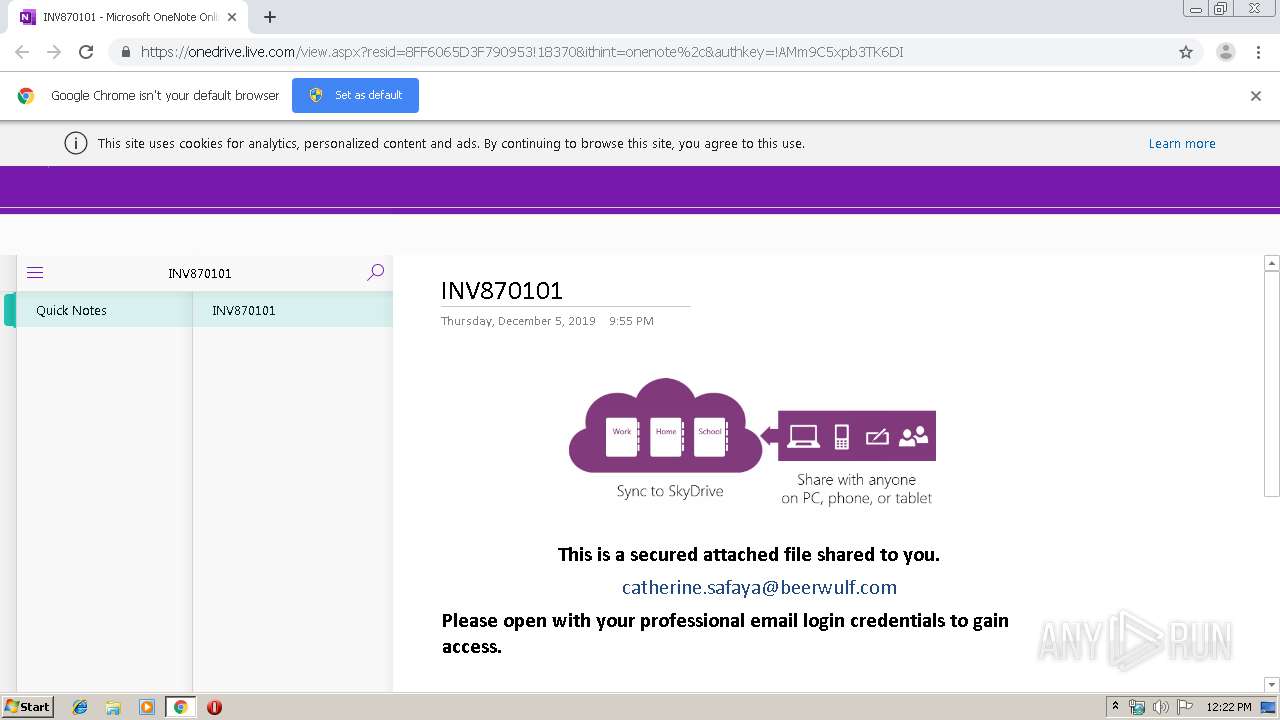
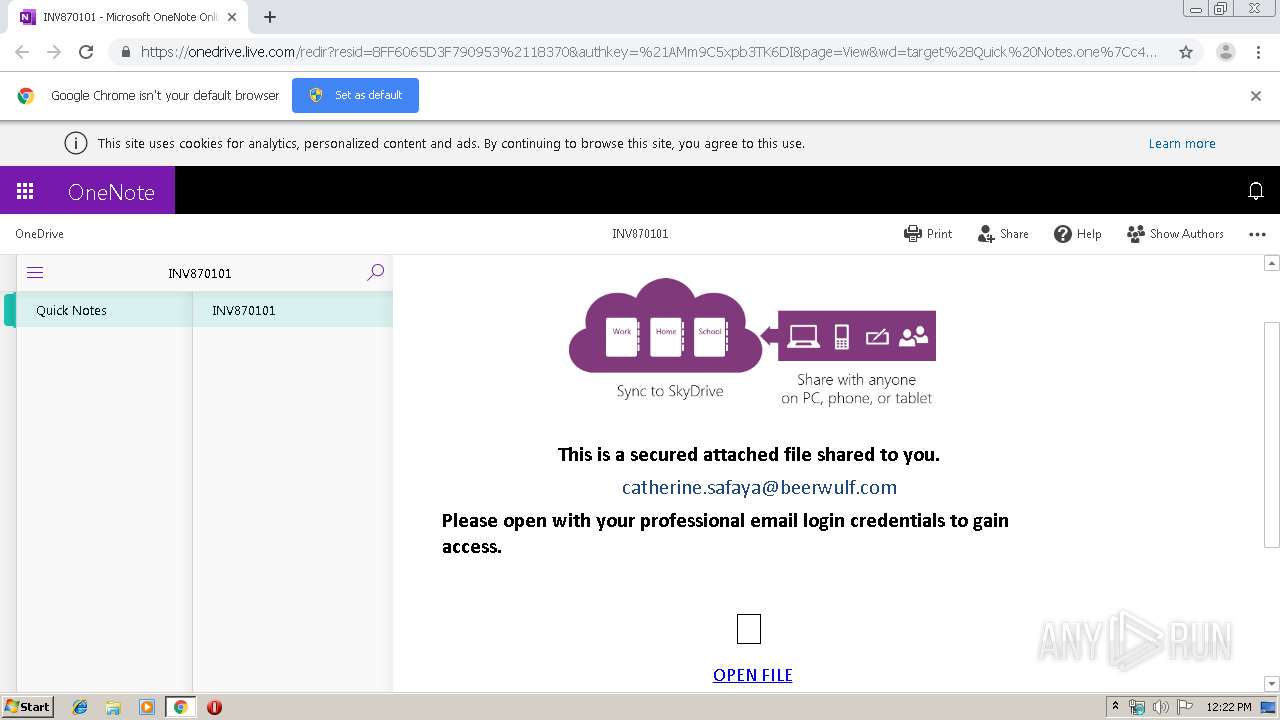
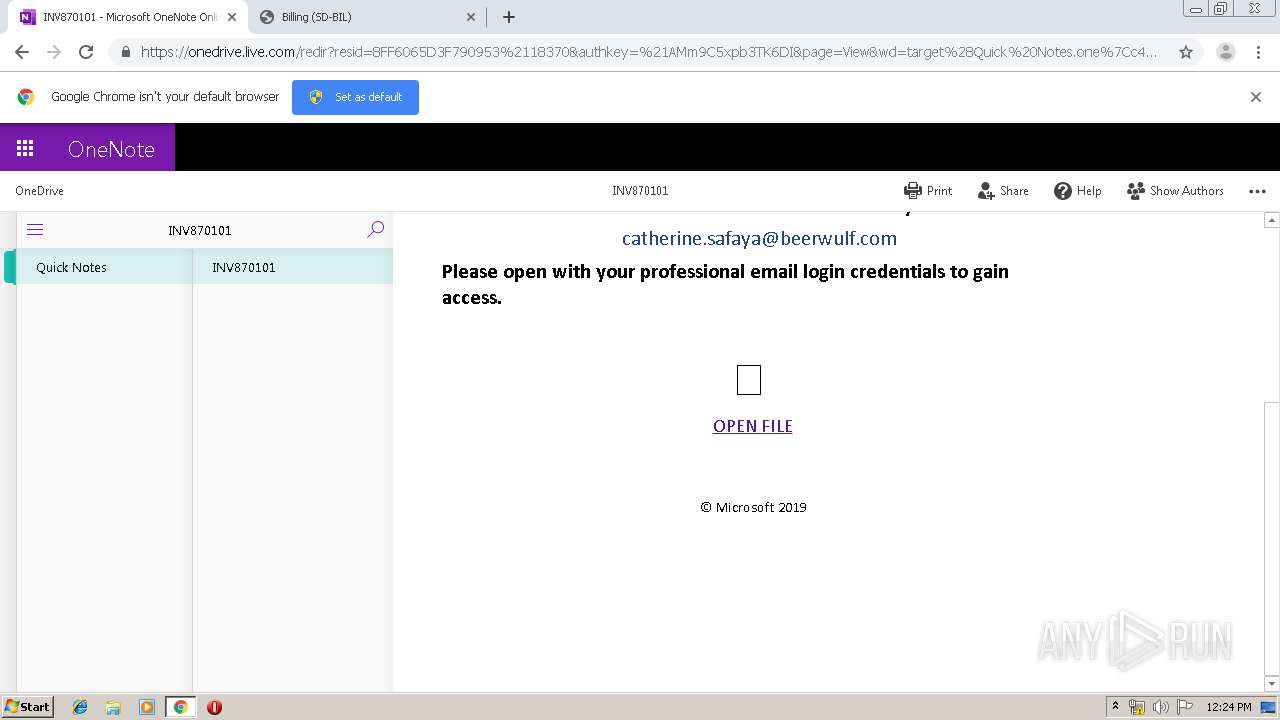
| URL: | Https://1drv.ms/o/s!AlMJeT9dBvaPgY9Cyb0LnGlvdMroMg |
| Full analysis: | https://app.any.run/tasks/36160204-17c3-4b54-ae47-890052b8432c |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 12:22:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FD929C6DD3D260024FD2B1F7AB5EA005 |
| SHA1: | 870ABB68BC4281AA9E8E16E2E4DD06E849C32782 |
| SHA256: | 299ED09133A10266A9302AD57571357A7BC9313399CCA237542861655320A32B |
| SSDEEP: | 3:nn5DLIWKRBYKI/XgcoXu:n5XgBz0wco+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1944)
INFO
Reads the hosts file
- chrome.exe (PID: 1944)
- chrome.exe (PID: 4000)
Reads settings of System Certificates
- chrome.exe (PID: 4000)
Application launched itself
- chrome.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9444710071512482012 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11581341959556821738 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16858317473658935529 --mojo-platform-channel-handle=3008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16217228598746887897 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17507107535524089210 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18006538910821047578 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1265025556224676493 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3498874799464162662 --mojo-platform-channel-handle=3936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "Https://1drv.ms/o/s!AlMJeT9dBvaPgY9Cyb0LnGlvdMroMg" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,13295521692237414746,15435509559317568879,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2542937622355714597 --mojo-platform-channel-handle=3548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
644
Read events
539
Write events
100
Delete events
5
Modification events
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1944-13220108544029750 |
Value: 259 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1944) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
121
Text files
386
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c170c108-de1f-468b-992f-492e63e9e6ca.tmp | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1944 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
102
DNS requests
43
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4000 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
4000 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
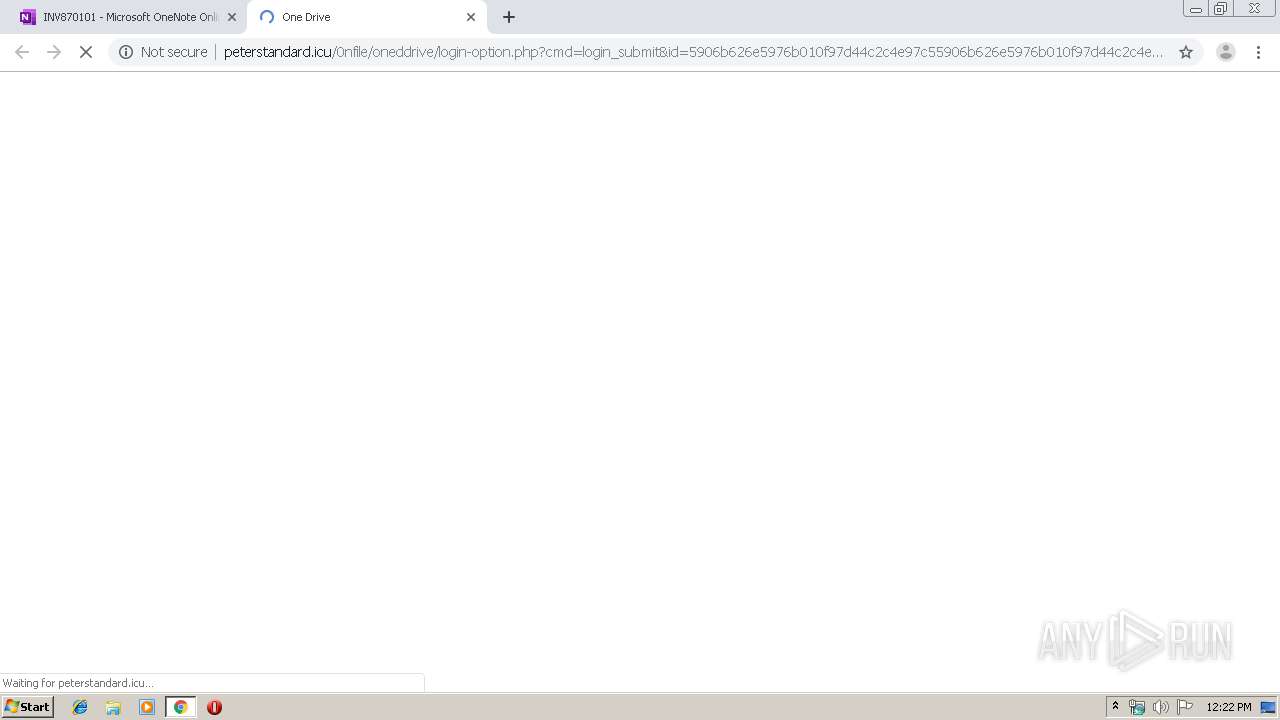
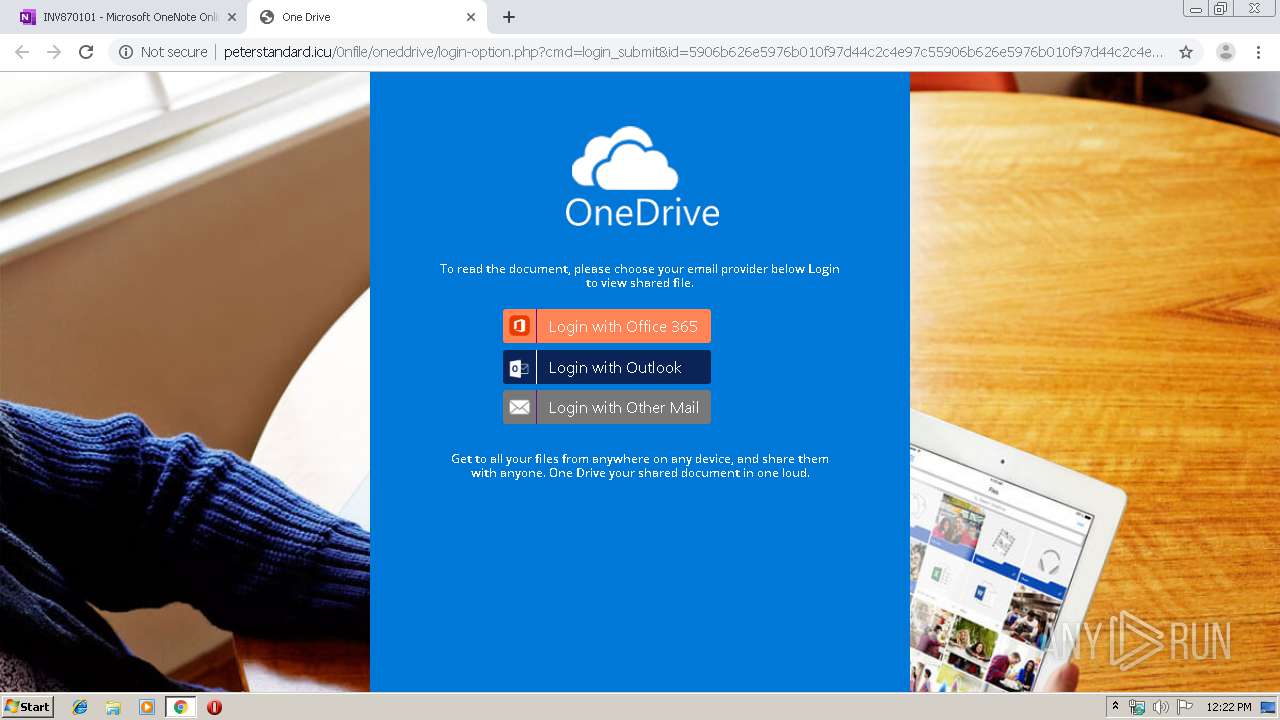
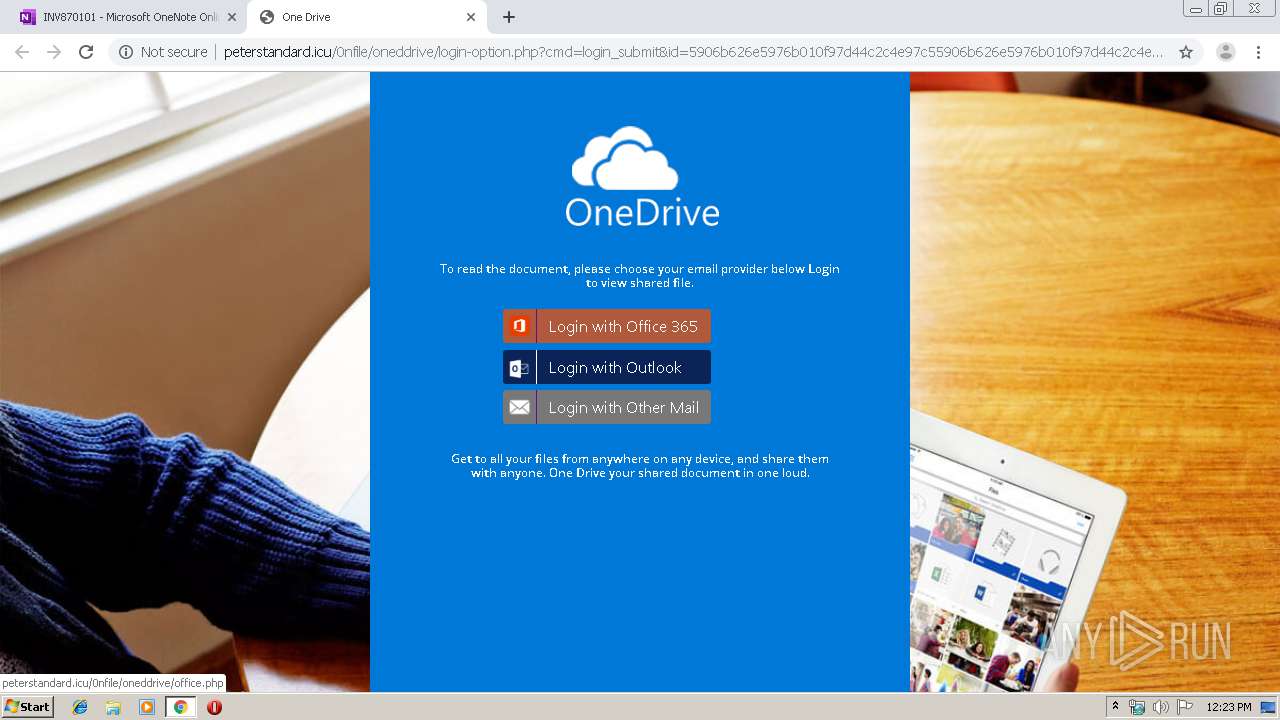
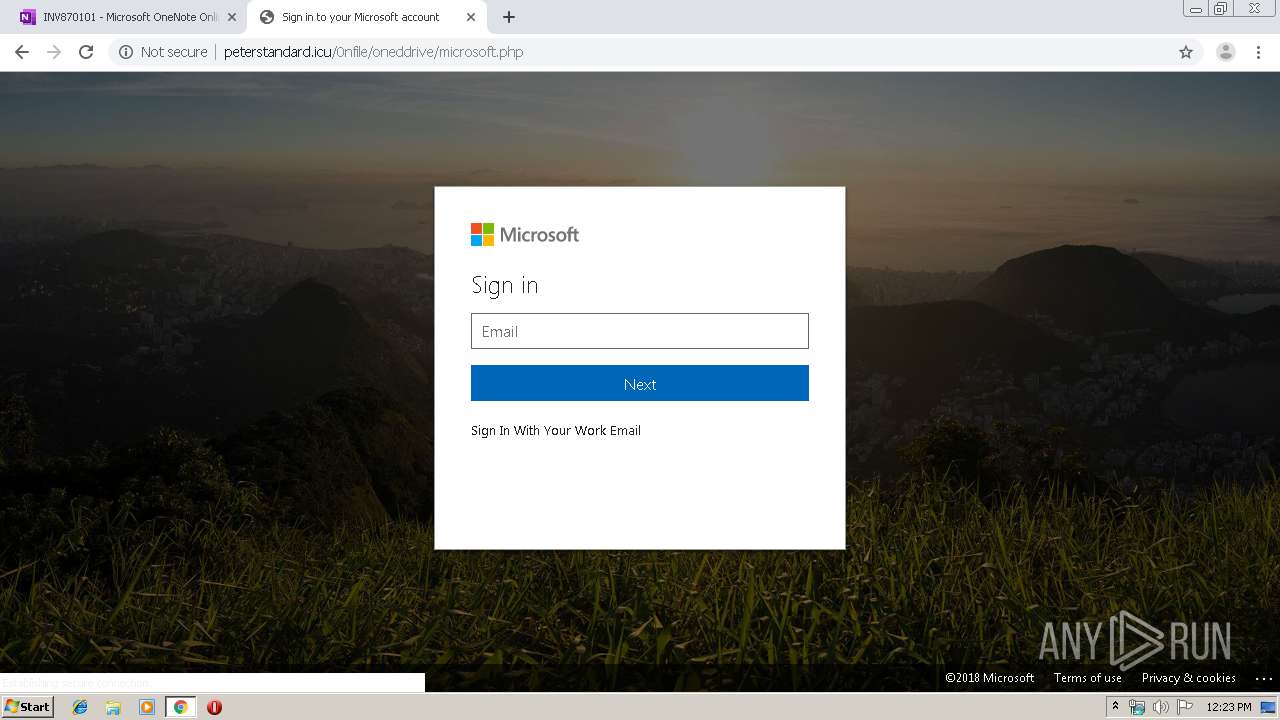
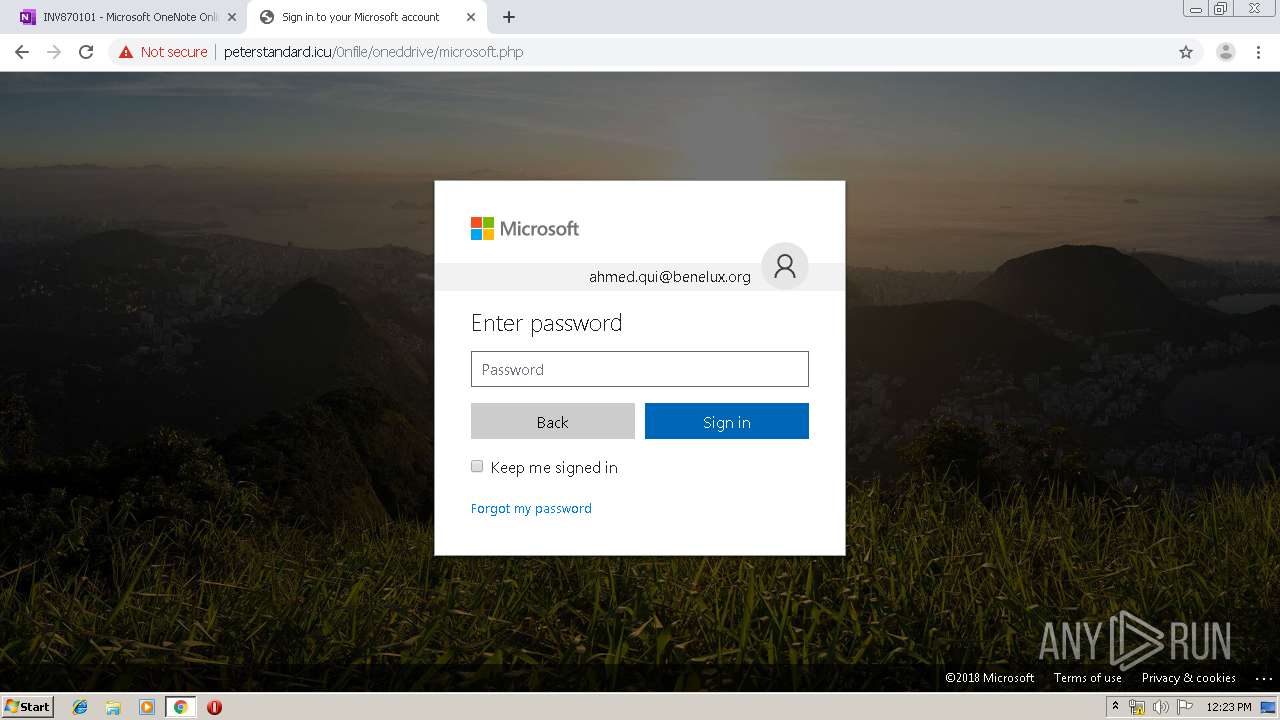
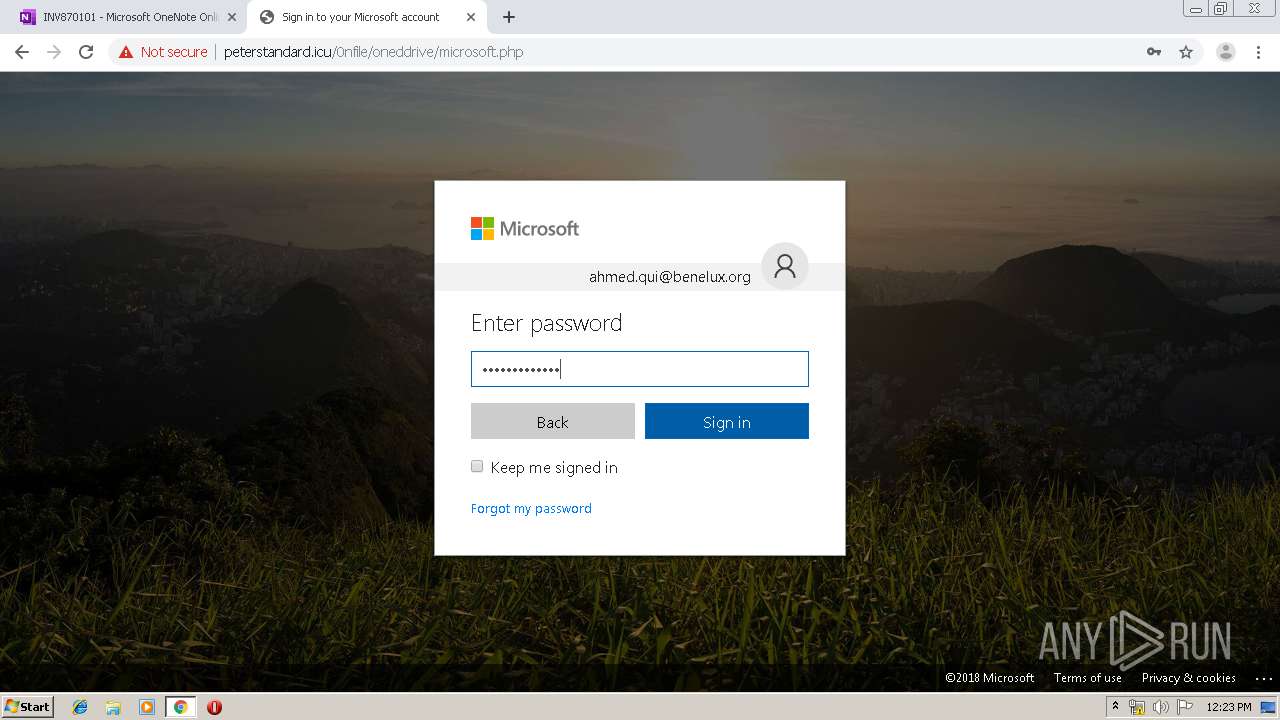
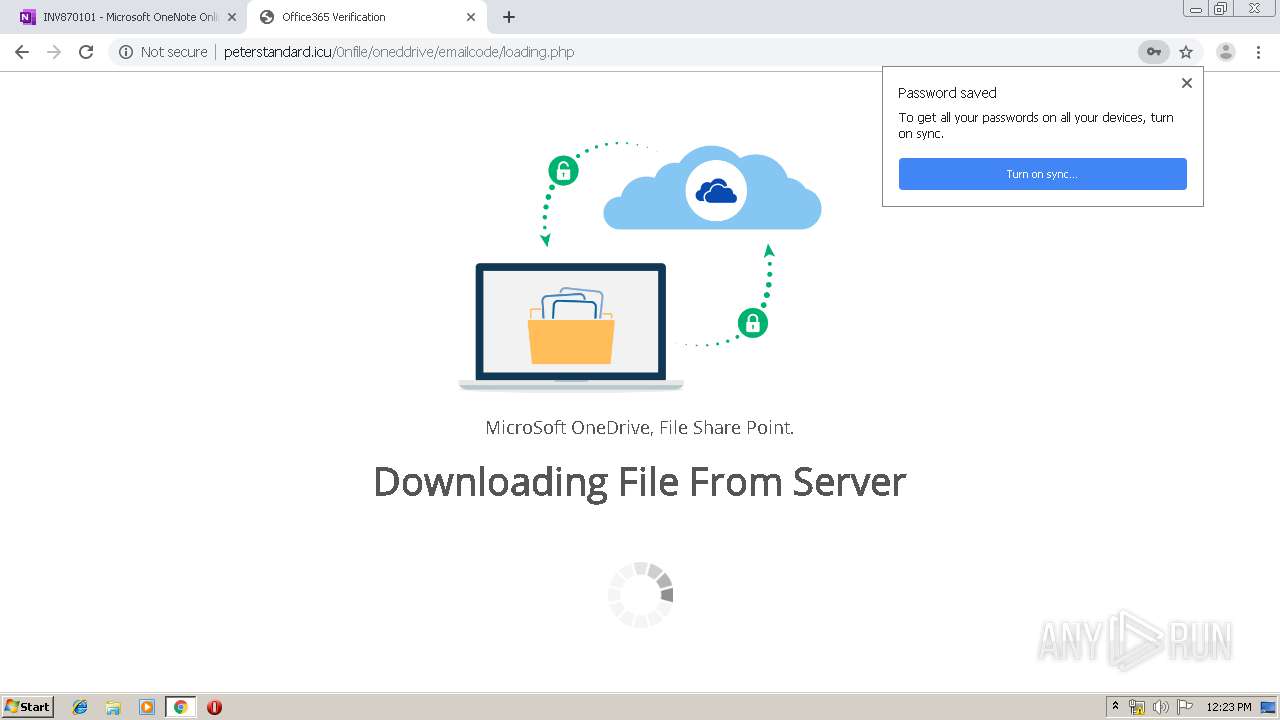
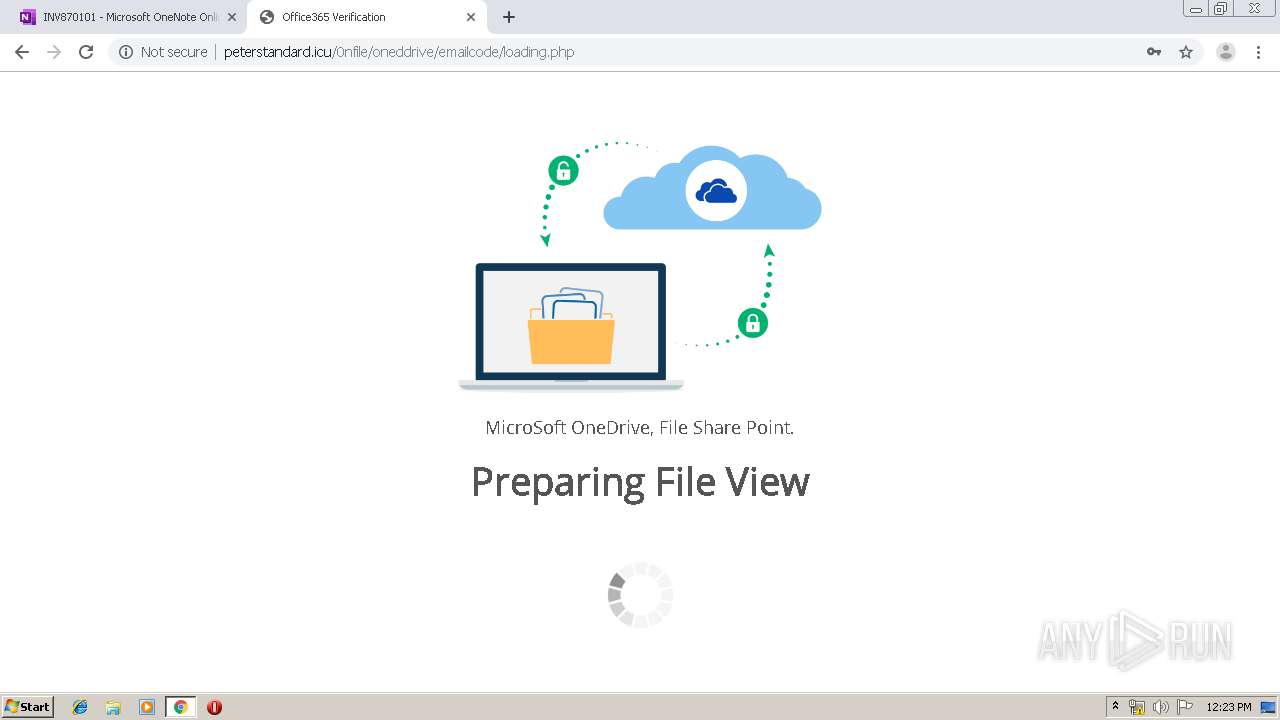
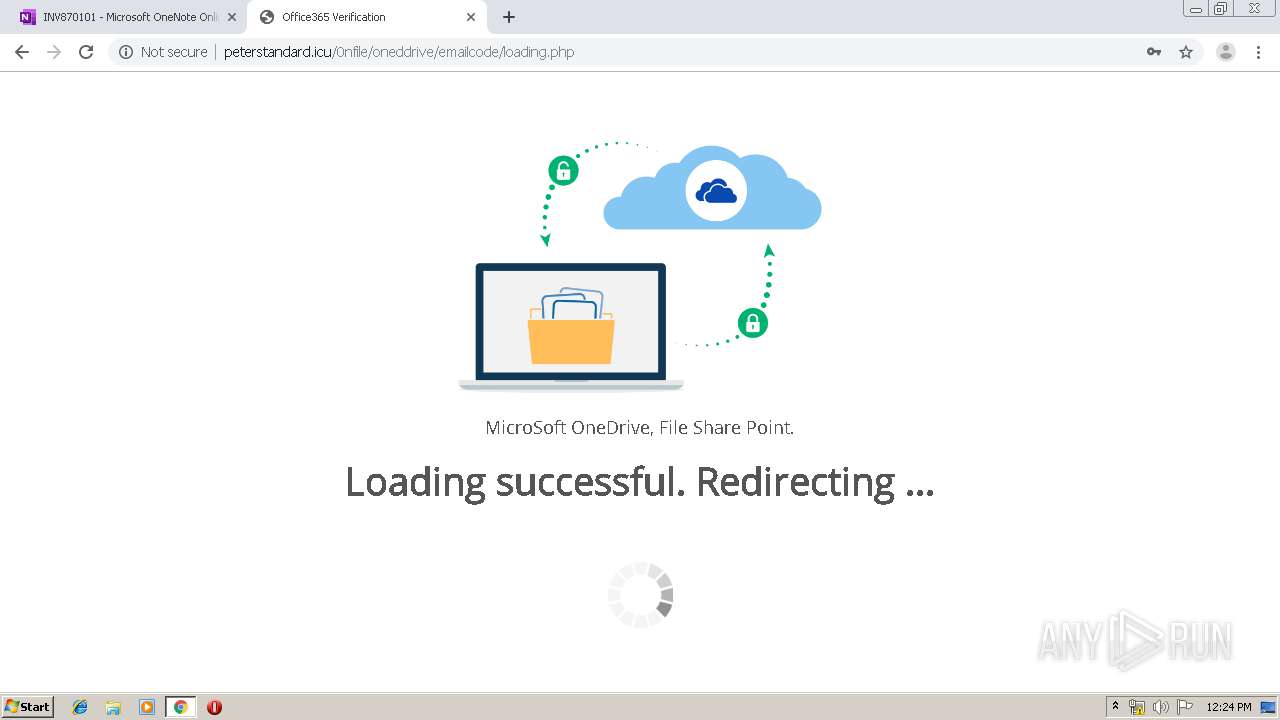
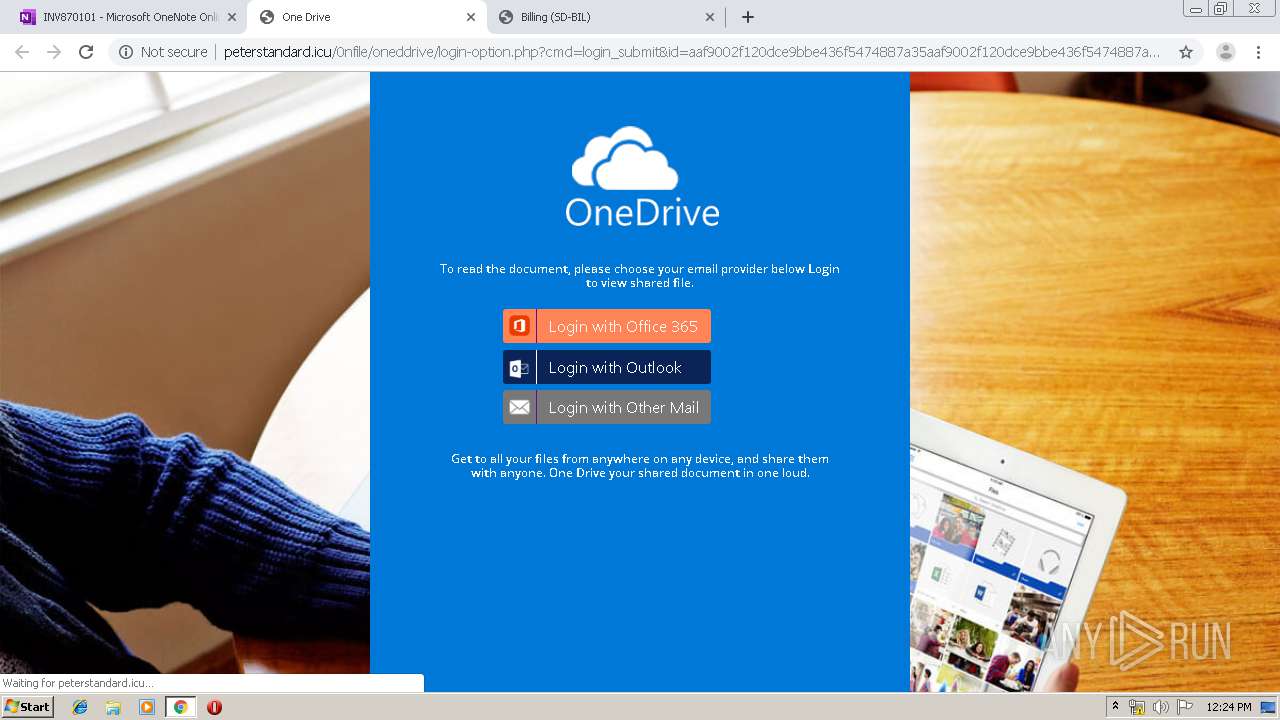
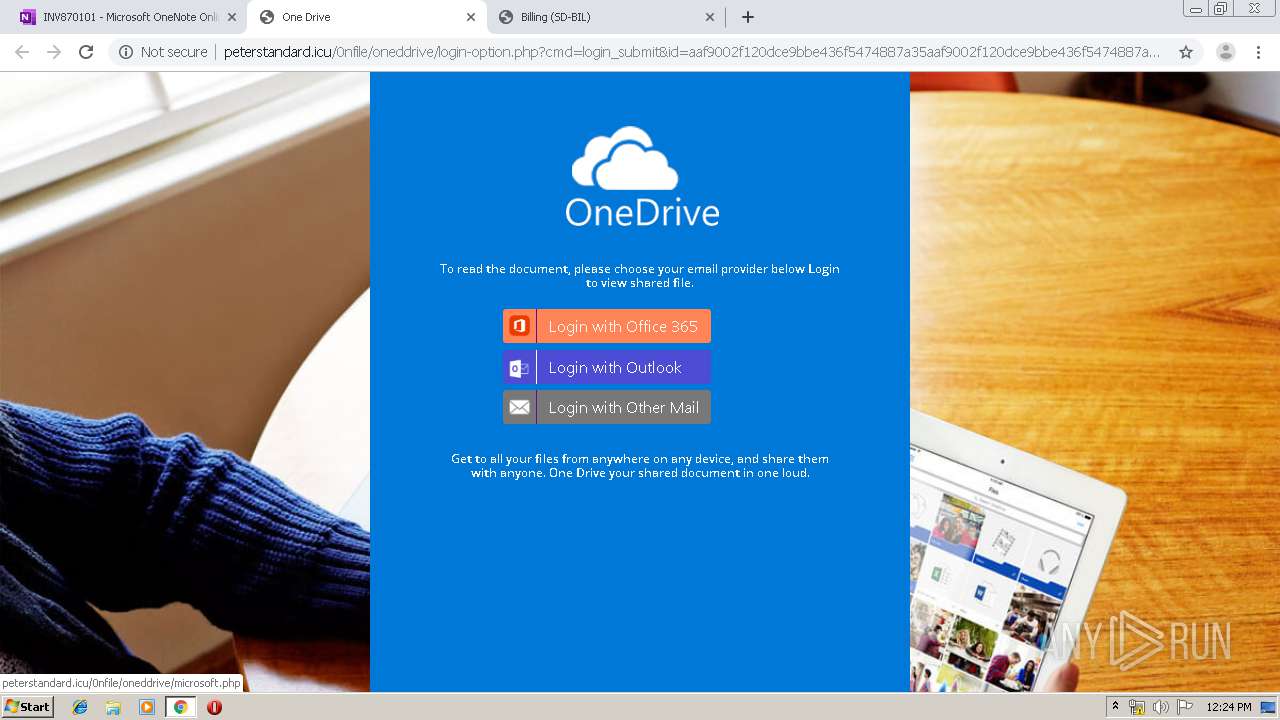
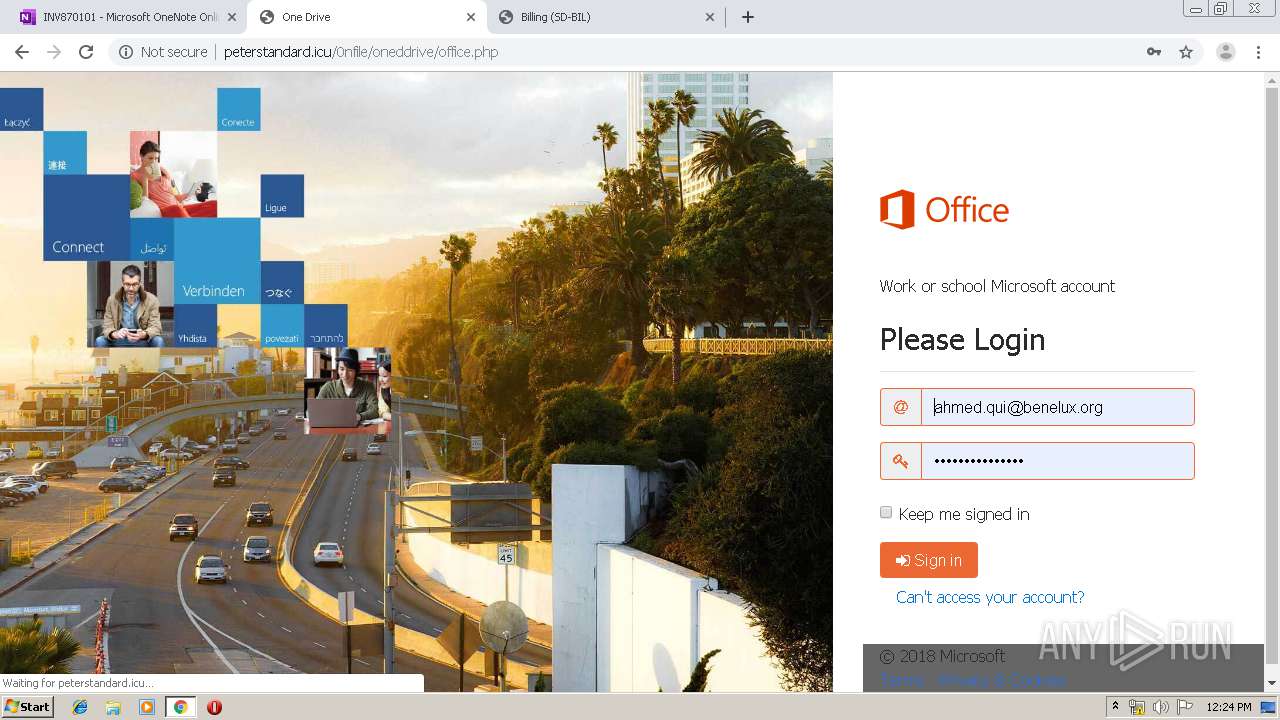
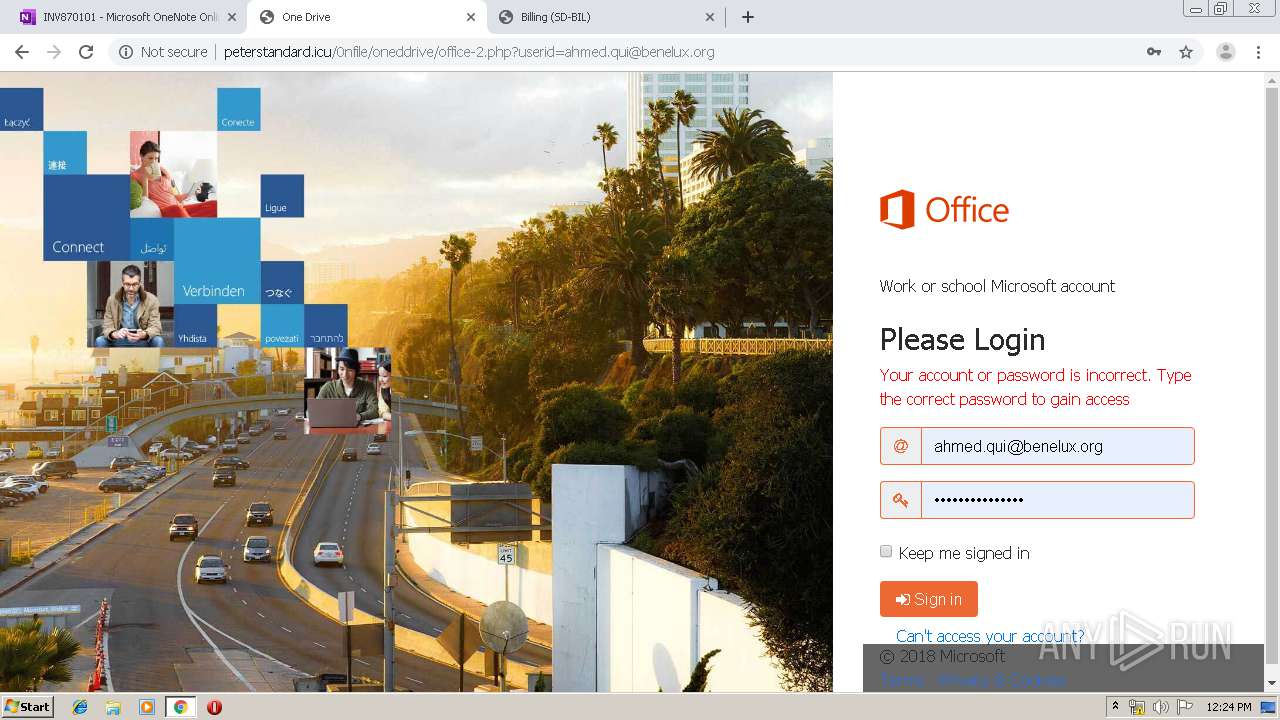
4000 | chrome.exe | GET | 200 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/microsoft.php | RU | html | 8.82 Kb | malicious |
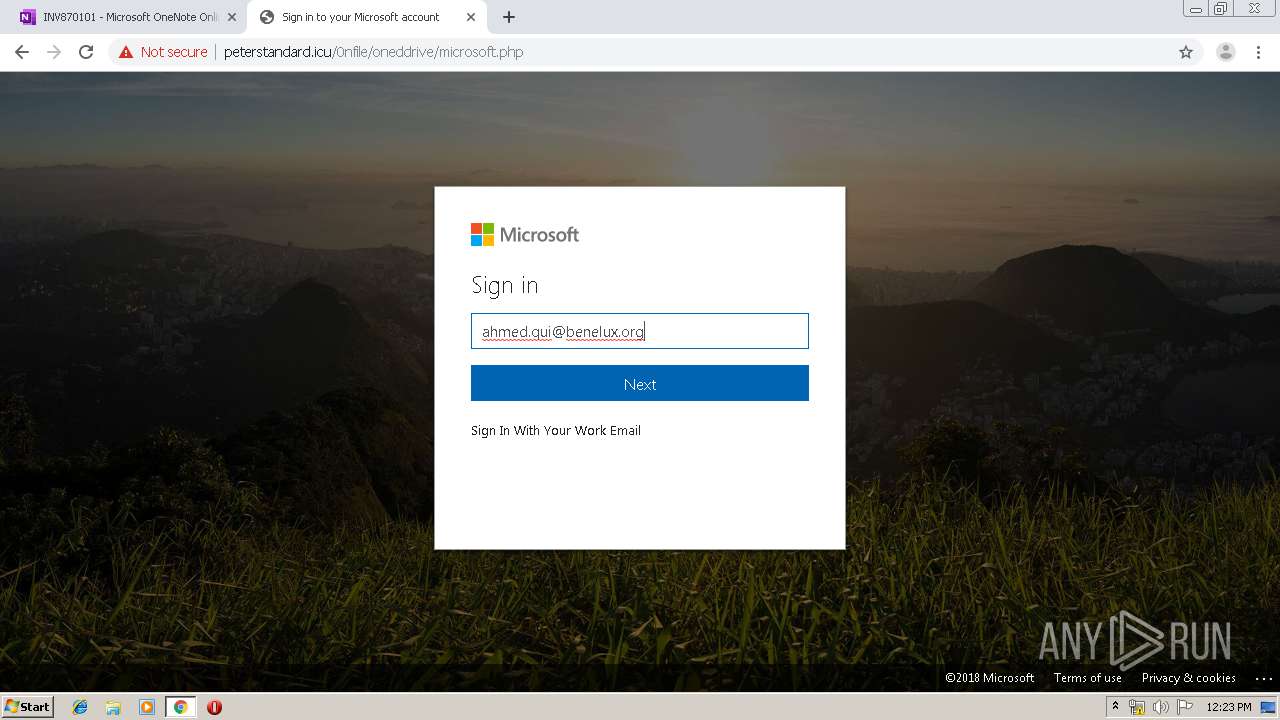
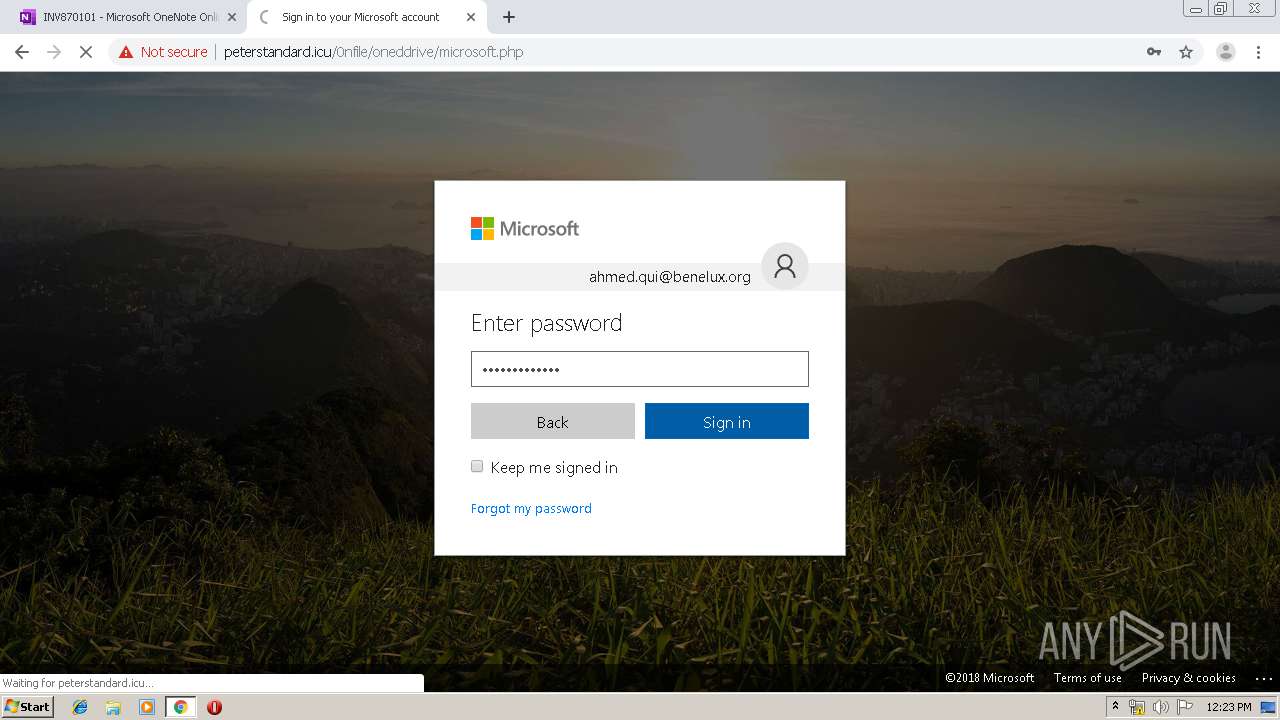
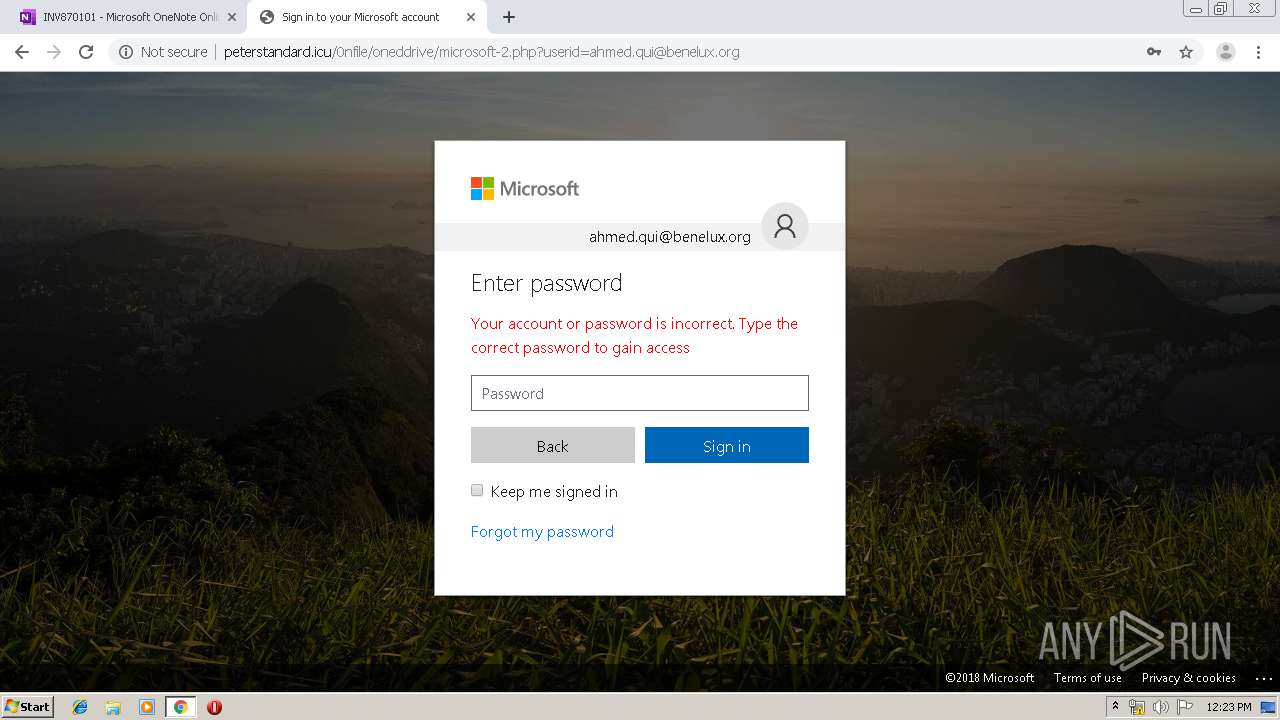
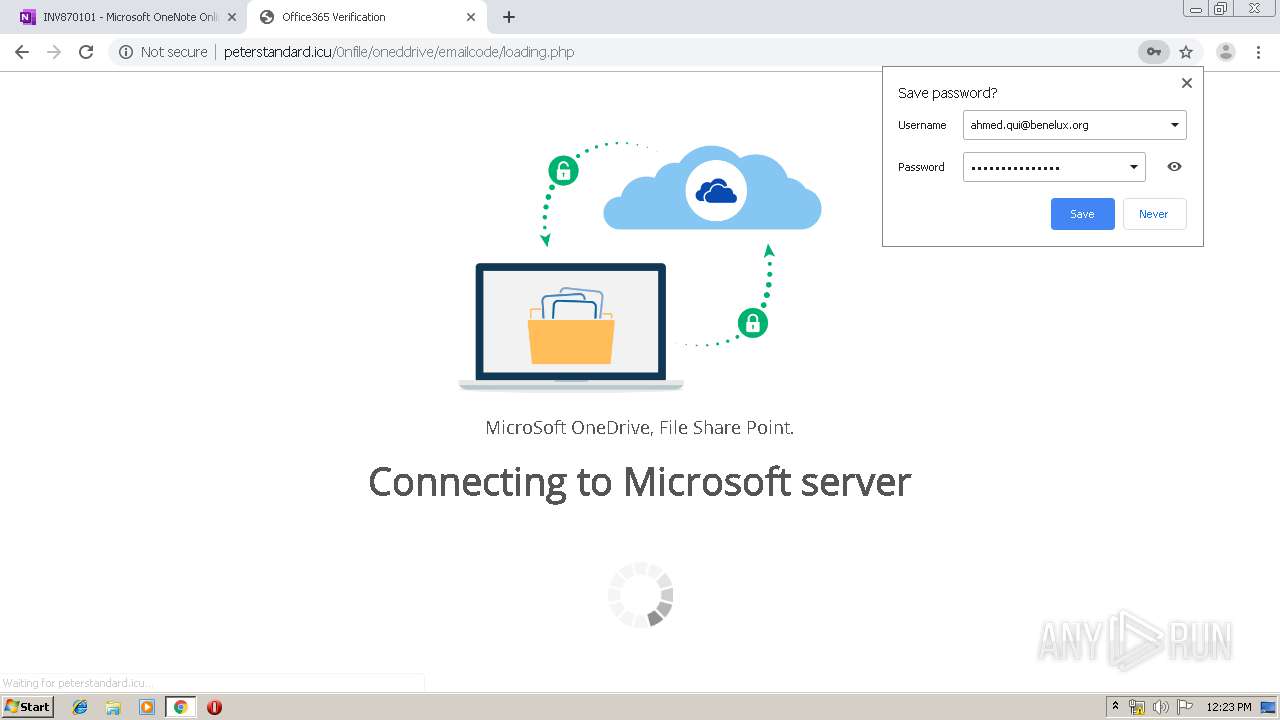
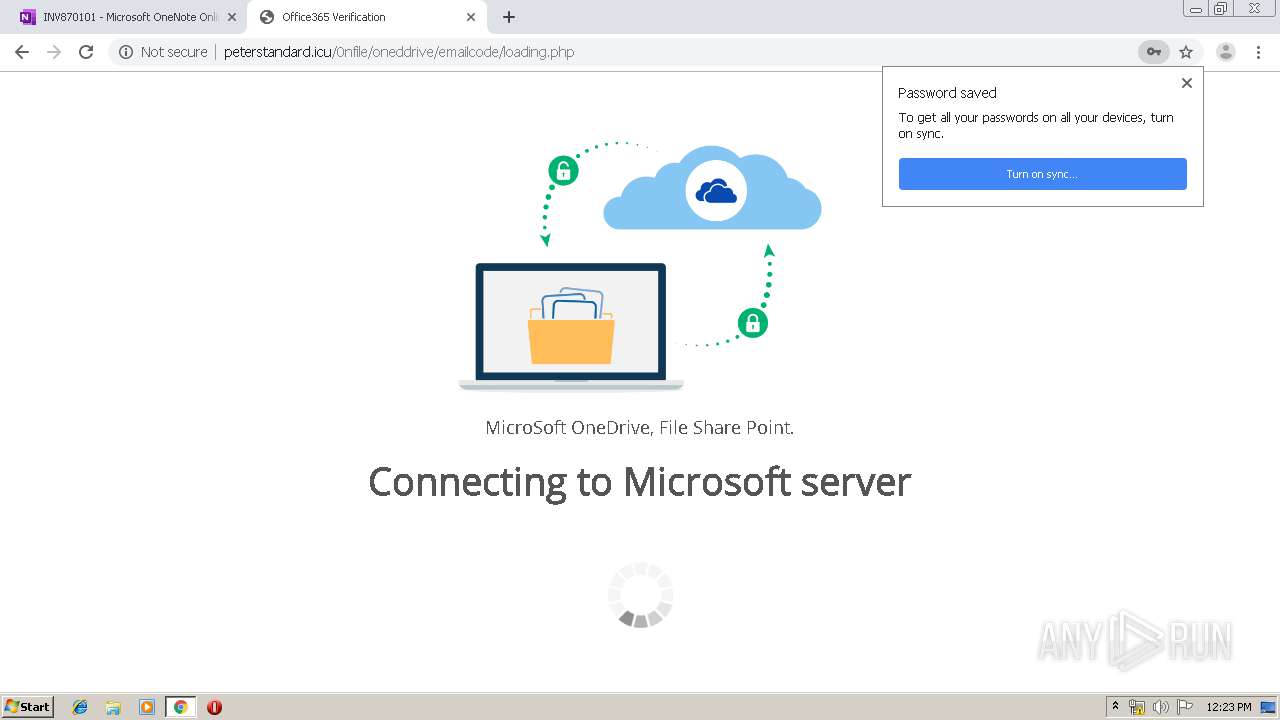
4000 | chrome.exe | GET | 302 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/microsoft.php?email=ahmed.qui%40benelux.org&password=siydyfdwsq624&logintype=outlook&submit_btn= | RU | html | 8.82 Kb | malicious |
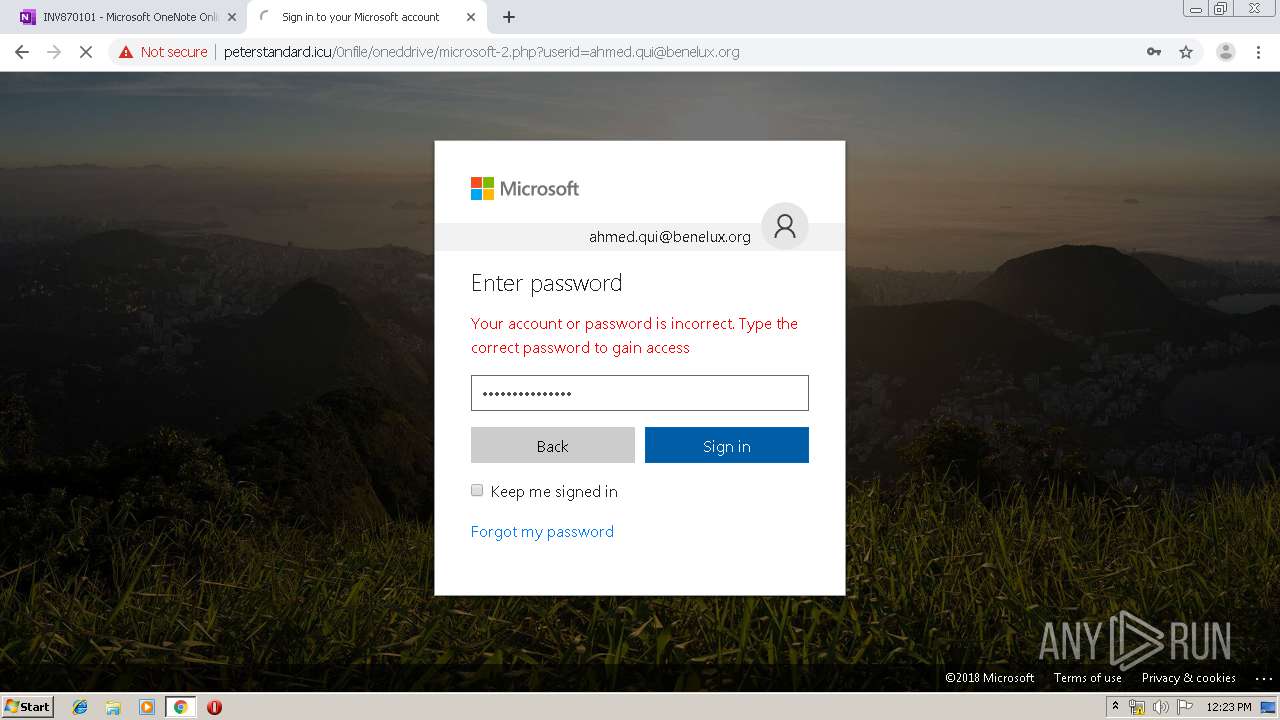
4000 | chrome.exe | GET | 200 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/microsoft-2.php?userid=ahmed.qui@benelux.org | RU | html | 9.03 Kb | malicious |
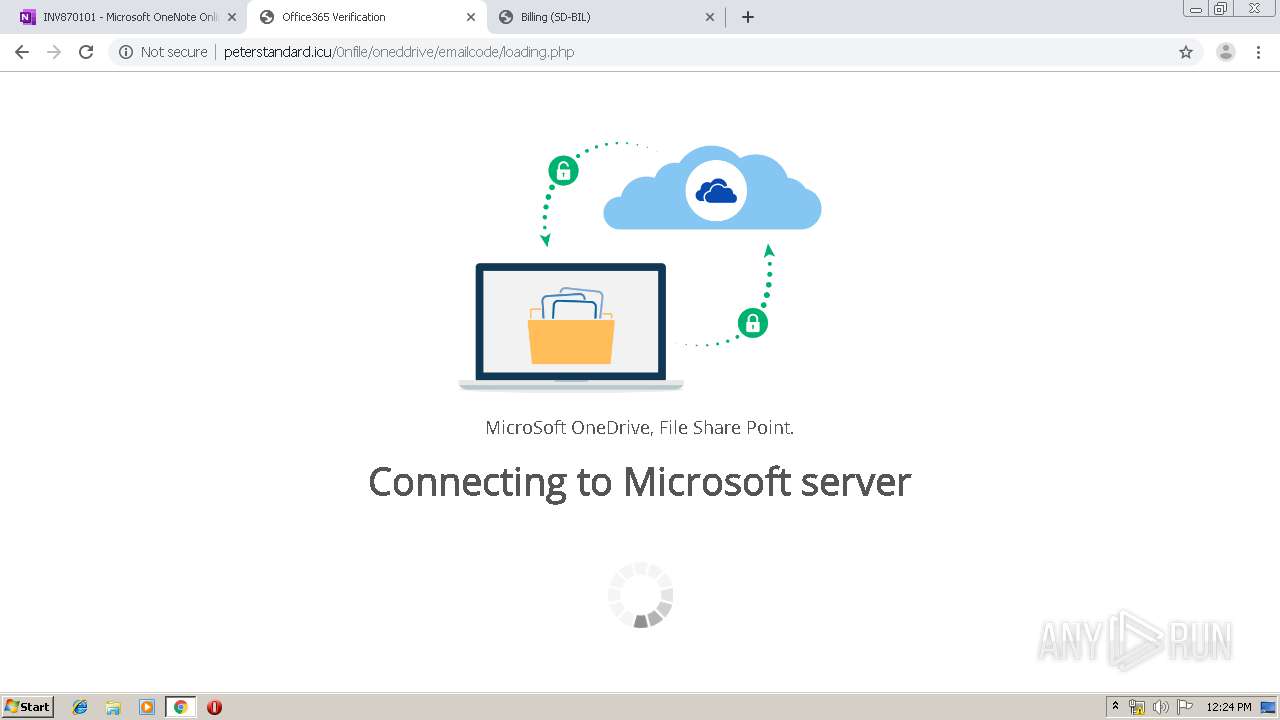
4000 | chrome.exe | GET | 302 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/ | RU | html | 250 b | malicious |
4000 | chrome.exe | GET | 301 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive | RU | html | 250 b | malicious |
4000 | chrome.exe | GET | 200 | 209.85.226.10:80 | http://r5---sn-5hnekn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=95.211.188.11&mm=28&mn=sn-5hnekn76&ms=nvh&mt=1575634880&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4000 | chrome.exe | GET | 200 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/css/bootstrap.min.css | RU | text | 141 Kb | malicious |
4000 | chrome.exe | GET | 200 | 178.159.36.236:80 | http://peterstandard.icu/0nfile/oneddrive/css/style.css | RU | text | 9.85 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4000 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4000 | chrome.exe | 13.107.42.12:443 | 1drv.ms | Microsoft Corporation | US | suspicious |
4000 | chrome.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4000 | chrome.exe | 2.16.186.40:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
4000 | chrome.exe | 13.107.6.171:443 | onenote.officeapps.live.com | Microsoft Corporation | US | whitelisted |
4000 | chrome.exe | 95.100.197.21:443 | c3-onenote-15.cdn.office.net | Akamai Technologies, Inc. | — | unknown |
4000 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
4000 | chrome.exe | 23.210.249.93:443 | c.s-microsoft.com | Akamai International B.V. | NL | whitelisted |
4000 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
4000 | chrome.exe | 23.210.248.247:443 | c1-onenote-15.cdn.office.net | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
1drv.ms |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
onedrive.live.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
spoprod-a.akamaihd.net |
| whitelisted |
p.sfx.ms |
| whitelisted |
onenote.officeapps.live.com |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
4000 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Google Drive Phishing Landing |
4000 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Google Drive Phishing Landing |
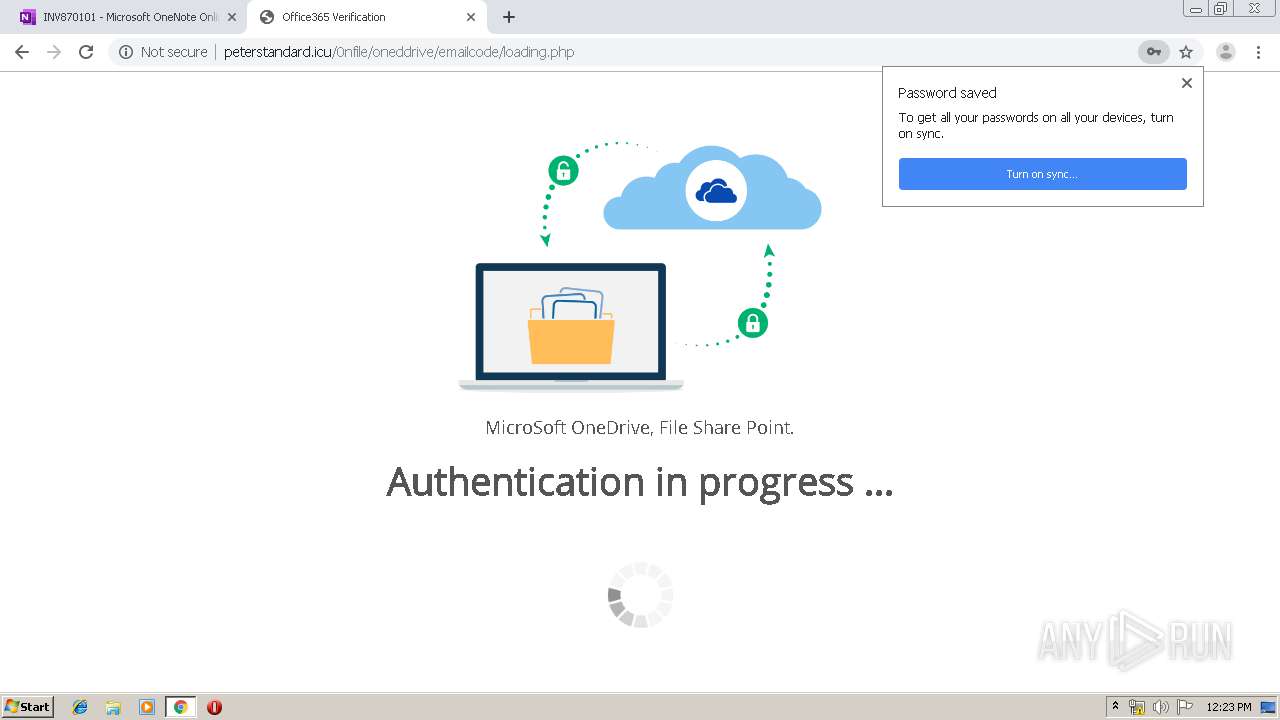
4000 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish to .icu Domain 2019-02-06 |
4000 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
4000 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
9 ETPRO signatures available at the full report