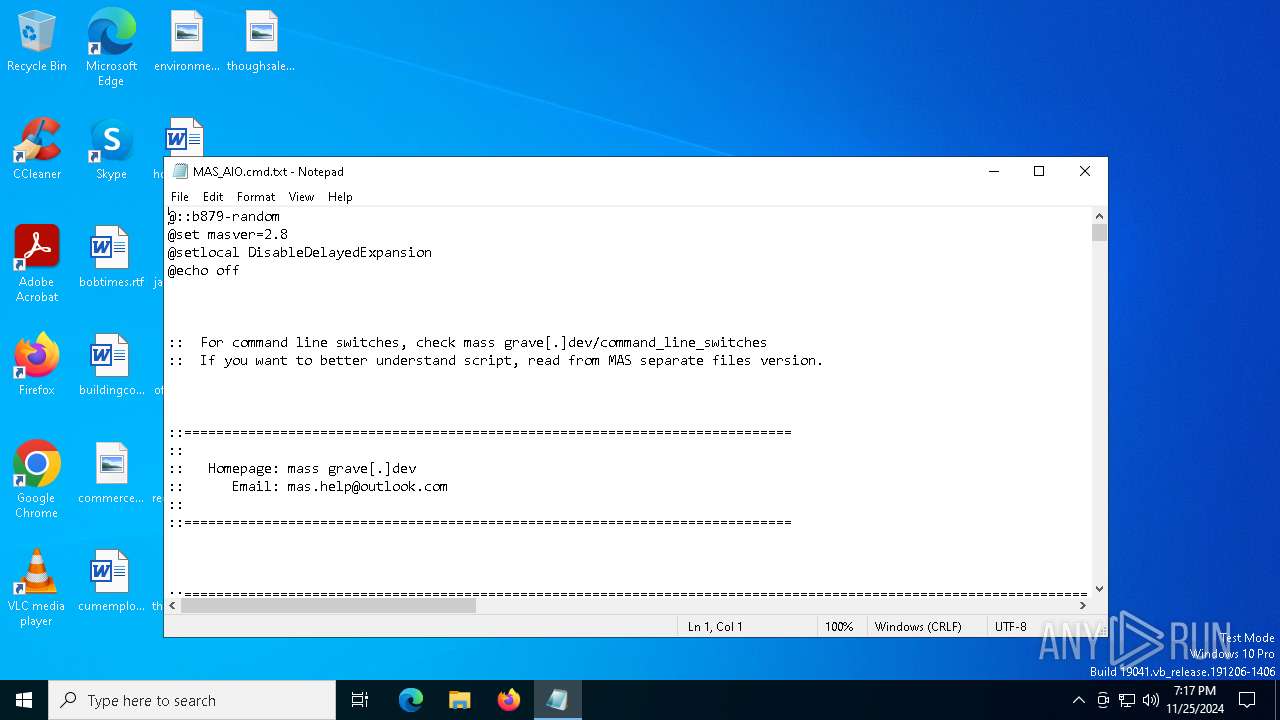
| File name: | MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/d5619a9f-0f90-4cbb-a701-5e6749a8f392 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2024, 19:17:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (348), with CRLF line terminators |
| MD5: | 4B888D91EFF0C5F1C811EE82CBE07C06 |
| SHA1: | DCB7A702E0F2A3B17AF78D858AF01B736FAD7C31 |
| SHA256: | 2A0A5F9675BA93D11DF5EB531810F8097D1C13CE3A723FC2235A85127E86E172 |
| SSDEEP: | 3072:6I7RnkRVR8Rr0FaRYIzOBFRZA5RvFw2JGBMZgnnwBRdpRkRuRzRDCj4SRKRYRoZV:YtICrwFwYi5enlTsmBUAJ0ykpBwuI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 1080)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4640)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 3288)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4640)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 3288)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 4308)
- powershell.exe (PID: 6344)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 4012)
- powershell.exe (PID: 1540)
- cmd.exe (PID: 1080)
Application launched itself
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 4012)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4640)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 3288)
Executing commands from ".cmd" file
- cmd.exe (PID: 4308)
- powershell.exe (PID: 6344)
- cmd.exe (PID: 6908)
- powershell.exe (PID: 1540)
- cmd.exe (PID: 1080)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 1080)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6452)
Checks operating system version
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 1080)
Manual execution by a user
- cmd.exe (PID: 4308)
Starts MODE.COM to configure console settings
- mode.com (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
207
Monitored processes
81
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | find /i "True" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | "C:\WINDOWS\System32\cmd.exe" /c ""C:\Users\admin\Desktop\MAS_AIO.cmd" -el -el -qedit" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | powershell.exe "$t=[AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); $t.DefinePInvokeMethod('GetStdHandle', 'kernel32.dll', 22, 1, [IntPtr], @([Int32]), 1, 3).SetImplementationFlags(128); $t.DefinePInvokeMethod('SetConsoleMode', 'kernel32.dll', 22, 1, [Boolean], @([IntPtr], [Int32]), 1, 3).SetImplementationFlags(128); $k=$t.CreateType(); $b=$k::SetConsoleMode($k::GetStdHandle(-10), 0x0080); & cmd.exe '/c' '"""C:\Users\admin\Desktop\MAS_AIO.cmd""" -el -el -qedit'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 348
Read events
30 348
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hsg4fjfm.fty.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jvdtflg2.soe.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wsqgep3g.4yu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yzj1ckun.n3t.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nkrso5is.inj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6004 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_45xnkc4s.slj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0qeomkyp.j0n.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4668 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:3FD4B4487620D4EE724CC724304FB979 | SHA256:B0C8AA046945418A3EA8087321FC746596FCF7A7A483790F38EAD66E5F1946F6 | |||
| 5488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dffmxfks.ey4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hehzhrug.ser.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.42.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.42.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6336 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1536 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.16.110.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.42.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.42.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |