| File name: | Nyx.exe |
| Full analysis: | https://app.any.run/tasks/7ed02c35-99b5-4e42-933f-0586c21d1a88 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2024, 02:09:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2160B2F130898499895E342E29434DB2 |
| SHA1: | E7D5E6BB5362B1C9B7F341546C1B801C35AC1071 |
| SHA256: | 2A5A392717E8095EB3B0A0D4E5DF01648E94F23DB3973F8D1DFA4DBBF77900F8 |
| SSDEEP: | 98304:BzcPQ17pm3B0D6xkKhu0NGaNs24qMqLSYIWYaihWxlSU7Z3aCTVuMobgOZZp1JT2:pUG5V6G4kg8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- Nyx.exe (PID: 6444)
Reads security settings of Internet Explorer
- Nyx.exe (PID: 6444)
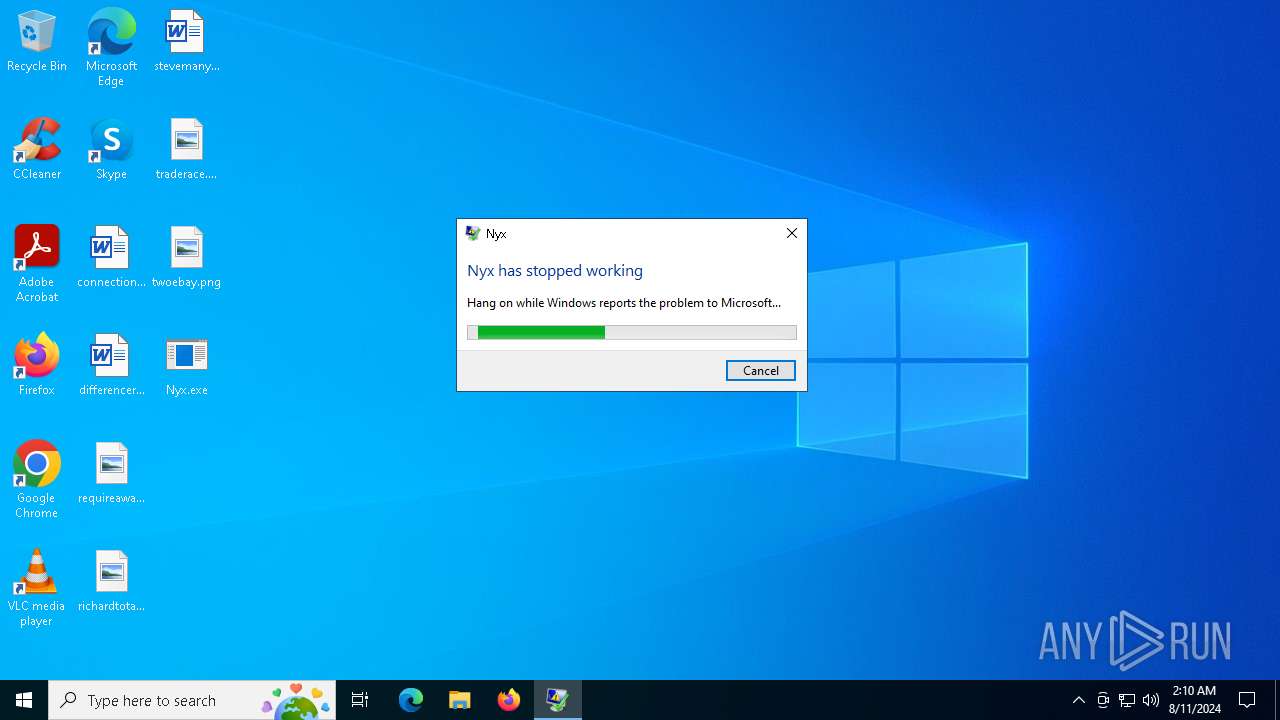
Executes application which crashes
- Nyx.exe (PID: 6444)
Searches for installed software
- Nyx.exe (PID: 6444)
INFO
Reads Environment values
- Nyx.exe (PID: 6444)
Reads the computer name
- Nyx.exe (PID: 6444)
Checks supported languages
- Nyx.exe (PID: 6444)
Checks proxy server information
- Nyx.exe (PID: 6444)
- WerFault.exe (PID: 5140)
Disables trace logs
- Nyx.exe (PID: 6444)
Reads the machine GUID from the registry
- Nyx.exe (PID: 6444)
Reads the software policy settings
- Nyx.exe (PID: 6444)
- WerFault.exe (PID: 5140)
.NET Reactor protector has been detected
- Nyx.exe (PID: 6444)
Creates files or folders in the user directory
- WerFault.exe (PID: 5140)
Attempting to use instant messaging service
- Nyx.exe (PID: 6444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2098:03:17 22:47:49+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5033984 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4cee5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Nyx scripting utility. |
| CompanyName: | - |
| FileDescription: | Nyx |
| FileVersion: | 1.0.0.0 |
| InternalName: | Nyx.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Nyx.exe |
| ProductName: | Nyx |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 4.6.0.0 |
Total processes
122
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5140 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6444 -s 3344 | C:\Windows\SysWOW64\WerFault.exe | Nyx.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6444 | "C:\Users\admin\Desktop\Nyx.exe" | C:\Users\admin\Desktop\Nyx.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Nyx Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
12 143
Read events
12 120
Write events
23
Delete events
0
Modification events
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6444) Nyx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Nyx_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Nyx.exe_834aae2e2bdcf646ef3cd30e2c6a4401644c573_8a50933e_94c0f8b9-a396-42a4-8c40-75da155a23cd\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5140 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Nyx.exe.6444.dmp | — | |
MD5:— | SHA256:— | |||
| 5140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7ED2.tmp.xml | xml | |
MD5:C75F63C6A27CD94BF37FA7E76B0A7391 | SHA256:7B3923D6AFFBBB29B3A4FBAE152FF5744C820DD6F367F90B2C2808114FEA62E9 | |||
| 5140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7EB2.tmp.WERInternalMetadata.xml | xml | |
MD5:88101BB5278ADE8B659B39D4809000D6 | SHA256:B3ED7C30FA127BDD226F2C967E8E480DE3D49A54086D1AE004C3A7E032989374 | |||
| 5140 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7C40.tmp.dmp | binary | |
MD5:8D5855DBE474B76D8D8A9A017491B29B | SHA256:3F12ED59ECA2A4857857A938A39C88197EDC3C503C4AC558CF195D2949939B50 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 162.159.130.233:443 | https://cdn.discordapp.com/attachments/1087906108909289586/1271905896473296896/nyxplayerbeta.vmp.exe?ex=66b90a2c&is=66b7b8ac&hm=8356c50086ce95b05afe436341b5c0d15294056dd51a984e09bf3d5a161497f7& | unknown | — | — | unknown |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/speedstarkawaii/nyx/main/nyxbeta.link | unknown | text | 194 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4064 | RUXIMICS.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
2120 | MoUsoCoreWorker.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6444 | Nyx.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
5796 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
cdn.discordapp.com |
| shared |
watson.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6444 | Nyx.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |