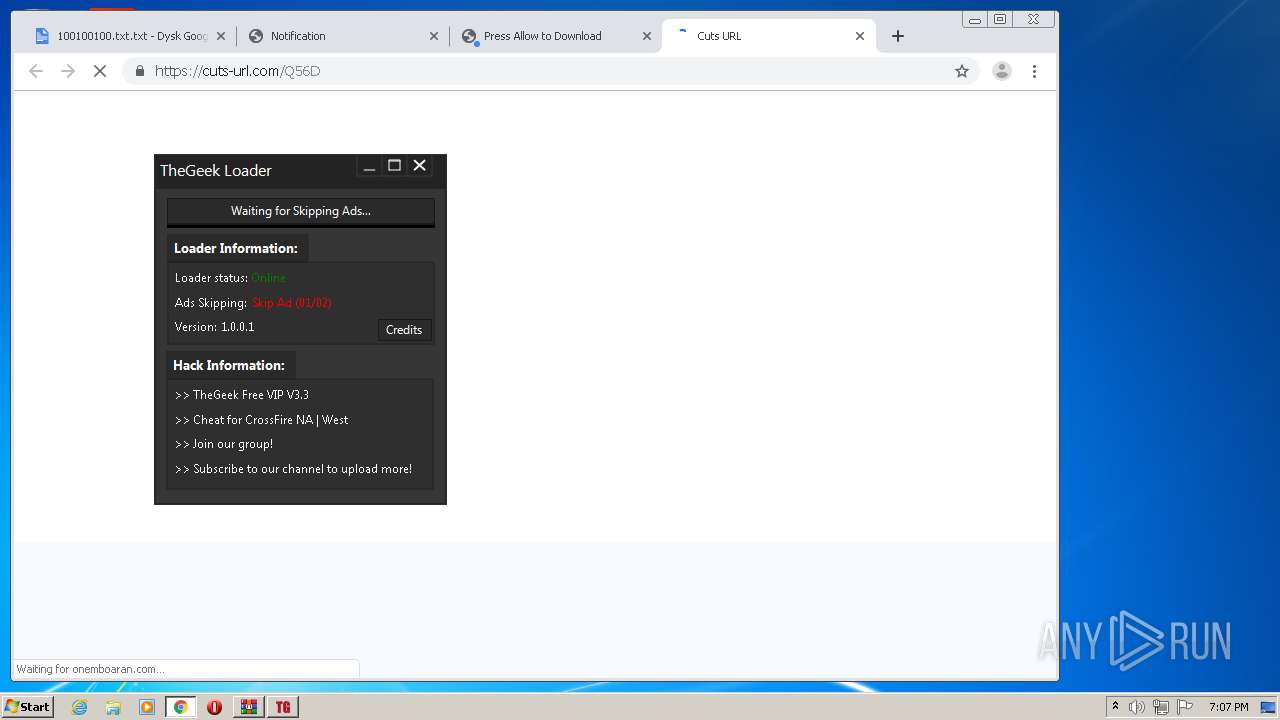
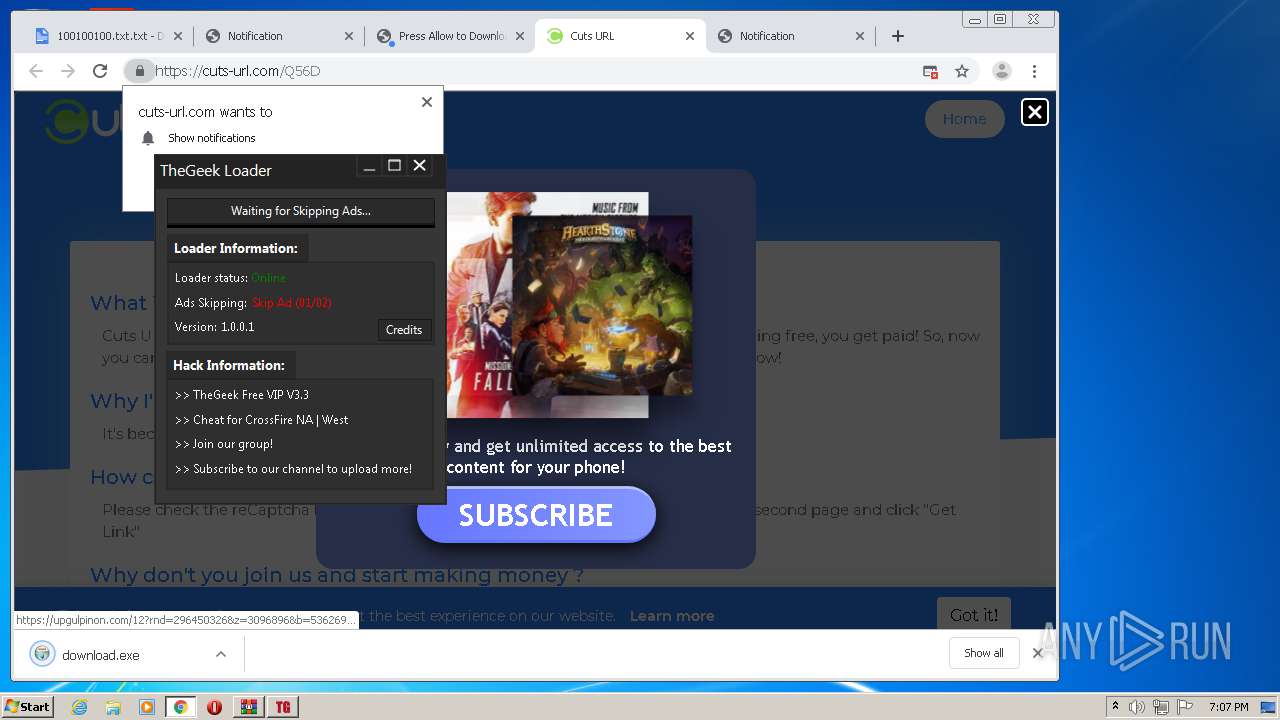
1540 | TheGeek Loader.exe | 204.12.192.242:80 | tgramo.guncheats.com | WholeSale Internet, Inc. | US | suspicious |
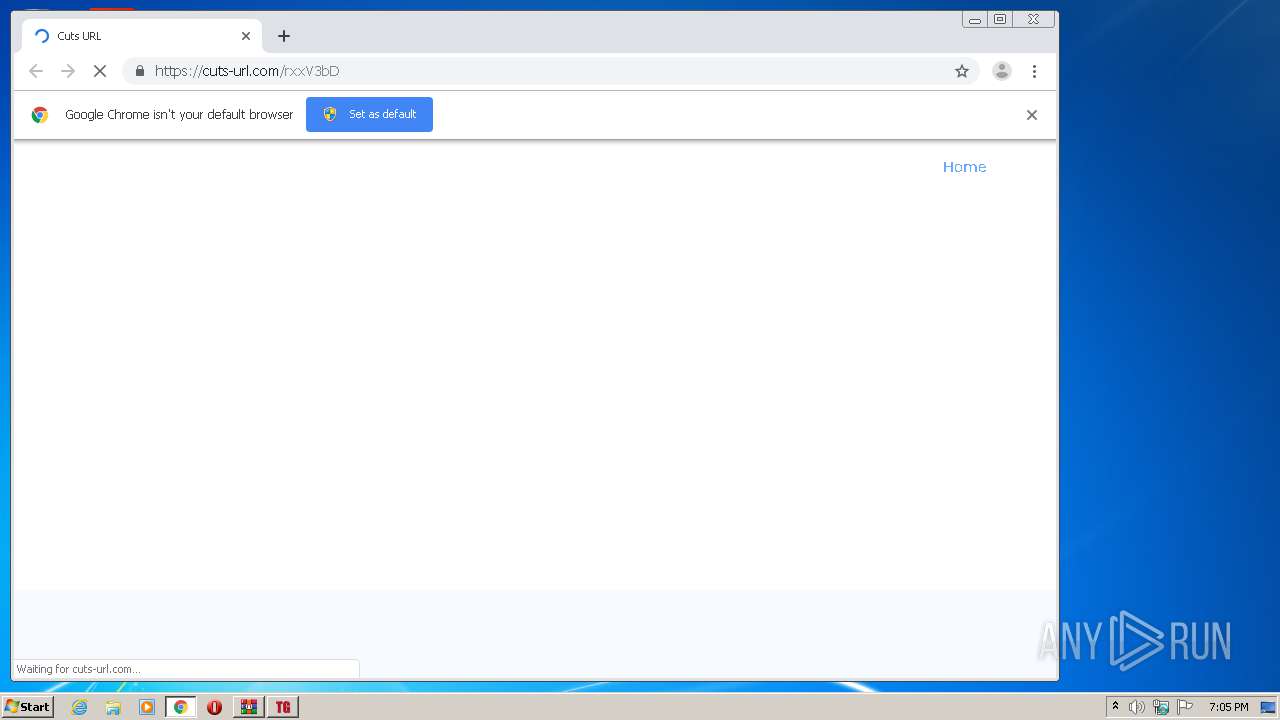
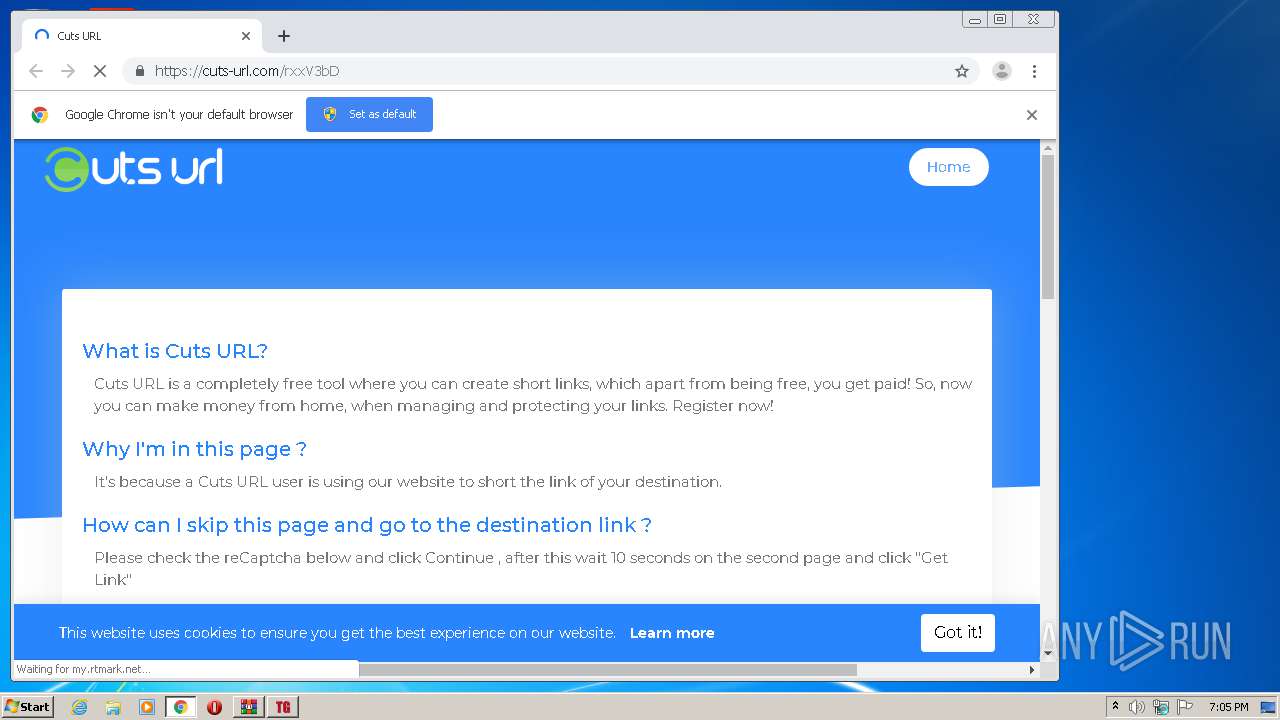
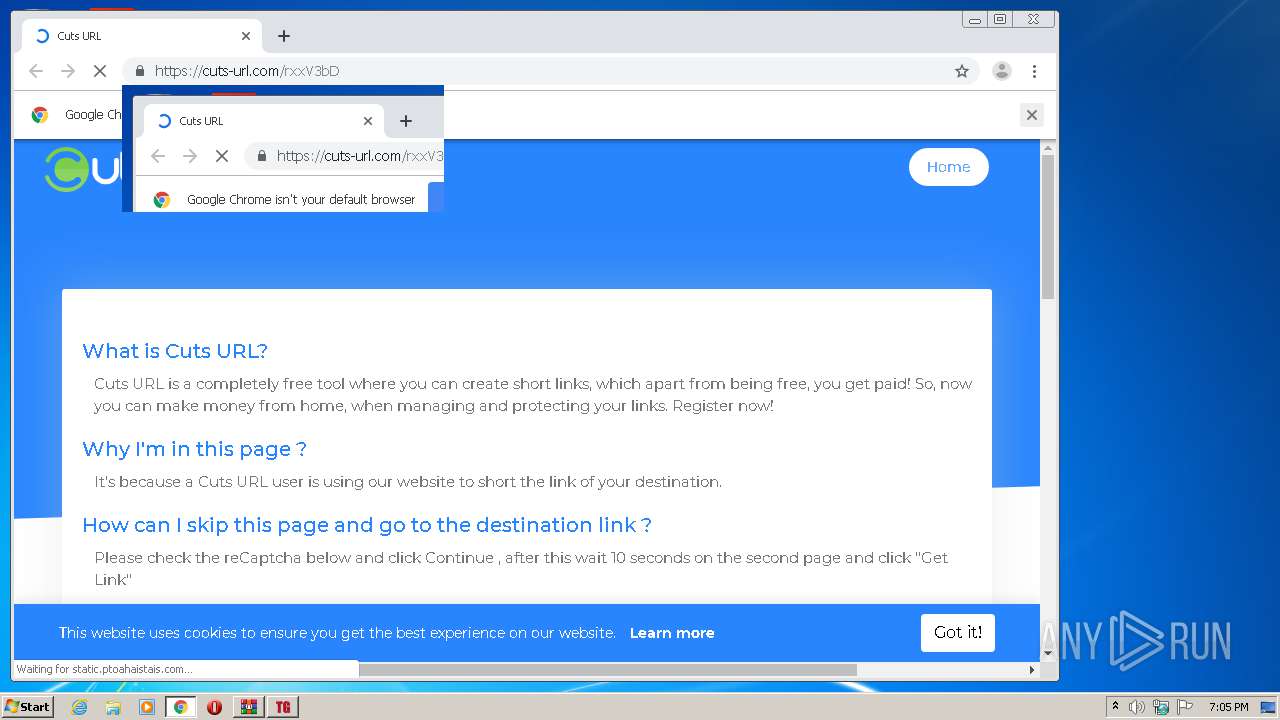
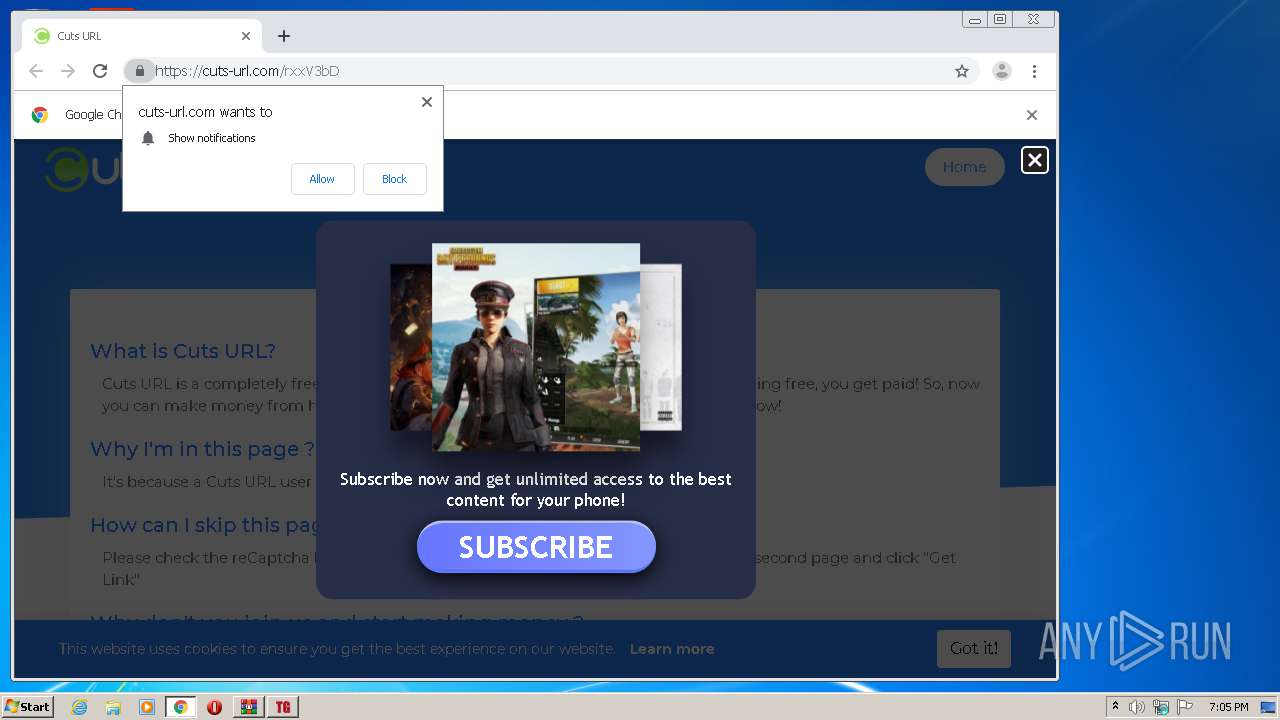
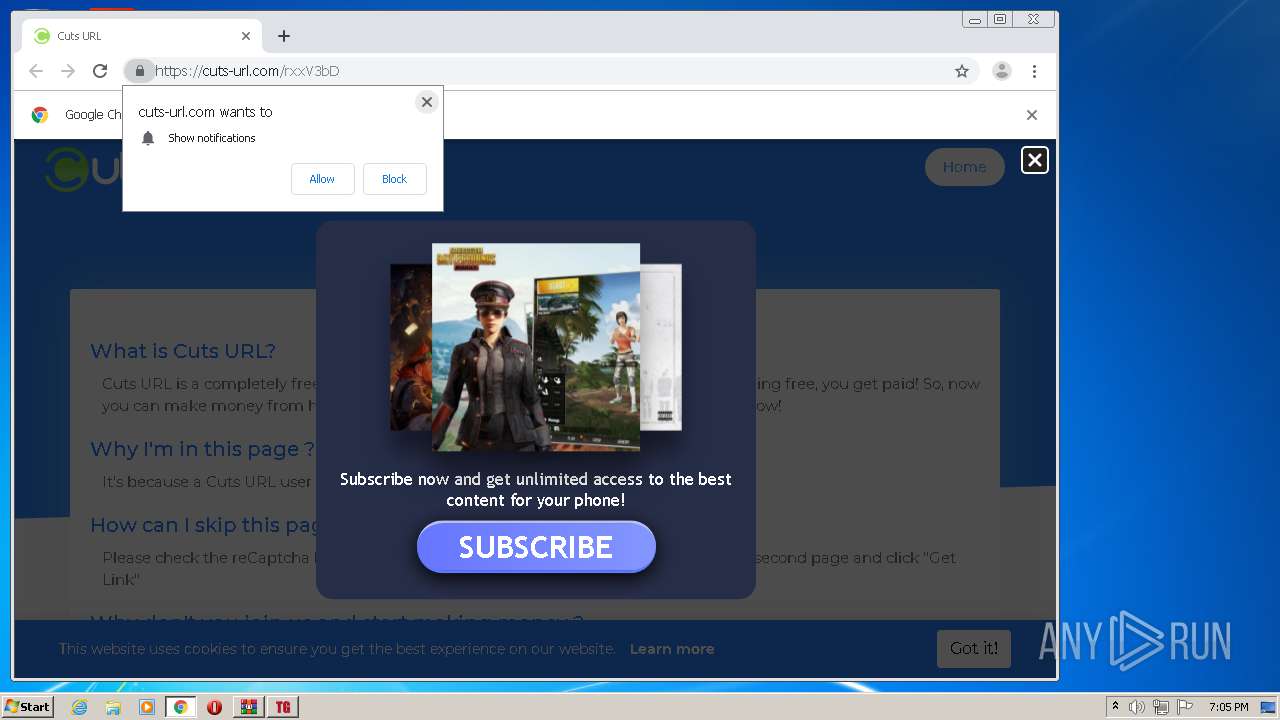
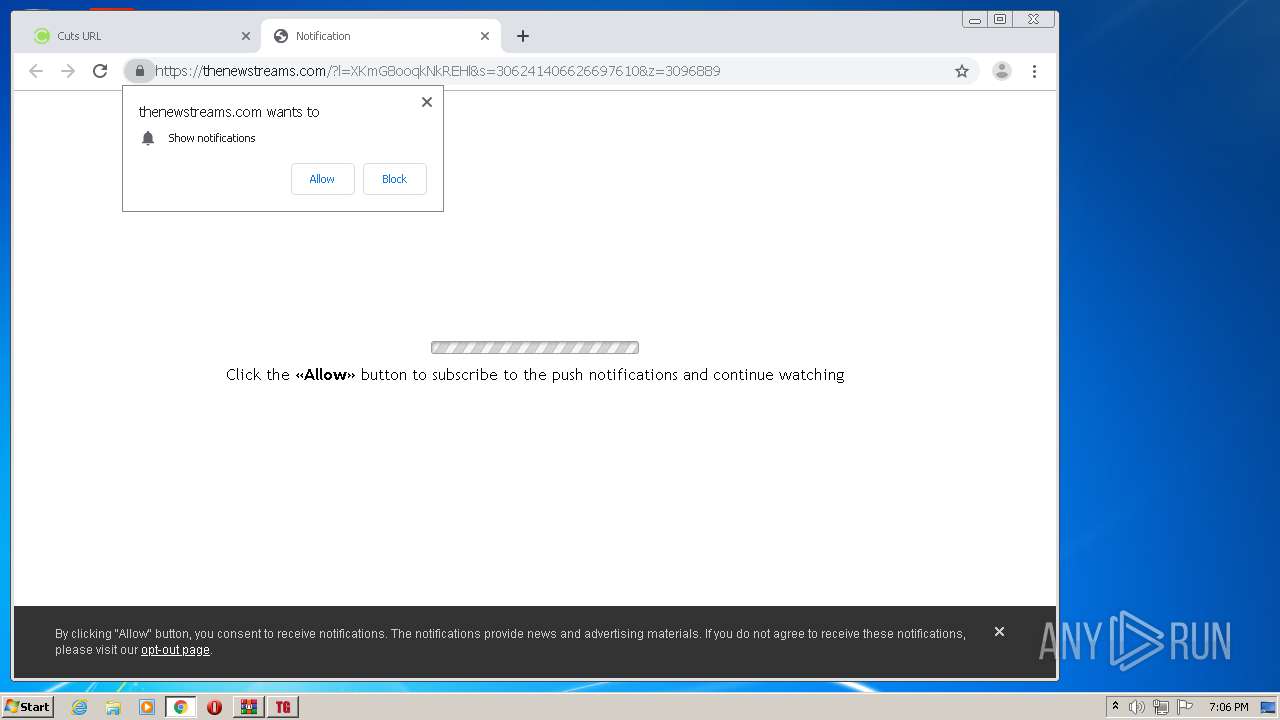
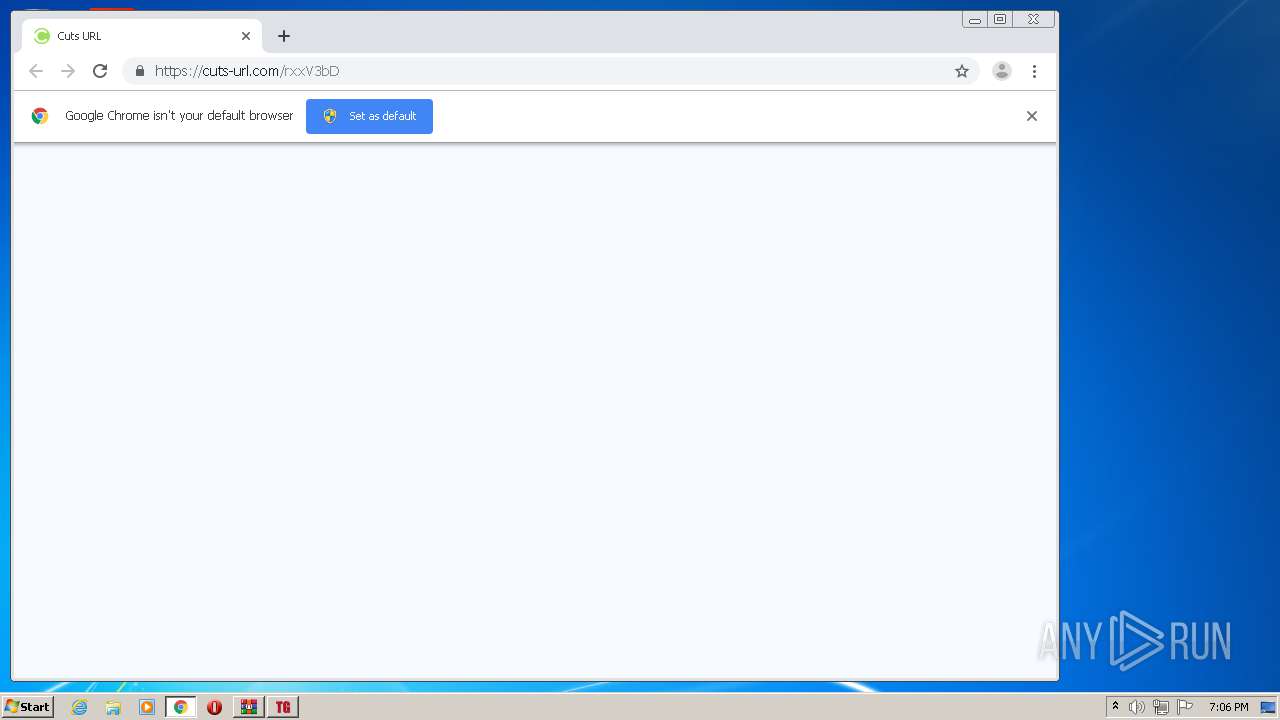
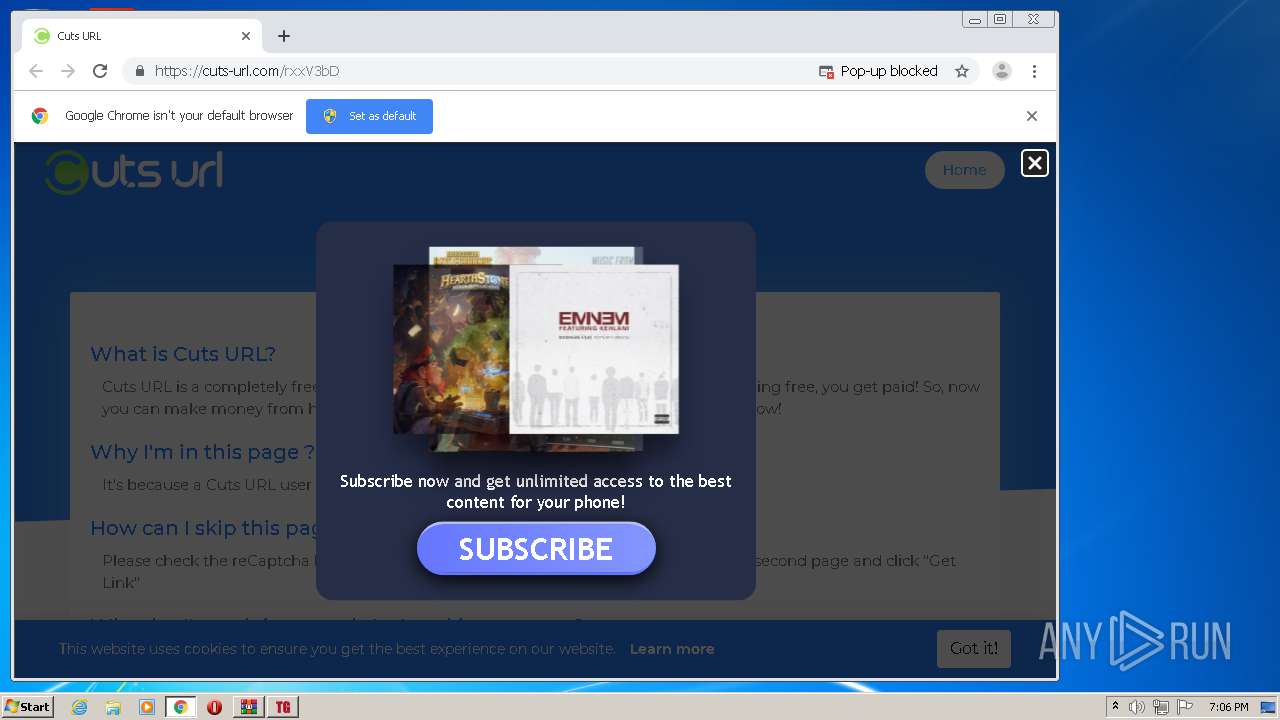
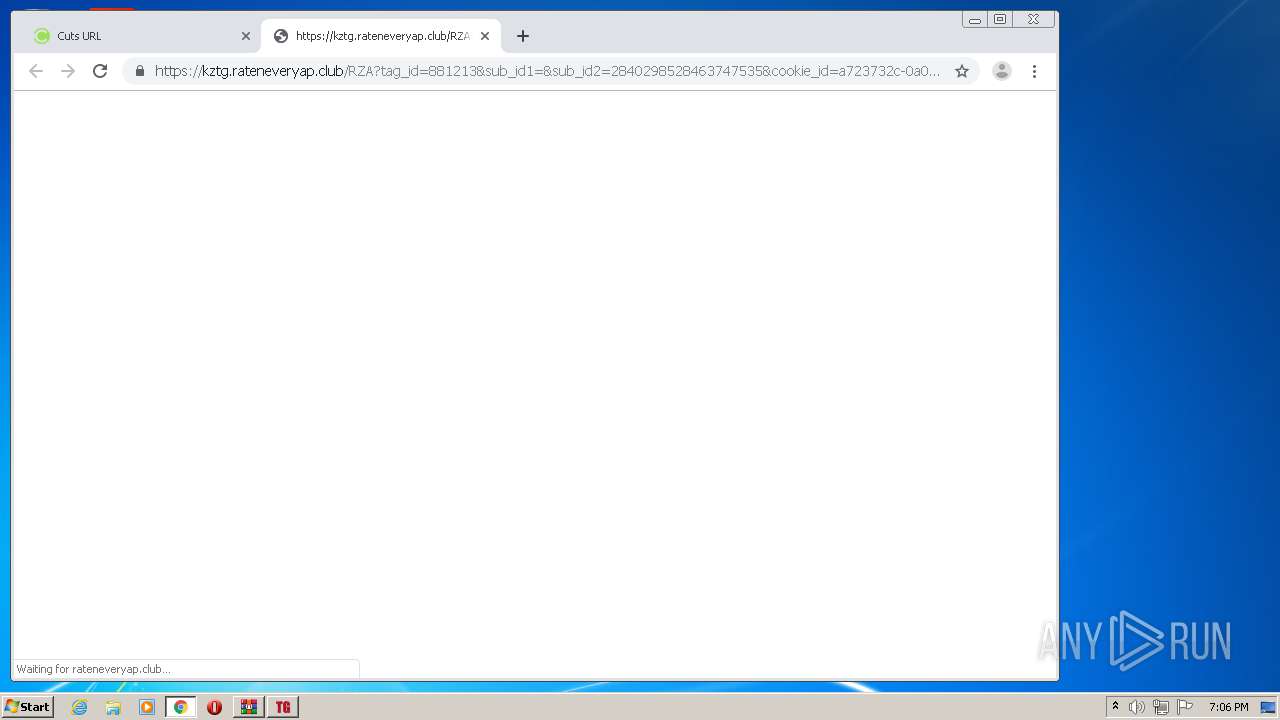
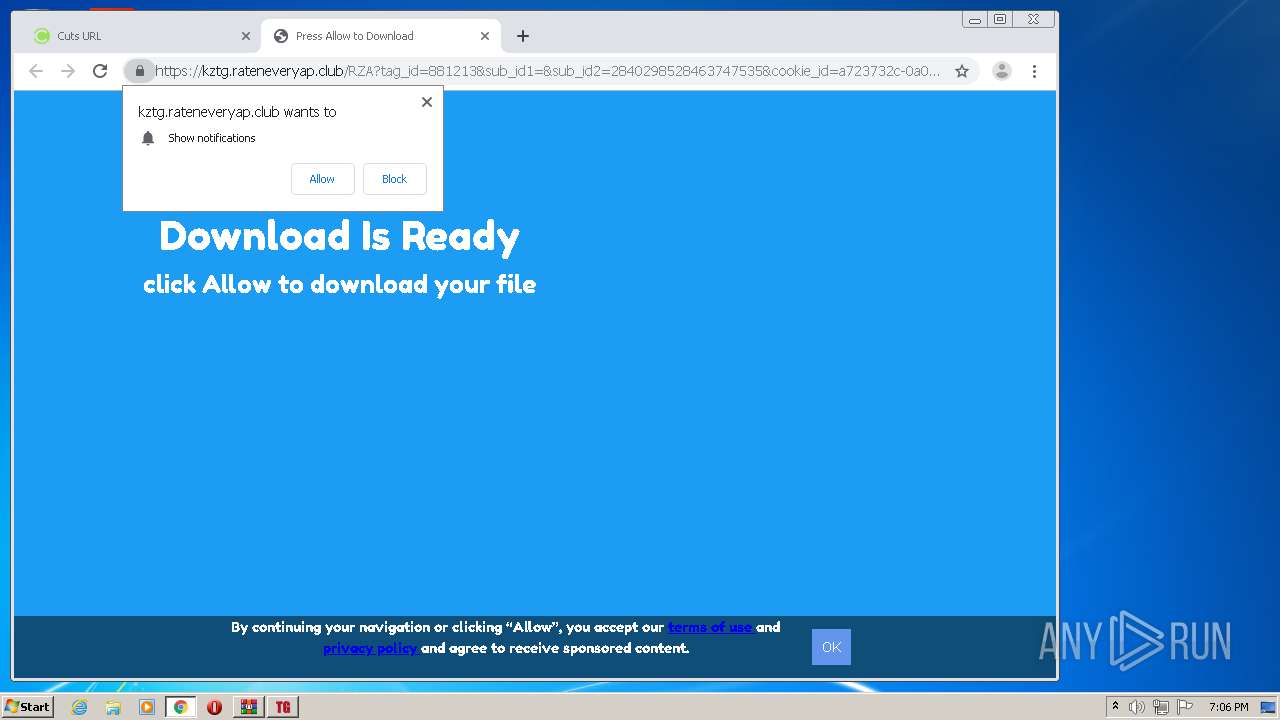
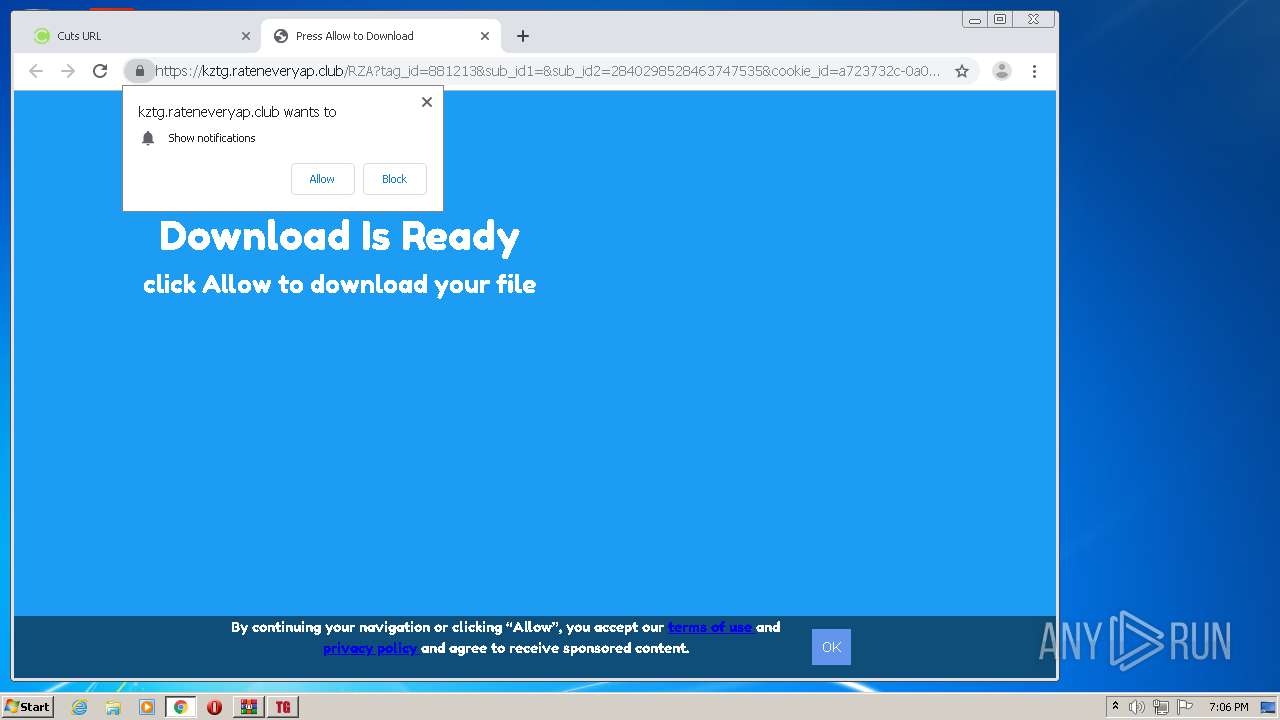
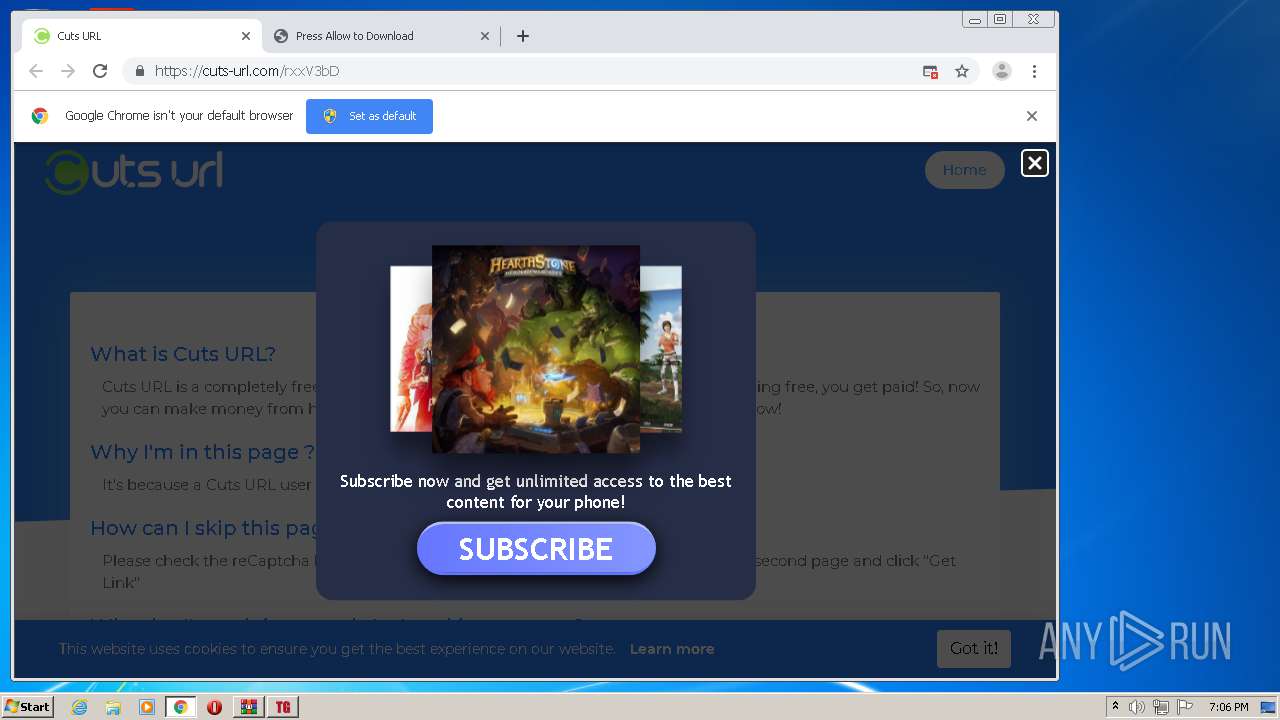
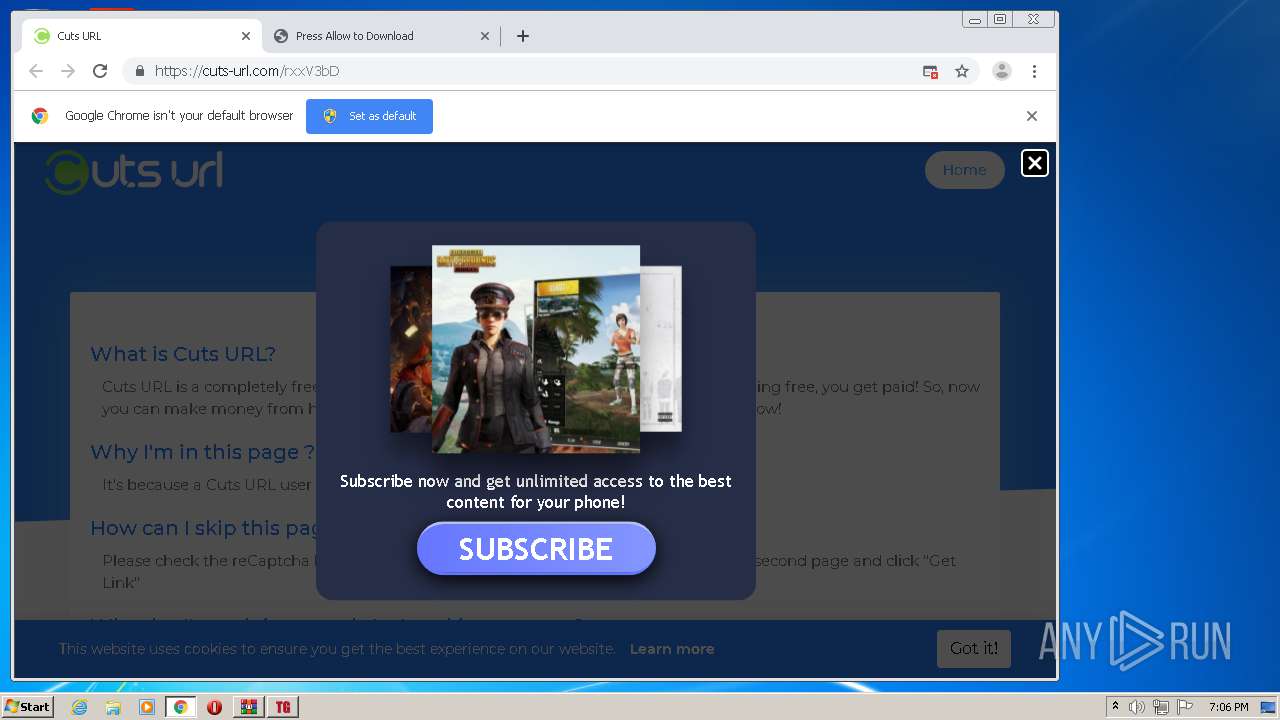
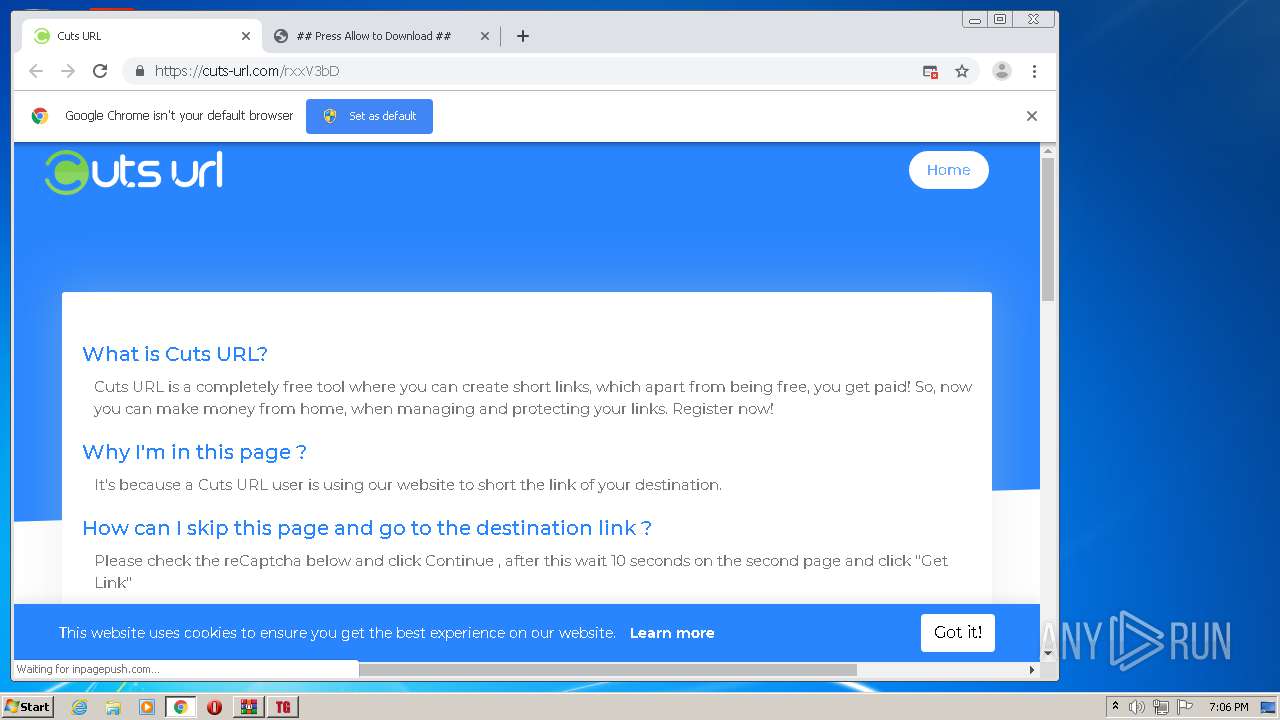
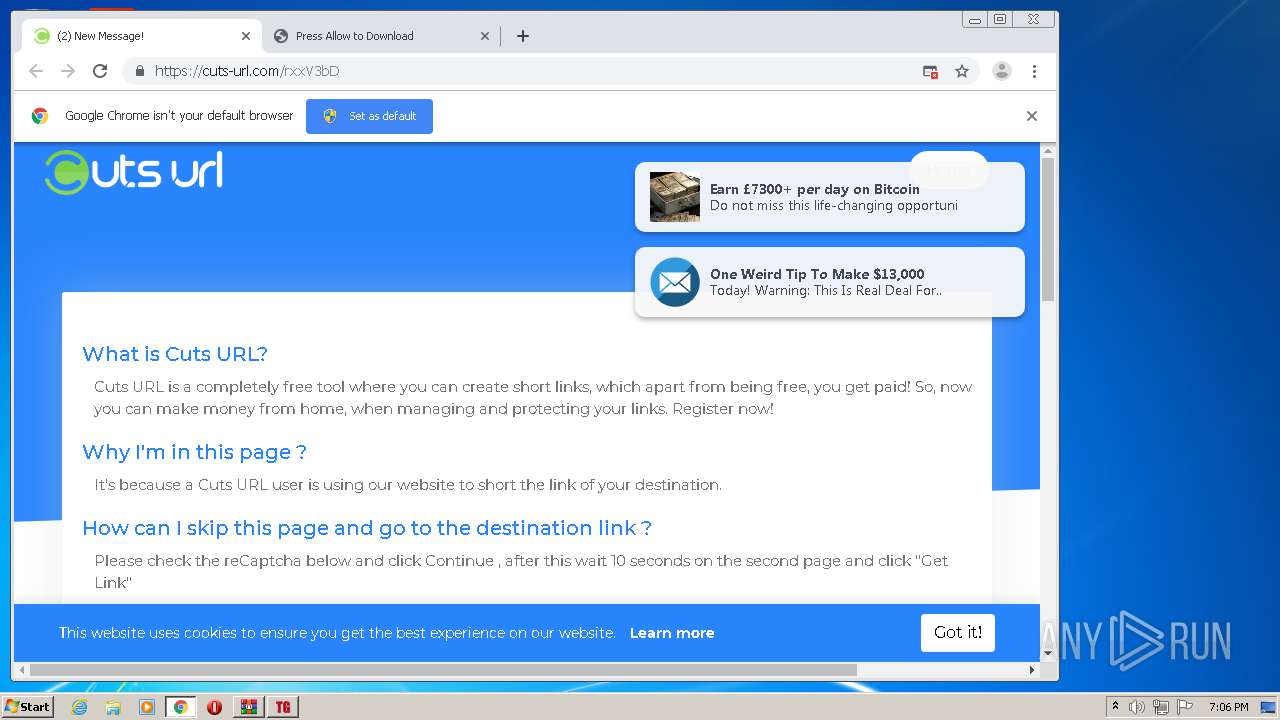
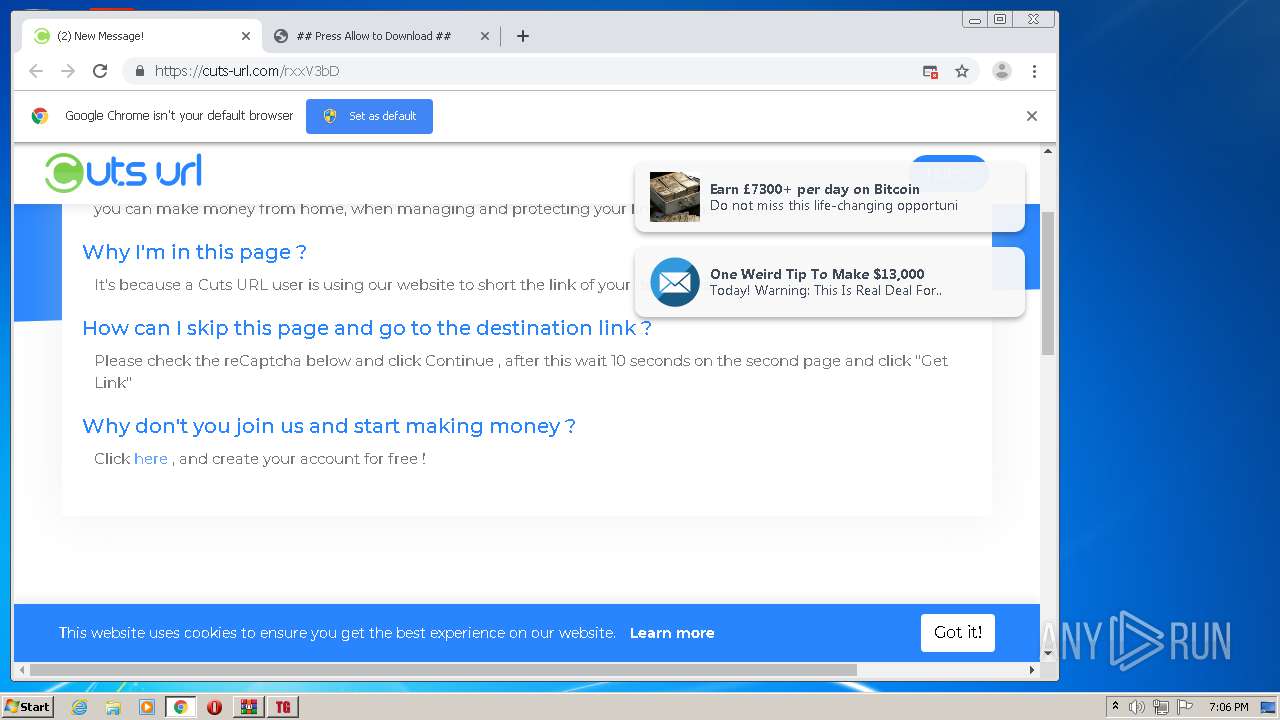
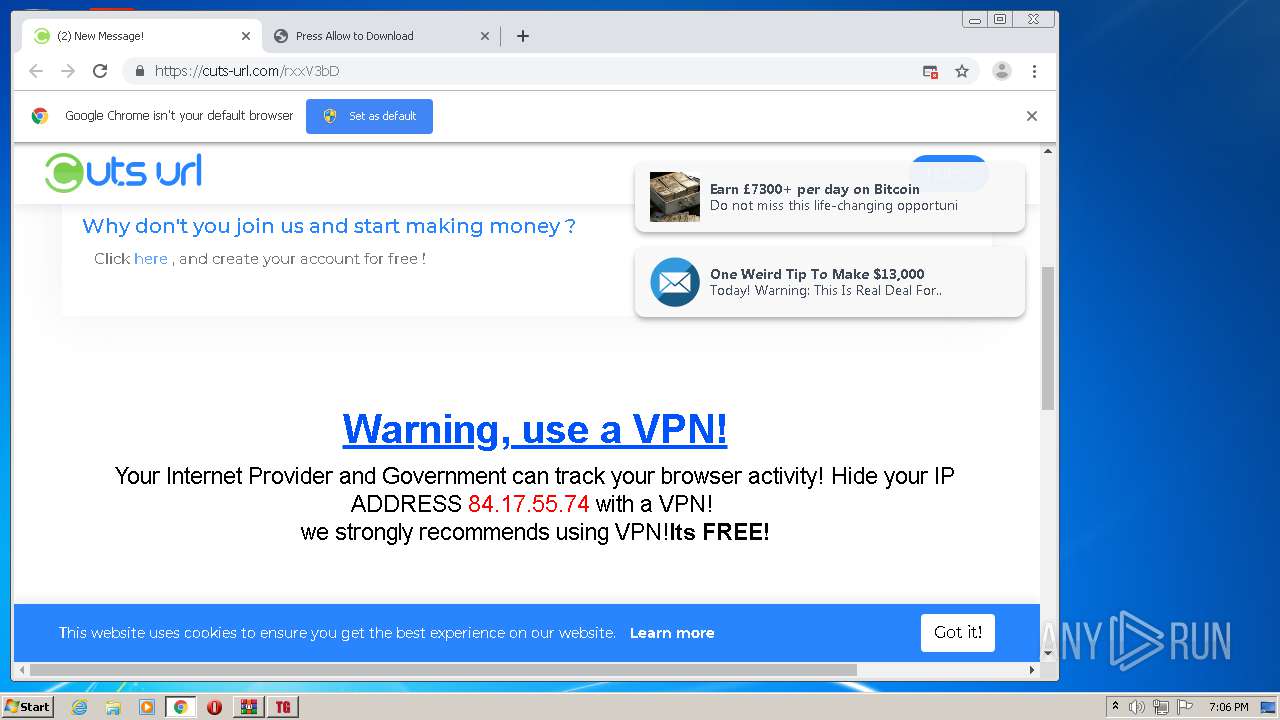
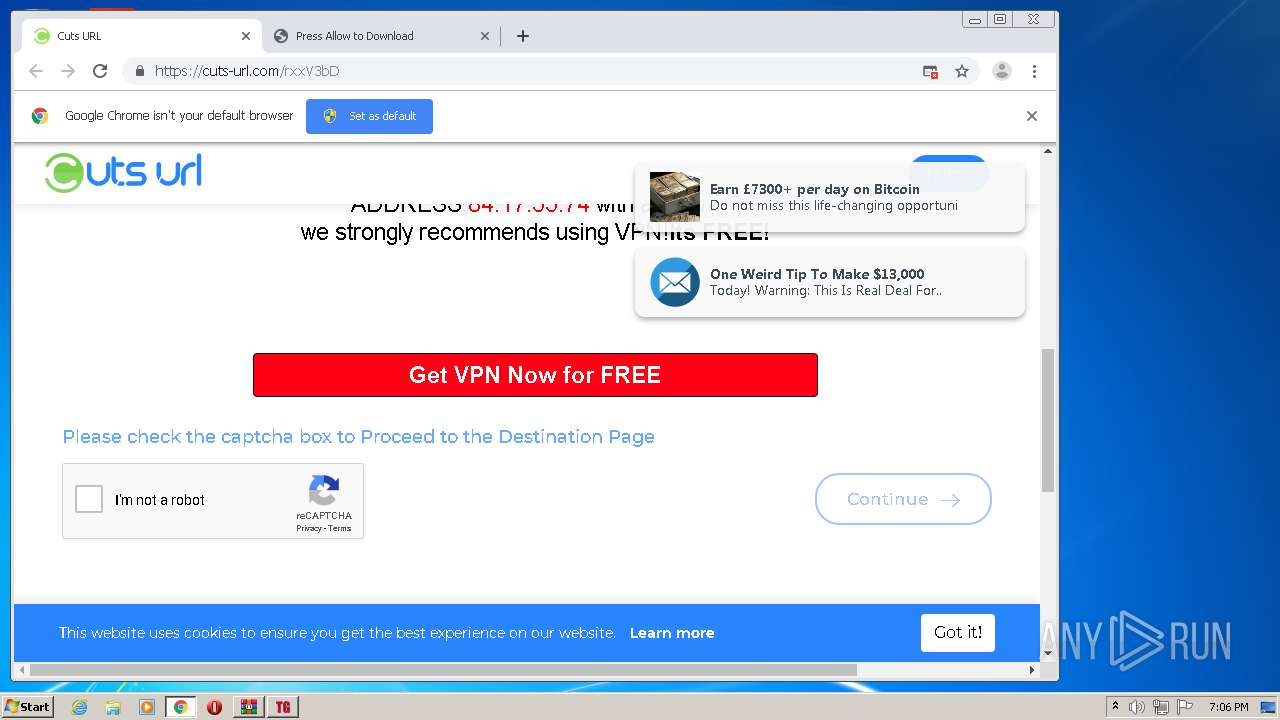
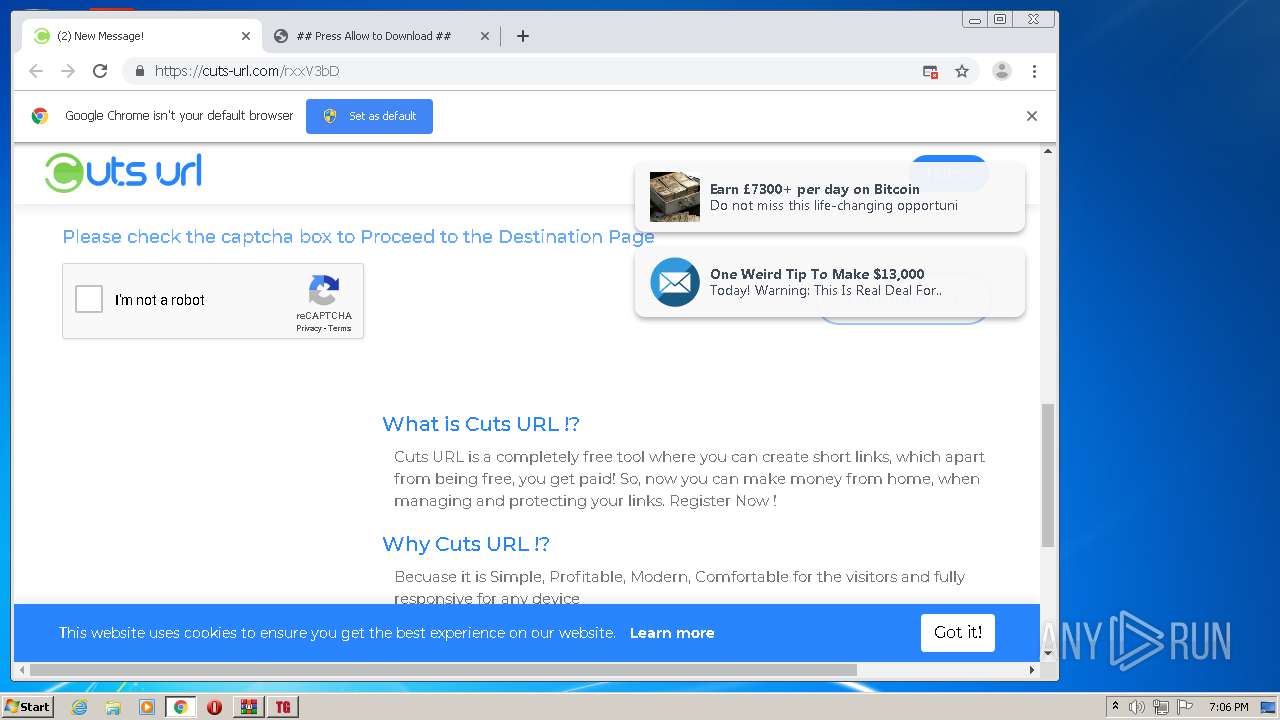
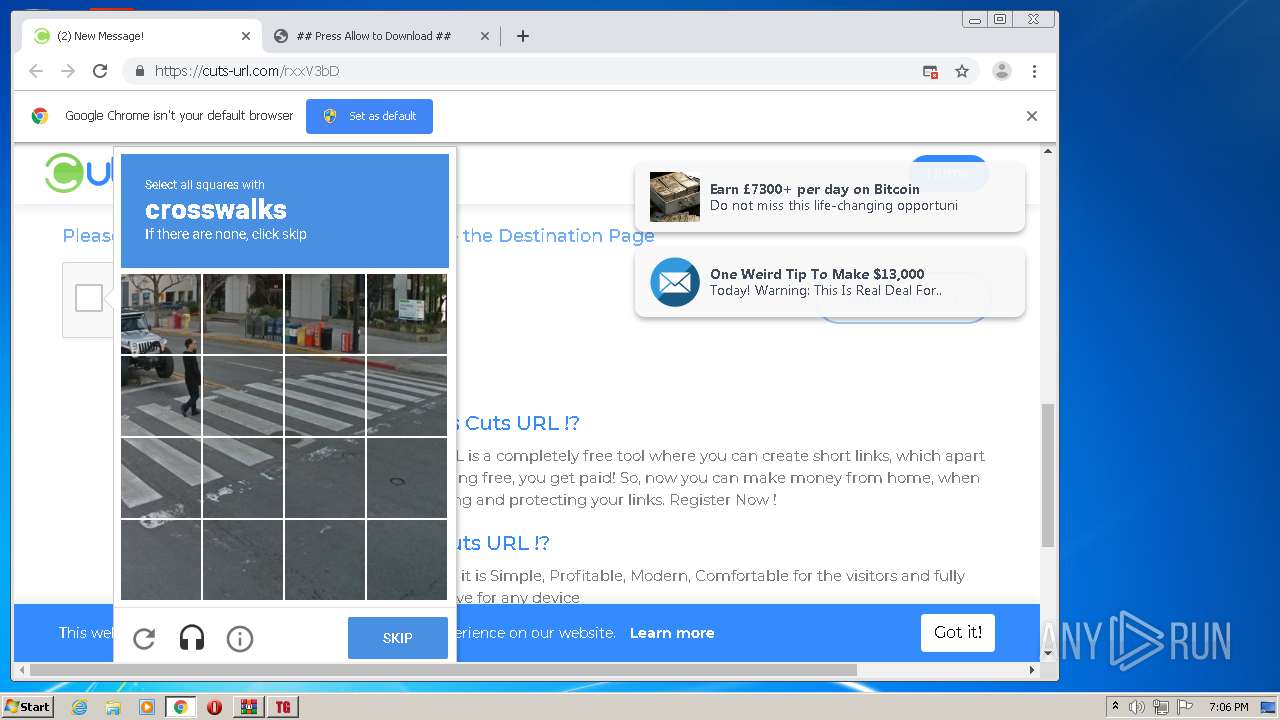
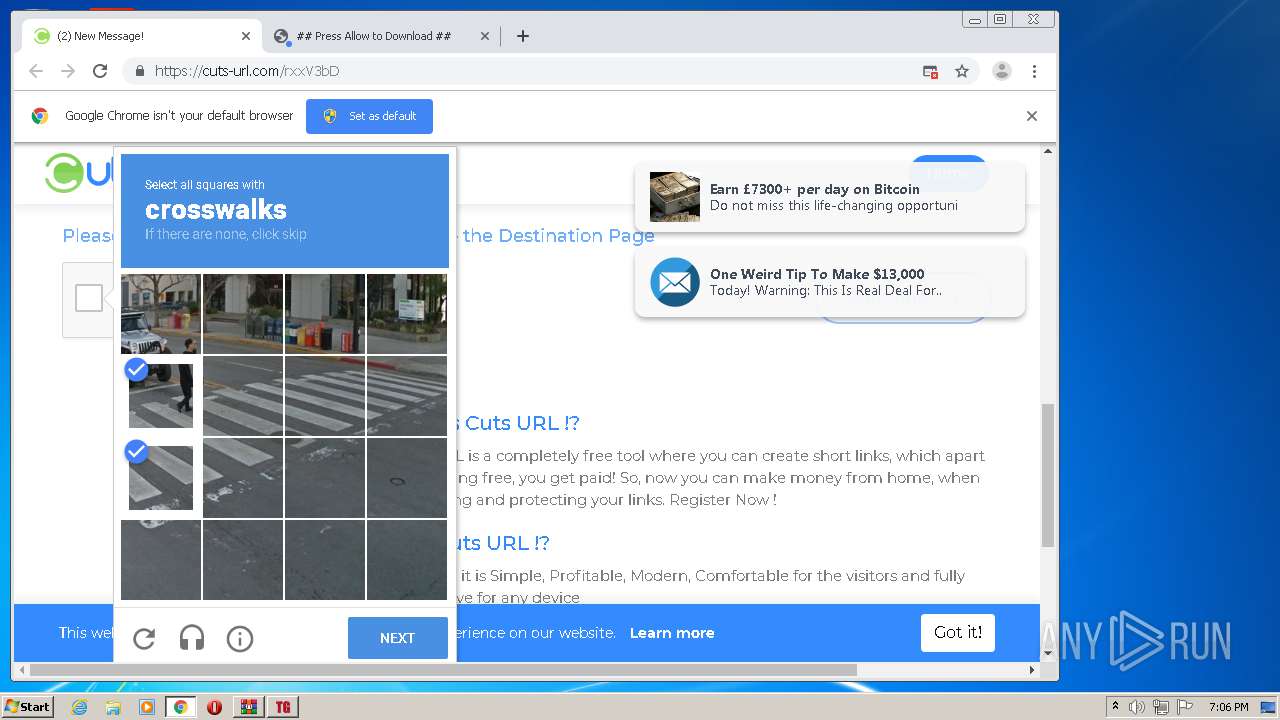
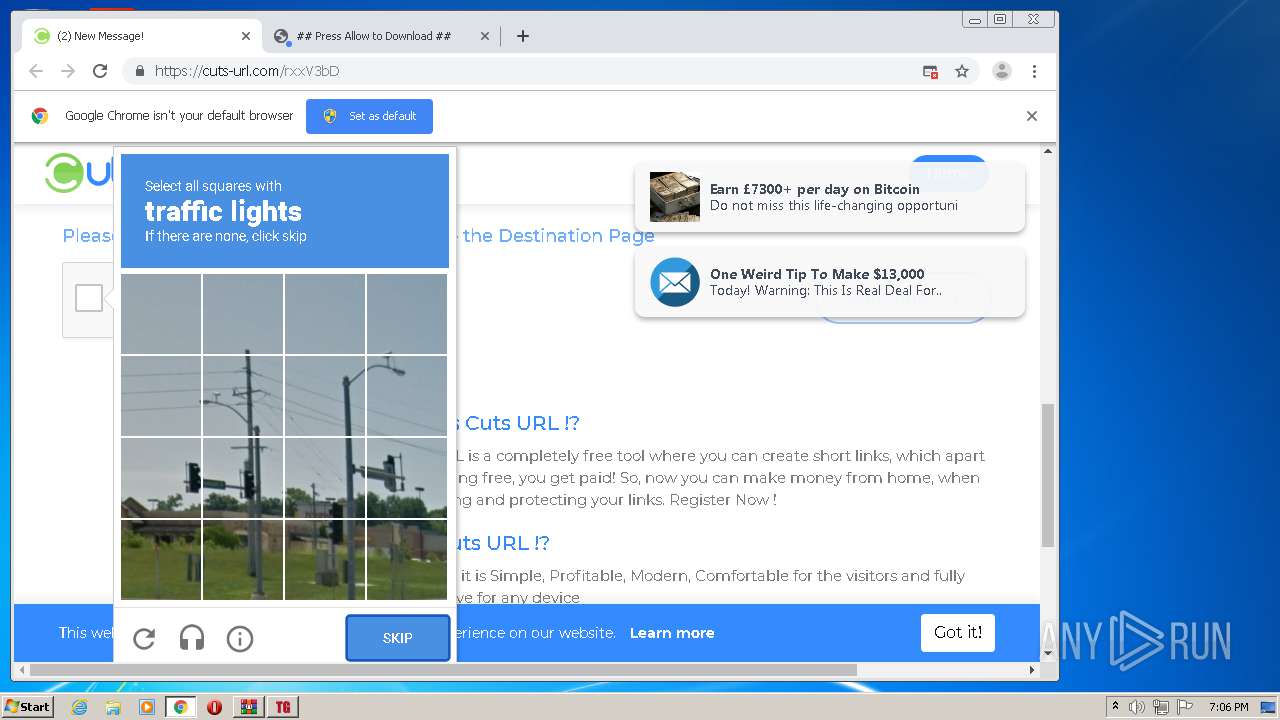
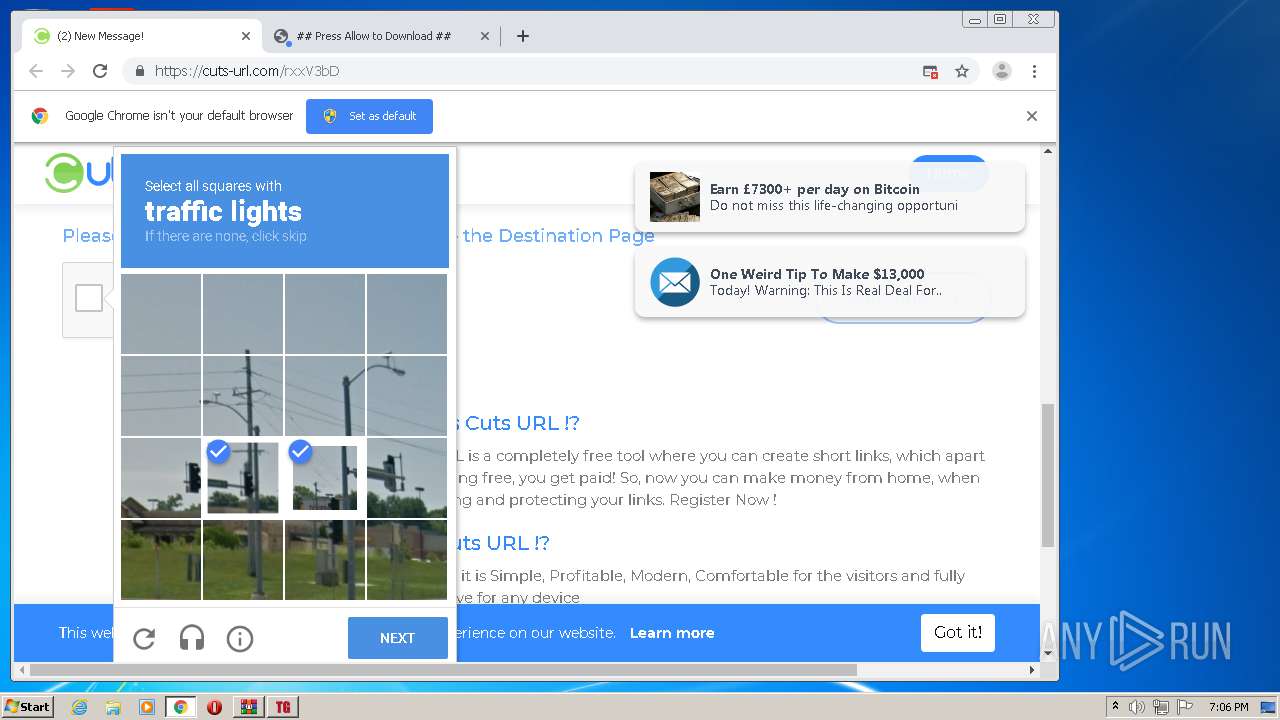
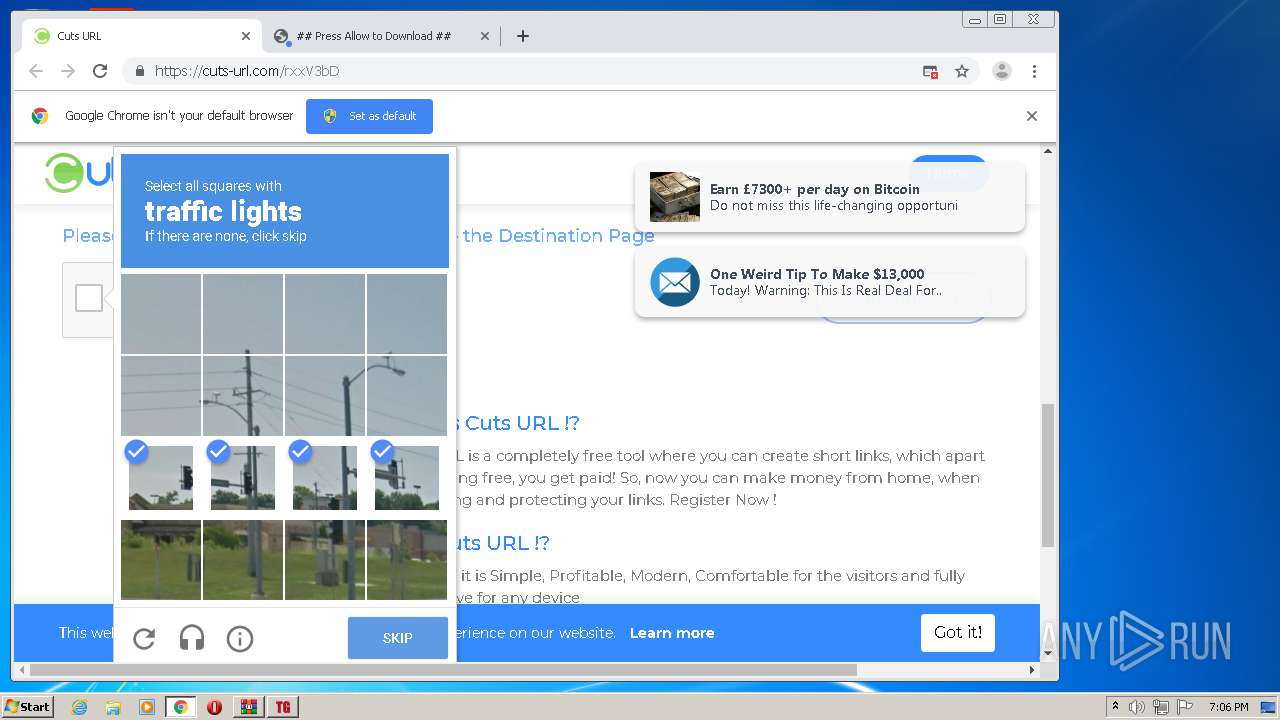
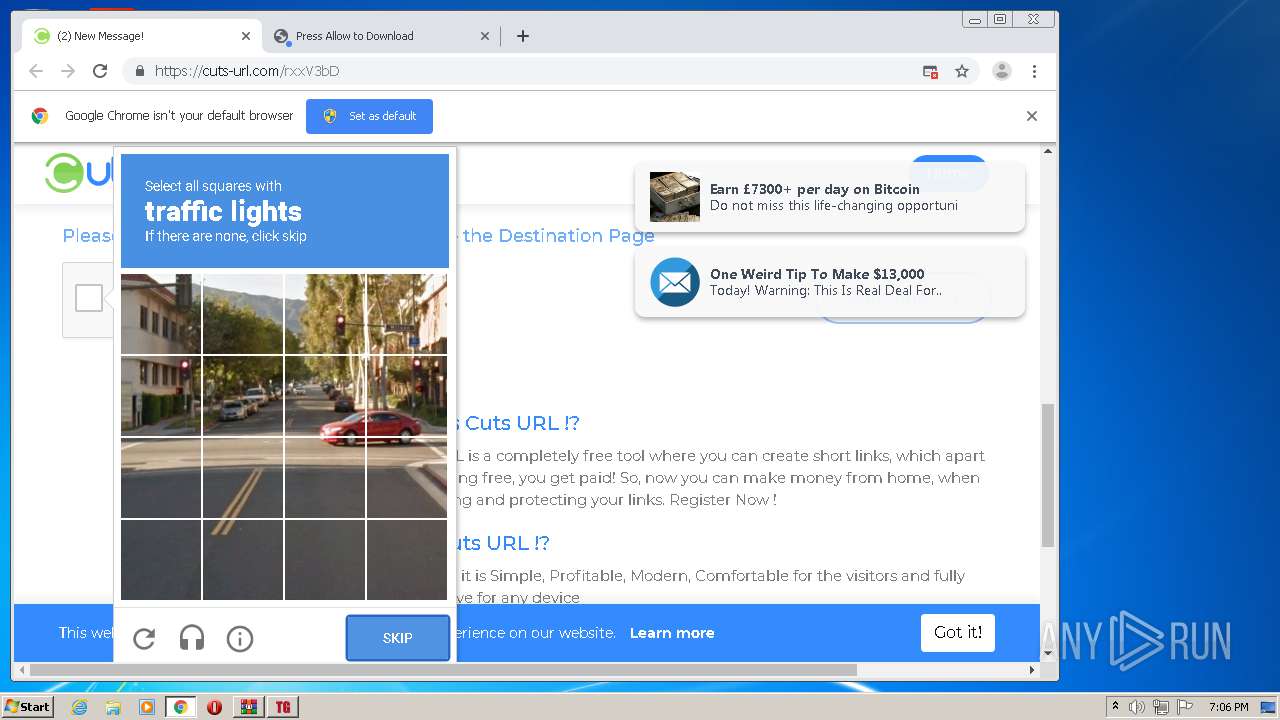
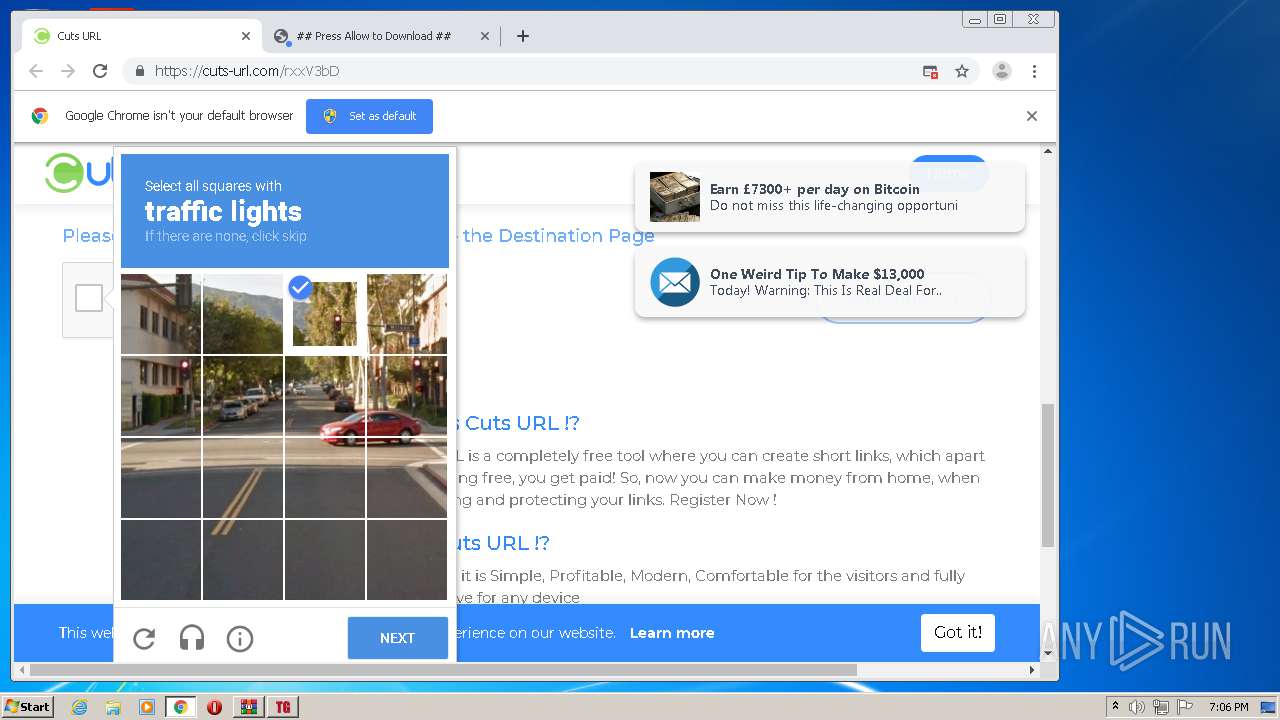
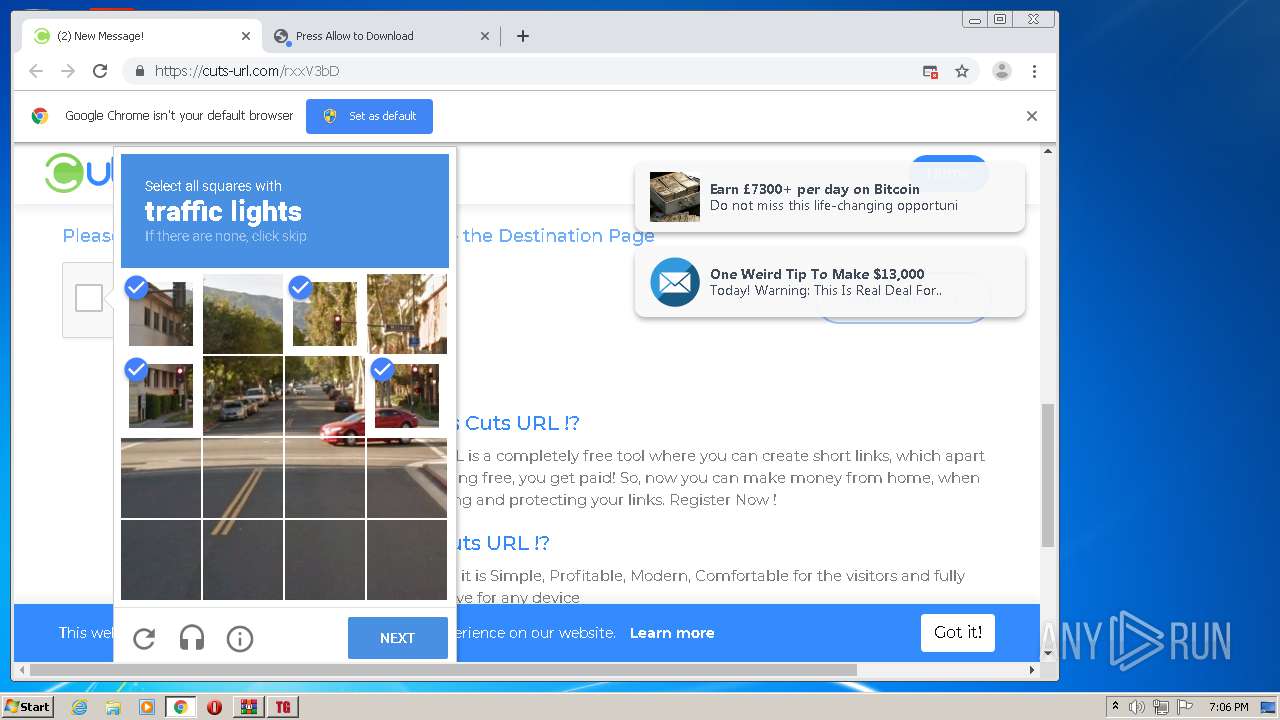
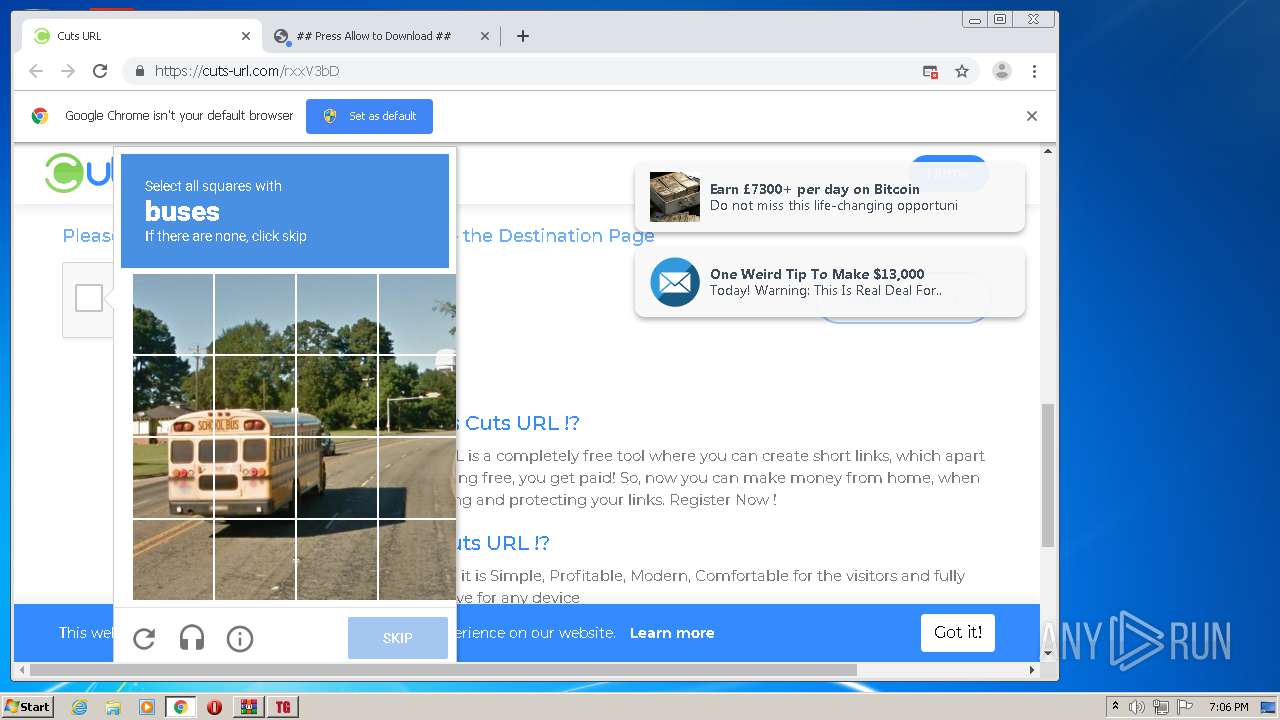
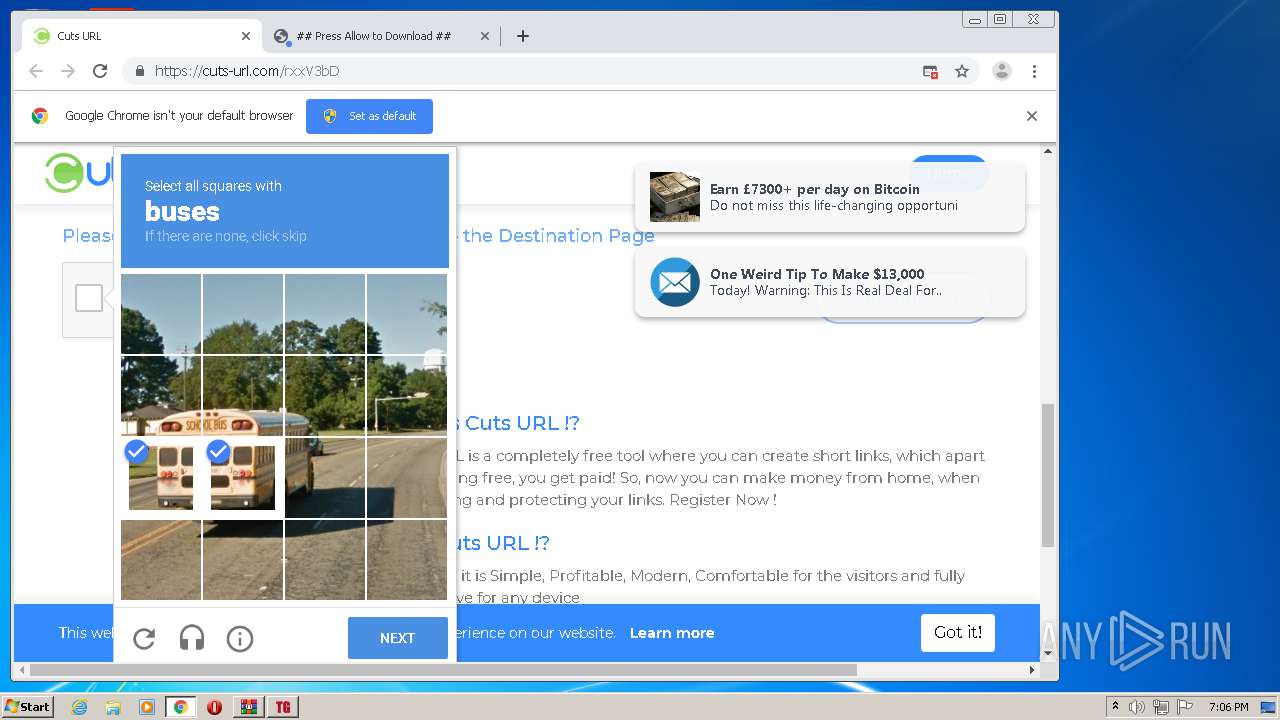
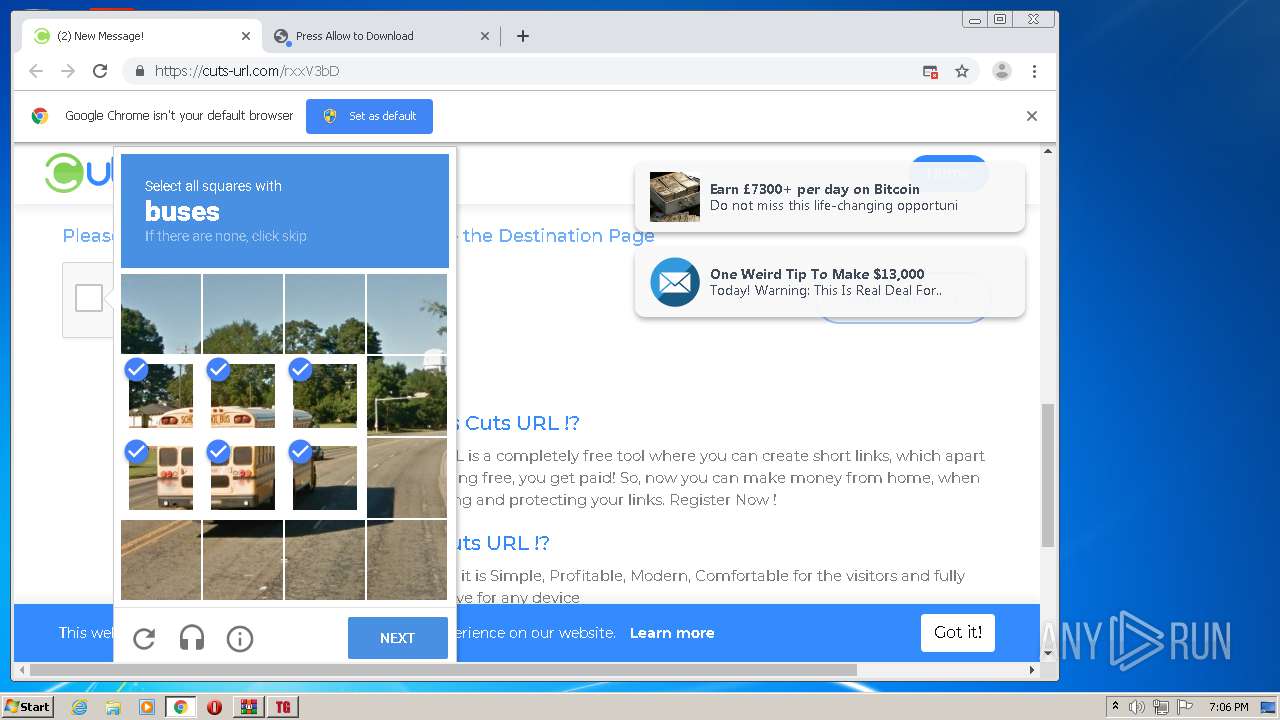
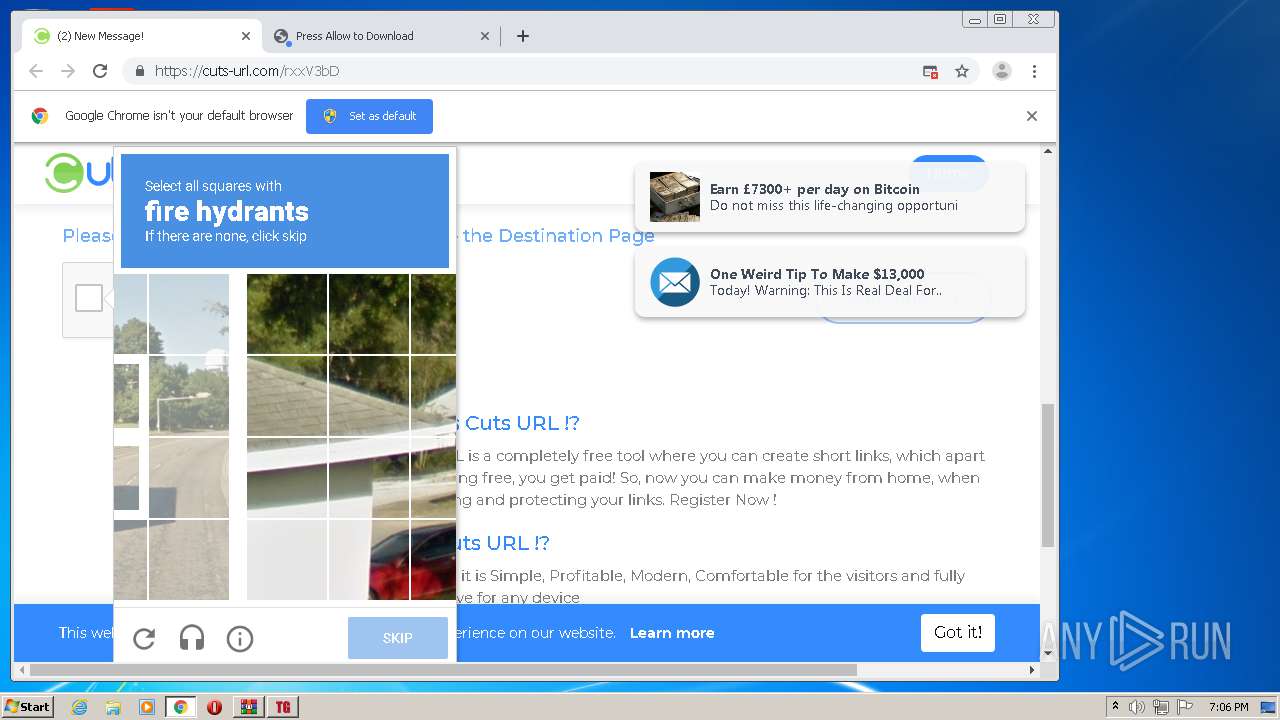
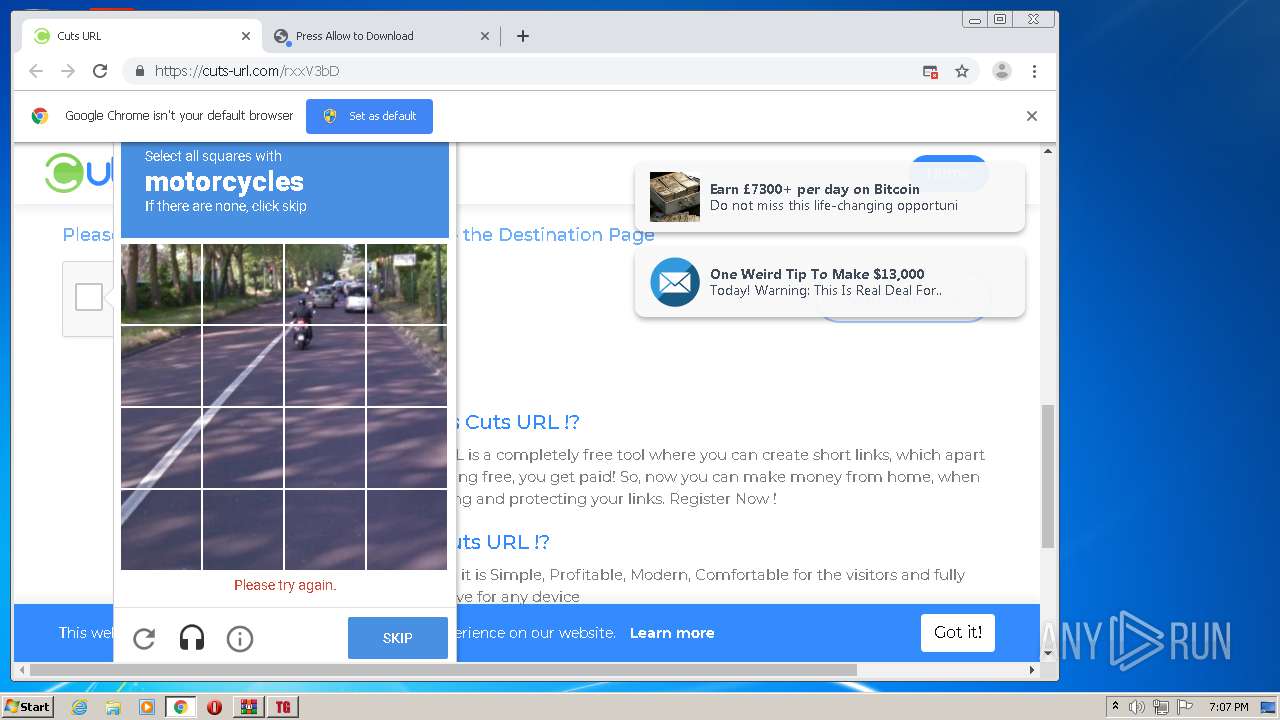
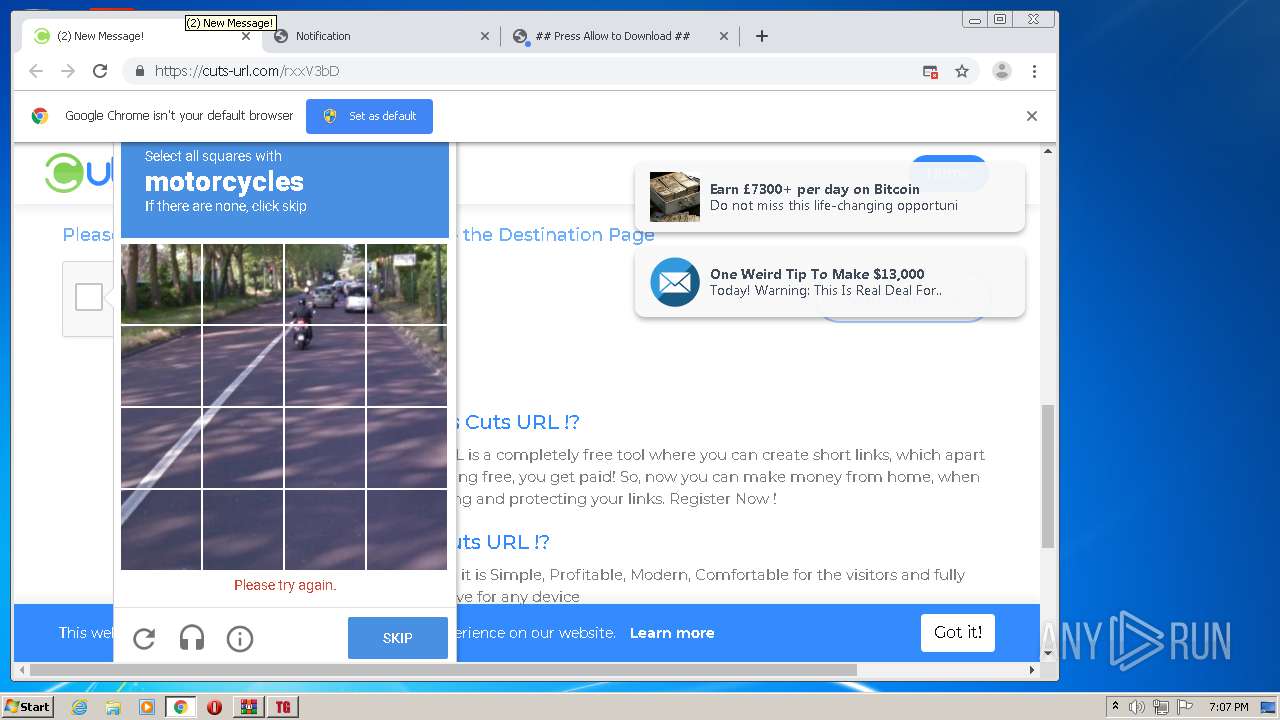
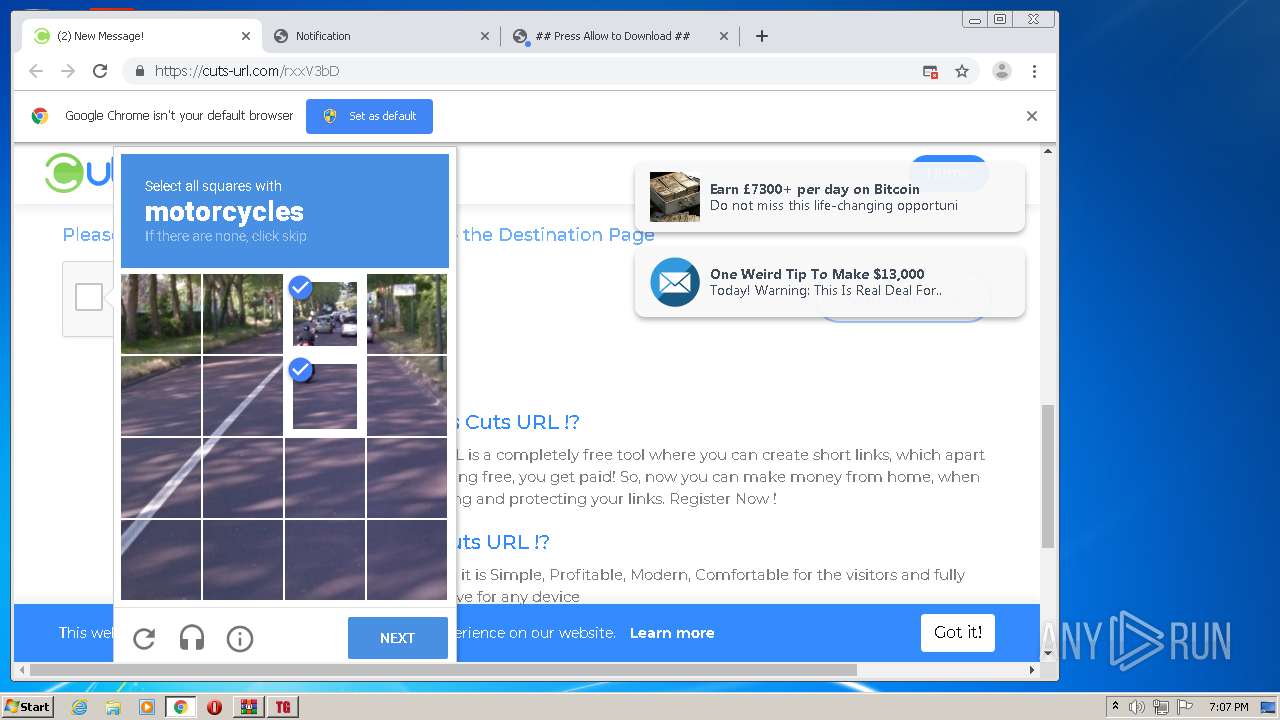
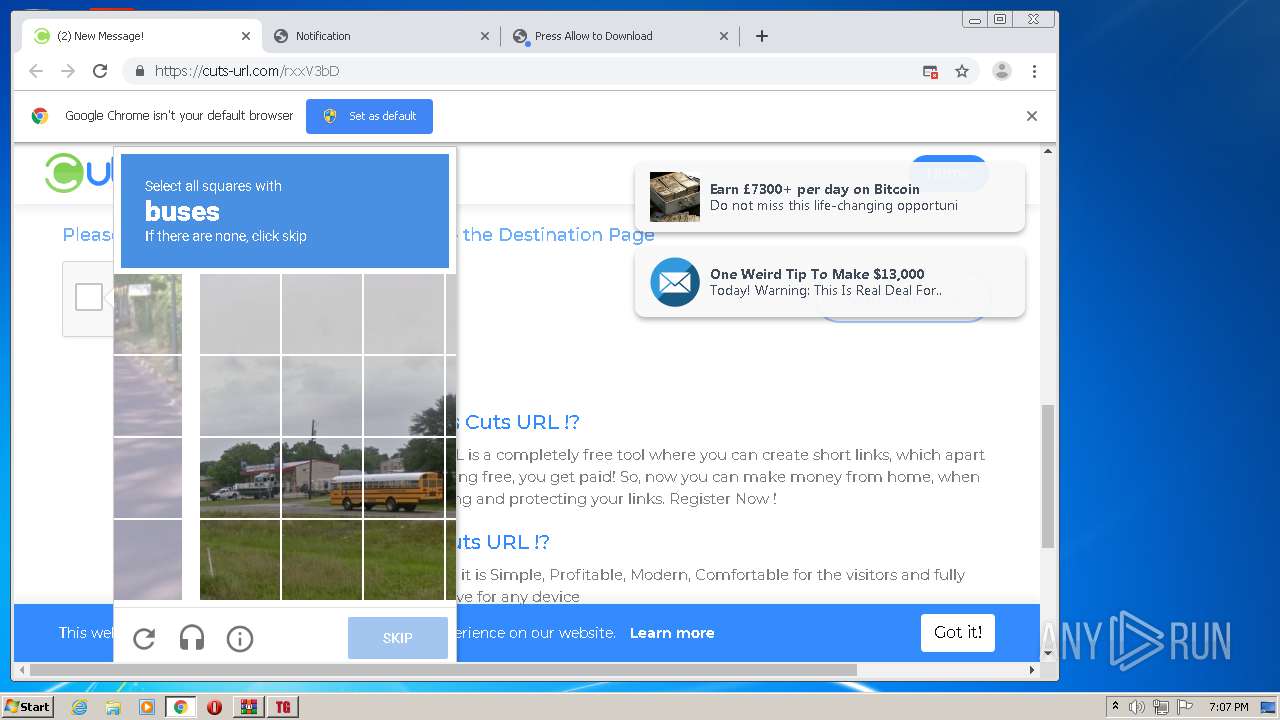
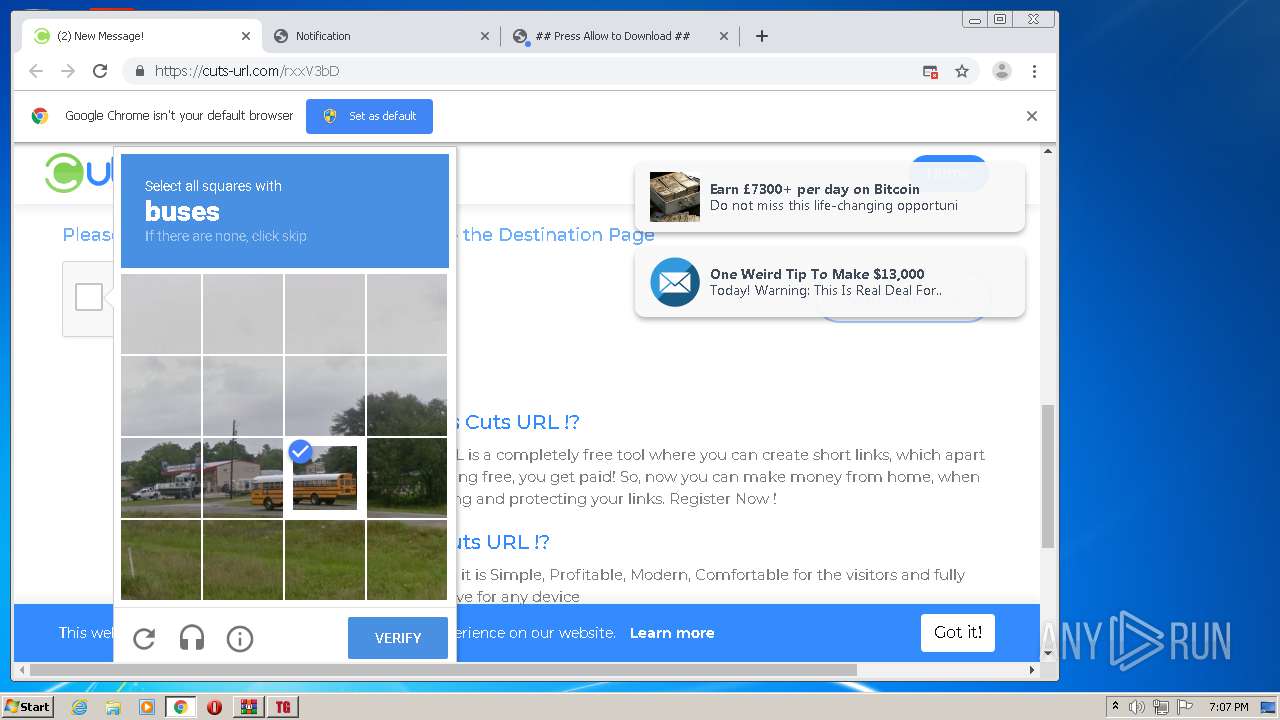
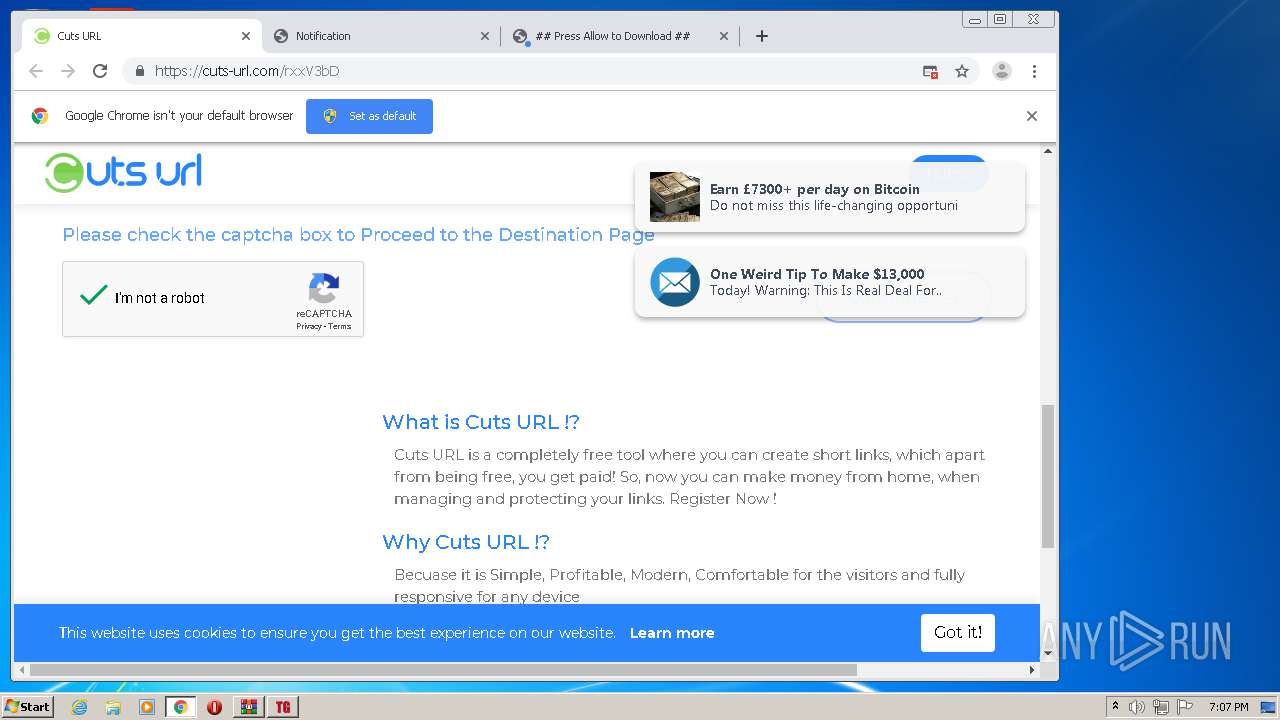
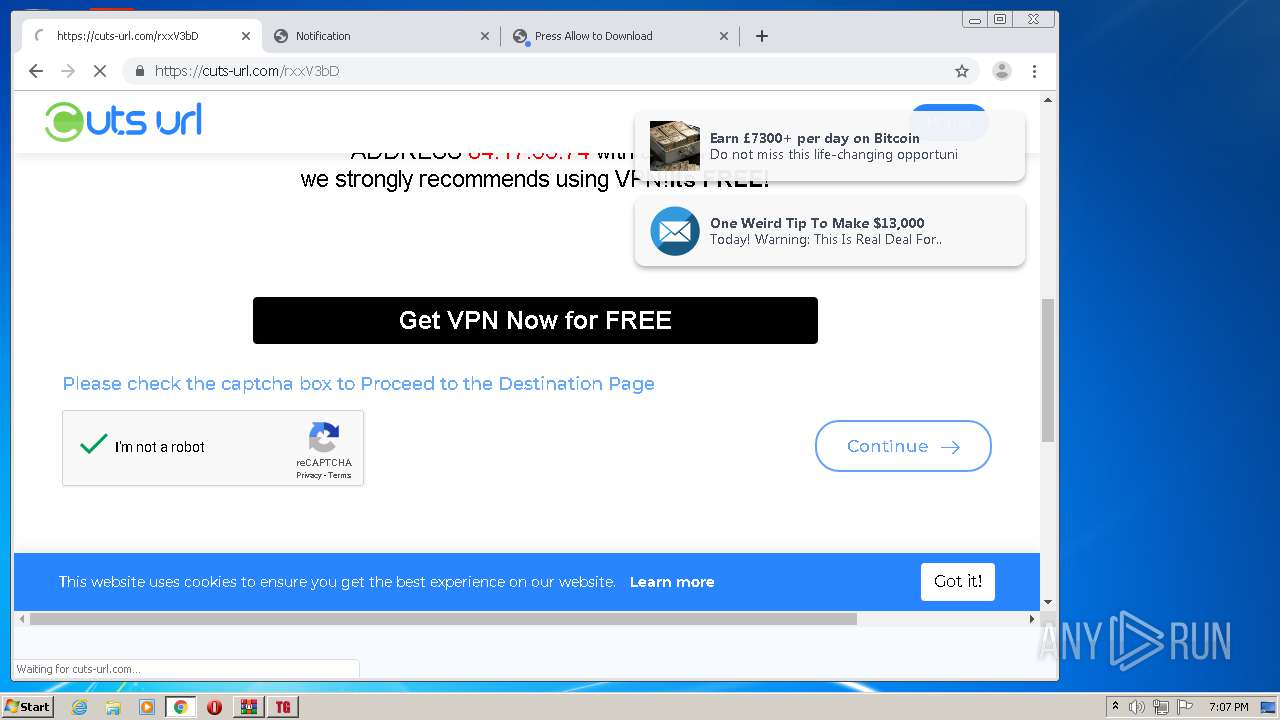
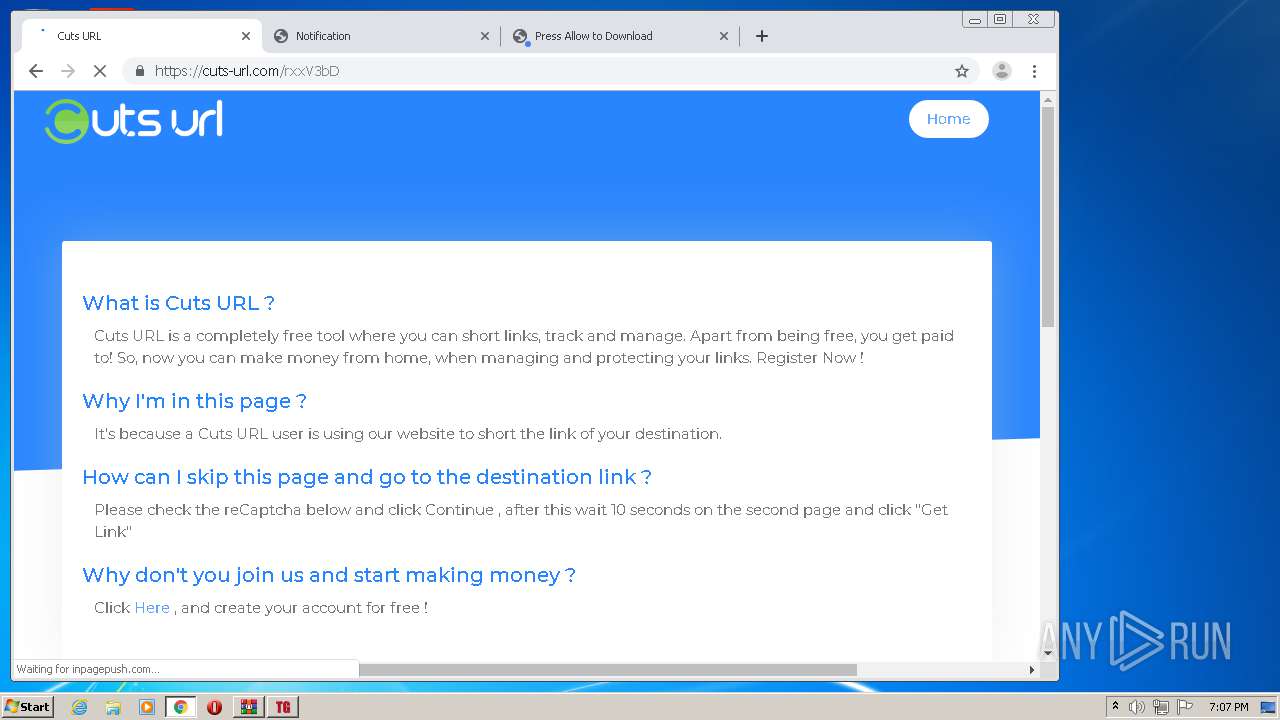
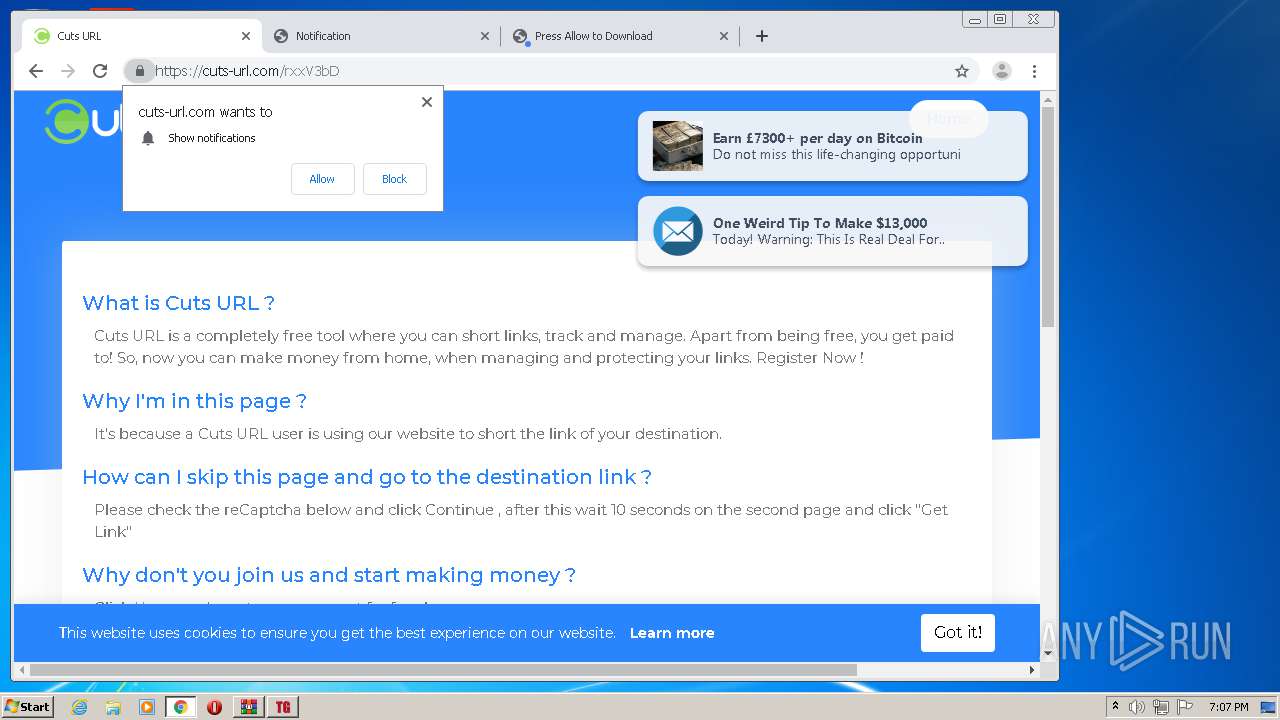
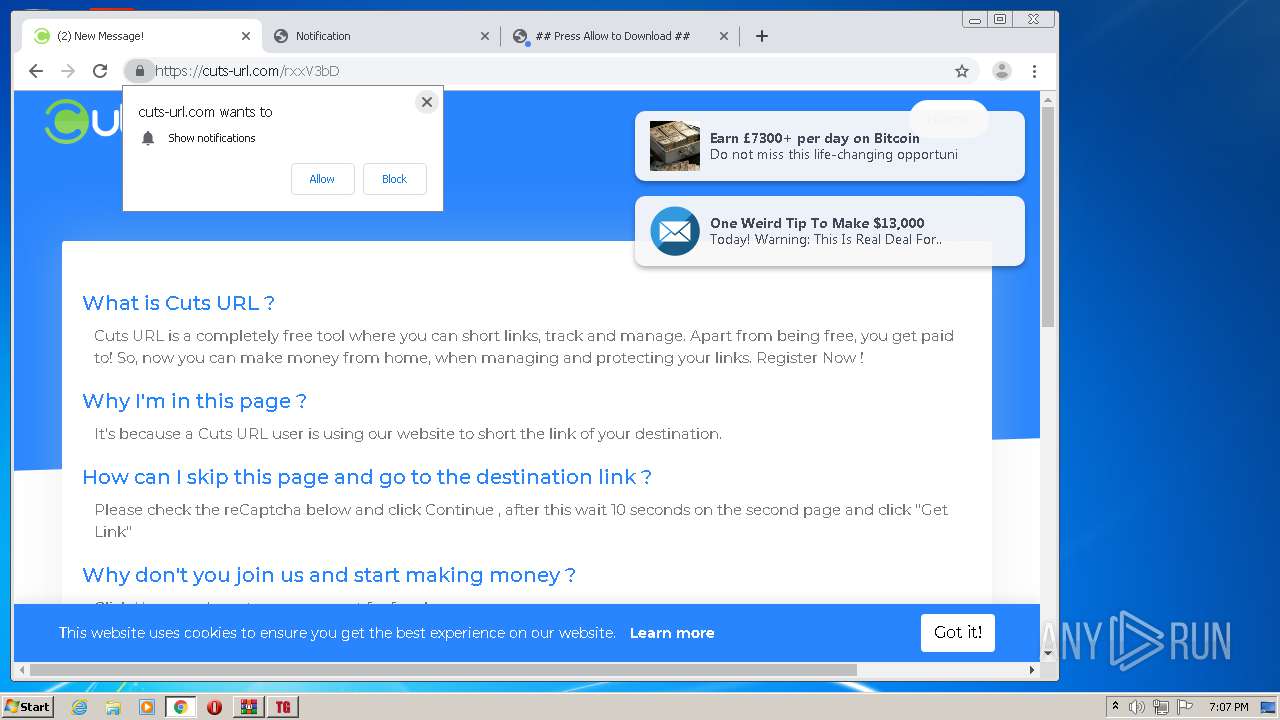
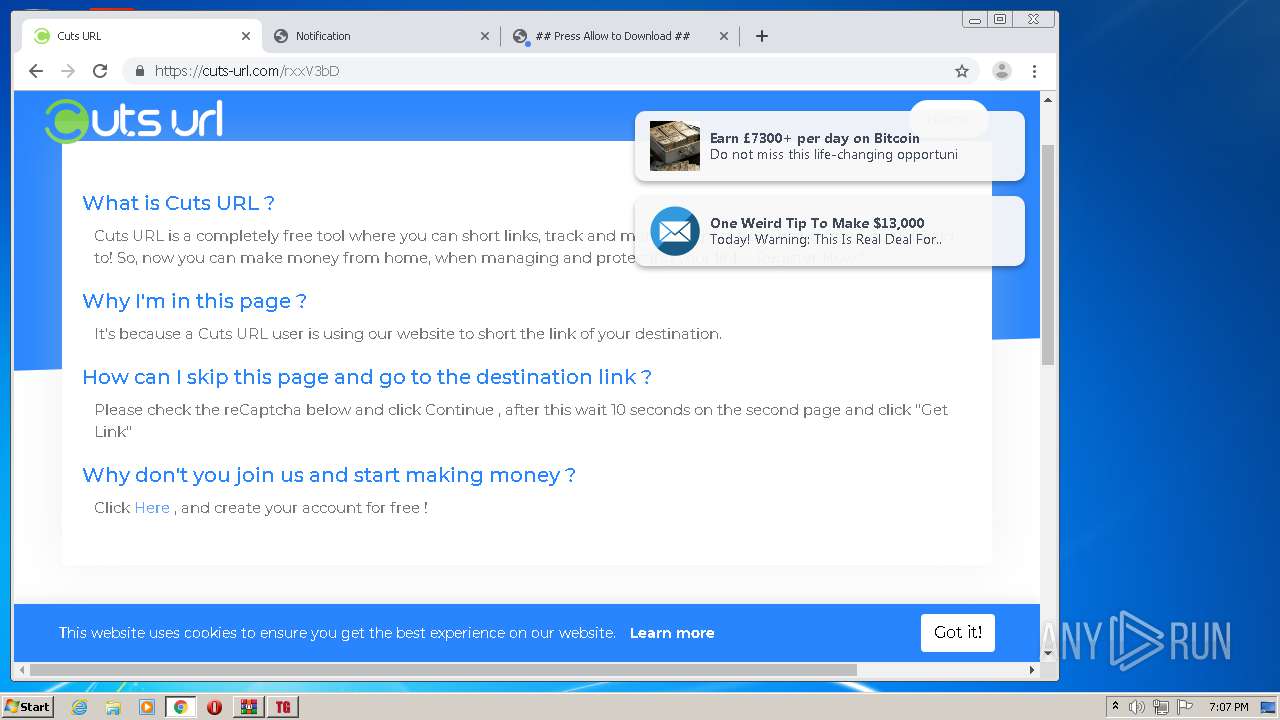
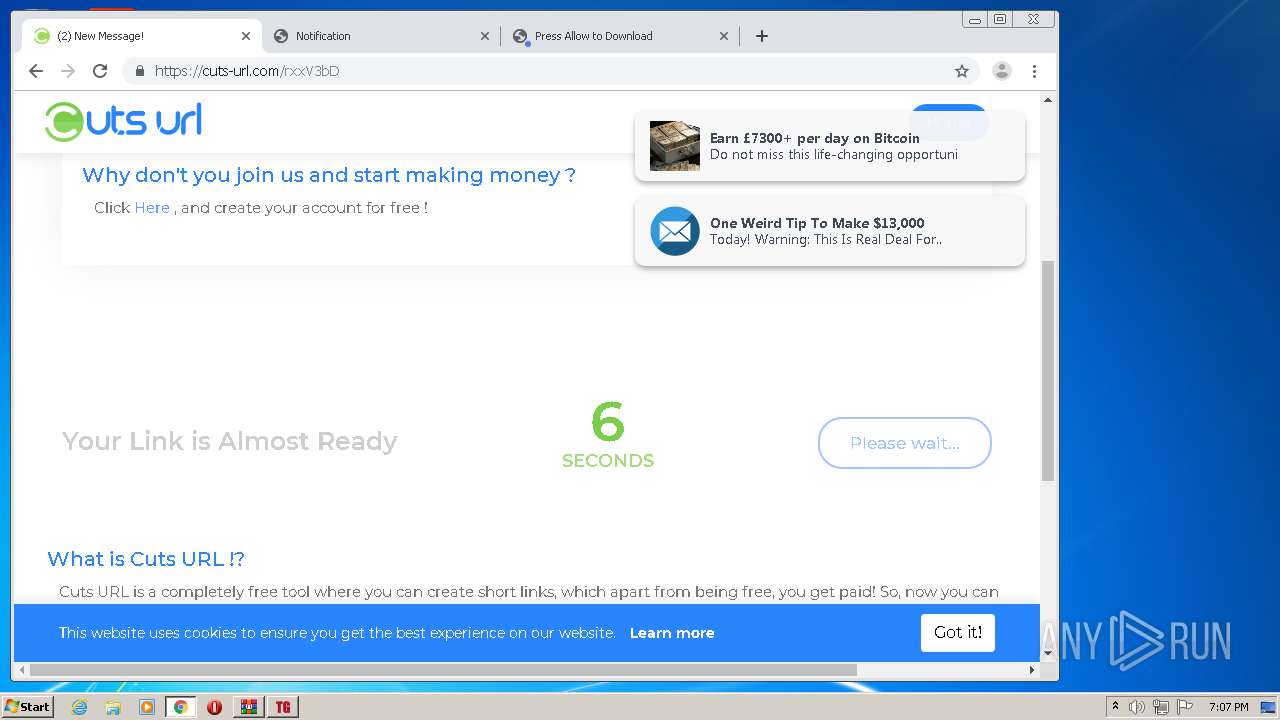
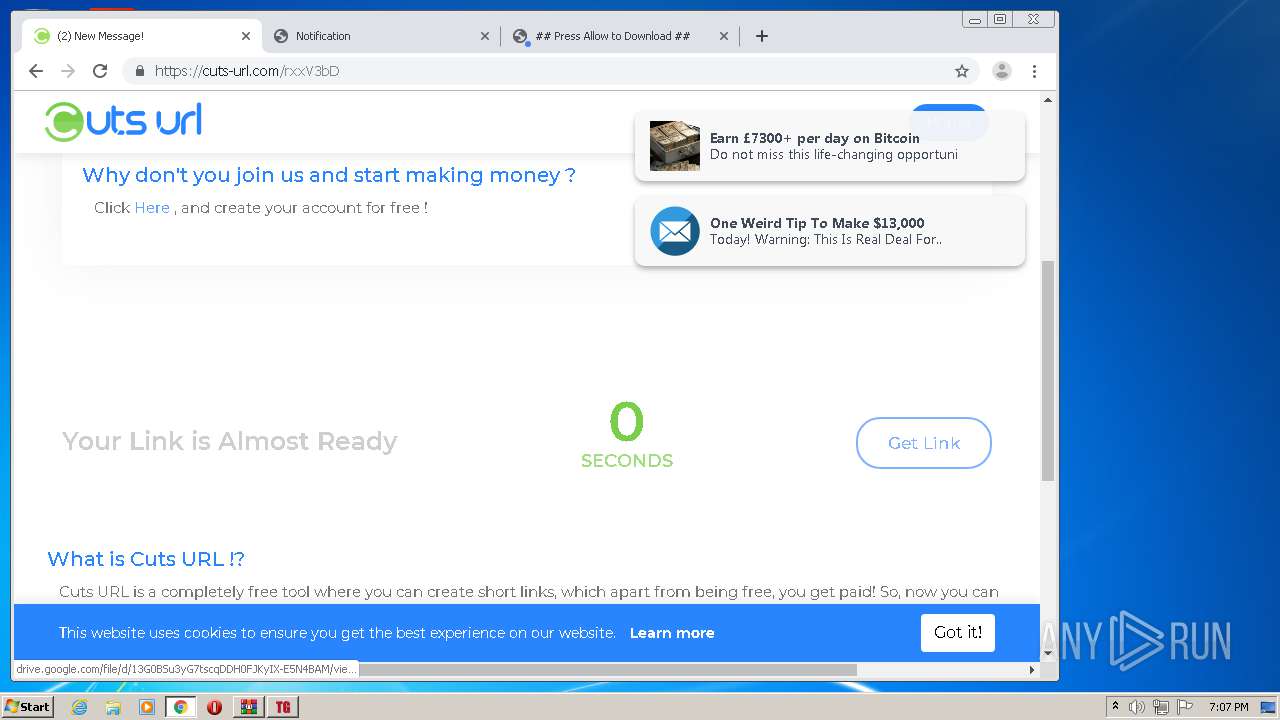
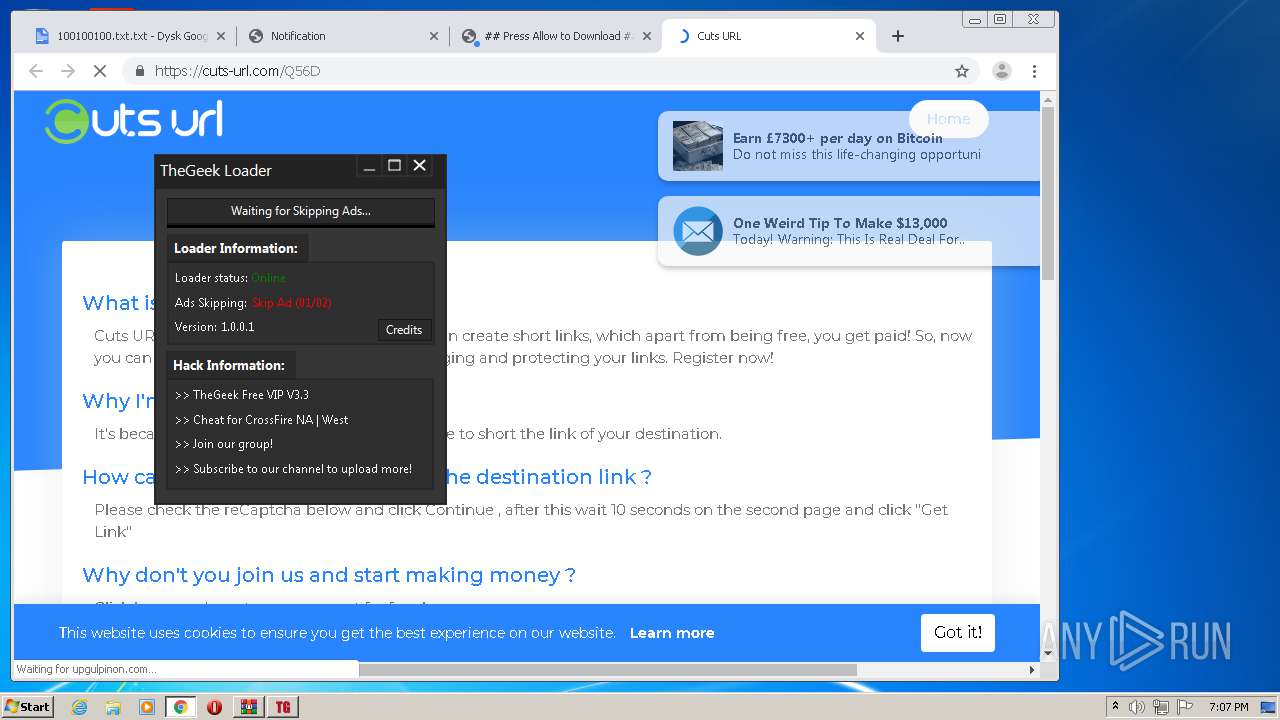
2796 | chrome.exe | 35.208.223.29:443 | cuts-url.com | — | US | unknown |
2796 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2796 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
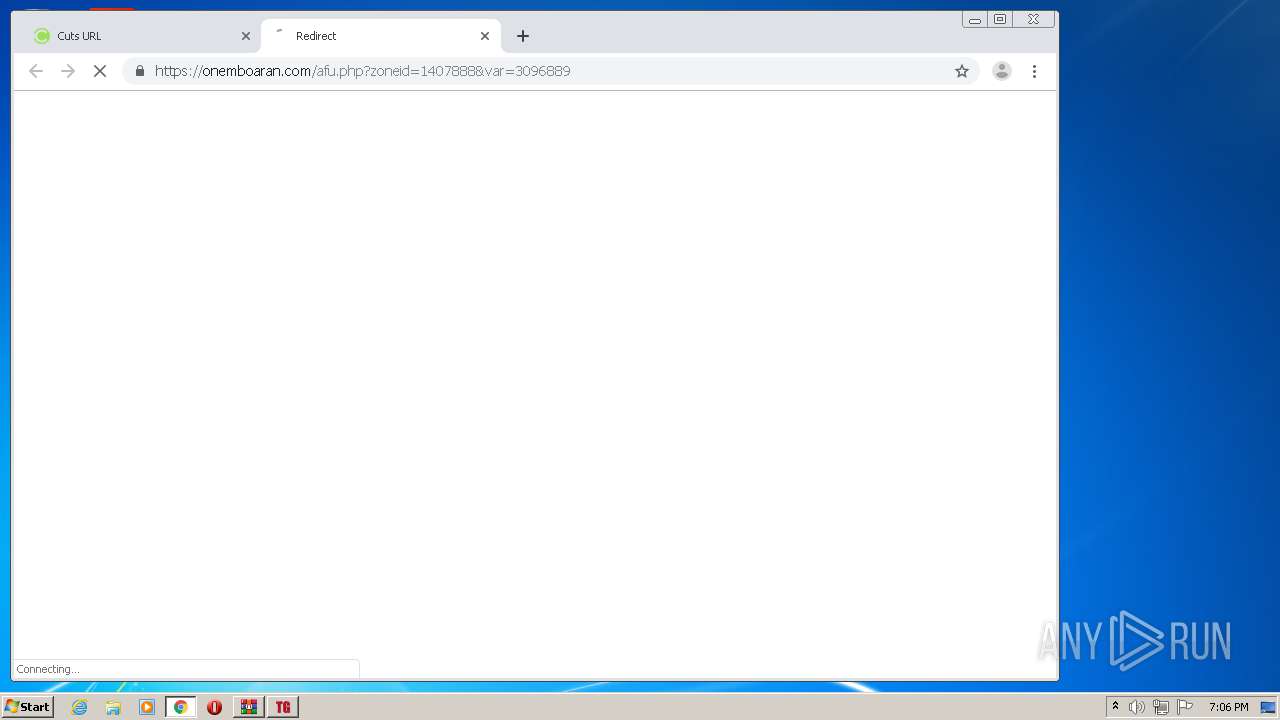
2796 | chrome.exe | 139.45.196.14:443 | onemboaran.com | — | US | unknown |
2796 | chrome.exe | 99.84.158.168:443 | d36zfztxfflmqo.cloudfront.net | AT&T Services, Inc. | US | unknown |
2796 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2796 | chrome.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
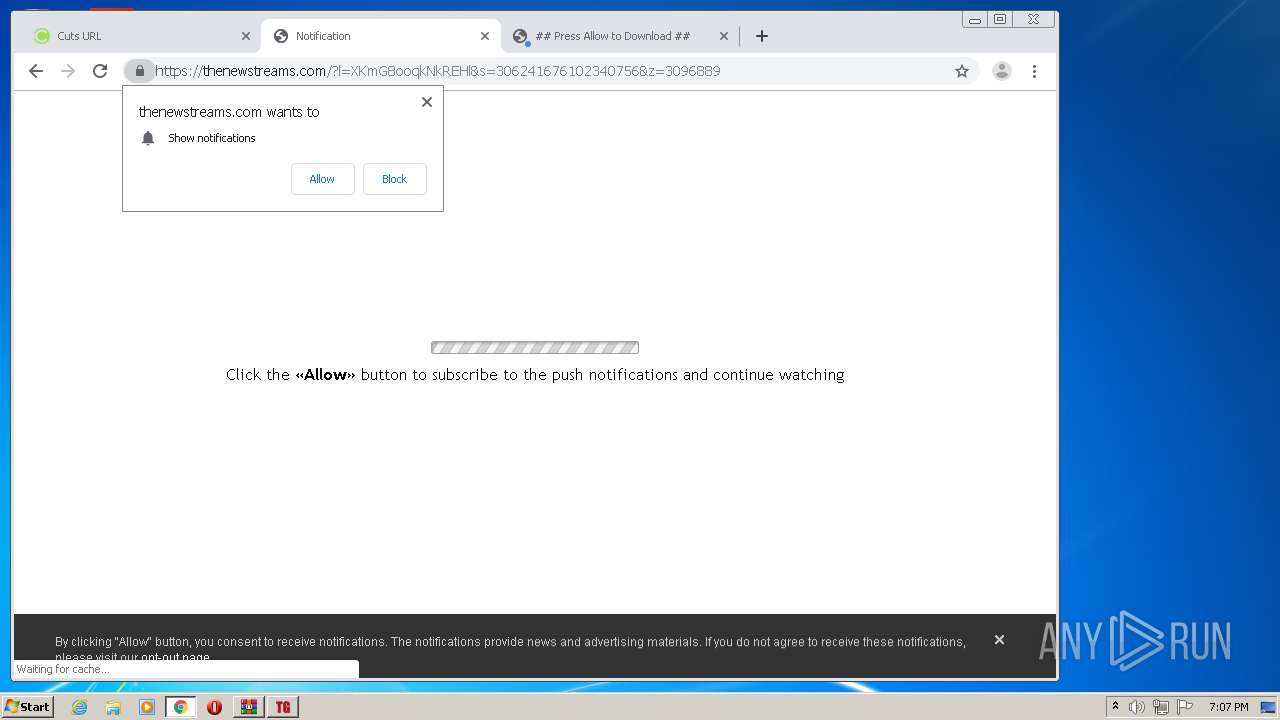
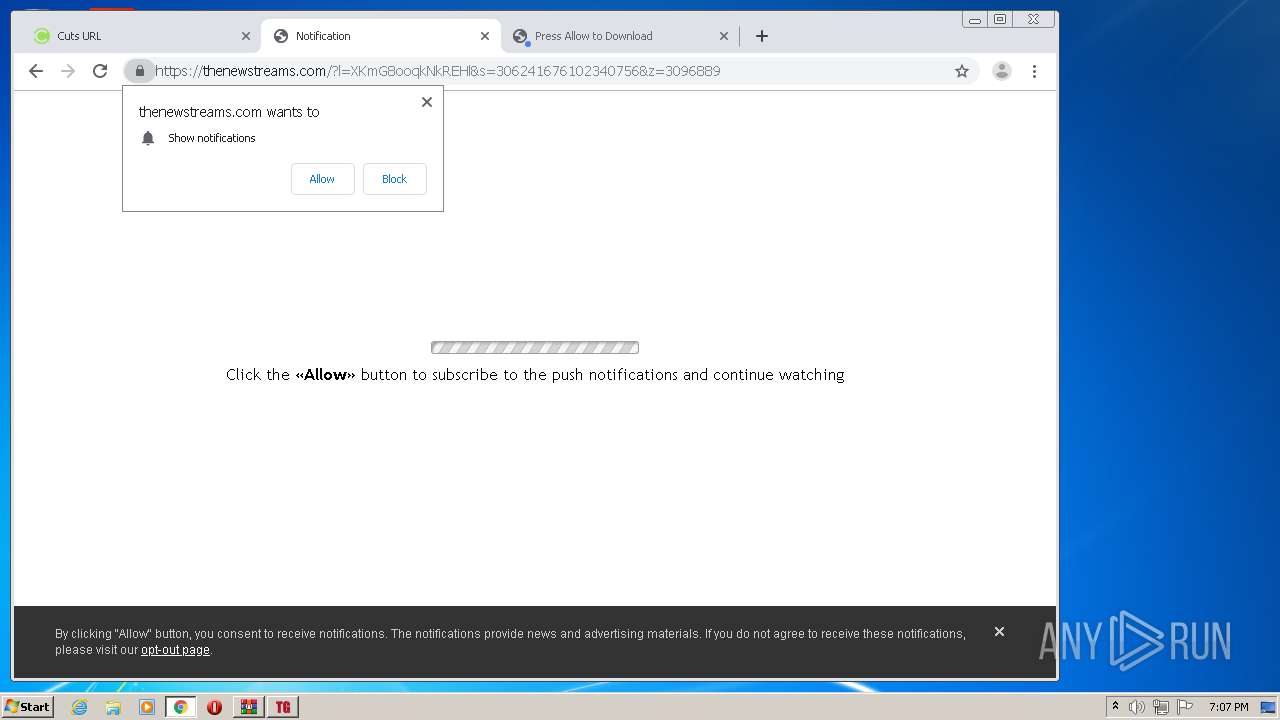
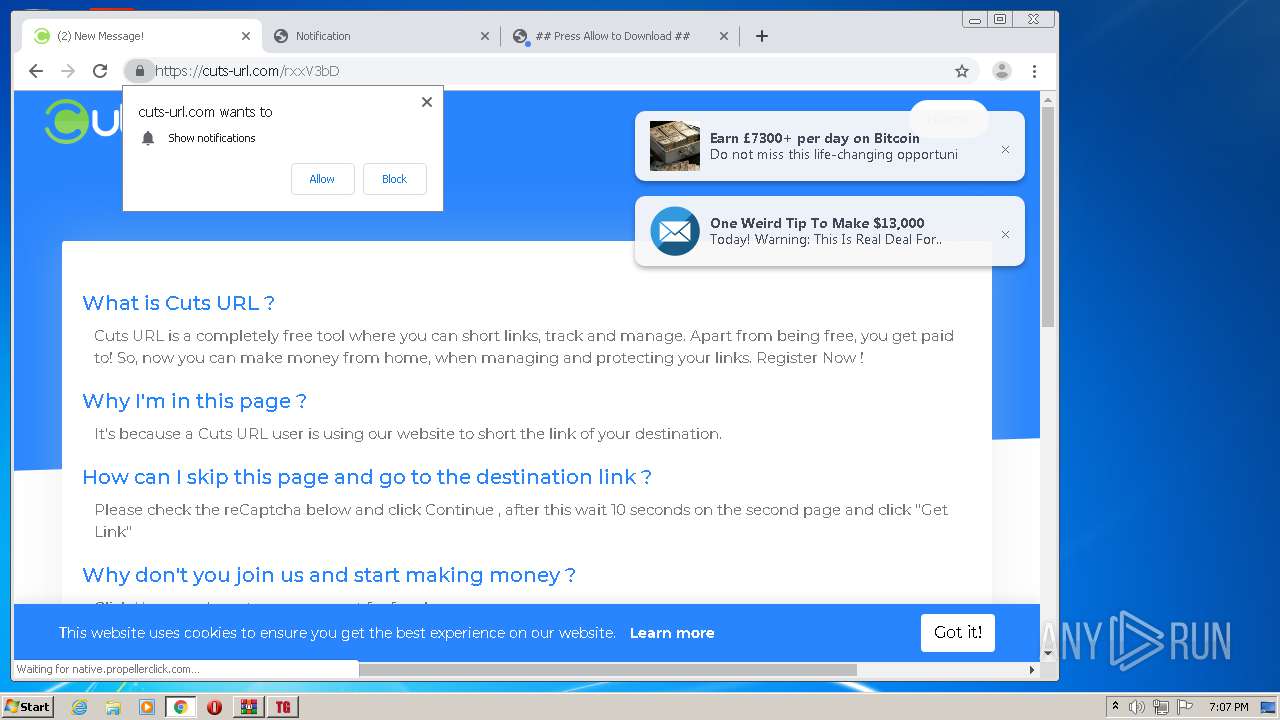
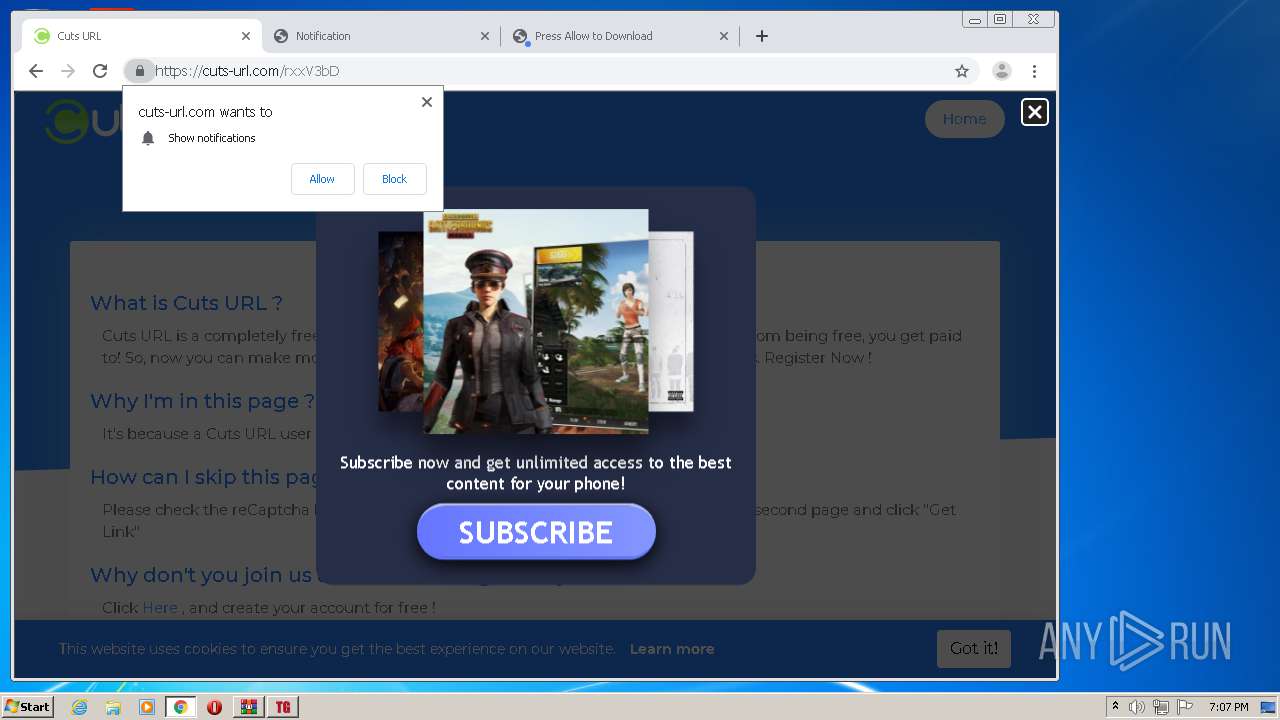
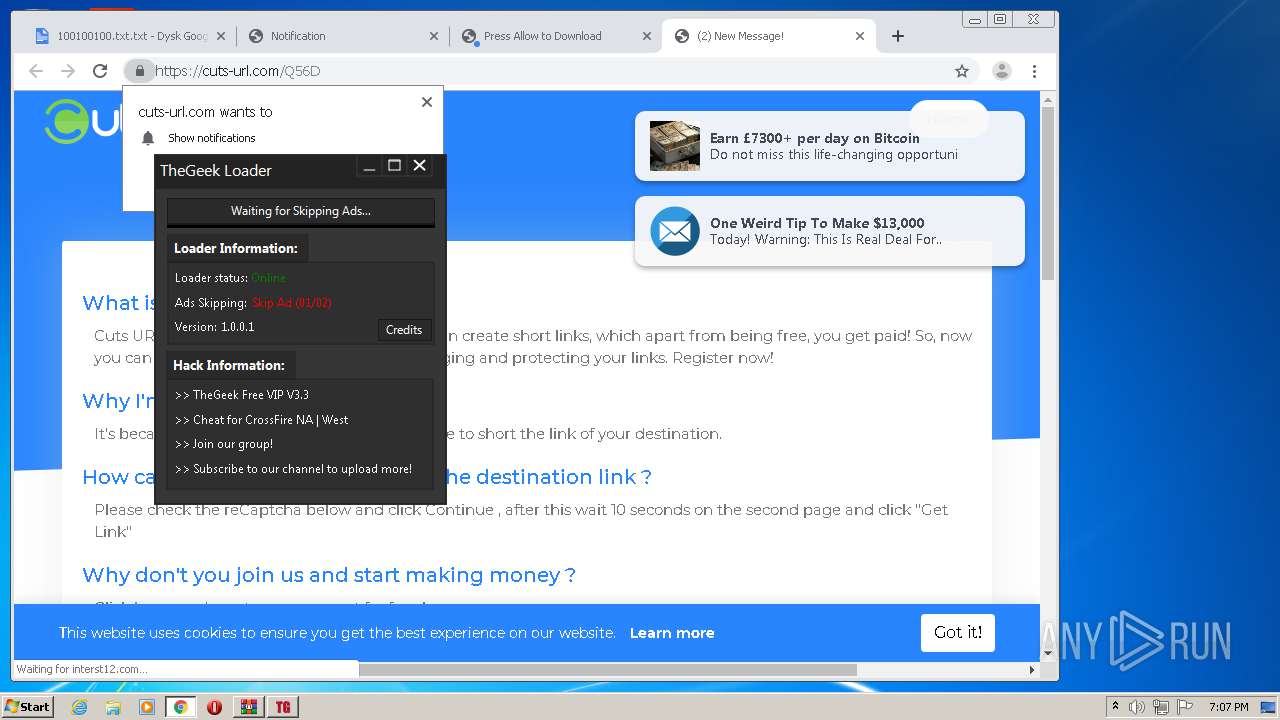
2796 | chrome.exe | 139.45.196.132:443 | propu.sh | — | US | suspicious |
2796 | chrome.exe | 139.45.195.116:443 | native.propellerclick.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tgramo.guncheats.com |
| suspicious |
cuts-url.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.linearicons.com |
| shared |
www.googletagmanager.com |
| whitelisted |
onemboaran.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report