| File name: | CL-Eye-Driver-5.3.0.0341-Emuline.exe |
| Full analysis: | https://app.any.run/tasks/c08234d8-e356-4e4f-9c3f-05e531ab9305 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2022, 19:22:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 64112C1DF0D80D195D006DA9C15BF710 |
| SHA1: | F0BFBC32171ECFB03614470B9C06EF34C07E66B0 |
| SHA256: | 29CBD9D9BC6571D15D6A2B29DD2532FE6C7FB81D255778DEB40F64DC79502BF5 |
| SSDEEP: | 98304:4cf1PgNuKGzp9kp2aqDNsmXWtKI/cdVo+J2v1I54UJV17j7MayZkxMCOaX:7xz3zApCXEtECd64eV1TyZkxJ |
MALICIOUS
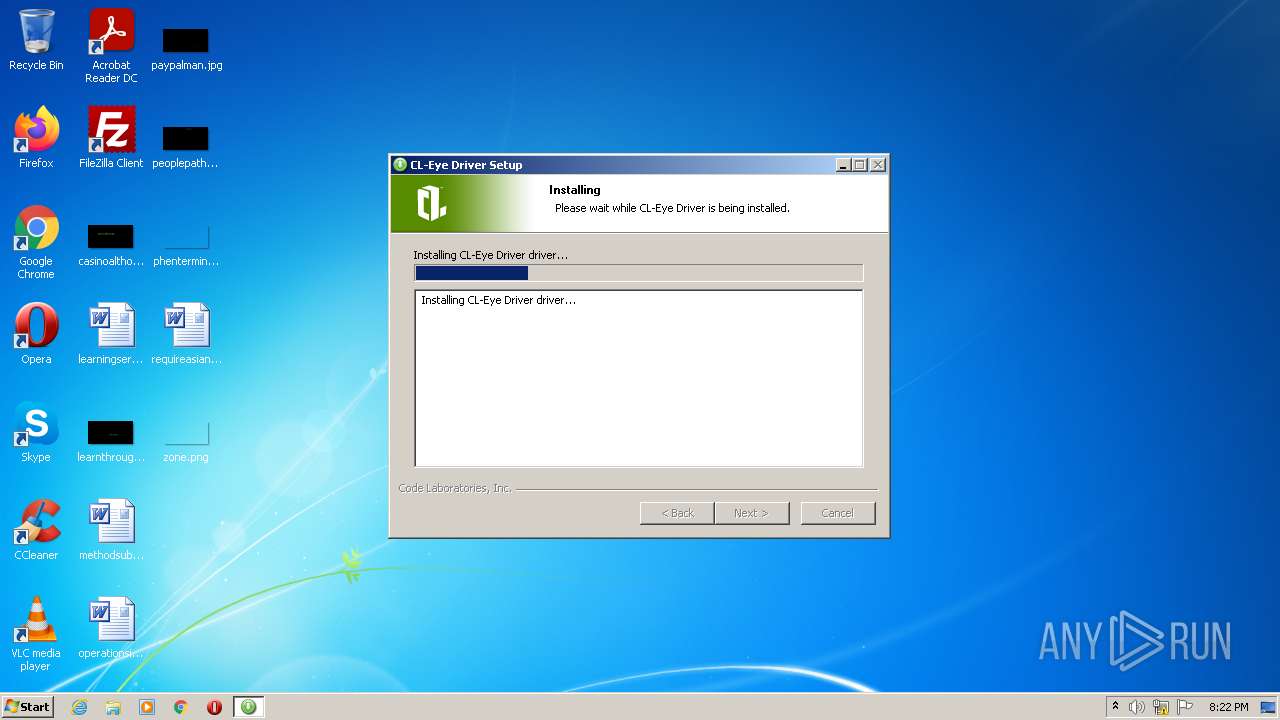
Loads dropped or rewritten executable
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
Drops executable file immediately after starts
- wdreg.exe (PID: 3604)
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
- DrvInst.exe (PID: 3572)
Changes settings of System certificates
- CertMgr.exe (PID: 3104)
Application was dropped or rewritten from another process
- CertMgr.exe (PID: 3104)
- wdreg.exe (PID: 3604)
- CL-EyeTest.exe (PID: 2768)
Registers / Runs the DLL via REGSVR32.EXE
- nsEEFF.tmp (PID: 3336)
SUSPICIOUS
Reads the computer name
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
- wdreg.exe (PID: 3604)
- DrvInst.exe (PID: 3572)
- CL-EyeTest.exe (PID: 2768)
Checks supported languages
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
- nsCACD.tmp (PID: 3416)
- CertMgr.exe (PID: 3104)
- wdreg.exe (PID: 3604)
- nsC7BE.tmp (PID: 2352)
- DrvInst.exe (PID: 3572)
- nsEEFF.tmp (PID: 3336)
- CL-EyeTest.exe (PID: 2768)
Starts application with an unusual extension
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
Creates files in the Windows directory
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
- DrvInst.exe (PID: 3572)
Executable content was dropped or overwritten
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
- wdreg.exe (PID: 3604)
- DrvInst.exe (PID: 3572)
Creates files in the program directory
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
Creates a directory in Program Files
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
Drops a file with a compile date too recent
- wdreg.exe (PID: 3604)
- DrvInst.exe (PID: 3572)
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
Executed via COM
- DrvInst.exe (PID: 3572)
Removes files from Windows directory
- DrvInst.exe (PID: 3572)
Creates files in the driver directory
- DrvInst.exe (PID: 3572)
Executed as Windows Service
- vssvc.exe (PID: 2960)
Reads Environment values
- vssvc.exe (PID: 2960)
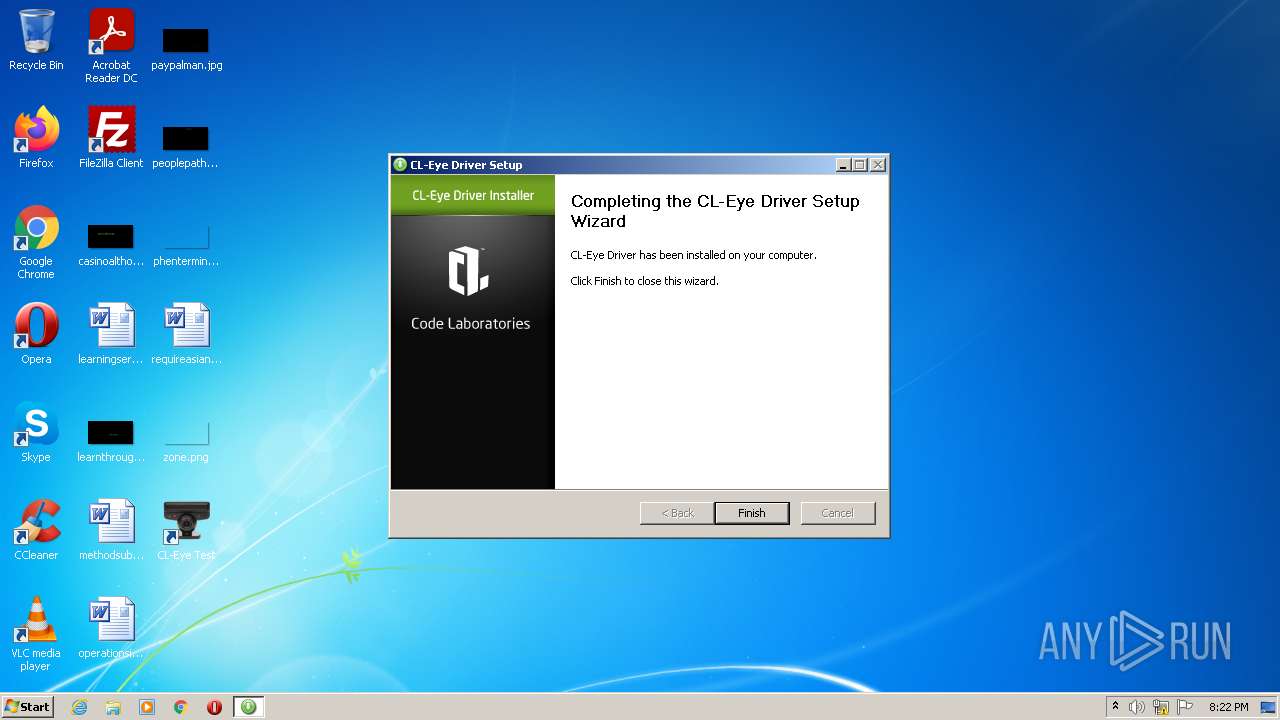
Creates a software uninstall entry
- CL-Eye-Driver-5.3.0.0341-Emuline.exe (PID: 3004)
INFO
Reads settings of System Certificates
- DrvInst.exe (PID: 3572)
Checks Windows Trust Settings
- DrvInst.exe (PID: 3572)
Reads the computer name
- vssvc.exe (PID: 2960)
Changes settings of System certificates
- DrvInst.exe (PID: 3572)
Checks supported languages
- regsvr32.exe (PID: 3508)
- vssvc.exe (PID: 2960)
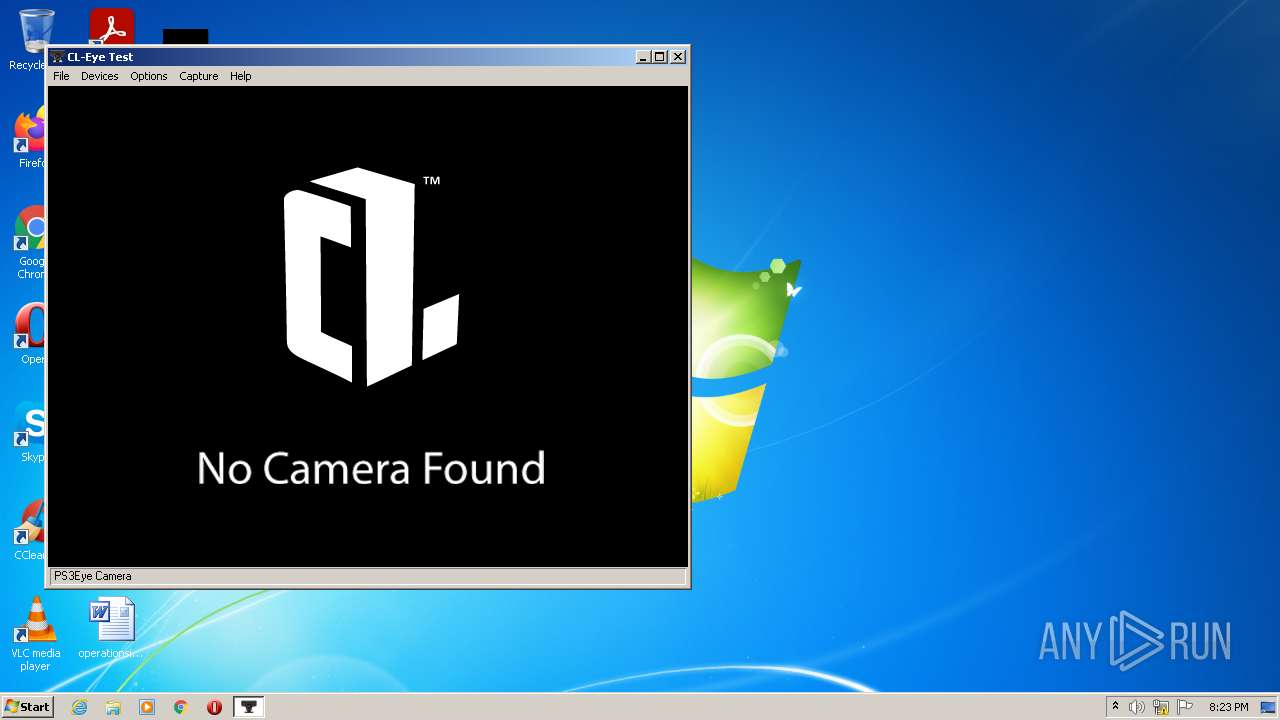
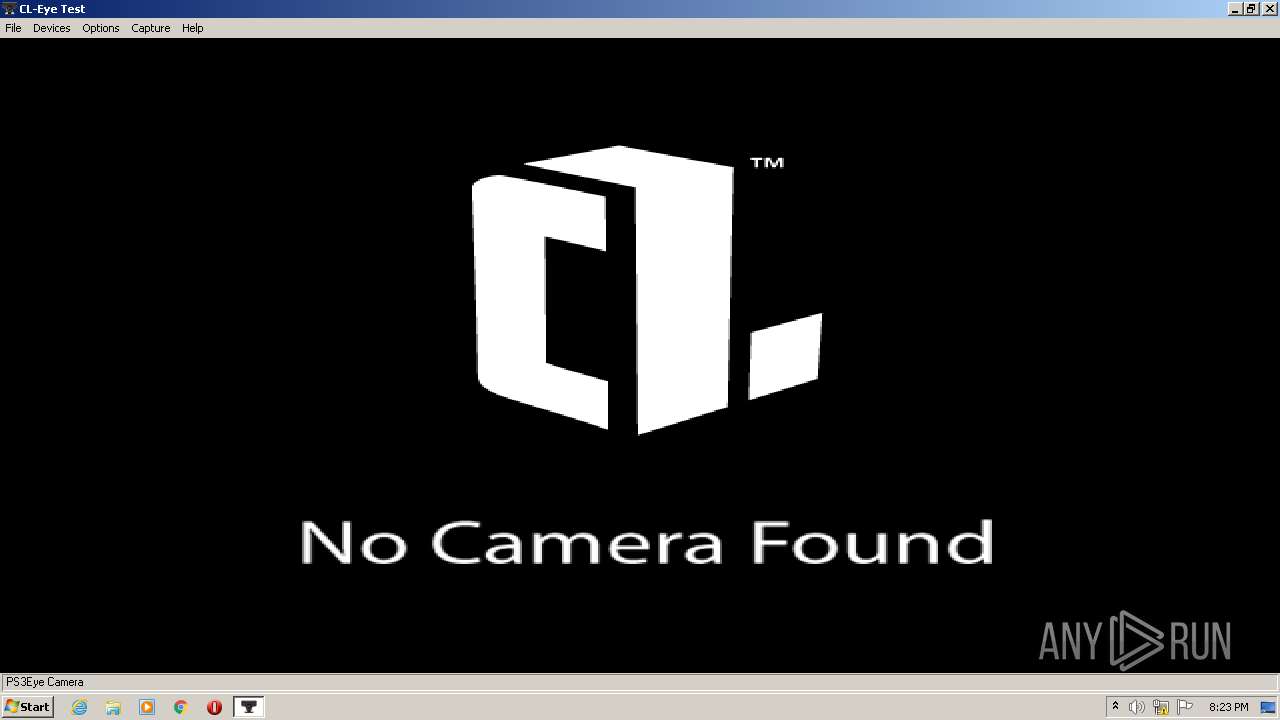
Manual execution by user
- CL-EyeTest.exe (PID: 2768)
Searches for installed software
- DrvInst.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| ProductVersion: | 5.3.0.0341 |
|---|---|
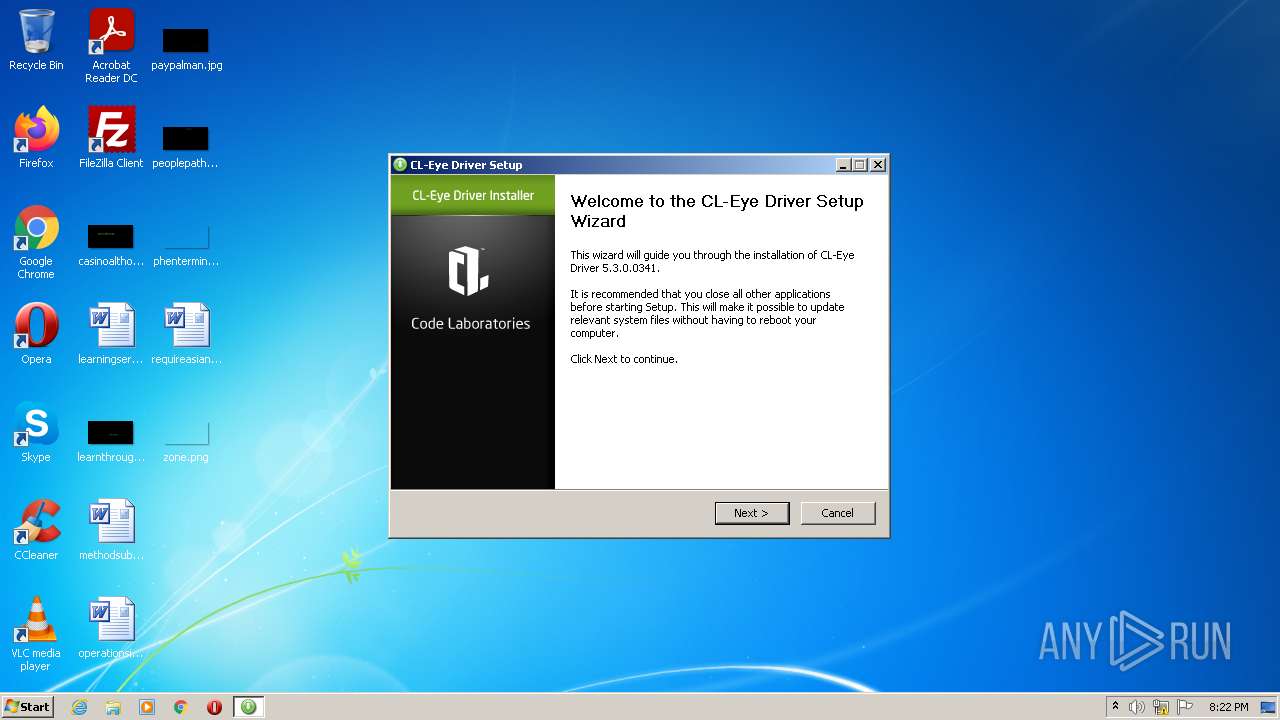
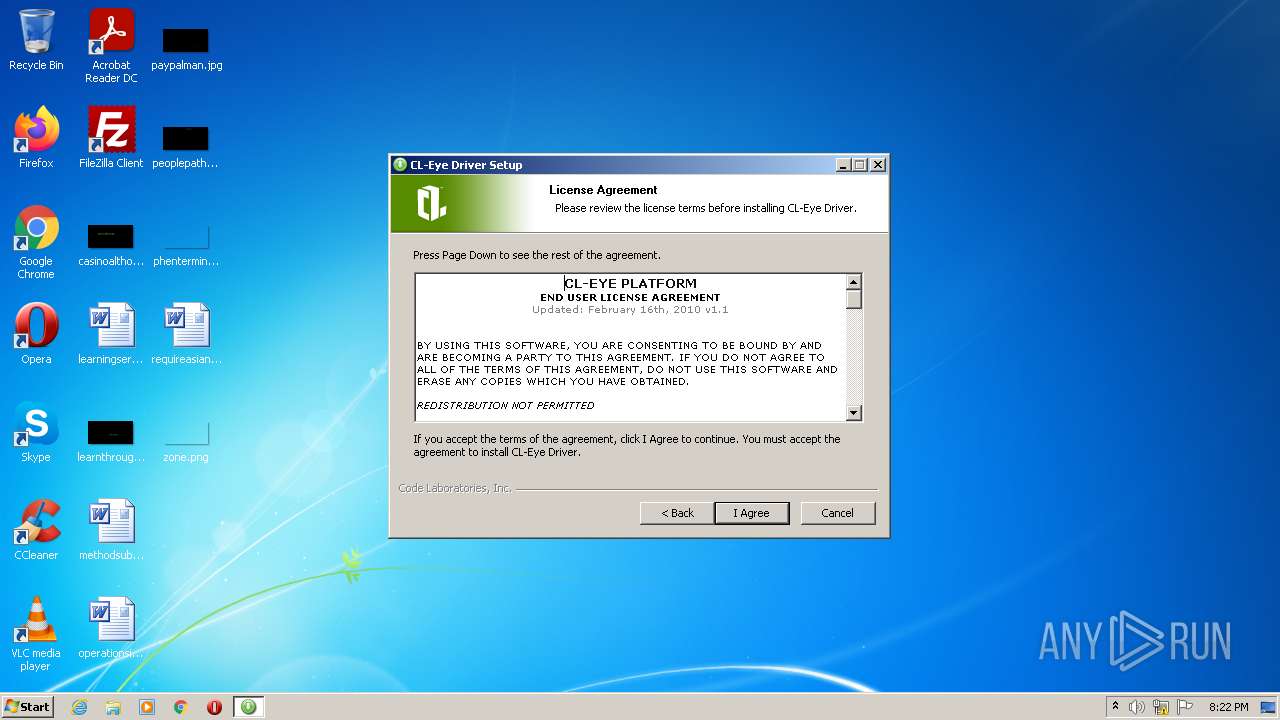
| ProductName: | CL-Eye Platform Driver for PS3Eye |
| OriginalFileName: | CL-Eye-Driver-5.3.0.0341.exe |
| LegalCopyright: | © 2008-2012 Code Laboratories, Inc.. All rights reserved. |
| InternalName: | CL-Eye Driver Setup |
| FileVersion: | 5.3.0.0341 |
| FileDescription: | CL-Eye Platform Driver Setup |
| CompanyName: | Code Laboratories, Inc. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 5.3.0.341 |
| FileVersionNumber: | 5.3.0.341 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | Code Laboratories, Inc. |
| FileDescription: | CL-Eye Platform Driver Setup |
| FileVersion: | 5.3.0.0341 |
| InternalName: | CL-Eye Driver Setup |
| LegalCopyright: | © 2008-2012 Code Laboratories, Inc.. All rights reserved. |
| OriginalFilename: | CL-Eye-Driver-5.3.0.0341.exe |
| ProductName: | CL-Eye Platform Driver for PS3Eye |
| ProductVersion: | 5.3.0.0341 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00036000 | 0x00007208 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.93552 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.66399 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 2.2236 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
51
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Users\admin\AppData\Local\Temp\CL-Eye-Driver-5.3.0.0341-Emuline.exe" | C:\Users\admin\AppData\Local\Temp\CL-Eye-Driver-5.3.0.0341-Emuline.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Code Laboratories, Inc. Integrity Level: MEDIUM Description: CL-Eye Platform Driver Setup Exit code: 3221226540 Version: 5.3.0.0341 Modules
| |||||||||||||||
| 2352 | "C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsC7BE.tmp" C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CertMgr.exe -add C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CodeLabs.cer -c -s -r localMachine TrustedPublisher | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsC7BE.tmp | — | CL-Eye-Driver-5.3.0.0341-Emuline.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Code Laboratories\CL-Eye Driver\CL-EyeTest.exe" | C:\Program Files\Code Laboratories\CL-Eye Driver\CL-EyeTest.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2960 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\CL-Eye-Driver-5.3.0.0341-Emuline.exe" | C:\Users\admin\AppData\Local\Temp\CL-Eye-Driver-5.3.0.0341-Emuline.exe | Explorer.EXE | ||||||||||||
User: admin Company: Code Laboratories, Inc. Integrity Level: HIGH Description: CL-Eye Platform Driver Setup Exit code: 0 Version: 5.3.0.0341 Modules
| |||||||||||||||
| 3104 | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CertMgr.exe -add C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CodeLabs.cer -c -s -r localMachine TrustedPublisher | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CertMgr.exe | — | nsC7BE.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsEEFF.tmp" regsvr32 /s PS3EyeAxFilter.ax | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsEEFF.tmp | — | CL-Eye-Driver-5.3.0.0341-Emuline.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsCACD.tmp" C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\wdreg.exe -inf PS3EyeCamera.inf -silent -compat install | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsCACD.tmp | — | CL-Eye-Driver-5.3.0.0341-Emuline.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3508 | regsvr32 /s PS3EyeAxFilter.ax | C:\Windows\system32\regsvr32.exe | — | nsEEFF.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3572 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{69e647f9-398f-4293-d7d9-854caf97ca25}\PS3EyeCamera.inf" "0" "6f5e04b87" "00000064" "WinSta0\Default" "000004B0" "208" "C:\Program Files\Code Laboratories\CL-Eye Driver\Driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 655
Read events
5 428
Write events
227
Delete events
0
Modification events
| (PID) Process: | (3104) CertMgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\97B8DB93E99E6D5D8F6424143BE1F8F96D0F4FA7 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000097B8DB93E99E6D5D8F6424143BE1F8F96D0F4FA7200000000100000077050000308205733082045BA00302010202103621615D5DC8015358E6E878C541ABF0300D06092A864886F70D01010505003081B4310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313B3039060355040B13325465726D73206F66207573652061742068747470733A2F2F7777772E766572697369676E2E636F6D2F727061202863293130312E302C06035504031325566572695369676E20436C617373203320436F6465205369676E696E672032303130204341301E170D3132313230323030303030305A170D3134303130313233353935395A3081B6310B3009060355040613025553310F300D060355040813064E6576616461311230100603550407130948656E646572736F6E3120301E060355040A1417436F6465204C61626F7261746F726965732C20496E632E313E303C060355040B13354469676974616C20494420436C6173732033202D204D6963726F736F667420536F6674776172652056616C69646174696F6E2076323120301E06035504031417436F6465204C61626F7261746F726965732C20496E632E30820122300D06092A864886F70D01010105000382010F003082010A0282010100DB4B56899F9BD1E780BE42D133BEB8426D253C6B5CF7B128E80D41BD72F947737C78608B0B45DEDDDB081BBD9E049FC4A29D5F1C3AC2F04299858CCE5D349E6D9AA60E86BC37A16538944AA347B47B9A0E4BE17E3FF56D4EB4B8982B6DB146F6DEC8DF75E49C0403E4E97B201E95EDBF7E76D1B1FFC11DA2D142734E9BC5D3E4BA589B1633D3A8ABA95E7CA19B179B0BB8B91ADA8EA120F6ACD01CCA47869D41FD4455258E8AD5ED4ED96E74152434AEBC2D4B60212E79B9BBEF9E70D80243E2A3B22EF9FC852CB328F11B921C88980DEB34891439674778E653DEE265537A42DE0953083CCD56B57242A4279B7D6A4EDA6F31B6335AE56864CA65D5DFAC073D0203010001A382017B3082017730090603551D1304023000300E0603551D0F0101FF04040302078030400603551D1F043930373035A033A031862F687474703A2F2F637363332D323031302D63726C2E766572697369676E2E636F6D2F435343332D323031302E63726C30440603551D20043D303B3039060B6086480186F84501071703302A302806082B06010505070201161C68747470733A2F2F7777772E766572697369676E2E636F6D2F72706130130603551D25040C300A06082B06010505070303307106082B0601050507010104653063302406082B060105050730018618687474703A2F2F6F6373702E766572697369676E2E636F6D303B06082B06010505073002862F687474703A2F2F637363332D323031302D6169612E766572697369676E2E636F6D2F435343332D323031302E636572301F0603551D23041830168014CF99A9EA7B26F44BC98E8FD7F00526EFE3D2A79D301106096086480186F84201010404030204103016060A2B06010401823702011B040830060101000101FF300D06092A864886F70D010105050003820101006CB2632AB501FF6EEE27631A111C2F2066724399BBD09C80E7A0A68E2AB14816DC7D13C4A7285A640F8A8B63FCC40E718B81513D7B1D12B65408C093B14F0D4A3BD2DF599DE287B5A5AC62B71B795FA33D5F1EE81A07117EF04CD43C2C68E4E94088D62324B1B0D9A4362E3FBE8A9398A89E17315DD942E782F36DE5B3CB1B58C6C4DD67DA13277B2CBCFD5BB48E1133BEF9D2BF1EC2D26A3ACBB93DA0A94EC01DEF19F79F5B442FD29A648BFDC96996BD9C64945C39AF5E3603706C7677000B9F5776BF339FC650701617B12C45478F56052249A68E0996F4B54E89A747C157D113F7ED5C4790EA1D6EA9C874B86C3F52135E9BBF755121319043F441E6A07B | |||
| (PID) Process: | (3604) wdreg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (3604) wdreg.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\97B8DB93E99E6D5D8F6424143BE1F8F96D0F4FA7 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000140000009429B7BA3C207E859F3B6087EBF608F3AF34A09303000000010000001400000097B8DB93E99E6D5D8F6424143BE1F8F96D0F4FA7200000000100000077050000308205733082045BA00302010202103621615D5DC8015358E6E878C541ABF0300D06092A864886F70D01010505003081B4310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313B3039060355040B13325465726D73206F66207573652061742068747470733A2F2F7777772E766572697369676E2E636F6D2F727061202863293130312E302C06035504031325566572695369676E20436C617373203320436F6465205369676E696E672032303130204341301E170D3132313230323030303030305A170D3134303130313233353935395A3081B6310B3009060355040613025553310F300D060355040813064E6576616461311230100603550407130948656E646572736F6E3120301E060355040A1417436F6465204C61626F7261746F726965732C20496E632E313E303C060355040B13354469676974616C20494420436C6173732033202D204D6963726F736F667420536F6674776172652056616C69646174696F6E2076323120301E06035504031417436F6465204C61626F7261746F726965732C20496E632E30820122300D06092A864886F70D01010105000382010F003082010A0282010100DB4B56899F9BD1E780BE42D133BEB8426D253C6B5CF7B128E80D41BD72F947737C78608B0B45DEDDDB081BBD9E049FC4A29D5F1C3AC2F04299858CCE5D349E6D9AA60E86BC37A16538944AA347B47B9A0E4BE17E3FF56D4EB4B8982B6DB146F6DEC8DF75E49C0403E4E97B201E95EDBF7E76D1B1FFC11DA2D142734E9BC5D3E4BA589B1633D3A8ABA95E7CA19B179B0BB8B91ADA8EA120F6ACD01CCA47869D41FD4455258E8AD5ED4ED96E74152434AEBC2D4B60212E79B9BBEF9E70D80243E2A3B22EF9FC852CB328F11B921C88980DEB34891439674778E653DEE265537A42DE0953083CCD56B57242A4279B7D6A4EDA6F31B6335AE56864CA65D5DFAC073D0203010001A382017B3082017730090603551D1304023000300E0603551D0F0101FF04040302078030400603551D1F043930373035A033A031862F687474703A2F2F637363332D323031302D63726C2E766572697369676E2E636F6D2F435343332D323031302E63726C30440603551D20043D303B3039060B6086480186F84501071703302A302806082B06010505070201161C68747470733A2F2F7777772E766572697369676E2E636F6D2F72706130130603551D25040C300A06082B06010505070303307106082B0601050507010104653063302406082B060105050730018618687474703A2F2F6F6373702E766572697369676E2E636F6D303B06082B06010505073002862F687474703A2F2F637363332D323031302D6169612E766572697369676E2E636F6D2F435343332D323031302E636572301F0603551D23041830168014CF99A9EA7B26F44BC98E8FD7F00526EFE3D2A79D301106096086480186F84201010404030204103016060A2B06010401823702011B040830060101000101FF300D06092A864886F70D010105050003820101006CB2632AB501FF6EEE27631A111C2F2066724399BBD09C80E7A0A68E2AB14816DC7D13C4A7285A640F8A8B63FCC40E718B81513D7B1D12B65408C093B14F0D4A3BD2DF599DE287B5A5AC62B71B795FA33D5F1EE81A07117EF04CD43C2C68E4E94088D62324B1B0D9A4362E3FBE8A9398A89E17315DD942E782F36DE5B3CB1B58C6C4DD67DA13277B2CBCFD5BB48E1133BEF9D2BF1EC2D26A3ACBB93DA0A94EC01DEF19F79F5B442FD29A648BFDC96996BD9C64945C39AF5E3603706C7677000B9F5776BF339FC650701617B12C45478F56052249A68E0996F4B54E89A747C157D113F7ED5C4790EA1D6EA9C874B86C3F52135E9BBF755121319043F441E6A07B | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000002029937F236AD801F40D000020060000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000002029937F236AD801F40D000020060000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000003EAEF97F236AD801F40D000020060000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009810FC7F236AD801F40D0000840A0000E803000001000000000000000000000086385DA1FFD73D45ACEAAE7E0A84CAD00000000000000000 | |||
Executable files
23
Suspicious files
15
Text files
5
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsDialogs.dll | executable | |
MD5:C10E04DD4AD4277D5ADC951BB331C777 | SHA256:E31AD6C6E82E603378CB6B80E67D0E0DCD9CF384E1199AC5A65CB4935680021A | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Program Files\Code Laboratories\CL-Eye Driver\Driver\CLEyeDevices.dll | executable | |
MD5:26A48E71CB34E066C4CFF8D7550A10E6 | SHA256:1AC37C755C24D760C85BE01FC026023B3C6CA0444352FA14A2B93E59BDAEBDDC | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\modern-header.bmp | image | |
MD5:BF0CAC9A510A5C7C674734F70CC78EED | SHA256:EA407BA58AB565DA56864C02BE188D42F4C35E1124AF85AC668601C7D9FE885C | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Program Files\Code Laboratories\CL-Eye Driver\Driver\PS3EyeCamera.inf | binary | |
MD5:60BB6D15F8989D61064565C5E7B7E7BB | SHA256:3D75843CF756E744177C3C5B31B9100D2C18C9FE8A7B6D0CF62FFEE9B5F53788 | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CodeLabs.cer | der | |
MD5:972B62B8C7088AF29C364514E6582F0B | SHA256:7D535AD3E333875076288791BBCE84FD7DB67624940B2639418EB40BF39CE465 | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Windows\system32\CLEyeDevices.dll | executable | |
MD5:DAD1C55402BFE58EE7E051EB26F367E7 | SHA256:6DB1860BC51C56A0B552ABCEA593F1243409D9D07D19265D18110B45A7E3B6F0 | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\CertMgr.exe | executable | |
MD5:1444BCFEFF029BB1E9B1CA3B896CD143 | SHA256:781F4ECA34D7EA200EC534F556AE0D39A89E0E38D909899166A6E910B57E2CBD | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsExec.dll | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
| 3004 | CL-Eye-Driver-5.3.0.0341-Emuline.exe | C:\Users\admin\AppData\Local\Temp\nstA83F.tmp\nsC7BE.tmp | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report