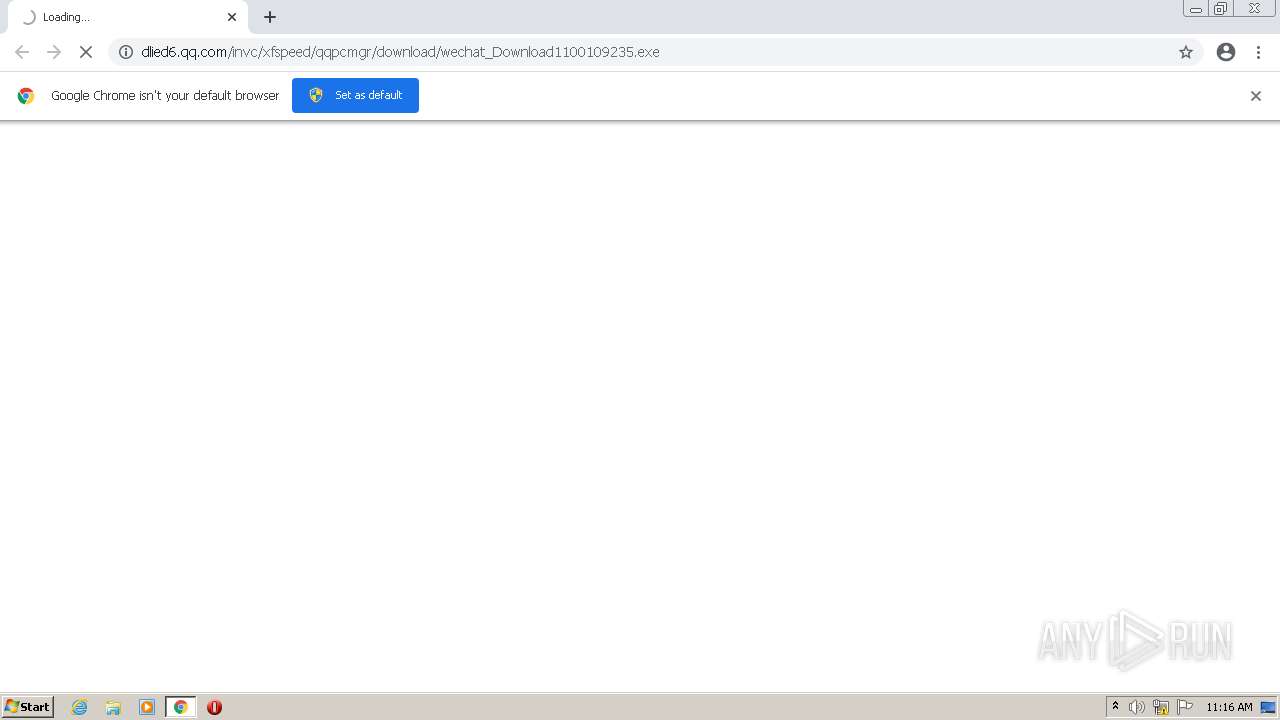
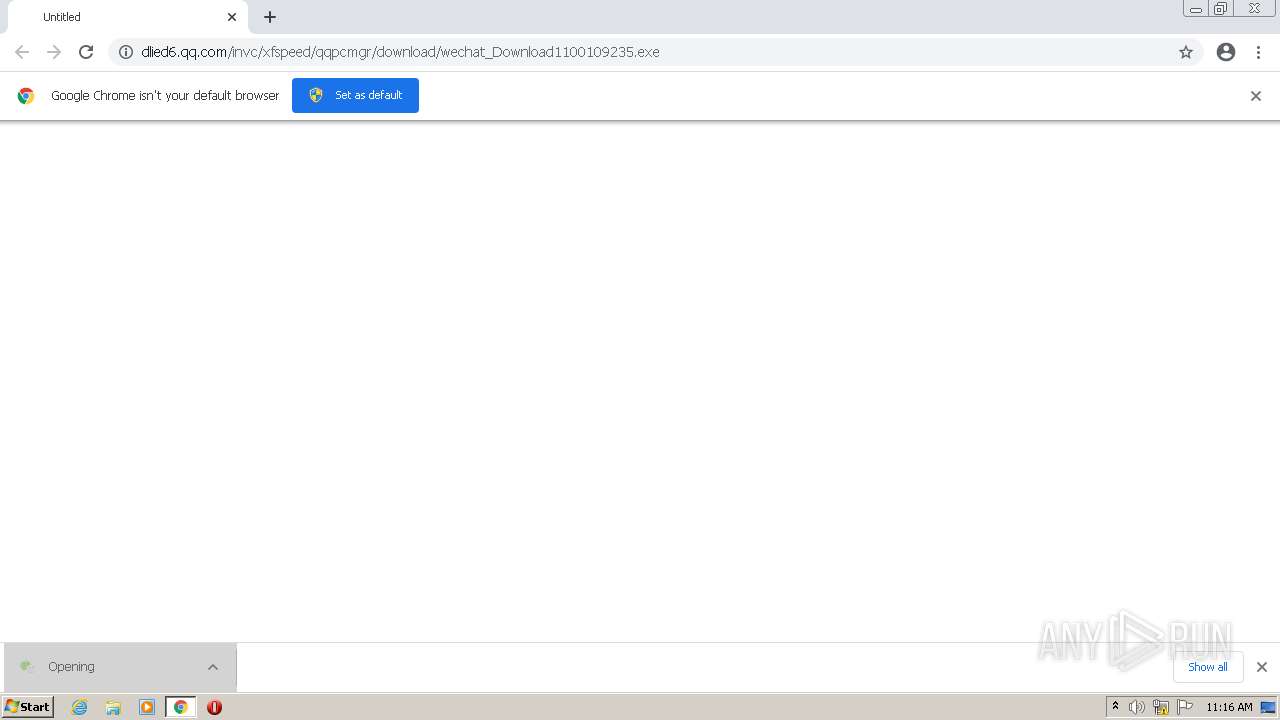
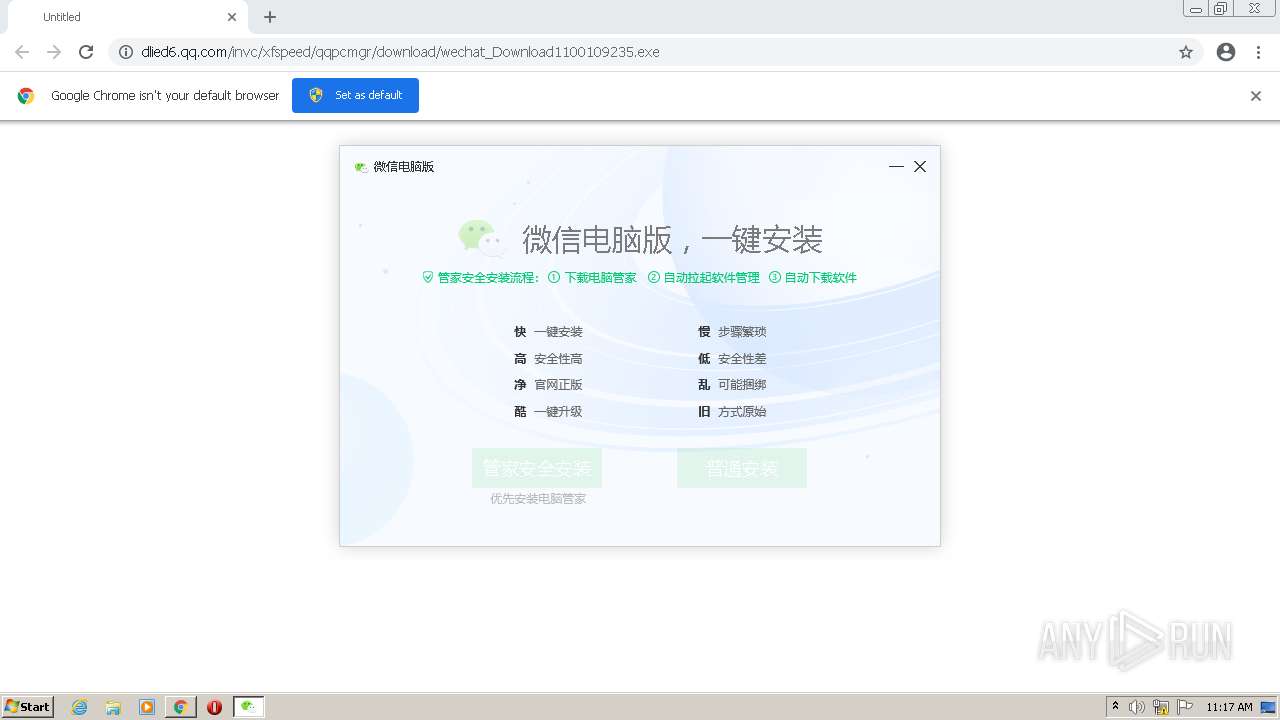
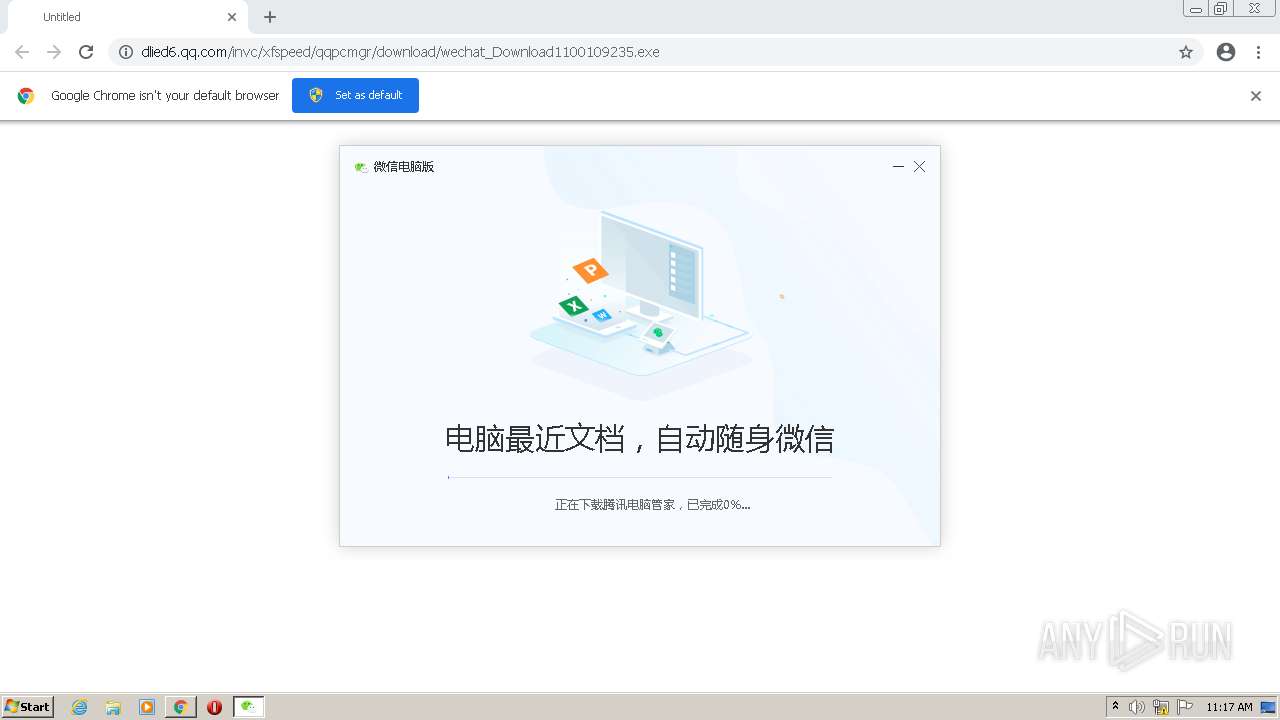
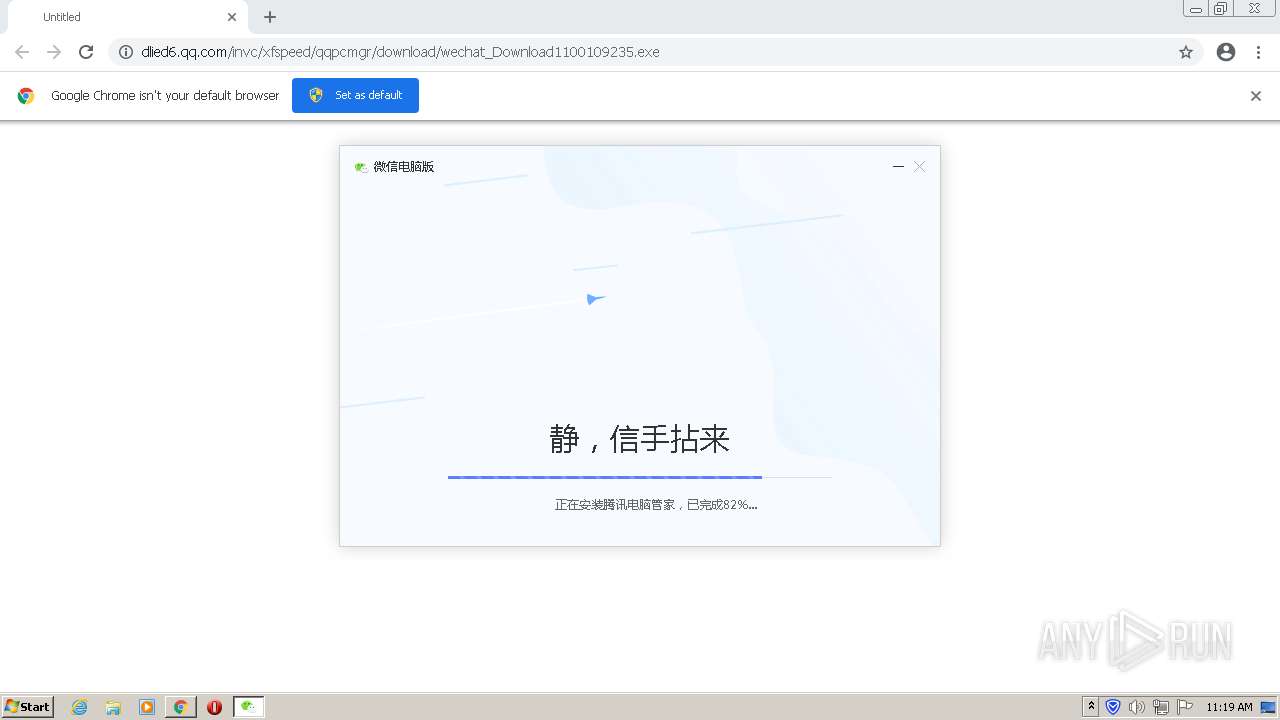
| URL: | https://dlied6.qq.com/invc/xfspeed/qqpcmgr/download/wechat_Download1100109235.exe |
| Full analysis: | https://app.any.run/tasks/653e79ef-a030-4a3a-b6c5-74e241508299 |
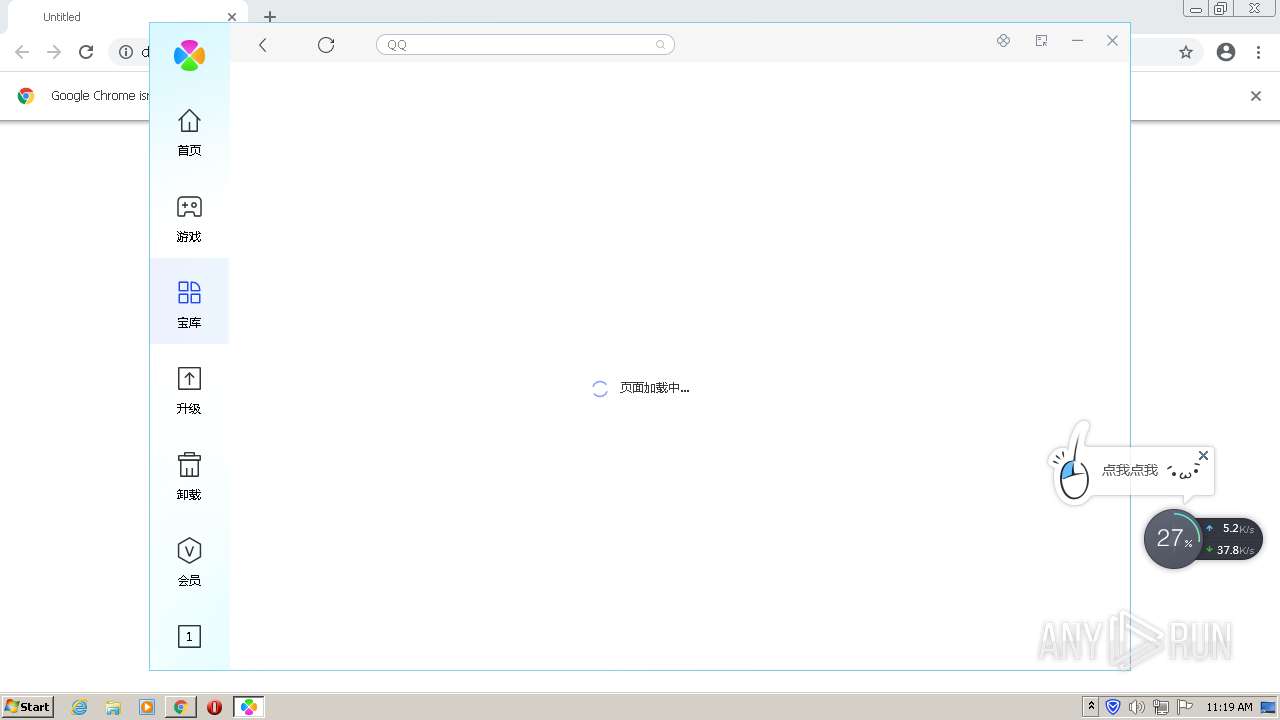
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2022, 11:16:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F99D6DBEF65464A7A5C05F3A0F906FC5 |
| SHA1: | 443139D3C65E05AD2EF6546554855E3DF94BFAF0 |
| SHA256: | 29405D9EB2B84035671A66996335B714CF468F821F1215A564954037FAE9AE3F |
| SSDEEP: | 3:N8RBBTL4K8dQbJEkjR6jZiUVVMk:27lLH8dCRRy3H |
MALICIOUS
Application was dropped or rewritten from another process
- wechat_Download1100109235.exe (PID: 2180)
- wechat_Download1100109235.exe (PID: 3612)
- QMBluerayInsHlp.exe (PID: 2176)
- QQPCSoftCmd.exe (PID: 4044)
- QQPCRTP.exe (PID: 4060)
- RemNPX.exe (PID: 2768)
- QMSuperScan.exe (PID: 3836)
- QMCheckNetwork.exe (PID: 2656)
- QMCheckNetwork.exe (PID: 2336)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCRTP.exe (PID: 3924)
- QQPCTray.exe (PID: 1512)
- QQPCRTP.exe (PID: 2492)
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
- UpdateTrayIcon.exe (PID: 2420)
- InstallUninstallCube.exe (PID: 3832)
- QMqbclientSetup_15_20_10058_201.exe (PID: 2244)
Drops executable file immediately after starts
- QQPCMgr_Setup.exe (PID: 1968)
- chrome.exe (PID: 3504)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCTray.exe (PID: 2176)
Loads dropped or rewritten executable
- QMBluerayInsHlp.exe (PID: 2176)
- regsvr32.exe (PID: 3900)
- QQPCSoftCmd.exe (PID: 4044)
- QQPCRTP.exe (PID: 4060)
- regsvr32.exe (PID: 416)
- regsvr32.exe (PID: 2444)
- regsvr32.exe (PID: 3416)
- QMSuperScan.exe (PID: 3836)
- QMCheckNetwork.exe (PID: 2656)
- QMCheckNetwork.exe (PID: 2336)
- QQPCTray.exe (PID: 1512)
- QQPCRTP.exe (PID: 2492)
- QQPCRTP.exe (PID: 3924)
- QQPCRtp.exe (PID: 3100)
- UpdateTrayIcon.exe (PID: 2420)
- QQPCTray.exe (PID: 2176)
- InstallUninstallCube.exe (PID: 3832)
- svchost.exe (PID: 860)
- QMExtraPackageSetup.exe (PID: 3076)
Registers / Runs the DLL via REGSVR32.EXE
- QQPCMgr_Setup.exe (PID: 1968)
Actions looks like stealing of personal data
- QQPCRtp.exe (PID: 3100)
- QQPCTray.exe (PID: 2176)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3504)
- QQPCMgr_Setup.exe (PID: 1968)
- QMExtraPackageSetup.exe (PID: 3076)
- wechat_Download1100109235.exe (PID: 3612)
- QQPCTray.exe (PID: 2176)
- QMqbclientSetup_15_20_10058_201.exe (PID: 2244)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3504)
- QQPCMgr_Setup.exe (PID: 1968)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCTray.exe (PID: 2176)
- QMqbclientSetup_15_20_10058_201.exe (PID: 2244)
Creates files in the user directory
- wechat_Download1100109235.exe (PID: 3612)
- QQPCMgr_Setup.exe (PID: 1968)
- QMSuperScan.exe (PID: 3836)
- UpdateTrayIcon.exe (PID: 2420)
- QQPCTray.exe (PID: 2176)
Reads the computer name
- wechat_Download1100109235.exe (PID: 3612)
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCSoftCmd.exe (PID: 4044)
- QQPCRTP.exe (PID: 4060)
- RemNPX.exe (PID: 2768)
- QMSuperScan.exe (PID: 3836)
- QMCheckNetwork.exe (PID: 2656)
- QMCheckNetwork.exe (PID: 2336)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCRTP.exe (PID: 2492)
- QQPCRTP.exe (PID: 3924)
- QQPCRtp.exe (PID: 3100)
- UpdateTrayIcon.exe (PID: 2420)
- InstallUninstallCube.exe (PID: 3832)
- QQPCTray.exe (PID: 2176)
- QMqbclientSetup_15_20_10058_201.exe (PID: 2244)
- VolSnapshot.exe (PID: 1044)
- QQPCRealTimeSpeedup.exe (PID: 2144)
Checks supported languages
- wechat_Download1100109235.exe (PID: 3612)
- QQPCMgr_Setup.exe (PID: 1968)
- QMBluerayInsHlp.exe (PID: 2176)
- QQPCSoftCmd.exe (PID: 4044)
- QQPCRTP.exe (PID: 4060)
- RemNPX.exe (PID: 2768)
- QMSuperScan.exe (PID: 3836)
- QMCheckNetwork.exe (PID: 2656)
- QMCheckNetwork.exe (PID: 2336)
- QQPCRTP.exe (PID: 2492)
- QQPCTray.exe (PID: 1512)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCRTP.exe (PID: 3924)
- QQPCRtp.exe (PID: 3100)
- UpdateTrayIcon.exe (PID: 2420)
- QQPCTray.exe (PID: 2176)
- InstallUninstallCube.exe (PID: 3832)
- QMqbclientSetup_15_20_10058_201.exe (PID: 2244)
- VolSnapshot.exe (PID: 1044)
- QQPCRealTimeSpeedup.exe (PID: 2144)
Drops a file with too old compile date
- QQPCMgr_Setup.exe (PID: 1968)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCTray.exe (PID: 2176)
Creates a directory in Program Files
- QQPCMgr_Setup.exe (PID: 1968)
- wechat_Download1100109235.exe (PID: 3612)
- QQPCRtp.exe (PID: 3100)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCTray.exe (PID: 2176)
Searches for installed software
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
Creates files in the program directory
- wechat_Download1100109235.exe (PID: 3612)
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCRTP.exe (PID: 4060)
- QMSuperScan.exe (PID: 3836)
- QQPCTray.exe (PID: 1512)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCRtp.exe (PID: 3100)
- InstallUninstallCube.exe (PID: 3832)
- QQPCTray.exe (PID: 2176)
- QQPCRealTimeSpeedup.exe (PID: 2144)
Changes default file association
- QQPCMgr_Setup.exe (PID: 1968)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3900)
- regsvr32.exe (PID: 416)
- regsvr32.exe (PID: 3416)
- regsvr32.exe (PID: 2444)
Drops a file with a compile date too recent
- QQPCMgr_Setup.exe (PID: 1968)
- QMExtraPackageSetup.exe (PID: 3076)
- QQPCTray.exe (PID: 2176)
Creates a software uninstall entry
- QQPCMgr_Setup.exe (PID: 1968)
Creates files in the Windows directory
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCRtp.exe (PID: 3100)
- QQPCTray.exe (PID: 2176)
Creates files in the driver directory
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCTray.exe (PID: 2176)
Uses NETSH.EXE for network configuration
- QQPCMgr_Setup.exe (PID: 1968)
Reads Environment values
- Netsh.exe (PID: 2480)
Creates or modifies windows services
- QQPCMgr_Setup.exe (PID: 1968)
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
Reads the date of Windows installation
- RemNPX.exe (PID: 2768)
- UpdateTrayIcon.exe (PID: 2420)
- QQPCTray.exe (PID: 2176)
Uses REG.EXE to modify Windows registry
- regsvr32.exe (PID: 416)
Application launched itself
- QMCheckNetwork.exe (PID: 2656)
Executed as Windows Service
- QQPCRtp.exe (PID: 3100)
- vssvc.exe (PID: 3244)
Checks Windows language
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
Reads Microsoft Outlook installation path
- QQPCRealTimeSpeedup.exe (PID: 2144)
INFO
Reads the computer name
- chrome.exe (PID: 2160)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3552)
- cacls.exe (PID: 4044)
- Netsh.exe (PID: 2480)
- vssvc.exe (PID: 3244)
Checks supported languages
- chrome.exe (PID: 3444)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 1364)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 2760)
- svchost.exe (PID: 860)
- chrome.exe (PID: 992)
- chrome.exe (PID: 3552)
- cacls.exe (PID: 4044)
- chrome.exe (PID: 3504)
- regsvr32.exe (PID: 3900)
- chrome.exe (PID: 1120)
- chrome.exe (PID: 3648)
- Netsh.exe (PID: 2480)
- regsvr32.exe (PID: 416)
- regsvr32.exe (PID: 2444)
- regsvr32.exe (PID: 3416)
- reg.exe (PID: 1144)
- reg.exe (PID: 1764)
- reg.exe (PID: 3724)
- reg.exe (PID: 2228)
- reg.exe (PID: 3716)
- reg.exe (PID: 3048)
- reg.exe (PID: 4080)
- reg.exe (PID: 3256)
- chrome.exe (PID: 592)
- vssvc.exe (PID: 3244)
Application launched itself
- chrome.exe (PID: 2160)
Reads the hosts file
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3560)
Reads settings of System Certificates
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2160)
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
Checks Windows Trust Settings
- chrome.exe (PID: 2160)
- QQPCTray.exe (PID: 2176)
- QQPCRtp.exe (PID: 3100)
Reads the date of Windows installation
- chrome.exe (PID: 3008)
Dropped object may contain Bitcoin addresses
- QQPCMgr_Setup.exe (PID: 1968)
- QMExtraPackageSetup.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
62
Malicious processes
21
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Tencent\QQPCMgr\15.3.22652.301\npQMExtensionsIE.dll" | C:\Windows\system32\regsvr32.exe | — | QQPCMgr_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Tencent\QQPCMgr\15.3.22652.301\VolSnapshot.exe" 00000003000000010501010000000000000205010000000000000003050150000000 | C:\Program Files\Tencent\QQPCMgr\15.3.22652.301\VolSnapshot.exe | QQPCRtp.exe | ||||||||||||
User: SYSTEM Company: Tencent Integrity Level: SYSTEM Description: ???? Exit code: 0 Version: 15.3.22652.301 | |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1144 | reg delete "hkcr\CLSID\{29B6CFD5-0064-411A-8C42-9890C83F9922}" /f | C:\Windows\system32\reg.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Tencent\QQPCMgr\15.3.22652.301\QQPCTxtExt.exe" | C:\Program Files\Tencent\QQPCMgr\15.3.22652.301\QQPCTxtExt.exe | — | QQPCSoftMgr.exe | |||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: ??????-TxT?? Exit code: 0 Version: 15.3.22652.301 | |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1052,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3320 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,6310239344549221109,16280871944150092008,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2664 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
29 384
Read events
28 272
Write events
1 093
Delete events
19
Modification events
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
602
Suspicious files
351
Text files
441
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61F27F15-870.pma | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a077e609-cd81-481f-b7de-f4305804d14c.tmp | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF113238.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF113248.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF113371.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3444 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
145
DNS requests
132
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3612 | wechat_Download1100109235.exe | GET | — | 203.205.137.72:80 | http://dlied6.qq.com/invc/xfspeed/qqpcmgr/versetup/portal/portal/PCMgr_Setup_15_3_22652_301.exe | CN | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
3612 | wechat_Download1100109235.exe | GET | 200 | 203.205.253.140:80 | http://c.gj.qq.com/packconfig?serviceid=2230&clientver=1000&gjguid=b07fdbb6a82ee52f5df1f8e62b476643&check=6364593&livetime=0 | CN | binary | 1.28 Kb | suspicious |
3612 | wechat_Download1100109235.exe | GET | 206 | 203.205.137.72:80 | http://dlied6.qq.com/invc/xfspeed/qqpcmgr/versetup/portal/portal/PCMgr_Setup_15_3_22652_301.exe | CN | binary | 12.5 Mb | whitelisted |
3612 | wechat_Download1100109235.exe | GET | 200 | 203.205.253.140:80 | http://c.gj.qq.com/fcgi-bin/downurlquery?id=1100109235&guid=QN2U1b7Dzh4Vs2FVXlUssrOjQg4cfuONh3tWObctm28wp8gT3sWzzGrBIfjc6x7h&ver=15.0.20505.201 | CN | text | 984 b | suspicious |
3612 | wechat_Download1100109235.exe | GET | 206 | 203.205.137.72:80 | http://dlied6.qq.com/invc/xfspeed/qqpcmgr/versetup/portal/portal/PCMgr_Setup_15_3_22652_301.exe | CN | binary | 12.5 Mb | whitelisted |
3612 | wechat_Download1100109235.exe | GET | 206 | 203.205.137.72:80 | http://dlied6.qq.com/invc/xfspeed/qqpcmgr/versetup/portal/portal/PCMgr_Setup_15_3_22652_301.exe | CN | binary | 12.5 Mb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 20.0 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 20.0 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3560 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3560 | chrome.exe | 203.205.137.72:443 | dlied6.qq.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
3560 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3560 | chrome.exe | 142.250.185.67:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3612 | wechat_Download1100109235.exe | 203.205.137.72:80 | dlied6.qq.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
1968 | QQPCMgr_Setup.exe | 58.251.106.185:443 | master.etl.desktop.qq.com | China Unicom Guangdong IP network | CN | malicious |
860 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
3836 | QMSuperScan.exe | 203.205.254.111:36688 | connc.gj.qq.com | — | CN | malicious |
3836 | QMSuperScan.exe | 203.205.239.243:80 | conna.gj.qq.com | — | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
dlied6.qq.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
c.gj.qq.com |
| unknown |
master.etl.desktop.qq.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3612 | wechat_Download1100109235.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1968 | QQPCMgr_Setup.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
1968 | QQPCMgr_Setup.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1968 | QQPCMgr_Setup.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3612 | wechat_Download1100109235.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3612 | wechat_Download1100109235.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3612 | wechat_Download1100109235.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
— | — | Potential Corporate Privacy Violation | ET POLICY QQ Browser WUP Request - qbpcstatf.stat |
Process | Message |
|---|---|
QQPCMgr_Setup.exe | "cacls" "C:\Program Files\Tencent\QQPCMgr\15.3.22652.301" /t /e /c /g SYSTEM:f |
QQPCSoftCmd.exe |
=========== mem dump after here is valid ========
|
QQPCMgr_Setup.exe | CreateService |
QQPCMgr_Setup.exe | 0 |
QQPCMgr_Setup.exe | StartService |
QQPCMgr_Setup.exe | 0 |
QQPCMgr_Setup.exe | CreateService |
QQPCMgr_Setup.exe | 0 |
QQPCMgr_Setup.exe | StartService |
QQPCMgr_Setup.exe | 0 |