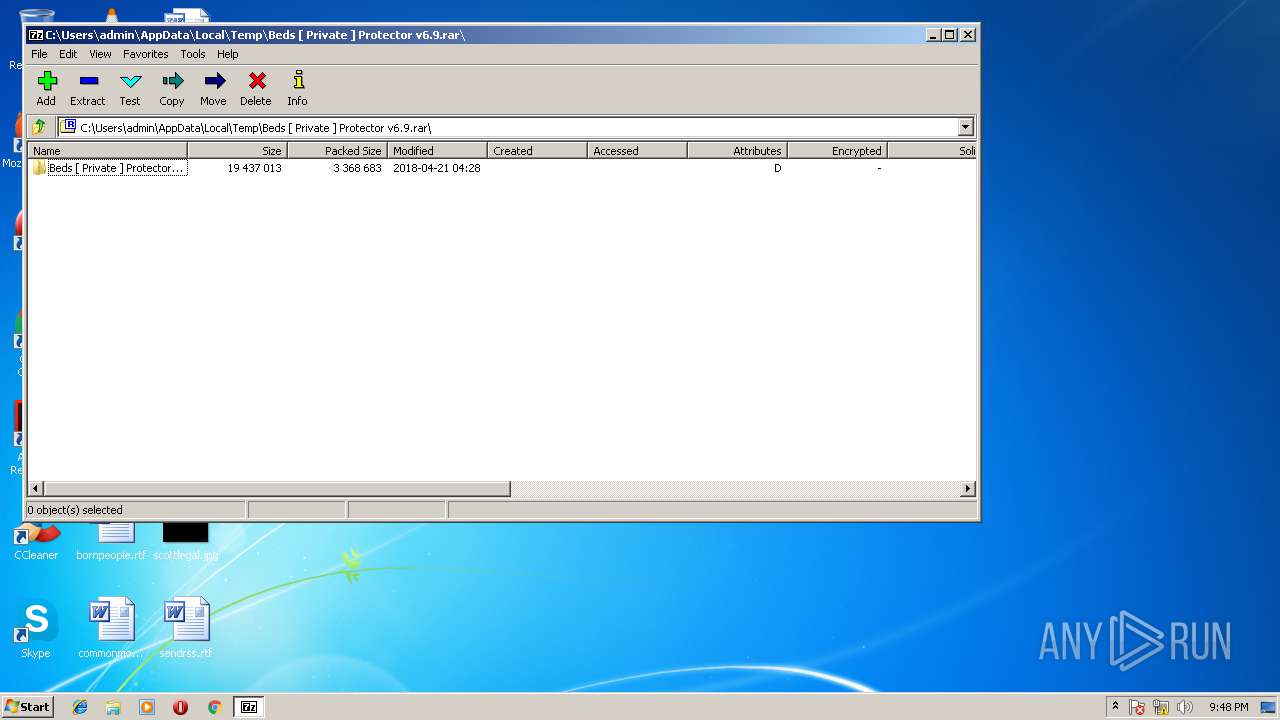
| File name: | Beds [ Private ] Protector v6.9.rar |
| Full analysis: | https://app.any.run/tasks/e76ce33a-862c-49f7-af9c-67518497259a |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2018, 20:47:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 98AE9D8A39C88E42565C7CC7ADE850DB |
| SHA1: | DD6BE4975C76CBA7AE48CEAD7A496C9F5E67BFF6 |
| SHA256: | 293C39348B1F0AFDDAE5043194868B5A154C1FAFED8E6701E68C3B045C899DA8 |
| SSDEEP: | 49152:L/rQcG4UwYjap1E0p9xsPUzu10ibAWt/81wMIEz90K3pYft9Ir+eK3:DUc89CZD5ultqwMTz90K3paterO |
MALICIOUS
Application loaded dropped or rewritten executable
- SearchProtocolHost.exe (PID: 788)
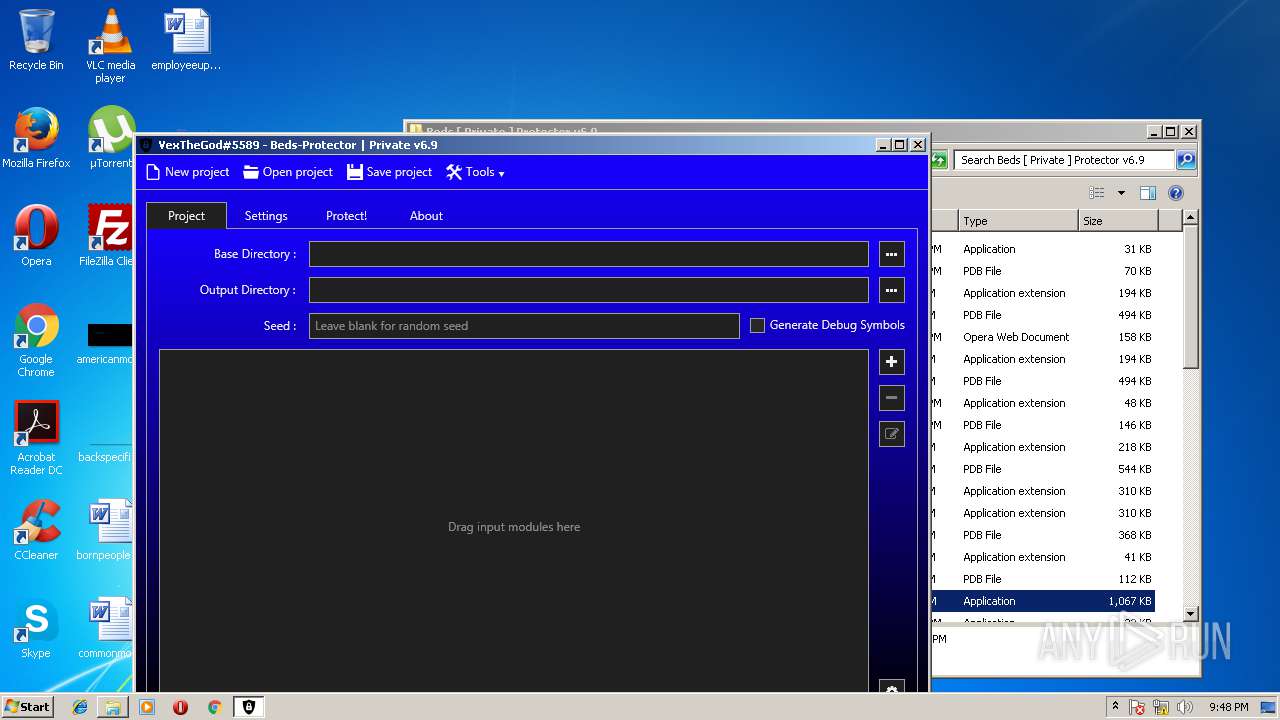
- ConfuserEx.exe (PID: 2700)
Application was dropped or rewritten from another process
- ConfuserEx.exe (PID: 2700)
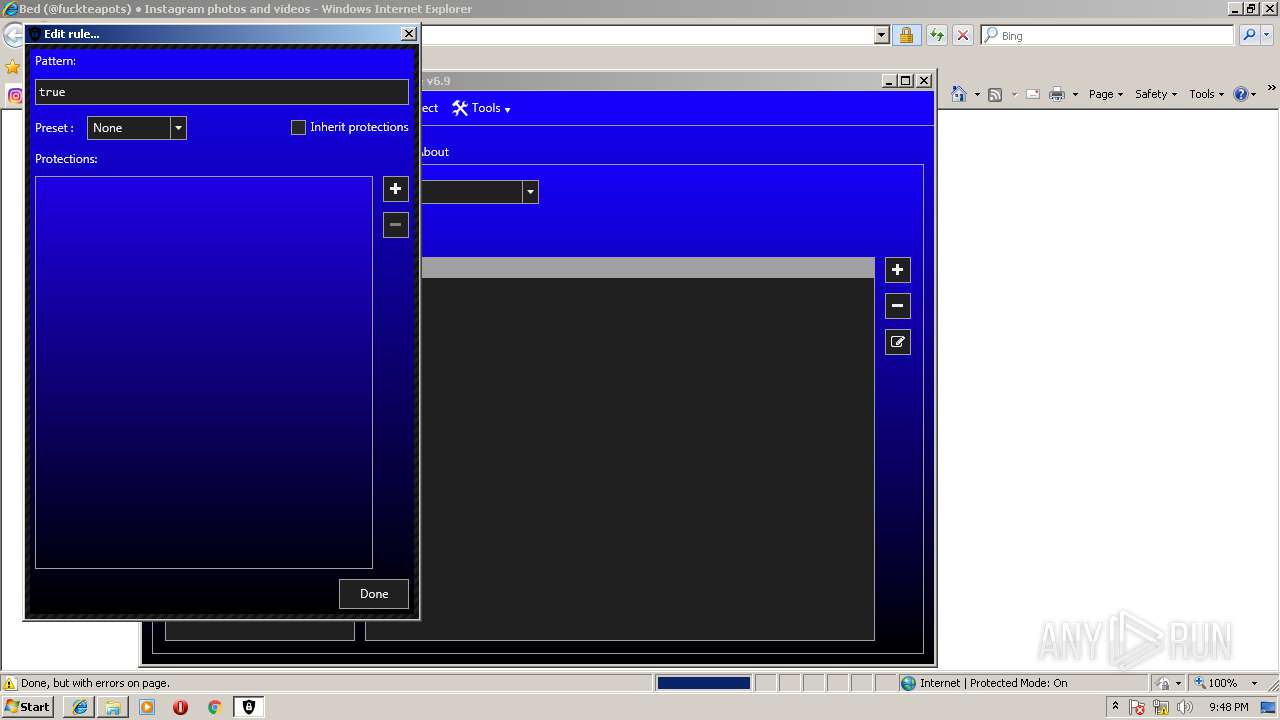
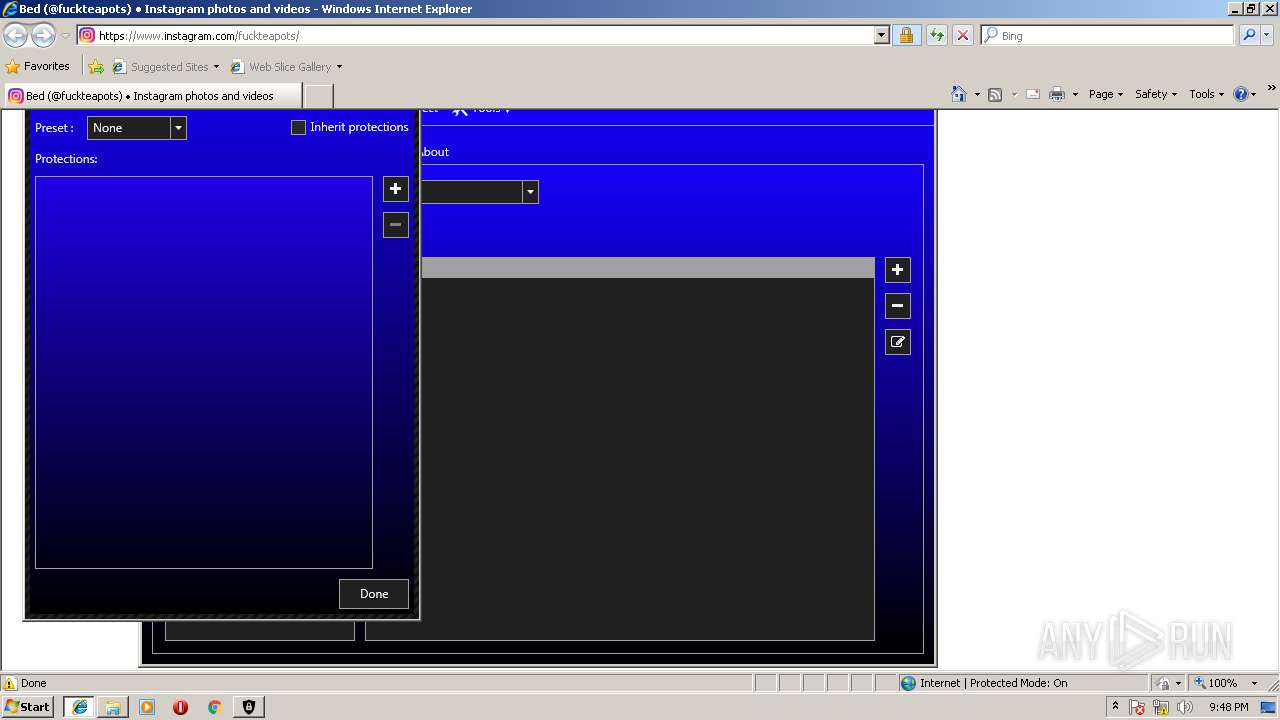
SUSPICIOUS
Starts Internet Explorer
- ConfuserEx.exe (PID: 2700)
INFO
Dropped object may contain URL's
- 7zFM.exe (PID: 3384)
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 1004)
Loads the .NET runtime environment
- ConfuserEx.exe (PID: 2700)
Changes internet zones settings
- iexplore.exe (PID: 1004)
Application launched itself
- iexplore.exe (PID: 1004)
Reads Internet Cache Settings
- iexplore.exe (PID: 2532)
Creates files in the user directory
- iexplore.exe (PID: 2532)
Reads internet explorer settings
- iexplore.exe (PID: 2532)
Reads settings of System Certificates
- iexplore.exe (PID: 1004)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1004)
Changes settings of System certificates
- iexplore.exe (PID: 1004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 13867 |
|---|---|
| UncompressedSize: | 31232 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2017:07:11 23:45:19 |
| PackingMethod: | Normal |
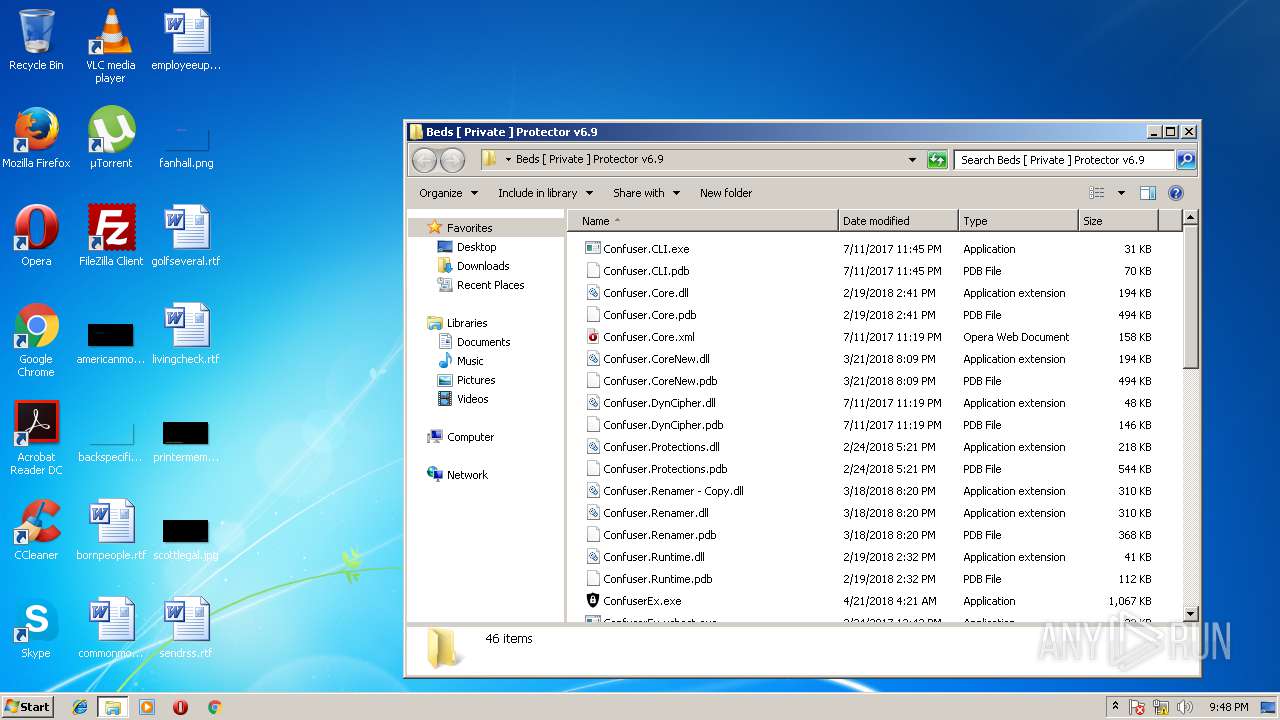
| ArchivedFileName: | Beds [ Private ] Protector v6.9\Confuser.CLI.exe |
Total processes
35
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | ConfuserEx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1004 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
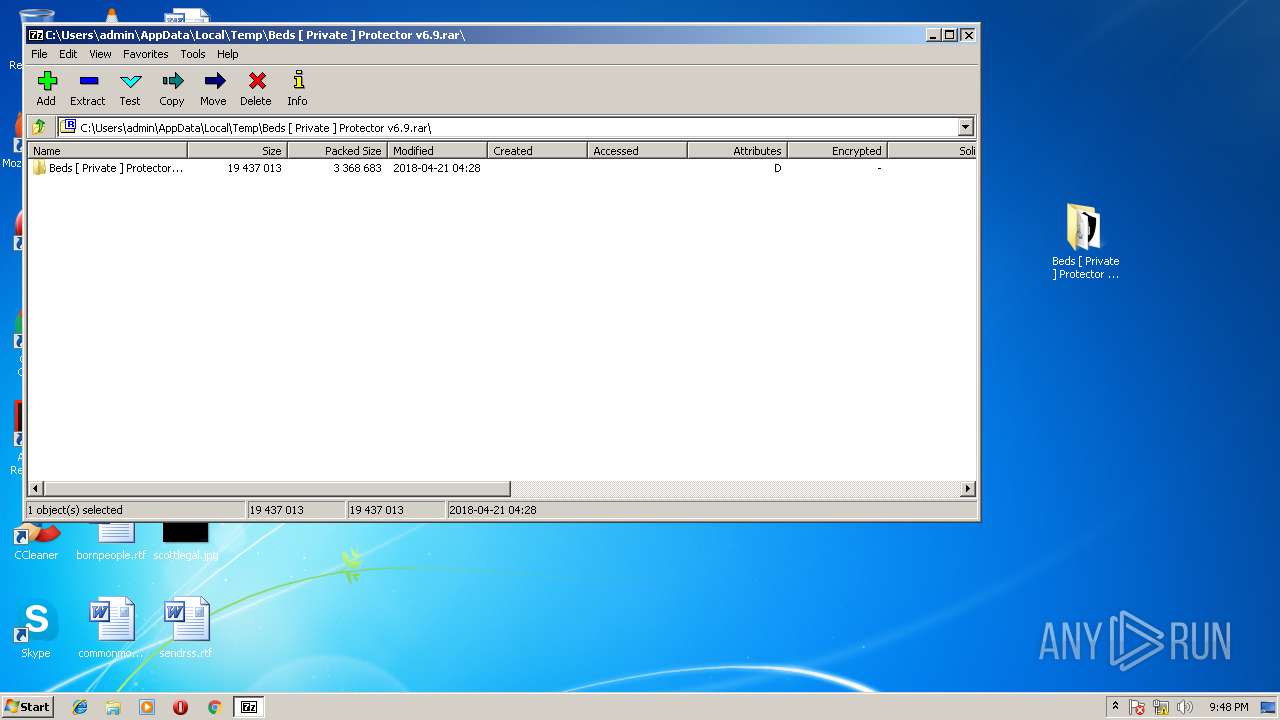
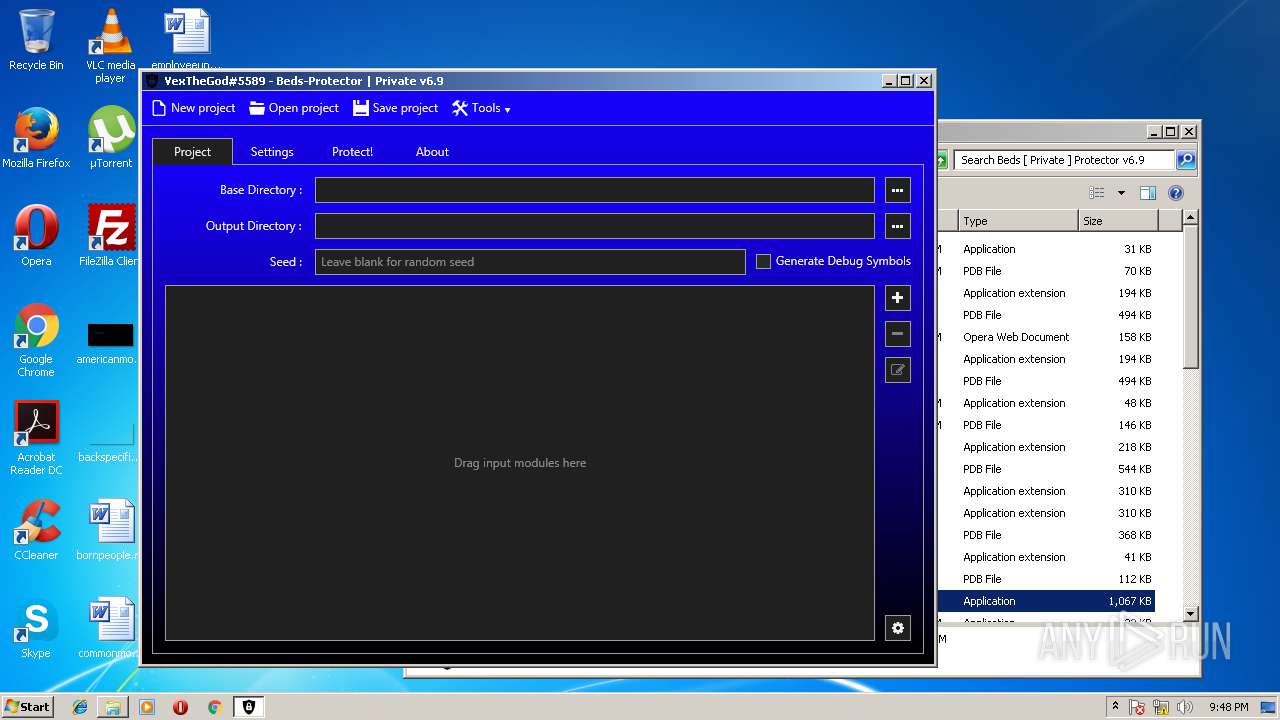
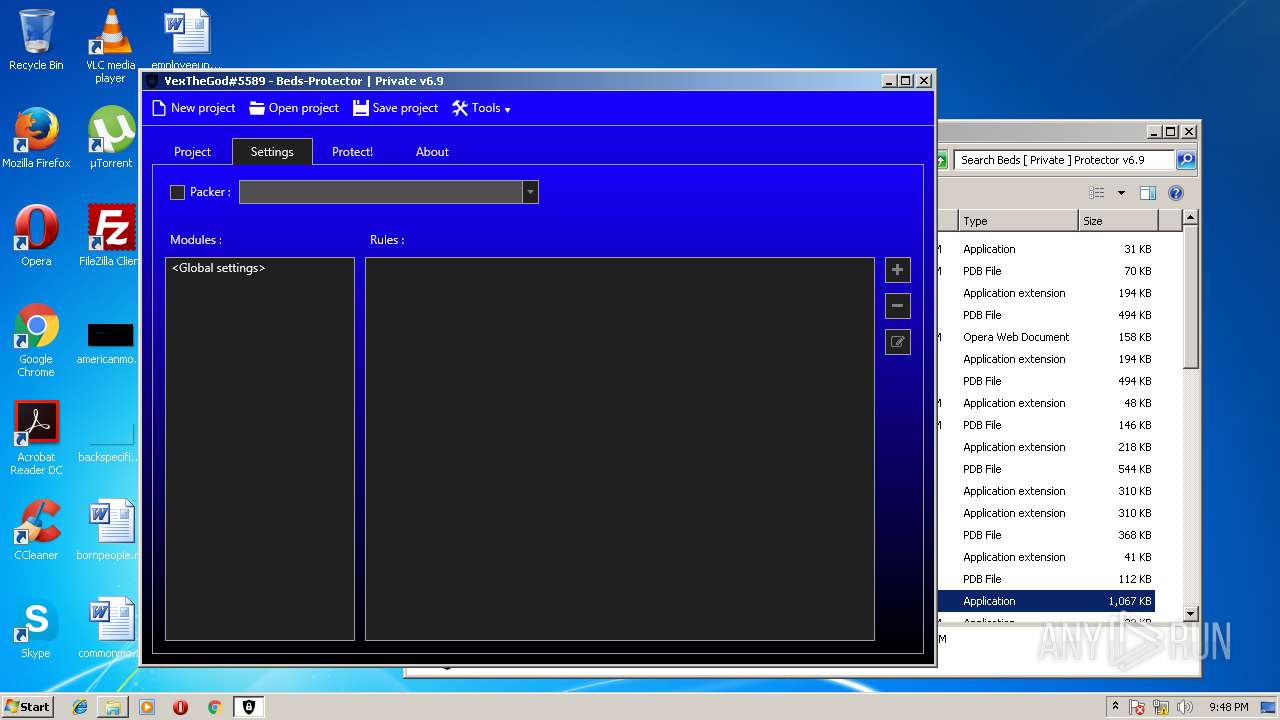
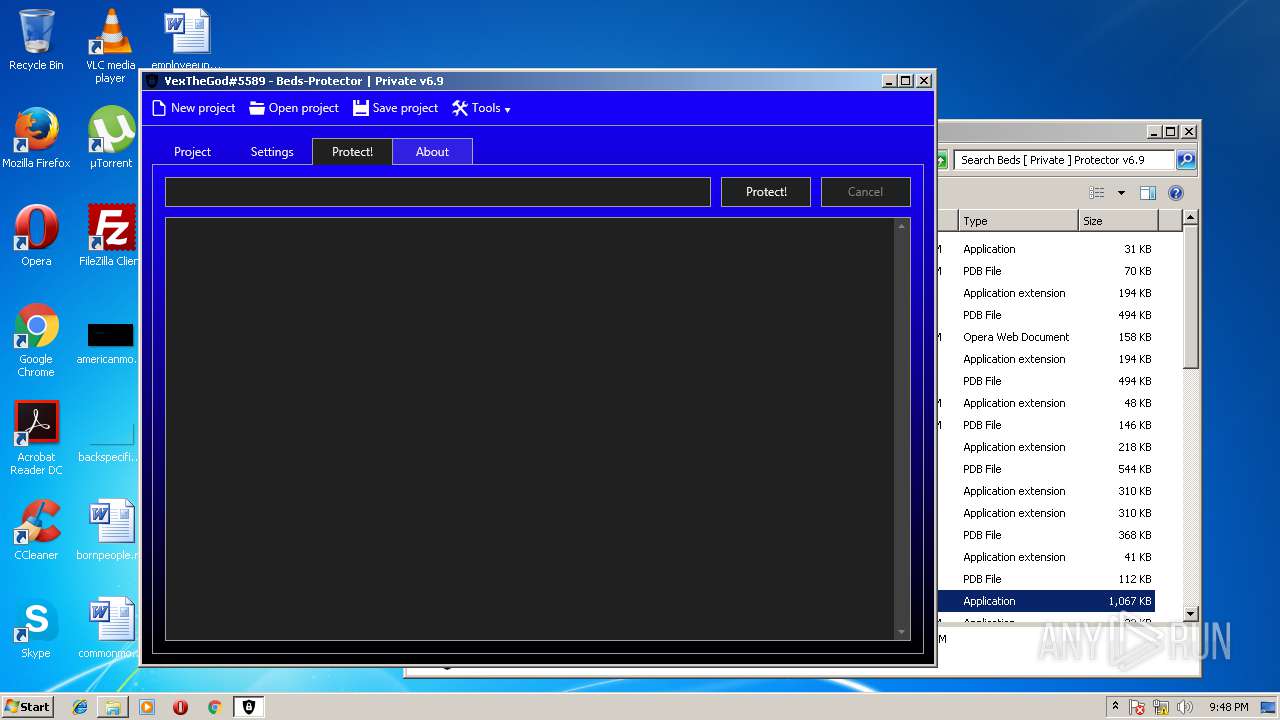
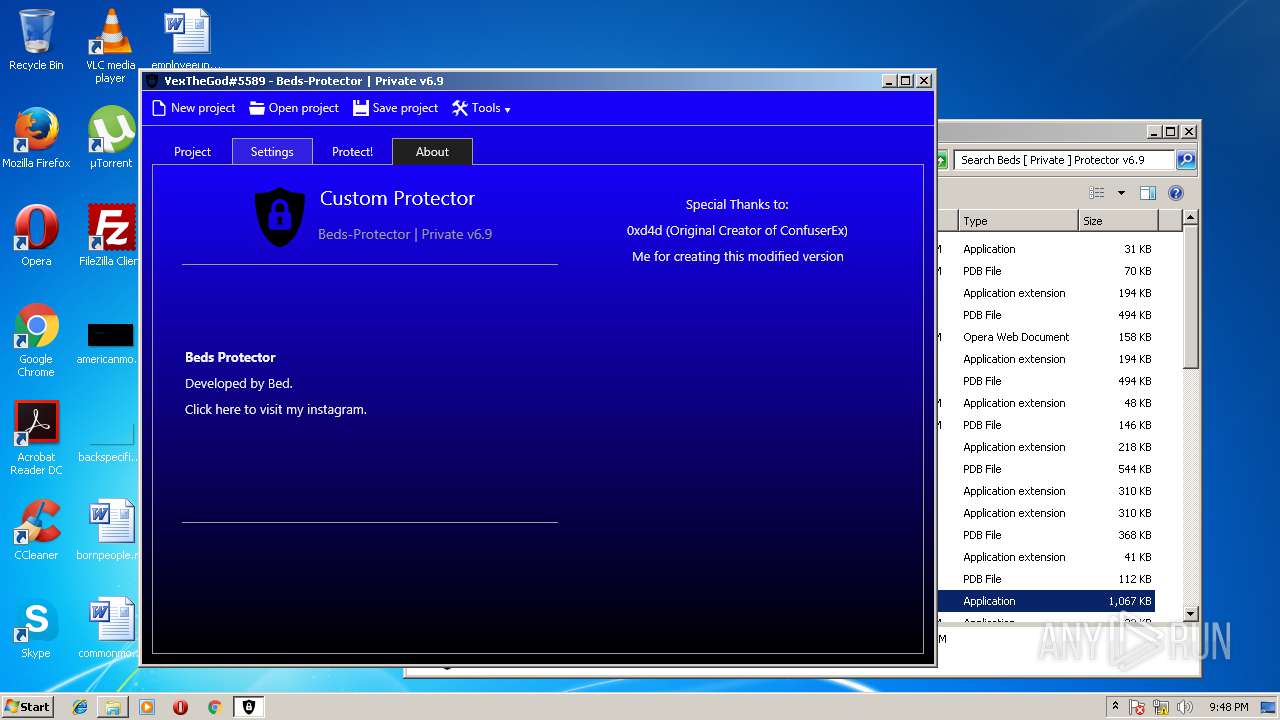
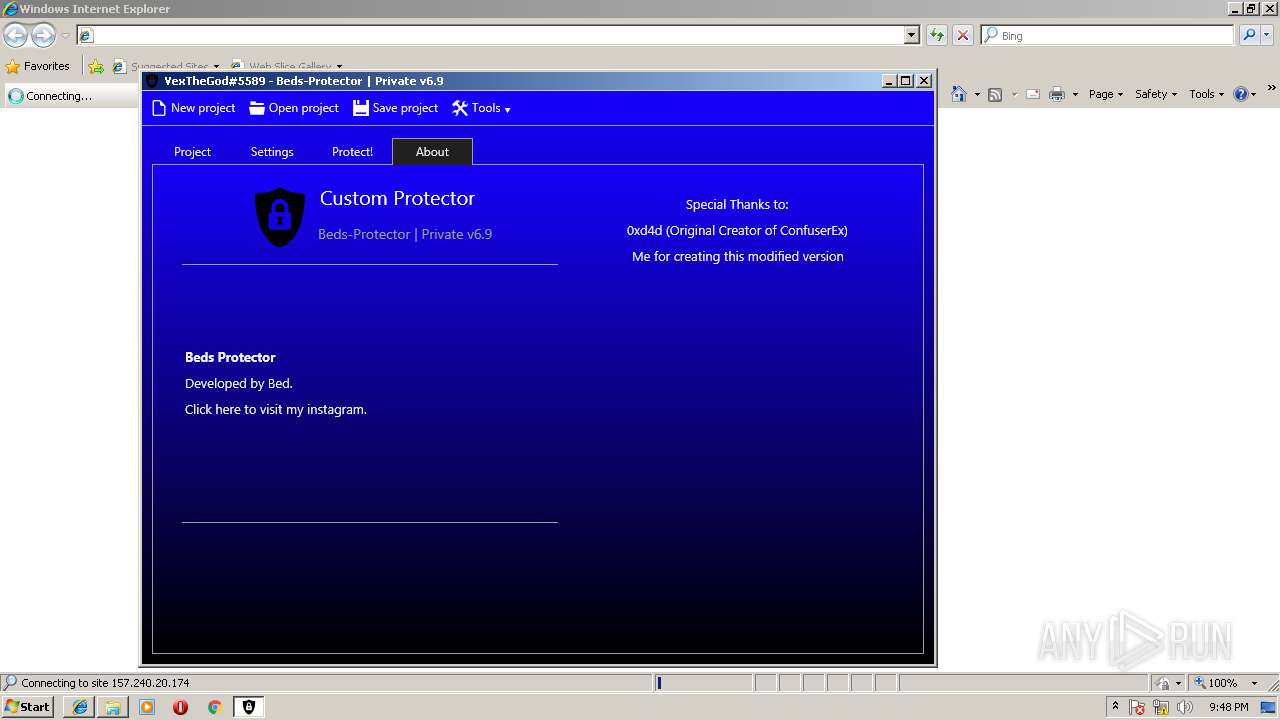
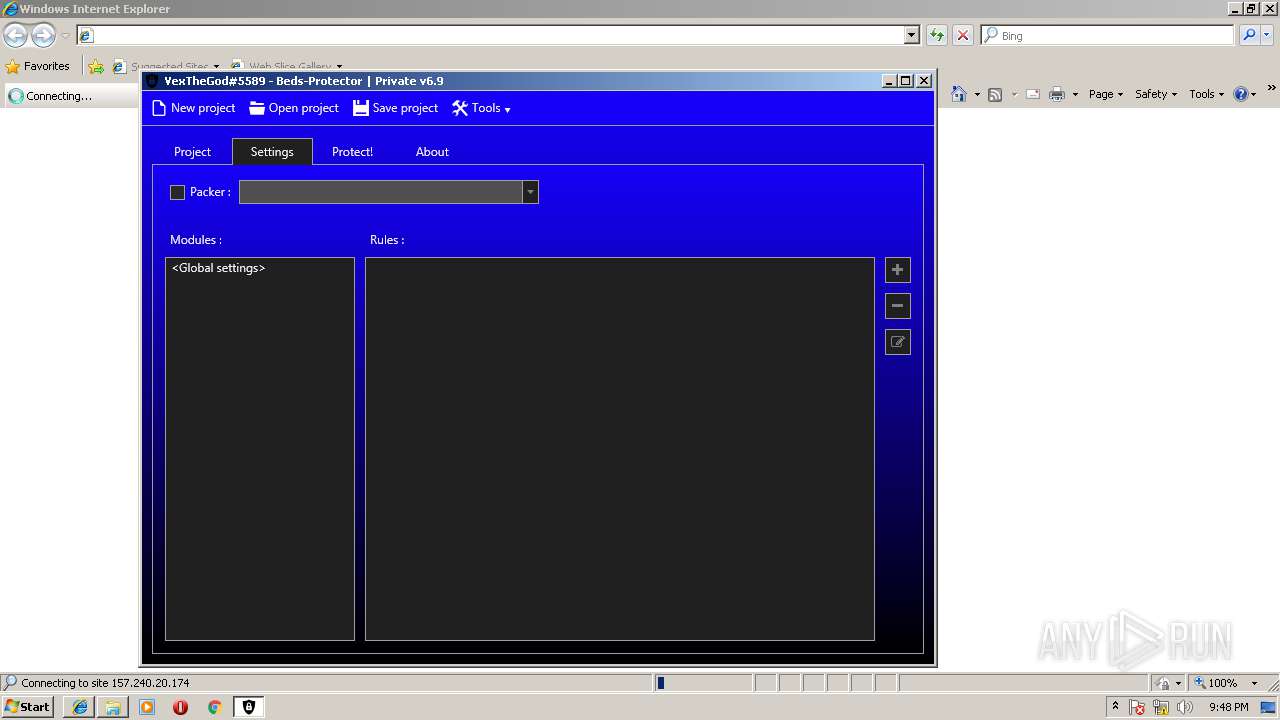
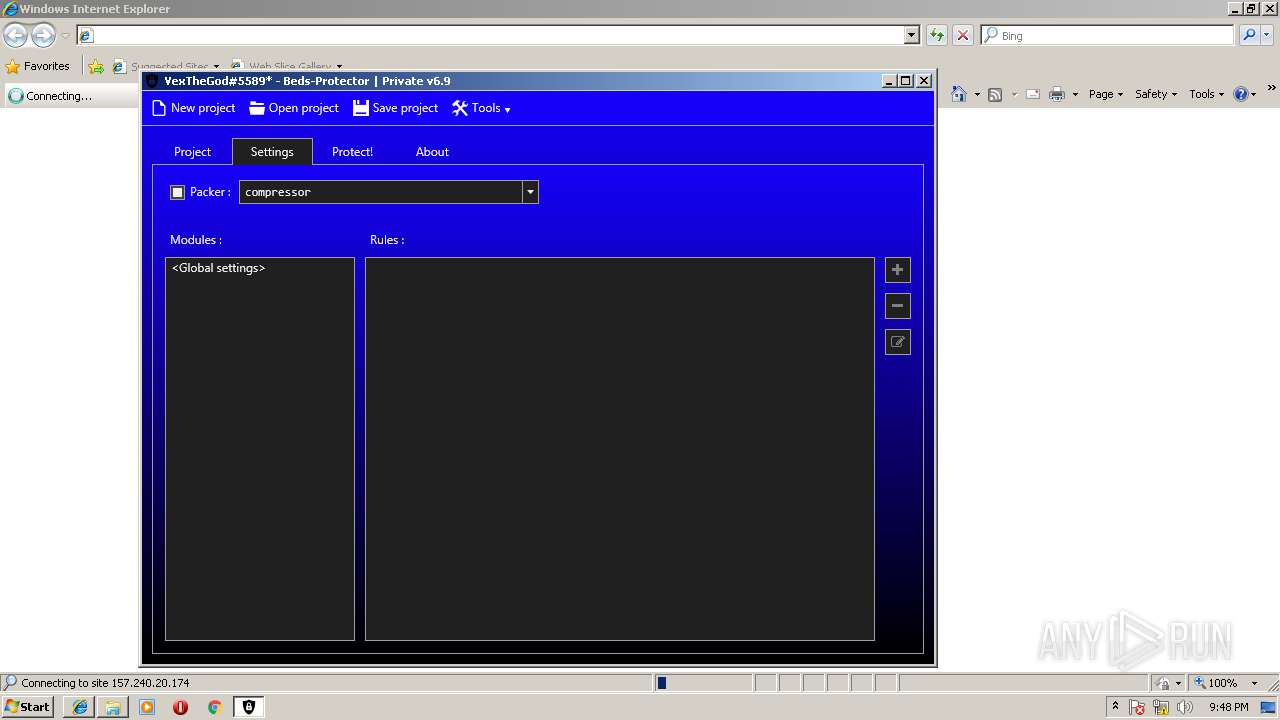
| 2700 | "C:\Users\admin\Desktop\Beds [ Private ] Protector v6.9\ConfuserEx.exe" | C:\Users\admin\Desktop\Beds [ Private ] Protector v6.9\ConfuserEx.exe | — | explorer.exe | |||||||||||
User: admin Company: Bed Integrity Level: MEDIUM Description: ConfuserEx Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\Beds [ Private ] Protector v6.9.rar" | C:\Program Files\7-Zip\7zFM.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
Total events
843
Read events
733
Write events
108
Delete events
2
Modification events
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderShortcuts |
Value: | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderHistory |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00420065006400730020005B002000500072006900760061007400650020005D002000500072006F0074006500630074006F0072002000760036002E0039002E007200610072005C000000 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath0 |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc0 |
Value: 0 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath1 |
Value: | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc1 |
Value: 0 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | ListMode |
Value: 771 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Position |
Value: 1600000016000000D60300000B02000000000000 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Panels |
Value: 0100000000000000DA010000 | |||
| (PID) Process: | (3384) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM\Columns |
| Operation: | write | Name: | 7-Zip.Rar |
Value: 0100000004000000010000000400000001000000A00000000700000001000000640000000800000001000000640000000C00000001000000640000000A00000001000000640000000B00000001000000640000000900000001000000640000000F00000001000000640000000D00000001000000640000000E00000001000000640000001000000001000000640000001100000001000000640000001300000001000000640000001700000001000000640000001600000001000000640000002100000001000000640000001F0000000100000064000000200000000100000064000000 | |||
Executable files
10
Suspicious files
7
Text files
11
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\dnlib.dll | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\dnlib.dll.CodeAnalysisLog.xml | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\dnlib.pdb | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\dnlib.xml | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.Extras.WPF4.dll | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.Extras.WPF4.pdb | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.Extras.WPF4.xml | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.WPF4.dll | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.WPF4.pdb | — | |
MD5:— | SHA256:— | |||
| 3384 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE83DB8F61\Beds [ Private ] Protector v6.9\GalaSoft.MvvmLight.WPF4.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAdlEAnRDanldTvliVr8hq8%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 157.240.20.174:443 | www.instagram.com | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.instagram.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |