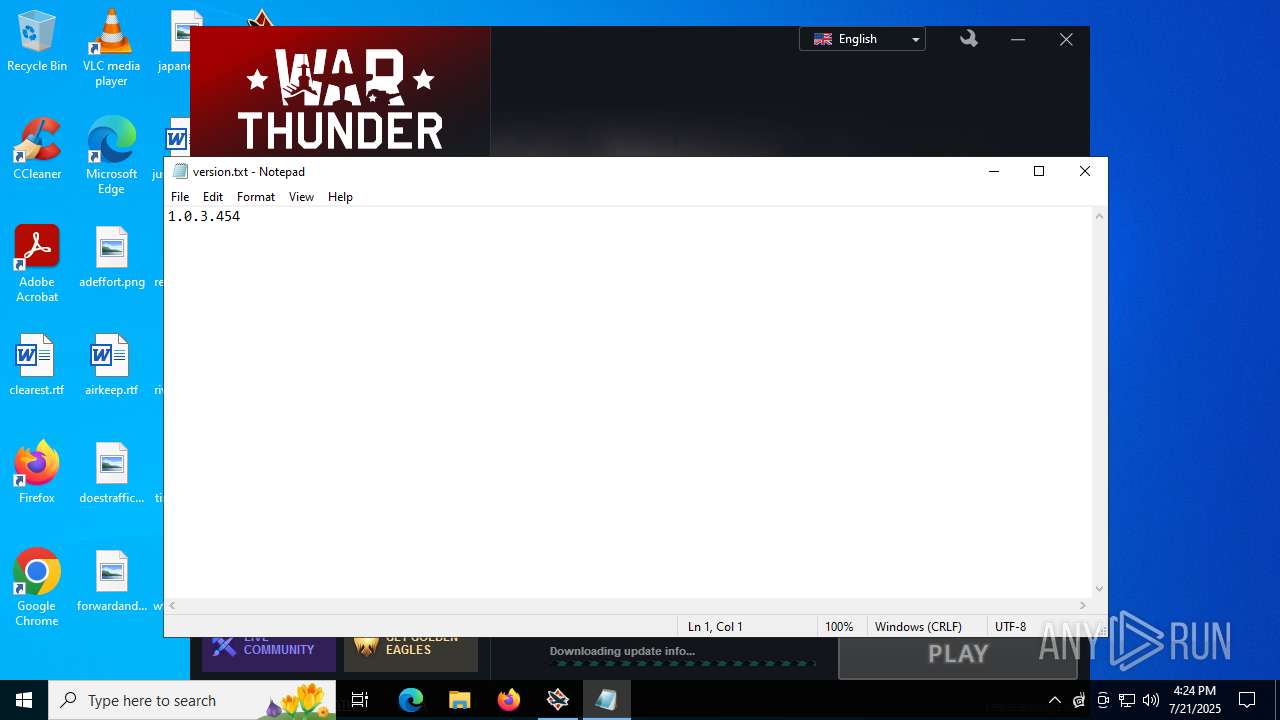
| File name: | wt_launcher_1.0.3.454-l9079vp7i.exe |
| Full analysis: | https://app.any.run/tasks/19a90670-93f1-49da-95d8-d44b7972b221 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2025, 16:23:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | 6558085A1C51EEE8E7C6B1A0D6ABD6A9 |
| SHA1: | ACA62ADFE17C18F88A5E7422A7CF47E6AF673A5D |
| SHA256: | 2A6F2D12F1254FC82D4E75DE516C795A22EFC6C85747335FB027FF4F751941C7 |
| SSDEEP: | 98304:N+cD4dnveSD45rVVZg8R5ljpuvcMOIZxIu7XuMBcWjgJB4V1H7VpBt9JplknATDw:dM0H1DSeuVuttiSBSCoAKK |
MALICIOUS
Changes the autorun value in the registry
- gjagent.exe (PID: 436)
SUSPICIOUS
Executable content was dropped or overwritten
- wt_launcher_1.0.3.454-l9079vp7i.exe (PID: 6840)
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- launcher.exe (PID: 1976)
Reads the Windows owner or organization settings
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
Uses NETSH.EXE to add a firewall rule or allowed programs
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
Creates file in the systems drive root
- launcher.exe (PID: 1976)
- gaijin_downloader.exe (PID: 4084)
- launcher.exe (PID: 3504)
- gaijin_downloader.exe (PID: 2432)
Reads security settings of Internet Explorer
- launcher.exe (PID: 1976)
- launcher.exe (PID: 3504)
Application launched itself
- launcher.exe (PID: 1976)
- updater.exe (PID: 7184)
There is functionality for taking screenshot (YARA)
- gjagent.exe (PID: 436)
- launcher.exe (PID: 3504)
There is functionality for sending ICMP (YARA)
- launcher.exe (PID: 3504)
Reads data from a file (MACROS)
- EXCEL.EXE (PID: 7220)
Opens a file (MACROS)
- EXCEL.EXE (PID: 7220)
The process executes via Task Scheduler
- updater.exe (PID: 7184)
INFO
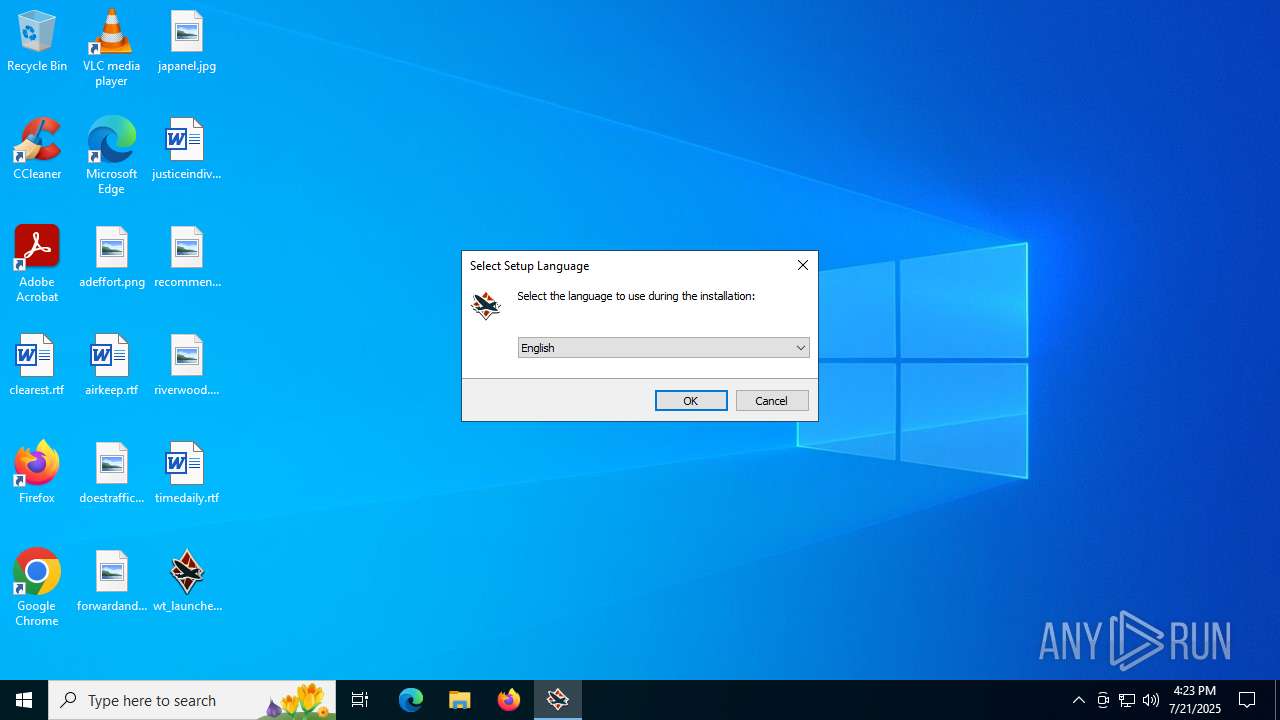
Checks supported languages
- wt_launcher_1.0.3.454-l9079vp7i.exe (PID: 6840)
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- launcher.exe (PID: 1976)
- gaijin_downloader.exe (PID: 4084)
- gjagent.exe (PID: 436)
- gjagent.exe (PID: 7052)
- gjagent.exe (PID: 5496)
- launcher.exe (PID: 3504)
- gaijin_downloader.exe (PID: 2432)
- gjagent.exe (PID: 3956)
- identity_helper.exe (PID: 7764)
- updater.exe (PID: 7184)
- updater.exe (PID: 7124)
Reads the computer name
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- launcher.exe (PID: 1976)
- gaijin_downloader.exe (PID: 4084)
- gjagent.exe (PID: 436)
- gaijin_downloader.exe (PID: 2432)
- launcher.exe (PID: 3504)
- identity_helper.exe (PID: 7764)
- updater.exe (PID: 7184)
Create files in a temporary directory
- wt_launcher_1.0.3.454-l9079vp7i.exe (PID: 6840)
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
Reads the software policy settings
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- slui.exe (PID: 8068)
Reads the machine GUID from the registry
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- launcher.exe (PID: 1976)
- gjagent.exe (PID: 436)
- gaijin_downloader.exe (PID: 4084)
- gjagent.exe (PID: 5496)
- launcher.exe (PID: 3504)
- gjagent.exe (PID: 3956)
- gaijin_downloader.exe (PID: 2432)
- gjagent.exe (PID: 7052)
Creates files or folders in the user directory
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
- launcher.exe (PID: 1976)
- gaijin_downloader.exe (PID: 4084)
- gjagent.exe (PID: 436)
- gjagent.exe (PID: 7052)
- launcher.exe (PID: 3504)
- gaijin_downloader.exe (PID: 2432)
- gjagent.exe (PID: 3956)
- gjagent.exe (PID: 5496)
Detects InnoSetup installer (YARA)
- wt_launcher_1.0.3.454-l9079vp7i.exe (PID: 6840)
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
Compiled with Borland Delphi (YARA)
- wt_launcher_1.0.3.454-l9079vp7i.exe (PID: 6840)
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
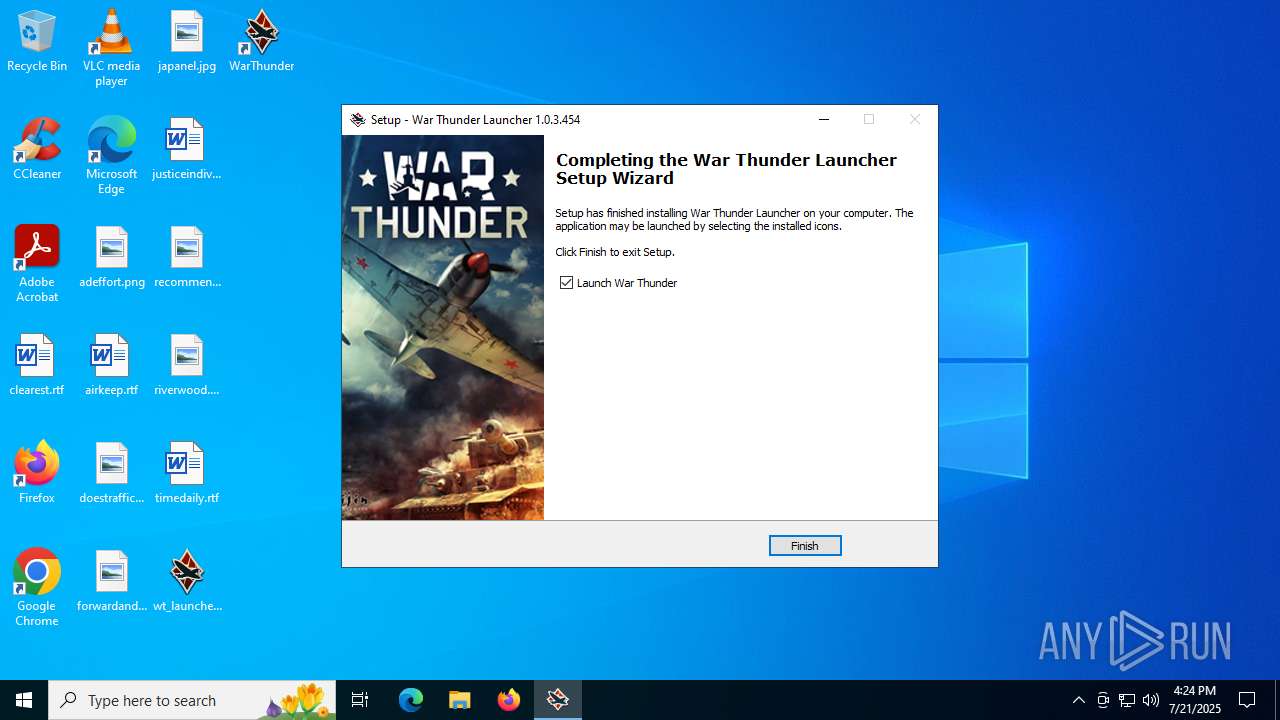
Creates a software uninstall entry
- wt_launcher_1.0.3.454-l9079vp7i.tmp (PID: 6956)
Creates files in the program directory
- launcher.exe (PID: 1976)
Process checks computer location settings
- launcher.exe (PID: 1976)
- launcher.exe (PID: 3504)
Launching a file from a Registry key
- gjagent.exe (PID: 436)
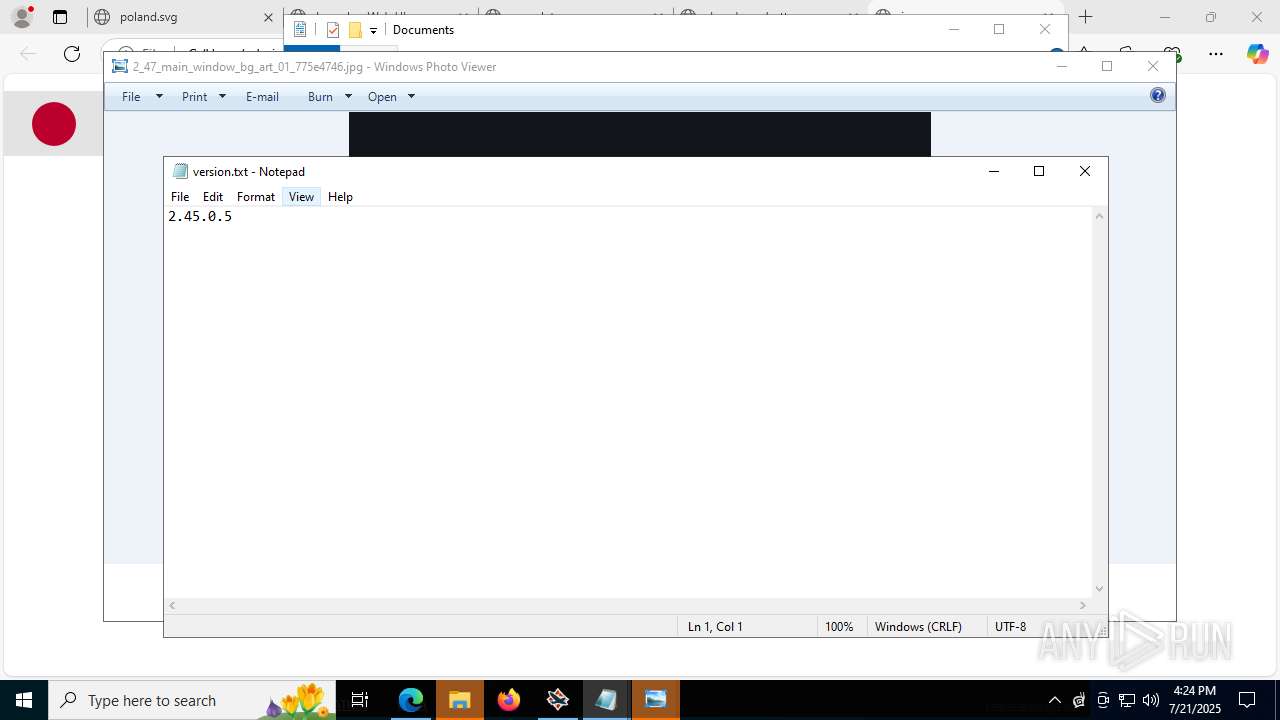
Manual execution by a user
- gjagent.exe (PID: 7052)
- notepad.exe (PID: 2532)
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 620)
- rundll32.exe (PID: 4680)
- iexplore.exe (PID: 6704)
- rundll32.exe (PID: 7504)
- iexplore.exe (PID: 7716)
- iexplore.exe (PID: 8020)
- notepad.exe (PID: 6472)
- EXCEL.EXE (PID: 7220)
- rundll32.exe (PID: 8088)
- rundll32.exe (PID: 7080)
- rundll32.exe (PID: 7744)
- iexplore.exe (PID: 8920)
- iexplore.exe (PID: 8512)
- iexplore.exe (PID: 8320)
- iexplore.exe (PID: 9112)
- iexplore.exe (PID: 8712)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2532)
- notepad.exe (PID: 6472)
- rundll32.exe (PID: 7744)
Application launched itself
- msedge.exe (PID: 5528)
Reads Environment values
- identity_helper.exe (PID: 7764)
Checks proxy server information
- slui.exe (PID: 8068)
Reads Microsoft Office registry keys
- rundll32.exe (PID: 7744)
Process checks whether UAC notifications are on
- updater.exe (PID: 7184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 182272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Gaijin Network |
| FileDescription: | War Thunder Launcher Setup |
| FileVersion: | |
| LegalCopyright: | Copyright © 2019-2025 by Gaijin Entertainment |
| OriginalFileName: | |
| ProductName: | War Thunder Launcher |
| ProductVersion: |
Total processes
272
Monitored processes
131
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | "C:\Users\admin\AppData\Local\Gaijin\Program Files (x86)\NetAgent\gjagent.exe" | C:\Users\admin\AppData\Local\Gaijin\Program Files (x86)\NetAgent\gjagent.exe | launcher.exe | ||||||||||||
User: admin Company: Gaijin Integrity Level: MEDIUM Description: Gaijin.Net Updater Version: 1.0.51 Modules
| |||||||||||||||
| 440 | "C:\WINDOWS\system32\netsh" netsh advfirewall firewall add rule name="War Thunder" program="C:\Users\admin\AppData\Local\WarThunder\win64\aces.exe" dir=in action=allow protocol=TCP localport=7852 | C:\Windows\SysWOW64\netsh.exe | — | wt_launcher_1.0.3.454-l9079vp7i.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" C:\Users\admin\Desktop\poland.svg | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\WINDOWS\system32\netsh.exe" advfirewall firewall add rule name="War Thunder Game Min Client" dir=in action=allow program="C:\Users\admin\AppData\Local\WarThunder\win64\aces-min-cpu.exe" enable=yes | C:\Windows\SysWOW64\netsh.exe | — | wt_launcher_1.0.3.454-l9079vp7i.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2400,i,12465675122294917358,873585556713021545,262144 --variations-seed-version --mojo-platform-channel-handle=2396 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --always-read-main-dll --field-trial-handle=7620,i,12465675122294917358,873585556713021545,262144 --variations-seed-version --mojo-platform-channel-handle=7636 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\WINDOWS\system32\netsh" netsh advfirewall firewall add rule name="War Thunder" program="C:\Users\admin\AppData\Local\WarThunder\win64\aces.exe" dir=in action=allow protocol=TCP localport=443 | C:\Windows\SysWOW64\netsh.exe | — | wt_launcher_1.0.3.454-l9079vp7i.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
53 903
Read events
53 484
Write events
396
Delete events
23
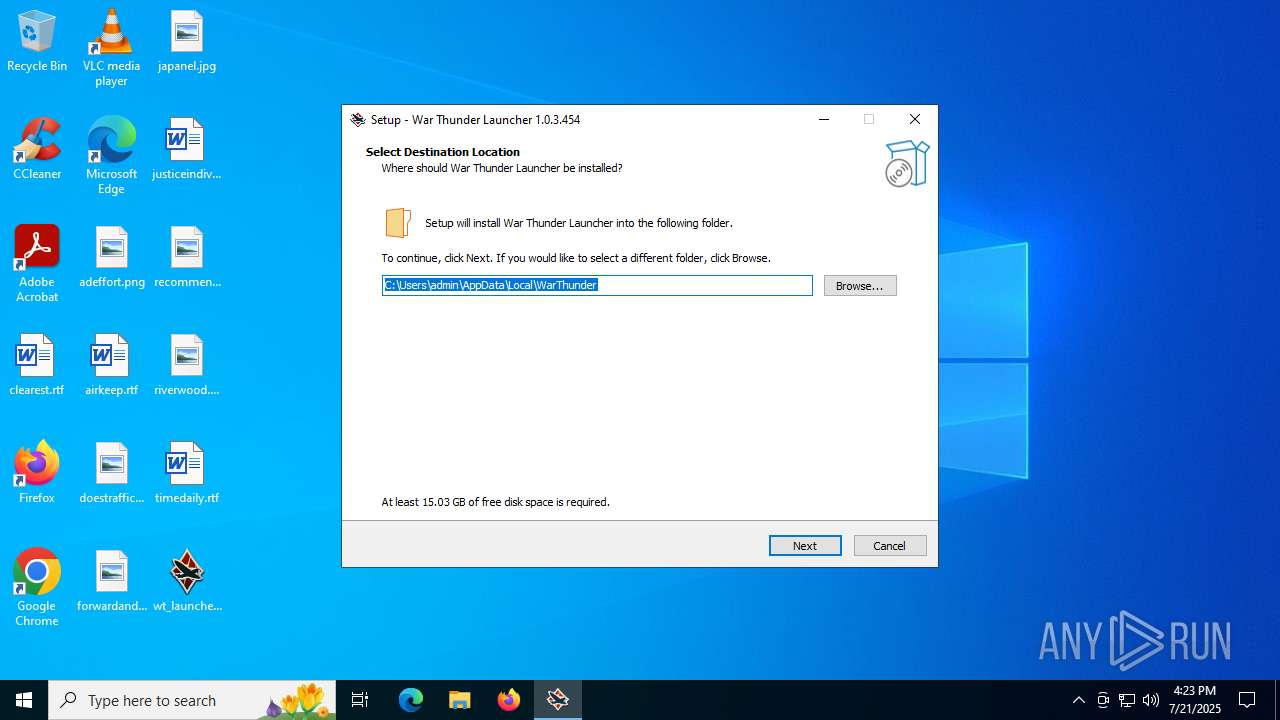
Modification events
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | StartupWithWindows |
Value: Yes | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | InstallDir |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | InstallPath |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | Dir |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\AppData\Local\WarThunder\launcher.exe | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Gaijin\WarThunder |
| Operation: | write | Name: | language |
Value: English | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{ed8deea4-29fa-3932-9612-e2122d8a62d9}}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{ed8deea4-29fa-3932-9612-e2122d8a62d9}}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{ed8deea4-29fa-3932-9612-e2122d8a62d9}}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\WarThunder\ | |||
| (PID) Process: | (6956) wt_launcher_1.0.3.454-l9079vp7i.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{ed8deea4-29fa-3932-9612-e2122d8a62d9}}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: WarThunder | |||
Executable files
16
Suspicious files
253
Text files
922
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6840 | wt_launcher_1.0.3.454-l9079vp7i.exe | C:\Users\admin\AppData\Local\Temp\is-D3BG3.tmp\wt_launcher_1.0.3.454-l9079vp7i.tmp | executable | |
MD5:462351849F2845C6EDC10A3215642F6D | SHA256:FE2E68697A084A60F738AAC6A21BCD94249E4E27CC0FDBBB3D7F21EDD73878FF | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\is-KO73J.tmp | executable | |
MD5:462351849F2845C6EDC10A3215642F6D | SHA256:FE2E68697A084A60F738AAC6A21BCD94249E4E27CC0FDBBB3D7F21EDD73878FF | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\unins000.exe | executable | |
MD5:462351849F2845C6EDC10A3215642F6D | SHA256:FE2E68697A084A60F738AAC6A21BCD94249E4E27CC0FDBBB3D7F21EDD73878FF | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\bpreport.exe | executable | |
MD5:31911C6EA459F516D1DA0A12EC677BEA | SHA256:44C1DB6B7BF4103B2C4D3A1F014A1EA8FAFBBEBA19CD028525D494E3E390A896 | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\is-8IH14.tmp | executable | |
MD5:4605B74B5E6281385BEAFCAAC11789F9 | SHA256:8B951DEA0BCDBB323C63F3C6C2D1F19BA6AD9D881FD4BEC360FFA5DBE02DA4F2 | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\is-0J4Q0.tmp | executable | |
MD5:31911C6EA459F516D1DA0A12EC677BEA | SHA256:44C1DB6B7BF4103B2C4D3A1F014A1EA8FAFBBEBA19CD028525D494E3E390A896 | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\Temp\is-LA11N.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\is-SKQGN.tmp | executable | |
MD5:ADC796431F36632ED86663E8BCAFDDB8 | SHA256:699783D9218C730A4334532DD0ADC6FA9D6E22395E96274B20CDB32EFEA6EDBA | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\is-DOD5H.tmp | executable | |
MD5:65F9CBA4FB02014A13685D8358CB0E67 | SHA256:2ED5BFDA0B759B4CD795514C0F1FFBDBD0DF40A82EA4FD50044BDFD8AD25CE37 | |||
| 6956 | wt_launcher_1.0.3.454-l9079vp7i.tmp | C:\Users\admin\AppData\Local\WarThunder\gjagent.exe | executable | |
MD5:65F9CBA4FB02014A13685D8358CB0E67 | SHA256:2ED5BFDA0B759B4CD795514C0F1FFBDBD0DF40A82EA4FD50044BDFD8AD25CE37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
132
DNS requests
78
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2324 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 20.190.159.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 200 | 20.190.159.68:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 188.42.61.240:443 | https://launcher-bq.gaijin.net/launcher | unknown | binary | 15 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2324 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
launcher-bq.gaijin.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
client-stats.gaijin.net |
| whitelisted |
client-stats.warthunder.com |
| whitelisted |
yupmaster.gaijinent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
launcher.exe | |
launcher.exe | Log path C:\Users\admin\AppData\Local\WarThunder\.launcher_log\2025_07_21_16_24_15_1976.txt |
launcher.exe | BUILD TIMESTAMP: Mar 4 2025 17:38:21
|
launcher.exe | 0.31 [D] TIMER freq: ticks/usec=3 ticks/msec=3579
|
launcher.exe | 0.33 [D] Creating thread "Watchdog thread"...
|
launcher.exe | 0.33 [D] Registered message 0xC19F
|
launcher.exe | ---$01 (null) ---
0.33 [D] $01 Thread "Watchdog thread" started
|
launcher.exe | 0.34 [D] Mounting C:\Users\admin\AppData\Local\WarThunder\launcherr.dat...
|
launcher.exe | 0.37 [D] launcherr.dat sign match
|
launcher.exe | 0.37 [D] Mounted custom.css
|