| File name: | MoneyRobotSetup.exe |
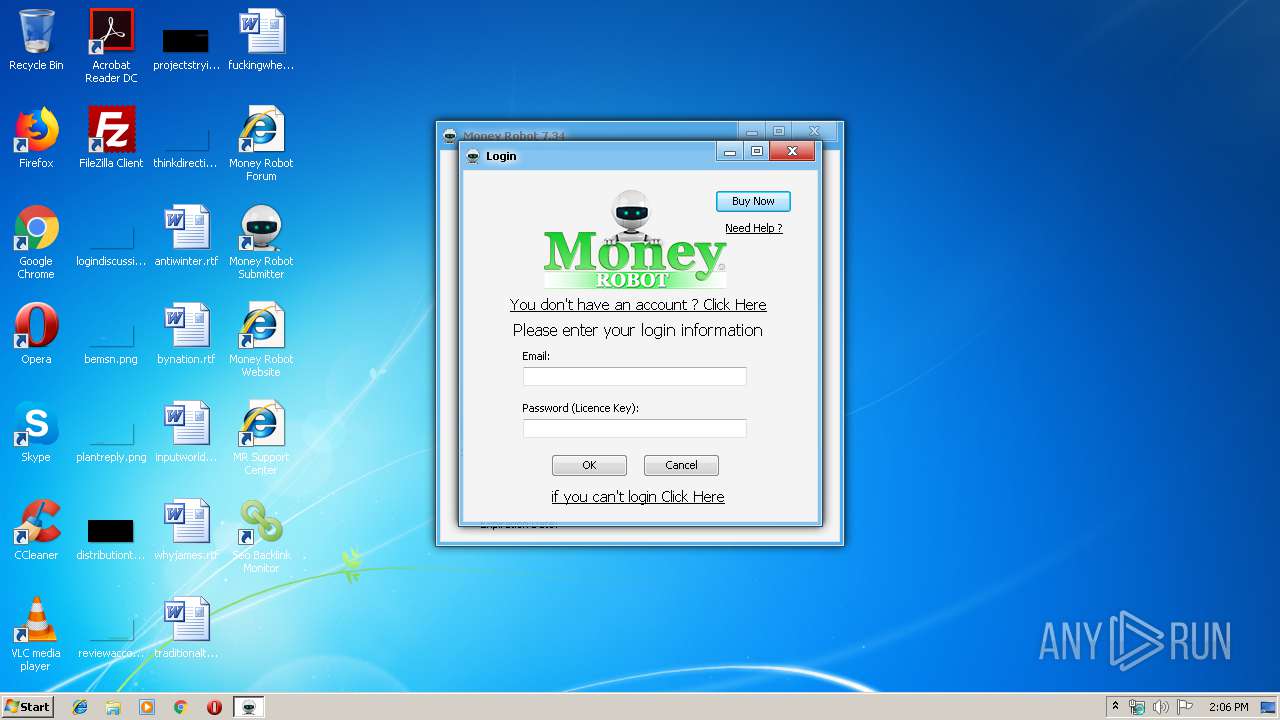
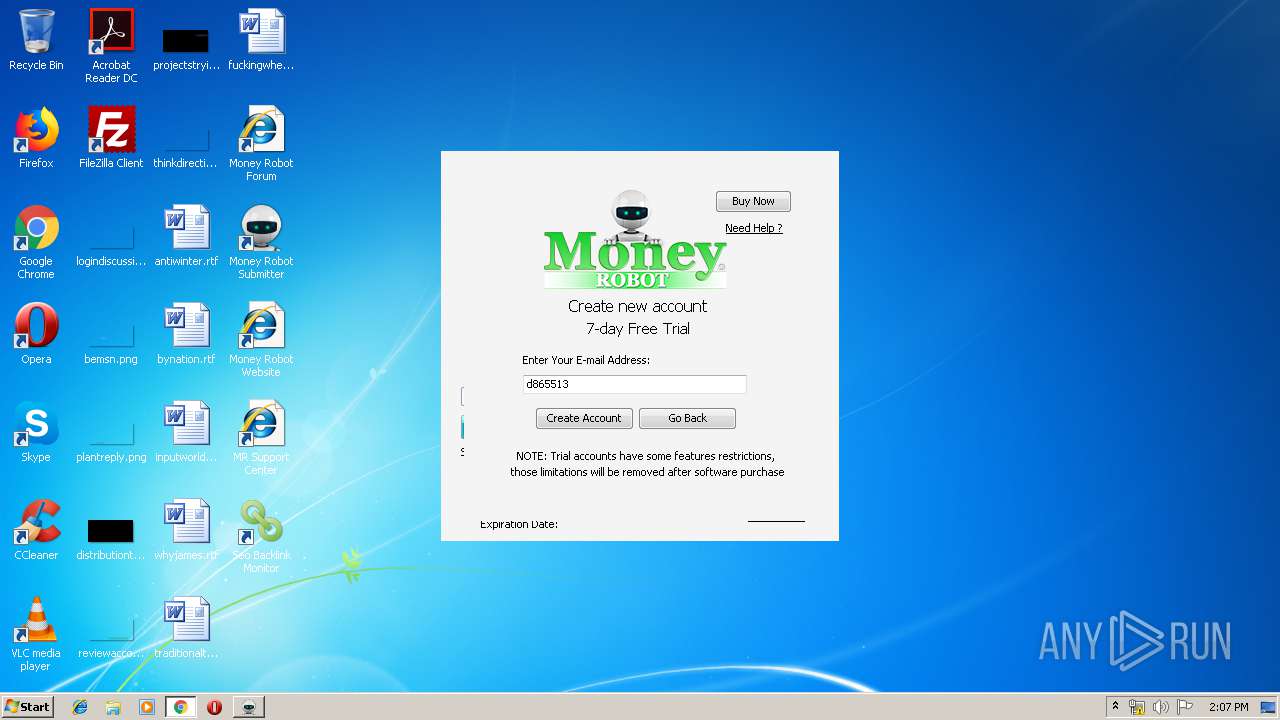
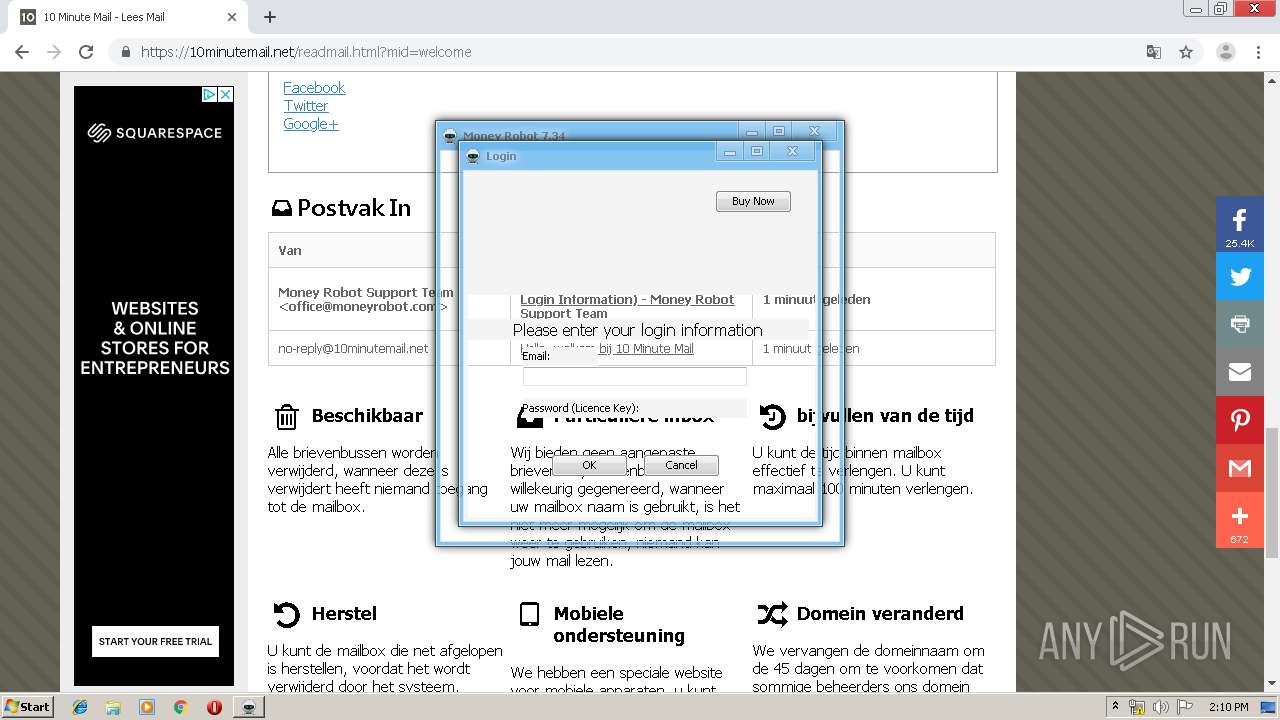
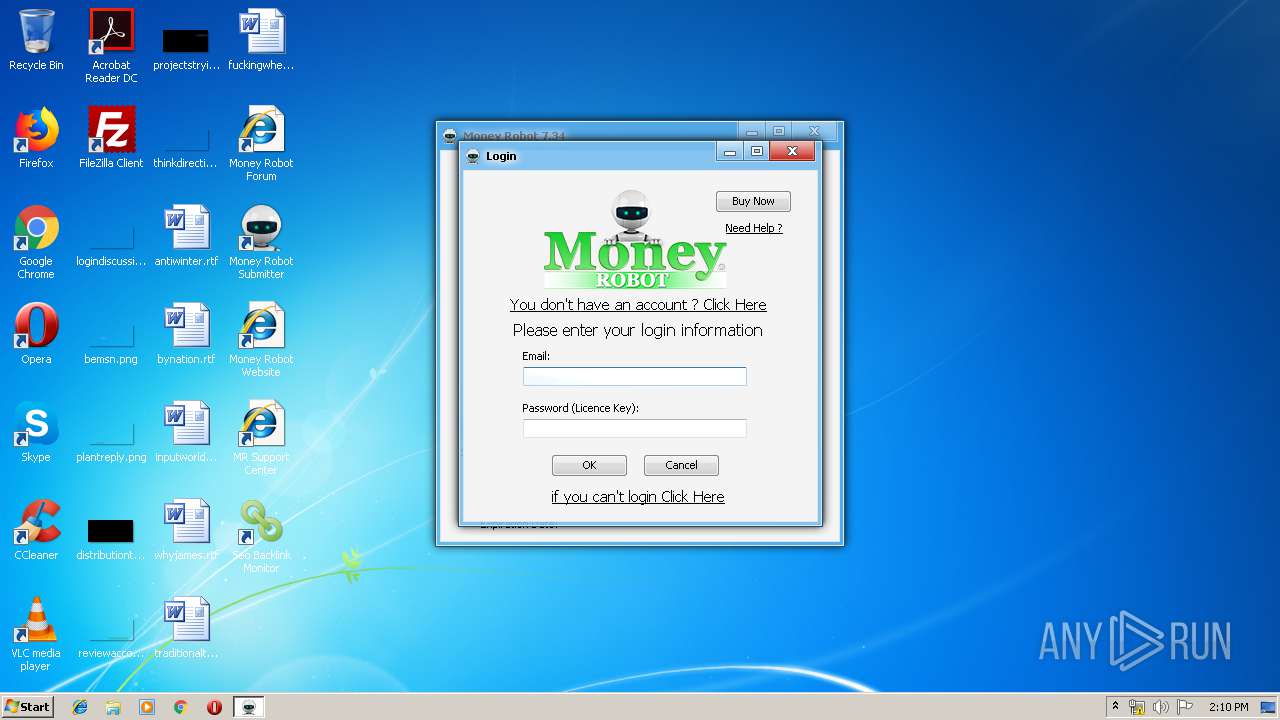
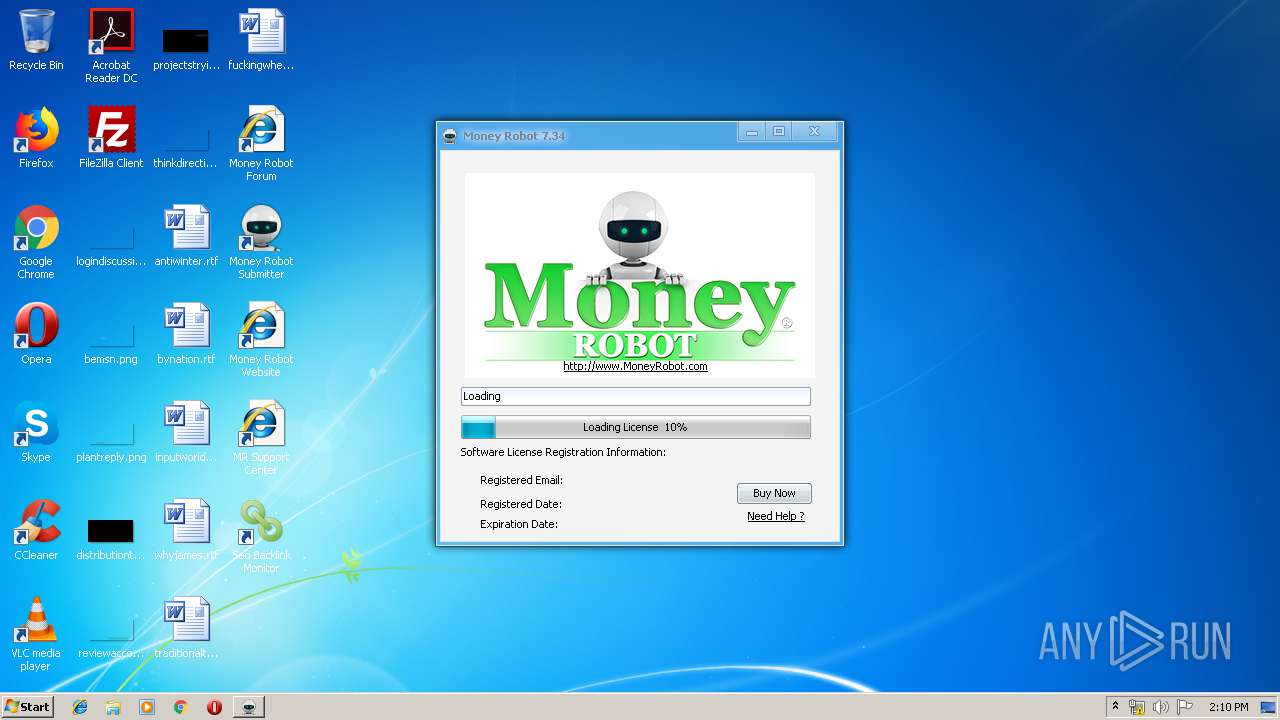
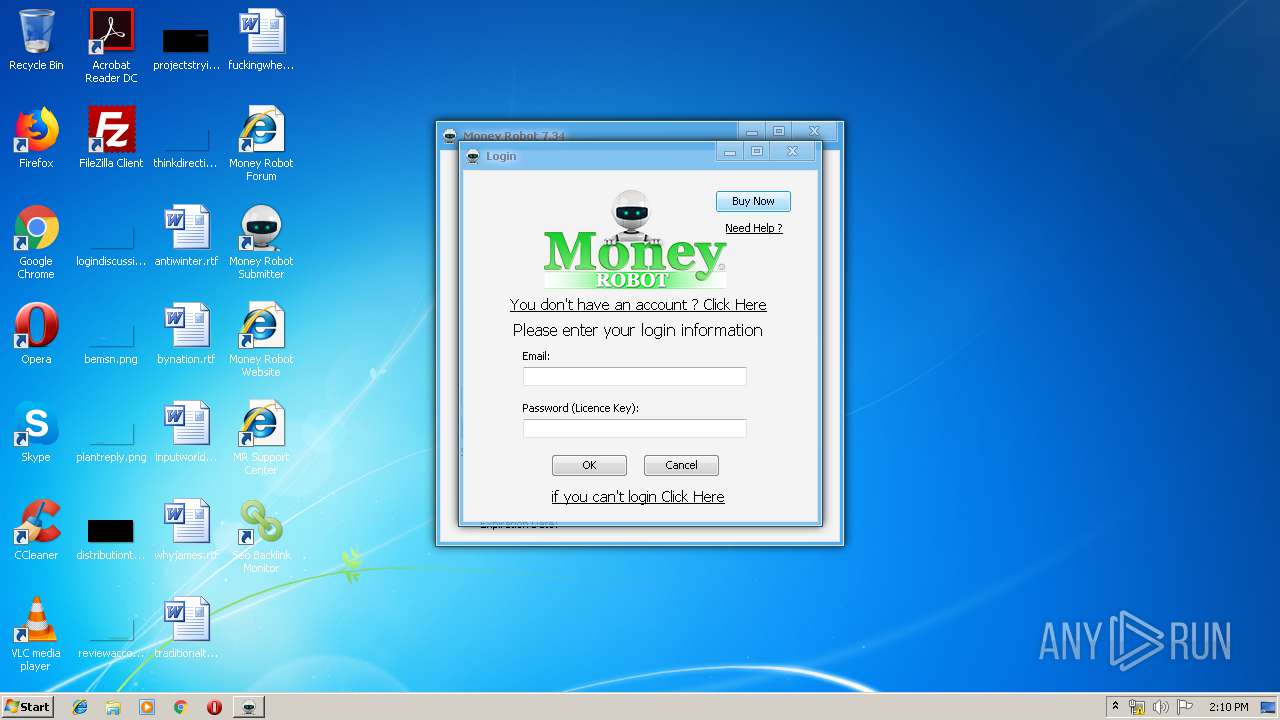
| Full analysis: | https://app.any.run/tasks/15fad5a6-4f43-4379-ac54-24f001a0f81d |
| Verdict: | Suspicious activity |
| Analysis date: | January 21, 2020, 14:05:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ED4E5336687539639BD40B2FAFE3000A |
| SHA1: | E6EC5AC1F0DC315C733B45783A1C37AFA14A0A27 |
| SHA256: | 29C88F2DB6DE8D2885F73D2799005B29A7958E42E9C79F791016C5484DCA63B4 |
| SSDEEP: | 98304:y5gj2N1f4q+ye0saDBWrDV70uBegFS1kQdESHEMKbRzk+IKYOIZXeF:zCN52yeGDBWrDt5Ho1kQdEPFYyYOIZXW |
MALICIOUS
Application was dropped or rewritten from another process
- MoneyRobot.exe (PID: 1728)
- MoneyRobot.exe (PID: 2688)
SUSPICIOUS
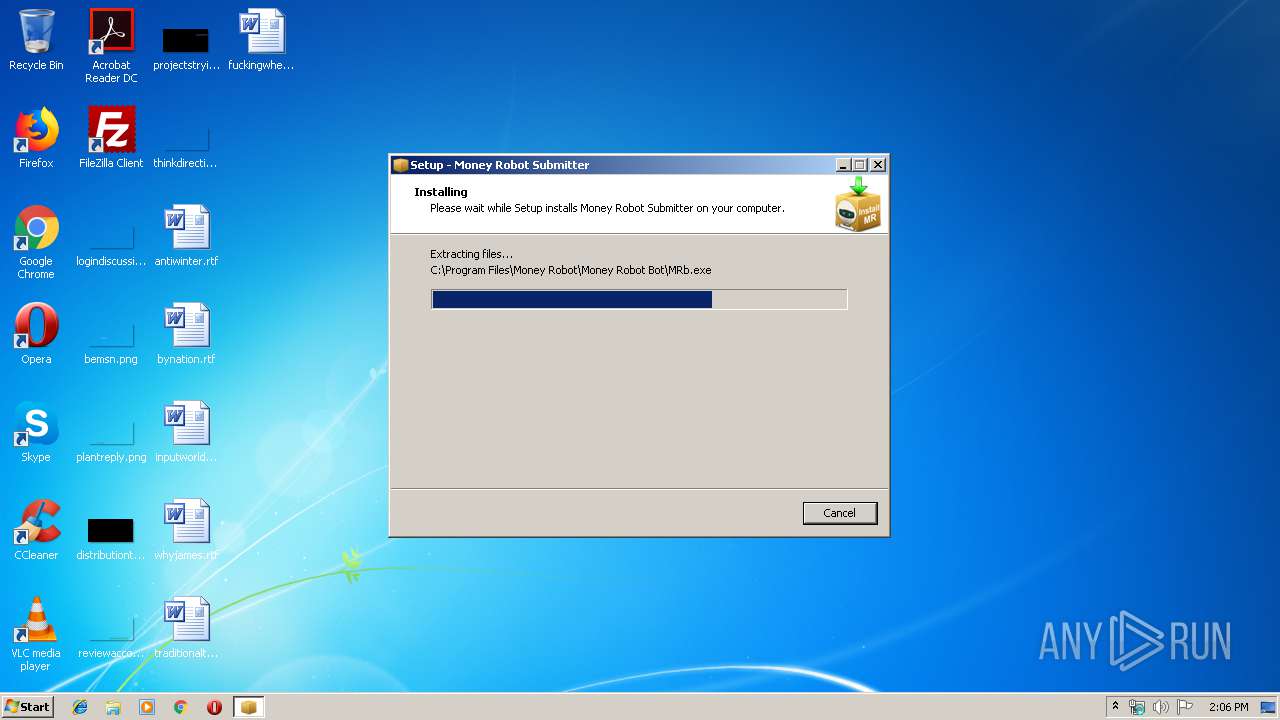
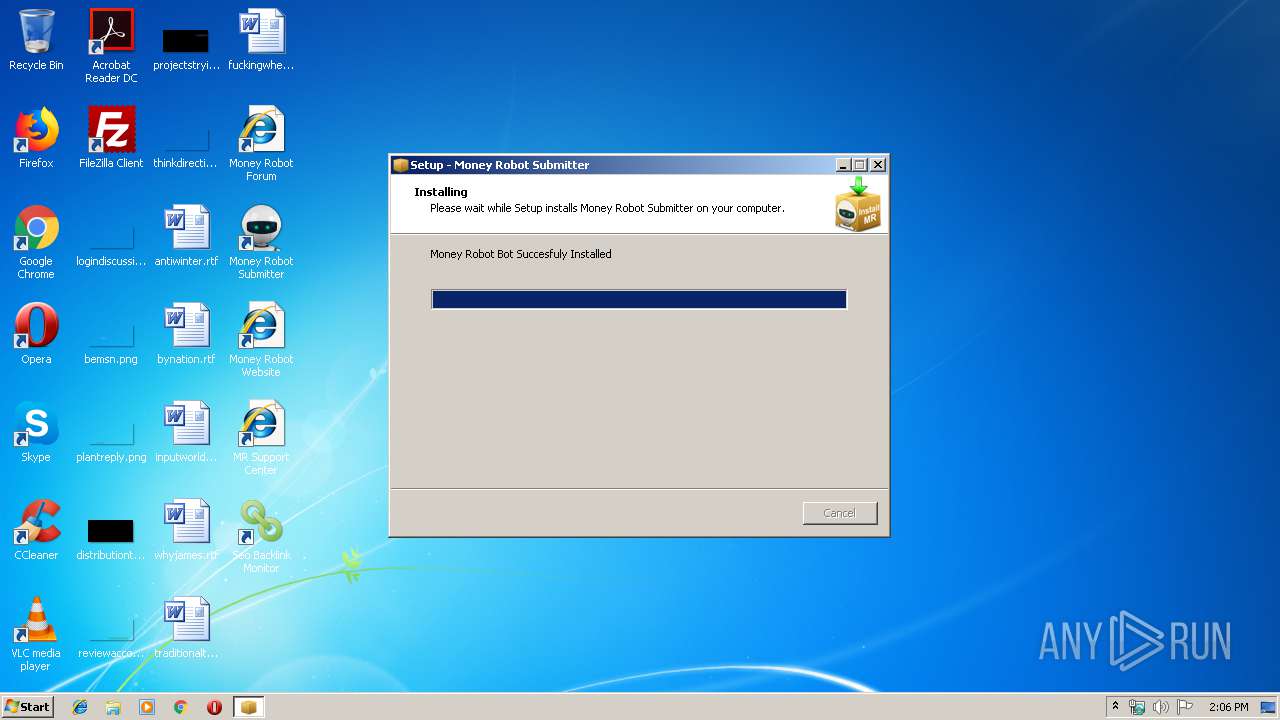
Executable content was dropped or overwritten
- MoneyRobotSetup.exe (PID: 2212)
- MoneyRobotSetup.exe (PID: 3864)
- MoneyRobotSetup.tmp (PID: 504)
Uses NETSH.EXE for network configuration
- MoneyRobotSetup.tmp (PID: 504)
Changes IE settings (feature browser emulation)
- MoneyRobotSetup.tmp (PID: 504)
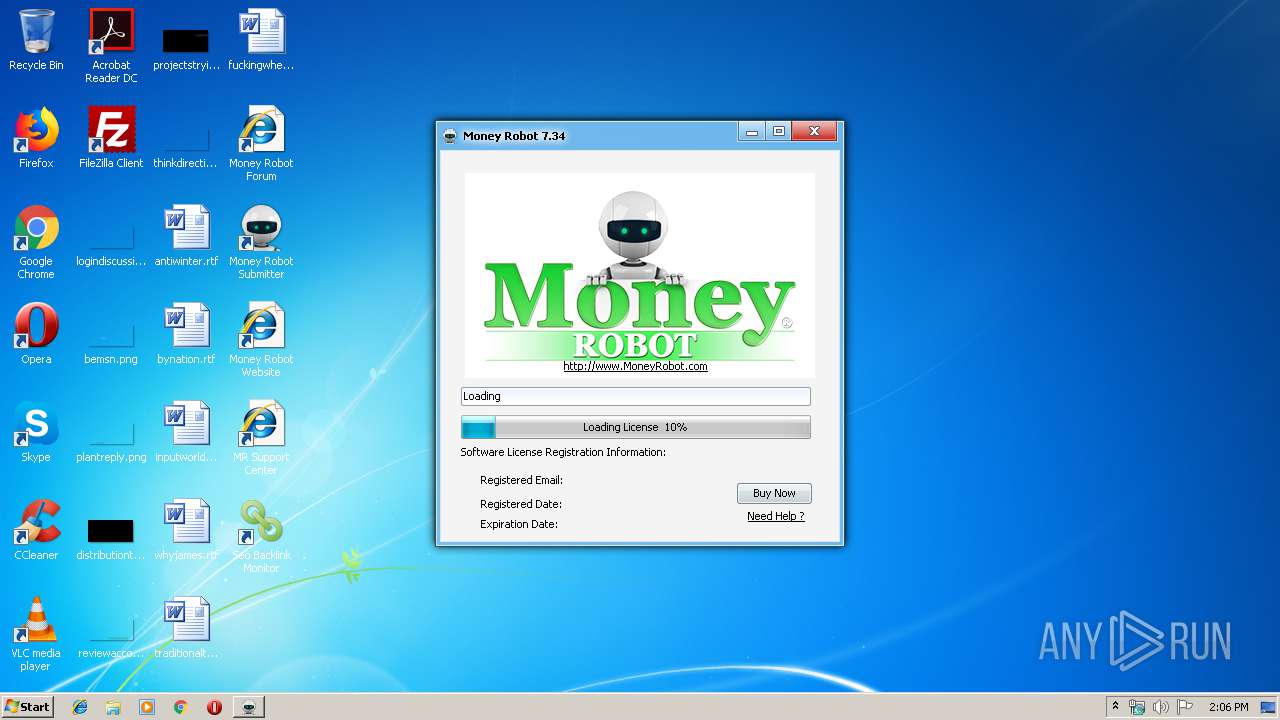
Application launched itself
- MoneyRobot.exe (PID: 1728)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1600)
INFO
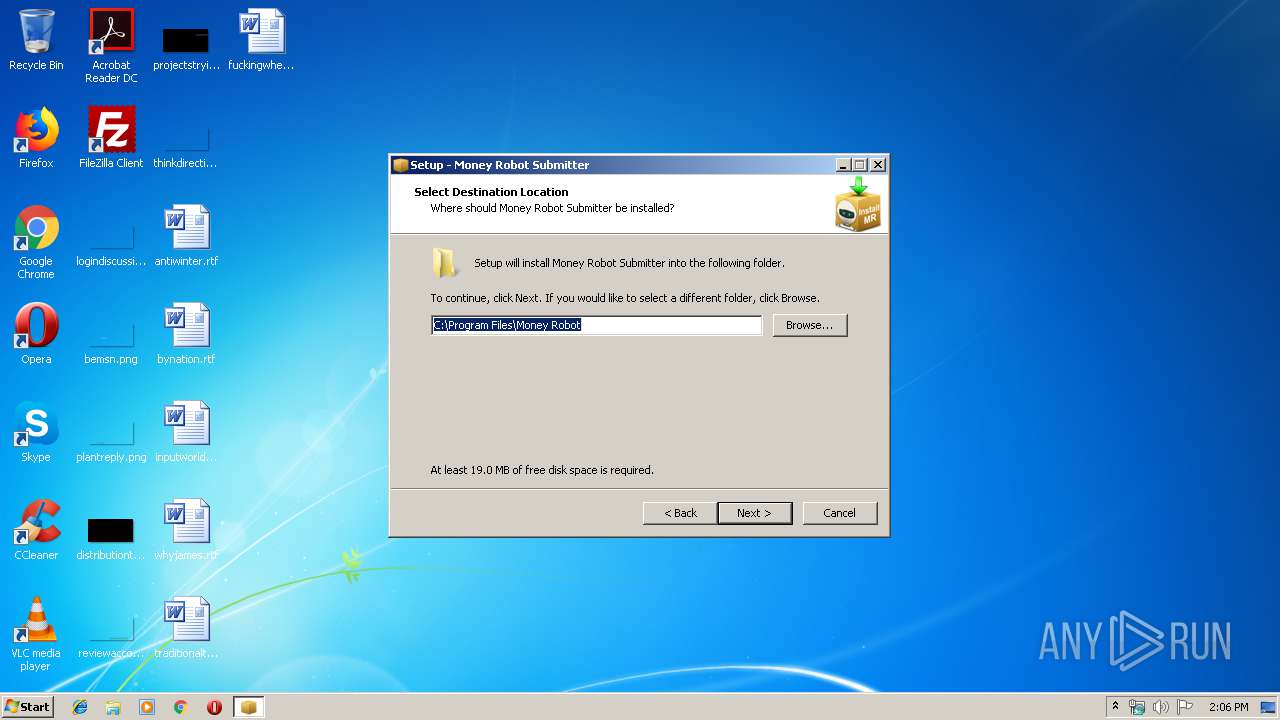
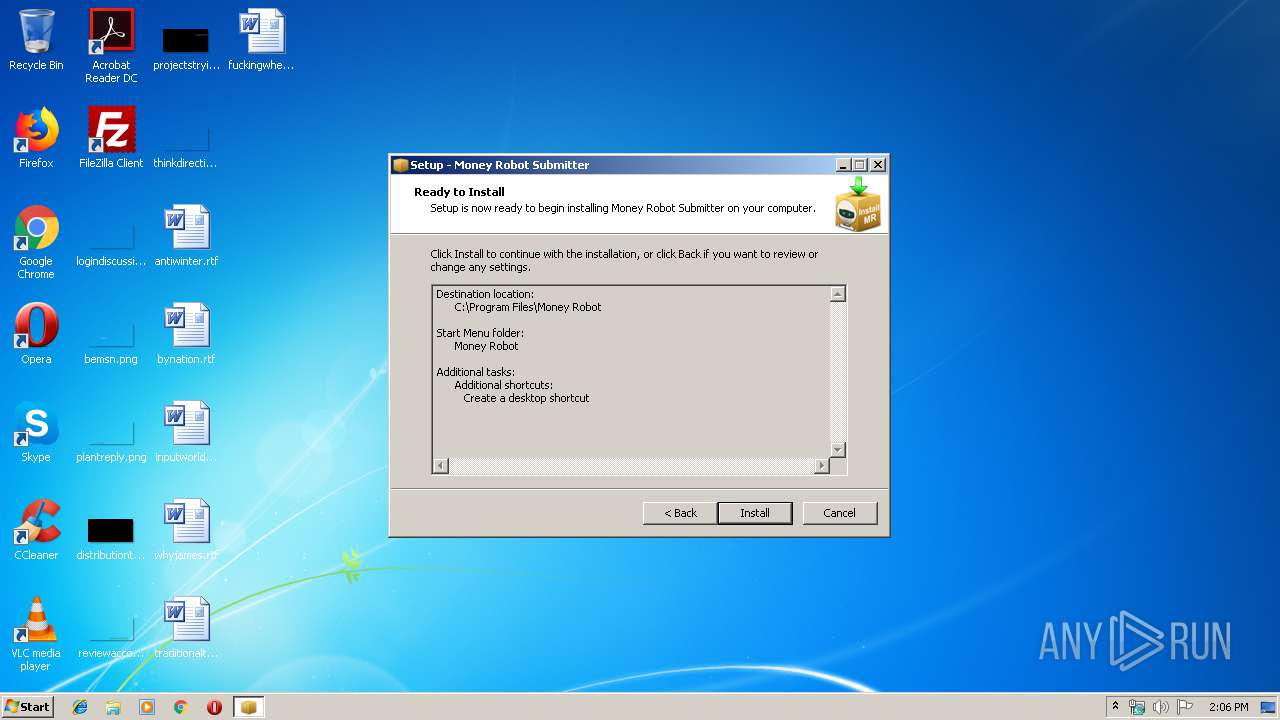
Creates files in the program directory
- MoneyRobotSetup.tmp (PID: 504)
Application was dropped or rewritten from another process
- MoneyRobotSetup.tmp (PID: 3400)
- MoneyRobotSetup.tmp (PID: 504)
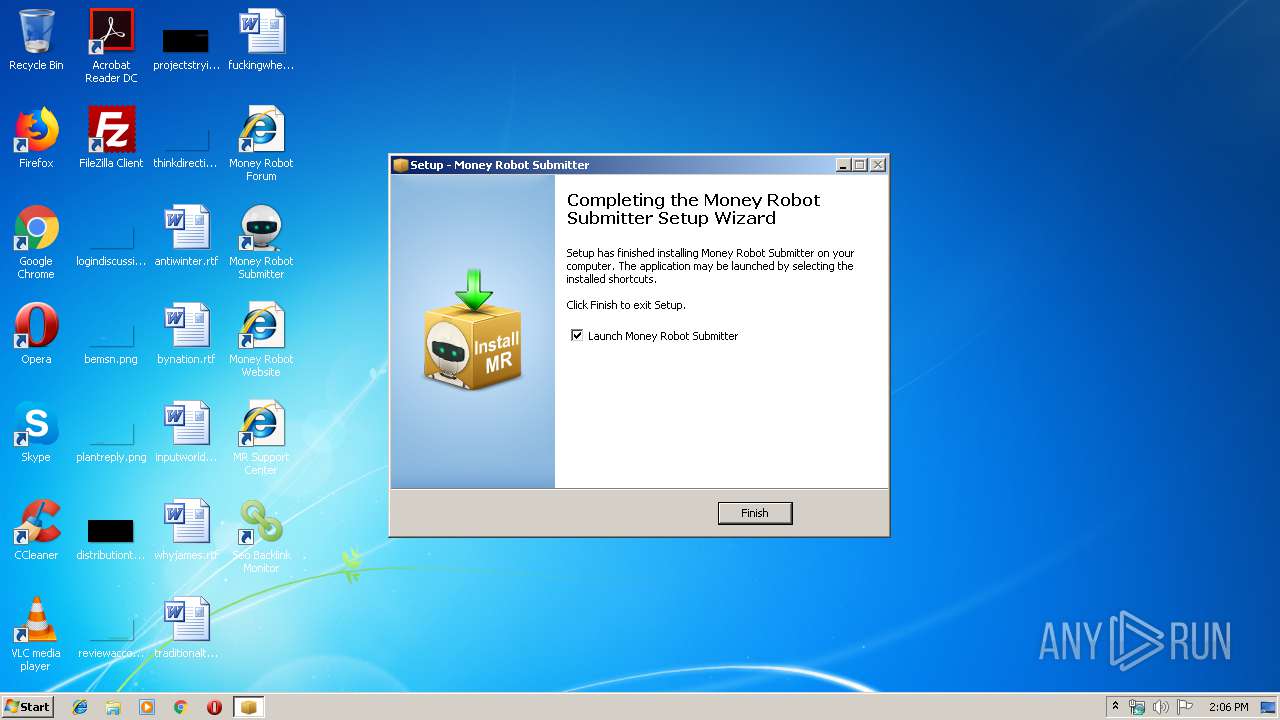
Creates a software uninstall entry
- MoneyRobotSetup.tmp (PID: 504)
Reads the hosts file
- chrome.exe (PID: 1600)
- chrome.exe (PID: 3960)
Reads settings of System Certificates
- chrome.exe (PID: 3960)
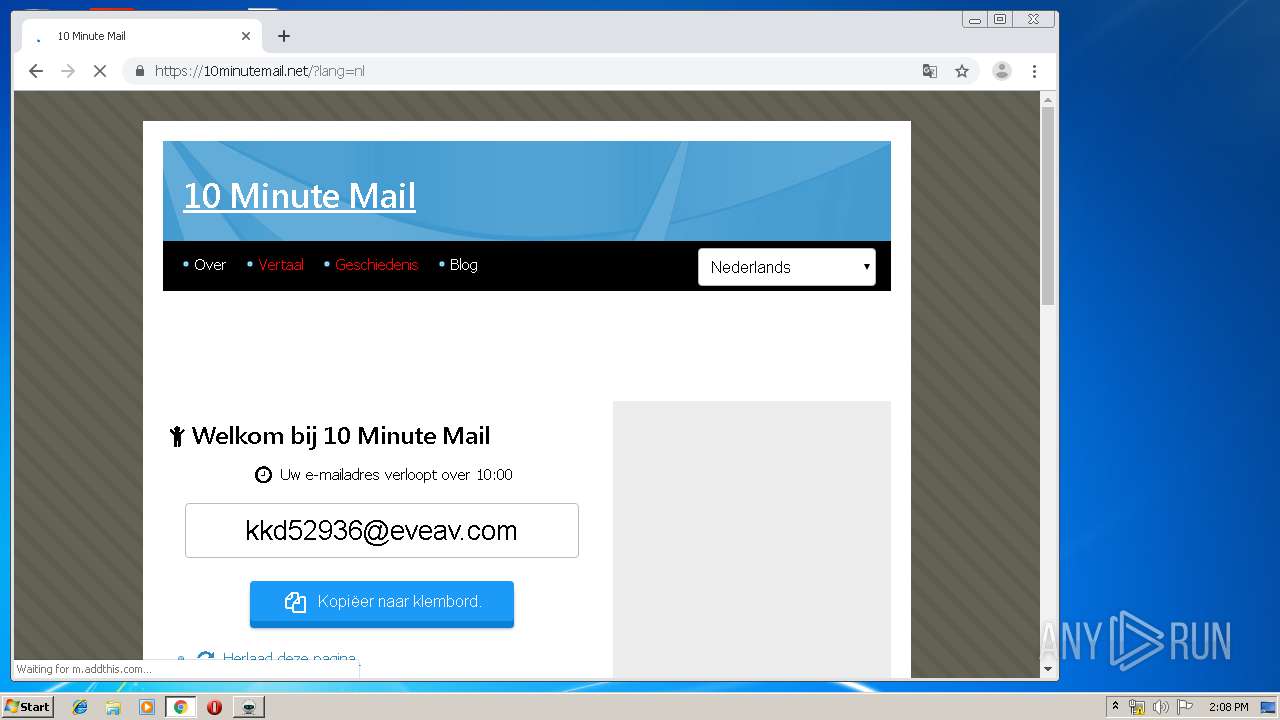
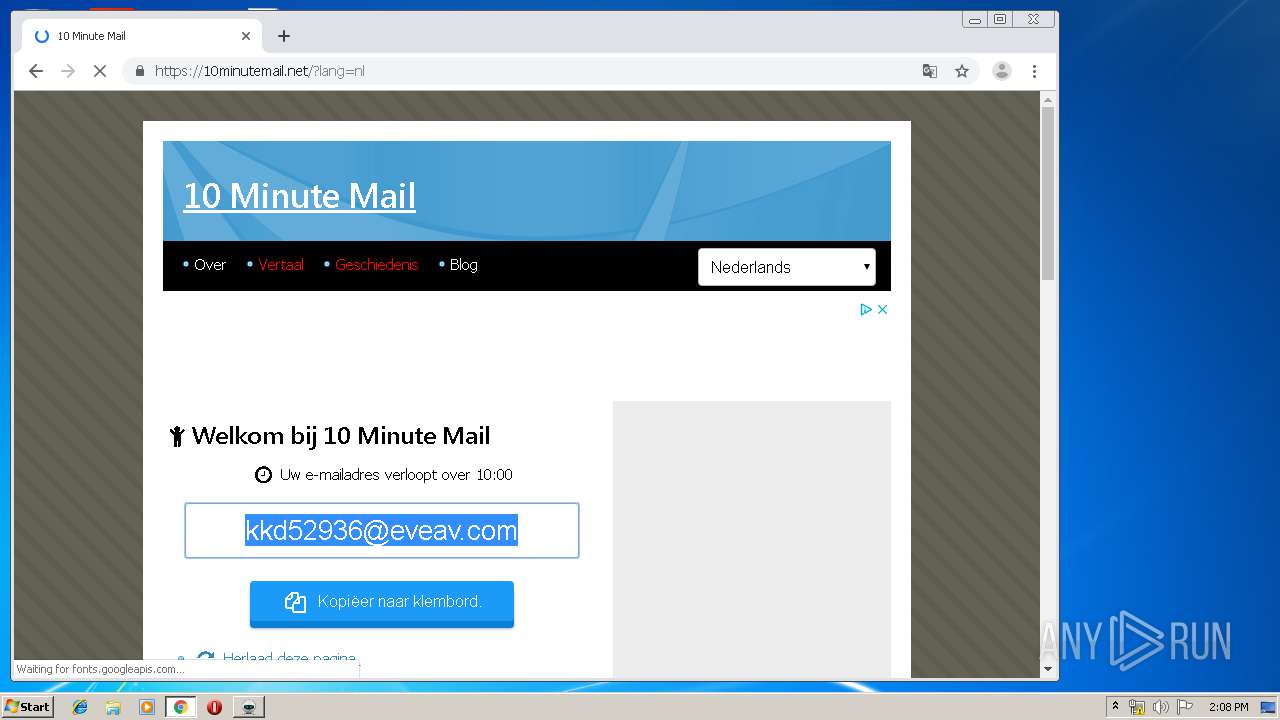
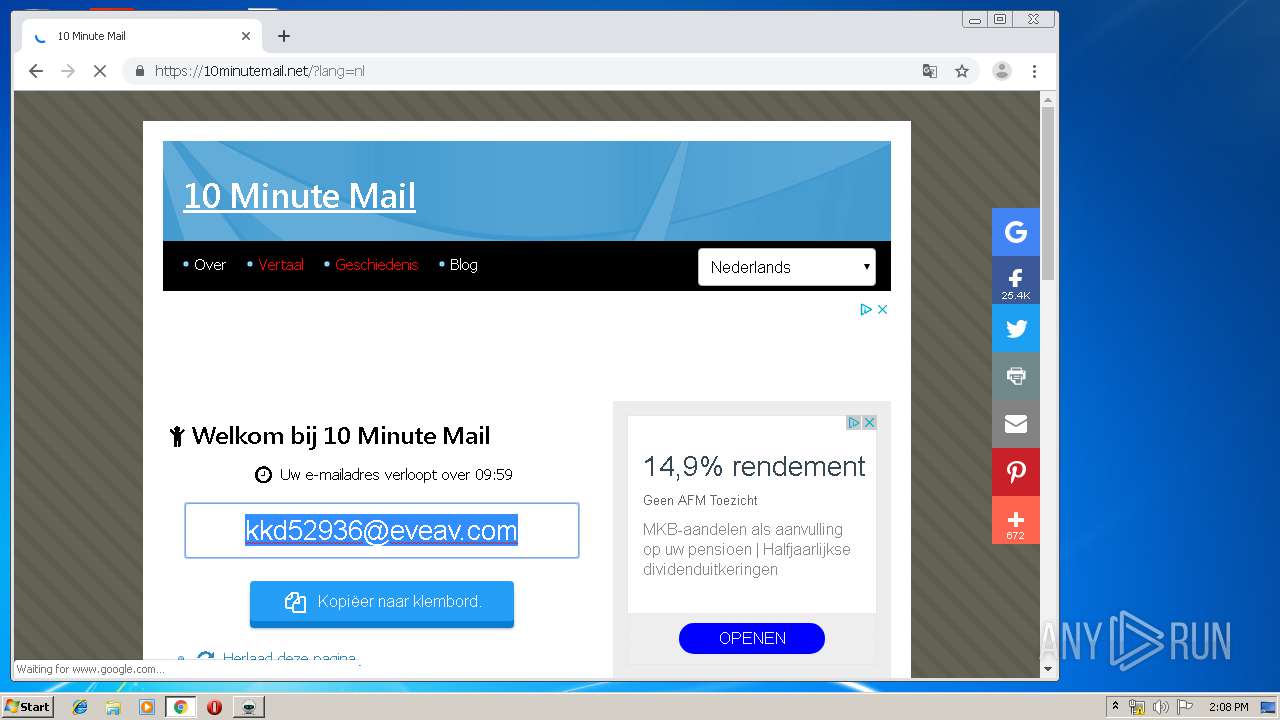
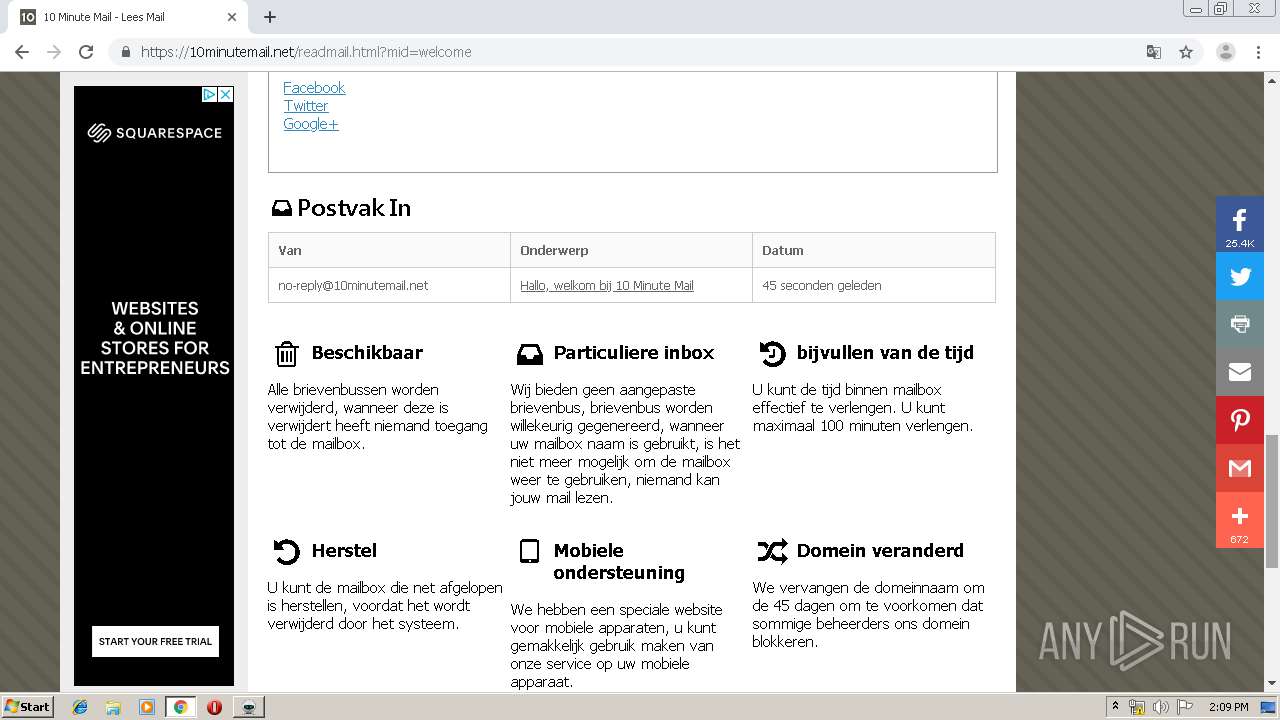
Manual execution by user
- chrome.exe (PID: 1600)
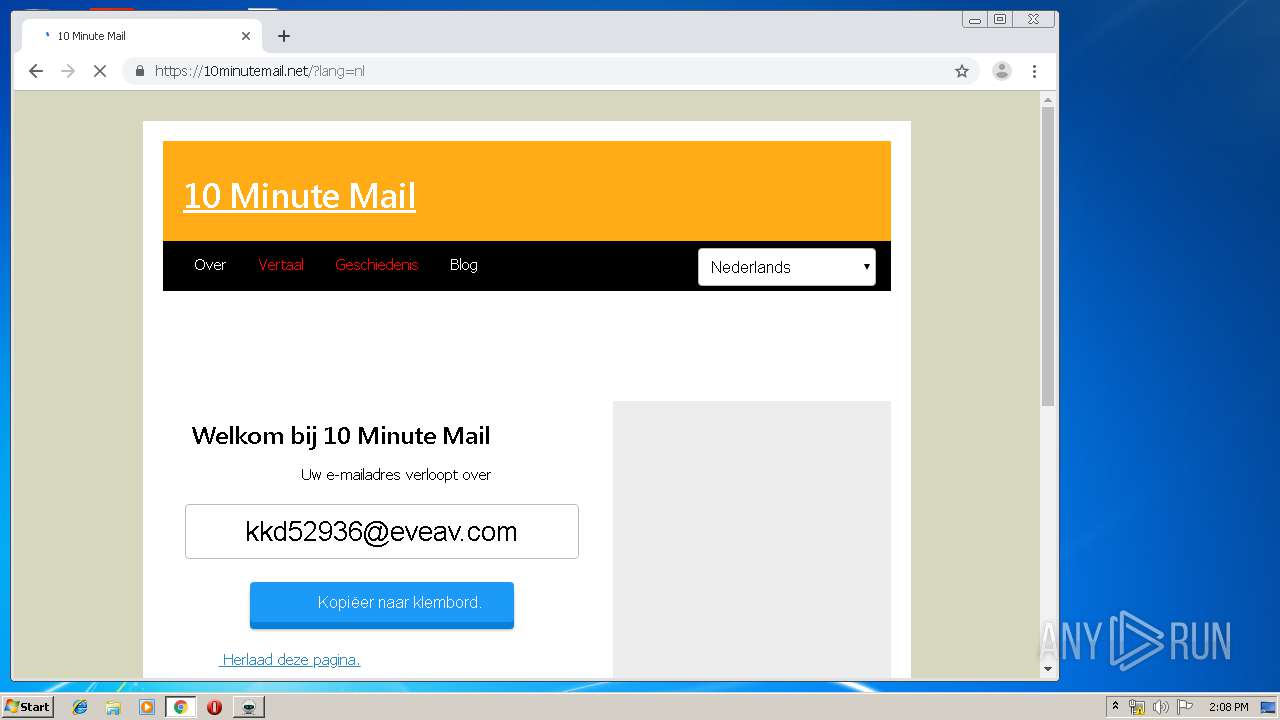
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1600)
Changes settings of System certificates
- chrome.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 1600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (62.3) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (23.6) |
| .exe | | | Win32 Executable Delphi generic (8) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 136704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
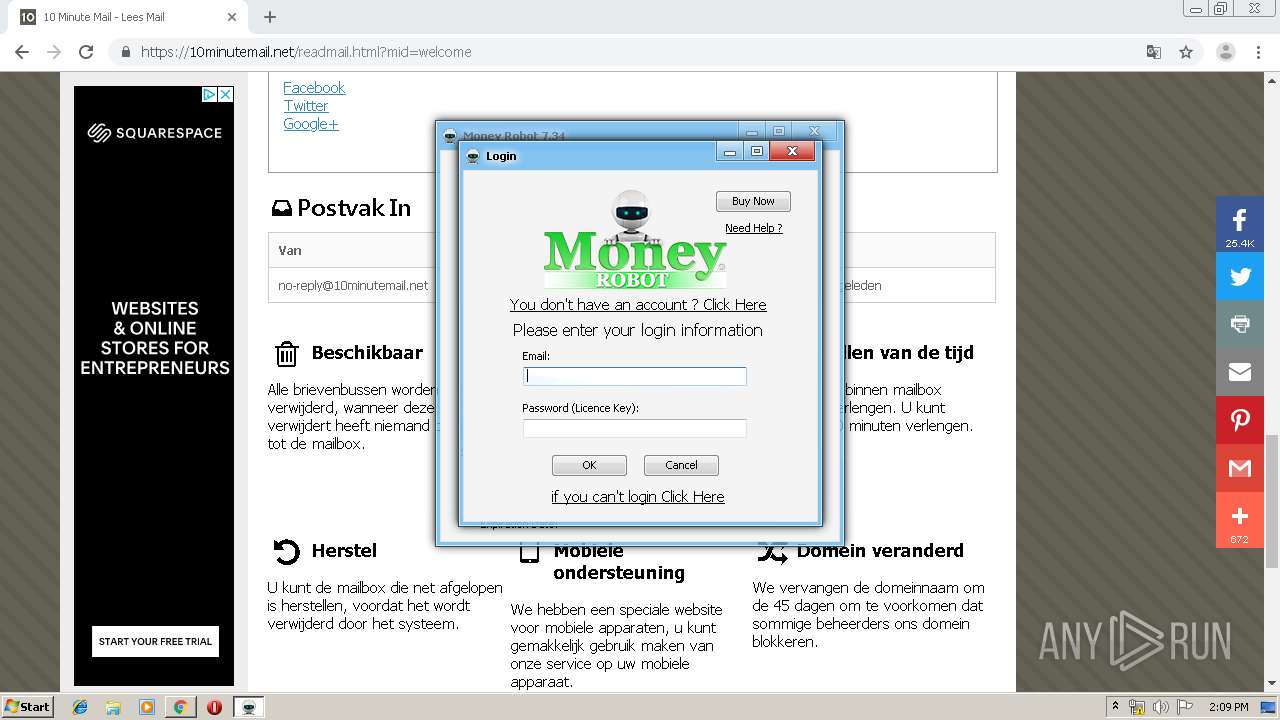
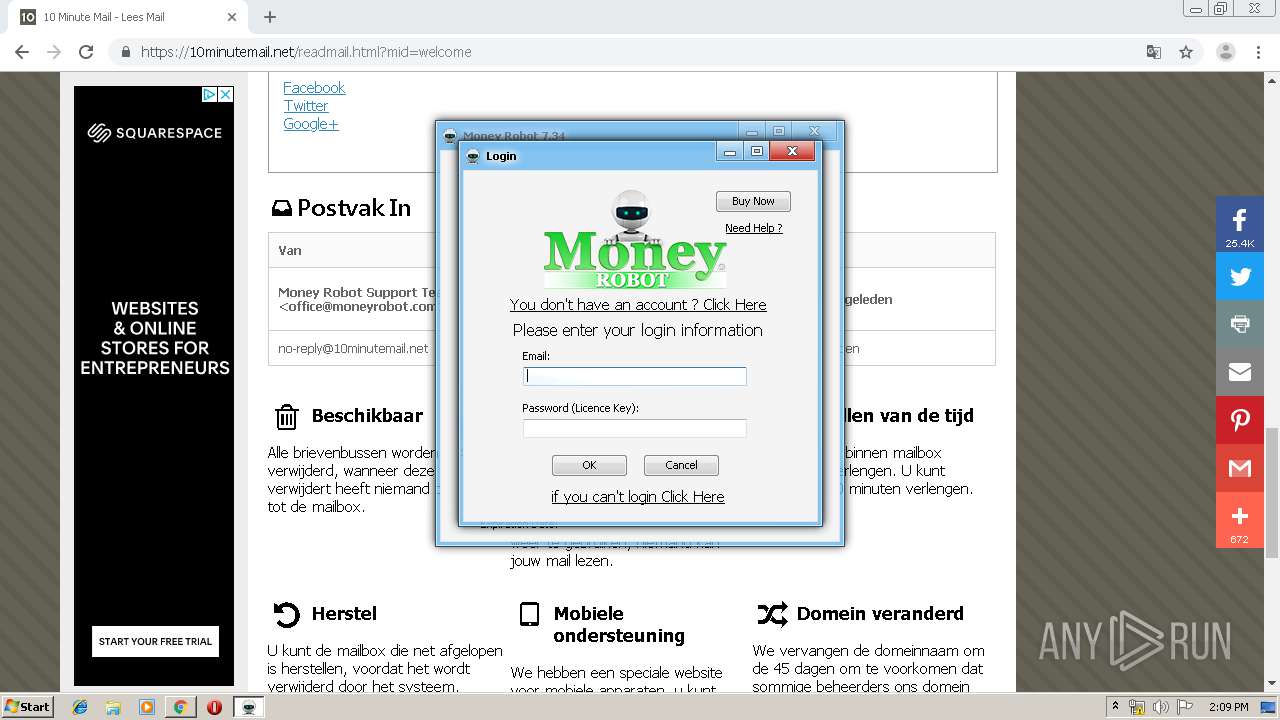
| CompanyName: | Money Robot srl LTD |
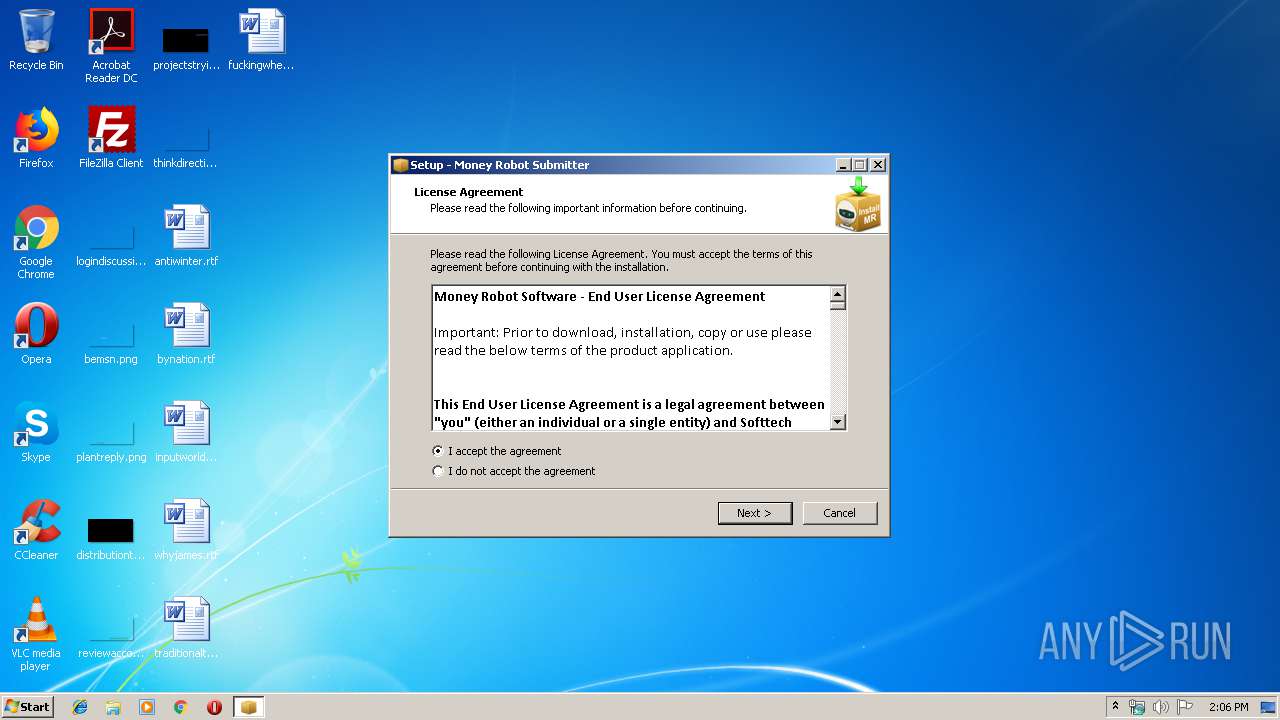
| FileDescription: | Money Robot Submitter Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Money Robot Submitter |
| ProductVersion: | 7.34.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Money Robot srl LTD |
| FileDescription: | Money Robot Submitter Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Money Robot Submitter |
| ProductVersion: | 7.34.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x0002042C | 0x00020600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.38572 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.28989 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.57142 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.78965 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.83981 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.36534 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.24533 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
105
Monitored processes
63
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8982661817872190579 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14677104271962557272 --mojo-platform-channel-handle=2220 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18409253122548525815 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16776586722733820032 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Users\admin\AppData\Local\Temp\is-8CH3F.tmp\MoneyRobotSetup.tmp" /SL5="$5012C,5091549,179200,C:\Users\admin\AppData\Local\Temp\MoneyRobotSetup.exe" /SPAWNWND=$40126 /NOTIFYWND=$4013A | C:\Users\admin\AppData\Local\Temp\is-8CH3F.tmp\MoneyRobotSetup.tmp | MoneyRobotSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8180569893341183437 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18302411575801822171 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6255082027086090499 --mojo-platform-channel-handle=3536 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13705120136117432137 --mojo-platform-channel-handle=4332 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,482817757363318740,1439669495286525207,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13817002297821260516 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 494
Read events
1 177
Write events
305
Delete events
12
Modification events
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F8010000D2FF76F663D0D501 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 061C4046B7514EF95B64A3ADC842DC354229FFDD34726AC93D0B86877CE89115 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Money Robot\Money Robot Submitter\MoneyRobot.exe | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 7380DD34A984AB8871B42C5321091DB623916E444E252A52B12BA49A0C26DDF0 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\MAIN\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | MRb.exe |
Value: 11000 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\MAIN\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | MoneyRobot.exe |
Value: 11000 | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D8331B58-377C-4350-B879-21133B050E19}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D8331B58-377C-4350-B879-21133B050E19}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Money Robot | |||
| (PID) Process: | (504) MoneyRobotSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D8331B58-377C-4350-B879-21133B050E19}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Money Robot\ | |||
Executable files
8
Suspicious files
207
Text files
419
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\is-7BJ92.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Submitter\is-ARK3G.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Submitter\is-3GJ8T.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Submitter\is-IQUA5.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Bot\is-T49FP.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Seo Backlink Monitor\is-C6D83.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Submitter\is-DM3EU.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Program Files\Money Robot\Money Robot Submitter\Skins\is-8JBJC.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\Users\Public\Desktop\Money Robot Submitter.lnk | lnk | |
MD5:— | SHA256:— | |||
| 504 | MoneyRobotSetup.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Money Robot\Money Robot Submitter.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
121
DNS requests
90
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
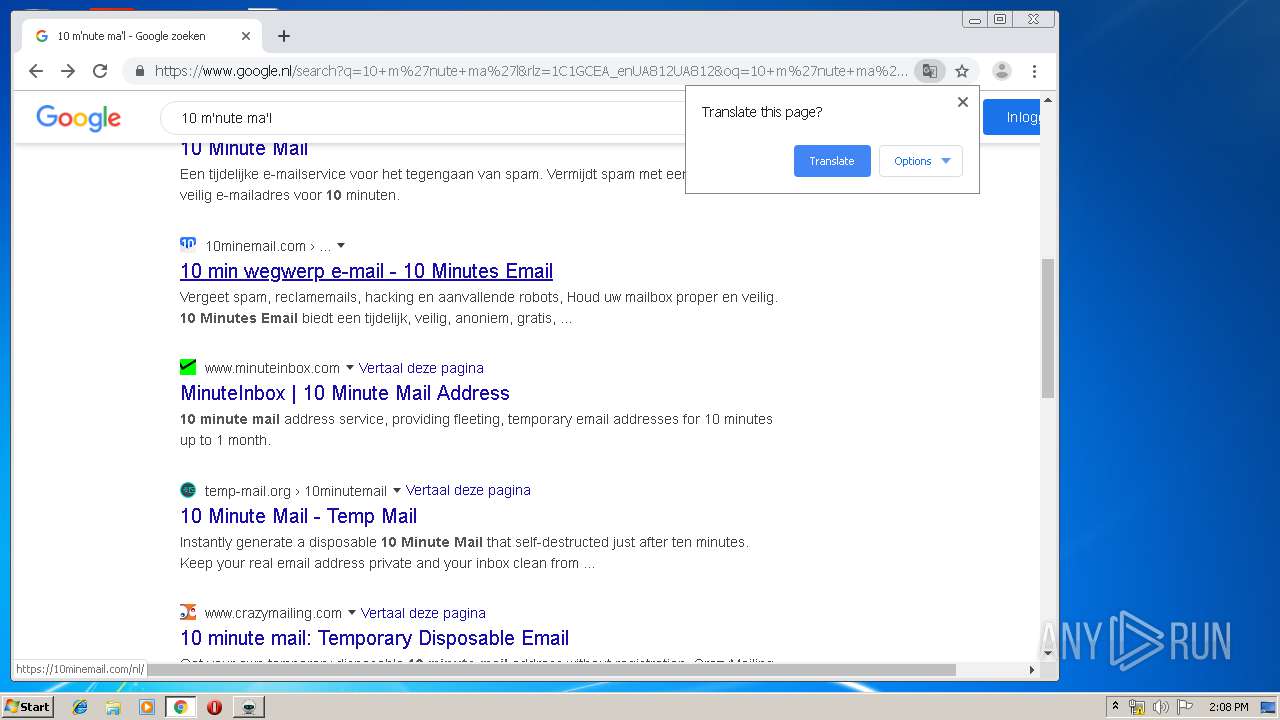
3960 | chrome.exe | GET | — | 31.11.33.224:80 | http://www.20minutemail.com/ | IT | — | — | unknown |
3960 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3960 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3960 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
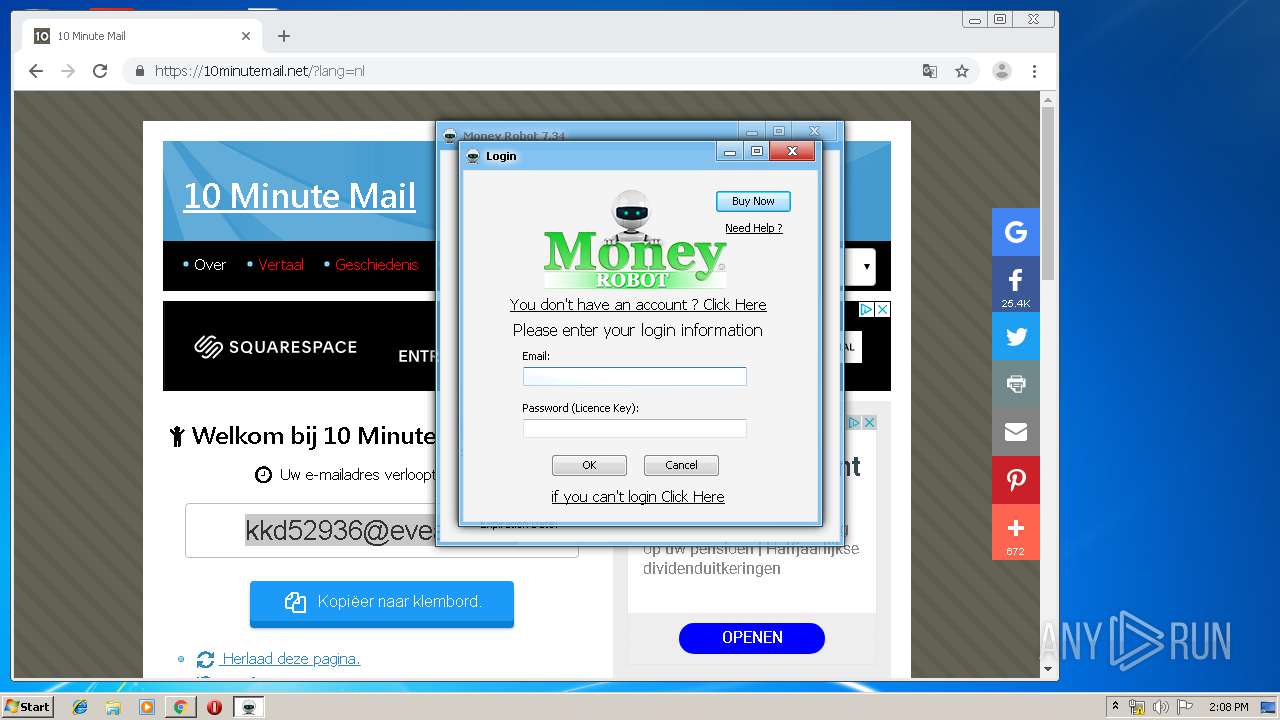
2688 | MoneyRobot.exe | POST | — | 138.229.109.103:80 | http://exe.moneyrobot.com/ | US | — | — | suspicious |
3960 | chrome.exe | GET | 200 | 172.217.132.6:80 | http://r1---sn-5hne6nsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.44.113&mm=28&mn=sn-5hne6nsd&ms=nvh&mt=1579615576&mv=m&mvi=0&pl=27&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3960 | chrome.exe | GET | 200 | 143.204.208.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3960 | chrome.exe | GET | 200 | 8.248.119.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
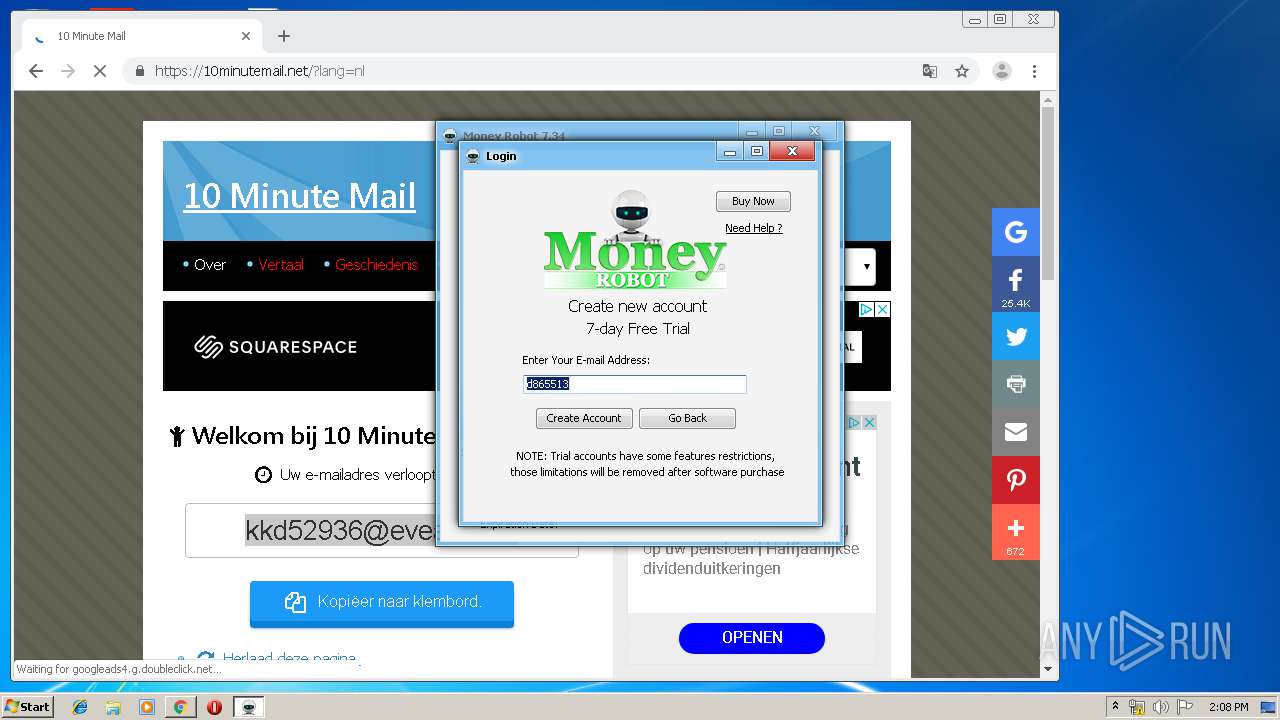
1728 | MoneyRobot.exe | POST | — | 138.229.109.103:80 | http://exe.moneyrobot.com/ | US | — | — | suspicious |
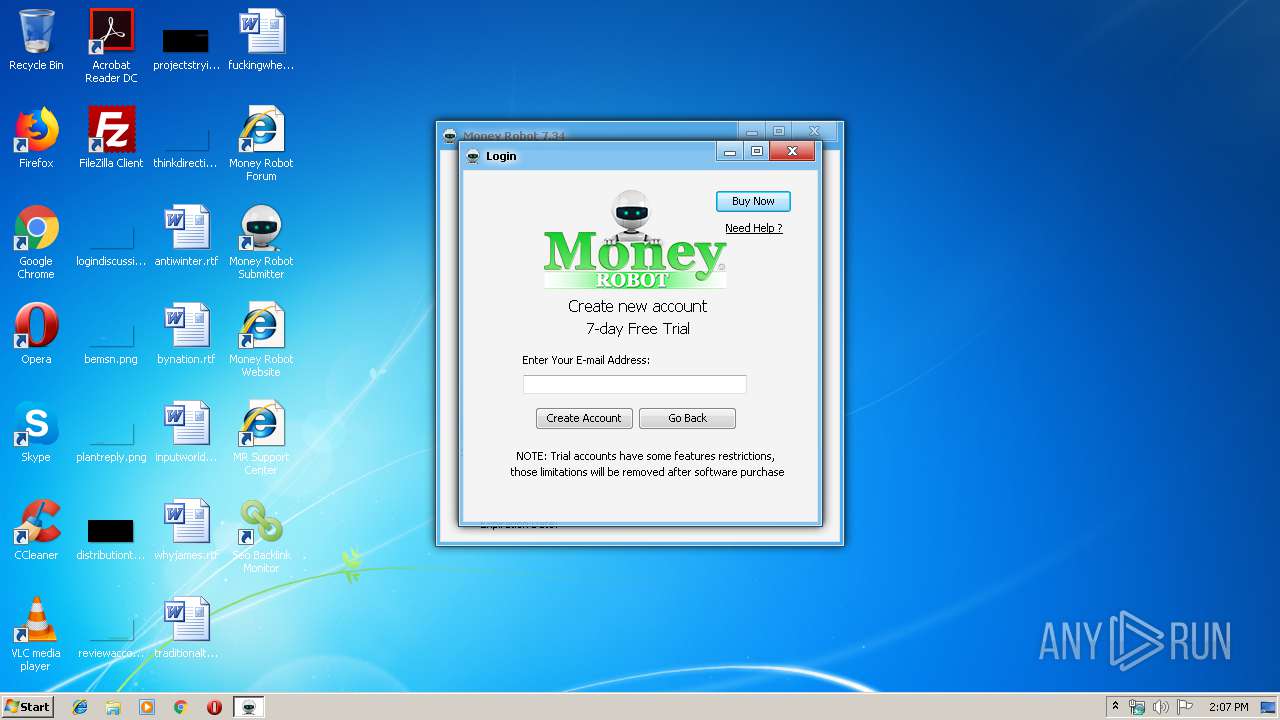
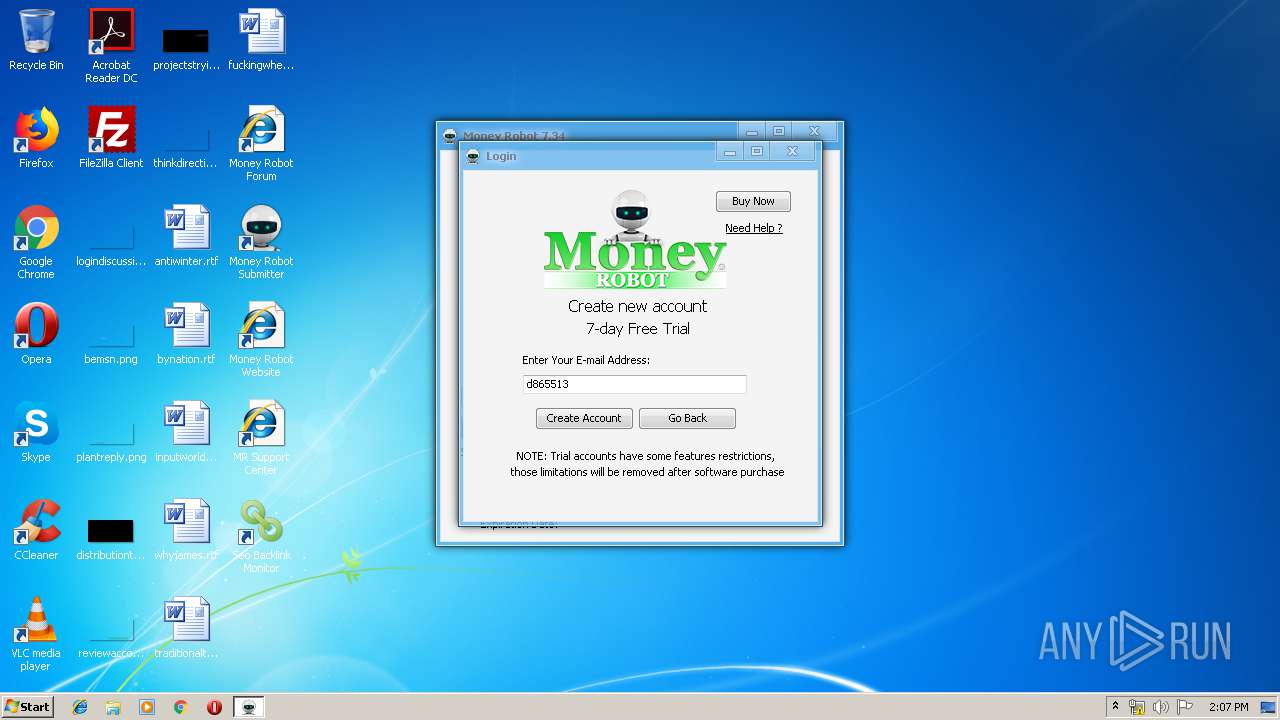
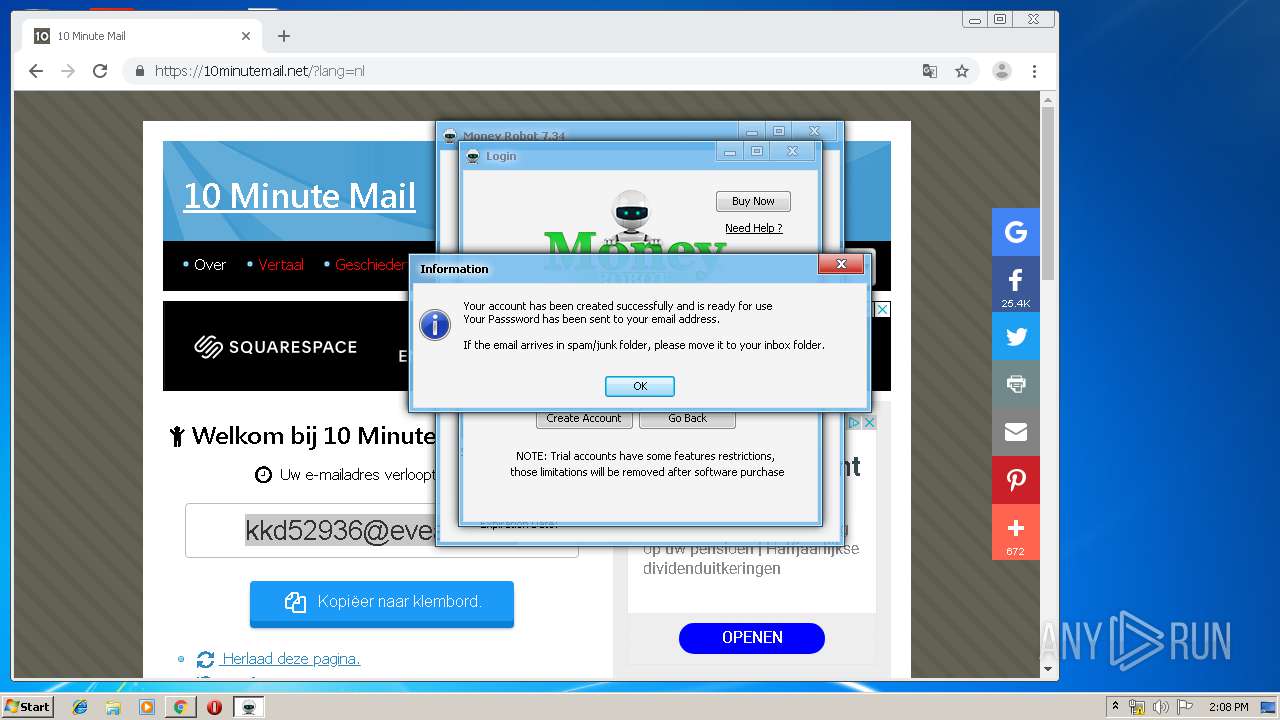
1728 | MoneyRobot.exe | POST | — | 138.229.109.103:80 | http://exe.moneyrobot.com/Create_New_Trial_Account.php | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1728 | MoneyRobot.exe | 138.229.109.103:80 | exe.moneyrobot.com | SUBRIGO CORPORATION | US | suspicious |
3960 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 216.239.32.117:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.142:443 | consent.google.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.132.6:80 | r1---sn-5hne6nsd.gvt1.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.16.202:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exe.moneyrobot.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
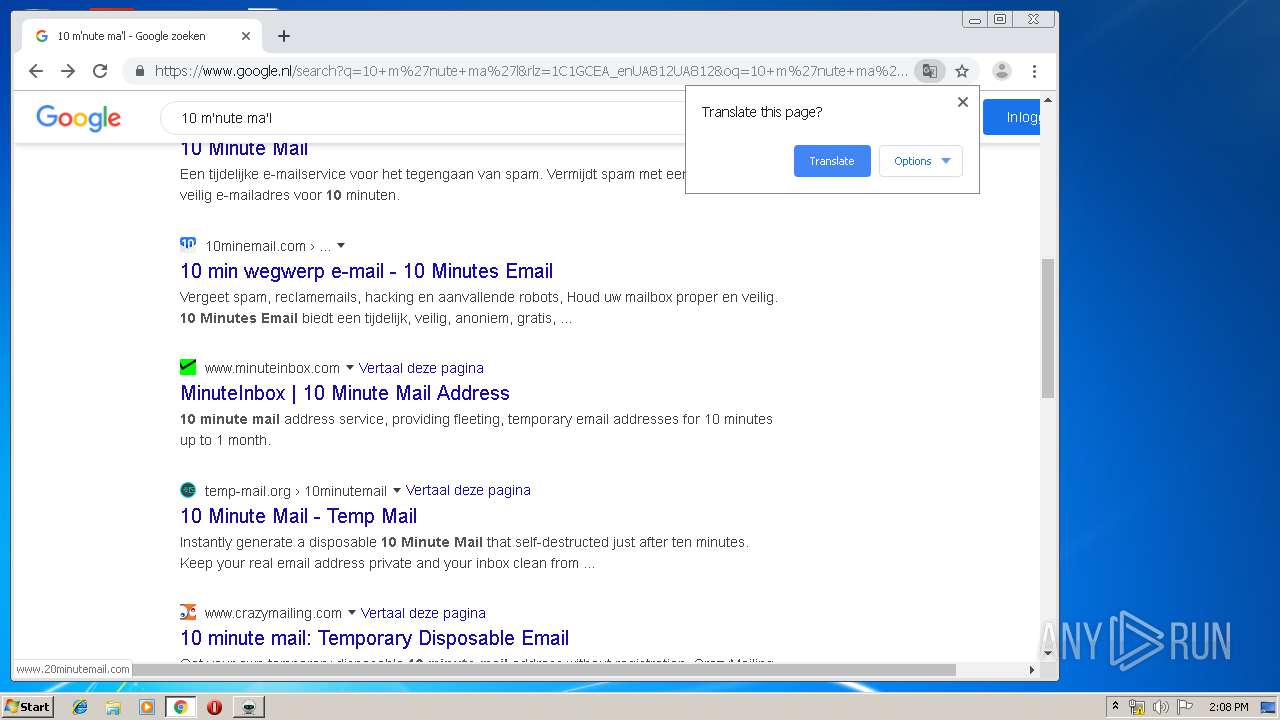
www.google.nl |
| whitelisted |
www.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1728 | MoneyRobot.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |
2688 | MoneyRobot.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |