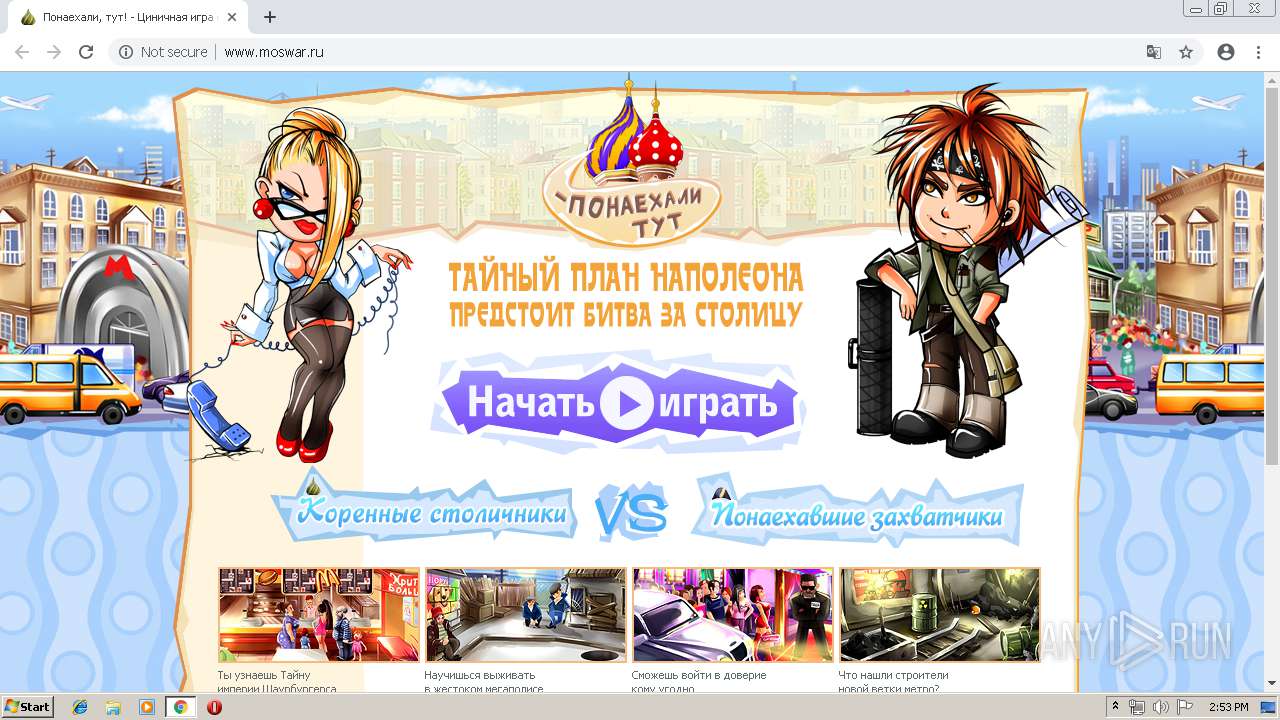
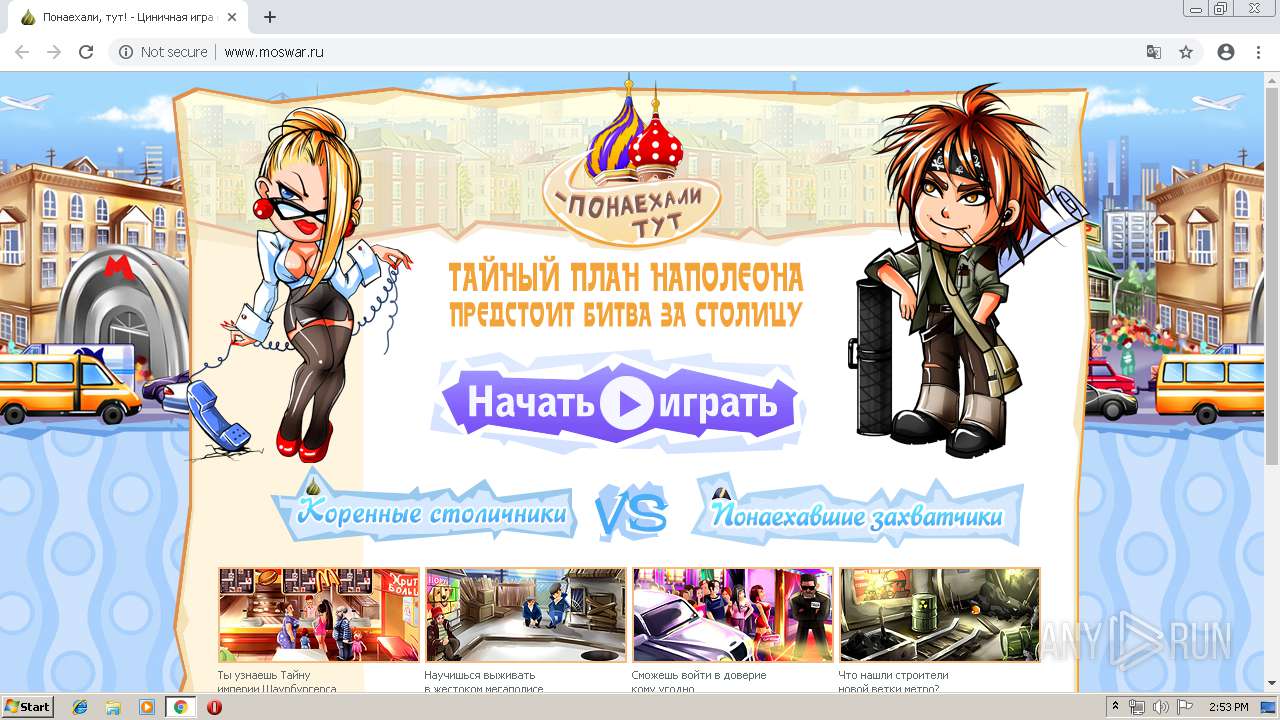
| URL: | http://www.moswar.ru |
| Full analysis: | https://app.any.run/tasks/497ce128-3fcb-41f9-ba67-dc55757a9bad |
| Verdict: | No threats detected |
| Analysis date: | May 24, 2019, 13:52:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6FEBE2B235D93024815BC199A334A66B |
| SHA1: | 8A68FC674AB47649387F8975357B11DF1BD7CC99 |
| SHA256: | 29254BBA5DD73C57EFC79553E6A4FCDE533F71D4DF9E7653662F8DB6397357C5 |
| SSDEEP: | 3:N1KJS4mSf:Cc4ms |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2900)
INFO
Application launched itself
- chrome.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16589144551784671864 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --service-pipe-token=14546942598935794404 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14546942598935794404 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cd70f18,0x6cd70f28,0x6cd70f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14655207970139929768 --mojo-platform-channel-handle=2756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7231448384192090222 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7231448384192090222 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --service-pipe-token=12128264879794129795 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12128264879794129795 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16287572526061252603 --mojo-platform-channel-handle=2672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3332 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8639851330957251698 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8639851330957251698 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,12194093747140051168,517320274234751869,131072 --enable-features=PasswordImport --service-pipe-token=14279282990171535355 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14279282990171535355 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
547
Read events
459
Write events
83
Delete events
5
Modification events
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2900-13203179575776625 |
Value: 259 | |||
| (PID) Process: | (2900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
136
Text files
141
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3d301307-d462-4239-bbc1-9b32c3896bce.tmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
207
TCP/UDP connections
38
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/js/index.js | RU | text | 2.38 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/images/logo.png | RU | image | 30.1 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/main.css | RU | text | 36.2 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/common.css | RU | text | 3.72 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/phone.css | RU | text | 16.1 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/forum.css | RU | text | 1.10 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/photos.css | RU | text | 2.22 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/images/index/2.jpg | RU | image | 21.8 Kb | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/rating.css | RU | text | 591 b | suspicious |
2900 | chrome.exe | GET | 200 | 91.225.238.162:80 | http://www.moswar.ru/@/css/locations.css | RU | text | 689 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2900 | chrome.exe | 87.240.129.133:443 | vk.com | VKontakte Ltd | RU | malicious |
2900 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2900 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2900 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2900 | chrome.exe | 87.240.129.133:80 | vk.com | VKontakte Ltd | RU | malicious |
2900 | chrome.exe | 91.225.238.162:80 | www.moswar.ru | Destiny Development Ltd. | RU | suspicious |
2900 | chrome.exe | 172.217.22.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2900 | chrome.exe | 91.225.237.85:80 | lbn2.ddestiny.ru | Destiny Development Ltd. | RU | unknown |
2900 | chrome.exe | 88.212.201.195:80 | counter.yadro.ru | United Network LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.moswar.ru |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
vk.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
vkontakte.ru |
| whitelisted |
forum.theabyss.ru |
| malicious |
www.roswar.ru |
| unknown |