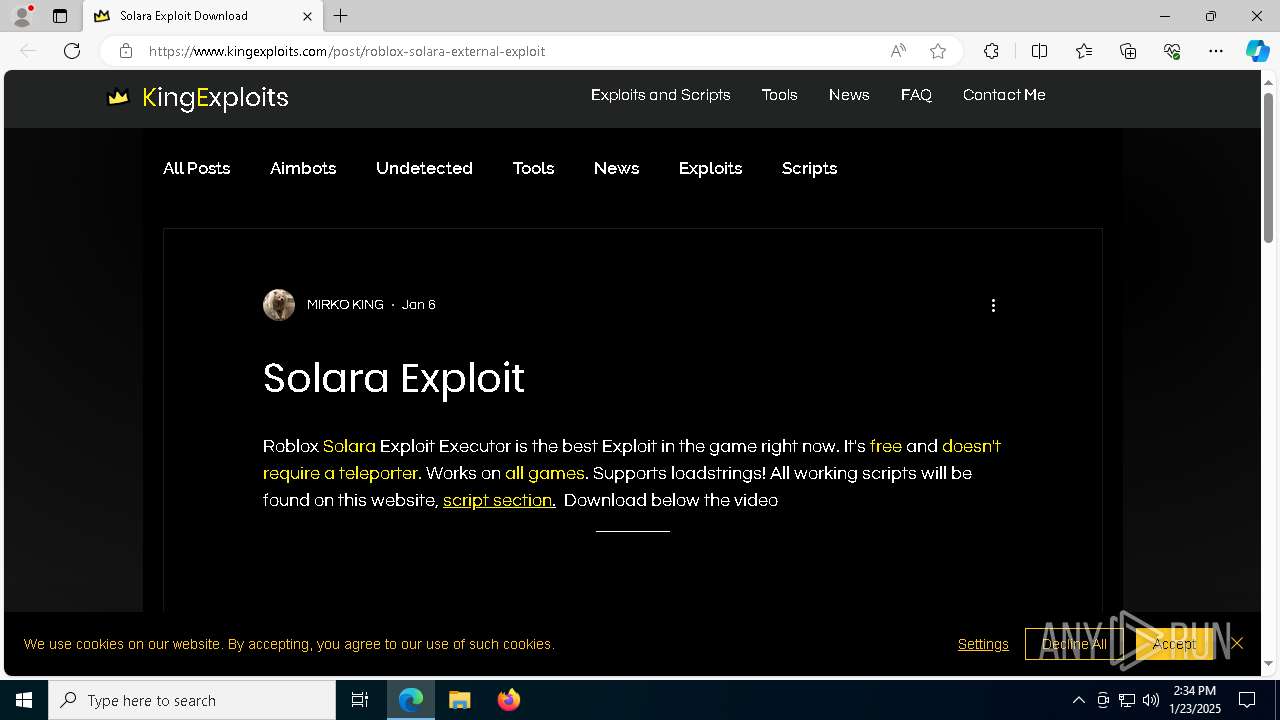
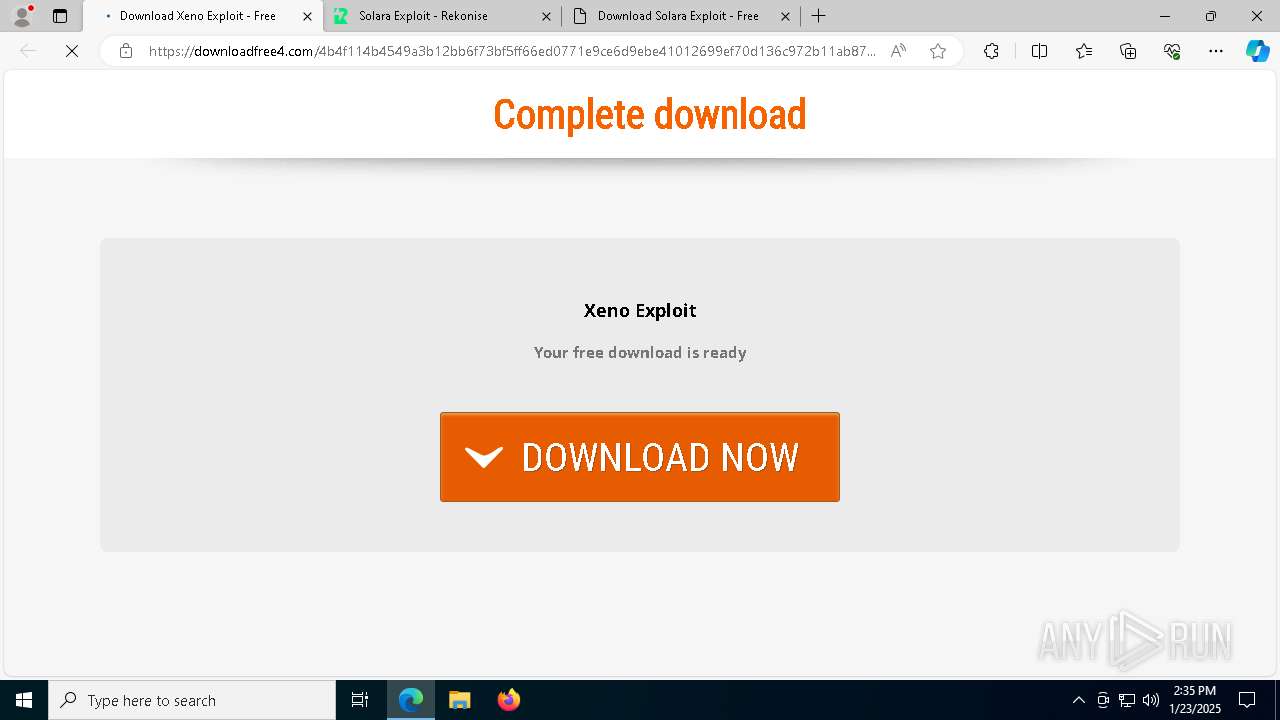
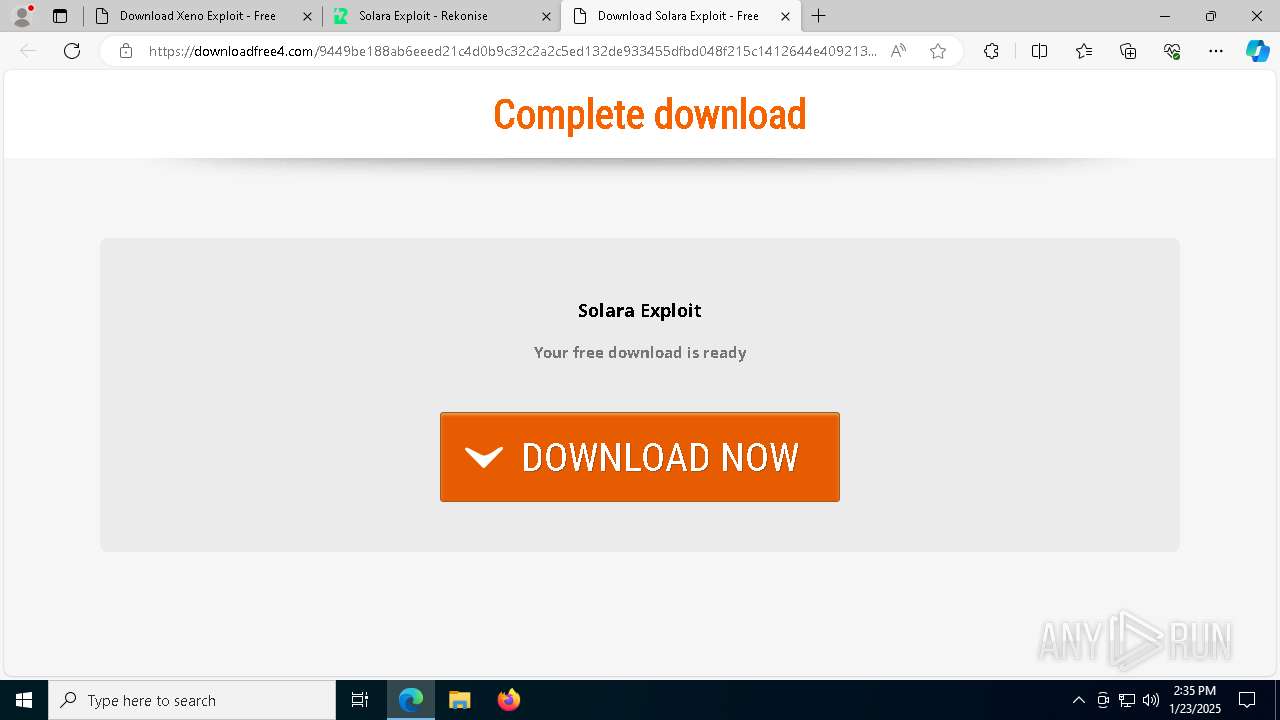
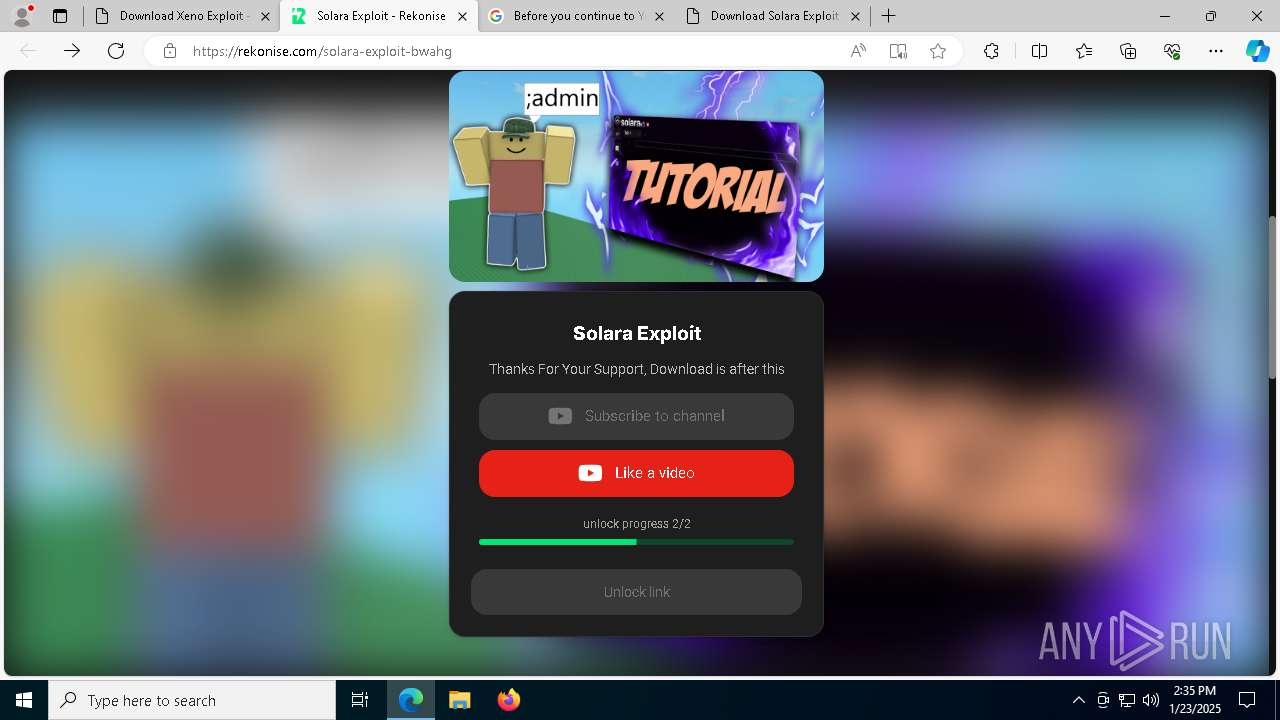
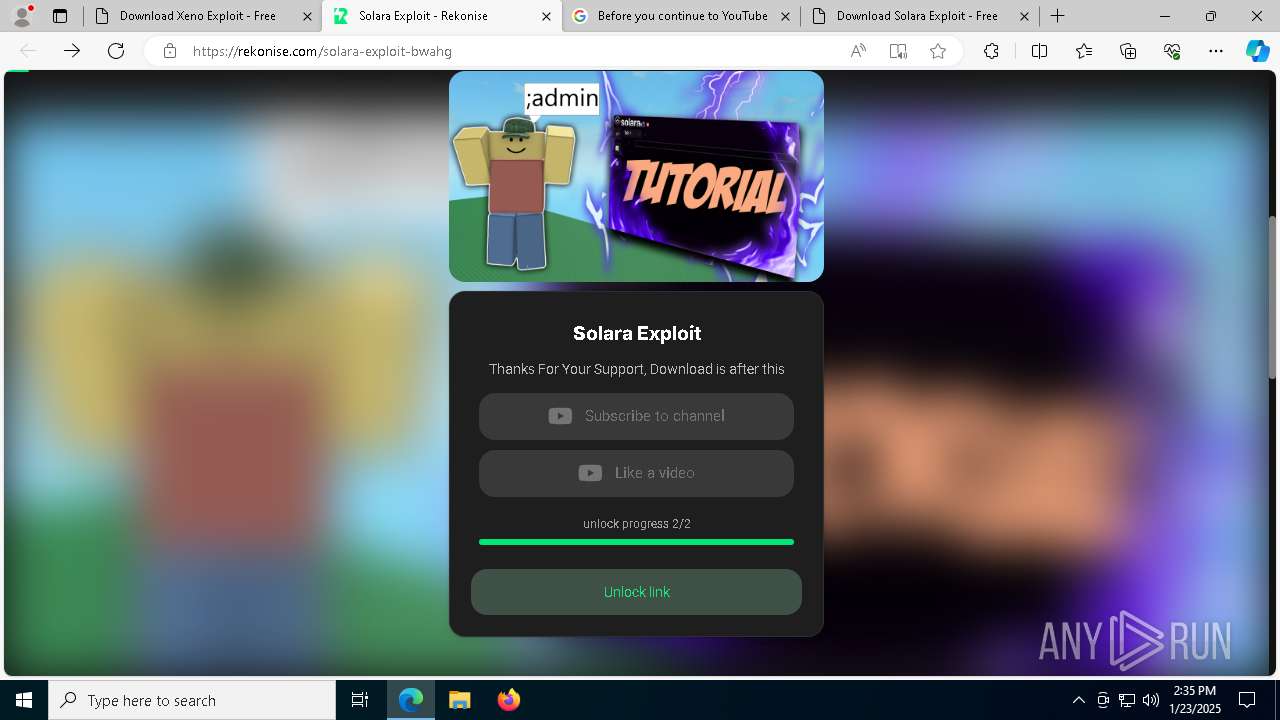
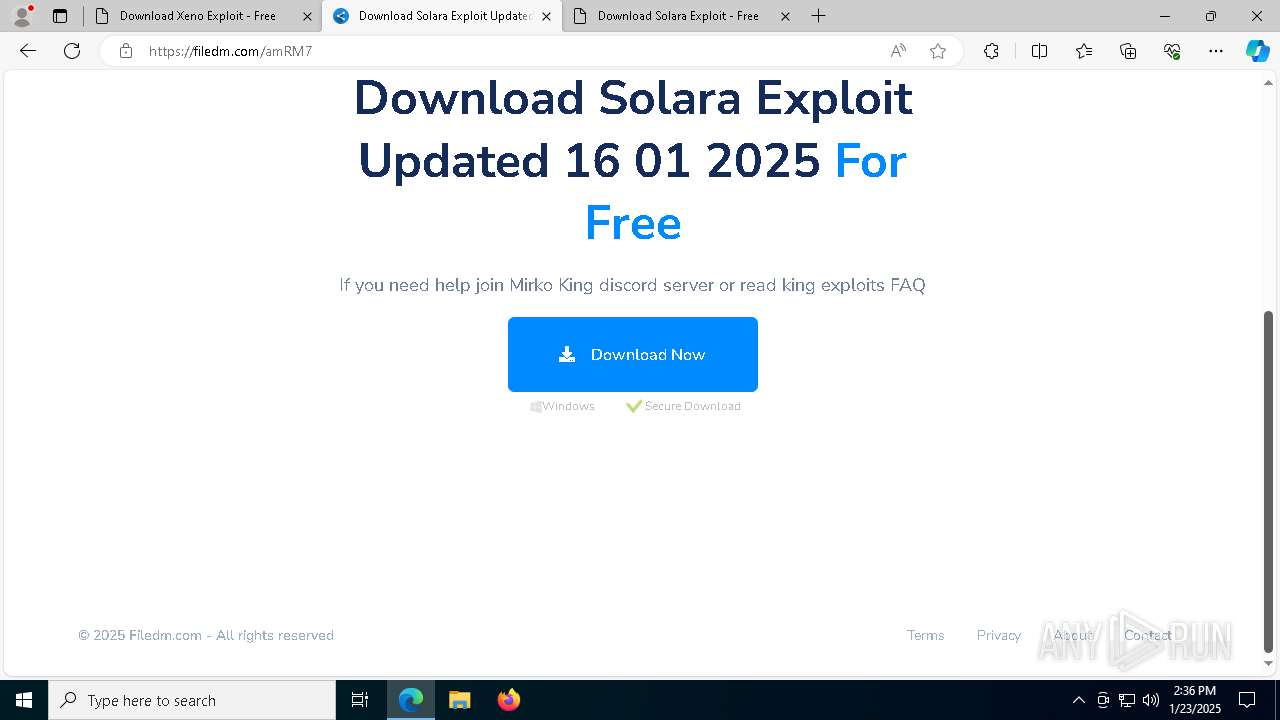
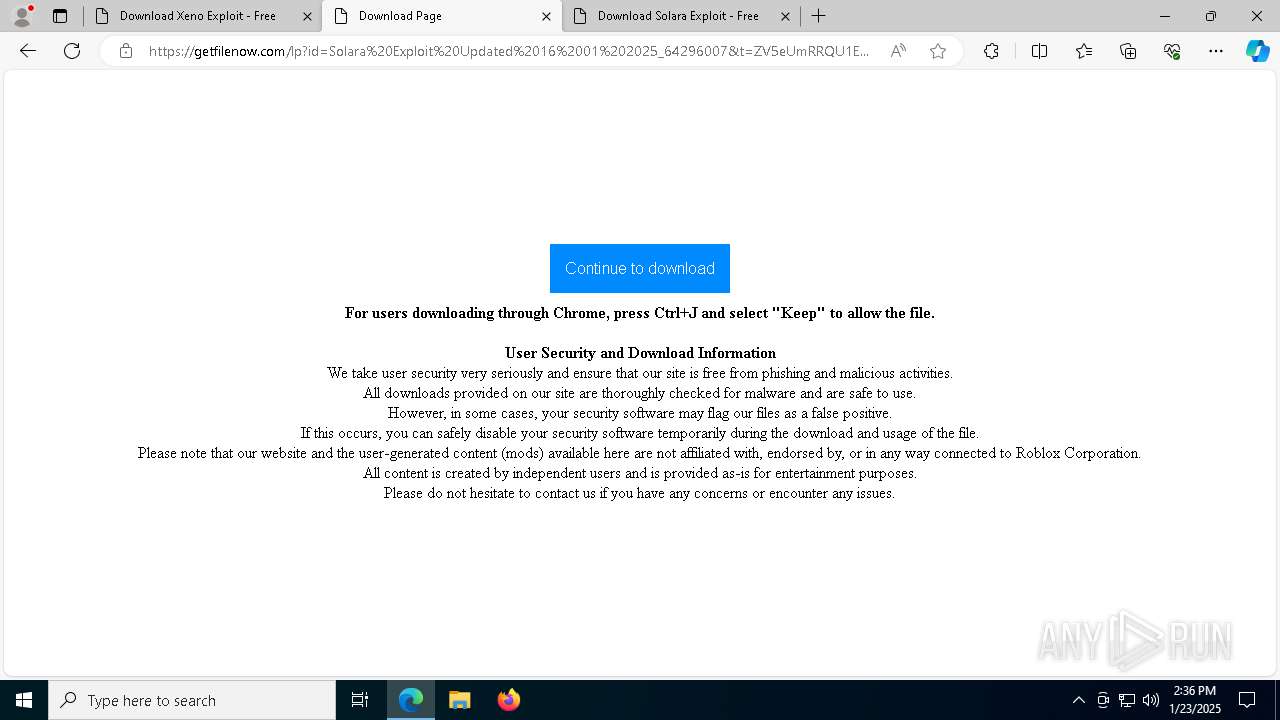
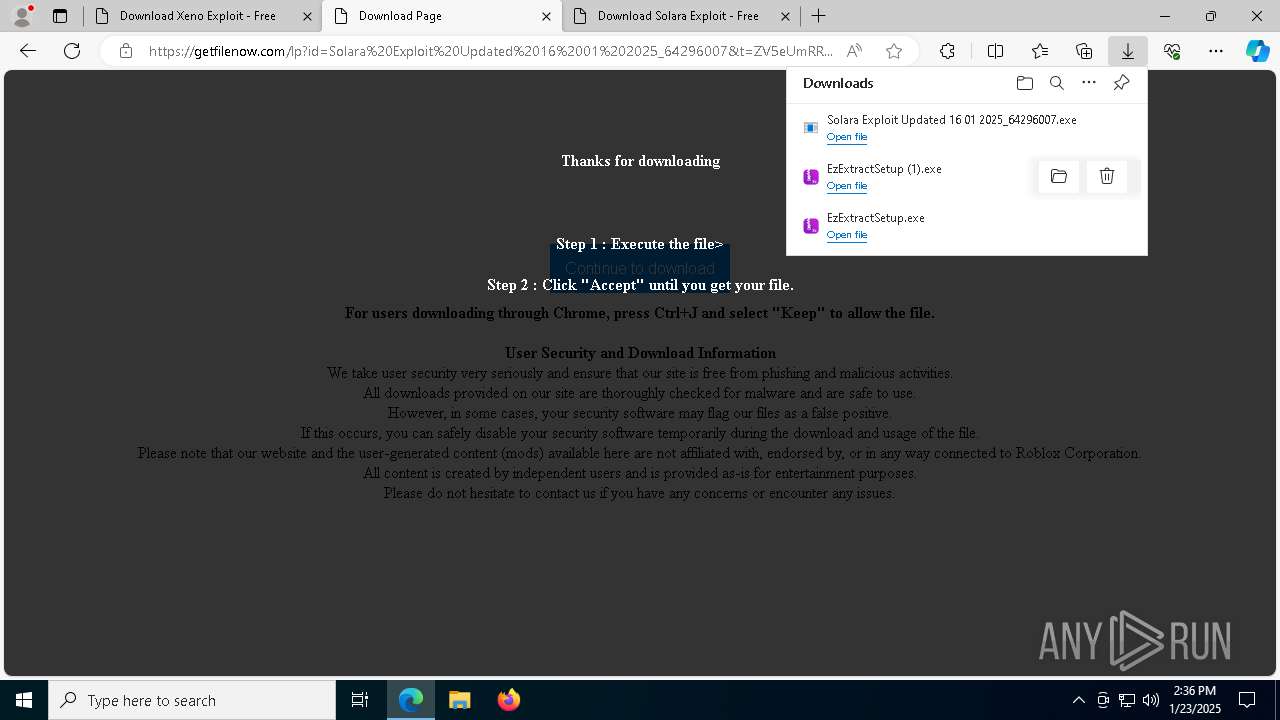
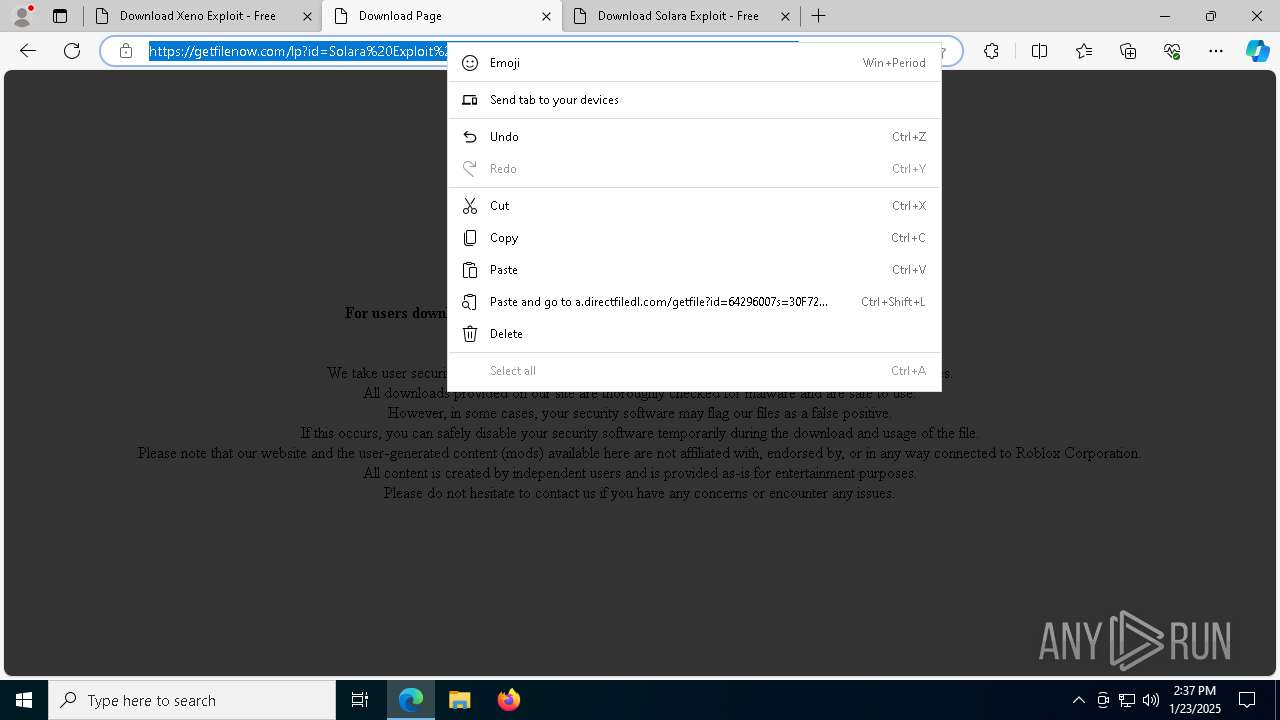
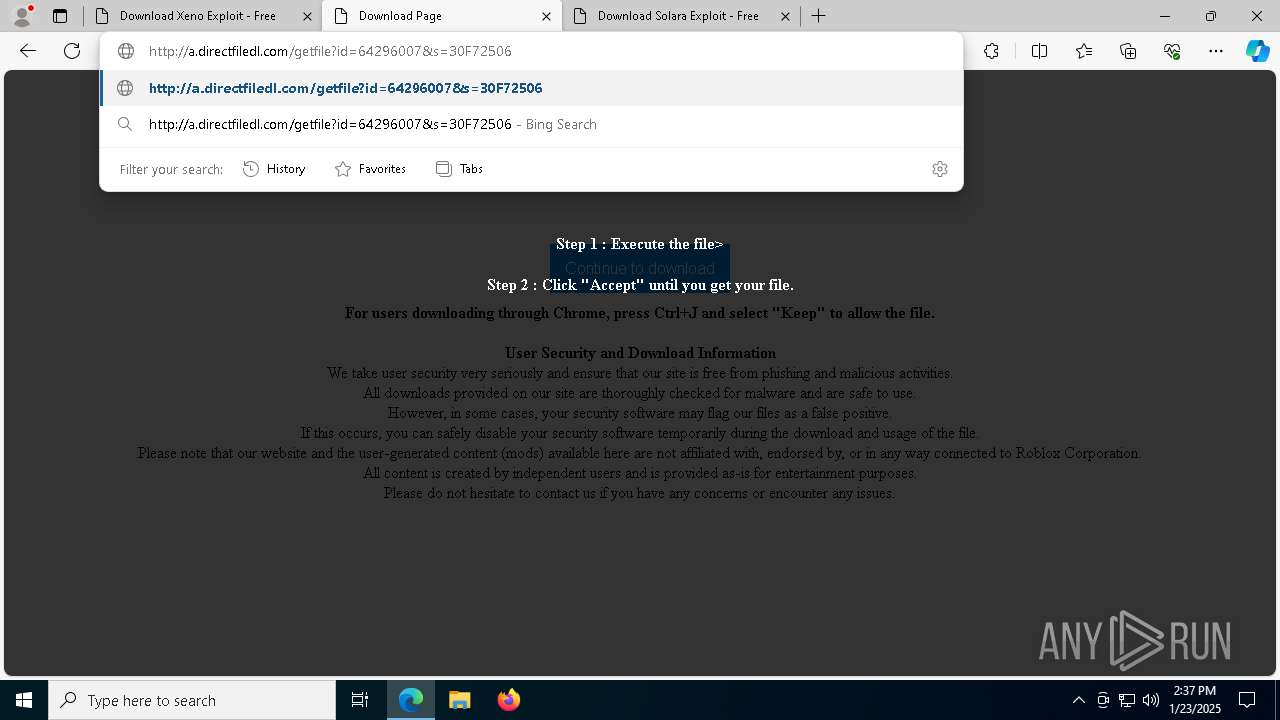
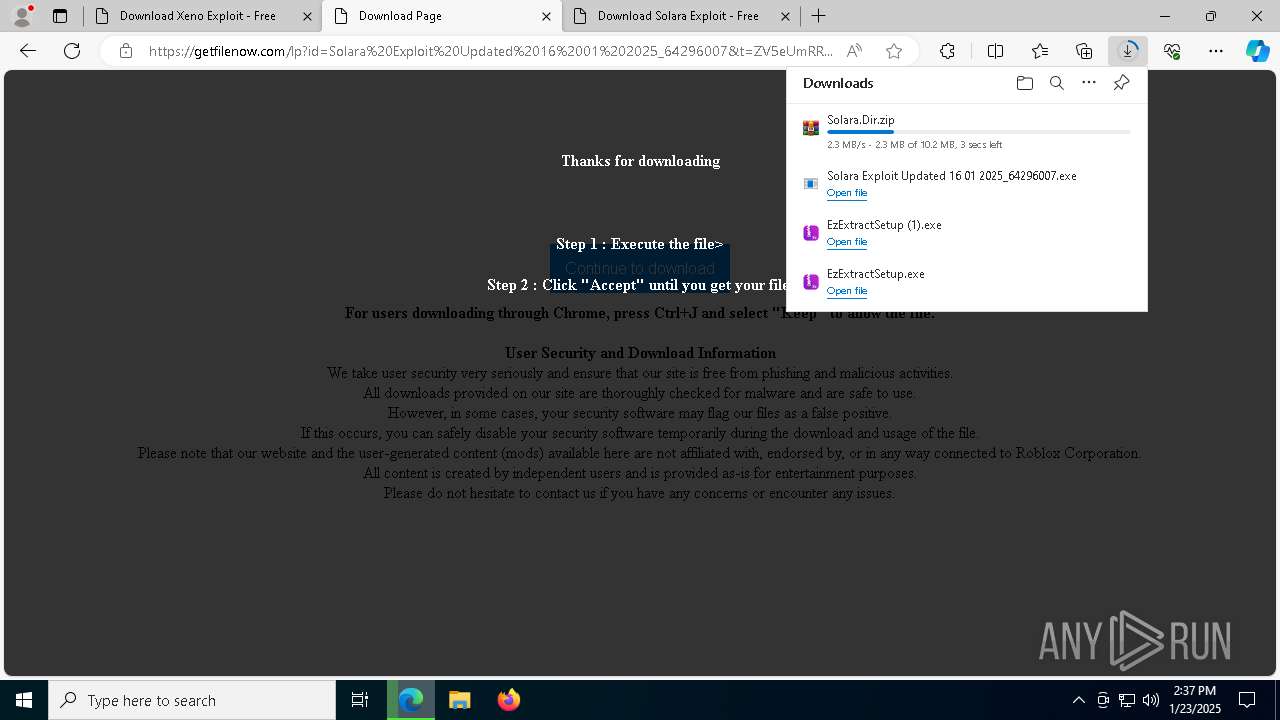
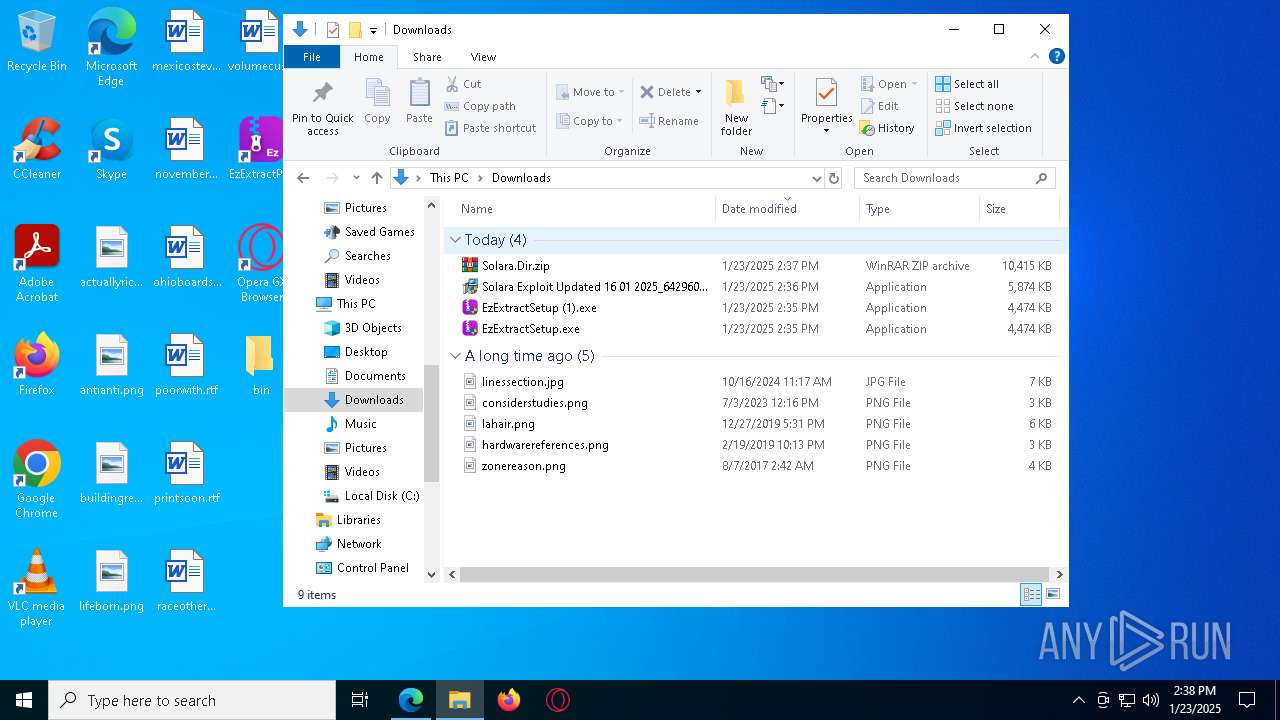
| URL: | https://www.kingexploits.com/post/roblox-solara-external-exploit |
| Full analysis: | https://app.any.run/tasks/218a5d20-56cd-4b2b-8515-05bbb7c8bff5 |
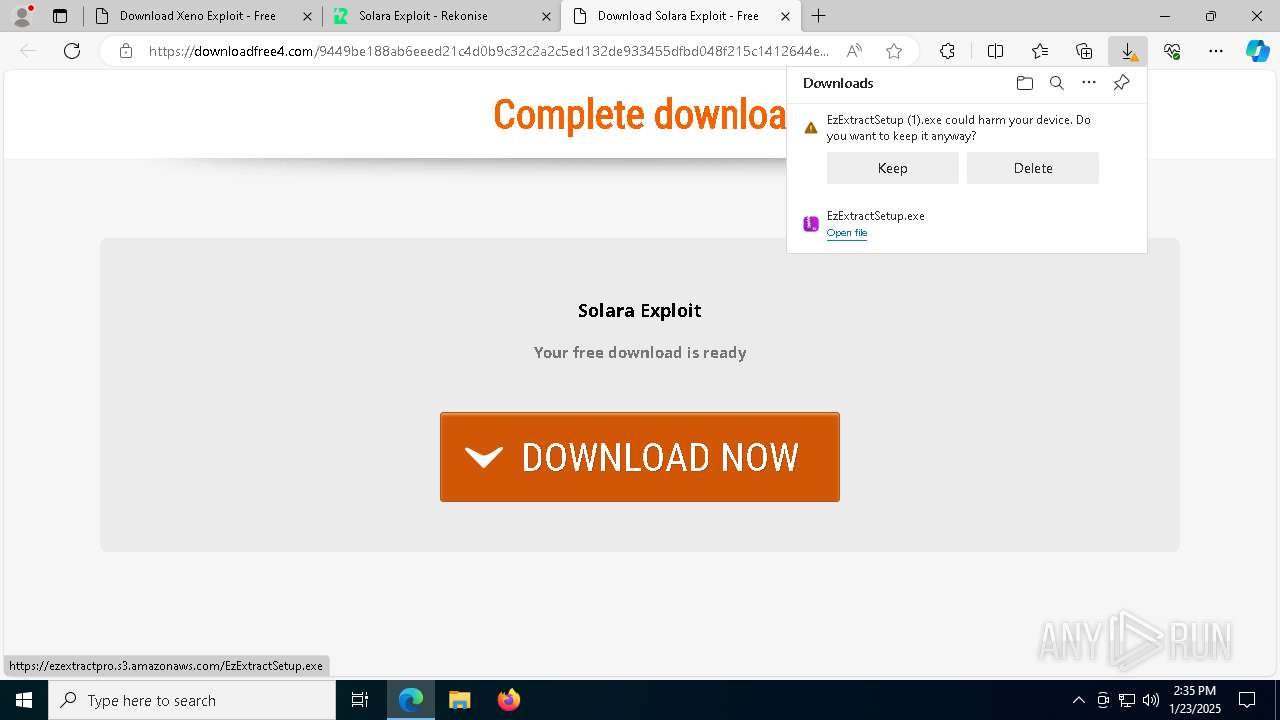
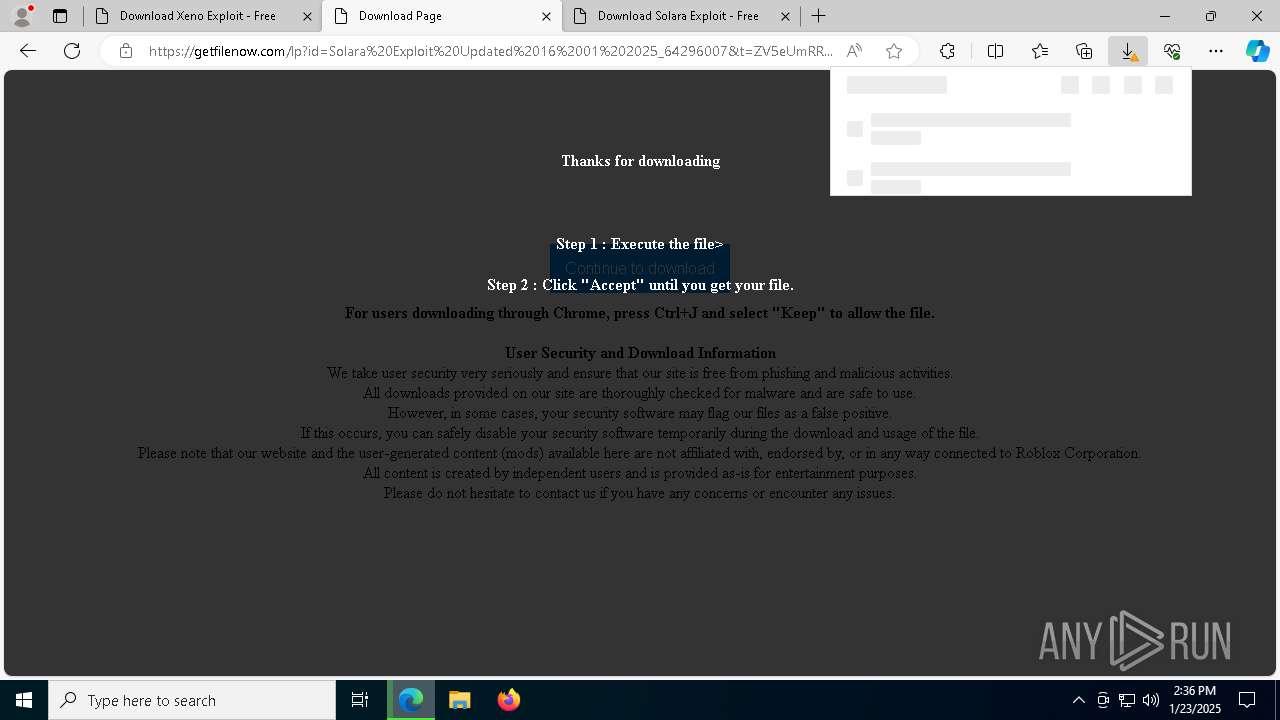
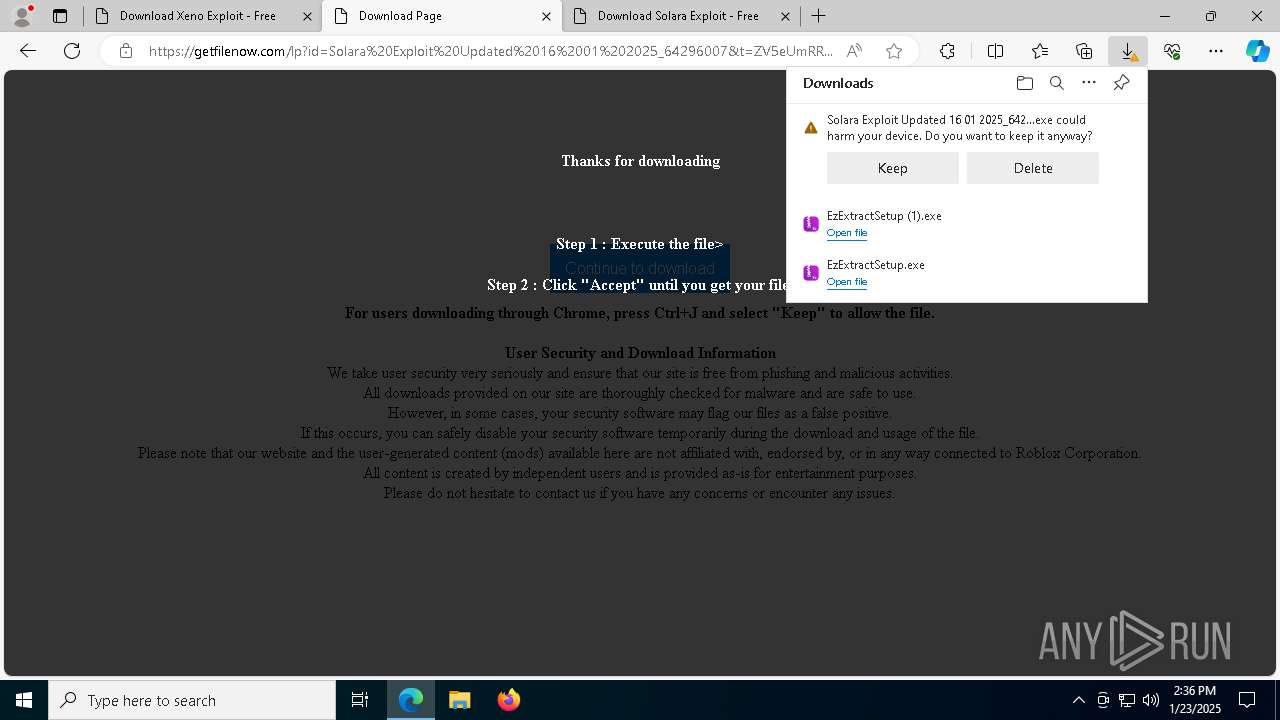
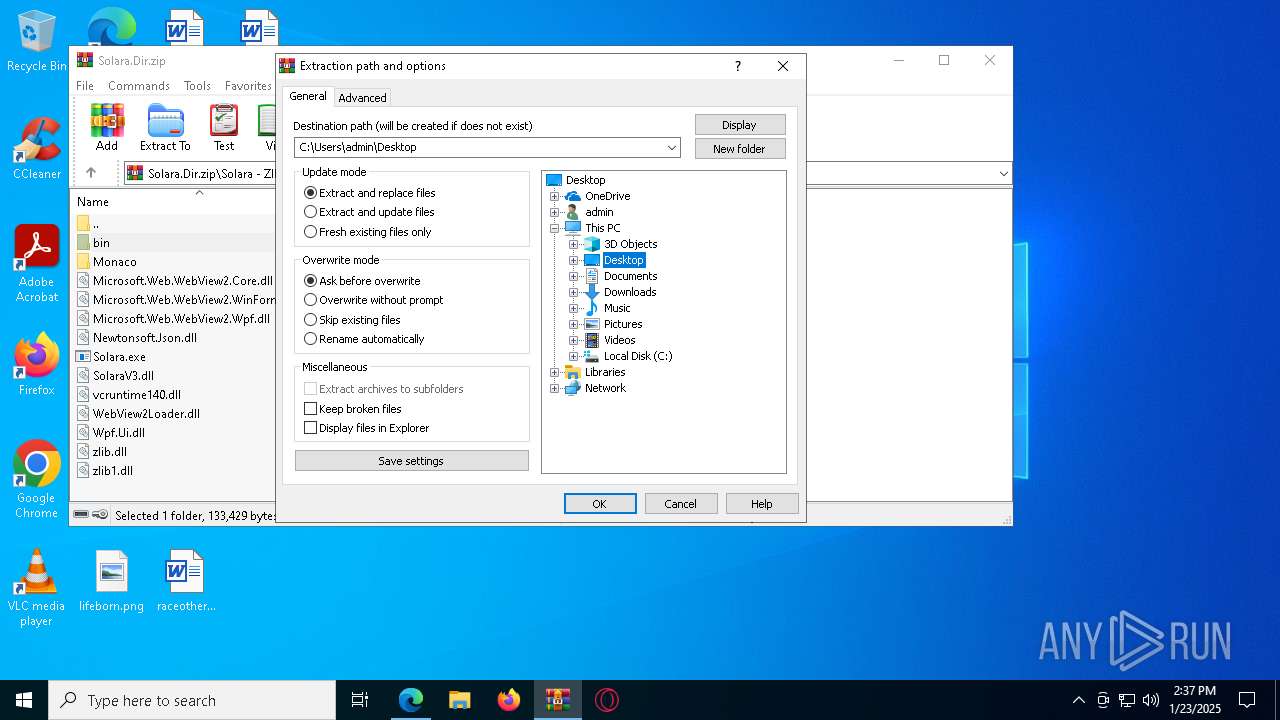
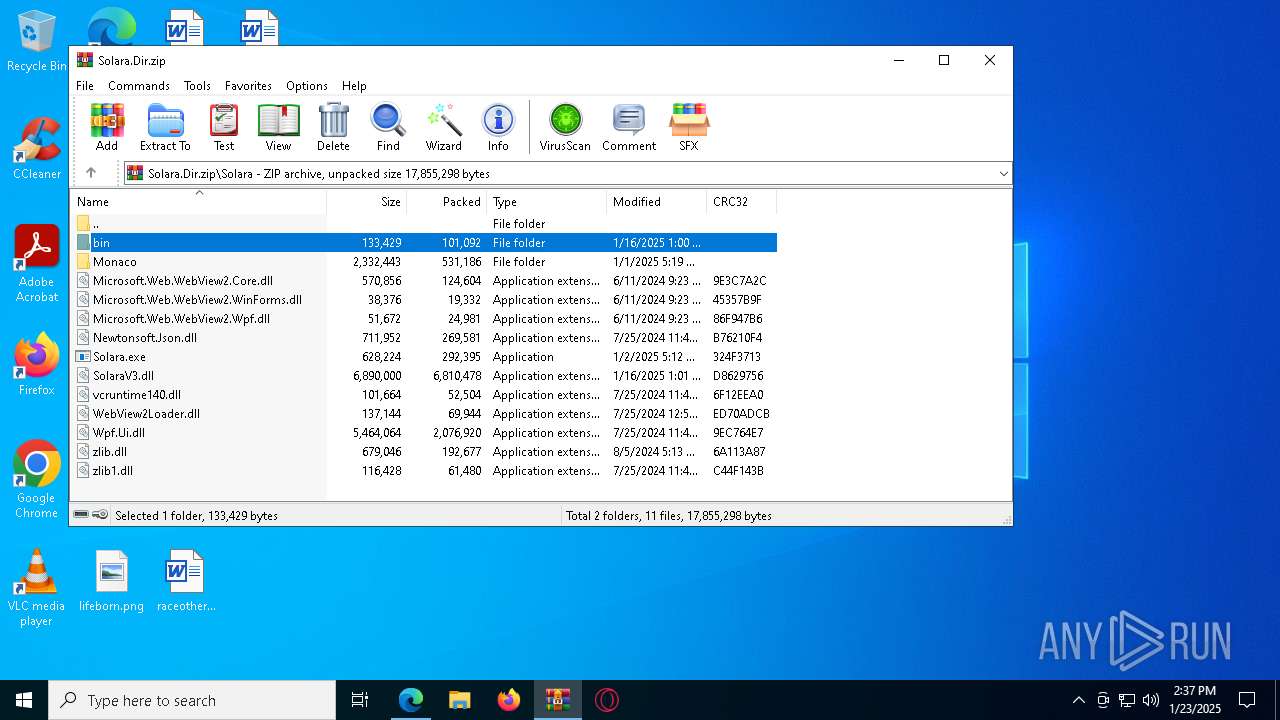
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2025, 14:34:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F23C68ABD0E4A3F6D745B782F6906DB7 |
| SHA1: | 95B8D2B3DDC005A42F643DC0B72963591808F7B9 |
| SHA256: | 2A081CB6913DD02443FDB5EAE22E9ACBC5CBD71FE887997023DC83D9D7EB09C4 |
| SSDEEP: | 3:N8DSLRqKKVKN3dDmMEGYEQ:2OLBN3dTS |
MALICIOUS
The DLL Hijacking
- regsvr32.exe (PID: 6268)
Registers / Runs the DLL via REGSVR32.EXE
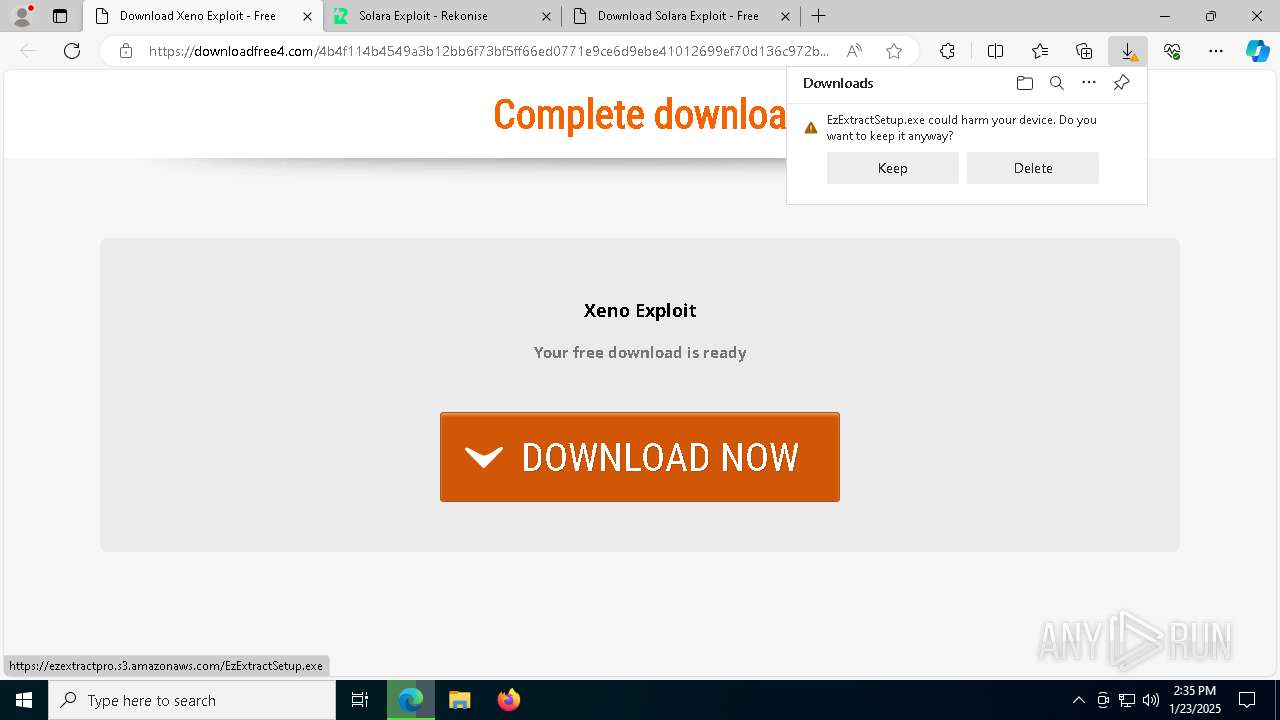
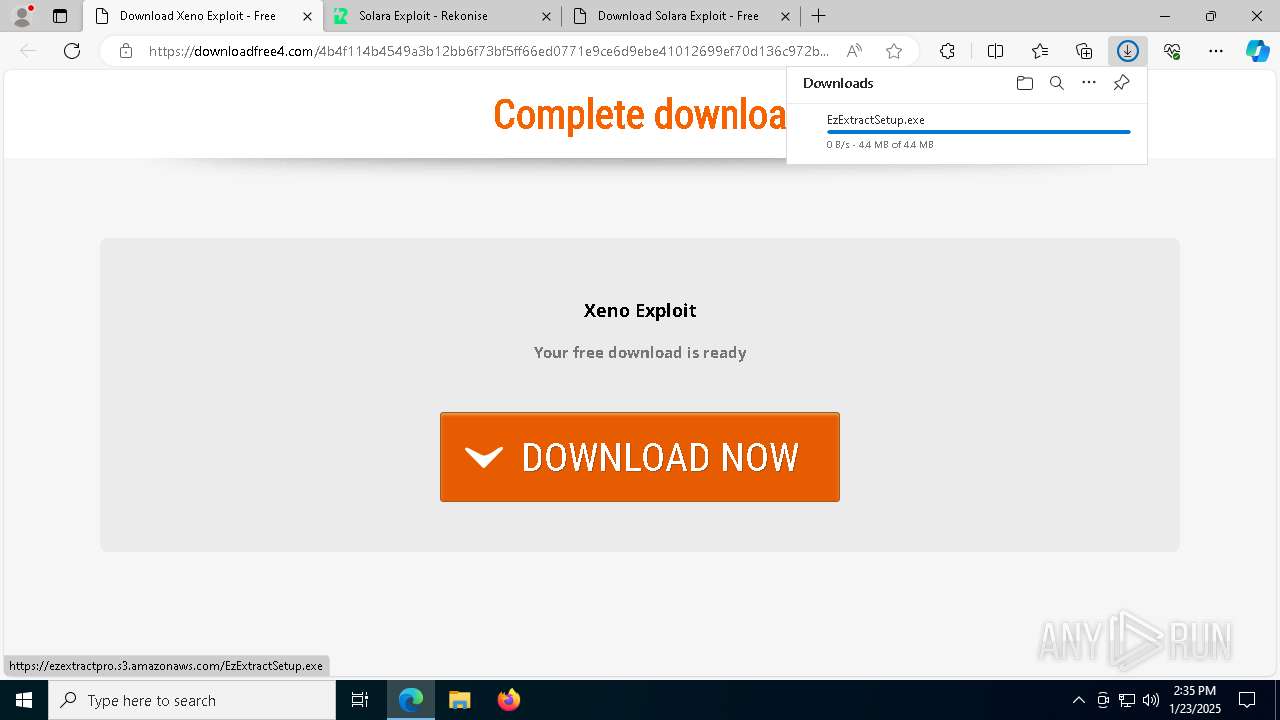
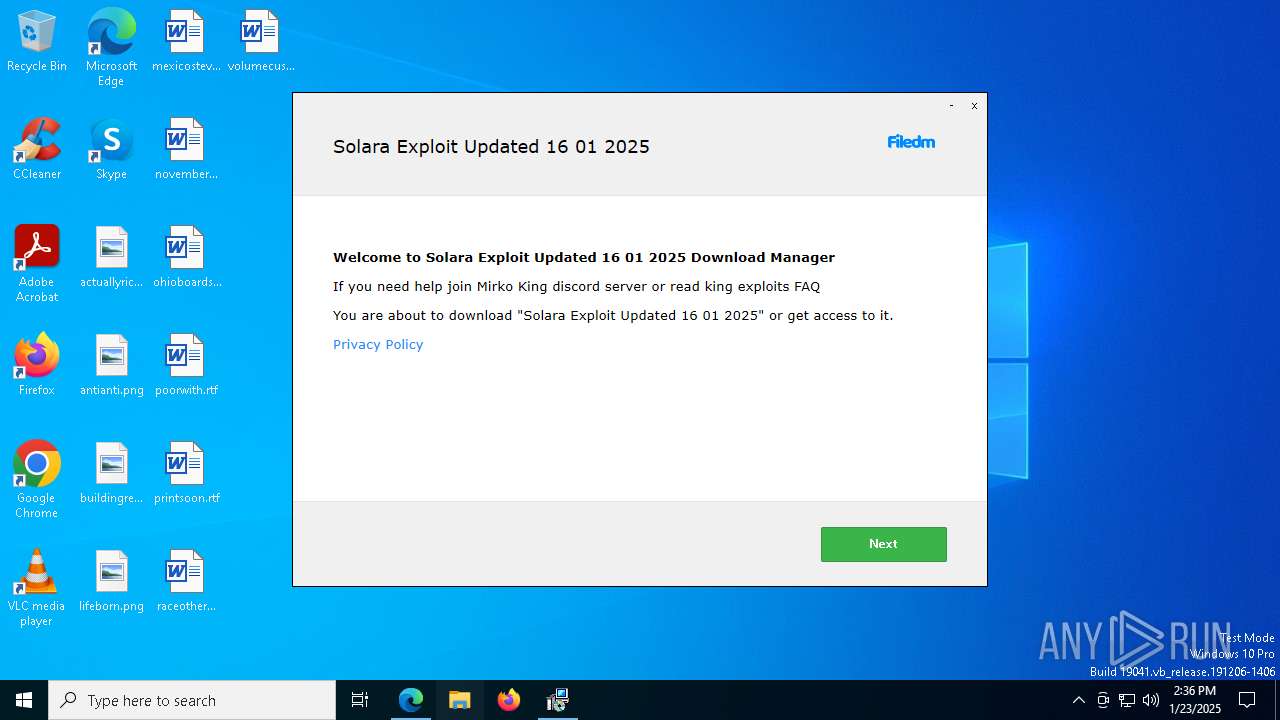
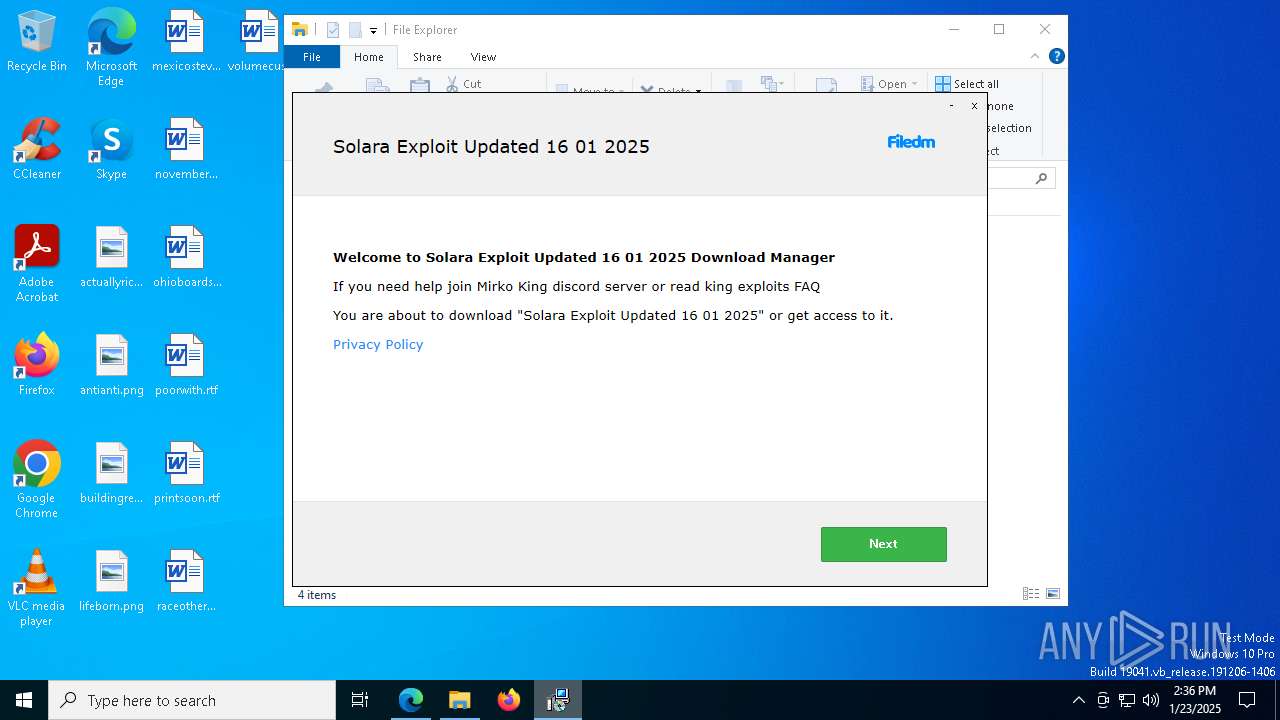
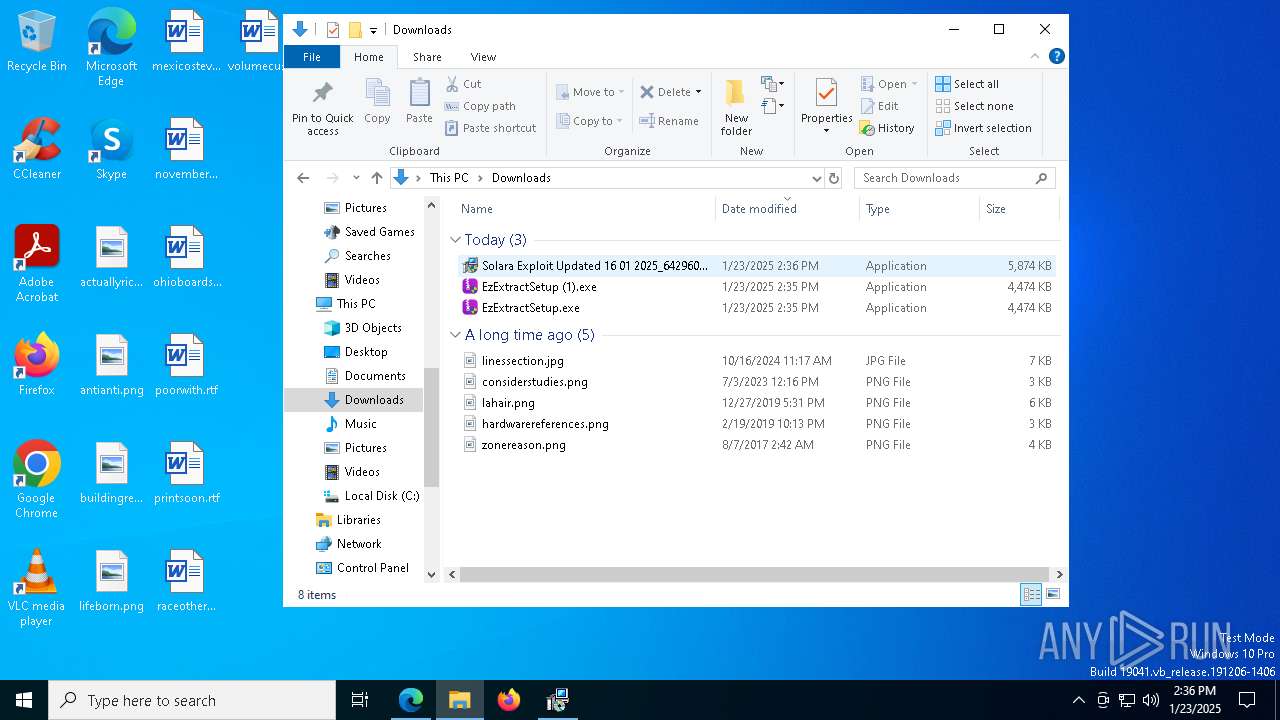
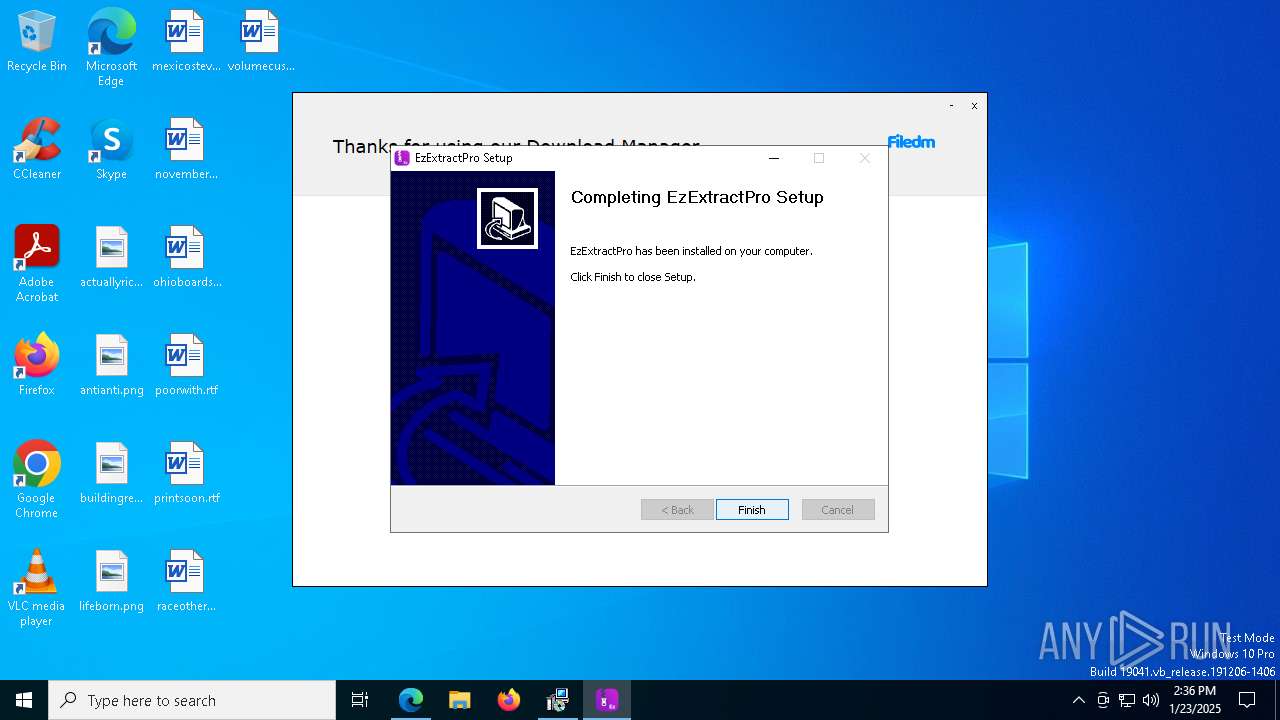
- EzExtractSetup.exe (PID: 4024)
Changes the autorun value in the registry
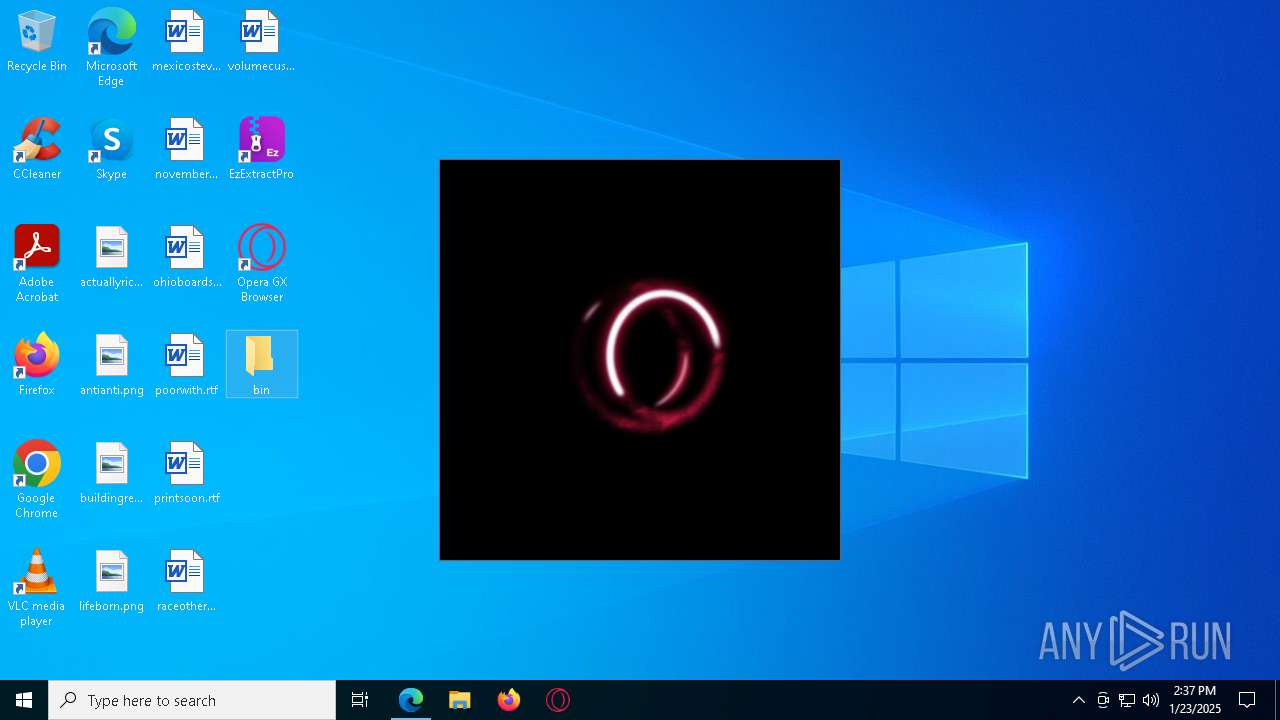
- opera.exe (PID: 6580)
SUSPICIOUS
Reads security settings of Internet Explorer
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- installer.exe (PID: 6248)
- EzExtractProApp.exe (PID: 2512)
Executable content was dropped or overwritten
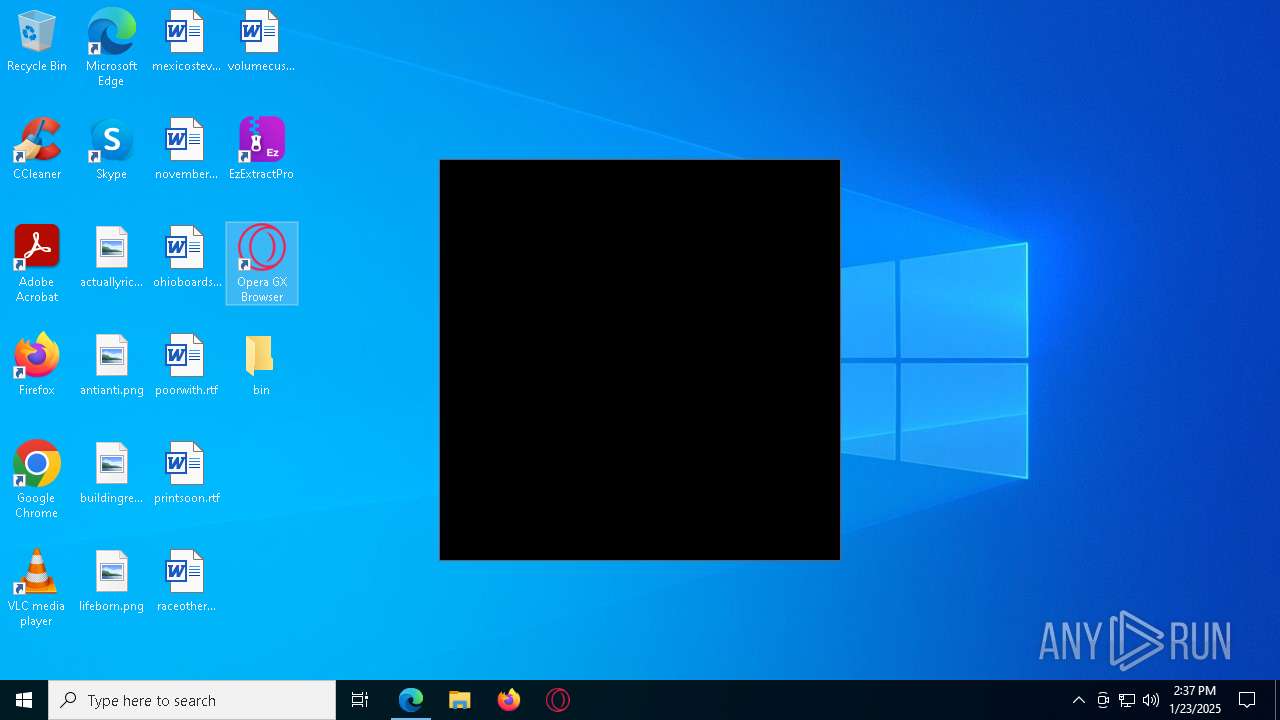
- OperaGX.exe (PID: 7816)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- setup.exe (PID: 7700)
- setup.exe (PID: 6620)
- setup.exe (PID: 8172)
- setup.exe (PID: 4984)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 7308)
- EzExtractSetup.exe (PID: 768)
- Opera_GX_assistant_73.0.3856.382_Setup.exe_sfx.exe (PID: 7448)
- installer.exe (PID: 188)
- installer.exe (PID: 6248)
There is functionality for taking screenshot (YARA)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- setup.exe (PID: 7700)
- setup.exe (PID: 8172)
Application launched itself
- setup.exe (PID: 6520)
- setup.exe (PID: 8172)
- assistant_installer.exe (PID: 3896)
- installer.exe (PID: 6248)
- opera.exe (PID: 6580)
- opera_autoupdate.exe (PID: 8656)
- installer.exe (PID: 7384)
- opera_autoupdate.exe (PID: 8504)
Starts itself from another location
- setup.exe (PID: 6520)
Checks Windows Trust Settings
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
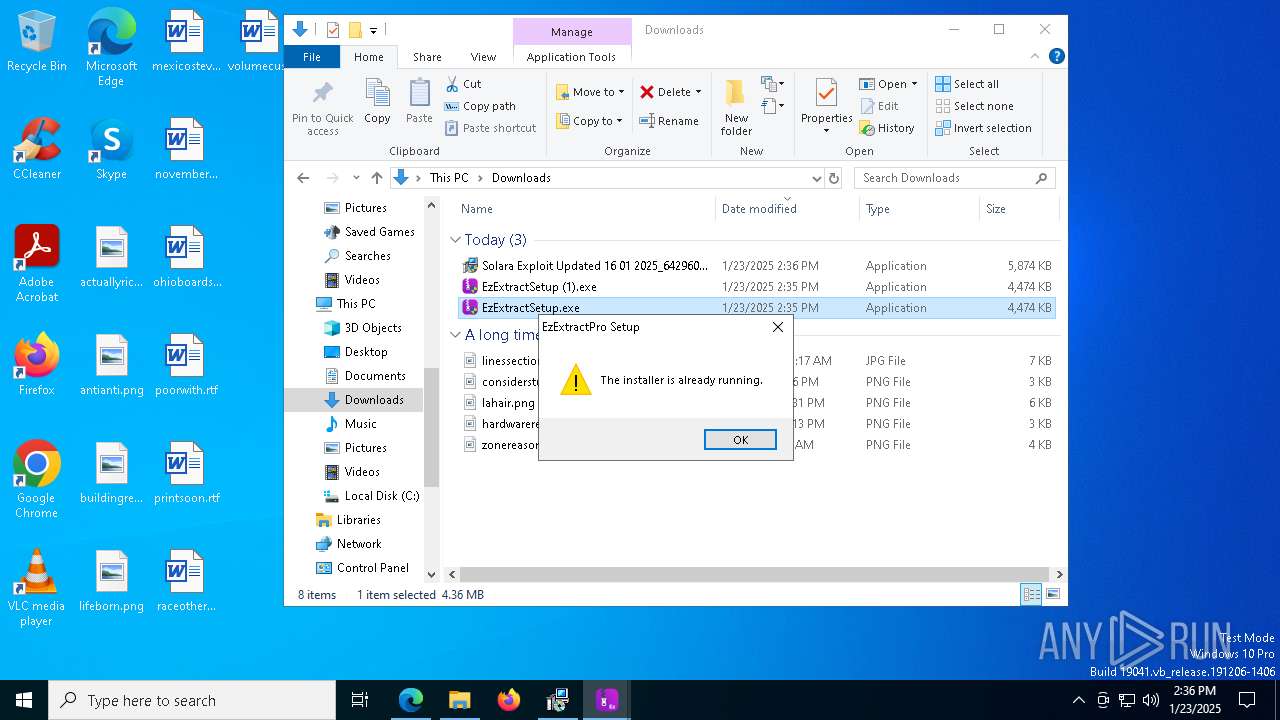
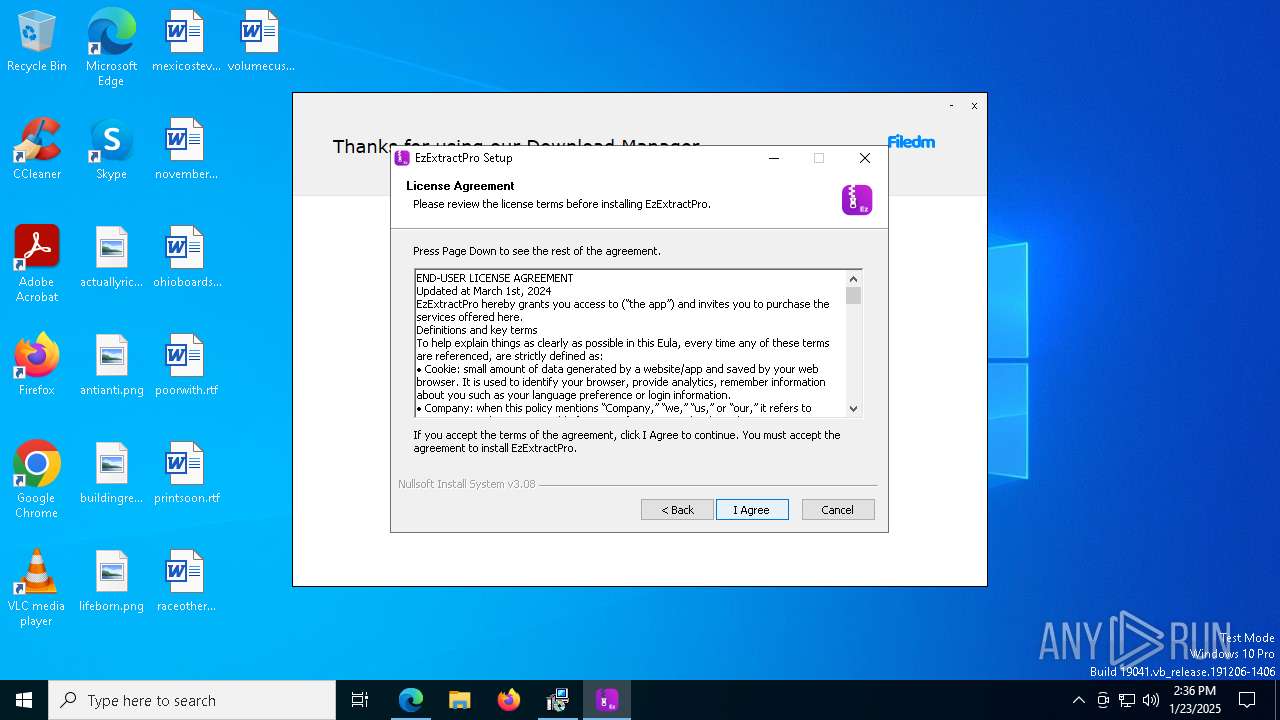
Malware-specific behavior (creating "System.dll" in Temp)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 7308)
- EzExtractSetup.exe (PID: 768)
The process creates files with name similar to system file names
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6268)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 8092)
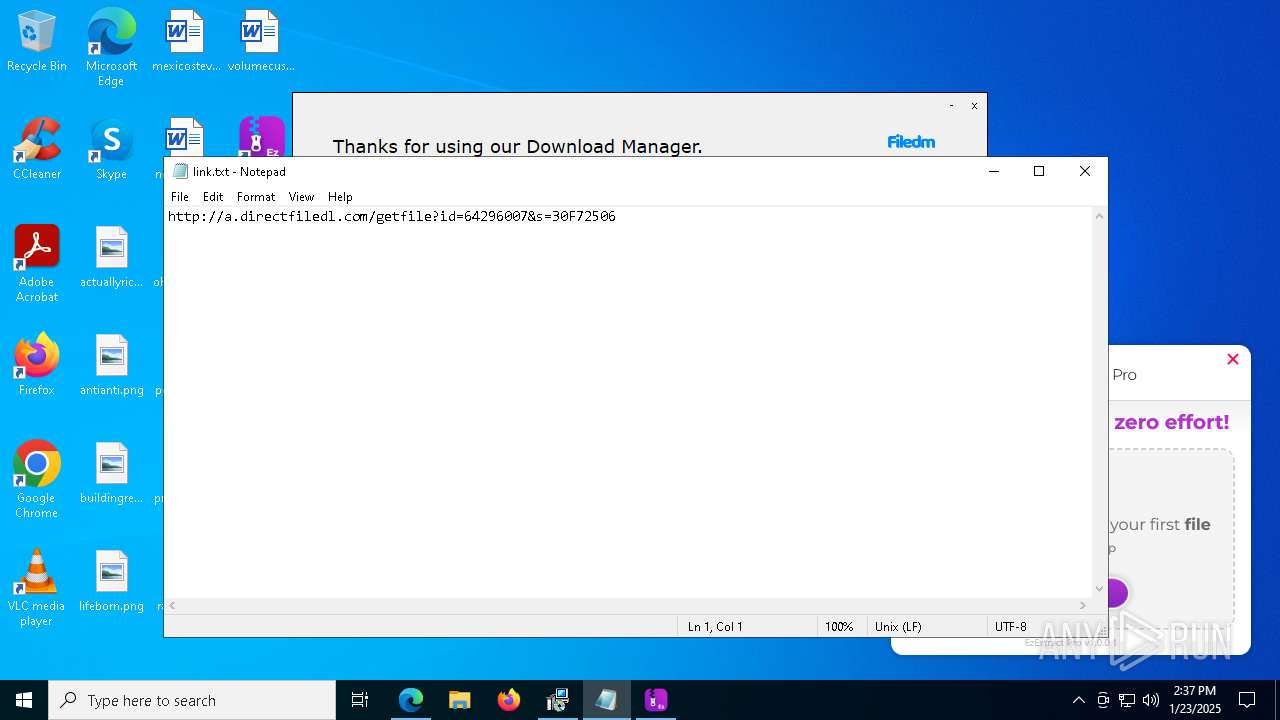
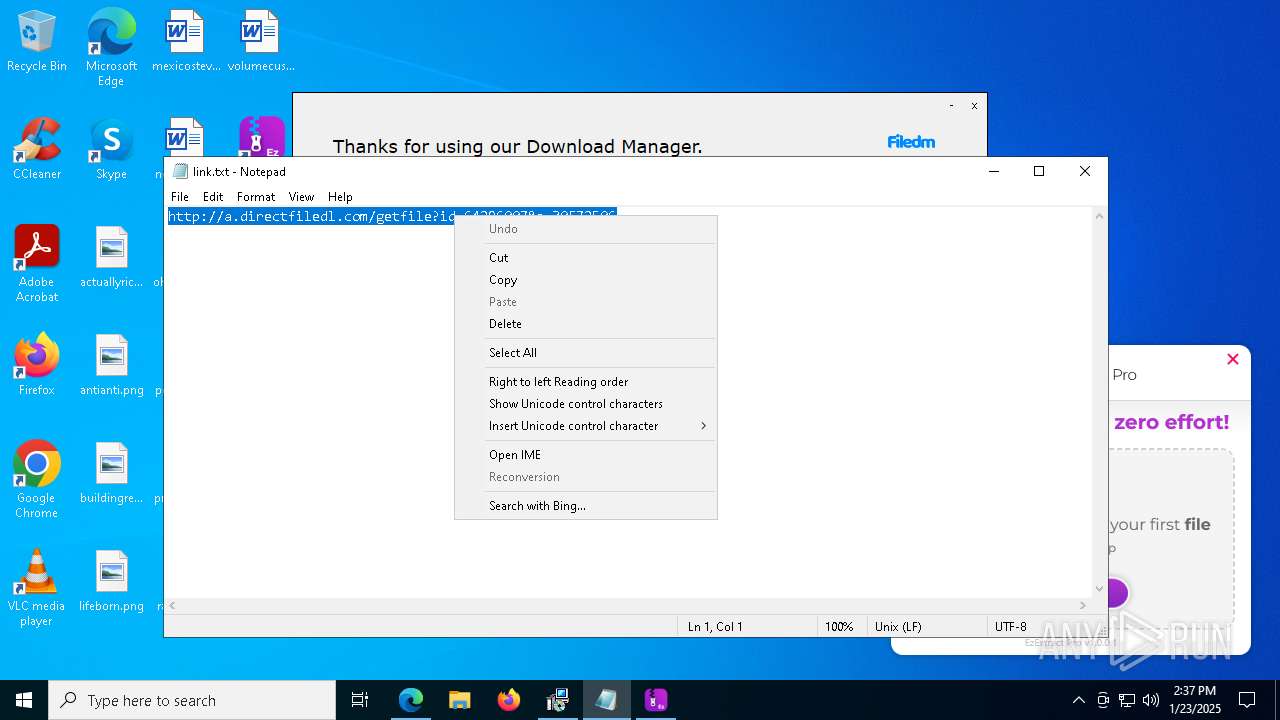
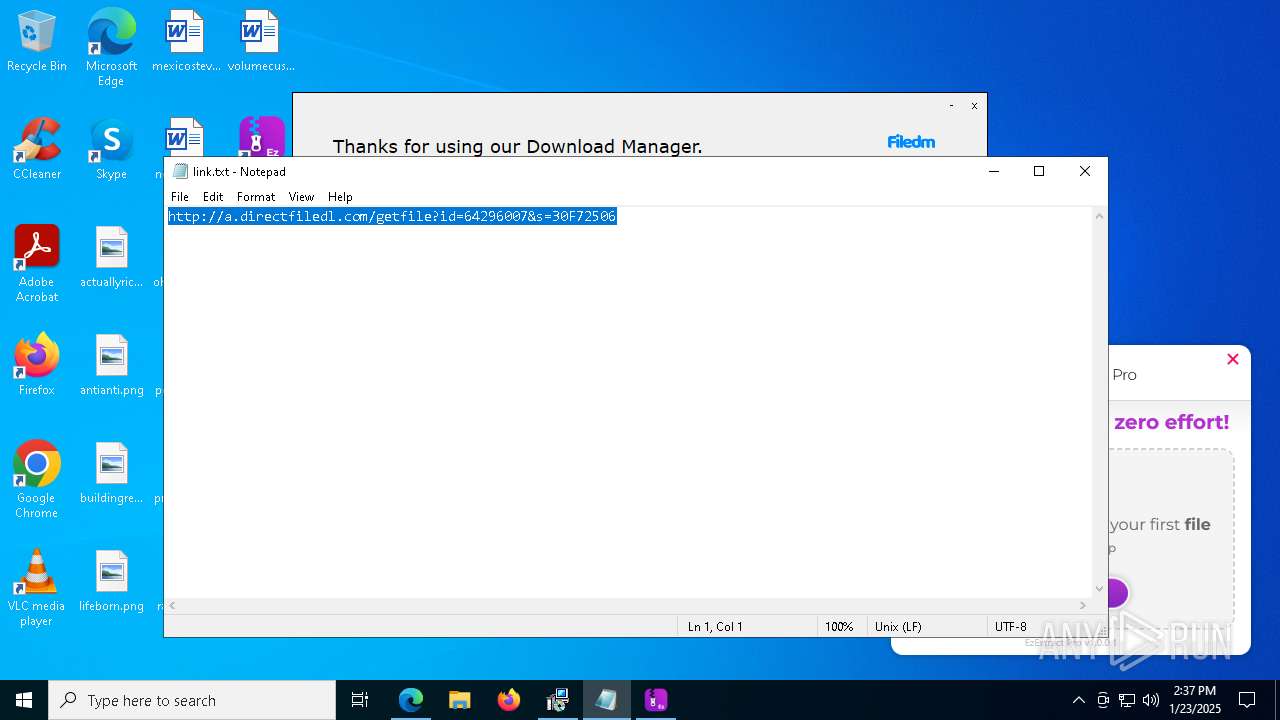
Start notepad (likely ransomware note)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
The process drops C-runtime libraries
- msedge.exe (PID: 6932)
- msedge.exe (PID: 6624)
Process drops legitimate windows executable
- msedge.exe (PID: 6932)
- msedge.exe (PID: 6624)
Reads the date of Windows installation
- opera.exe (PID: 6580)
The process executes via Task Scheduler
- opera_autoupdate.exe (PID: 8504)
INFO
Checks supported languages
- identity_helper.exe (PID: 7712)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- OperaGX.exe (PID: 7816)
- setup.exe (PID: 6520)
- setup.exe (PID: 6620)
- setup.exe (PID: 4984)
- setup.exe (PID: 8172)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- EzExtractProApp.exe (PID: 2512)
- Opera_GX_assistant_73.0.3856.382_Setup.exe_sfx.exe (PID: 7448)
- installer.exe (PID: 6248)
- installer.exe (PID: 188)
- setup.exe (PID: 7700)
- opera.exe (PID: 7652)
- opera.exe (PID: 6580)
- opera.exe (PID: 7752)
- opera.exe (PID: 6148)
- opera.exe (PID: 7840)
- opera_gx_splash.exe (PID: 7720)
- opera.exe (PID: 6400)
- opera.exe (PID: 8112)
- opera.exe (PID: 7560)
- opera.exe (PID: 7496)
- opera.exe (PID: 5876)
- opera.exe (PID: 1544)
- opera.exe (PID: 6172)
- opera.exe (PID: 7308)
- opera.exe (PID: 6264)
- opera.exe (PID: 5544)
- opera.exe (PID: 4012)
- opera.exe (PID: 6248)
- opera.exe (PID: 2736)
- opera.exe (PID: 7524)
- opera.exe (PID: 7464)
- opera.exe (PID: 8716)
- opera.exe (PID: 524)
- opera.exe (PID: 7508)
- opera.exe (PID: 8700)
- opera.exe (PID: 8788)
- opera.exe (PID: 1224)
- opera.exe (PID: 6096)
- opera.exe (PID: 8772)
- opera.exe (PID: 8740)
- opera.exe (PID: 8296)
- opera.exe (PID: 5488)
- opera.exe (PID: 8236)
- opera.exe (PID: 8160)
Reads the computer name
- identity_helper.exe (PID: 7712)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- setup.exe (PID: 8172)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- EzExtractProApp.exe (PID: 2512)
- opera.exe (PID: 7308)
- opera.exe (PID: 1224)
Connects to unusual port
- msedge.exe (PID: 6932)
Executable content was dropped or overwritten
- msedge.exe (PID: 6932)
- msedge.exe (PID: 6624)
- msedge.exe (PID: 5308)
Reads Environment values
- identity_helper.exe (PID: 7712)
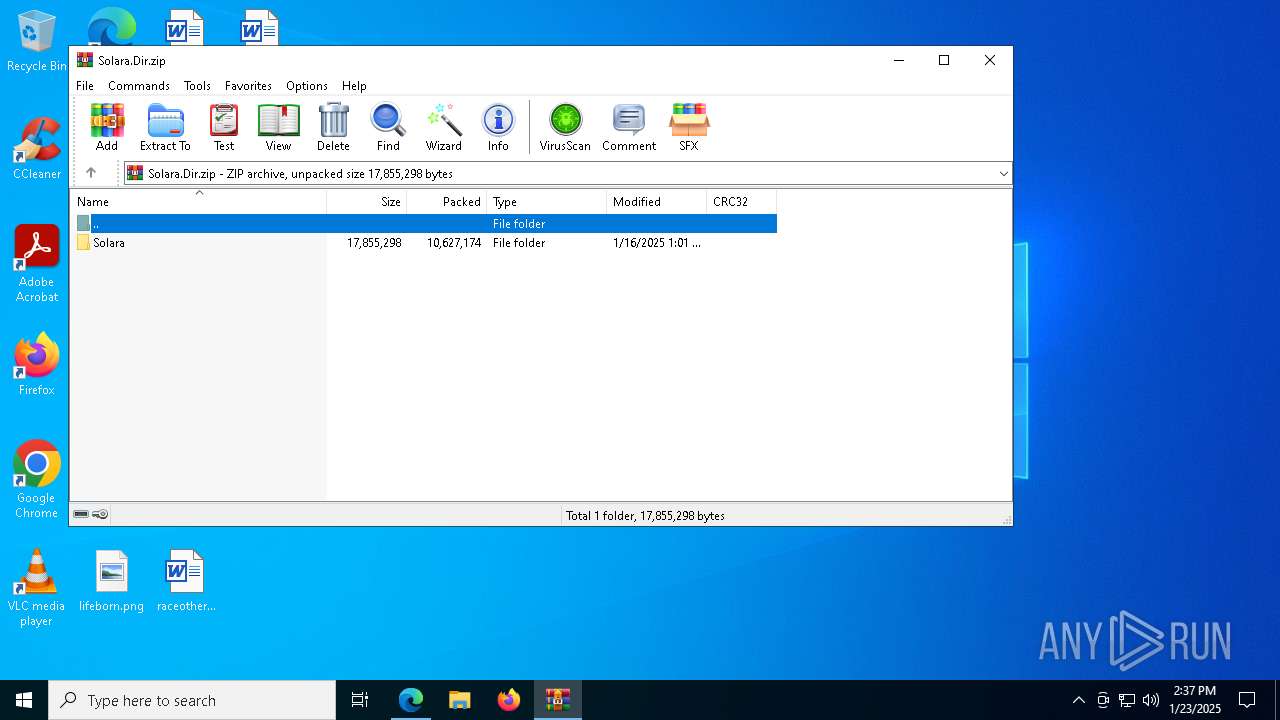
The process uses the downloaded file
- msedge.exe (PID: 5988)
- msedge.exe (PID: 8092)
- msedge.exe (PID: 5572)
- msedge.exe (PID: 6624)
- explorer.exe (PID: 2120)
- msedge.exe (PID: 7312)
- WinRAR.exe (PID: 7484)
The sample compiled with english language support
- msedge.exe (PID: 6932)
- msedge.exe (PID: 6624)
- OperaGX.exe (PID: 7816)
- setup.exe (PID: 6520)
- setup.exe (PID: 7700)
- setup.exe (PID: 6620)
- setup.exe (PID: 8172)
- setup.exe (PID: 4984)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- msedge.exe (PID: 5308)
- Opera_GX_assistant_73.0.3856.382_Setup.exe_sfx.exe (PID: 7448)
- installer.exe (PID: 6248)
- installer.exe (PID: 188)
Checks proxy server information
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- opera.exe (PID: 6580)
Creates files or folders in the user directory
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractProApp.exe (PID: 2512)
- setup.exe (PID: 8172)
- installer.exe (PID: 6248)
- opera.exe (PID: 6580)
- opera.exe (PID: 6400)
Reads the machine GUID from the registry
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7308)
- EzExtractProApp.exe (PID: 2512)
Reads the software policy settings
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
- setup.exe (PID: 6520)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 768)
Application launched itself
- msedge.exe (PID: 6624)
Create files in a temporary directory
- OperaGX.exe (PID: 7816)
- setup.exe (PID: 6520)
- setup.exe (PID: 7700)
- setup.exe (PID: 6620)
- setup.exe (PID: 4984)
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 7308)
- EzExtractSetup.exe (PID: 768)
- Opera_GX_assistant_73.0.3856.382_Setup.exe_sfx.exe (PID: 7448)
- installer.exe (PID: 6248)
- opera.exe (PID: 6580)
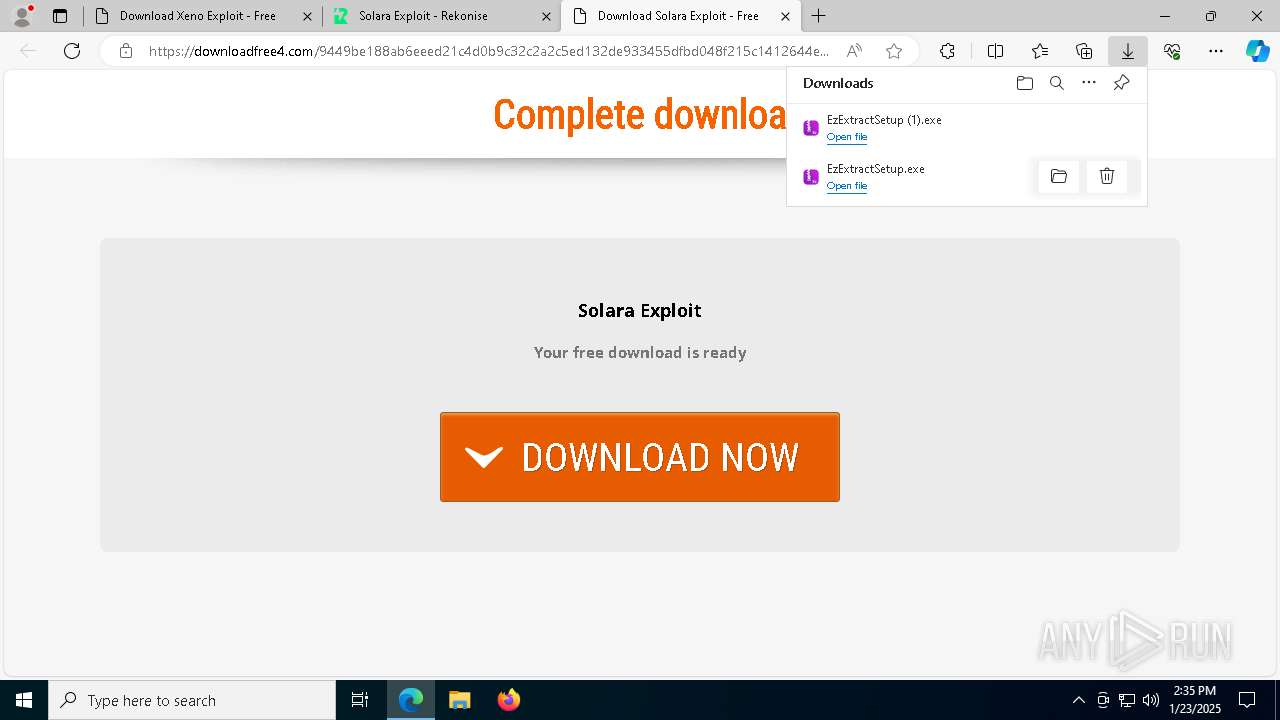
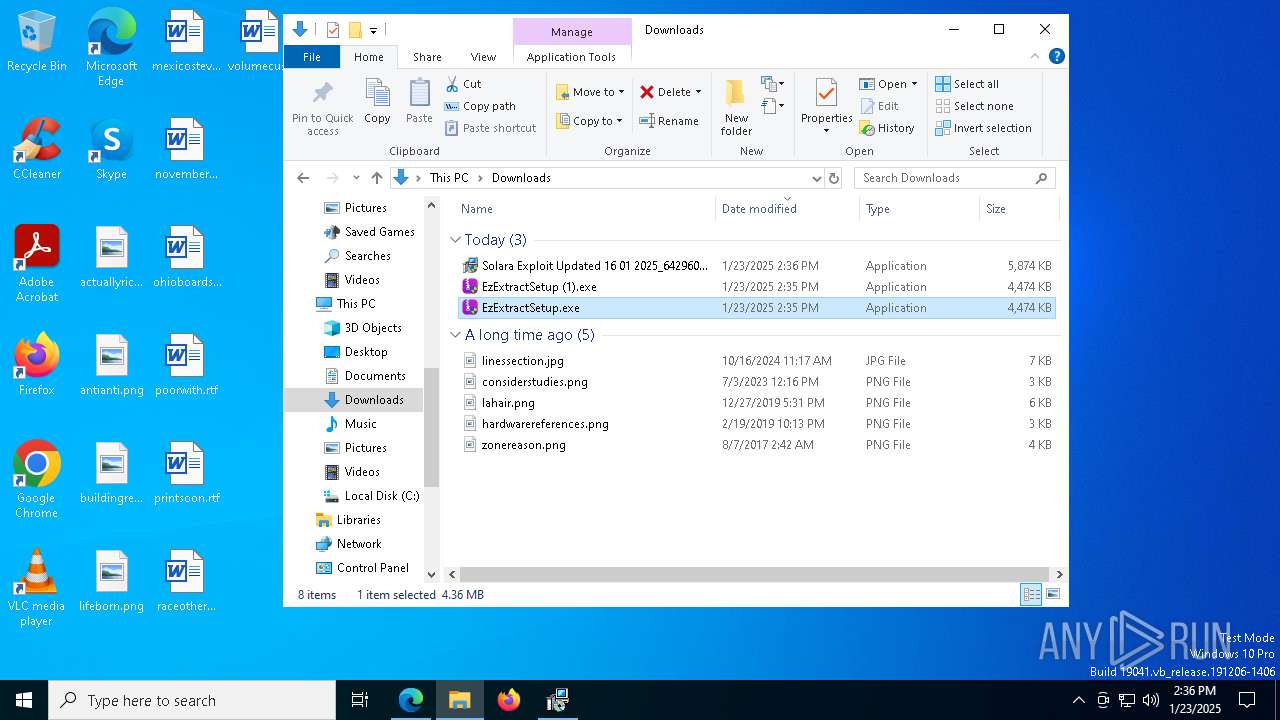
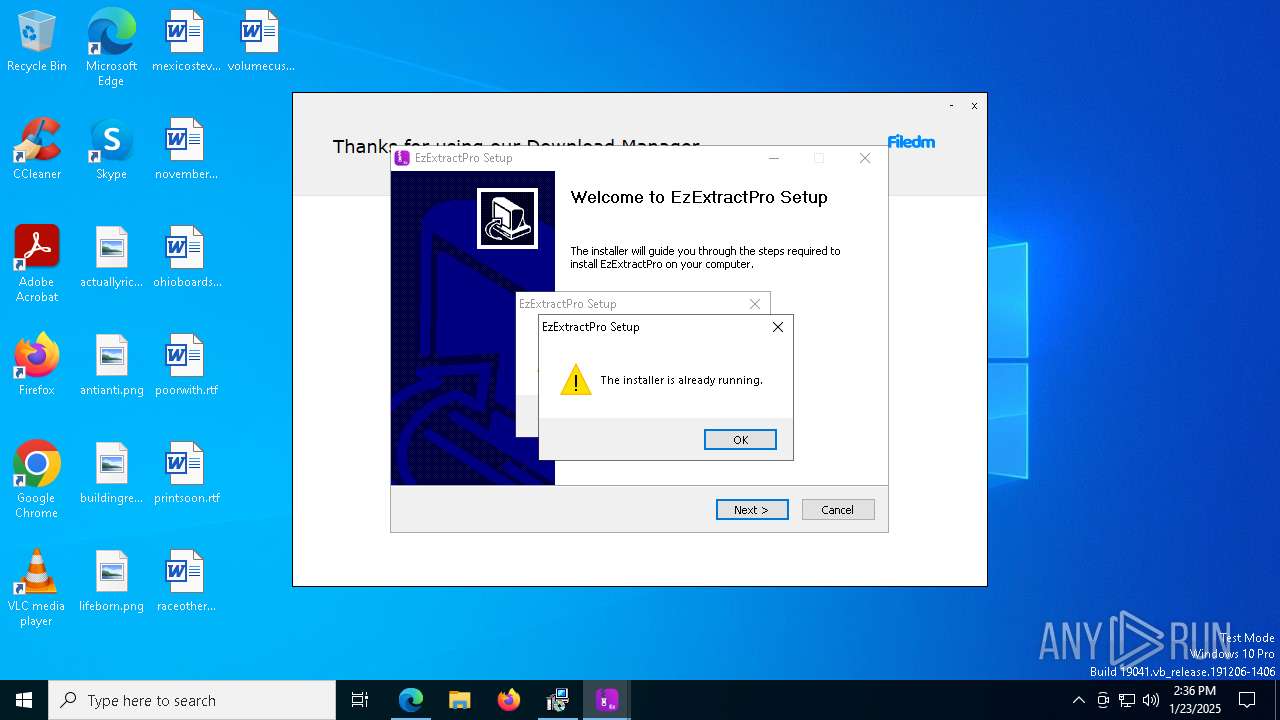
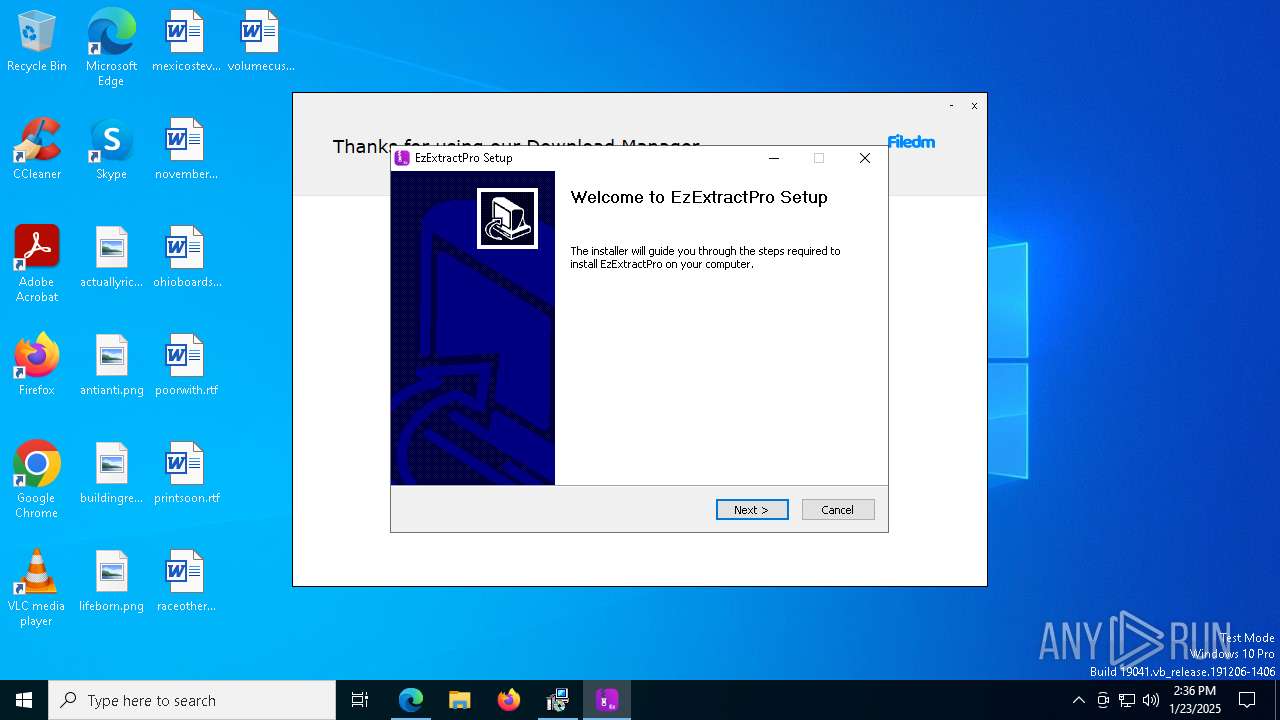
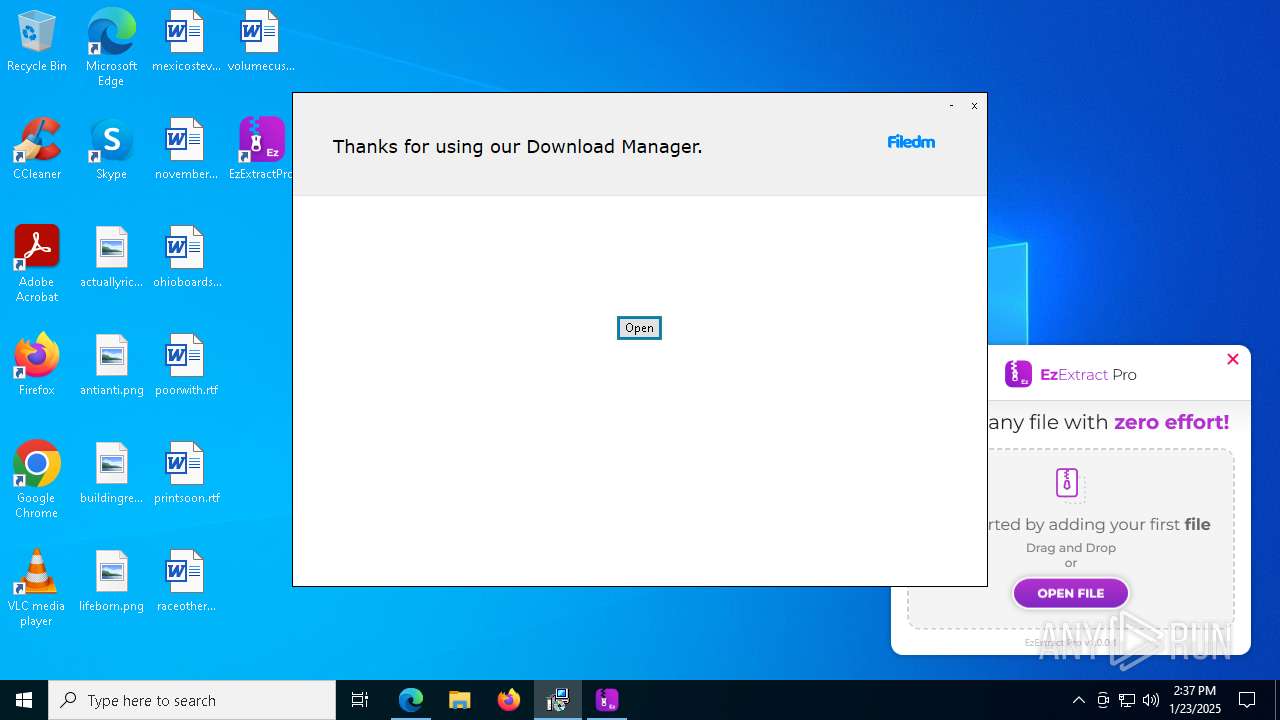
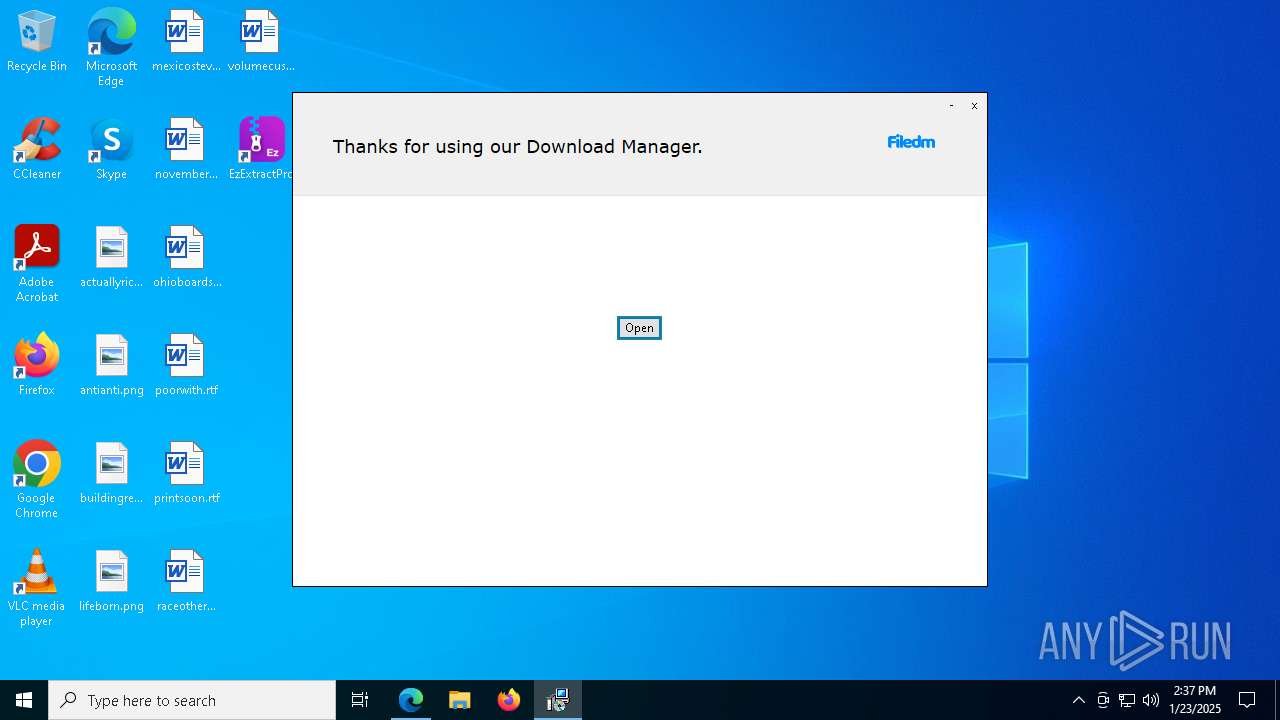
Manual execution by a user
- EzExtractSetup.exe (PID: 4024)
- EzExtractSetup.exe (PID: 436)
- EzExtractSetup.exe (PID: 1416)
- EzExtractSetup.exe (PID: 768)
- EzExtractSetup.exe (PID: 7236)
- EzExtractSetup.exe (PID: 7308)
- opera.exe (PID: 6580)
- WinRAR.exe (PID: 9140)
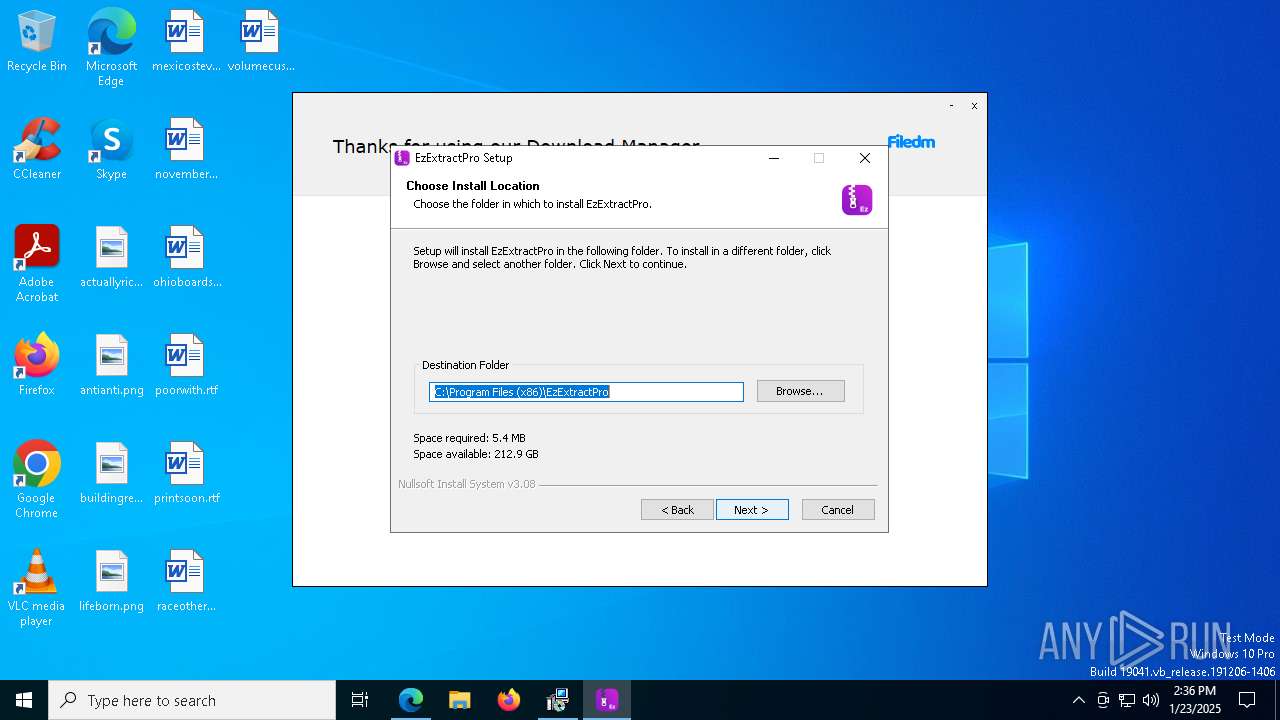
Creates files in the program directory
- EzExtractSetup.exe (PID: 4024)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7740)
Process checks computer location settings
- opera.exe (PID: 6580)
- opera.exe (PID: 5544)
- opera.exe (PID: 4012)
- opera.exe (PID: 6096)
- opera.exe (PID: 6264)
- opera.exe (PID: 1544)
- Solara Exploit Updated 16 01 2025_64296007.exe (PID: 7744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
318
Monitored processes
177
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=60 --mojo-platform-channel-handle=8060 --field-trial-handle=2304,i,17430060517075647597,8742647657862927308,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 188 | "C:\Users\admin\AppData\Local\Programs\Opera GX\116.0.5366.54\installer.exe" --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Roaming\Opera Software\Opera GX Stable\Crash Reports" "--crash-count-file=C:\Users\admin\AppData\Roaming\Opera Software\Opera GX Stable\crash_count.txt" --url=https://crashstats-collector-2.opera.com/ --annotation=channel=Stable --annotation=plat=Win64 --annotation=prod=OperaDesktopGX --annotation=ver=116.0.5366.54 --initial-client-data=0x288,0x28c,0x290,0x26c,0x294,0x7ff81f7e10d8,0x7ff81f7e10e4,0x7ff81f7e10f0 | C:\Users\admin\AppData\Local\Programs\Opera GX\116.0.5366.54\installer.exe | installer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera GX Installer Exit code: 0 Version: 116.0.5366.54 Modules
| |||||||||||||||
| 436 | "C:\Users\admin\Downloads\EzExtractSetup.exe" | C:\Users\admin\Downloads\EzExtractSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: MEDIUM Description: EzExtractPro Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=78 --mojo-platform-channel-handle=3888 --field-trial-handle=2304,i,17430060517075647597,8742647657862927308,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 524 | "C:\Users\admin\AppData\Local\Programs\Opera GX\opera.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --enable-quic --with-feature:cashback-assistant=on --with-feature:address-bar-dropdown-autocompleted-domains=on --with-feature:address-bar-dropdown-unfiltered-full=off --with-feature:amazon-new-ids=on --with-feature:cashback-assistant=on --with-feature:continue-on-booking=on --with-feature:continue-on-shopping-via-amp=off --with-feature:continue-shopping=on --with-feature:continue-shopping-2=on --with-feature:continue-shopping-5=on --with-feature:continue-shopping-cms-configuration=on --with-feature:continue-shopping-explore=off --with-feature:continue-shopping-structured-partners=on --with-feature:feature-remote-disable-updates-testing-flag=off --with-feature:feature-remote-updates-testing-flag=on --with-feature:game-servers=off --with-feature:gx-post-mortem=on --with-feature:gx-reactinator=on --with-feature:gx-spotlight=on --with-feature:gx-video-to-phone=on --with-feature:hide-navigations-from-extensions=on --with-feature:lucid-mode-hide-text=on --with-feature:panic-button=on --with-feature:password-generator=off --with-feature:play-again=on --with-feature:realtime-impressions-reporting=on --with-feature:run-at-startup-default=on --with-feature:sd-suggestions-external=on --with-feature:session-restore-attribution=on --with-feature:side-profiles=on --with-feature:sitecheck-age=on --with-feature:tiktok-panel=on --with-feature:ui-compositor-multithreaded=on --with-feature:installer-experiment-test=off --field-trial-handle=8176,i,2508708960377280382,6566974425985090559,262144 --disable-features=CertificateTransparencyAskBeforeEnabling,PlatformSoftwareH264EncoderInGpu --variations-seed-version --mojo-platform-channel-handle=8708 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\Opera GX\opera.exe | — | opera.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: LOW Description: Opera GX Internet Browser Exit code: 0 Version: 116.0.5366.54 | |||||||||||||||
| 768 | "C:\Users\admin\Downloads\EzExtractSetup.exe" | C:\Users\admin\Downloads\EzExtractSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: HIGH Description: EzExtractPro Exit code: 2 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3700 --field-trial-handle=2304,i,17430060517075647597,8742647657862927308,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=79 --mojo-platform-channel-handle=7304 --field-trial-handle=2304,i,17430060517075647597,8742647657862927308,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\AppData\Local\Programs\Opera GX\opera.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --enable-quic --with-feature:cashback-assistant=on --with-feature:address-bar-dropdown-autocompleted-domains=on --with-feature:address-bar-dropdown-unfiltered-full=off --with-feature:amazon-new-ids=on --with-feature:cashback-assistant=on --with-feature:continue-on-booking=on --with-feature:continue-on-shopping-via-amp=off --with-feature:continue-shopping=on --with-feature:continue-shopping-2=on --with-feature:continue-shopping-5=on --with-feature:continue-shopping-cms-configuration=on --with-feature:continue-shopping-explore=off --with-feature:continue-shopping-structured-partners=on --with-feature:feature-remote-disable-updates-testing-flag=off --with-feature:feature-remote-updates-testing-flag=on --with-feature:game-servers=off --with-feature:gx-post-mortem=on --with-feature:gx-reactinator=on --with-feature:gx-spotlight=on --with-feature:gx-video-to-phone=on --with-feature:hide-navigations-from-extensions=on --with-feature:lucid-mode-hide-text=on --with-feature:panic-button=on --with-feature:password-generator=off --with-feature:play-again=on --with-feature:realtime-impressions-reporting=on --with-feature:run-at-startup-default=on --with-feature:sd-suggestions-external=on --with-feature:session-restore-attribution=on --with-feature:side-profiles=on --with-feature:sitecheck-age=on --with-feature:tiktok-panel=on --with-feature:ui-compositor-multithreaded=on --with-feature:installer-experiment-test=off --field-trial-handle=1768,i,2508708960377280382,6566974425985090559,262144 --disable-features=CertificateTransparencyAskBeforeEnabling,PlatformSoftwareH264EncoderInGpu --variations-seed-version --mojo-platform-channel-handle=6348 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\Opera GX\opera.exe | — | opera.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: LOW Description: Opera GX Internet Browser Exit code: 0 Version: 116.0.5366.54 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=54 --mojo-platform-channel-handle=5492 --field-trial-handle=2304,i,17430060517075647597,8742647657862927308,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
26 460
Read events
26 184
Write events
258
Delete events
18
Modification events
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9714AFC9F68A2F00 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590334 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {13EBC07B-C470-42A5-B480-B09A6C6E378B} | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0AE483CAF68A2F00 | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590334 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {50772213-F505-46DA-97FA-F3FD8B57553D} | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6624) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
66
Suspicious files
1 320
Text files
311
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135ff6.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135ff6.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135ff6.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136005.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136005.TMP | — | |
MD5:— | SHA256:— | |||
| 6624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
435
DNS requests
421
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1344 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1344 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4624 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1738134739&P2=404&P3=2&P4=c74QQVFxiNfZG5j4XQD2OgzWAn182CrkUFp43jcIdEiUfvpiMmc9omEcXK%2f2VWN59iEF0%2fWTmU2jXQKQVKXTWQ%3d%3d | unknown | — | — | whitelisted |
732 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
732 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6400 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1344 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1344 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.kingexploits.com |
| unknown |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6932 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
Solara Exploit Updated 16 01 2025_64296007.exe | Error: (undefined) has no property - value
|
Solara Exploit Updated 16 01 2025_64296007.exe | at initializeDynamicVariables (this://app/main.html(351))
|
Solara Exploit Updated 16 01 2025_64296007.exe | at getFileInfo.@307@46 (this://app/main.html(329))
|
Solara Exploit Updated 16 01 2025_64296007.exe | |
Solara Exploit Updated 16 01 2025_64296007.exe | |
Solara Exploit Updated 16 01 2025_64296007.exe | scanning node questions /questions
|
Solara Exploit Updated 16 01 2025_64296007.exe | scanning node question /questions/question
|
Solara Exploit Updated 16 01 2025_64296007.exe | scanning node question /questions/question
|
Solara Exploit Updated 16 01 2025_64296007.exe | scanning node question /questions/question
|
Solara Exploit Updated 16 01 2025_64296007.exe | scanning node question /questions/question
|