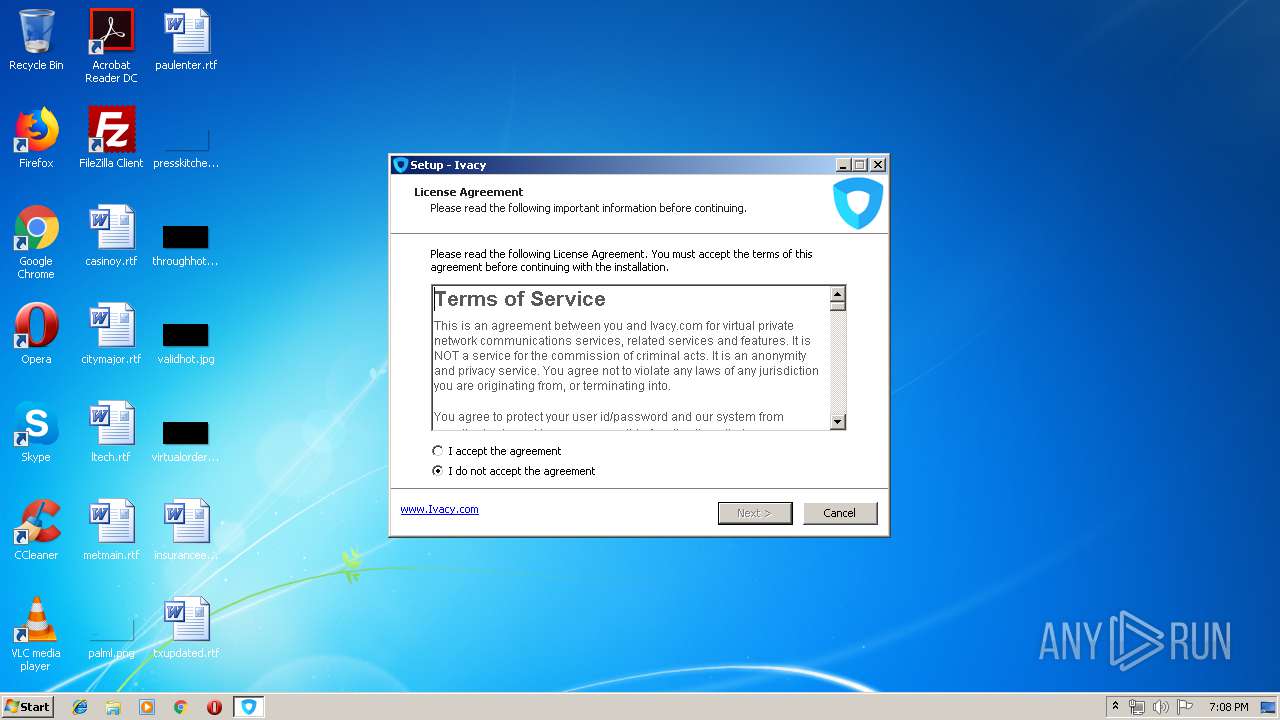
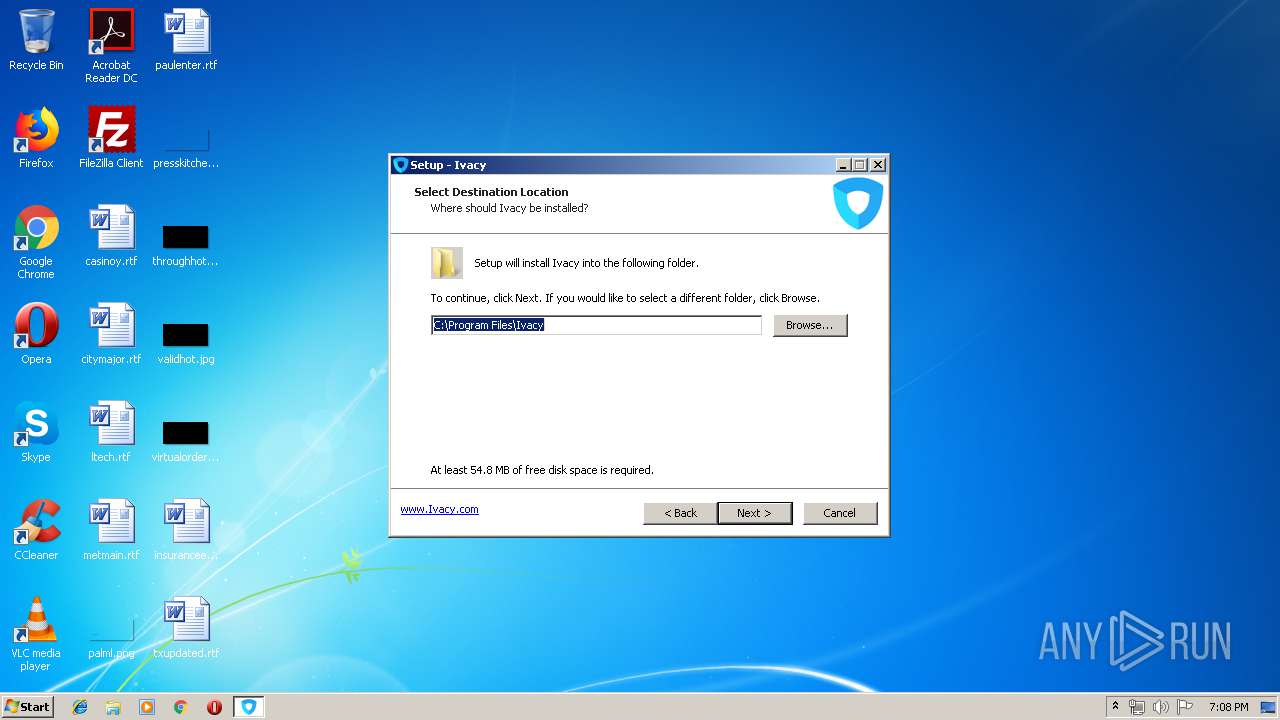
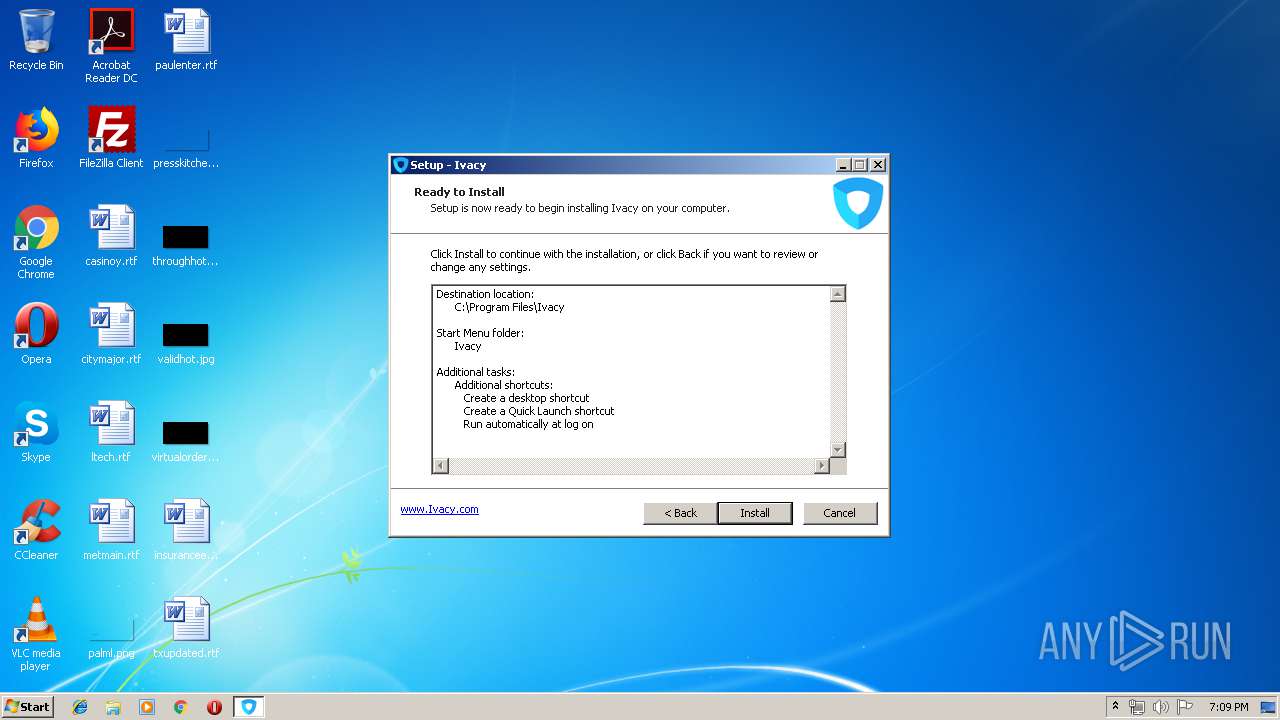
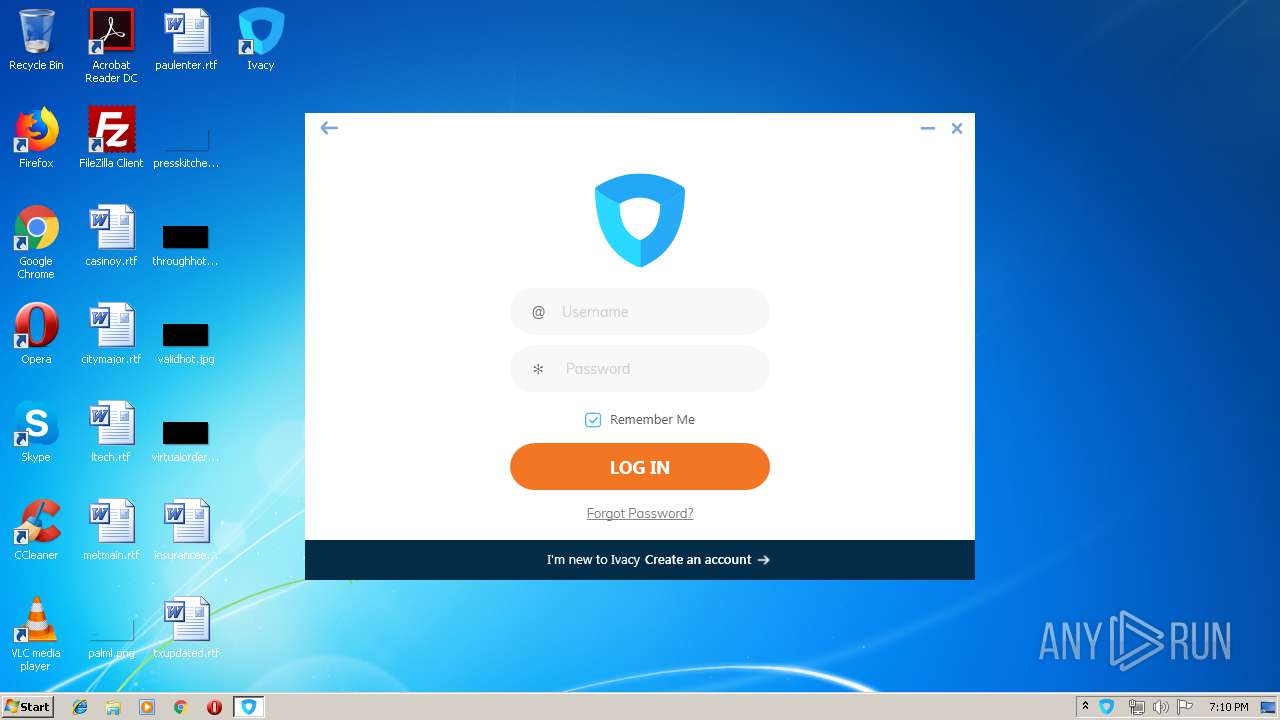
| download: | ivacy-windows-setup.exe |
| Full analysis: | https://app.any.run/tasks/8fe50e79-82a3-4de2-95e3-cd65c3072339 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 18:08:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DB6422157FA2CB97AA1B8391E61A76EC |
| SHA1: | 51F4B8940BC7E0B77E71B5B29A30814E4539C5E0 |
| SHA256: | 2A2363C37A7C0FA9CD39829B333B229EC2A649A5BB0569B63D56610159532A3E |
| SSDEEP: | 393216:3XigndvRQFhdjV1YA45/P92ZtoX76dORnz1REEAxKUHqmGbhYPQQ2hb1j9Q:HiuROJe/x92ZiL/hPMSmQhYP7yW |
MALICIOUS
Writes to a start menu file
- ivacy-windows-setup.tmp (PID: 2664)
Loads dropped or rewritten executable
- InstallerWithDisplay.exe (PID: 2740)
- Ivacy.exe (PID: 3060)
- Atom.SDK.Installer.exe (PID: 3244)
- Atom.SDK.WindowsService.exe (PID: 2620)
- Ivacy.exe (PID: 3728)
Application was dropped or rewritten from another process
- InstallerWithDisplay.exe (PID: 2740)
- CloseApp.exe (PID: 2872)
- Ivacy.exe (PID: 3060)
- devcon.exe (PID: 964)
- Atom.SDK.Installer.exe (PID: 3244)
- devcon.exe (PID: 2996)
- subinacl.exe (PID: 2628)
- subinacl.exe (PID: 2788)
- Ivacy.exe (PID: 3728)
- subinacl.exe (PID: 3680)
- subinacl.exe (PID: 2836)
- Atom.SDK.WindowsService.exe (PID: 2620)
- subinacl.exe (PID: 2868)
- subinacl.exe (PID: 3392)
Changes settings of System certificates
- Ivacy.exe (PID: 3060)
- Ivacy.exe (PID: 3728)
Changes the autorun value in the registry
- ivacy-windows-setup.tmp (PID: 2664)
SUSPICIOUS
Creates files in the user directory
- ivacy-windows-setup.tmp (PID: 2664)
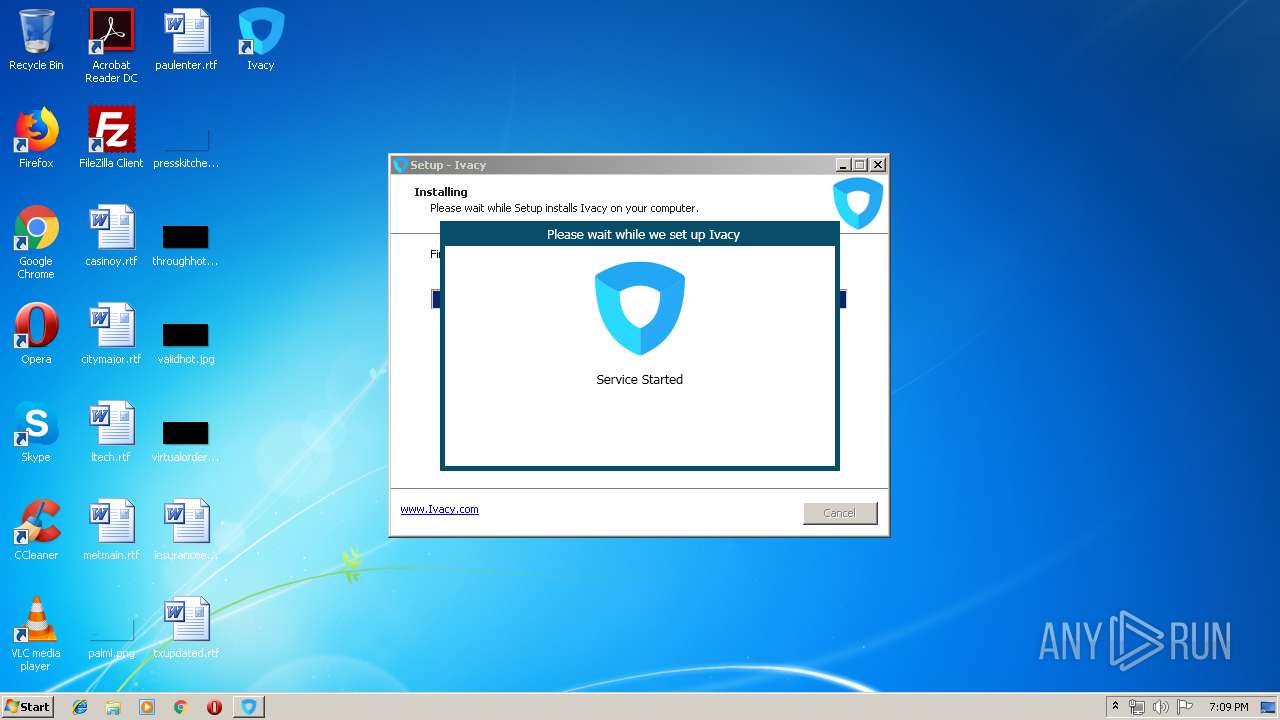
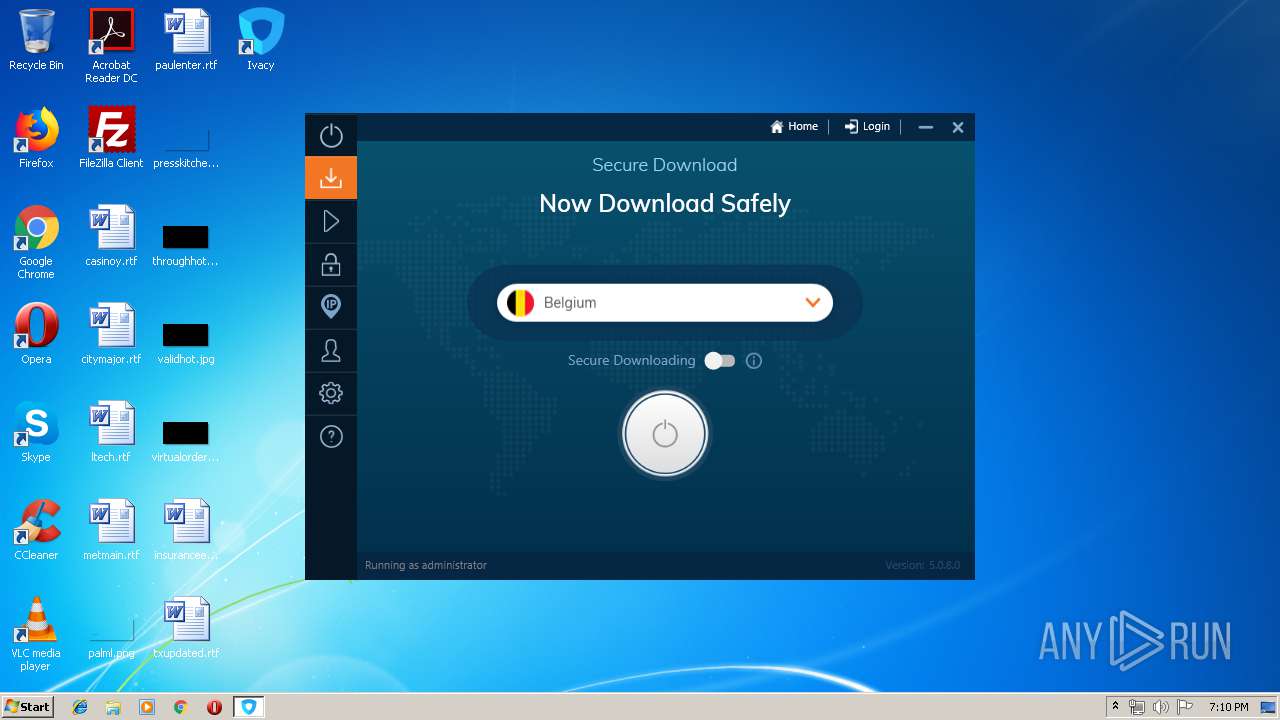
Starts SC.EXE for service management
- ivacy-windows-setup.tmp (PID: 2664)
- InstallerWithDisplay.exe (PID: 2740)
Creates files in the program directory
- Ivacy.exe (PID: 3060)
- InstallerWithDisplay.exe (PID: 2740)
- Atom.SDK.Installer.exe (PID: 3244)
- Atom.SDK.WindowsService.exe (PID: 2620)
- Ivacy.exe (PID: 3728)
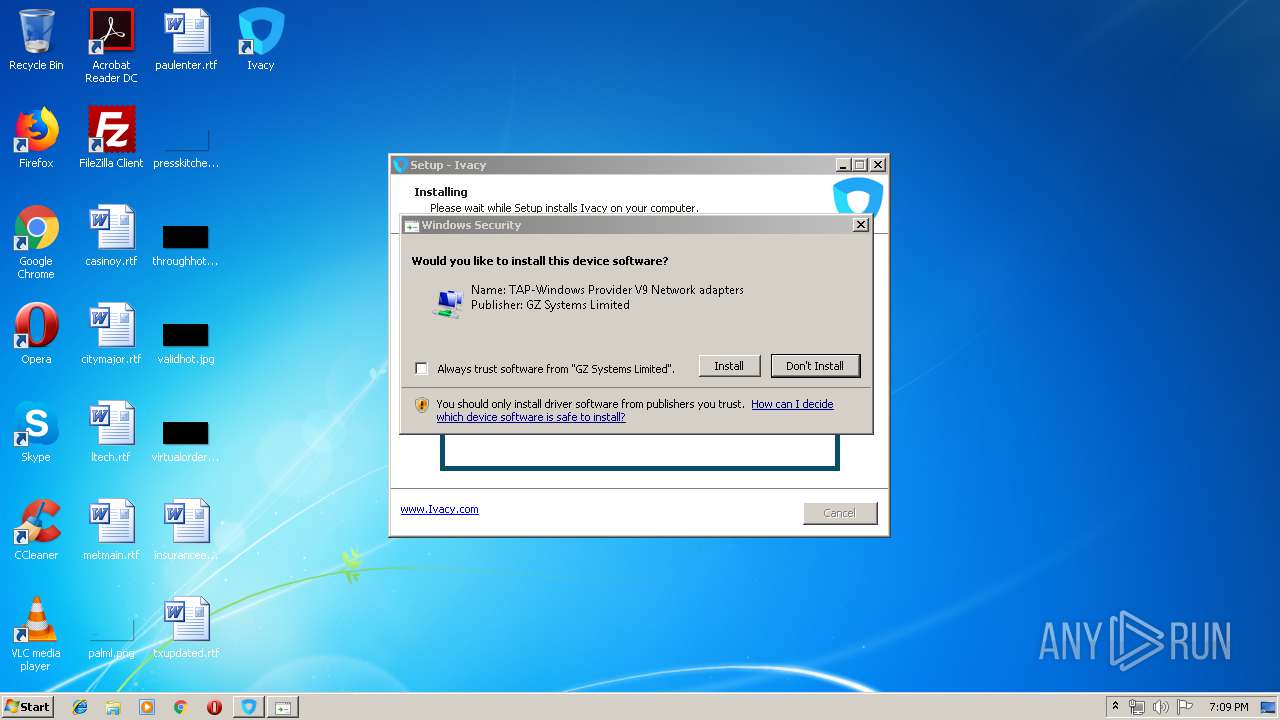
Executable content was dropped or overwritten
- ivacy-windows-setup.exe (PID: 1944)
- ivacy-windows-setup.exe (PID: 2288)
- devcon.exe (PID: 2996)
- Atom.SDK.Installer.exe (PID: 3244)
- DrvInst.exe (PID: 2440)
- DrvInst.exe (PID: 2388)
- ivacy-windows-setup.tmp (PID: 2664)
Adds / modifies Windows certificates
- Ivacy.exe (PID: 3060)
- Ivacy.exe (PID: 3728)
Uses NETSH.EXE for network configuration
- InstallerWithDisplay.exe (PID: 2740)
Reads Environment values
- Ivacy.exe (PID: 3060)
- Atom.SDK.WindowsService.exe (PID: 2620)
- Ivacy.exe (PID: 3728)
Creates files in the Windows directory
- devcon.exe (PID: 2996)
- DrvInst.exe (PID: 2388)
- DrvInst.exe (PID: 2440)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2388)
Removes files from Windows directory
- DrvInst.exe (PID: 2440)
- DrvInst.exe (PID: 2388)
Creates files in the driver directory
- DrvInst.exe (PID: 2440)
- DrvInst.exe (PID: 2388)
Searches for installed software
- DrvInst.exe (PID: 2388)
Uses TASKKILL.EXE to kill process
- ivacy-windows-setup.tmp (PID: 2664)
INFO
Application was dropped or rewritten from another process
- ivacy-windows-setup.tmp (PID: 4044)
- ivacy-windows-setup.tmp (PID: 2664)
Creates a software uninstall entry
- ivacy-windows-setup.tmp (PID: 2664)
Creates files in the program directory
- ivacy-windows-setup.tmp (PID: 2664)
Reads settings of System Certificates
- Ivacy.exe (PID: 3060)
- Ivacy.exe (PID: 3728)
Dropped object may contain Bitcoin addresses
- Atom.SDK.Installer.exe (PID: 3244)
- ivacy-windows-setup.tmp (PID: 2664)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3236)
Loads dropped or rewritten executable
- ivacy-windows-setup.tmp (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (91.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 43008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
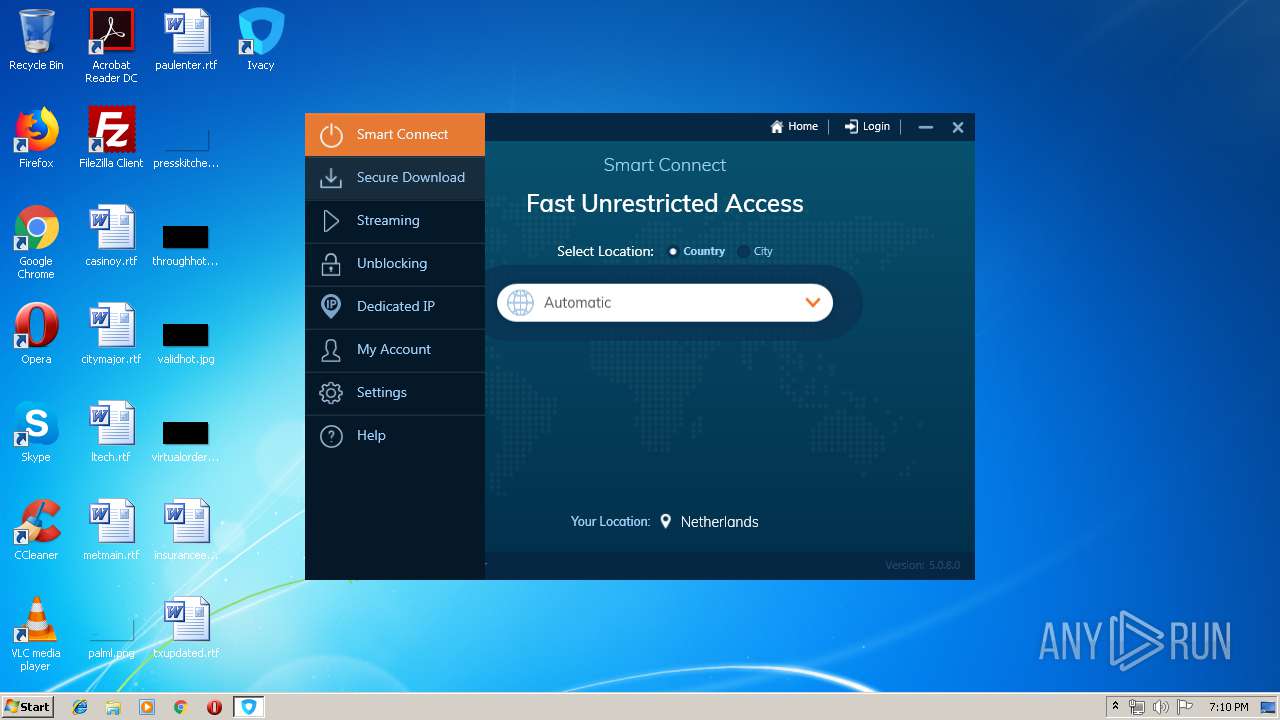
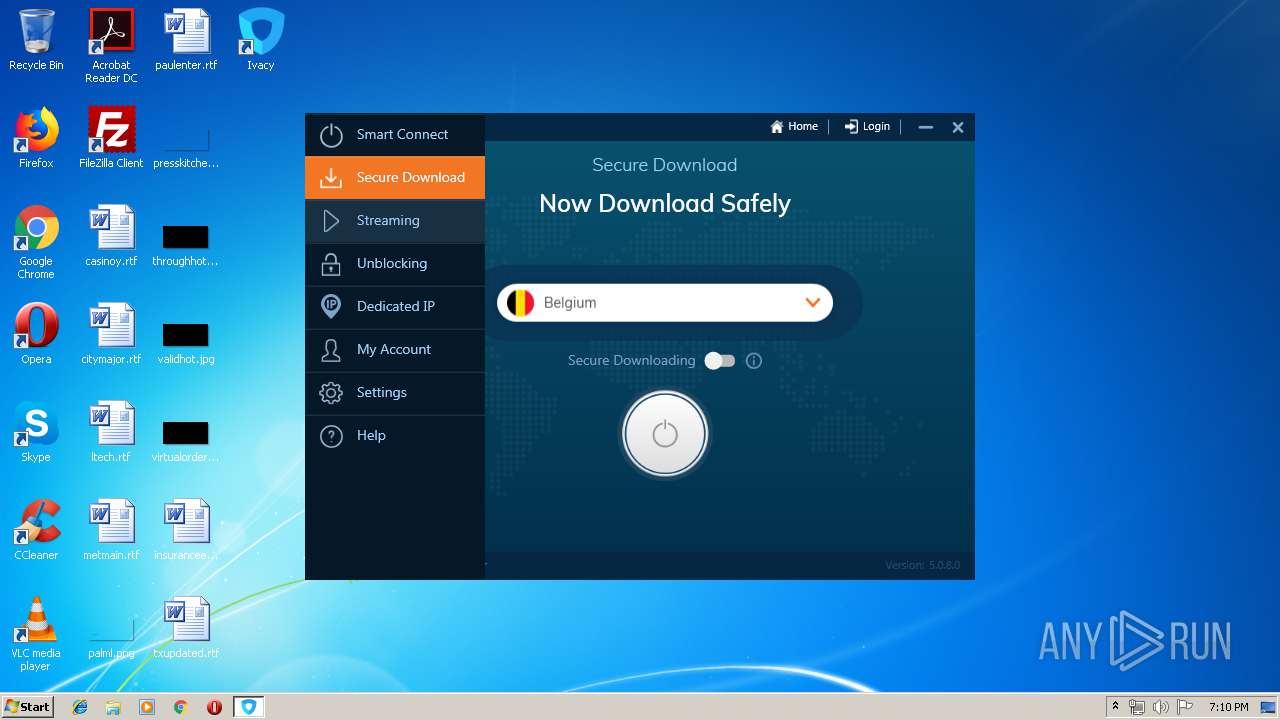
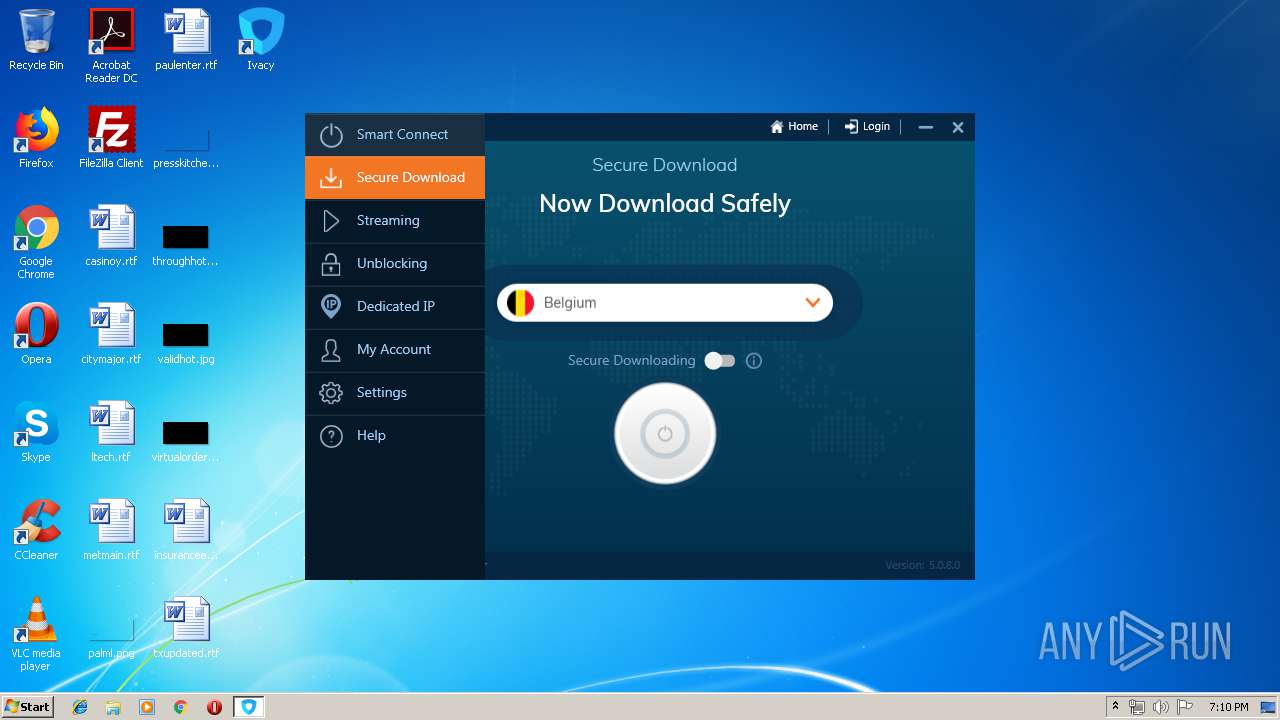
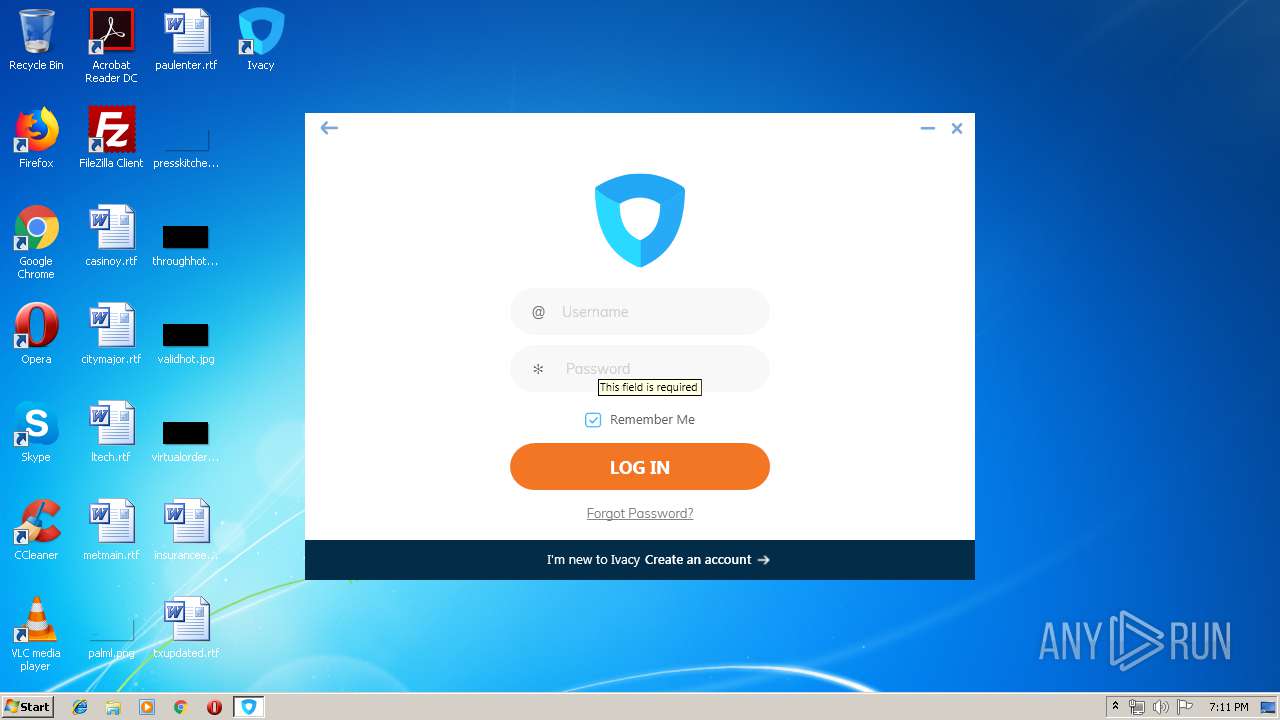
| FileVersionNumber: | 5.0.8.0 |
| ProductVersionNumber: | 5.0.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Ivacy |
| FileDescription: | Ivacy Setup |
| FileVersion: | 5.0.8.0 |
| LegalCopyright: | Ivacy |
| ProductName: | Ivacy |
| ProductVersion: | 5.0.8.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Ivacy |
| FileDescription: | Ivacy Setup |
| FileVersion: | 5.0.8.0 |
| LegalCopyright: | Ivacy |
| ProductName: | Ivacy |
| ProductVersion: | 5.0.8.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x0000965C | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.18105 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.57696 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.65218 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.25596 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
89
Monitored processes
34
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Program Files\Ivacy\driver\i386\devcon.exe" remove tap0901 | C:\Program Files\Ivacy\driver\i386\devcon.exe | — | Atom.SDK.Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 5.2.3718.0 (dnsrv.021114-1947) Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\taskkill.exe" /f /im Ivacy.exe | C:\Windows\System32\taskkill.exe | — | ivacy-windows-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "netsh" advfirewall set publicprofile firewallpolicy blockinboundalways,allowoutbound | C:\Windows\system32\netsh.exe | — | InstallerWithDisplay.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\AppData\Local\Temp\ivacy-windows-setup.exe" | C:\Users\admin\AppData\Local\Temp\ivacy-windows-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Ivacy Integrity Level: MEDIUM Description: Ivacy Setup Exit code: 0 Version: 5.0.8.0 Modules
| |||||||||||||||
| 2088 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2216 | "netsh" interface ipv6 6to4 set state disabled | C:\Windows\system32\netsh.exe | — | InstallerWithDisplay.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\ivacy-windows-setup.exe" /SPAWNWND=$30134 /NOTIFYWND=$30112 | C:\Users\admin\AppData\Local\Temp\ivacy-windows-setup.exe | ivacy-windows-setup.tmp | ||||||||||||
User: admin Company: Ivacy Integrity Level: HIGH Description: Ivacy Setup Exit code: 0 Version: 5.0.8.0 Modules
| |||||||||||||||
| 2388 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4d3e4ca9-4195-4e0b-572c-d83c8bca191d}\oemwin2k.inf" "0" "6d14a44ff" "000005D4" "WinSta0\Default" "000005CC" "208" "c:\program files\ivacy\driver\i386" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "oemwin2k.inf:tap0901:tap0901.ndi:9.0.0.9:tap0901" "6d14a44ff" "000005D4" "000005E0" "000005E8" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005F0" "000005D8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 073
Read events
1 170
Write events
848
Delete events
55
Modification events
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 680A00006021D749B6F3D401 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 3194C6A38C2BEA3EC24AFFF56544B91AE4C2828FD0EDBC2DD0866718DF3B7A64 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Ivacy\Atom.SDK.Core.dll | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: C46E4D13055FA781F52FE7EF484EF02DAE21A96AD9098FAFB84E675BFEEBEC96 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Ivacy |
Value: autorun | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ivacy_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
| (PID) Process: | (2664) ivacy-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Ivacy_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Ivacy | |||
Executable files
128
Suspicious files
25
Text files
518
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-M837B.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-OVCV4.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-DQ58B.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-NPCHK.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-FNU89.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-VD12Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-CLALO.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-NFBRM.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-4JFTJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | ivacy-windows-setup.tmp | C:\Program Files\Ivacy\is-VU2SE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3060 | Ivacy.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3060 | Ivacy.exe | 35.186.241.51:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
3060 | Ivacy.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3728 | Ivacy.exe | 52.219.72.80:443 | s3.eu-central-1.amazonaws.com | Amazon.com, Inc. | DE | unknown |
3728 | Ivacy.exe | 104.25.136.37:443 | atomapi.com | Cloudflare Inc | US | shared |
3728 | Ivacy.exe | 104.16.204.233:443 | dialerxn.dialertoserver.com | Cloudflare Inc | US | shared |
3728 | Ivacy.exe | 130.211.34.183:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
3728 | Ivacy.exe | 104.17.38.89:443 | apiv2.ivacy.com | Cloudflare Inc | US | shared |
— | — | 130.211.34.183:443 | api.mixpanel.com | Google Inc. | US | whitelisted |
3728 | Ivacy.exe | 13.32.222.163:443 | d3uym7n1flvv1x.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
3728 | Ivacy.exe | 52.216.137.126:443 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
s3.eu-central-1.amazonaws.com |
| shared |
atomapi.com |
| unknown |
dialerxn.dialertoserver.com |
| unknown |
s3.amazonaws.com |
| shared |
apiv2.ivacy.com |
| unknown |
d3uym7n1flvv1x.cloudfront.net |
| whitelisted |