| File name: | dontrun.ps1 |
| Full analysis: | https://app.any.run/tasks/bc0b7f20-c4f6-44ef-ac42-5c366be0652c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 01:36:56 |
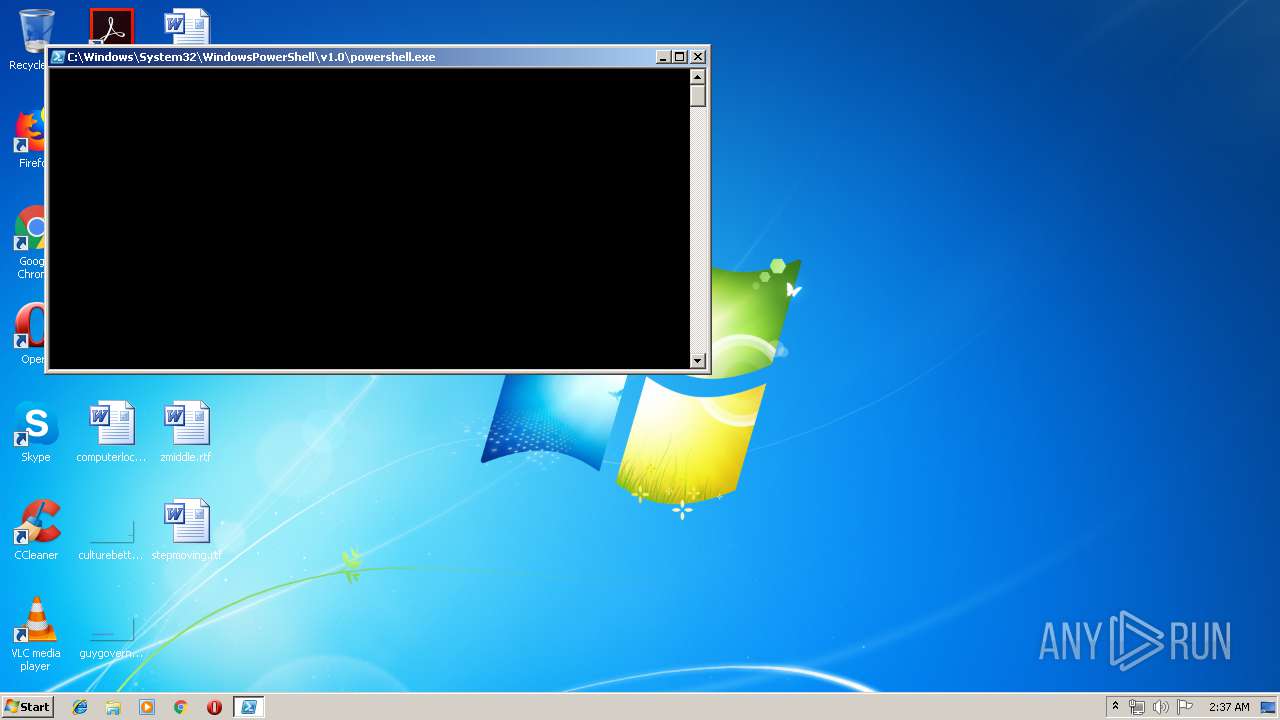
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 6AD2F0761DA9B6785288C8C40D58F047 |
| SHA1: | 17D8BB3BA1640F9C75E7E4B339EC0F598E830D61 |
| SHA256: | 2A4C30BFCEF64BC4C41B86866C9D61BFED9411121F2DA23BEAB10F9CCEBE1AC8 |
| SSDEEP: | 12:fDcecTDOOctZh4dcgo3AMoZ0u+vmocJUq/R+RIZoyBgmvfTyhl8fQDiran:7crTDOOcedcgowrCmoO8hyymvehmQDLn |
MALICIOUS
Application was dropped or rewritten from another process
- 235.exe (PID: 3668)
- soundser.exe (PID: 3008)
- soundser.exe (PID: 2344)
- 235.exe (PID: 3600)
- erb3BgsB1N8khltH3k.exe (PID: 3700)
- erb3BgsB1N8khltH3k.exe (PID: 3644)
- soundser.exe (PID: 3560)
- soundser.exe (PID: 3352)
Downloads executable files from the Internet
- powershell.exe (PID: 1892)
Emotet process was detected
- soundser.exe (PID: 3008)
- soundser.exe (PID: 3560)
EMOTET was detected
- soundser.exe (PID: 2344)
- soundser.exe (PID: 3352)
Connects to CnC server
- soundser.exe (PID: 2344)
- soundser.exe (PID: 3352)
Changes the autorun value in the registry
- soundser.exe (PID: 2344)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1892)
- 235.exe (PID: 3668)
- soundser.exe (PID: 2344)
- erb3BgsB1N8khltH3k.exe (PID: 3644)
Creates files in the user directory
- powershell.exe (PID: 1892)
Starts itself from another location
- 235.exe (PID: 3668)
- erb3BgsB1N8khltH3k.exe (PID: 3644)
Connects to server without host name
- soundser.exe (PID: 2344)
- soundser.exe (PID: 3352)
Application launched itself
- soundser.exe (PID: 3560)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
9
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1892 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\dontrun.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 235.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3352 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3560 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | erb3BgsB1N8khltH3k.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\235.exe" | C:\Users\admin\235.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3644 | --d45c70d9 | C:\Users\admin\AppData\Local\soundser\erb3BgsB1N8khltH3k.exe | erb3BgsB1N8khltH3k.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3668 | --ebe2cb72 | C:\Users\admin\235.exe | 235.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\soundser\erb3BgsB1N8khltH3k.exe" | C:\Users\admin\AppData\Local\soundser\erb3BgsB1N8khltH3k.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
616
Read events
528
Write events
88
Delete events
0
Modification events
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EW722YM7E7GDIWD5CE72.temp | — | |
MD5:— | SHA256:— | |||
| 3668 | 235.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 2344 | soundser.exe | C:\Users\admin\AppData\Local\soundser\erb3BgsB1N8khltH3k.exe | executable | |
MD5:— | SHA256:— | |||
| 1892 | powershell.exe | C:\Users\admin\235.exe | executable | |
MD5:— | SHA256:— | |||
| 1892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF133de7.TMP | binary | |
MD5:— | SHA256:— | |||
| 1892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3644 | erb3BgsB1N8khltH3k.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1892 | powershell.exe | GET | 200 | 99.198.101.186:80 | http://riversoftbd.com/wp-content/vFikaQjYg/ | US | executable | 74.5 Kb | suspicious |
2344 | soundser.exe | POST | 200 | 200.85.46.122:80 | http://200.85.46.122/schema/site/ | PY | binary | 65.8 Kb | malicious |
3352 | soundser.exe | POST | — | 200.85.46.122:80 | http://200.85.46.122/cab/enabled/ringin/merge/ | PY | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1892 | powershell.exe | 99.198.101.186:80 | riversoftbd.com | SingleHop, Inc. | US | suspicious |
2344 | soundser.exe | 200.85.46.122:80 | — | Telecel S.A. | PY | malicious |
— | — | 200.85.46.122:80 | — | Telecel S.A. | PY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
riversoftbd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1892 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1892 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1892 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2344 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3352 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report