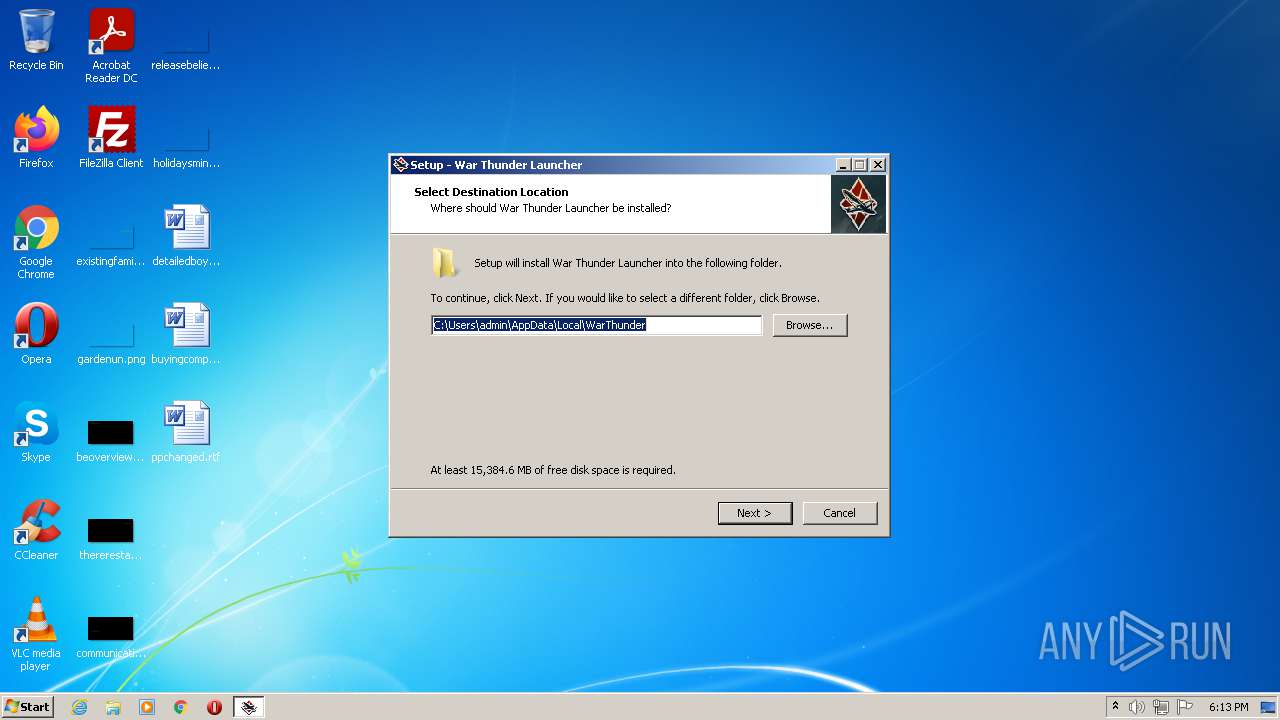
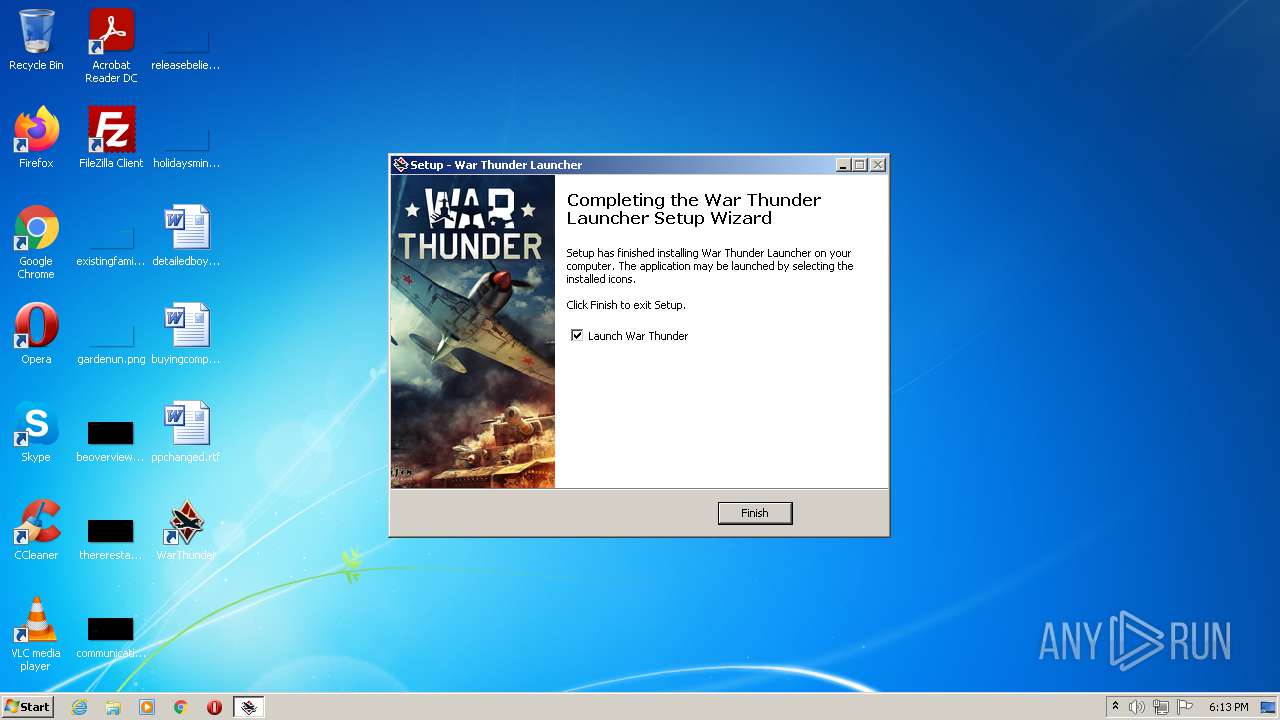
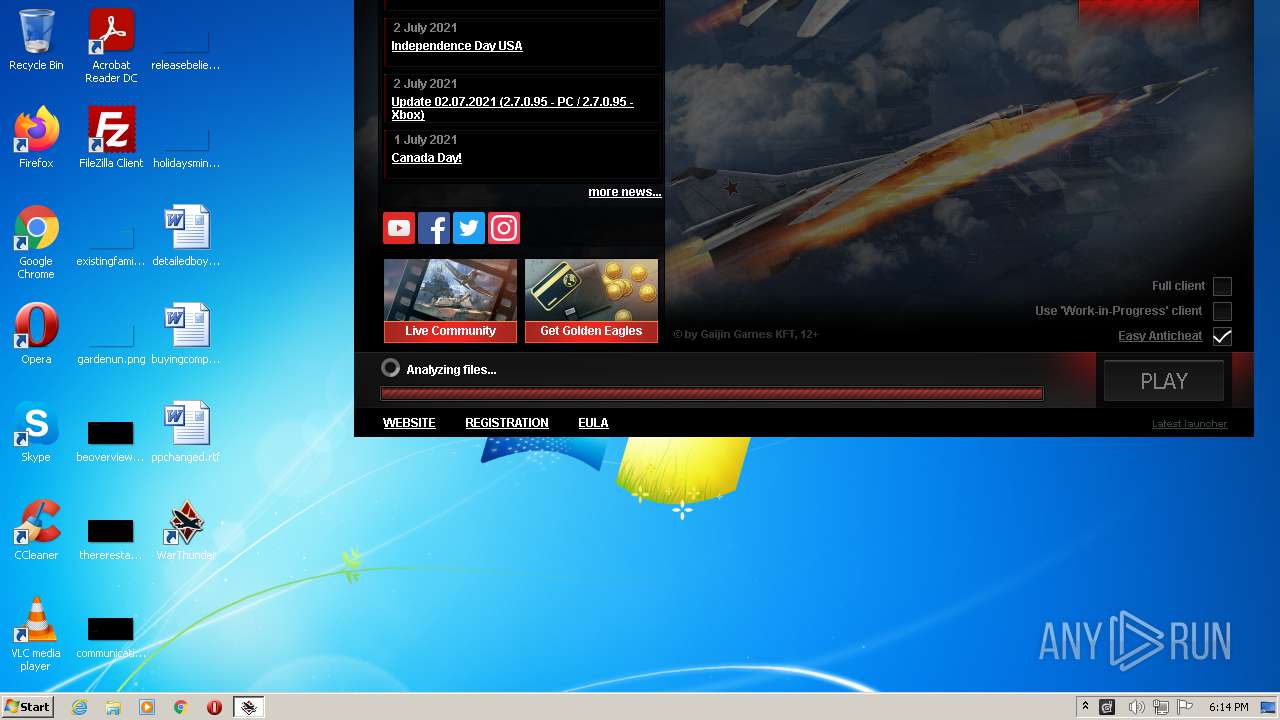
| File name: | wt_launcher_1.0.3.281-bwnv7jzmt.exe |
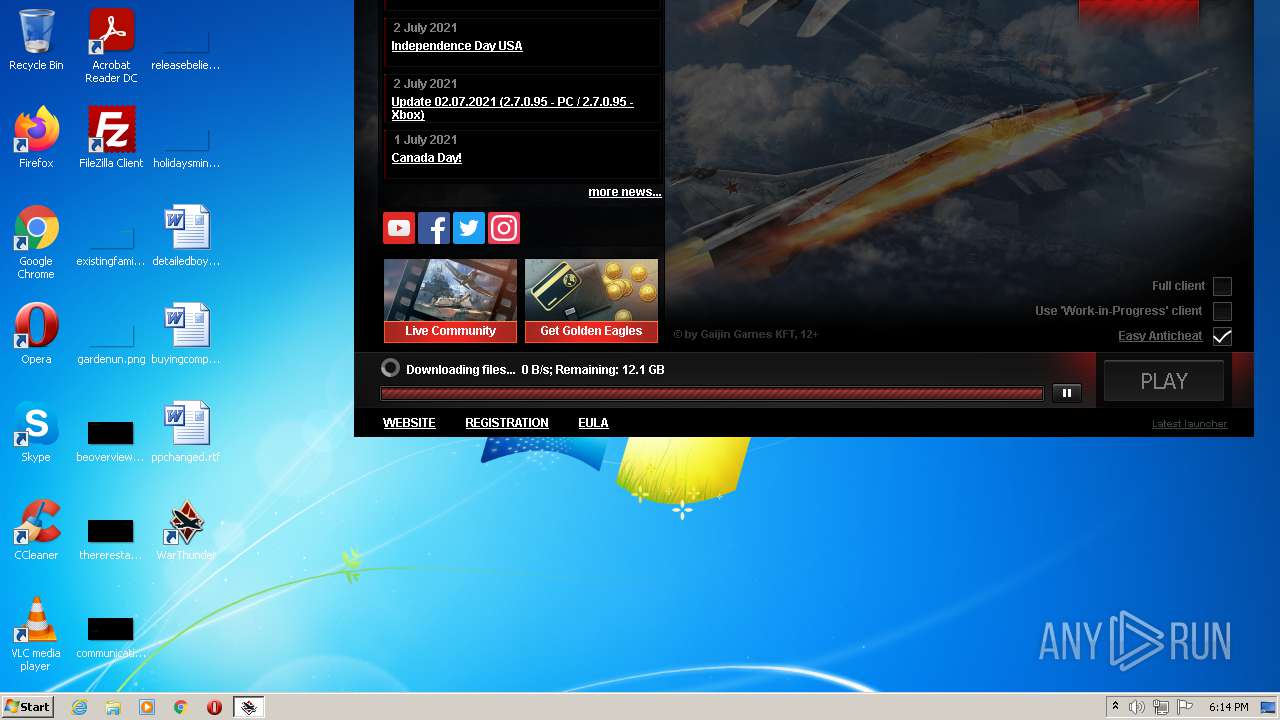
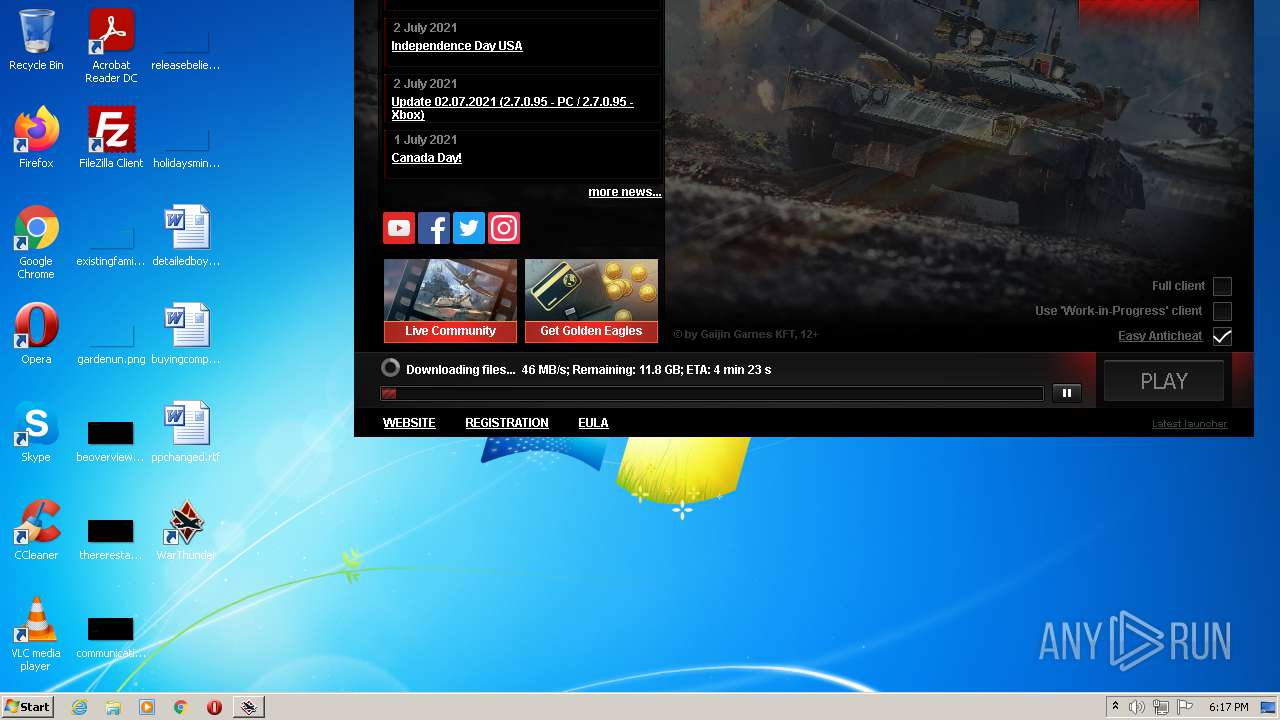
| Full analysis: | https://app.any.run/tasks/45ec9419-1d08-48c7-a56e-0d3cc5ca36a8 |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2021, 17:12:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 41AF89903762BE157F13D999DADDF092 |
| SHA1: | 69967AE2BA8CD4204FA477FC4BAA47A01B489330 |
| SHA256: | 295E0D8A0D6E59C6EA6B2140B53C06430B990387A28386D84CC4A4320C073B1E |
| SSDEEP: | 196608:a4BNt6EXMH3wXJMFj6Isi+AJvFlLmSPueWpemDL+LNlhFYBlRwxL6I:HtqH3wWBbnLvPuz8mvi4pieI |
MALICIOUS
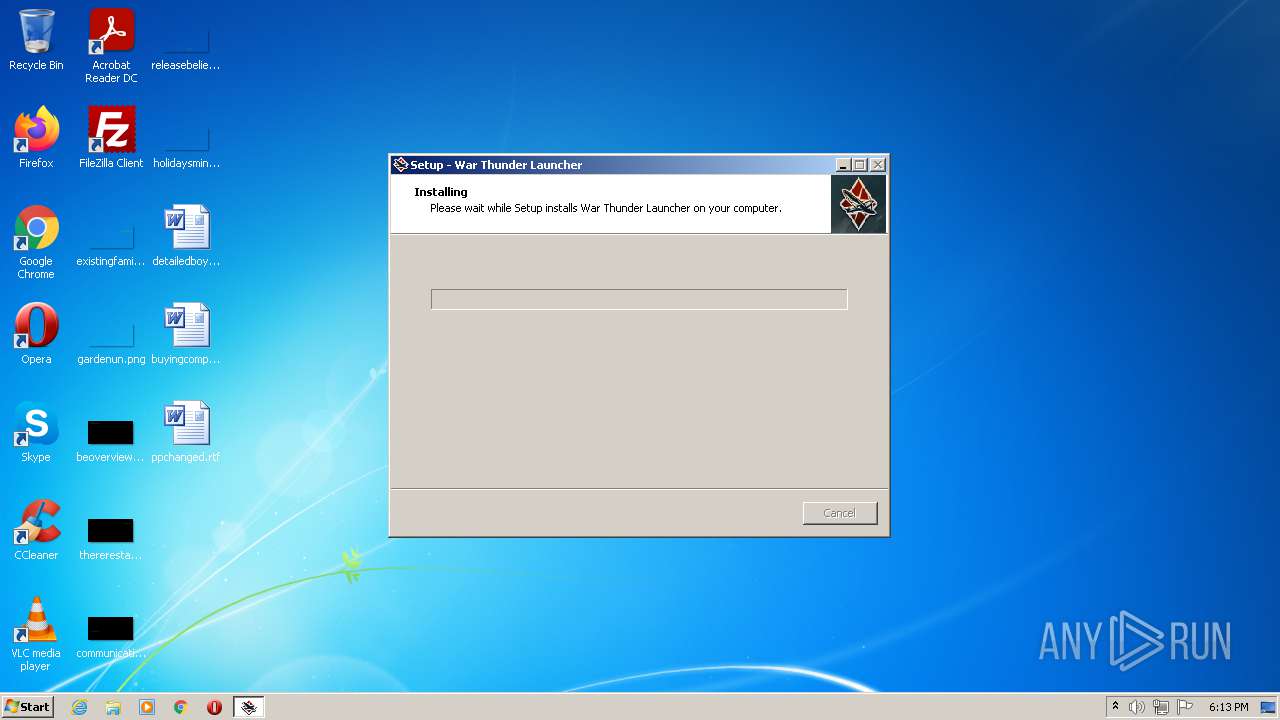
Drops executable file immediately after starts
- wt_launcher_1.0.3.281-bwnv7jzmt.exe (PID: 1788)
Loads dropped or rewritten executable
- launcher.exe (PID: 4040)
- gaijin_downloader.exe (PID: 328)
Application was dropped or rewritten from another process
- launcher.exe (PID: 4040)
- gaijin_downloader.exe (PID: 328)
- gjagent.exe (PID: 3888)
Changes the autorun value in the registry
- launcher.exe (PID: 4040)
SUSPICIOUS
Executable content was dropped or overwritten
- wt_launcher_1.0.3.281-bwnv7jzmt.exe (PID: 1788)
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
- launcher.exe (PID: 4040)
Checks supported languages
- wt_launcher_1.0.3.281-bwnv7jzmt.exe (PID: 1788)
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
- launcher.exe (PID: 4040)
- gaijin_downloader.exe (PID: 328)
- gjagent.exe (PID: 3888)
Reads the computer name
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
- launcher.exe (PID: 4040)
- gaijin_downloader.exe (PID: 328)
- gjagent.exe (PID: 3888)
Drops a file that was compiled in debug mode
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
- launcher.exe (PID: 4040)
Reads Windows owner or organization settings
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Uses NETSH.EXE for network configuration
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Drops a file with too old compile date
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Creates files in the user directory
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Reads Environment values
- netsh.exe (PID: 1064)
- netsh.exe (PID: 3568)
- netsh.exe (PID: 1956)
- netsh.exe (PID: 3600)
- netsh.exe (PID: 3216)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 1620)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 2716)
- netsh.exe (PID: 3912)
- netsh.exe (PID: 4040)
- netsh.exe (PID: 3740)
- netsh.exe (PID: 3632)
- netsh.exe (PID: 3844)
- netsh.exe (PID: 3092)
- netsh.exe (PID: 1240)
- netsh.exe (PID: 3248)
- netsh.exe (PID: 3040)
- netsh.exe (PID: 3492)
- netsh.exe (PID: 2696)
- netsh.exe (PID: 2528)
- netsh.exe (PID: 3192)
- netsh.exe (PID: 2468)
- netsh.exe (PID: 3960)
Reads the Windows organization settings
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
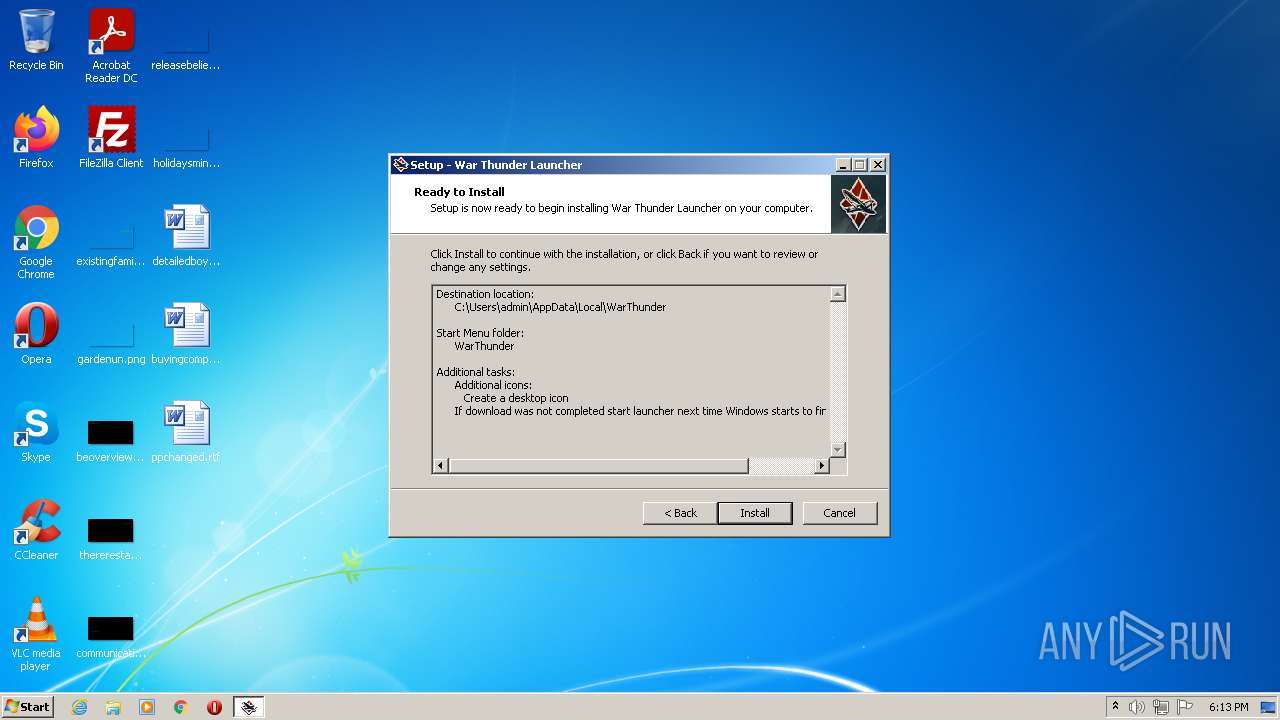
Creates a directory in Program Files
- launcher.exe (PID: 4040)
- gjagent.exe (PID: 3888)
Creates files in the program directory
- launcher.exe (PID: 4040)
- gjagent.exe (PID: 3888)
INFO
Application was dropped or rewritten from another process
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Dropped object may contain Bitcoin addresses
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Reads settings of System Certificates
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
- launcher.exe (PID: 4040)
Checks supported languages
- netsh.exe (PID: 3600)
- netsh.exe (PID: 1064)
- netsh.exe (PID: 3568)
- netsh.exe (PID: 3216)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 1956)
- netsh.exe (PID: 1620)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 3912)
- netsh.exe (PID: 4040)
- netsh.exe (PID: 3740)
- netsh.exe (PID: 2716)
- netsh.exe (PID: 3844)
- netsh.exe (PID: 3632)
- netsh.exe (PID: 1240)
- netsh.exe (PID: 3248)
- netsh.exe (PID: 3040)
- netsh.exe (PID: 3492)
- netsh.exe (PID: 3092)
- netsh.exe (PID: 2696)
- netsh.exe (PID: 2528)
- netsh.exe (PID: 3960)
- netsh.exe (PID: 2468)
- netsh.exe (PID: 3192)
Reads the computer name
- netsh.exe (PID: 1064)
- netsh.exe (PID: 1956)
- netsh.exe (PID: 3216)
- netsh.exe (PID: 3600)
- netsh.exe (PID: 3568)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 1620)
- netsh.exe (PID: 3912)
- netsh.exe (PID: 4040)
- netsh.exe (PID: 3740)
- netsh.exe (PID: 2716)
- netsh.exe (PID: 3844)
- netsh.exe (PID: 3632)
- netsh.exe (PID: 2656)
- netsh.exe (PID: 3040)
- netsh.exe (PID: 1240)
- netsh.exe (PID: 3248)
- netsh.exe (PID: 3492)
- netsh.exe (PID: 3092)
- netsh.exe (PID: 2696)
- netsh.exe (PID: 3960)
- netsh.exe (PID: 3192)
- netsh.exe (PID: 2468)
- netsh.exe (PID: 2528)
Creates a software uninstall entry
- wt_launcher_1.0.3.281-bwnv7jzmt.tmp (PID: 1776)
Checks Windows Trust Settings
- launcher.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| ProductVersion: | |
|---|---|
| ProductName: | War Thunder Launcher |
| LegalCopyright: | 2014-2021 Gaijin Games KFT |
| FileVersion: | |
| FileDescription: | War Thunder Launcher Setup |
| CompanyName: | Gaijin Network |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x117dc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 197632 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Gaijin Network |
| FileDescription: | War Thunder Launcher Setup |
| FileVersion: | - |
| LegalCopyright: | 2014-2021 Gaijin Games KFT |
| ProductName: | War Thunder Launcher |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0002E388 | 0x0002E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98585 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.06242 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.60642 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.56266 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.21177 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.97494 | 40363 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.01385 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.29994 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.39193 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.11809 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
86
Monitored processes
29
Malicious processes
2
Suspicious processes
2
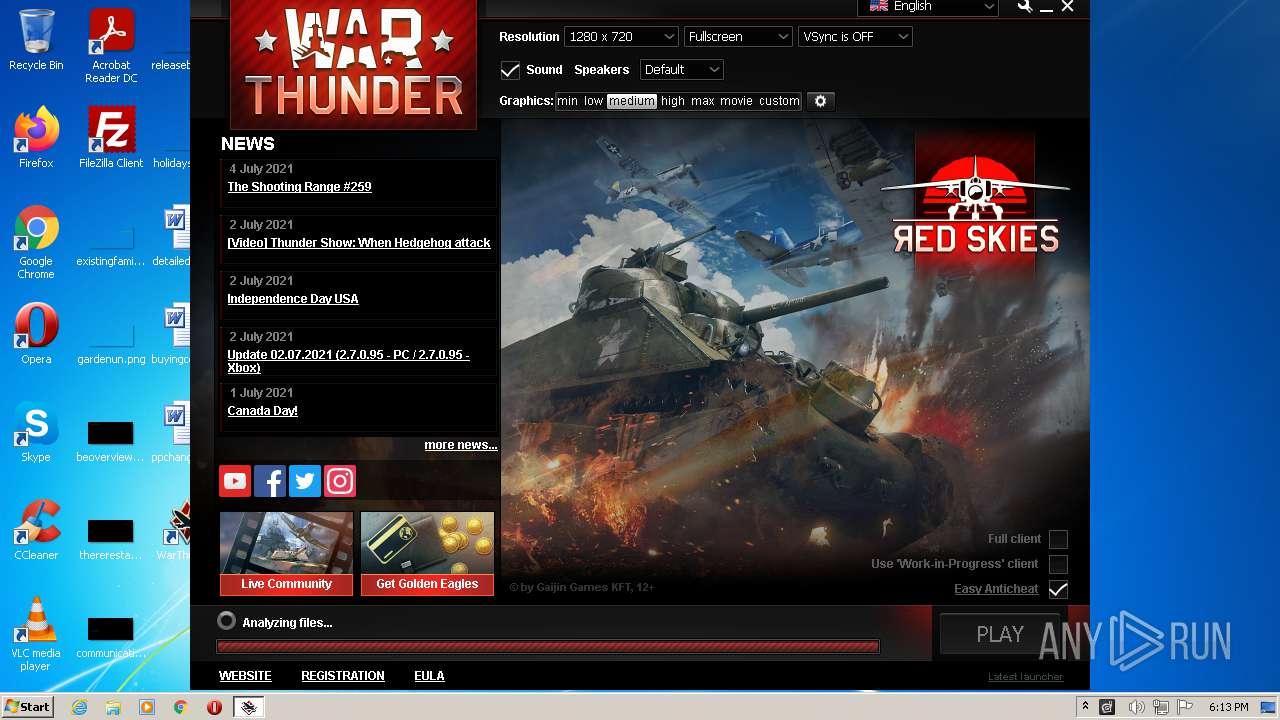
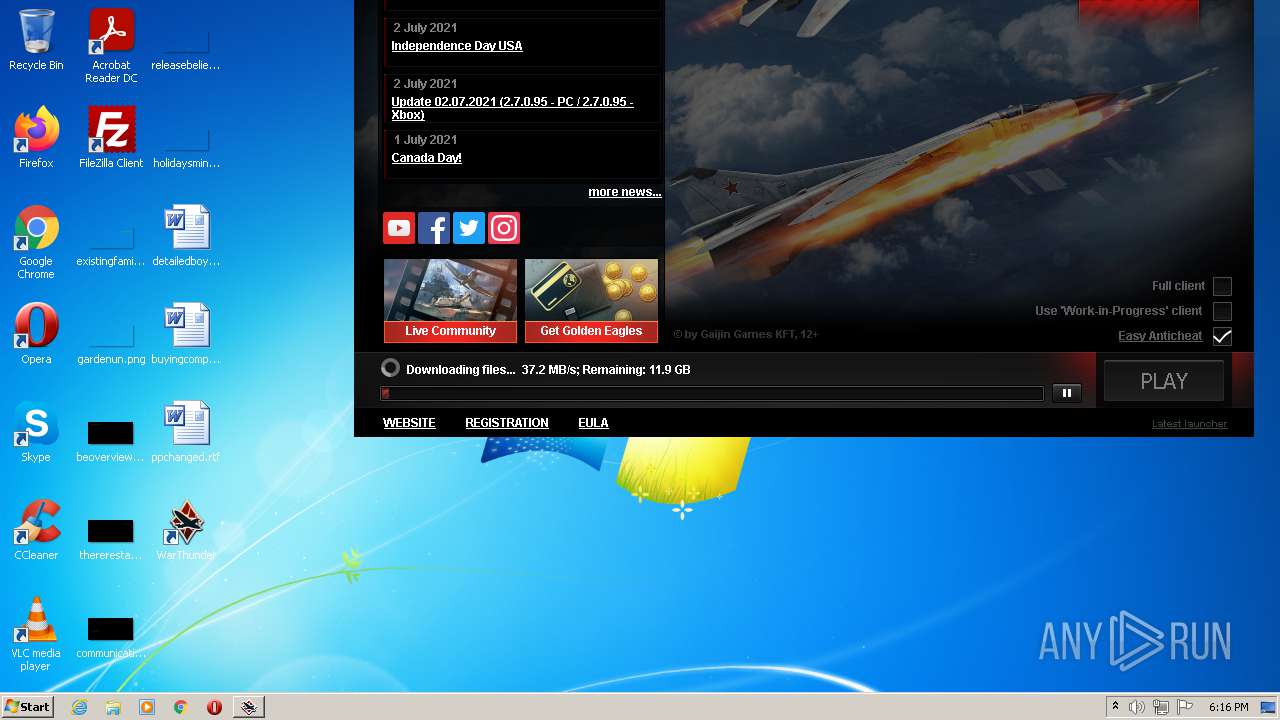
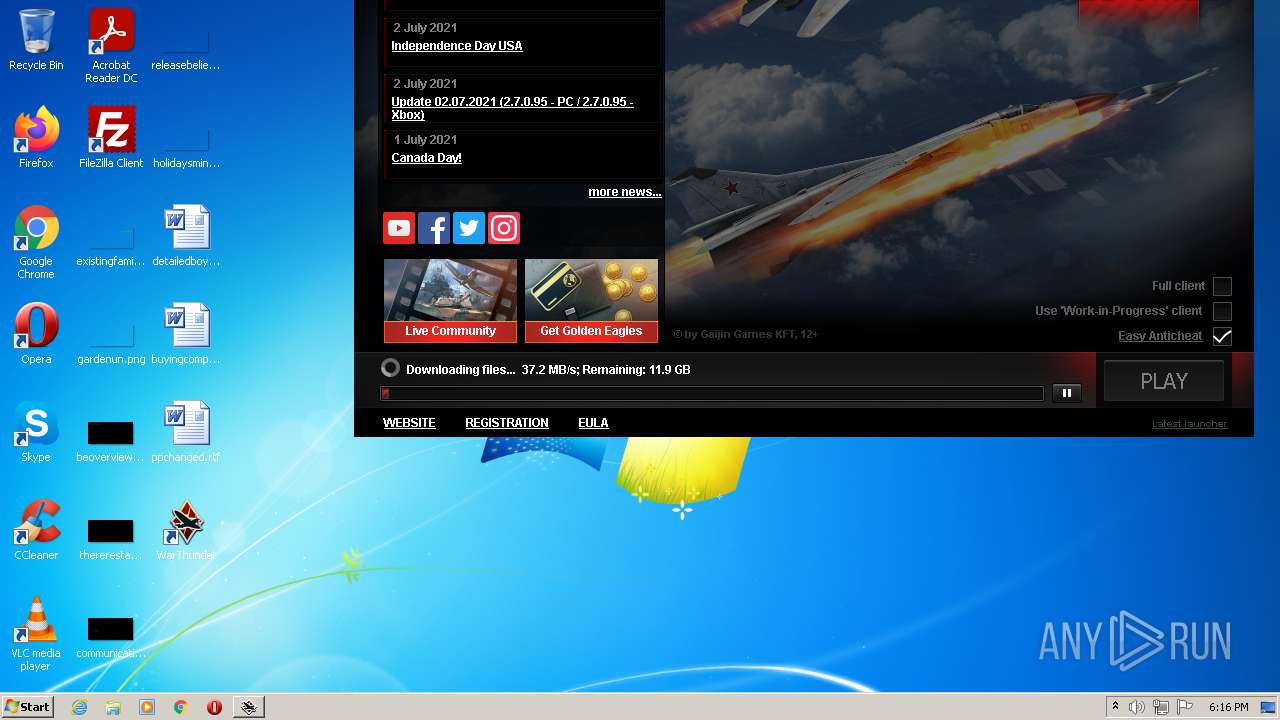
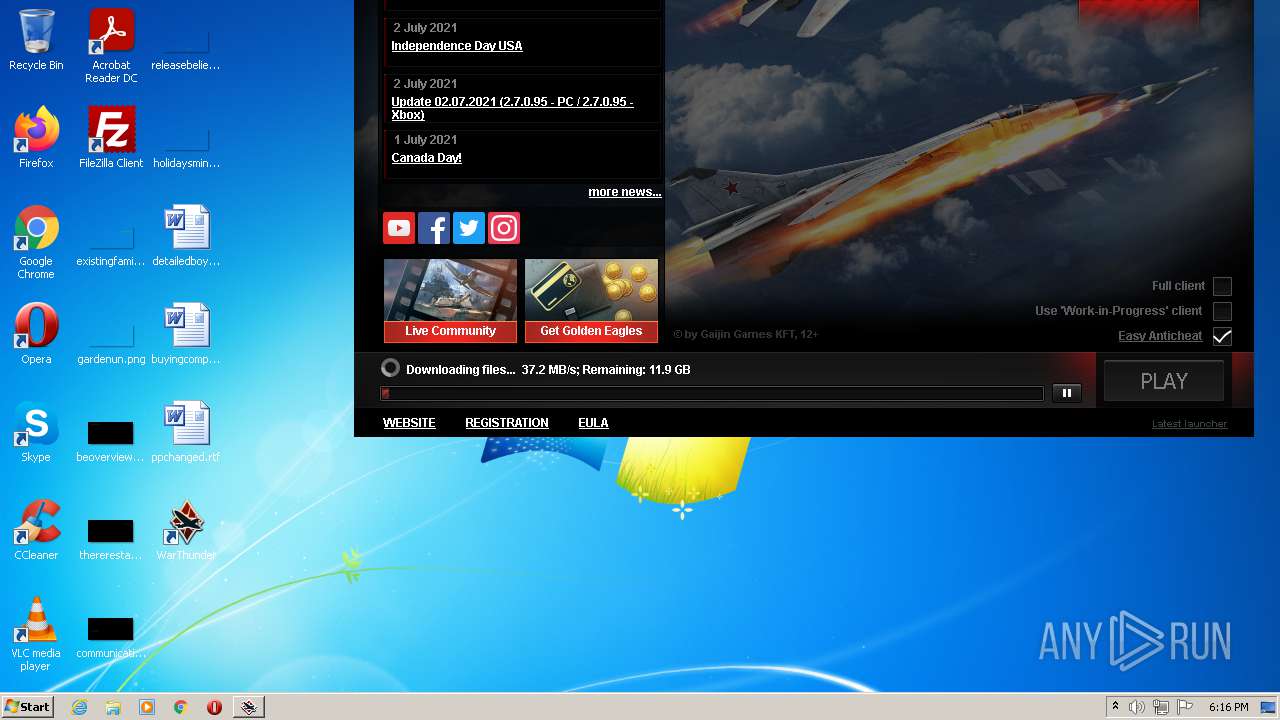
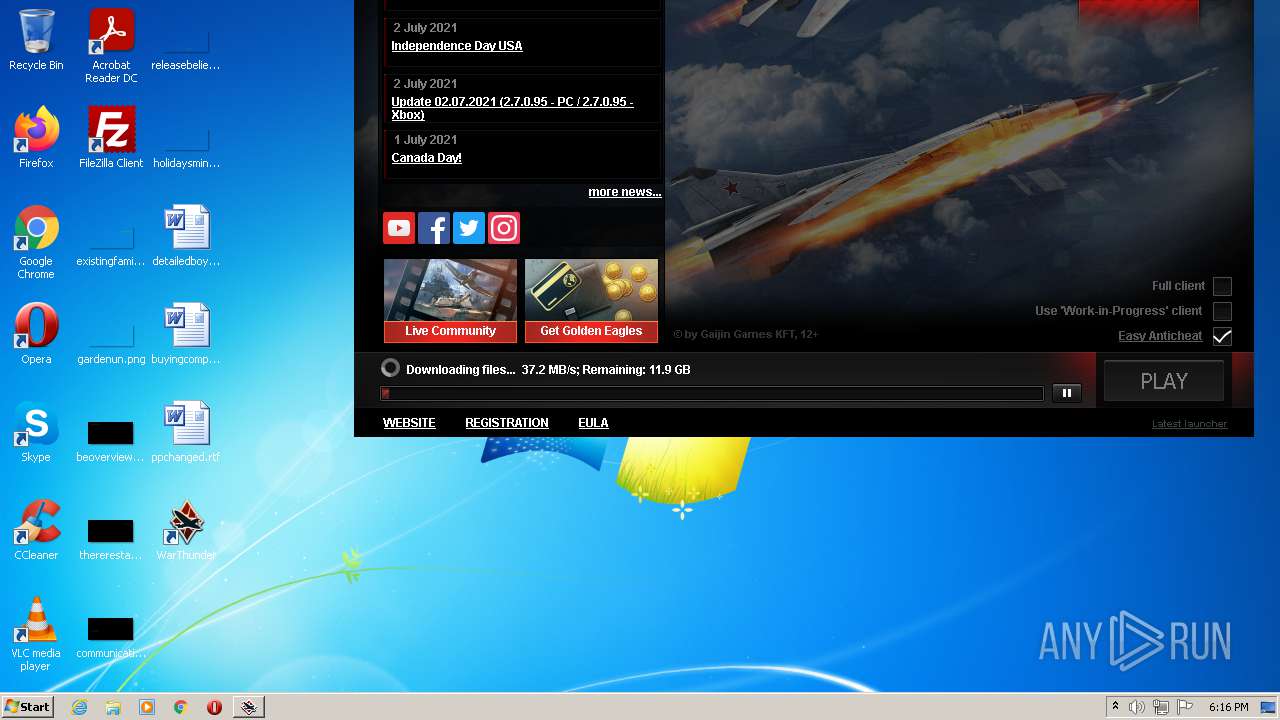
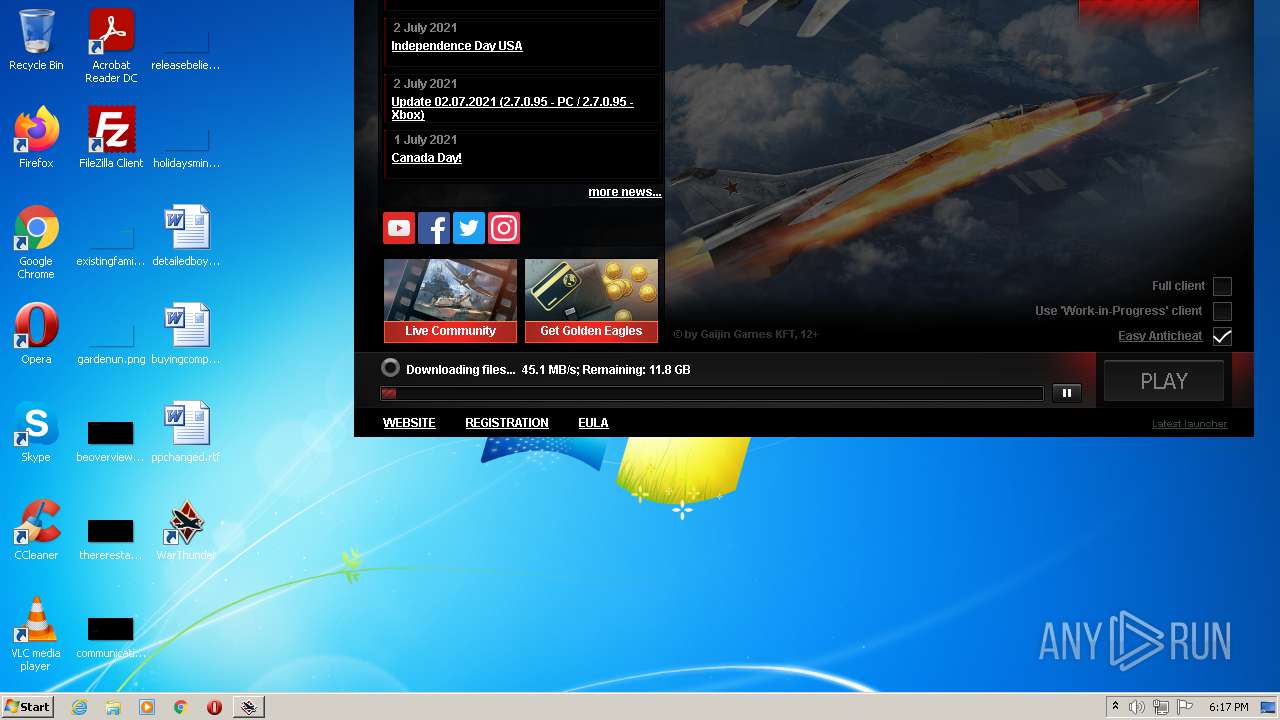
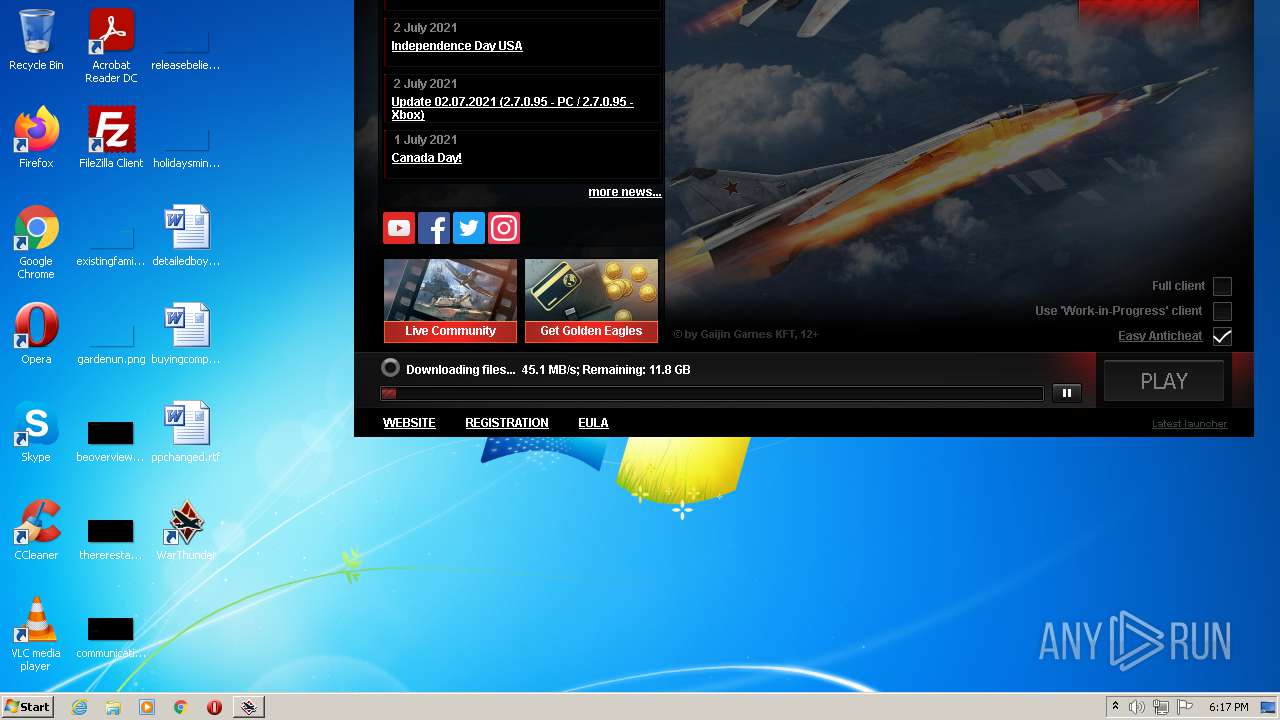
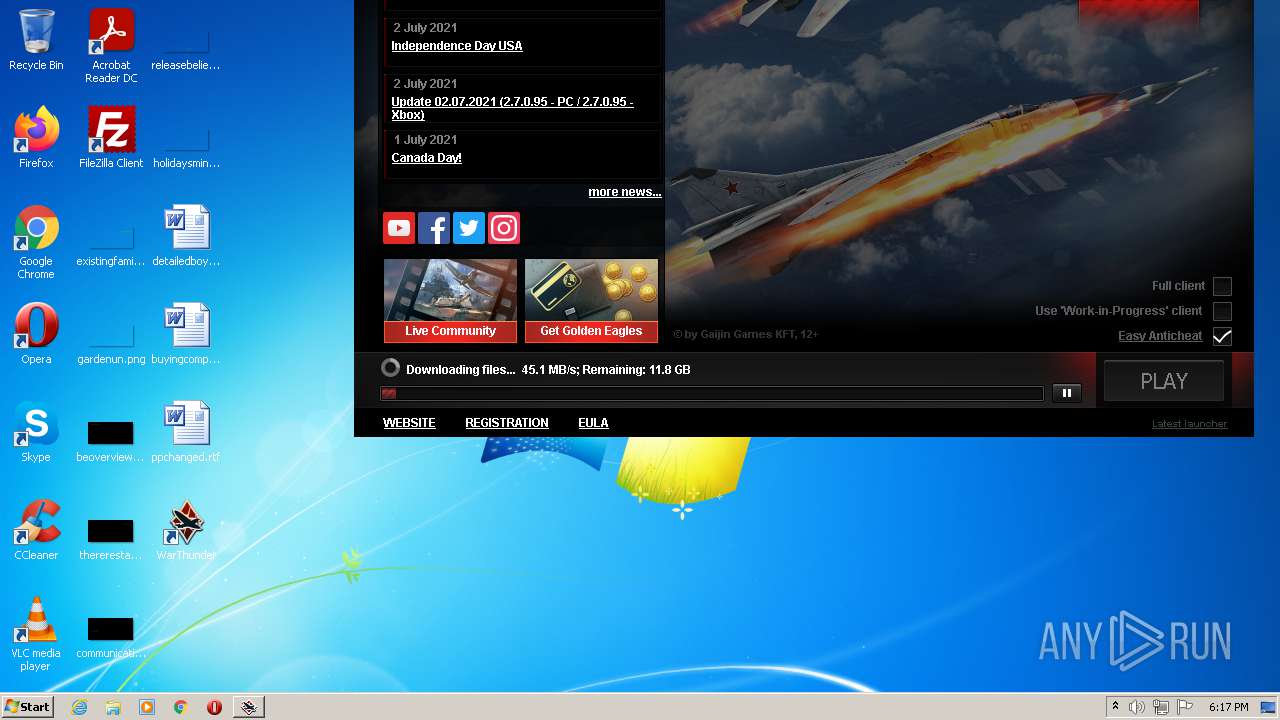
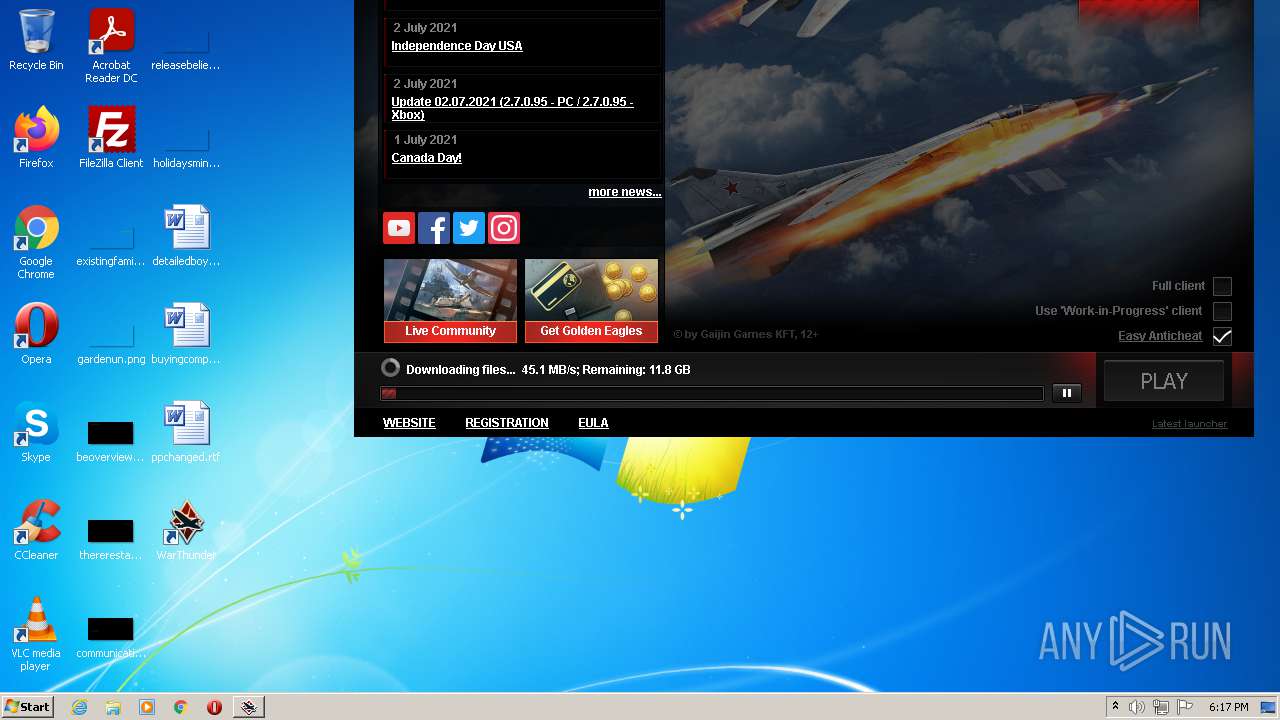
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Users\admin\AppData\Local\WarThunder\gaijin_downloader.exe" -appid WarThunderLauncherZip -localversion 1.0.3.281 -execpath launcher.exe -notify_user_about_failure -conditional_gui_app_restart | C:\Users\admin\AppData\Local\WarThunder\gaijin_downloader.exe | launcher.exe | ||||||||||||
User: admin Company: Gaijin Integrity Level: MEDIUM Description: Gaijin Downloader Exit code: 0 Modules
| |||||||||||||||
| 1064 | "C:\Windows\system32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\WarThunder\launcher.exe" "War Thunder launcher" ENABLE ALL | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | "C:\Windows\system32\netsh" firewall add portopening protocol = UDP port = 20010-20500 name = "War Thunder" | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | "C:\Windows\system32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\WarThunder\win32\bpreport.exe" "War Thunder Crash Reporter" ENABLE ALL | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | "C:\Users\admin\AppData\Local\Temp\is-VVUBH.tmp\wt_launcher_1.0.3.281-bwnv7jzmt.tmp" /SL5="$1801B8,9861467,265216,C:\Users\admin\AppData\Local\Temp\wt_launcher_1.0.3.281-bwnv7jzmt.exe" | C:\Users\admin\AppData\Local\Temp\is-VVUBH.tmp\wt_launcher_1.0.3.281-bwnv7jzmt.tmp | wt_launcher_1.0.3.281-bwnv7jzmt.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1788 | "C:\Users\admin\AppData\Local\Temp\wt_launcher_1.0.3.281-bwnv7jzmt.exe" | C:\Users\admin\AppData\Local\Temp\wt_launcher_1.0.3.281-bwnv7jzmt.exe | Explorer.EXE | ||||||||||||
User: admin Company: Gaijin Network Integrity Level: MEDIUM Description: War Thunder Launcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1956 | "C:\Windows\system32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\WarThunder\win64\aces.exe" "War Thunder Game Client" ENABLE ALL | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Windows\system32\netsh" firewall add portopening protocol = TCP port = 8090 name = "War Thunder" | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2508 | "C:\Windows\system32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\WarThunder\win32\aces.exe" "War Thunder Game Client" ENABLE ALL | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2528 | "C:\Windows\system32\netsh" firewall add portopening protocol = TCP port = 6881 name = "War Thunder" | C:\Windows\system32\netsh.exe | — | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 618
Read events
19 474
Write events
1 137
Delete events
7
Modification events
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F0060000D9155CF8C071D701 | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 99DD6E3283A32D856F48B51F57704C95E27A8E028D8295590F94EE8D226292D3 | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\WarThunder\launcher.exe | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 7D74FA60611AB54E82CE72EA6F6BED337C6E03CC1E4718B5F5CF442C237C4155 | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Gaijin\WarThunder |
| Operation: | write | Name: | StartupWithWindows |
Value: Yes | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Gaijin\WarThunder |
| Operation: | write | Name: | InstallDir |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Gaijin\WarThunder |
| Operation: | write | Name: | InstallPath |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
| (PID) Process: | (1776) wt_launcher_1.0.3.281-bwnv7jzmt.tmp | Key: | HKEY_CURRENT_USER\Software\Gaijin\WarThunder |
| Operation: | write | Name: | Dir |
Value: C:\Users\admin\AppData\Local\WarThunder | |||
Executable files
17
Suspicious files
6
Text files
14
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1788 | wt_launcher_1.0.3.281-bwnv7jzmt.exe | C:\Users\admin\AppData\Local\Temp\is-VVUBH.tmp\wt_launcher_1.0.3.281-bwnv7jzmt.tmp | executable | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\is-MBJ8B.tmp | executable | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\is-KPK2M.tmp | executable | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\launcher.exe | executable | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\is-UNBIM.tmp | executable | |
MD5:31911C6EA459F516D1DA0A12EC677BEA | SHA256:44C1DB6B7BF4103B2C4D3A1F014A1EA8FAFBBEBA19CD028525D494E3E390A896 | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\is-G04KI.tmp | compressed | |
MD5:— | SHA256:— | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\bpreport.exe | executable | |
MD5:31911C6EA459F516D1DA0A12EC677BEA | SHA256:44C1DB6B7BF4103B2C4D3A1F014A1EA8FAFBBEBA19CD028525D494E3E390A896 | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\gaijin_downloader.exe | executable | |
MD5:EAA3A102475E51AA992C1897A754F8CA | SHA256:E04BC3C12FF0F36F7E82C68FCBC28CD443AB0779B58DB004BE3B4D770B599B76 | |||
| 1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | C:\Users\admin\AppData\Local\WarThunder\launcherr.dat | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
14
DNS requests
17
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
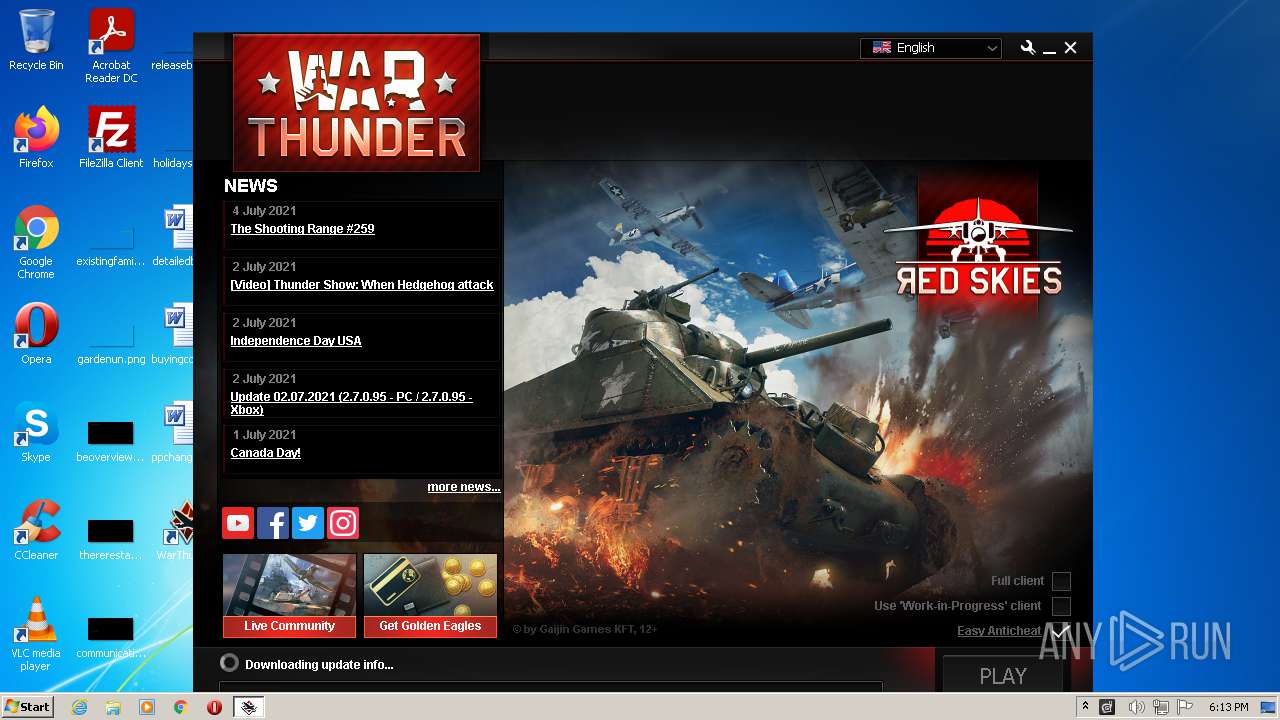
4040 | launcher.exe | GET | — | 92.38.179.230:80 | http://all-seed-gc-us-03.cdn.gaijin.net/content/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/cef_paks.zip | RU | — | — | suspicious |
4040 | launcher.exe | GET | — | 99.86.4.45:80 | http://warthunder-amazon.cdn.gaijin.net/content/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/compiledShaders/game.compatibilityDX12.ps50.shdump.bin | US | — | — | malicious |
4040 | launcher.exe | GET | 206 | 92.38.179.230:80 | http://all-seed-gc-us-03.cdn.gaijin.net/content/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/compiledShaders/game.compatibility.ps40.shdump.bin | RU | — | 3.69 Mb | suspicious |
4040 | launcher.exe | GET | — | 92.223.124.254:80 | http://02-warthunder-gcore.cdn.gaijin.net/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/compiledShaders/game.compatibility.ps40.shdump.bin | DE | — | — | suspicious |
4040 | launcher.exe | GET | — | 92.38.179.230:80 | http://all-seed-gc-us-03.cdn.gaijin.net/content/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/char.vromfs.bin | RU | — | — | suspicious |
4040 | launcher.exe | GET | — | 99.86.4.45:80 | http://warthunder-amazon.cdn.gaijin.net/content/warthunder/2.7.0.95/179de1bb700a7dd2648545ee82665d9572d5faf7/compiledShaders/game.compatibility.ps40.shdump.bin | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1776 | wt_launcher_1.0.3.281-bwnv7jzmt.tmp | 188.42.61.240:443 | launcher-bq.gaijin.net | Servers.com, Inc. | LU | unknown |
328 | gaijin_downloader.exe | 52.214.22.213:443 | yupmaster.gaijinent.com | Amazon.com, Inc. | IE | unknown |
4040 | launcher.exe | 52.214.22.213:443 | yupmaster.gaijinent.com | Amazon.com, Inc. | IE | unknown |
— | — | 52.214.22.213:443 | yupmaster.gaijinent.com | Amazon.com, Inc. | IE | unknown |
— | — | 104.20.82.98:443 | warthunder.com | Cloudflare Inc | US | shared |
4040 | launcher.exe | 13.225.82.142:443 | aws-yup-distr-04.gaijinent.com | — | US | unknown |
328 | gaijin_downloader.exe | 185.253.20.201:443 | — | — | — | unknown |
4040 | launcher.exe | 92.38.179.230:80 | all-seed-gc-us-03.cdn.gaijin.net | JSC Digital Network | RU | suspicious |
4040 | launcher.exe | 99.86.4.45:80 | warthunder-amazon.cdn.gaijin.net | AT&T Services, Inc. | US | suspicious |
4040 | launcher.exe | 151.139.128.11:443 | 04-warthunder-stackpath.cdn.gaijin.net | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
launcher-bq.gaijin.net |
| unknown |
client-stats.gaijin.net |
| unknown |
client-stats.warthunder.com |
| unknown |
yupmaster.gaijinent.com |
| unknown |
seeder.gaijin.lan |
| unknown |
warthunder.com |
| whitelisted |
aws-yup-distr-04.gaijinent.com |
| unknown |
aws-yup-distr-02.gaijinent.com |
| unknown |
dht.libtorrent.org |
| suspicious |
router.bittorrent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
4040 | launcher.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent peer sync |
27 ETPRO signatures available at the full report