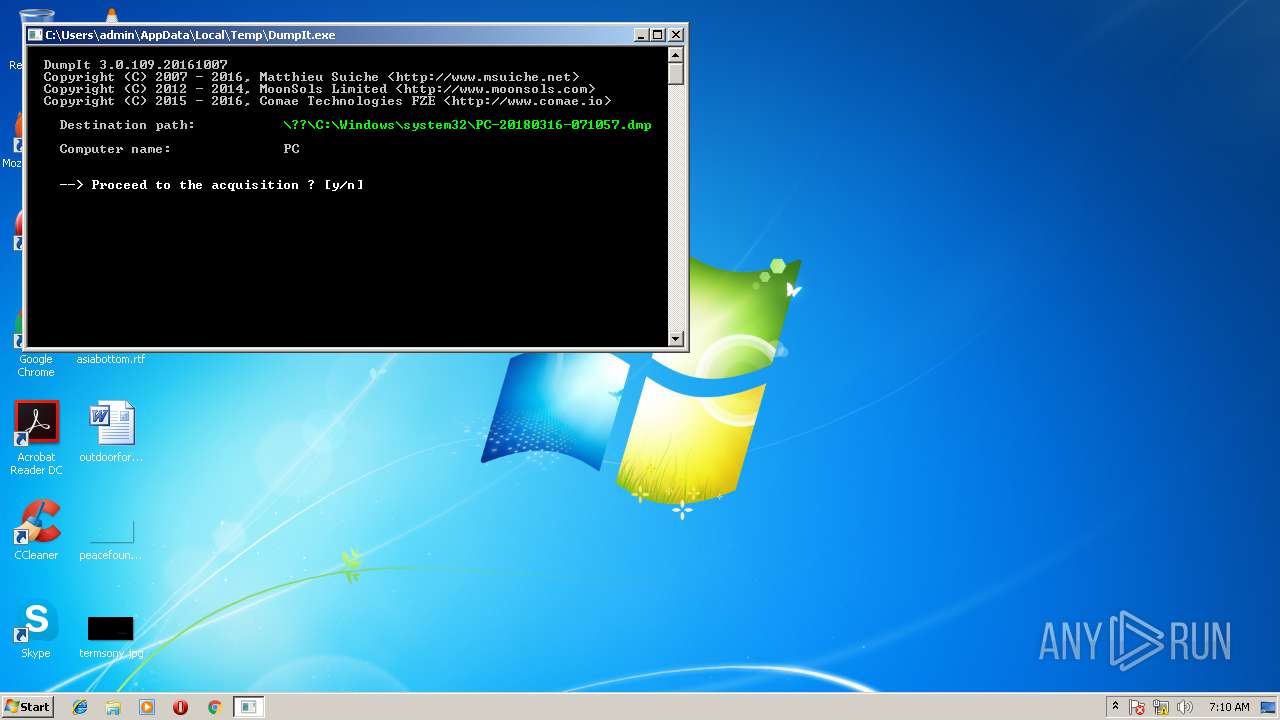
| File name: | DumpIt.exe |
| Full analysis: | https://app.any.run/tasks/2fe6a60f-4b0f-4e9d-97dc-86234185c025 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2018, 07:10:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | FA3E4D90530ABE25293C59742E4C8C6C |
| SHA1: | 38AFAB2479CF6EC37D91C50D7A885FE37F612D6E |
| SHA256: | 2A6346DD58CE312422BC613D239088C4F9562CED7F4899882C6E8AAF965C3F91 |
| SSDEEP: | 12288:SVdmay9czfxKuw32N5DjHrTDgN4R+BgF:ShBwmDjHrTm4a |
MALICIOUS
No malicious indicators.SUSPICIOUS
Removes files from Windows directory
- DumpIt.exe (PID: 3752)
Creates or modifies windows services
- DumpIt.exe (PID: 3752)
Creates files in the Windows directory
- DumpIt.exe (PID: 3752)
Creates files in the driver directory
- DumpIt.exe (PID: 3752)
Modifies files in the system directory
- DumpIt.exe (PID: 3752)
INFO
Dropped object may contain URL's
- DumpIt.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:07 21:16:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 245248 |
| InitializedDataSize: | 267776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16574 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Comae Technologies FZE |
| FileDescription: | Memory Acquisition Tool |
| FileVersion: | 3.0.0.0 |
| InternalName: | DumpIt.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFileName: | DumpIt.exe |
| ProductName: | Comae Memory Acquisition Tool |
| ProductVersion: | 3.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 07-Oct-2016 19:16:50 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Comae Technologies FZE |
| FileDescription: | Memory Acquisition Tool |
| FileVersion: | 3.0.0.0 |
| InternalName: | DumpIt.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFilename: | DumpIt.exe |
| ProductName: | Comae Memory Acquisition Tool |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 07-Oct-2016 19:16:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003BD5C | 0x0003BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61278 |
.rdata | 0x0003D000 | 0x00014EE2 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.34198 |
.data | 0x00052000 | 0x00002468 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.36024 |
.gfids | 0x00055000 | 0x00000254 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.57201 |
.tls | 0x00056000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00057000 | 0x00025FA0 | 0x00026000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.98967 |
.reloc | 0x0007D000 | 0x00003860 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59973 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 1.51664 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
203 | 7.0049 | 69840 | UNKNOWN | English - United States | BIN |
204 | 6.76653 | 78032 | UNKNOWN | English - United States | BIN |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
Secur32.dll |
WINHTTP.dll |
WS2_32.dll |
ole32.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2908 | "C:\Users\admin\AppData\Local\Temp\DumpIt.exe" | C:\Users\admin\AppData\Local\Temp\DumpIt.exe | — | explorer.exe | |||||||||||
User: admin Company: Comae Technologies FZE Integrity Level: MEDIUM Description: Memory Acquisition Tool Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3752 | "C:\Users\admin\AppData\Local\Temp\DumpIt.exe" | C:\Users\admin\AppData\Local\Temp\DumpIt.exe | explorer.exe | ||||||||||||
User: admin Company: Comae Technologies FZE Integrity Level: HIGH Description: Memory Acquisition Tool Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
39
Read events
24
Write events
15
Delete events
0
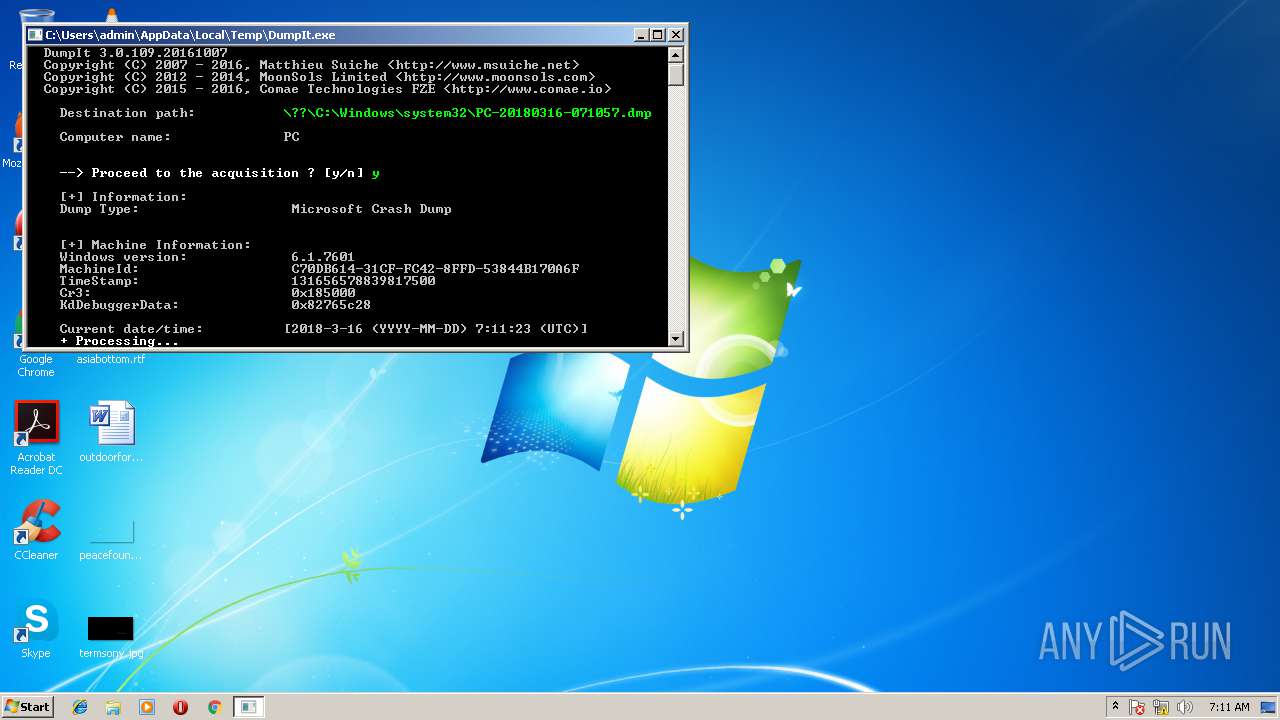
Modification events
| (PID) Process: | (3752) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3752) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Windows\system32\Drivers\DumpIt.sys | |||
| (PID) Process: | (3752) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3752) DumpIt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | DumpIt.exe | C:\Windows\system32\Drivers\DumpIt.sys | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\CabEB9.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\TarEBA.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\CabECA.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\TarECB.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\Cab237D.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\Tar237E.tmp | — | |
MD5:— | SHA256:— | |||
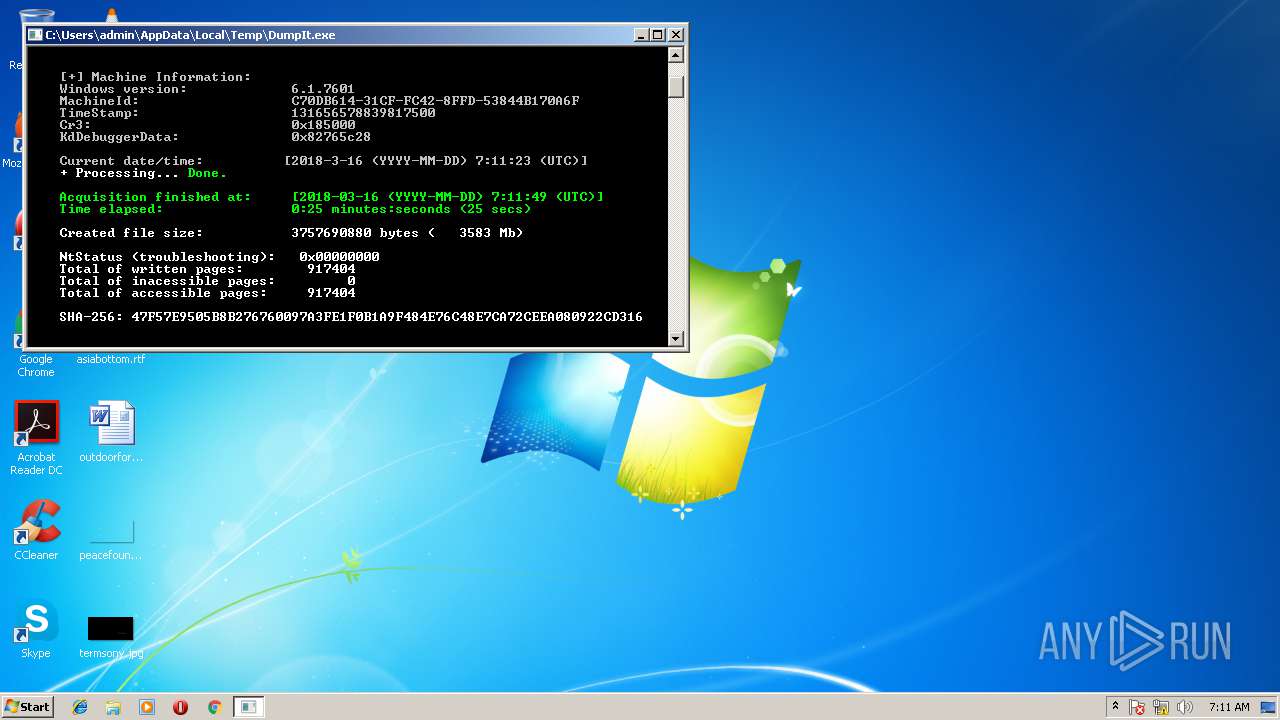
| 3752 | DumpIt.exe | C:\Windows\system32\PC-20180316-071057.dmp | — | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Windows\System32\PC-20180316-071057.json | text | |
MD5:— | SHA256:— | |||
| 3752 | DumpIt.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
— | — | GET | 200 | 173.236.227.251:80 | http://www.comae.io/getip.php | US | text | 68 b | suspicious |
— | — | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 174.138.111.38:443 | sheetsu.com | Digital Ocean, Inc. | US | unknown |
— | — | 173.236.227.251:80 | www.comae.io | New Dream Network, LLC | US | suspicious |
— | — | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
— | — | 8.253.207.120:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.comae.io |
| suspicious |
sheetsu.com |
| unknown |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
DumpIt.exe | [comae:3900] -> totalUploadLength = 0x300
|