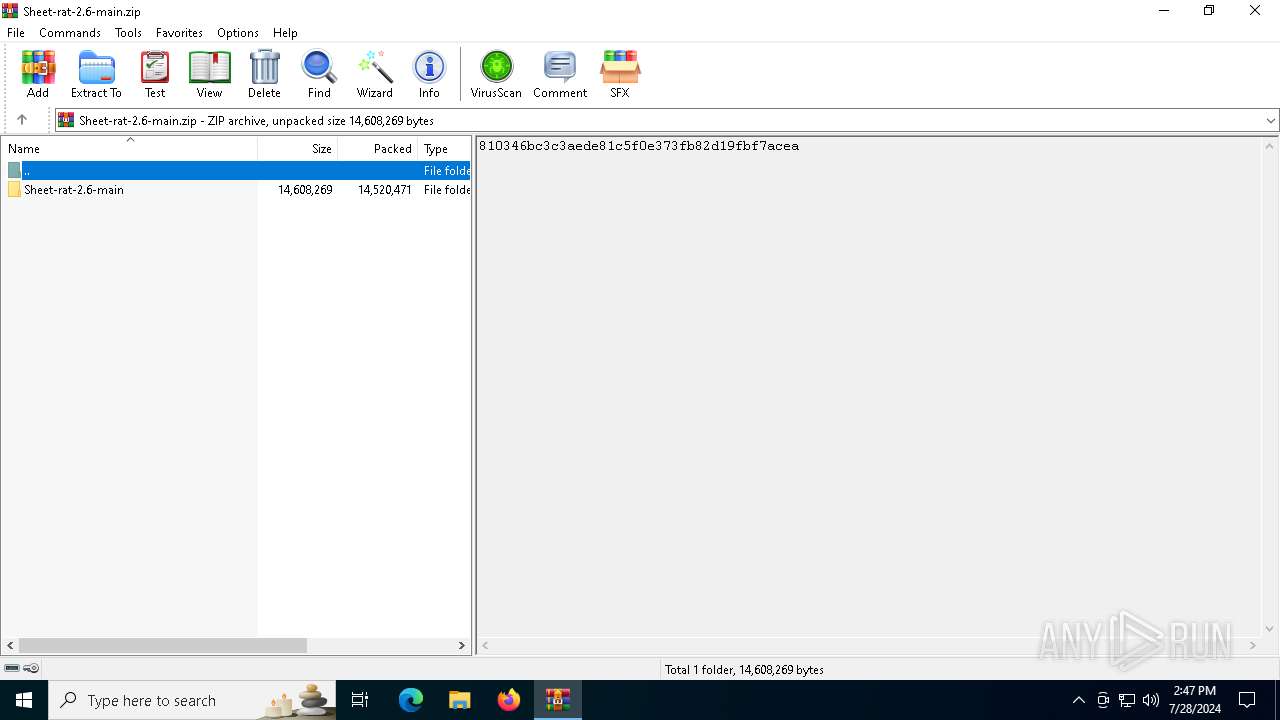
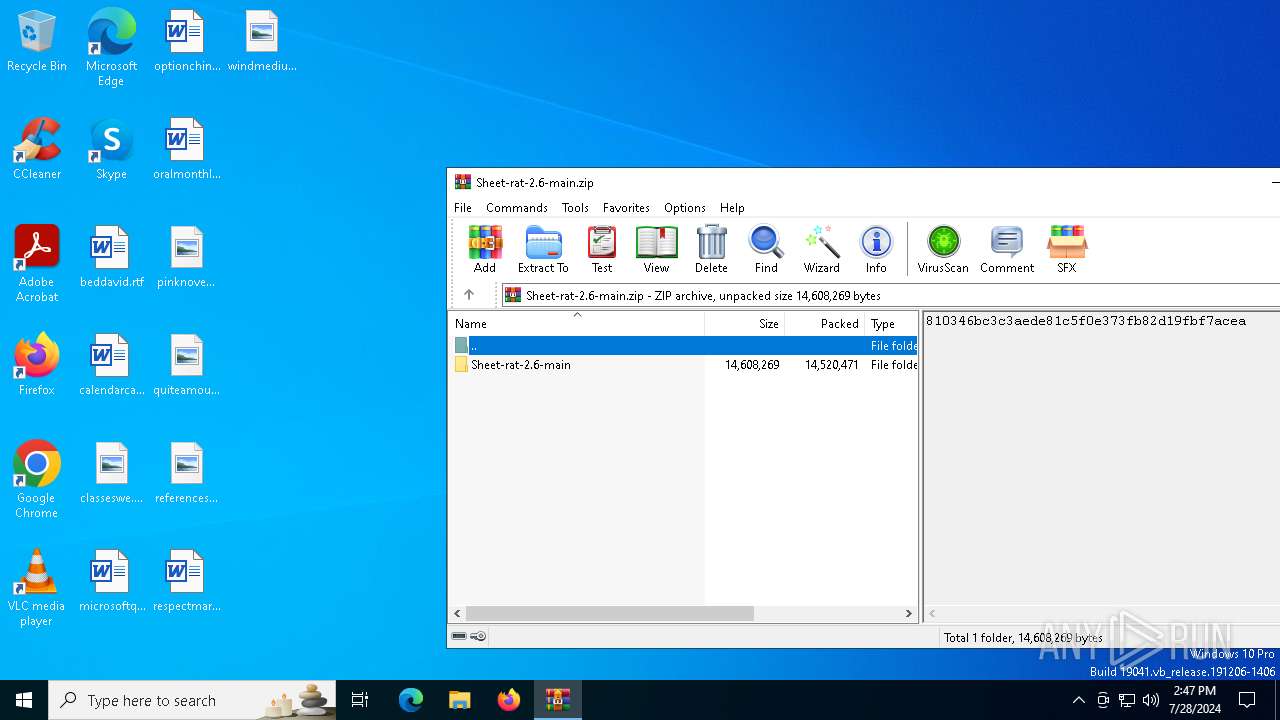
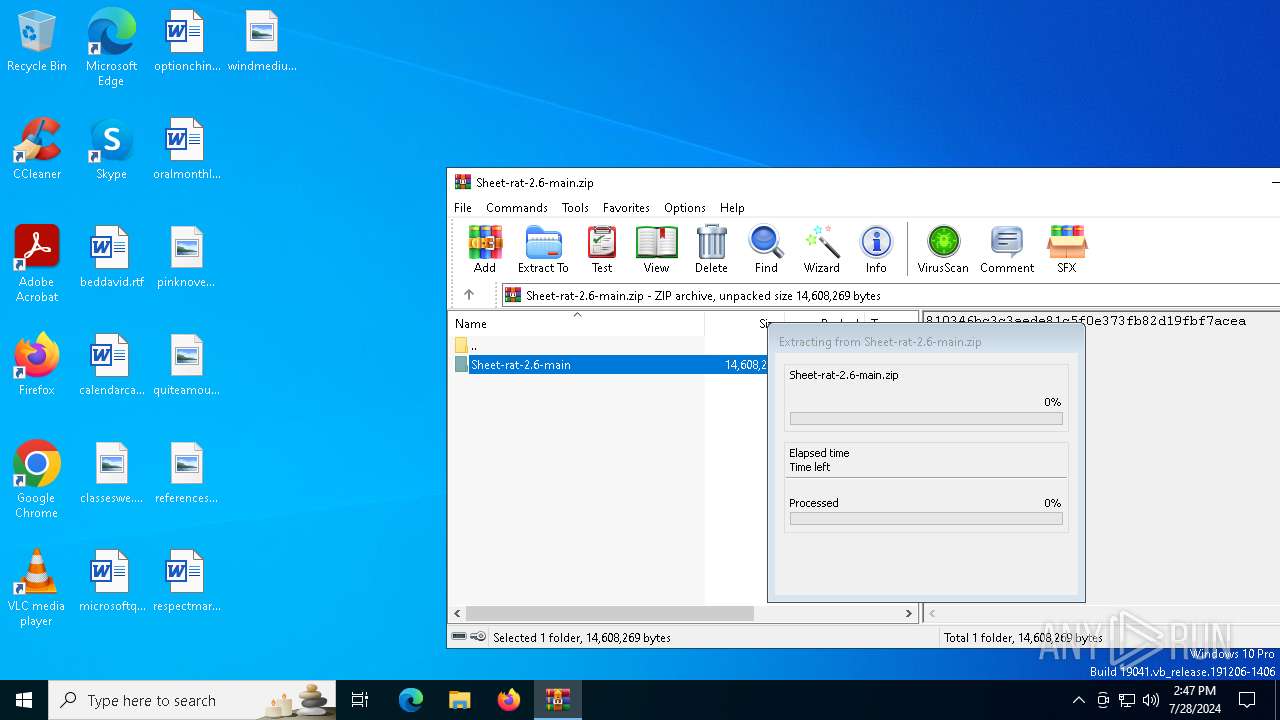
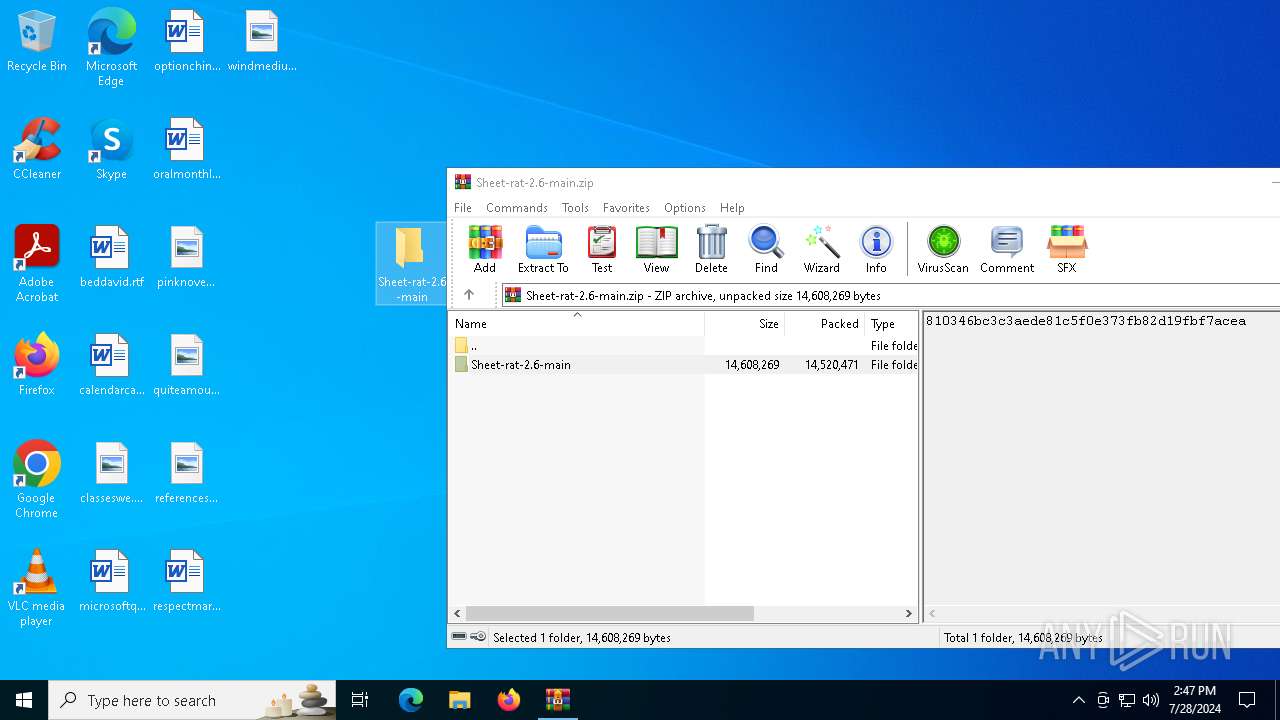
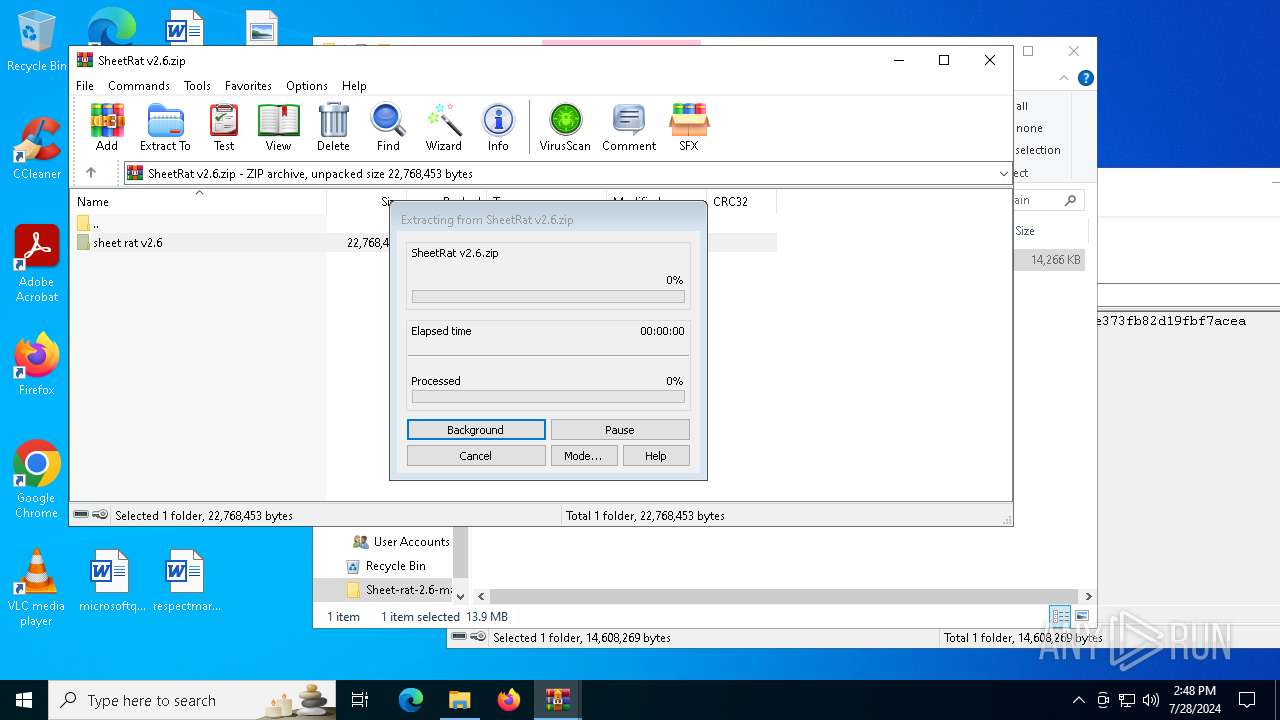
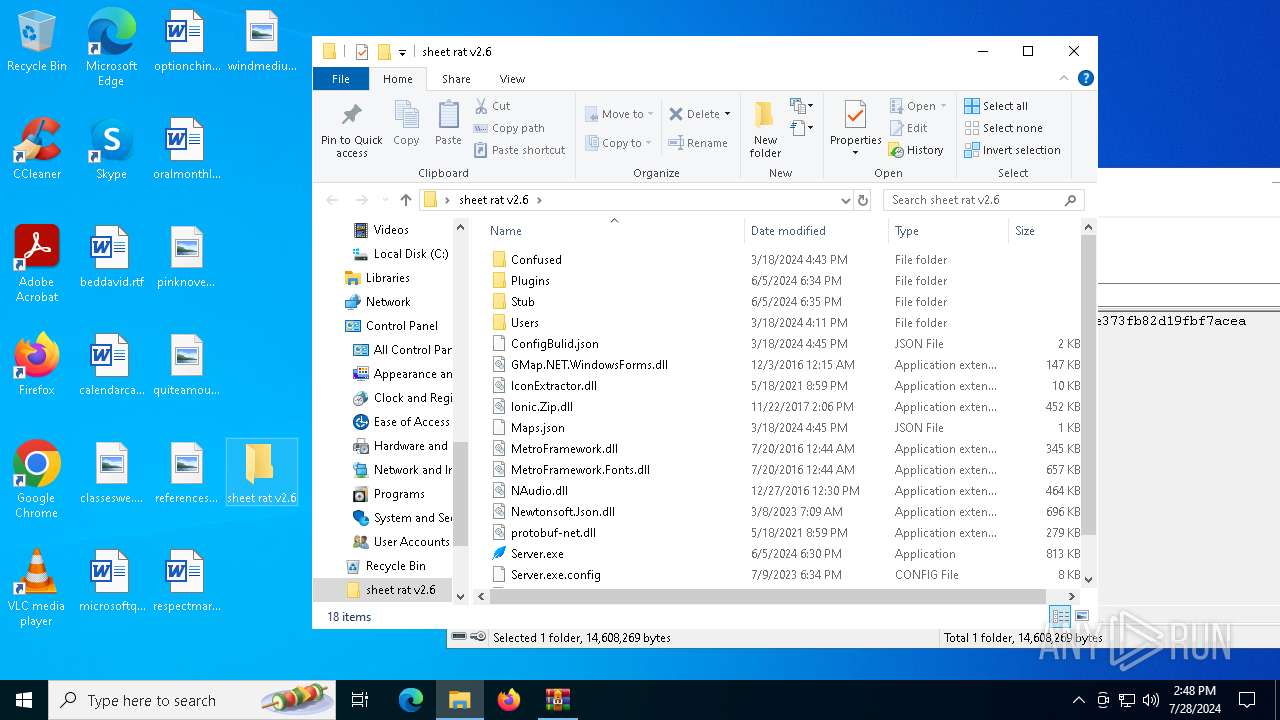
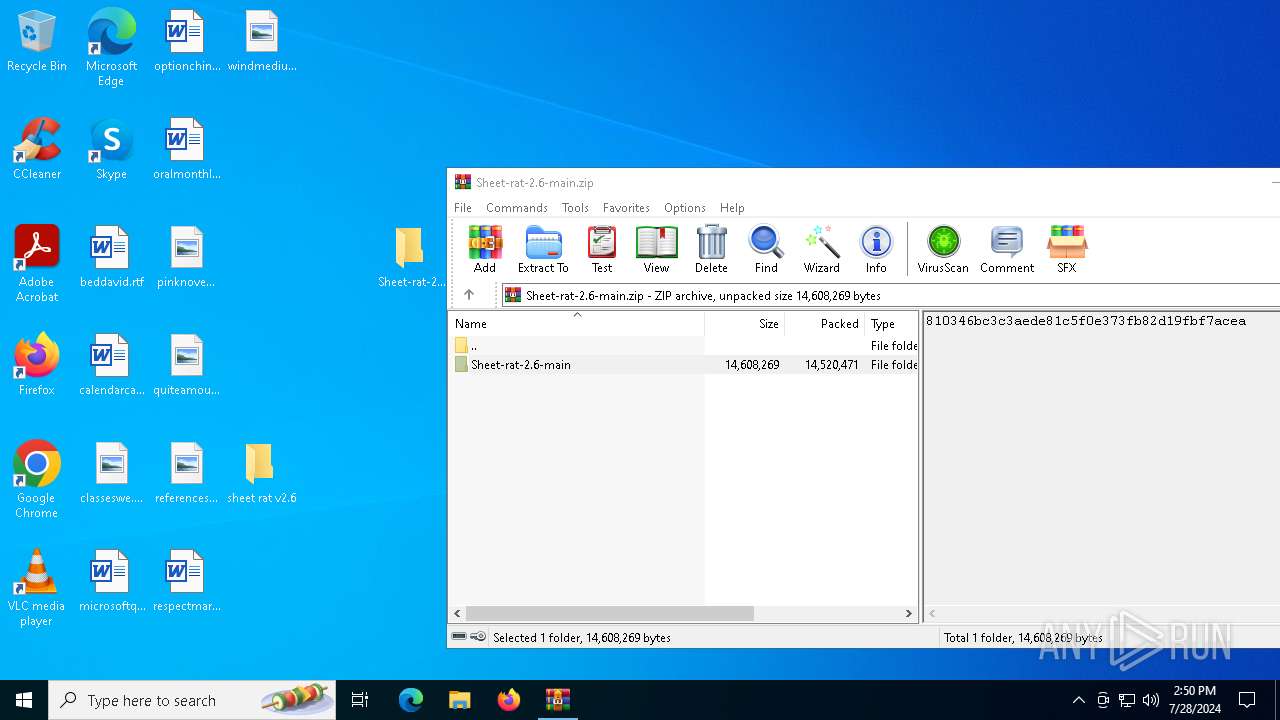
| File name: | Sheet-rat-2.6-main.zip |
| Full analysis: | https://app.any.run/tasks/863a52be-f395-41a5-bd99-f1af5094fc81 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2024, 14:47:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 7AADFCAF76AFFDCE9D8F02B4FB66D88A |
| SHA1: | 3CA15804C1FA0A44E37EAEBEAA4235C86A6F1FA8 |
| SHA256: | 29ED2CD26EE85330727502CA1E9E60E598F0D3975CE8C845DBCB1DA07E5EA902 |
| SSDEEP: | 98304:ToyG3GCtM/XG6NoTeFgdrRA2/6Psf7IS0i8flOFu3yBDdtABx2j+kXX5AOWDaRwb:wUN0HUCUG+PnN8DiI0bV+Traqa |
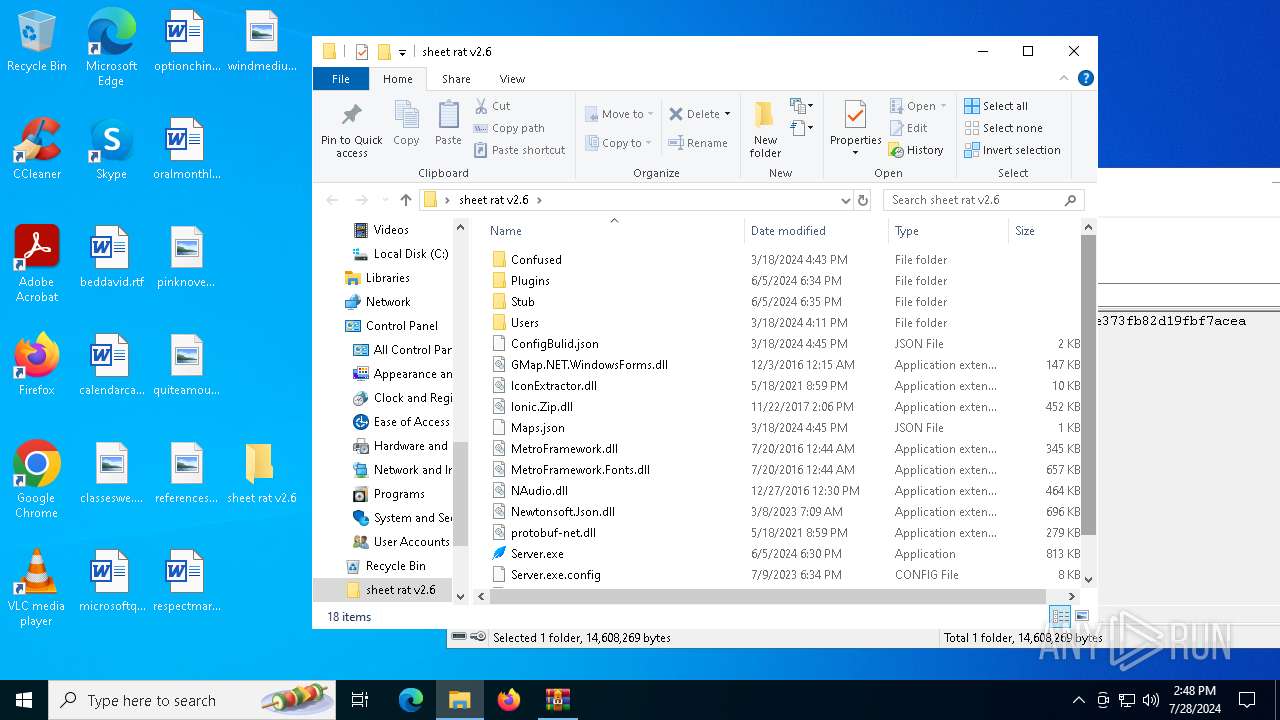
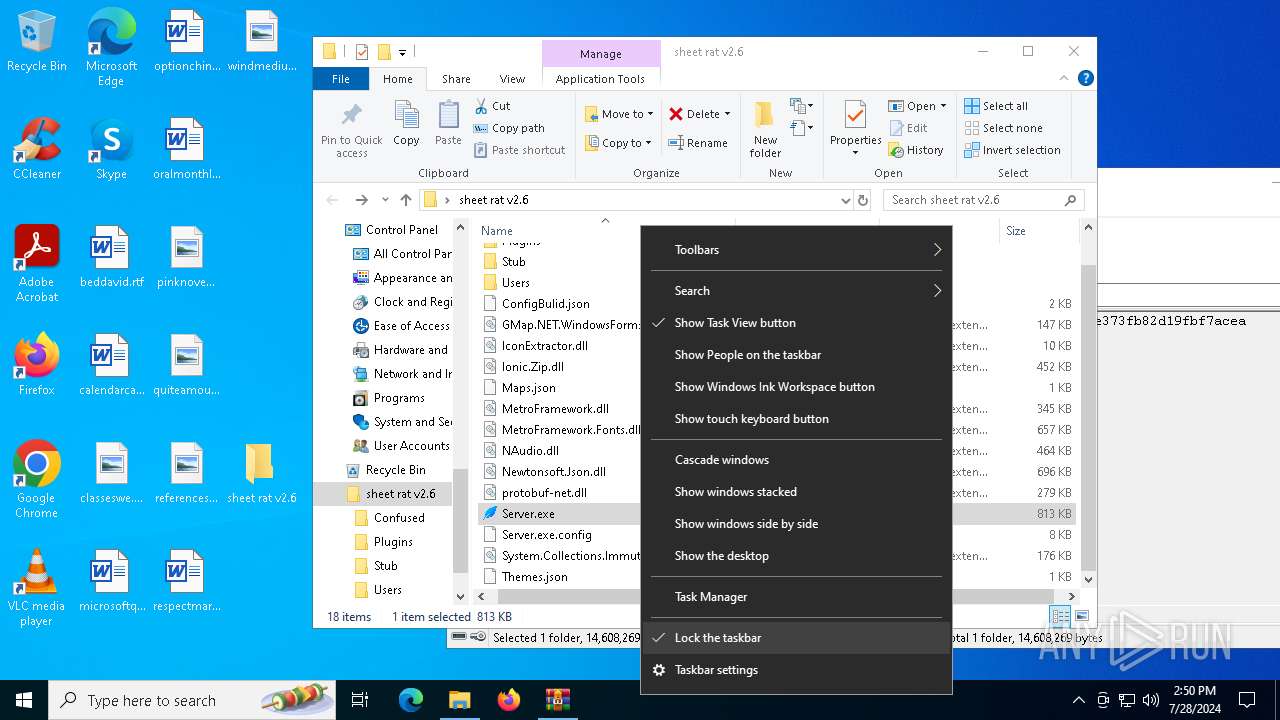
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6420)
- Server.exe (PID: 4356)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 5532)
- Server.exe (PID: 4356)
Process drops legitimate windows executable
- Server.exe (PID: 4356)
- WinRAR.exe (PID: 6420)
- WinRAR.exe (PID: 5532)
Executable content was dropped or overwritten
- Server.exe (PID: 4356)
Starts a Microsoft application from unusual location
- svchost.exe (PID: 1108)
- svchost.exe (PID: 1996)
Reads the date of Windows installation
- Server.exe (PID: 4356)
- Server.exe (PID: 1108)
Executes application which crashes
- Server.exe (PID: 1164)
- Server.exe (PID: 5848)
Reads security settings of Internet Explorer
- Server.exe (PID: 4356)
- Server.exe (PID: 1108)
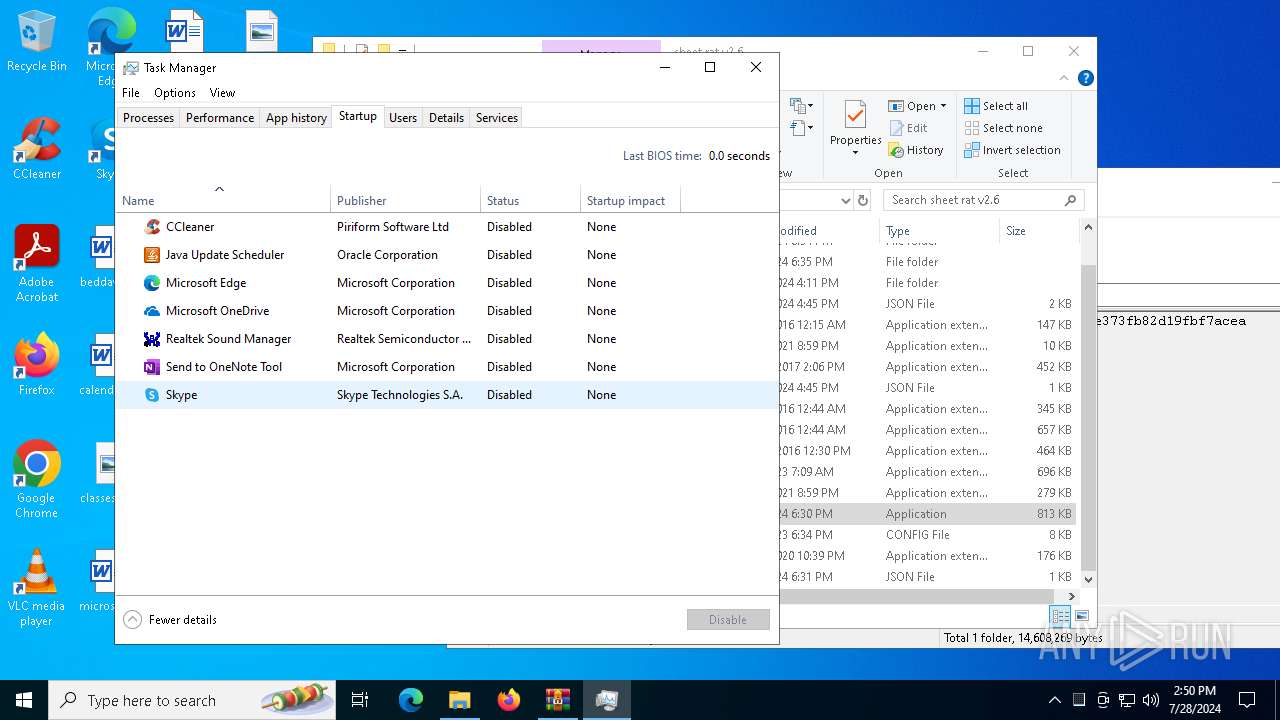
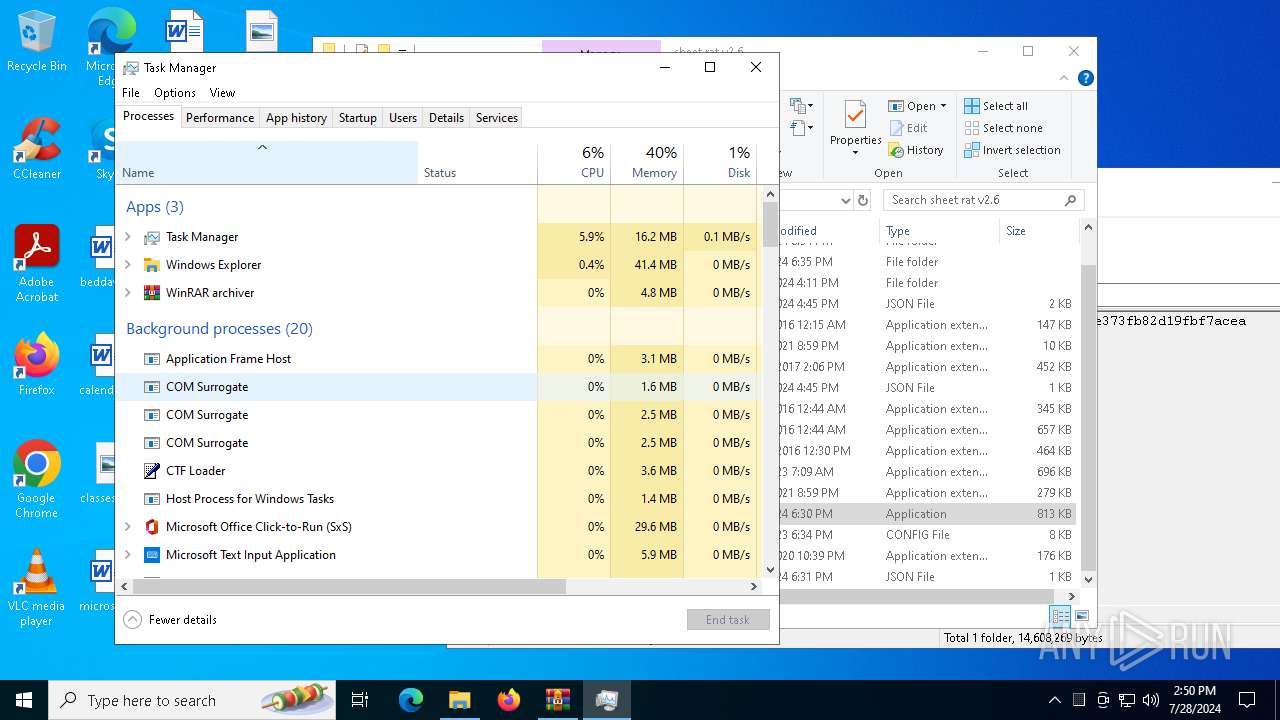
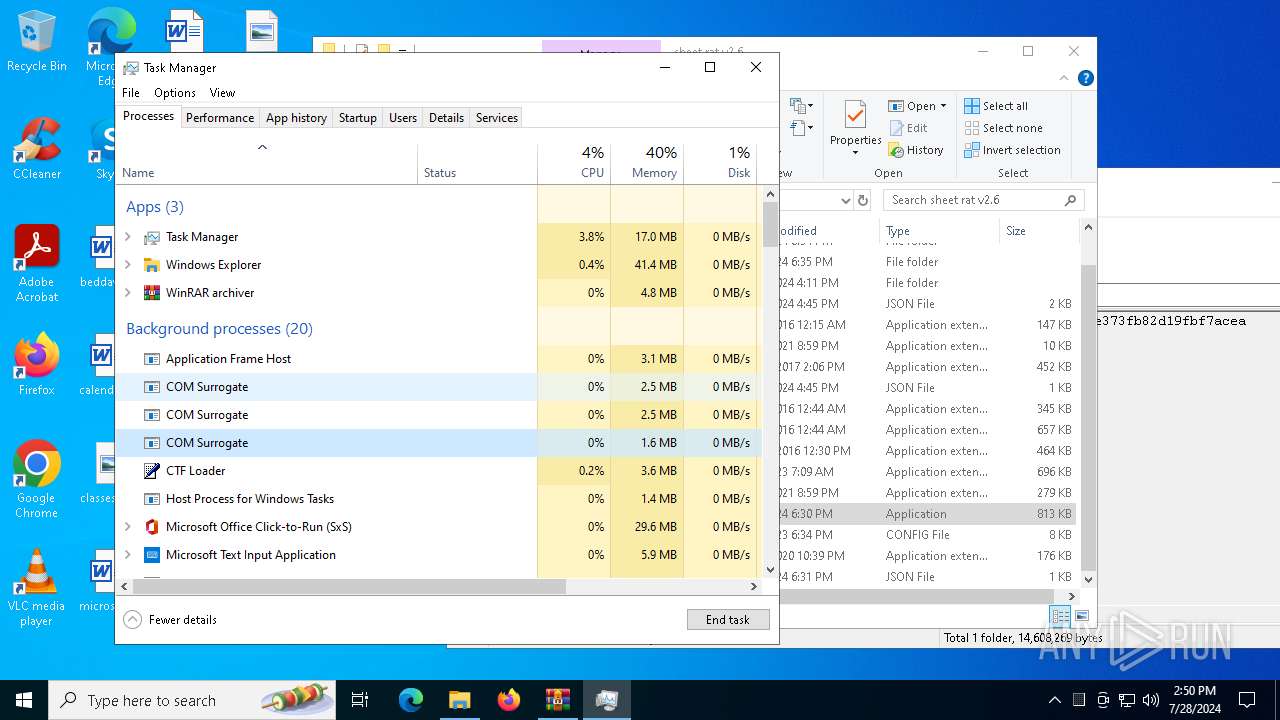
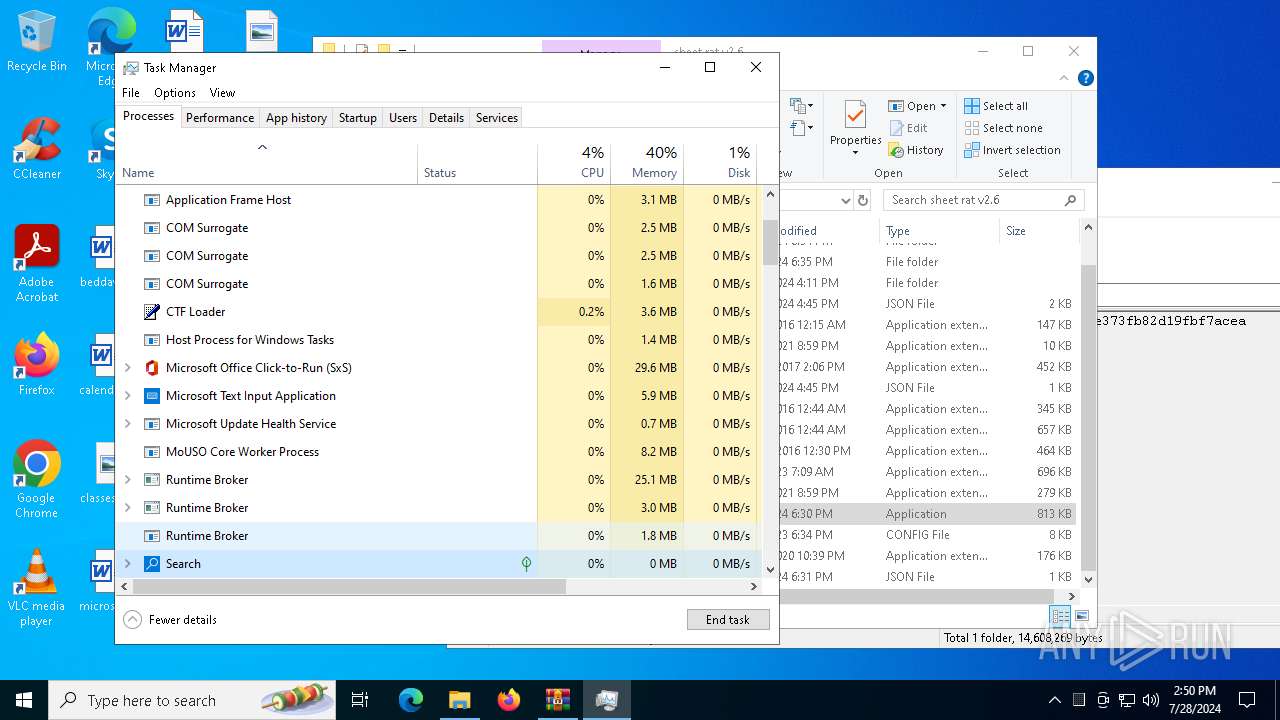
INFO
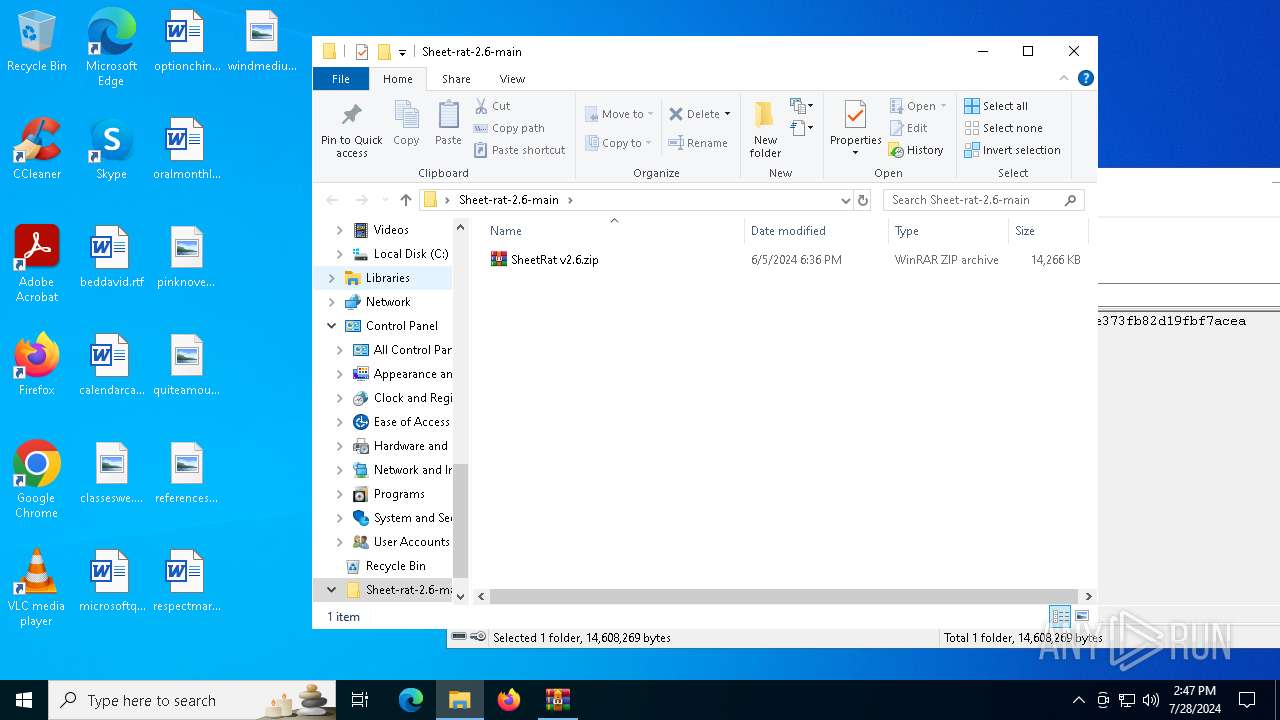
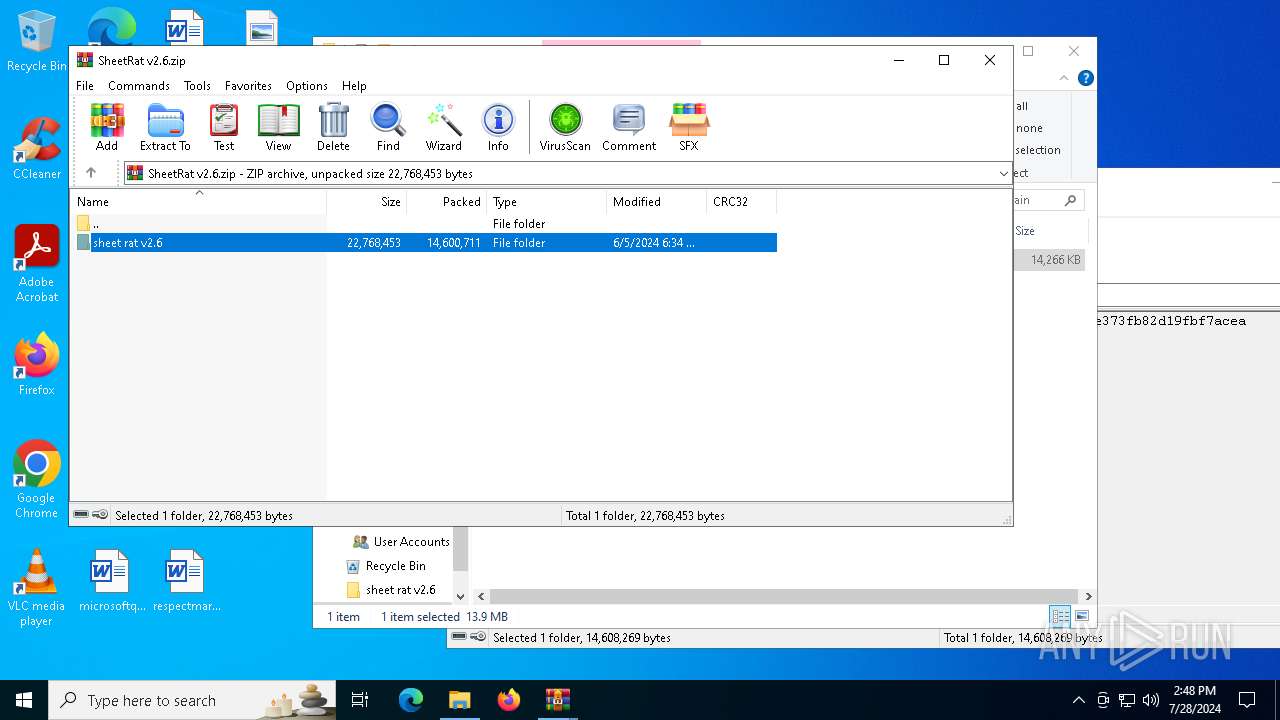
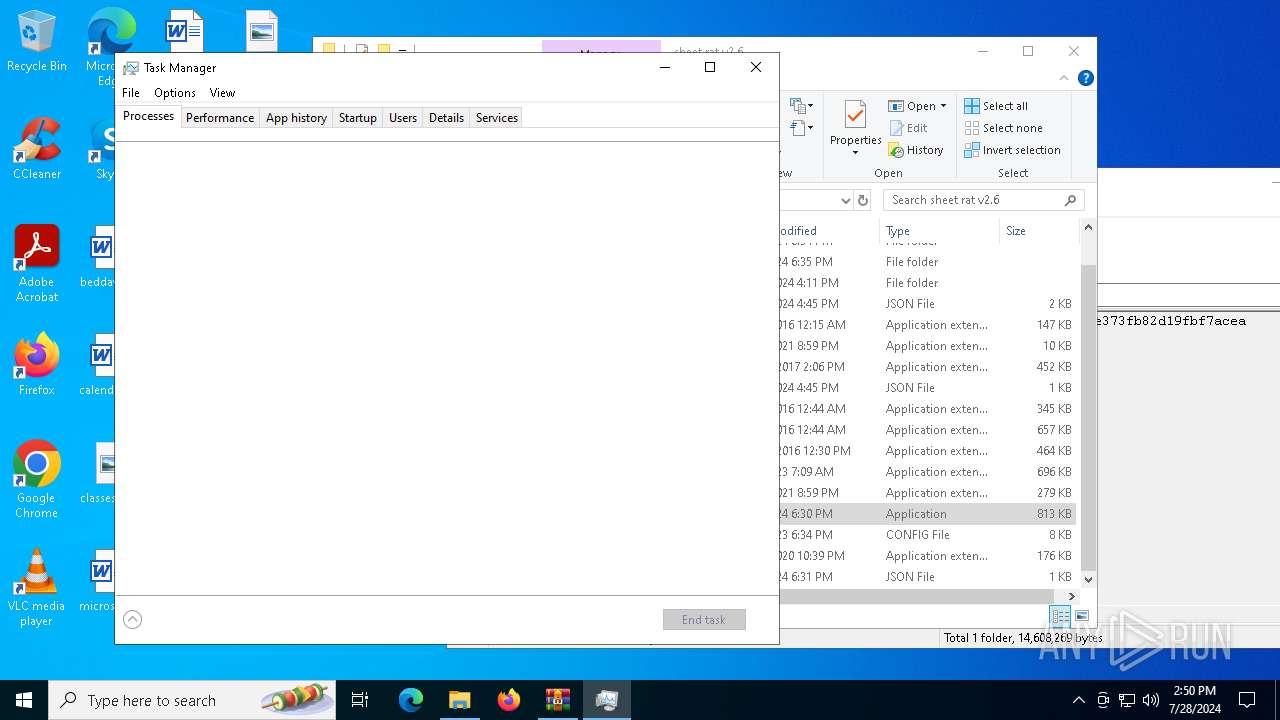
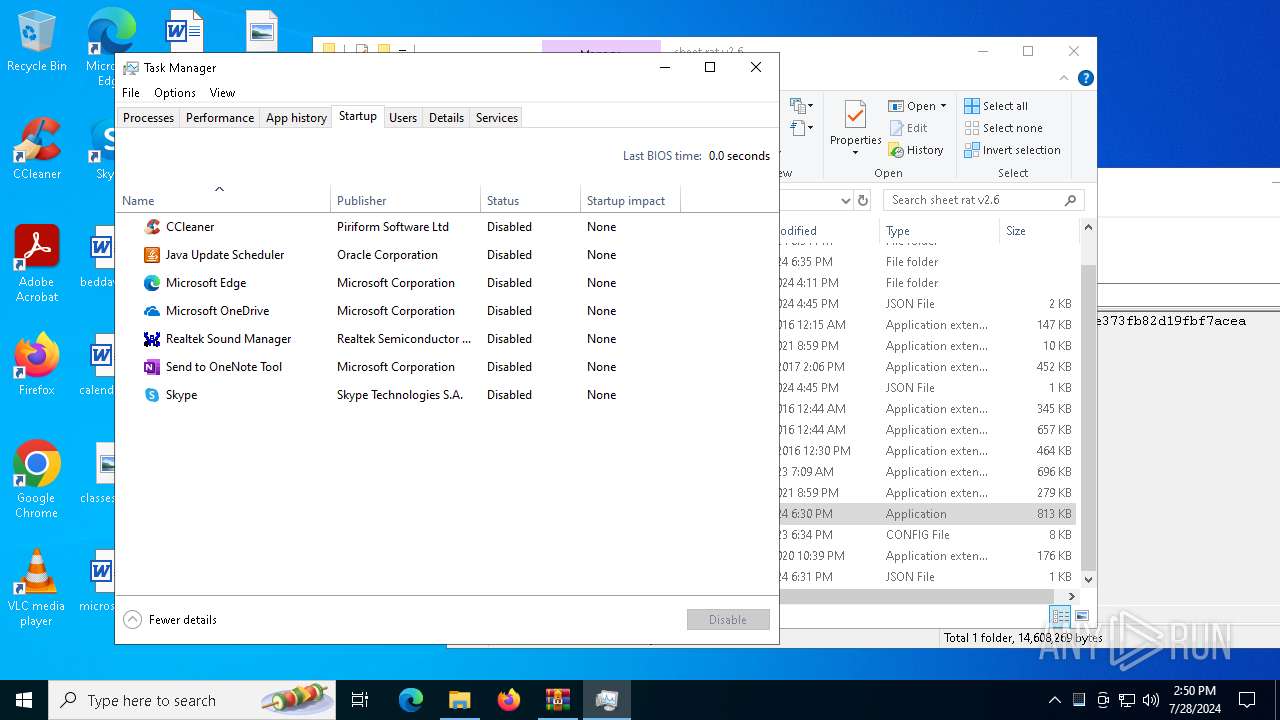
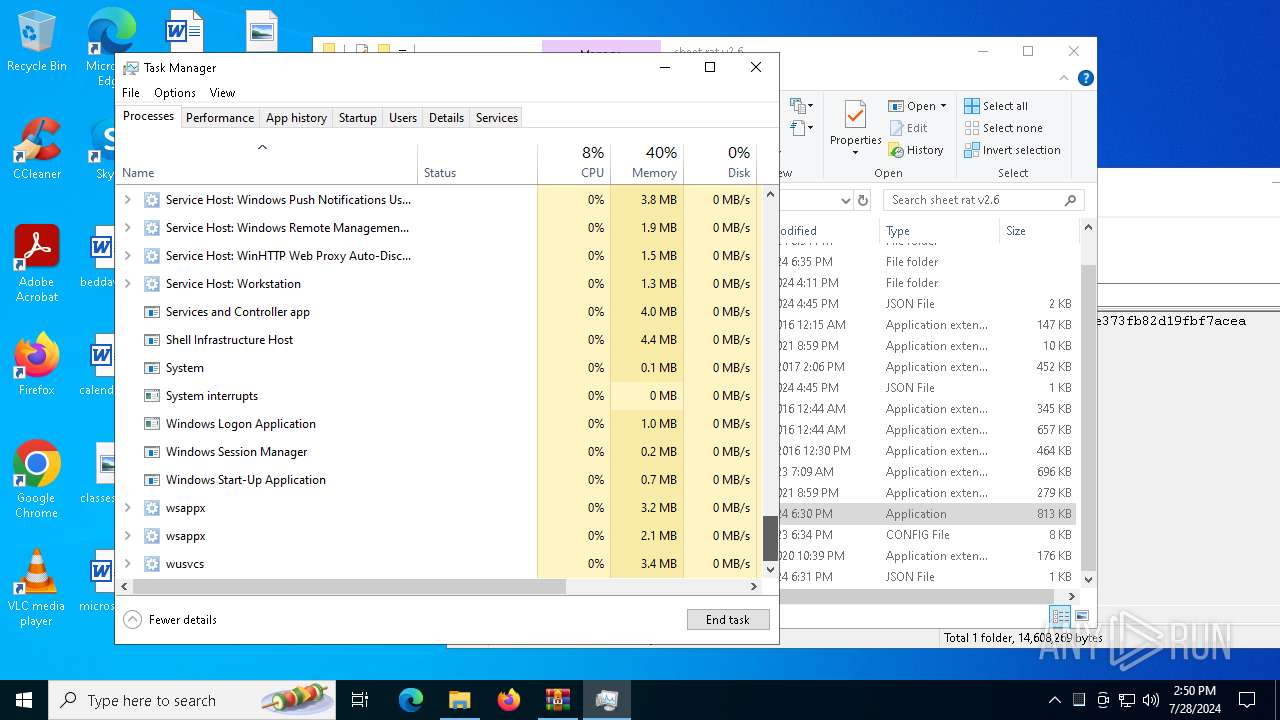
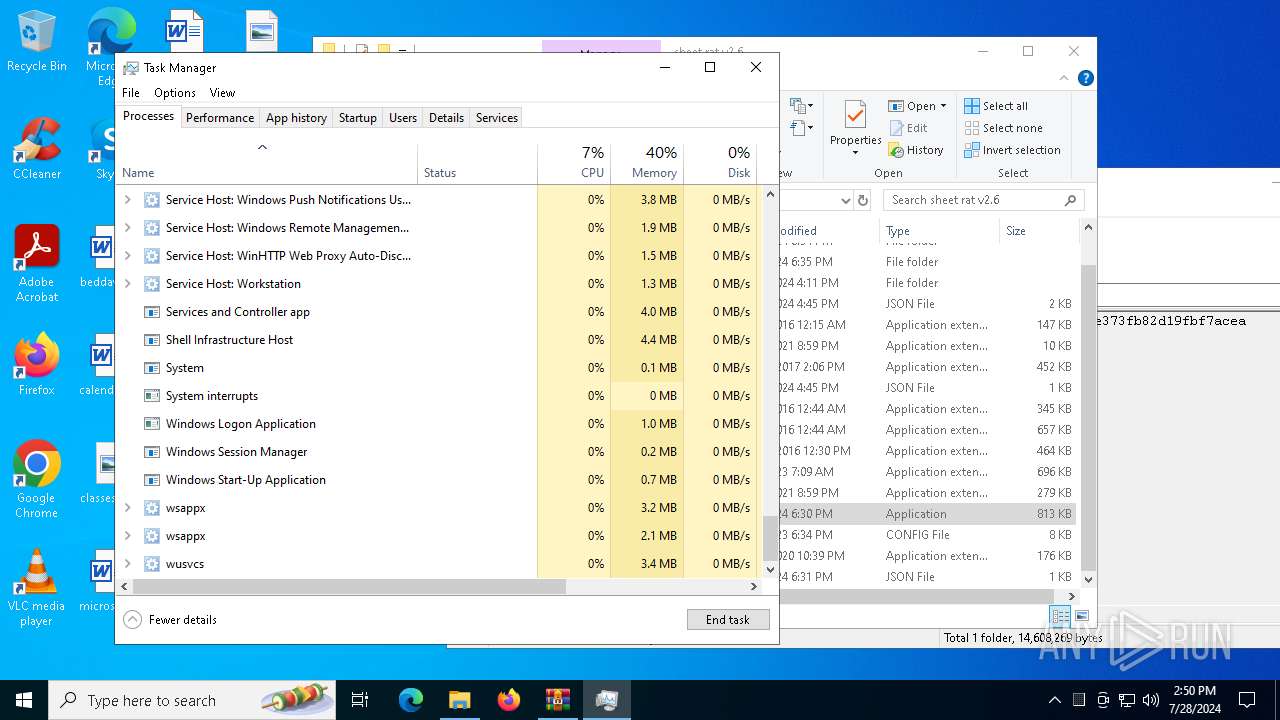
Manual execution by a user
- WinRAR.exe (PID: 5532)
- Server.exe (PID: 4356)
- Server.exe (PID: 1108)
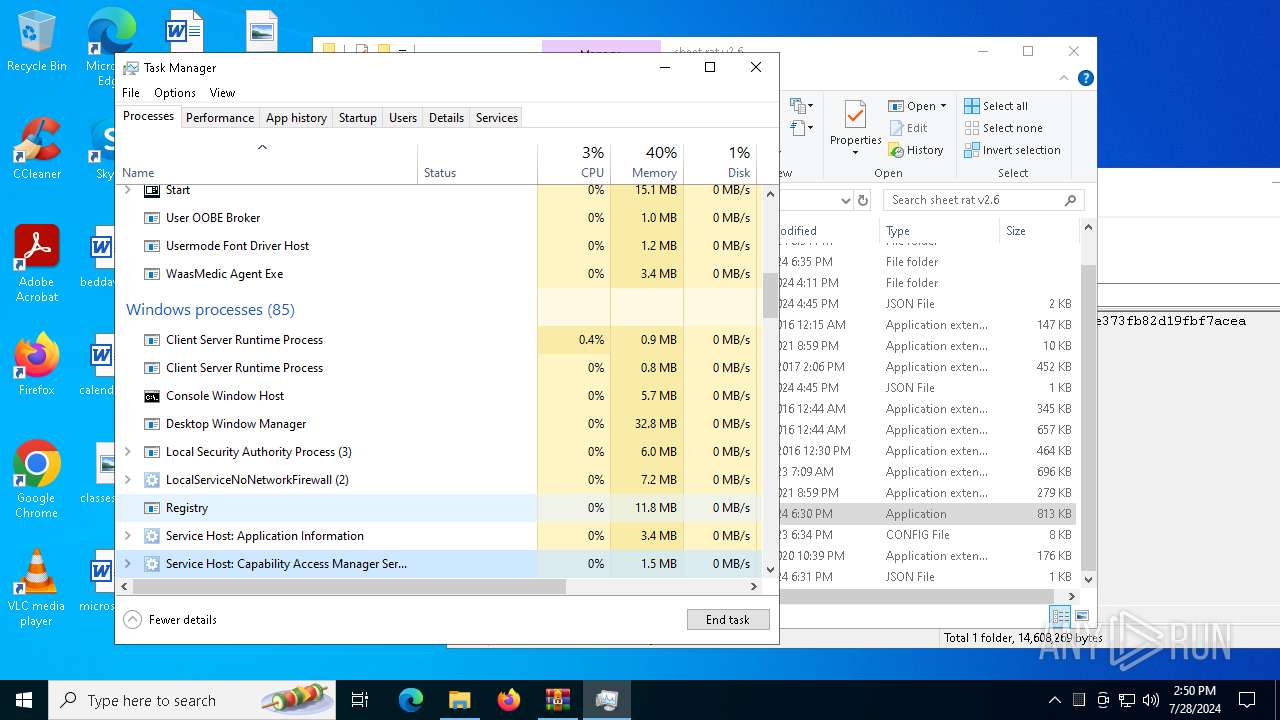
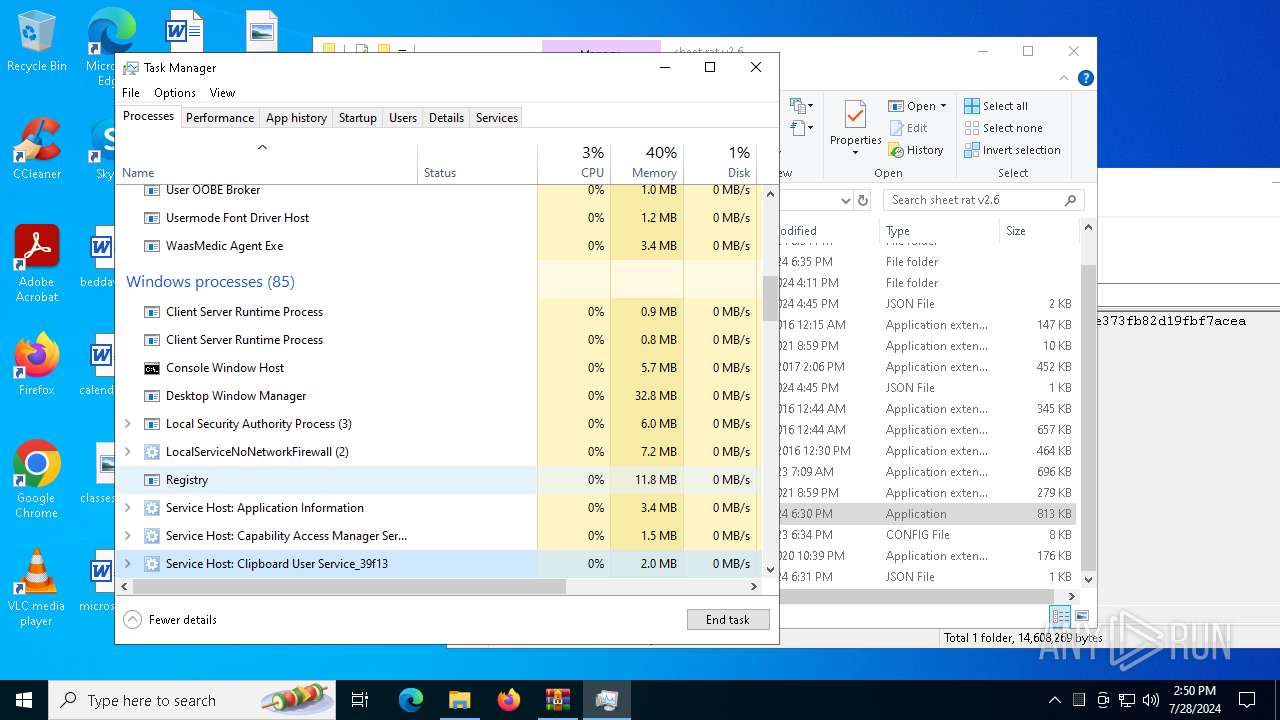
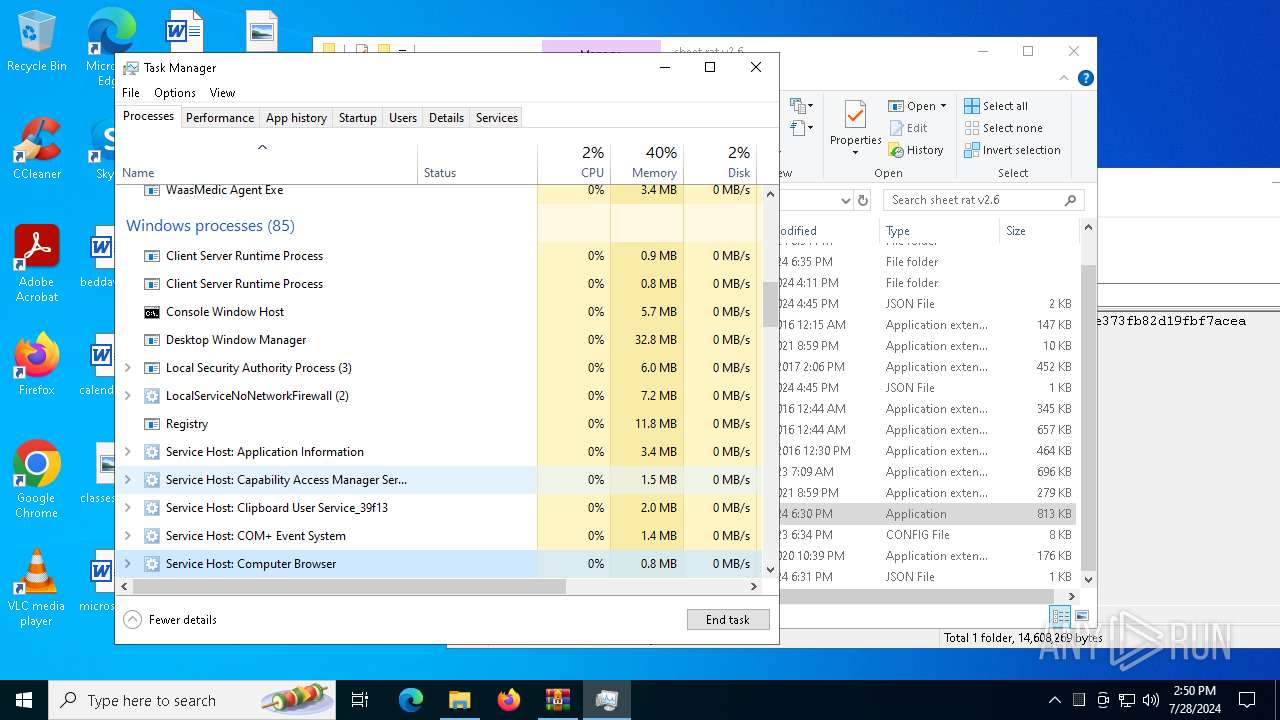
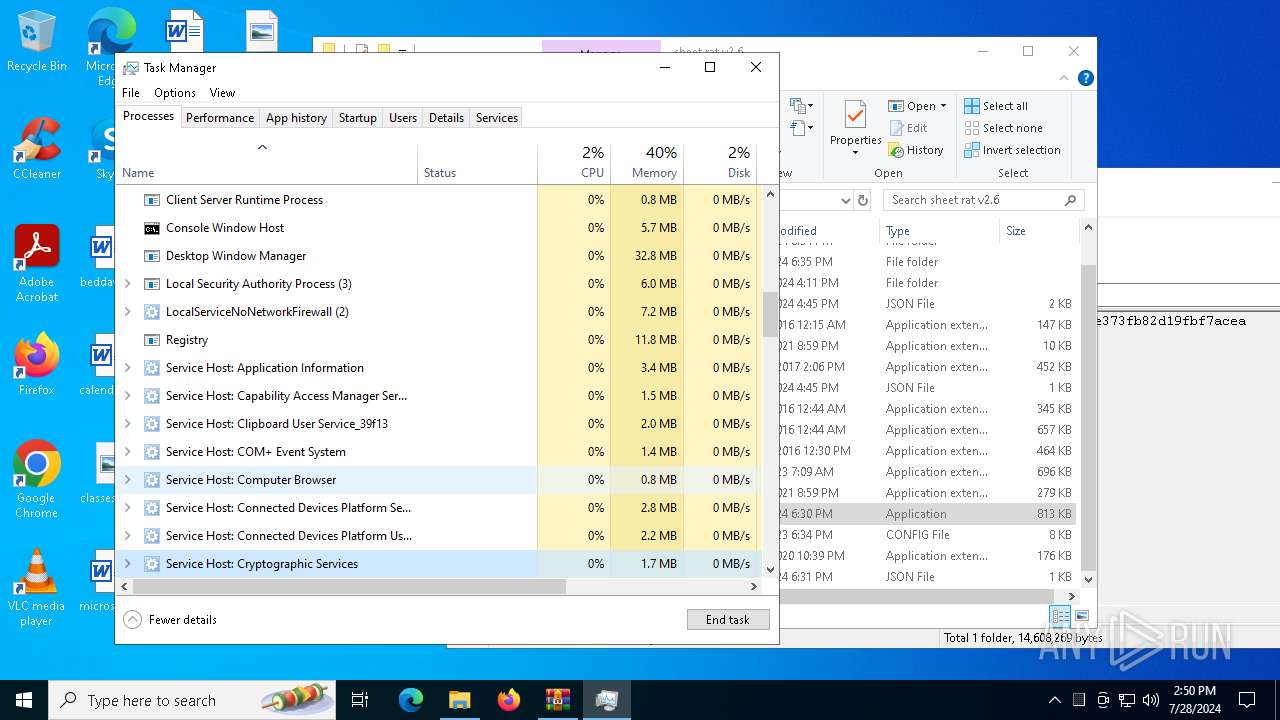
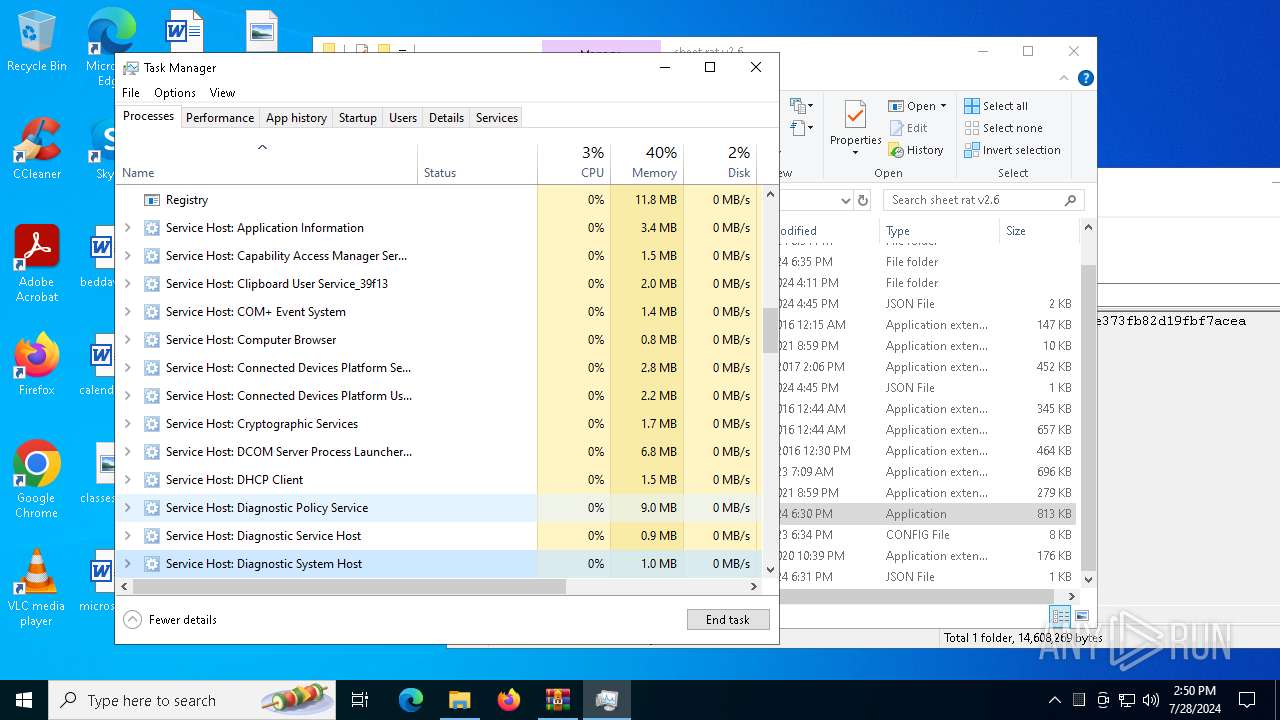
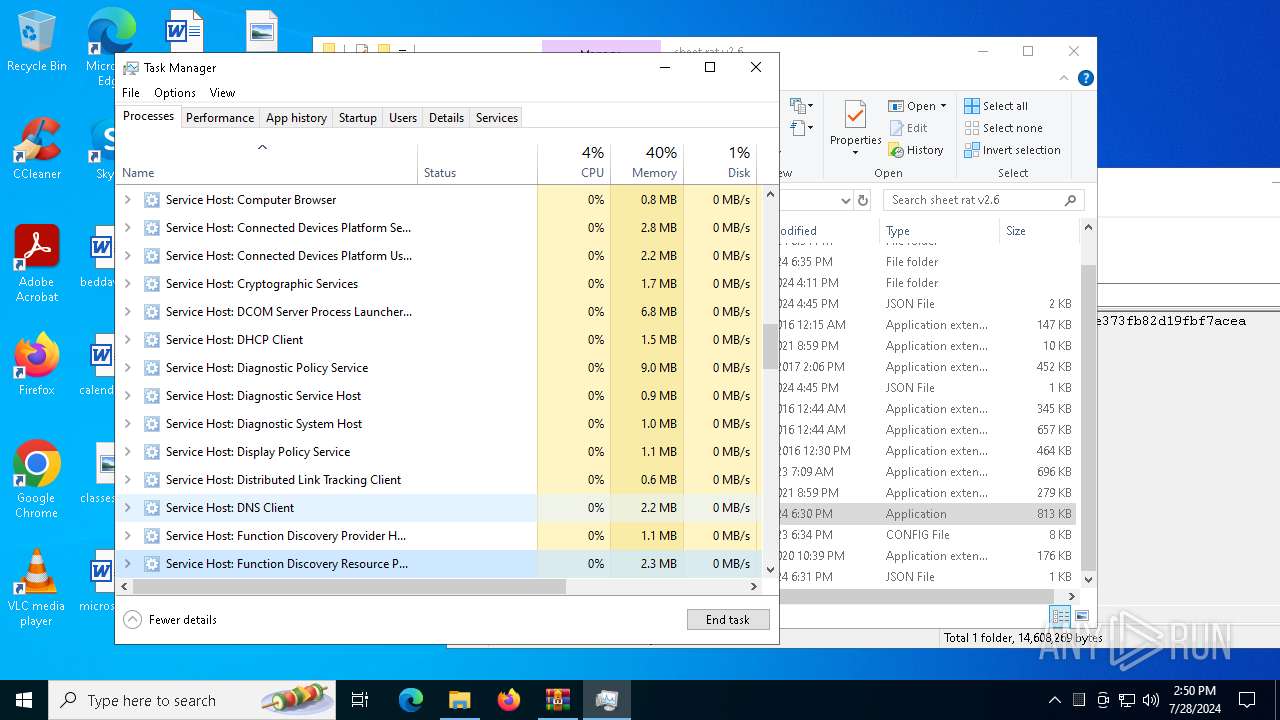
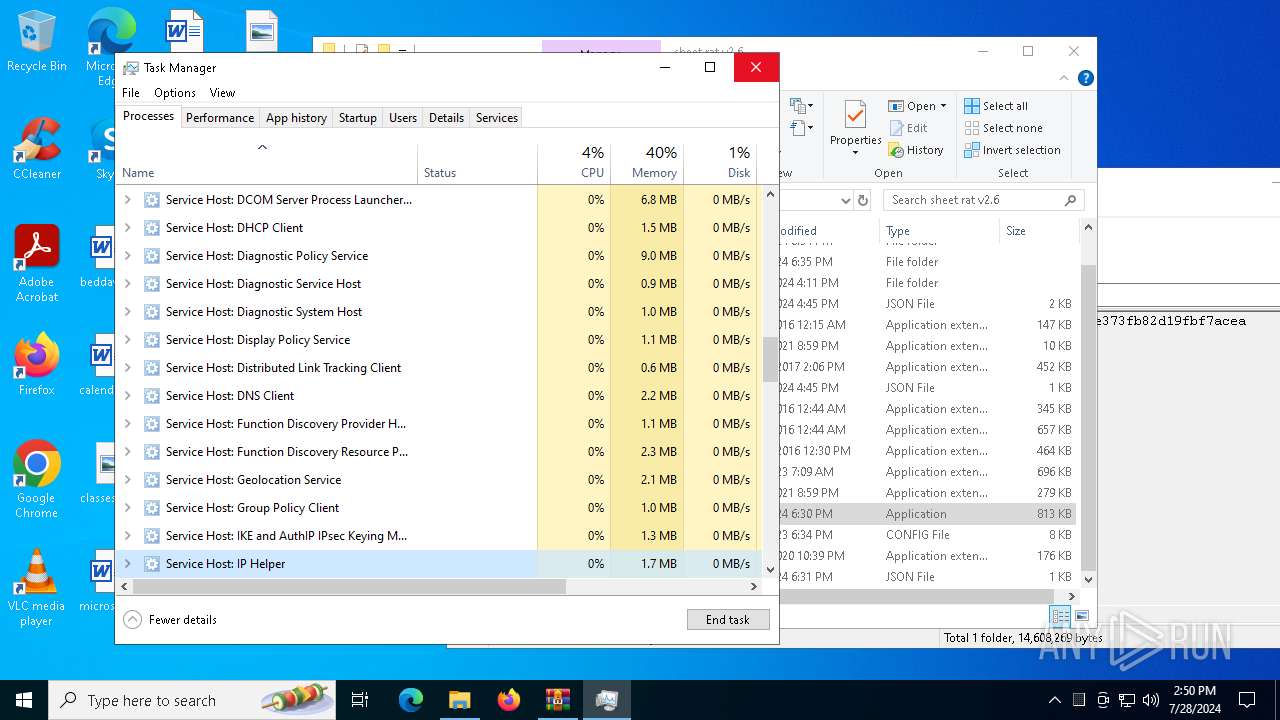
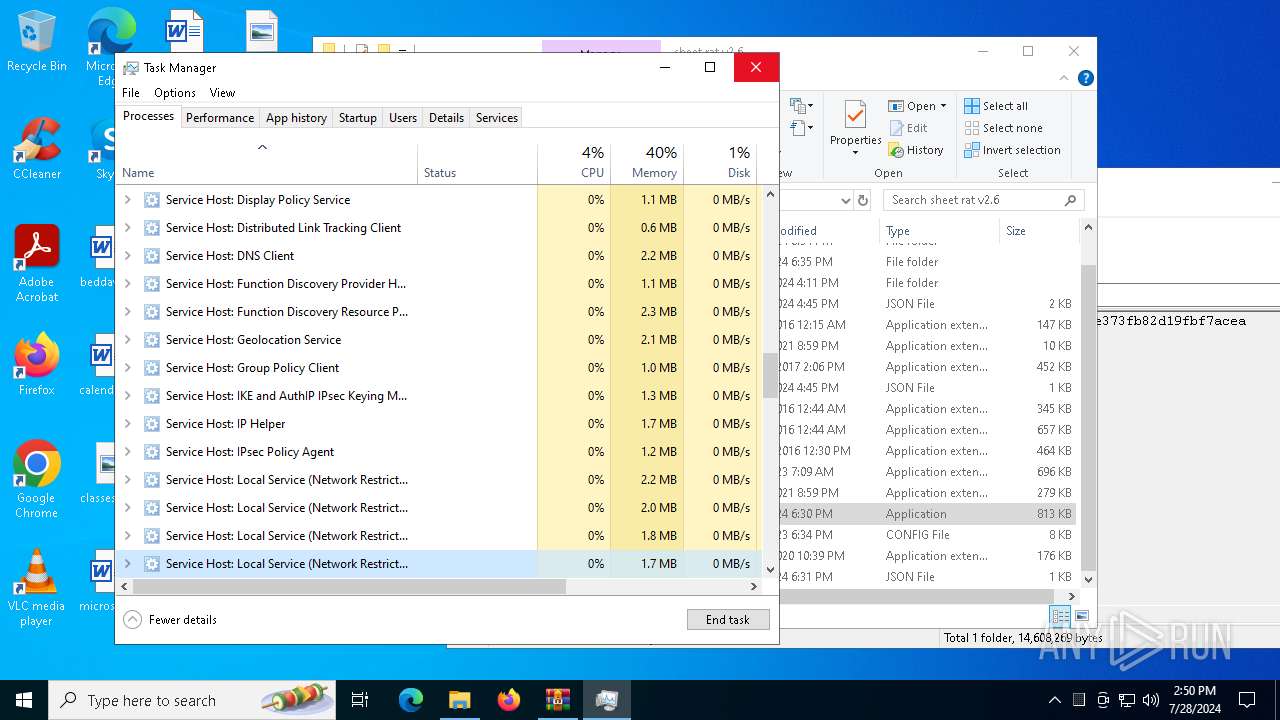
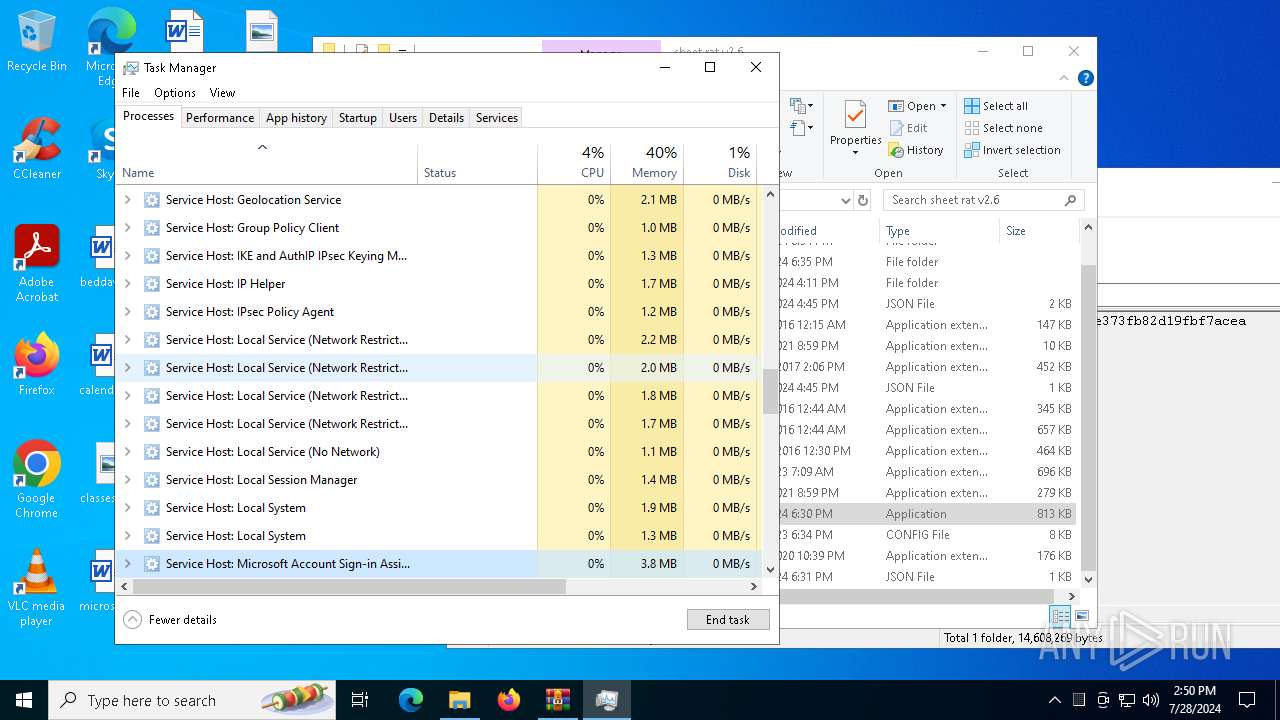
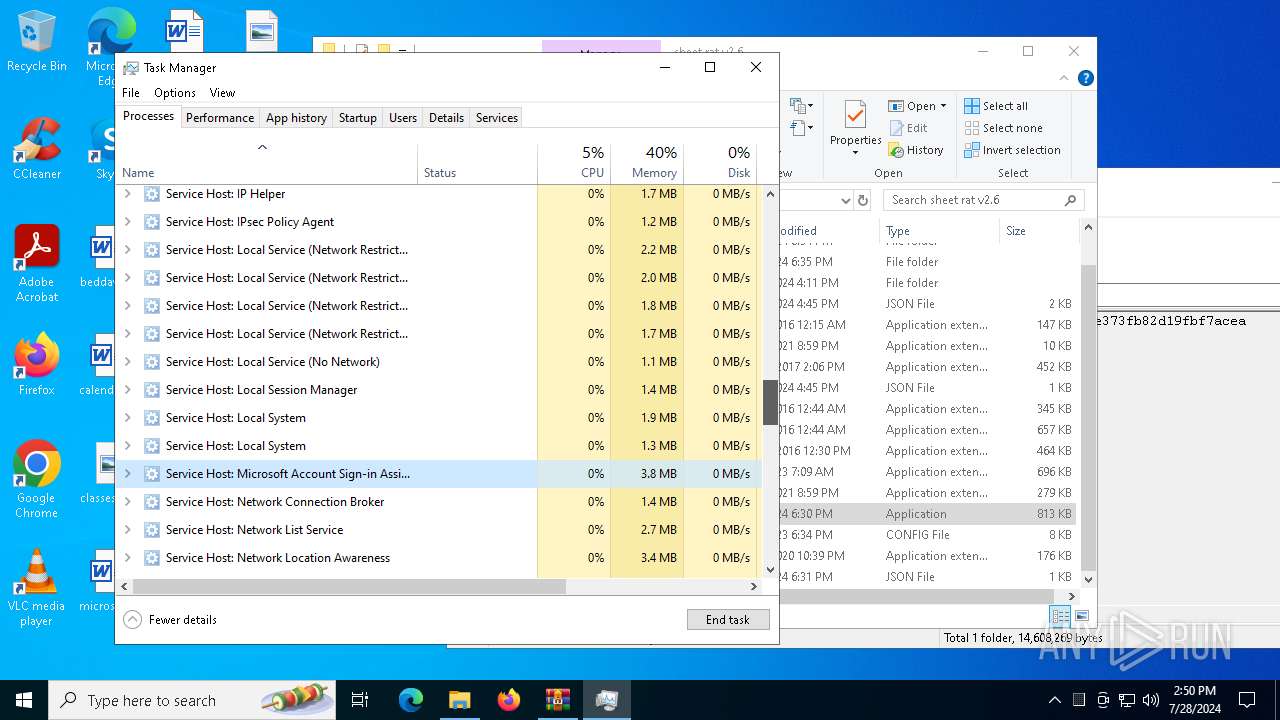
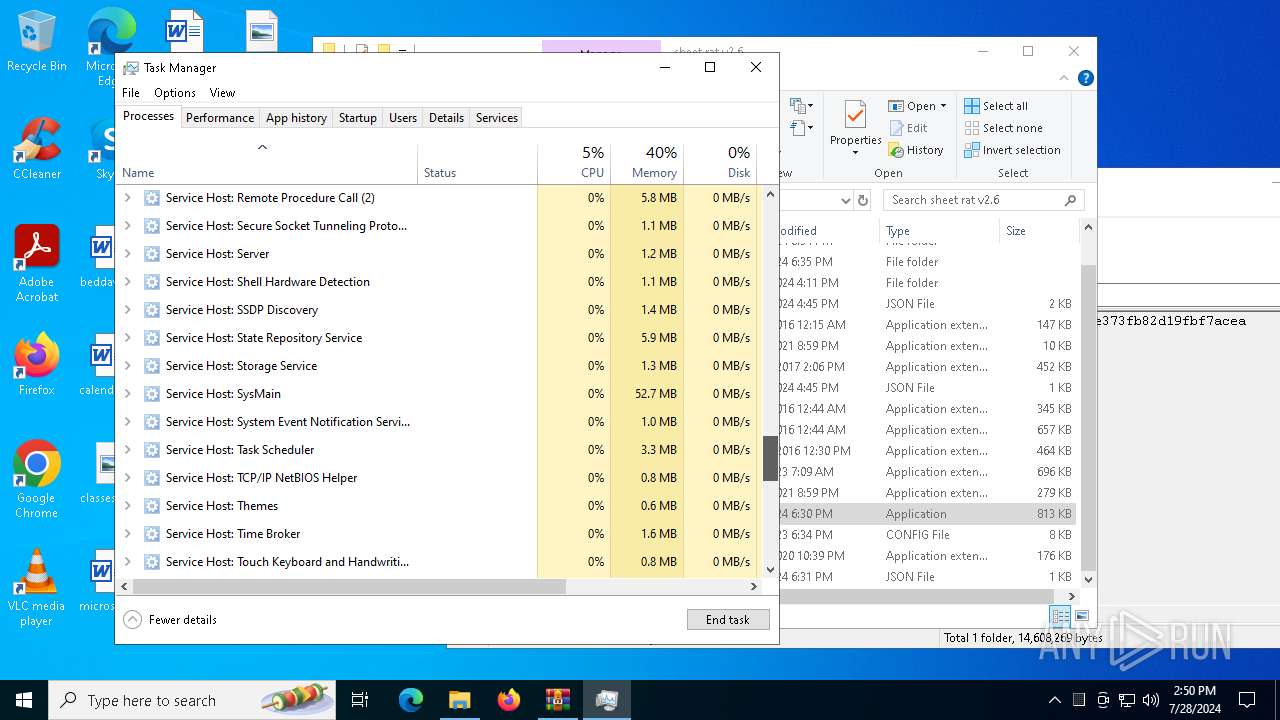
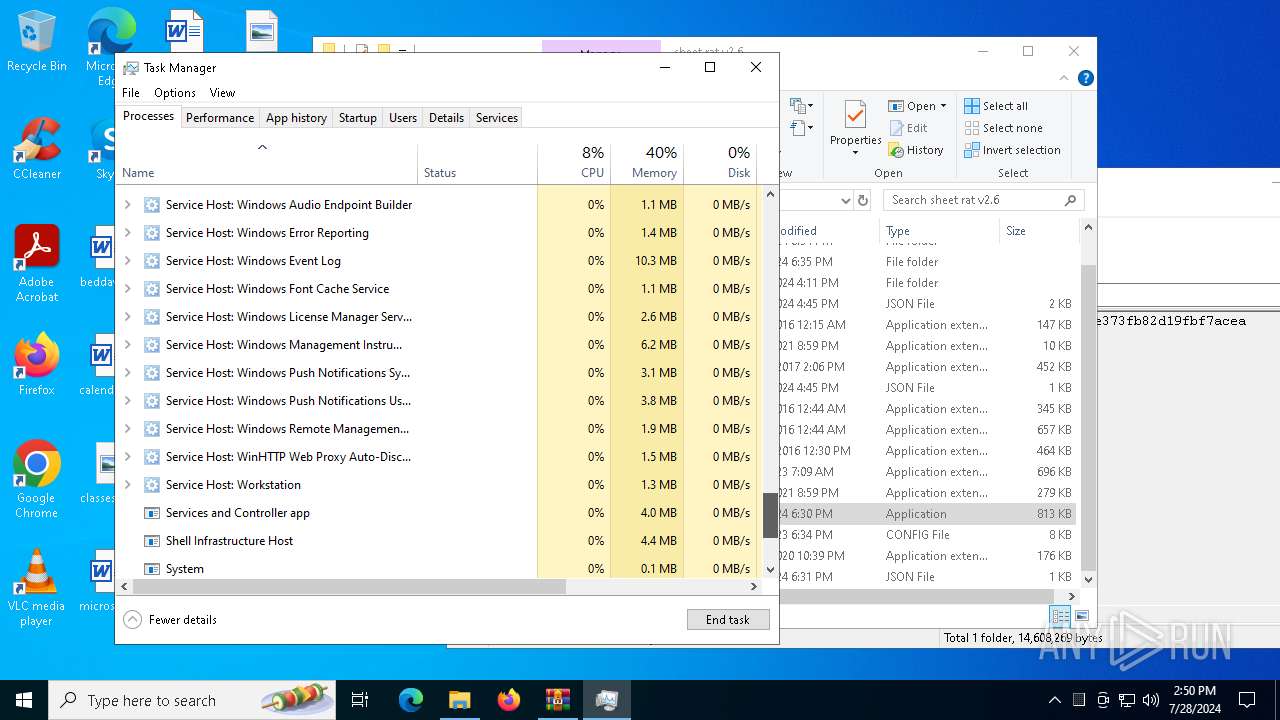
- Taskmgr.exe (PID: 6140)
- Taskmgr.exe (PID: 7104)
Reads the computer name
- Server.exe (PID: 4356)
- svchost.exe (PID: 1108)
- svchost.exe (PID: 1996)
- Server.exe (PID: 5848)
- Server.exe (PID: 1108)
- Server.exe (PID: 1164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5532)
Checks supported languages
- Server.exe (PID: 4356)
- Server.exe (PID: 1164)
- svchost.exe (PID: 1108)
- Server.exe (PID: 1108)
- svchost.exe (PID: 1996)
- Server.exe (PID: 5848)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5532)
Reads the machine GUID from the registry
- Server.exe (PID: 4356)
- Server.exe (PID: 1108)
Create files in a temporary directory
- Server.exe (PID: 4356)
- Server.exe (PID: 1108)
Checks proxy server information
- WerFault.exe (PID: 4520)
- slui.exe (PID: 5740)
- WerFault.exe (PID: 6296)
Reads the software policy settings
- WerFault.exe (PID: 4520)
- slui.exe (PID: 5740)
- WerFault.exe (PID: 6296)
Process checks computer location settings
- Server.exe (PID: 1108)
- Server.exe (PID: 4356)
Creates files or folders in the user directory
- WerFault.exe (PID: 6296)
- WerFault.exe (PID: 4520)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:06:05 11:36:28 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Sheet-rat-2.6-main/ |
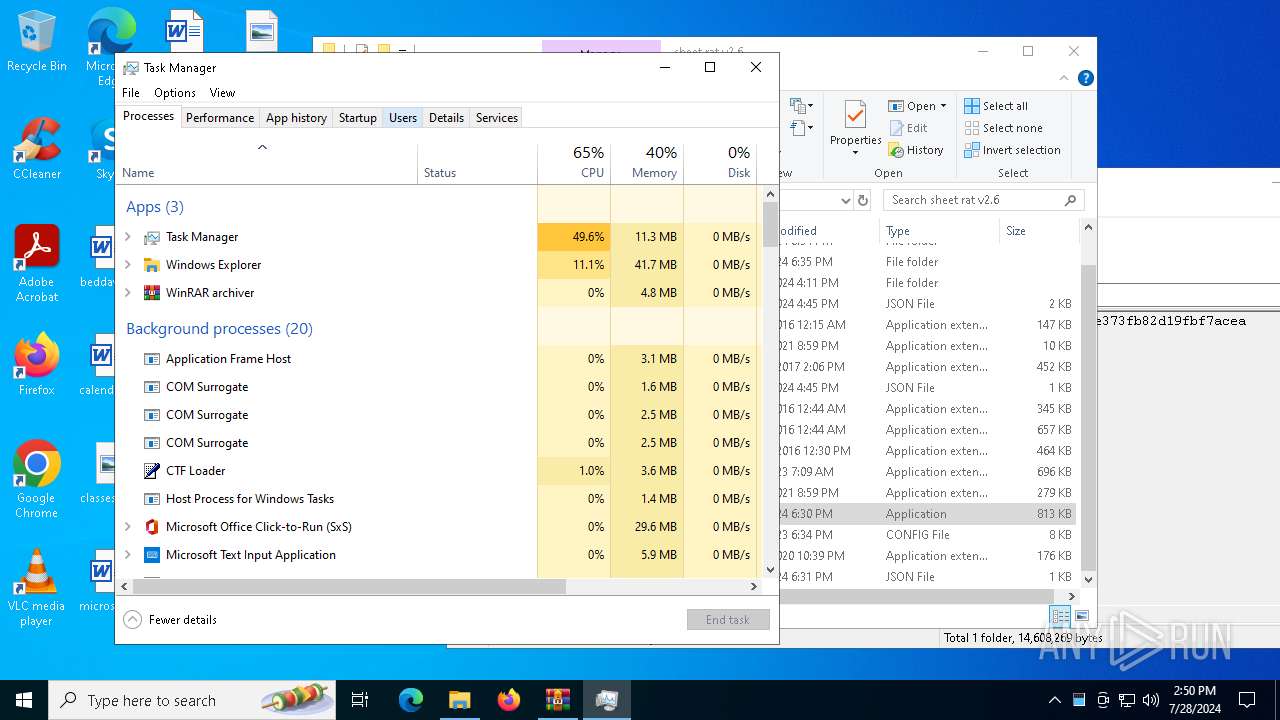
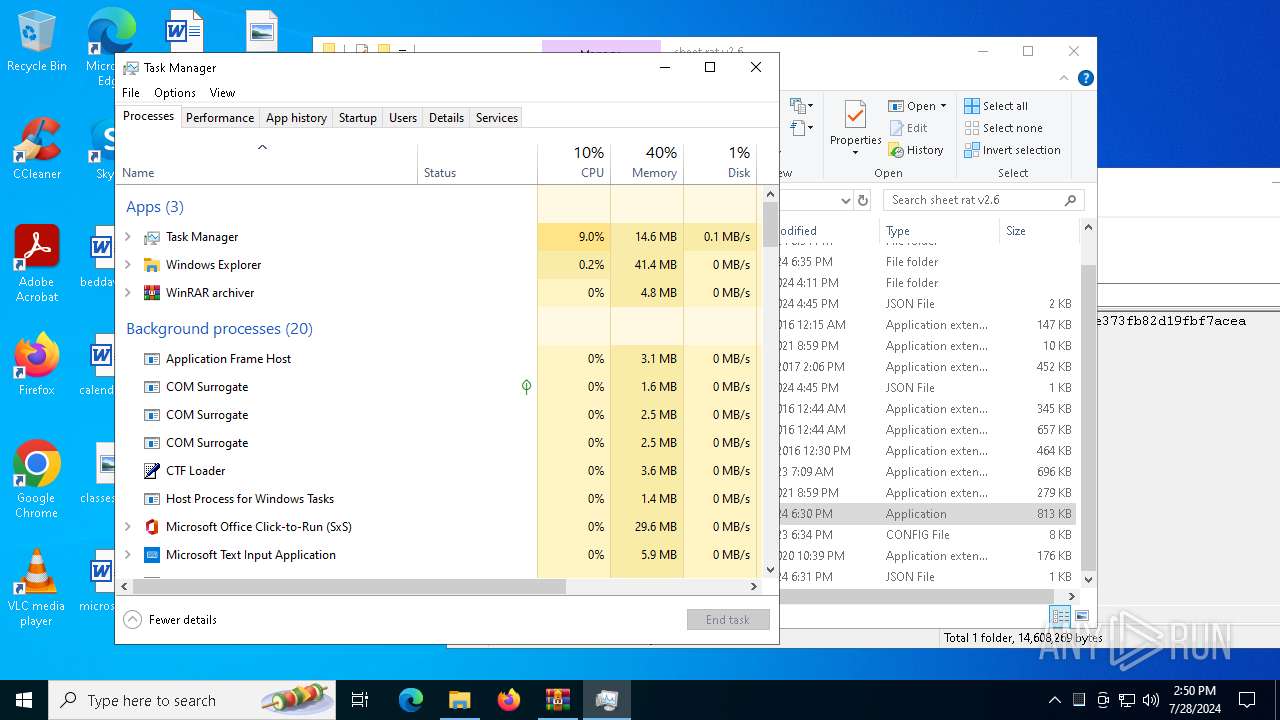
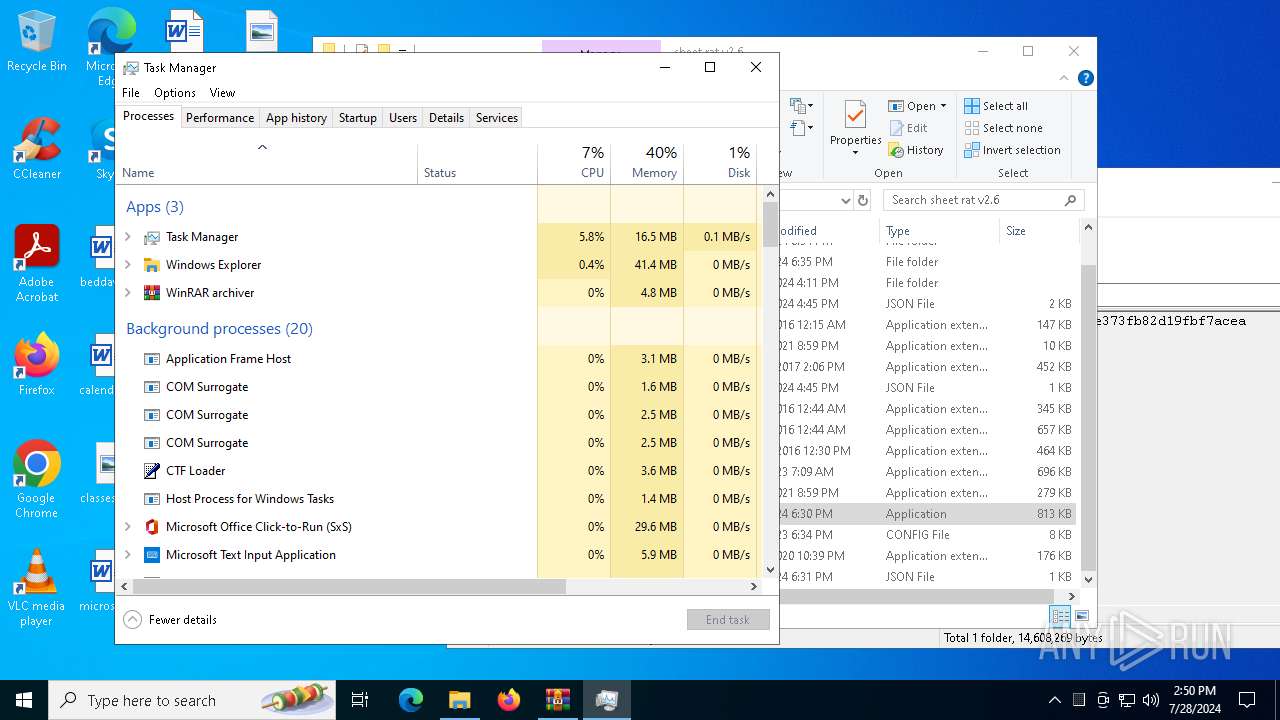
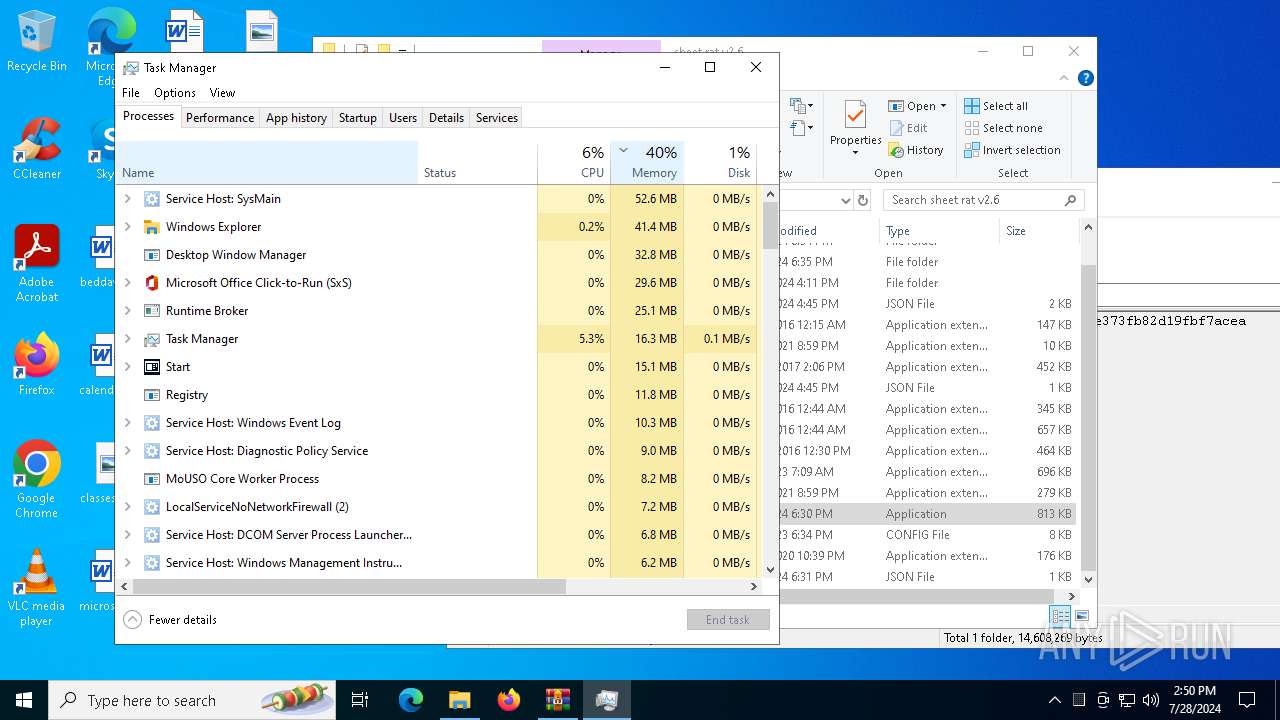
Total processes
156
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
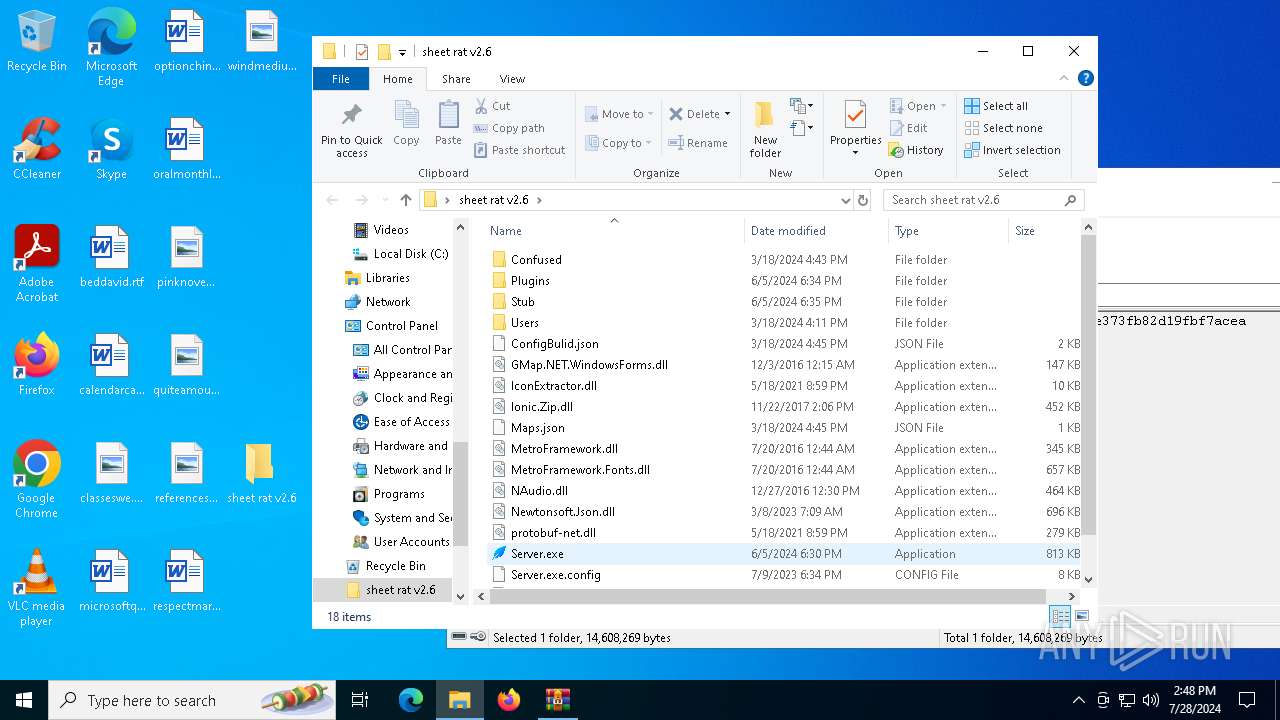
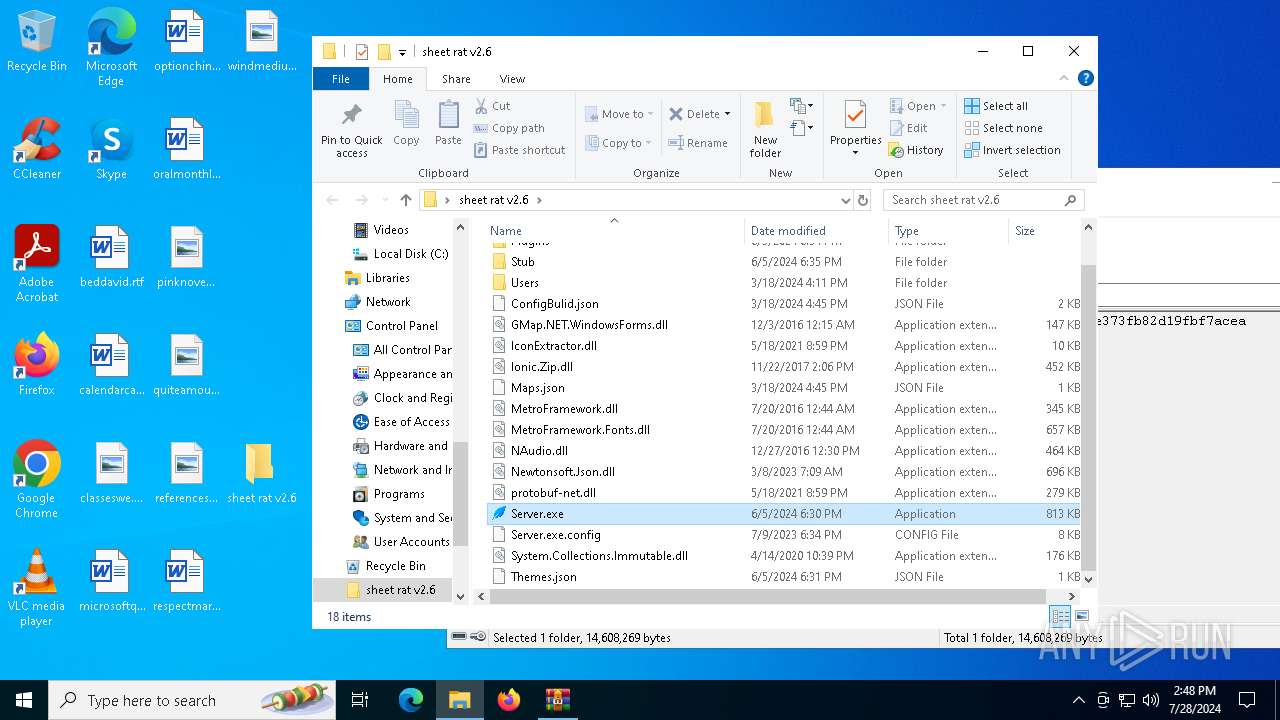
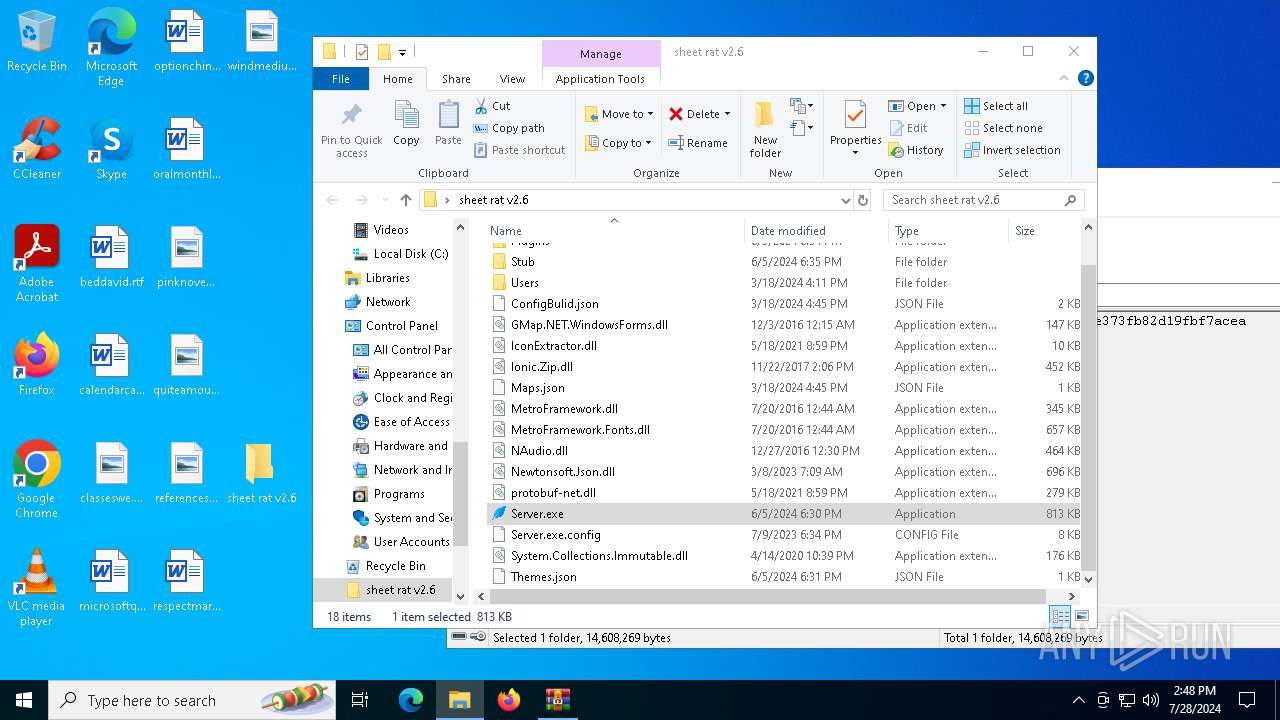
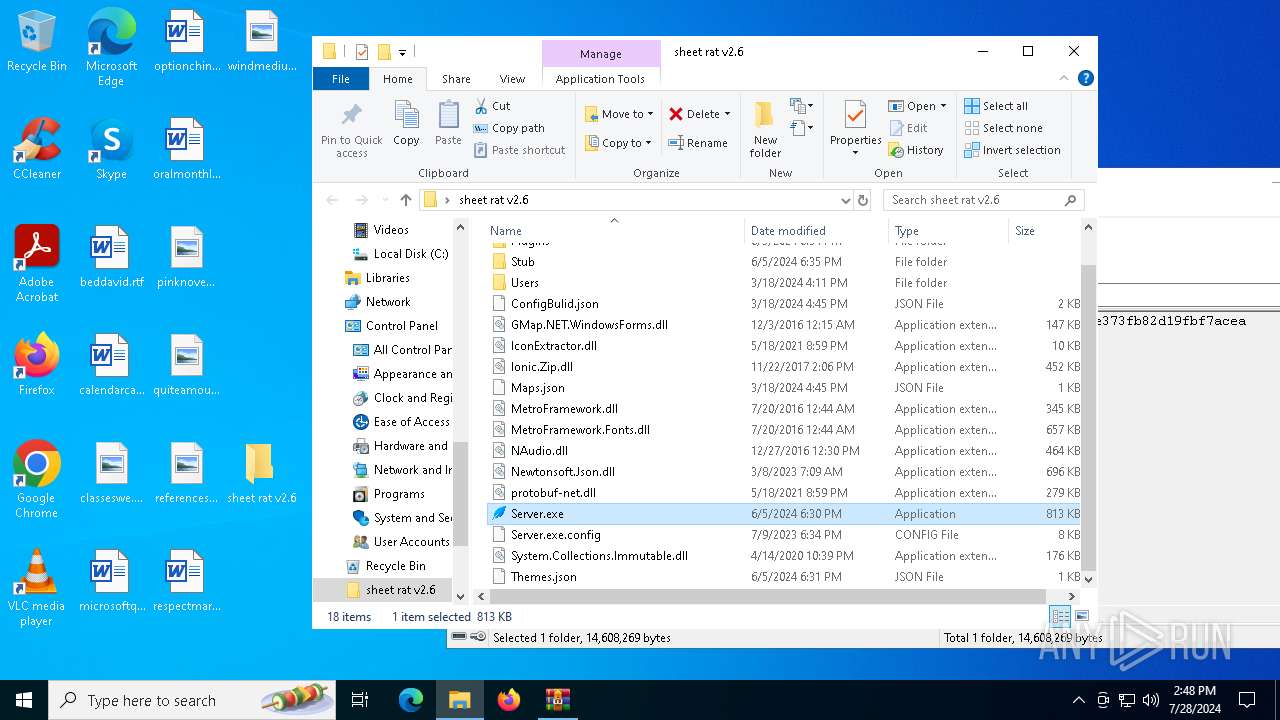
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
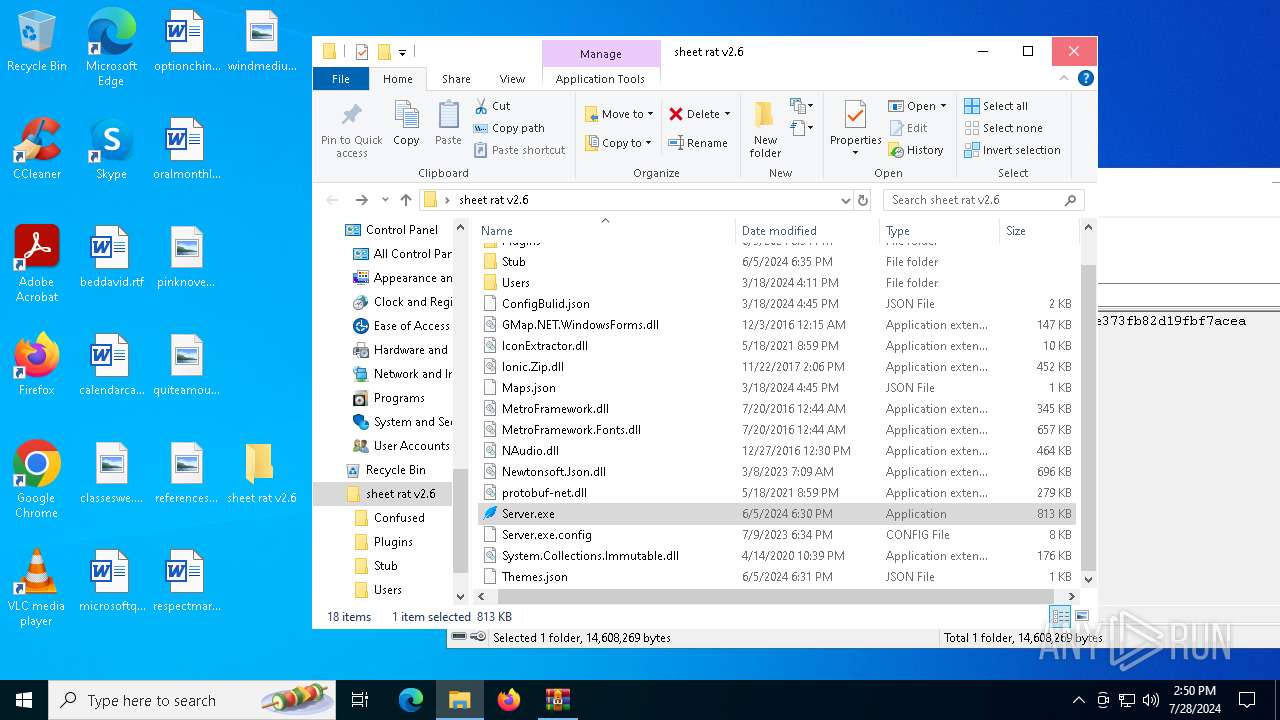
| 1108 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | — | Server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 459 Version: 10.0.19041.4355 Modules
| |||||||||||||||
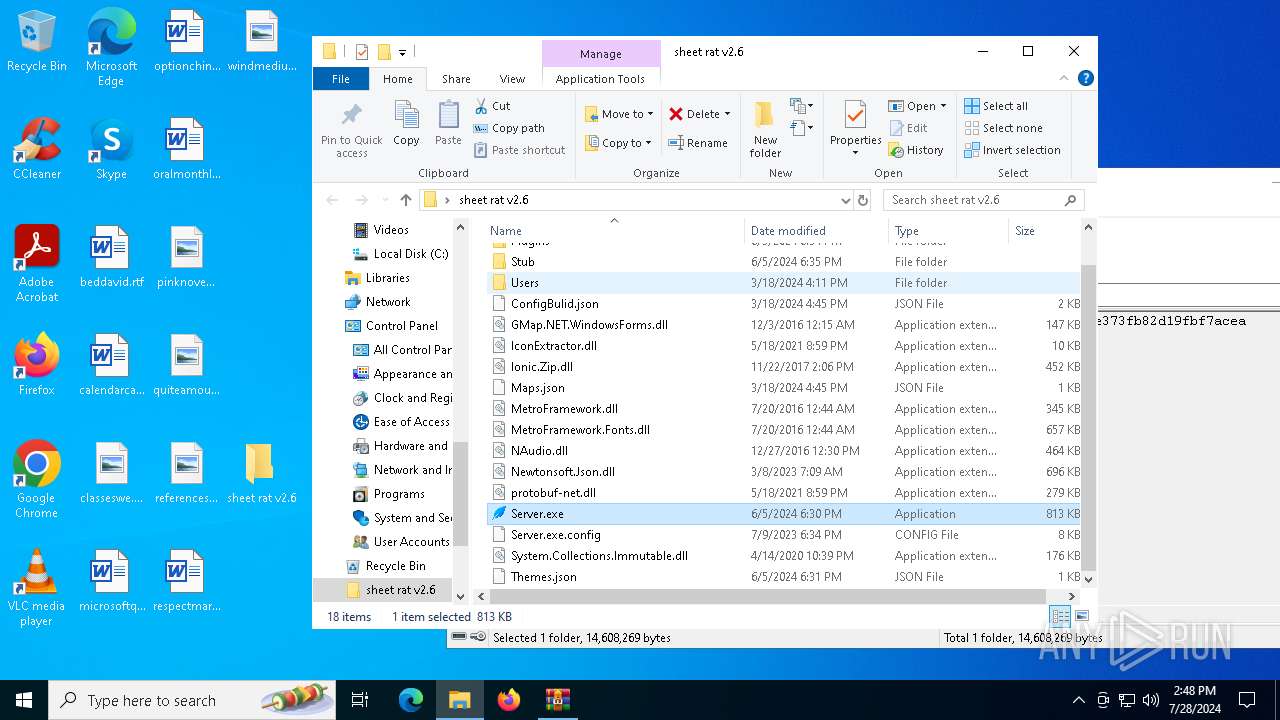
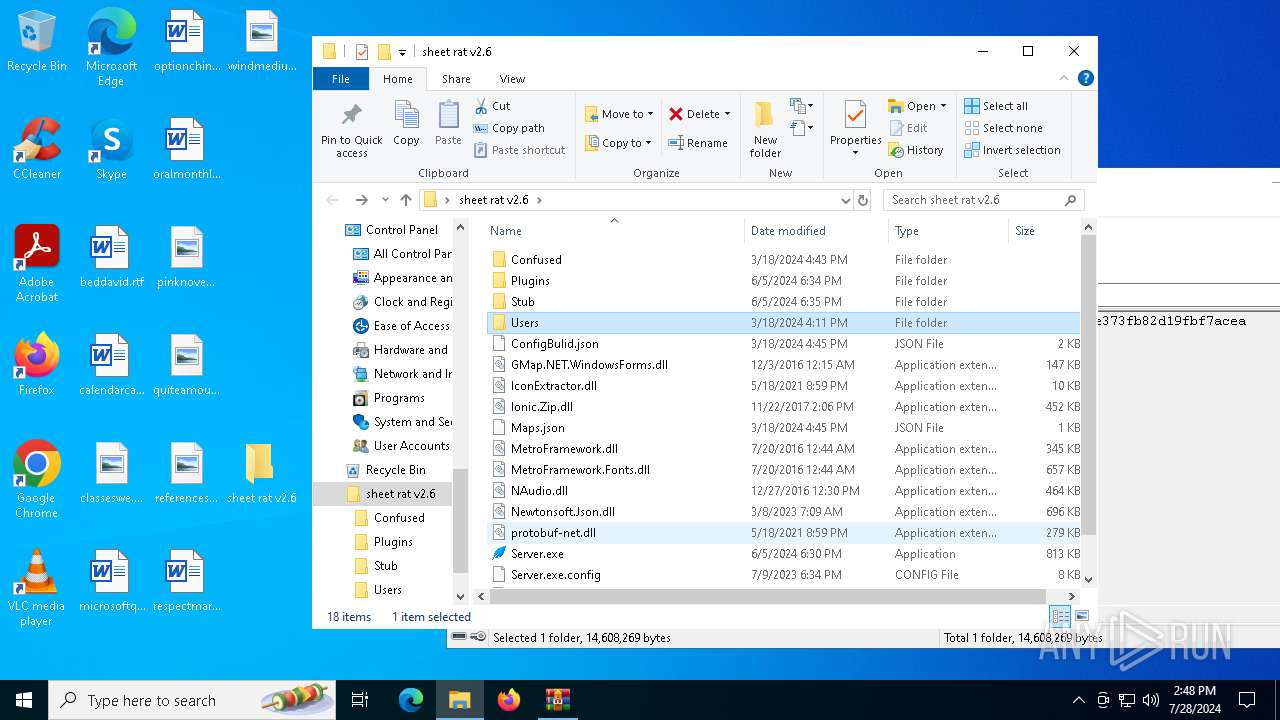
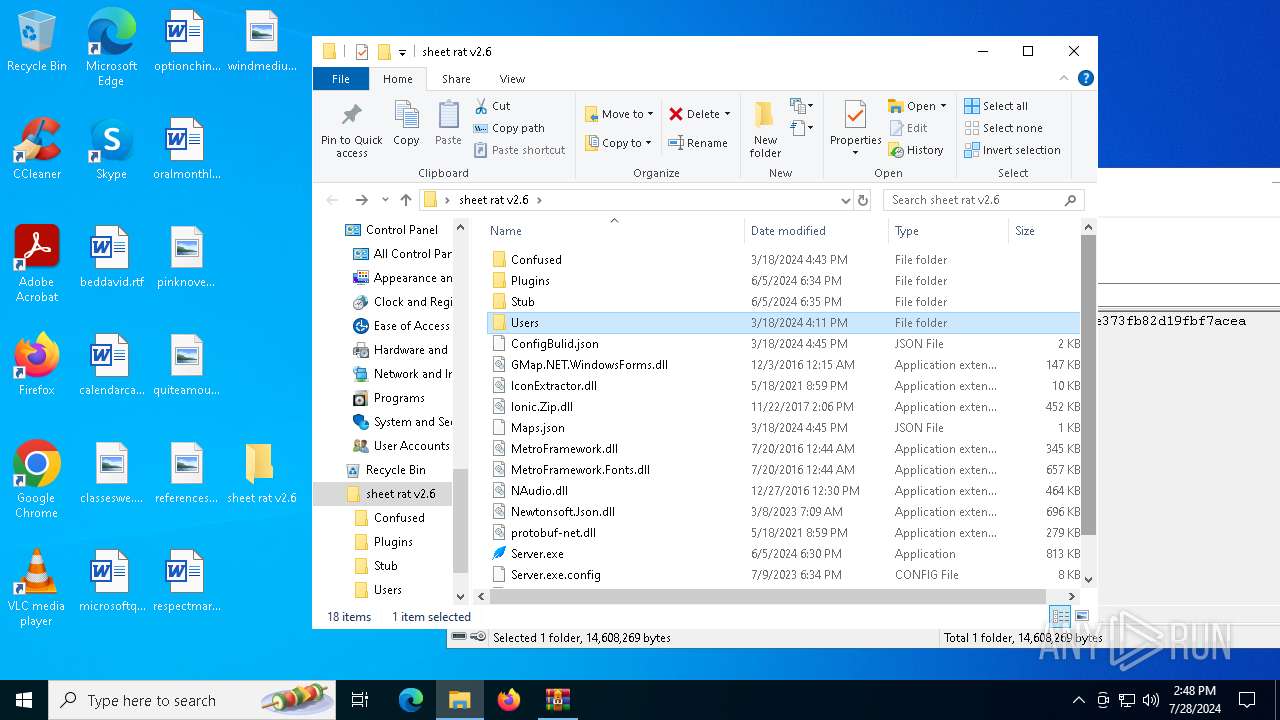
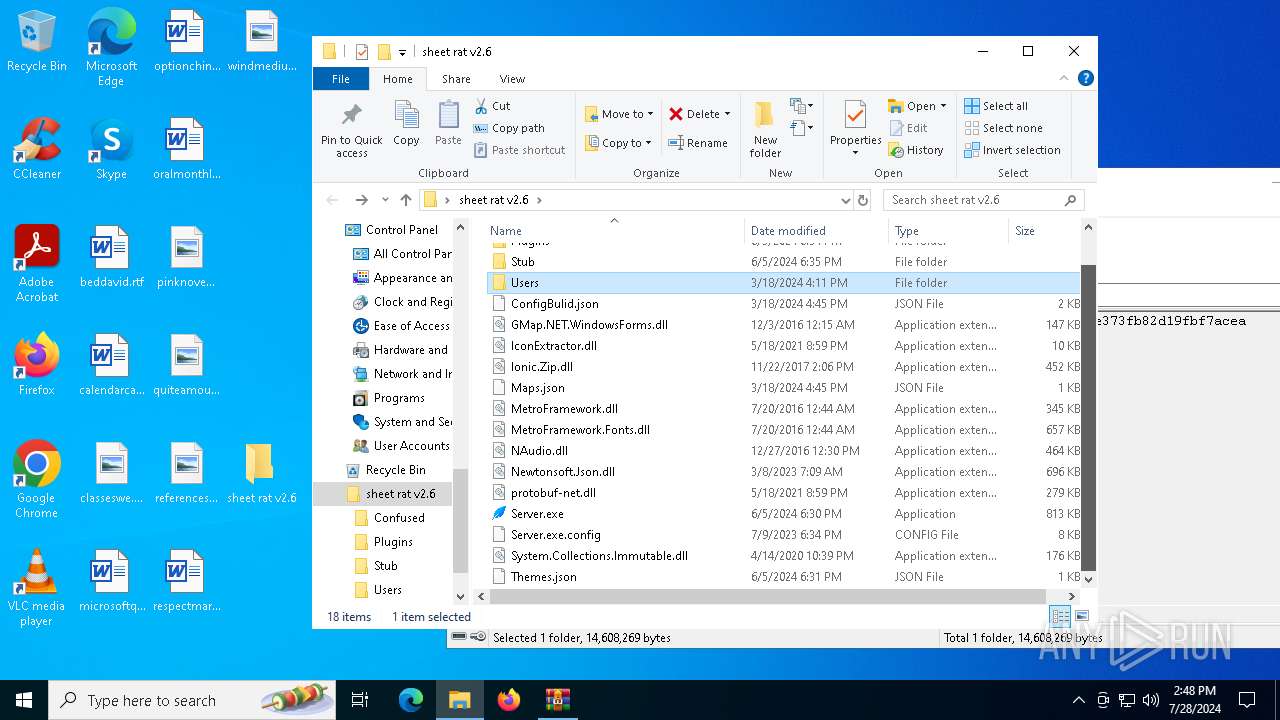
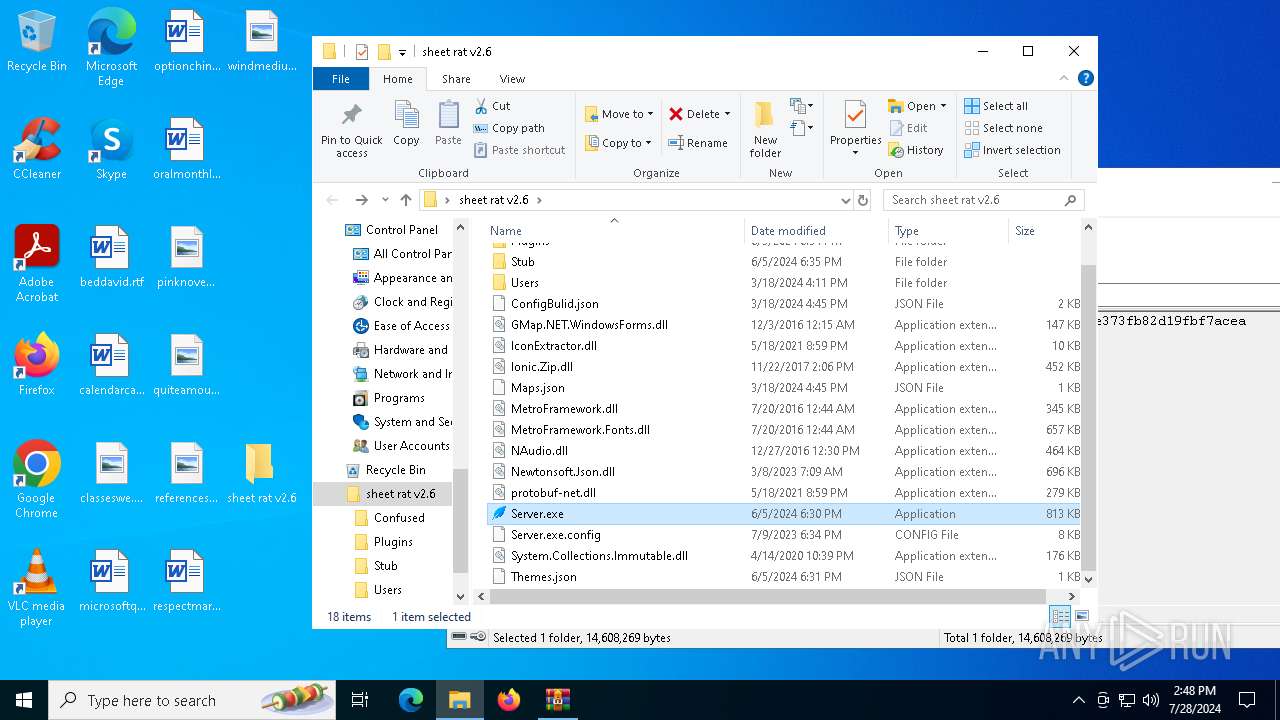
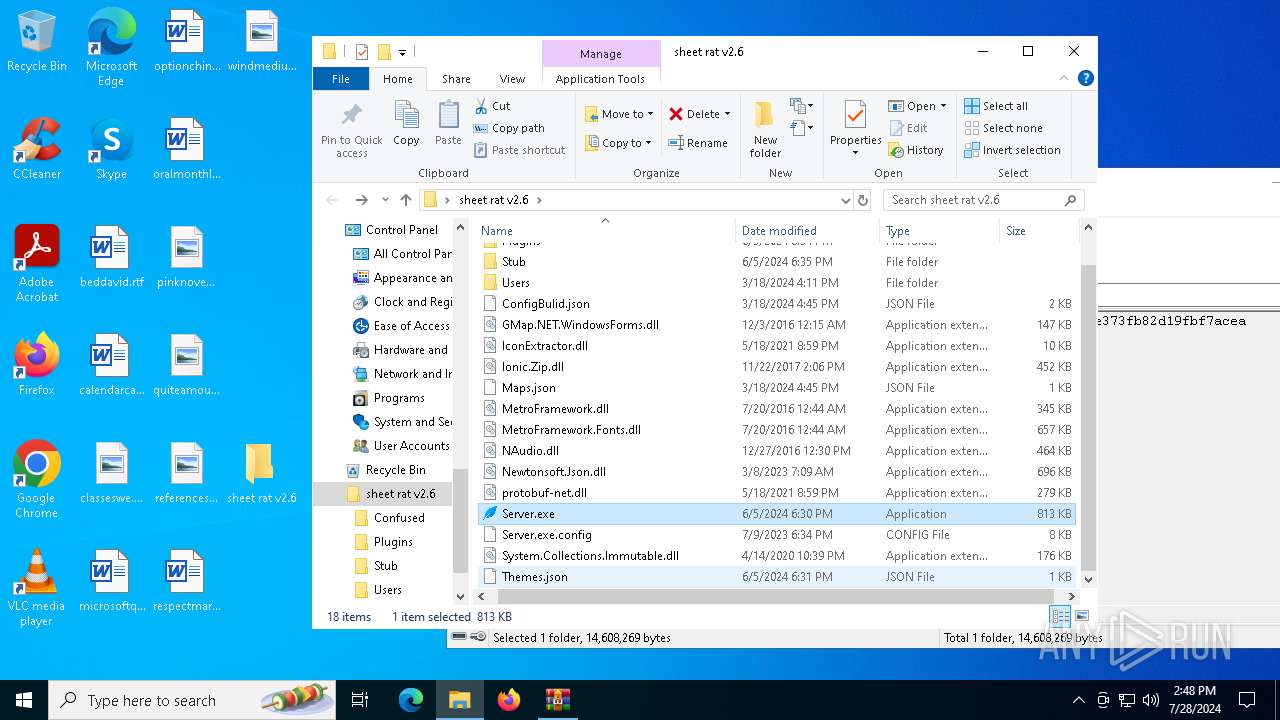
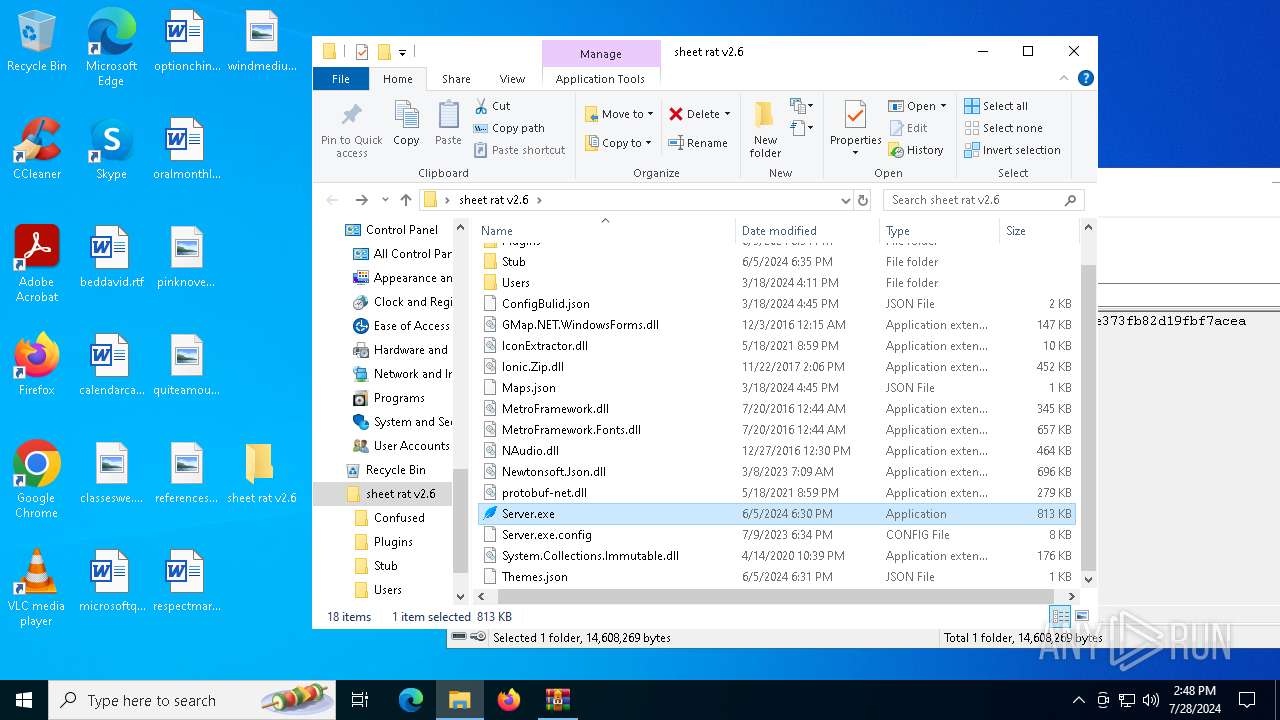
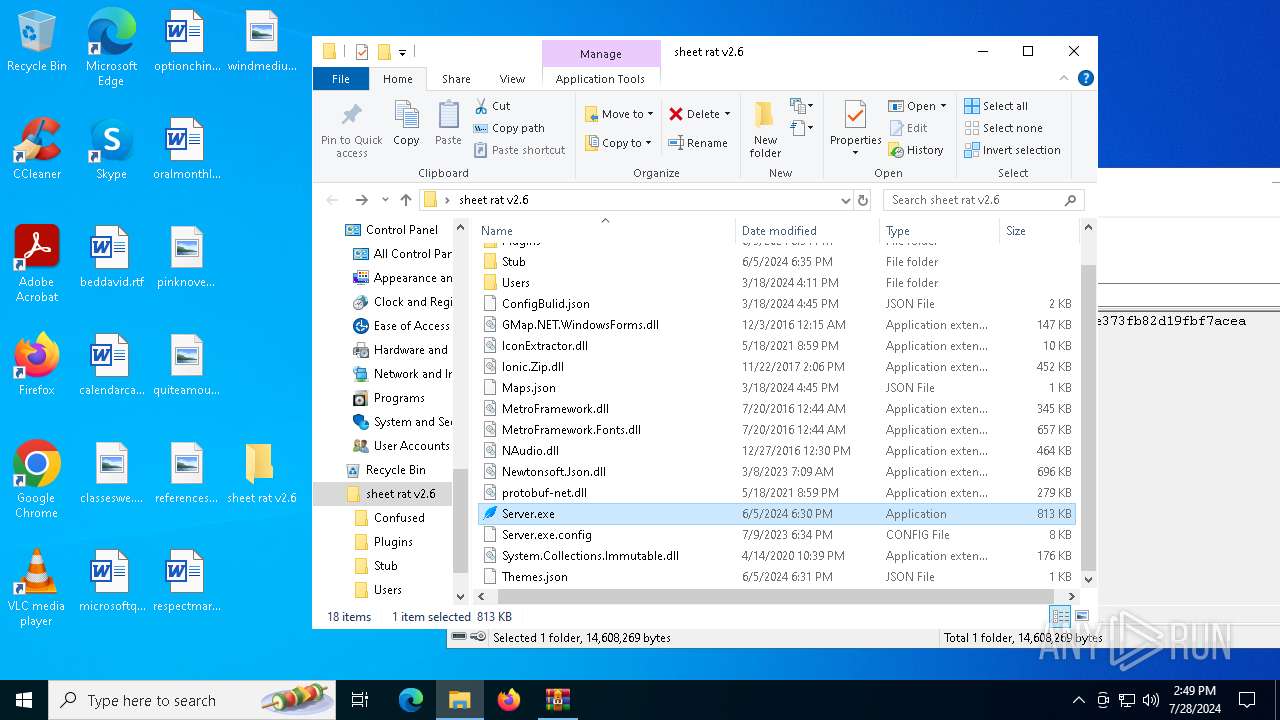
| 1108 | "C:\Users\admin\Desktop\sheet rat v2.6\Server.exe" | C:\Users\admin\Desktop\sheet rat v2.6\Server.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Sheet Rat Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\AppData\Local\Temp\Server.exe" | C:\Users\admin\AppData\Local\Temp\Server.exe | Server.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Sheet Rat Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | — | Server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 530 Version: 10.0.19041.4355 Modules
| |||||||||||||||
| 4356 | "C:\Users\admin\Desktop\sheet rat v2.6\Server.exe" | C:\Users\admin\Desktop\sheet rat v2.6\Server.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Sheet Rat Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4520 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1164 -s 860 | C:\Windows\SysWOW64\WerFault.exe | Server.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
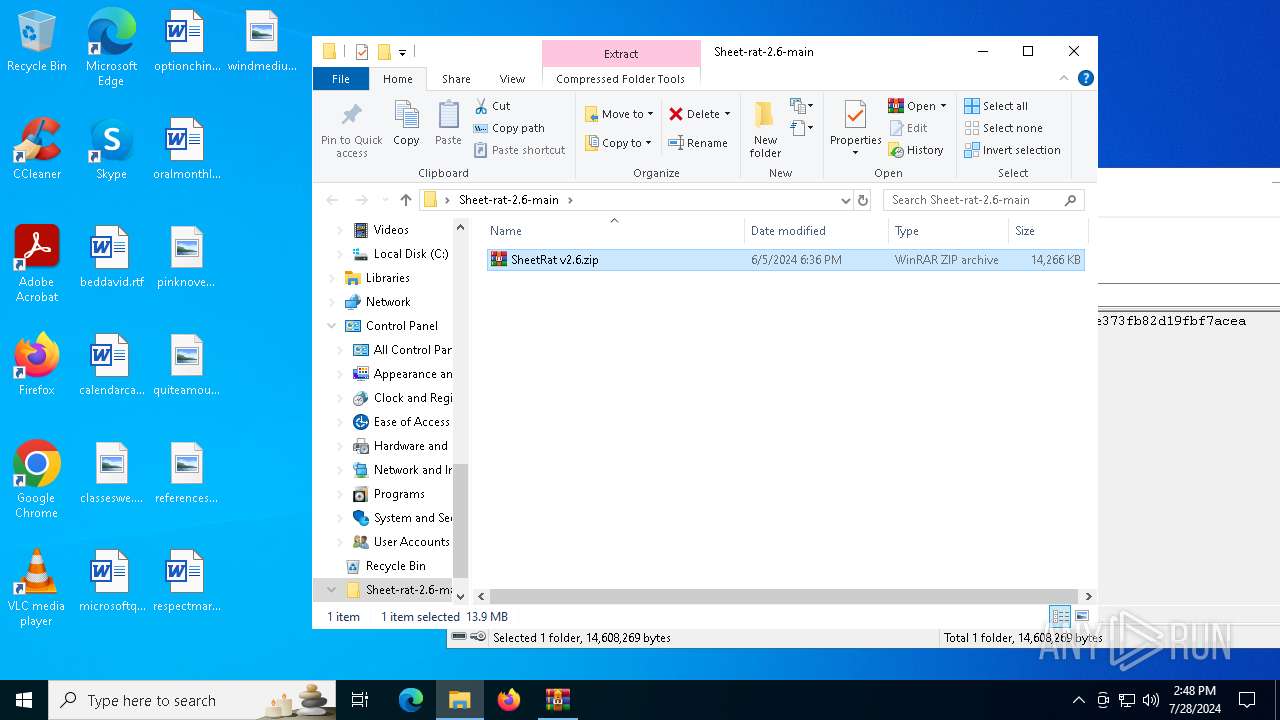
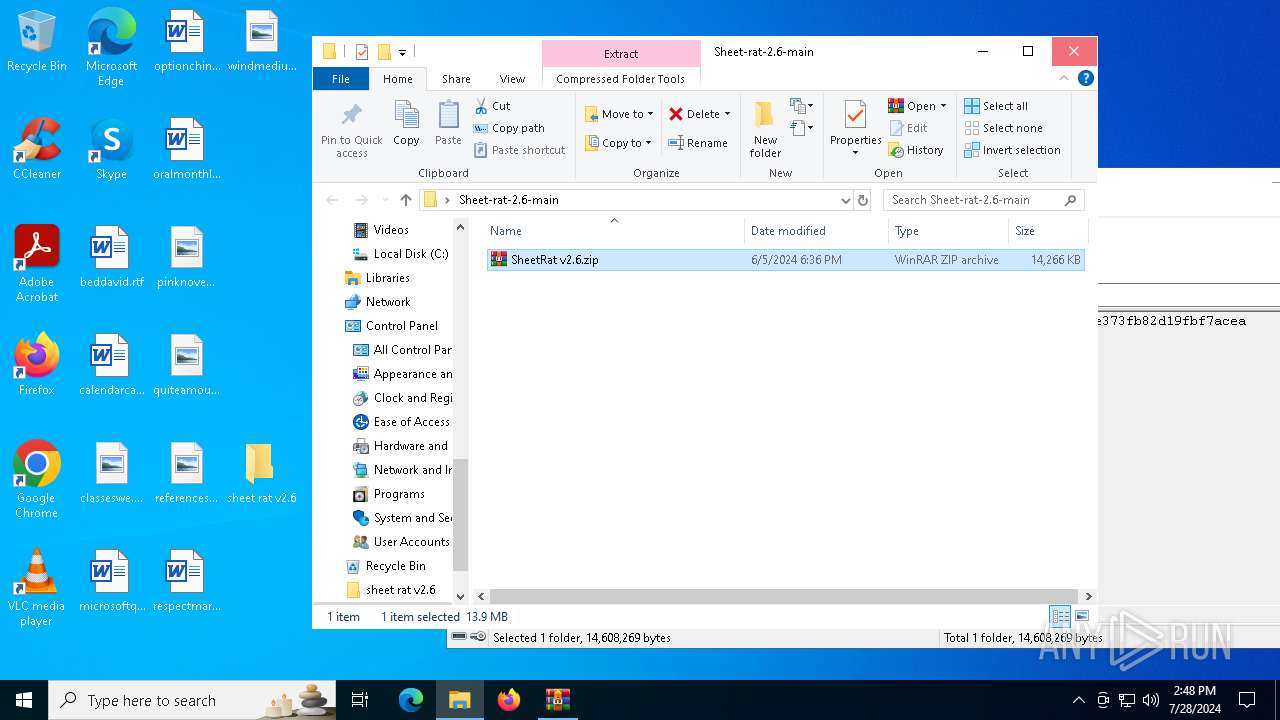
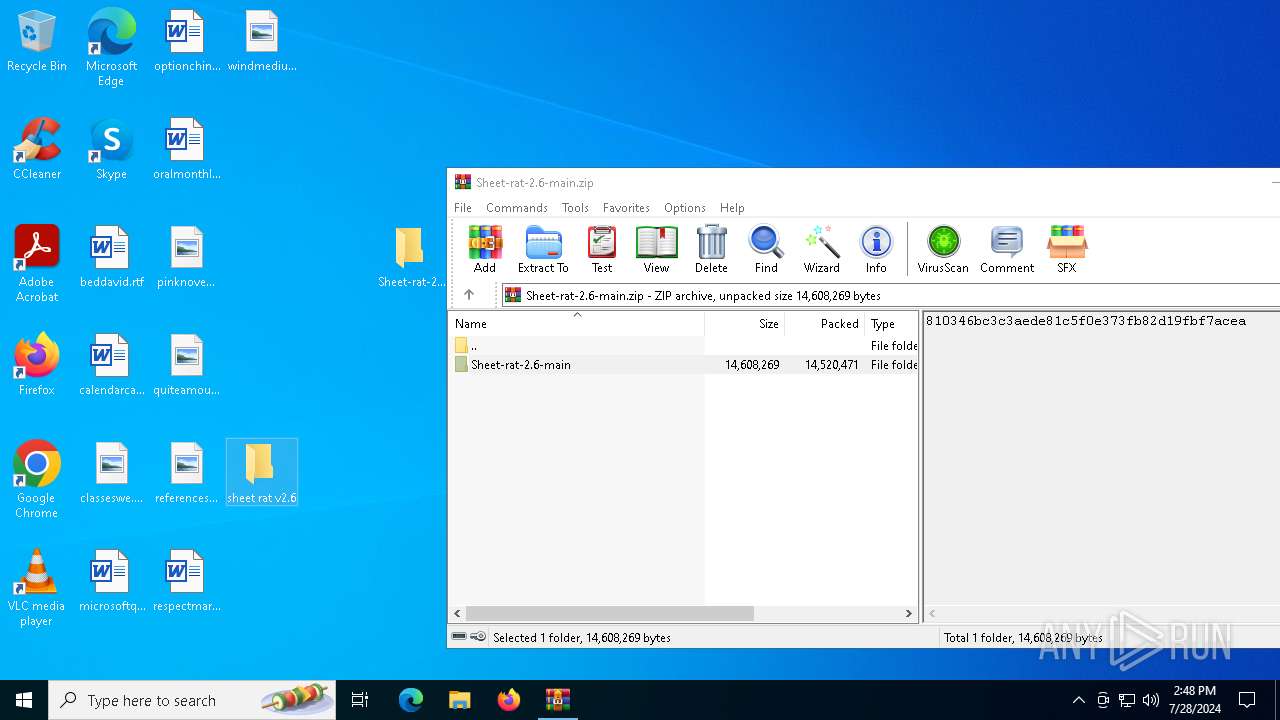
| 5532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Sheet-rat-2.6-main\SheetRat v2.6.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5740 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5848 | "C:\Users\admin\AppData\Local\Temp\Server.exe" | C:\Users\admin\AppData\Local\Temp\Server.exe | Server.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Sheet Rat Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6140 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 016
Read events
26 958
Write events
57
Delete events
1
Modification events
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sheet-rat-2.6-main.zip | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
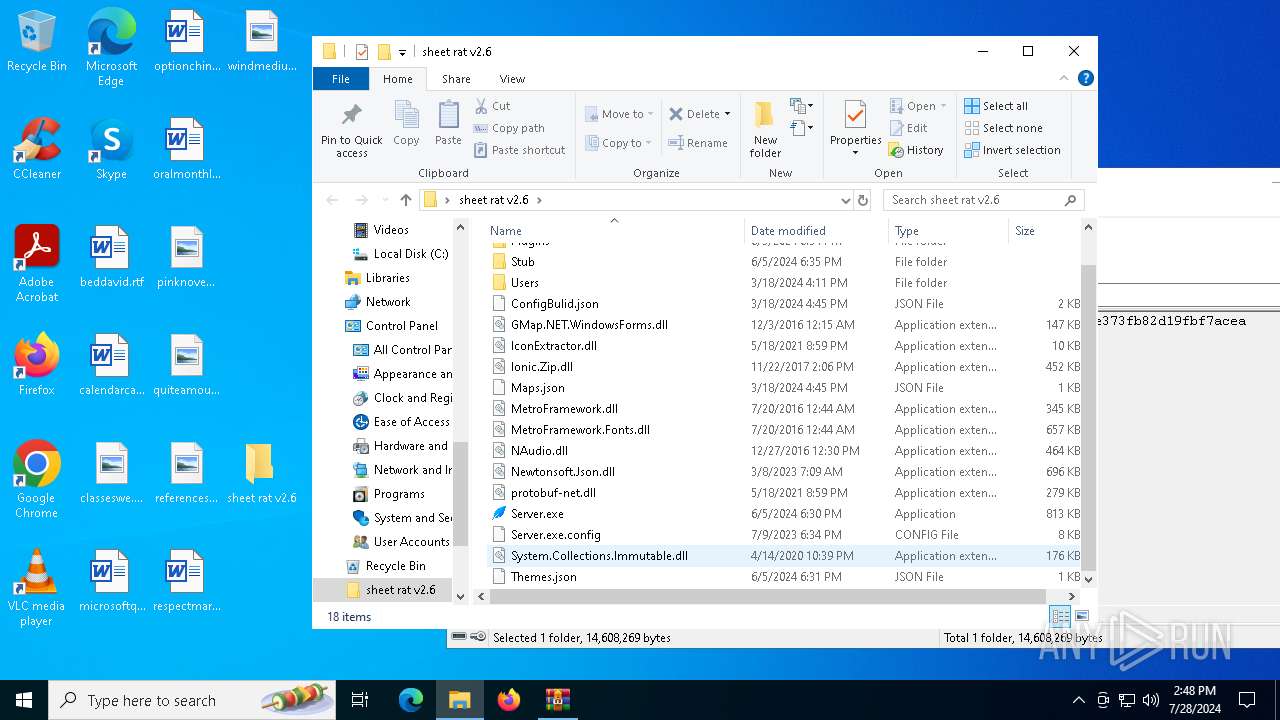
Executable files
36
Suspicious files
6
Text files
7
Unknown types
1
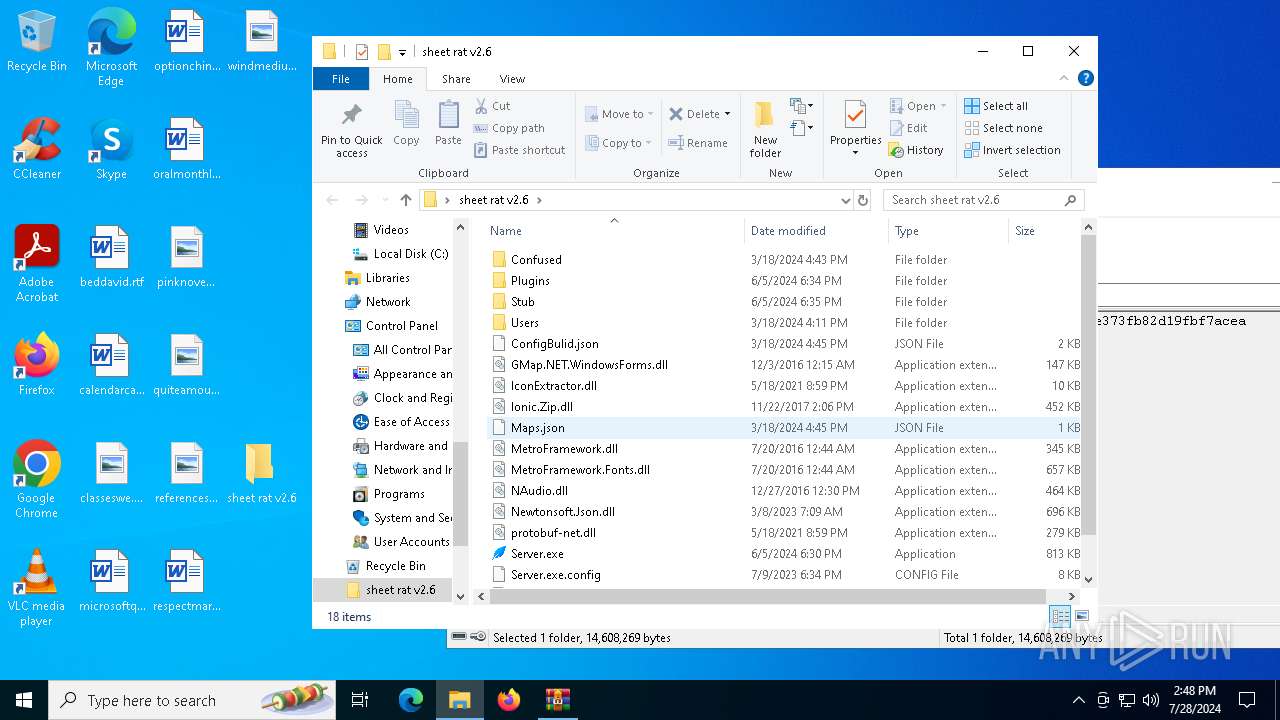
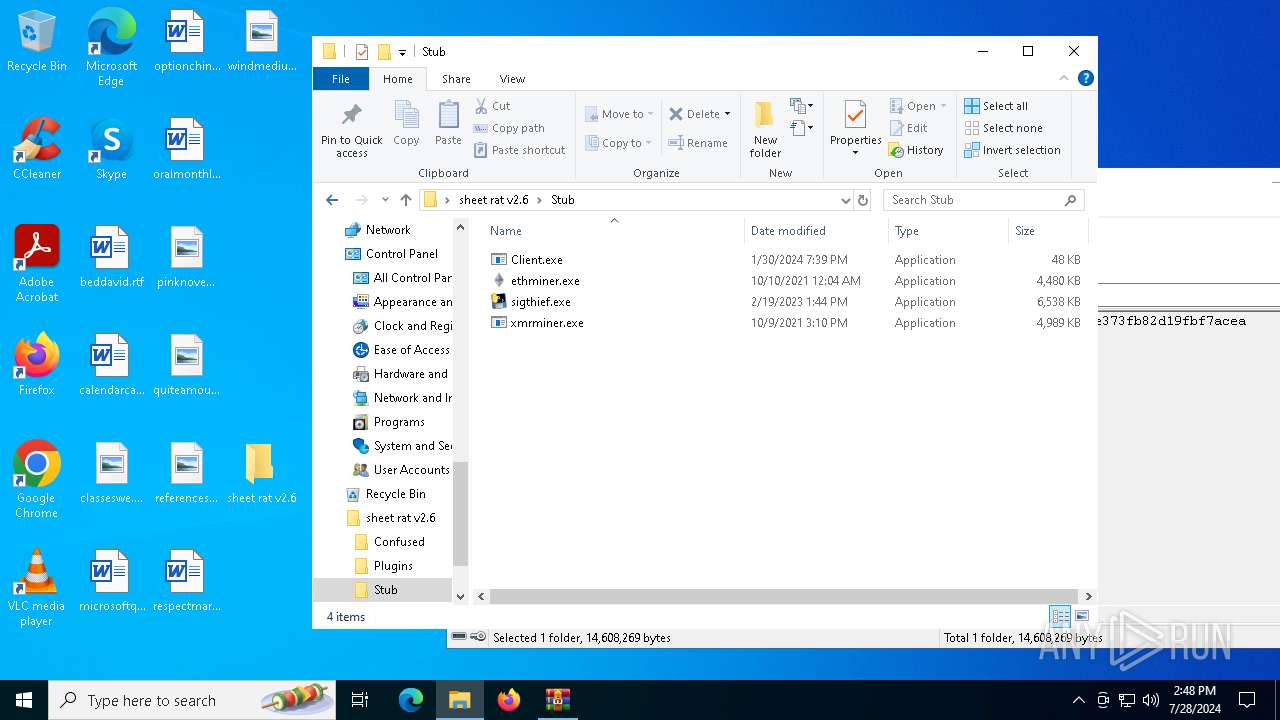
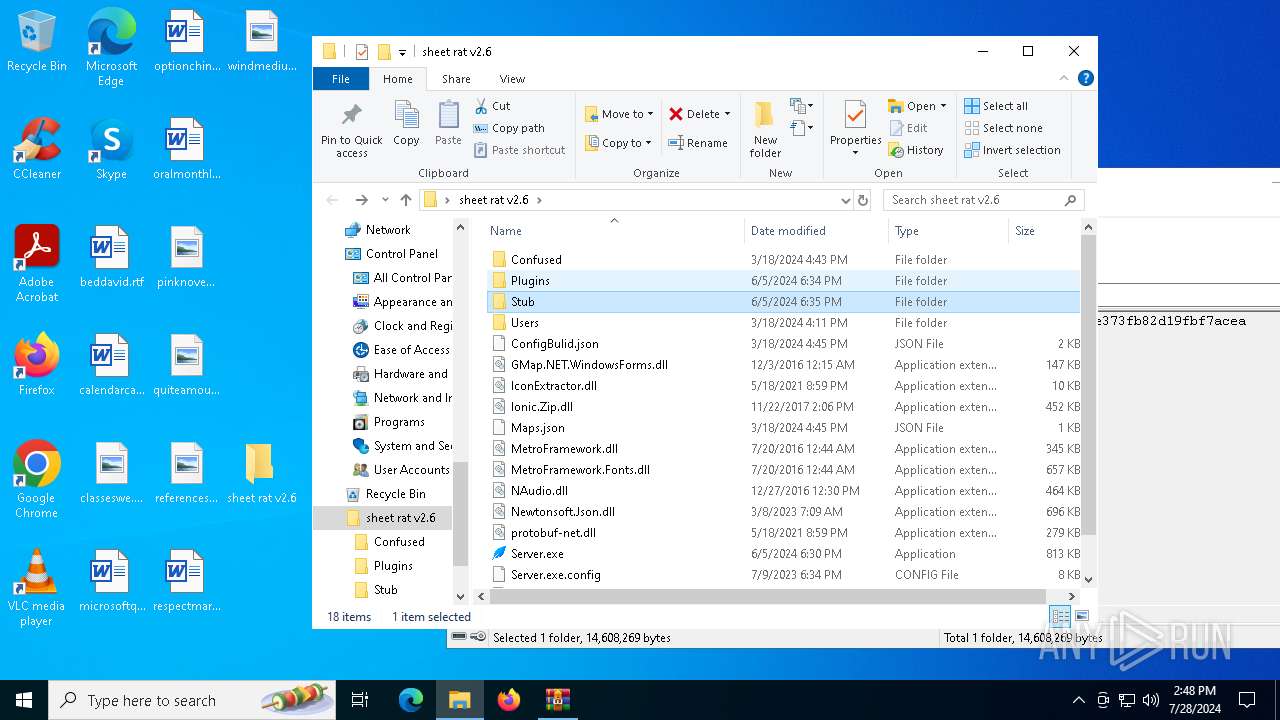
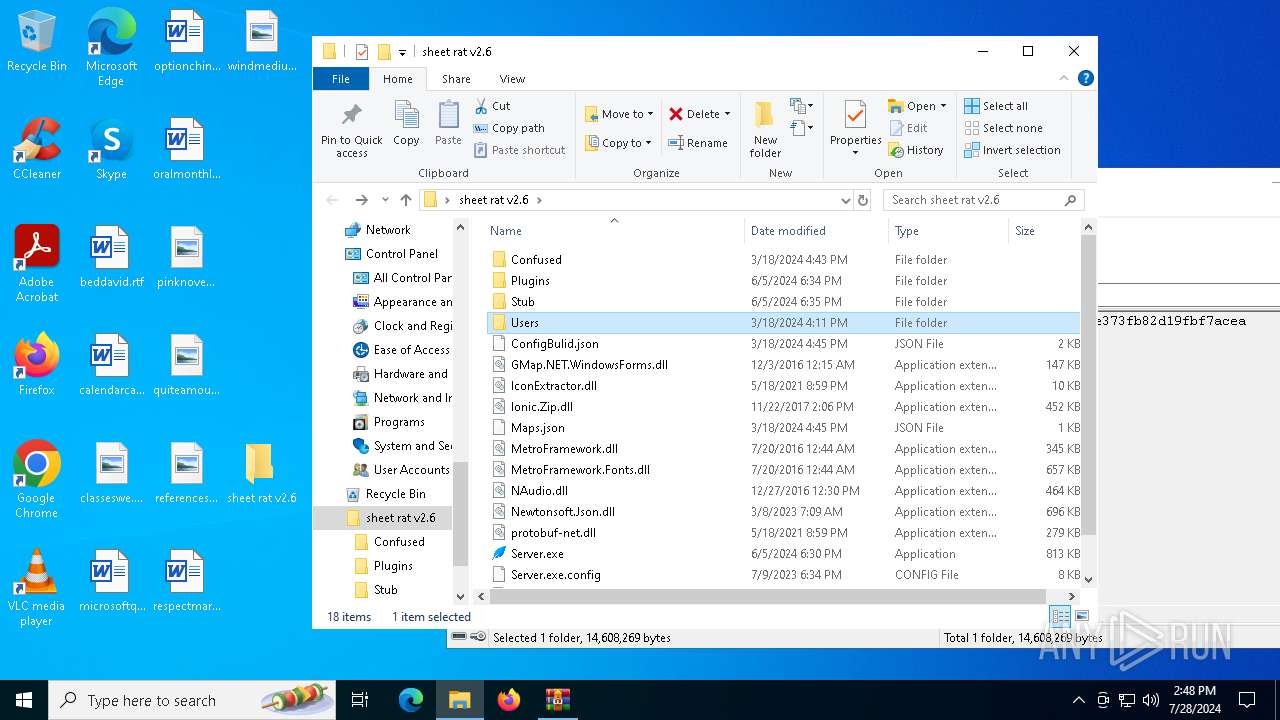
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
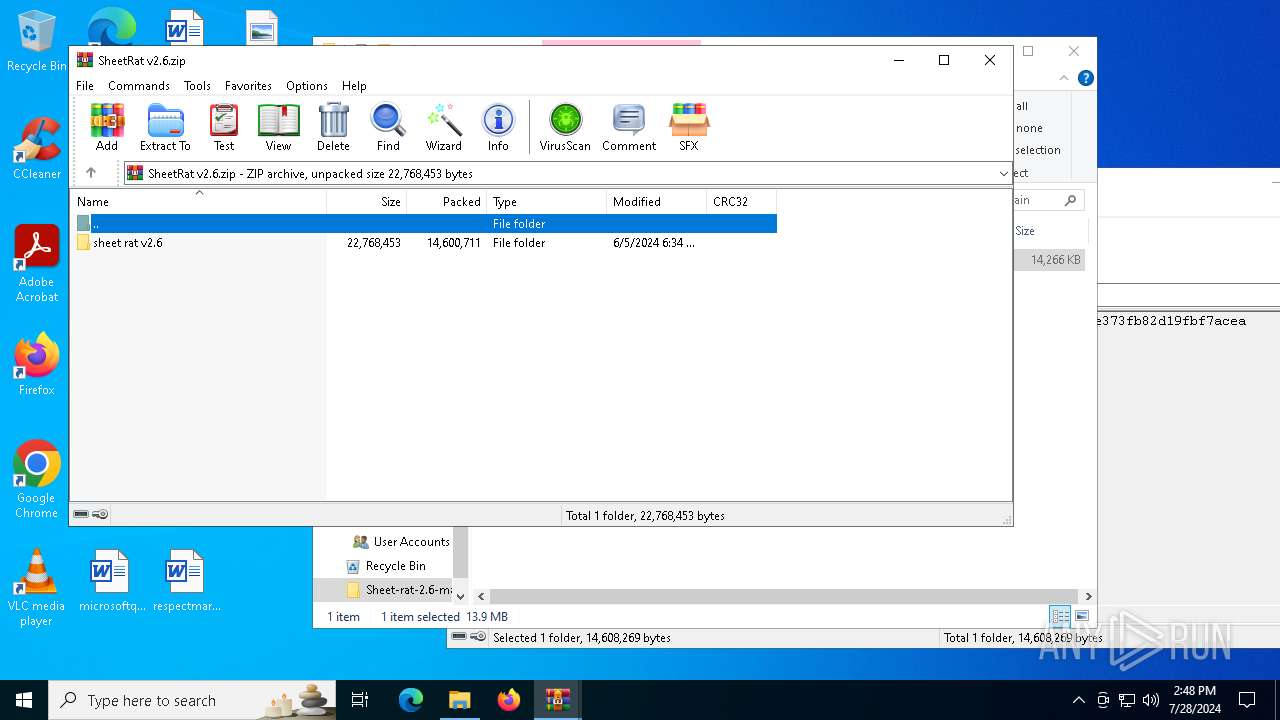
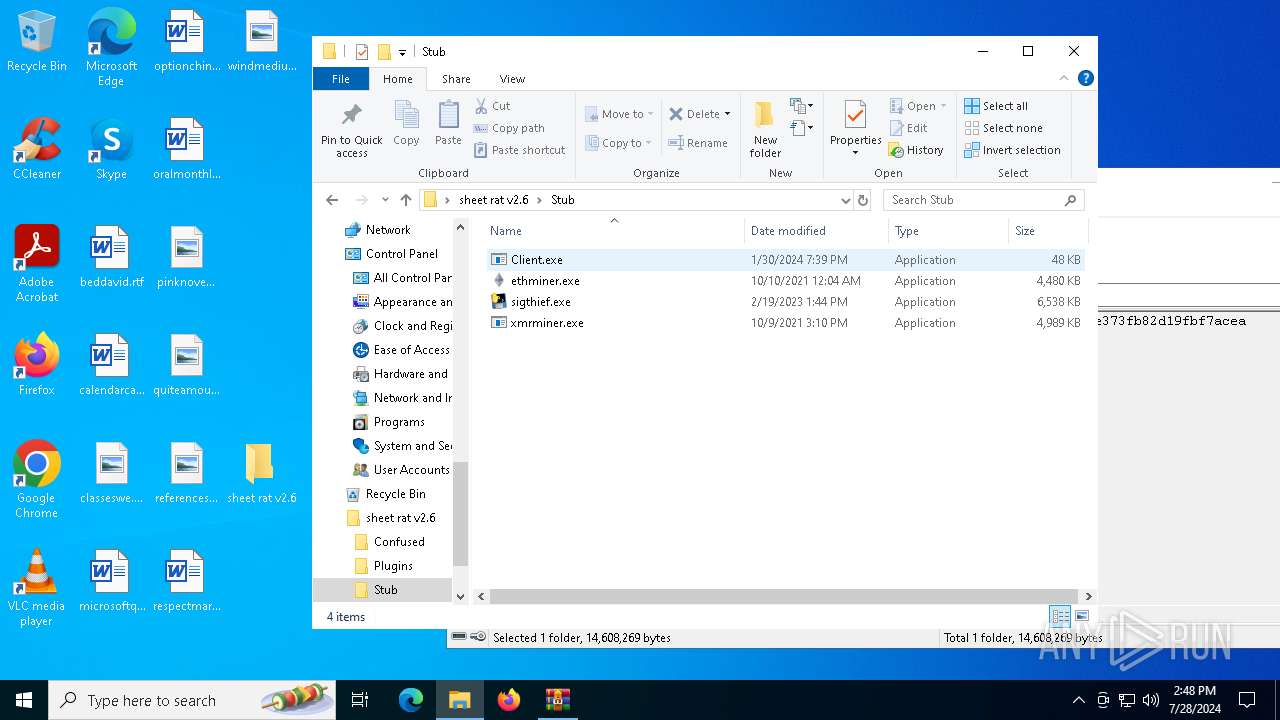
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\IconExtractor.dll | executable | |
MD5:640D8FFA779C6DD5252A262E440C66C0 | SHA256:440912D85D2F98BB4F508AB82847067C18E1E15BE0D8ECDCFF0CC19327527FC2 | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\Plugins\MinerXmr.dll | executable | |
MD5:99FA25800B9FAE285578F10F94028664 | SHA256:5C1D6717A5ADEDE293CA0CFBAEFFC805ADD2EB1086D50C9B3465EEA35391A395 | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\Plugins\Map.dll | executable | |
MD5:9A855FEF0FCBF9E52FC947DD50CC8C76 | SHA256:A43C0DFA281A5011FC24BDCB377AFCC6BFE6F0280A5452E993F8ECCBA695601D | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\GMap.NET.WindowsForms.dll | executable | |
MD5:32A8742009FFDFD68B46FE8FD4794386 | SHA256:741E1A8F05863856A25D101BD35BF97CBA0B637F0C04ECB432C1D85A78EF1365 | |||
| 6420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6420.38680\Sheet-rat-2.6-main\SheetRat v2.6.zip | compressed | |
MD5:9621F795789FB2AA71D5053C28E6E3BA | SHA256:C07BA7F9CDC382BEF10786321D80F1636A59158466D2FC0C25F2489801F7201E | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\NAudio.dll | executable | |
MD5:2E68AEB46E26A29FFE74CF97B94CBAF0 | SHA256:8E347ABC9301D67DD7493A0FBBE5CC1F912900C204A84220CC8CDF0E0B8DF0DE | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\MetroFramework.dll | executable | |
MD5:34EA7F7D66563F724318E322FF08F4DB | SHA256:C2C12D31B4844E29DE31594FC9632A372A553631DE0A0A04C8AF91668E37CF49 | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\Maps.json | ini | |
MD5:D751713988987E9331980363E24189CE | SHA256:4F53CDA18C2BAA0C0354BB5F9A3ECBE5ED12AB4D8E11BA873C2F11161202B945 | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 5532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5532.39370\sheet rat v2.6\Plugins\MinerEtc.dll | executable | |
MD5:9810D96BFD7236070008BAF843C9E3F9 | SHA256:5AD2970FC3B56FA9C9DB1DD1D2A309398B216CCE3DD750B6B562E13A7C198311 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6872 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2472 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 2.23.209.154:443 | www.bing.com | Akamai International B.V. | GB | unknown |
1736 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4648 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1044 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |