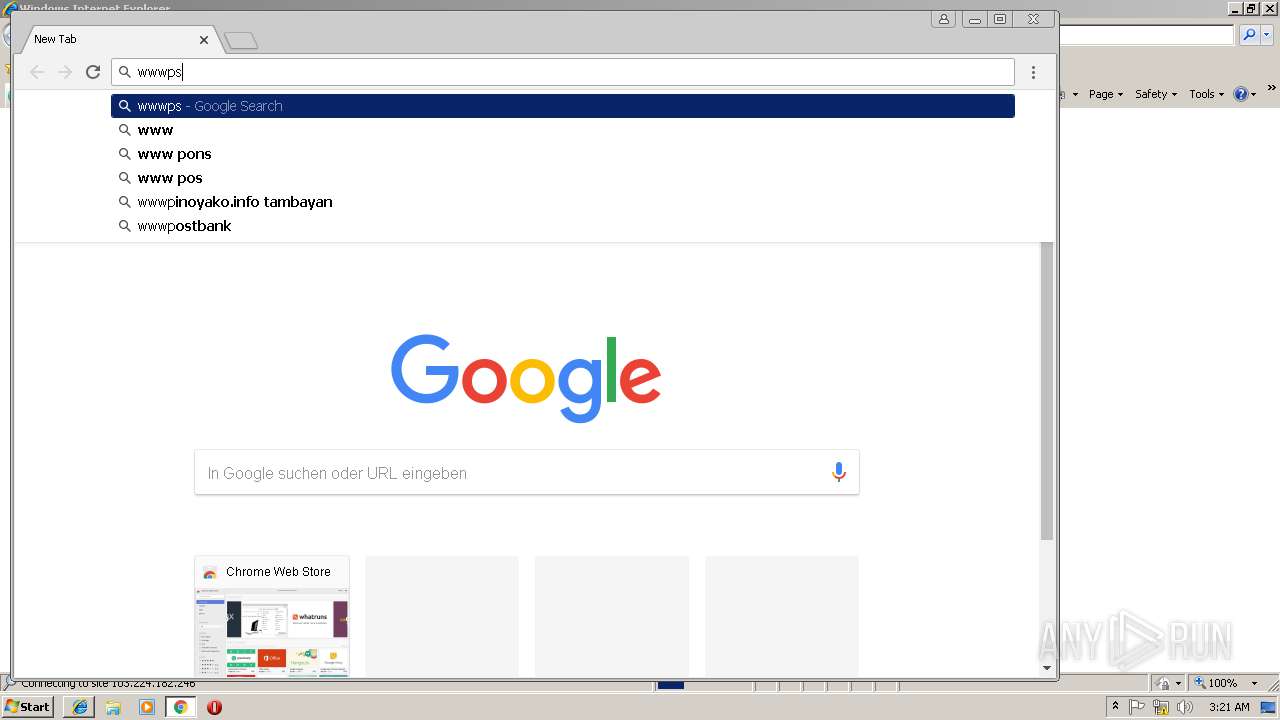
| URL: | https://wwwpsecu.com |
| Full analysis: | https://app.any.run/tasks/c62d0fb5-aa74-4cae-927c-312cc8049447 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 03:19:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CC2C42AEEF9E9E7E9C076D4E845DBC11 |
| SHA1: | 1705EB2FF4D3F3DABBB2EB28BAA95794A2539AB1 |
| SHA256: | 2928348C05CBF8AC3FCCFC2B77A38F19692DB495EAF6B229E7C6C9571FD57313 |
| SSDEEP: | 3:N8DS8sLGT:2O89T |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2816)
- chrome.exe (PID: 3144)
Changes internet zones settings
- iexplore.exe (PID: 2816)
Reads Internet Cache Settings
- iexplore.exe (PID: 3280)
Reads settings of System Certificates
- chrome.exe (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B6F460C152A7277E9DAA68CEA48E80B7 --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D468207366368C9EA1E29B43BFED89B4 --mojo-platform-channel-handle=940 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=EB6F44B17546795861554E32FF2AA3FD --mojo-platform-channel-handle=4232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --service-pipe-token=038E6A86817FB77D4AC41521370C20AA --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=038E6A86817FB77D4AC41521370C20AA --renderer-client-id=5 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3148 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=35D68F9F91E7C95664CE4DEB848242AA --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=35D68F9F91E7C95664CE4DEB848242AA --renderer-client-id=6 --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2816 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=912,2066167163831079509,3461745954016535131,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=68B615FCFFAA908FE984F22C399FE50B --mojo-platform-channel-handle=2812 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
864
Read events
753
Write events
107
Delete events
4
Modification events
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {2F05531F-FF4F-11E8-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C0005000E00030014001400A802 | |||
Executable files
0
Suspicious files
63
Text files
83
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\443dbc24-2c37-4c3e-a582-275e2ec3f971.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0b4649d7-d65f-4b03-beda-95febac992f4.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
33
DNS requests
22
Threats
48
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | chrome.exe | GET | 302 | 103.224.182.246:80 | http://wwwpsecu.com/ | AU | — | — | malicious |
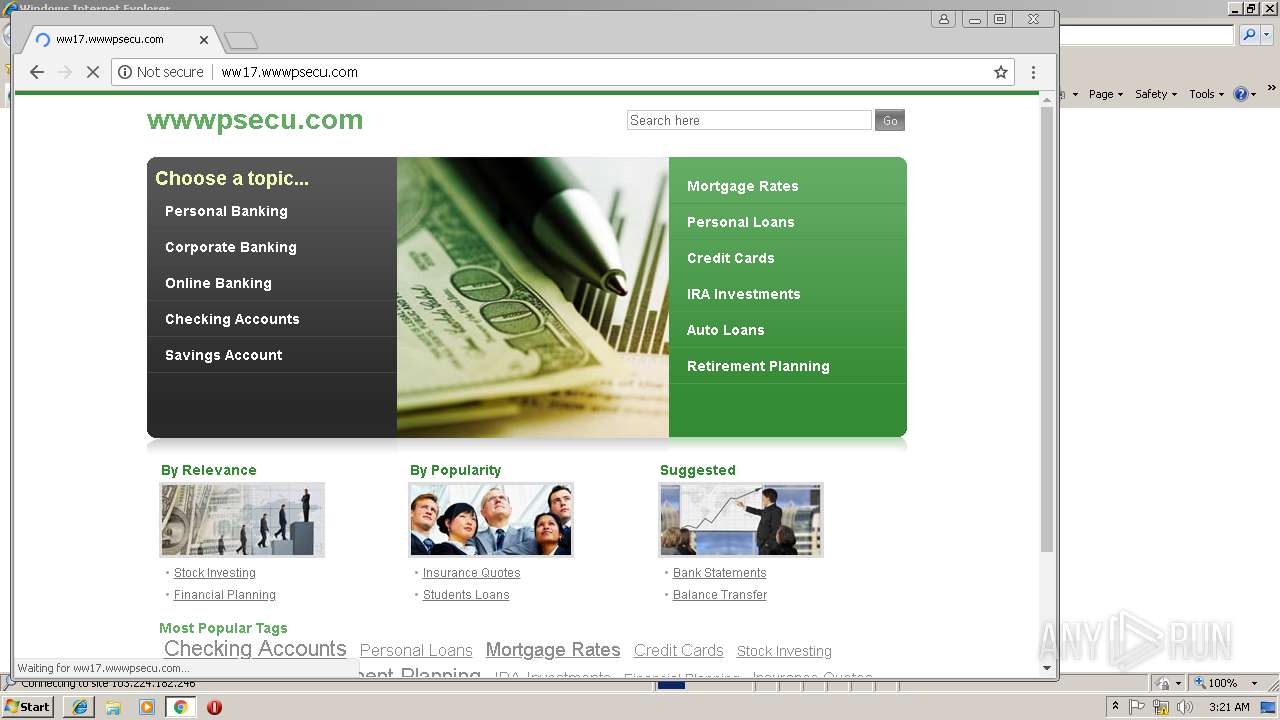
3144 | chrome.exe | GET | 200 | 208.91.196.148:80 | http://ww17.wwwpsecu.com/ | VG | html | 1.05 Kb | unknown |
3144 | chrome.exe | GET | 200 | 208.91.196.148:80 | http://ww17.wwwpsecu.com/?fp=X1orUiG9EhSAb3toiOq5hetky%2Ftmp8V0tr4PyVbvU5G1COrIK7qDSSB5BGlvE49kePZ5u3IW6TPBWRkVhcyRgZblELIKmPC%2BoFE2eRYnY1%2BIDxwH%2F1%2BrQo%2FNNDMB1D%2FucL2om%2BmfdEC4SlXOfFb8ijGMIPMAD1q%2ByAGvw%2BCjEmw%3D&prvtof=oivkSPHXR4OhHqfHmCB7XLsI2oxUrZG%2FqeTNgLNJHXg%3D&poru=Ha03txkMZ5Z7byjh%2B6KGWoCkQTHL%2BfjwAfQ1XeKNtkX1lf1dregE%2BqhIgk3%2Behyg& | VG | html | 9.42 Kb | unknown |
3144 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i2.cdn-image.com/__media__/pics/471/ChunkFive_400.font.js | unknown | text | 6.69 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/images/2384_Directi-green-Finance4.jpg | unknown | image | 3.67 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/images/2385_Directi-green-Finance3.jpg | unknown | image | 4.83 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/images/2386_Directi-green-Finance2.jpg | unknown | image | 3.70 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/pics/471/right-sidebar-bg.jpg | unknown | image | 5.26 Kb | whitelisted |
3144 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/pics/471/gray-dot.gif | unknown | image | 51 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | chrome.exe | 172.217.168.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3144 | chrome.exe | 52.71.49.60:3478 | stun.spamanalyst.com | Amazon.com, Inc. | US | whitelisted |
2816 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3280 | iexplore.exe | 103.224.182.246:443 | wwwpsecu.com | Trellian Pty. Limited | AU | suspicious |
3144 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3144 | chrome.exe | 172.217.168.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3144 | chrome.exe | 172.217.168.228:443 | www.google.com | Google Inc. | US | whitelisted |
3144 | chrome.exe | 103.224.182.246:80 | wwwpsecu.com | Trellian Pty. Limited | AU | suspicious |
3144 | chrome.exe | 208.91.196.148:80 | ww17.wwwpsecu.com | Confluence Networks Inc | VG | unknown |
3144 | chrome.exe | 2.16.186.106:80 | i1.cdn-image.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
wwwpsecu.com |
| malicious |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
ww17.wwwpsecu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3144 | chrome.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |