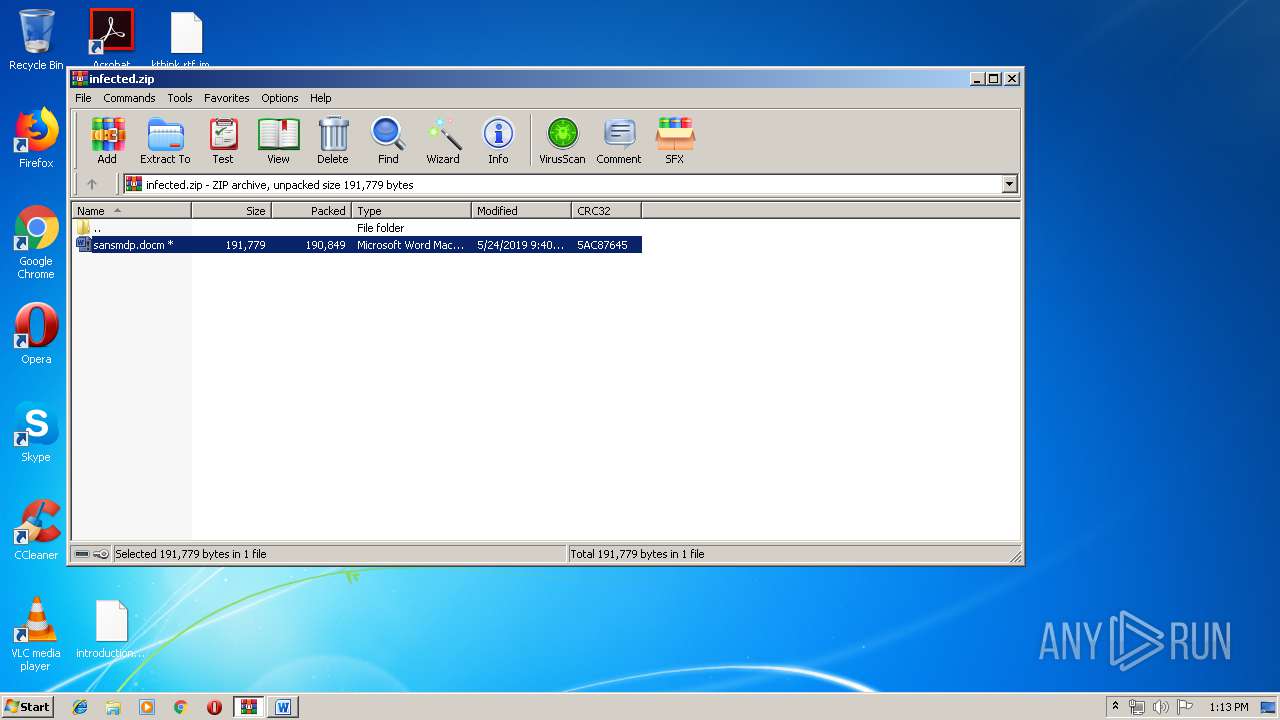
| File name: | infected.zip |
| Full analysis: | https://app.any.run/tasks/a3d67361-f4a1-4023-bb27-d16dbe3105d0 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 24, 2019, 12:10:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A155281886151663B451A2DFE470DACD |
| SHA1: | C9F86A29B5599EB6730D30BBB061087E5038FE09 |
| SHA256: | 2A1027BD978039615A122DD05D62FA60FAD6A6C9EA33361326225AC38A75DCE5 |
| SSDEEP: | 3072:hDk4DjcplonZEs3GkxFmnJk0yxduAqlkvBCbjBLoKJE2rHtxFyU5oWhtVcv5I+:HjcplwLXqJNEdjYcCb02hCeFVcvu+ |
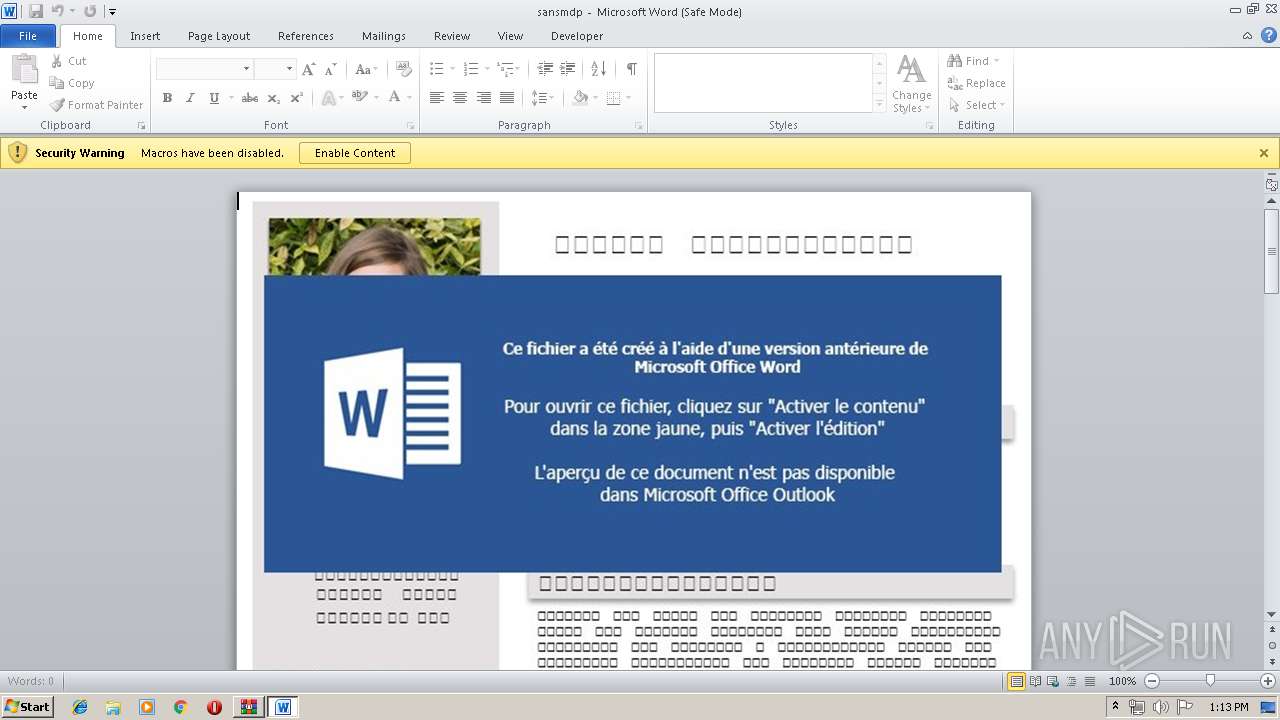
MALICIOUS
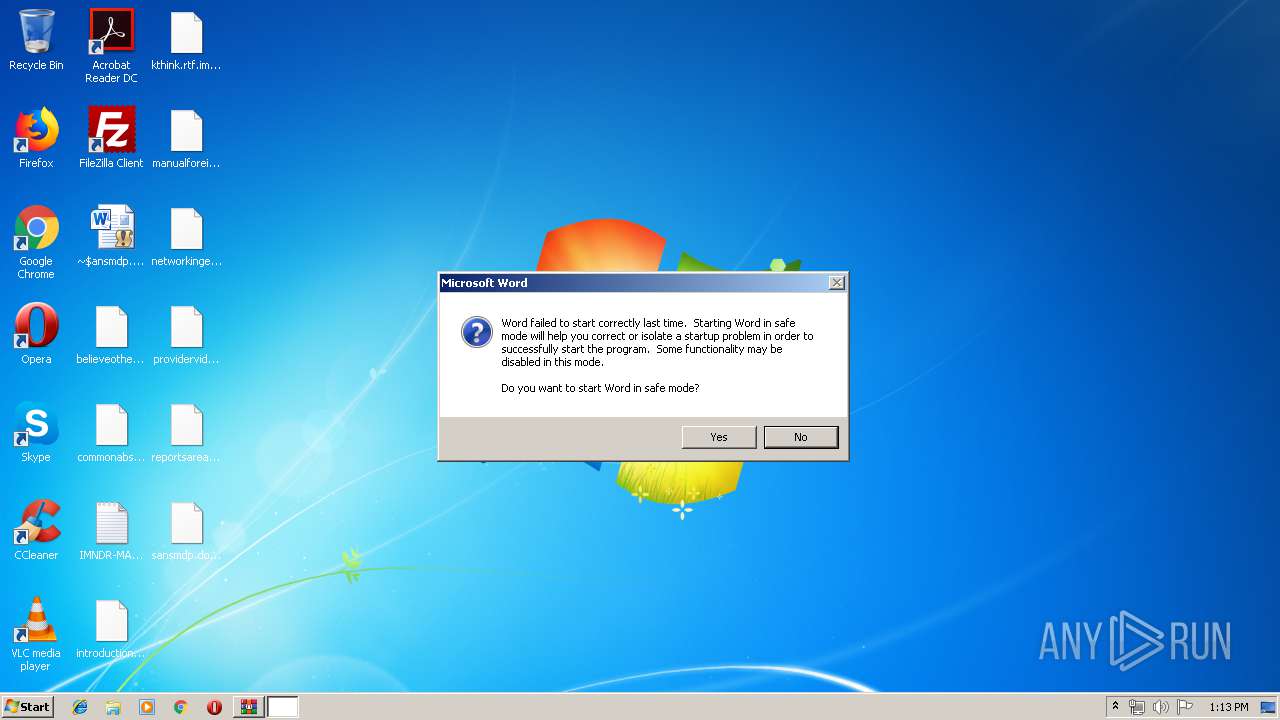
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
Application was dropped or rewritten from another process
- tryu234234.jmp (PID: 4080)
- tryu234234.jmp (PID: 6060)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
Actions looks like stealing of personal data
- tryu234234.jmp (PID: 4080)
Writes file to Word startup folder
- tryu234234.jmp (PID: 4080)
Changes settings of System certificates
- tryu234234.jmp (PID: 4080)
Connects to CnC server
- tryu234234.jmp (PID: 4080)
GANDCRAB detected
- tryu234234.jmp (PID: 4080)
Deletes shadow copies
- cmd.exe (PID: 1080)
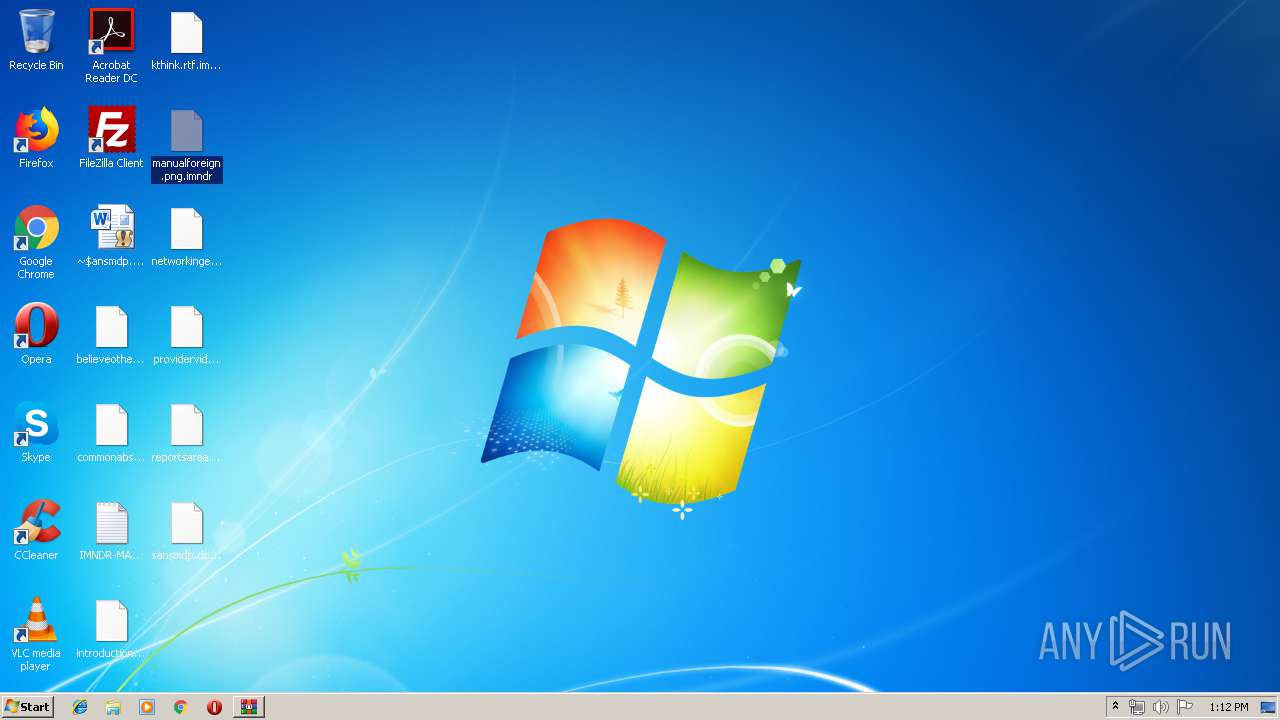
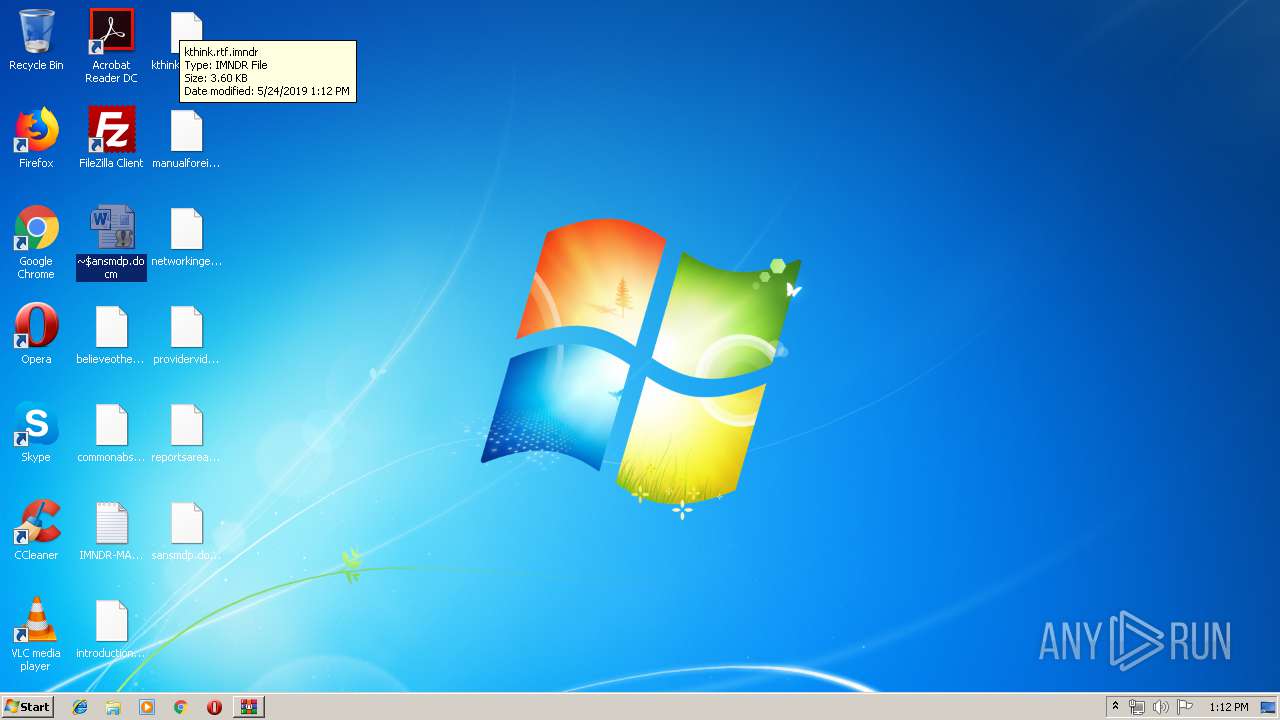
Renames files like Ransomware
- tryu234234.jmp (PID: 4080)
Dropped file may contain instructions of ransomware
- tryu234234.jmp (PID: 4080)
SUSPICIOUS
Starts application with an unusual extension
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
Creates files in the program directory
- tryu234234.jmp (PID: 4080)
Reads the cookies of Mozilla Firefox
- tryu234234.jmp (PID: 4080)
Starts CMD.EXE for commands execution
- tryu234234.jmp (PID: 4080)
- tryu234234.jmp (PID: 6060)
Adds / modifies Windows certificates
- tryu234234.jmp (PID: 4080)
Starts CMD.EXE for self-deleting
- tryu234234.jmp (PID: 6060)
Creates files in the user directory
- tryu234234.jmp (PID: 4080)
Executed as Windows Service
- vssvc.exe (PID: 6136)
INFO
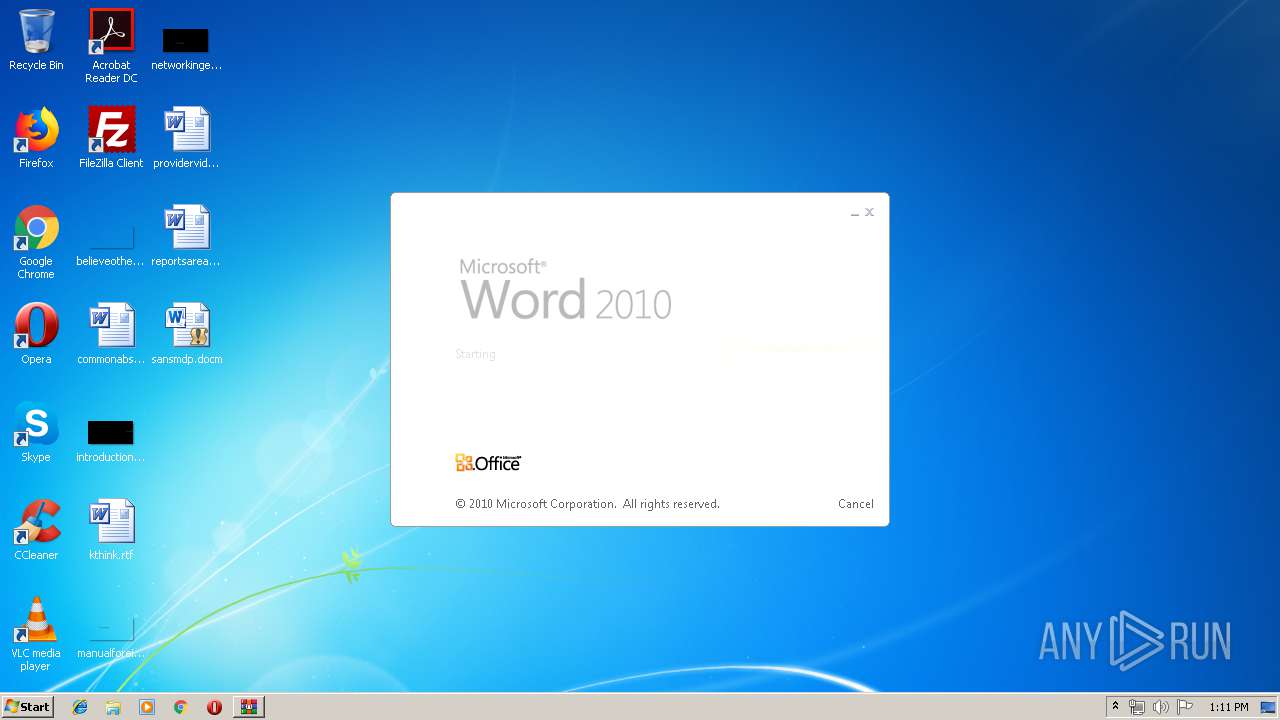
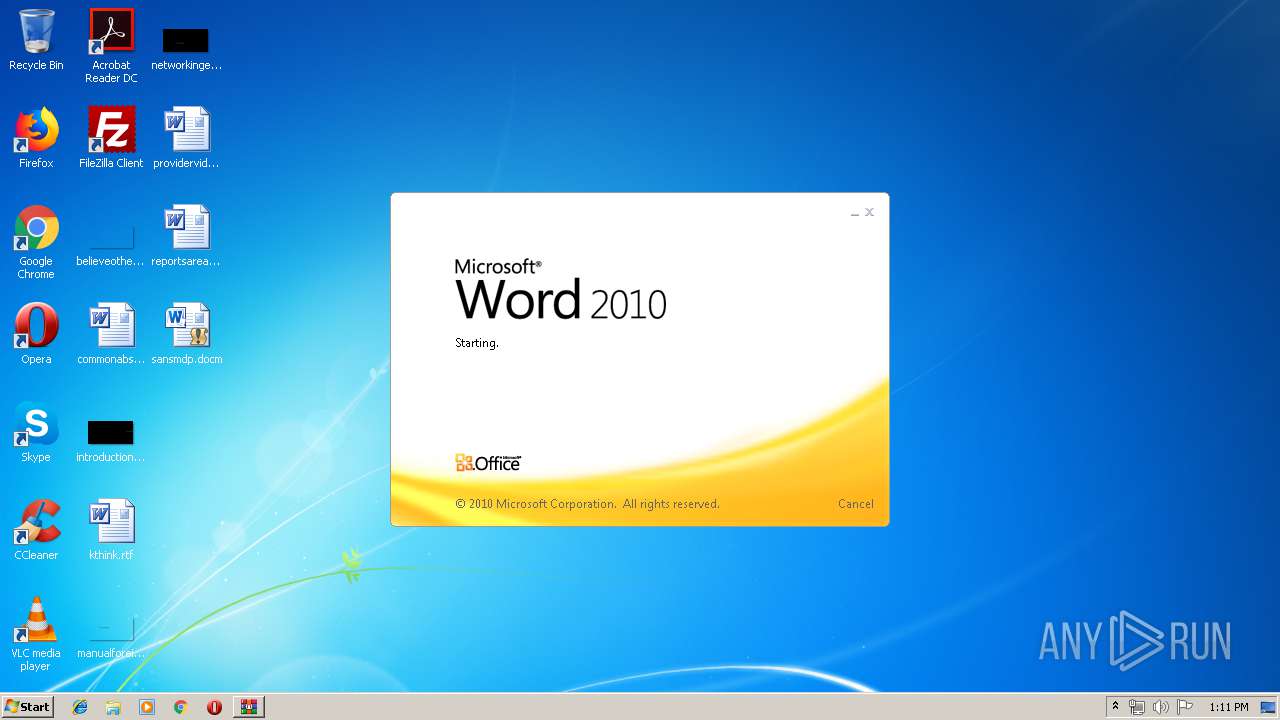
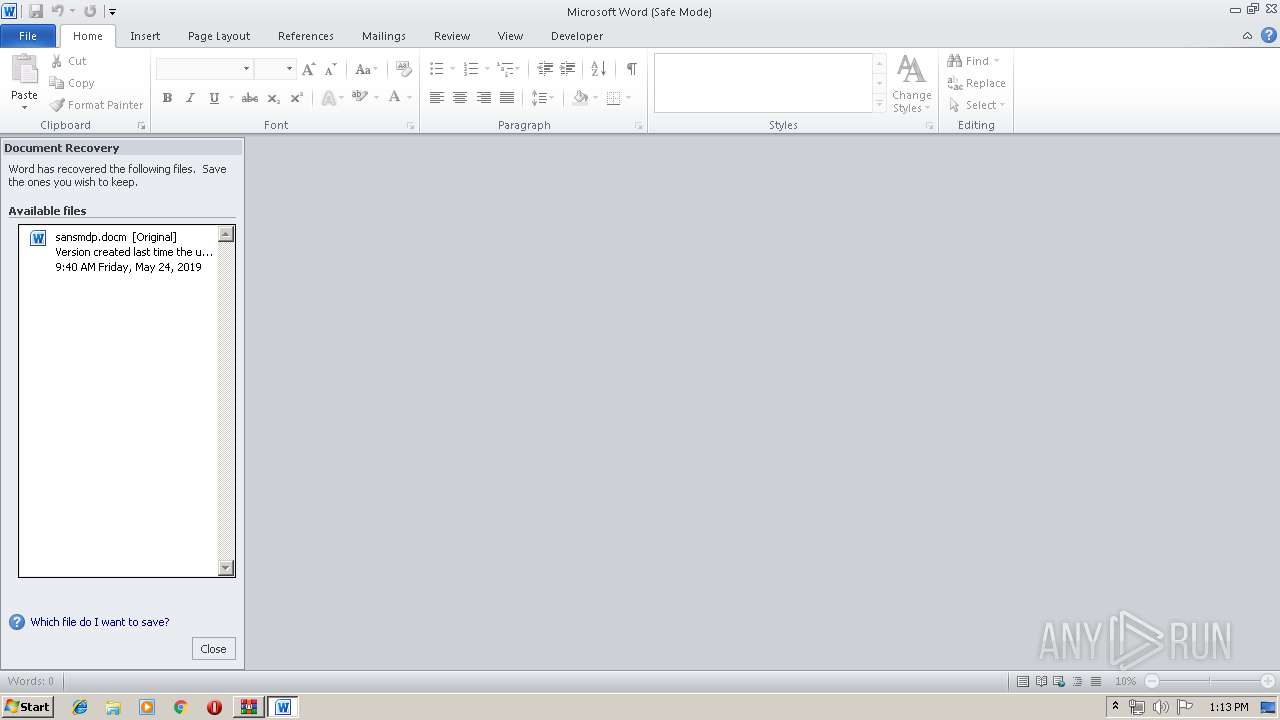
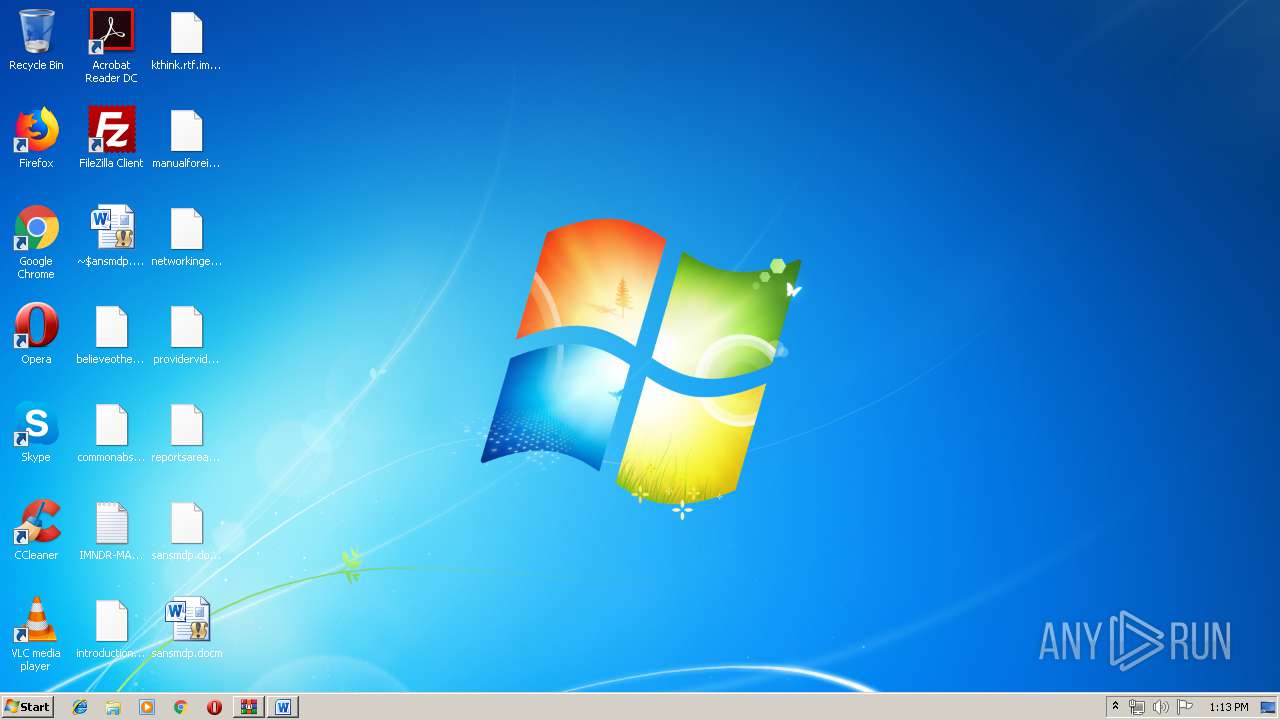
Manual execution by user
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
- WINWORD.EXE (PID: 5764)
Creates files in the user directory
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3408)
- WINWORD.EXE (PID: 5844)
- WINWORD.EXE (PID: 5764)
Dropped object may contain Bitcoin addresses
- tryu234234.jmp (PID: 4080)
Reads settings of System Certificates
- WINWORD.EXE (PID: 5844)
Dropped object may contain TOR URL's
- tryu234234.jmp (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
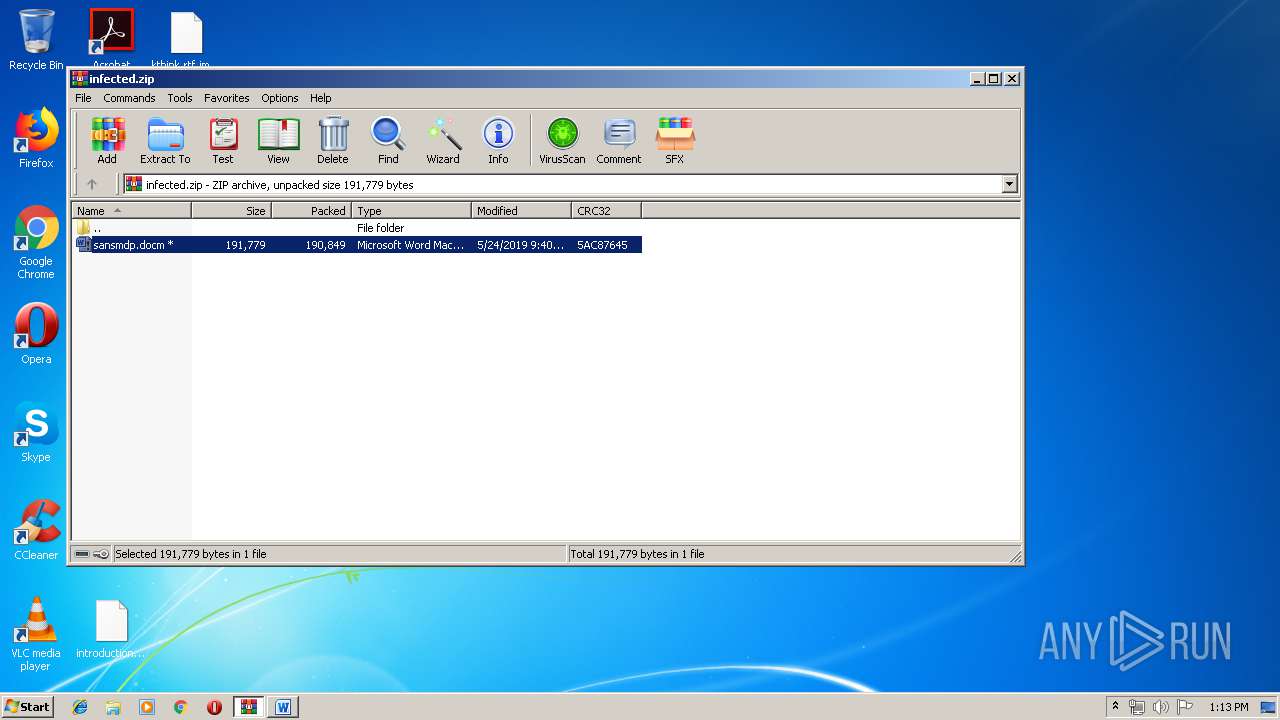
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
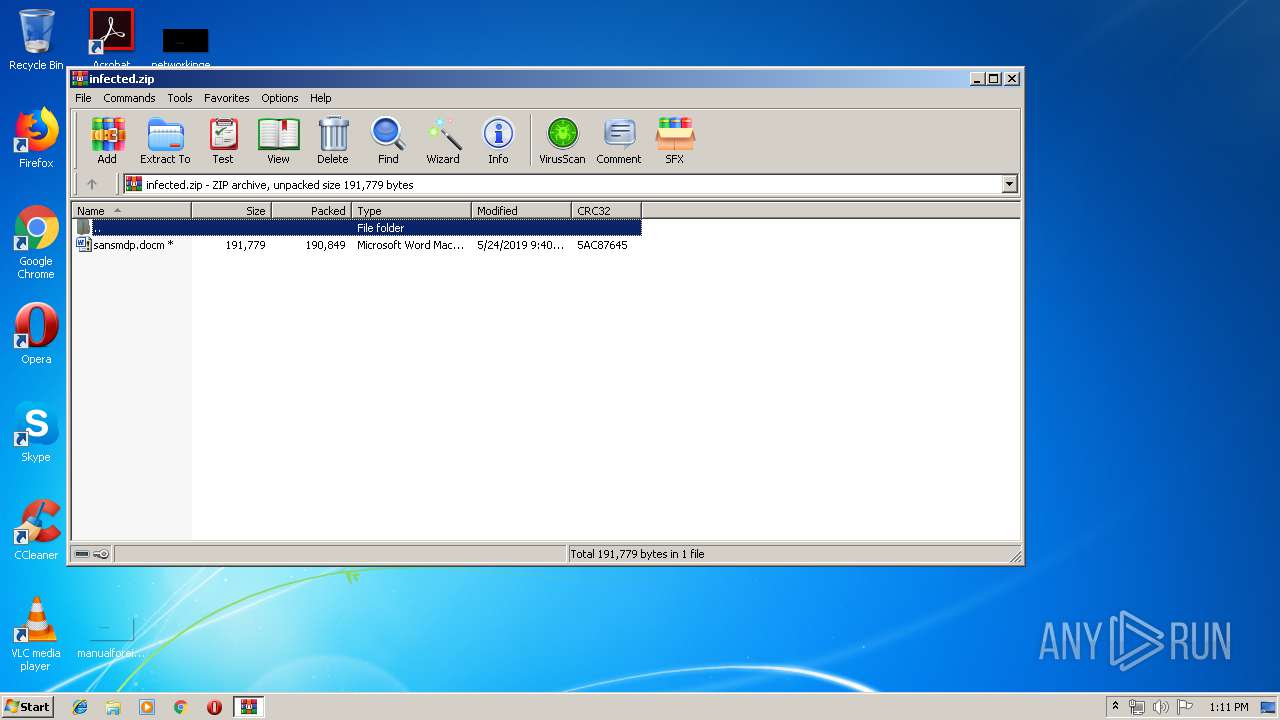
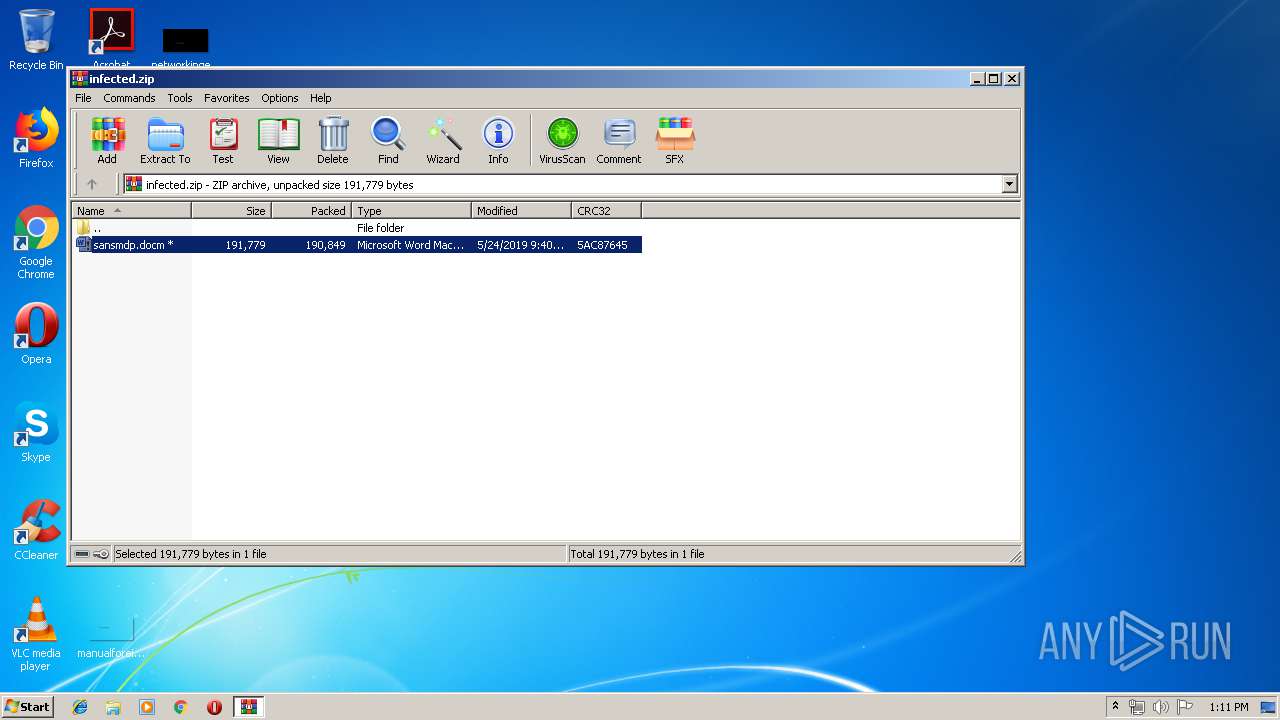
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 10:40:05 |
| ZipCRC: | 0x5ac87645 |
| ZipCompressedSize: | 190849 |
| ZipUncompressedSize: | 191779 |
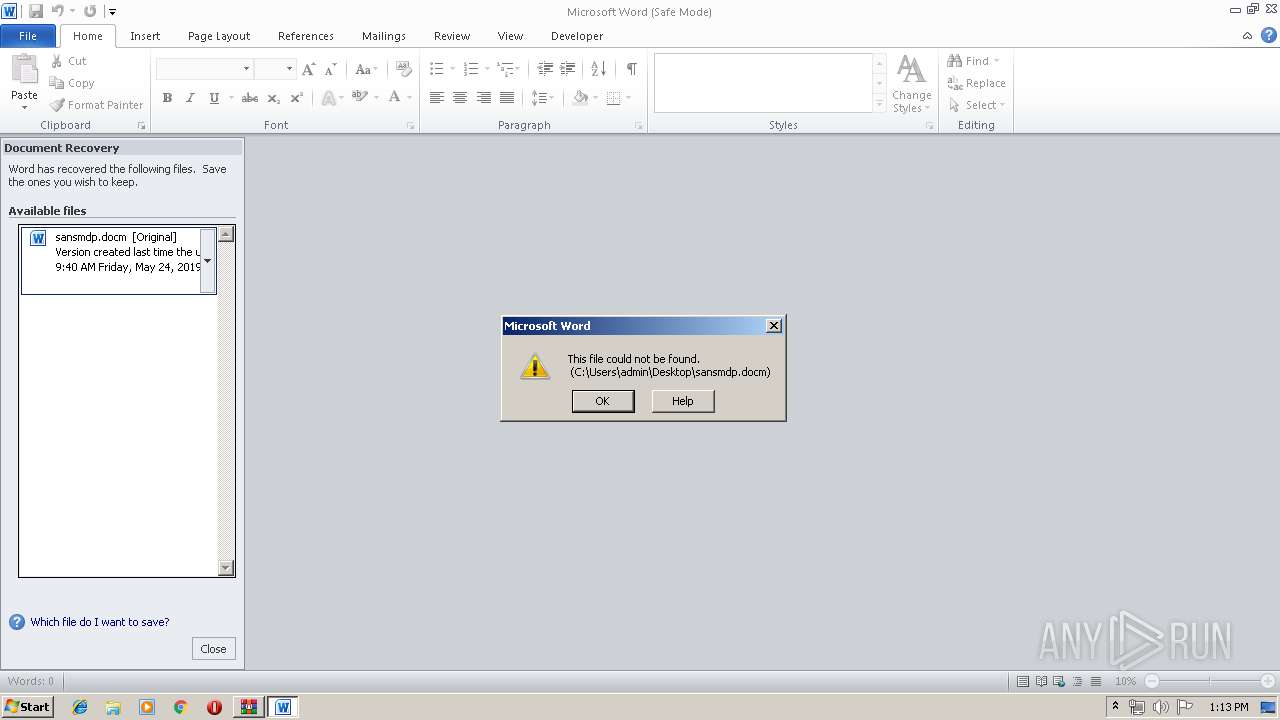
| ZipFileName: | sansmdp.docm |
Total processes
51
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
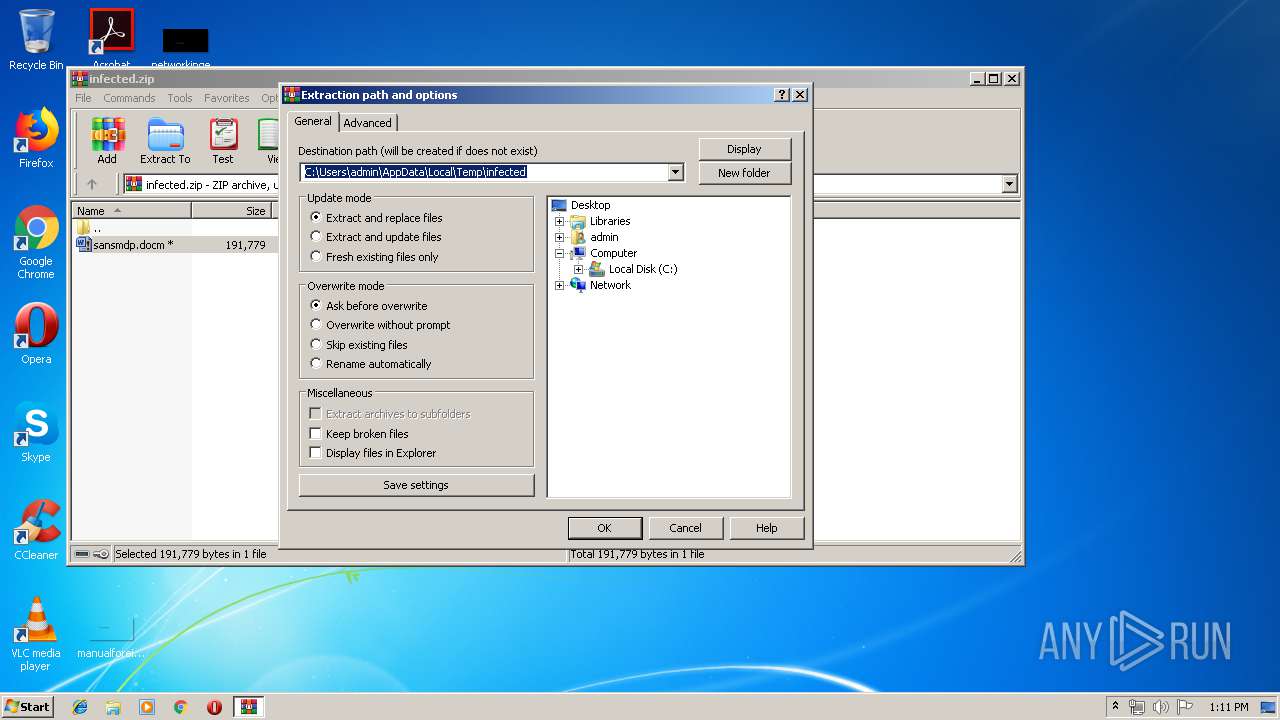
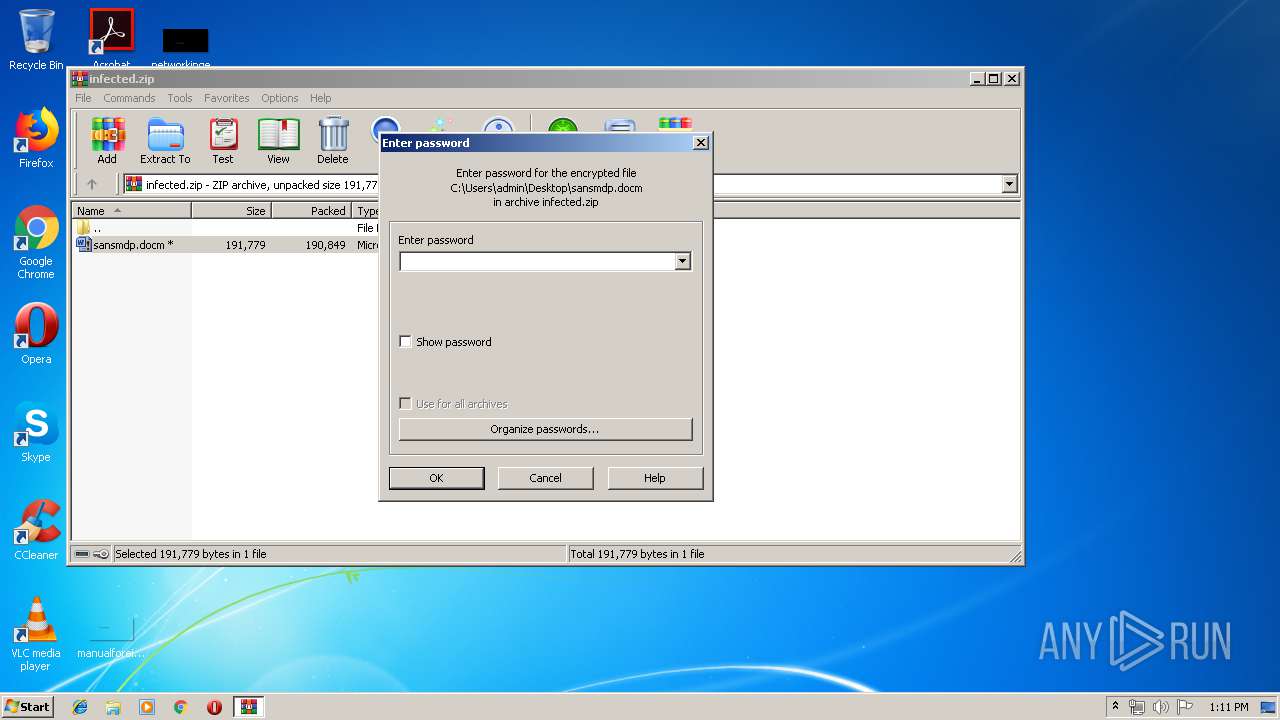
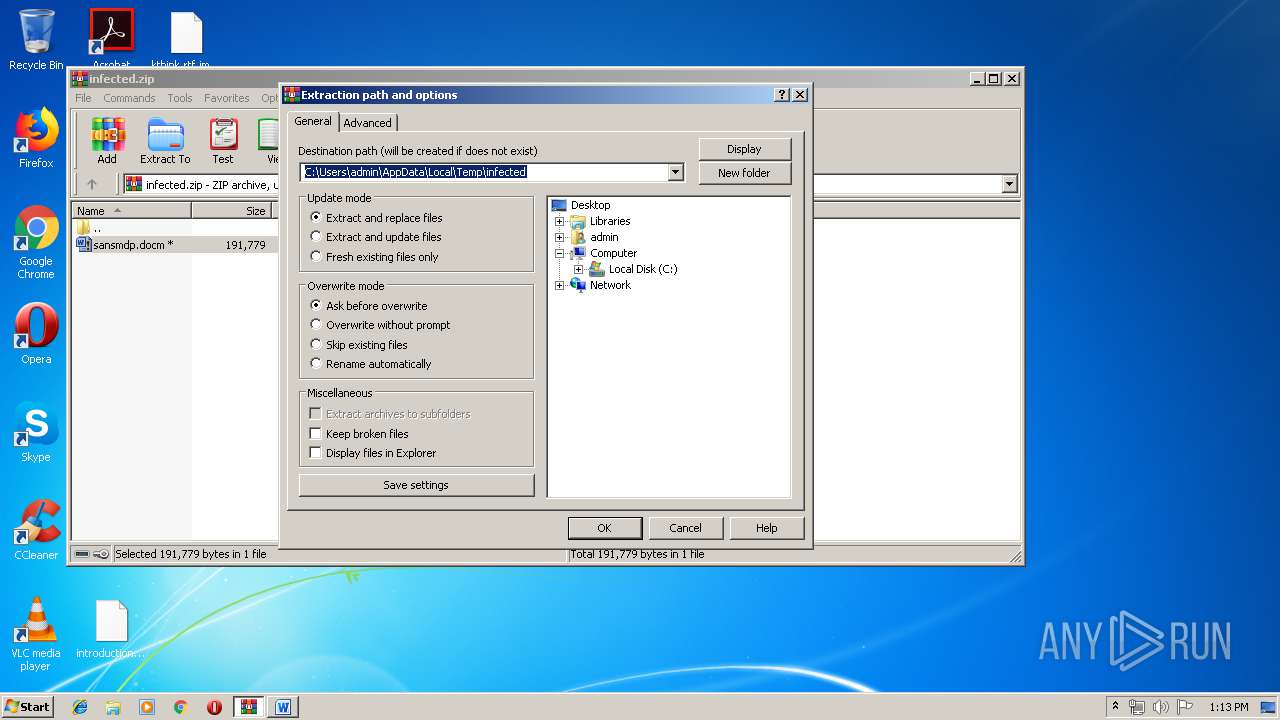
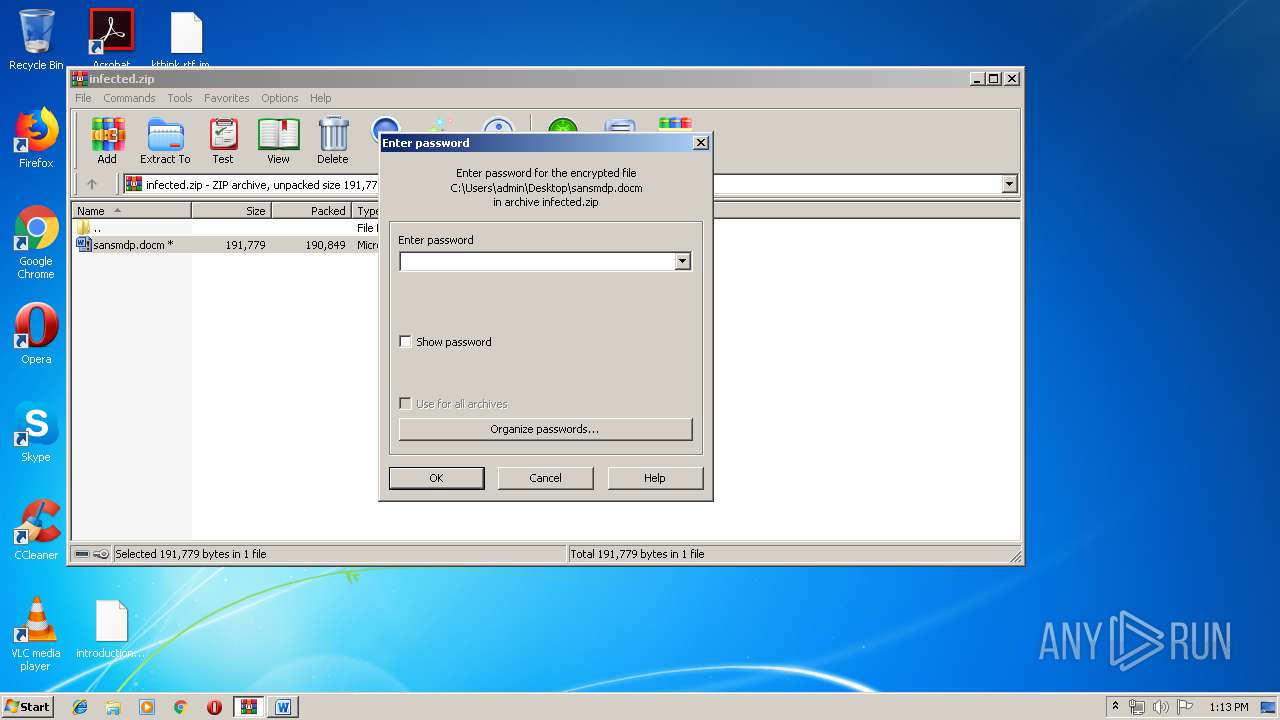
| 252 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\infected.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1080 | "C:\Windows\system32\cmd.exe" /c vssadmin delete shadows /all /quiet | C:\Windows\system32\cmd.exe | tryu234234.jmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
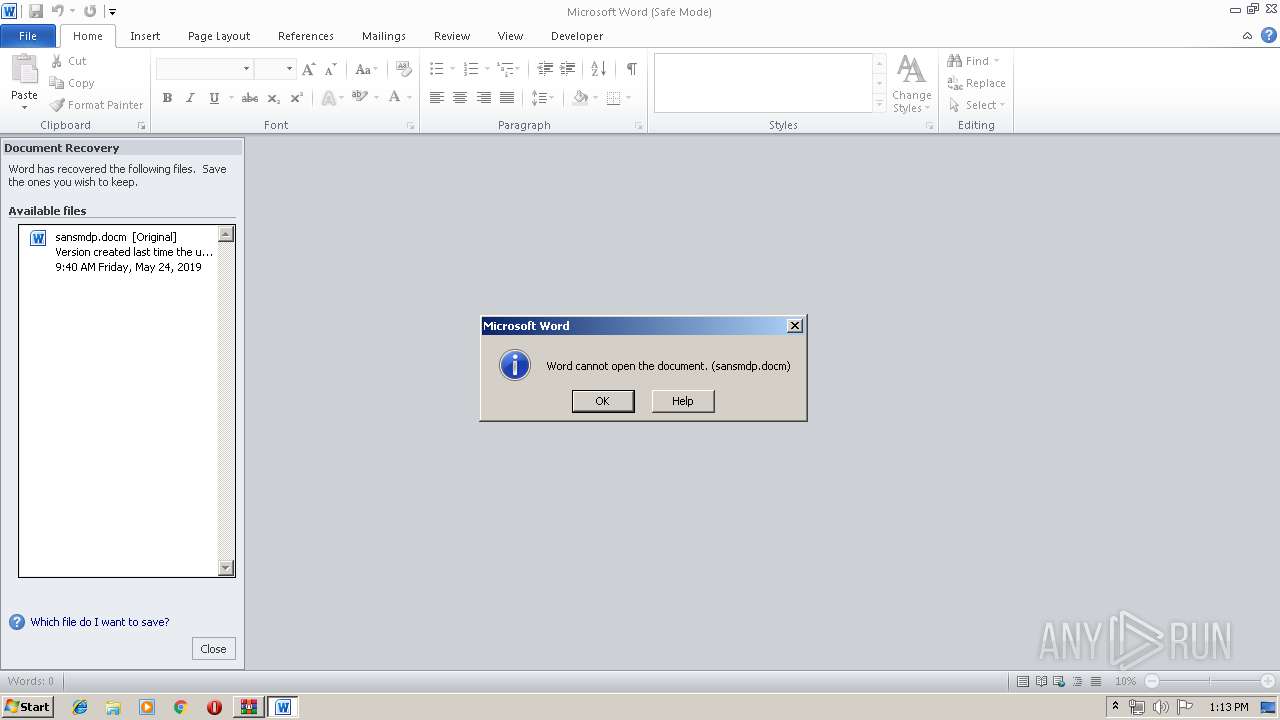
| 3408 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\sansmdp.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4080 | C:\Users\admin\AppData\Local\Temp\tryu234234.jmp | C:\Users\admin\AppData\Local\Temp\tryu234234.jmp | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5416 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5764 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\sansmdp.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 5844 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$ansmdp.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 6060 | C:\Users\admin\AppData\Local\Temp\tryu234234.jmp | C:\Users\admin\AppData\Local\Temp\tryu234234.jmp | — | WINWORD.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6136 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 9172 | "C:\Windows\System32\cmd.exe" /c timeout -c 5 & del "C:\Users\admin\AppData\Local\Temp\tryu234234.jmp" /f /q | C:\Windows\System32\cmd.exe | tryu234234.jmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 641
Read events
1 817
Write events
795
Delete events
29
Modification events
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\infected.zip | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
3
Suspicious files
472
Text files
323
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\320582B3.jpeg | — | |
MD5:— | SHA256:— | |||
| 3408 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\sansmdp.docm.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3408 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D5D0979F-F724-474F-B812-6A5736706DE9}.tmp | binary | |
MD5:— | SHA256:— | |||
| 4080 | tryu234234.jmp | C:\MSOCache\IMNDR-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 4080 | tryu234234.jmp | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3408 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 4080 | tryu234234.jmp | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 4080 | tryu234234.jmp | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.imndr | — | |
MD5:— | SHA256:— | |||
| 3408 | WINWORD.EXE | C:\Users\admin\Desktop\~$ansmdp.docm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
18
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5844 | WINWORD.EXE | GET | 200 | 52.109.32.27:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | GB | xml | 1.99 Kb | whitelisted |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
4080 | tryu234234.jmp | GET | 301 | 185.52.2.154:80 | http://www.kakaocorp.link/ | NL | html | 162 b | malicious |
5844 | WINWORD.EXE | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3408 | WINWORD.EXE | 87.98.179.183:443 | coelabetoregranteke.info | OVH SAS | FR | suspicious |
4080 | tryu234234.jmp | 185.52.2.154:80 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
4080 | tryu234234.jmp | 185.52.2.154:443 | www.kakaocorp.link | RouteLabel V.O.F. | NL | suspicious |
5844 | WINWORD.EXE | 52.109.32.27:80 | office14client.microsoft.com | Microsoft Corporation | GB | whitelisted |
5844 | WINWORD.EXE | 23.38.49.173:443 | officestore.microsoft.com | Akamai International B.V. | NL | whitelisted |
5844 | WINWORD.EXE | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
5844 | WINWORD.EXE | 2.18.232.50:443 | omextemplates.content.office.net | Akamai International B.V. | — | whitelisted |
5844 | WINWORD.EXE | 87.98.179.183:443 | coelabetoregranteke.info | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
coelabetoregranteke.info |
| suspicious |
www.kakaocorp.link |
| malicious |
office14client.microsoft.com |
| whitelisted |
officestore.microsoft.com |
| whitelisted |
omextemplates.content.office.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4080 | tryu234234.jmp | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
4080 | tryu234234.jmp | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2 ETPRO signatures available at the full report