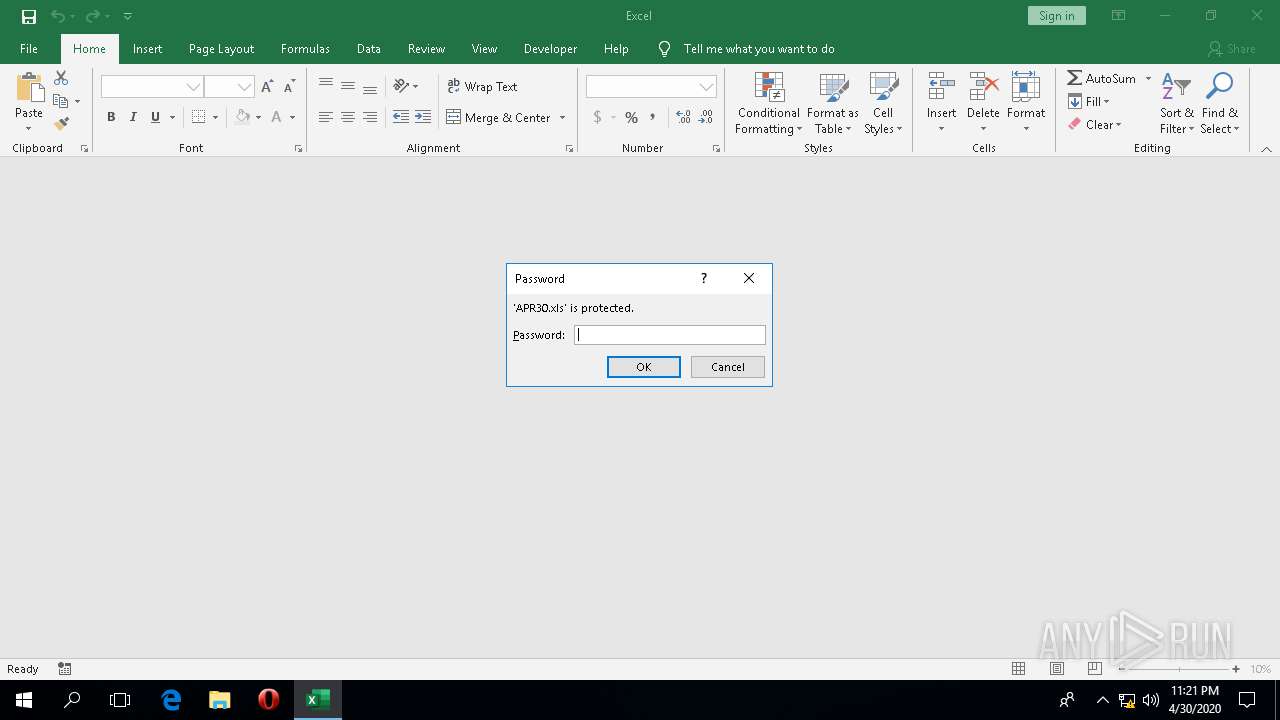
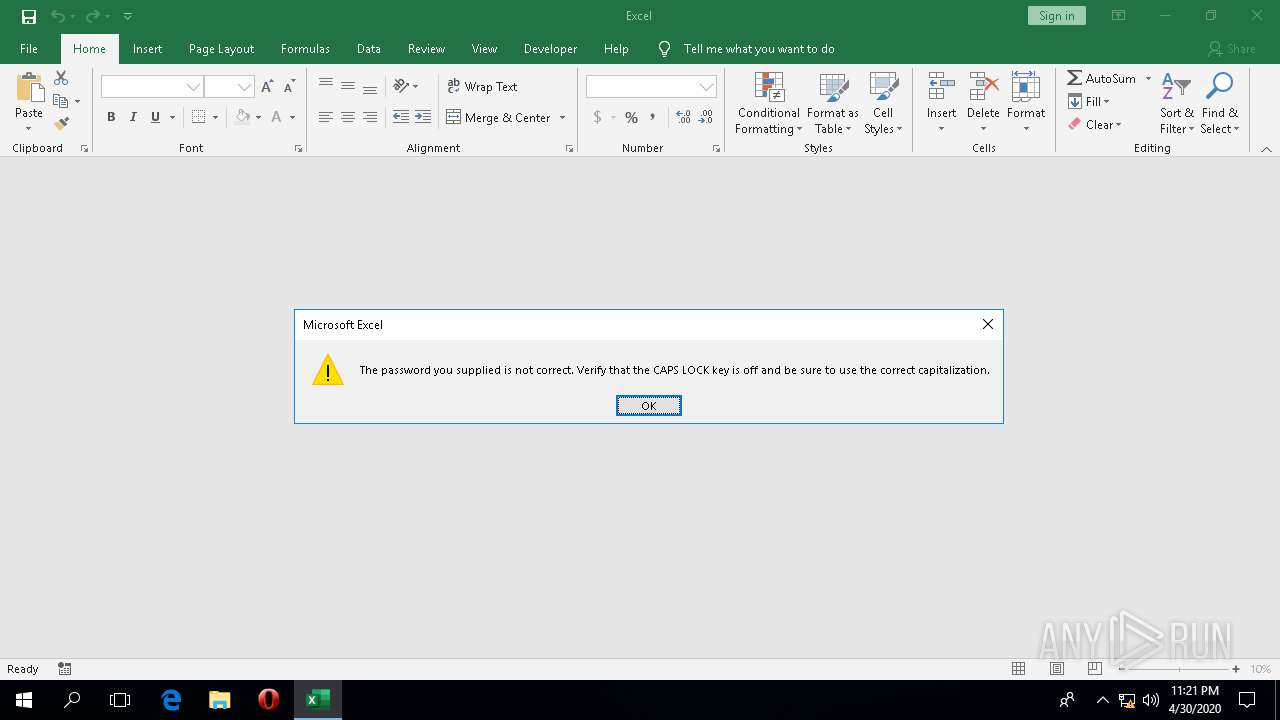
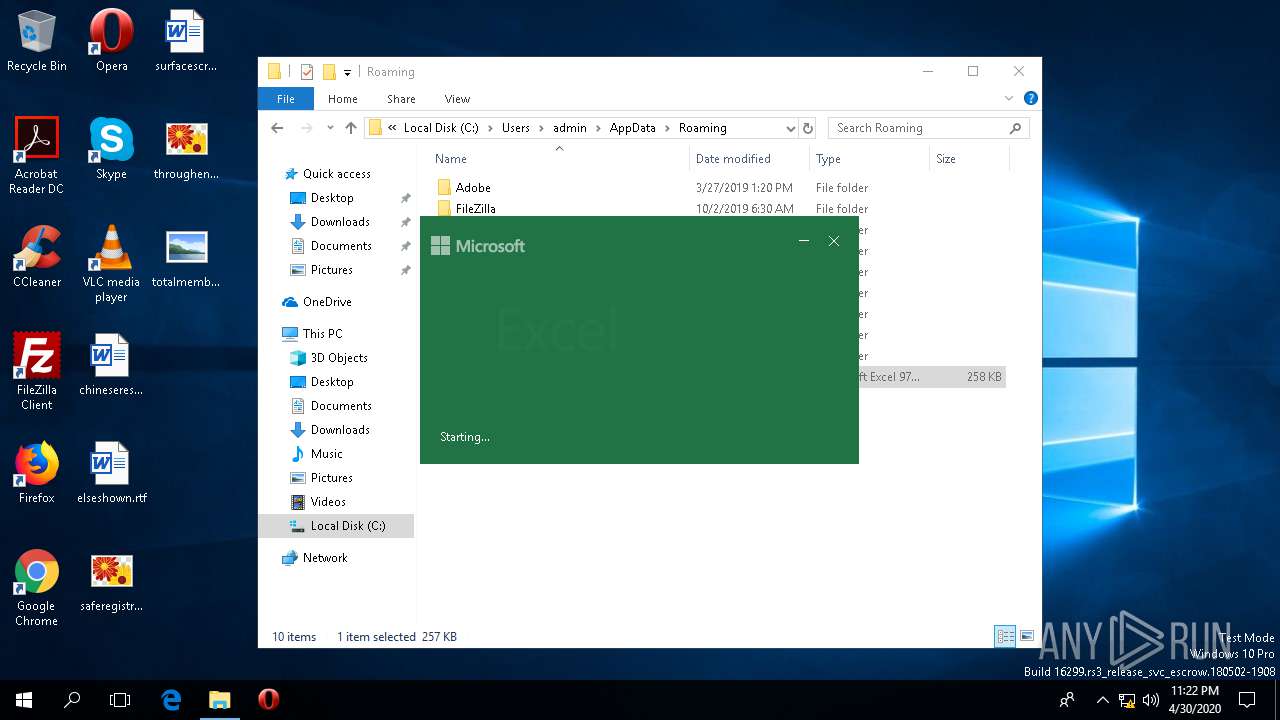
| File name: | APR30.xls |
| Full analysis: | https://app.any.run/tasks/8e5c3b0d-8f99-488e-a1b8-c60f588e2741 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2020, 23:20:46 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, Code page: 1251, Name of Creating Application: Microsoft Excel, Create Time/Date: Tue Mar 31 16:25:34 2020, Last Saved Time/Date: Tue Mar 31 16:39:43 2020, Security: 1 |
| MD5: | 9F4E918894AC6F97A2E66505CCD08070 |
| SHA1: | DC15BBCFA38CCFE7E9E90D2DFFDB3EBCBAAD93AD |
| SHA256: | 2A39FC9B7DEA58C26A2C6CCE253661DFE64C11D4F6BCCB8868B5B4CD4BDEBDB4 |
| SSDEEP: | 6144:eqB5XUGqkEFiY/A4Vfx0O3vP5JgoxXMwIbgPqo:eq3UD7FiNq0O3JtYbgyo |
MALICIOUS
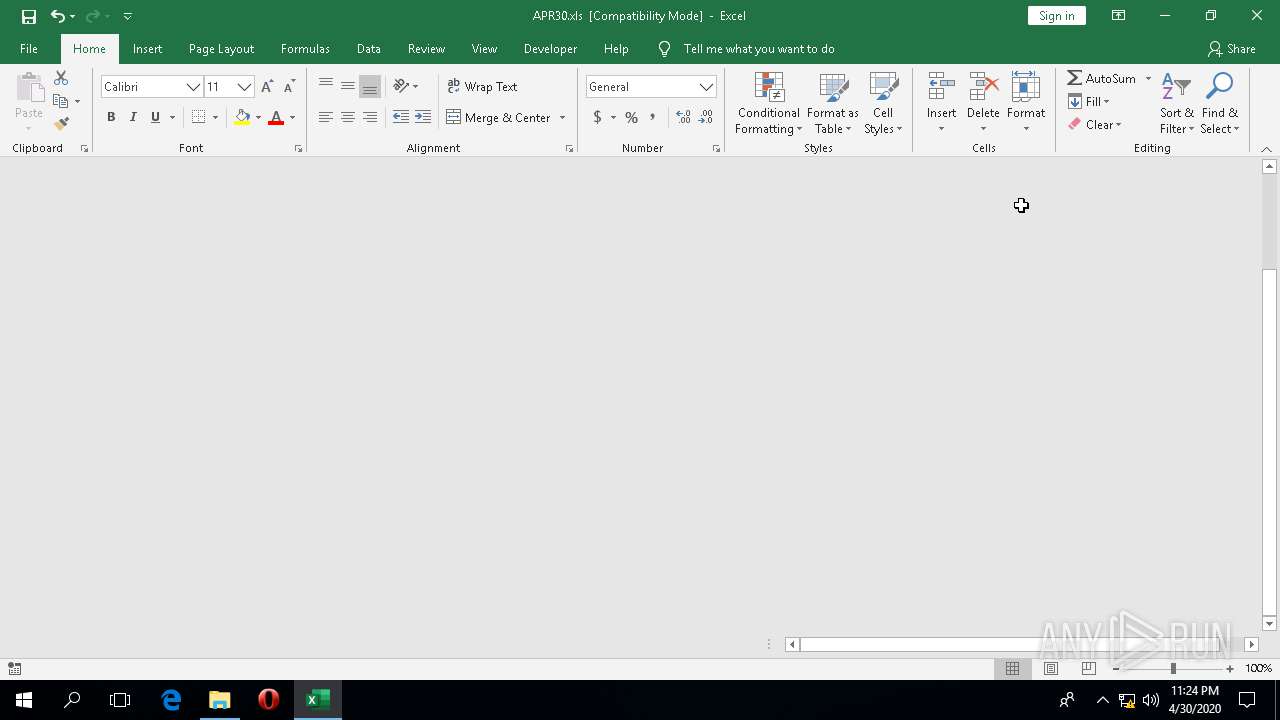
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1920)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1920)
Known privilege escalation attack
- DllHost.exe (PID: 1328)
Loads the Task Scheduler COM API
- wermgr.exe (PID: 2696)
Loads the Task Scheduler DLL interface
- wermgr.exe (PID: 2696)
Actions looks like stealing of personal data
- wermgr.exe (PID: 2696)
Connects to CnC server
- wermgr.exe (PID: 2696)
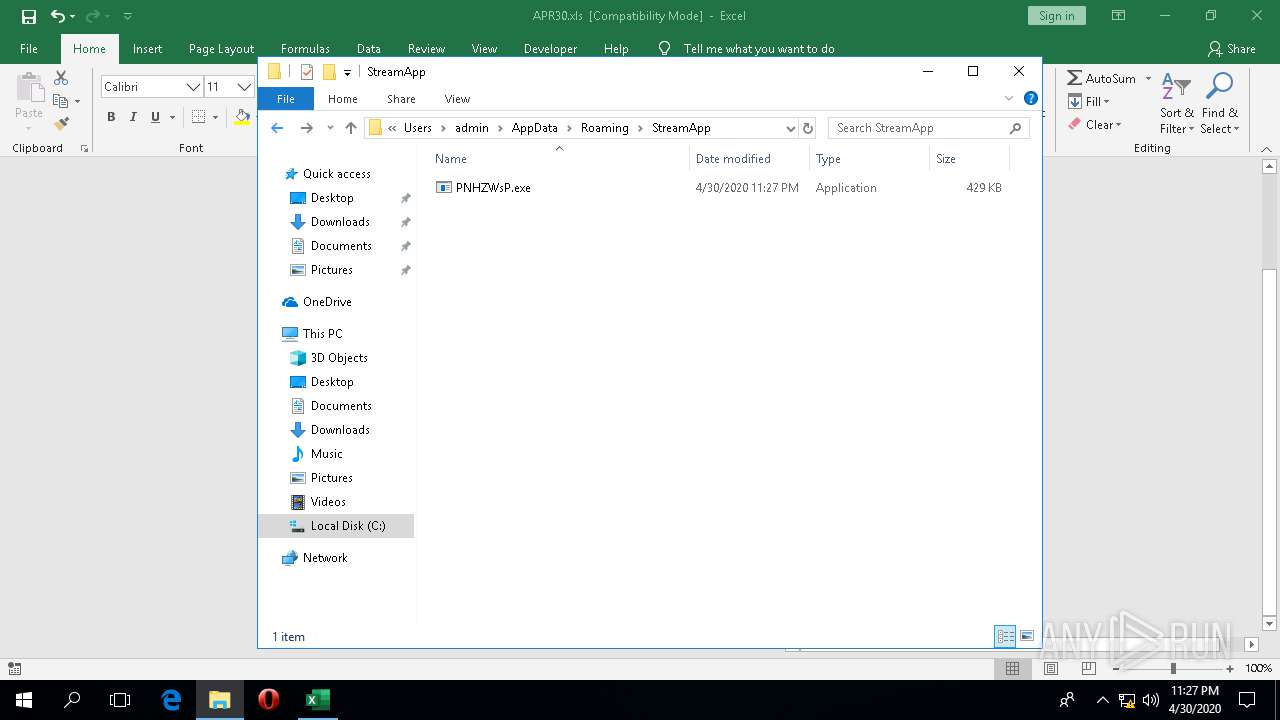
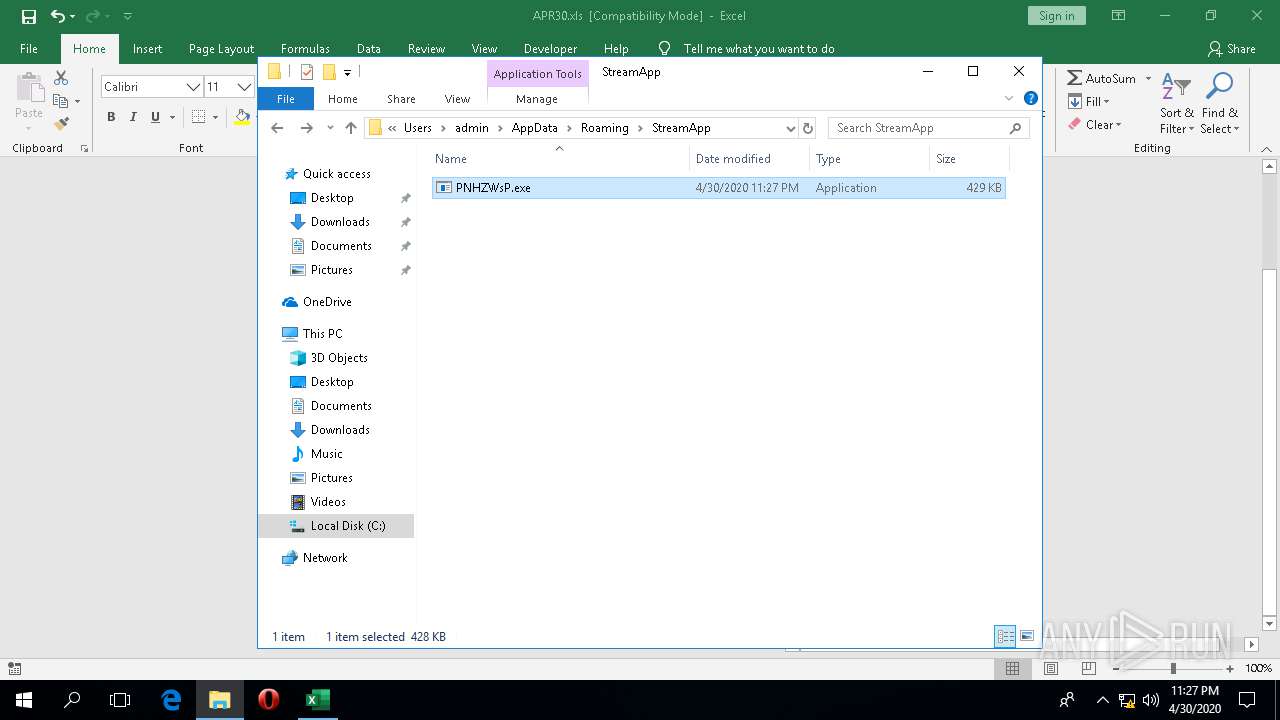
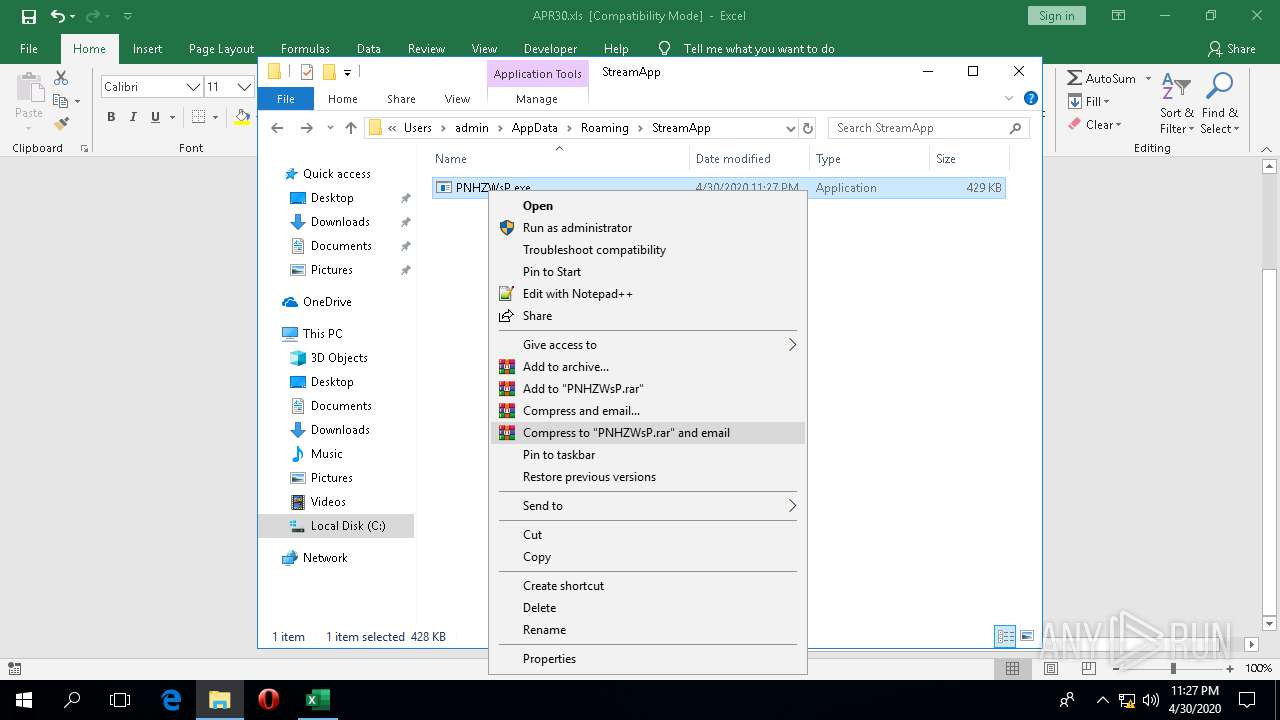
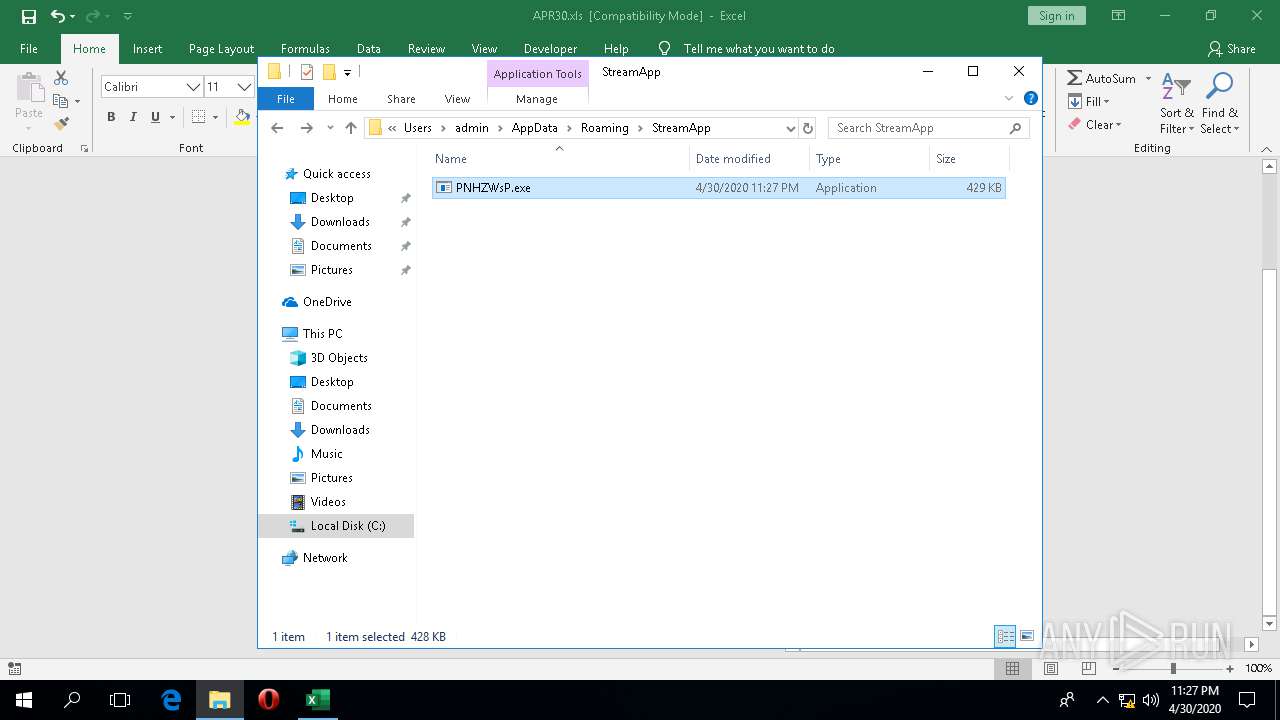
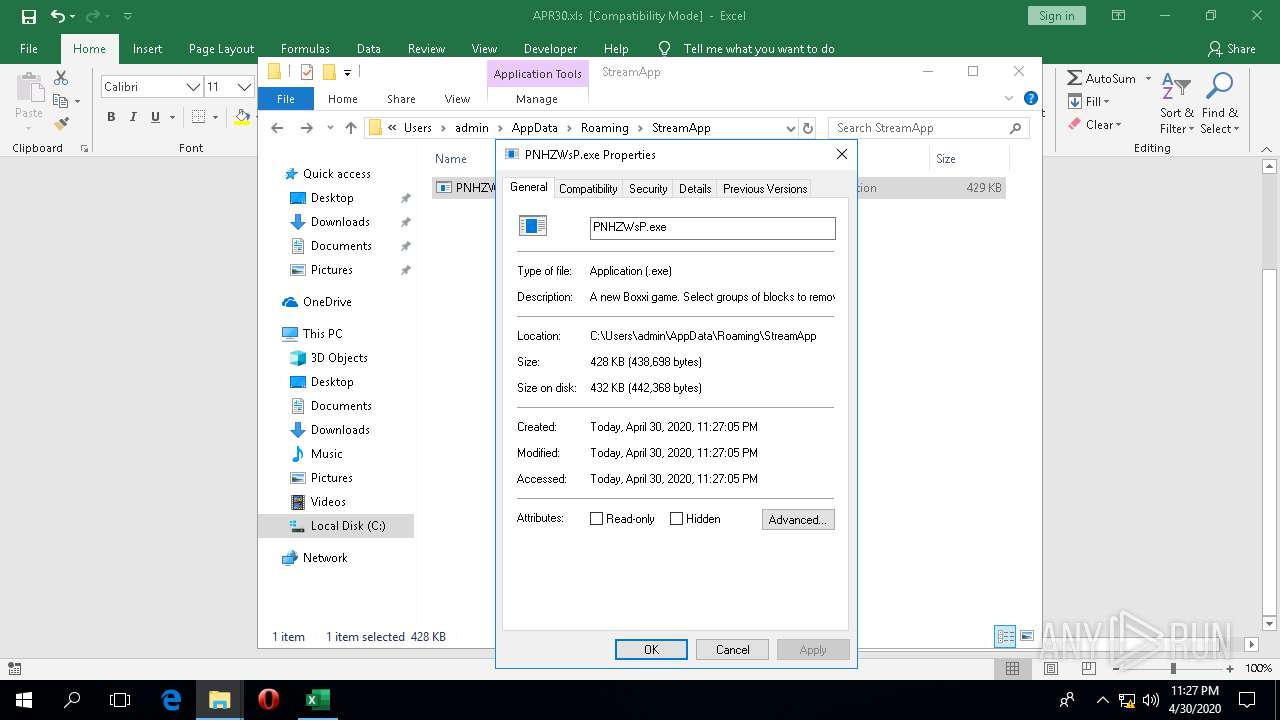
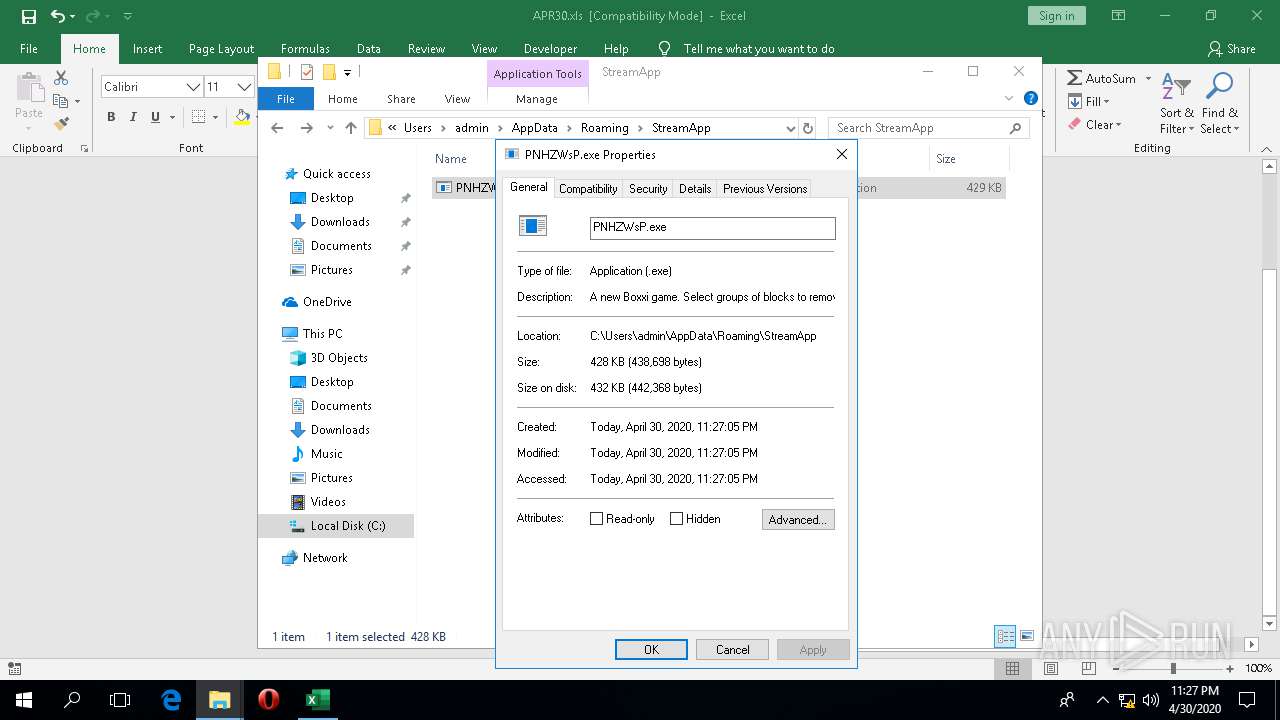
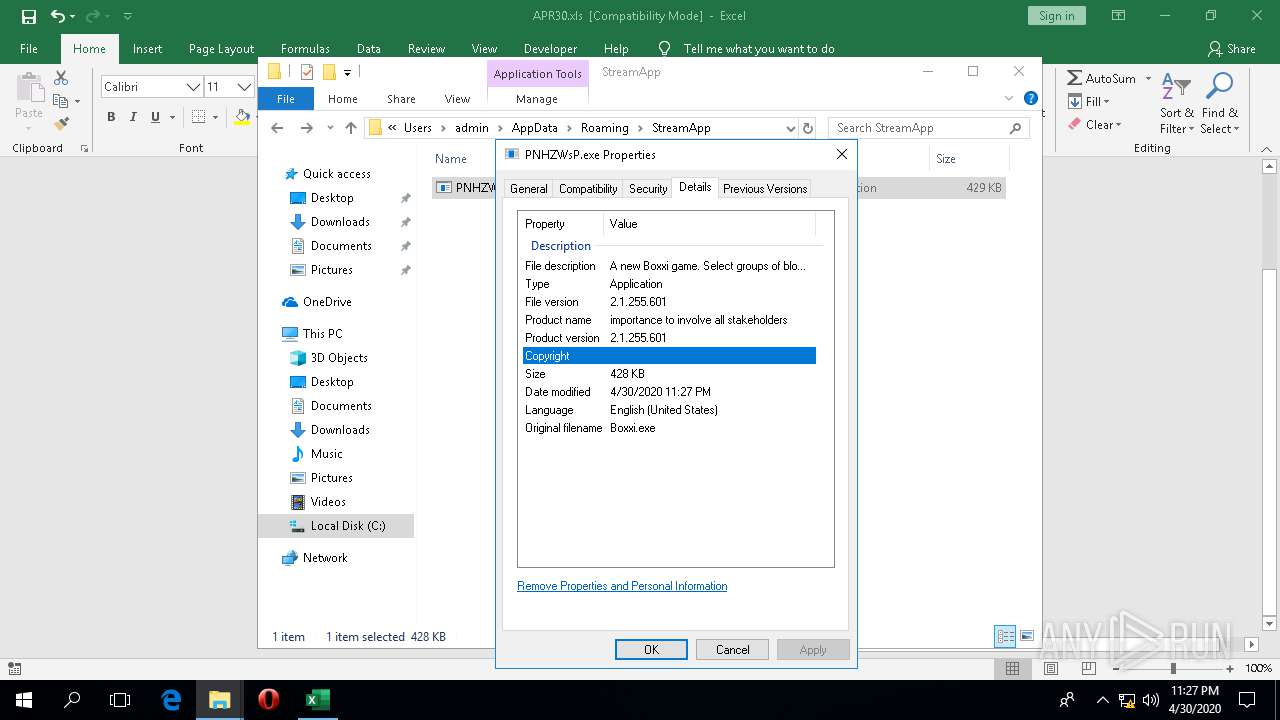
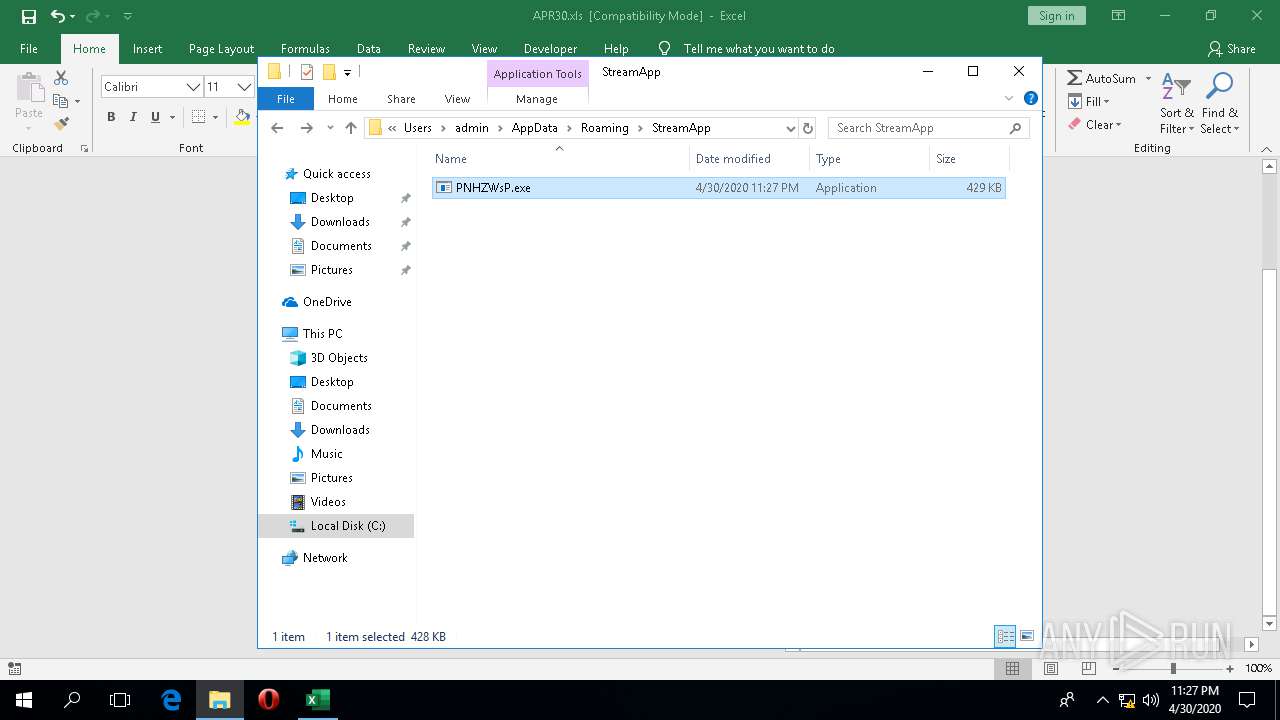
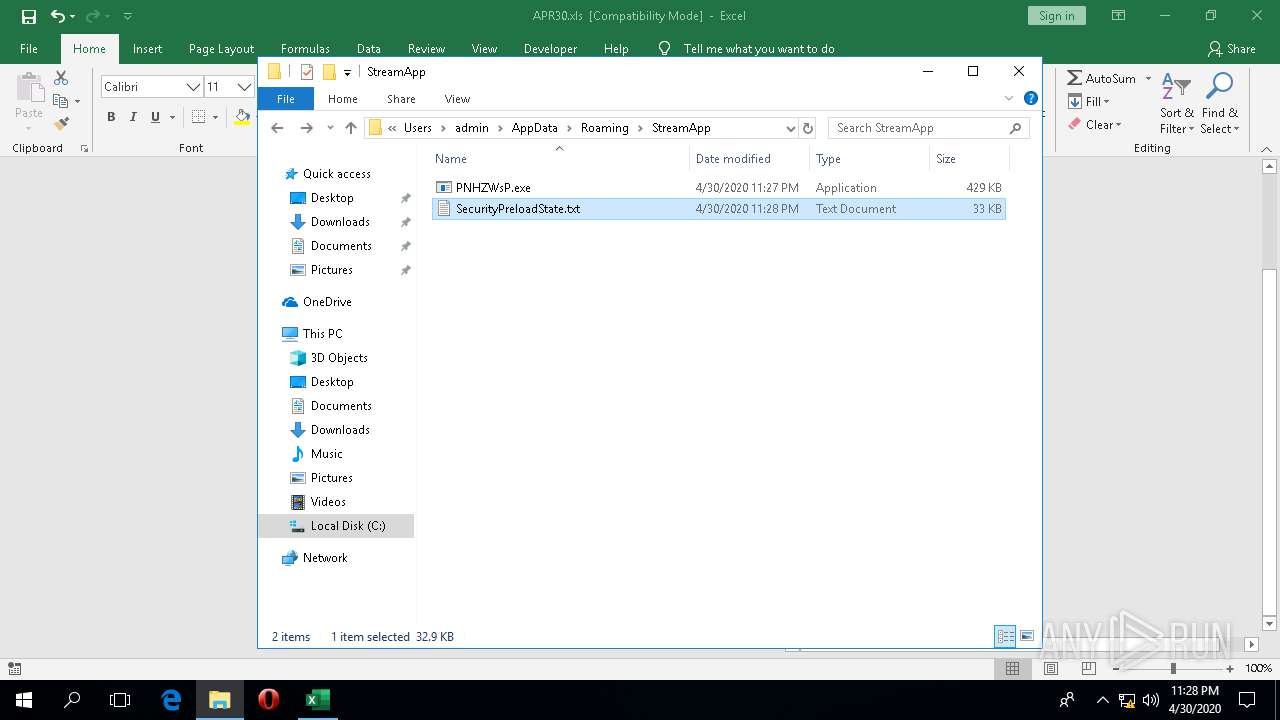
Application was dropped or rewritten from another process
- PNHZWsP.exe (PID: 5180)
- PNHZWsP.exe (PID: 4704)
SUSPICIOUS
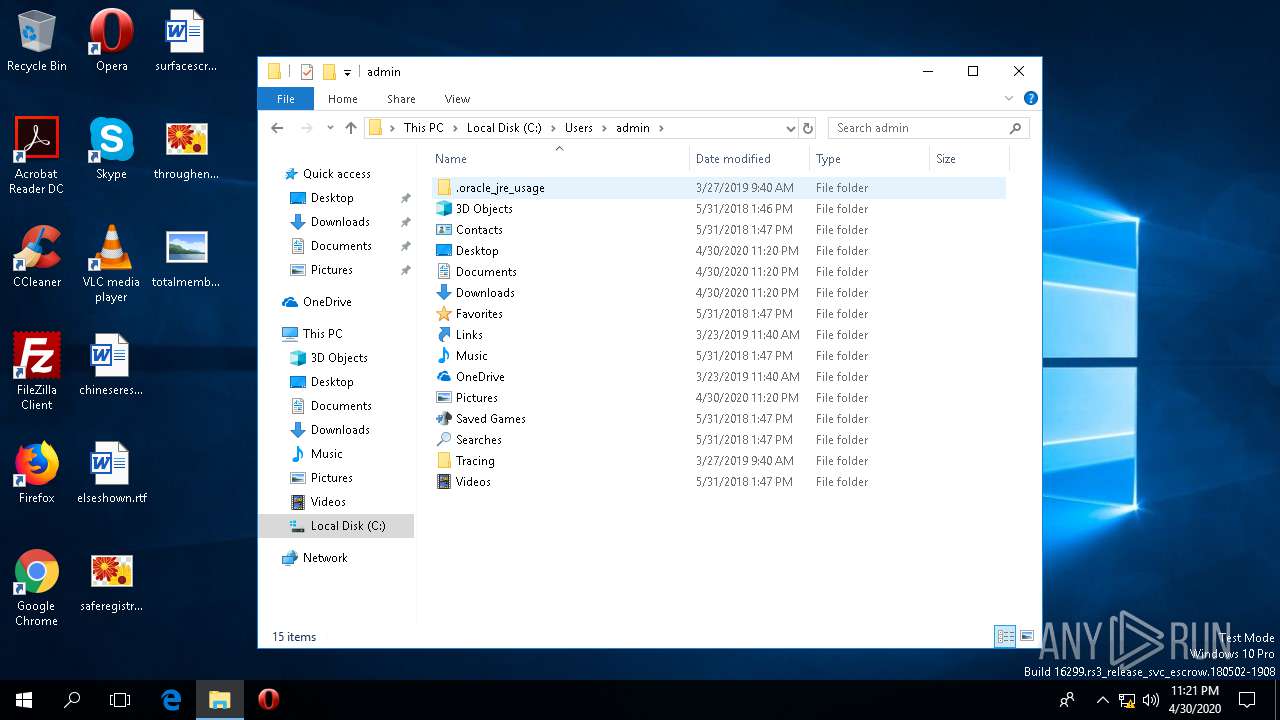
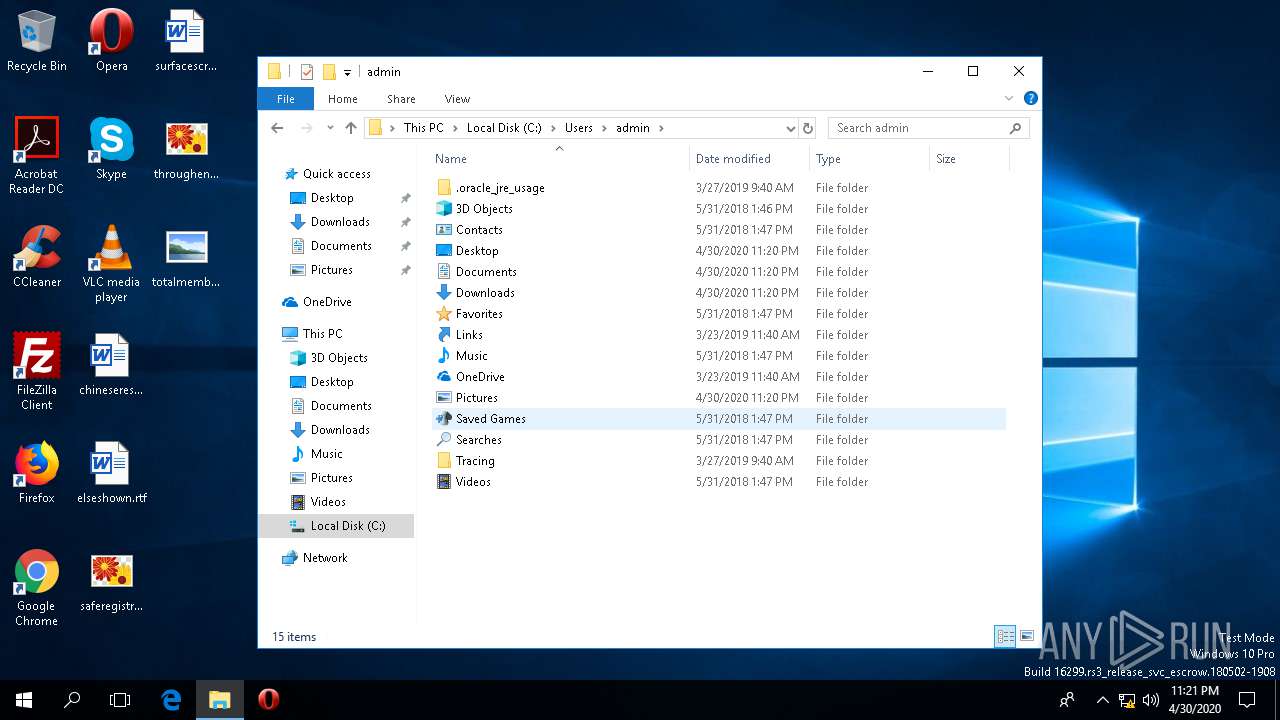
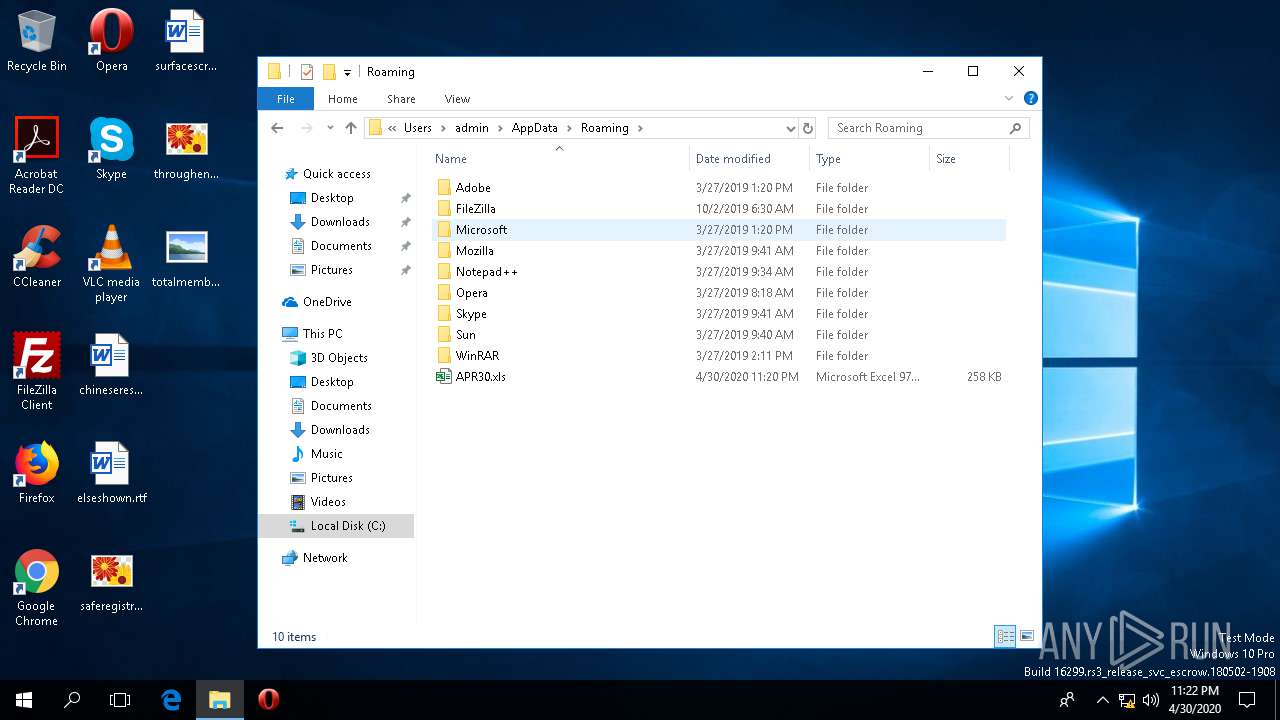
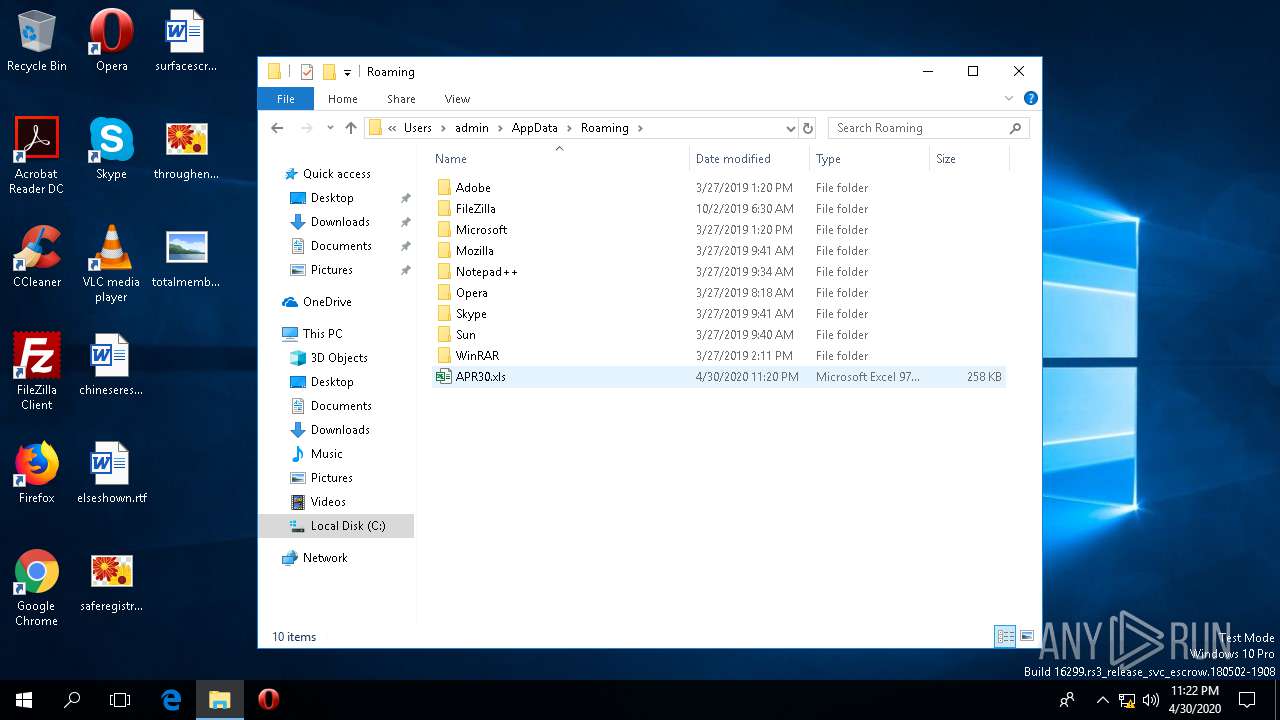
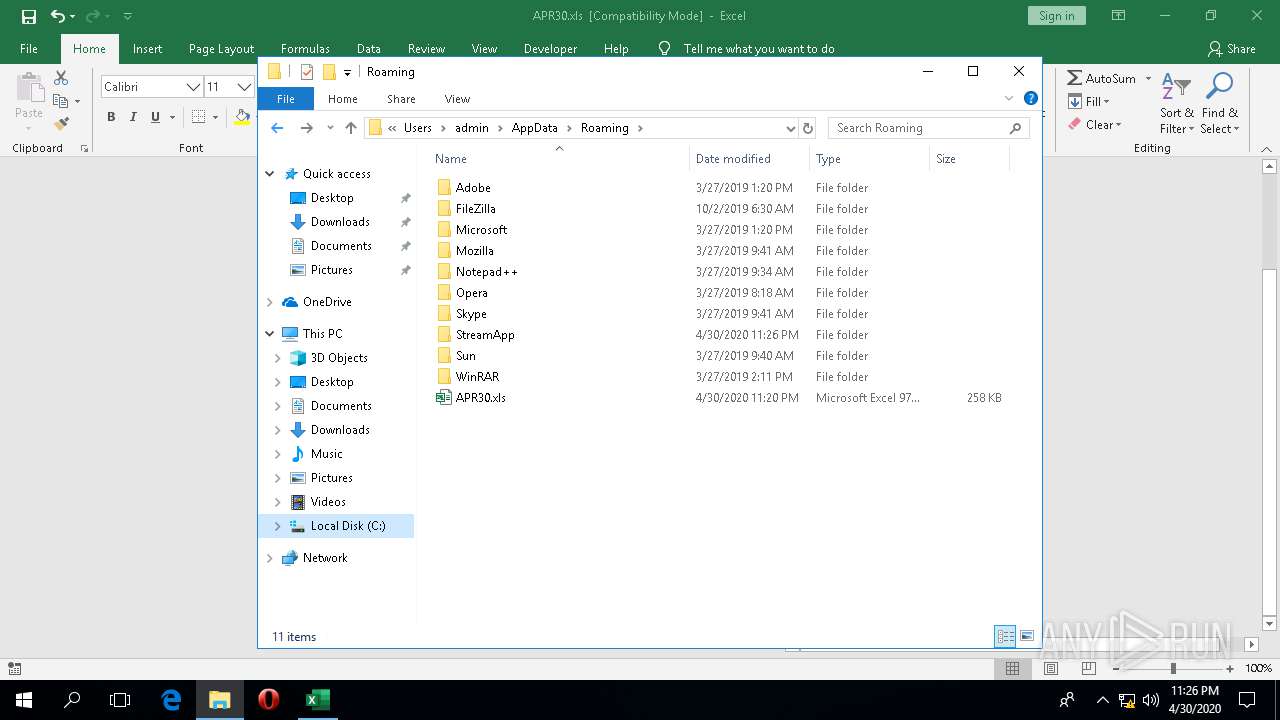
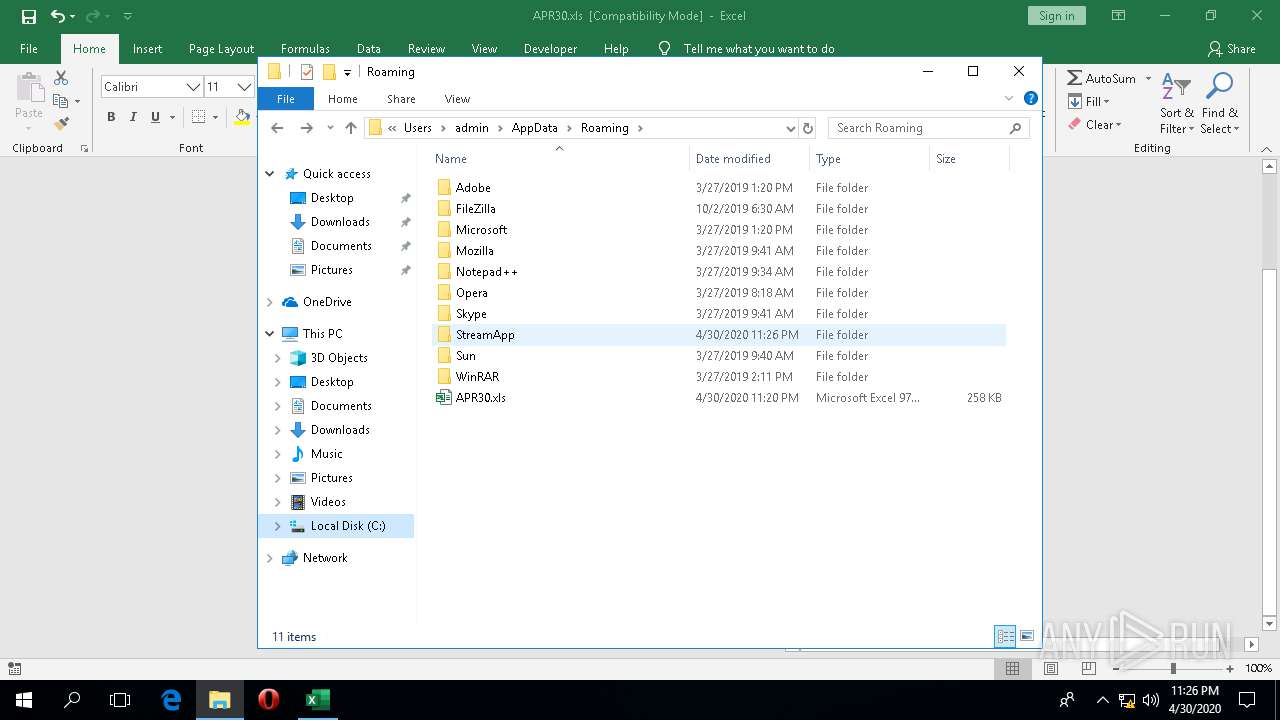
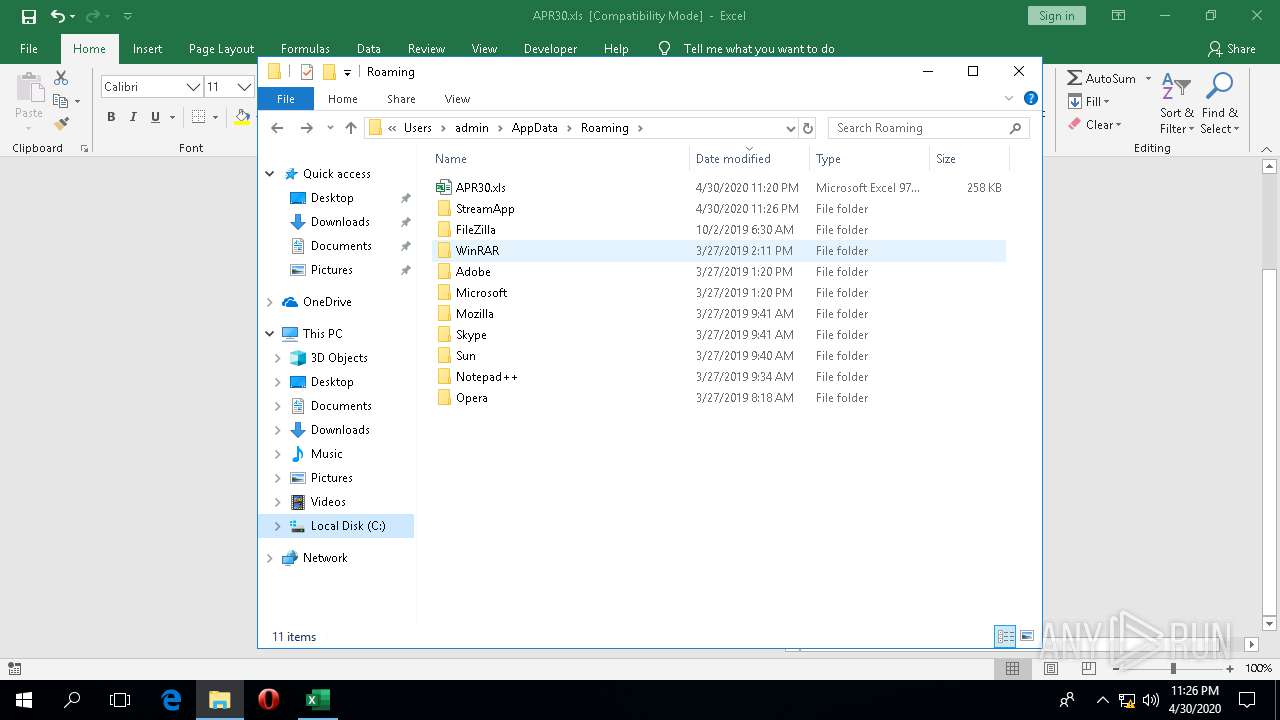
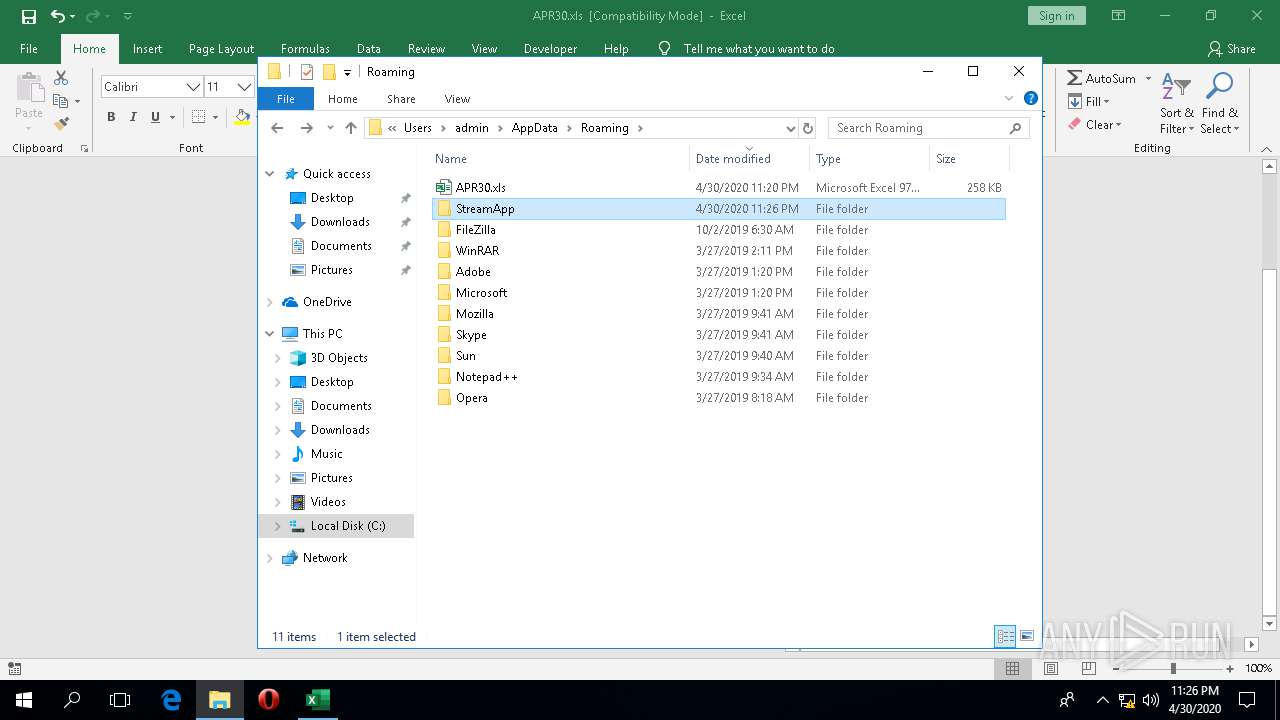
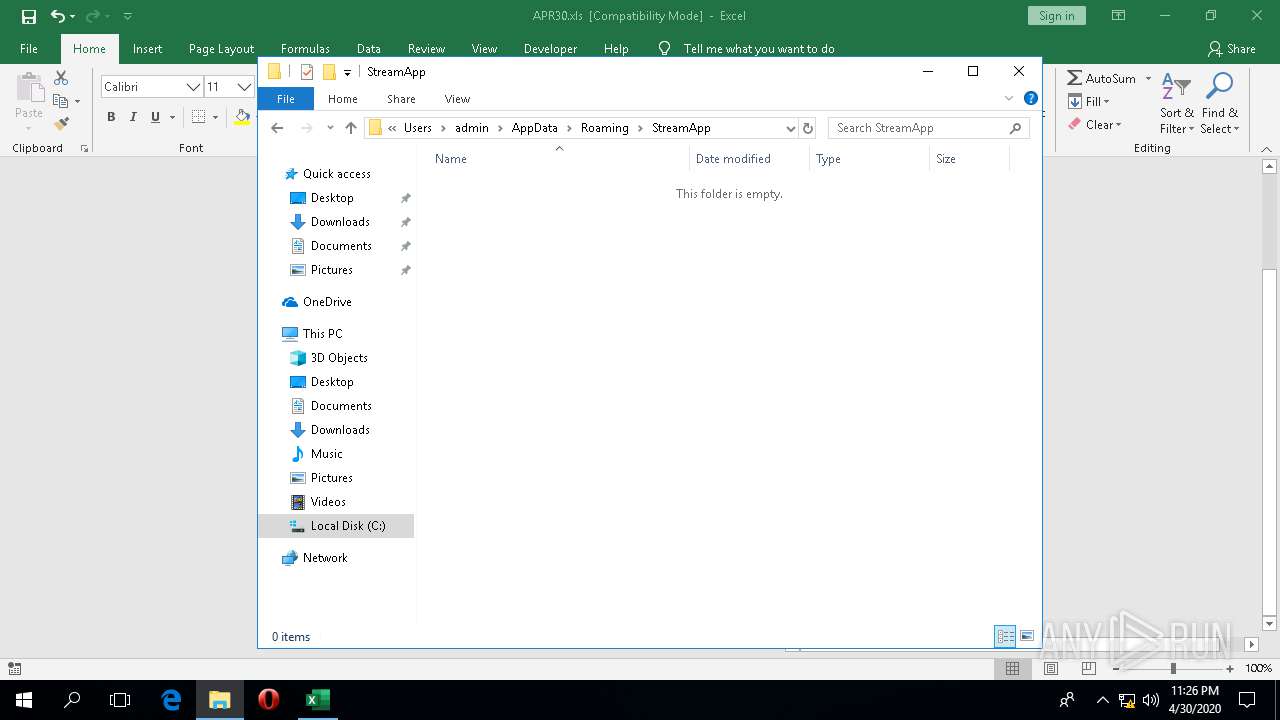
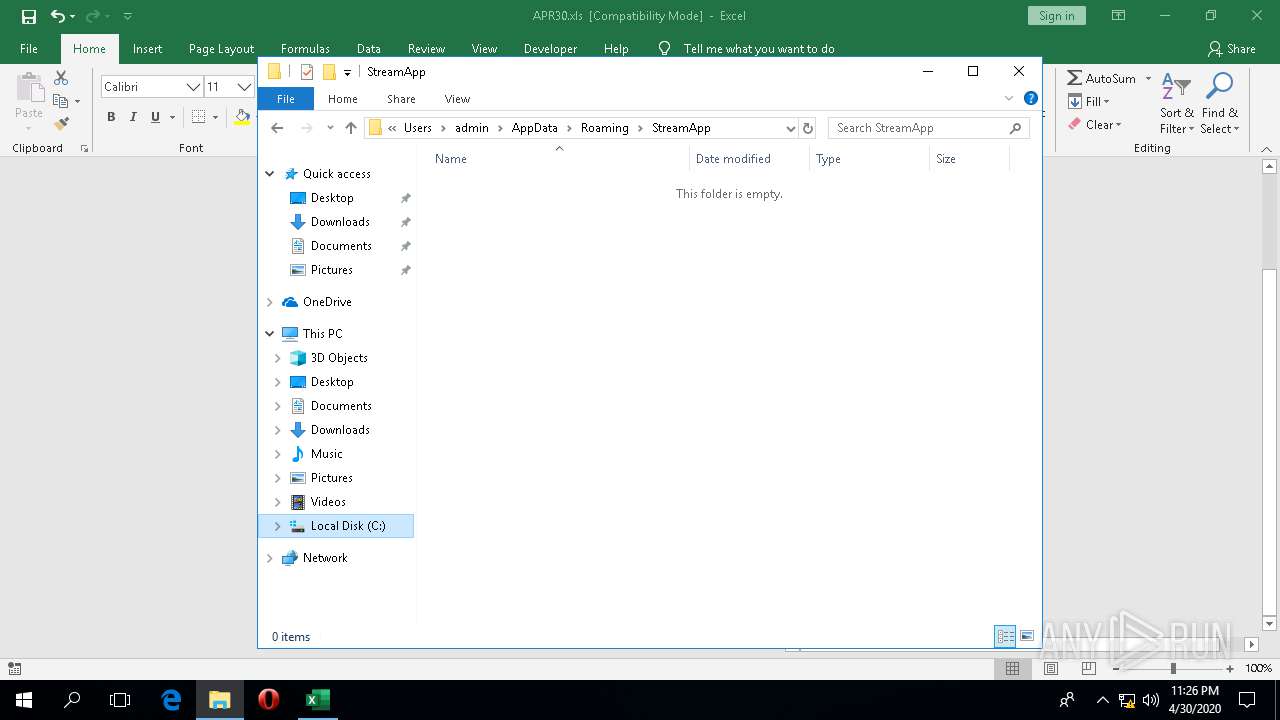
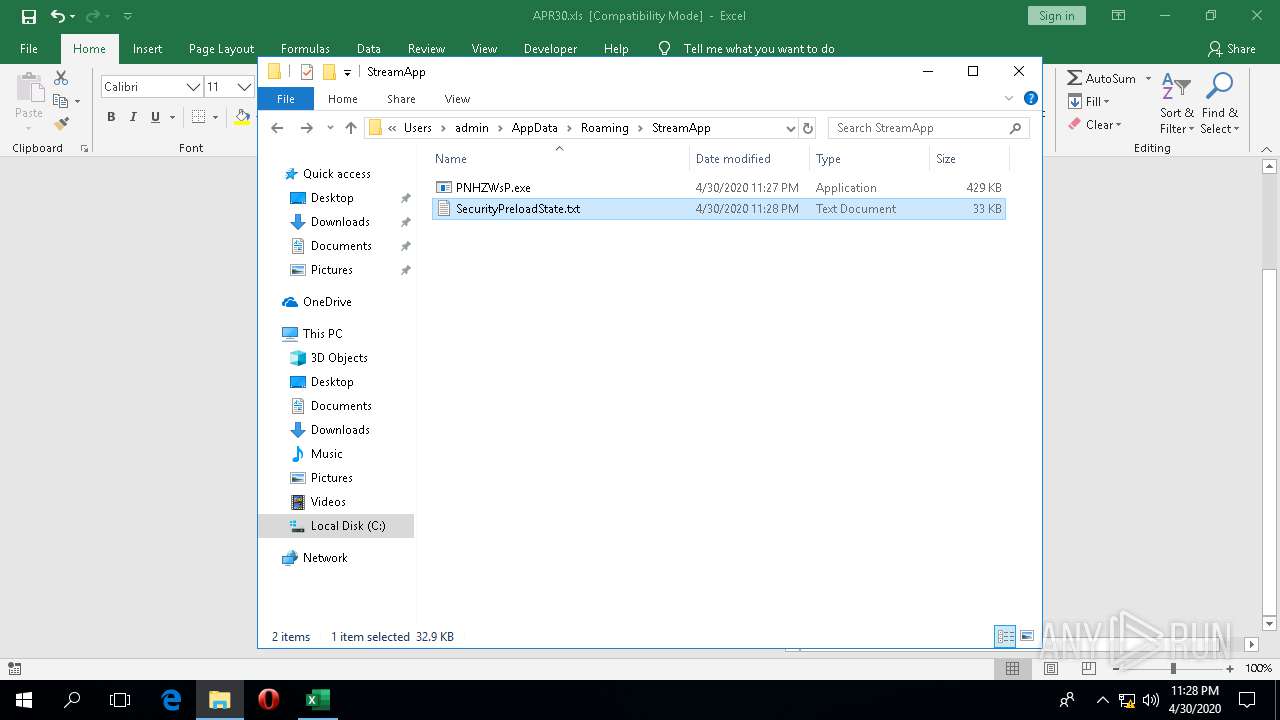
Creates files in the user directory
- wermgr.exe (PID: 2696)
- SystemSettings.exe (PID: 2332)
Executed via COM
- rundll32.exe (PID: 6088)
- ApplicationFrameHost.exe (PID: 1368)
- RuntimeBroker.exe (PID: 5216)
- backgroundTaskHost.exe (PID: 1208)
- SpeechRuntime.exe (PID: 4748)
- SystemSettings.exe (PID: 2332)
- DllHost.exe (PID: 1328)
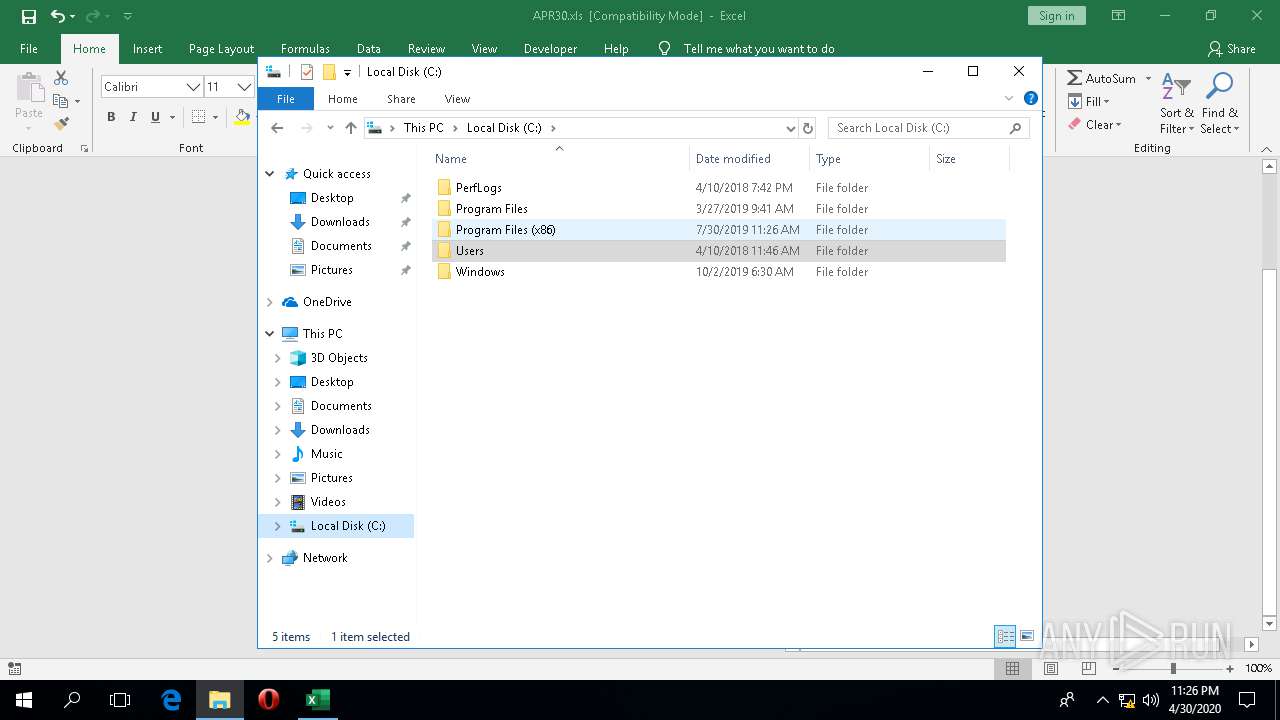
Creates files in the program directory
- EXCEL.EXE (PID: 1920)
Executable content was dropped or overwritten
- wermgr.exe (PID: 2696)
Checks supported languages
- SystemSettings.exe (PID: 2332)
- backgroundTaskHost.exe (PID: 1208)
Reads the machine GUID from the registry
- backgroundTaskHost.exe (PID: 1208)
- SpeechRuntime.exe (PID: 4748)
- wermgr.exe (PID: 2696)
INFO
Reads Environment values
- EXCEL.EXE (PID: 4336)
- EXCEL.EXE (PID: 1920)
Manual execution by user
- EXCEL.EXE (PID: 1920)
- NOTEPAD.EXE (PID: 5152)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 4336)
- EXCEL.EXE (PID: 1920)
Scans artifacts that could help determine the target
- EXCEL.EXE (PID: 4336)
- EXCEL.EXE (PID: 1920)
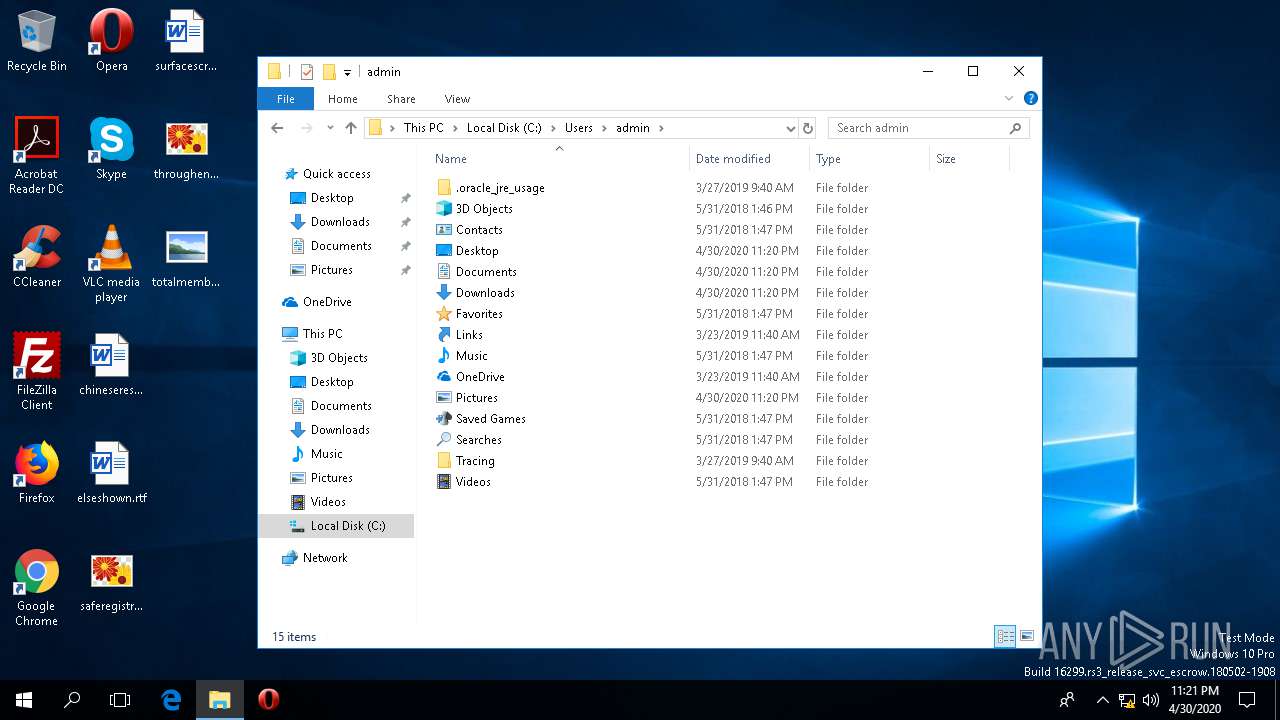
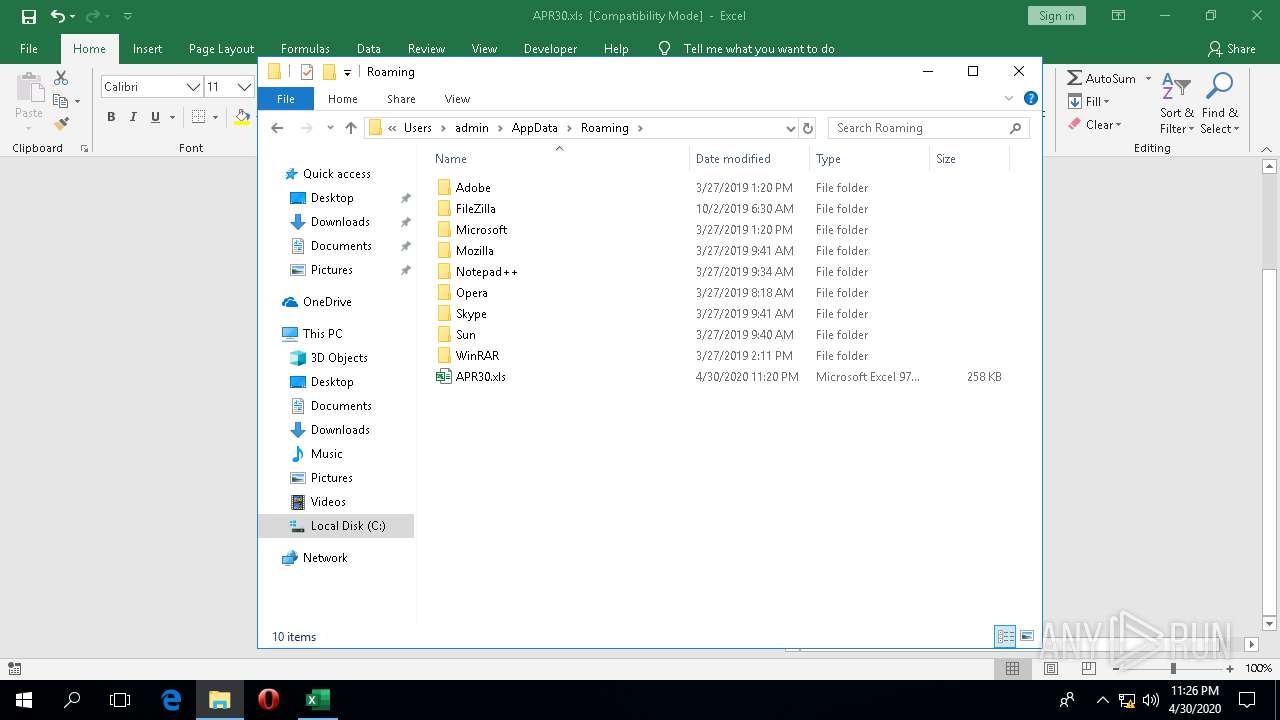
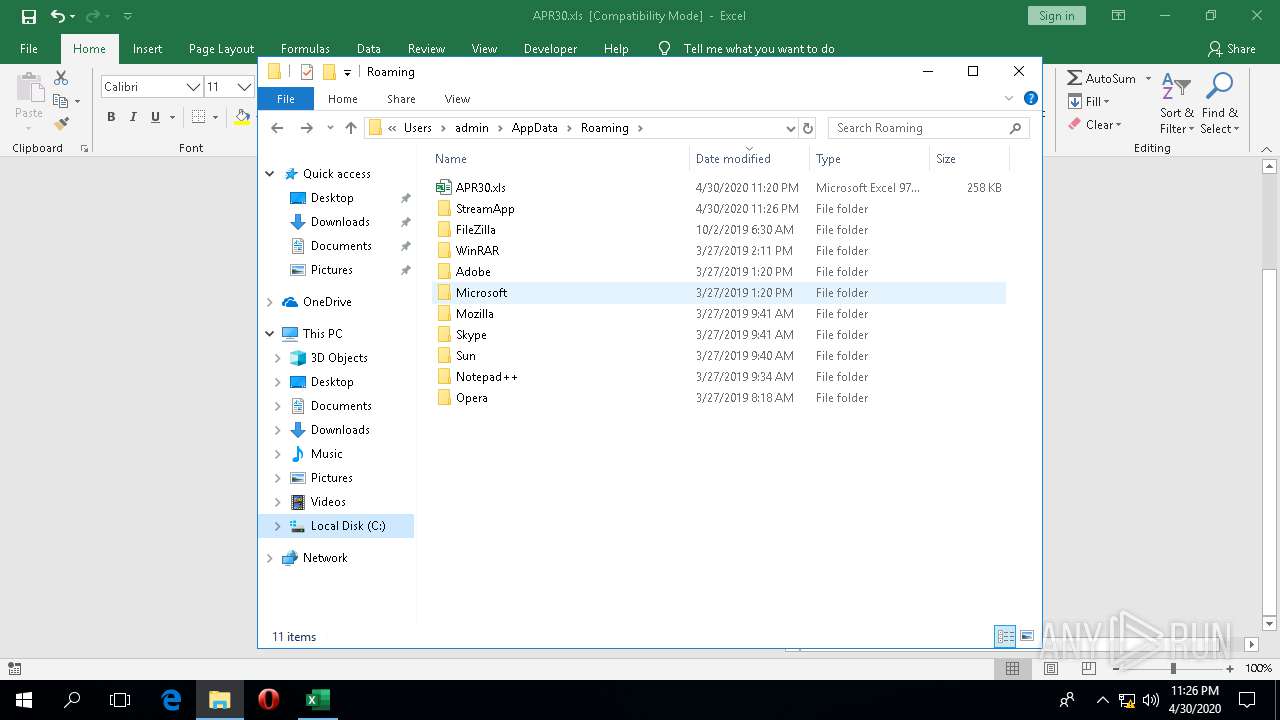
Creates files in the user directory
- EXCEL.EXE (PID: 1920)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 4336)
- EXCEL.EXE (PID: 1920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2020:04:30 15:25:34 |
| ModifyDate: | 2020:04:30 15:39:43 |
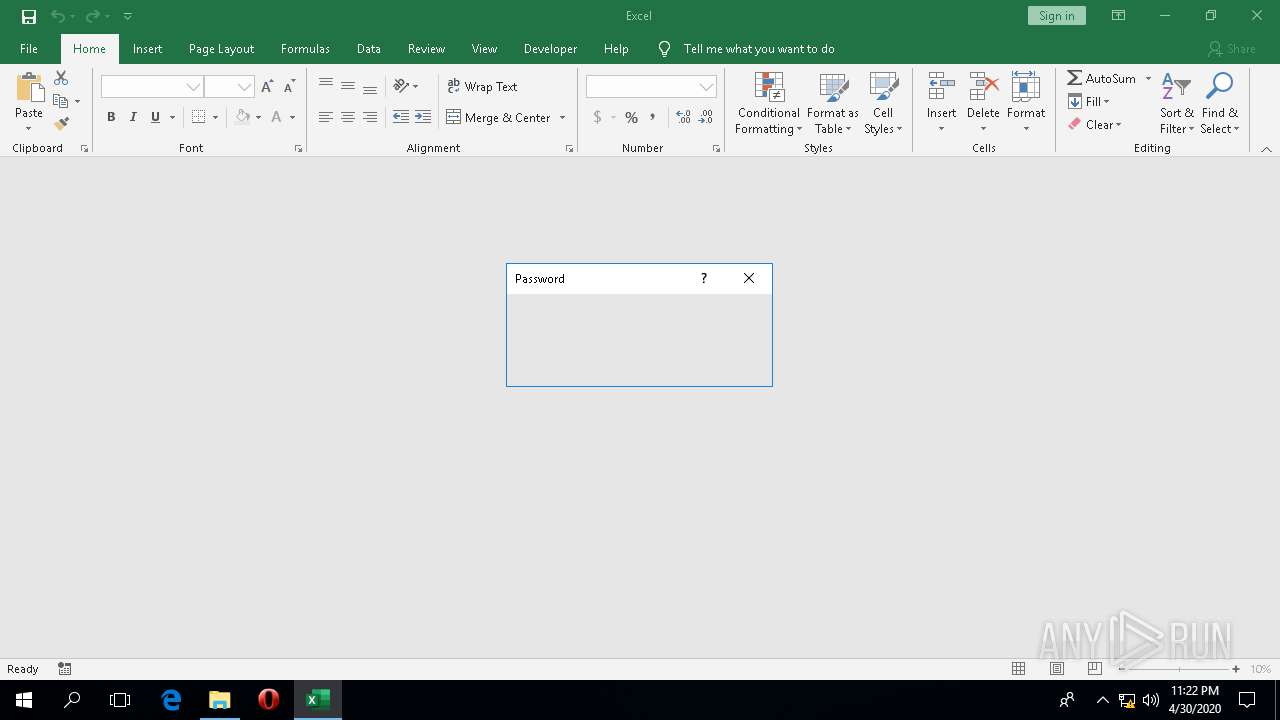
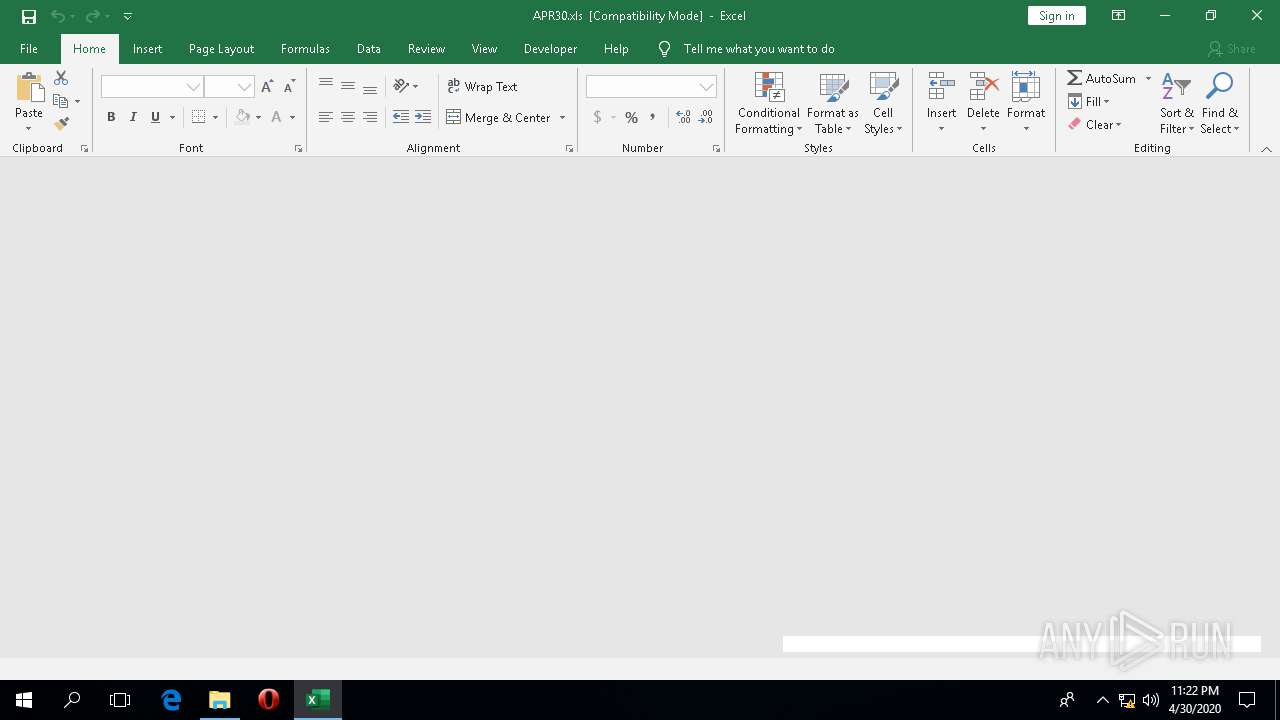
| Security: | Password protected |
| CodePage: | Windows Cyrillic |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
106
Monitored processes
13
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\WINDOWS\system32\backgroundTaskHost.exe" -ServerName:CortanaUI.AppXy7vb4pc2dr3kc93kfc509b1d0arkfb2x.mca | C:\WINDOWS\system32\backgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\WINDOWS\SysWOW64\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1368 | C:\WINDOWS\system32\ApplicationFrameHost.exe -Embedding | C:\WINDOWS\system32\ApplicationFrameHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Application Frame Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
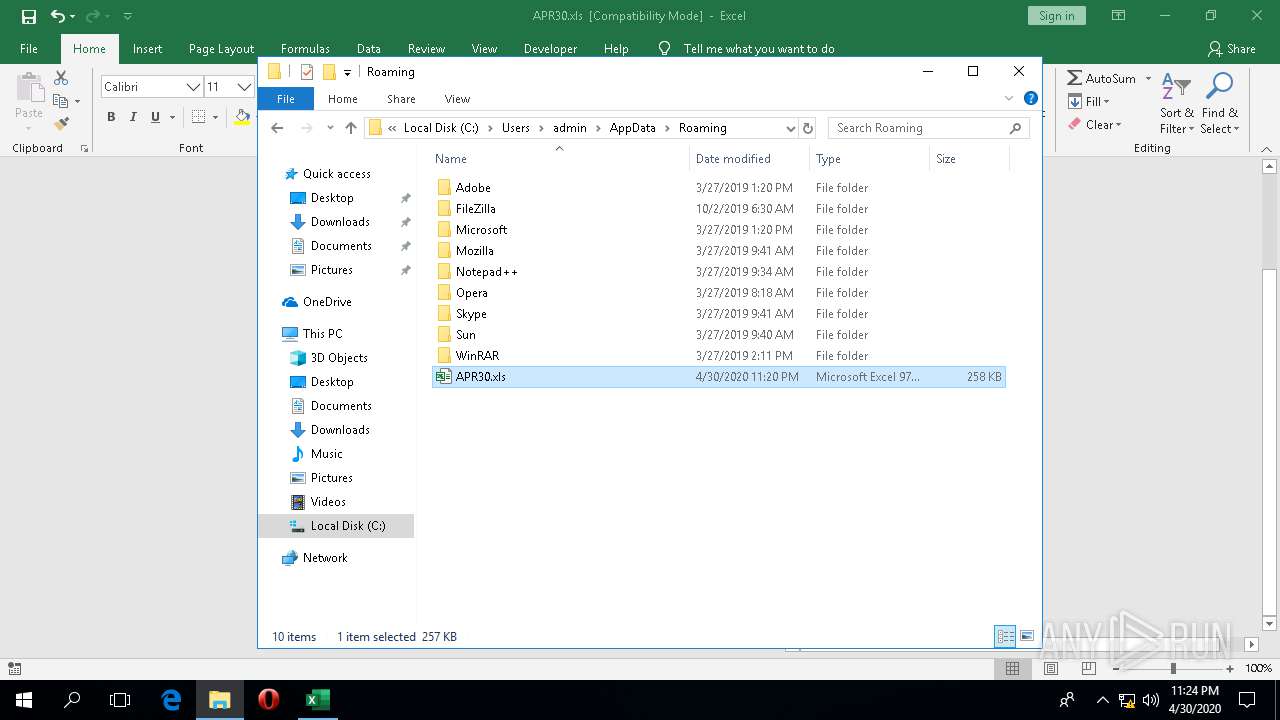
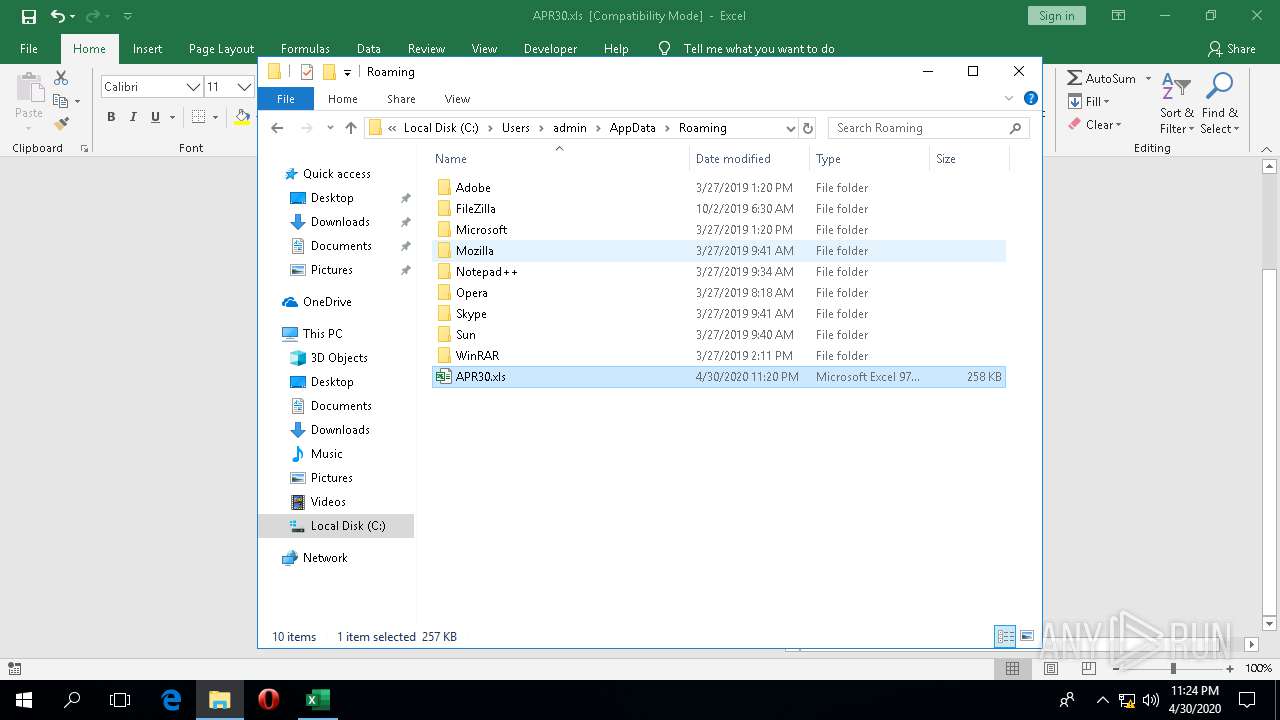
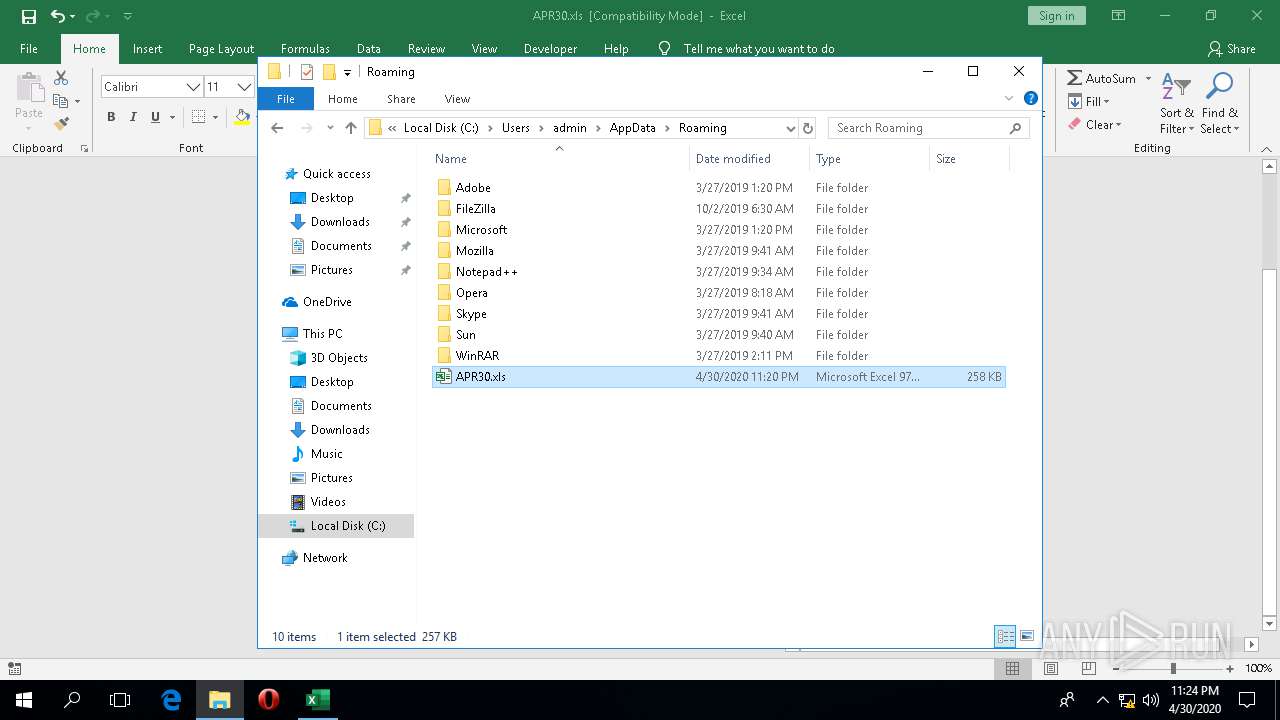
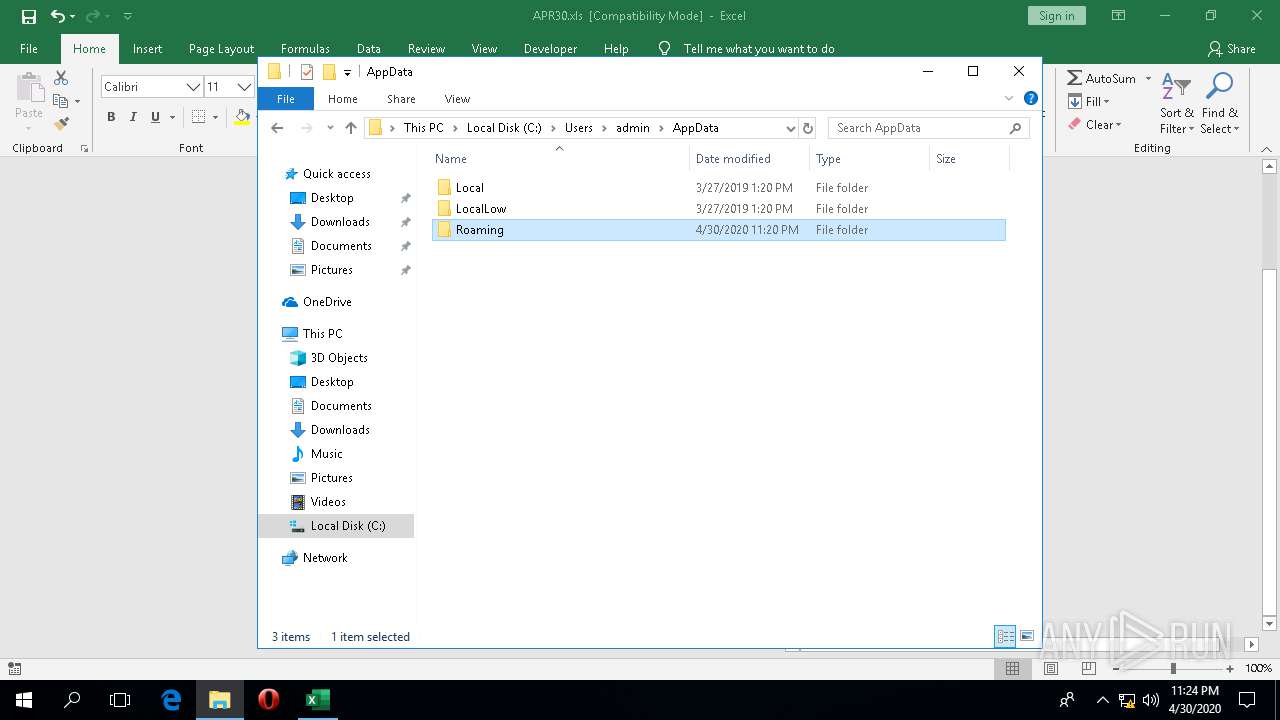
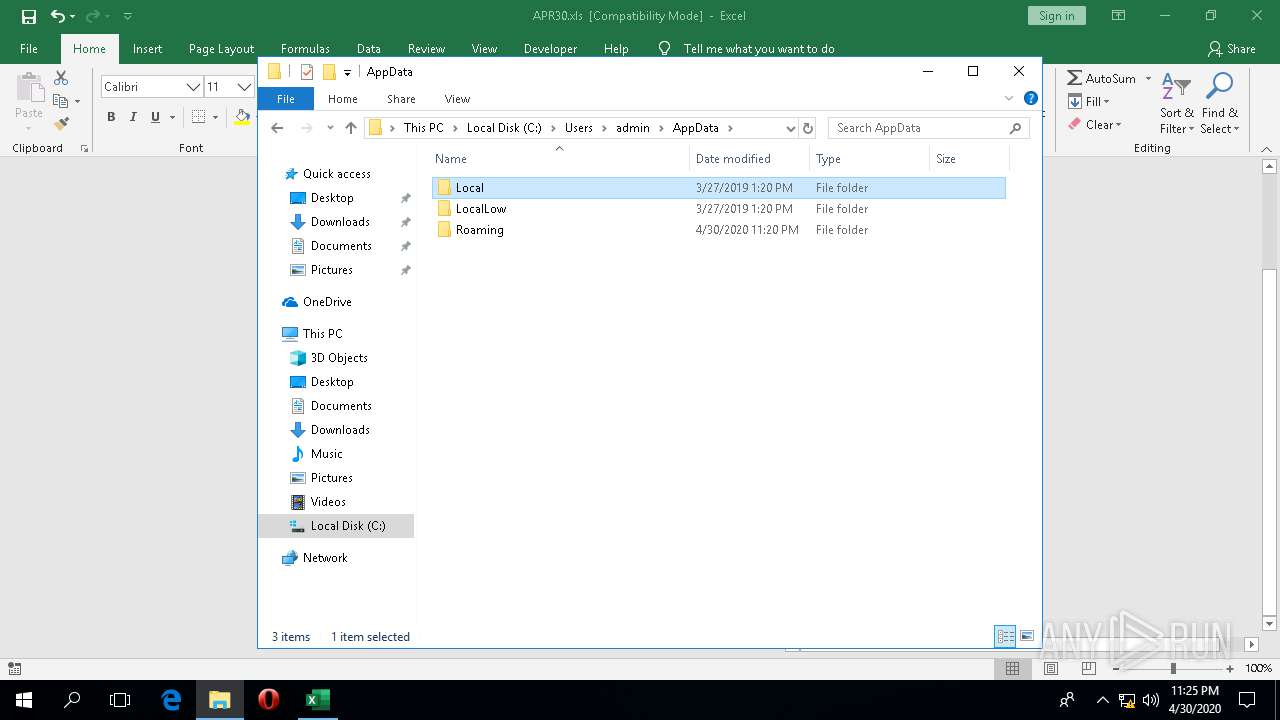
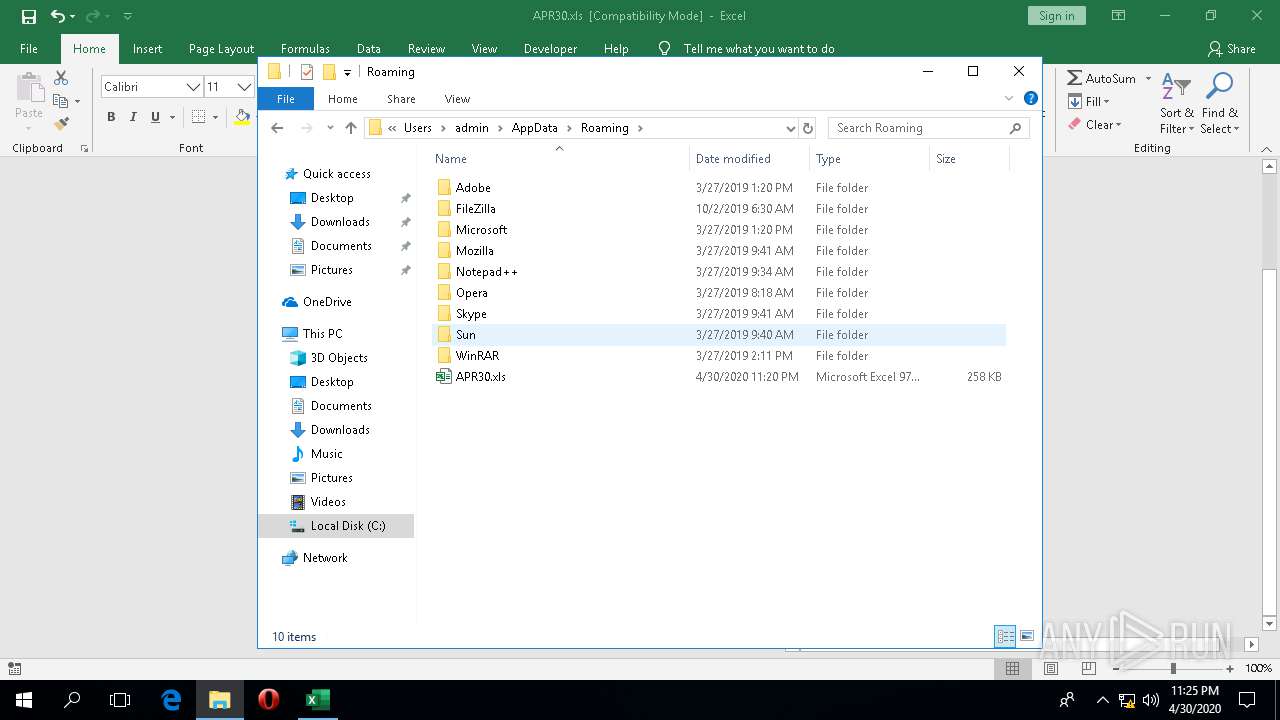
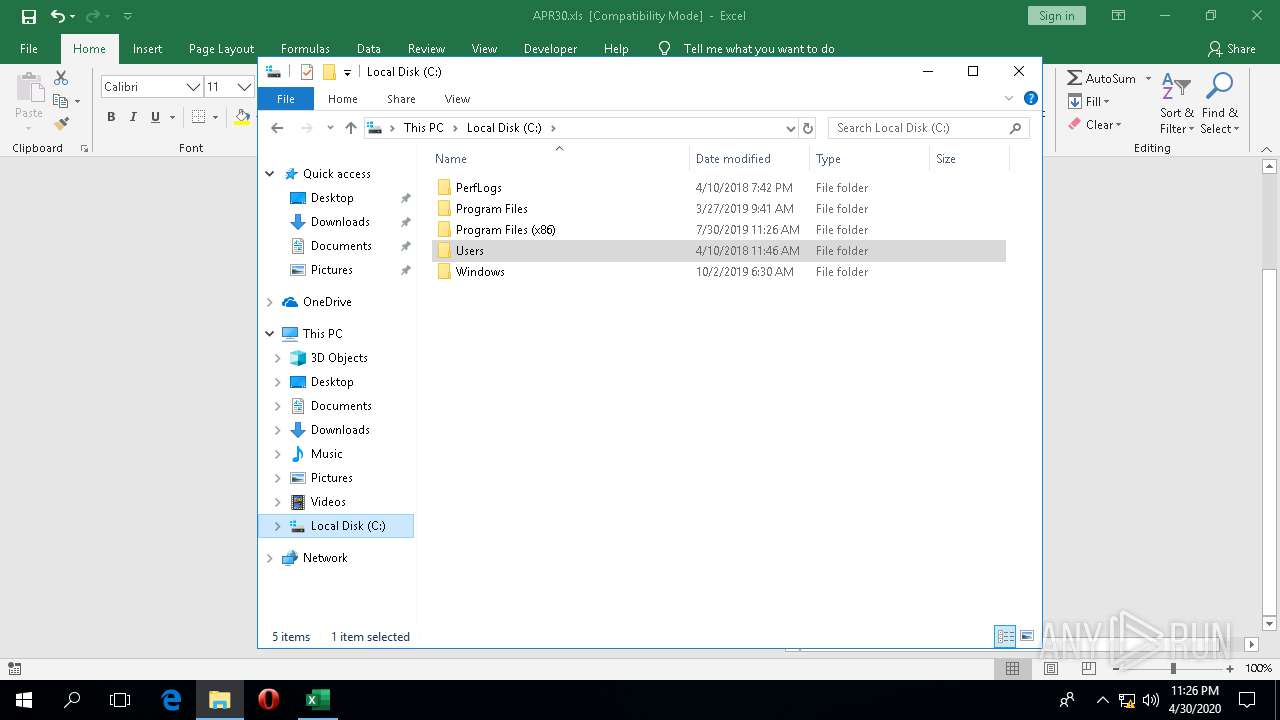
| 1920 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Roaming\APR30.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 2332 | "C:\Windows\ImmersiveControlPanel\SystemSettings.exe" -ServerName:microsoft.windows.immersivecontrolpanel | C:\Windows\ImmersiveControlPanel\SystemSettings.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Settings Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2696 | C:\WINDOWS\system32\wermgr.exe | C:\WINDOWS\system32\wermgr.exe | PNHZWsP.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Roaming\APR30.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 4704 | "C:\ProgramData\PNHZWsP.exe" | C:\ProgramData\PNHZWsP.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: A new Boxxi game. Select groups of blocks to remove Exit code: 0 Version: 2.1.255.601 Modules
| |||||||||||||||
| 4748 | C:\Windows\System32\Speech_OneCore\Common\SpeechRuntime.exe -Embedding | C:\Windows\System32\Speech_OneCore\Common\SpeechRuntime.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Speech Runtime Executable Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
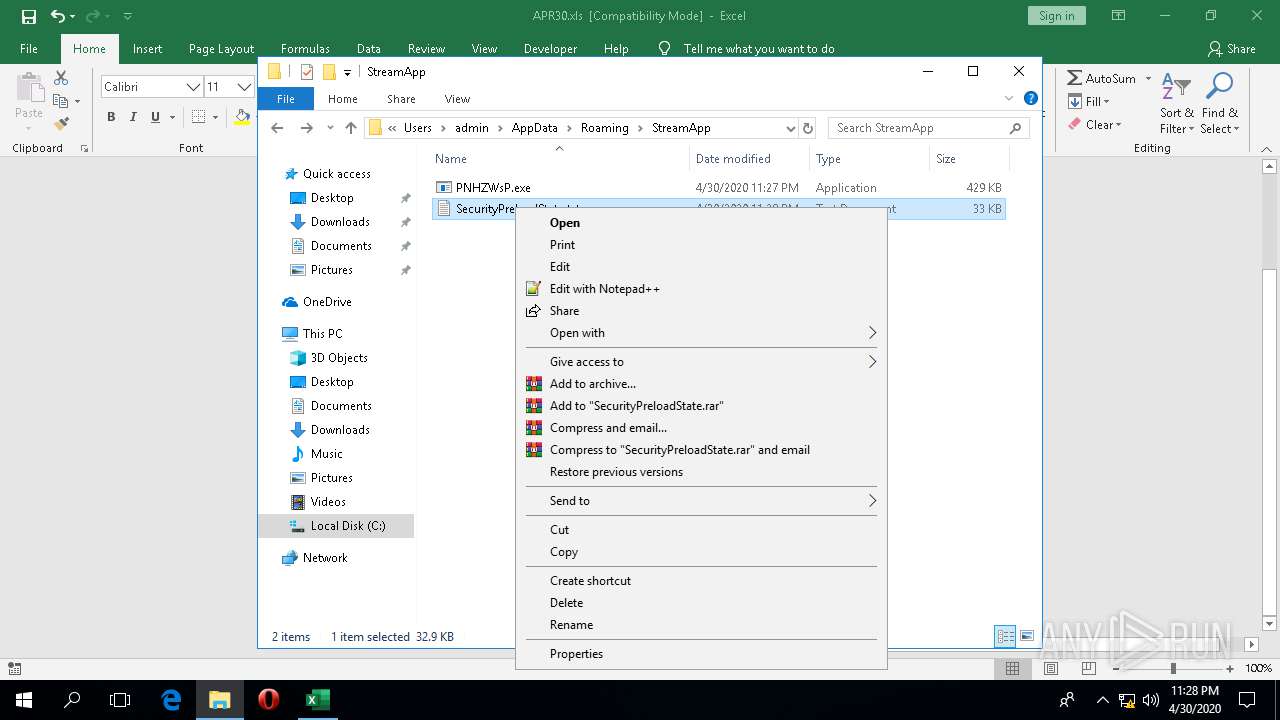
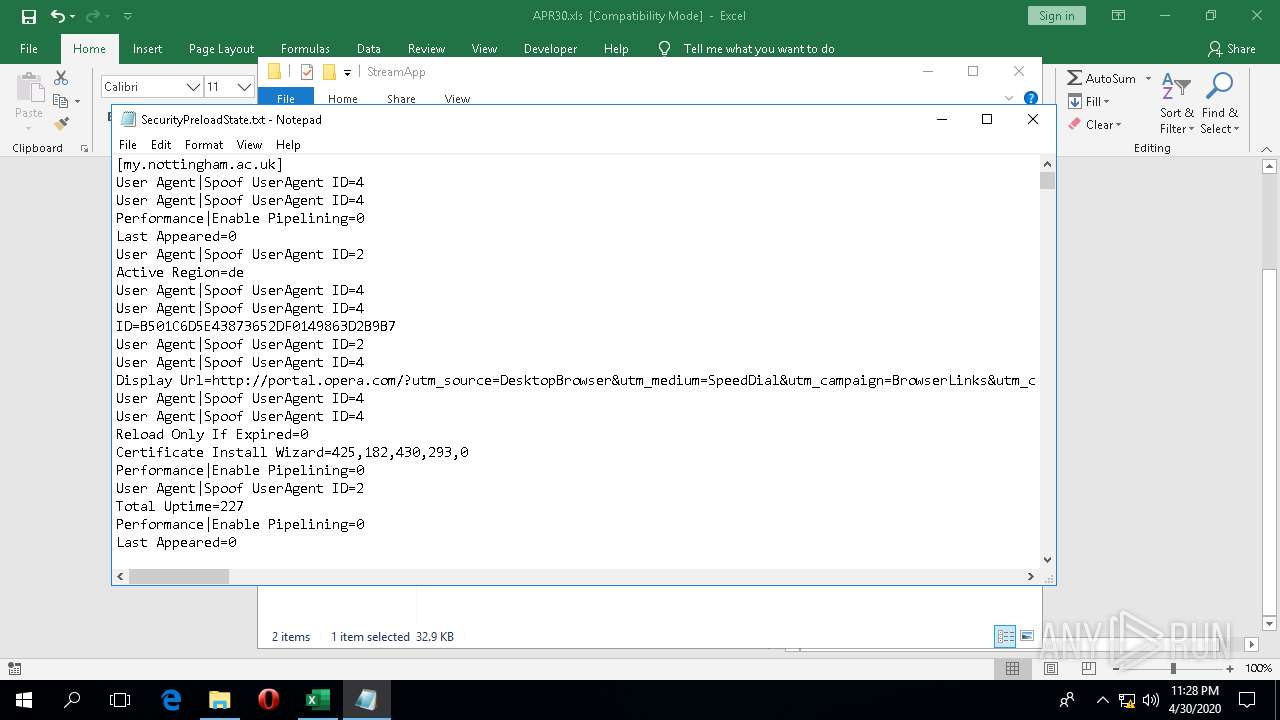
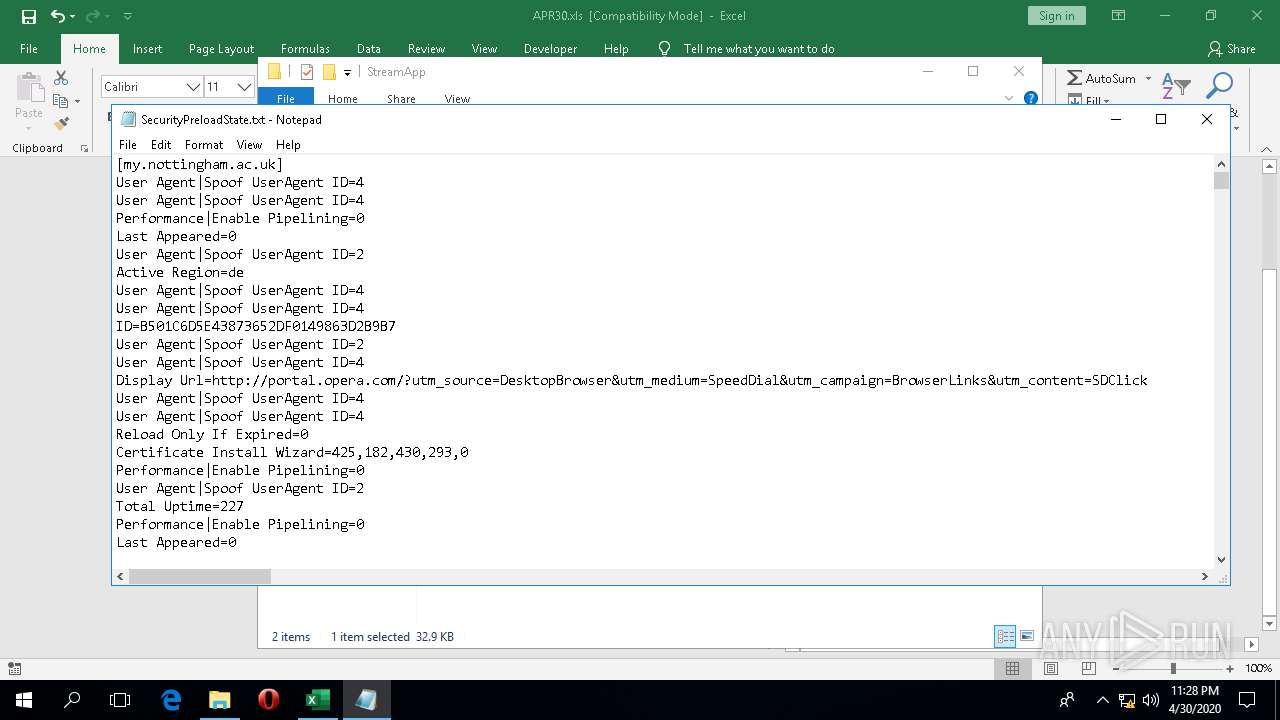
| 5152 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\StreamApp\SecurityPreloadState.txt | C:\WINDOWS\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 500
Read events
6 003
Write events
415
Delete events
82
Modification events
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\EXCEL\4336 |
| Operation: | write | Name: | 0 |
Value: 0B0E100CDC7D226A019D43A82B7850D3923E03230046A88ABC8BE0E887EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E226D2B484F4D616659574A5464337373702B3165327141506A326C775347586F6C4A7635624B6E337449506B3D2200 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4336) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
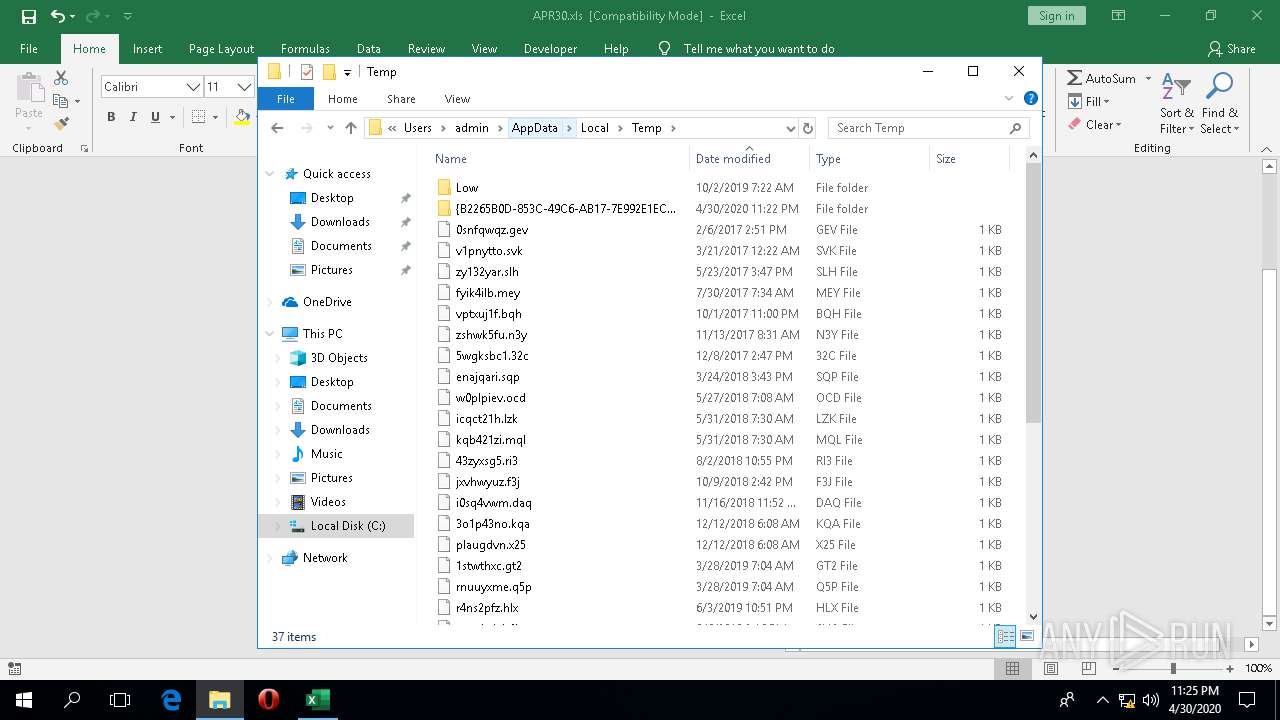
Executable files
3
Suspicious files
4
Text files
183
Unknown types
4
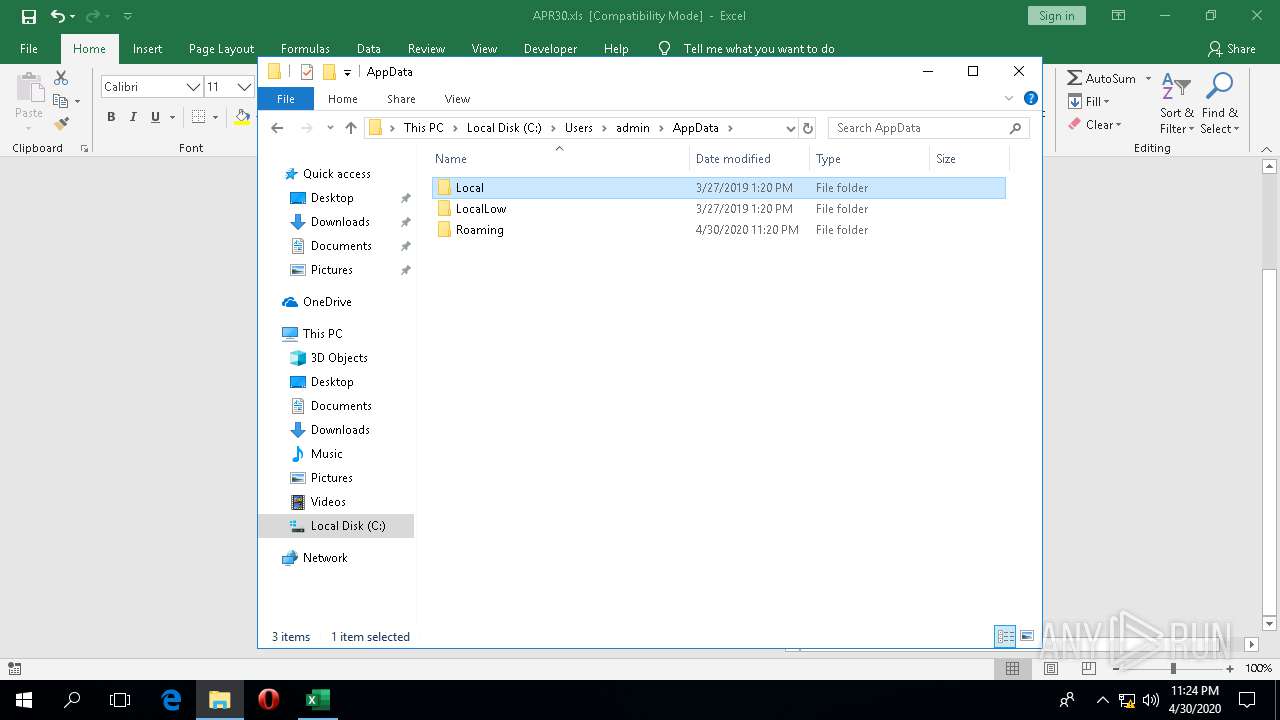
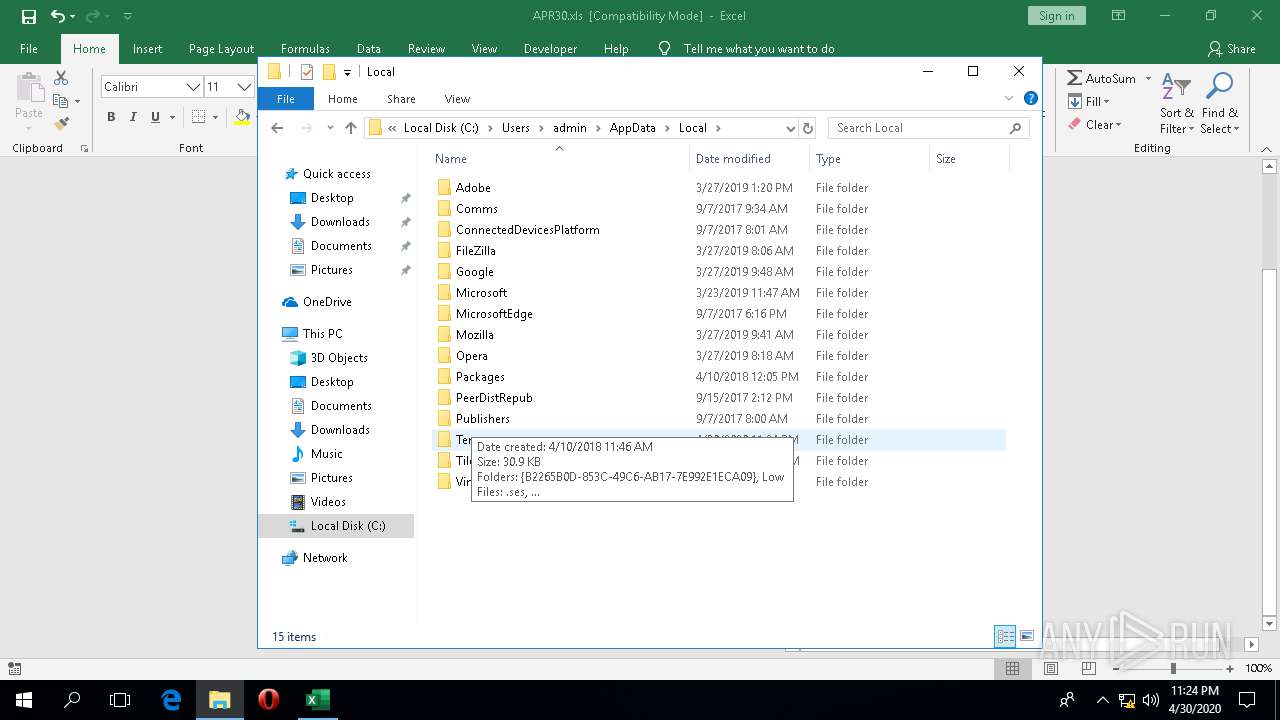
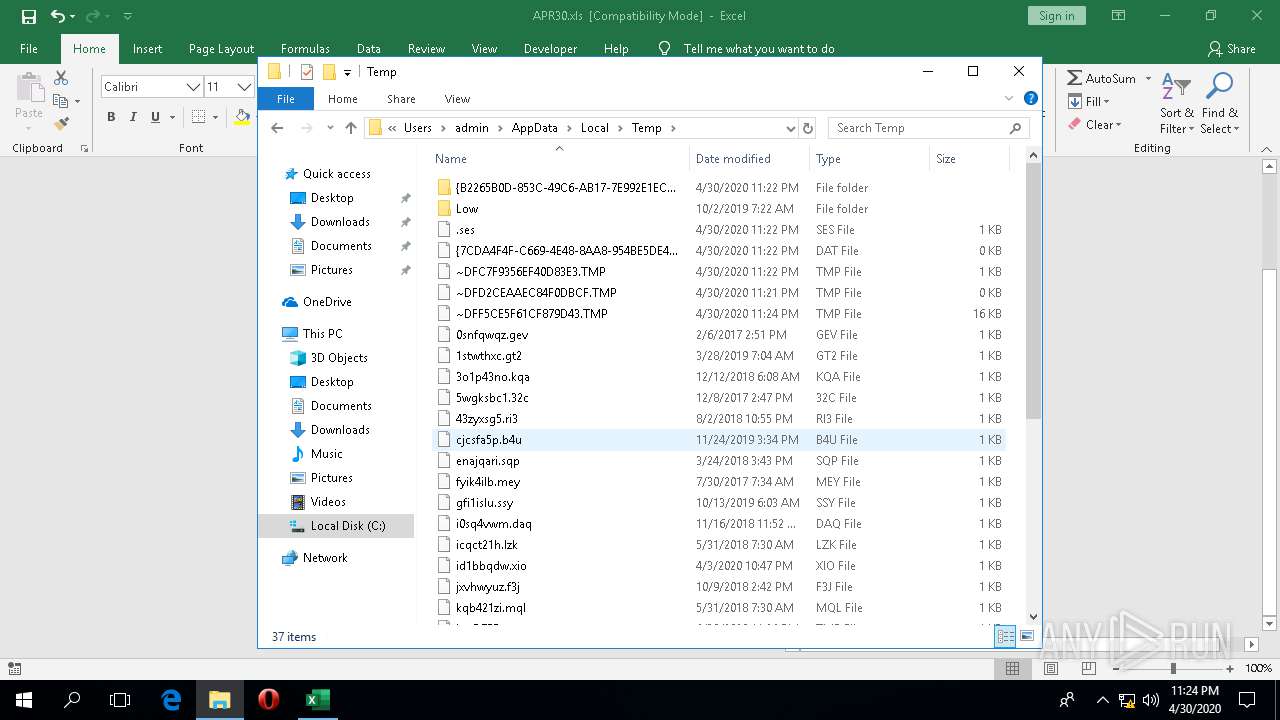
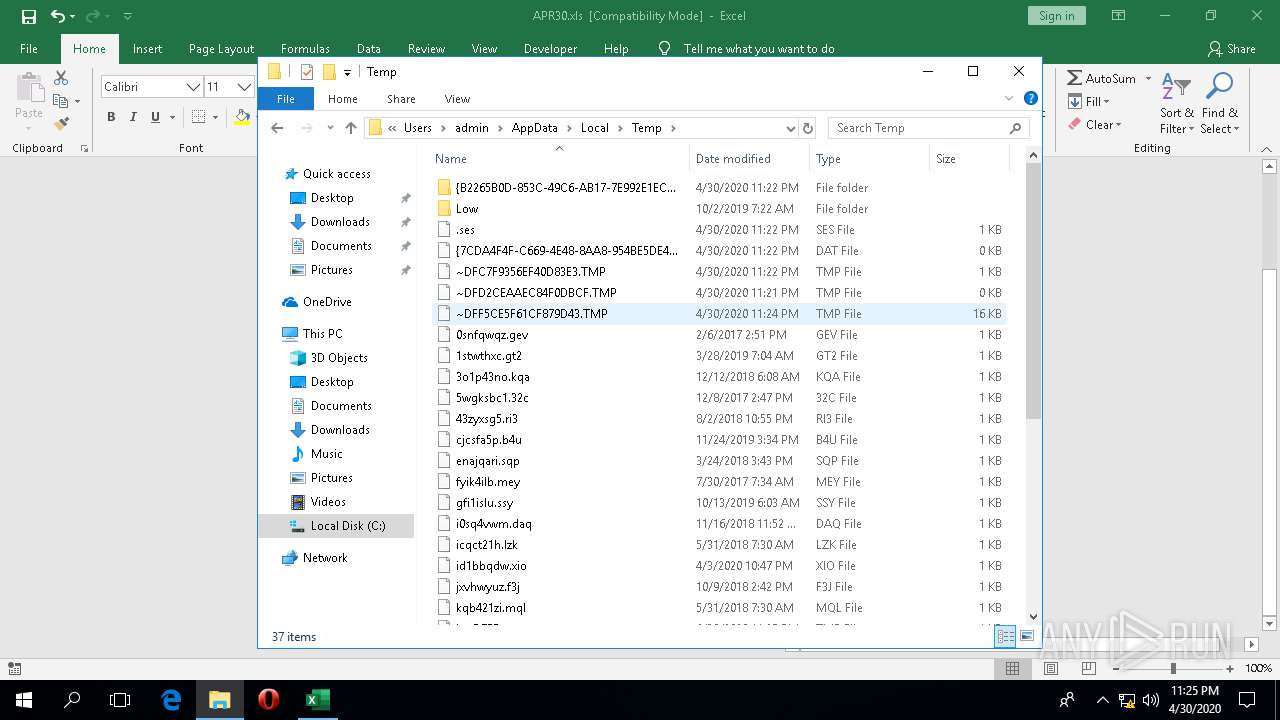
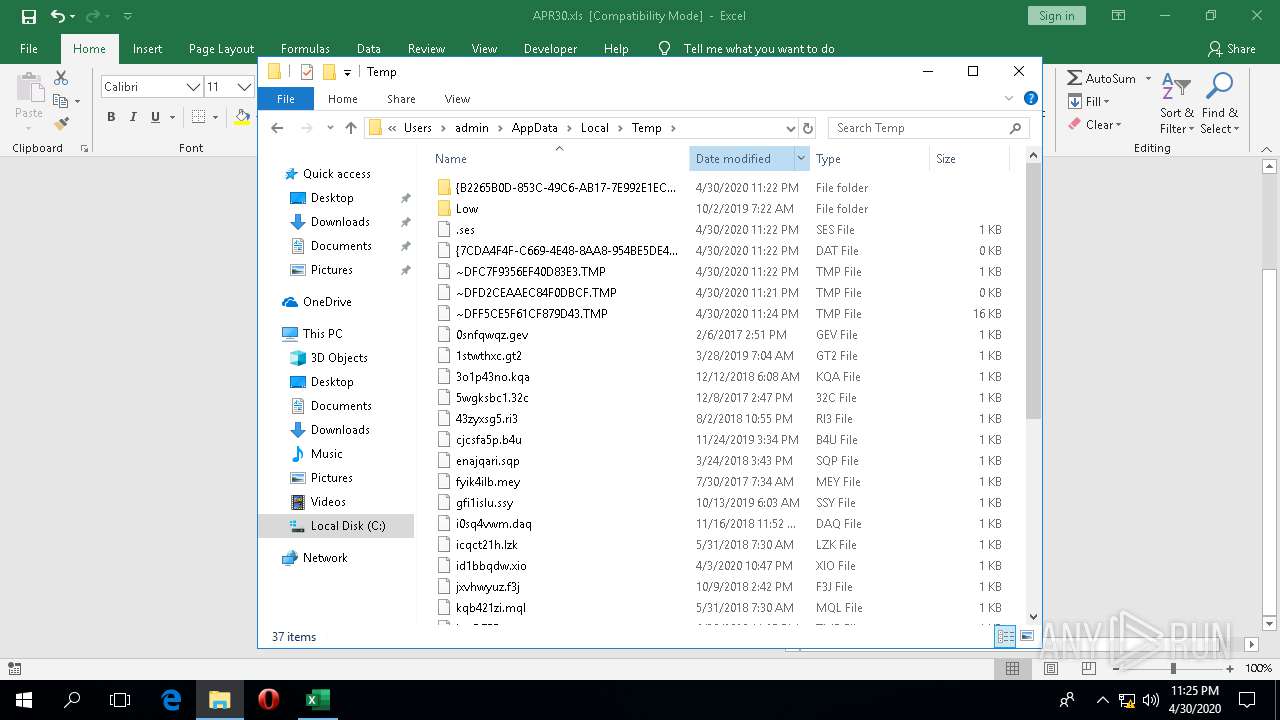
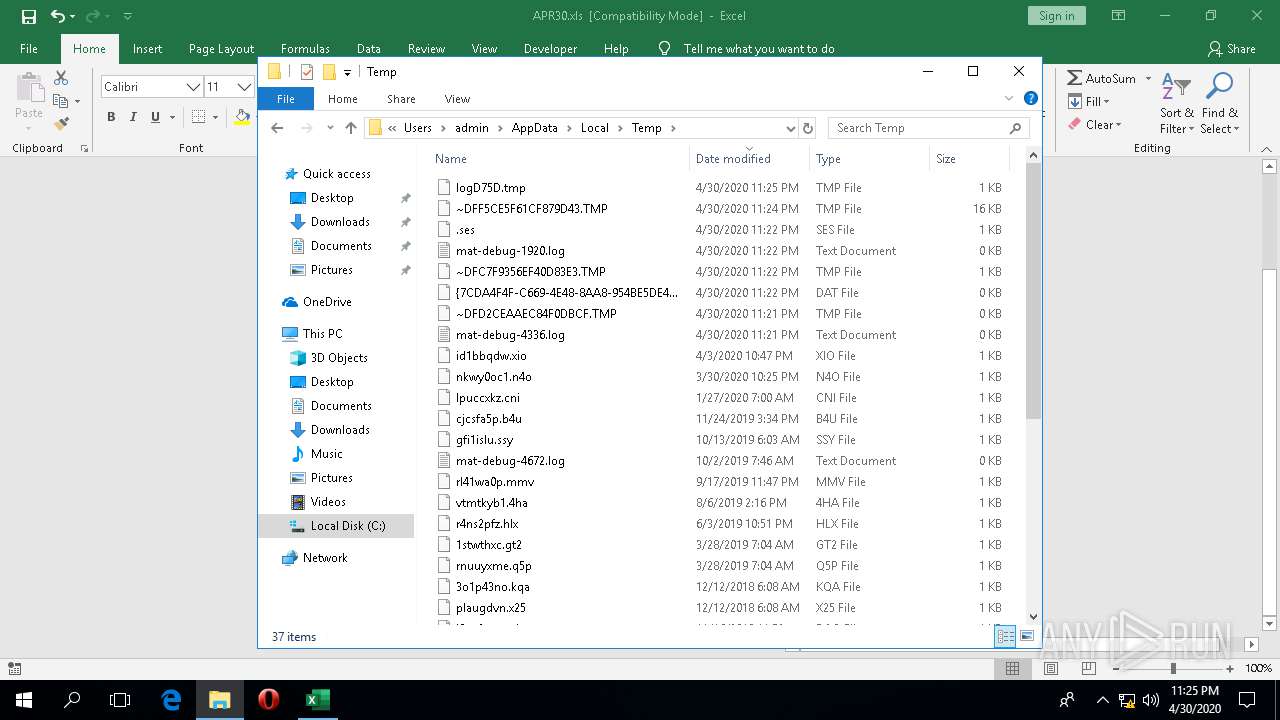
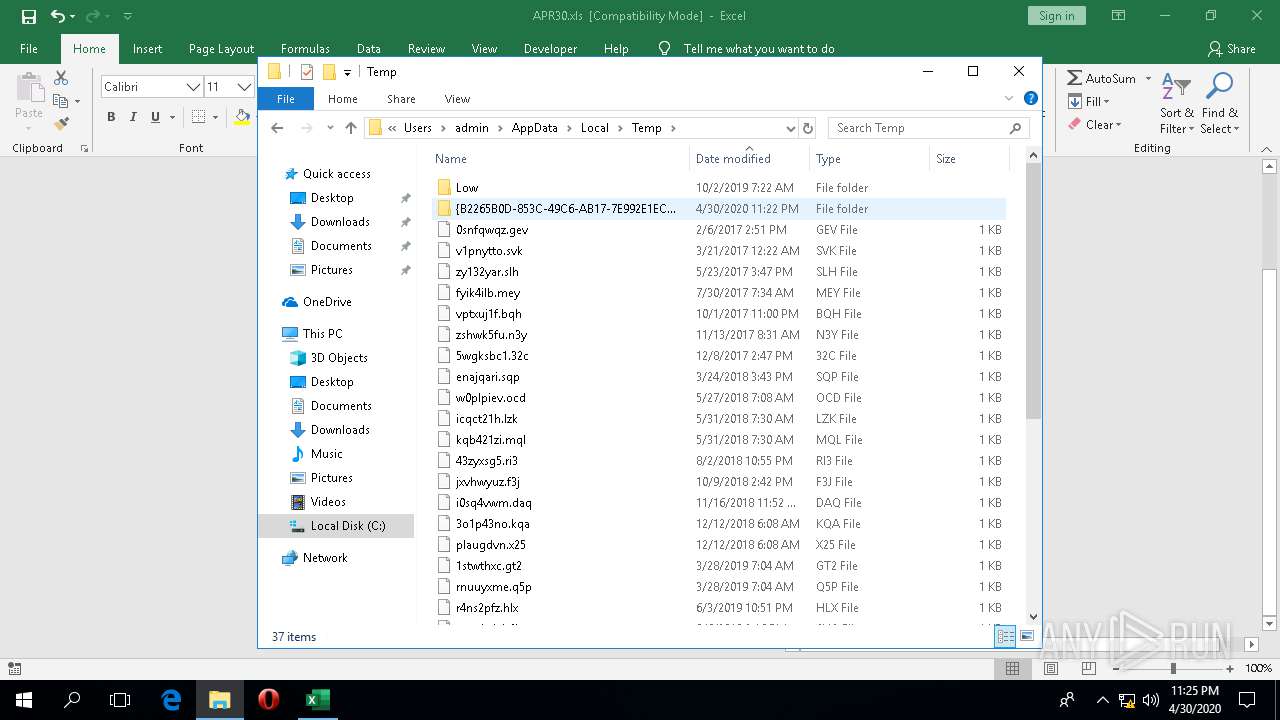
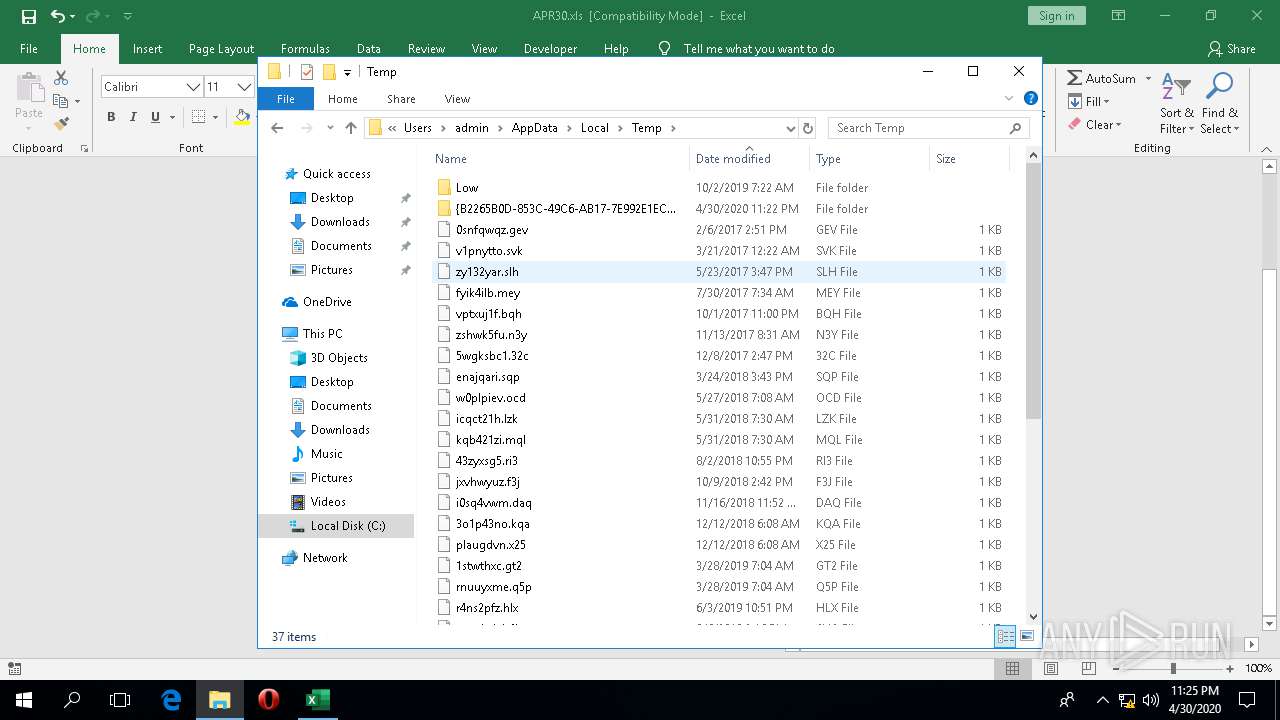
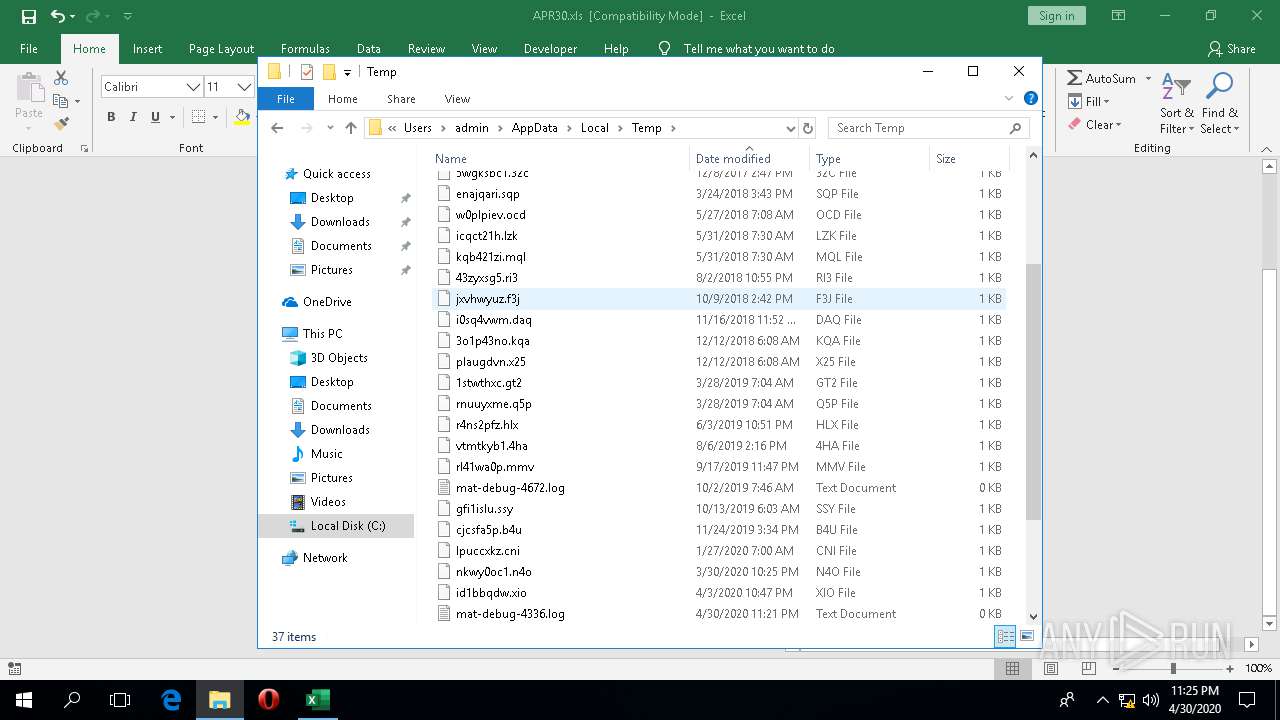
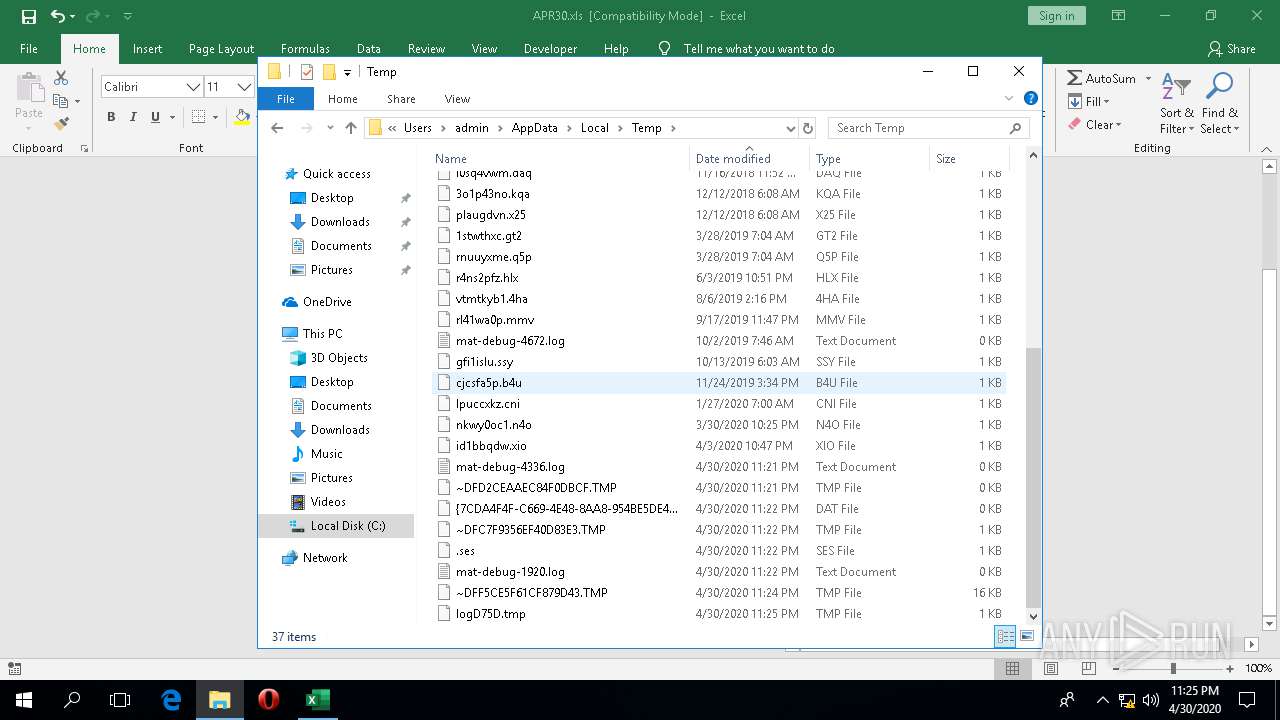
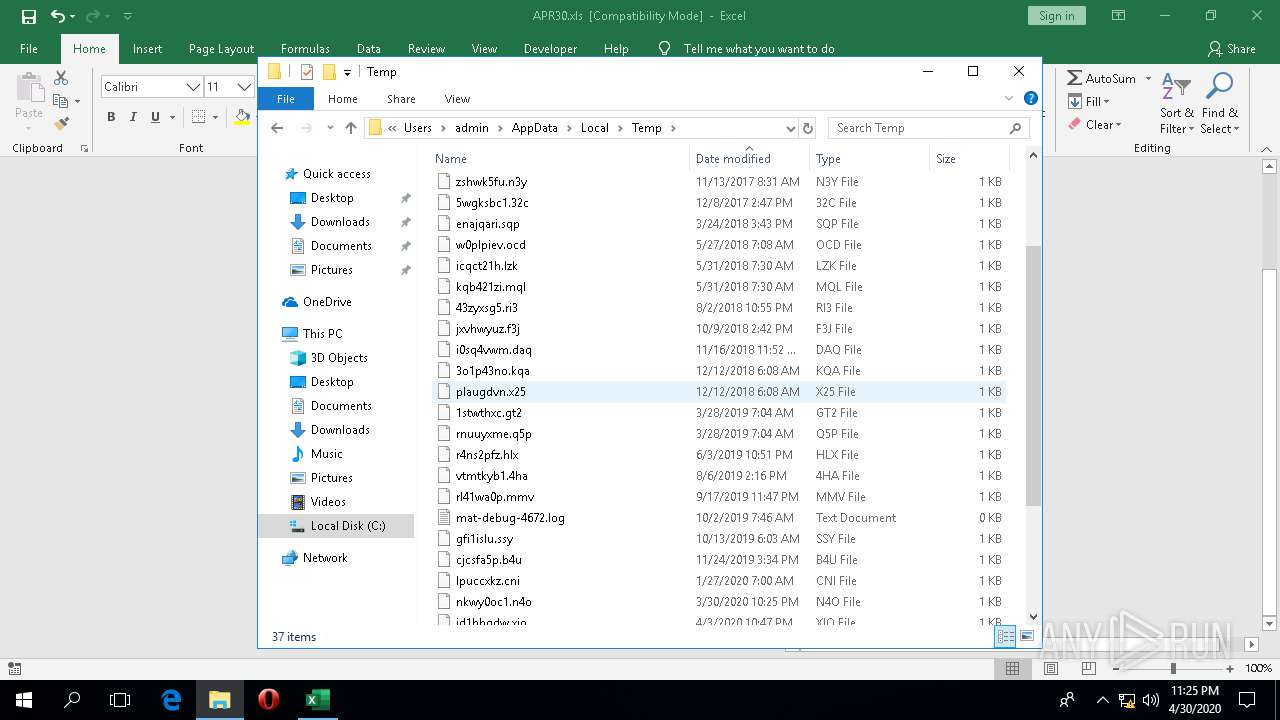
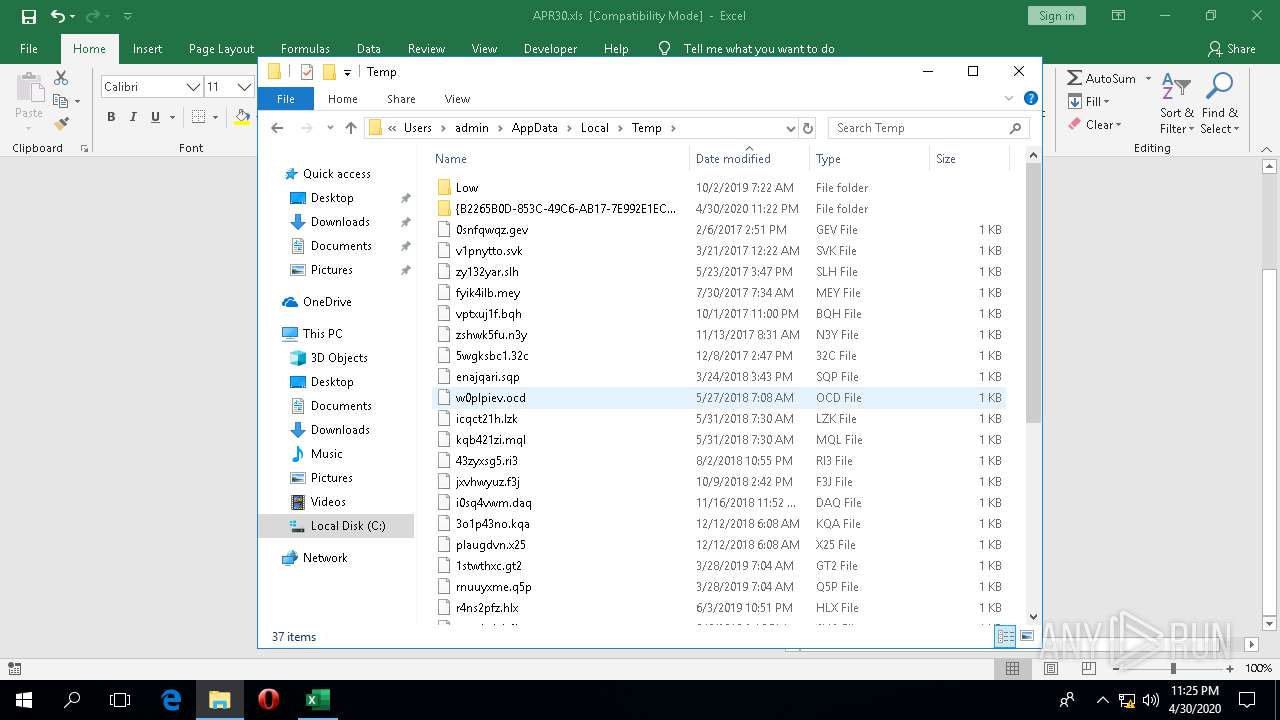
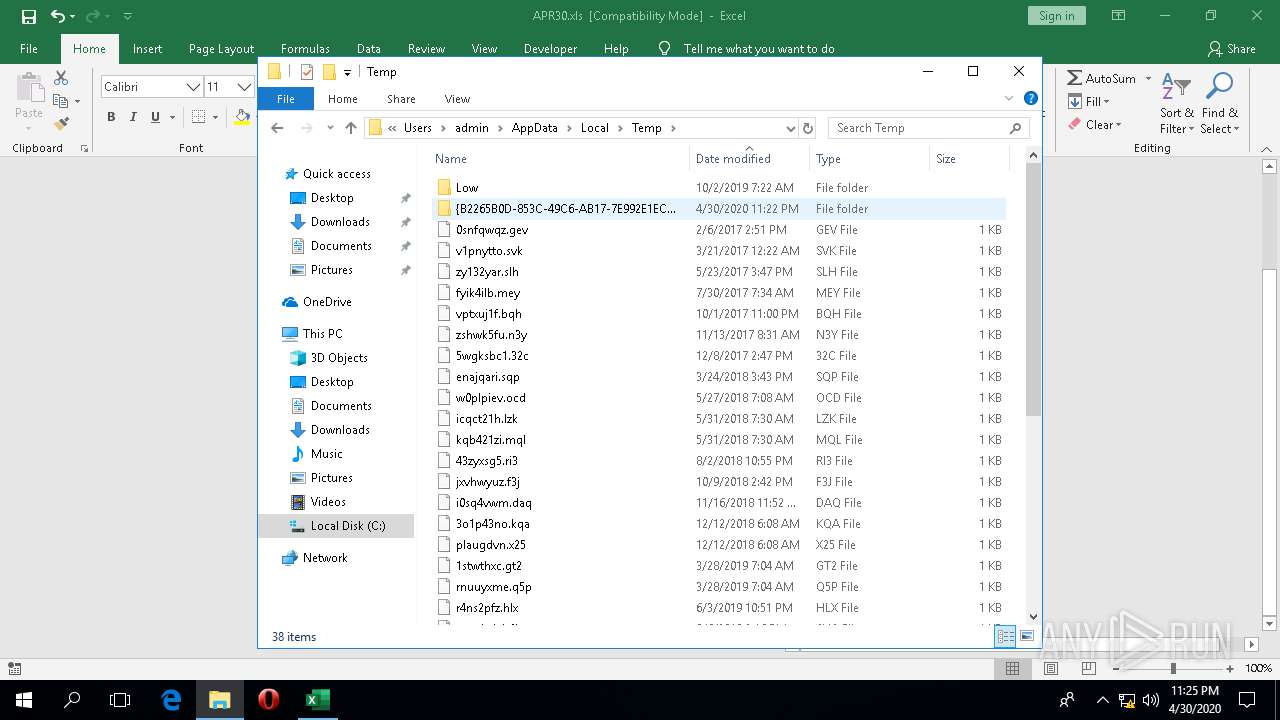
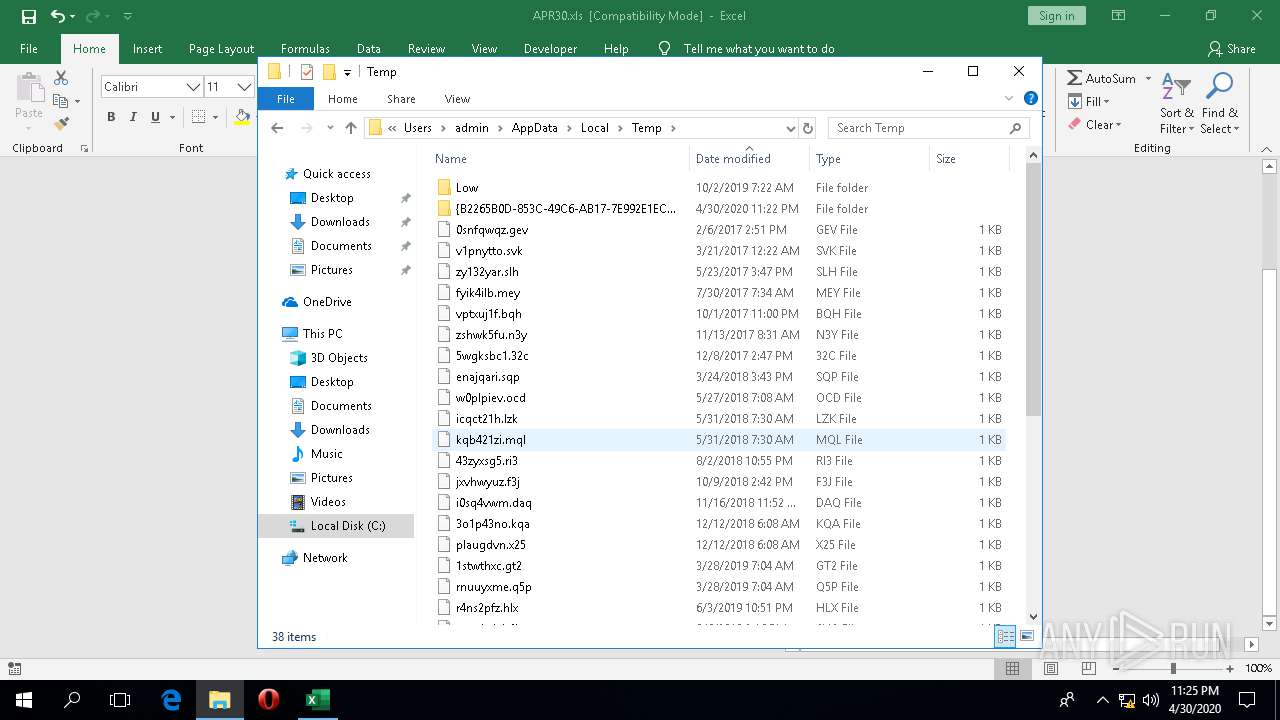
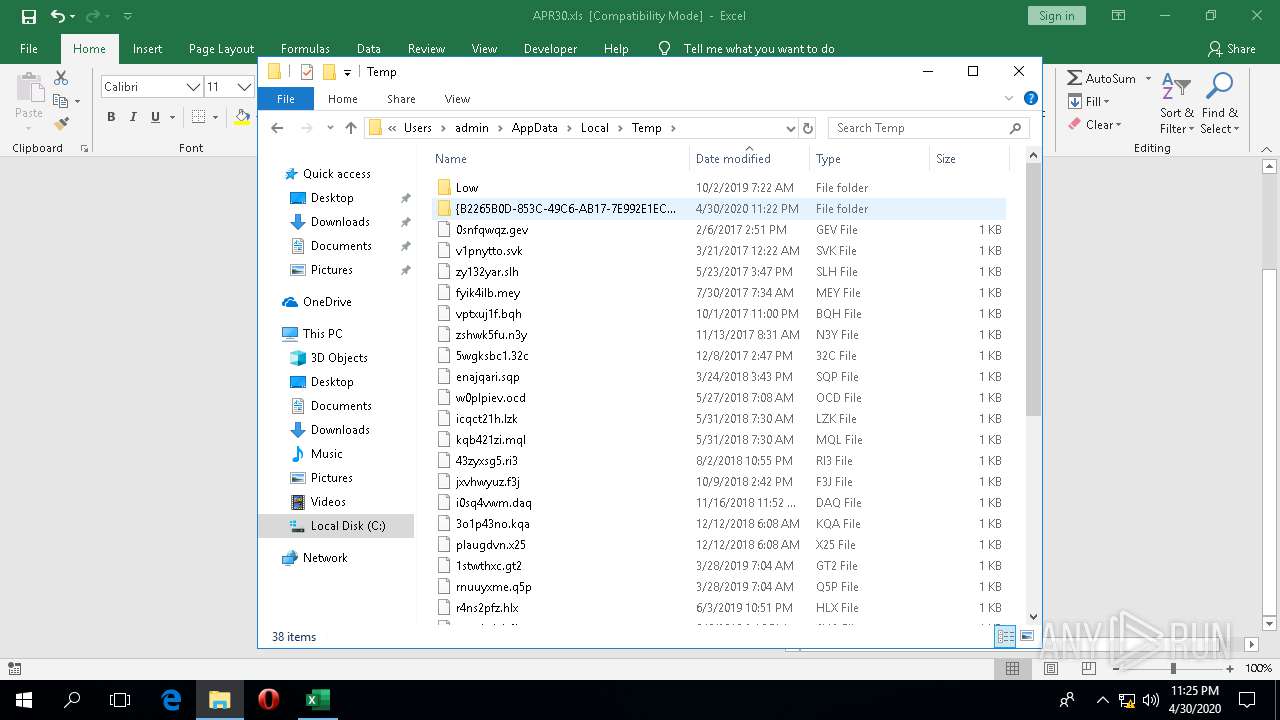
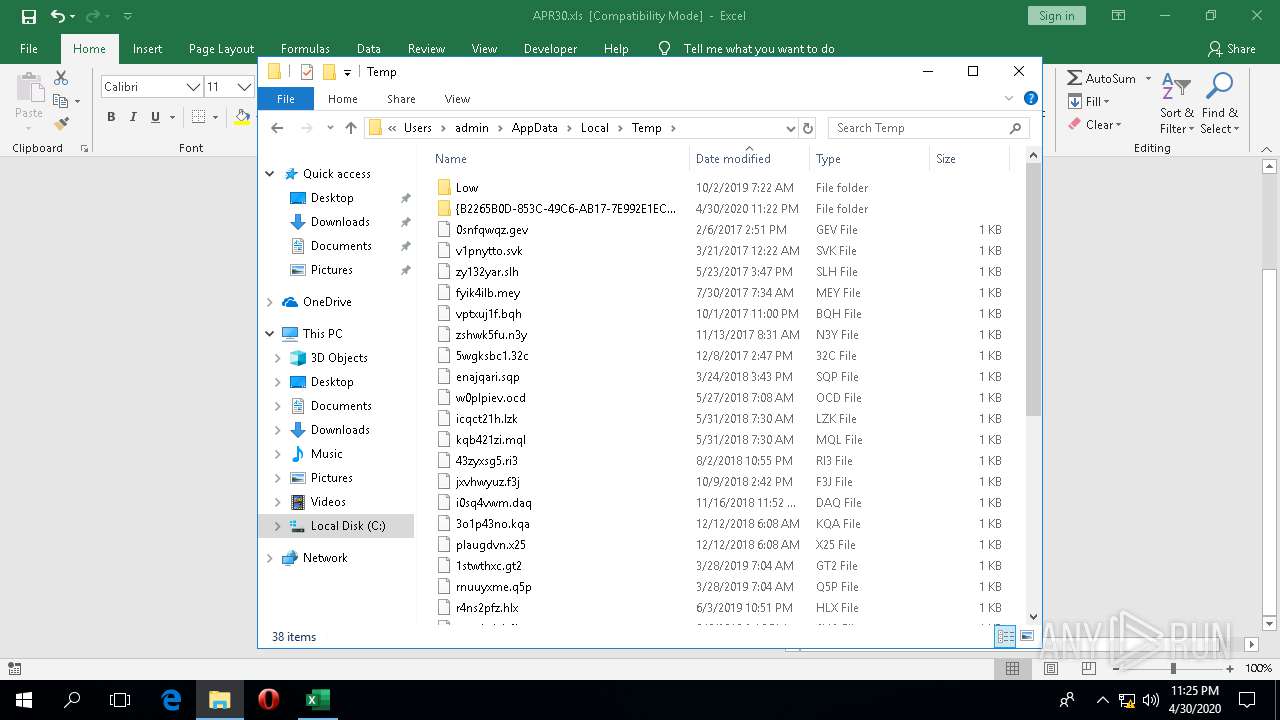
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFD2CEAAEC84F0DBCF.TMP | — | |
MD5:— | SHA256:— | |||
| 4336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\excel.exe.db-shm | — | |
MD5:— | SHA256:— | |||
| 4336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\excel.exe.db-wal | — | |
MD5:— | SHA256:— | |||
| 1920 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WYV06XWBDNSBTHHHUKJ0.temp | — | |
MD5:— | SHA256:— | |||
| 1920 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IQM3DKYVTL0JG078D2OB.temp | — | |
MD5:— | SHA256:— | |||
| 4336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\.ses | text | |
MD5:— | SHA256:— | |||
| 2332 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S7PIRRM2XIK50HXQVSN7.temp | — | |
MD5:— | SHA256:— | |||
| 4336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\excel.exe.db | sqlite | |
MD5:— | SHA256:— | |||
| 1920 | EXCEL.EXE | C:\ProgramData\PNHZWsP.exe | executable | |
MD5:— | SHA256:— | |||
| 1920 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\APR30.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
6
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4336 | EXCEL.EXE | 52.114.132.34:443 | self.events.data.microsoft.com | Microsoft Corporation | US | unknown |
5712 | svchost.exe | 20.191.48.196:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | US | unknown |
2696 | wermgr.exe | 194.5.250.69:443 | — | — | — | suspicious |
1920 | EXCEL.EXE | 45.77.36.234:443 | dichthuatsnu.com | Choopa, LLC | SG | suspicious |
1920 | EXCEL.EXE | 52.114.133.61:443 | self.events.data.microsoft.com | Microsoft Corporation | US | unknown |
4336 | EXCEL.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
dichthuatsnu.com |
| suspicious |
settings-win-ppe.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2696 | wermgr.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |