| File name: | Sandboxie-Classic-x64-v5.70.4.exe |
| Full analysis: | https://app.any.run/tasks/bfbbdca1-9ecc-4fb7-8f10-6015f185e4f4 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2025, 17:42:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 6A4FC7B7DA8E90713F19ADE3AD9904BC |
| SHA1: | 5E3C281DE206452022E3CCFB7AB4A0FEDEC2A5F8 |
| SHA256: | 299D70162376E9F3FDB4BCC2B0FD0A48AB27C293892F46D55FA96803734594F7 |
| SSDEEP: | 98304:Qv1rSY53NeL1MXHiPs1AcDcx14v0M2lMI6SXIE9hPf3vwGrwiiL/UYp2RzqwyX+f:2+BNy7qGpG |
MALICIOUS
Changes the autorun value in the registry
- SbieCtrl.exe (PID: 5788)
SUSPICIOUS
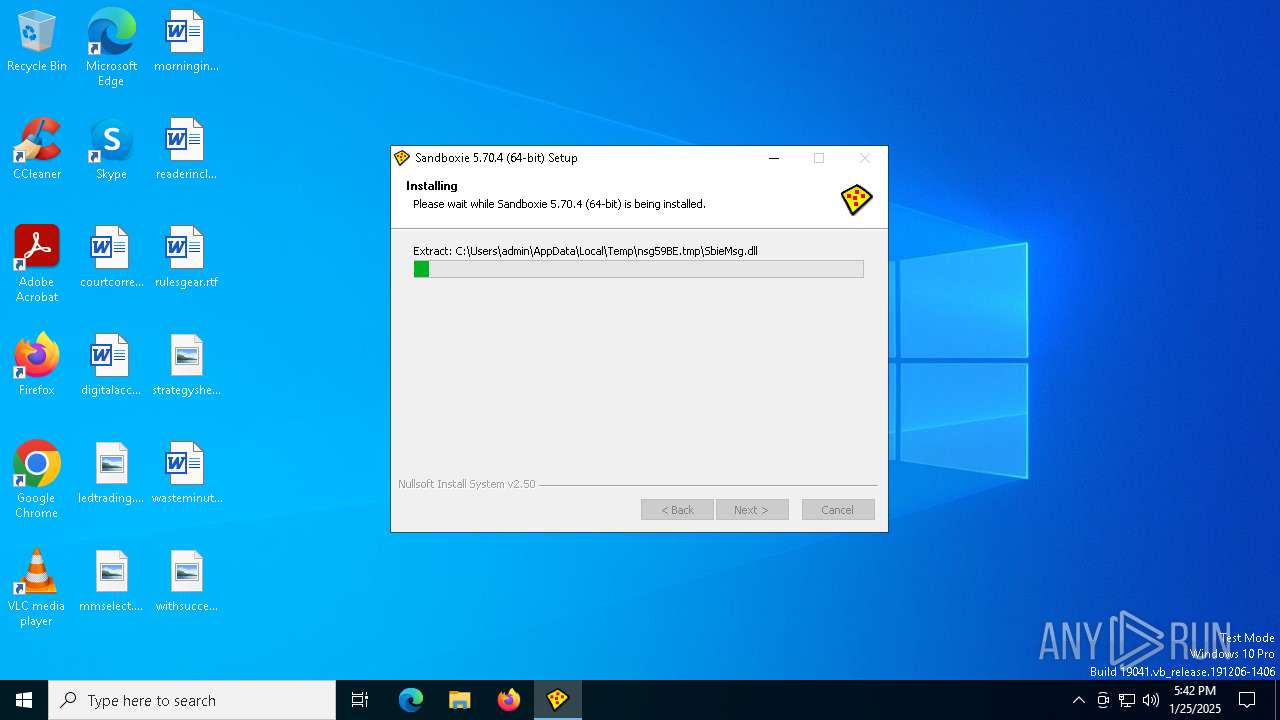
Malware-specific behavior (creating "System.dll" in Temp)
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
Executable content was dropped or overwritten
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
The process creates files with name similar to system file names
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
There is functionality for taking screenshot (YARA)
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
- SbieSvc.exe (PID: 6264)
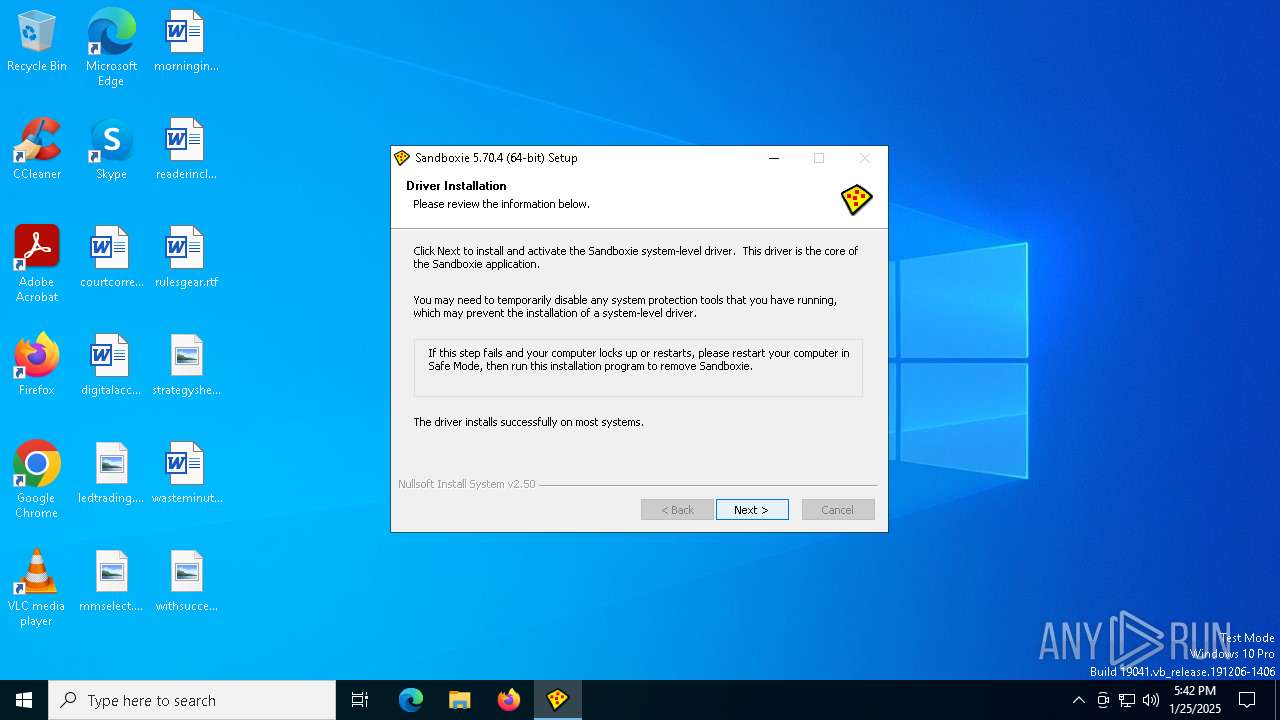
Drops a system driver (possible attempt to evade defenses)
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
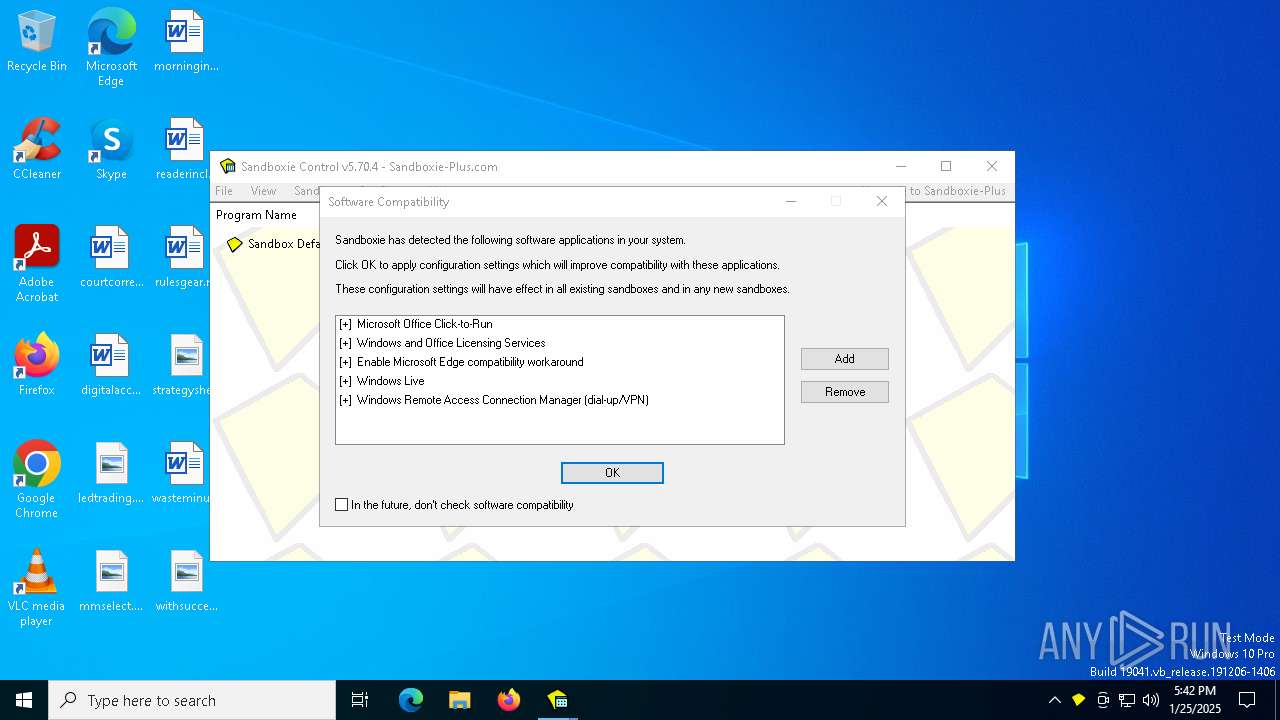
Reads security settings of Internet Explorer
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
- SbieCtrl.exe (PID: 5788)
- Start.exe (PID: 4640)
Creates a software uninstall entry
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
Creates or modifies Windows services
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
- KmdUtil.exe (PID: 1544)
Executes as Windows Service
- SbieSvc.exe (PID: 6264)
Reads Microsoft Outlook installation path
- SbieCtrl.exe (PID: 5788)
Reads Internet Explorer settings
- SbieCtrl.exe (PID: 5788)
Write to the desktop.ini file (may be used to cloak folders)
- Start.exe (PID: 4640)
Application launched itself
- SbieSvc.exe (PID: 6264)
Changes default file association
- SandboxieRpcSs.exe (PID: 5252)
Reads the date of Windows installation
- Start.exe (PID: 4640)
INFO
Checks supported languages
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
- KmdUtil.exe (PID: 7028)
- KmdUtil.exe (PID: 7052)
- KmdUtil.exe (PID: 7076)
- UpdUtil.exe (PID: 7112)
- KmdUtil.exe (PID: 1544)
- KmdUtil.exe (PID: 3436)
- SbieSvc.exe (PID: 6264)
- Start.exe (PID: 2744)
- SbieCtrl.exe (PID: 5788)
- KmdUtil.exe (PID: 6280)
- Start.exe (PID: 5576)
- SbieSvc.exe (PID: 2324)
- SandboxieDcomLaunch.exe (PID: 3688)
- SandboxieRpcSs.exe (PID: 5252)
- Start.exe (PID: 4640)
- SbieSvc.exe (PID: 6916)
Create files in a temporary directory
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
Reads the computer name
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
- KmdUtil.exe (PID: 7028)
- KmdUtil.exe (PID: 7052)
- KmdUtil.exe (PID: 7076)
- KmdUtil.exe (PID: 1544)
- KmdUtil.exe (PID: 3436)
- KmdUtil.exe (PID: 6280)
- SbieSvc.exe (PID: 6264)
- SbieCtrl.exe (PID: 5788)
- SbieSvc.exe (PID: 2324)
- SandboxieRpcSs.exe (PID: 5252)
- SandboxieDcomLaunch.exe (PID: 3688)
- Start.exe (PID: 4640)
- SbieSvc.exe (PID: 6916)
Reads Environment values
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
The sample compiled with english language support
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
Creates files in the program directory
- Sandboxie-Classic-x64-v5.70.4.exe (PID: 6684)
Creates files or folders in the user directory
- SbieCtrl.exe (PID: 5788)
Checks proxy server information
- SbieCtrl.exe (PID: 5788)
Application launched itself
- msedge.exe (PID: 848)
Process checks computer location settings
- Start.exe (PID: 4640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 05:38:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x324f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.70.4.0 |
| ProductVersionNumber: | 5.70.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
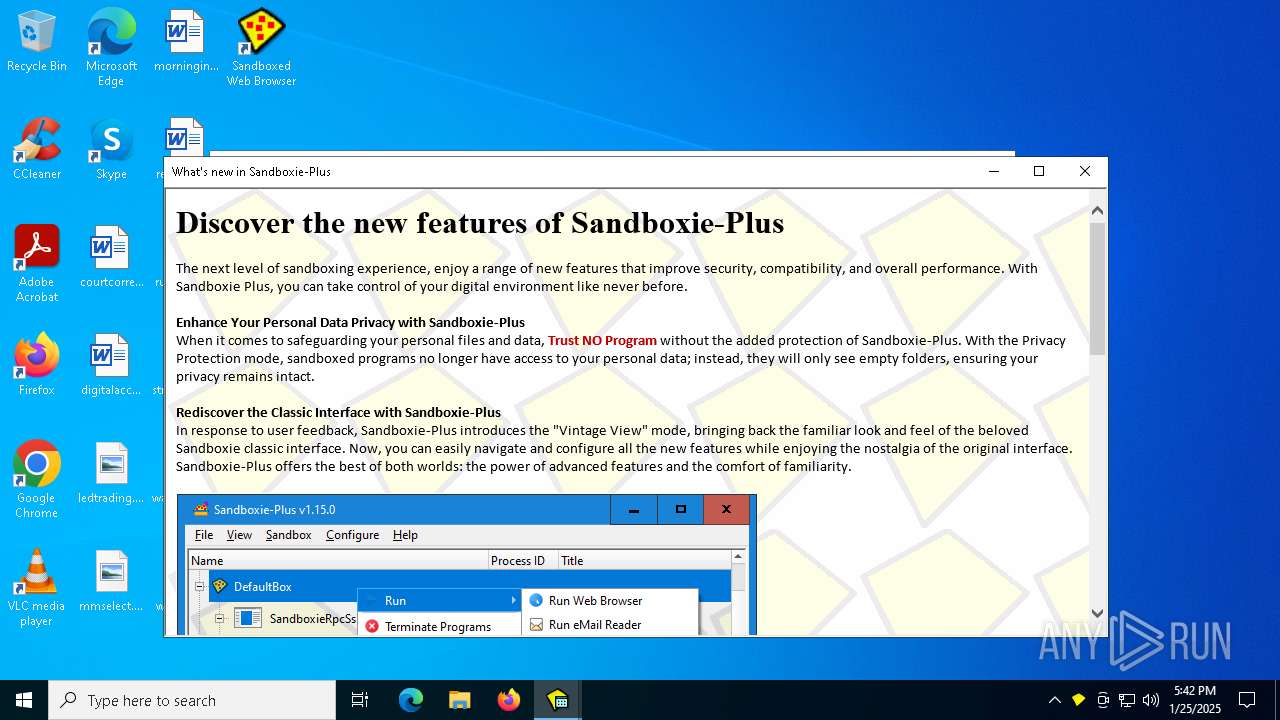
| CompanyName: | Sandboxie-Plus.com |
| FileDescription: | Sandboxie Installer |
| FileVersion: | 5.70.4 |
| LegalCopyright: | Copyright © 2020-2024 by David Xanatos (xanasoft.com) |
| ProductName: | Sandboxie |
| ProductVersion: | 5.70.4 |
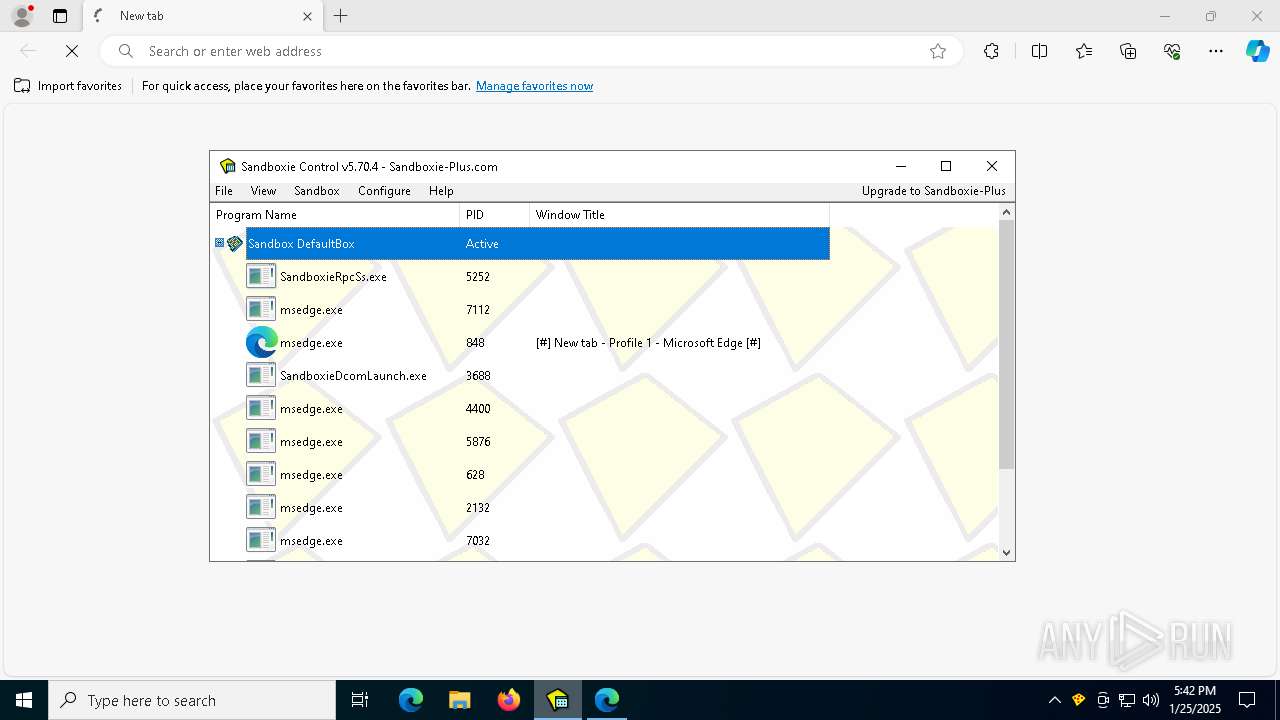
Total processes
165
Monitored processes
36
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6472 --field-trial-handle=2504,i,6293843282935921747,14173895118378014772,262144 --disable-features=PrintCompositorLPAC --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1073807364 Version: 122.0.2365.59 | |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | Start.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1073807364 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1544 | "C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\KmdUtil.exe" /lang=1033 install SbieDrv "C:\Program Files\Sandboxie\SbieDrv.sys" type=kernel start=demand "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" altitude=86900 | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\KmdUtil.exe | — | Sandboxie-Classic-x64-v5.70.4.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.70.4 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=10084 --field-trial-handle=2504,i,6293843282935921747,14173895118378014772,262144 --disable-features=PrintCompositorLPAC --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4528 --field-trial-handle=2504,i,6293843282935921747,14173895118378014772,262144 --disable-features=PrintCompositorLPAC --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1073807364 Version: 122.0.2365.59 | |||||||||||||||
| 2324 | "C:\Program Files\Sandboxie\SbieSvc.exe" Sandboxie_GuiProxy_00000001,6264 | C:\Program Files\Sandboxie\SbieSvc.exe | — | SbieSvc.exe | |||||||||||
User: SYSTEM Company: Sandboxie-Plus.com Integrity Level: SYSTEM Description: Sandboxie Service Version: 5.70.4 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Sandboxie\Start.exe" open_agent:"SbieCtrl.exe /open /sync /postsetup" | C:\Program Files\Sandboxie\Start.exe | — | Sandboxie-Classic-x64-v5.70.4.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie Start Exit code: 0 Version: 5.70.4 Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4332 --field-trial-handle=2504,i,6293843282935921747,14173895118378014772,262144 --disable-features=PrintCompositorLPAC --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 3436 | "C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\KmdUtil.exe" /lang=1033 install SbieSvc "\"C:\Program Files\Sandboxie\SbieSvc.exe"\" type=own start=auto "display=Sandboxie Service" group=UIGroup "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\KmdUtil.exe | — | Sandboxie-Classic-x64-v5.70.4.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.70.4 Modules
| |||||||||||||||
| 3444 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8116 --field-trial-handle=2504,i,6293843282935921747,14173895118378014772,262144 --disable-features=PrintCompositorLPAC --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 | |||||||||||||||
Total events
3 879
Read events
3 809
Write events
67
Delete events
3
Modification events
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayName |
Value: Sandboxie 5.70.4 (64-bit) | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Sandboxie\Start.exe | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayVersion |
Value: 5.70.4 | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | Publisher |
Value: Sandboxie-Plus.com | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | UninstallString |
Value: "C:\WINDOWS\Installer\SandboxieInstall64.exe" /remove | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\WINDOWS\Installer\SandboxieInstall64.exe" /remove /S | |||
| (PID) Process: | (6684) Sandboxie-Classic-x64-v5.70.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\AutoplayHandlers\CancelAutoplay\CLSID |
| Operation: | write | Name: | 7E950284-E123-49F4-B32B-A806C090D747 |
Value: | |||
| (PID) Process: | (1544) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\SbieDrv |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Program Files\Sandboxie\SbieMsg.dll | |||
| (PID) Process: | (1544) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\SbieDrv |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (1544) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SbieDrv |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
Executable files
136
Suspicious files
214
Text files
475
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\System.dll | executable | |
MD5:0FF5120F1AFD0F295C2BAA0F7192D3F8 | SHA256:4CA5BF1BEB4B802914C4D3E2F37861F6BA5ECF969CFEADF5855EDF58F647A721 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Program Files\Sandboxie\SbieSvc.exe.sig | binary | |
MD5:DC25810056351DE549F0F414205D01F6 | SHA256:092445508156DF3D978C582285C9F795C13D169B05235B952410DDD2CA86B7C8 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\InstallType.ini | text | |
MD5:46D2E7E6D3D5EE061B5646DF6834AF33 | SHA256:A9A81CA9A2EBEC41663E1DA4E5D480E6EAF9BCBDE266ABB9A0770DC9118186B9 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\LangDLL.dll | executable | |
MD5:4CDAAF5DA900A8EAED090CD22B8F8781 | SHA256:09477D605677BEA48019B896F068CE6C2E89004E5C5F0A86C0276DB30C6515A6 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\ioSpecial.ini | text | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\Warning.ini | text | |
MD5:4D358B27A971751E0C517061C948D96A | SHA256:74EE005CEB920094D99AA274ED37429EFE439FBC10E9D238C78DB4C836018A17 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\SbieDll.dll | executable | |
MD5:ABF633E9F8CF03A0E95A626F51F8C8D6 | SHA256:D45F8EC69DF2ACFE096849A76B84A0DFFF6C6C7DBD60EFE33BAC5FA6524349AD | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\SbieMsg.dll | executable | |
MD5:4D65C605A5A7DBEA3851EE7CCED7F491 | SHA256:2A00F585FE1FC15C9E2C4048937E40FD10904ABC94951F1F80F24FC12D9C6E22 | |||
| 6684 | Sandboxie-Classic-x64-v5.70.4.exe | C:\Users\admin\AppData\Local\Temp\nsg59BE.tmp\KmdUtil.exe | executable | |
MD5:74ACF8E35361A27924D250266812E40F | SHA256:D60FBE5766A3204A041330C5172FF9100AF0D0E80B904AADBCED62F7DFD16750 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6356 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
736 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |