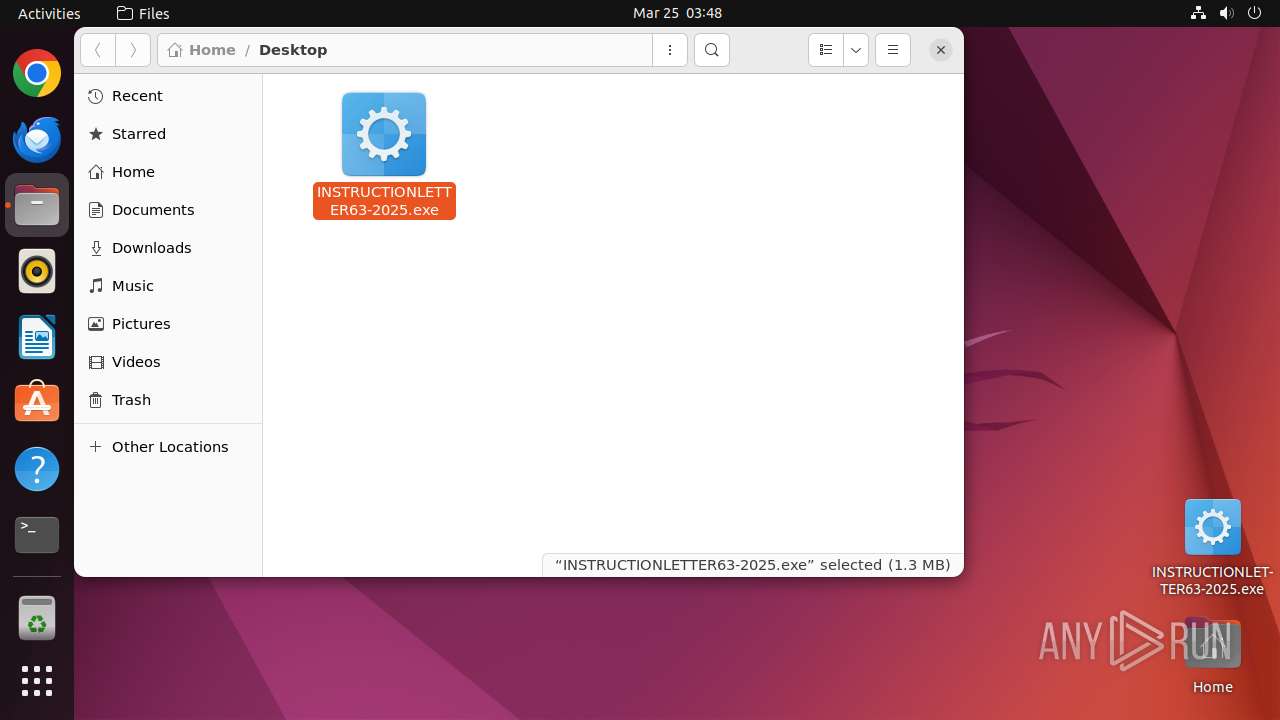
| File name: | INSTRUCTIONLETTER63-2025.exe |
| Full analysis: | https://app.any.run/tasks/175d7dc8-5fea-4dfe-96f2-d02152dbd7ef |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 03:48:52 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/vnd.microsoft.portable-executable |
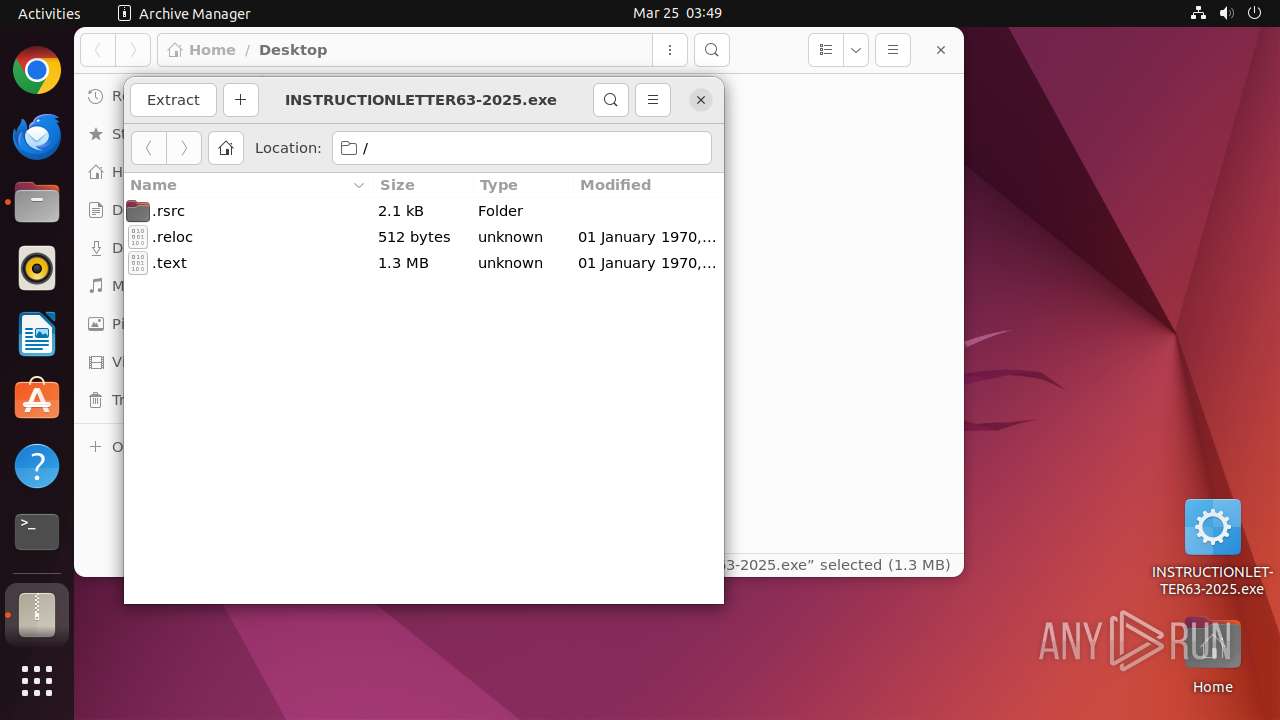
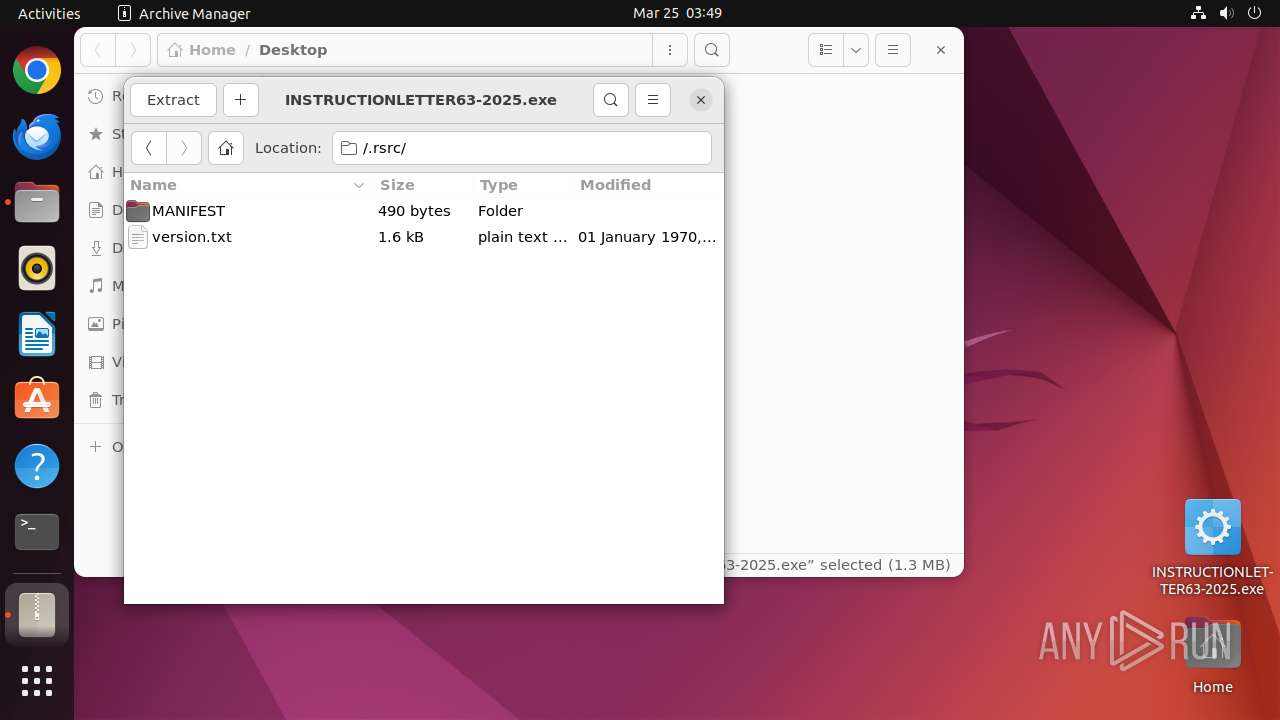
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 1CE4EEC150B3F140F72CE0DDCAD39337 |
| SHA1: | E5FB09B22C4C04025281DA6661D7C895D7D496A9 |
| SHA256: | 2A64D3212309DA646F5EF8210F6B8966C7A63CE82CB5BBD3C03838DD296BADCF |
| SSDEEP: | 49152:95akkiigYtI295TAChHWvd8GXW8Q7c1qWrW43ggZmzlrRemteQvkuyWhc6d1S0Dt:95h5iNfTnhHGyL8Q7ZWrWeg4mz73tRk2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads profile file
- nautilus (PID: 40666)
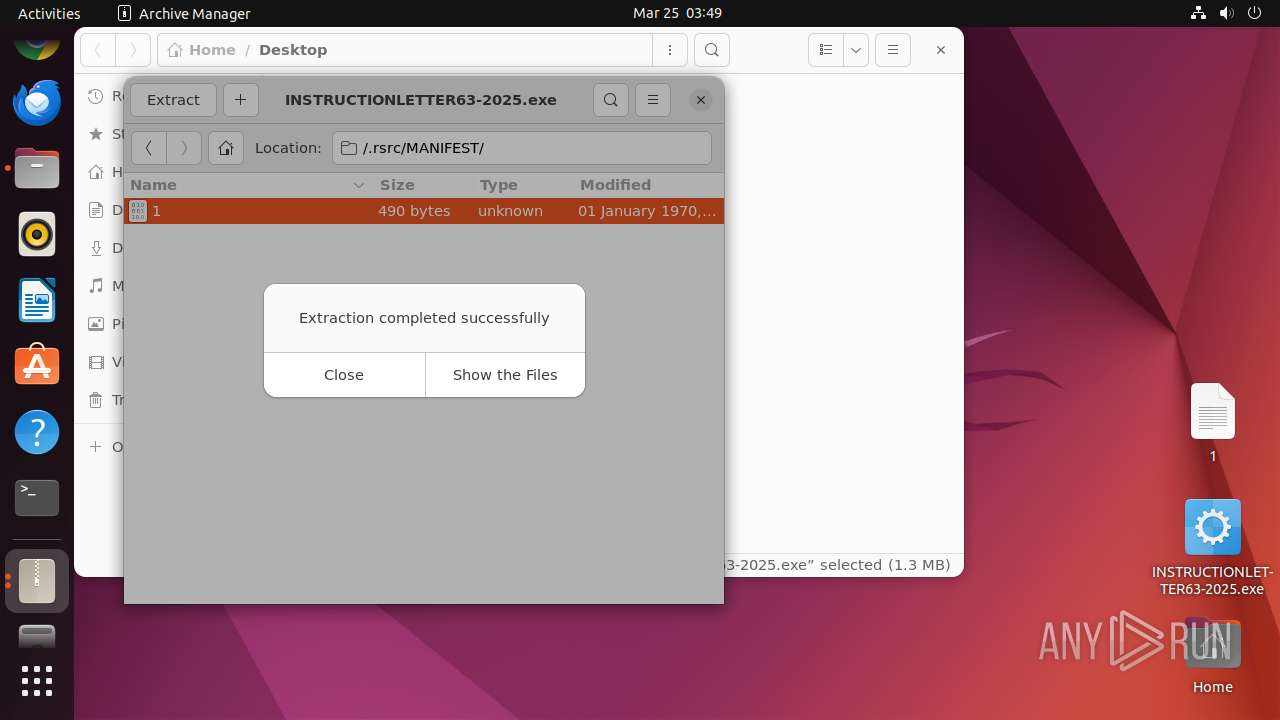
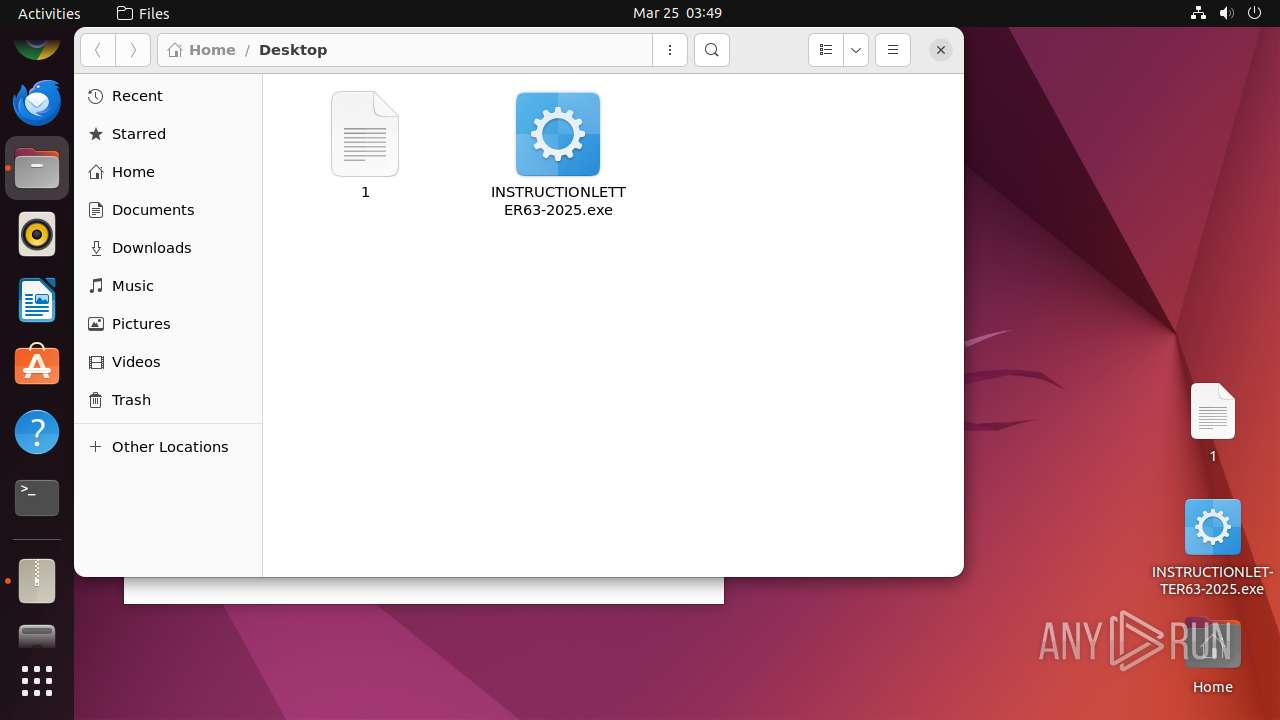
Creates files in the user directory
- 7z (PID: 40742)
- file-roller (PID: 40692)
Executes the "rm" command to delete files or directories
- file-roller (PID: 40692)
INFO
Checks timezone
- 7z (PID: 40742)
- 7z (PID: 40707)
- file-roller (PID: 40692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:24 21:50:21+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1315840 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14329e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Dlnfcrr |
| FileVersion: | 1.0.0.0 |
| InternalName: | Dlnfcrr.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | Dlnfcrr.exe |
| ProductName: | Dlnfcrr |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
241
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40664 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /home/user/Desktop/INSTRUCTIONLETTER63-2025\.exe " | /usr/bin/dash | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 40665 | sudo -iu user nautilus /home/user/Desktop/INSTRUCTIONLETTER63-2025.exe | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40666 | nautilus /home/user/Desktop/INSTRUCTIONLETTER63-2025.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40667 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40683 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN | ||||
| 40691 | nautilus /home/user/Desktop/INSTRUCTIONLETTER63-2025.exe | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
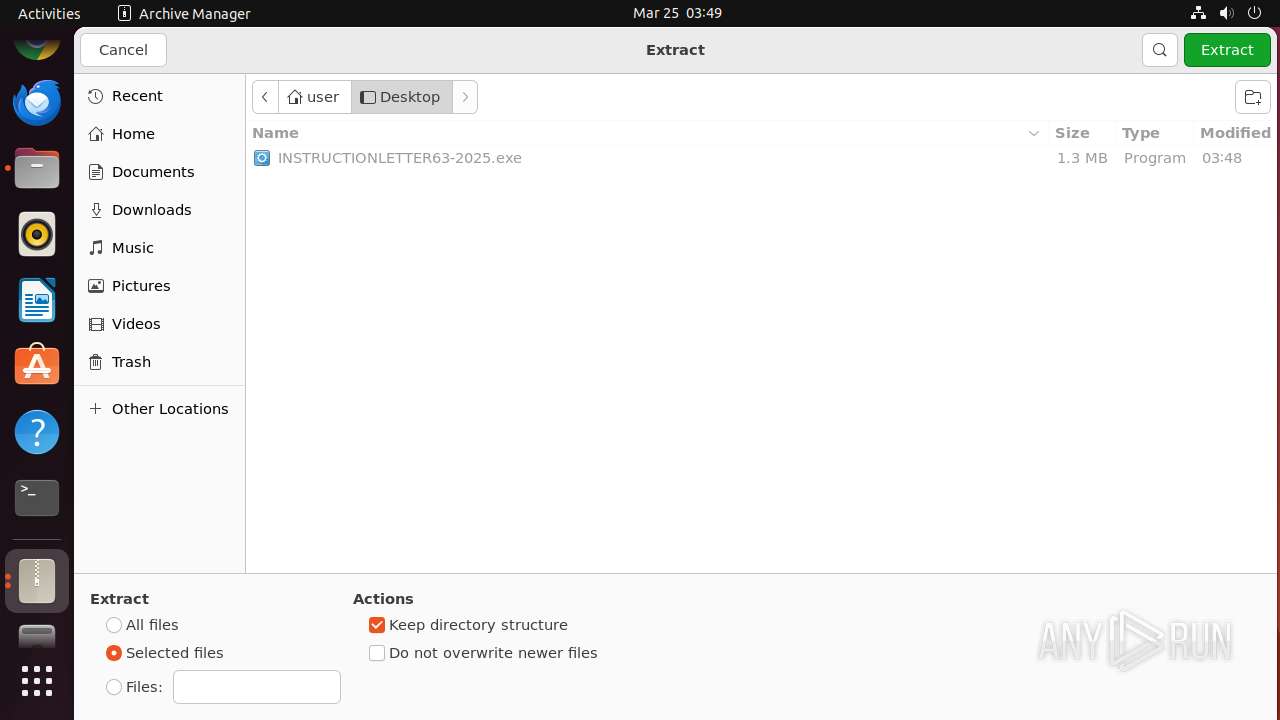
| 40692 | file-roller /home/user/Desktop/INSTRUCTIONLETTER63-2025.exe | /usr/bin/file-roller | — | nautilus |
User: user Integrity Level: UNKNOWN | ||||
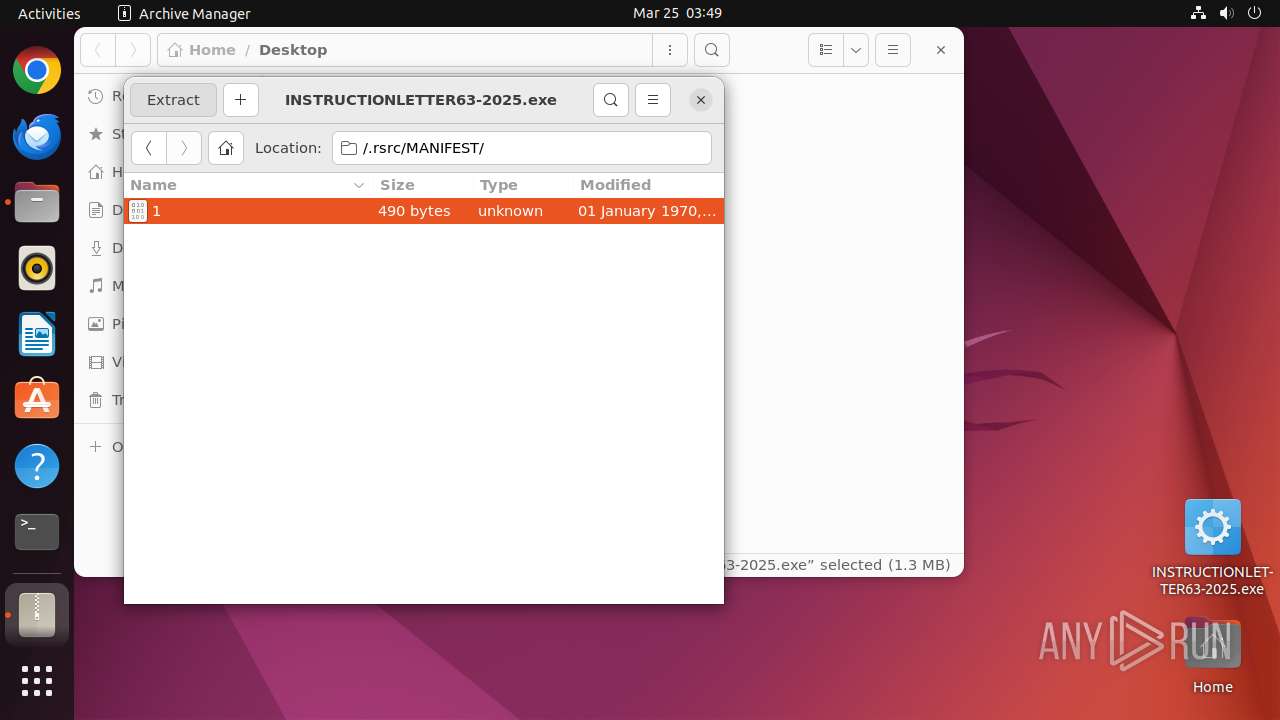
| 40707 | /usr/lib/p7zip/7z l -slt -bd -y -- /home/user/Desktop/INSTRUCTIONLETTER63-2025.exe | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40718 | /usr/libexec/gvfsd-network --spawner :1.6 /org/gtk/gvfs/exec_spaw/1 | /usr/libexec/gvfsd-network | — | gvfsd |
User: user Integrity Level: UNKNOWN | ||||
| 40724 | /usr/libexec/gvfsd-smb-browse --spawner :1.6 /org/gtk/gvfs/exec_spaw/2 | /usr/libexec/gvfsd-smb-browse | gvfsd | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
4
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40757 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/session.gvariant | binary | |
MD5:— | SHA256:— | |||
| 40666 | nautilus | /home/user/.local/share/recently-used.xbel.I1E032 | xml | |
MD5:— | SHA256:— | |||
| 40692 | file-roller | /home/user/.local/share/recently-used.xbel.PZB132 | xml | |
MD5:— | SHA256:— | |||
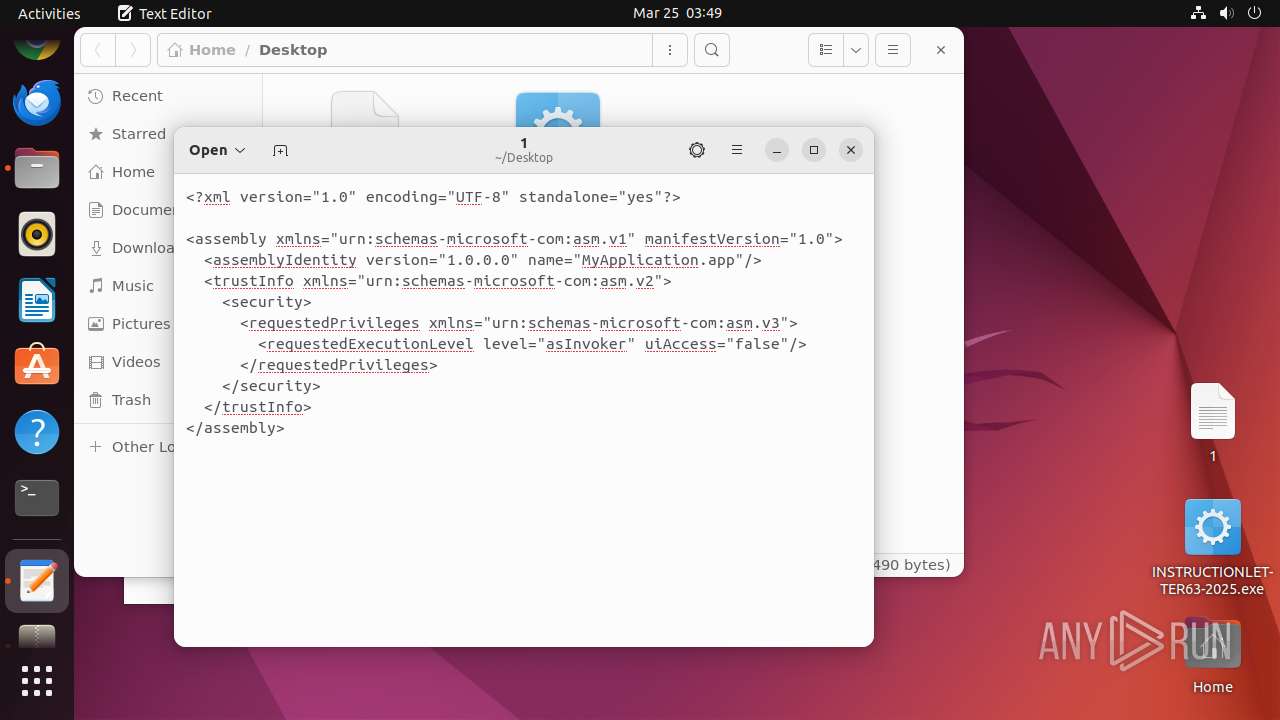
| 40742 | 7z | /home/user/Desktop/1 | xml | |
MD5:— | SHA256:— | |||
| 40692 | file-roller | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 40757 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 40666 | nautilus | /home/user/.local/share/recently-used.xbel | xml | |
MD5:— | SHA256:— | |||
| 40757 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/d2/ea27fa2c8972e4719271e6ea166eb60cb88796 | binary | |
MD5:— | SHA256:— | |||
| 40757 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/74/0feed80fcc6c9ed6fbc025c5e0aa962968fa40 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
40724 | gvfsd-smb-browse | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
15.100.168.192.in-addr.arpa |
| unknown |