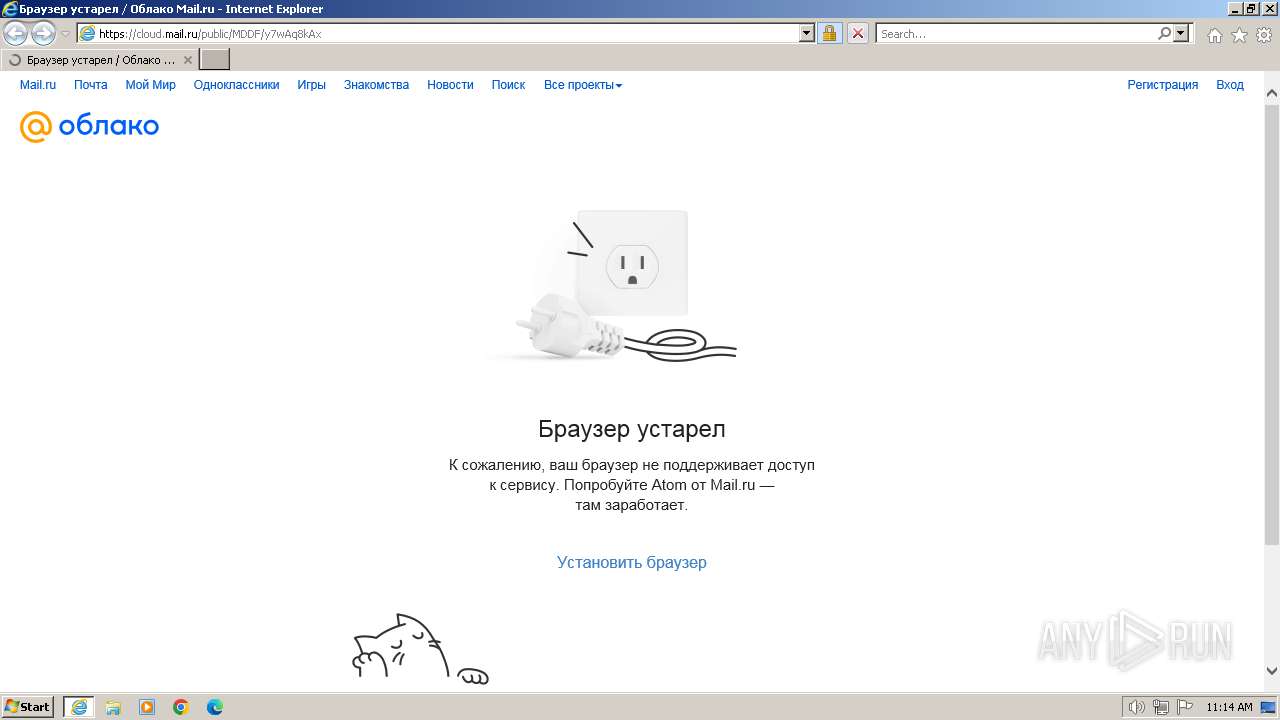
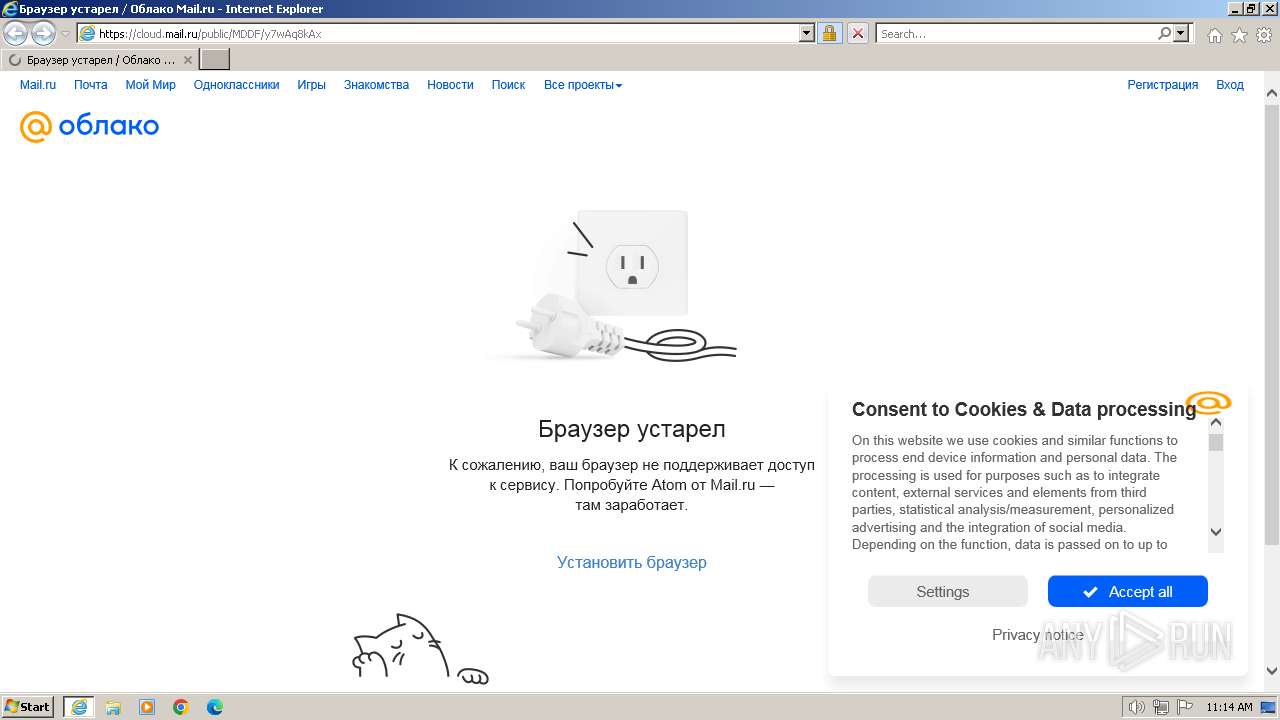
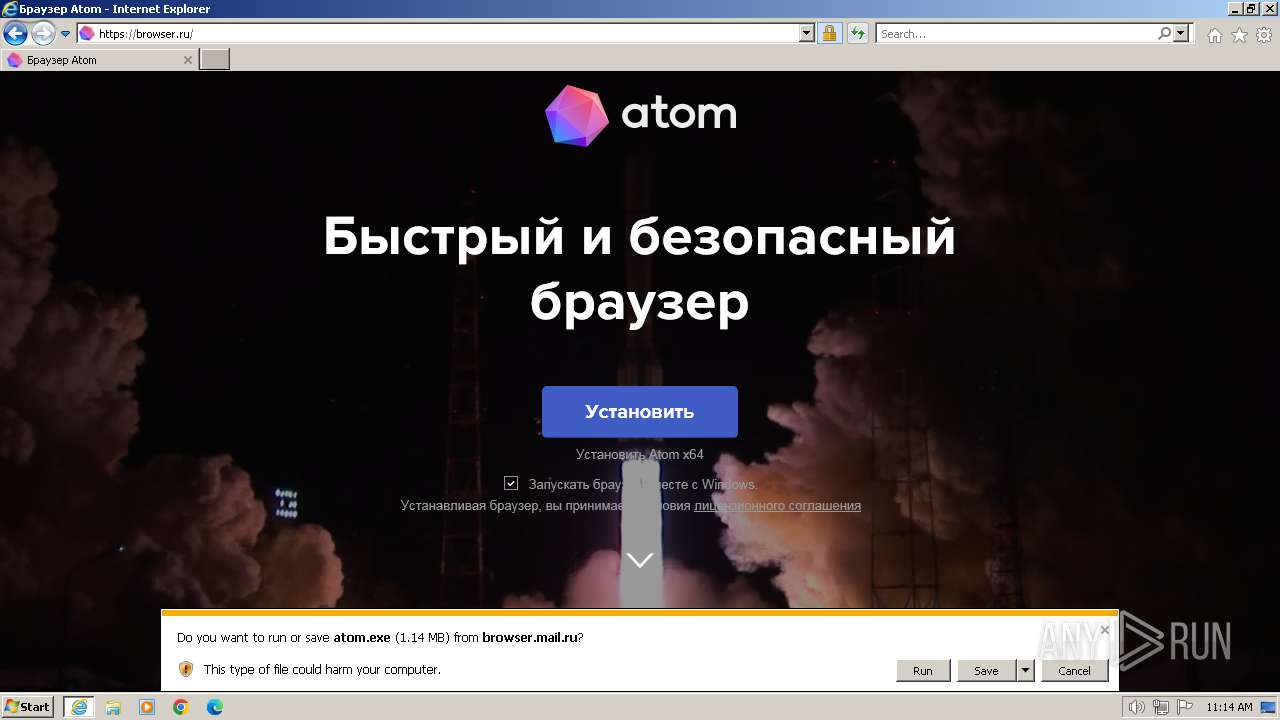
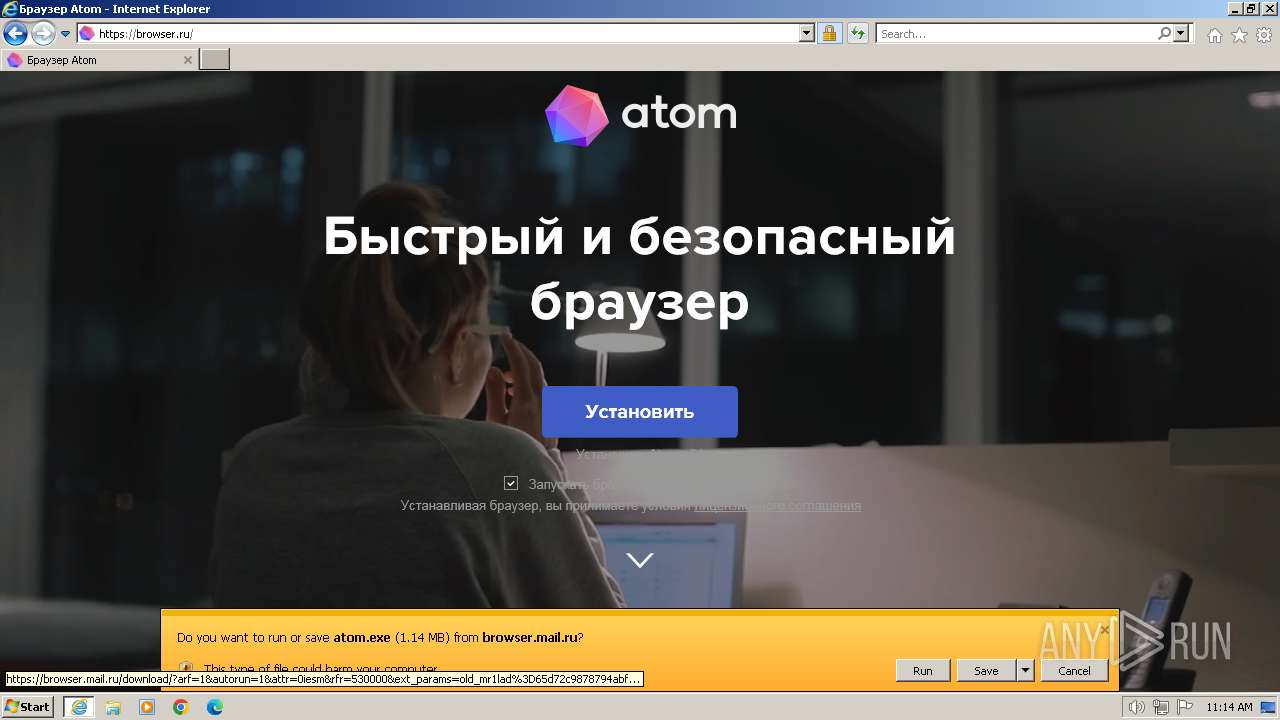
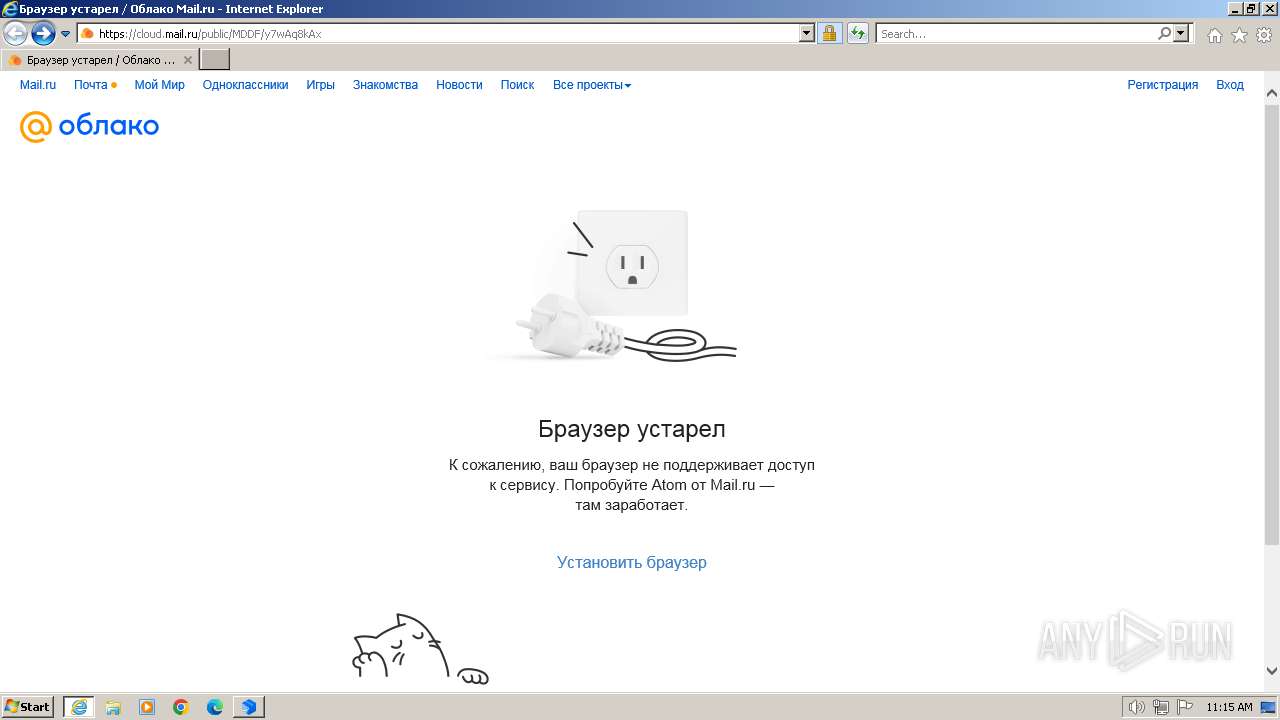
| URL: | https://cloud.mail.ru/public/MDDF/y7wAq8kAx |
| Full analysis: | https://app.any.run/tasks/27b9c87c-04b6-419d-8885-9a34ce519c7e |
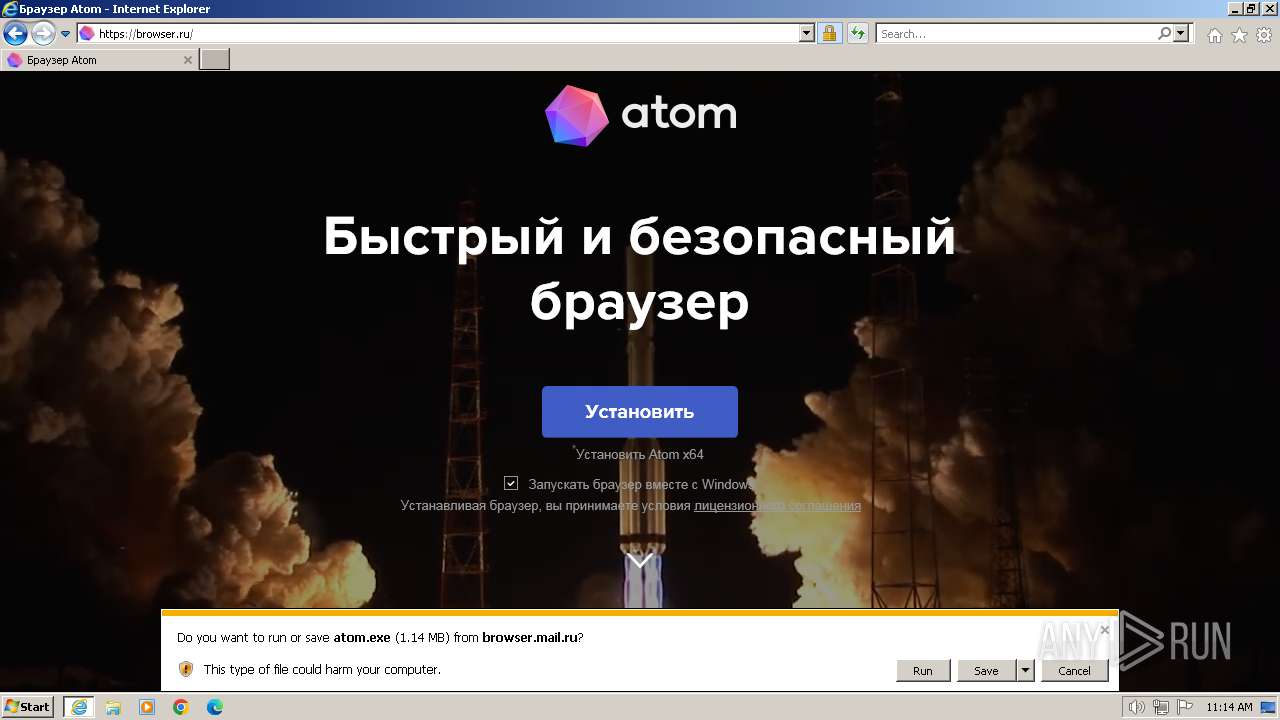
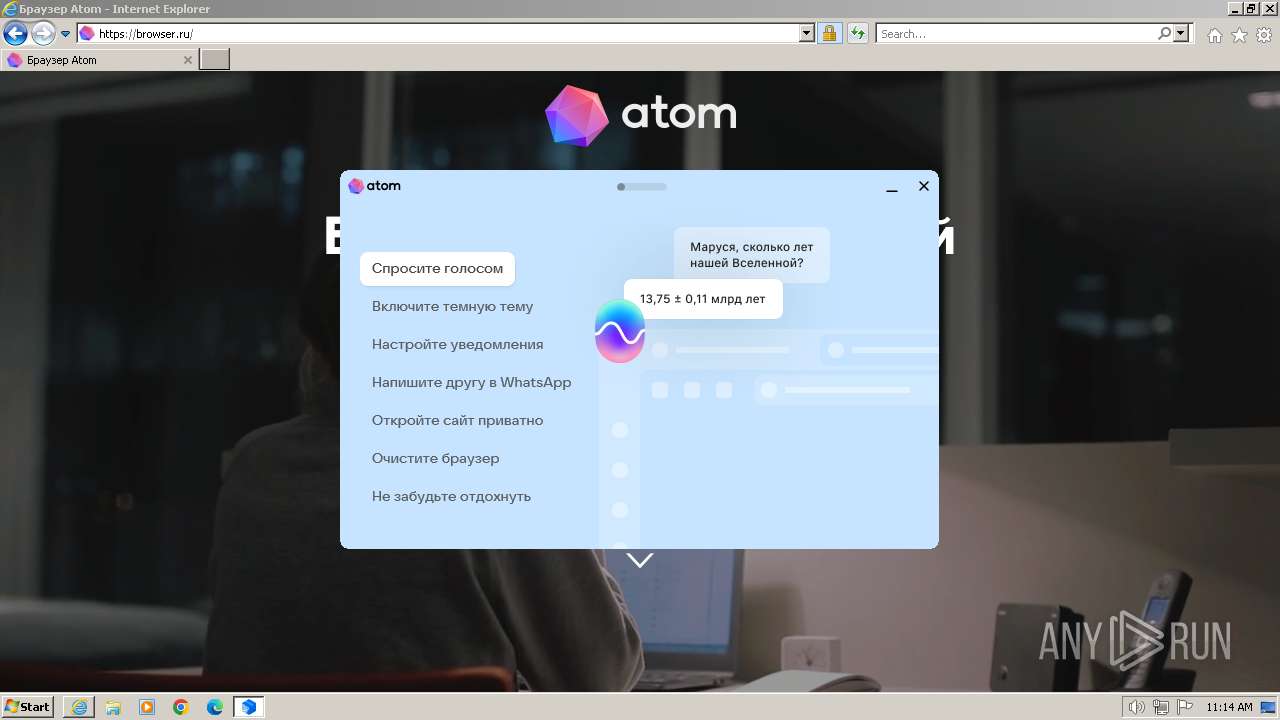
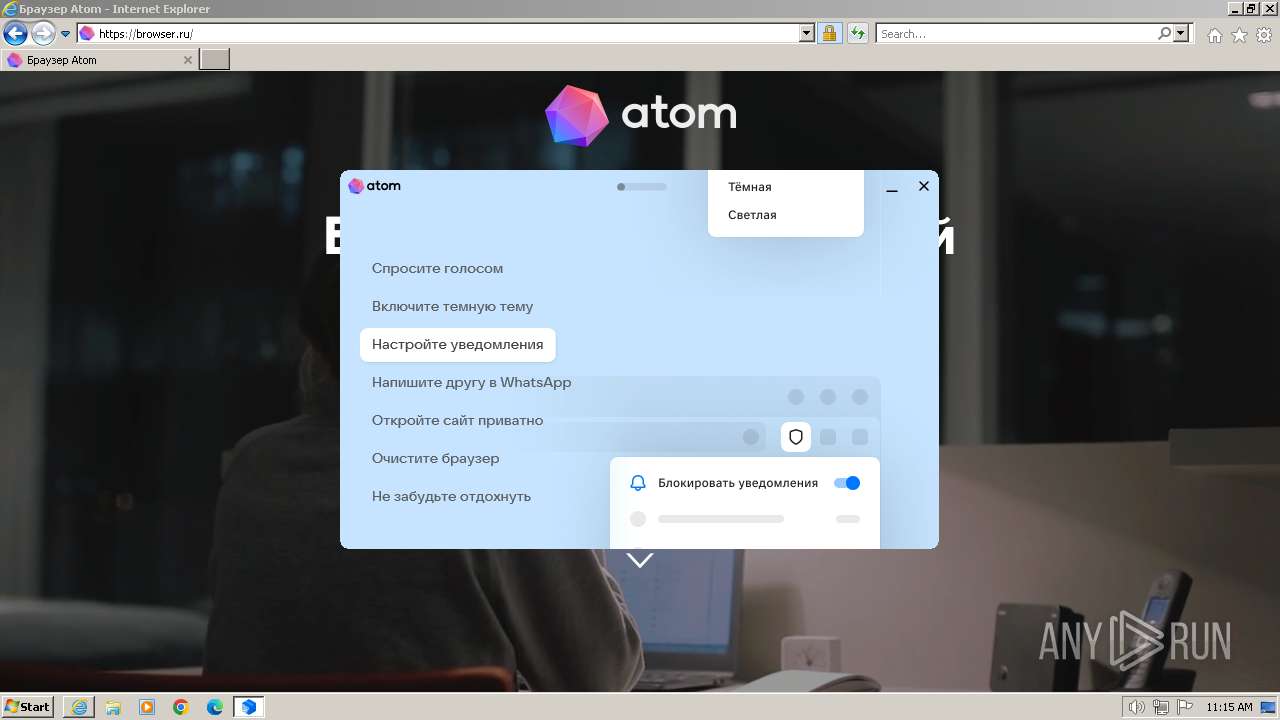
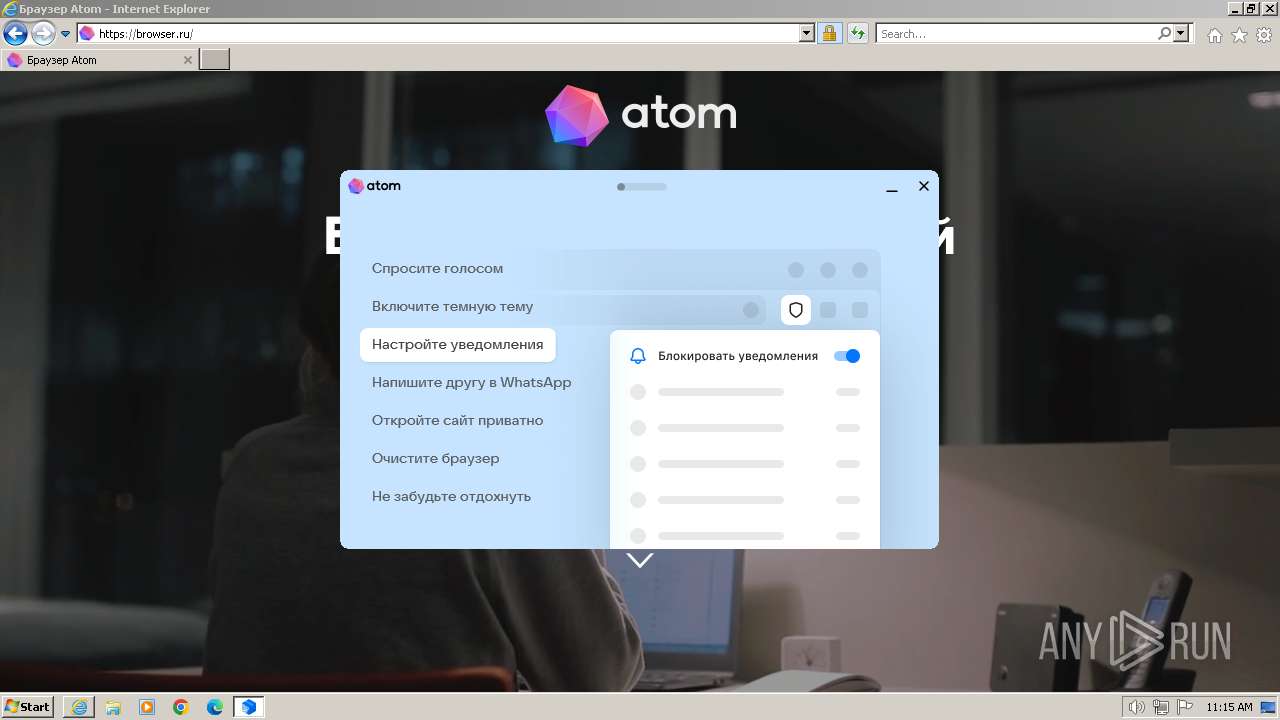
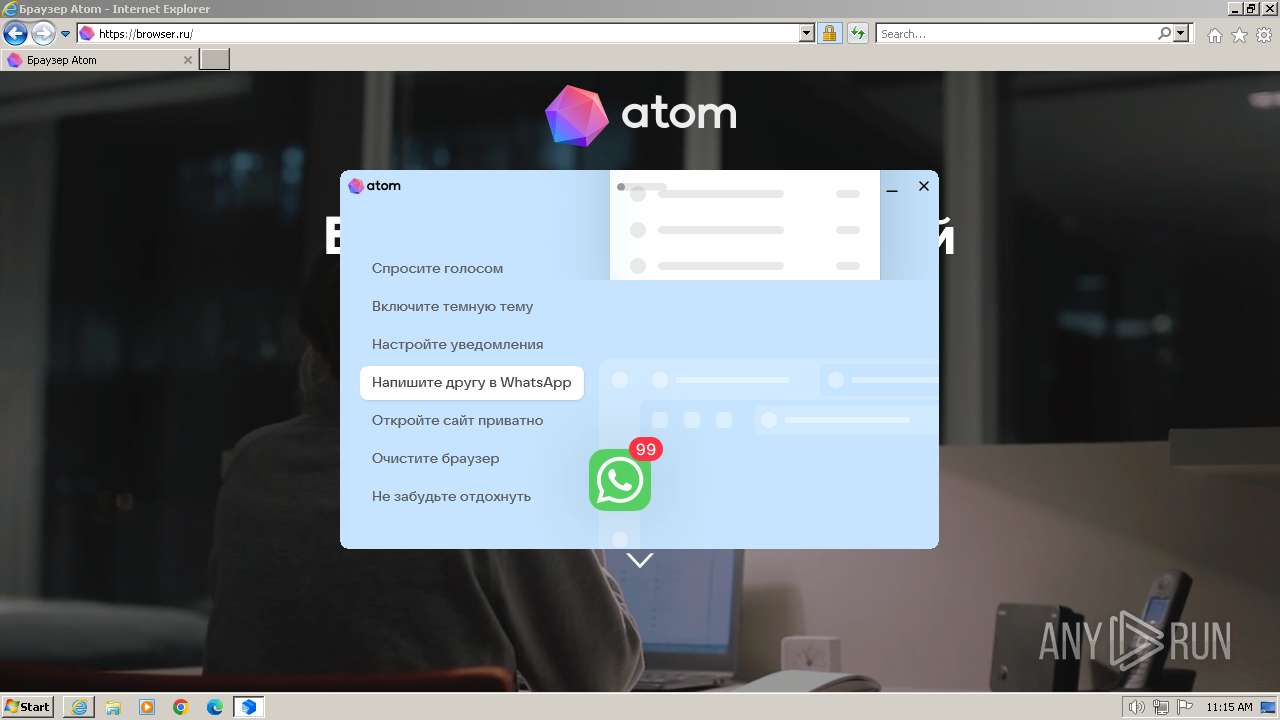
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2024, 11:14:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AC5768E7330F1325224E20E1FD89395C |
| SHA1: | E2457472C5A605F057B6E14862F0DC5496C38994 |
| SHA256: | 29587221731A06A183A533D71A70B3F31618991339C134983759F7FD59C9EE1C |
| SSDEEP: | 3:N8ULBLynq3jKchR:2UMnqLhR |
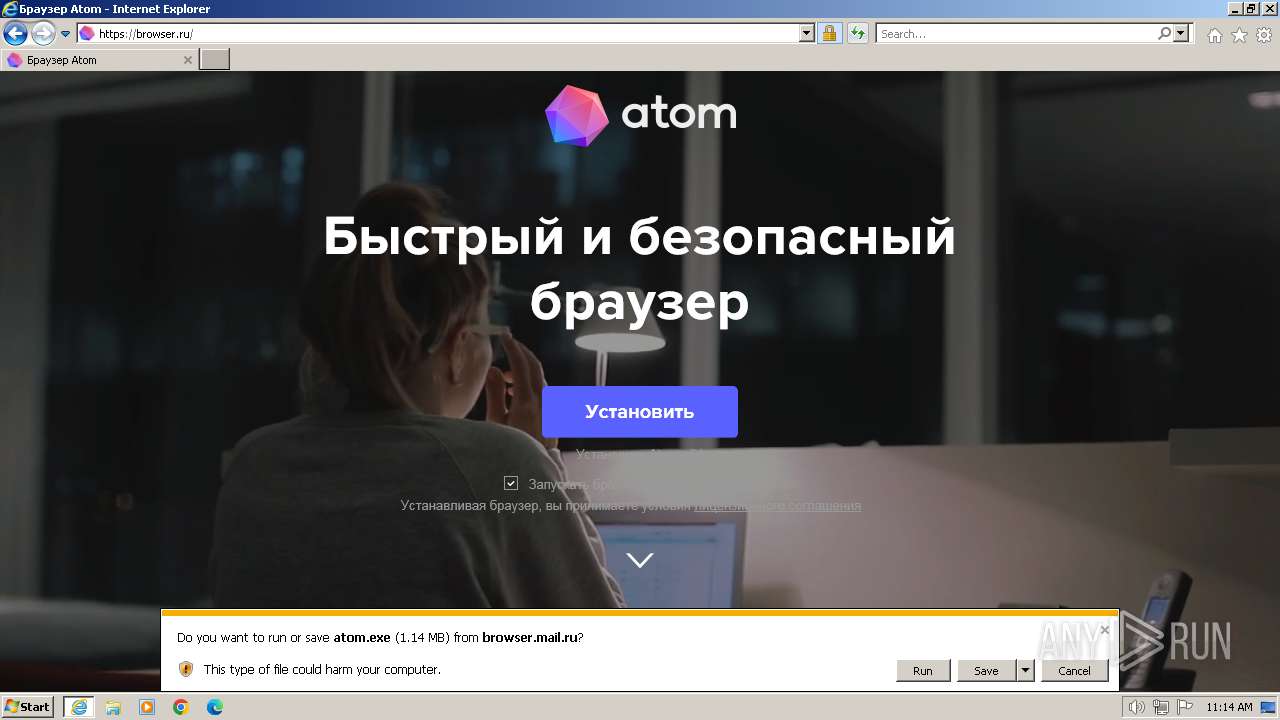
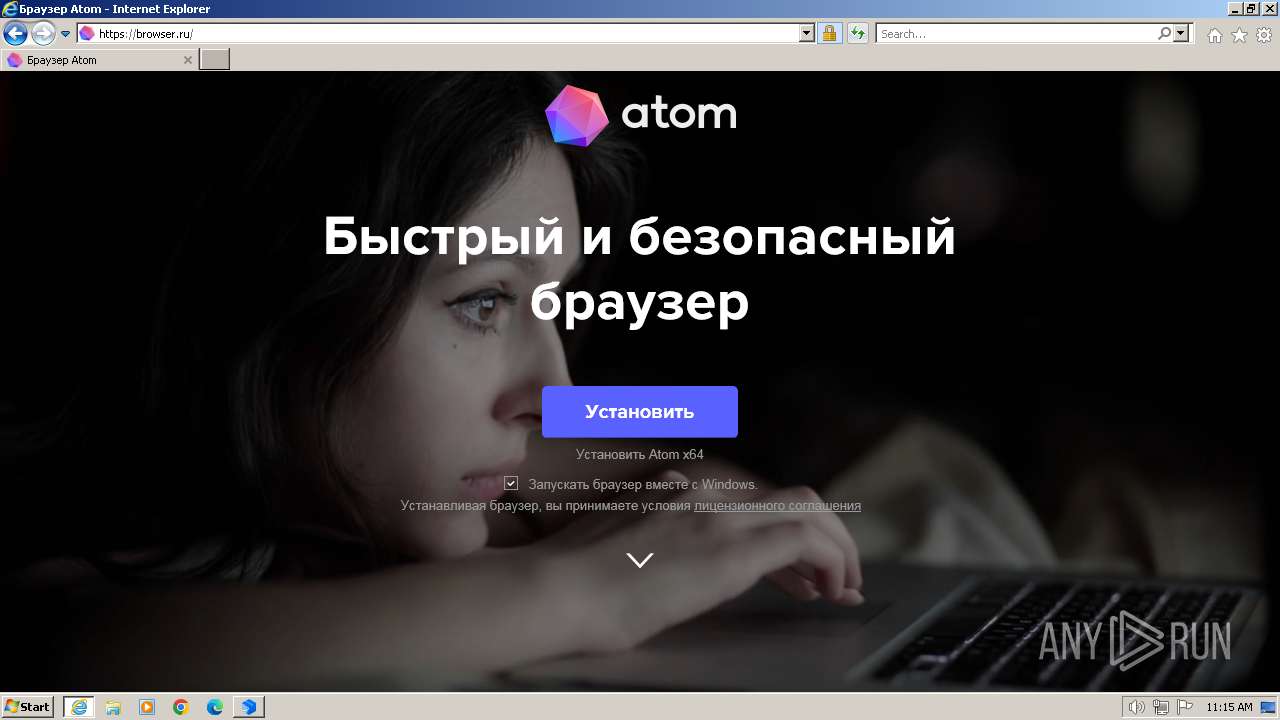
MALICIOUS
Drops the executable file immediately after the start
- atom.exe (PID: 2668)
- atom.exe (PID: 3496)
SUSPICIOUS
Executable content was dropped or overwritten
- atom.exe (PID: 2668)
- atom.exe (PID: 3496)
Application launched itself
- atom.exe (PID: 2668)
Cleans NTFS data stream (Zone Identifier)
- atom.exe (PID: 2668)
Reads the Internet Settings
- atom.exe (PID: 3496)
Reads security settings of Internet Explorer
- atom.exe (PID: 3496)
Reads Internet Explorer settings
- atom.exe (PID: 3496)
Reads settings of System Certificates
- atom.exe (PID: 3496)
Reads Microsoft Outlook installation path
- atom.exe (PID: 3496)
INFO
Executable content was dropped or overwritten
- iexplore.exe (PID: 2044)
- iexplore.exe (PID: 3700)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2044)
- iexplore.exe (PID: 3700)
Checks supported languages
- atom.exe (PID: 2668)
- atom.exe (PID: 3496)
The process uses the downloaded file
- iexplore.exe (PID: 3700)
- atom.exe (PID: 2668)
- atom.exe (PID: 3496)
Application launched itself
- iexplore.exe (PID: 3700)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3700)
Create files in a temporary directory
- atom.exe (PID: 2668)
- atom.exe (PID: 3496)
Reads the machine GUID from the registry
- atom.exe (PID: 3496)
Reads the computer name
- atom.exe (PID: 3496)
Creates files in the program directory
- atom.exe (PID: 3496)
Checks proxy server information
- atom.exe (PID: 3496)
Creates files or folders in the user directory
- atom.exe (PID: 3496)
Reads the software policy settings
- atom.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
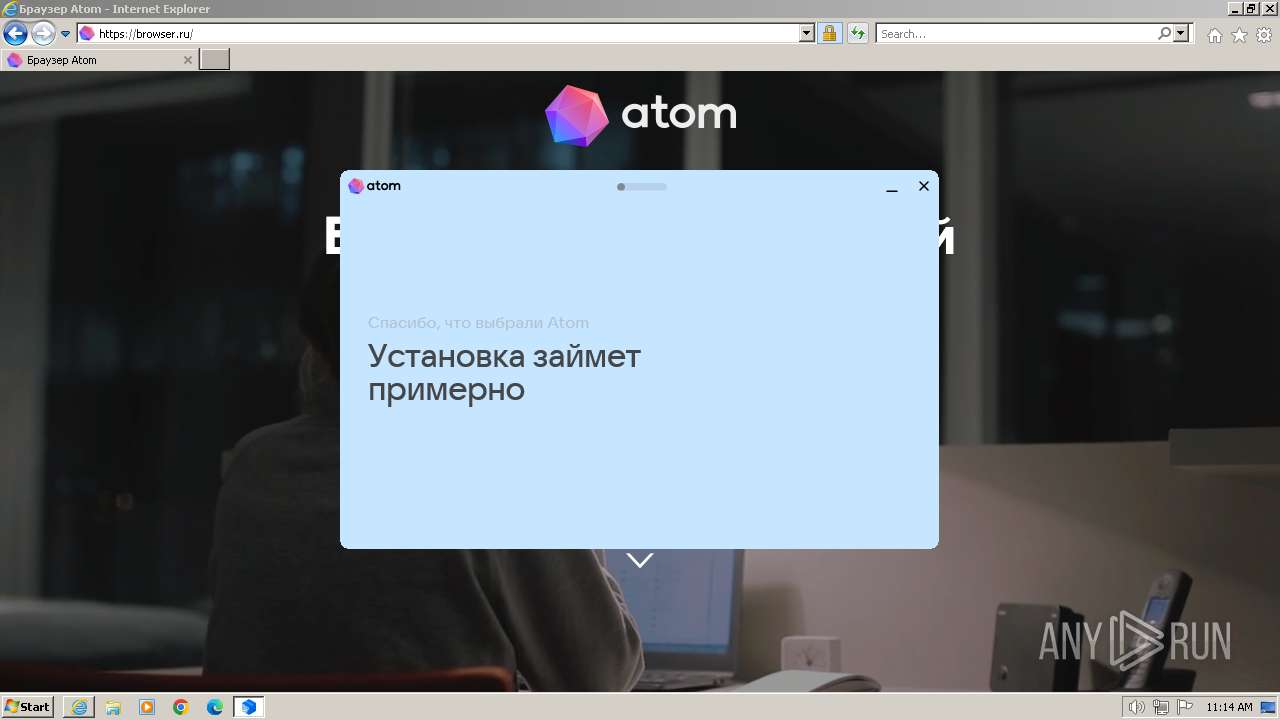
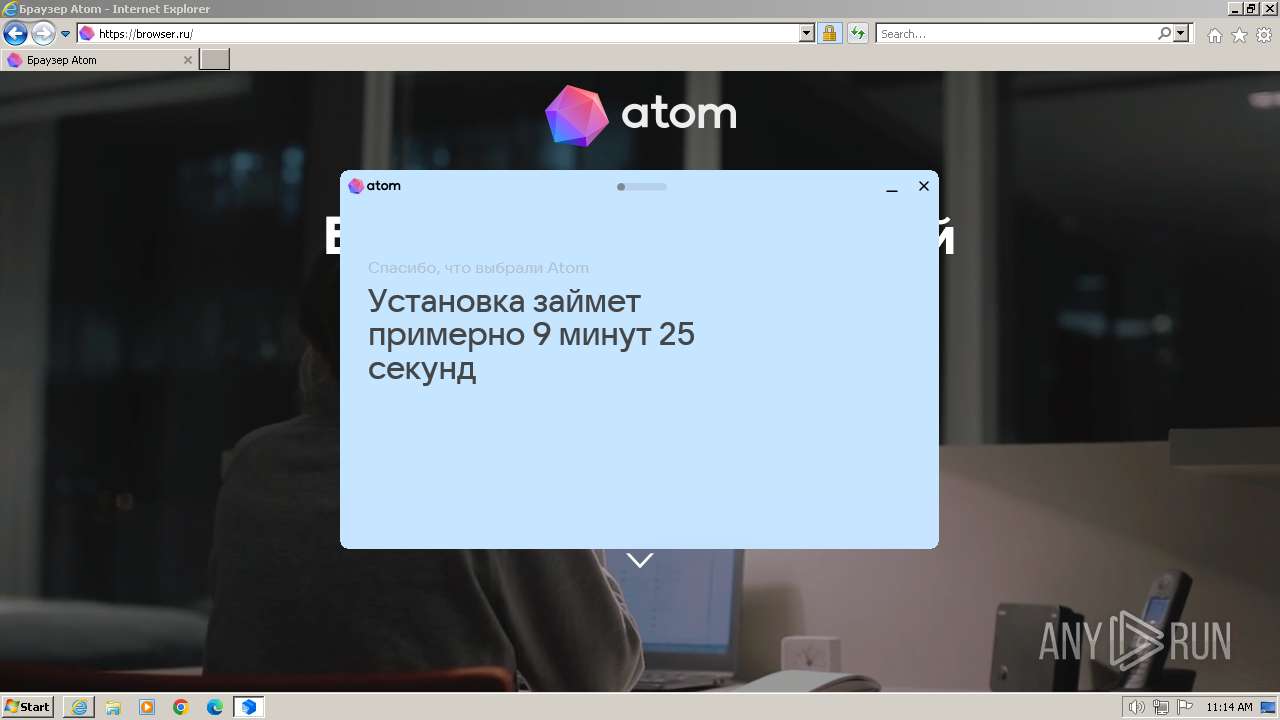
| 2668 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\atom.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\atom.exe | iexplore.exe | ||||||||||||
User: admin Company: VK Integrity Level: MEDIUM Description: Atom Browser Exit code: 0 Version: 7.0.0.134 Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\atom.exe" --cp | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\atom.exe | atom.exe | ||||||||||||
User: admin Company: VK Integrity Level: MEDIUM Description: Atom Browser Exit code: 0 Version: 7.0.0.134 Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cloud.mail.ru/public/MDDF/y7wAq8kAx" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
39 114
Read events
38 815
Write events
243
Delete events
56
Modification events
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090048 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090048 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
5
Suspicious files
55
Text files
230
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:106565DFF333FD90D599286AFBCE20A1 | SHA256:7CC84BE4398D7490D2CCDDC7C8C21C248E543F614F28221DD28D28B30FB1A5E7 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0464F5F01383554C80C40E4772F65A17 | binary | |
MD5:9D72DE893106BEA97CE99029BFAD6854 | SHA256:4E7EC1F0BA336CEFCB56E89D5FDA9E6CA0AC1DBB6527FDC4C73684725597F63C | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\y7wAq8kAx[1].htm | html | |
MD5:32F4A86B8BB0CC182A3D4796C056D376 | SHA256:0B1910AB705083D682B01DFEAE53B4038384667E07DDA91A6DA20E0849FC01BD | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:036F6AD203E2AAEA82C1BCEFFB530E8A | SHA256:3C700A477C74864741AF7F75164CC960D6B239DF56538693CE5C09D1E6A014E3 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:5D19CEEBEE821FAB3A6CE6FE4B1EF8EF | SHA256:BC44B9316318217DDB4F560645931122692D87190504B199170F3965B22970AA | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_50D7940D5D3FEDD8634D83074C7A46A3 | der | |
MD5:49BEDA55CA65FE86F7A5063AC0B74BCE | SHA256:738E2120159285881A14F3F73E8E2A3995C57DA2C572A633700BDC83F08B4A63 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0464F5F01383554C80C40E4772F65A17 | der | |
MD5:BEF651FFF00C0D246EDB0160378C13FC | SHA256:FCDBCCD798523F6A23EE384A77B0785A95198B766624DA9C26A7D48E03100C6D | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F8A2411A8BDDEB648F5845F9897FEA83 | binary | |
MD5:8DAC1BEA305C5E0921D19C79FF31FA08 | SHA256:C07E622AEA6010344150FDEECBFC35AF661E02591EE2BB6BEFCDC57021B17523 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A16C6C16D94F76E0808C087DFC657D99_279EB7E7074697CADB0A3844954F1B7D | der | |
MD5:6F3462B8DE626819F7538676F0951C96 | SHA256:16DE300FDF17CB6EF2A25CF9EC5A5F609F9CDE3A6CF94CD75439309C1963943B | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\DOTBATAV\cloud.mail[1].xml | text | |
MD5:C1DDEA3EF6BBEF3E7060A1A9AD89E4C5 | SHA256:B71E4D17274636B97179BA2D97C742735B6510EB54F22893D3A2DAFF2CEB28DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
179
DNS requests
54
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDDjMTZl7vzdbPPDllw%3D%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDBYR%2FOzufYL7OYFvhw%3D%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | binary | 1.41 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a08f35fbea17b647 | unknown | — | — | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFZ43noMCcDUxwQLHw%3D%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFwPfOXcb9eOnCF9aQ%3D%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFwPfOXcb9eOnCF9aQ%3D%3D | unknown | binary | 1.40 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyI%2BPTVbmSvIKrQ%3D | unknown | binary | 1.40 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | iexplore.exe | 95.163.57.16:443 | cloud.mail.ru | LLC VK | RU | unknown |
2044 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2044 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
2044 | iexplore.exe | 5.181.61.0:443 | cloud.imgsmail.ru | LLC VK | RU | unknown |
2044 | iexplore.exe | 142.250.185.136:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2044 | iexplore.exe | 95.163.52.80:443 | r.mradx.net | LLC VK | RU | unknown |
2044 | iexplore.exe | 95.163.41.56:443 | rs.mail.ru | LLC VK | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloud.mail.ru |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
cloud.imgsmail.ru |
| unknown |
www.googletagmanager.com |
| whitelisted |
r.mradx.net |
| whitelisted |
rs.mail.ru |
| whitelisted |
an.mail.ru |
| whitelisted |
img.imgsmail.ru |
| whitelisted |
Threats
3 ETPRO signatures available at the full report