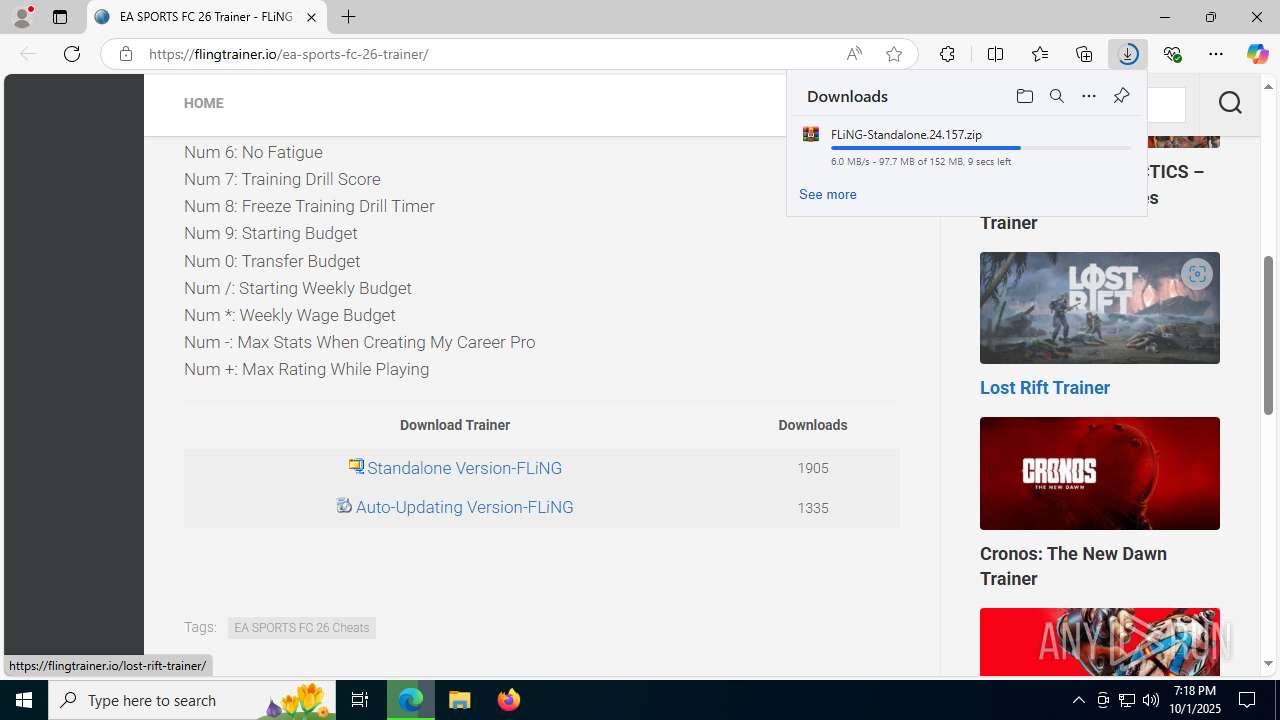
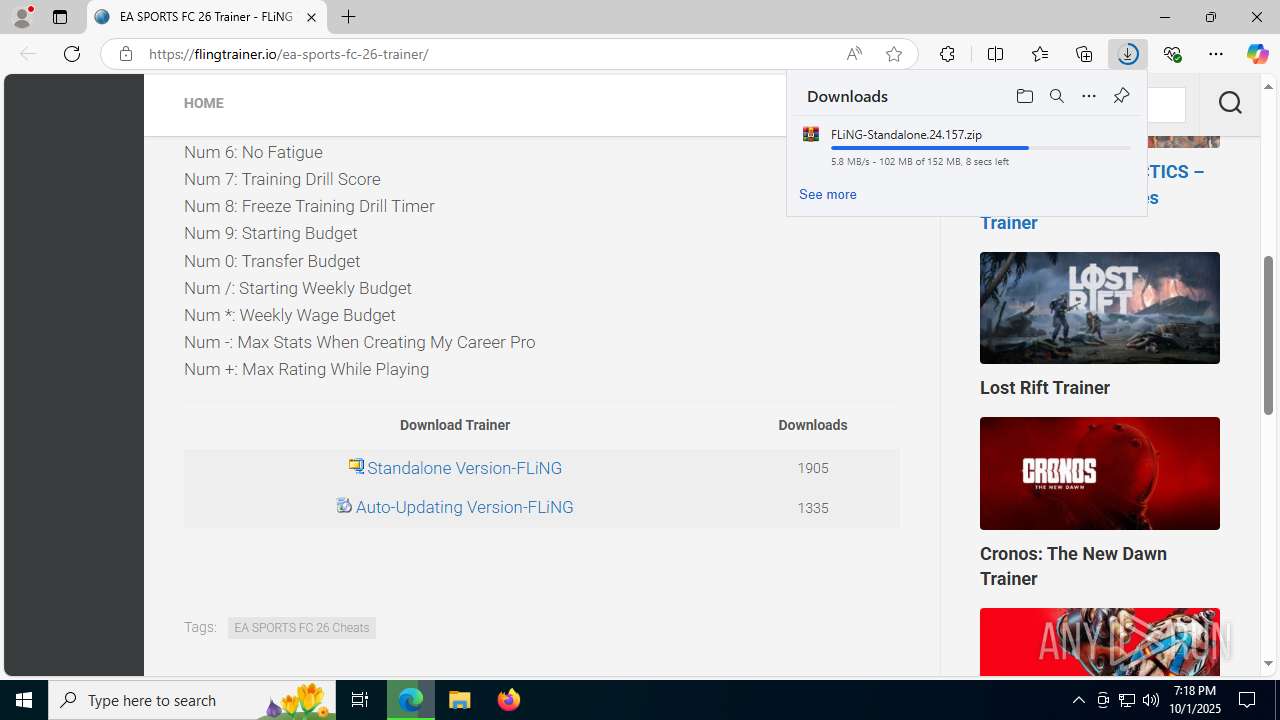
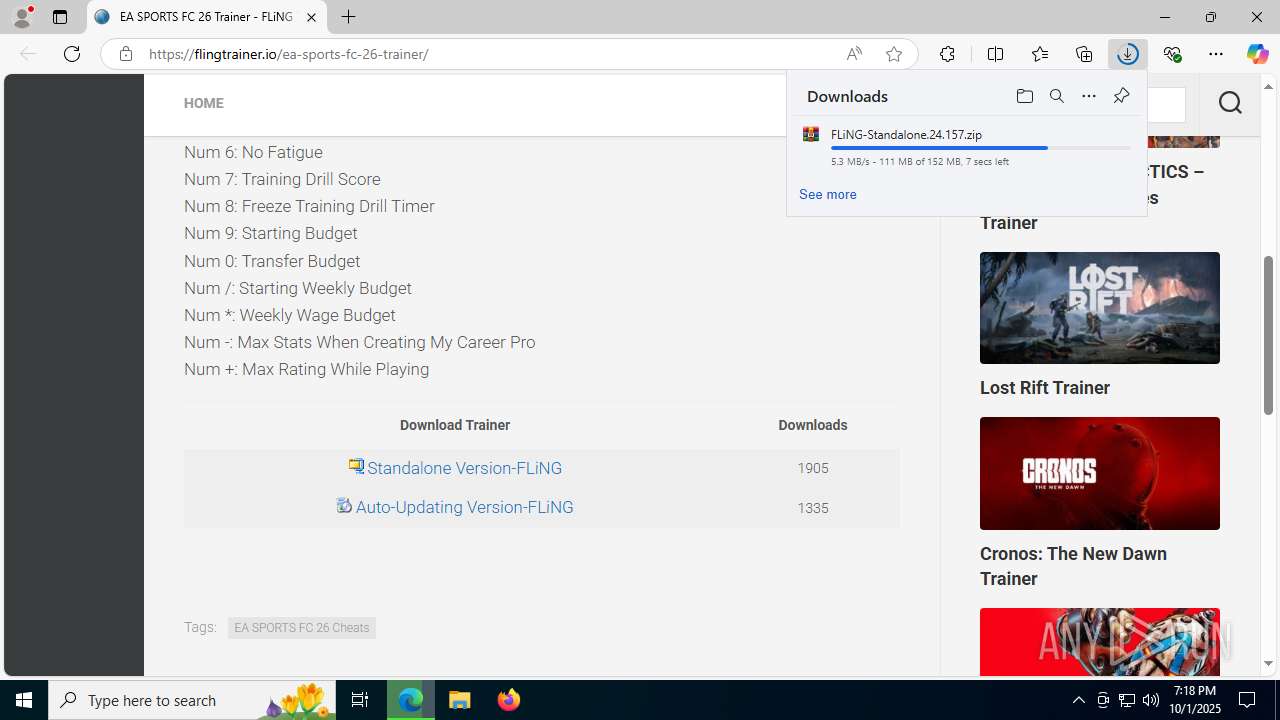
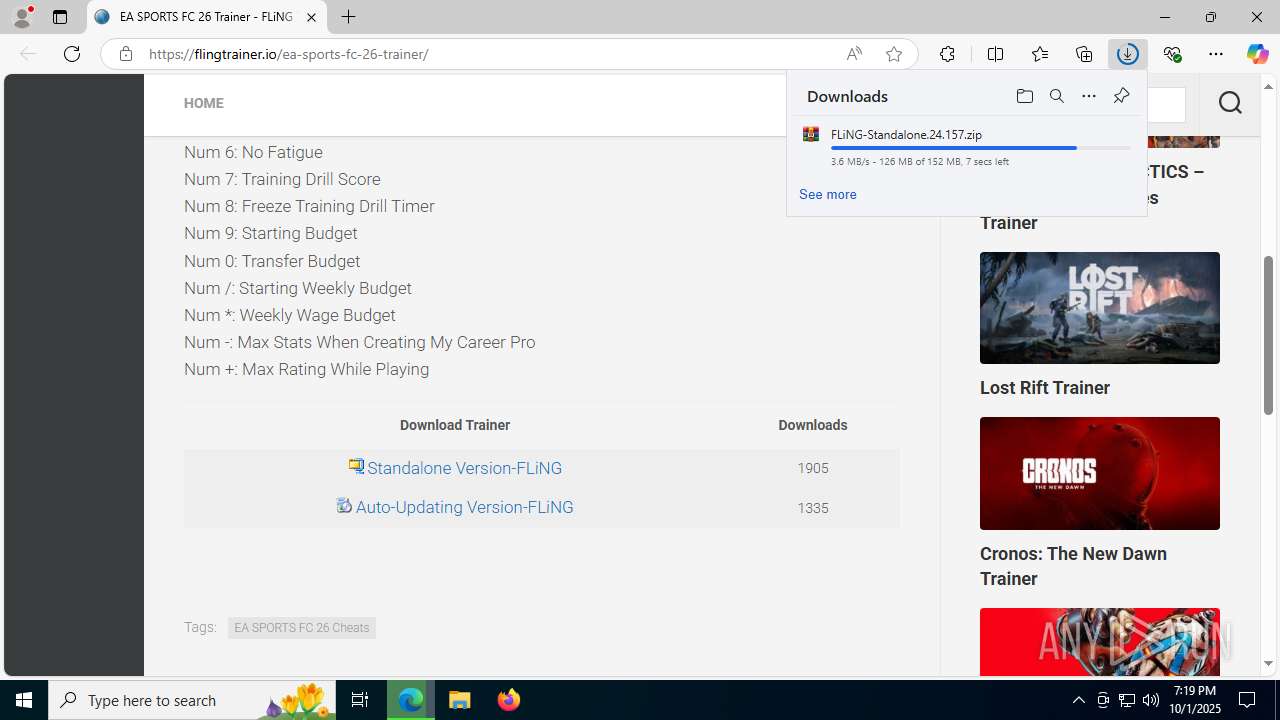
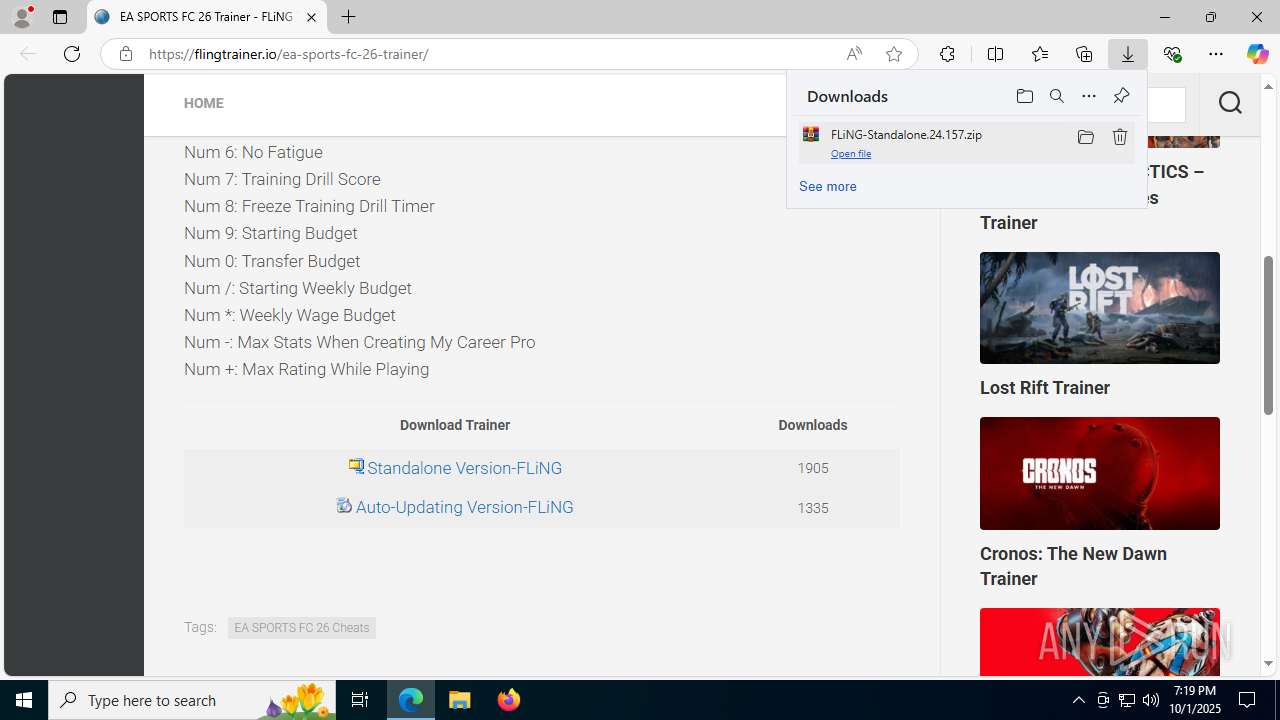
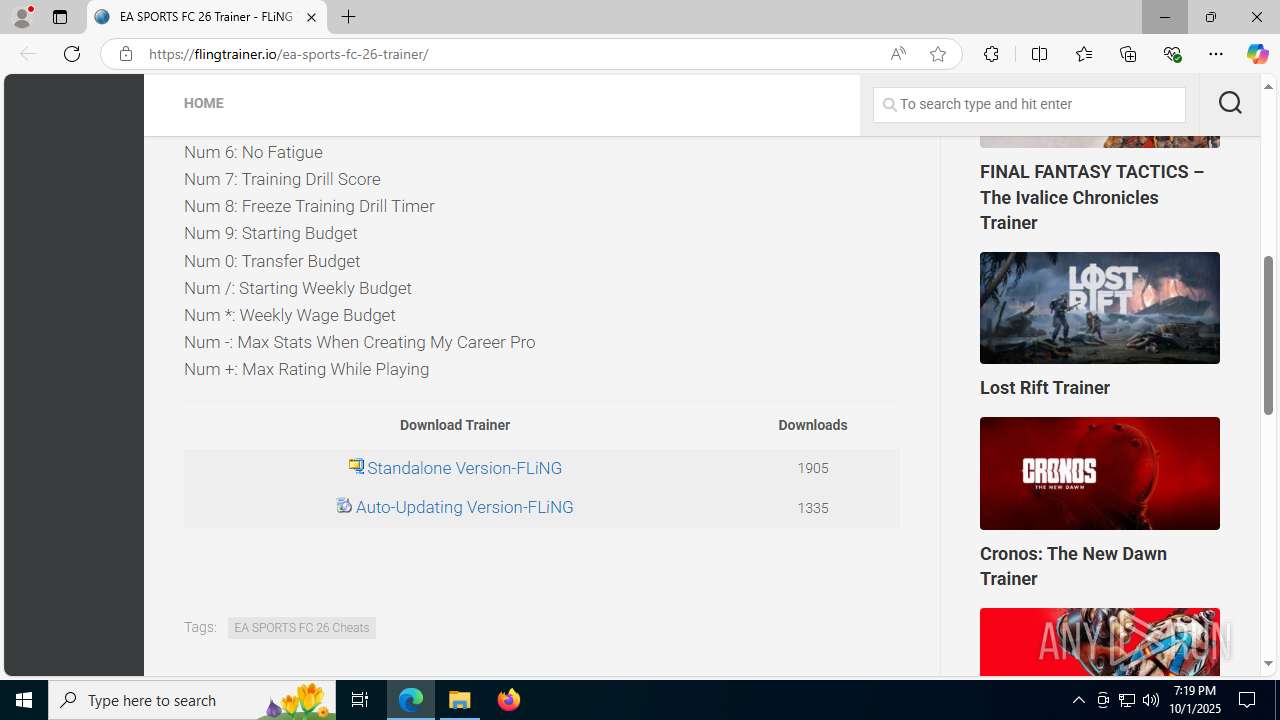
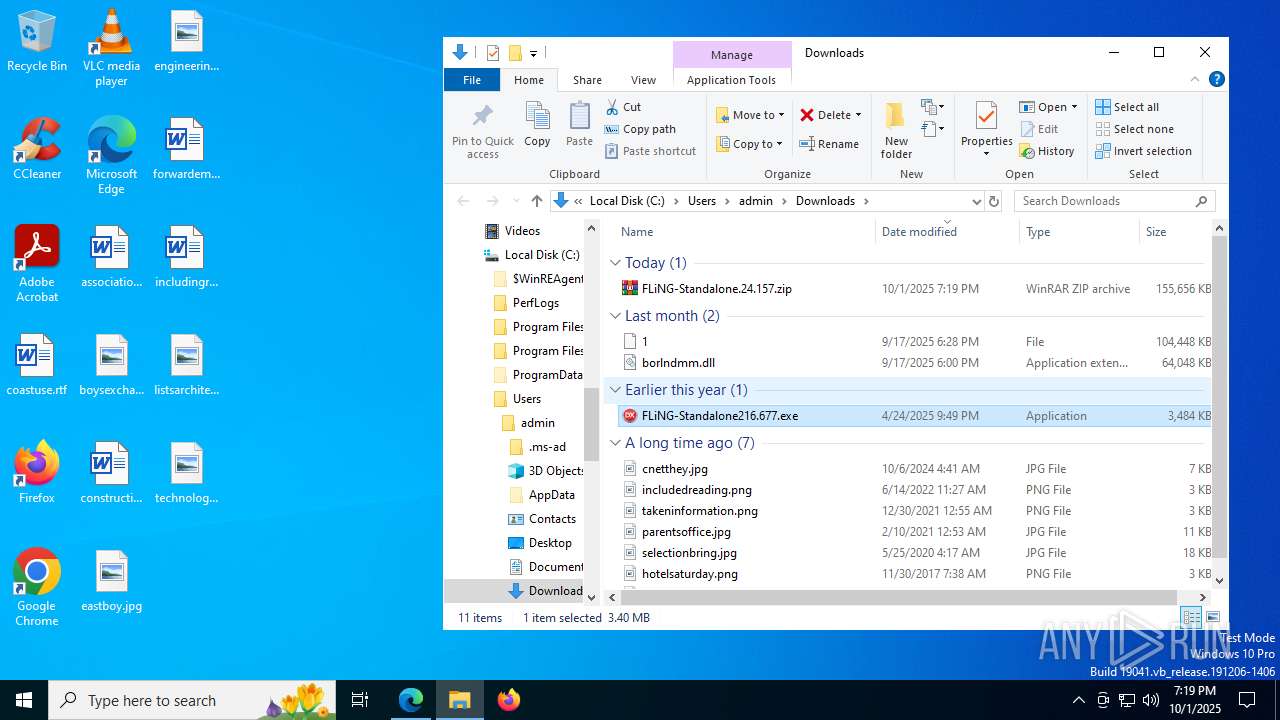
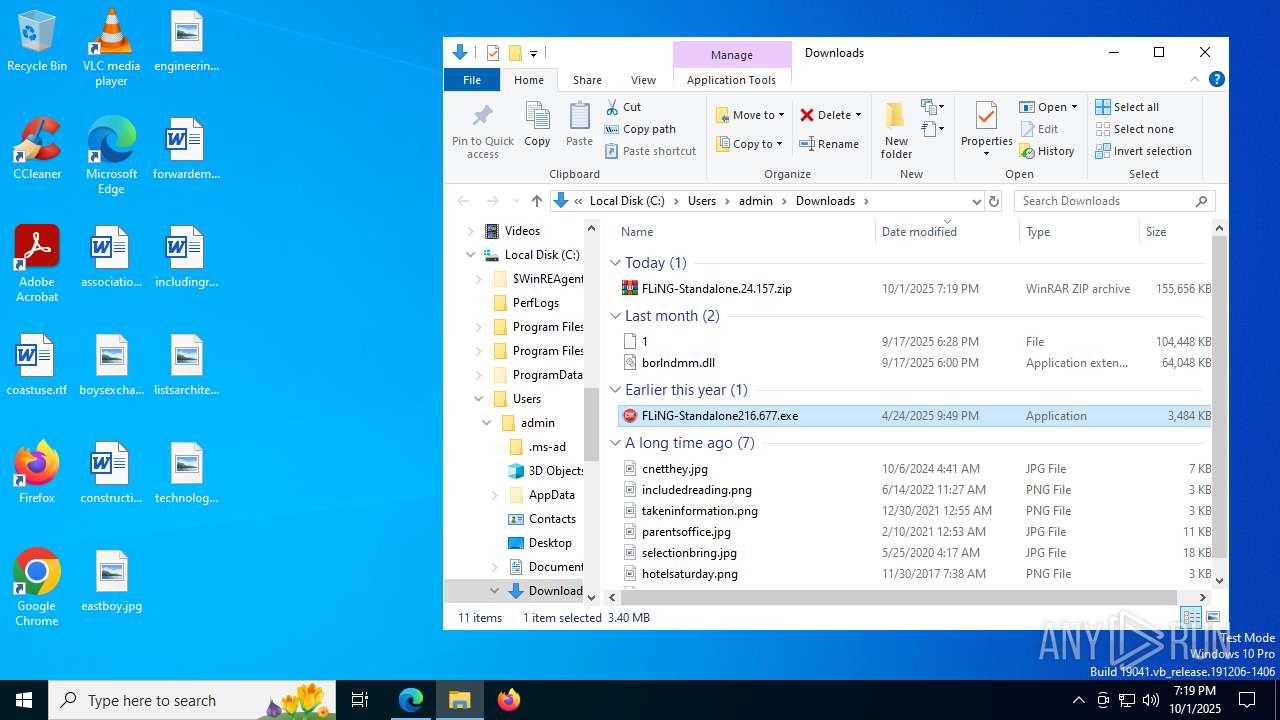
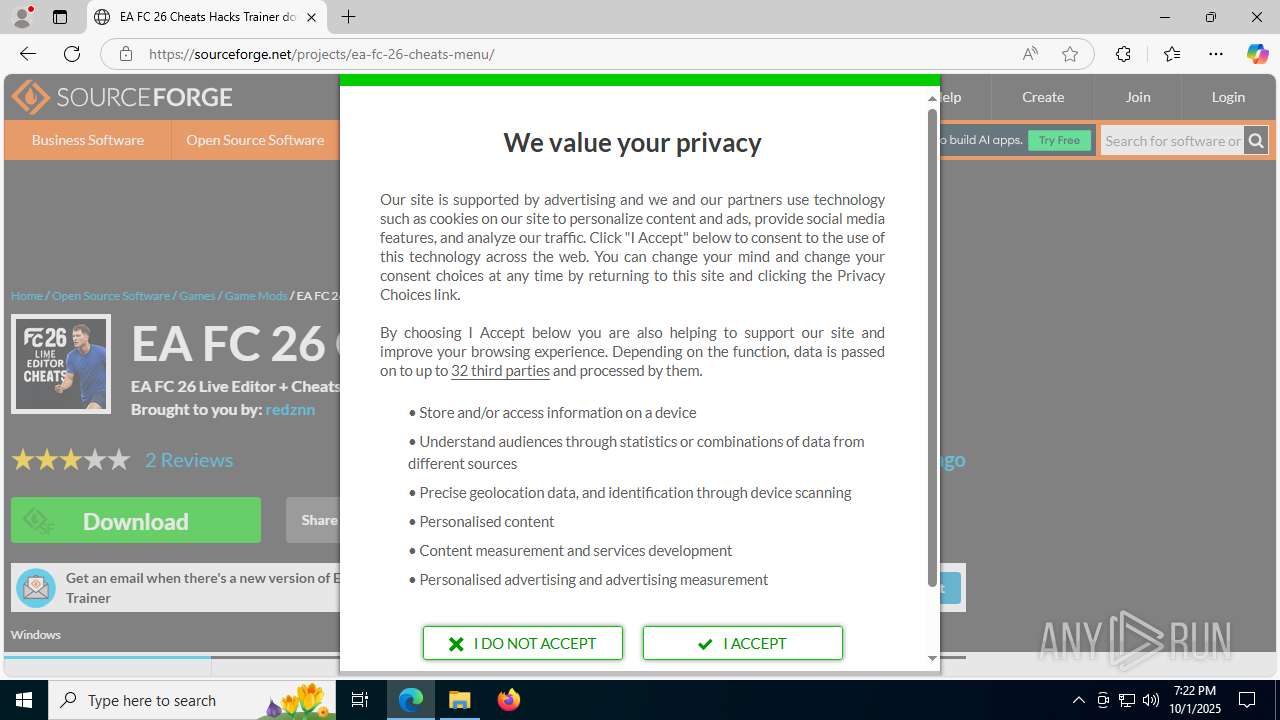
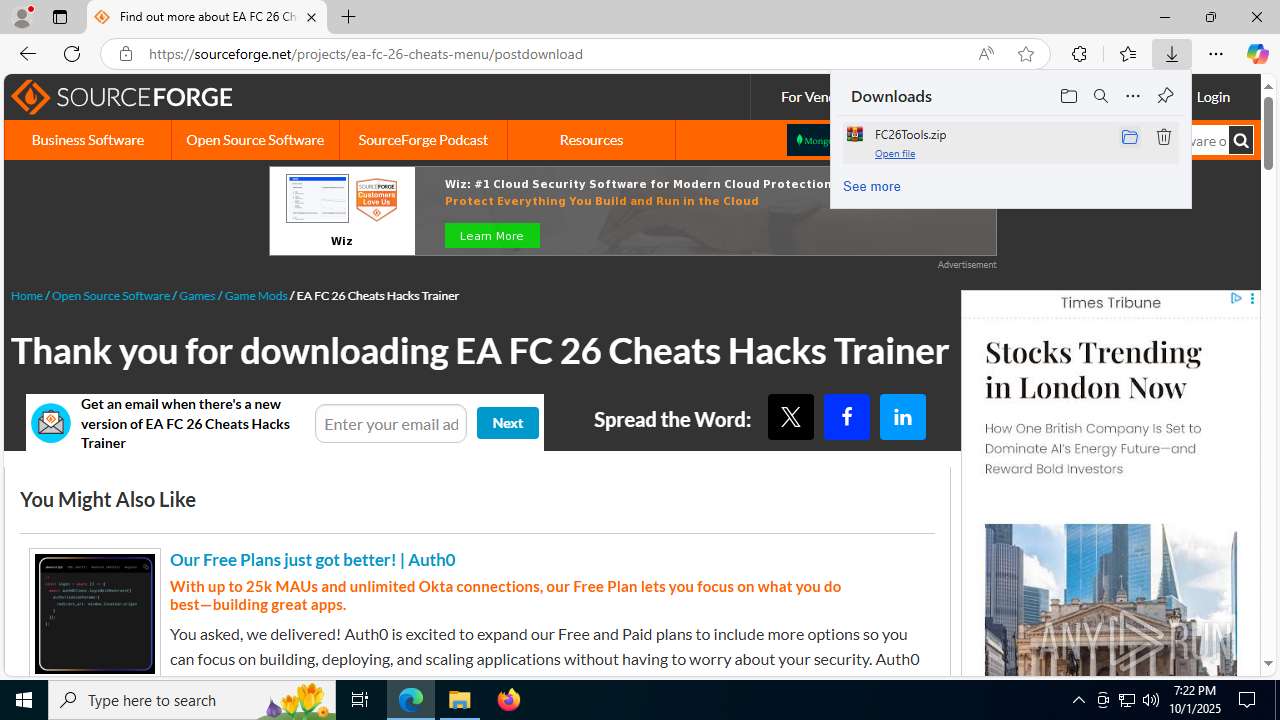
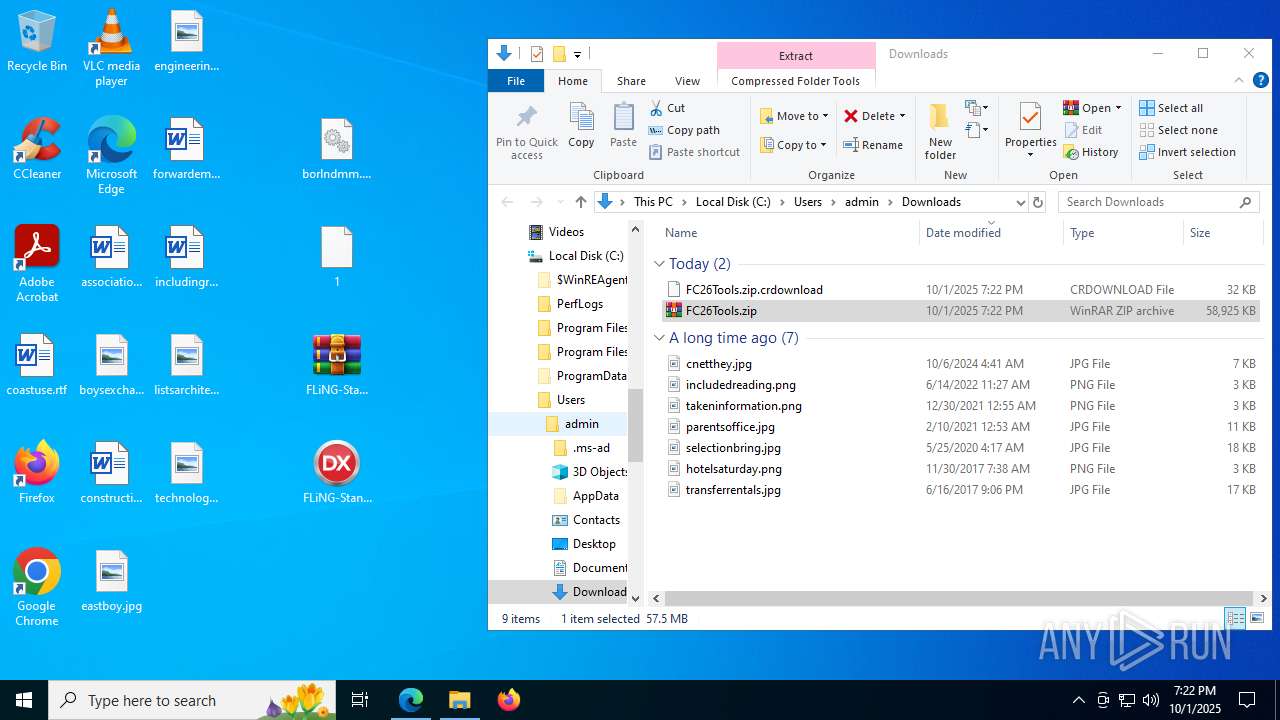
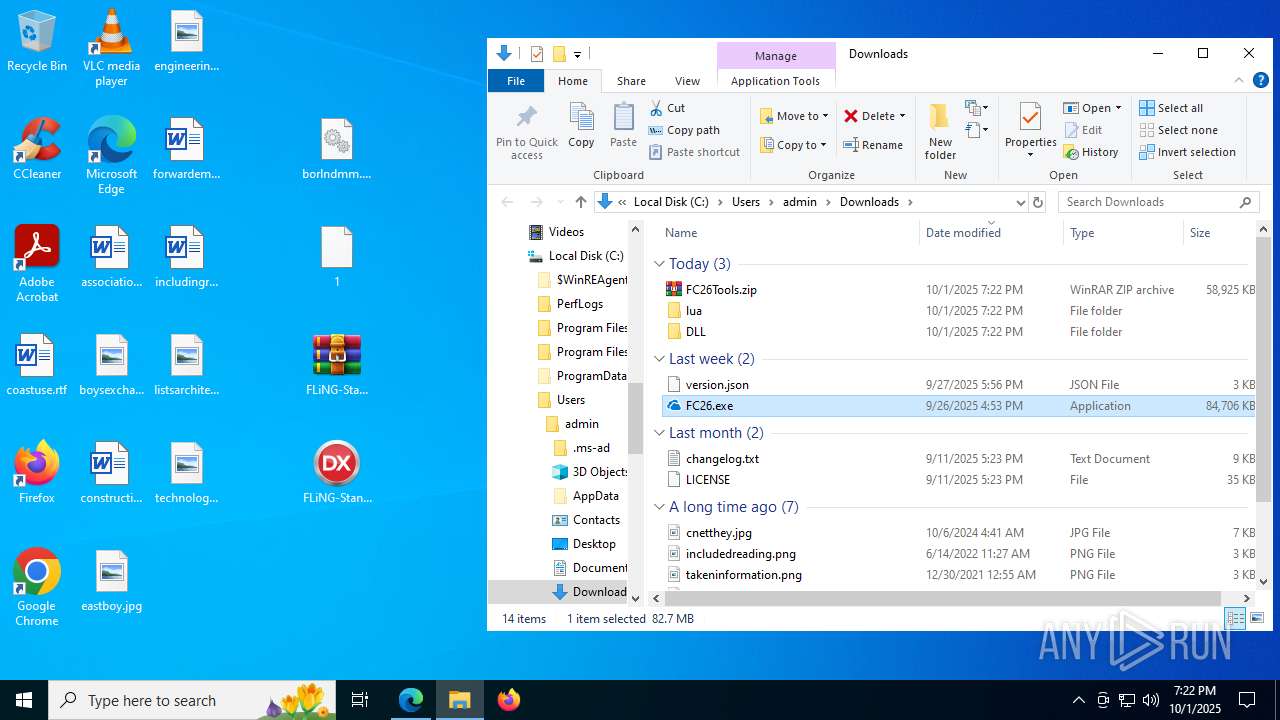
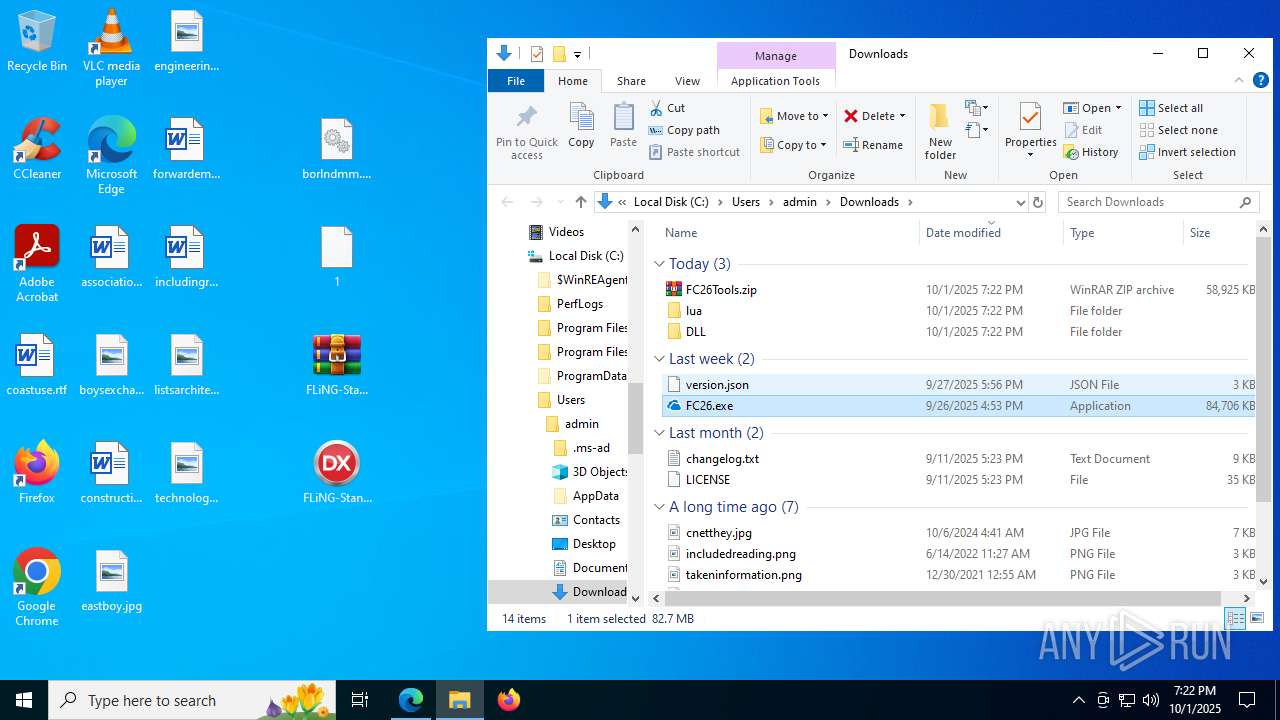
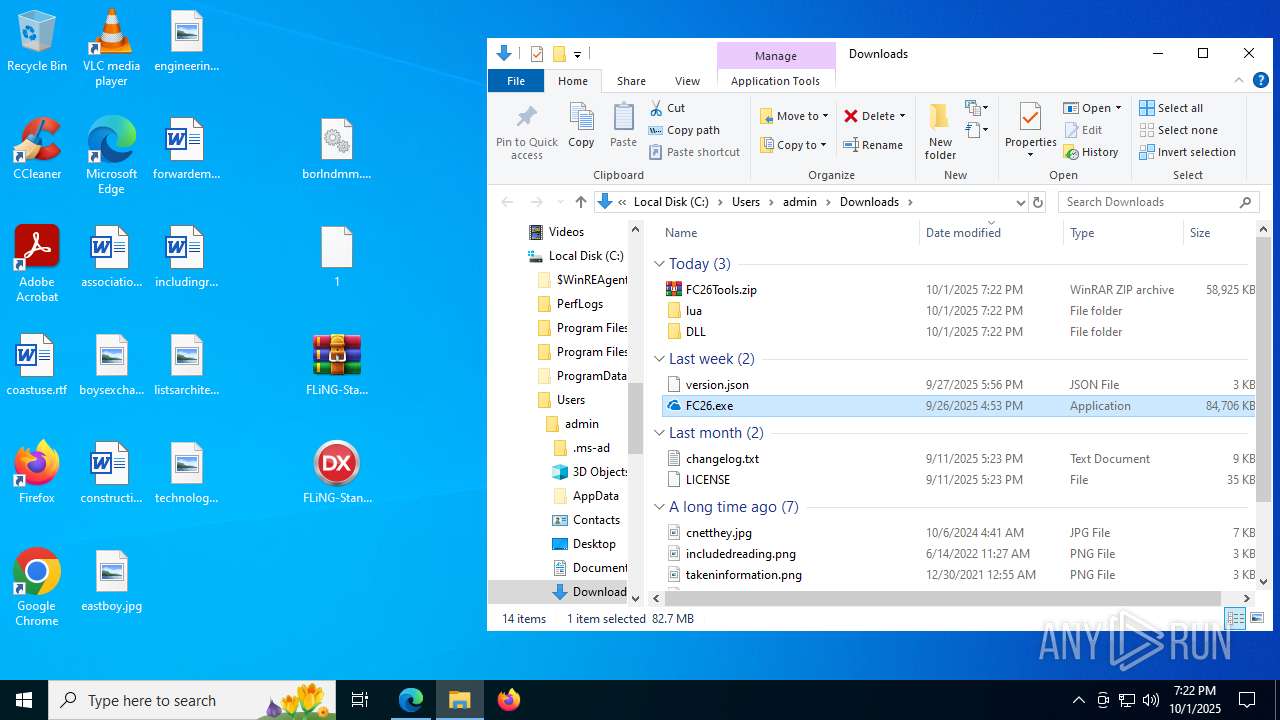
| URL: | https://flingtrainer.io/ea-sports-fc-26-trainer/ |
| Full analysis: | https://app.any.run/tasks/0a9e0750-6d33-405f-a301-685437201f07 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
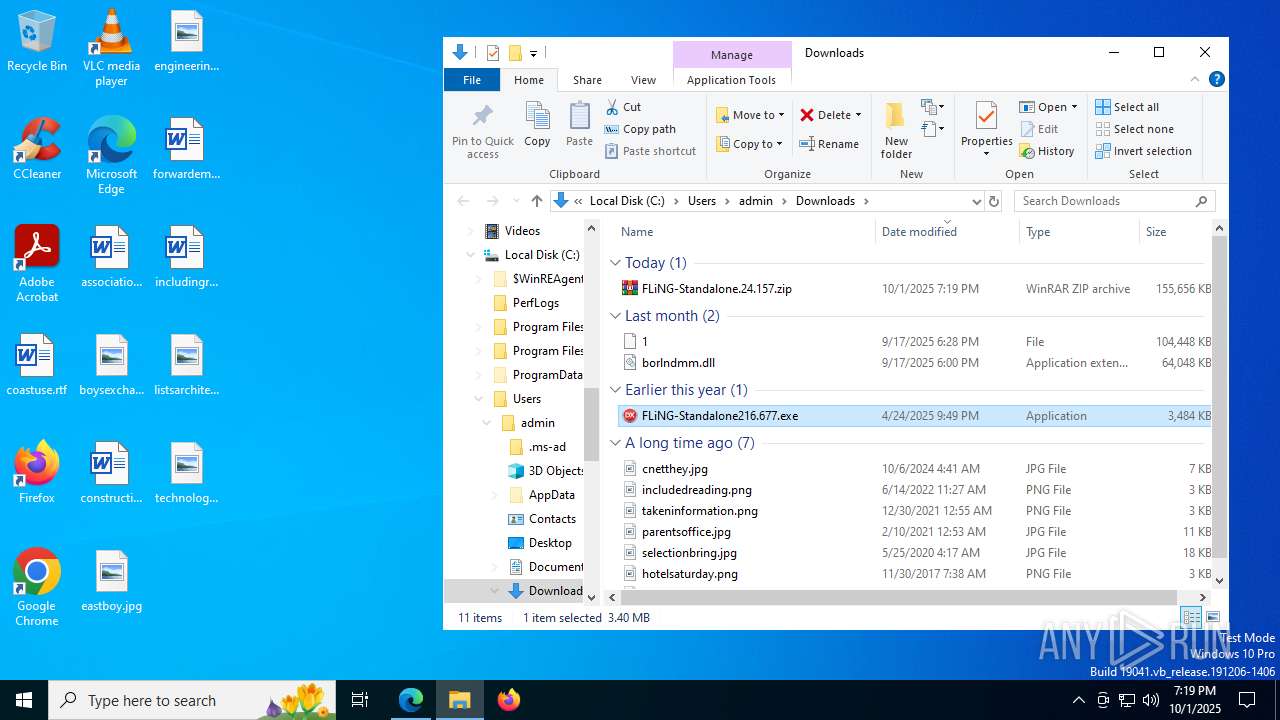
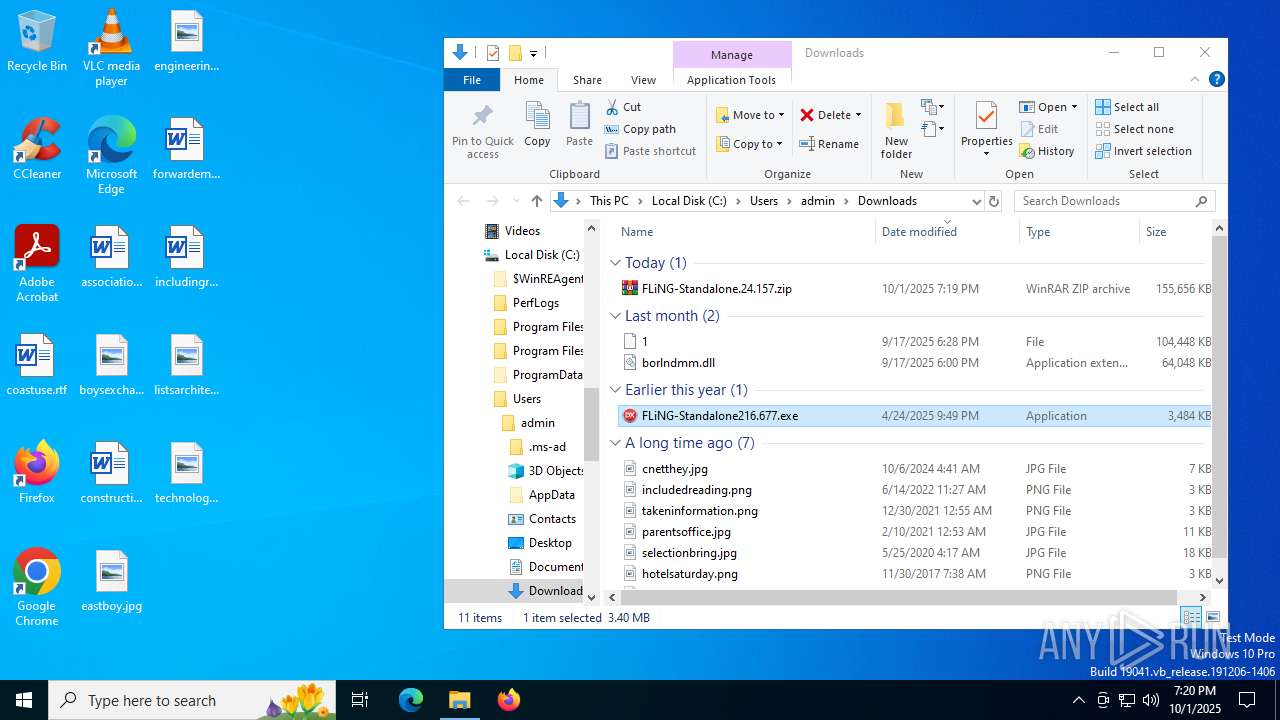
| Analysis date: | October 01, 2025, 19:18:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3FFC9D4A6818F8AE535DE7AAA65C7802 |
| SHA1: | 1BEDE16D1167D6A7A7E1E97D440EB31004EBE1E5 |
| SHA256: | 29549EBE10D1B69DBE3B38DECD9D0399099C42DA9152DEF3A2F9A86DECBD1BFD |
| SSDEEP: | 3:N8ILSTK8DWURXEm:2f9DWqP |
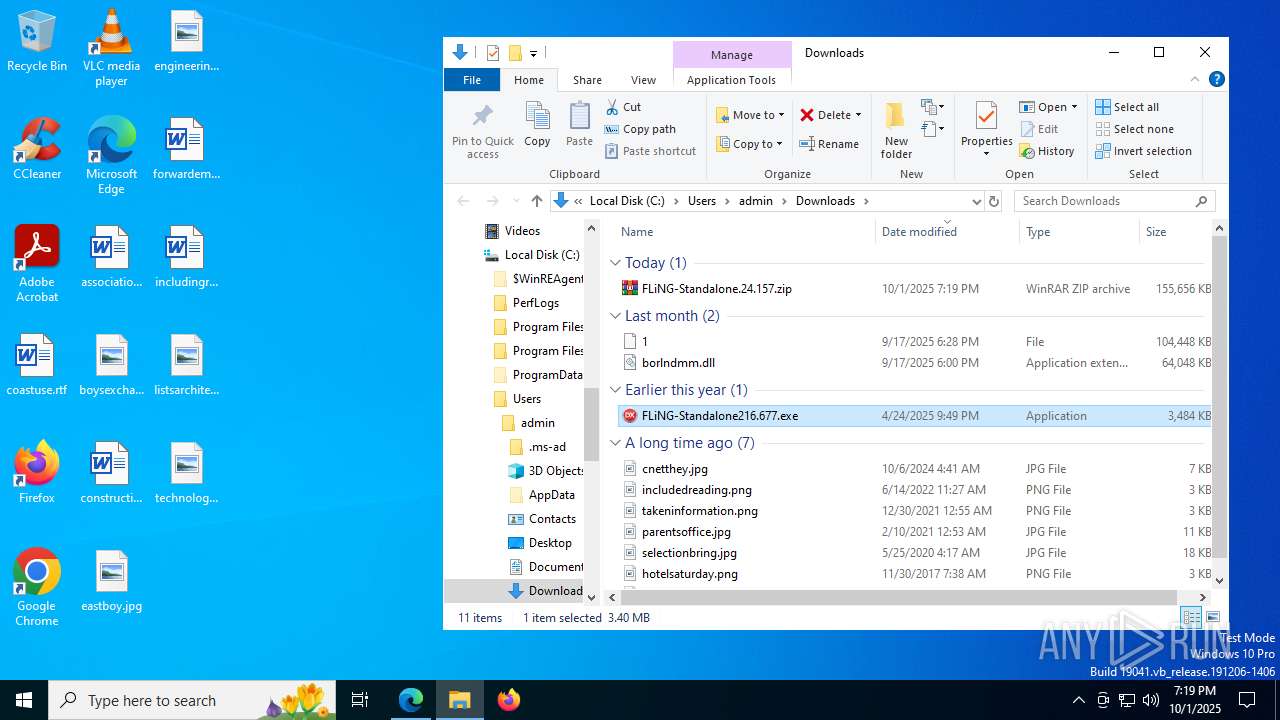
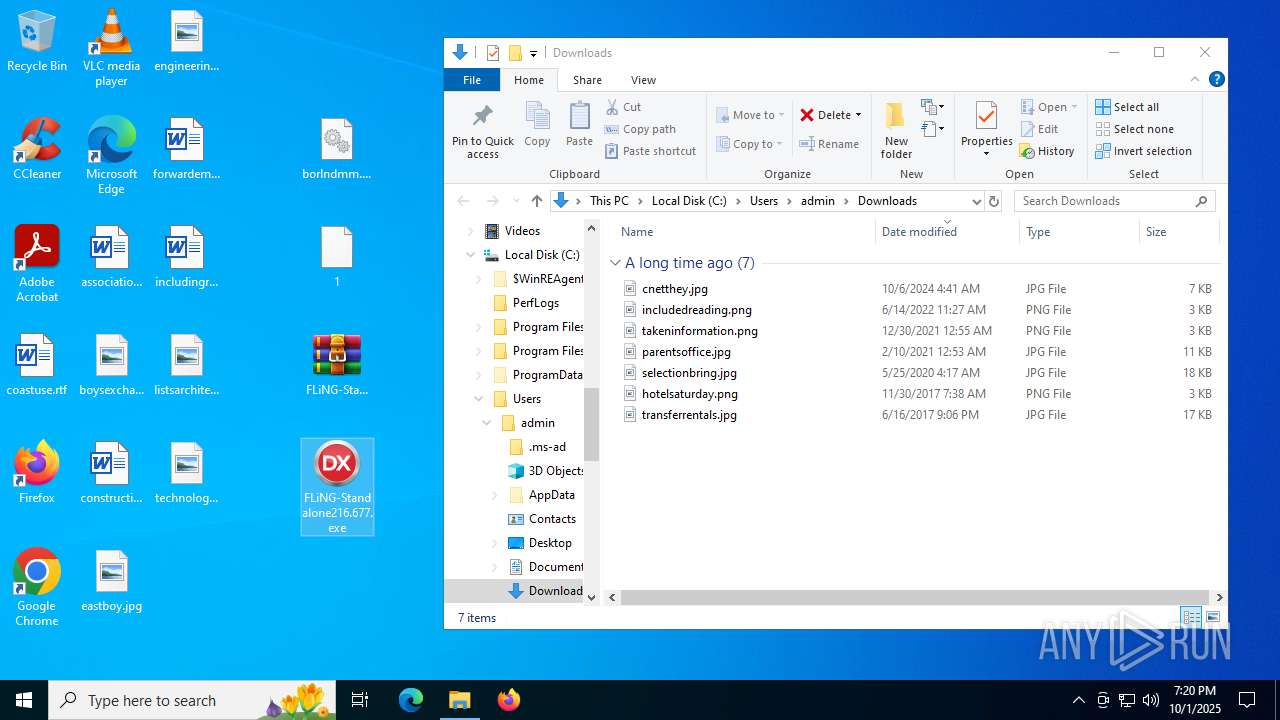
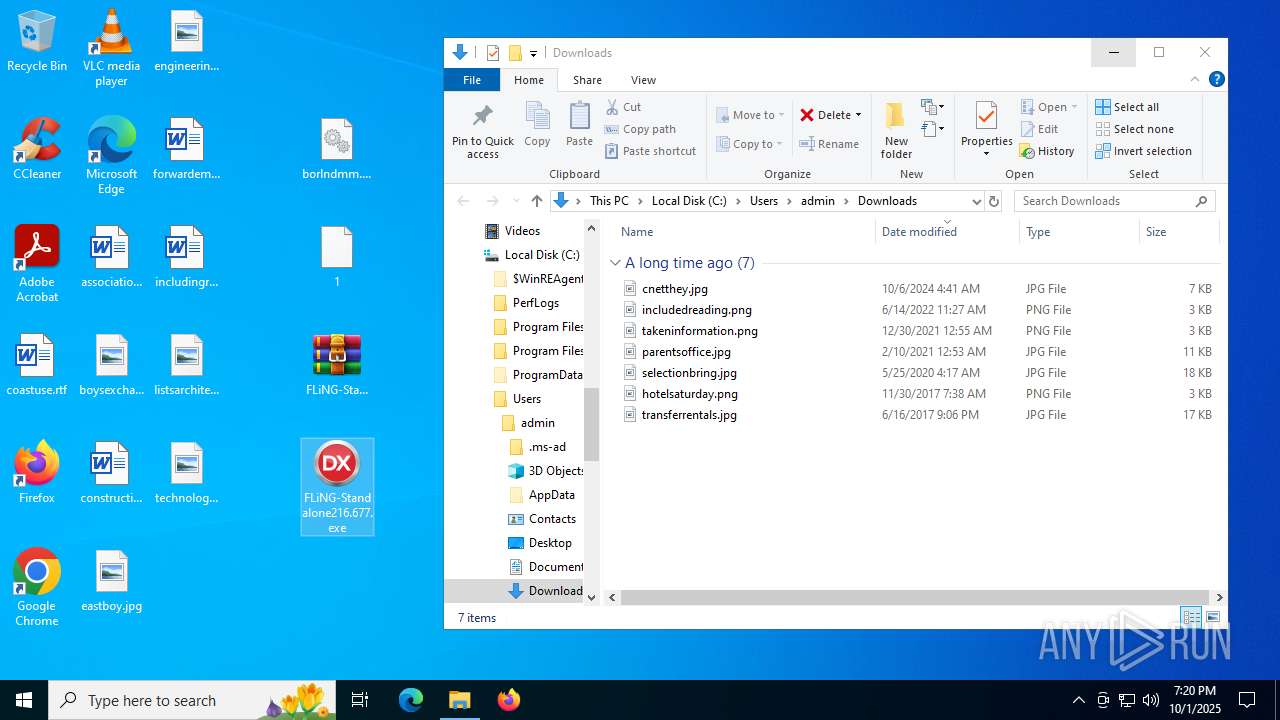
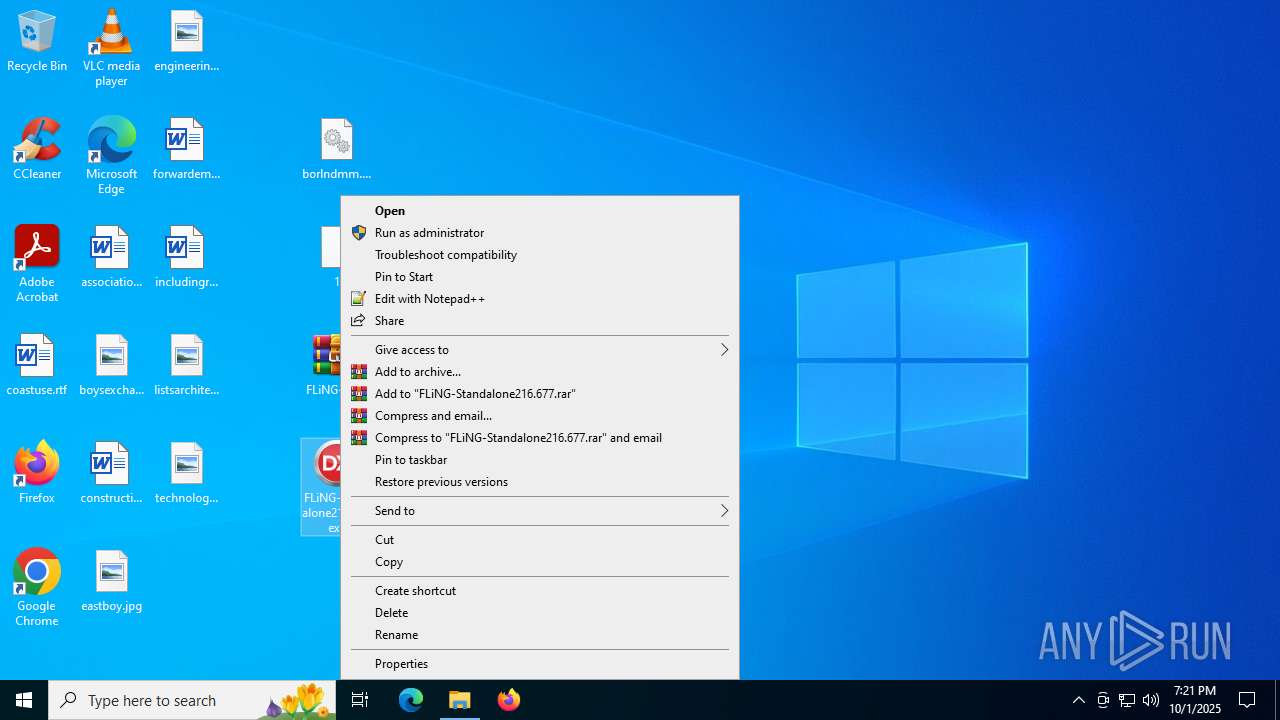
MALICIOUS
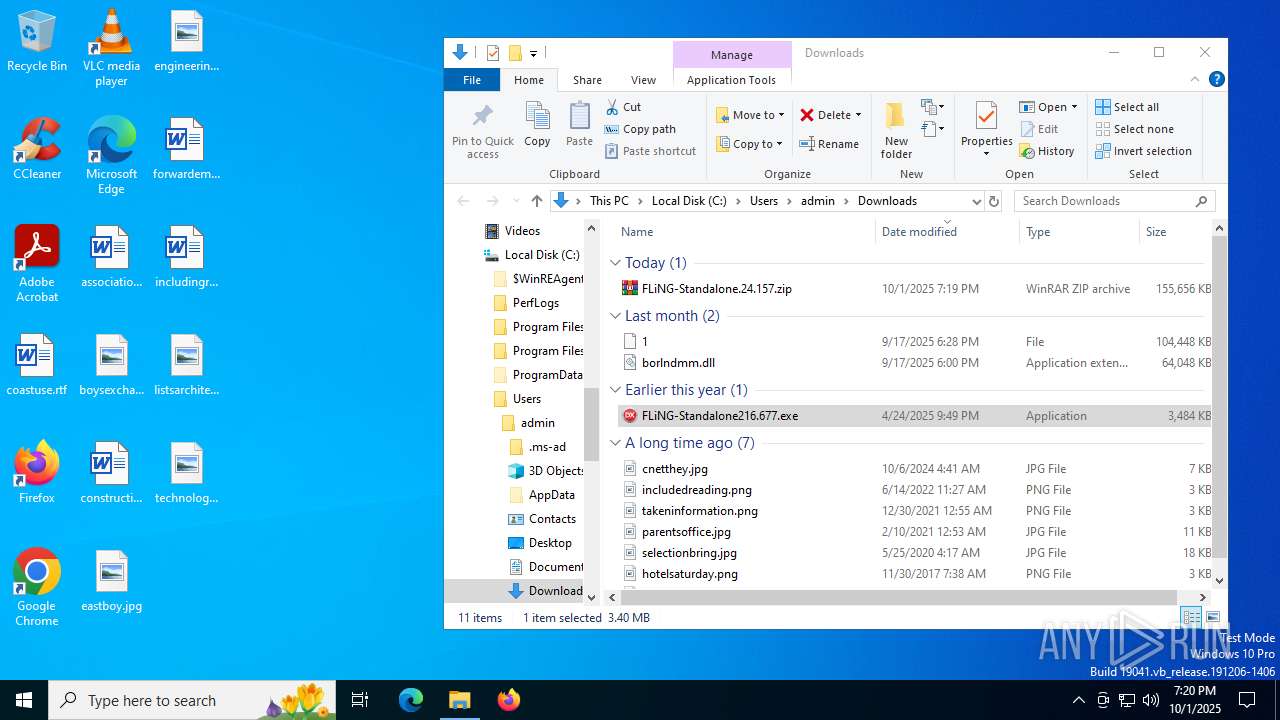
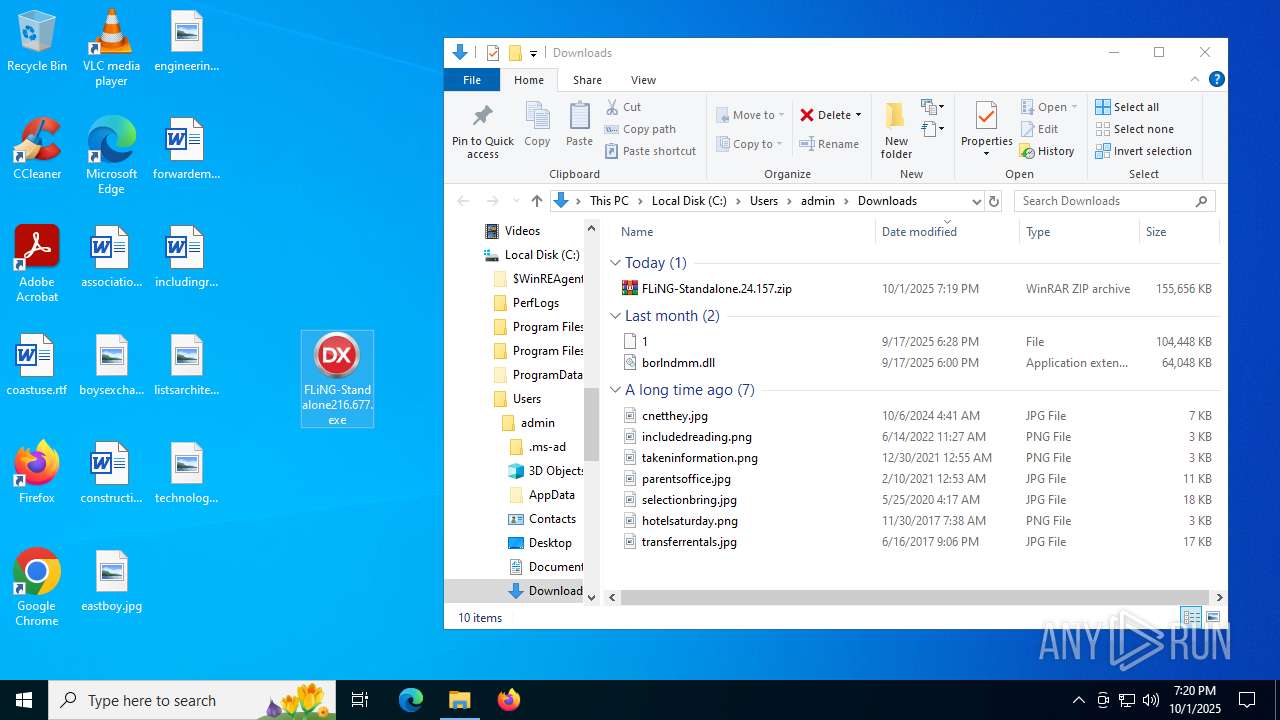
Executing a file with an untrusted certificate
- FLiNG-Standalone216.677.exe (PID: 5432)
- FLiNG-Standalone216.677.exe (PID: 7252)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 5348)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FLiNG-Standalone216.677.exe (PID: 7688)
AUROTUN mutex has been found
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FLiNG-Standalone216.677.exe (PID: 7688)
Connects to the CnC server
- FLiNG-Standalone216.677.exe (PID: 3976)
AUROTUN has been detected (YARA)
- FLiNG-Standalone216.677.exe (PID: 3976)
Run PowerShell with an invisible window
- powershell.exe (PID: 6676)
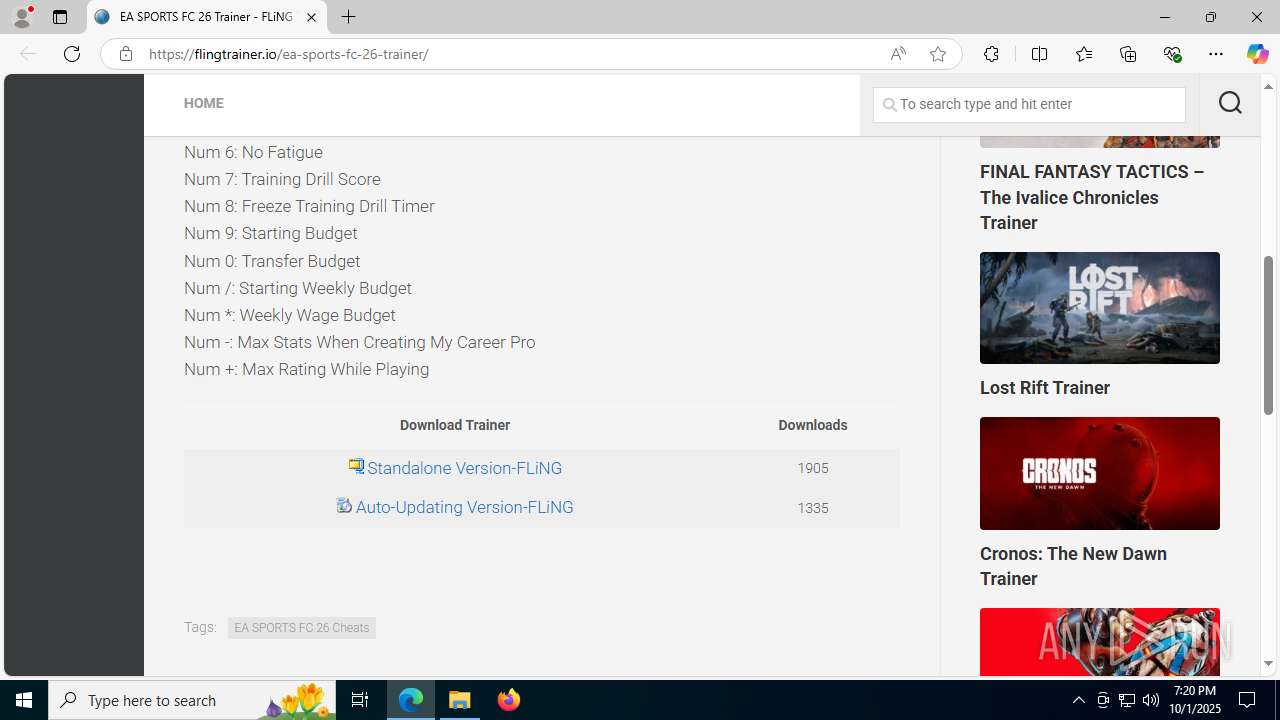
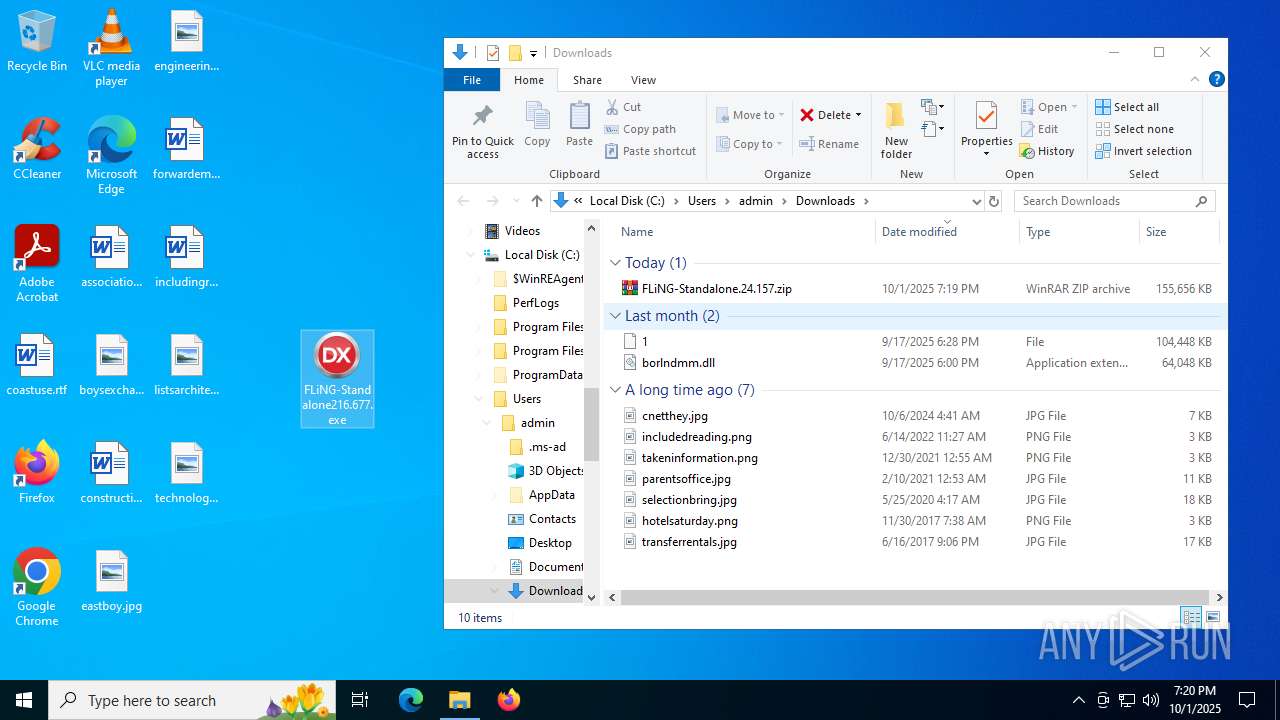
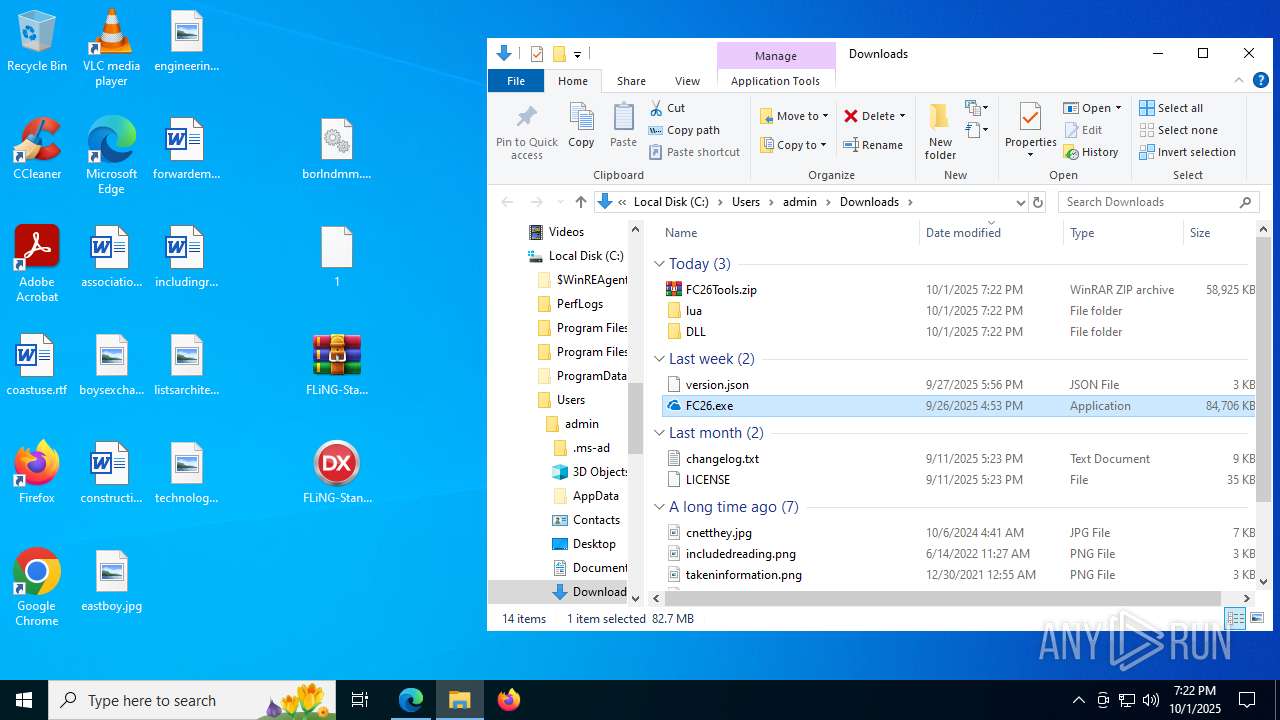
Adds path to the Windows Defender exclusion list
- FC26.exe (PID: 5904)
Changes Windows Defender settings
- FC26.exe (PID: 5904)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- FLiNG-Standalone216.677.exe (PID: 5432)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 5348)
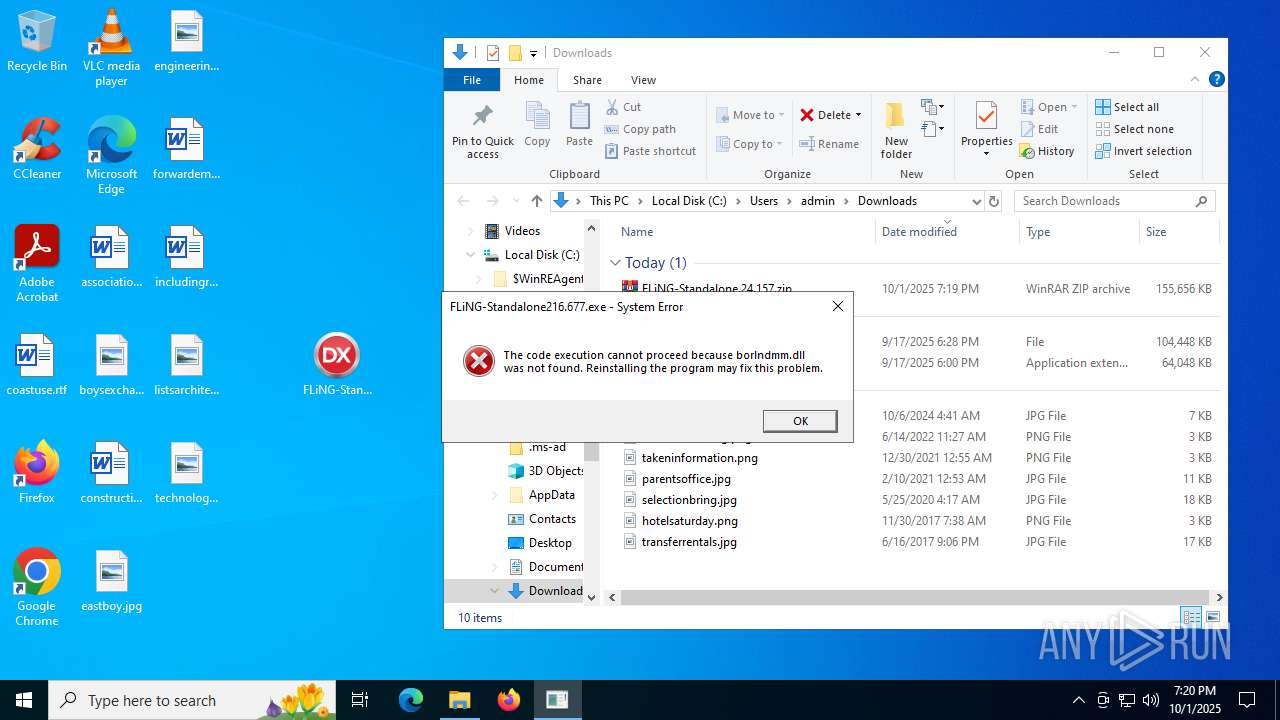
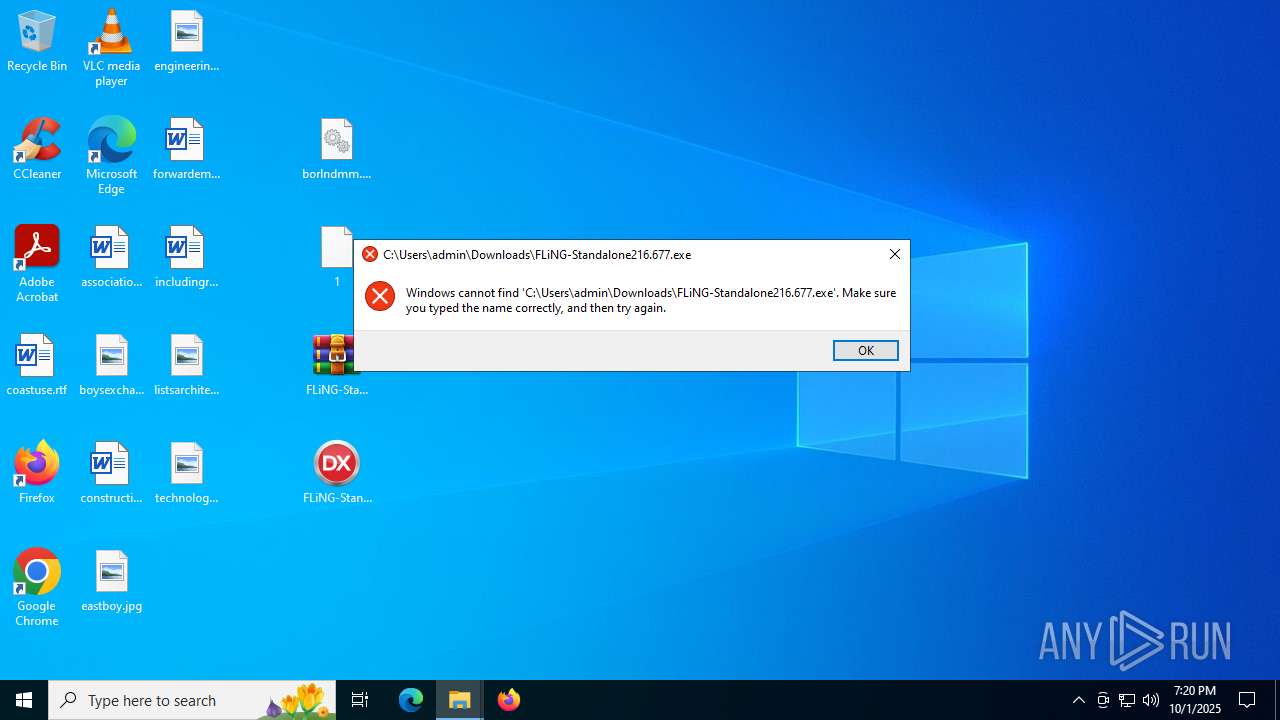
Executes application which crashes
- FLiNG-Standalone216.677.exe (PID: 5432)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 5348)
Application launched itself
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 5348)
- FLiNG-Standalone216.677.exe (PID: 4112)
Checks for external IP
- FLiNG-Standalone216.677.exe (PID: 3976)
- svchost.exe (PID: 2200)
Connects to unusual port
- FLiNG-Standalone216.677.exe (PID: 3976)
Get information on the list of running processes
- FC26.exe (PID: 3656)
- cmd.exe (PID: 2964)
- cmd.exe (PID: 3760)
- FC26.exe (PID: 5904)
Starts CMD.EXE for commands execution
- FC26.exe (PID: 3656)
- powershell.exe (PID: 6676)
- FC26.exe (PID: 5904)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4576)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 1332)
- FC26.exe (PID: 5904)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4576)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 4684)
- cmd.exe (PID: 1332)
- FC26.exe (PID: 5904)
Starts process via Powershell
- powershell.exe (PID: 6676)
The executable file from the user directory is run by the CMD process
- FC26.exe (PID: 5904)
Identifying current user with WHOAMI command
- cmd.exe (PID: 1840)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 2692)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 5348)
- net.exe (PID: 8060)
- cmd.exe (PID: 5928)
- net.exe (PID: 984)
- cmd.exe (PID: 1800)
- net.exe (PID: 7044)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1624)
The process hide an interactive prompt from the user
- FC26.exe (PID: 5904)
Script adds exclusion path to Windows Defender
- FC26.exe (PID: 5904)
INFO
Application launched itself
- msedge.exe (PID: 2288)
- msedge.exe (PID: 6536)
Checks supported languages
- identity_helper.exe (PID: 7764)
- FLiNG-Standalone216.677.exe (PID: 5432)
- identity_helper.exe (PID: 7988)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 5348)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FC26.exe (PID: 3656)
- FLiNG-Standalone216.677.exe (PID: 7688)
- FC26.exe (PID: 5904)
Reads Environment values
- identity_helper.exe (PID: 7764)
- identity_helper.exe (PID: 7988)
- FC26.exe (PID: 3656)
- FC26.exe (PID: 5904)
Reads the computer name
- identity_helper.exe (PID: 7764)
- identity_helper.exe (PID: 7988)
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FC26.exe (PID: 3656)
- FLiNG-Standalone216.677.exe (PID: 7688)
- FC26.exe (PID: 5904)
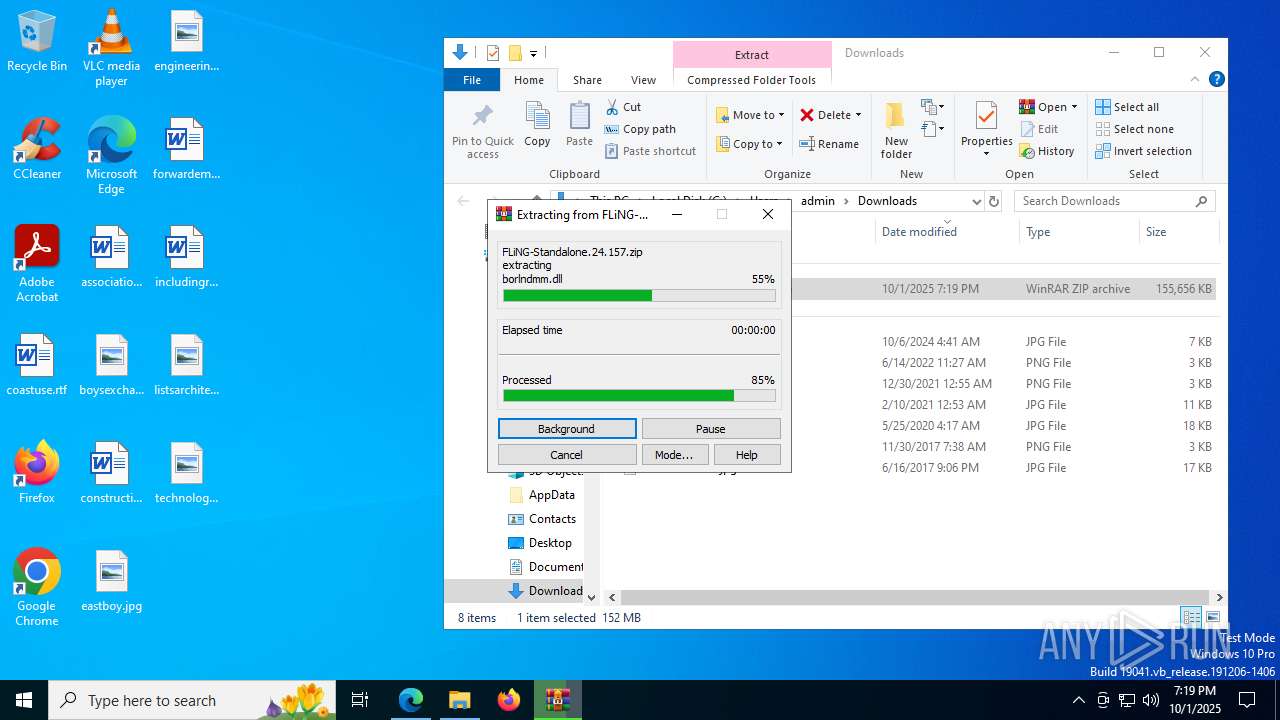
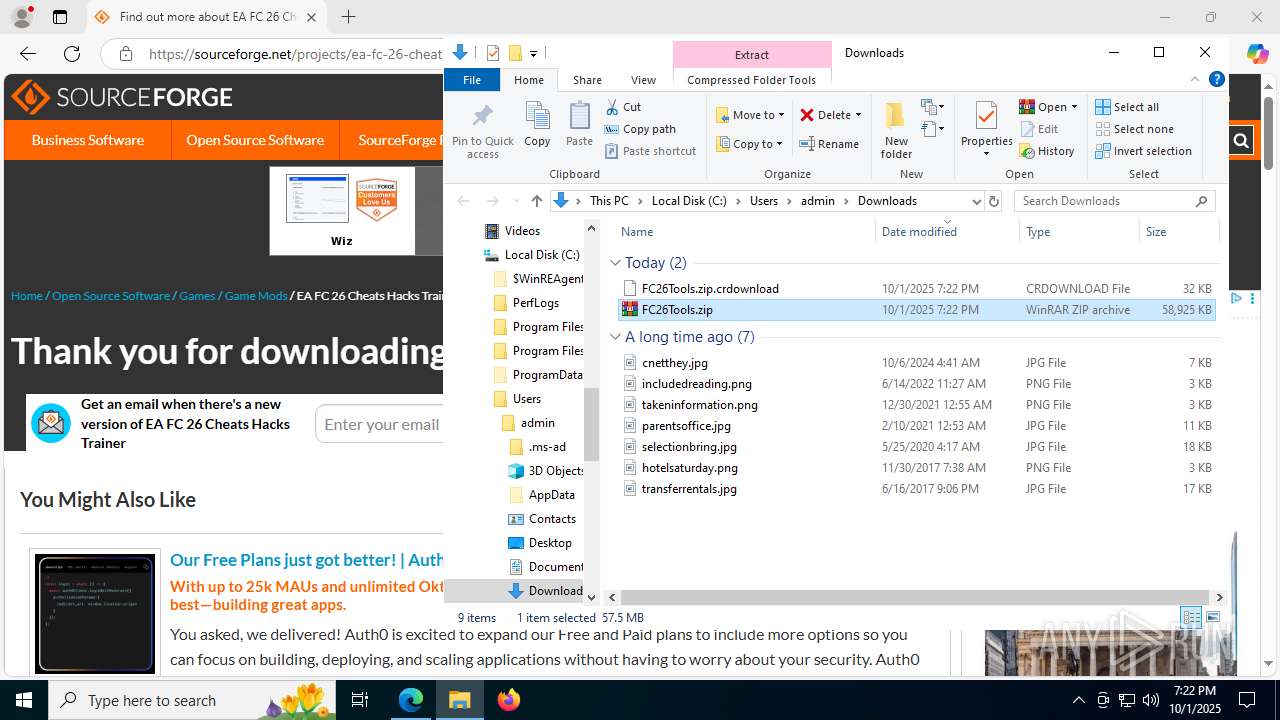
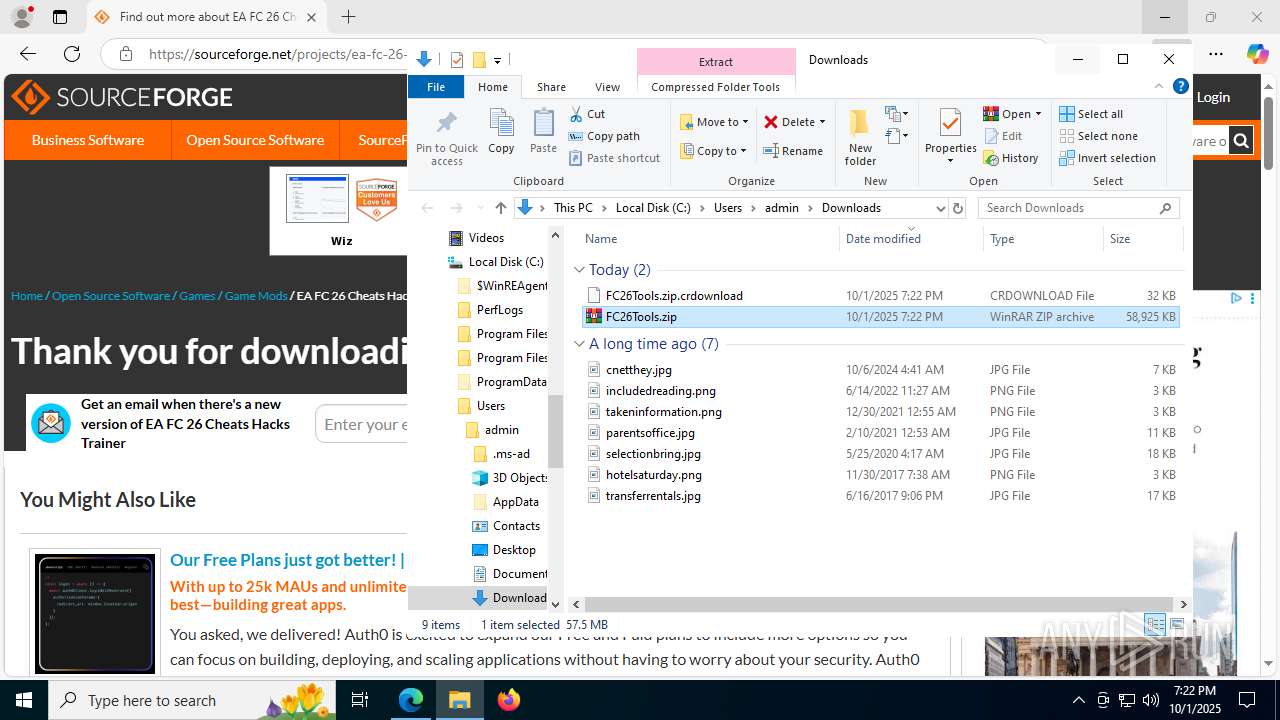
The sample compiled with english language support
- WinRAR.exe (PID: 7252)
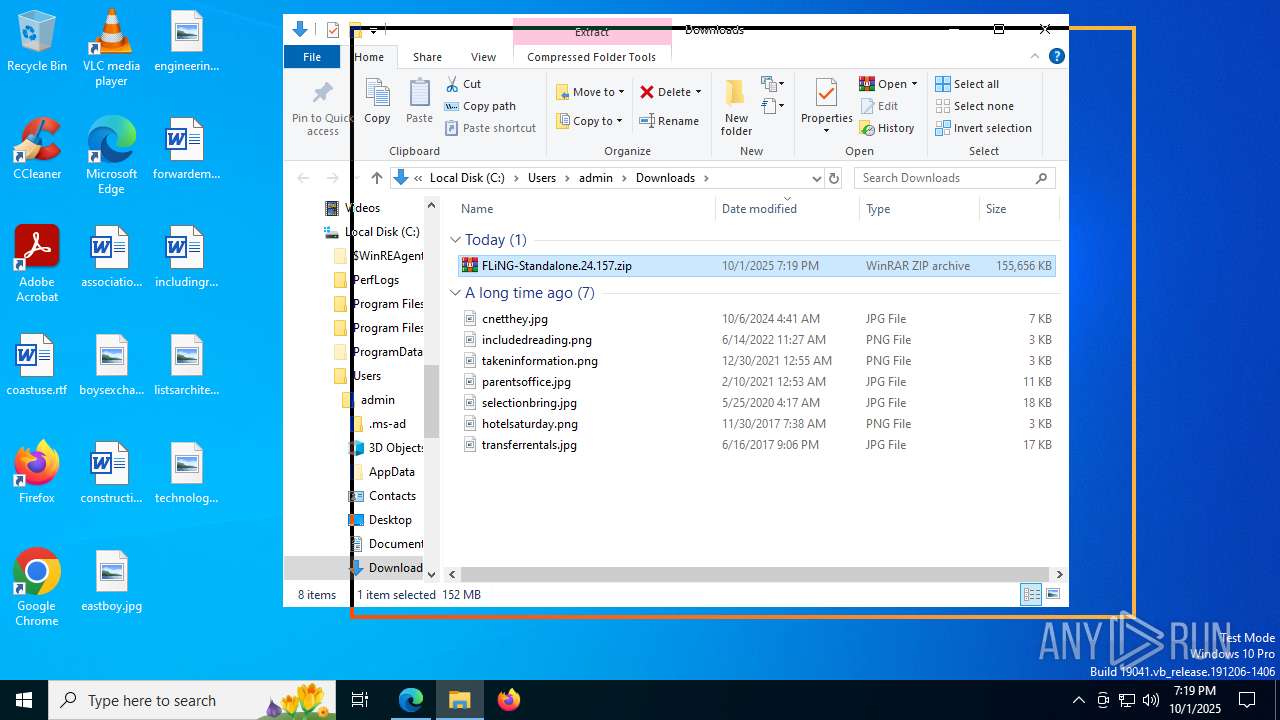
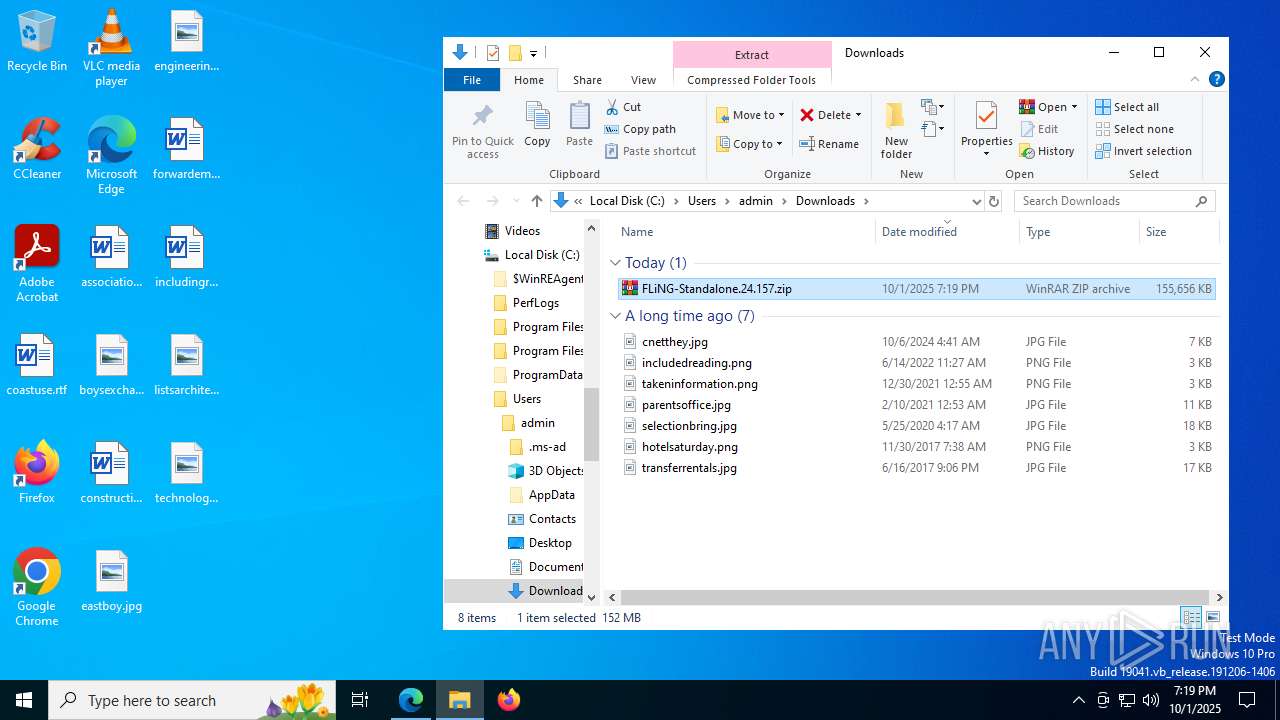
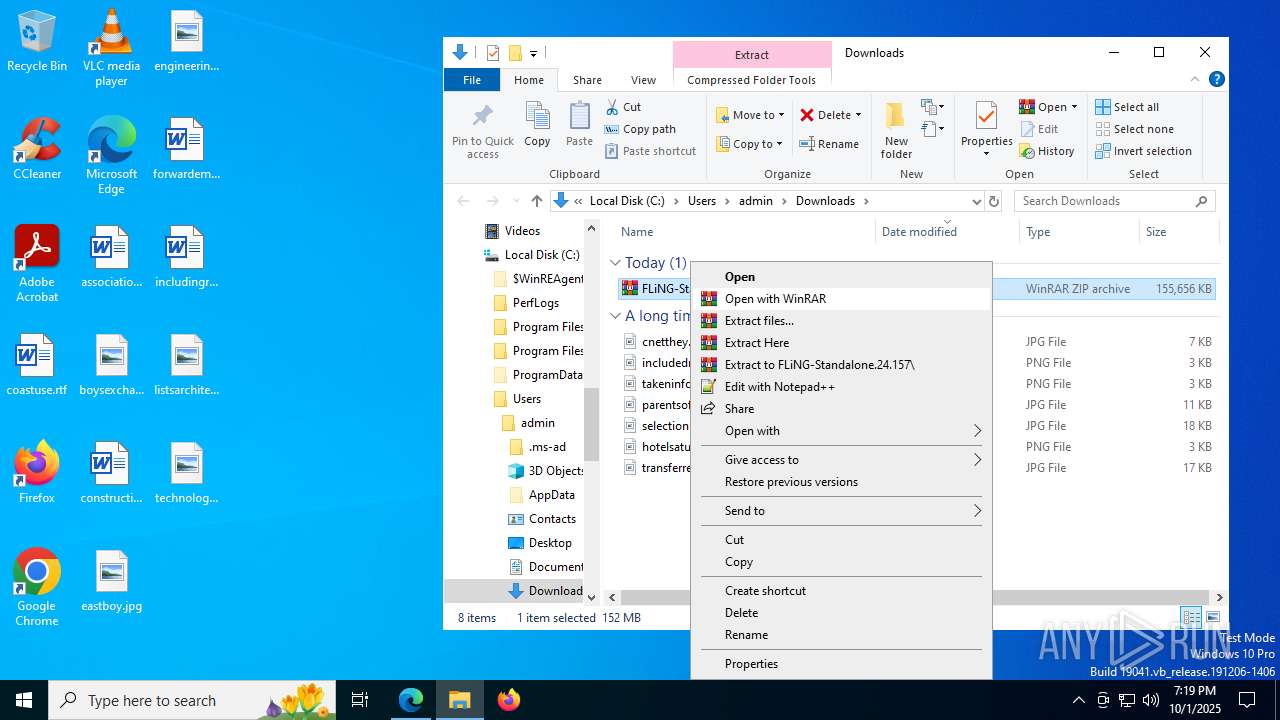
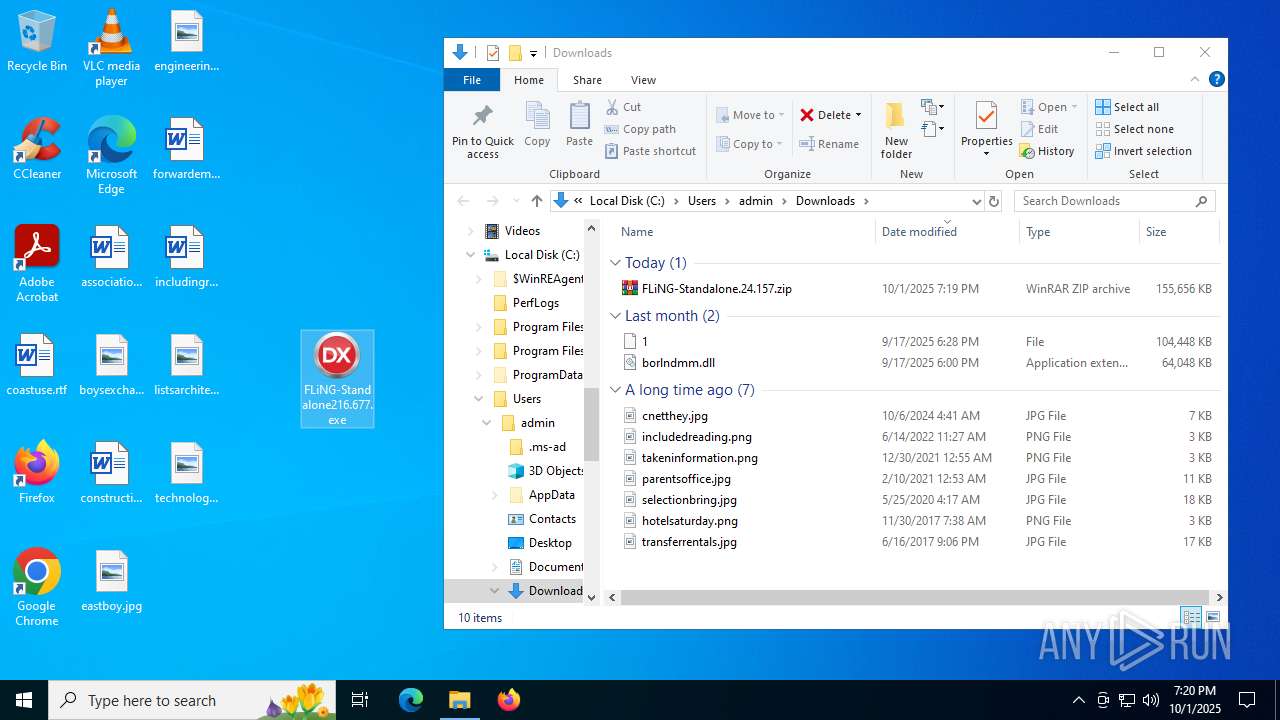
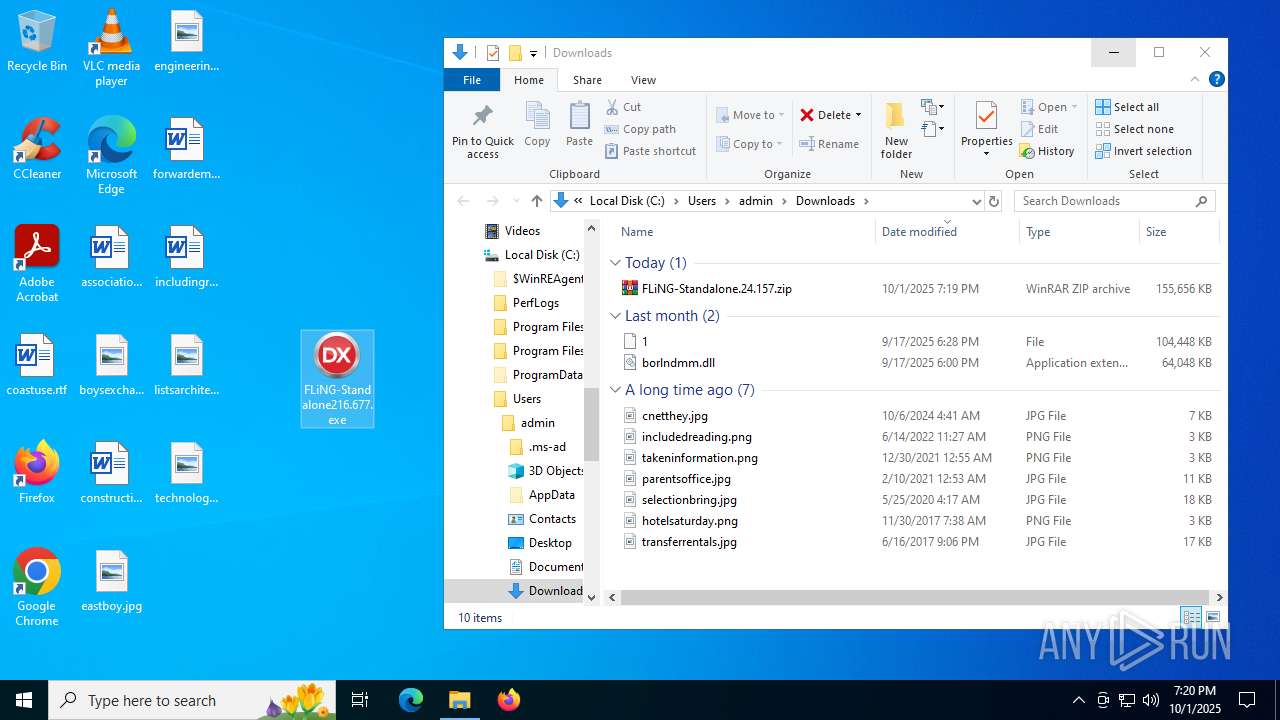
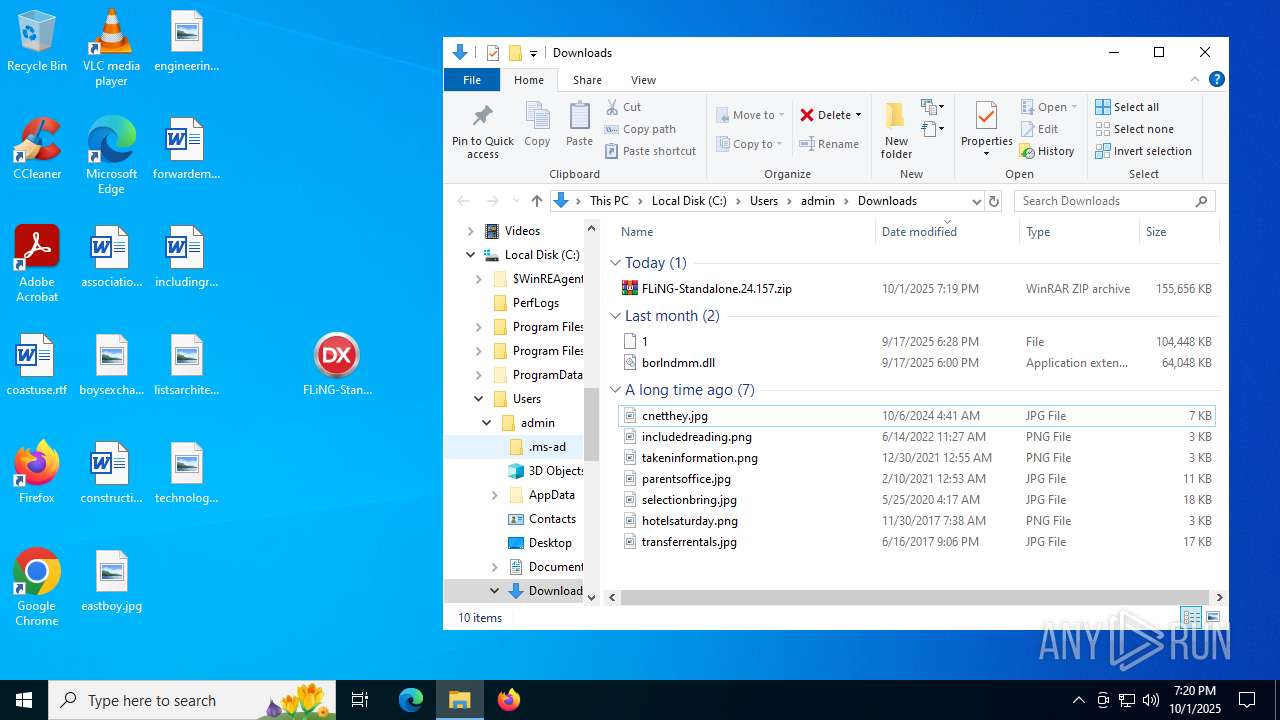
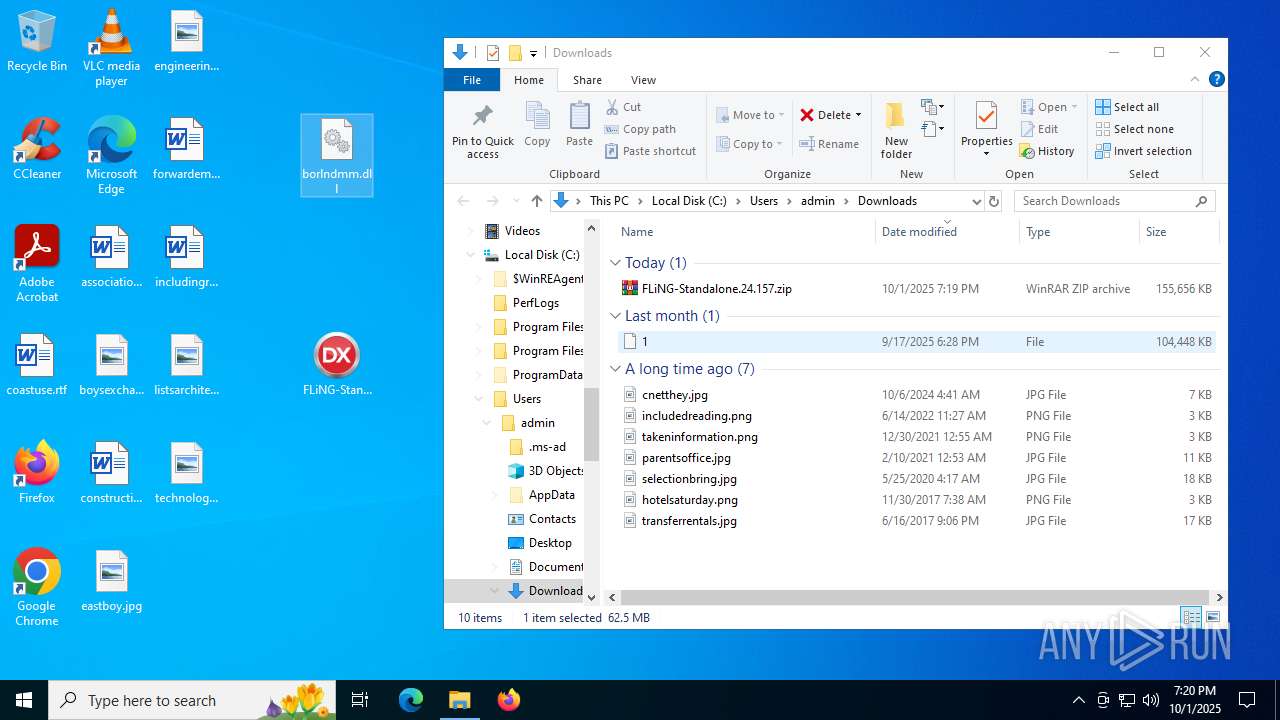
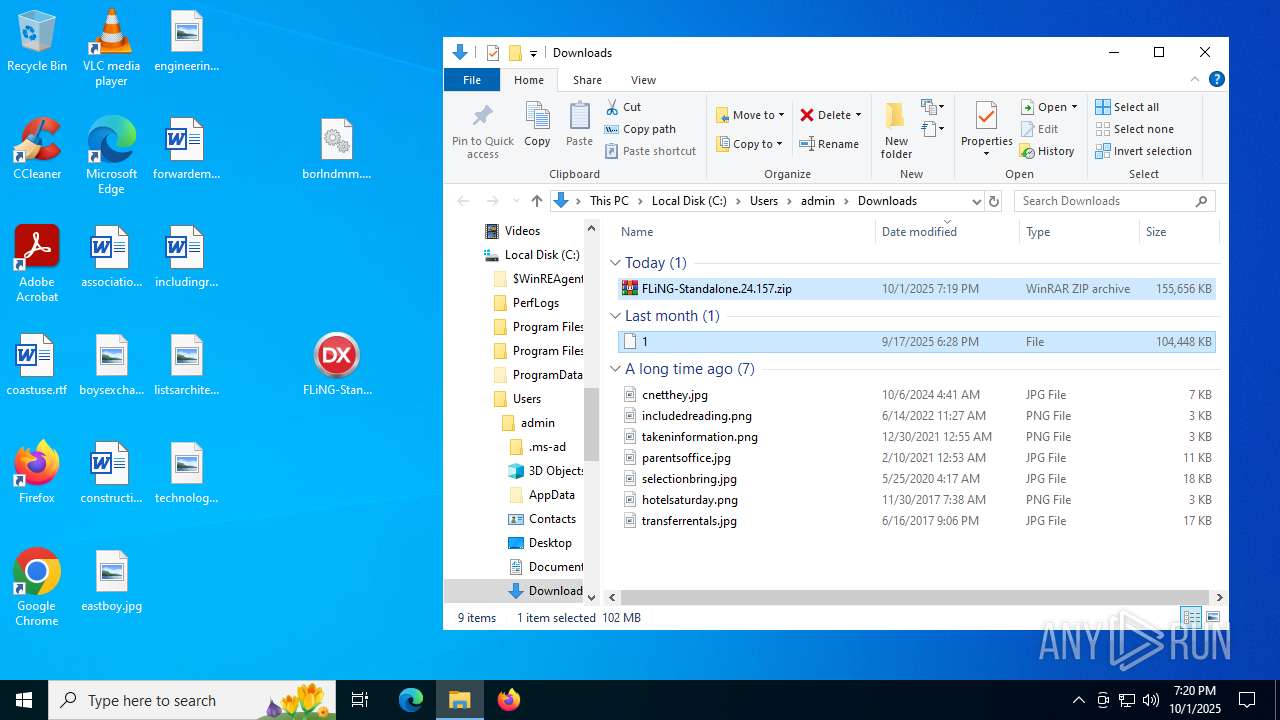
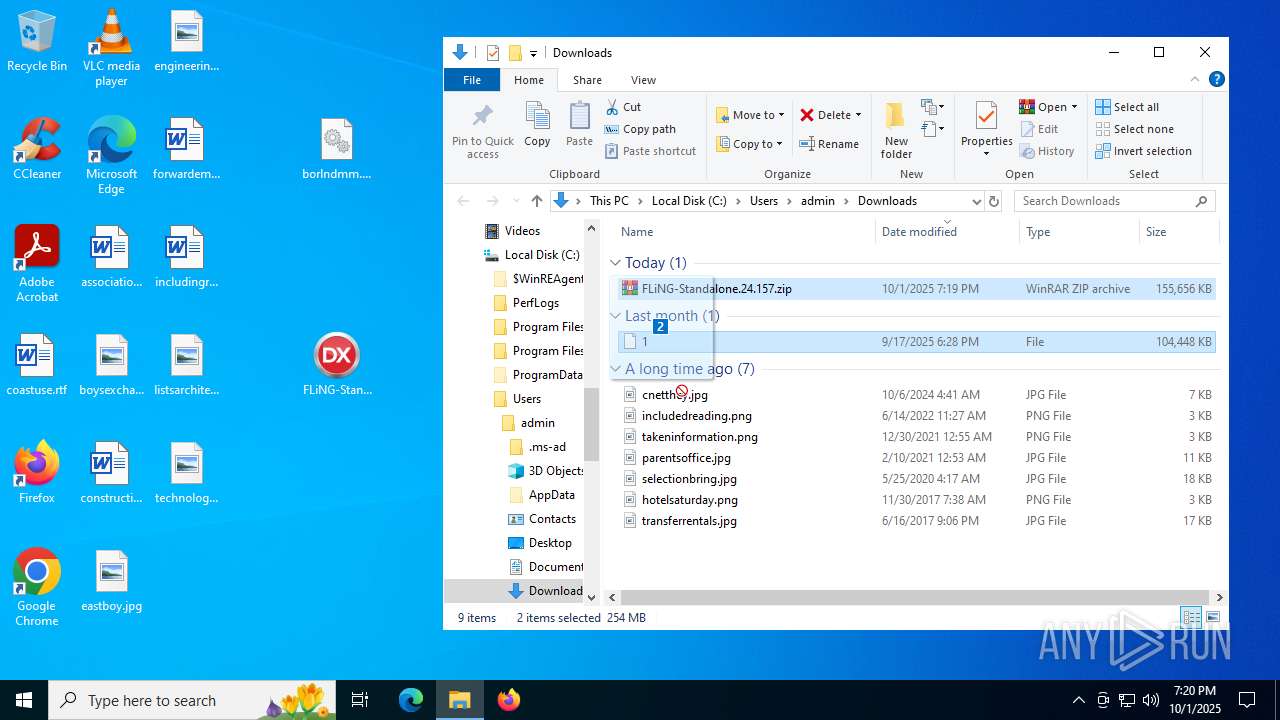
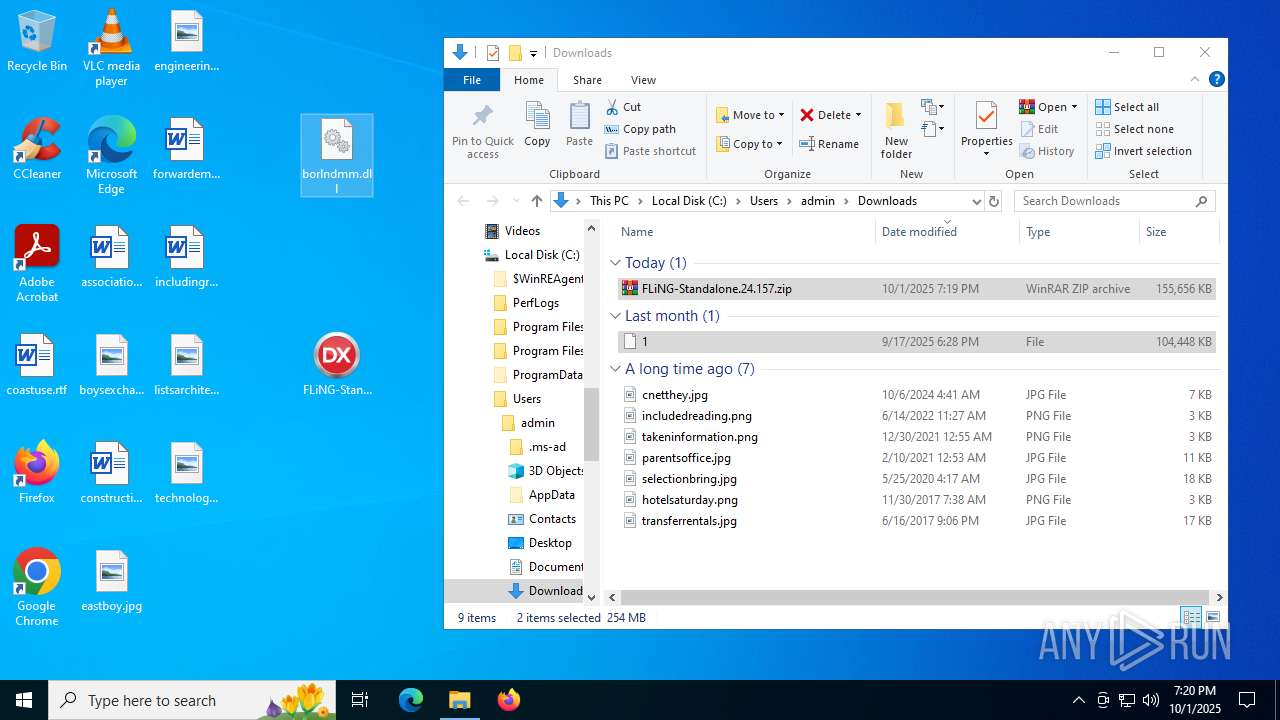
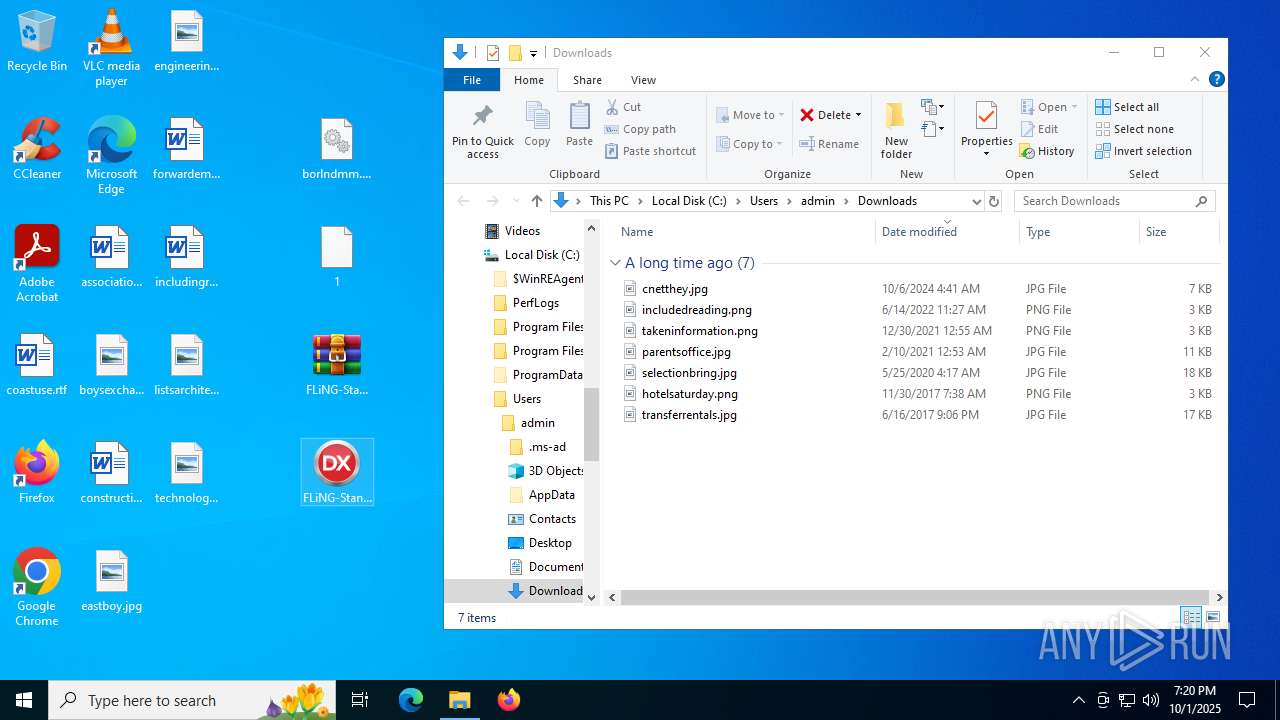
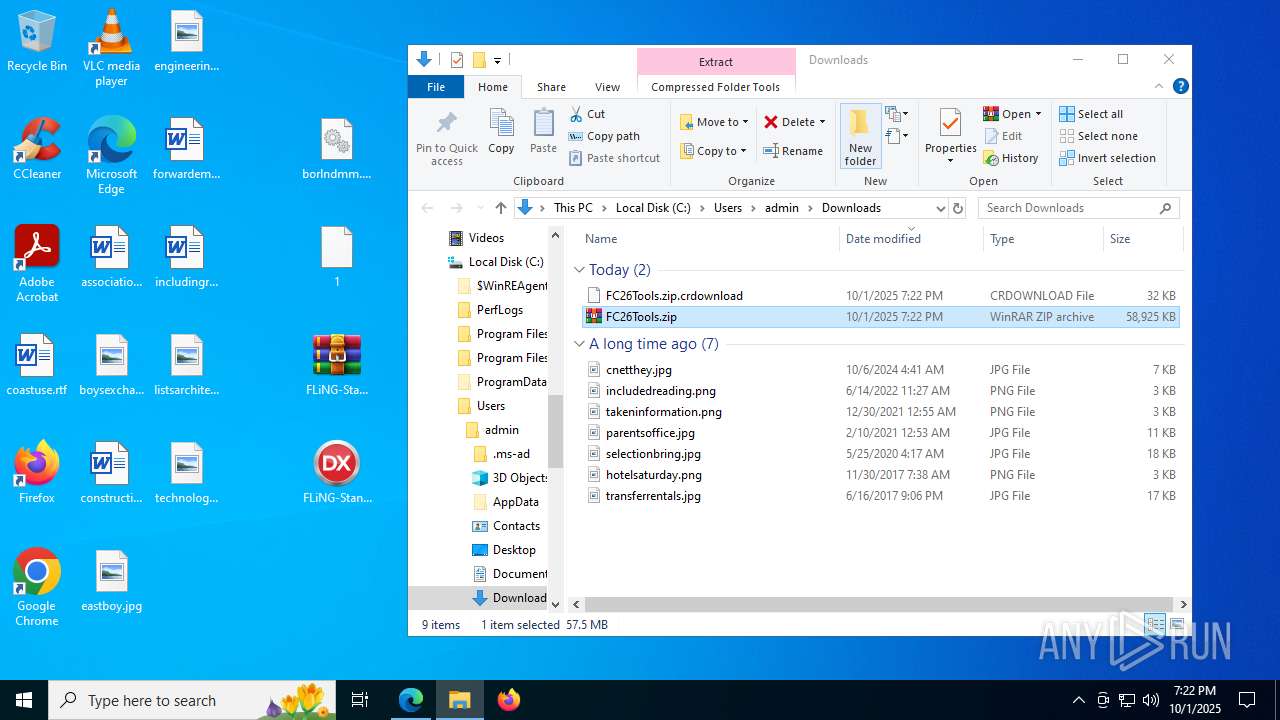
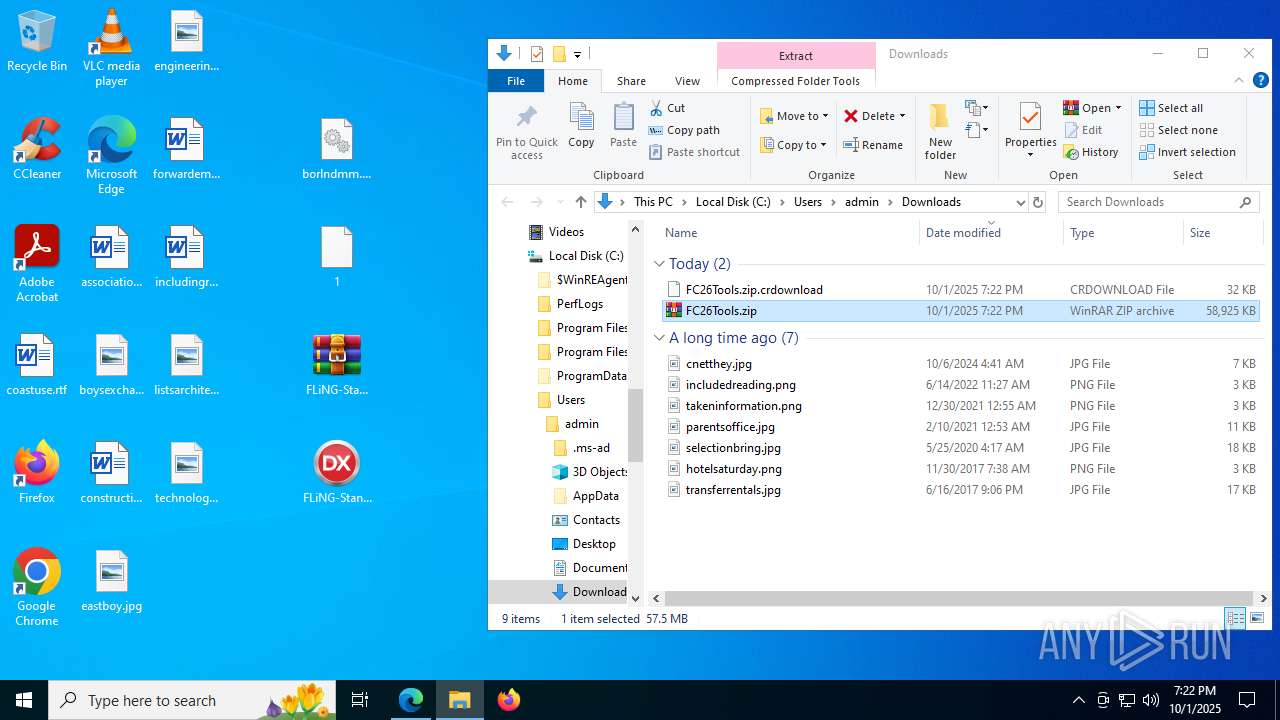
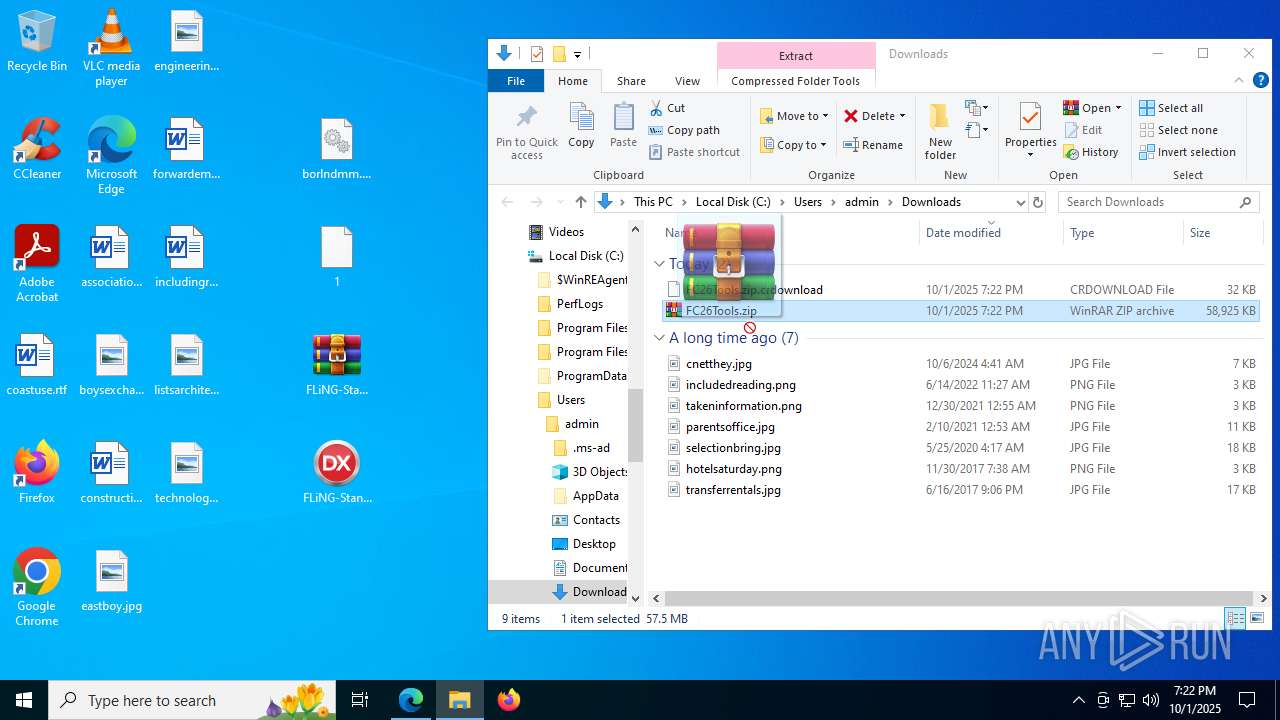
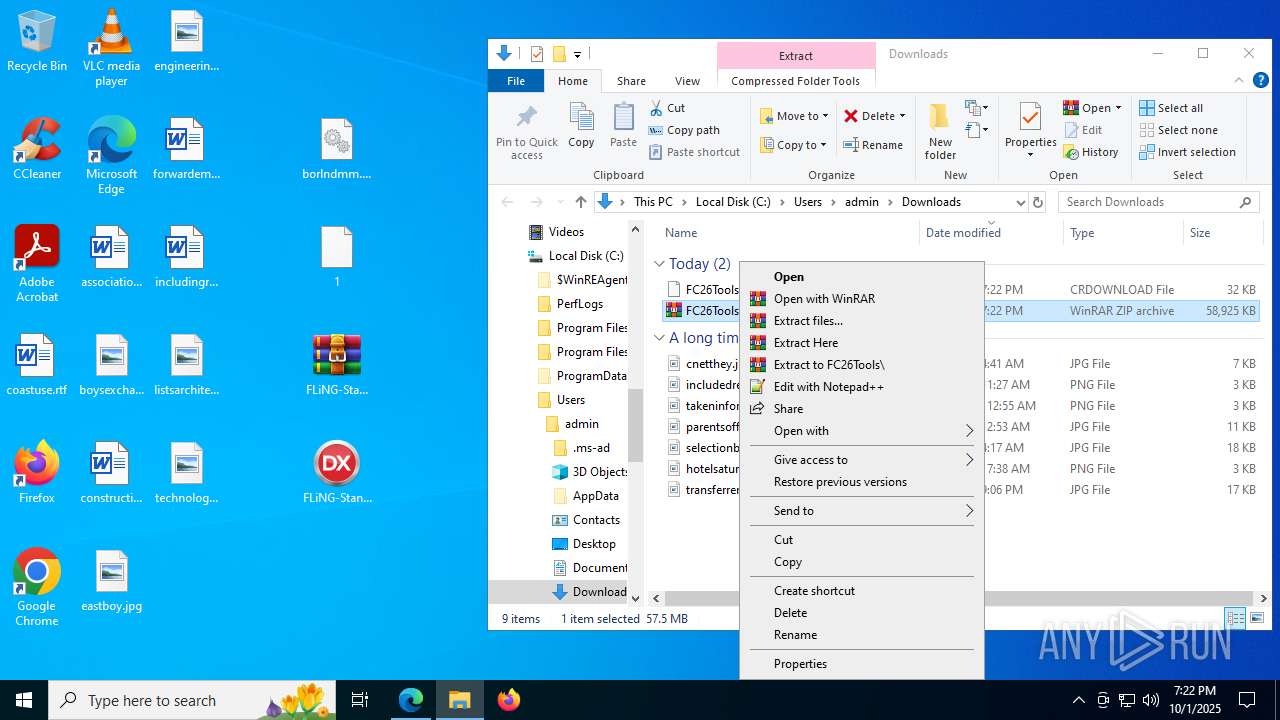
Manual execution by a user
- FLiNG-Standalone216.677.exe (PID: 5432)
- WinRAR.exe (PID: 7252)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 7252)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 5348)
- msedge.exe (PID: 7064)
- WinRAR.exe (PID: 7888)
- FC26.exe (PID: 3656)
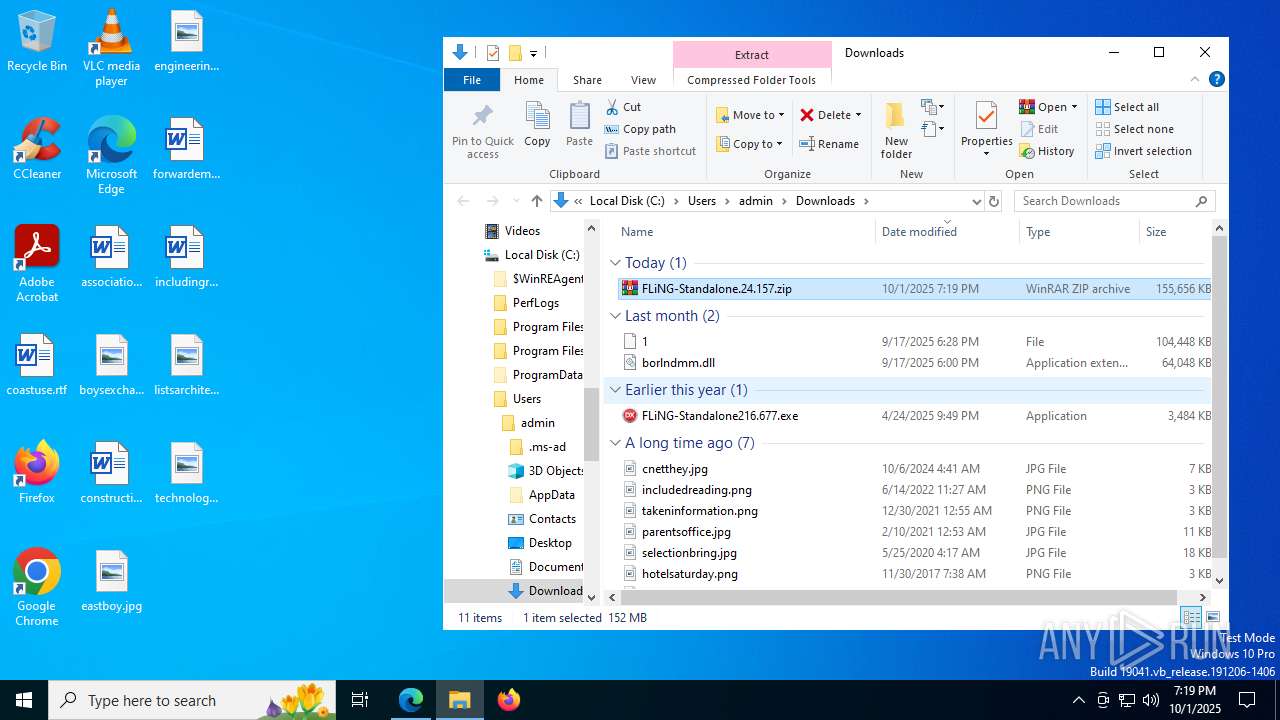
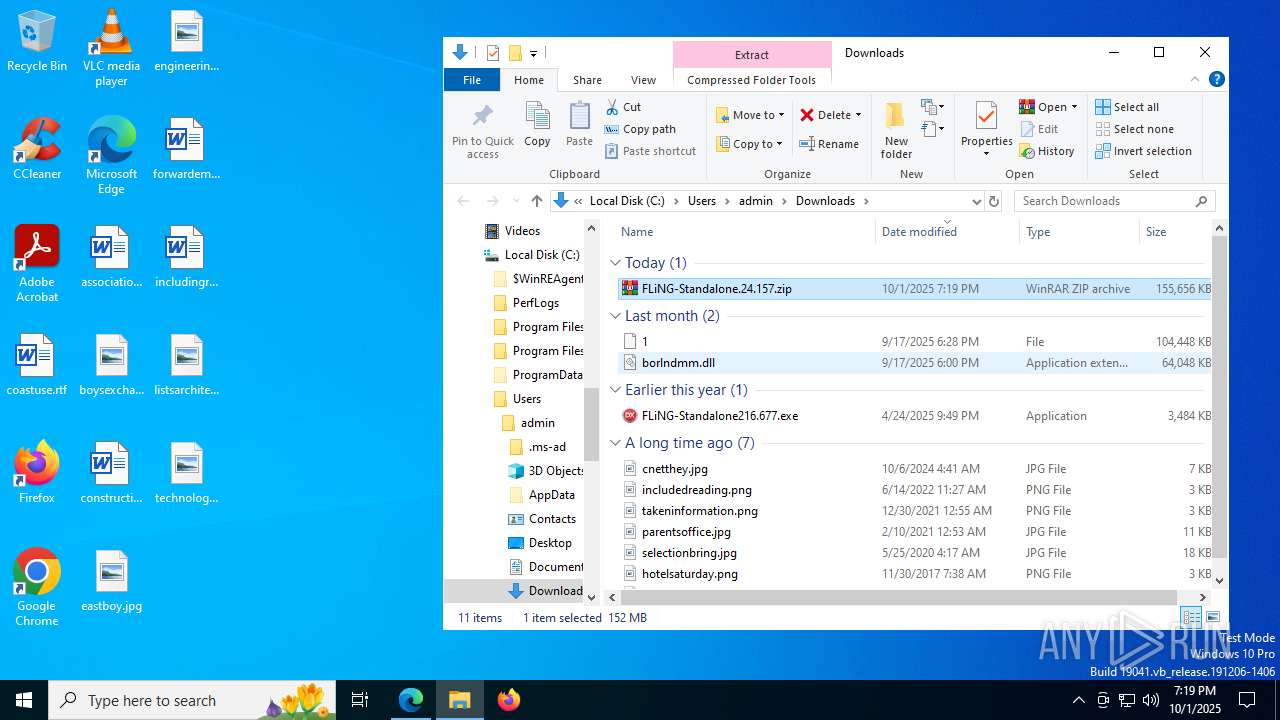
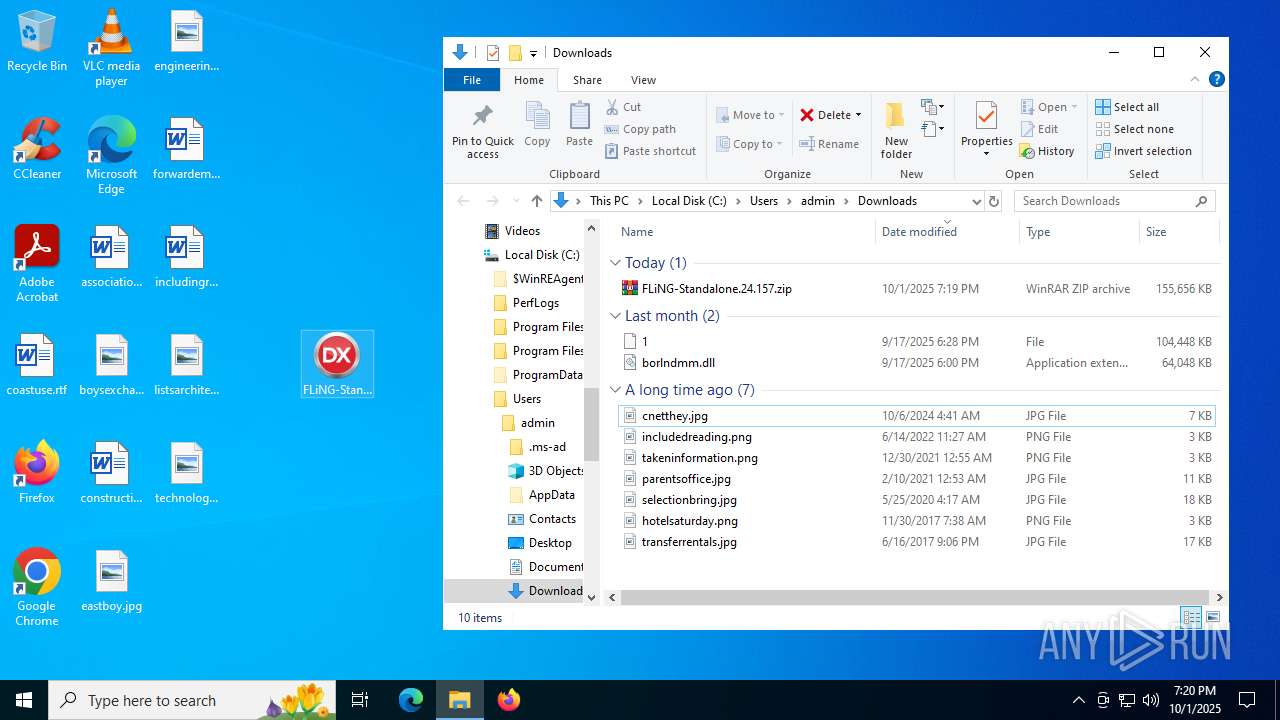
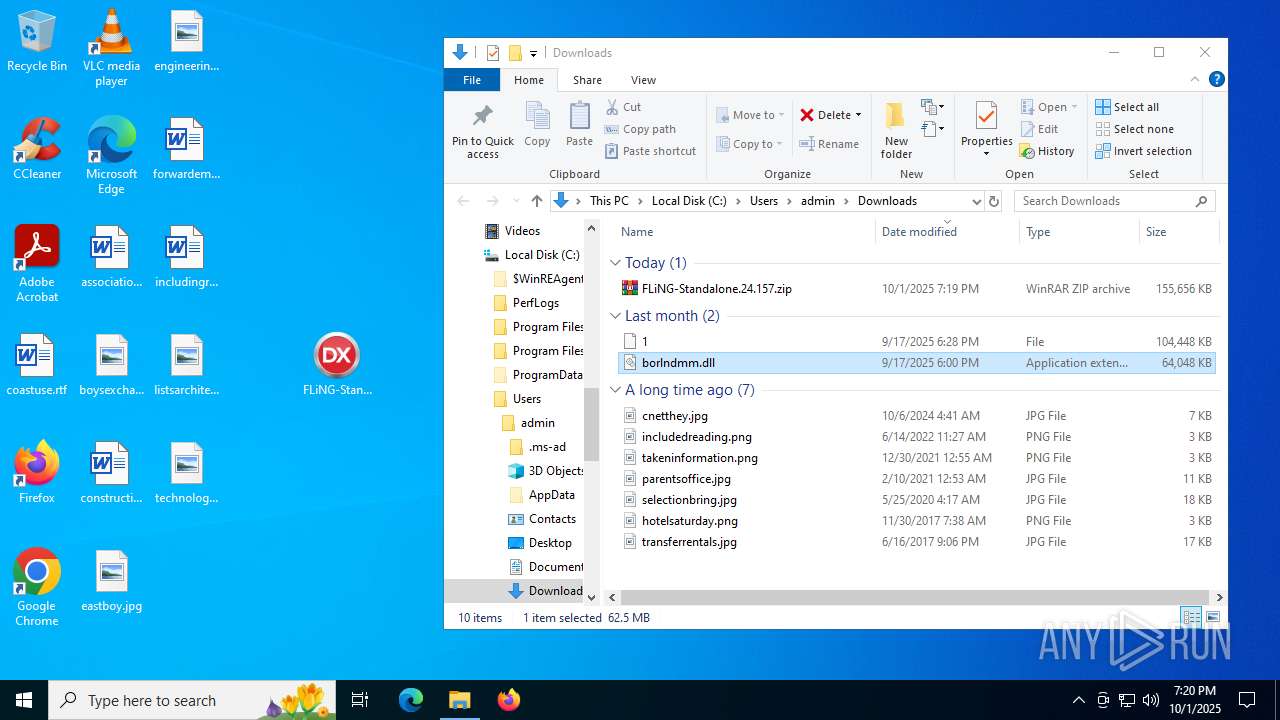
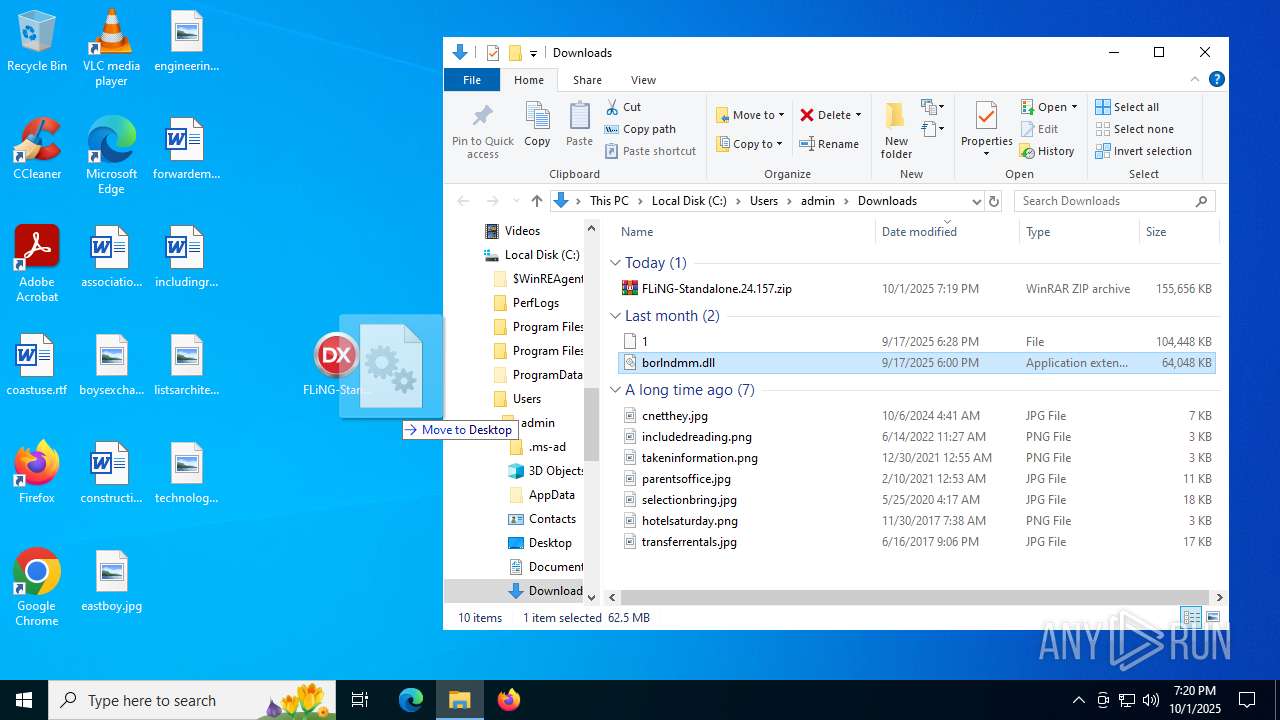
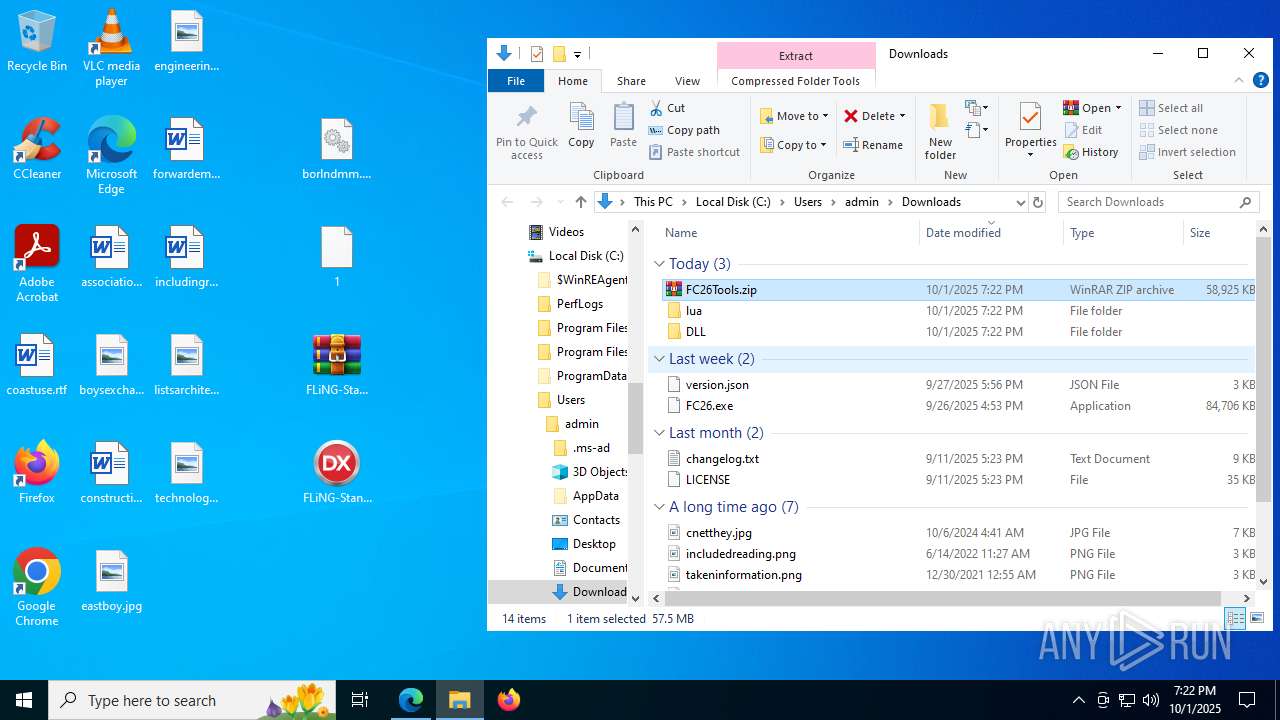
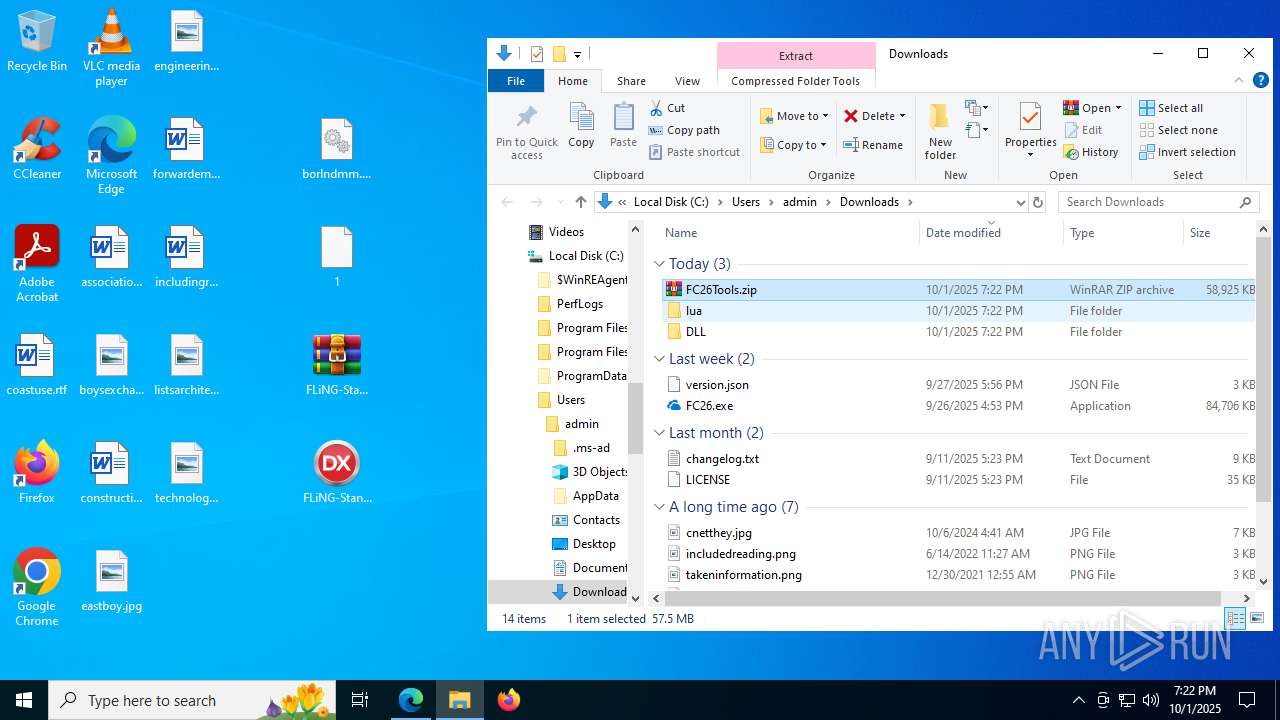
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7252)
Compiled with Borland Delphi (YARA)
- FLiNG-Standalone216.677.exe (PID: 5432)
- FLiNG-Standalone216.677.exe (PID: 7412)
- FLiNG-Standalone216.677.exe (PID: 8176)
- FLiNG-Standalone216.677.exe (PID: 4112)
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 5348)
Reads the software policy settings
- slui.exe (PID: 2596)
- WerFault.exe (PID: 1216)
- WerFault.exe (PID: 4460)
- WerFault.exe (PID: 4528)
- WerFault.exe (PID: 7224)
- WerFault.exe (PID: 2728)
Checks proxy server information
- WerFault.exe (PID: 1216)
- WerFault.exe (PID: 4460)
- slui.exe (PID: 2596)
- WerFault.exe (PID: 4528)
- WerFault.exe (PID: 7224)
- WerFault.exe (PID: 2728)
Creates files or folders in the user directory
- WerFault.exe (PID: 1216)
- WerFault.exe (PID: 4460)
- WerFault.exe (PID: 4528)
- WerFault.exe (PID: 7224)
- WerFault.exe (PID: 2728)
Process checks computer location settings
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FLiNG-Standalone216.677.exe (PID: 7688)
Reads the machine GUID from the registry
- FLiNG-Standalone216.677.exe (PID: 3976)
- FLiNG-Standalone216.677.exe (PID: 4380)
- FLiNG-Standalone216.677.exe (PID: 6676)
- FLiNG-Standalone216.677.exe (PID: 7688)
Reads product name
- FC26.exe (PID: 3656)
- FC26.exe (PID: 5904)
Reads CPU info
- FC26.exe (PID: 3656)
- FC26.exe (PID: 5904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
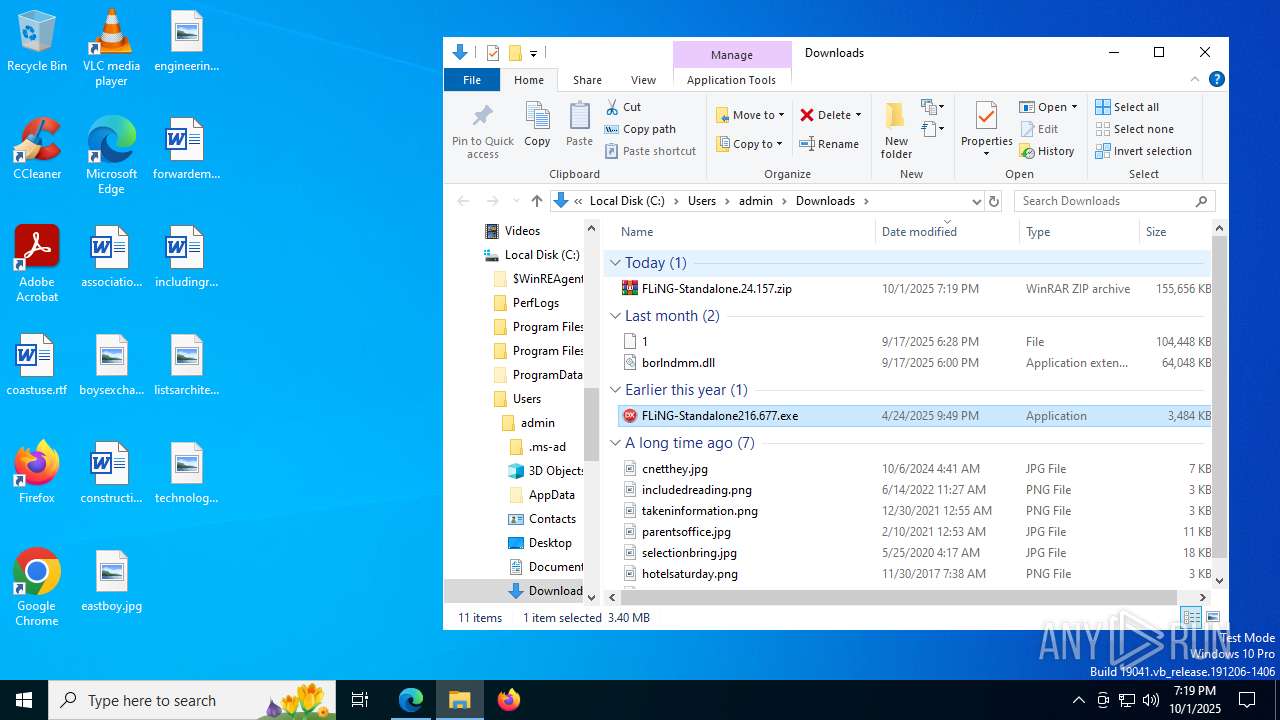
Total processes
313
Monitored processes
157
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | powershell.exe -NoProfile -NonInteractive -Command "Add-MpPreference -ExclusionPath 'C:\Users\'; Add-MpPreference -ExclusionPath 'C:\ProgramData\'; Add-MpPreference -ExclusionPath 'C:\Windows\'; Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | FC26.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | whoami /groups | C:\Windows\System32\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1592,i,755773914724307818,8116396062514142290,262144 --variations-seed-version --mojo-platform-channel-handle=3496 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | C:\WINDOWS\system32\cmd.exe /d /s /c "reg query "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v ConsentPromptBehaviorAdmin" | C:\Windows\System32\cmd.exe | — | FC26.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | C:\WINDOWS\system32\WerFault.exe -u -p 5432 -s 380 | C:\Windows\System32\WerFault.exe | FLiNG-Standalone216.677.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -NoProfile -Command "Get-WmiObject Win32_DiskDrive | Select-Object -ExpandProperty Model"" | C:\Windows\System32\cmd.exe | — | FC26.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1392 | powershell -NoProfile -Command "Get-WmiObject Win32_PortConnector | Measure-Object | Select-Object -ExpandProperty Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1624 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /F /IM SecHealthUI.exe" | C:\Windows\System32\cmd.exe | — | FC26.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 901
Read events
70 826
Write events
72
Delete events
3
Modification events
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5172) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (2288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
44
Suspicious files
888
Text files
277
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18dbf3.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18dc03.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18dc03.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18dc03.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18dc03.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18dc13.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
187
DNS requests
206
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6572 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:OSiEd0cpvWKcwVrVqWmjdostHcOmRsc3aOr364r808w&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 23.195.81.66:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
6956 | svchost.exe | GET | 200 | 23.38.59.250:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7352 | SIHClient.exe | GET | 200 | 2.20.170.89:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4024 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6572 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6572 | msedge.exe | 172.67.203.196:443 | flingtrainer.io | CLOUDFLARENET | US | unknown |
6572 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6572 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6572 | msedge.exe | 2.19.193.51:443 | copilot.microsoft.com | Akamai International B.V. | TR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
flingtrainer.io |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
fling-trainer.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
3976 | FLiNG-Standalone216.677.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3976 | FLiNG-Standalone216.677.exe | A Network Trojan was detected | ET MALWARE MonsterV2 Stealer CnC Checkin |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
— | — | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
— | — | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |