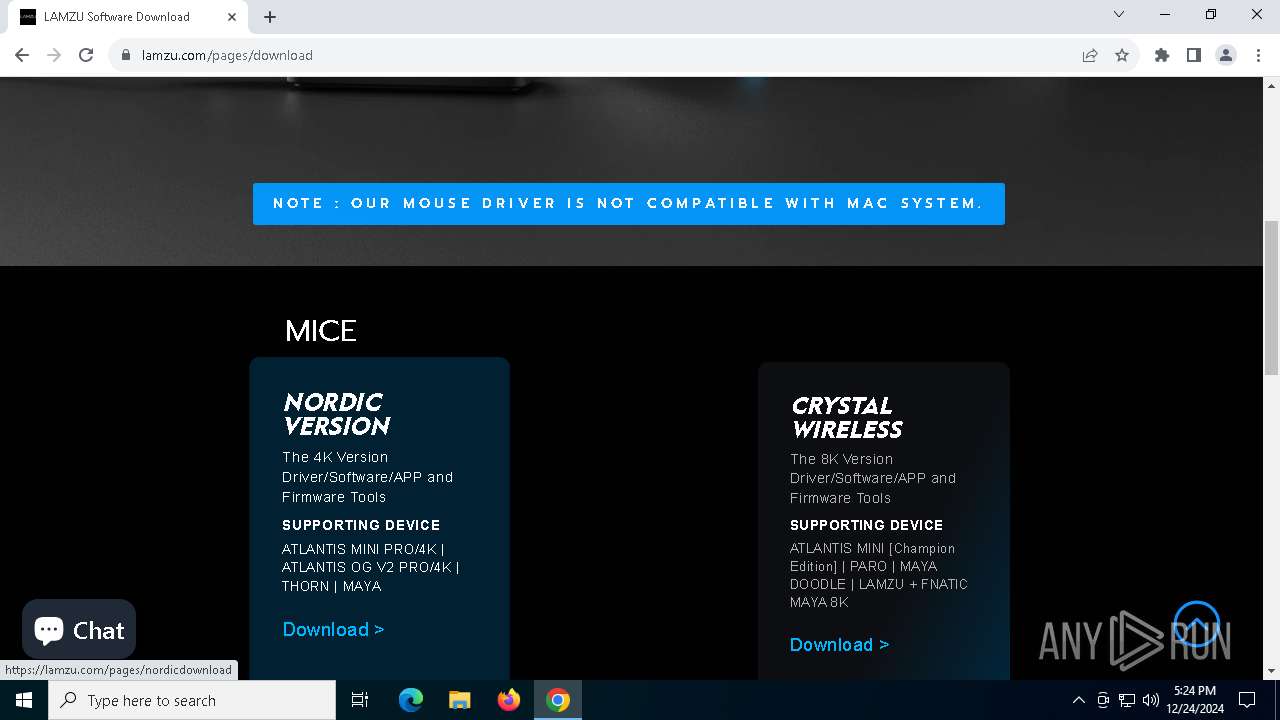
| URL: | https://lamzu.com/ |
| Full analysis: | https://app.any.run/tasks/7f1ca572-8ad0-4c1a-b602-4ff94b915362 |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2024, 17:24:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F2DBF6C7FE8AE0F9A5E1FA495EE87CEA |
| SHA1: | F05E740677F05264EECF82312BAB7BFB8F37D26C |
| SHA256: | 2919C97457760501C968E0AB2B9A9AFFB169E710FCD095182488499F1CC1E246 |
| SSDEEP: | 3:N8EIk:2EIk |
MALICIOUS
No malicious indicators.SUSPICIOUS
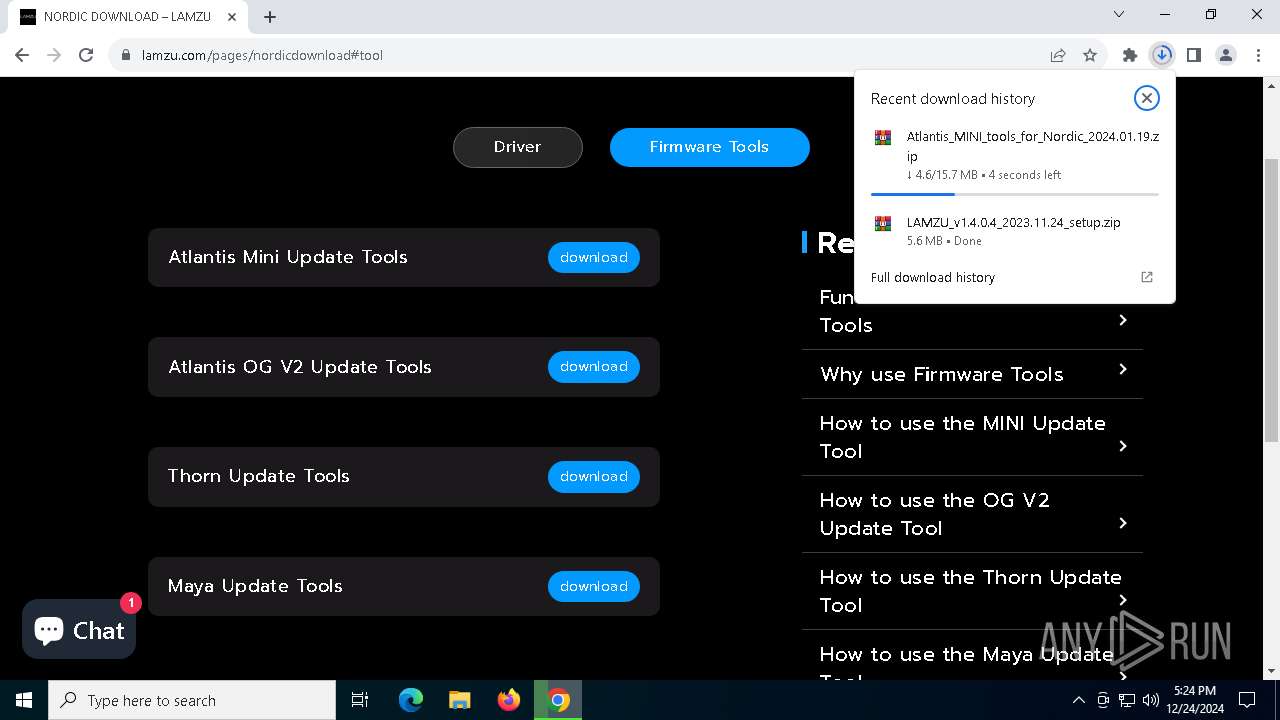
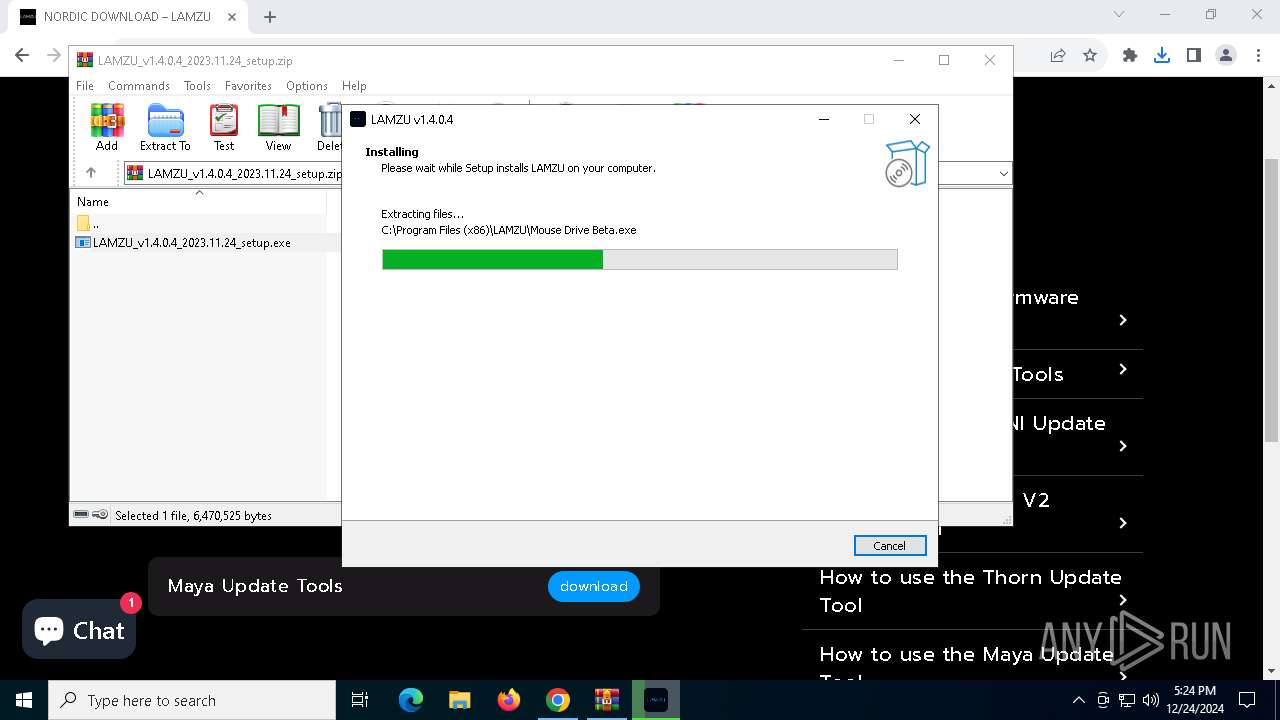
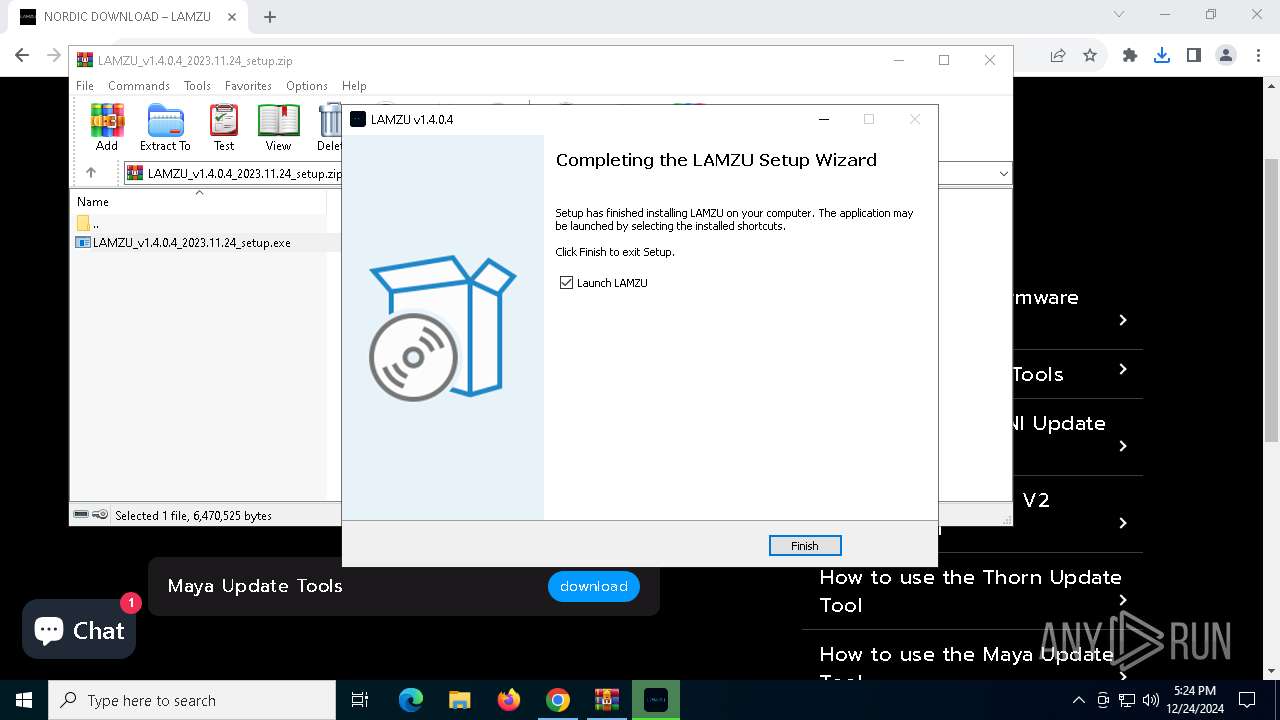
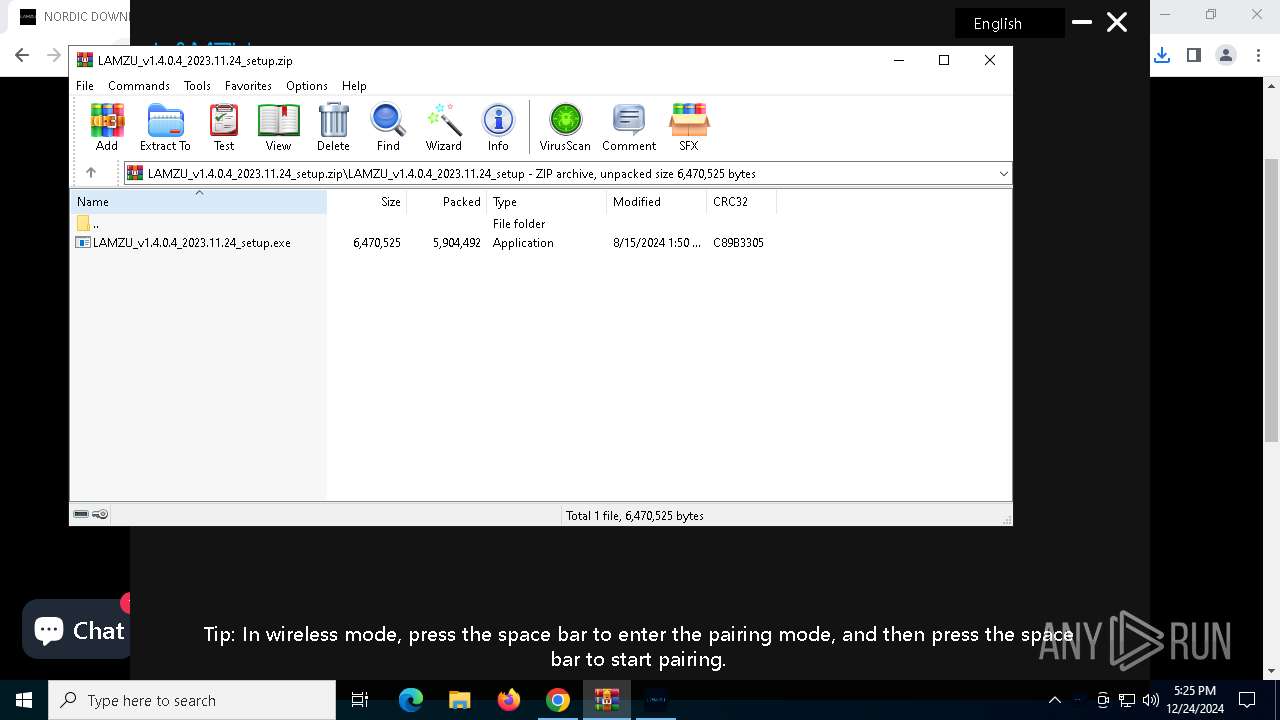
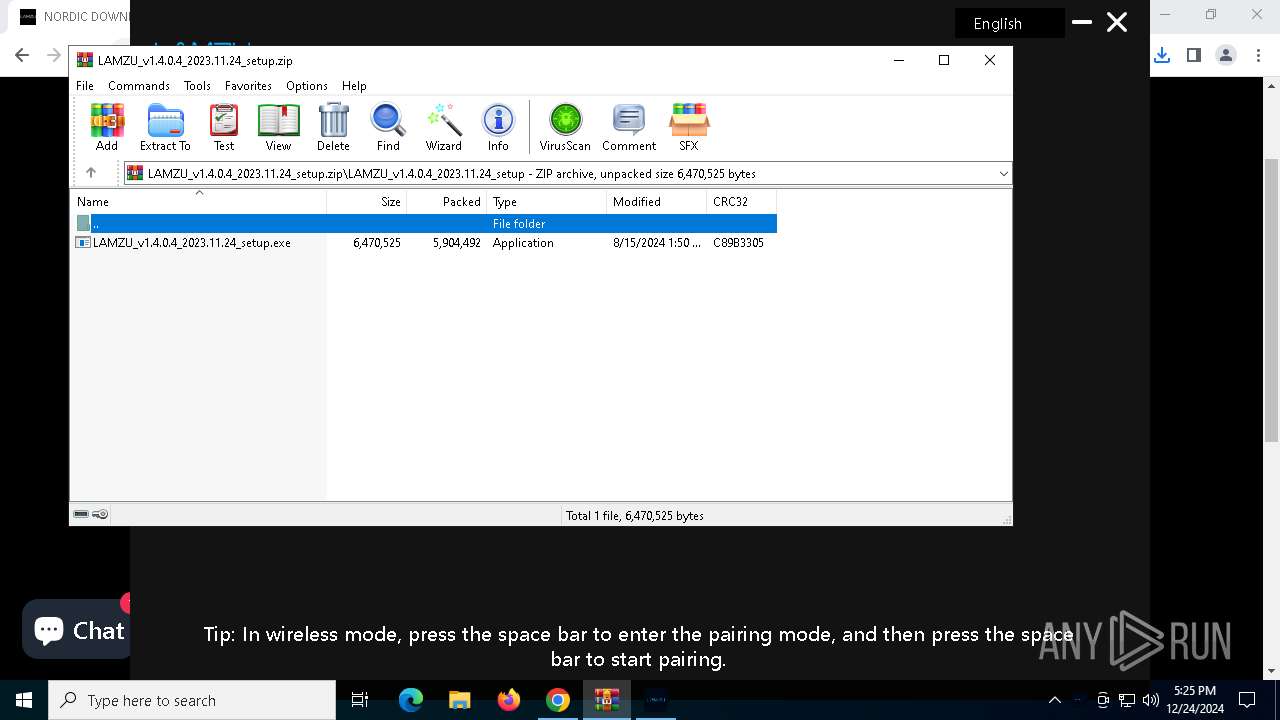
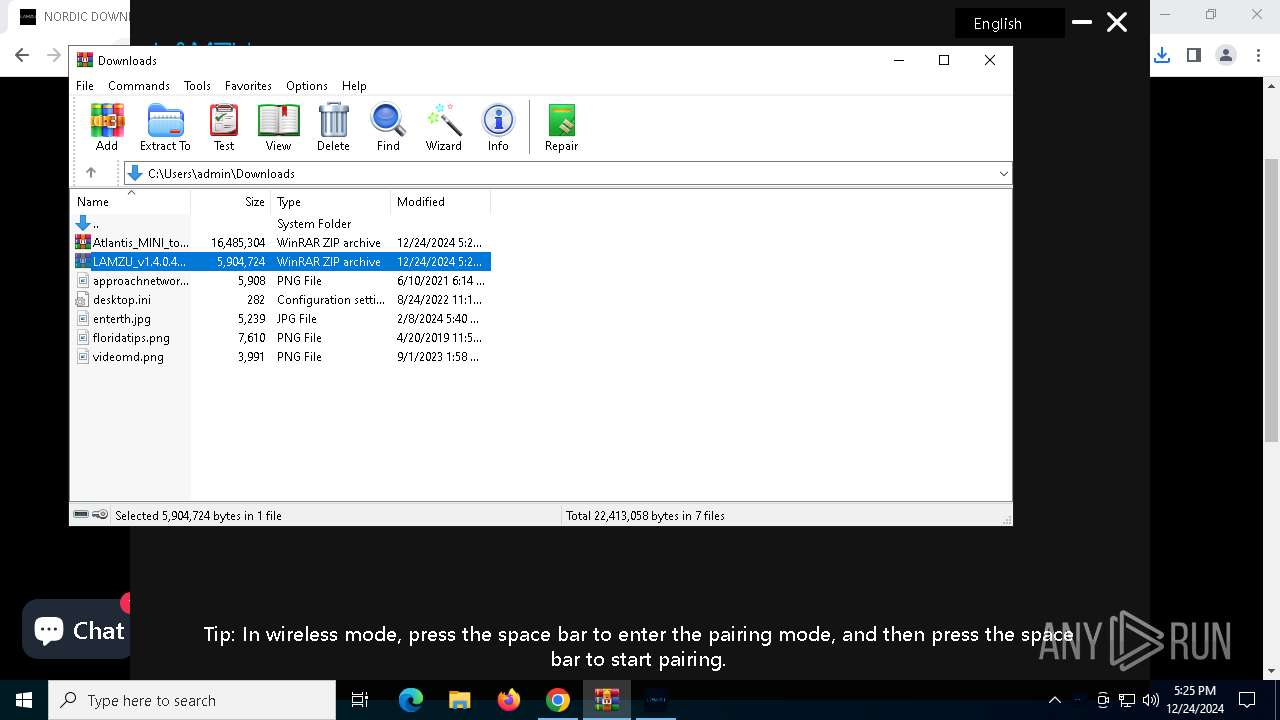
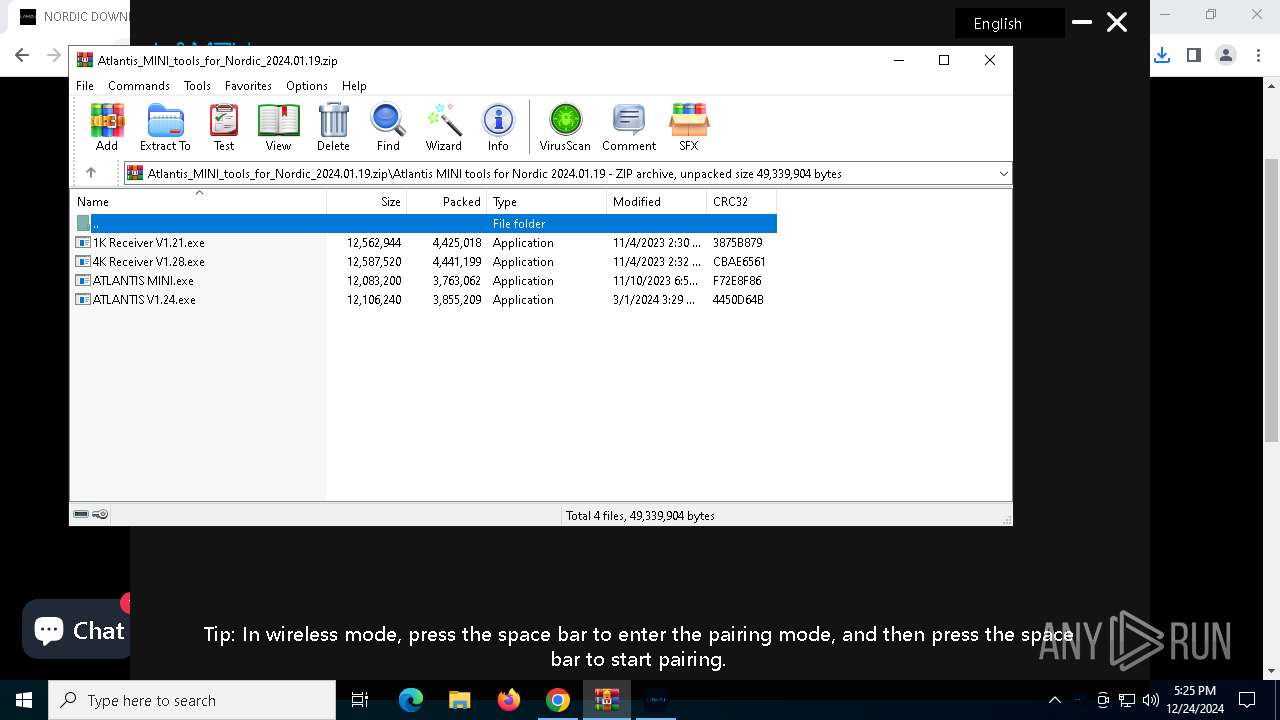
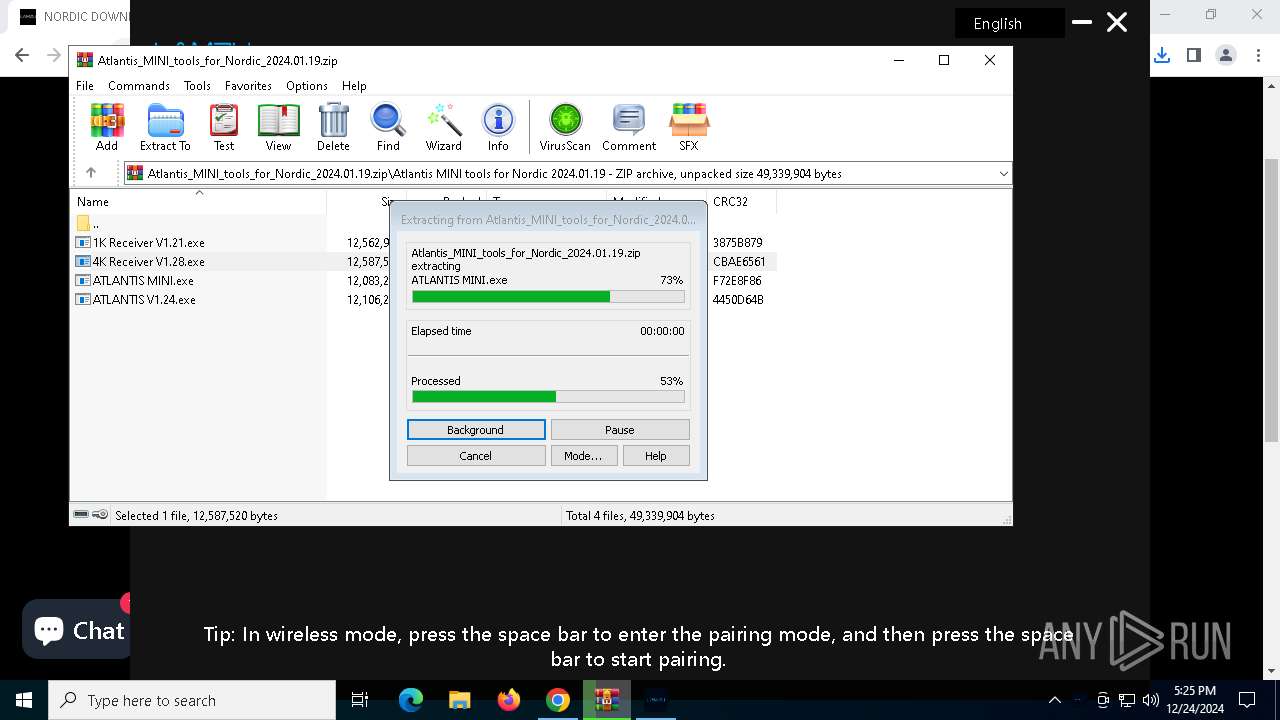
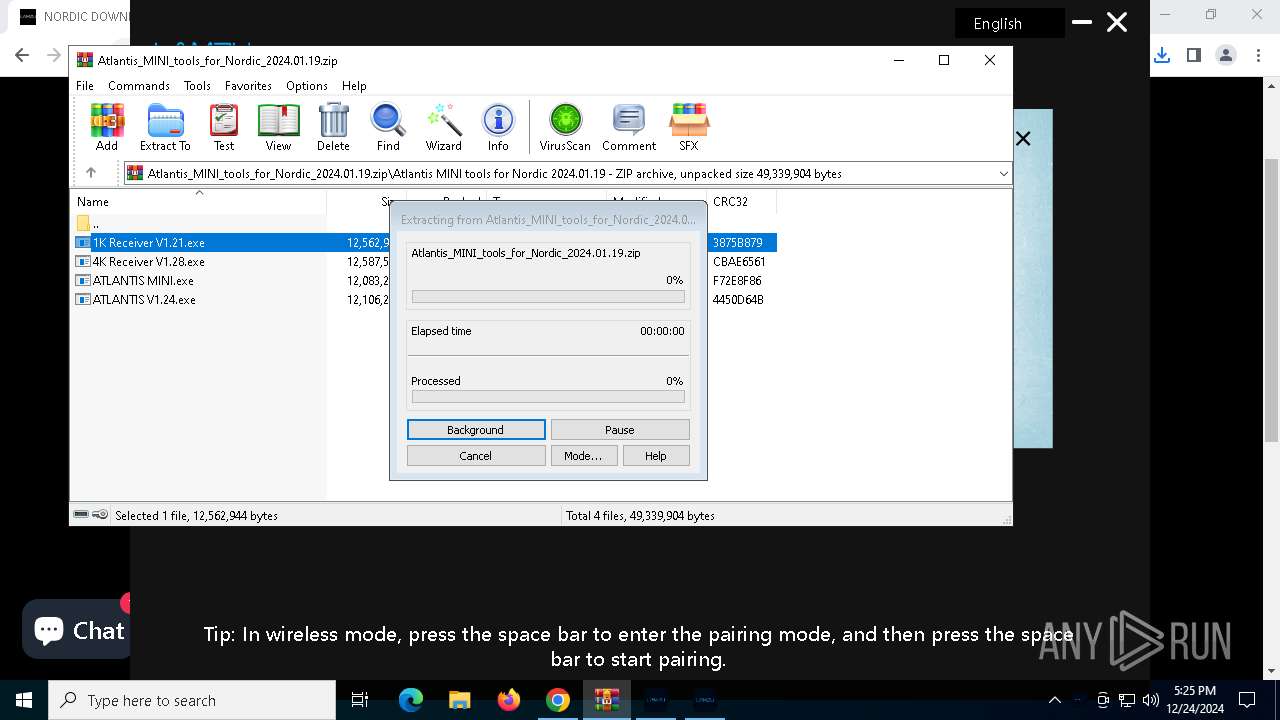
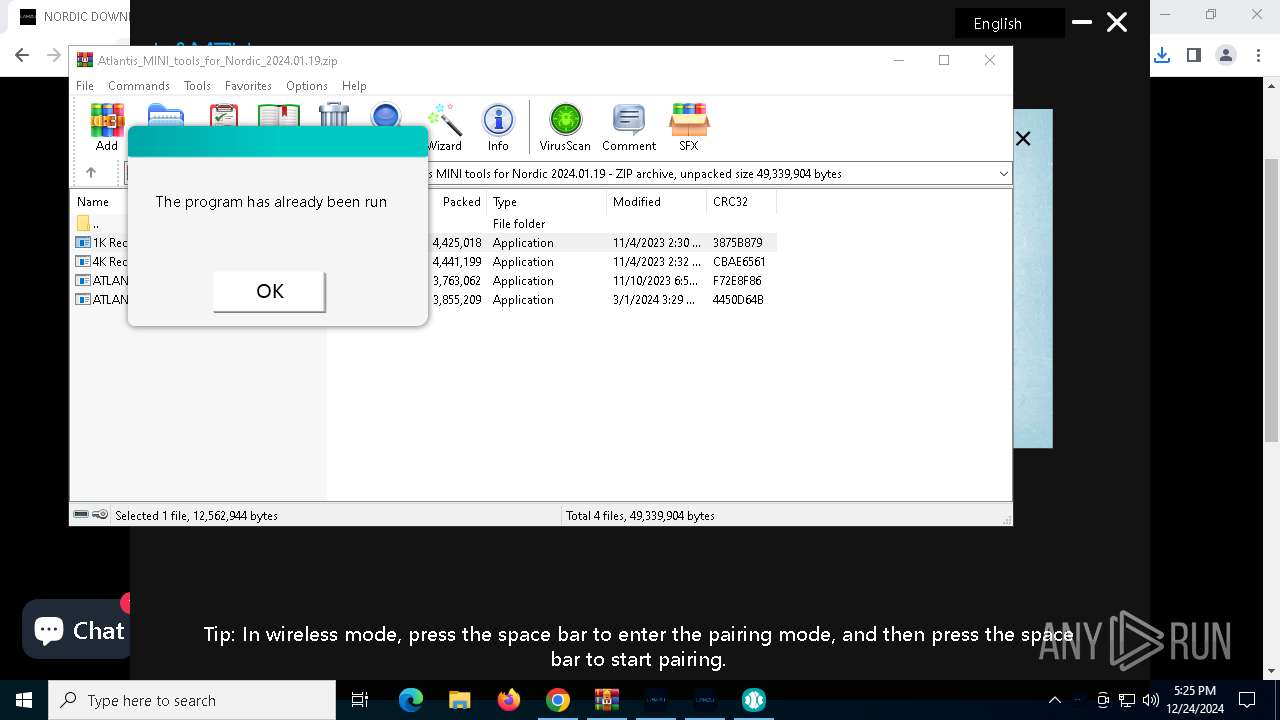
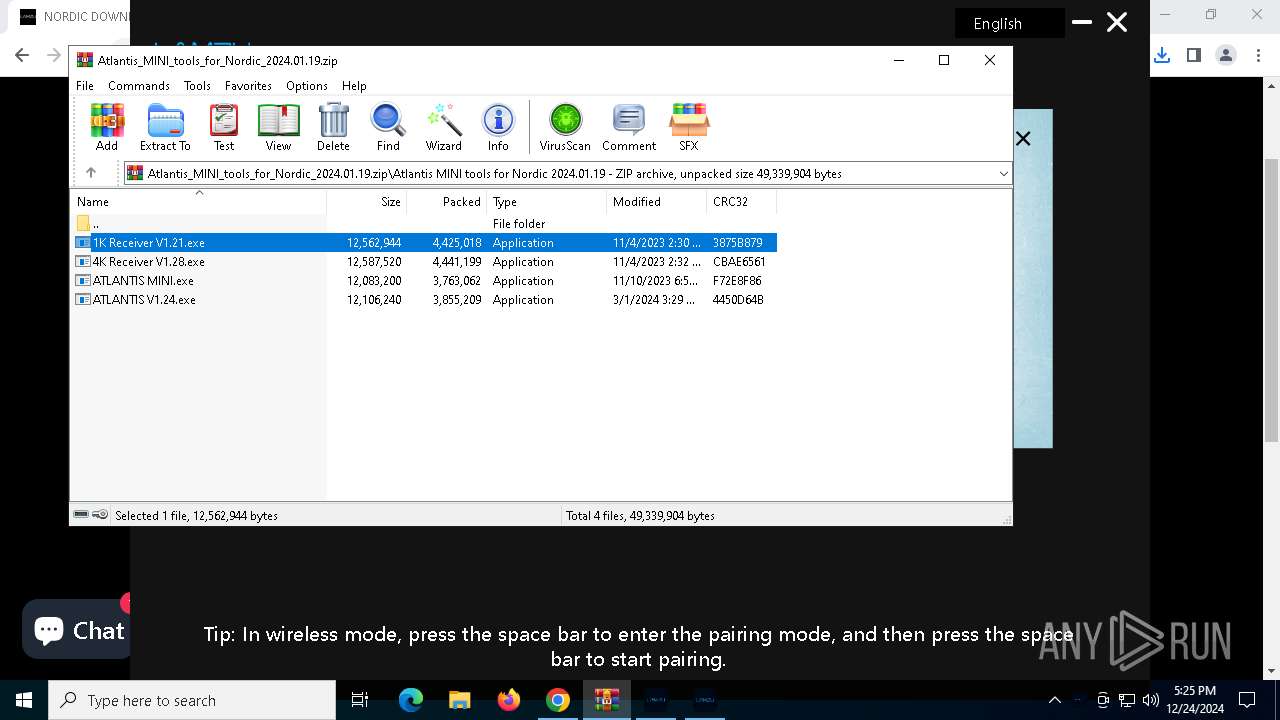
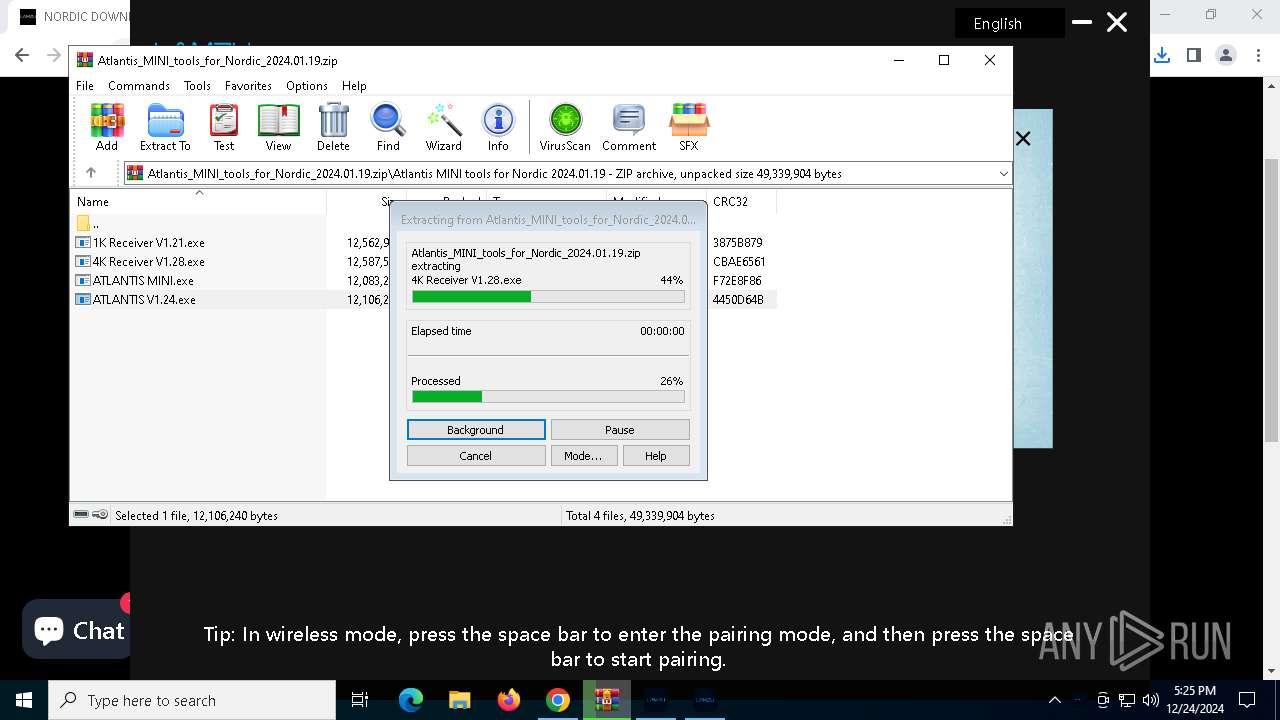
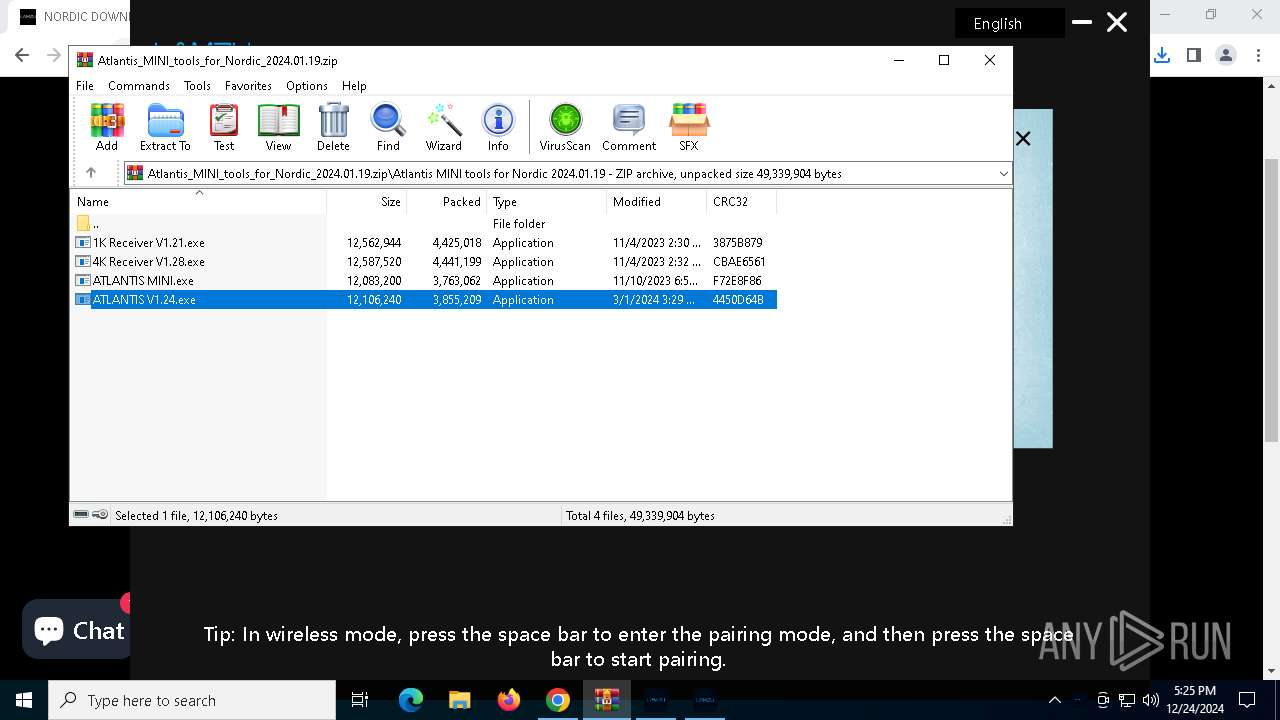
Executable content was dropped or overwritten
- LAMZU_v1.4.0.4_2023.11.24_setup.exe (PID: 3876)
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
- Mouse Drive Beta.exe (PID: 4504)
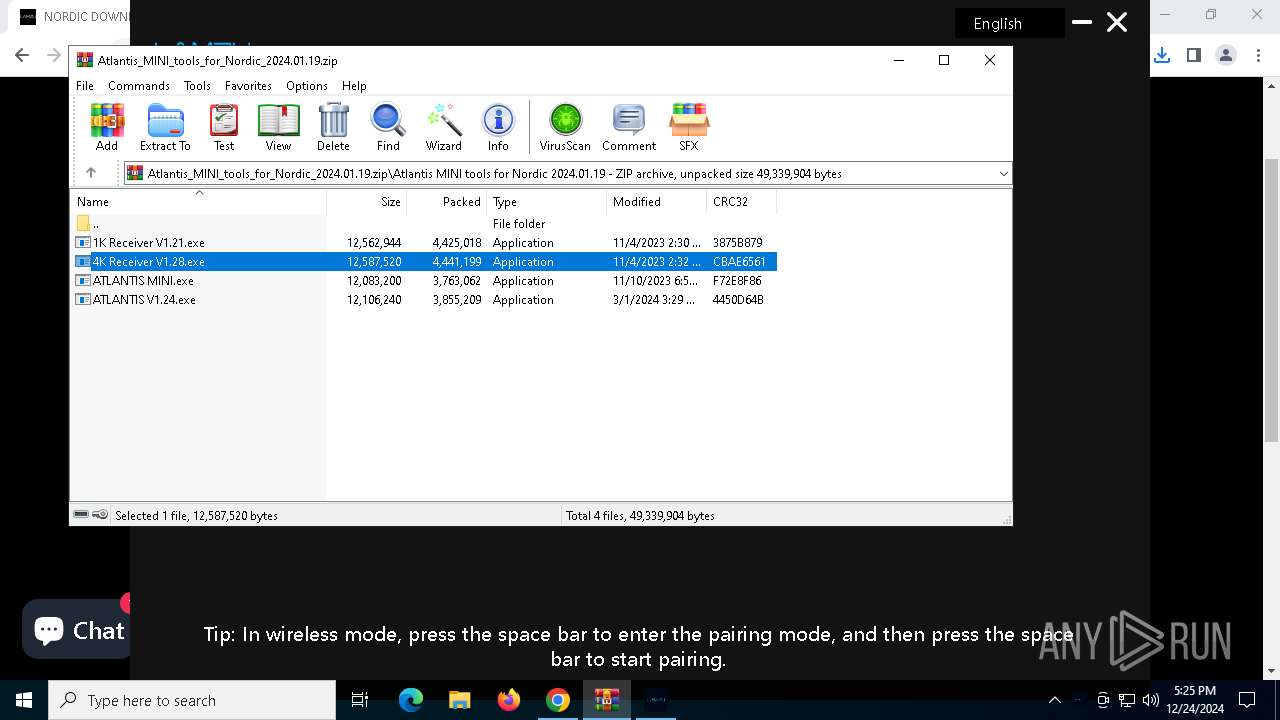
- 4K Receiver V1.28.exe (PID: 6208)
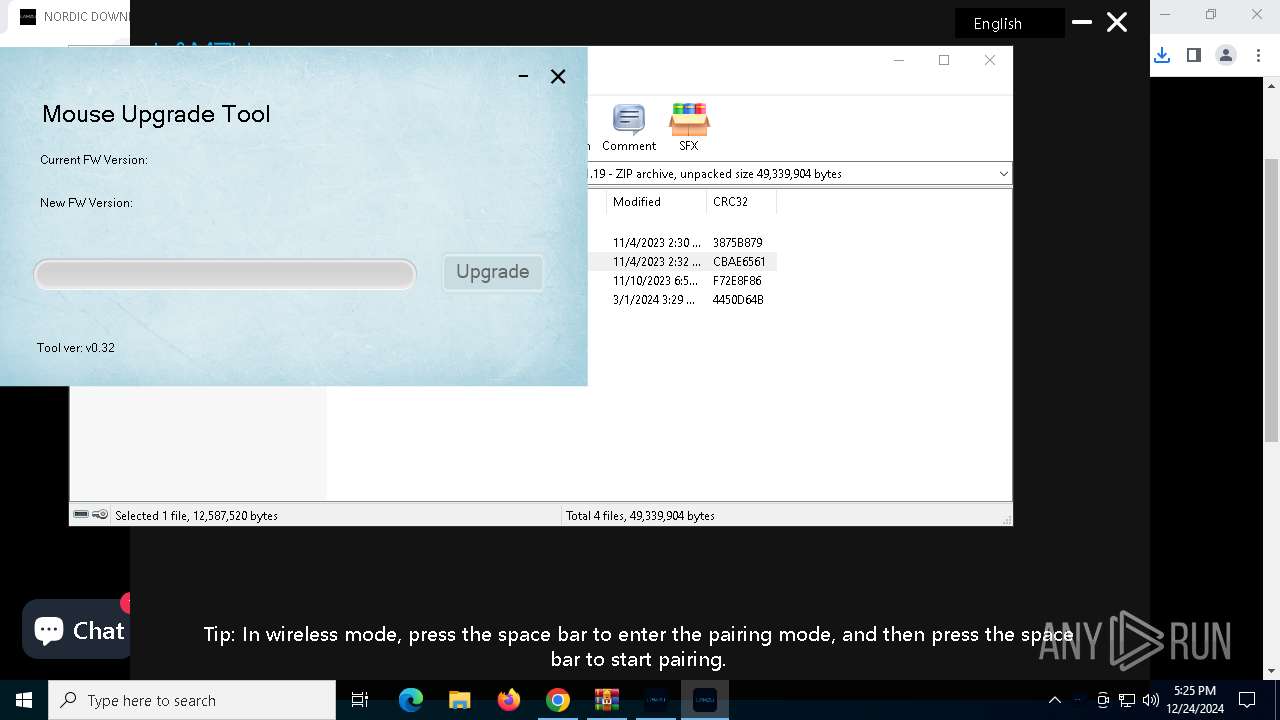
- ATLANTIS V1.24.exe (PID: 3608)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6244)
Process drops legitimate windows executable
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
- Mouse Drive Beta.exe (PID: 4504)
- 4K Receiver V1.28.exe (PID: 6208)
- ATLANTIS V1.24.exe (PID: 3608)
The process drops C-runtime libraries
- Mouse Drive Beta.exe (PID: 4504)
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
- 4K Receiver V1.28.exe (PID: 6208)
- ATLANTIS V1.24.exe (PID: 3608)
INFO
Application launched itself
- chrome.exe (PID: 6280)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6280)
Executable content was dropped or overwritten
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3820)
- WinRAR.exe (PID: 6244)
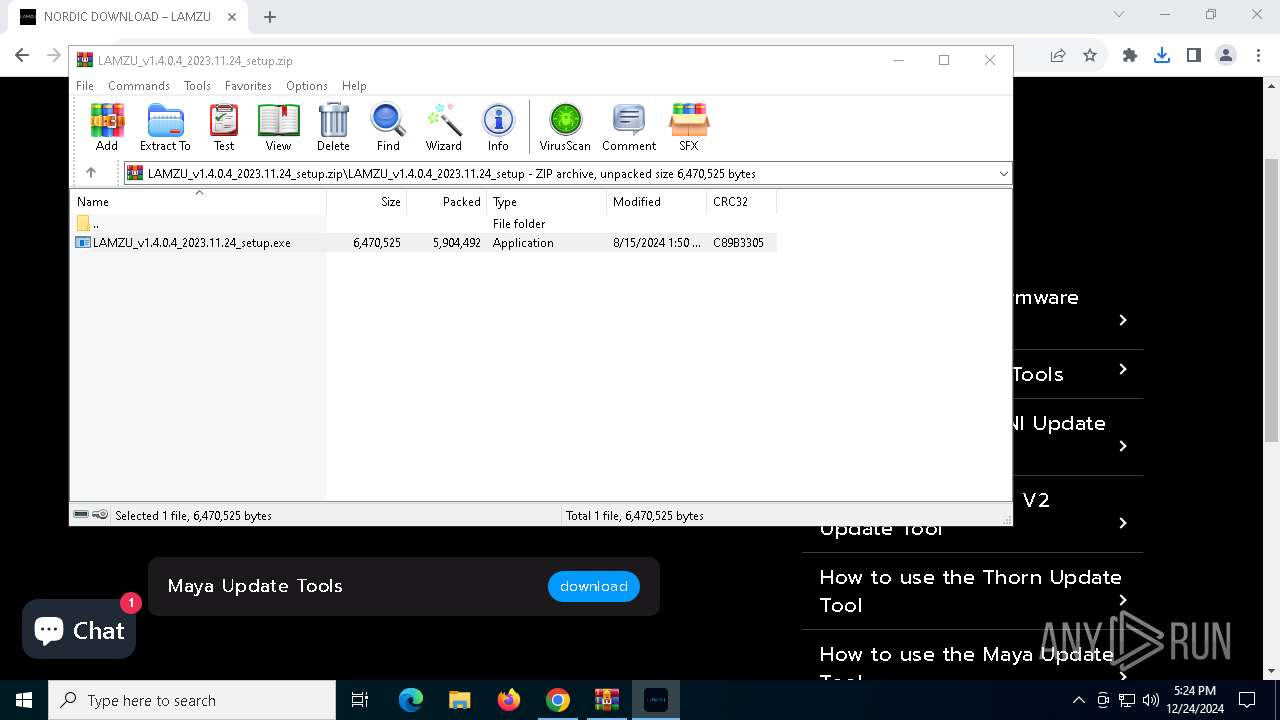
The process uses the downloaded file
- chrome.exe (PID: 5128)
- WinRAR.exe (PID: 6244)
- chrome.exe (PID: 5316)
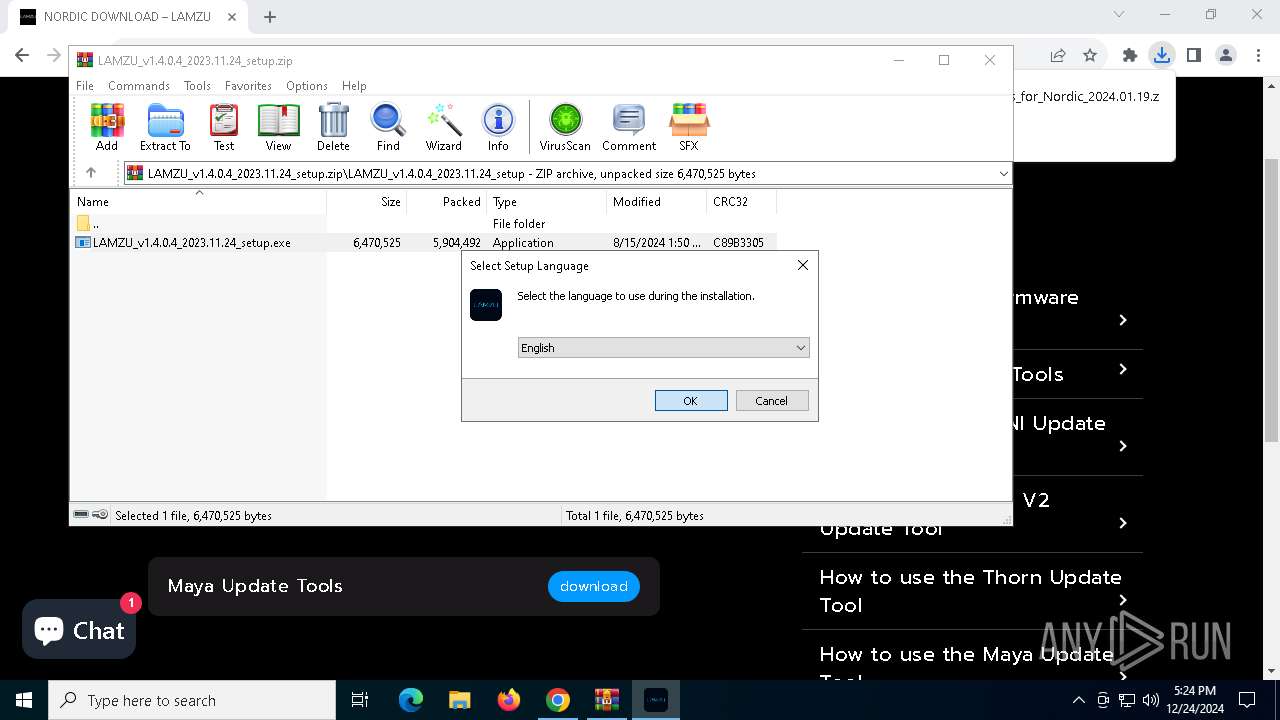
Checks supported languages
- LAMZU_v1.4.0.4_2023.11.24_setup.exe (PID: 3876)
- Mouse Drive Beta.exe (PID: 4504)
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
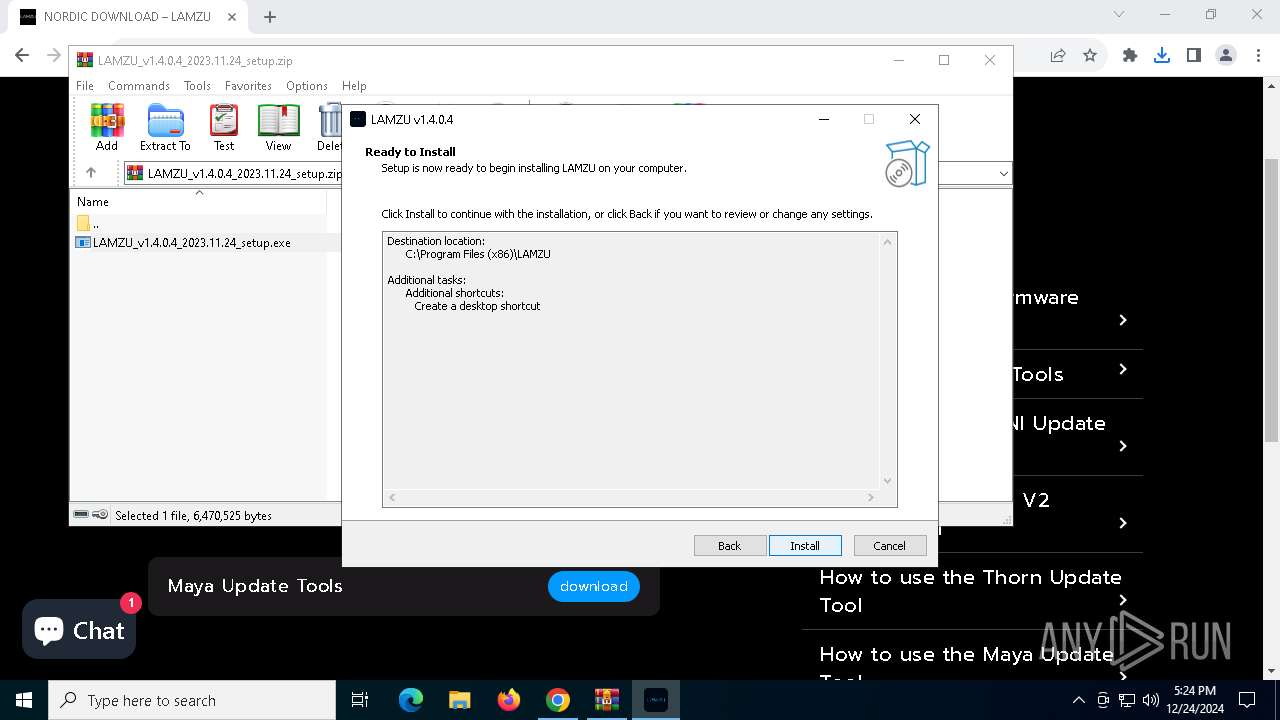
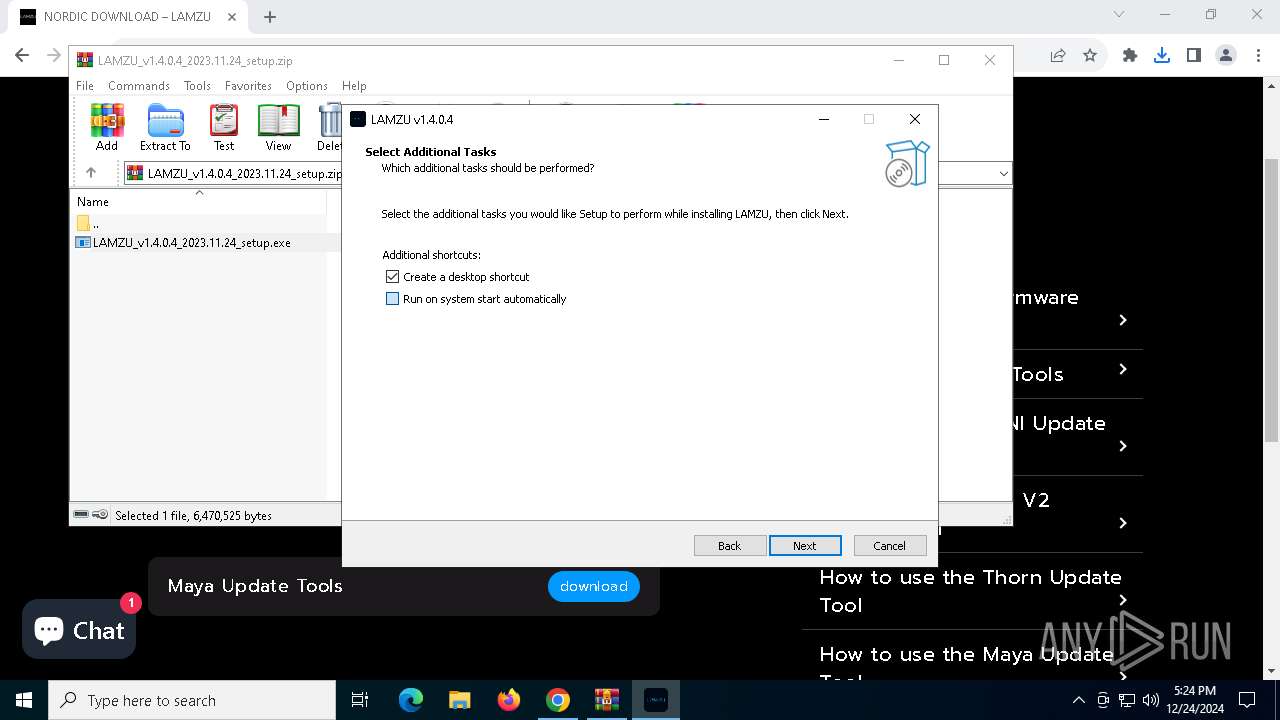
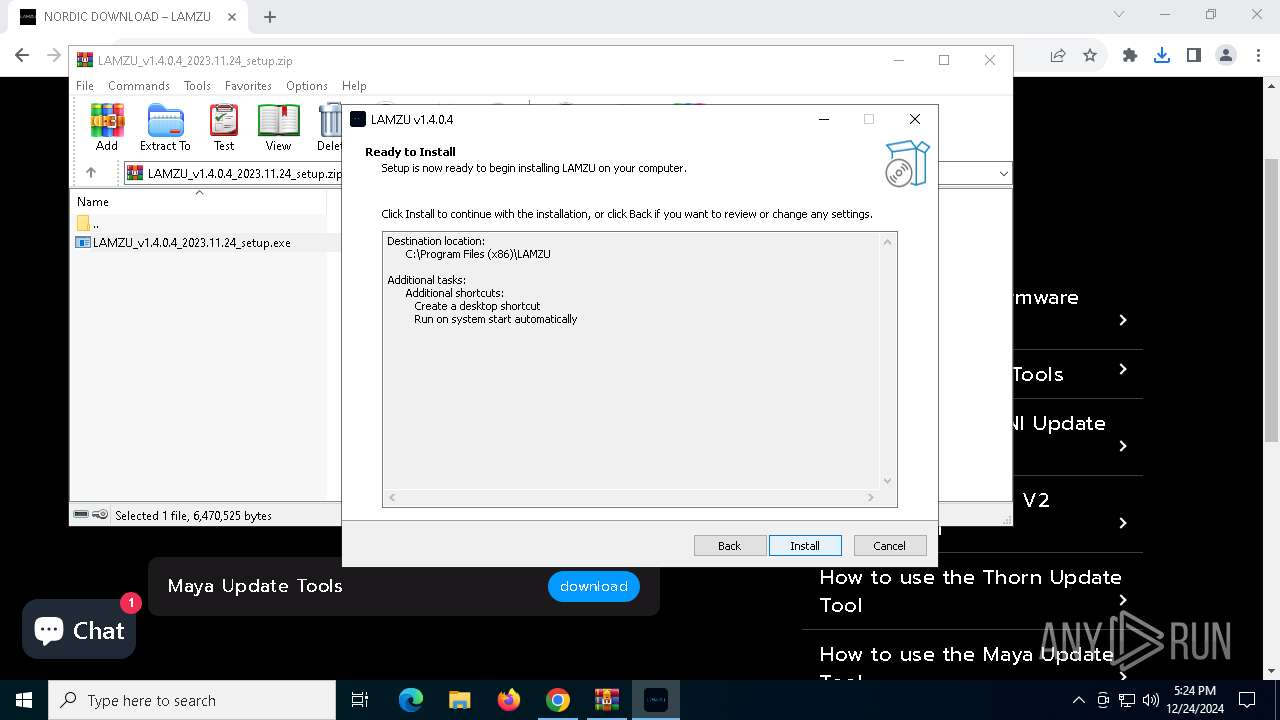
Creates files in the program directory
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
The sample compiled with english language support
- LAMZU_v1.4.0.4_2023.11.24_setup.tmp (PID: 3640)
- Mouse Drive Beta.exe (PID: 4504)
- 4K Receiver V1.28.exe (PID: 6208)
- ATLANTIS V1.24.exe (PID: 3608)
The sample compiled with chinese language support
- Mouse Drive Beta.exe (PID: 4504)
- 4K Receiver V1.28.exe (PID: 6208)
- ATLANTIS V1.24.exe (PID: 3608)
Create files in a temporary directory
- Mouse Drive Beta.exe (PID: 4504)
- 4K Receiver V1.28.exe (PID: 6208)
- ATLANTIS V1.24.exe (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
24
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5872 --field-trial-handle=1872,i,8232990844006573214,7507399715229529904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
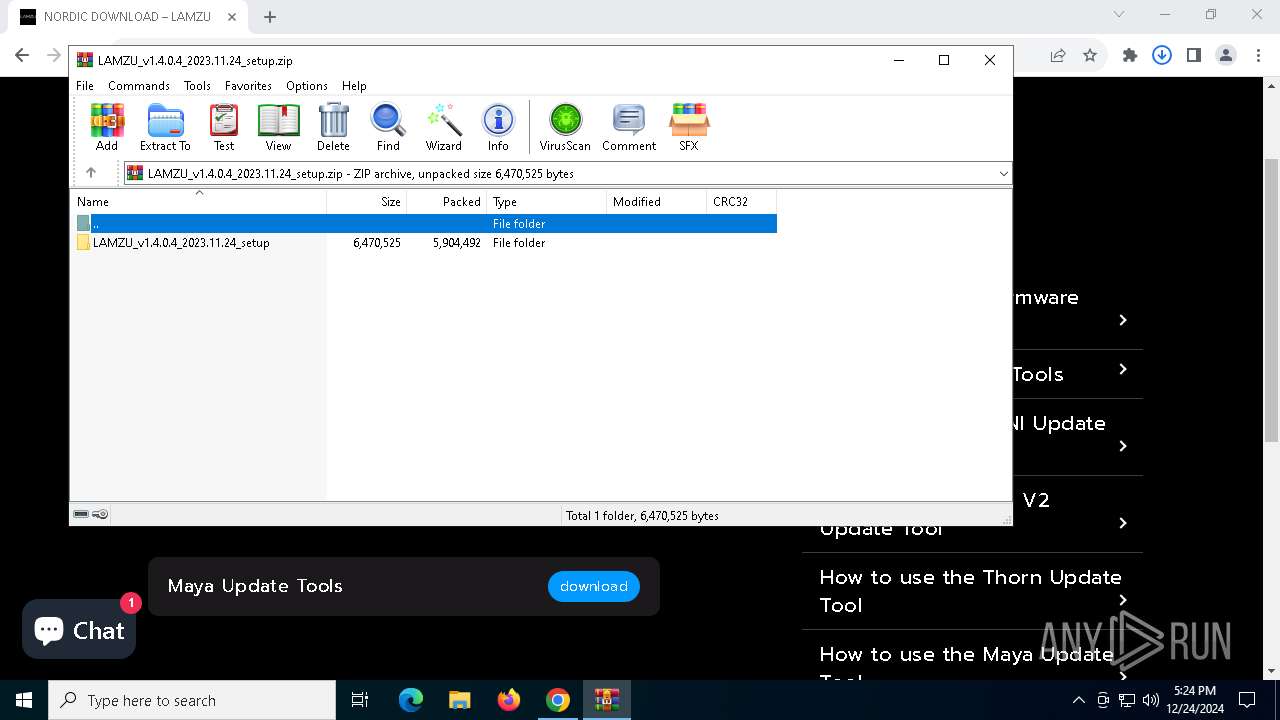
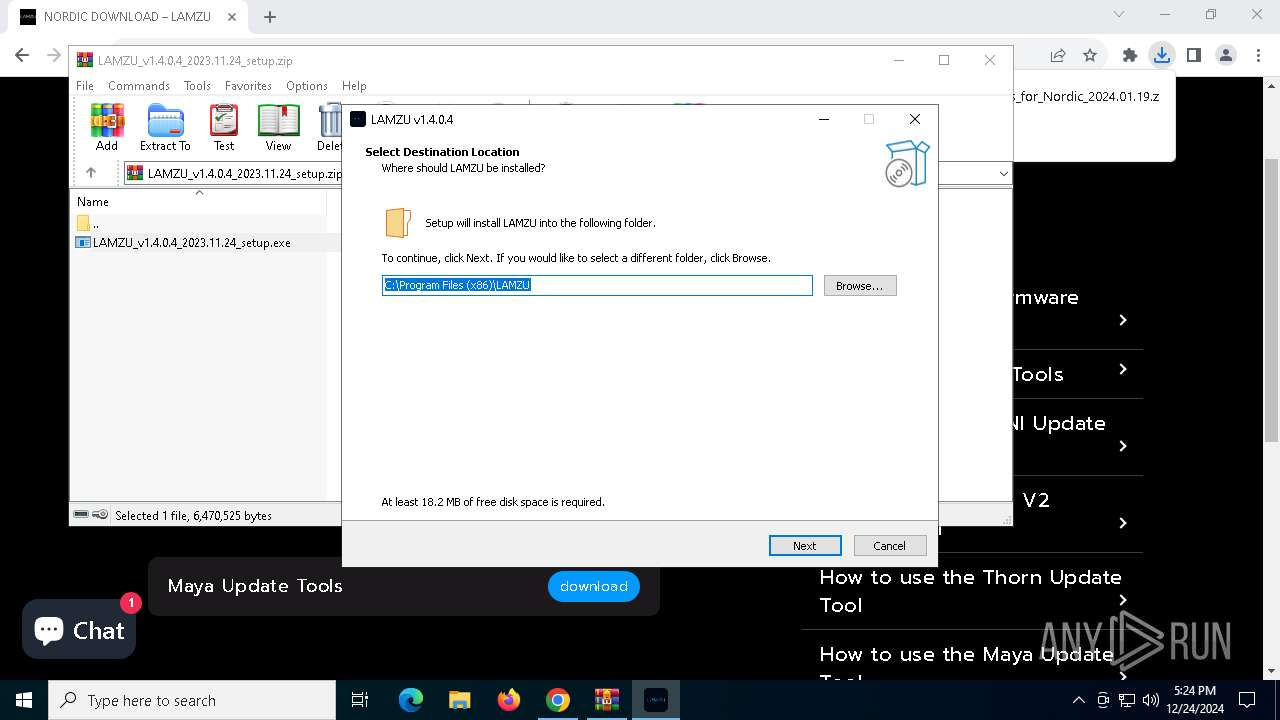
| 2800 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.39566\LAMZU_v1.4.0.4_2023.11.24_setup\LAMZU_v1.4.0.4_2023.11.24_setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.39566\LAMZU_v1.4.0.4_2023.11.24_setup\LAMZU_v1.4.0.4_2023.11.24_setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: LAMZU, Inc. Integrity Level: MEDIUM Description: LAMZU Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4736 --field-trial-handle=1872,i,8232990844006573214,7507399715229529904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
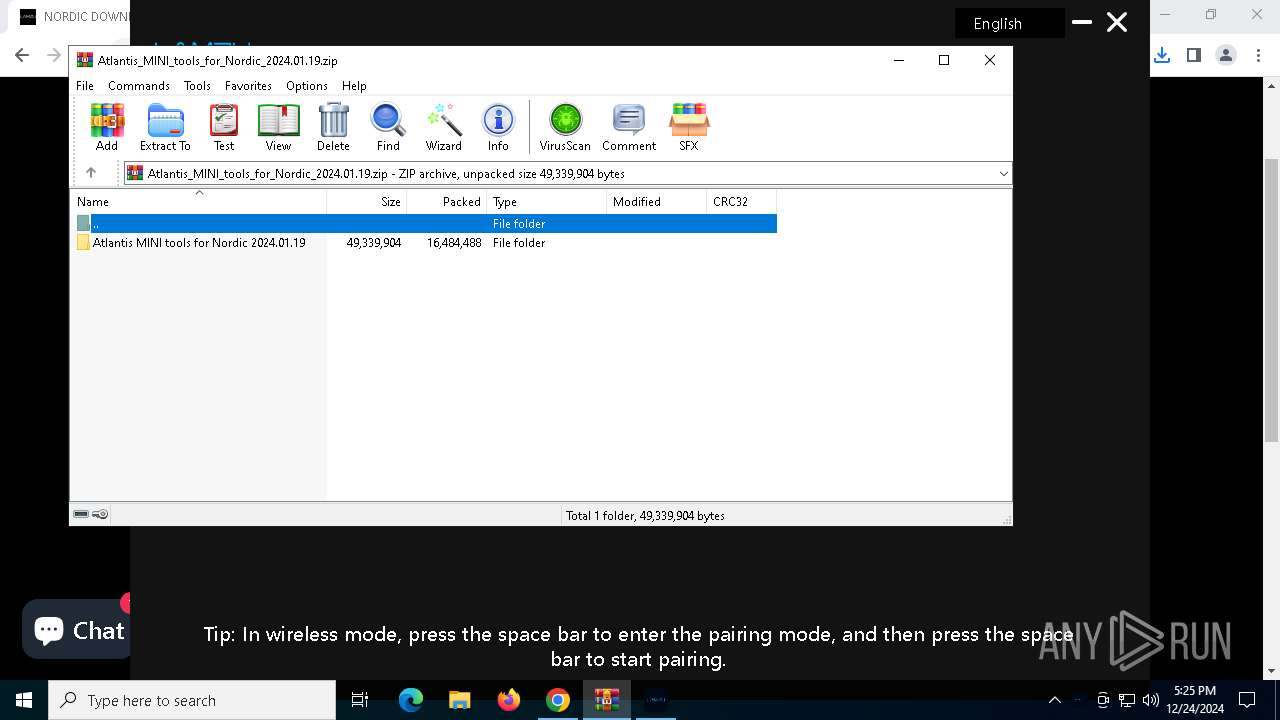
| 3608 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.42931\Atlantis MINI tools for Nordic 2024.01.19\ATLANTIS V1.24.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.42931\Atlantis MINI tools for Nordic 2024.01.19\ATLANTIS V1.24.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HID-All-in Upgrade Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
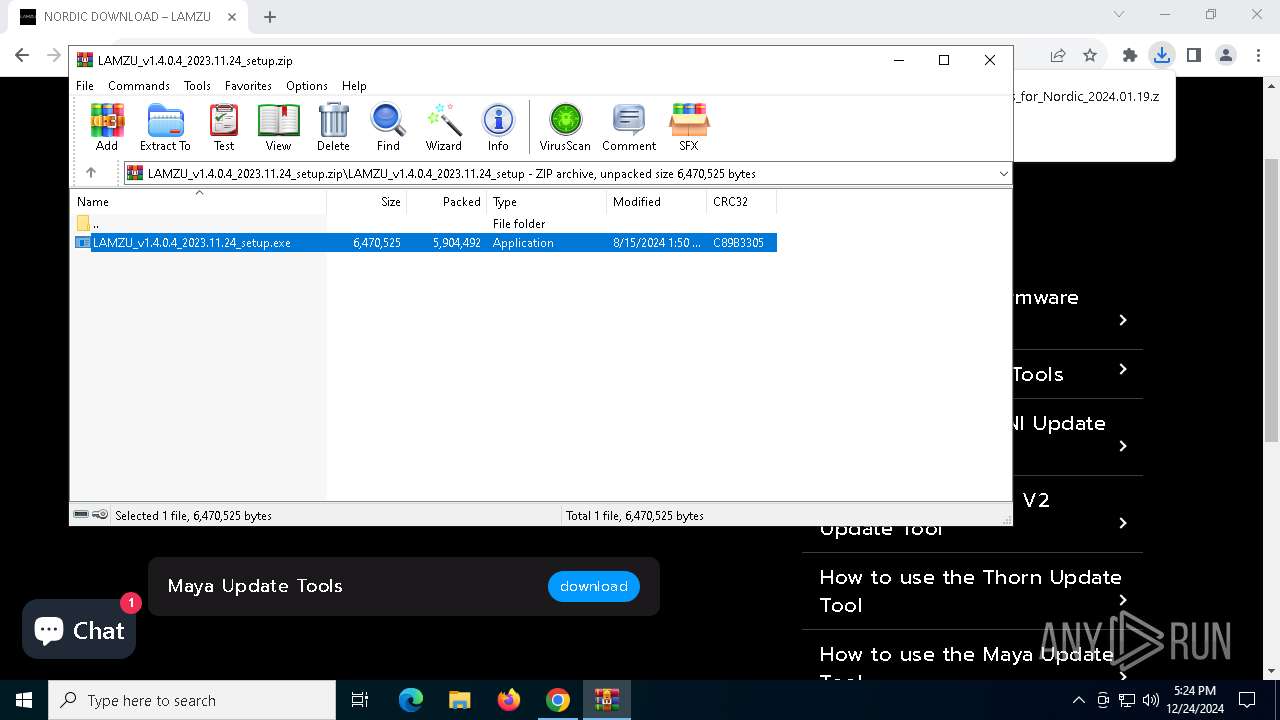
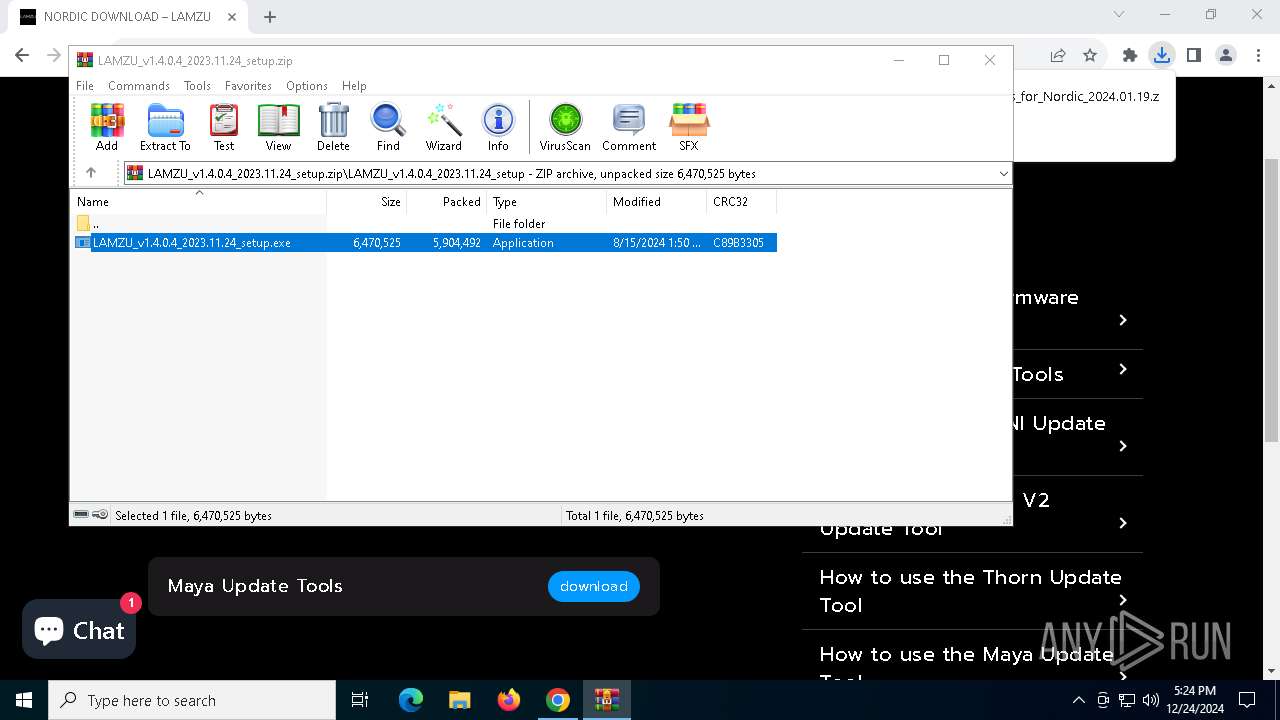
| 3640 | "C:\Users\admin\AppData\Local\Temp\is-AQ53L.tmp\LAMZU_v1.4.0.4_2023.11.24_setup.tmp" /SL5="$40276,5615505,843776,C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.39566\LAMZU_v1.4.0.4_2023.11.24_setup\LAMZU_v1.4.0.4_2023.11.24_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-AQ53L.tmp\LAMZU_v1.4.0.4_2023.11.24_setup.tmp | LAMZU_v1.4.0.4_2023.11.24_setup.exe | ||||||||||||
User: admin Company: LAMZU, Inc. Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5860 --field-trial-handle=1872,i,8232990844006573214,7507399715229529904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3876 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.39566\LAMZU_v1.4.0.4_2023.11.24_setup\LAMZU_v1.4.0.4_2023.11.24_setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6244.39566\LAMZU_v1.4.0.4_2023.11.24_setup\LAMZU_v1.4.0.4_2023.11.24_setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: LAMZU, Inc. Integrity Level: HIGH Description: LAMZU Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5792 --field-trial-handle=1872,i,8232990844006573214,7507399715229529904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5208 --field-trial-handle=1872,i,8232990844006573214,7507399715229529904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4504 | "C:\Program Files (x86)\LAMZU\Mouse Drive Beta.exe" | C:\Program Files (x86)\LAMZU\Mouse Drive Beta.exe | LAMZU_v1.4.0.4_2023.11.24_setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.4 Modules
| |||||||||||||||
Total events
7 520
Read events
7 459
Write events
60
Delete events
1
Modification events
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5316) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000AEFEABB62856DB01 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
50
Suspicious files
78
Text files
299
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135e7f.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135e7f.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135e8e.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135e8e.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135e8e.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
120
DNS requests
153
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6704 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://secure.globalsign.com/cacert/gsgccr6alphasslca2023.crt | unknown | — | — | whitelisted |
6536 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.80.56:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.38.73.129:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4308 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6704 | chrome.exe | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
lamzu.com |
| unknown |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
cdn.shopify.com |
| whitelisted |
cdn.staticfile.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6704 | chrome.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
6704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud Application Platform (.herokuapp .com) |
6704 | chrome.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |