| File name: | s_9960.exe |
| Full analysis: | https://app.any.run/tasks/b9af0880-2381-4155-a471-0176a230b285 |
| Verdict: | Suspicious activity |
| Analysis date: | July 02, 2019, 03:15:29 |
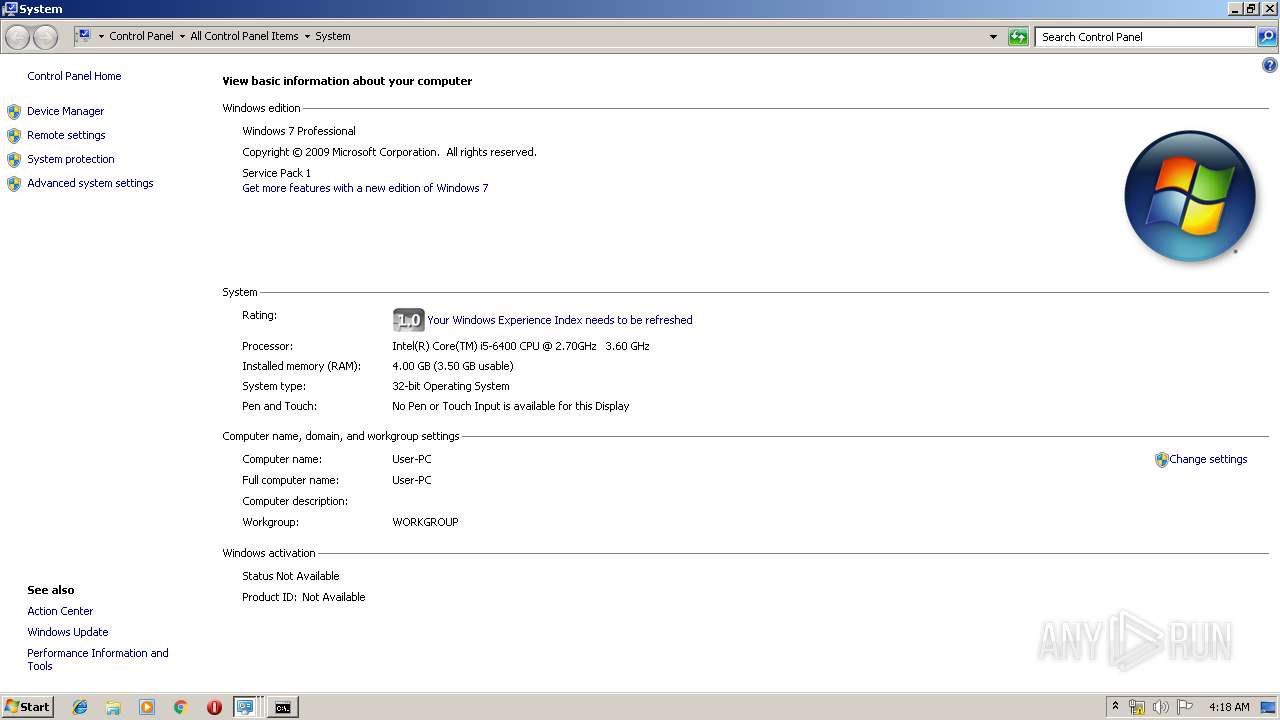
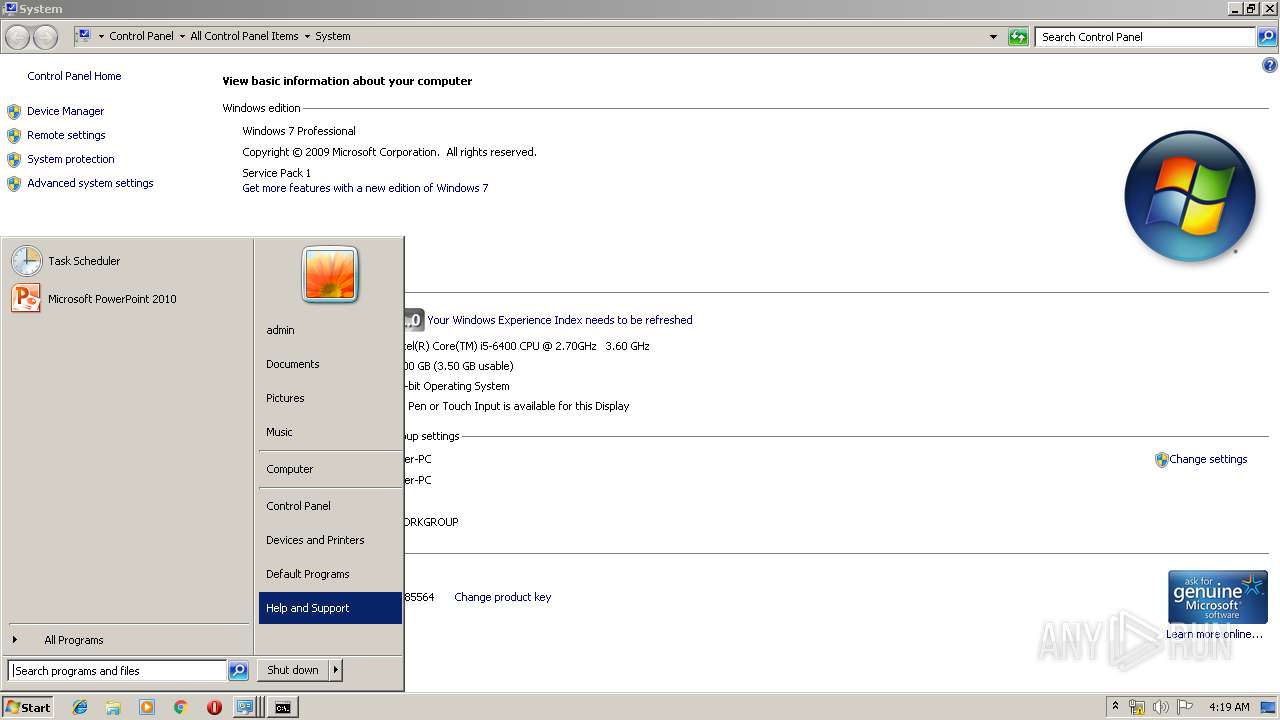
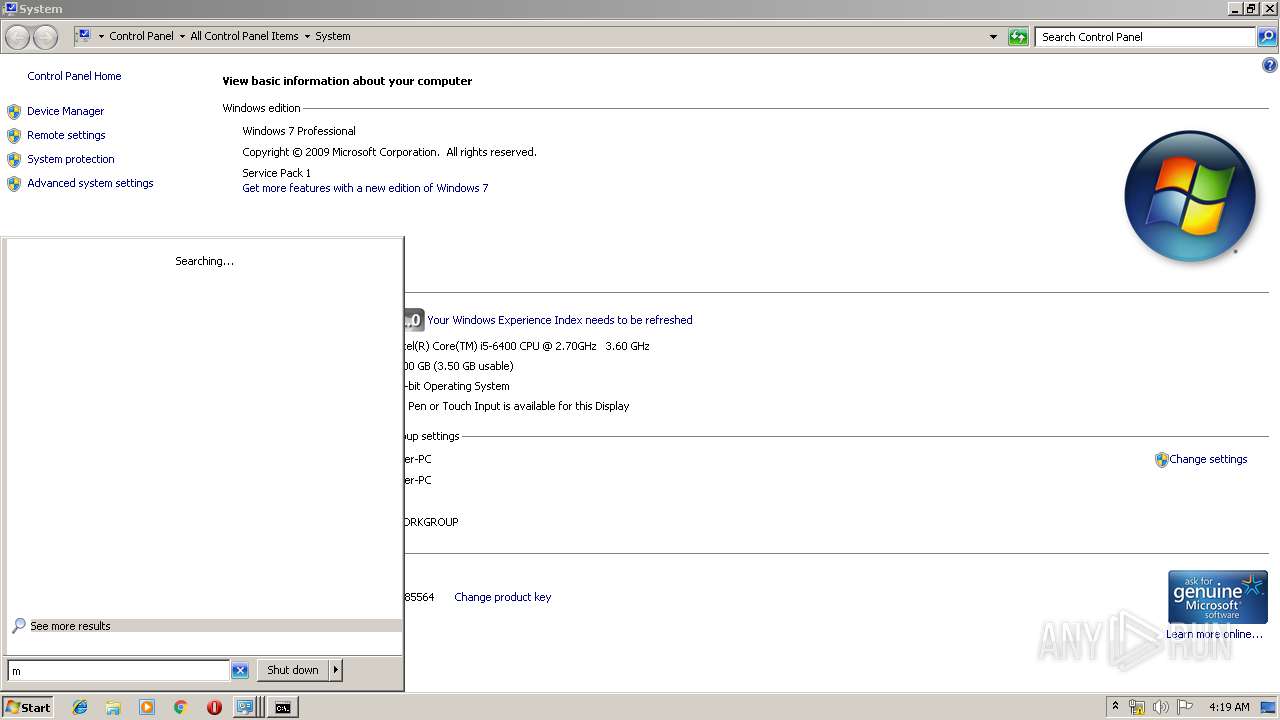
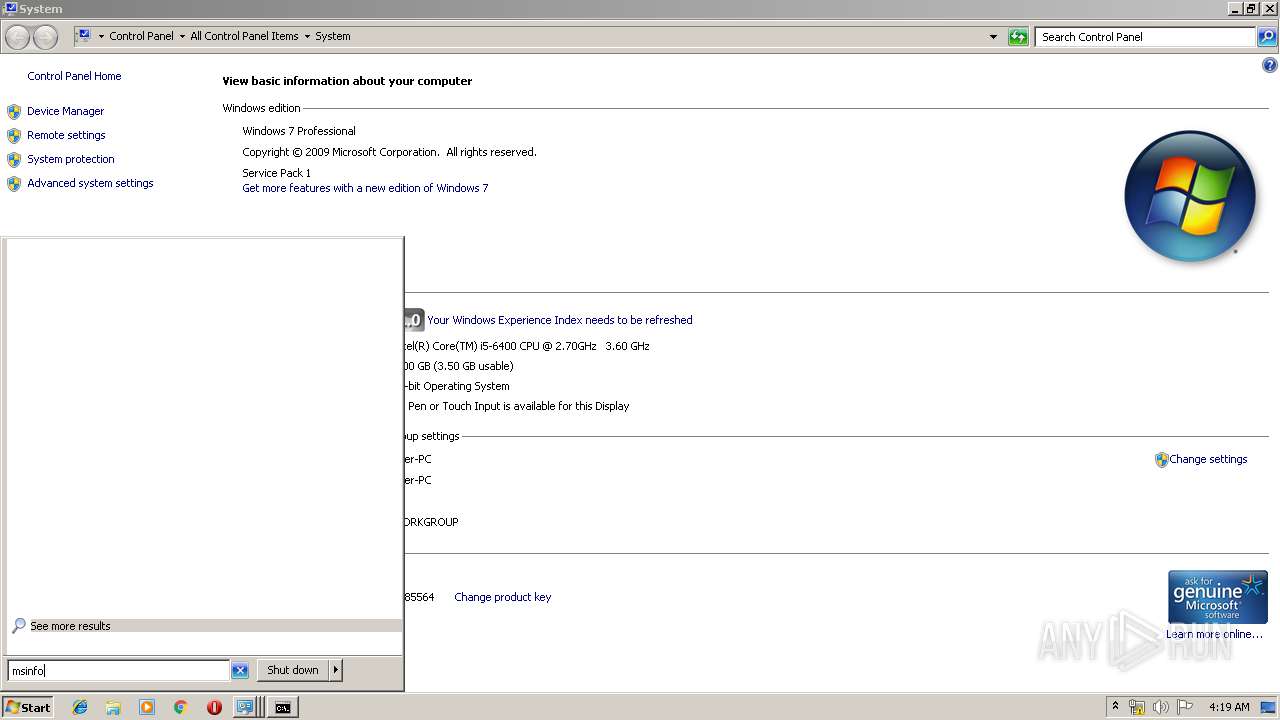
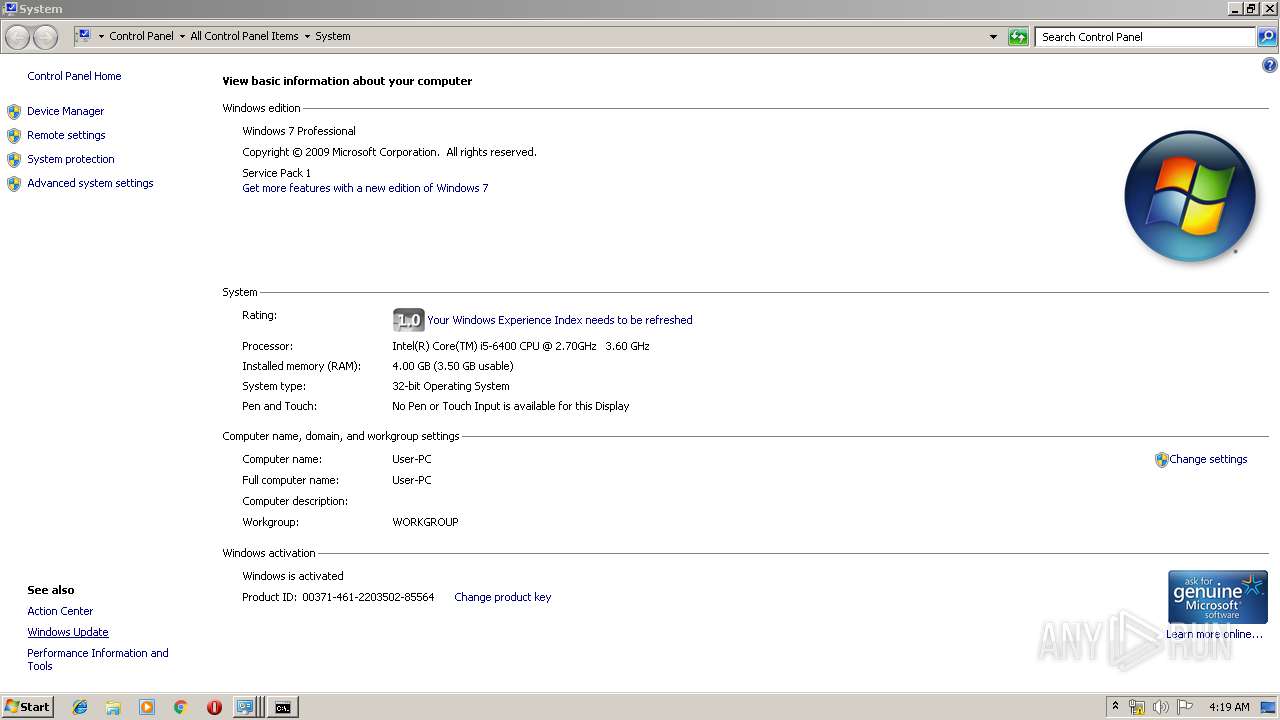
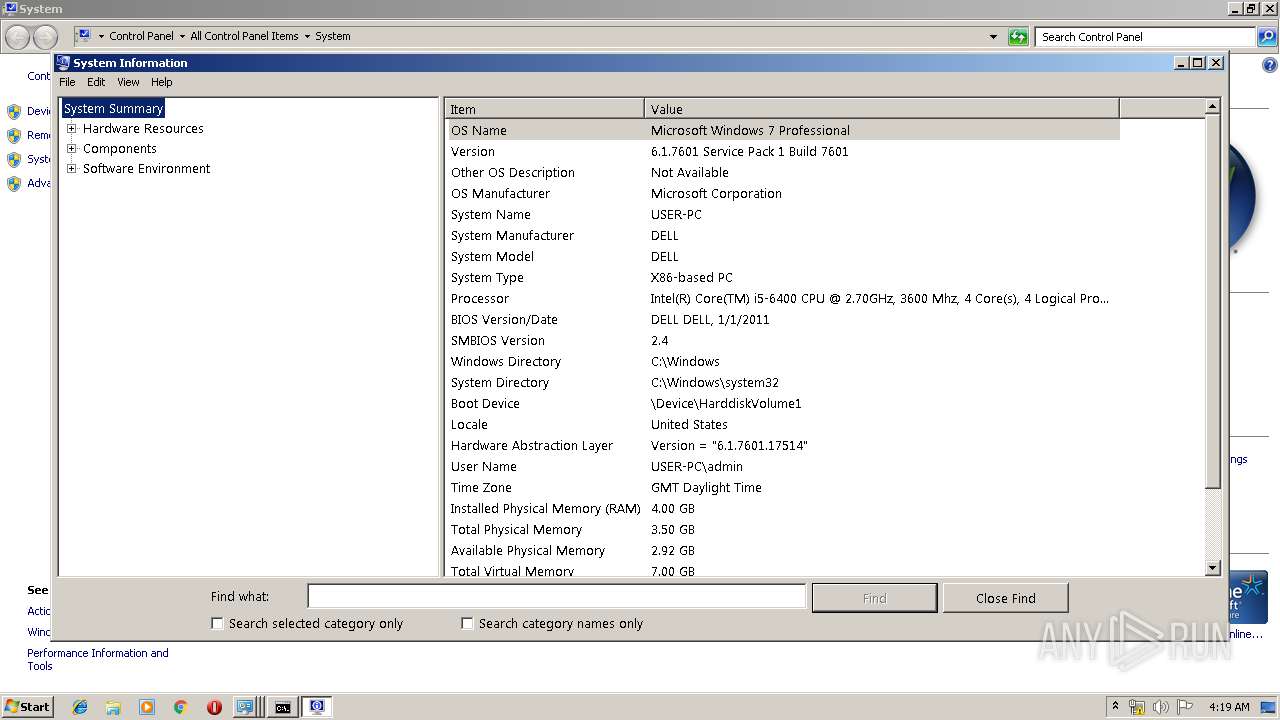
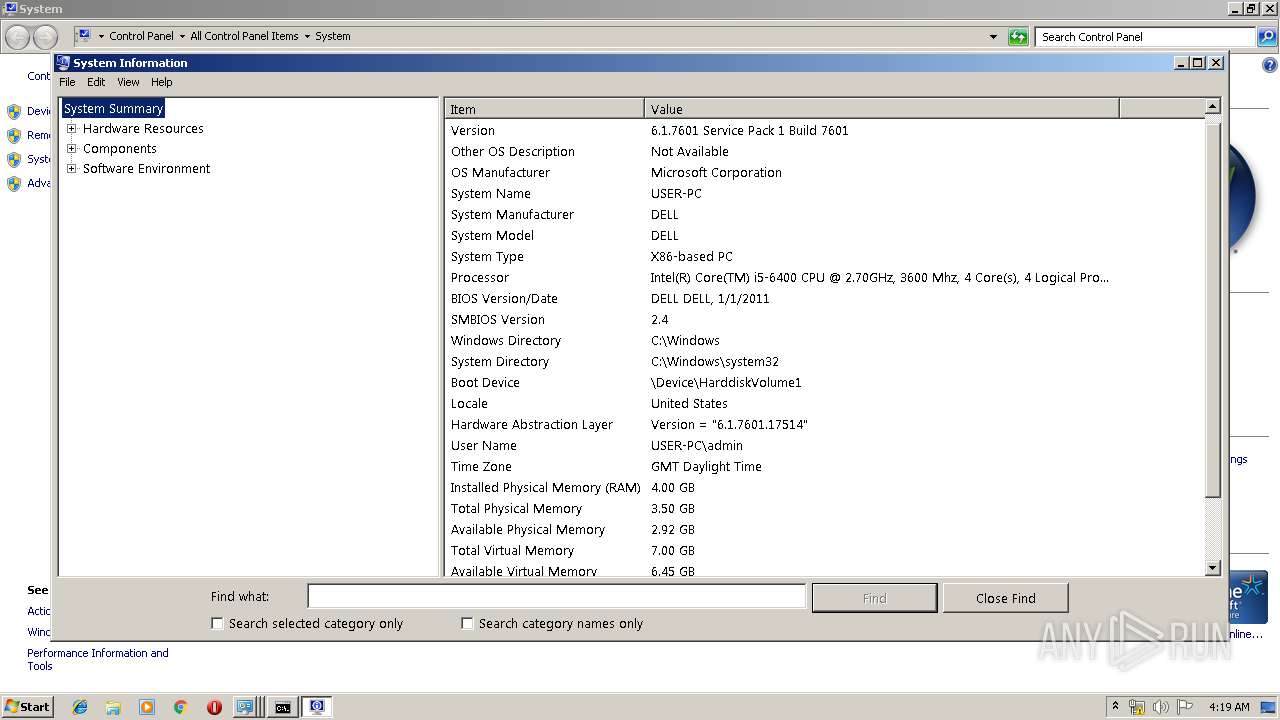
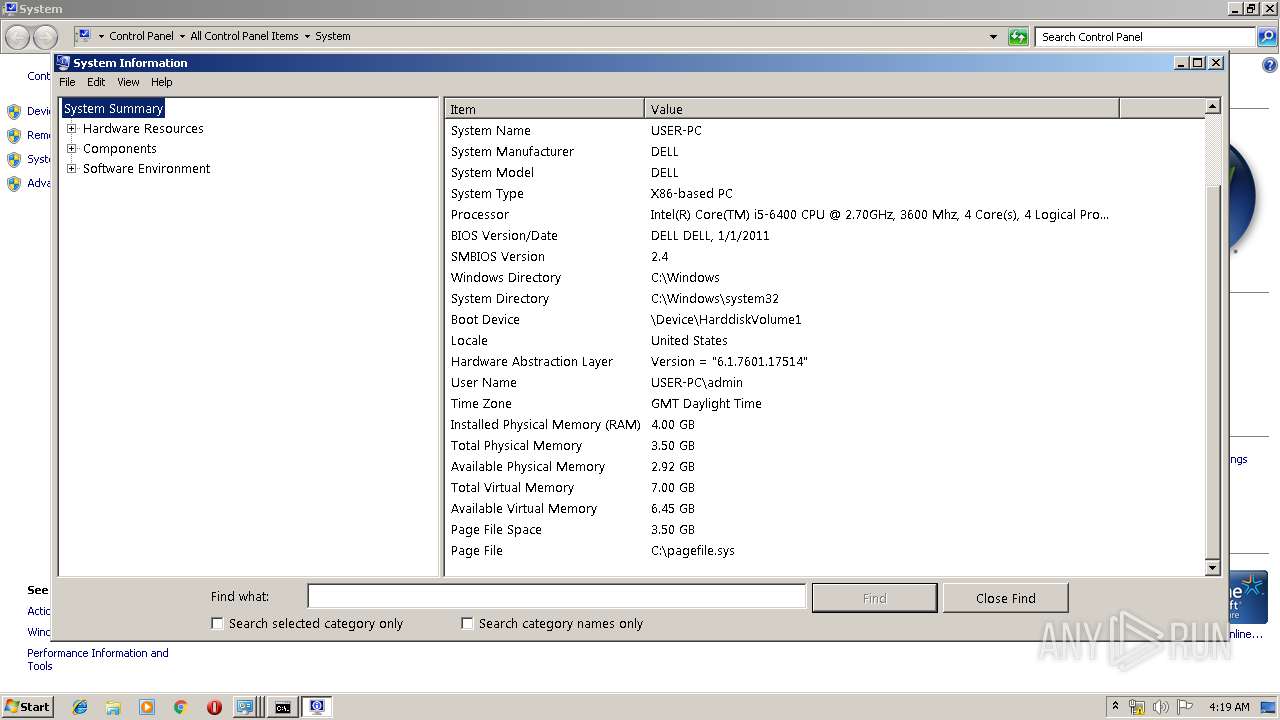
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B81BF51483EEBDCC24C5B805942759DE |
| SHA1: | 9FF01F11ABDB6C3A6196048B8838B702A8EB67D4 |
| SHA256: | 2909510A8F6C6A243469FD57FE3753A7D7C3D6474BE5E2E59548D62D58D65D8C |
| SSDEEP: | 12288:MEb2SrYcN/F+rx1t6tx/L6pyb+WupO/ar5ZTPQe+T/Kls/Jgbp8yle+Lri5zemnO:FZXubMpVZ5yMCPeHnOH2kEt6+K1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- s_9960.exe (PID: 2956)
Creates or modifies windows services
- s_9960.exe (PID: 2896)
Executed via COM
- DllHost.exe (PID: 3548)
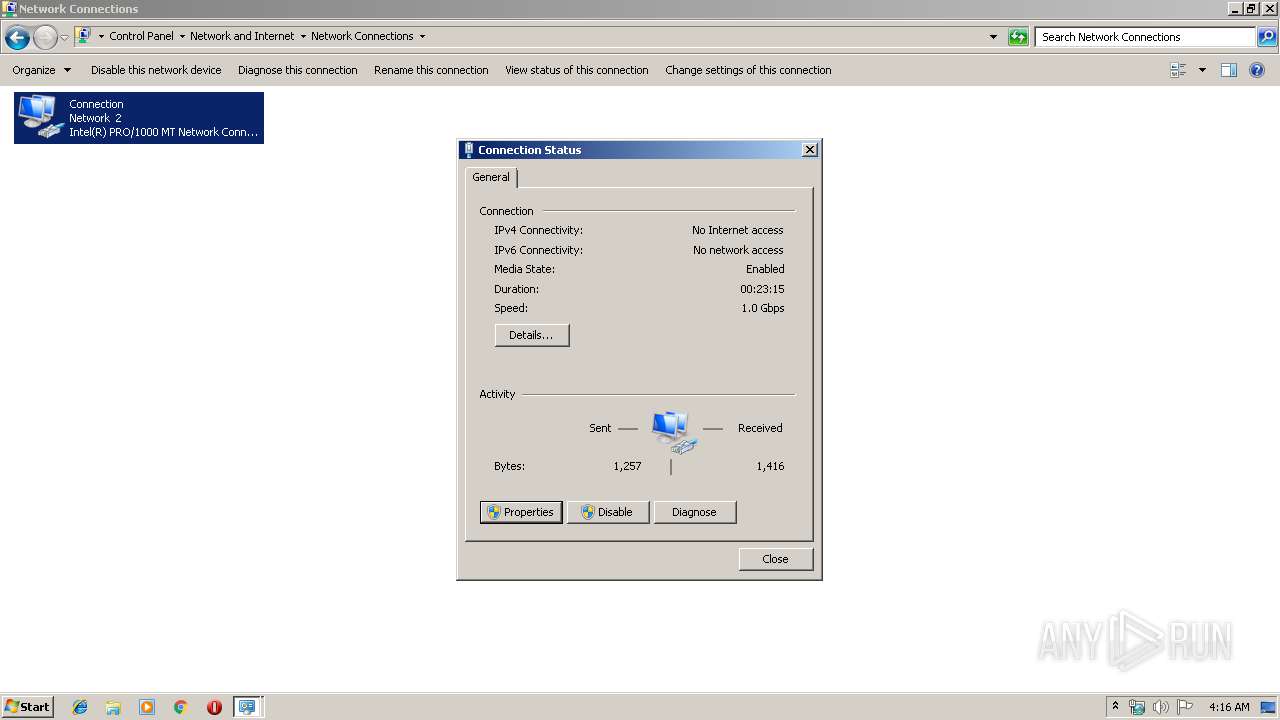
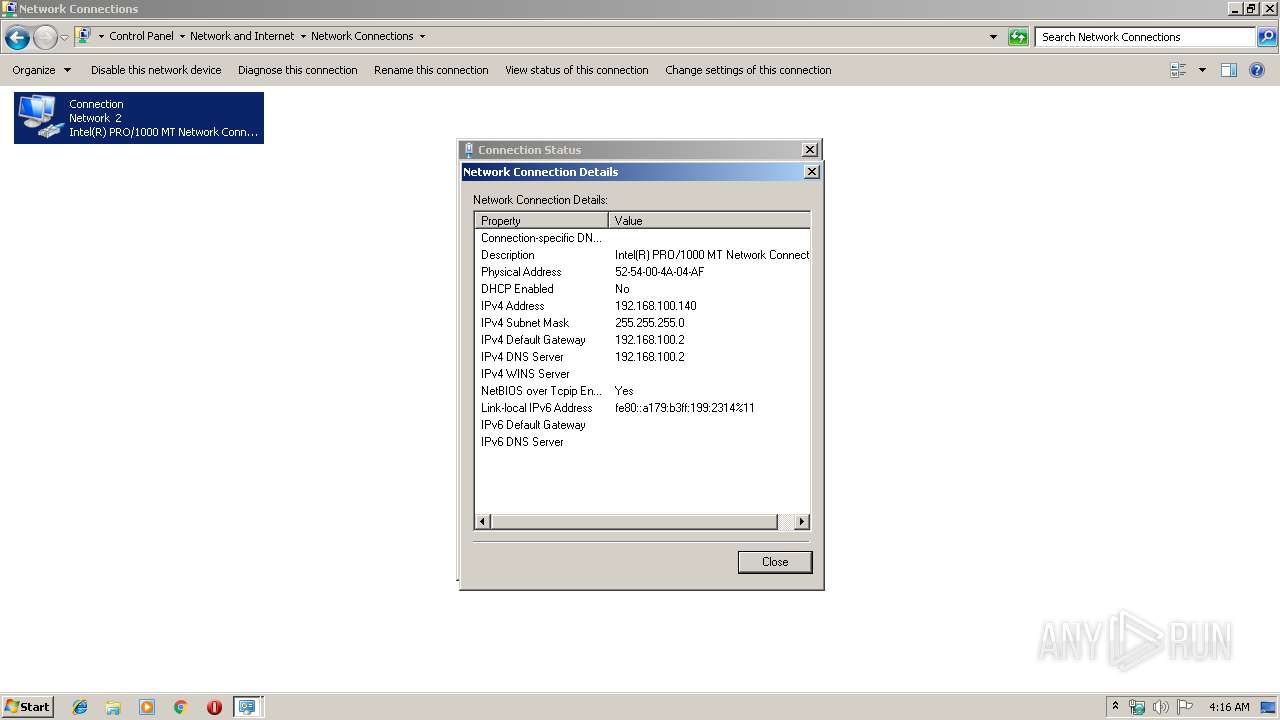
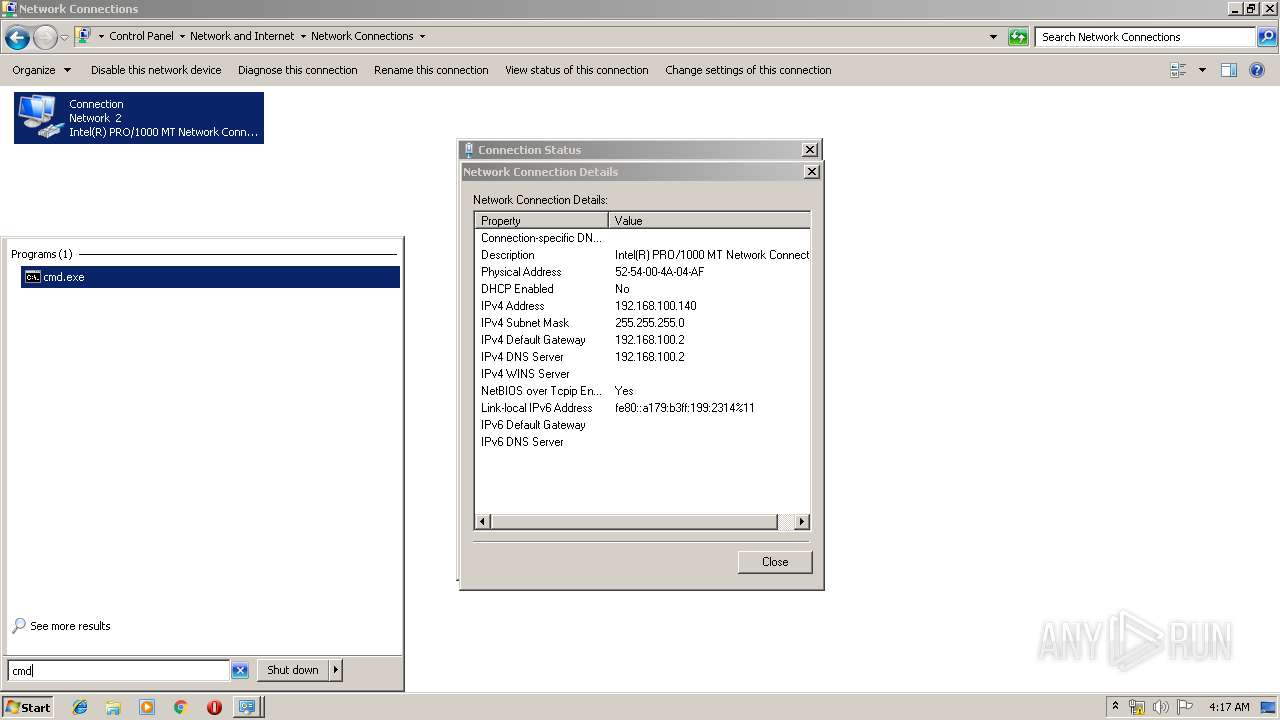
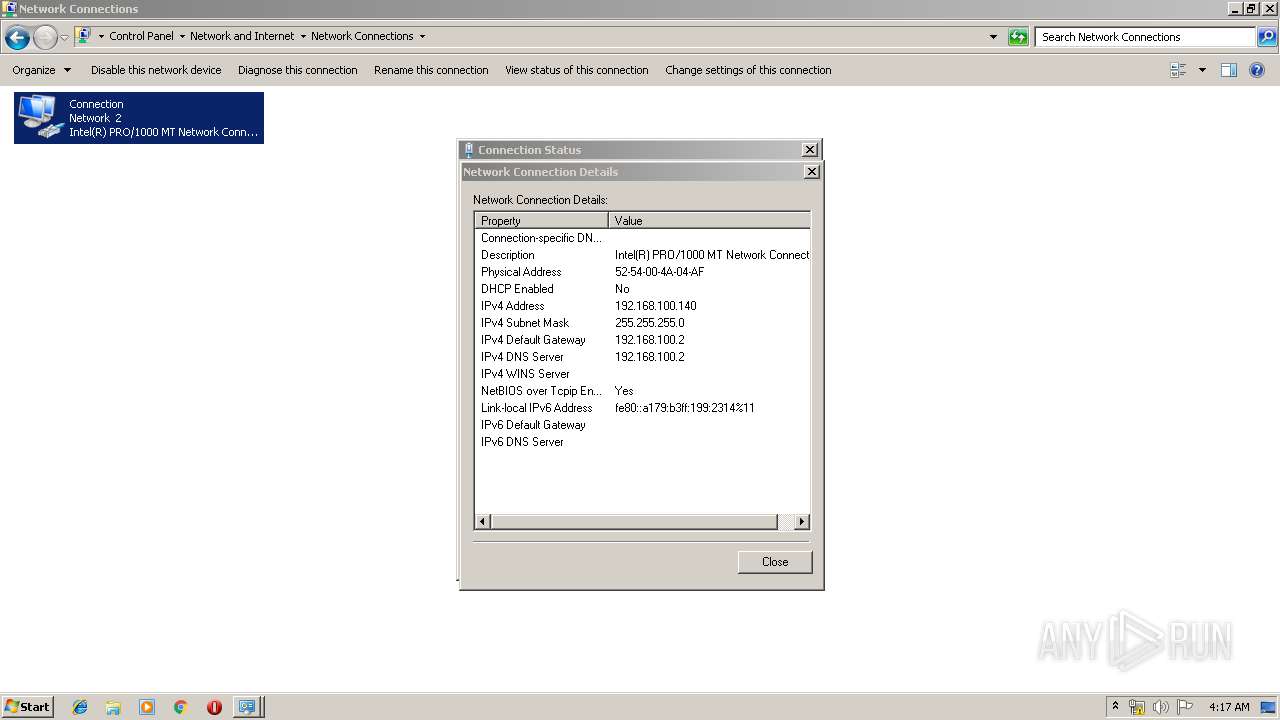
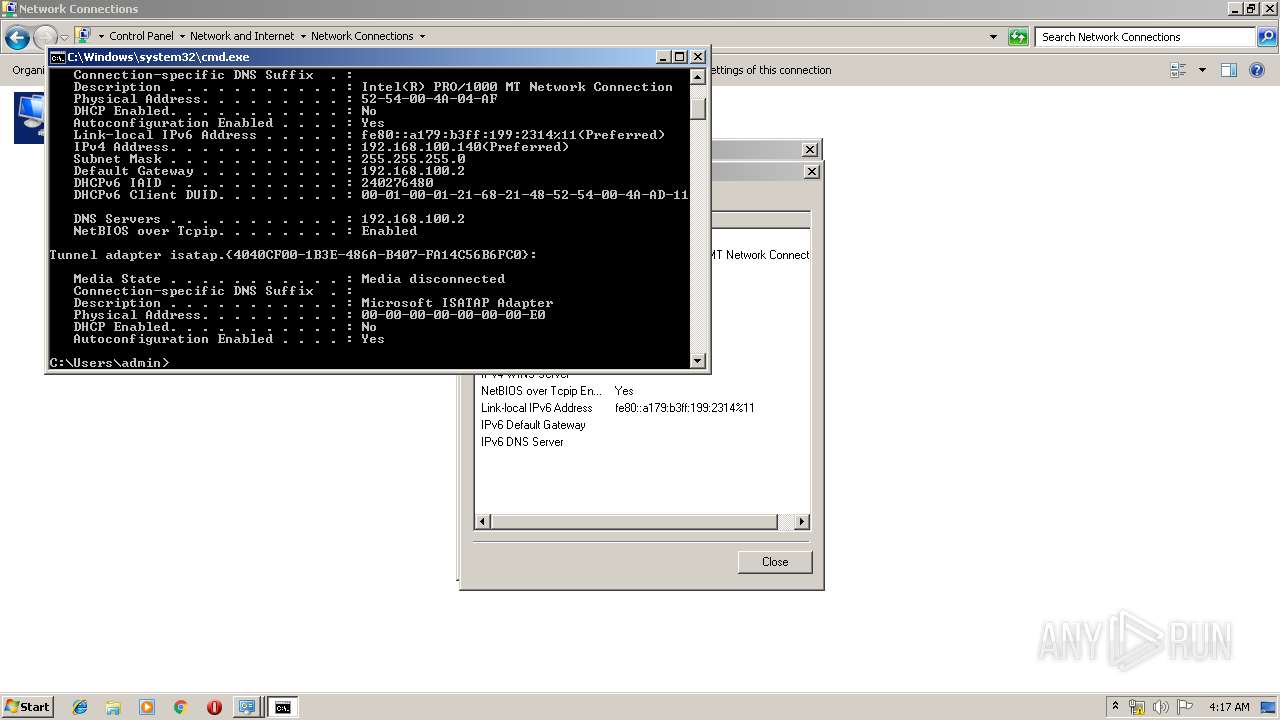
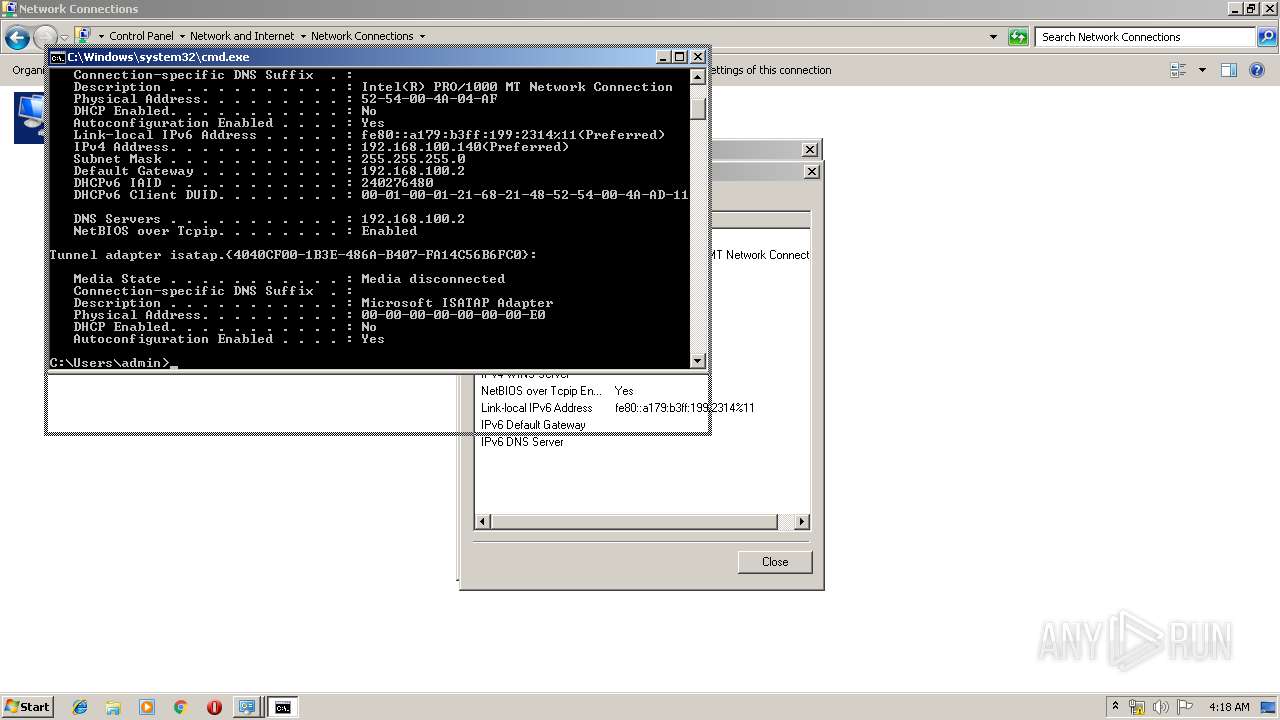
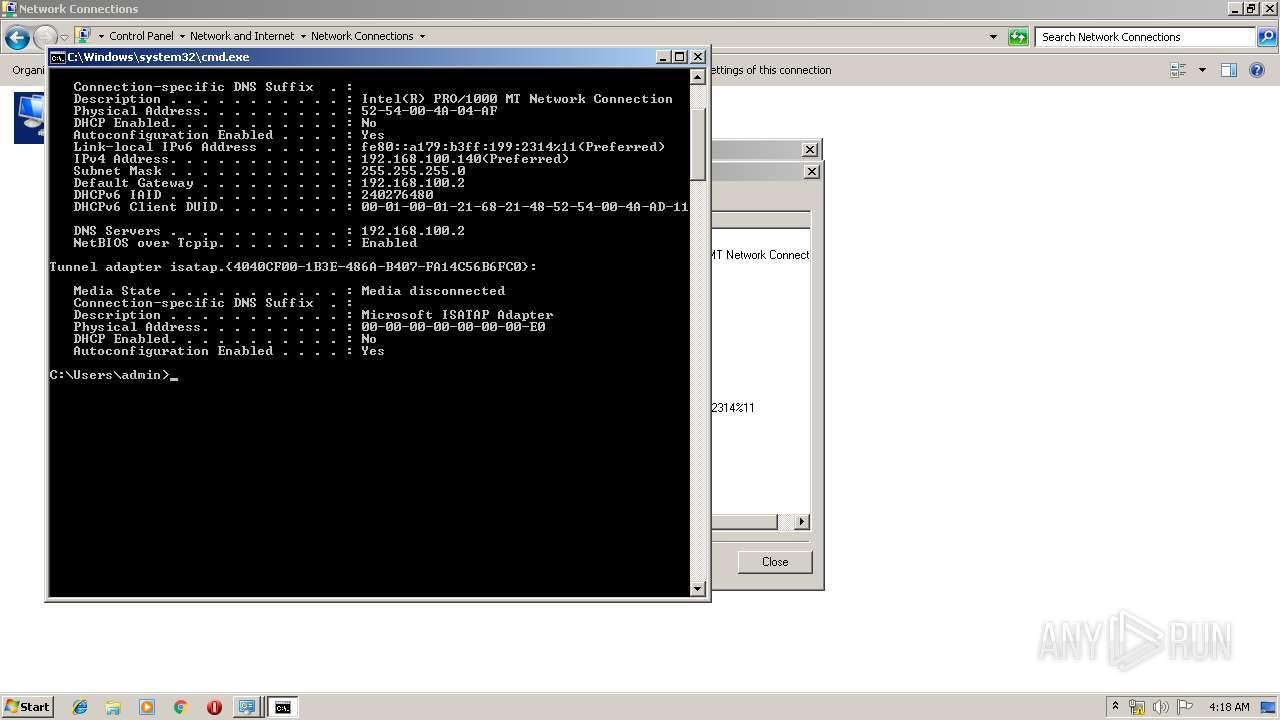
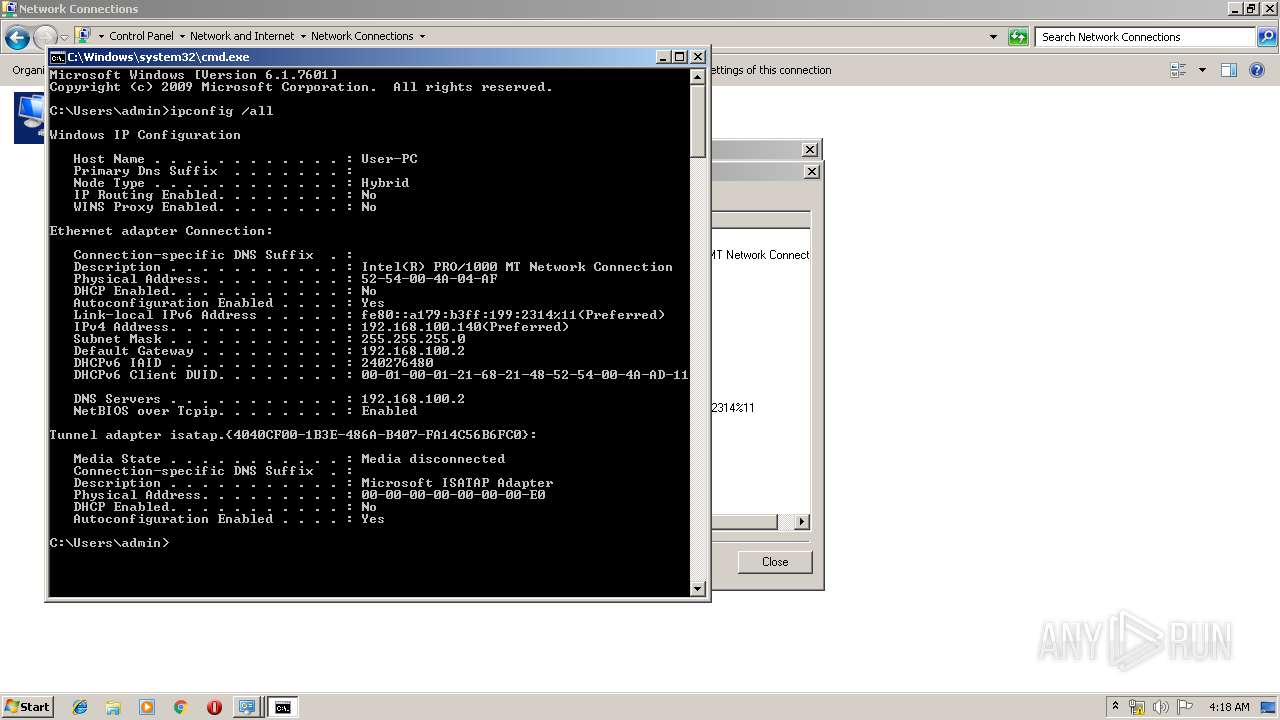
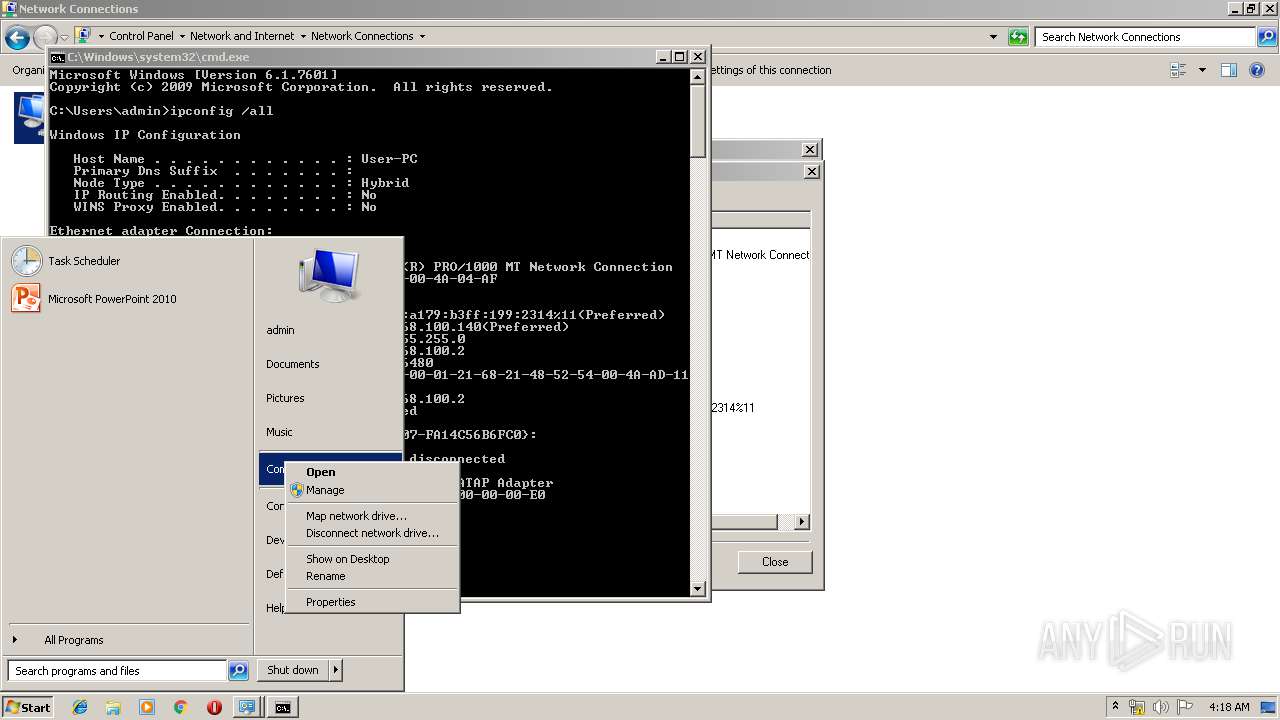
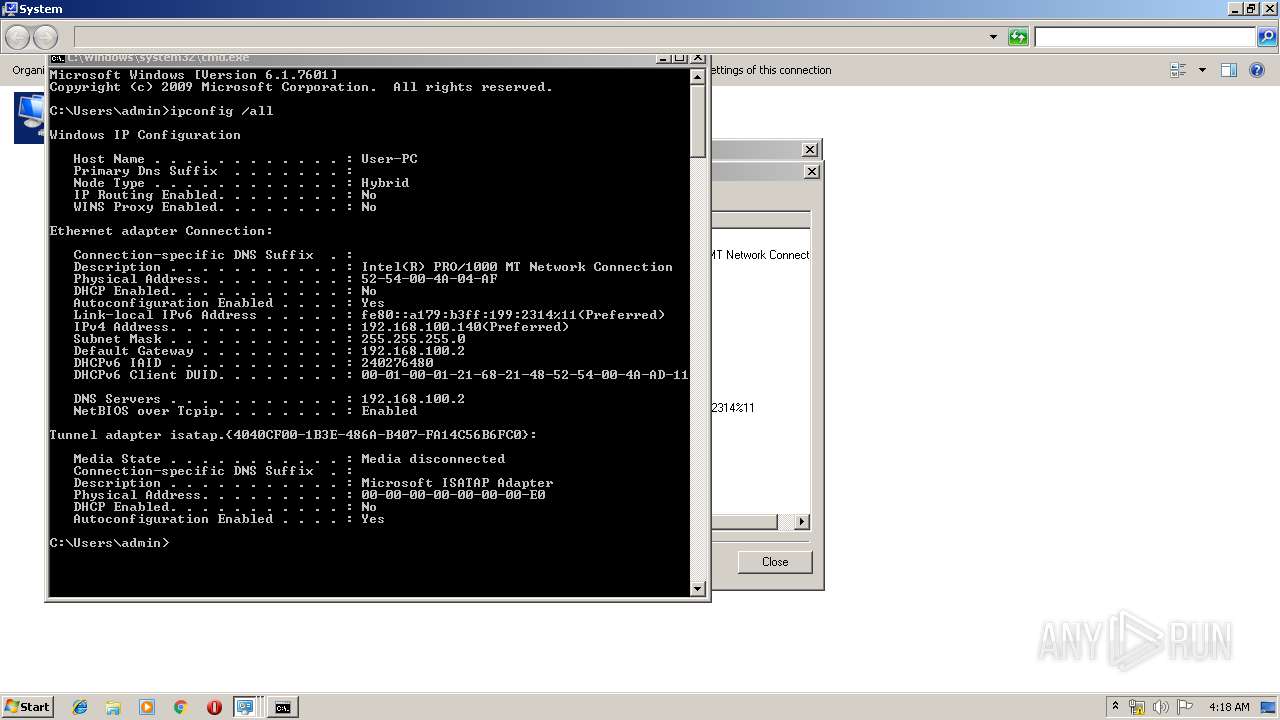
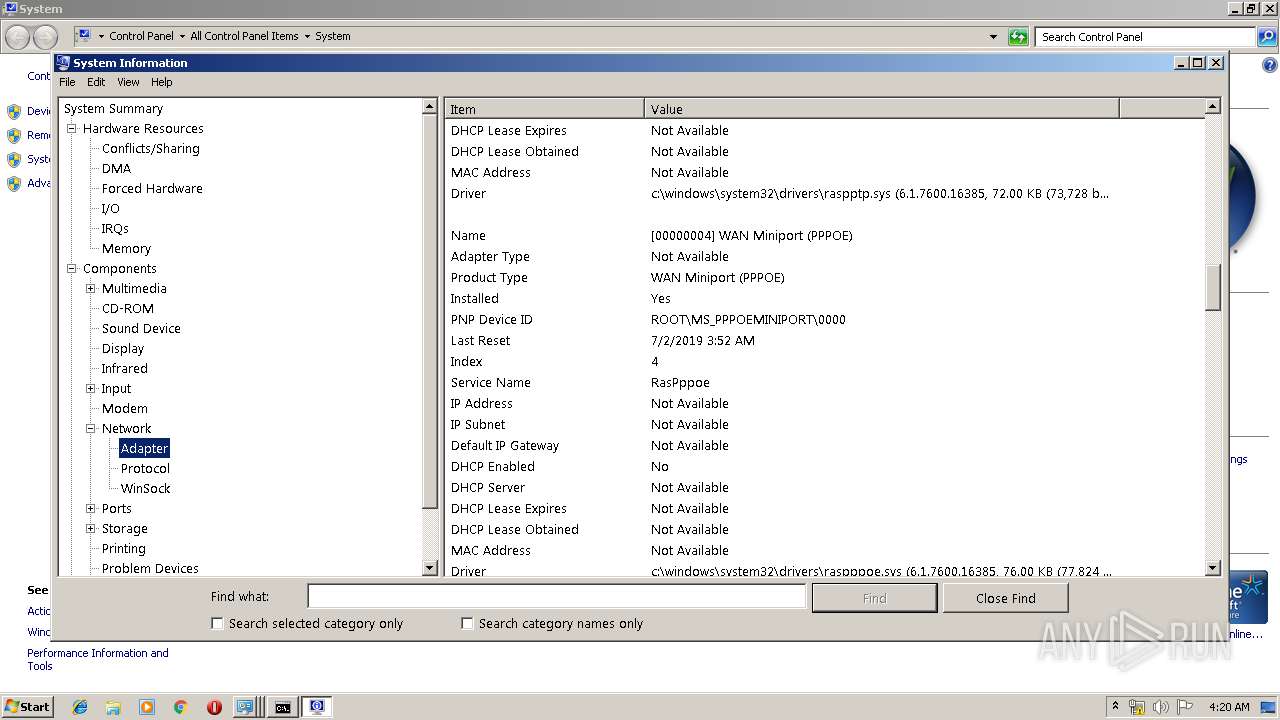
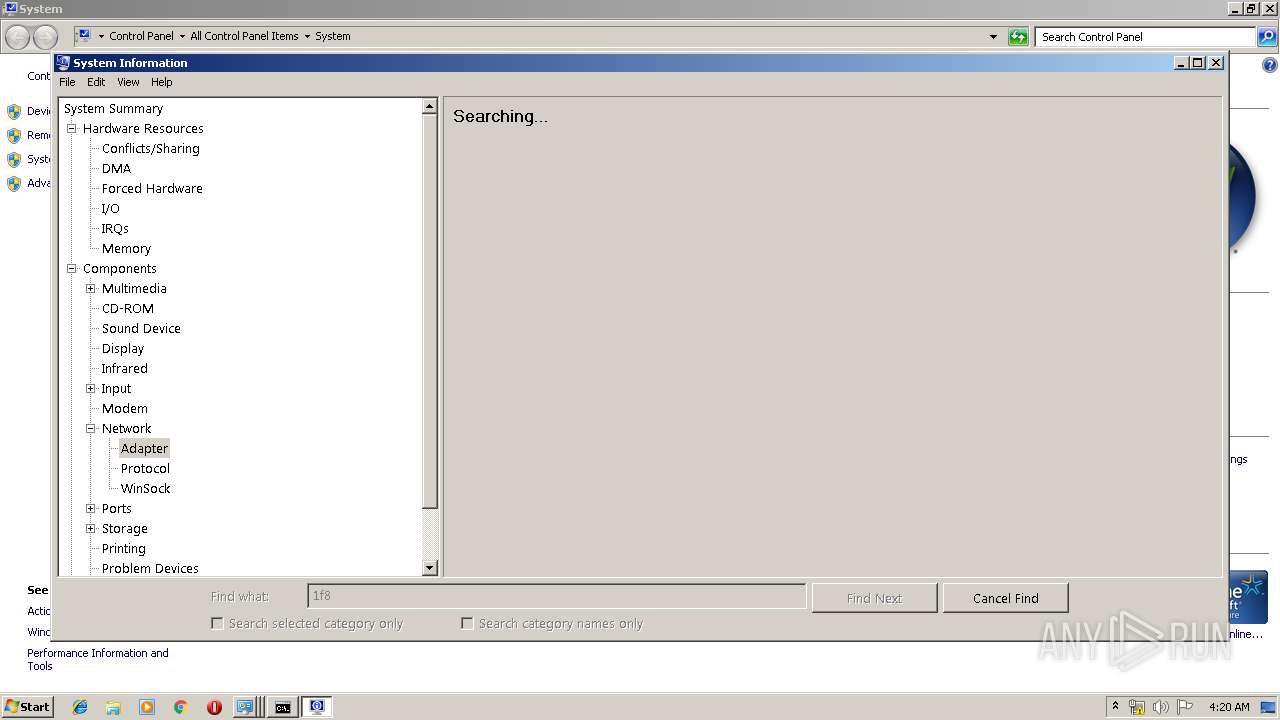
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3132)
INFO
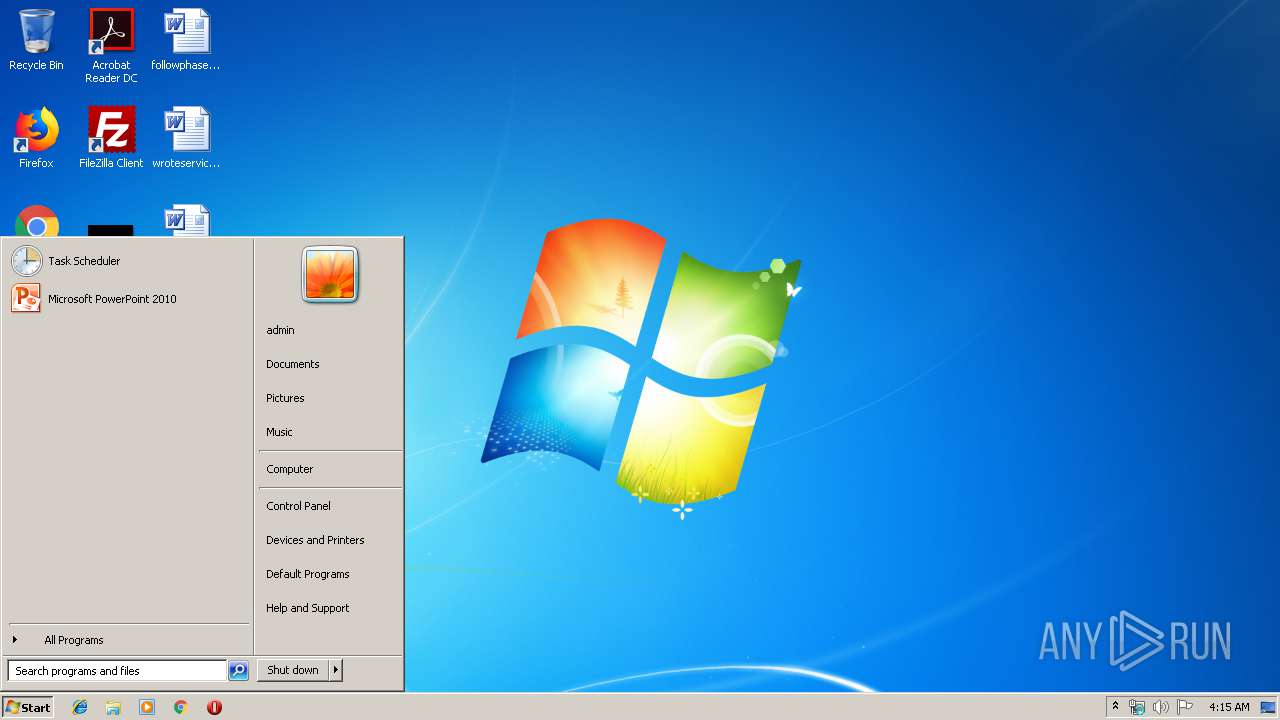
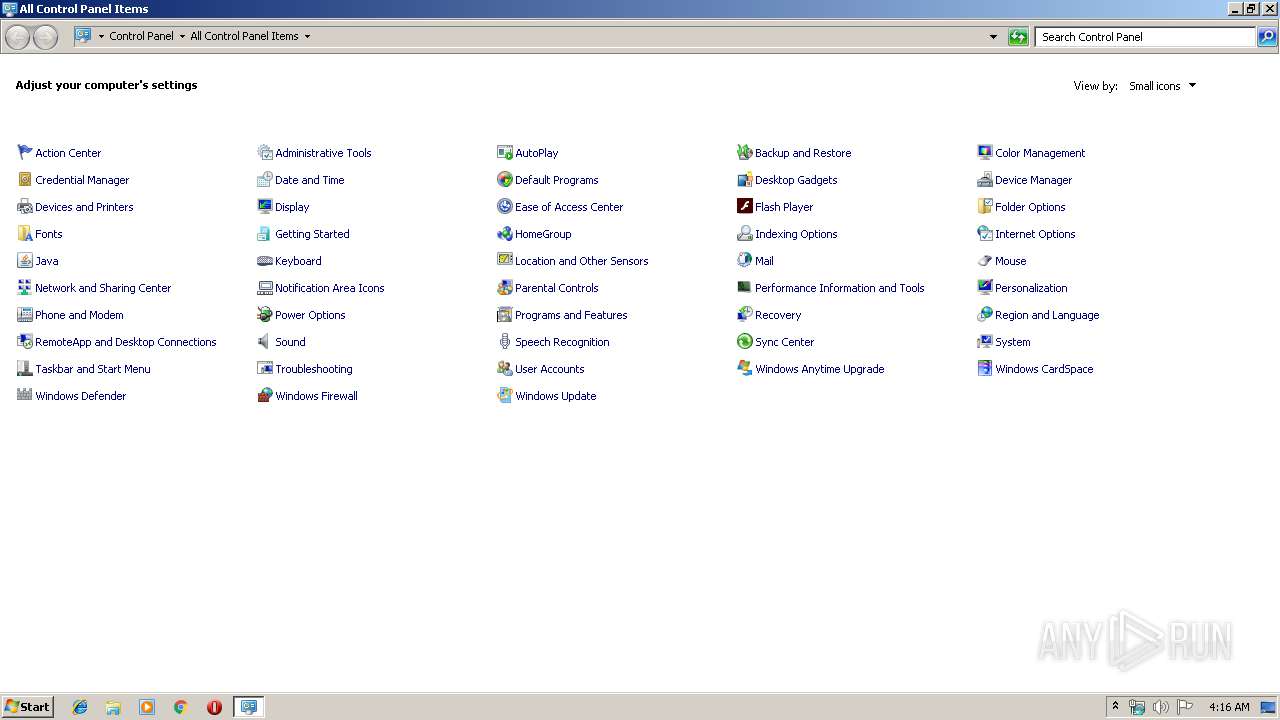
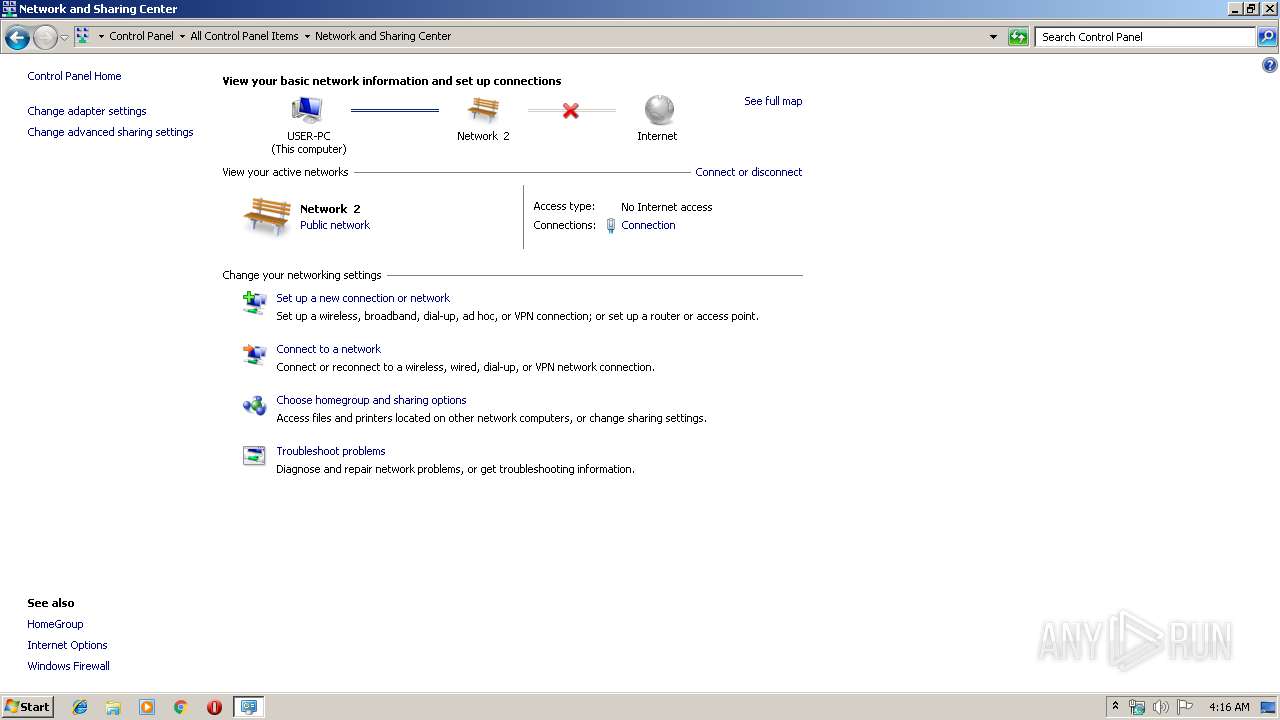
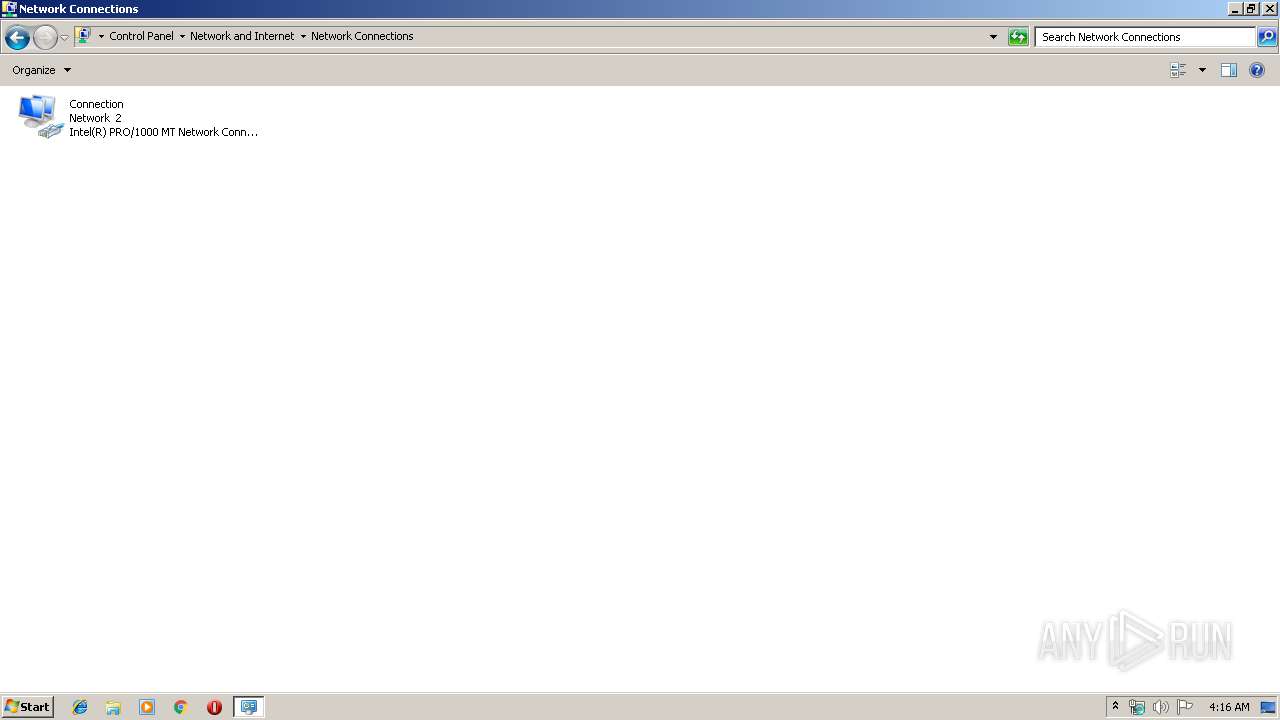
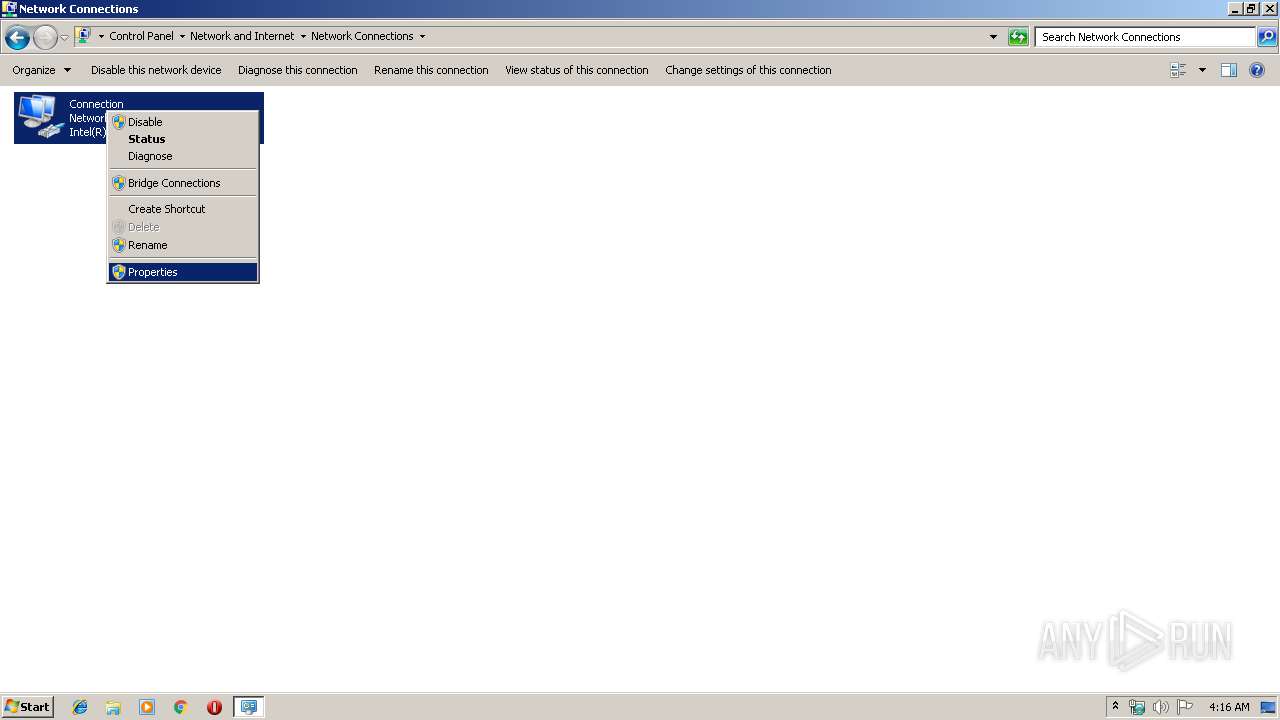
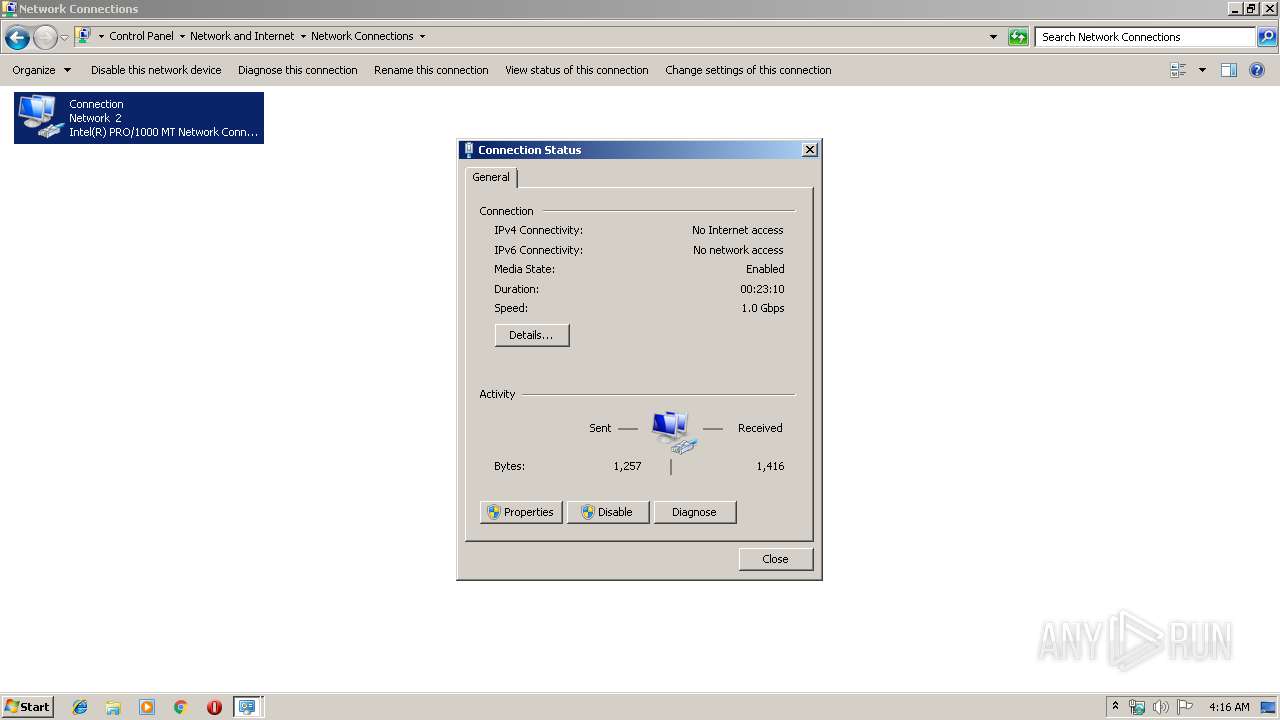
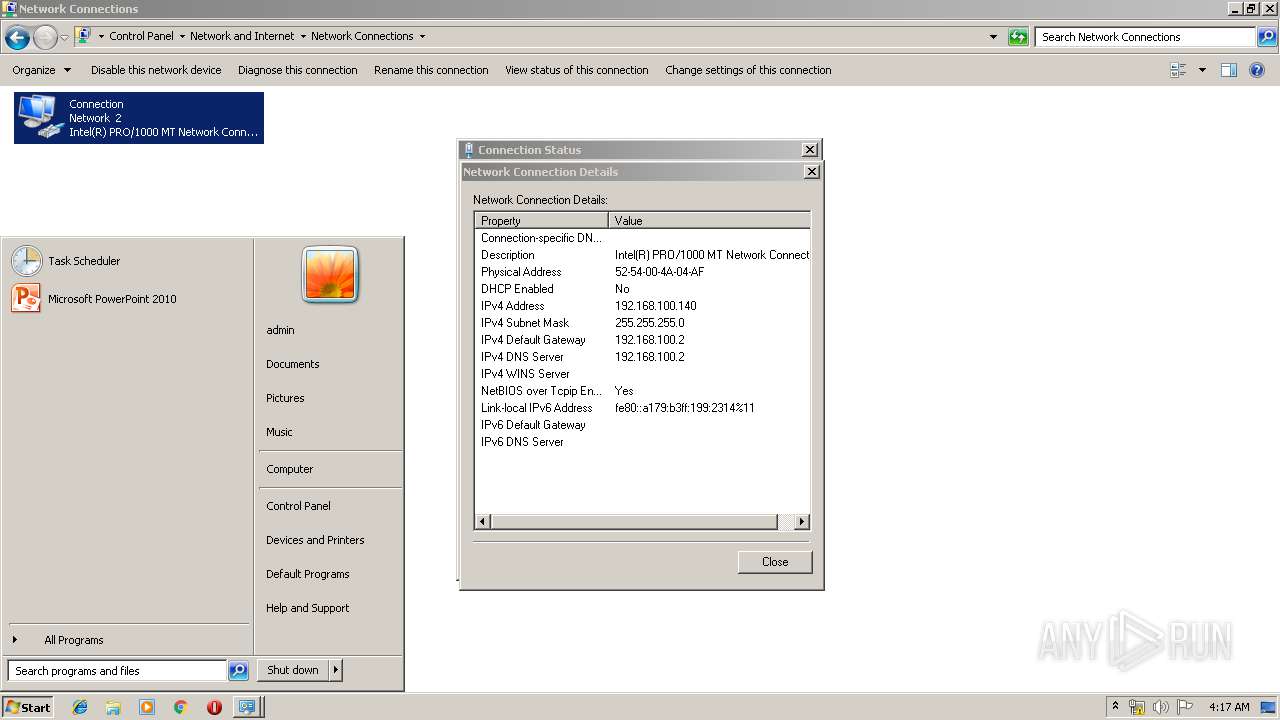
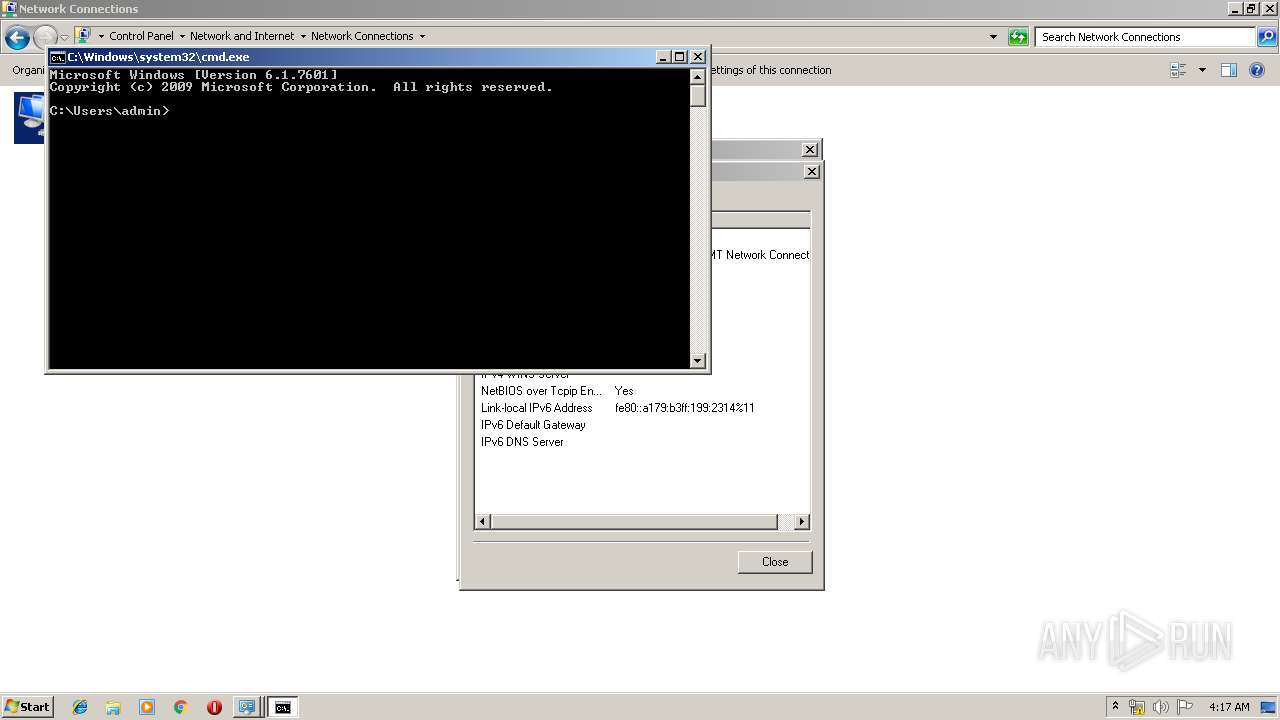
Manual execution by user
- control.exe (PID: 1656)
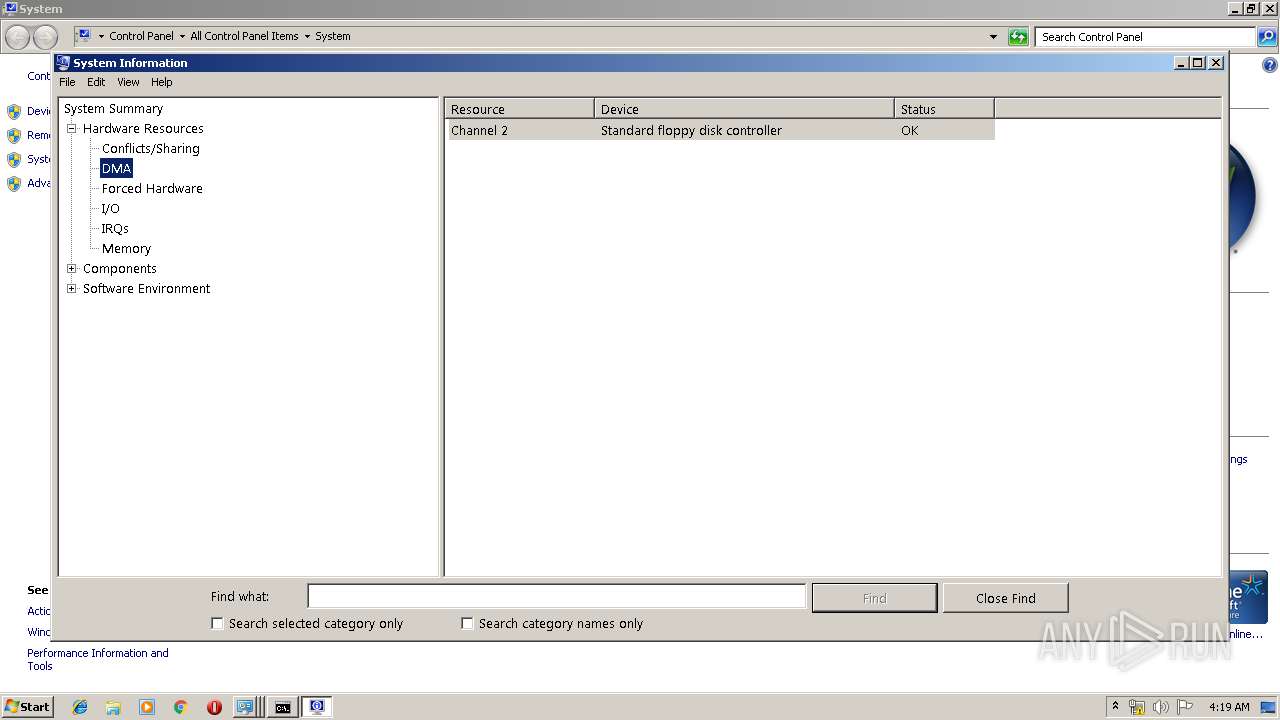
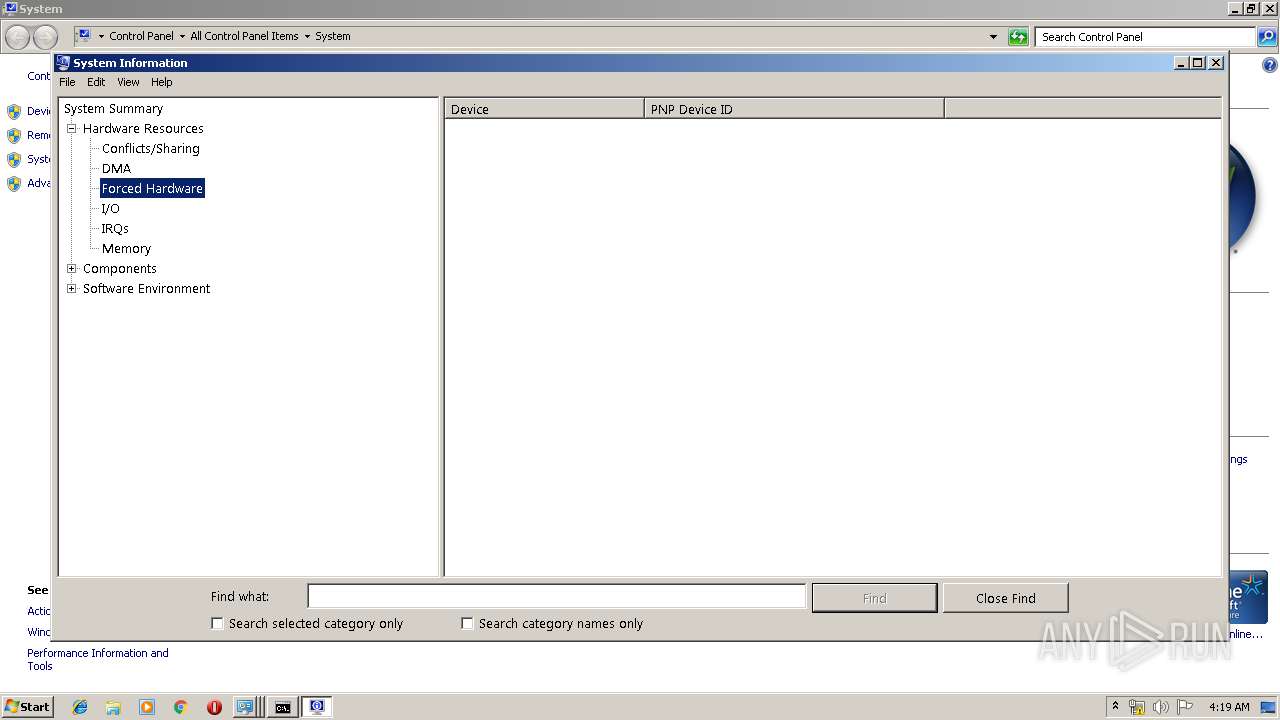
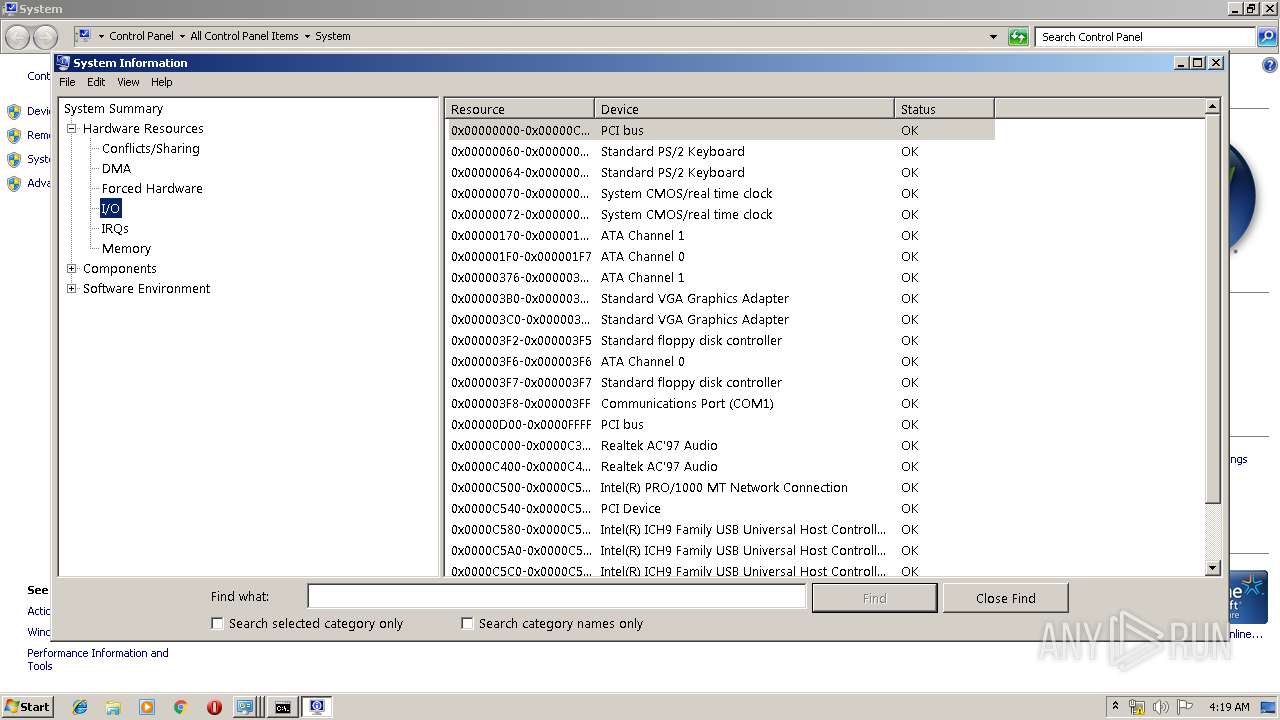
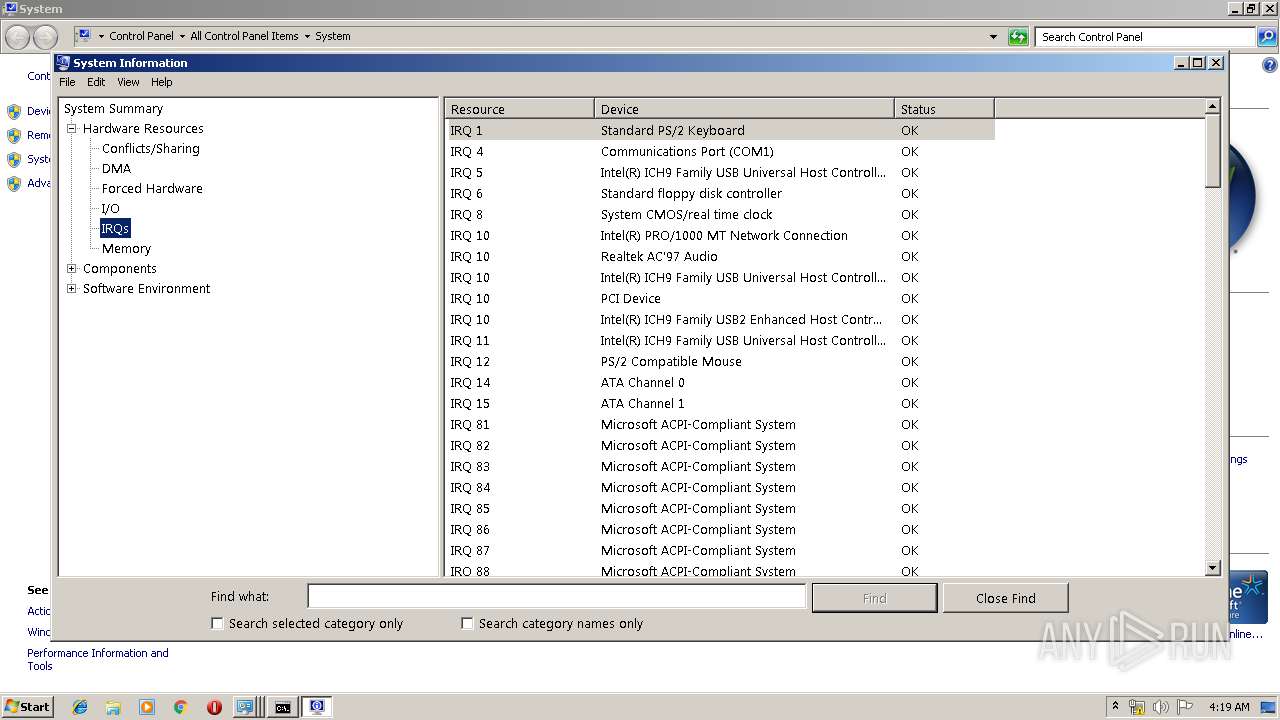
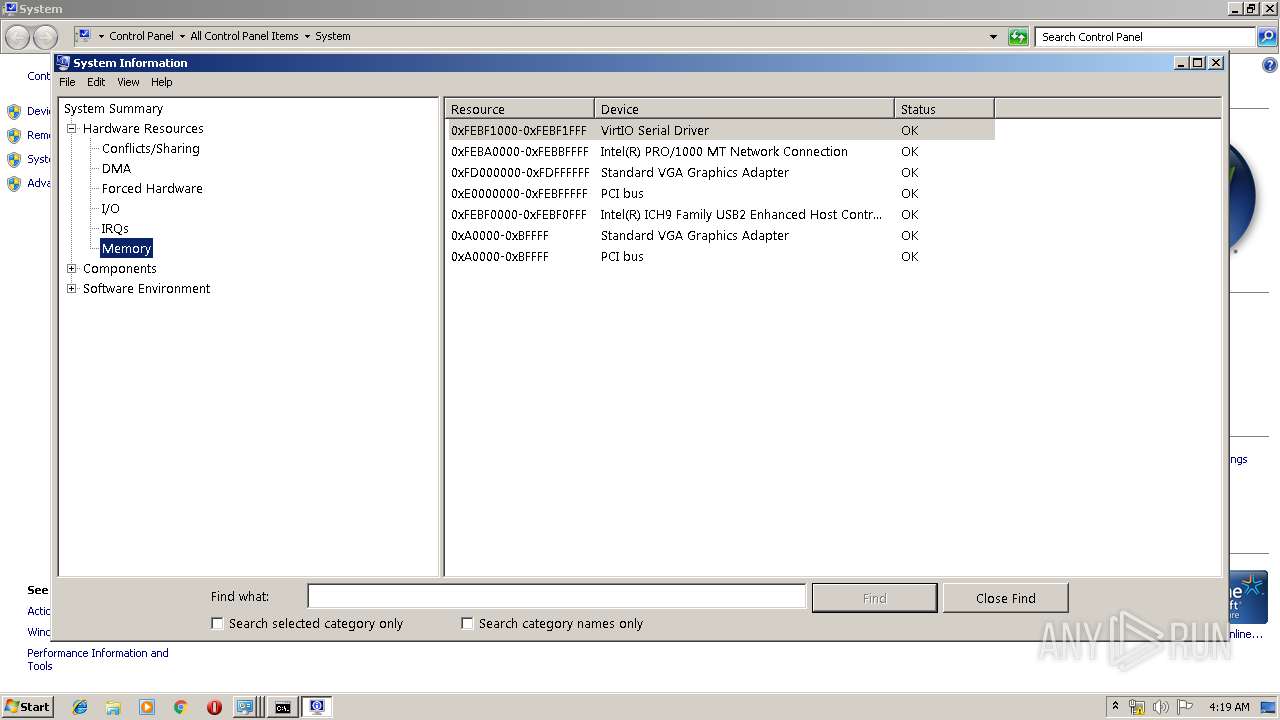
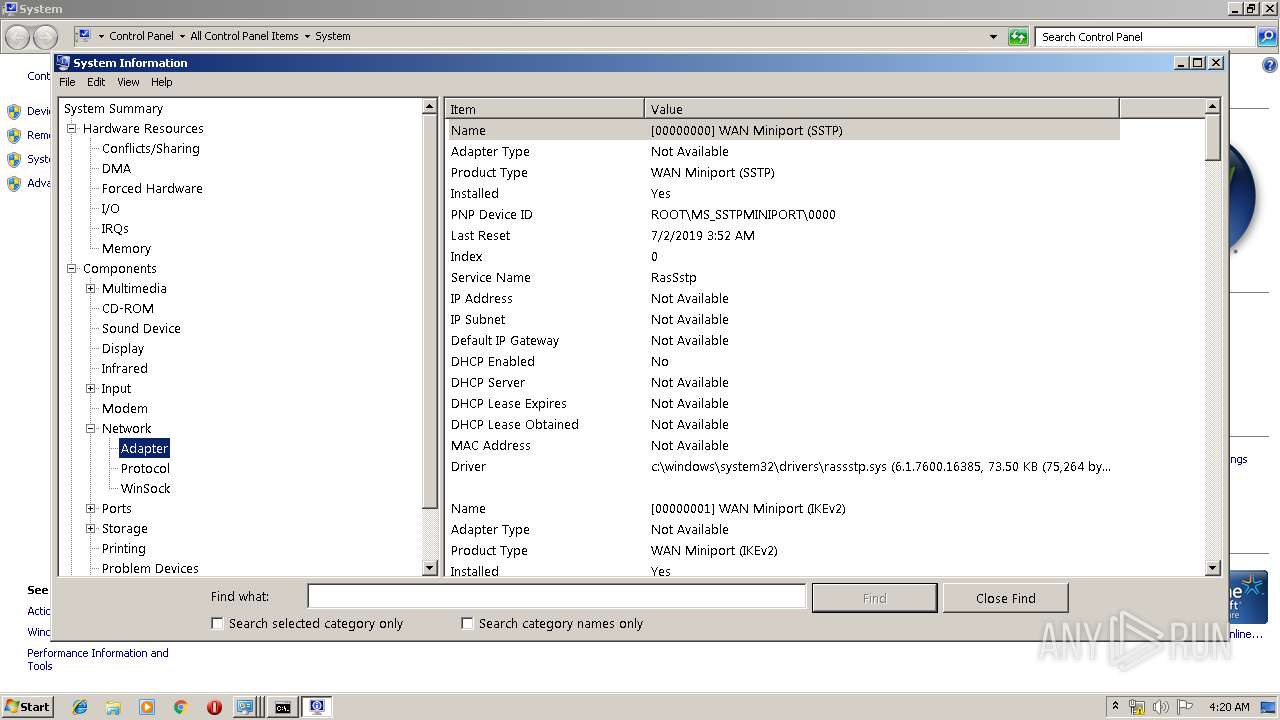
- msinfo32.exe (PID: 3136)
- cmd.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:25 05:34:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 73728 |
| InitializedDataSize: | 1165312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3b1e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.1 |
| LegalCopyright: | Copyright (C) 2017 |
| ProductVersion: | 1.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2019 03:34:02 |
| Detected languages: |
|
| FileVersion: | 1.0.0.1 |
| LegalCopyright: | Copyright (C) 2017 |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jun-2019 03:34:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011FEA | 0x00012000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65724 |
.rdata | 0x00013000 | 0x00005E84 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71546 |
.data | 0x00019000 | 0x00006080 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59173 |
.rsrc | 0x00020000 | 0x0010F188 | 0x0010F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88217 |
.reloc | 0x00130000 | 0x00001298 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.43037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 7.85639 | 500224 | UNKNOWN | Chinese - PRC | BIN |
103 | 7.86004 | 569864 | UNKNOWN | Chinese - PRC | BIN |
104 | 6.57151 | 17784 | UNKNOWN | Chinese - PRC | BIN |
105 | 6.35206 | 21368 | UNKNOWN | Chinese - PRC | BIN |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
WS2_32.dll |
mscoree.dll |
ntdll.dll |
Total processes
51
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | s_9960.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | s_9960.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\s_9960.exe" --RUNMAIN | C:\Users\admin\AppData\Local\Temp\s_9960.exe | s_9960.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\s_9960.exe" | C:\Users\admin\AppData\Local\Temp\s_9960.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3132 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
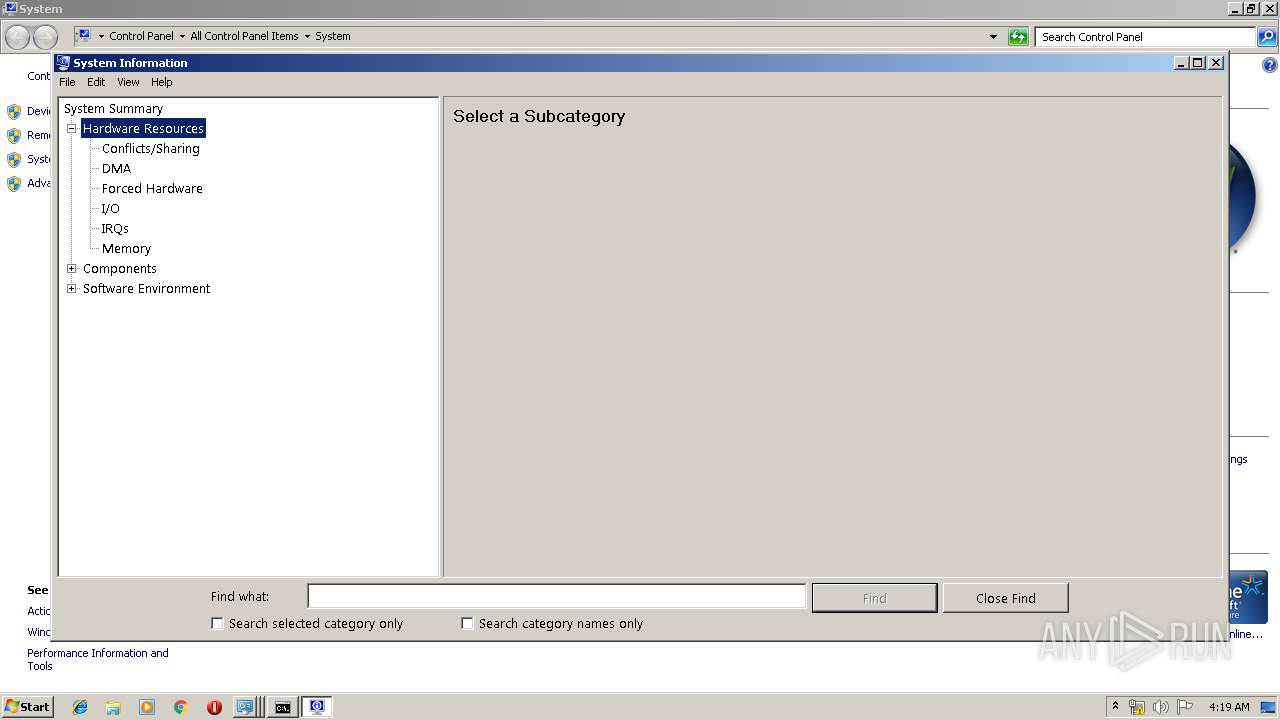
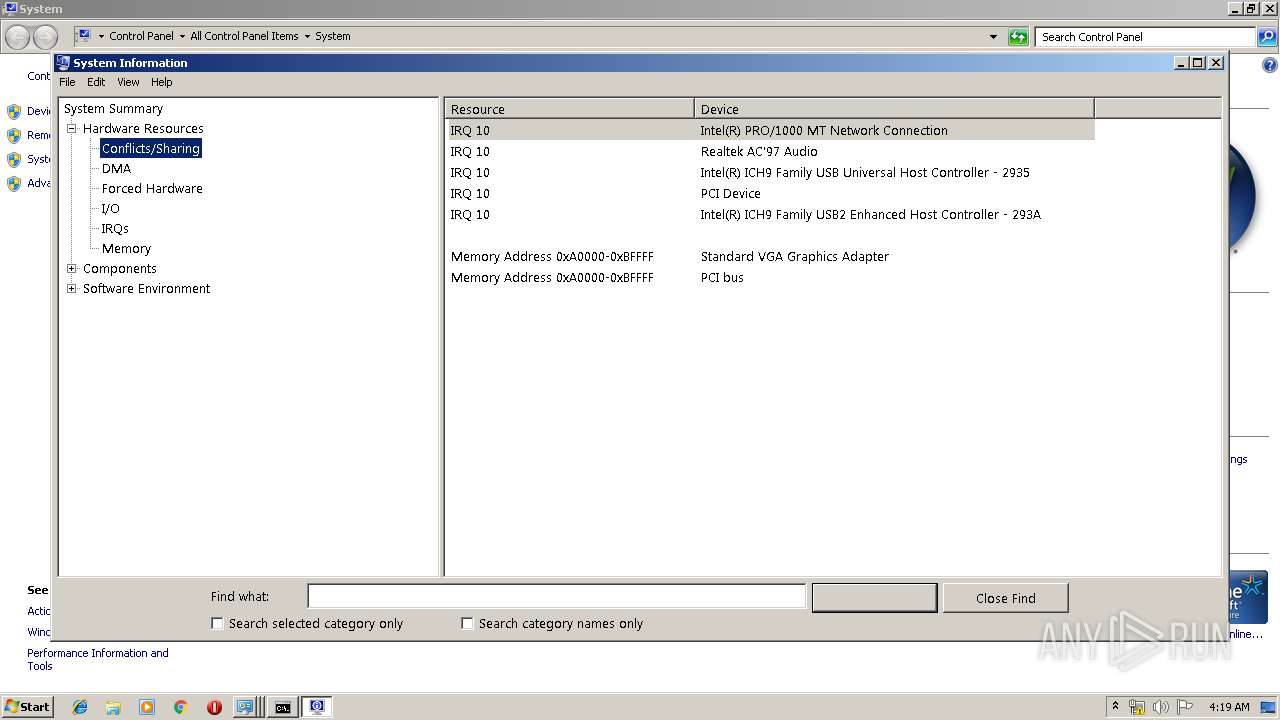
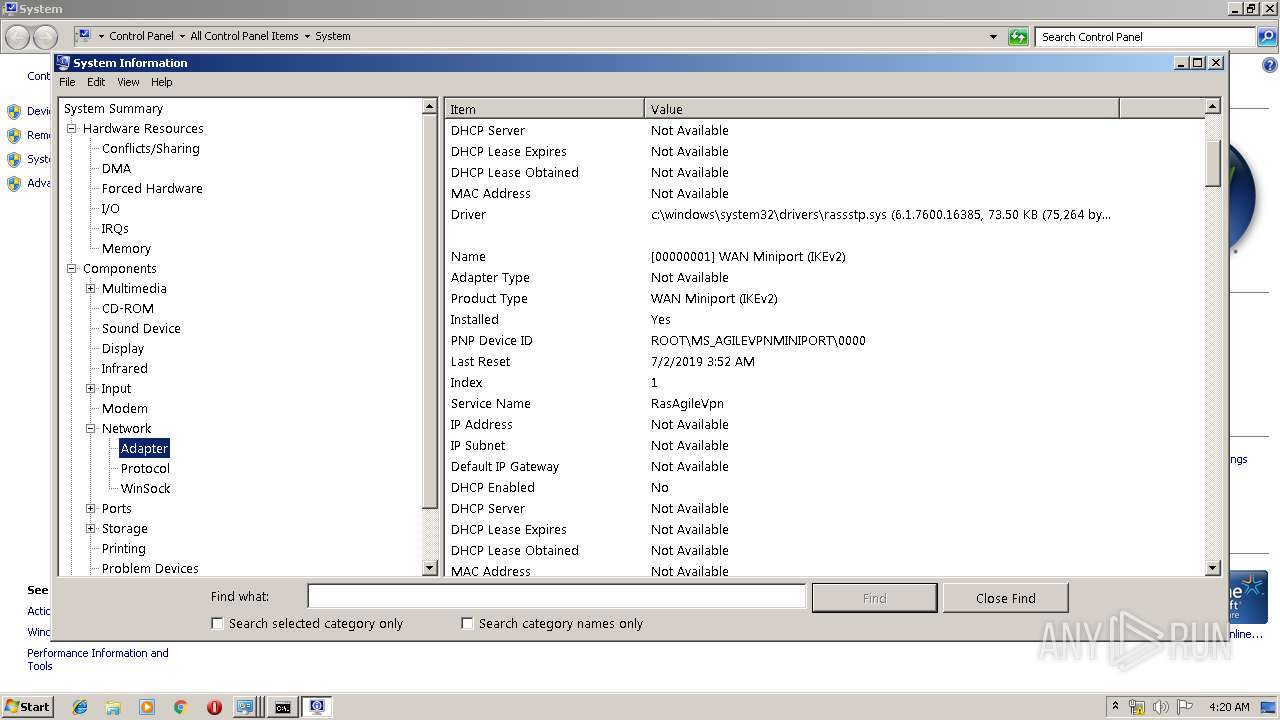
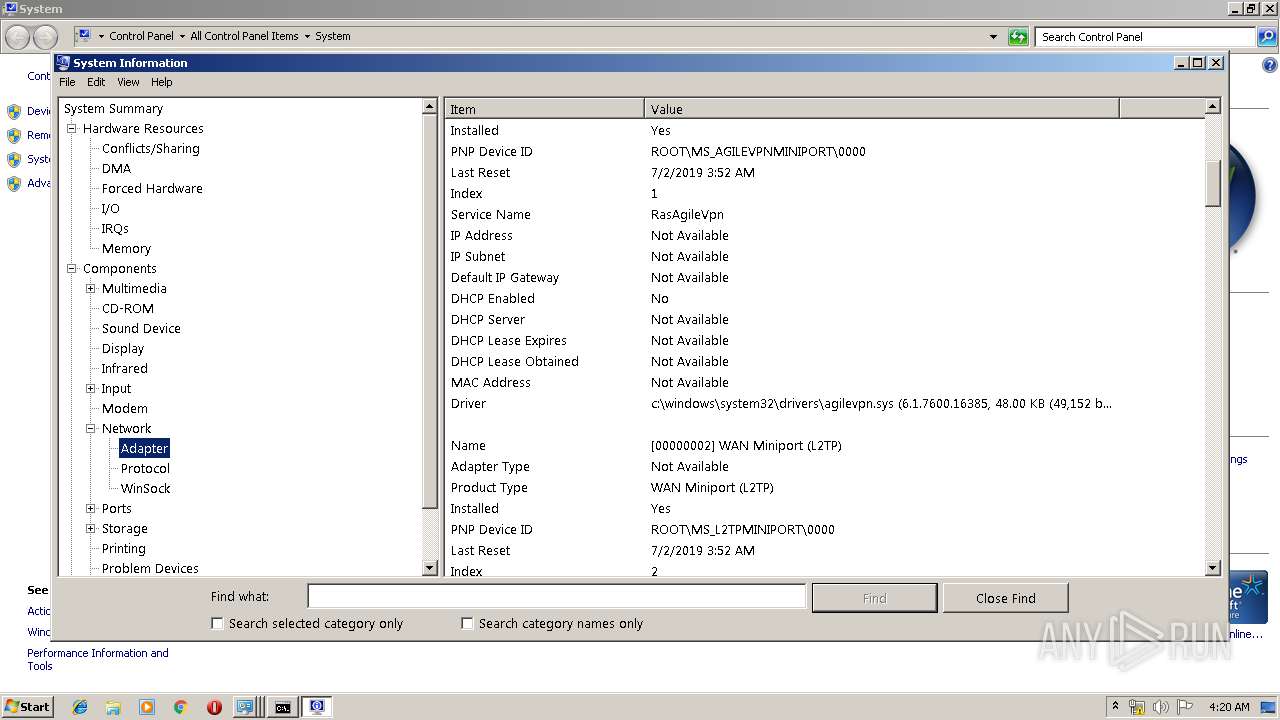
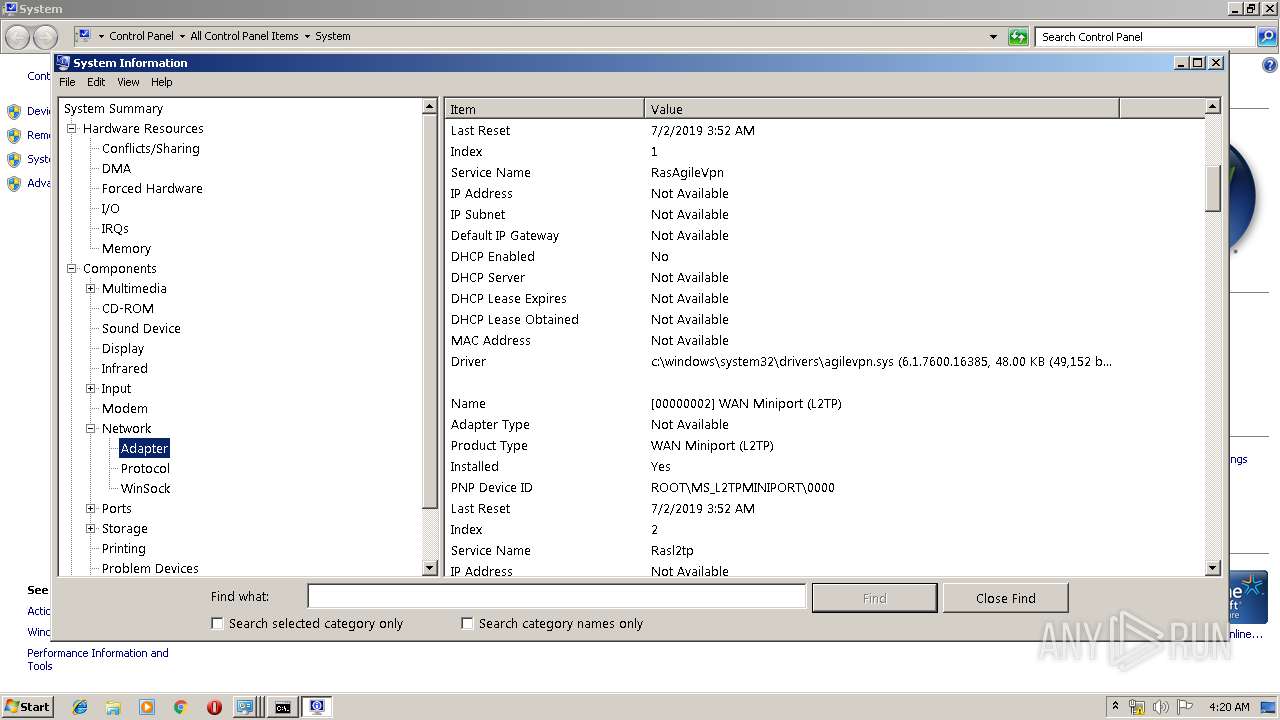
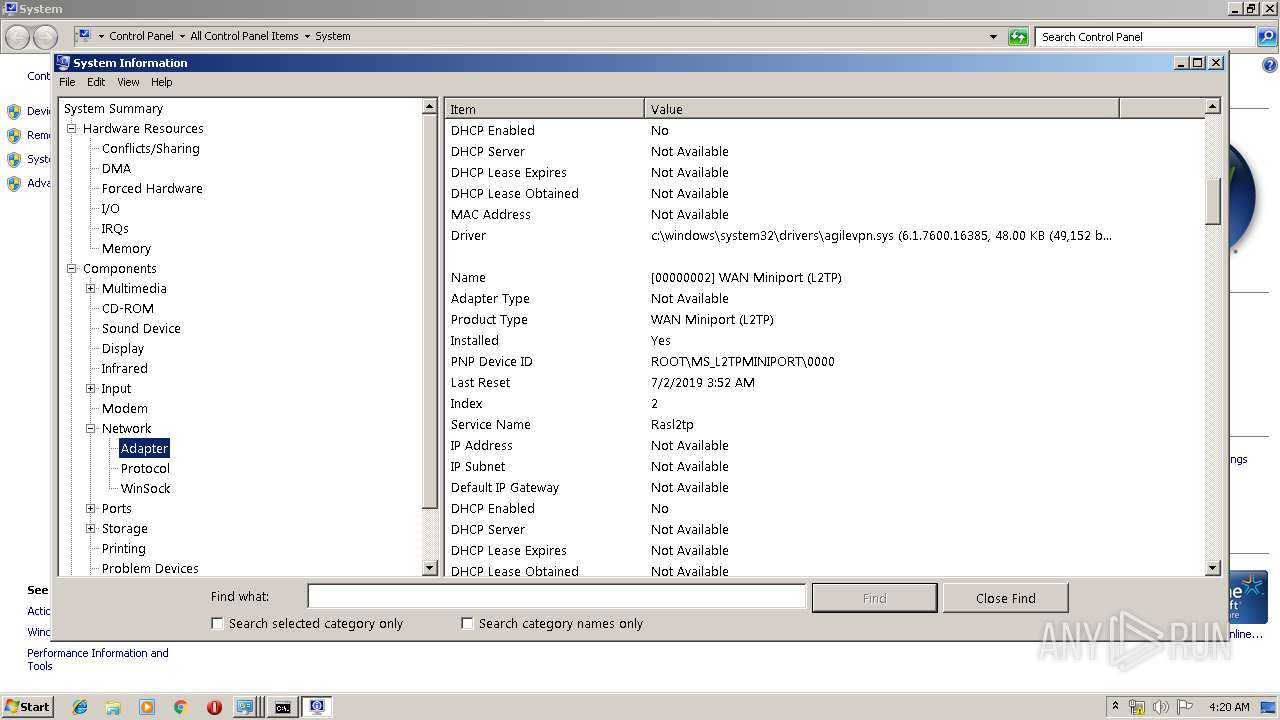
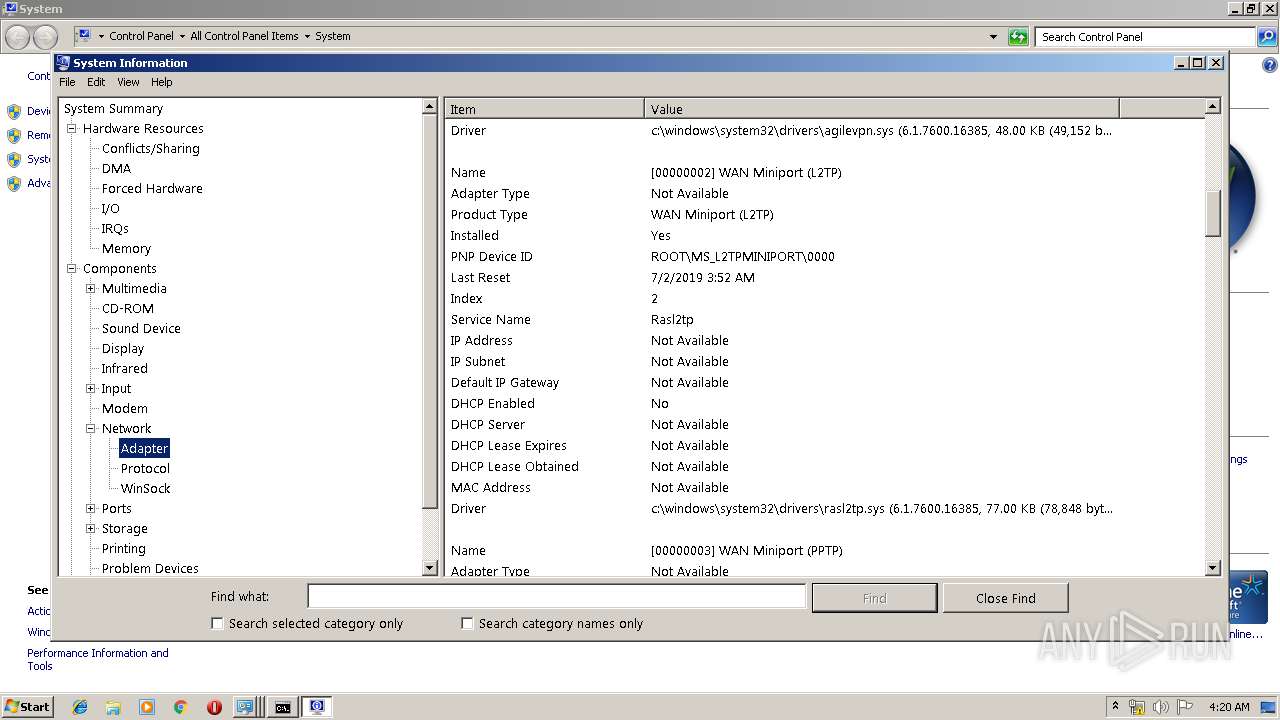
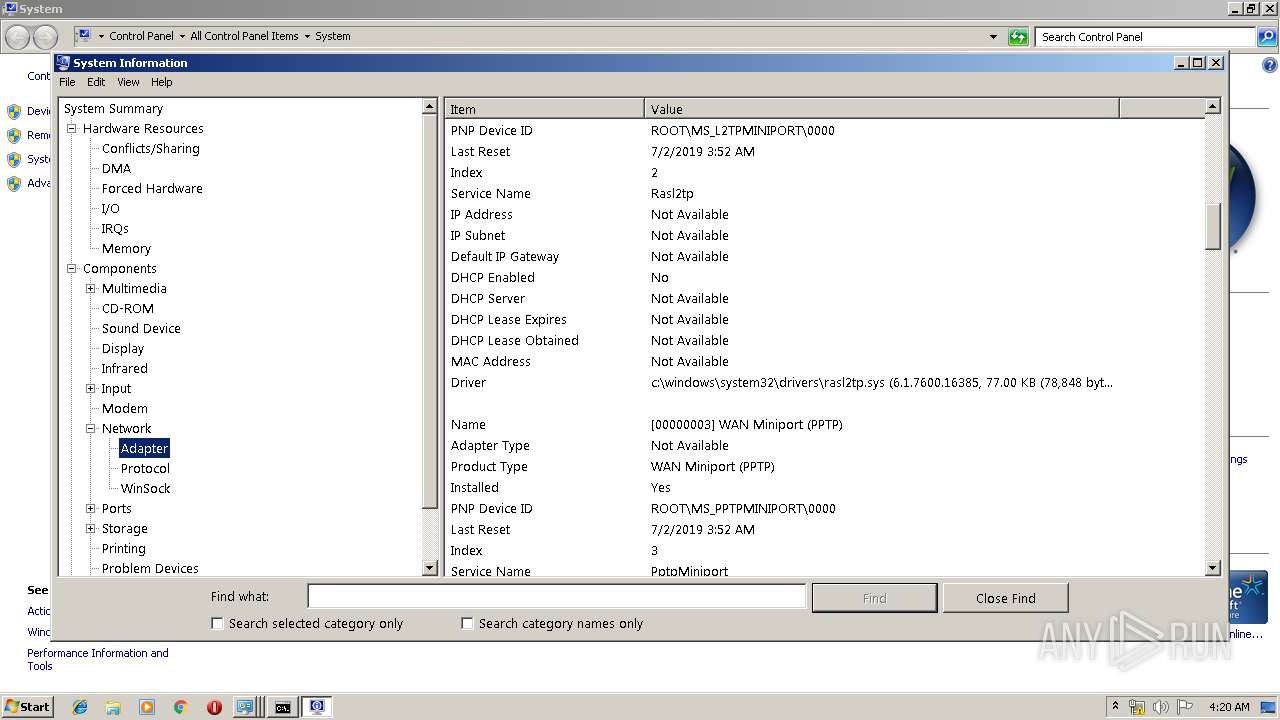
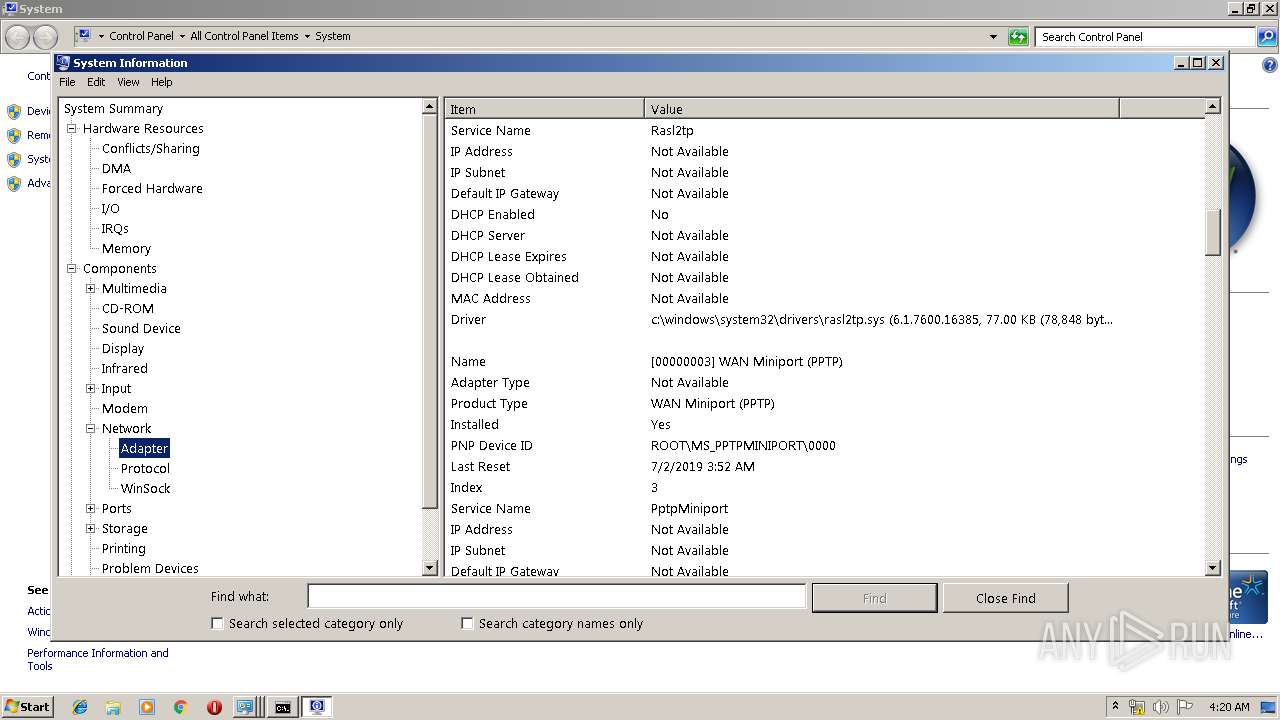
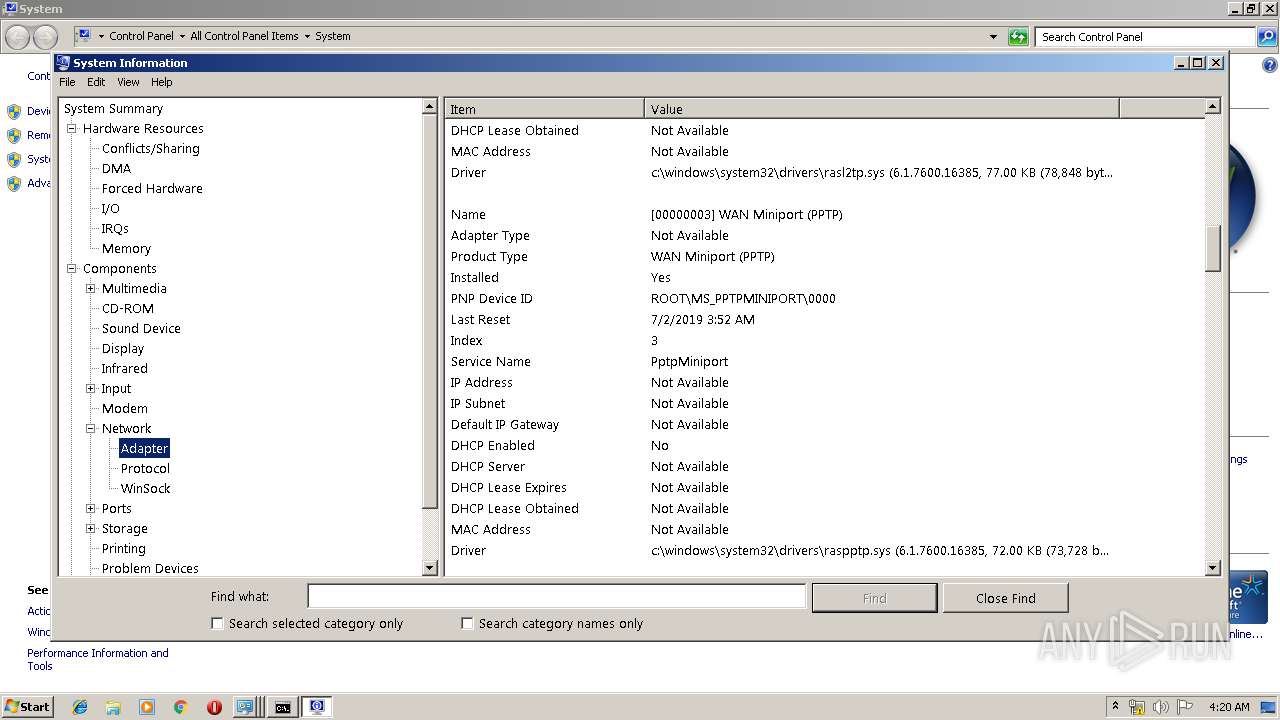
| 3136 | "C:\Windows\system32\msinfo32.exe" | C:\Windows\system32\msinfo32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3528 | ipconfig /all | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | C:\Windows\system32\DllHost.exe /Processid:{7007ACD1-3202-11D1-AAD2-00805FC1270E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
285
Read events
253
Write events
31
Delete events
1
Modification events
| (PID) Process: | (2956) s_9960.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) s_9960.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2896) s_9960.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\s_9960 |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (2896) s_9960.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\itranslator |
| Operation: | write | Name: | Guid |
Value: 9960 | |||
| (PID) Process: | (2896) s_9960.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\itranslator |
| Operation: | write | Name: | CreateTime |
Value: 20190702041555 | |||
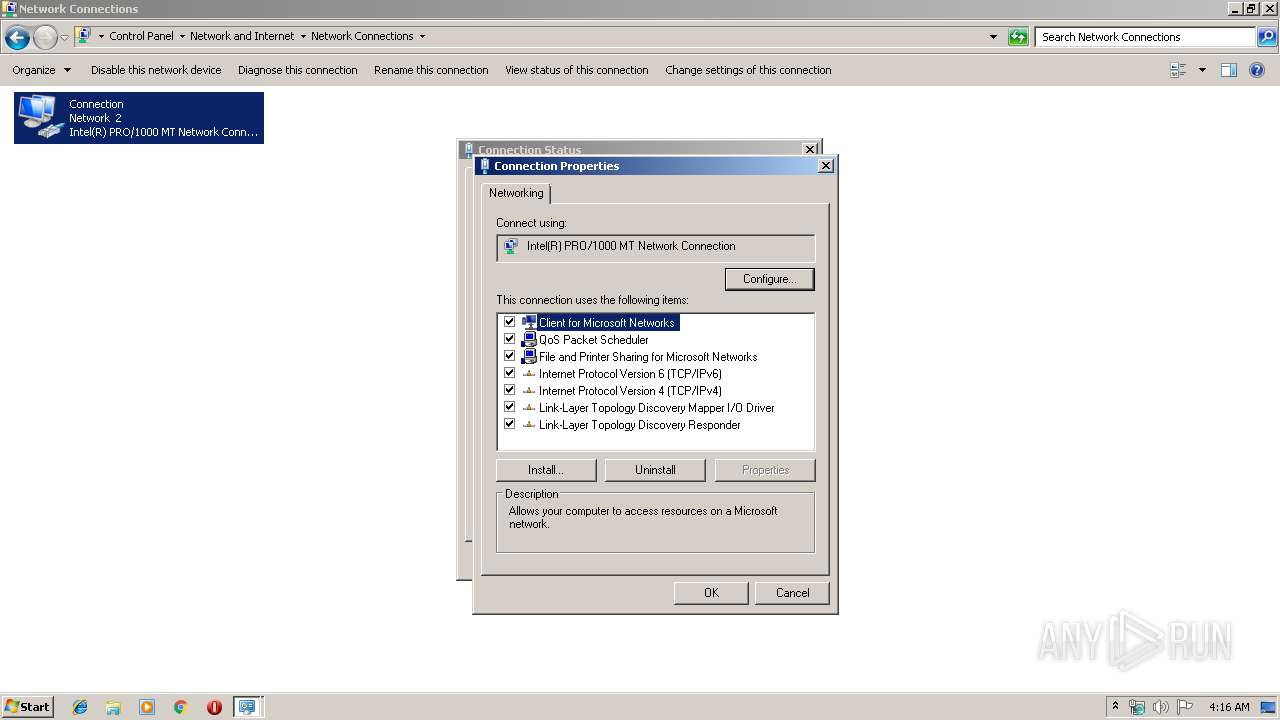
| (PID) Process: | (3548) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NetCfgLockHolder |
| Operation: | write | Name: | |
Value: Local Network Connection Properties | |||
| (PID) Process: | (3548) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3548) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @netcfgx.dll,-50002 |
Value: Allows your computer to access resources on a Microsoft network. | |||
| (PID) Process: | (3548) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\drivers\pacer.sys,-100 |
Value: Quality of Service Packet Scheduler. This component provides network traffic control, including rate-of-flow and prioritization services. | |||
| (PID) Process: | (3548) DllHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @netcfgx.dll,-50003 |
Value: Allows other computers to access resources on your computer using a Microsoft network. | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | s_9960.exe | C:\Users\admin\AppData\Local\Temp\s_9960.sys | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2896 | s_9960.exe | GET | — | 35.170.101.26:80 | http://tk.advennsha.info/in.php?type=is&ch=9960&mc=1F8BFBFF000506E3C4BA3647&os=Windows7&t=1507195196&m=5254004A04AF | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | s_9960.exe | 35.170.101.26:80 | tk.advennsha.info | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tk.advennsha.info |
| suspicious |