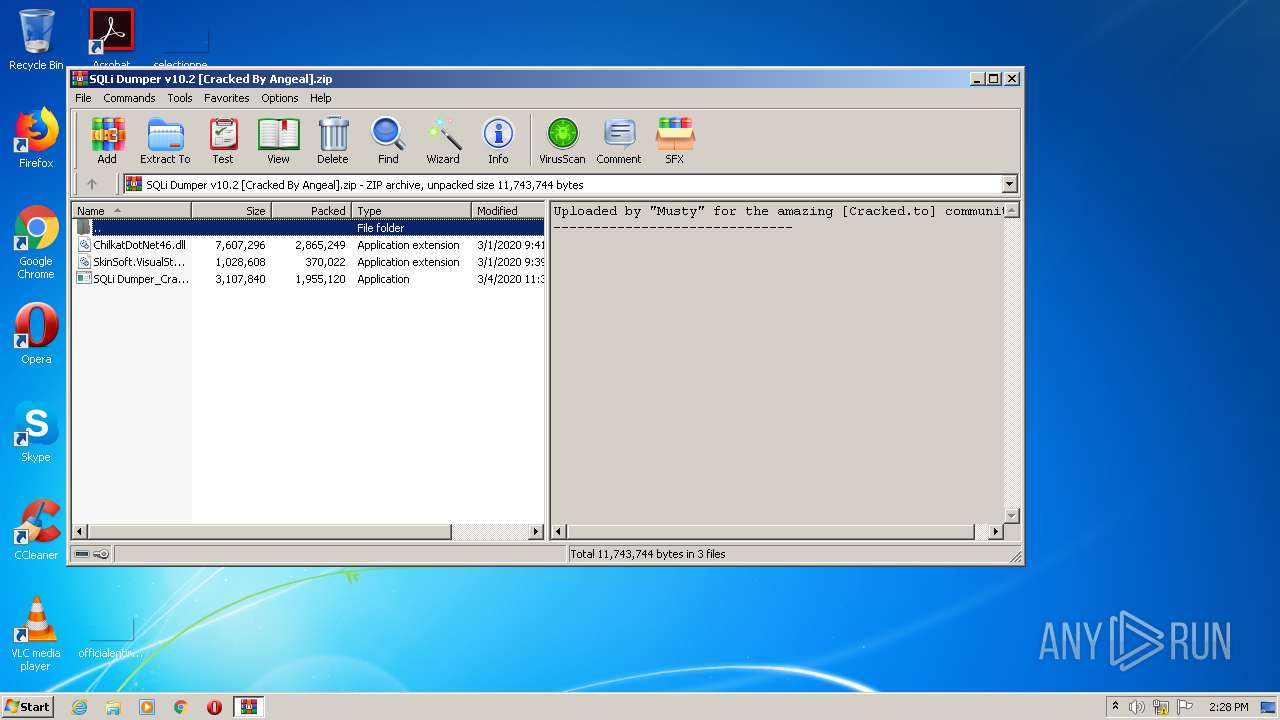
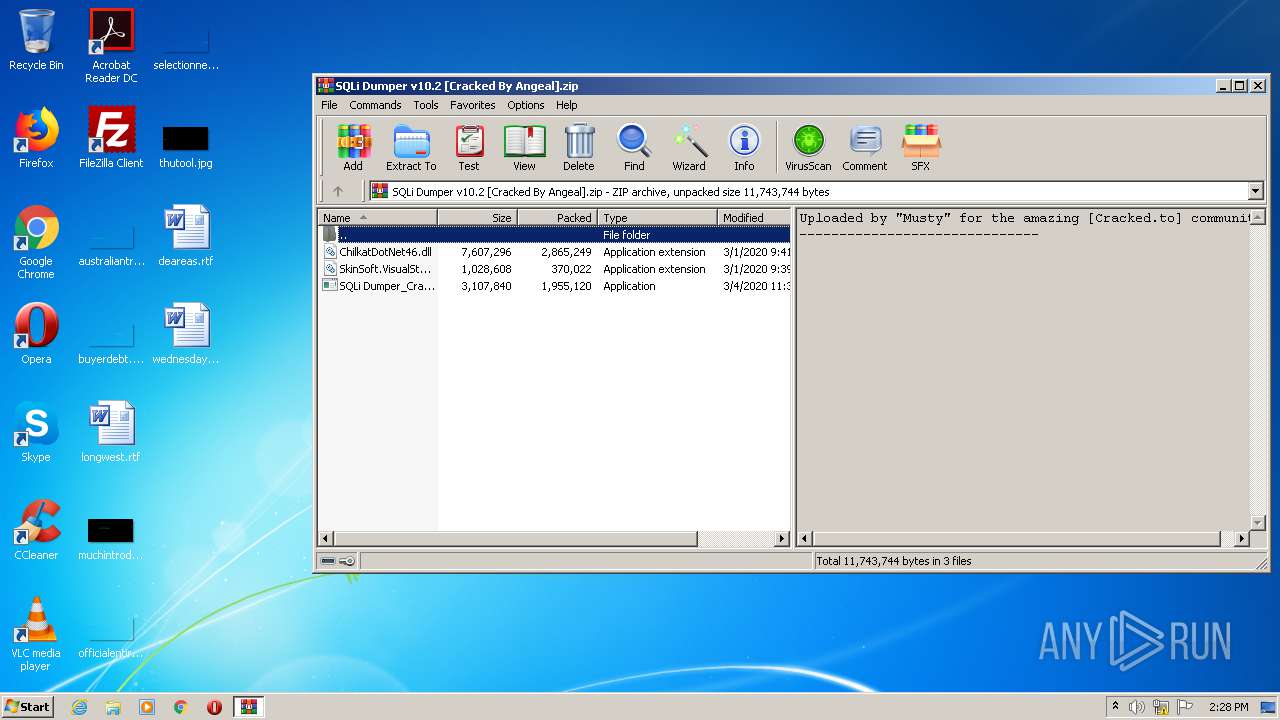
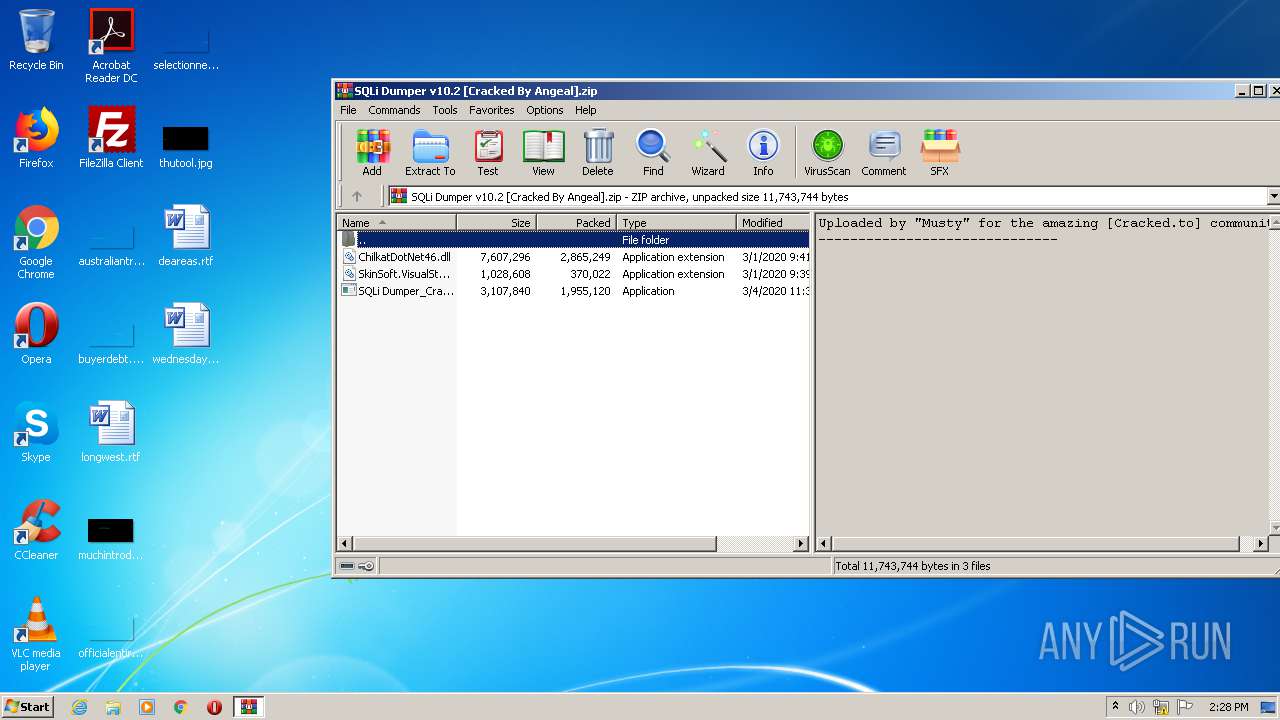
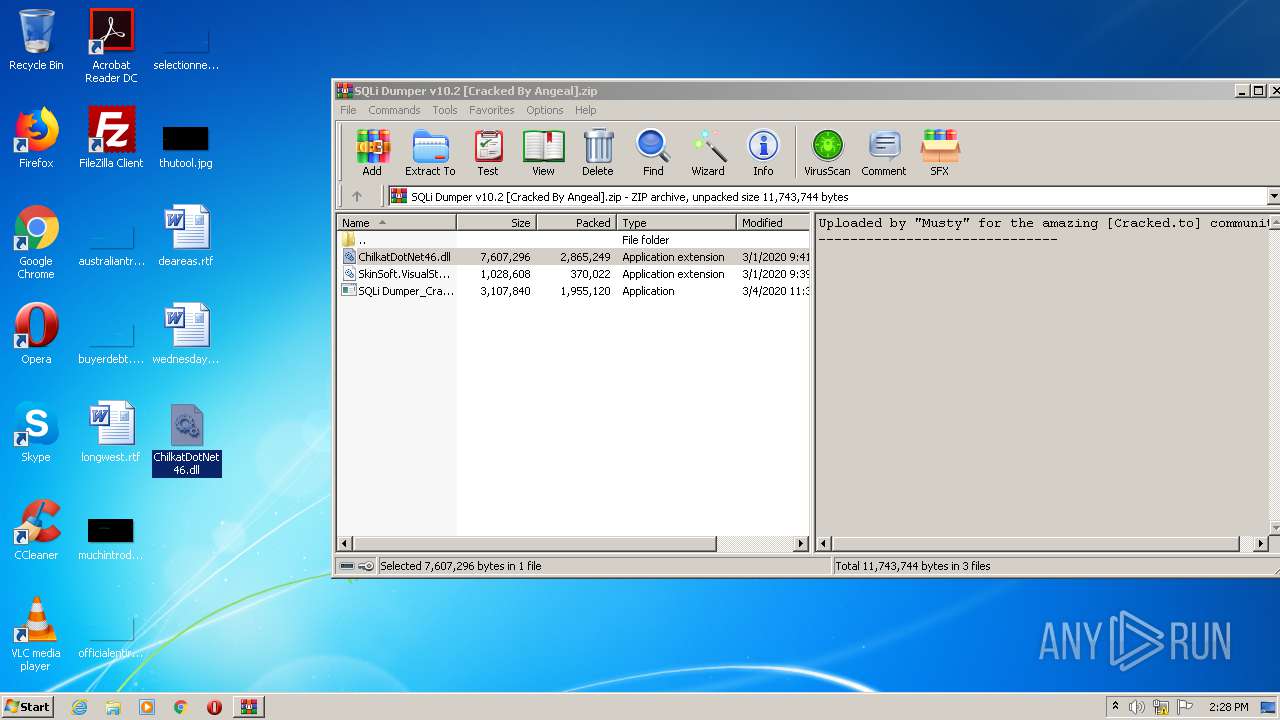
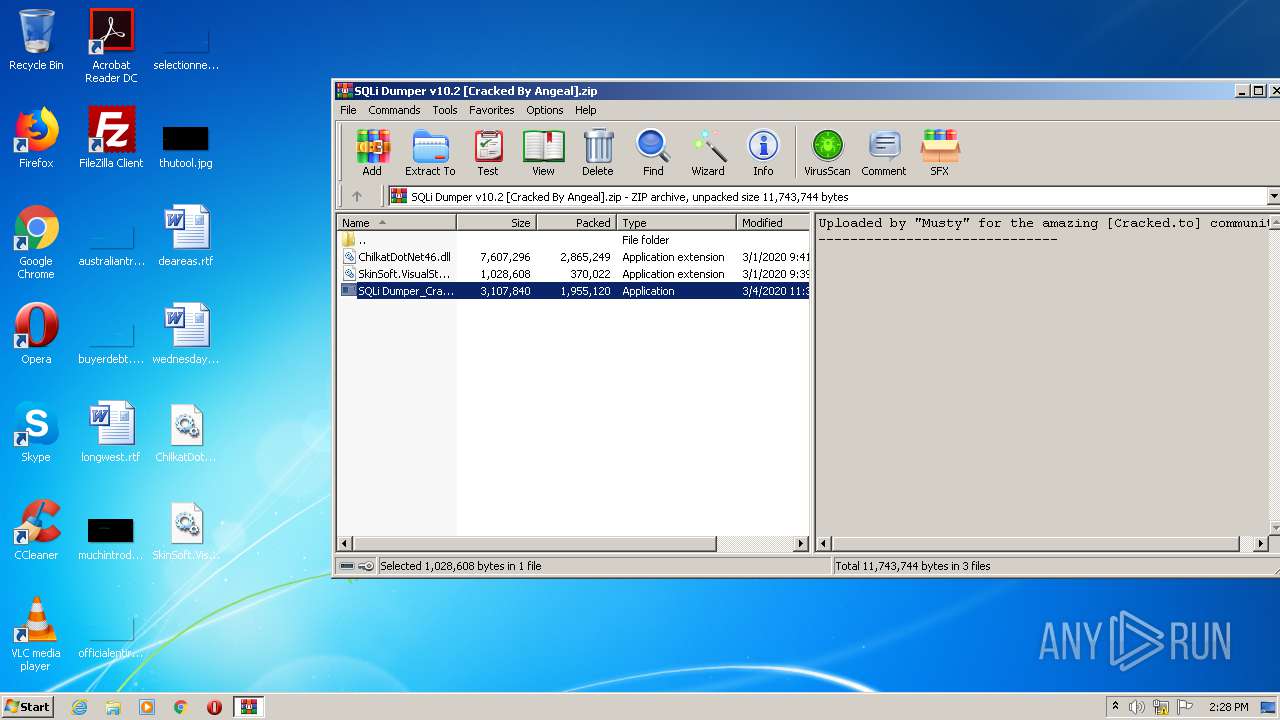
| File name: | SQLi Dumper v10.2 [Cracked By Angeal].zip |
| Full analysis: | https://app.any.run/tasks/d1a53d7f-a525-474f-a26c-0c04e9a7ec15 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2020, 14:28:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5F274A52046E58CB718973D15D77B270 |
| SHA1: | 3777C9FE9E4B2AFE3A3A6F3C861E5FFE756E717B |
| SHA256: | 29CD9431F2905166D4F9E193D2627714E09C8B9304AB34602BBF97CD7BCF4DA3 |
| SSDEEP: | 98304:6aZoMrNOh8VDizGwUgUeL7YvMuqCAzlKoC16HEbsoNxqusVapIzVuuz4LyyLjO9d:1ZoMROhSwUXEuqCAzloQ78aVapIJf4T8 |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3412)
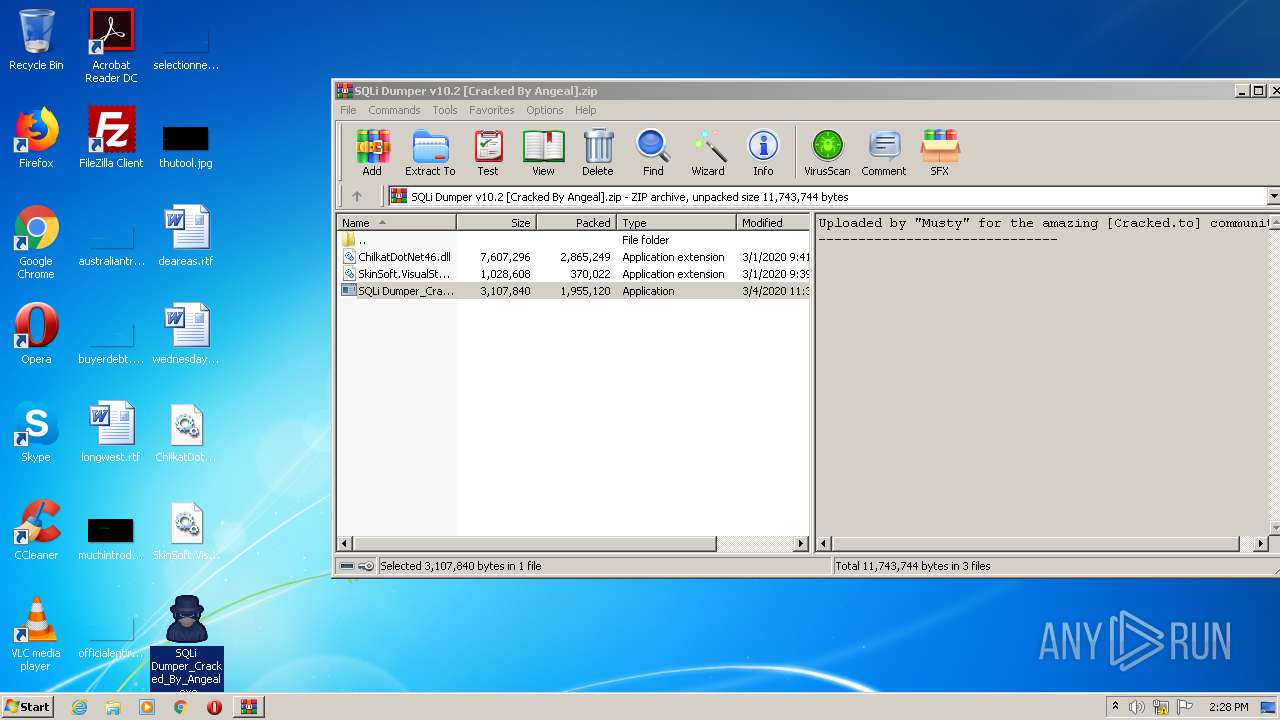
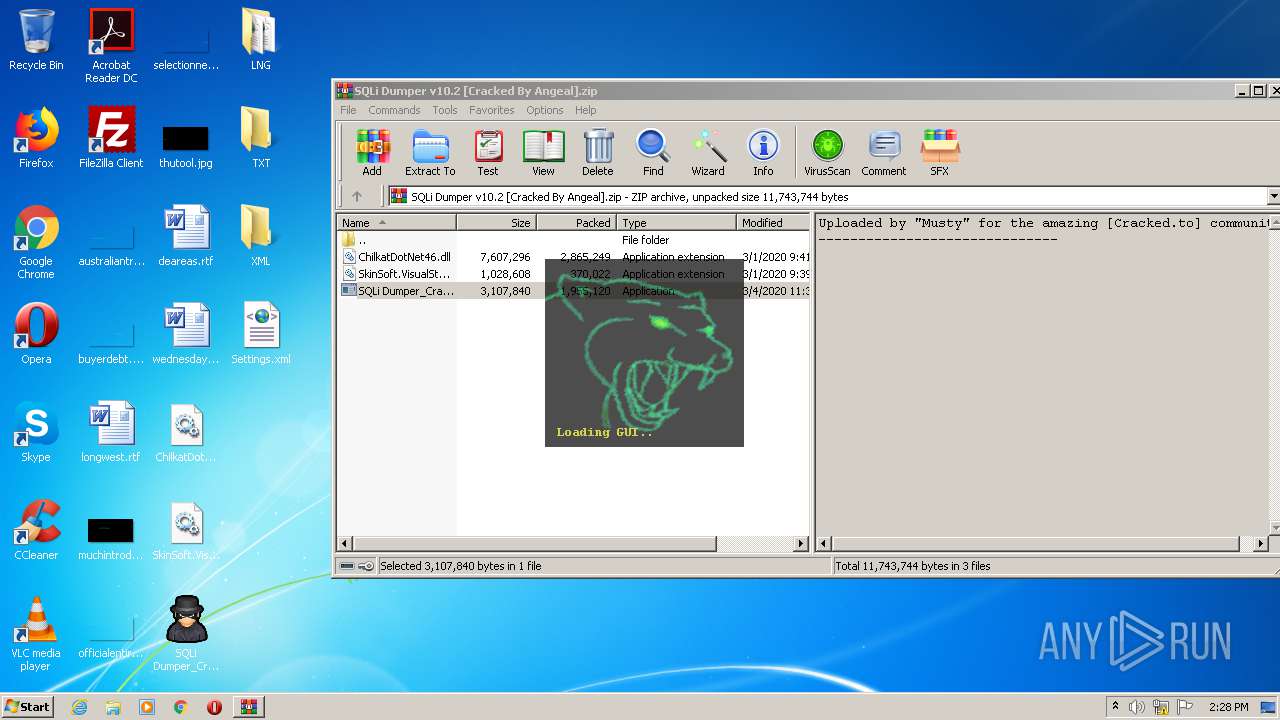
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
Application was dropped or rewritten from another process
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2760)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2760)
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
Checks for external IP
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
Reads Environment values
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
INFO
Manual execution by user
- SQLi Dumper_Cracked_By_Angeal.exe (PID: 1900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:05 03:03:23 |
| ZipCRC: | 0x11d95015 |
| ZipCompressedSize: | 1955120 |
| ZipUncompressedSize: | 3107840 |
| ZipFileName: | SQLi Dumper_Cracked_By_Angeal.exe |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
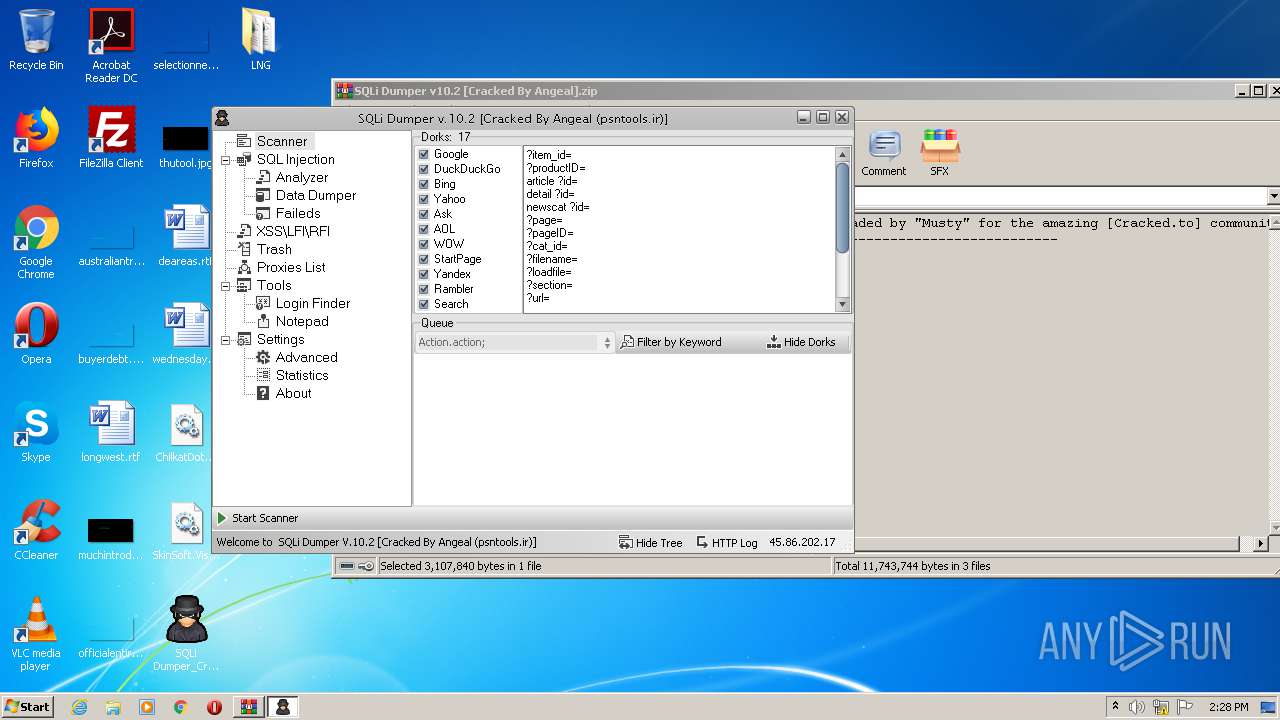
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1900 | "C:\Users\admin\Desktop\SQLi Dumper_Cracked_By_Angeal.exe" | C:\Users\admin\Desktop\SQLi Dumper_Cracked_By_Angeal.exe | explorer.exe | ||||||||||||
User: admin Company: fLaSh Integrity Level: MEDIUM Description: SQLi Dumper Exit code: 0 Version: 10.2.0.0 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\SQLi Dumper v10.2 [Cracked By Angeal].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
829
Read events
807
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SQLi Dumper v10.2 [Cracked By Angeal].zip | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2760) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3412) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3412) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
Executable files
3
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2760.36068\SkinSoft.VisualStyler.dll | — | |
MD5:— | SHA256:— | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\LNG\Portuguese.xml | xml | |
MD5:E1B7540D846CA89F57DE64305B94DBC9 | SHA256:F6CDC1E33C9F9637B56FDAAB6AD47C8E72E9F384A9CFC9C2B356825C62531DCB | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\LNG\Russian.xml | xml | |
MD5:4C3341A7BFC47F68E779A50F9E669900 | SHA256:72515A8F2B7A29FC06E3A8FFD28D3D0DEA9E98D00CD9EB7B941703F7A3AFAB3E | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\LNG\German.xml | xml | |
MD5:4A25B19B26DEF334C719E8D543F23486 | SHA256:97BB355062589C2C89E139E8174B71A15FBE89F10E2C72DE1489AD3B9B035B91 | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\LNG\English.xml | xml | |
MD5:E932EA4DD931CD9039EC0CEA098DDF85 | SHA256:E4284B97BE769C04F1E49DD649F7116D364D72EAC74443A7CD2C46C13220D06B | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\AppData\Local\SkinSoft\VisualStyler\2.4.0.0\x86\ssapihook.dll | executable | |
MD5:BB439BF268E538B714B0727F02945374 | SHA256:D1334AE830AC3EC69F2AE63C16DAE778E6B6AF2FF9A6226E4336451A0A1FFD5B | |||
| 2760 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2760.35866\ChilkatDotNet46.dll | executable | |
MD5:AC3C6280175E2FA87A761B20DD75973E | SHA256:A2152F98A37EF40BA8B411B1A061DC4FC503F20313CB1C0BBD3816E14F67A03A | |||
| 2760 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2760.36263\SQLi Dumper_Cracked_By_Angeal.exe | executable | |
MD5:9D8B946AE008BC962015CDB436A648D2 | SHA256:49606C156C838DB34E09A96369D0CB9C5097E9DBC6174BD6827C09AF4365EDF2 | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\Settings.xml | xml | |
MD5:BD5CD5E2C5CA6CDFD652AFC2F54D16BA | SHA256:69EFEFDBA31057B12E428B73D101CA89501F799CF88941A6DDB00ACEB15F3AE1 | |||
| 1900 | SQLi Dumper_Cracked_By_Angeal.exe | C:\Users\admin\Desktop\LNG\Persian.xml | xml | |
MD5:6BDC041287825A04B67895BB9111806C | SHA256:B947F3E9558296EEAEE767FFBF1CE4270DEFF8DBA8BC57EF648E1E86A1D55FB3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1900 | SQLi Dumper_Cracked_By_Angeal.exe | GET | 200 | 131.186.113.70:80 | http://checkip.dyndns.org/ | US | html | 104 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1900 | SQLi Dumper_Cracked_By_Angeal.exe | 131.186.113.70:80 | checkip.dyndns.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.dyndns.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1056 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
1900 | SQLi Dumper_Cracked_By_Angeal.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
1900 | SQLi Dumper_Cracked_By_Angeal.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Check checkip.dyndns.org |
1900 | SQLi Dumper_Cracked_By_Angeal.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
1 ETPRO signatures available at the full report