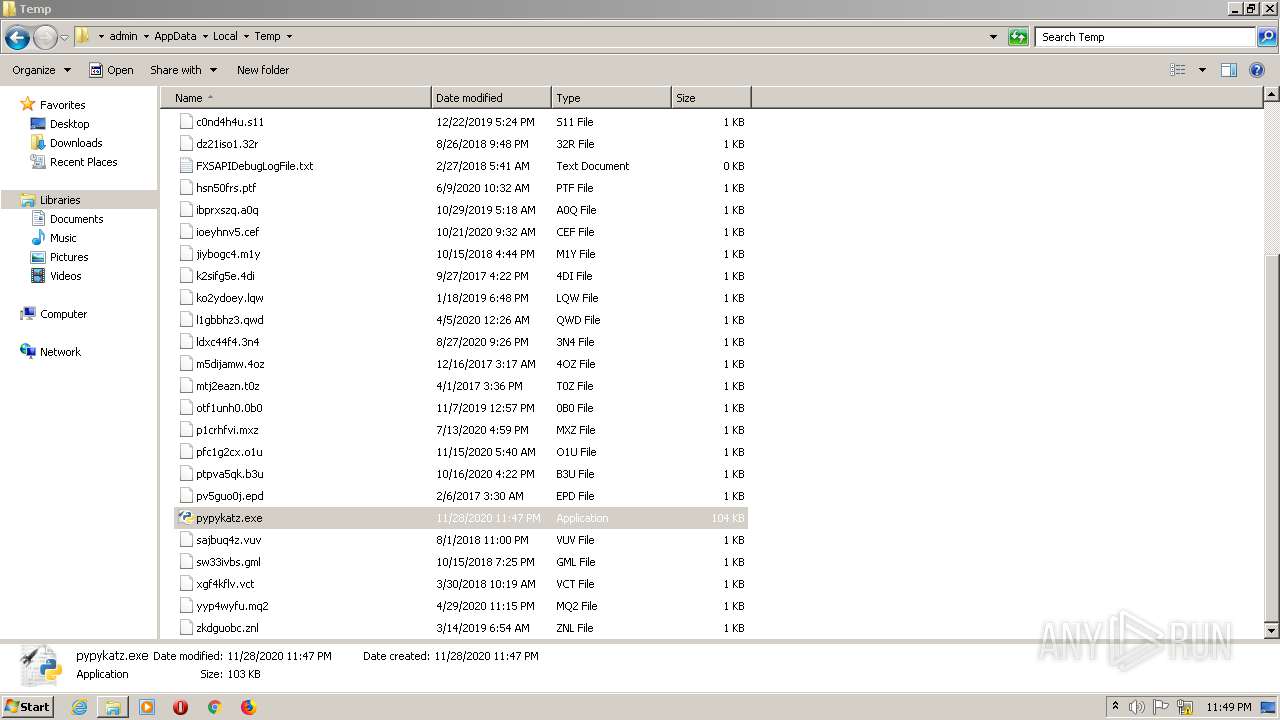
| File name: | pypykatz.exe |
| Full analysis: | https://app.any.run/tasks/20235d0b-a33c-4e99-ab2a-142bddb44239 |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2020, 23:46:42 |
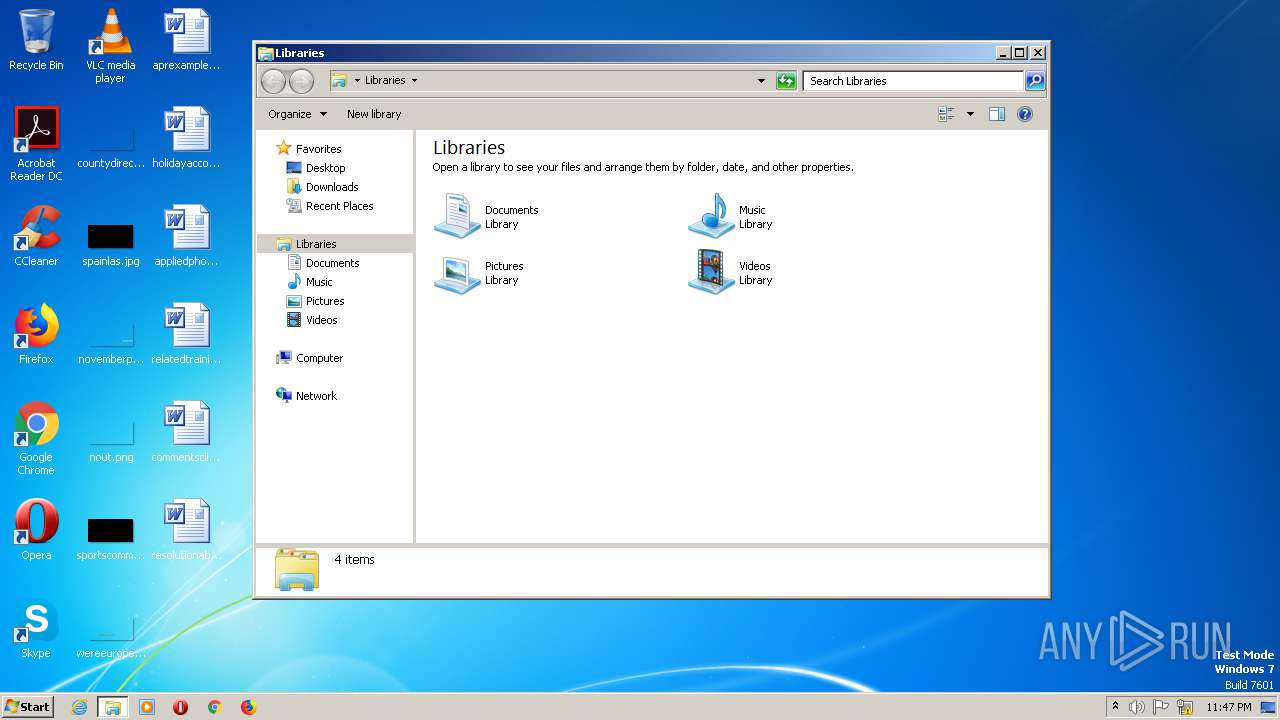
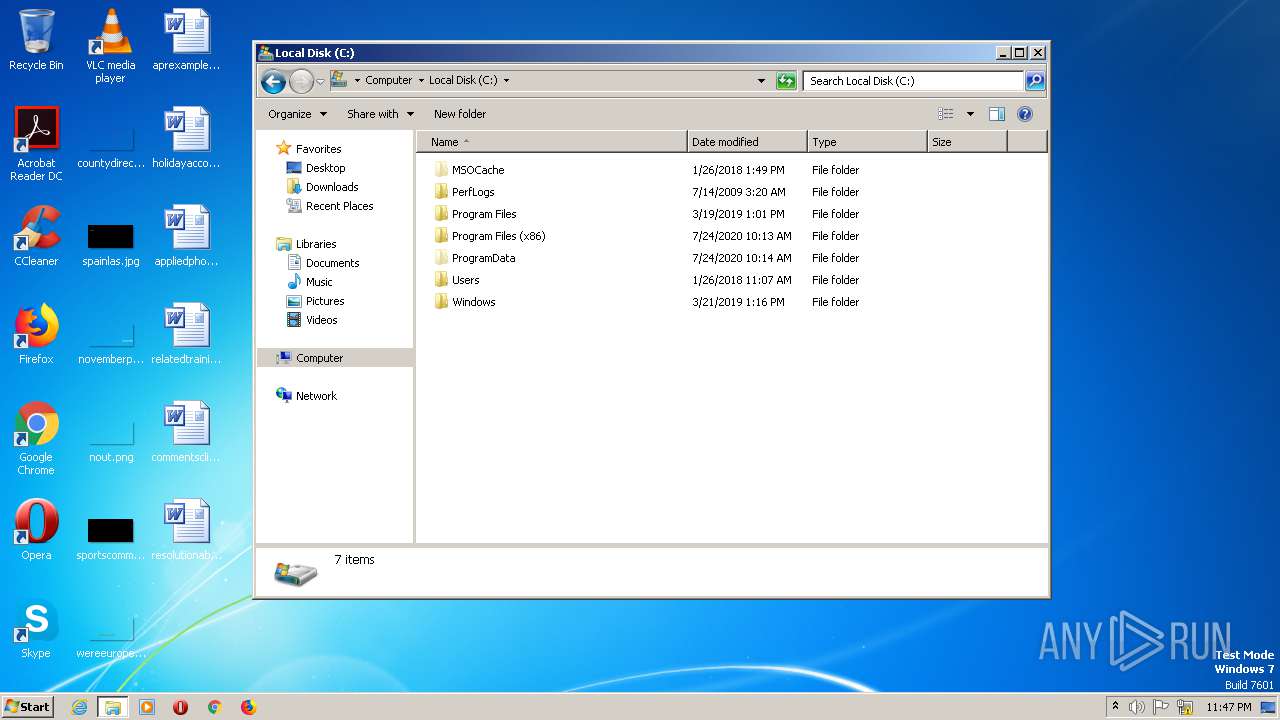
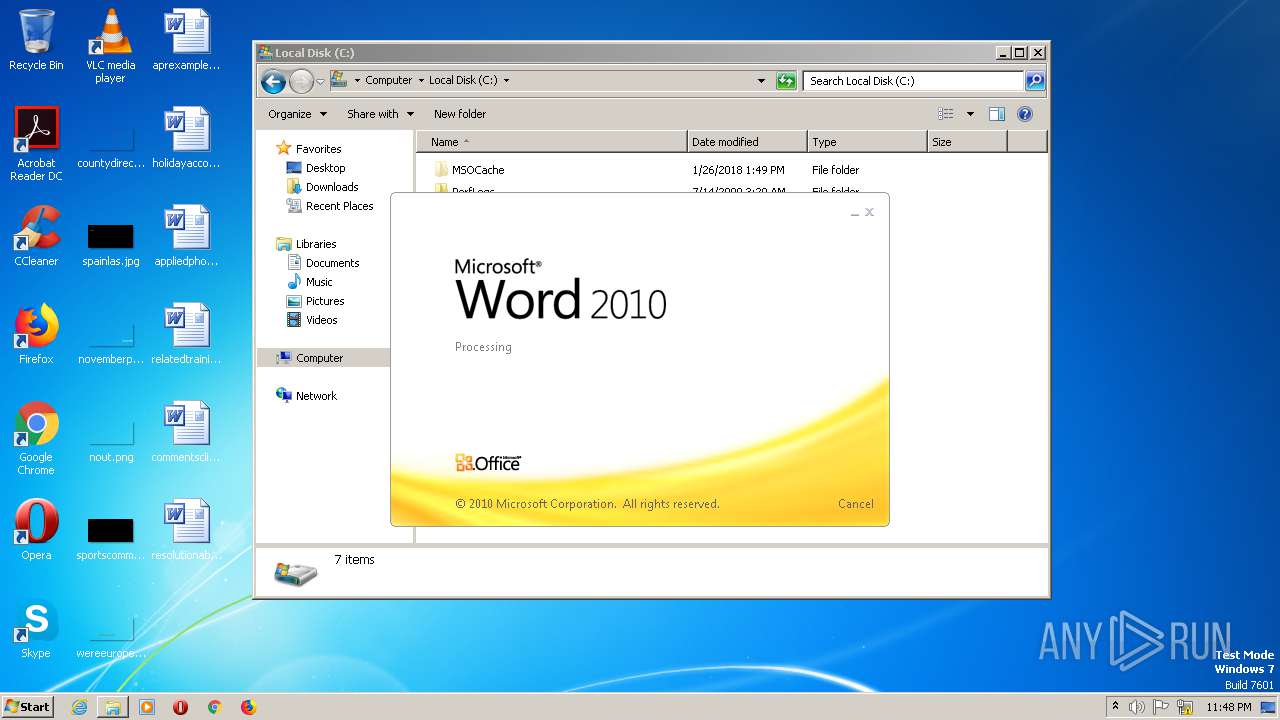
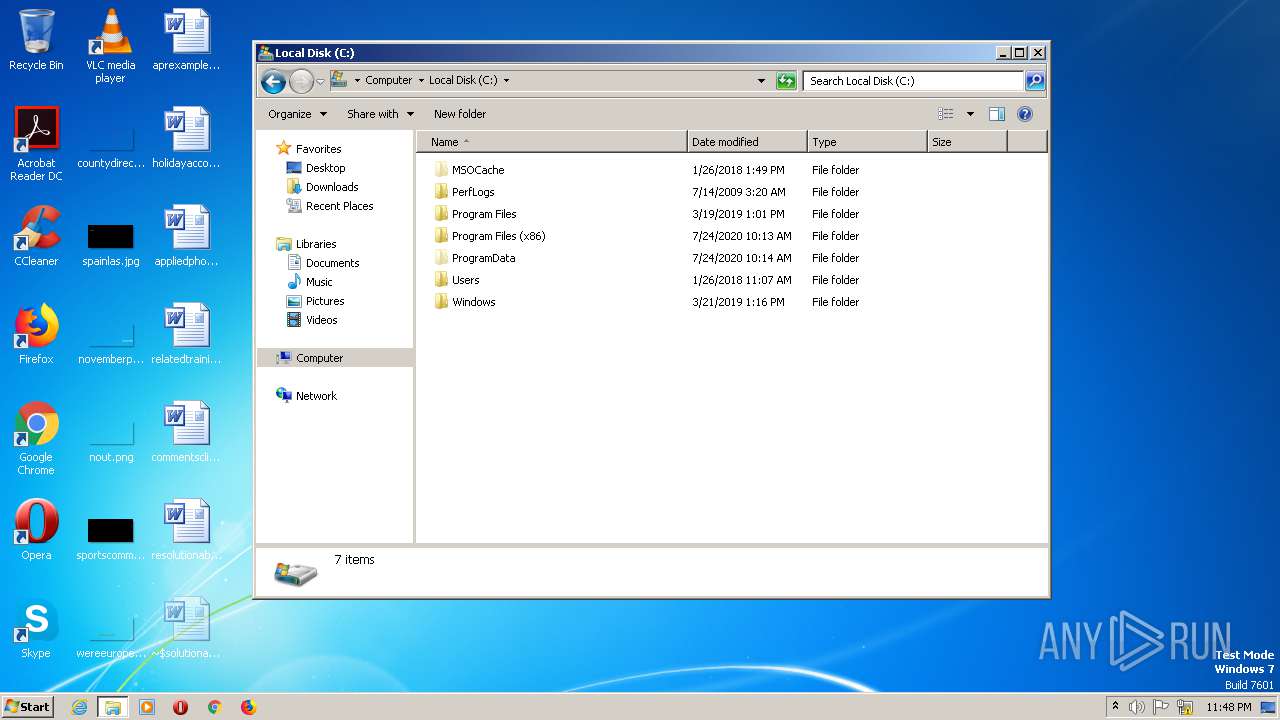
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | D3CBF1778DC64C1AFE0D4DF8AB64F76C |
| SHA1: | 72CC915E868ACC3B4480A8A34D2E29997CB40AA9 |
| SHA256: | 29696AB3BEF14460F90054A438FE7B5E1F2D7B537399426D6ABC7C9E268EB7FC |
| SSDEEP: | 1536:Oq9wlfW9aTR7gyTdneTaef5g9aJxgdS64Cdk+uJE4F4k1hEZqm6iM1FfHYTopLj:n9sfQvTbuaJG4vlP6k4qmKjfHYTodj |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
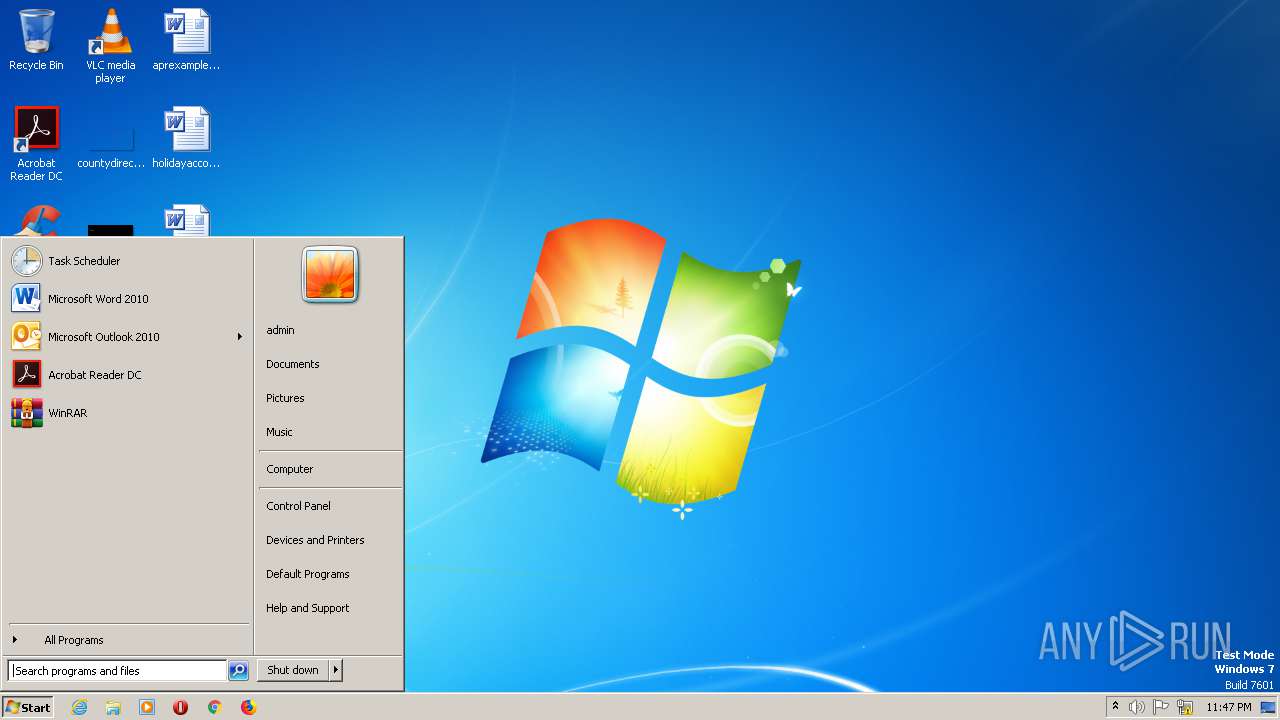
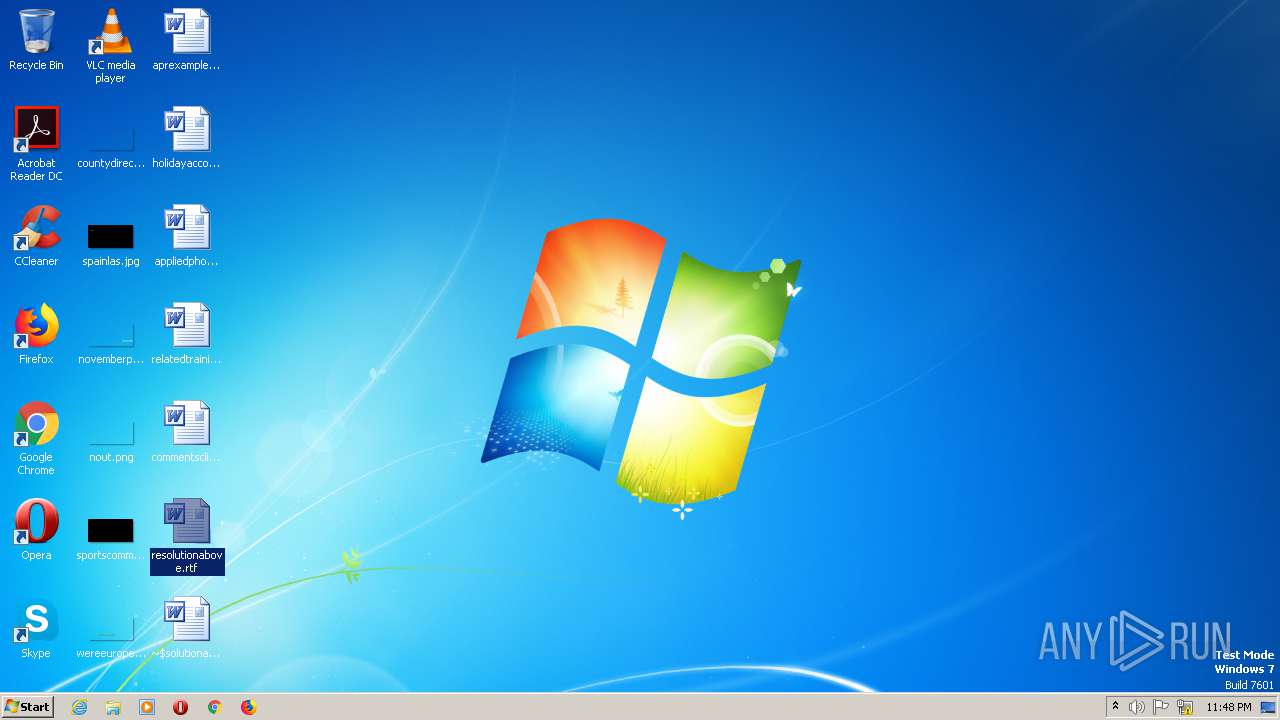
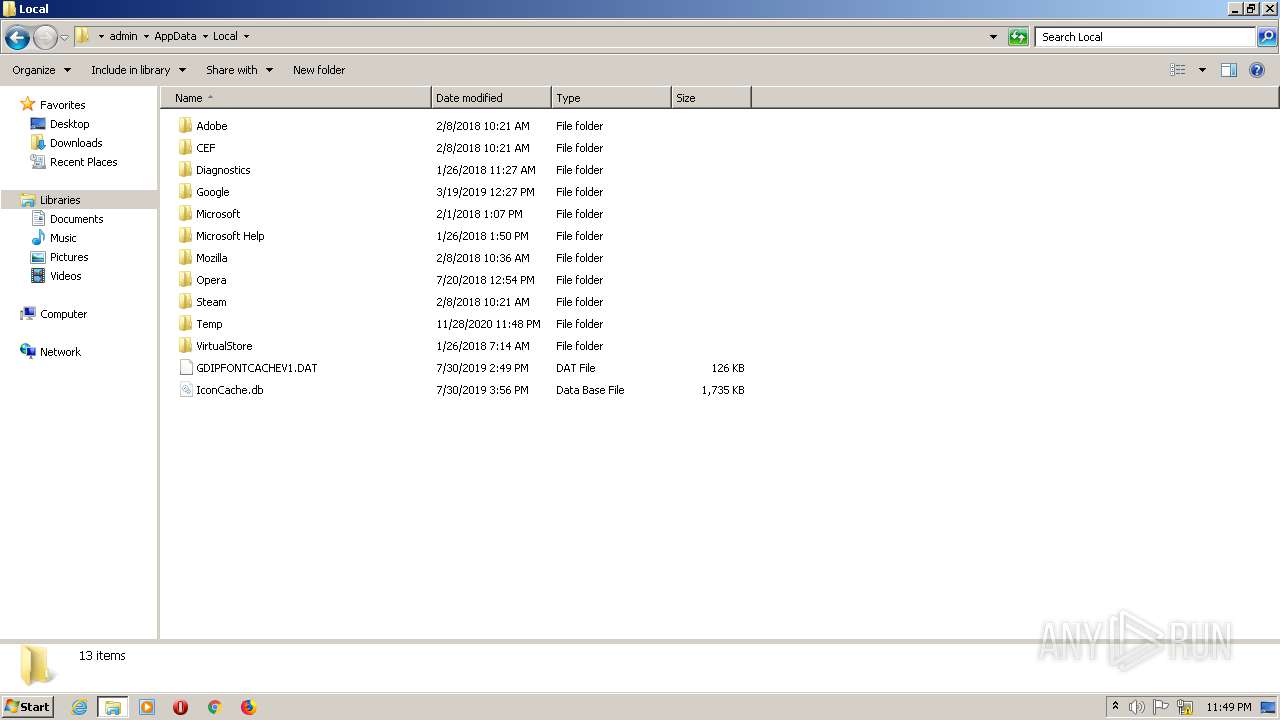
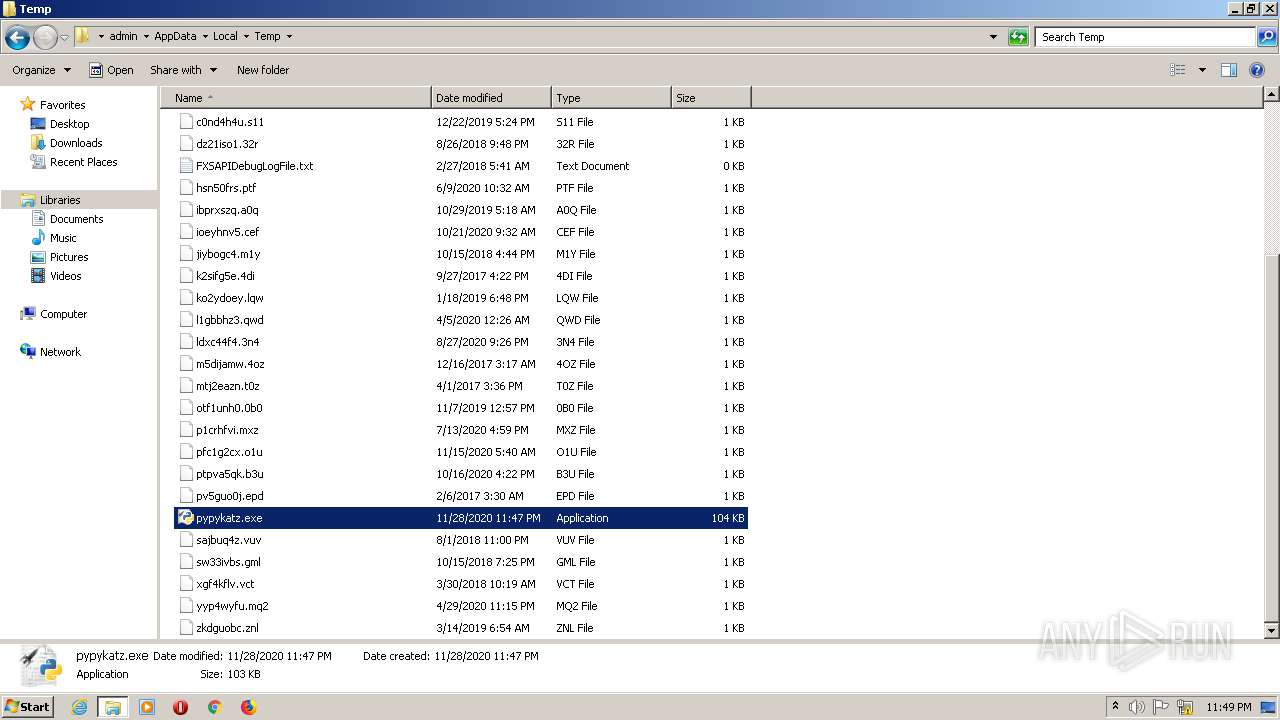
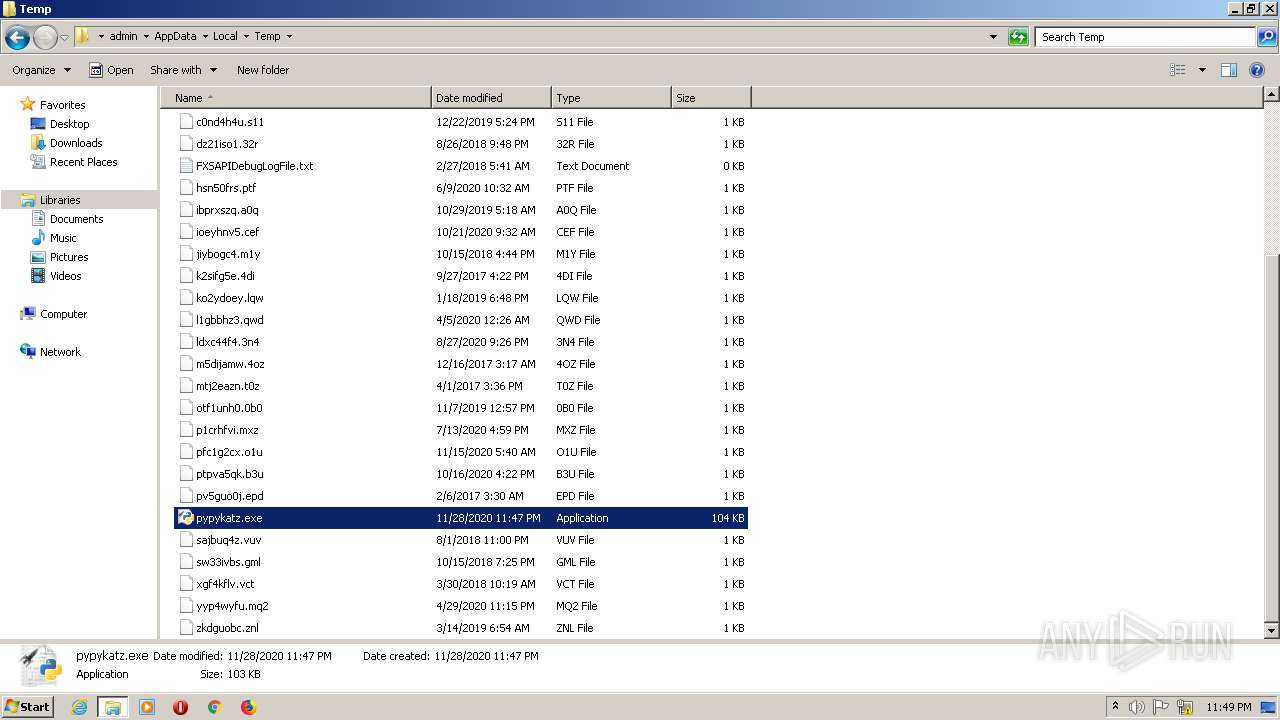
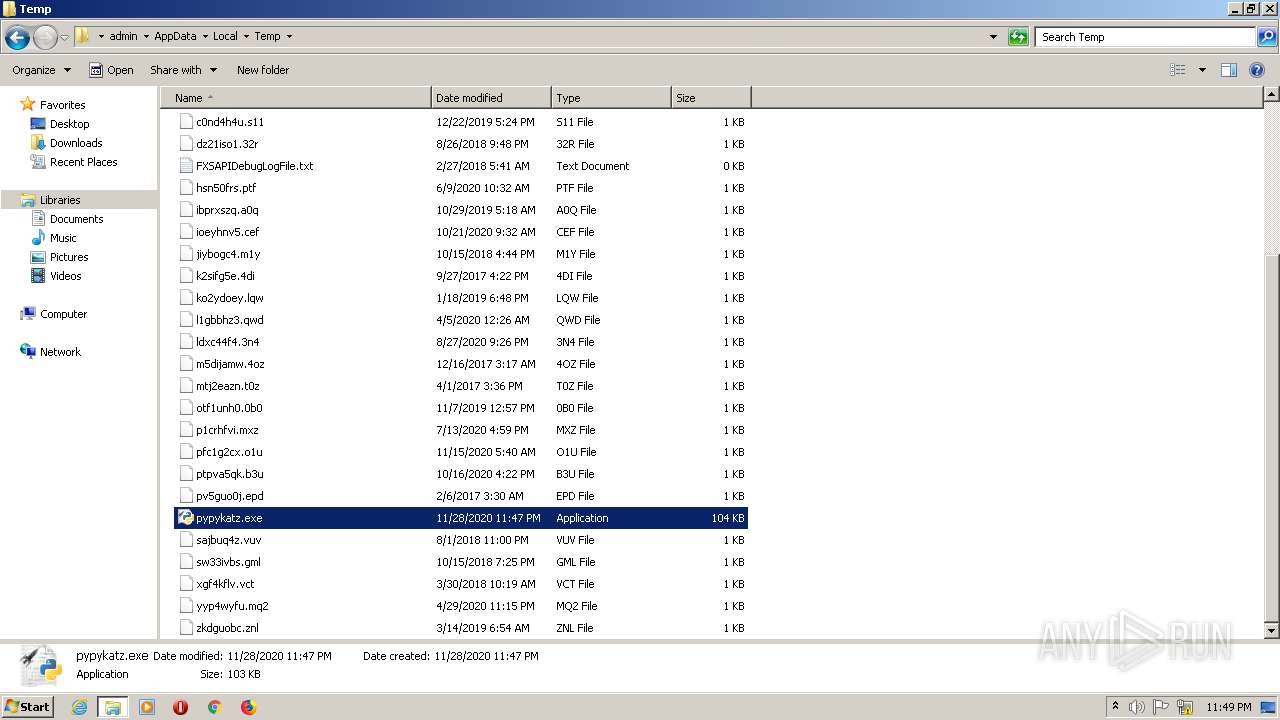
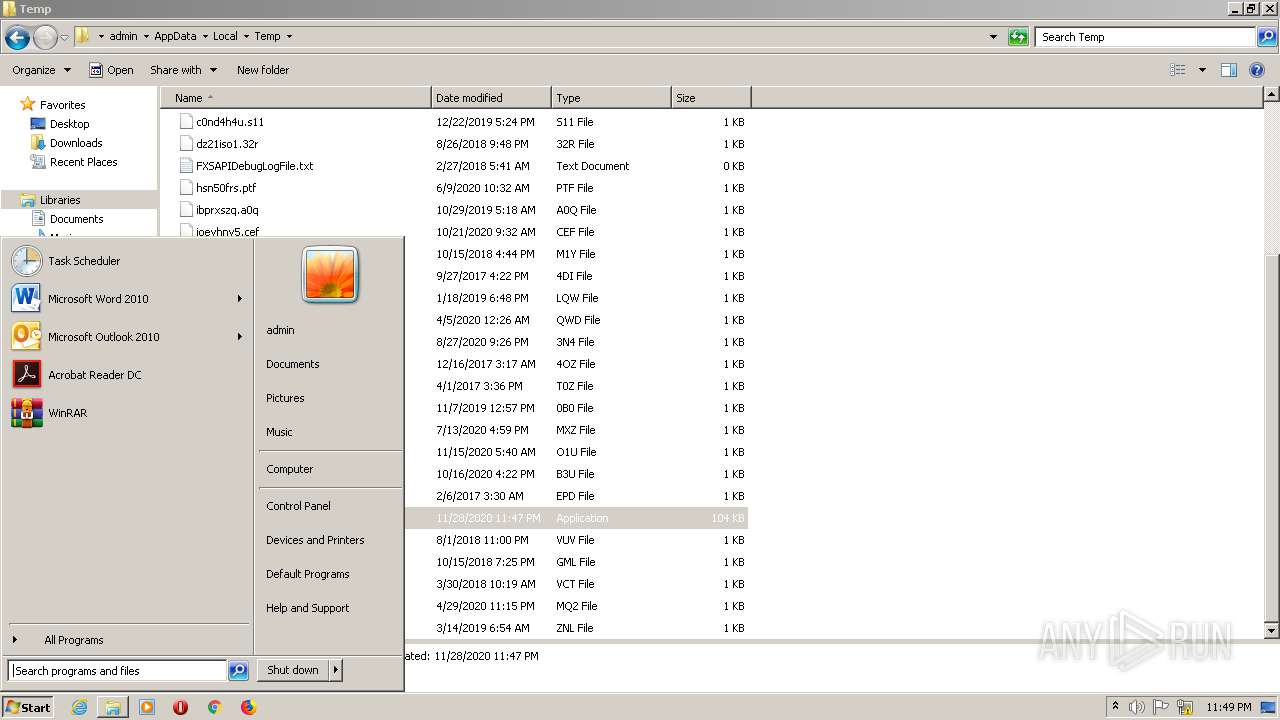
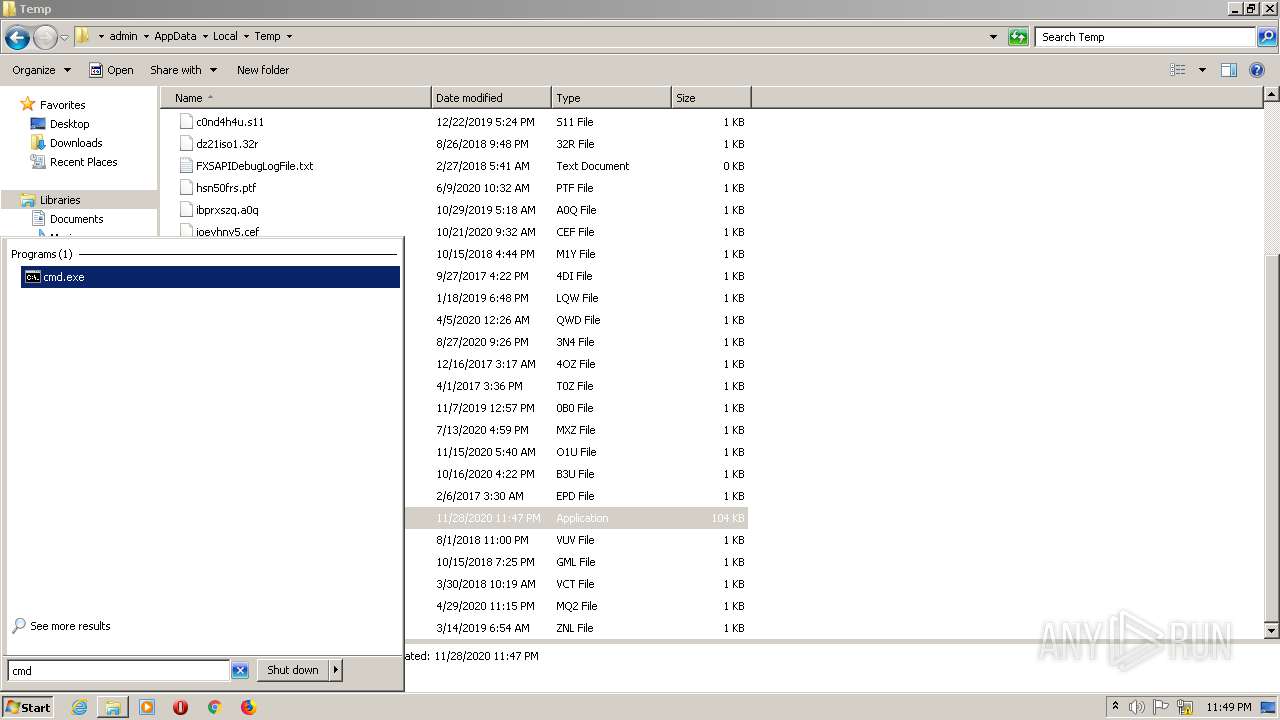
Manual execution by user
- explorer.exe (PID: 3000)
- explorer.exe (PID: 2908)
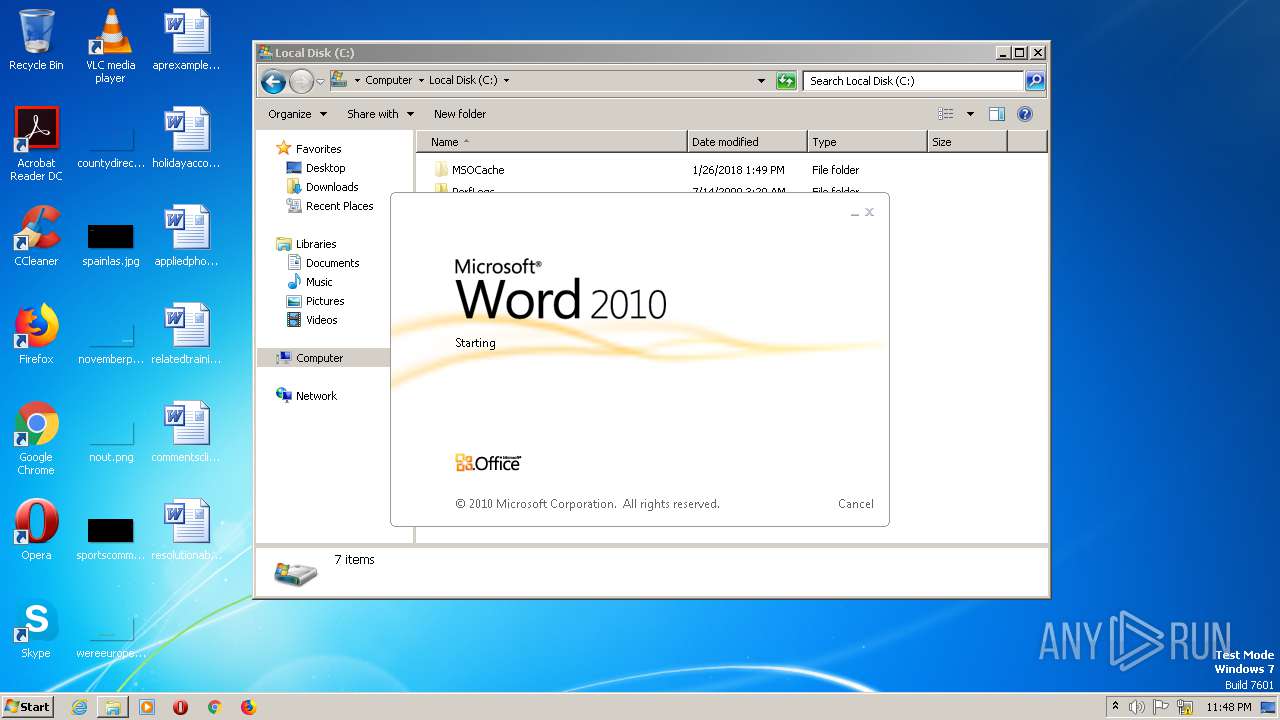
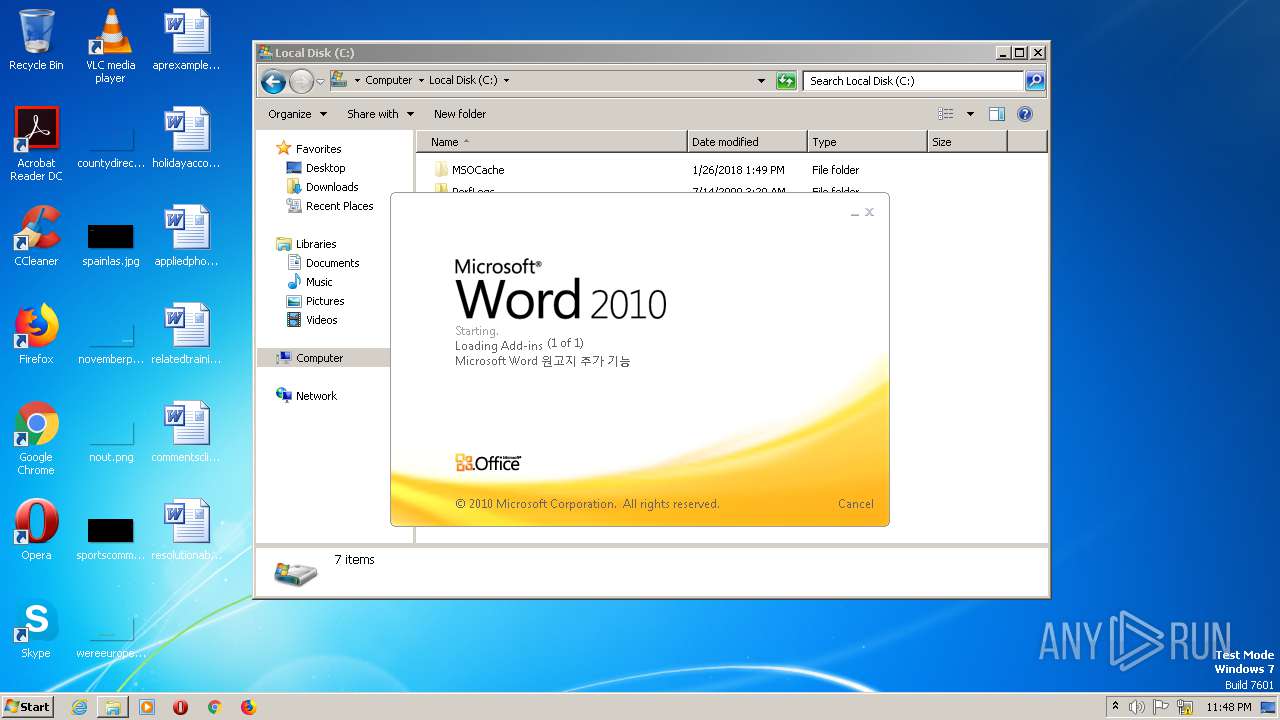
- WINWORD.EXE (PID: 2636)
- pypykatz.exe (PID: 2224)
- pypykatz.exe (PID: 1856)
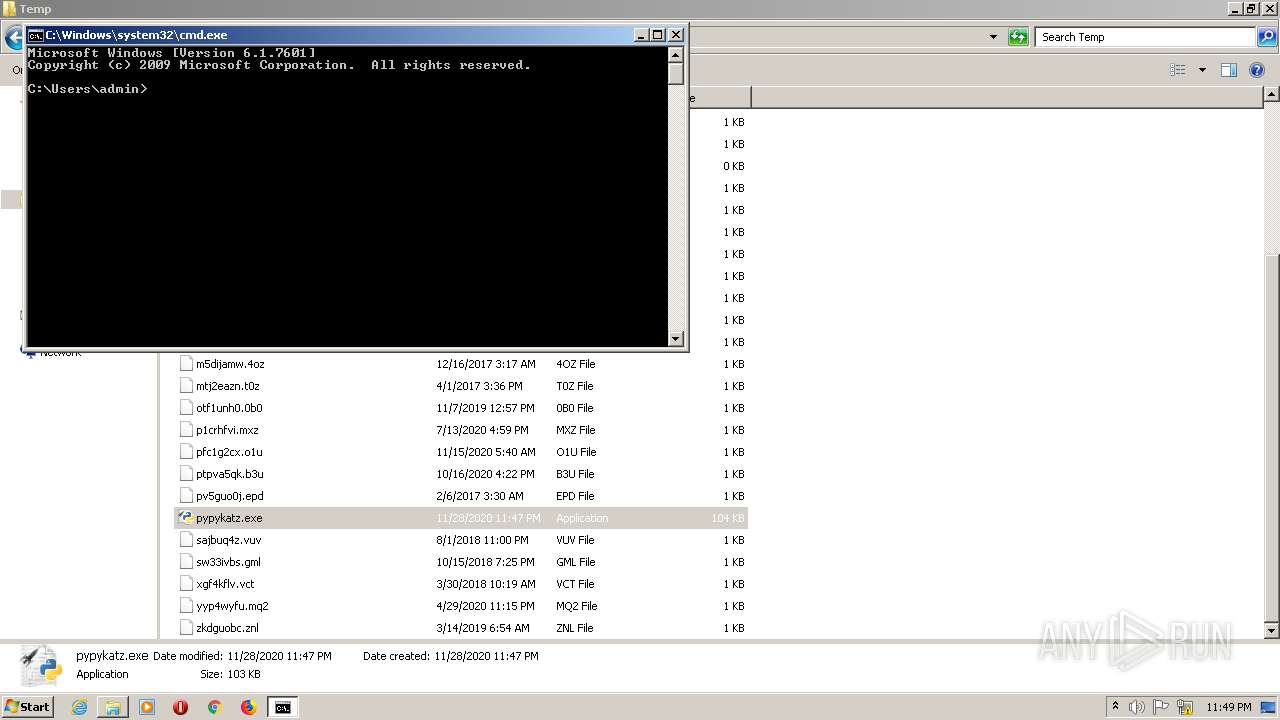
- cmd.exe (PID: 2692)
Creates files in the user directory
- WINWORD.EXE (PID: 2636)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:06:09 17:36:29+02:00 |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 60416 |
| InitializedDataSize: | 44544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x36c8 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jun-2019 15:36:29 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jun-2019 15:36:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EAEE | 0x0000EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39602 |
.rdata | 0x00010000 | 0x000037E8 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94664 |
.data | 0x00014000 | 0x00004084 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.98283 |
.pdata | 0x00019000 | 0x00000B1C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59842 |
.rsrc | 0x0001A000 | 0x000050A4 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.55595 |
.reloc | 0x00020000 | 0x0000034A | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.54205 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.40135 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.25903 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.90554 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.2247 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.14445 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.318 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.7862 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHLWAPI.dll |
Total processes
47
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
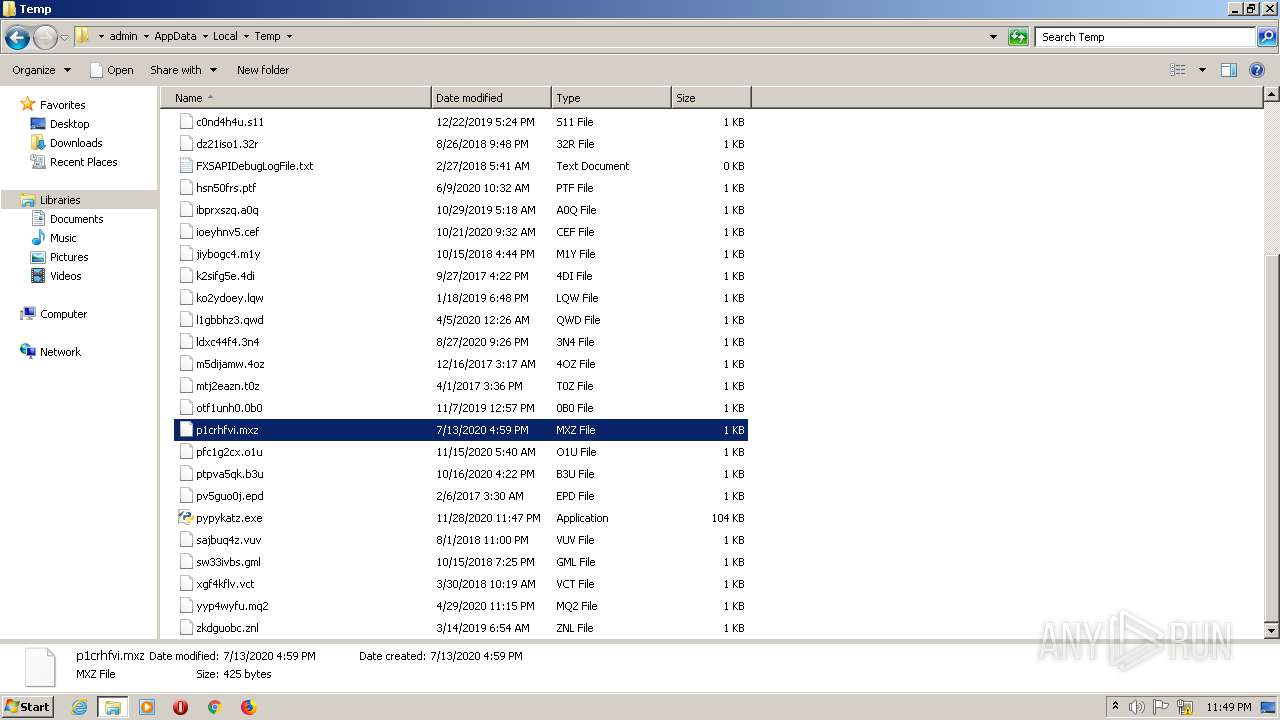
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
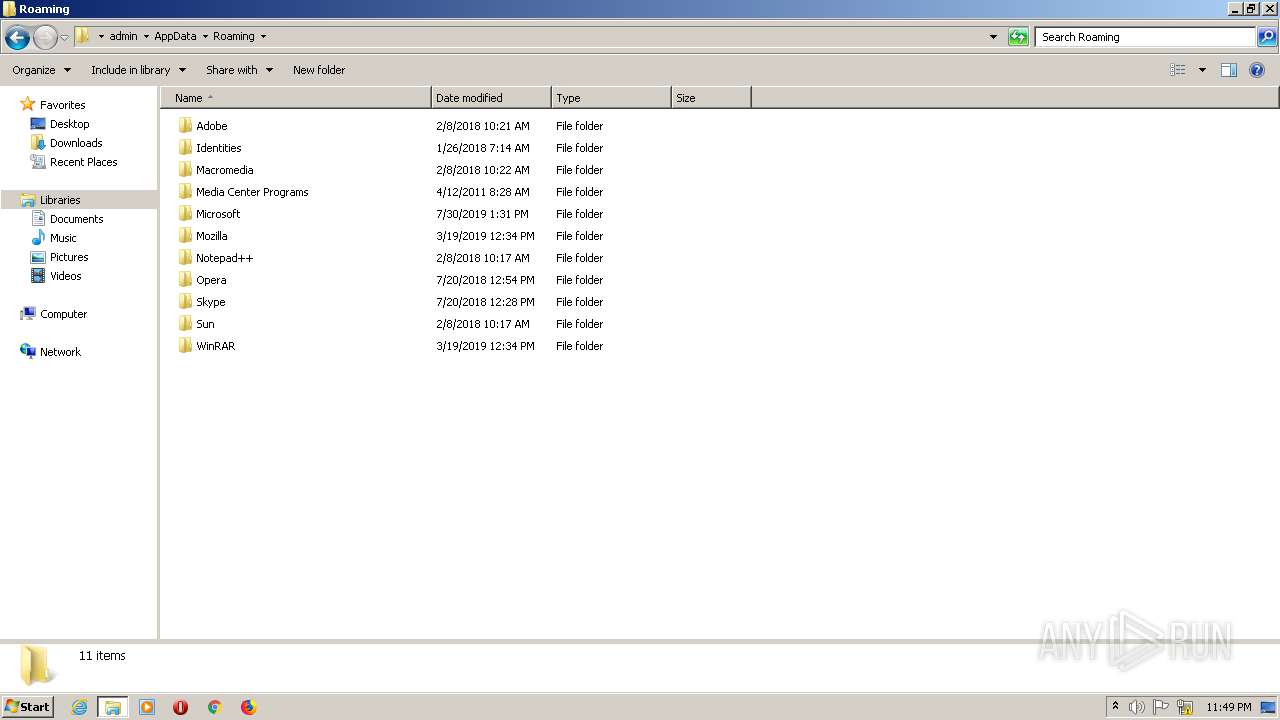
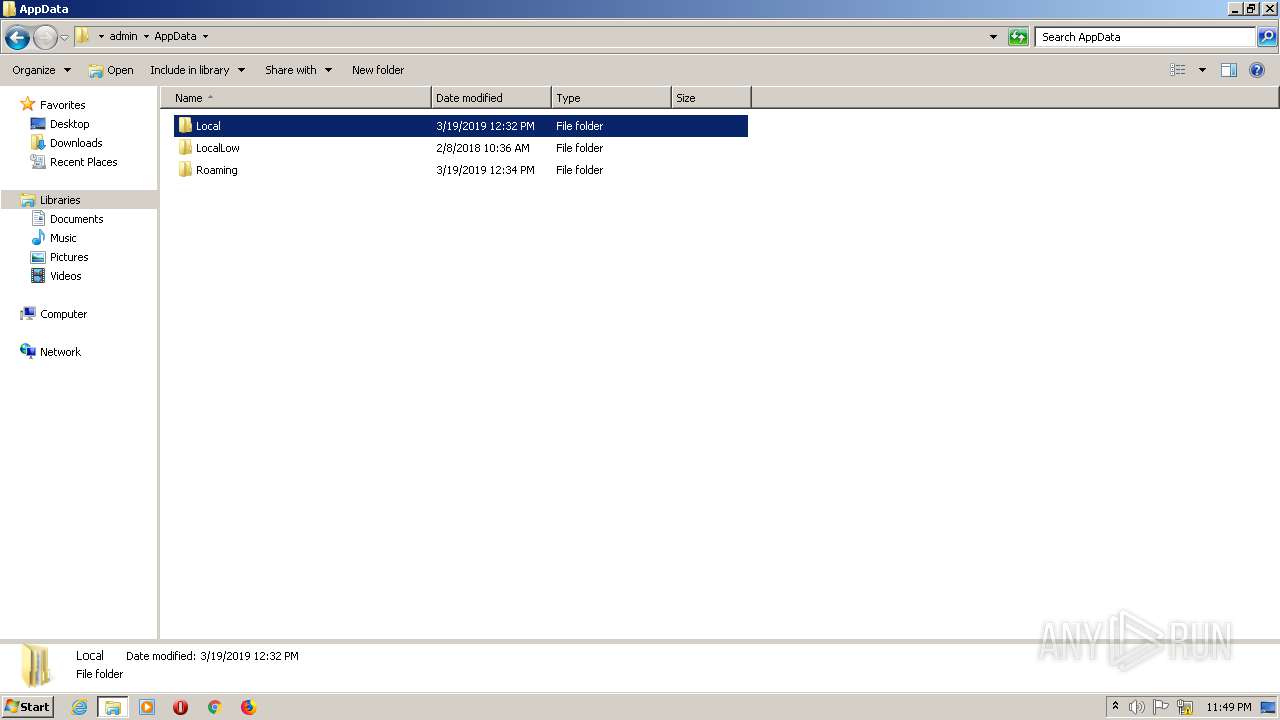
| 1856 | "C:\Users\admin\AppData\Local\Temp\pypykatz.exe" | C:\Users\admin\AppData\Local\Temp\pypykatz.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\pypykatz.exe" | C:\Users\admin\AppData\Local\Temp\pypykatz.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
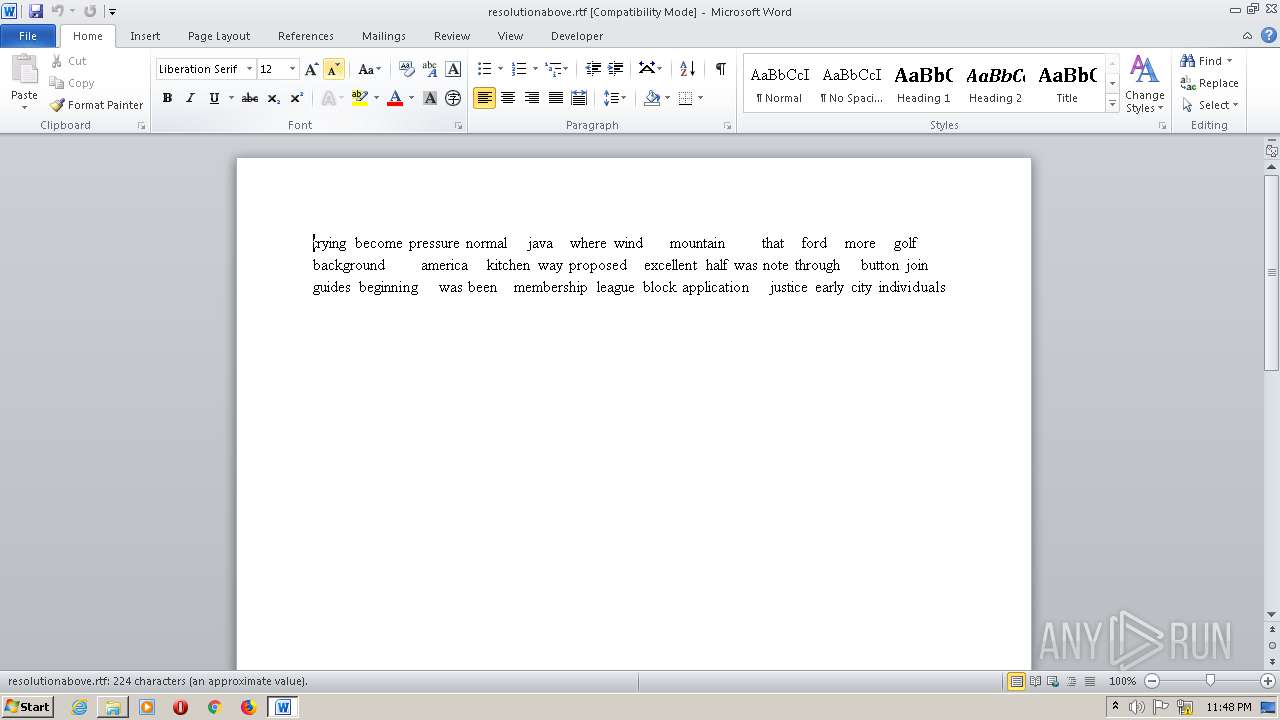
| 2636 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\resolutionabove.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 2692 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2908 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\pypykatz.exe" | C:\Users\admin\AppData\Local\Temp\pypykatz.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3000 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 203
Read events
896
Write events
168
Delete events
139
Modification events
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =b; |
Value: 3D623B004C0A0000010000000000000000000000 | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
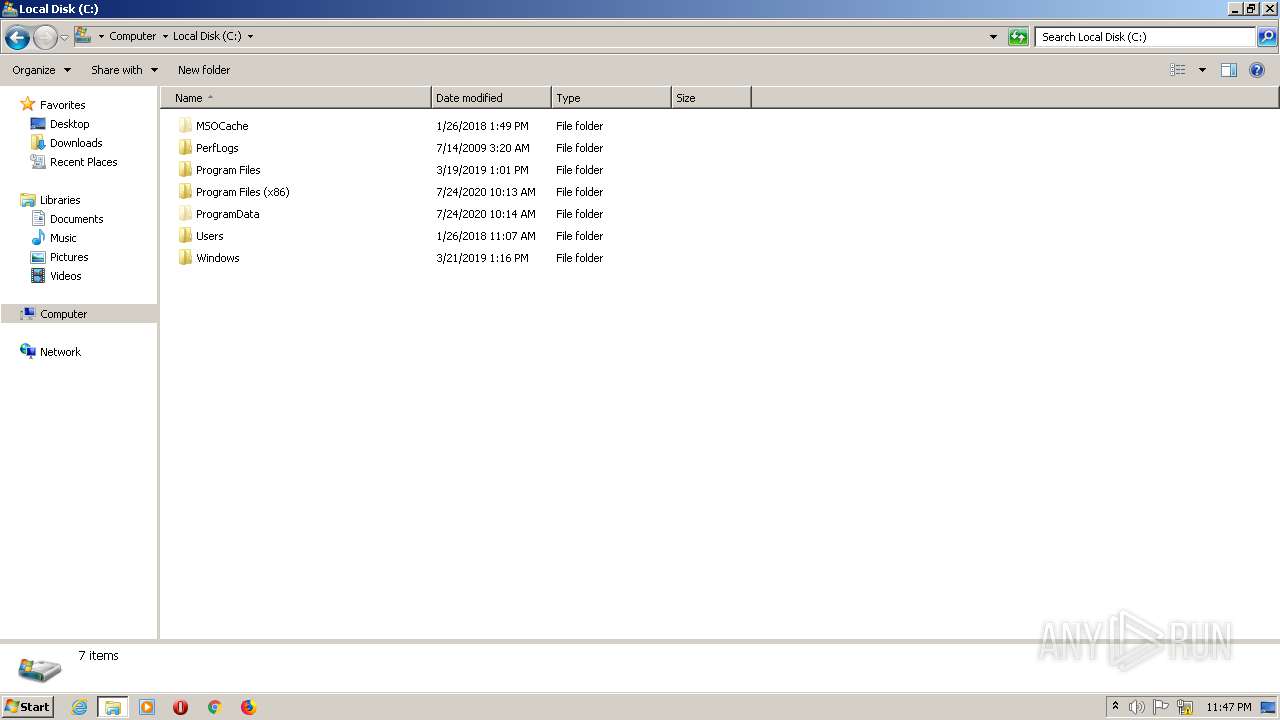
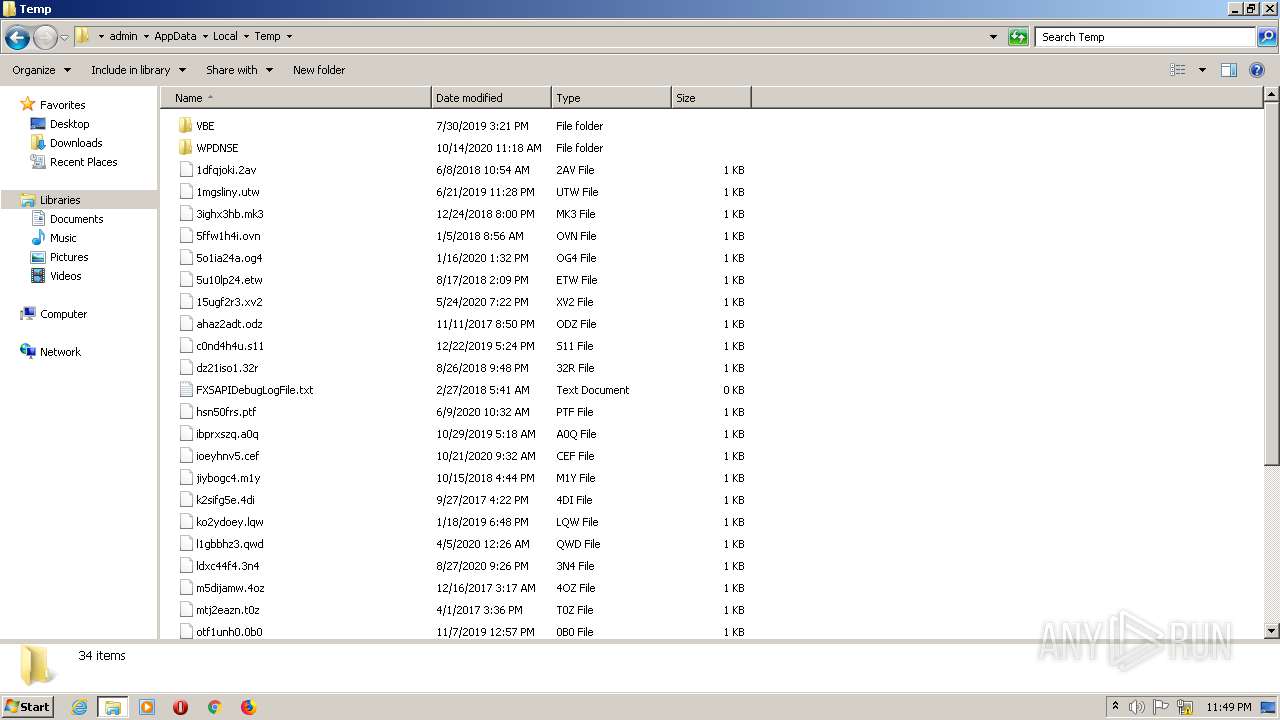
Executable files
0
Suspicious files
0
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCA3D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DCF7F17F-8E55-47F4-B877-734C4EA5AC91}.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{05D9F8EE-CCDD-4380-97F4-26000ED0F074}.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{7947B3D2-ADFA-4658-BBCF-70142BE066B5}.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\resolutionabove.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\Desktop\~$solutionabove.rtf | pgc | |
MD5:A0C0AED1BA11726D0FB198FBCE87EDF4 | SHA256:2BB341242EE27E9623EF8098AE465D3C0810F6C7F78164FCC7798DA0EC3E44BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report