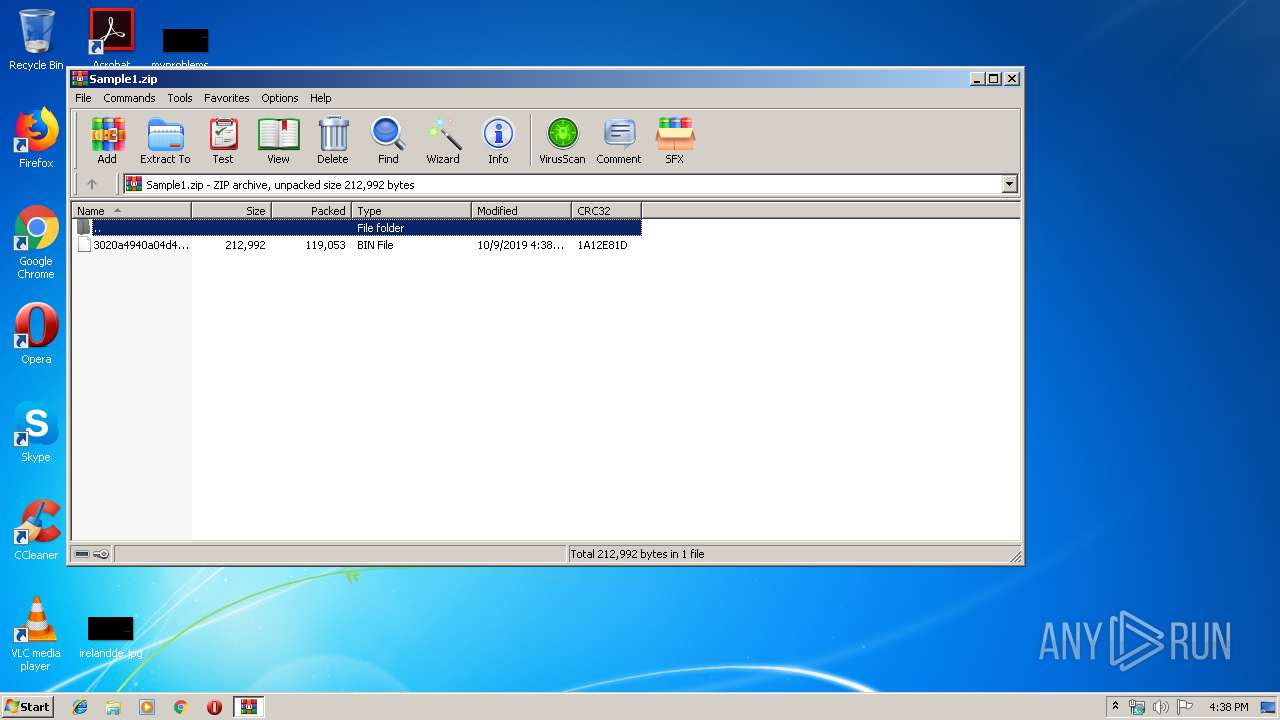
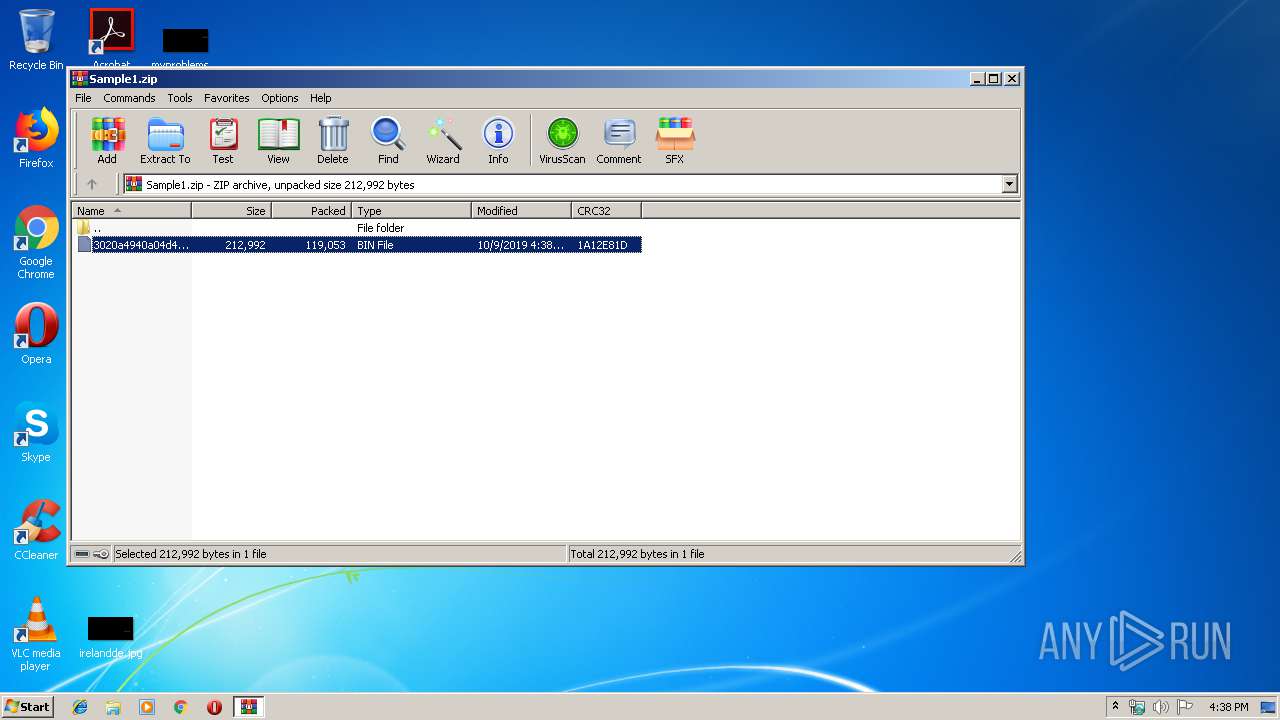
| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/43c98cf6-a3b0-4360-a7b9-b292312f6689 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 15:38:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
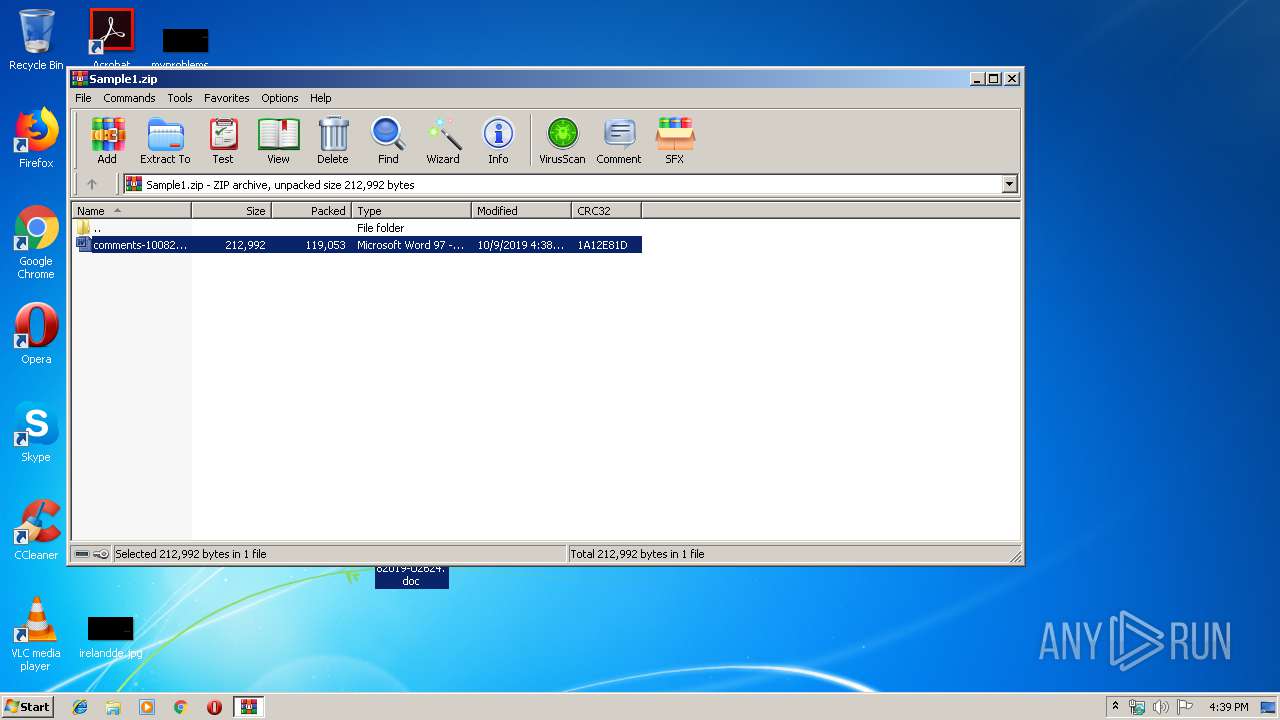
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 20A5E2D962B42A979F2A42895A69B9D9 |
| SHA1: | F8DA10926492085EAD4F82839B7BE5C41C0CC1F0 |
| SHA256: | 29E2F789EB4D73CDD6B2C6DE509A86A9C3A75AD2AEDBC907E671218C8F6F93FA |
| SSDEEP: | 3072:F6D5fF2Fwsn00wm0w9kcrtnrjq8WG2+bQ6G/F:EtF2FwvmFqcpeGg7N |
MALICIOUS
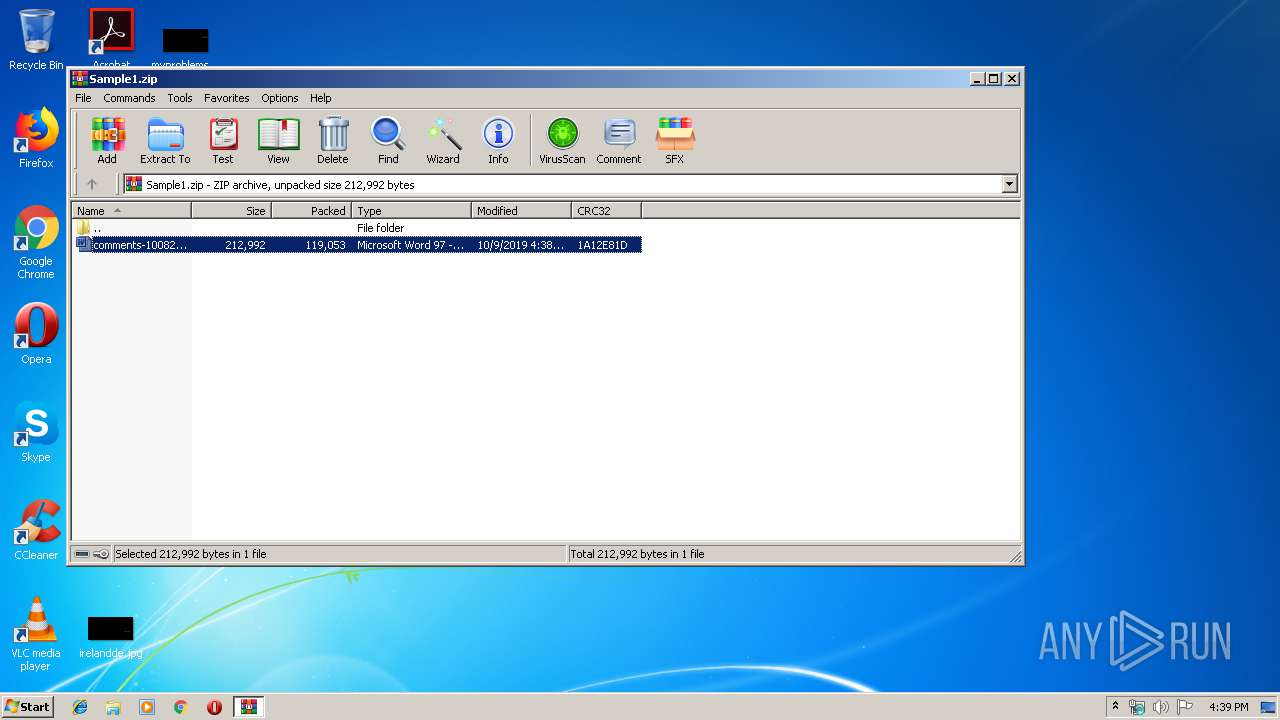
Drops known malicious document
- WinRAR.exe (PID: 2924)
Application was dropped or rewritten from another process
- 285.exe (PID: 1640)
- 285.exe (PID: 2712)
- msptermsizes.exe (PID: 272)
- msptermsizes.exe (PID: 2752)
- Sh1S6R5xkOzY.exe (PID: 1560)
- sh1s6r5xkozy.exe (PID: 2844)
- msptermsizes.exe (PID: 2776)
- msptermsizes.exe (PID: 2744)
Emotet process was detected
- 285.exe (PID: 1640)
- sh1s6r5xkozy.exe (PID: 2844)
EMOTET was detected
- msptermsizes.exe (PID: 2752)
Connects to CnC server
- msptermsizes.exe (PID: 2752)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 2752)
SUSPICIOUS
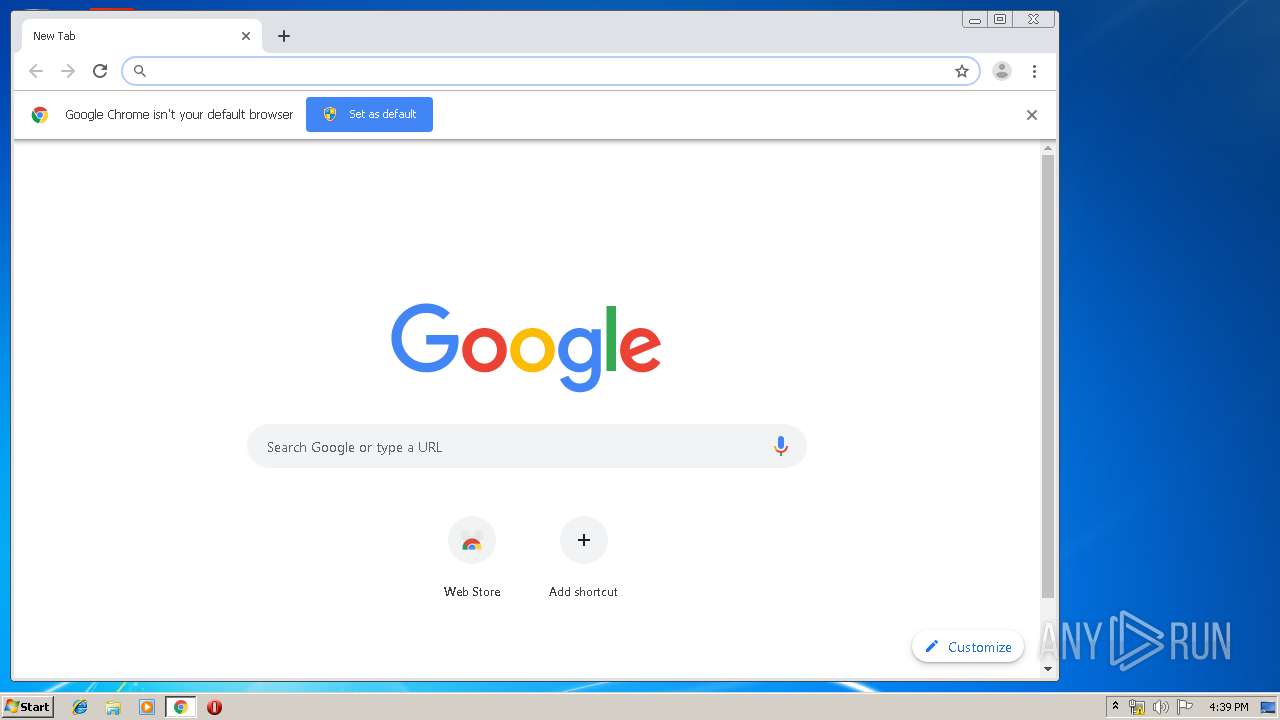
Modifies files in Chrome extension folder
- chrome.exe (PID: 3352)
Executed via WMI
- powershell.exe (PID: 2576)
PowerShell script executed
- powershell.exe (PID: 2576)
Creates files in the user directory
- powershell.exe (PID: 2576)
Executable content was dropped or overwritten
- 285.exe (PID: 1640)
- powershell.exe (PID: 2576)
- msptermsizes.exe (PID: 2752)
- sh1s6r5xkozy.exe (PID: 2844)
Starts itself from another location
- 285.exe (PID: 1640)
- sh1s6r5xkozy.exe (PID: 2844)
- msptermsizes.exe (PID: 2752)
INFO
Reads the hosts file
- chrome.exe (PID: 3352)
- chrome.exe (PID: 404)
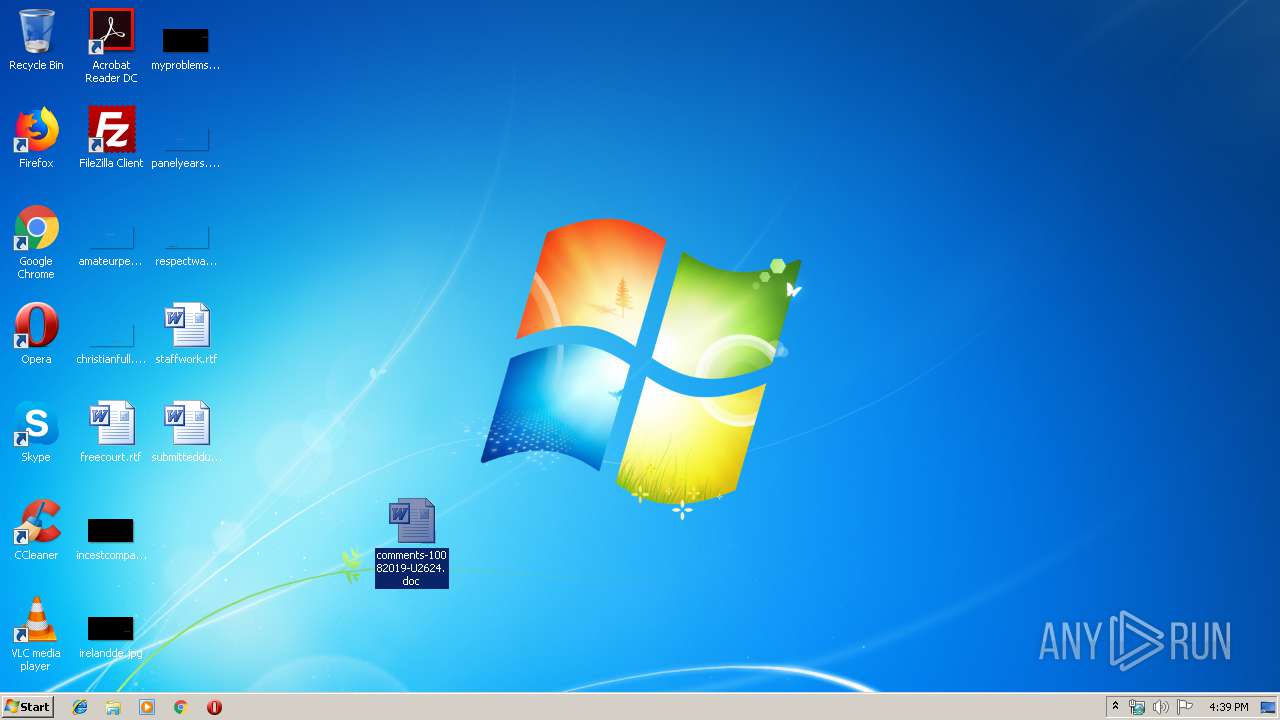
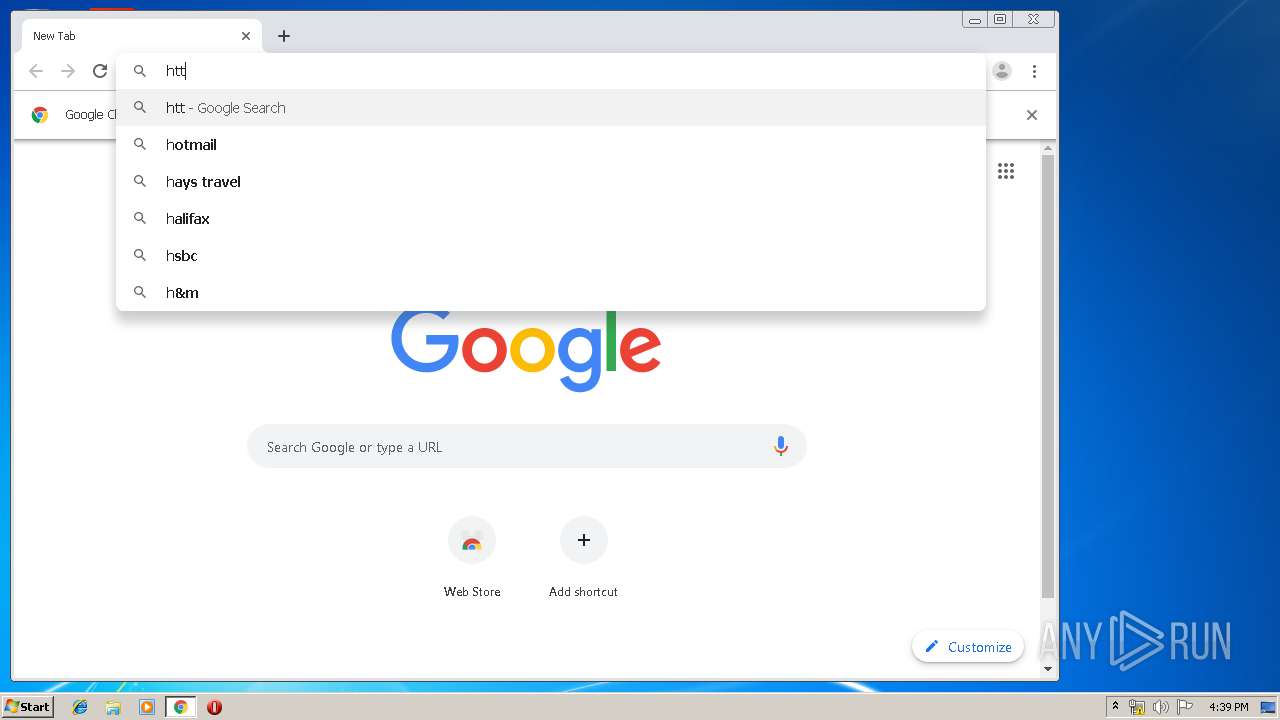
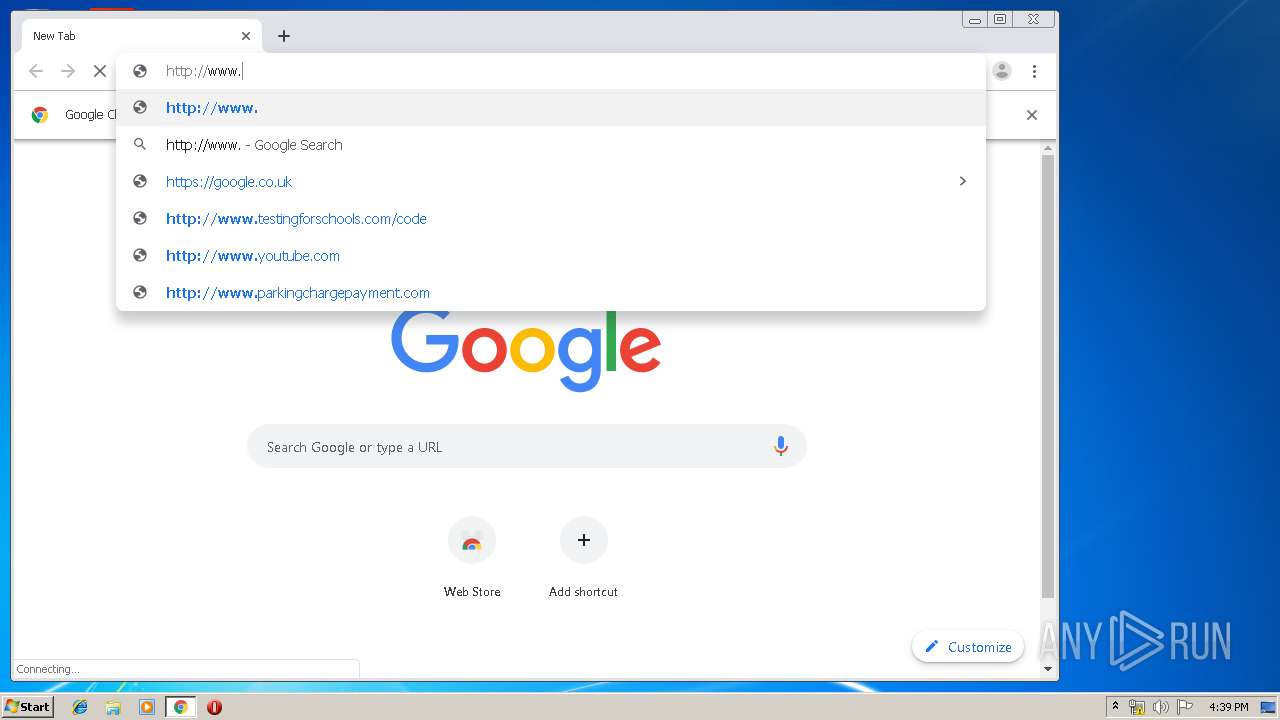
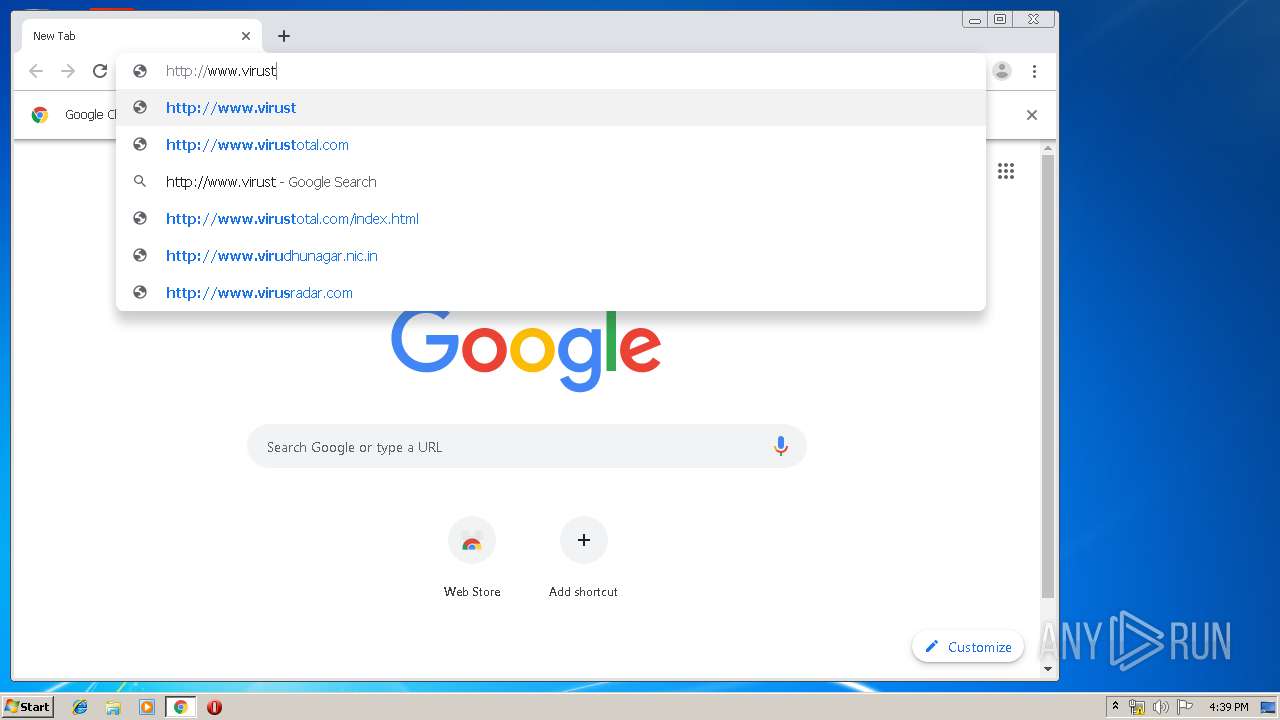
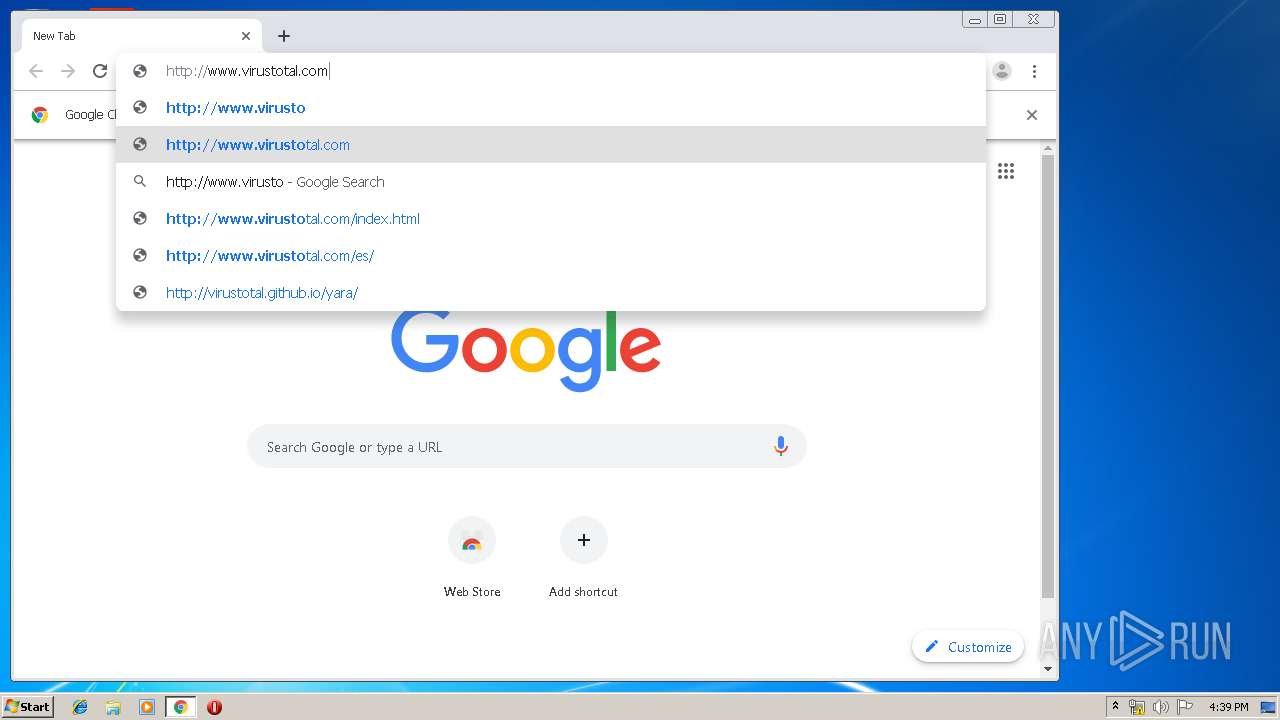
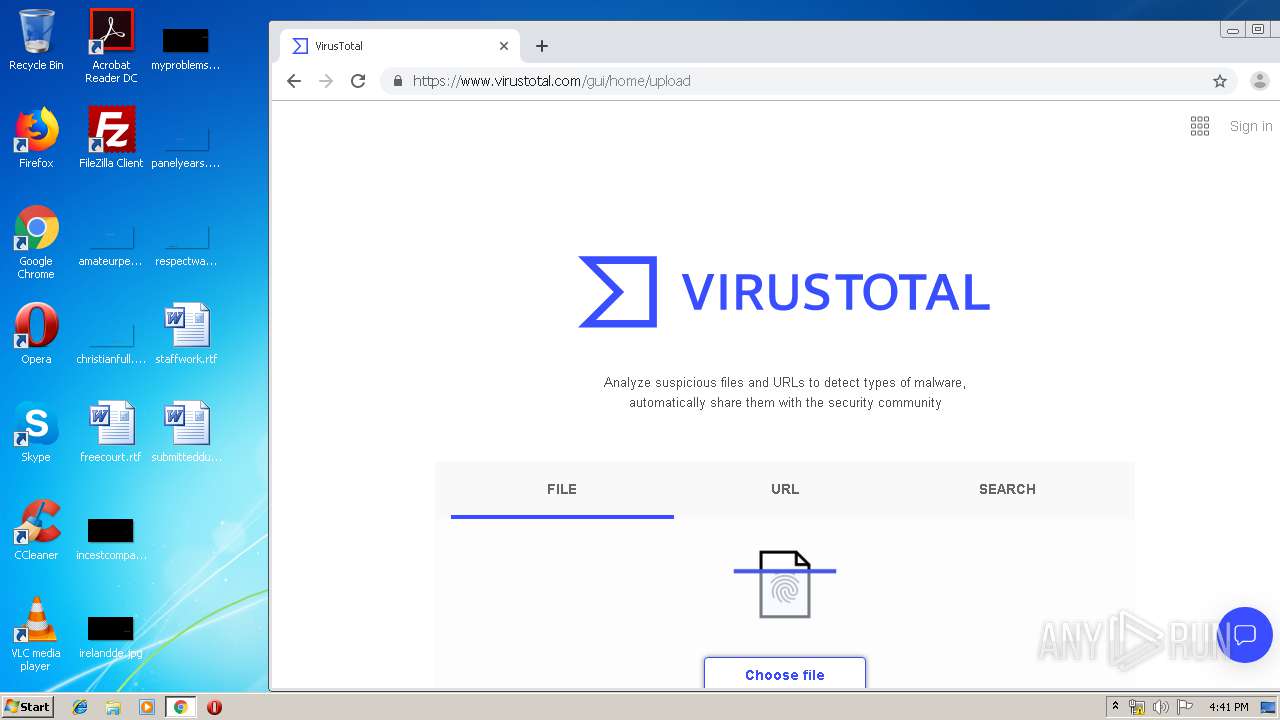
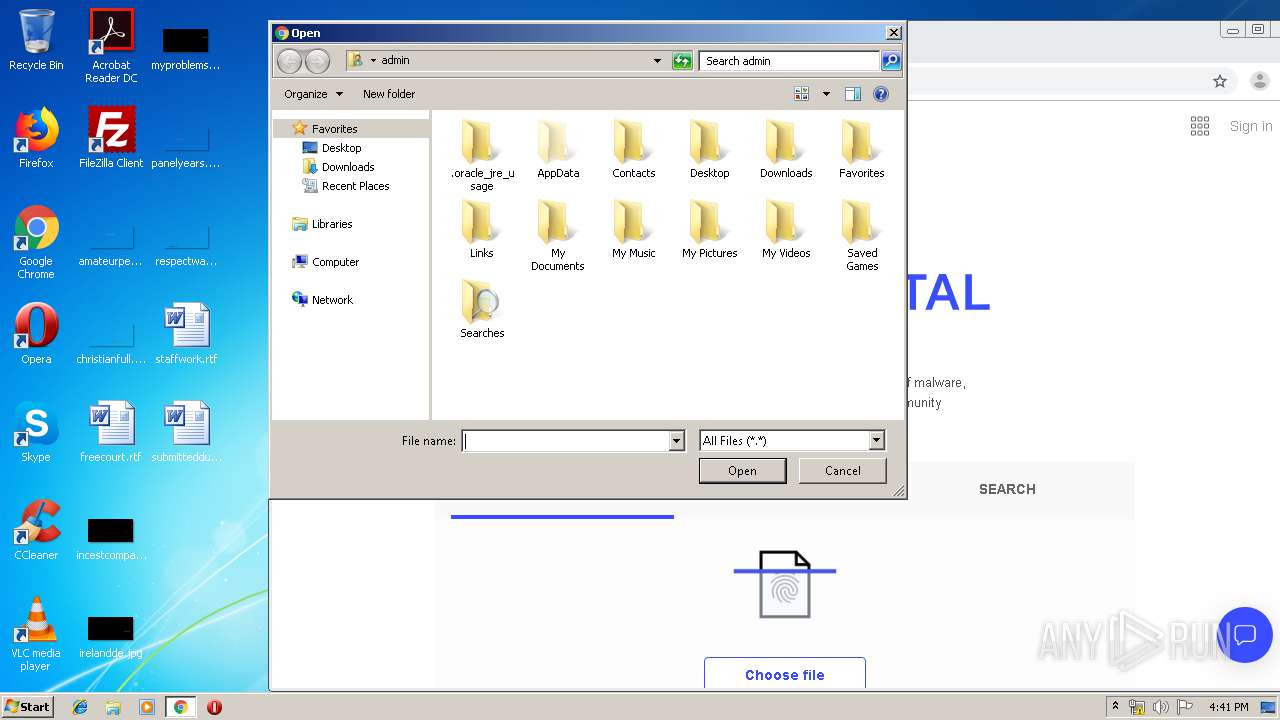
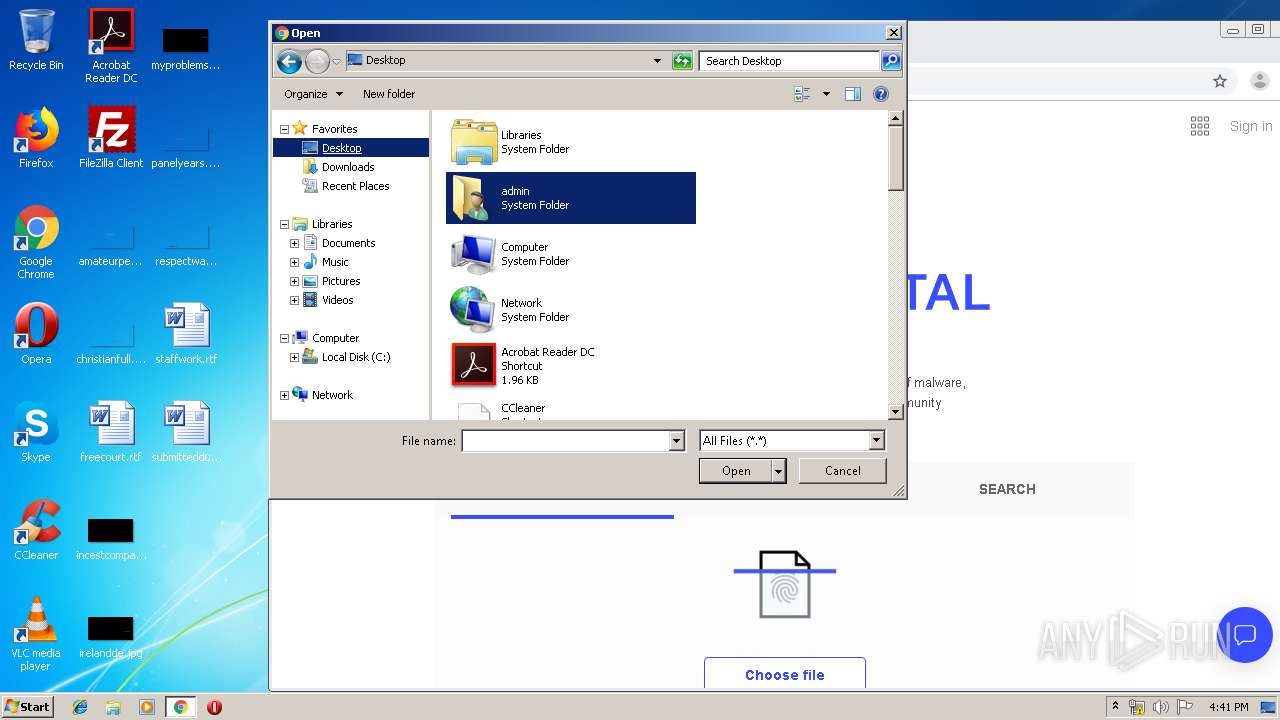
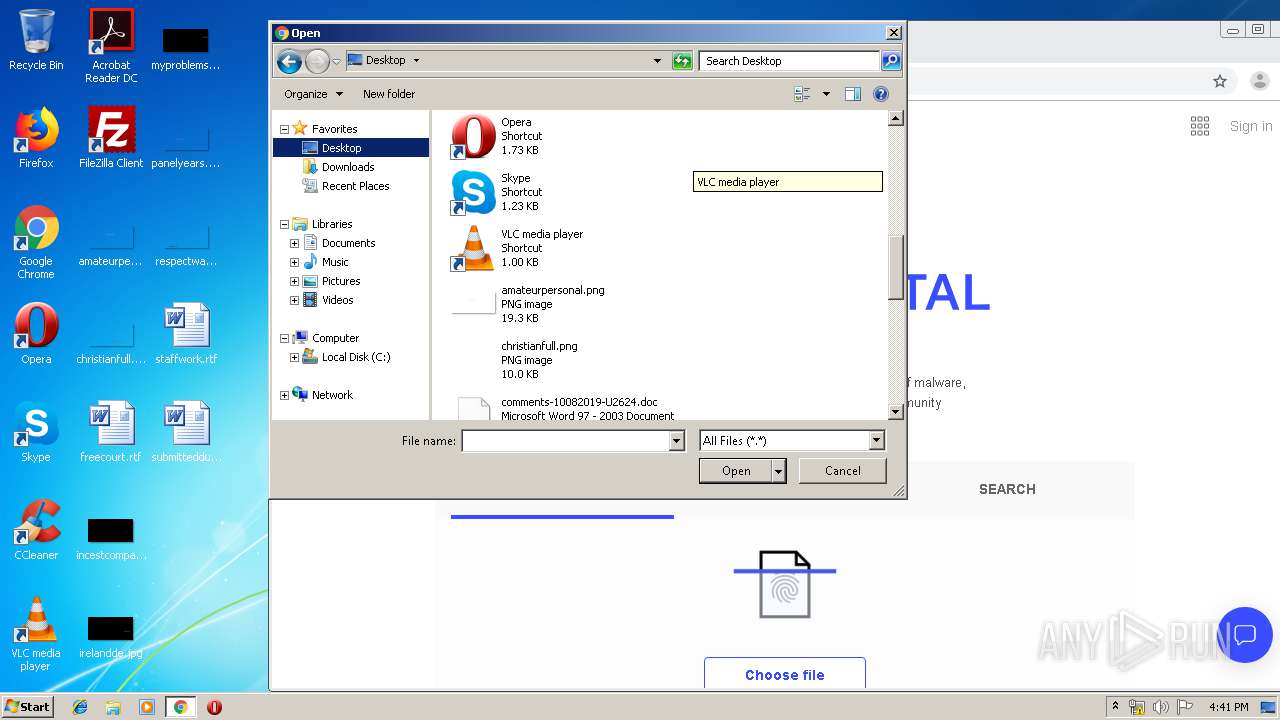
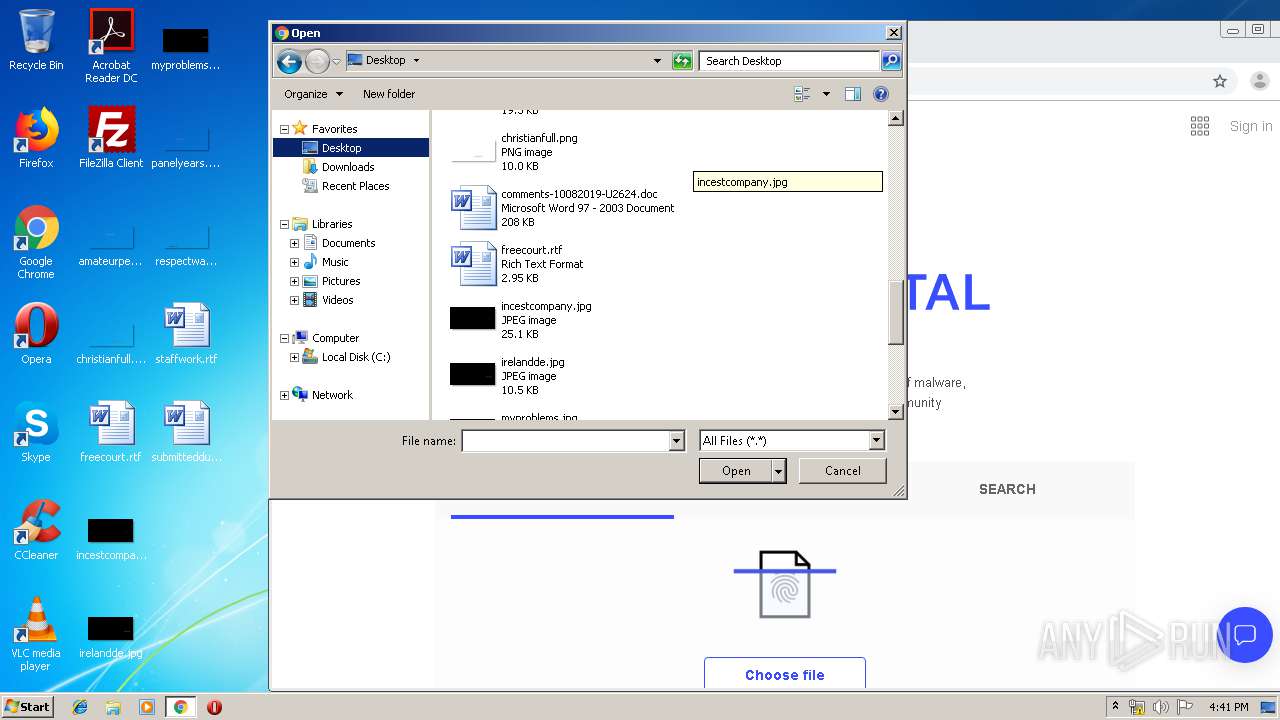
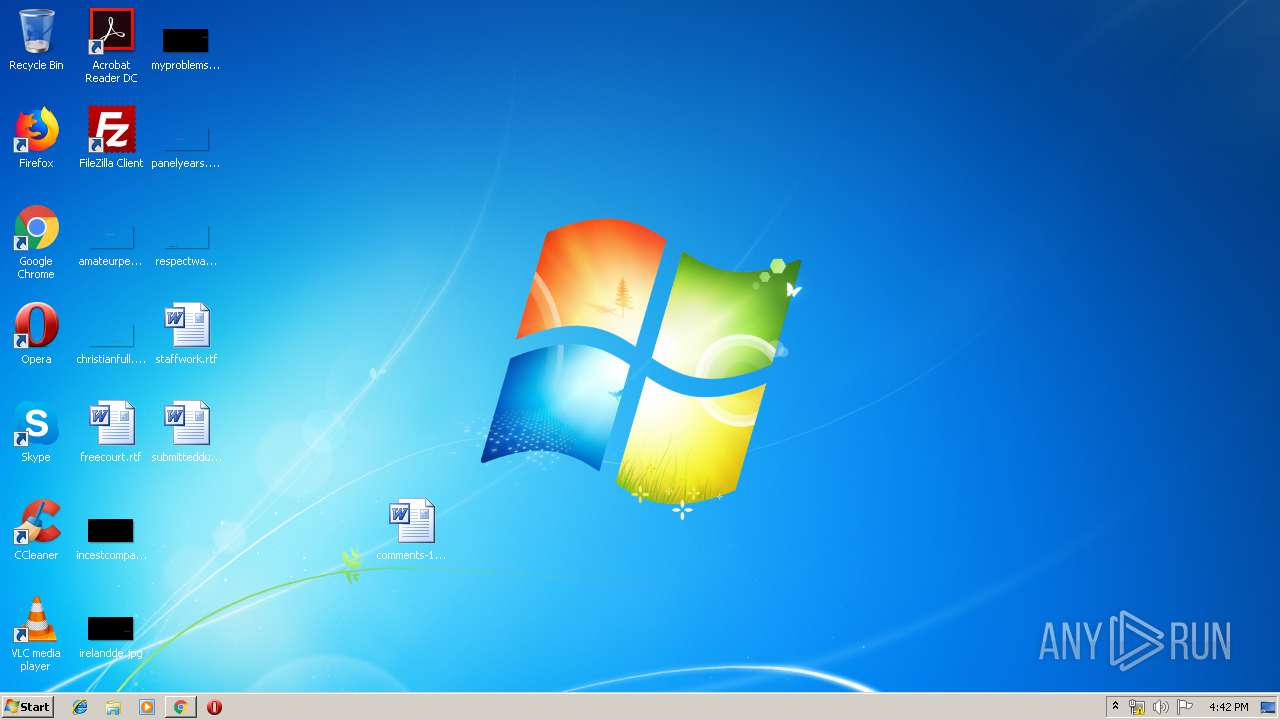
Manual execution by user
- chrome.exe (PID: 3352)
- WINWORD.EXE (PID: 2188)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3352)
Creates files in the user directory
- WINWORD.EXE (PID: 2188)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2188)
Application launched itself
- chrome.exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 15:38:01 |
| ZipCRC: | 0x1a12e81d |
| ZipCompressedSize: | 119053 |
| ZipUncompressedSize: | 212992 |
| ZipFileName: | 3020a4940a04d45cdcfd29aa6a07c011434427289647a633992d3e6469ef598c.bin |
Total processes
88
Monitored processes
45
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 285.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e12a9d0,0x6e12a9e0,0x6e12a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1072541661240084562,14534818688215428602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18238596877475331789 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,1072541661240084562,14534818688215428602,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7633878806595717599 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1072541661240084562,14534818688215428602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15652651485689410276 --mojo-platform-channel-handle=4508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1072541661240084562,14534818688215428602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11958853100144372194 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\msptermsizes\Sh1S6R5xkOzY.exe" | C:\Users\admin\AppData\Local\msptermsizes\Sh1S6R5xkOzY.exe | — | msptermsizes.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1640 | --5ac0b1ad | C:\Users\admin\285.exe | 285.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,1072541661240084562,14534818688215428602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4950783911385236486 --mojo-platform-channel-handle=4616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\comments-10082019-U2624.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 754
Read events
3 275
Write events
450
Delete events
29
Modification events
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
4
Suspicious files
235
Text files
288
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_2924.5229 | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\769e7b34-563f-4301-a8cd-5b9de64b94db.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
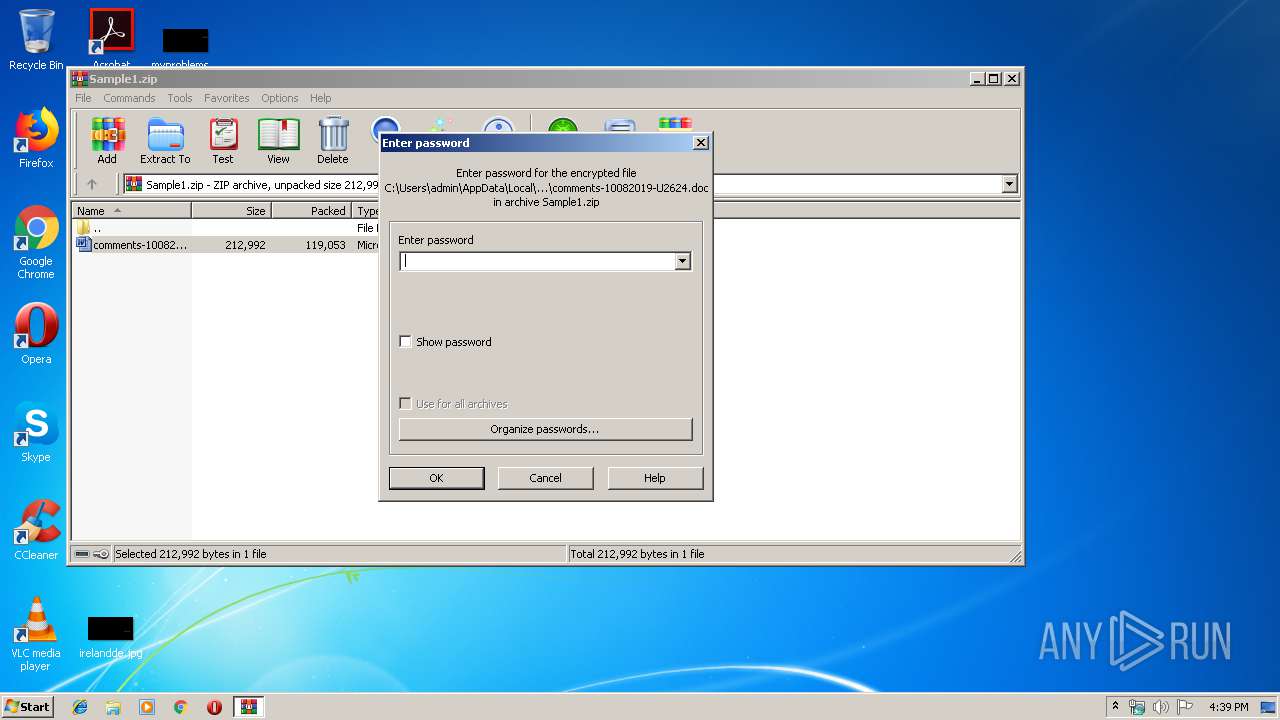
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2924.5504\comments-10082019-U2624.doc | document | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF121e1f.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Sample1.zip | compressed | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF121e00.TMP | text | |
MD5:— | SHA256:— | |||
| 3352 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
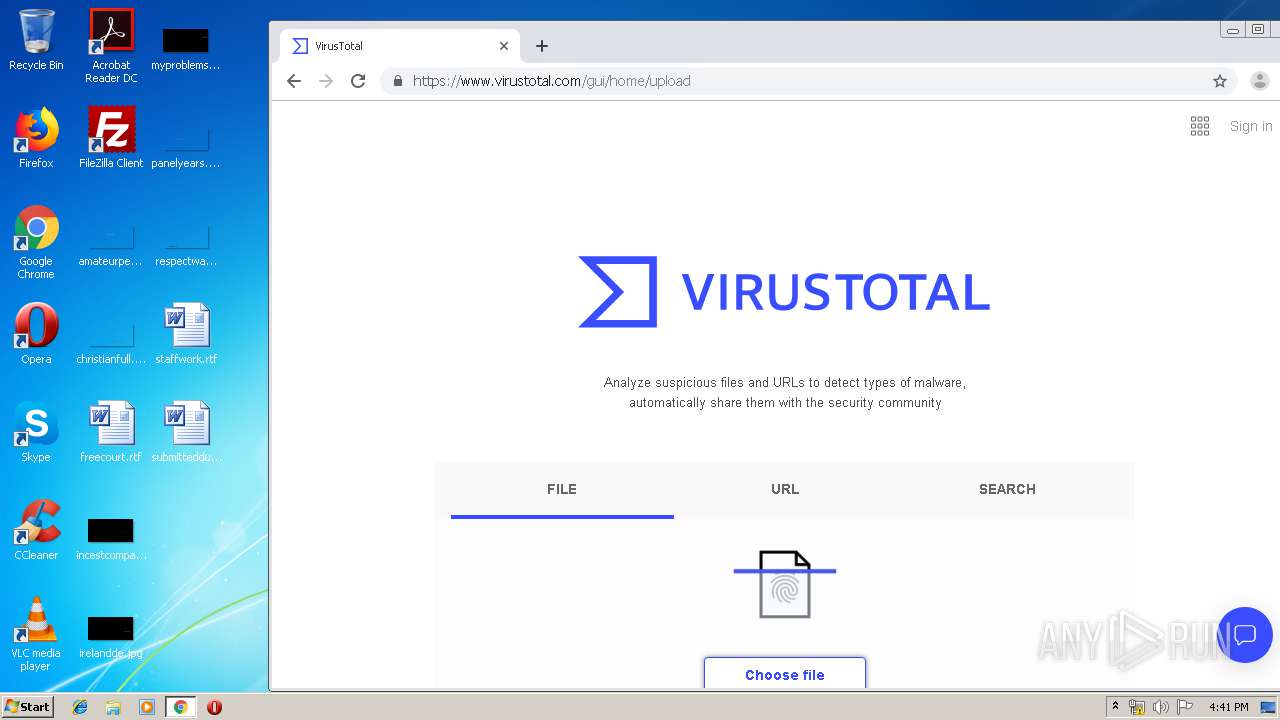
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
47
DNS requests
27
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
404 | chrome.exe | GET | 302 | 74.125.34.46:80 | http://www.virustotal.com/ | US | — | — | whitelisted |
404 | chrome.exe | GET | 204 | 216.58.208.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2576 | powershell.exe | GET | — | 23.229.199.41:80 | http://www.reviewchamp.net/wp-admin/4394/ | US | — | — | suspicious |
404 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
404 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2752 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/window/enable/ringin/merge/ | HU | binary | 142 Kb | malicious |
404 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=89.187.165.47&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1570635450&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2576 | powershell.exe | GET | 301 | 45.56.100.50:80 | http://www.denedolls.com/wp-content/upgrade/oghujlu568/ | US | html | 162 b | malicious |
404 | chrome.exe | GET | 200 | 74.125.104.104:80 | http://r2---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.47&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1570635450&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2576 | powershell.exe | GET | 301 | 45.56.101.4:80 | http://www.exquisiteextensions.net/5kjc/cache/8so9319/ | US | html | 162 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
404 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
404 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 172.217.16.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
404 | chrome.exe | 172.217.18.174:80 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2576 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2576 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2576 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2576 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2752 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2752 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report