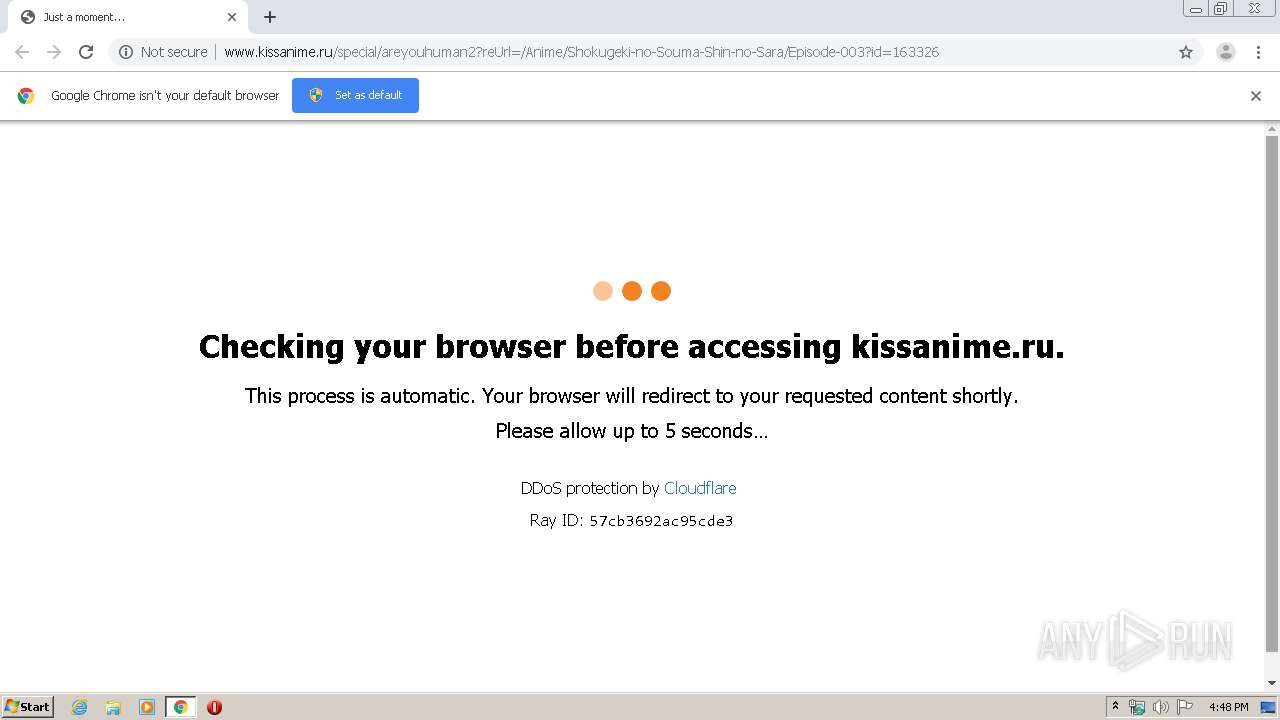
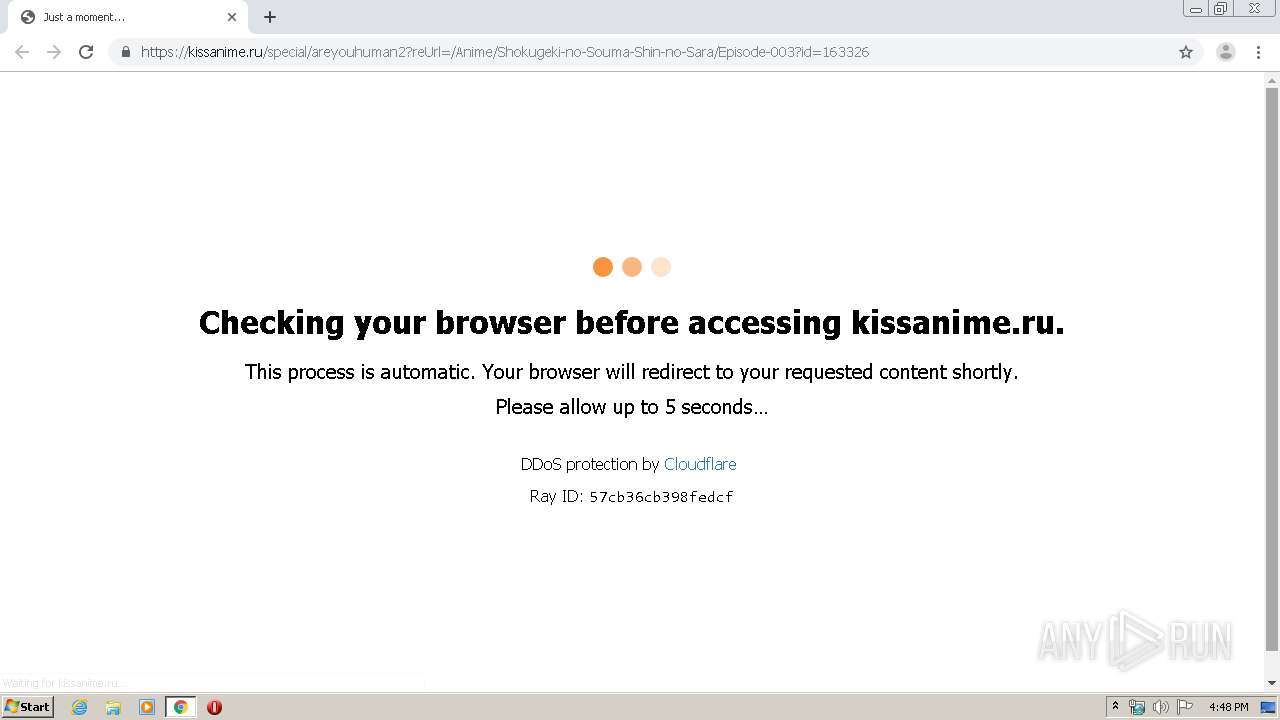
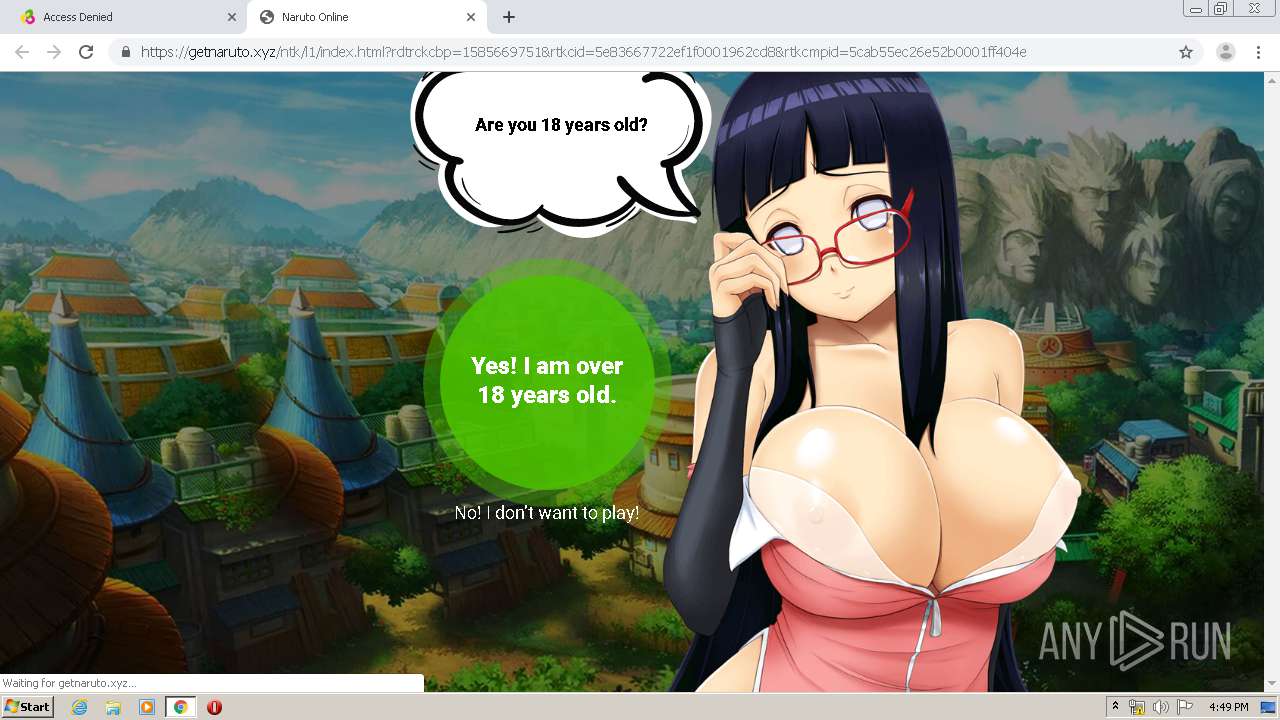
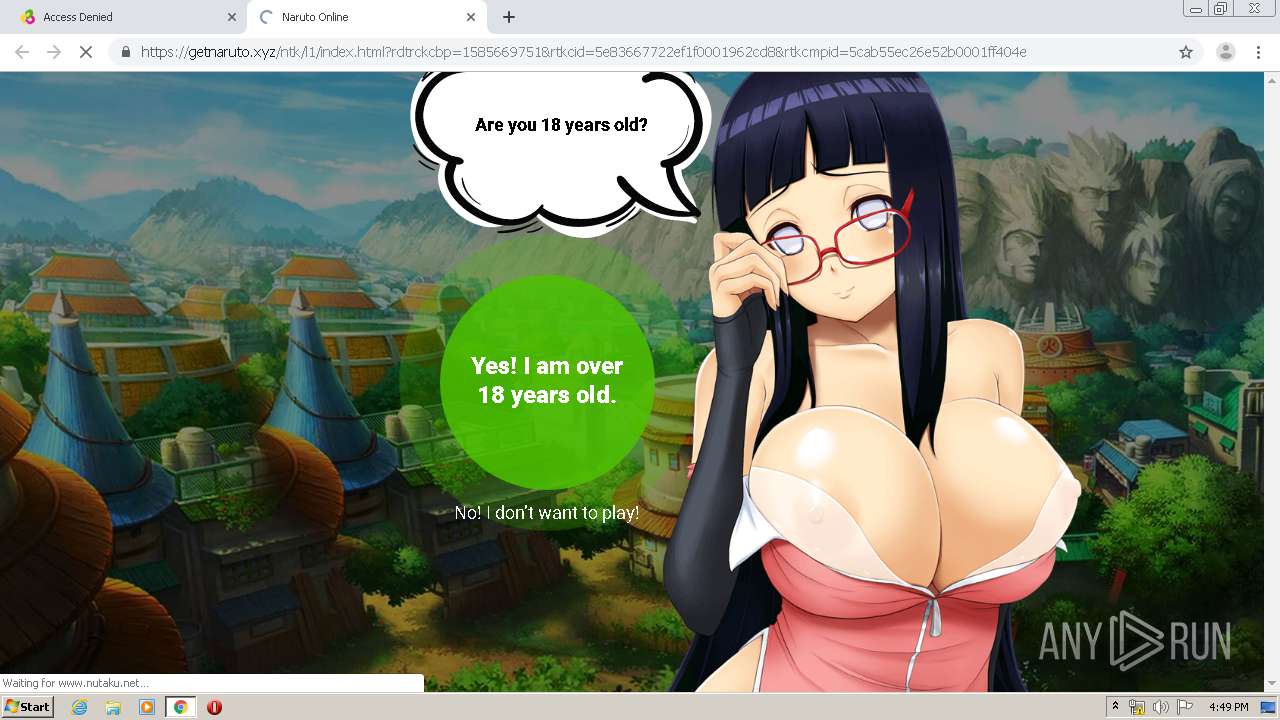
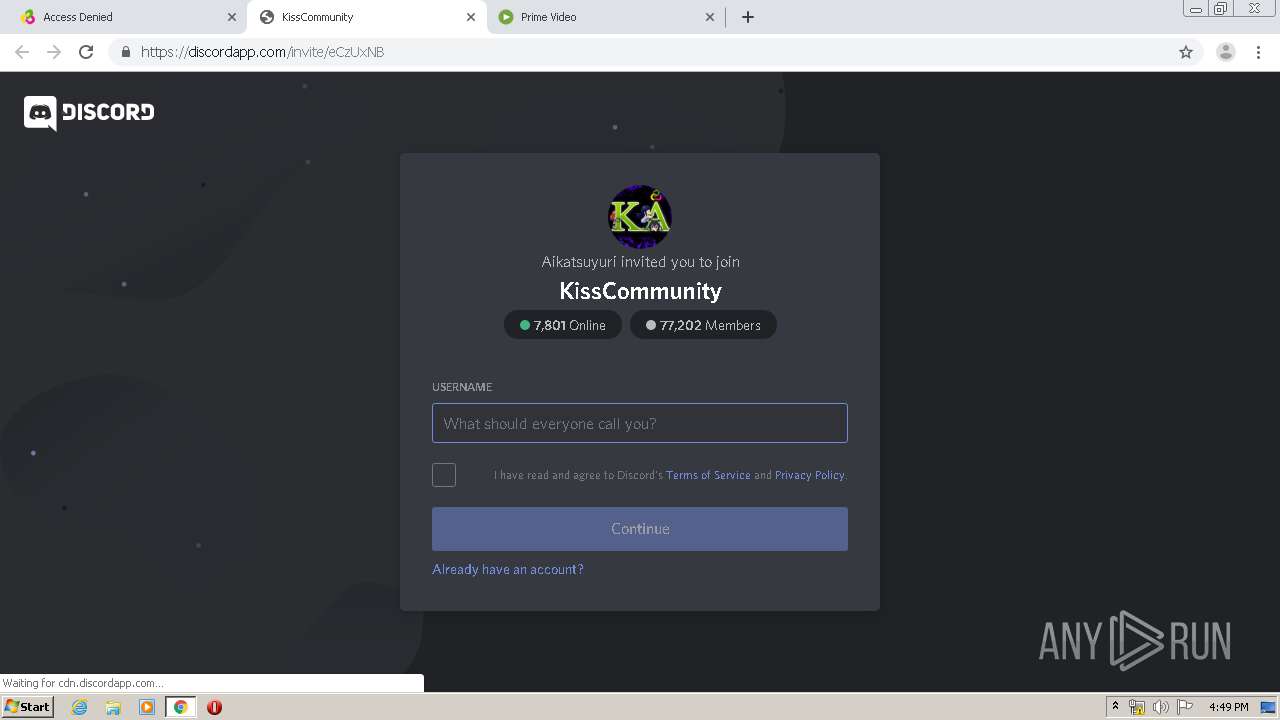
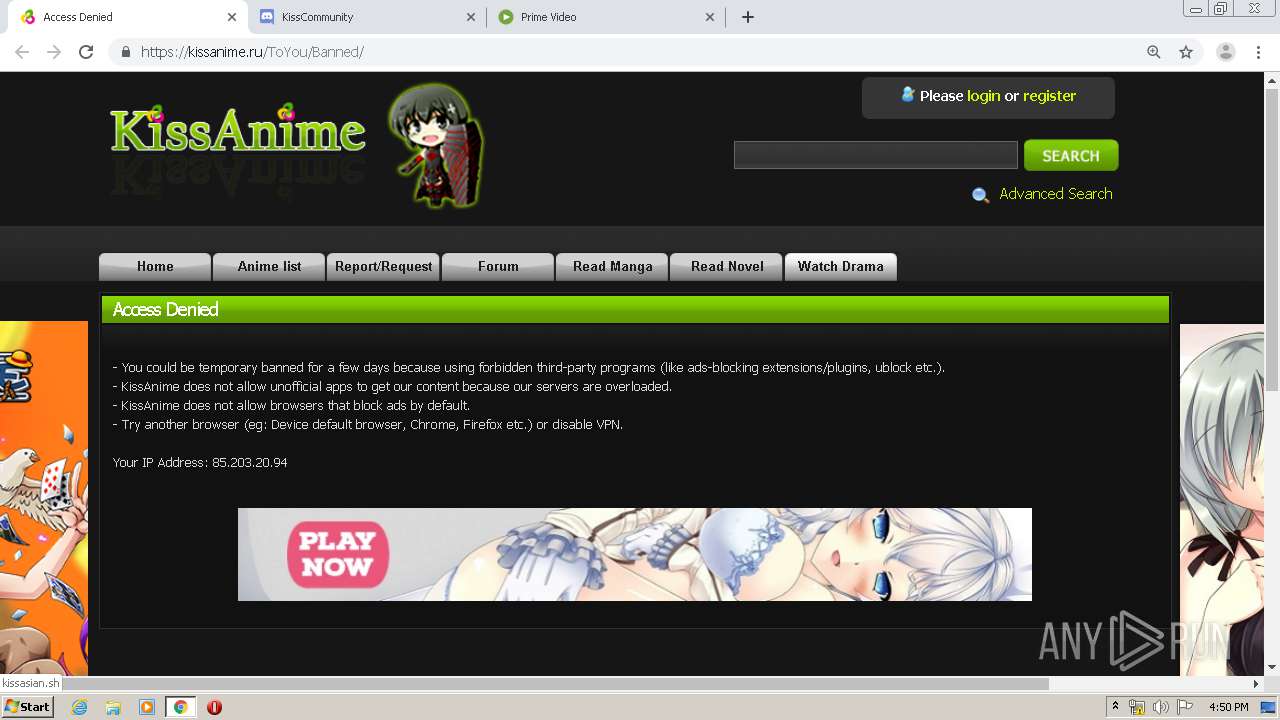
| URL: | http://www.kissanime.ru/special/areyouhuman2?reUrl=/Anime/Shokugeki-no-Souma-Shin-no-Sara/Episode-003?id=163326 |
| Full analysis: | https://app.any.run/tasks/920c12a0-421c-4c92-b117-73b270f83444 |
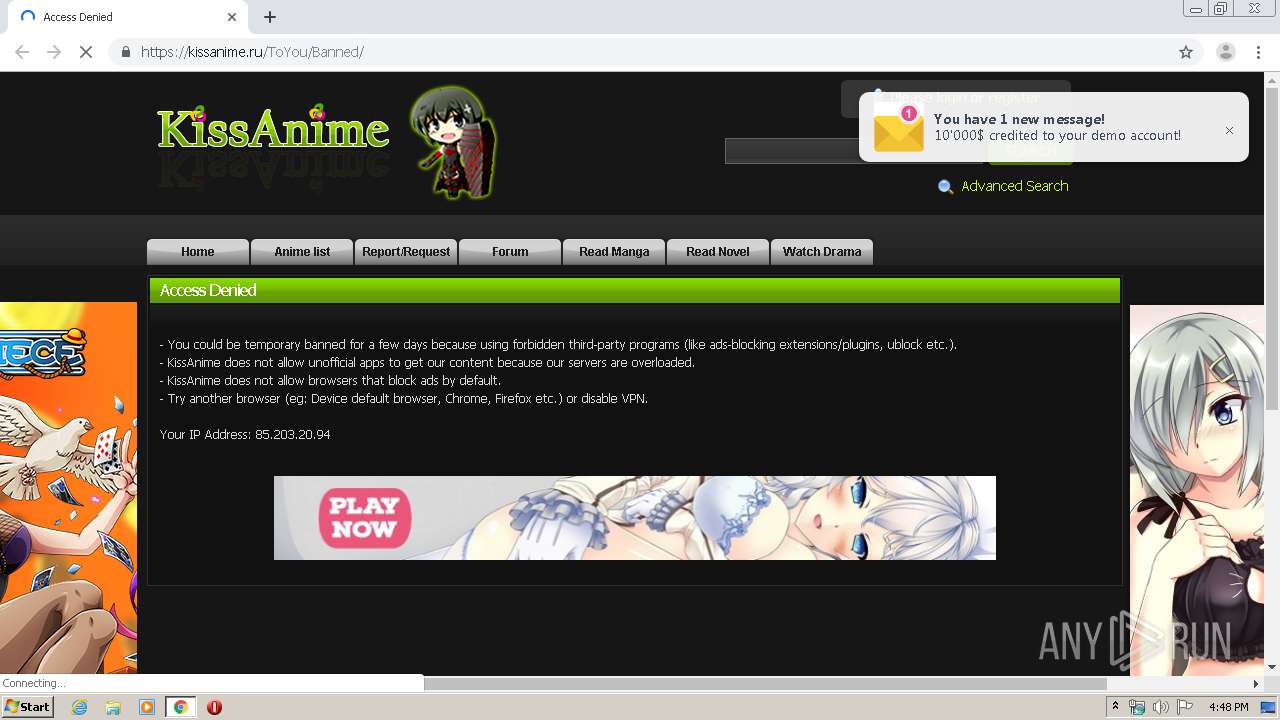
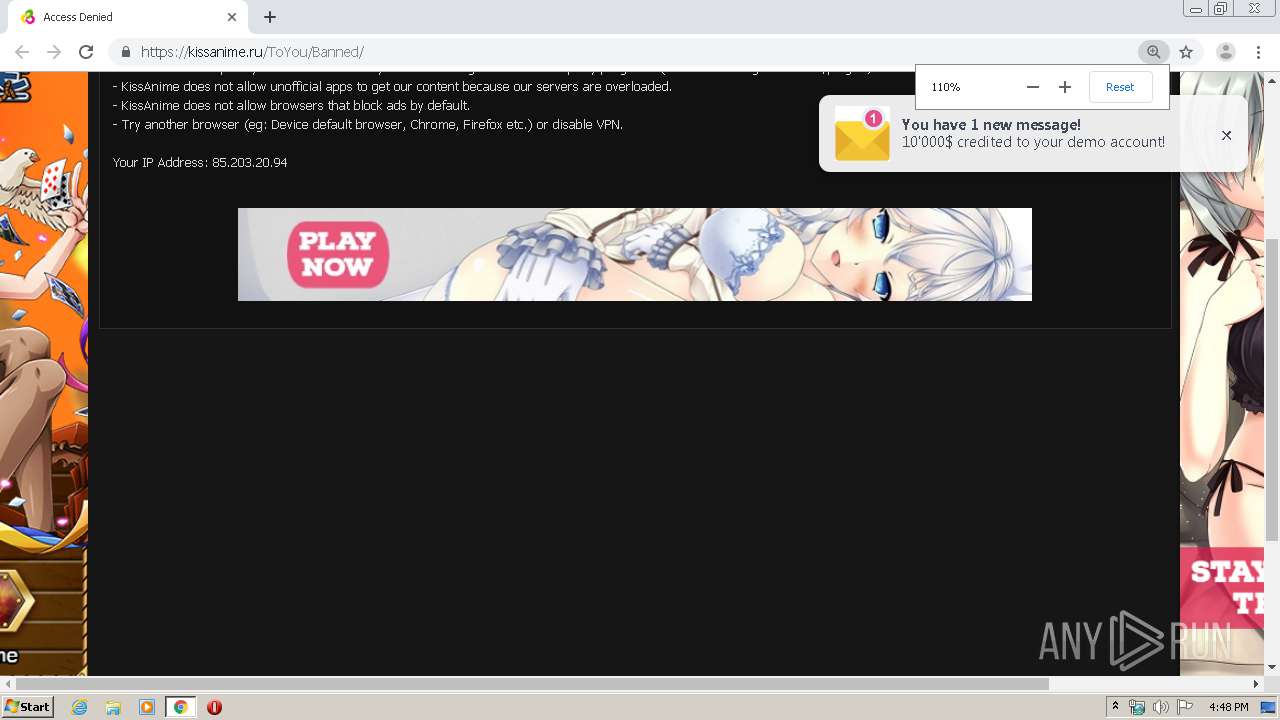
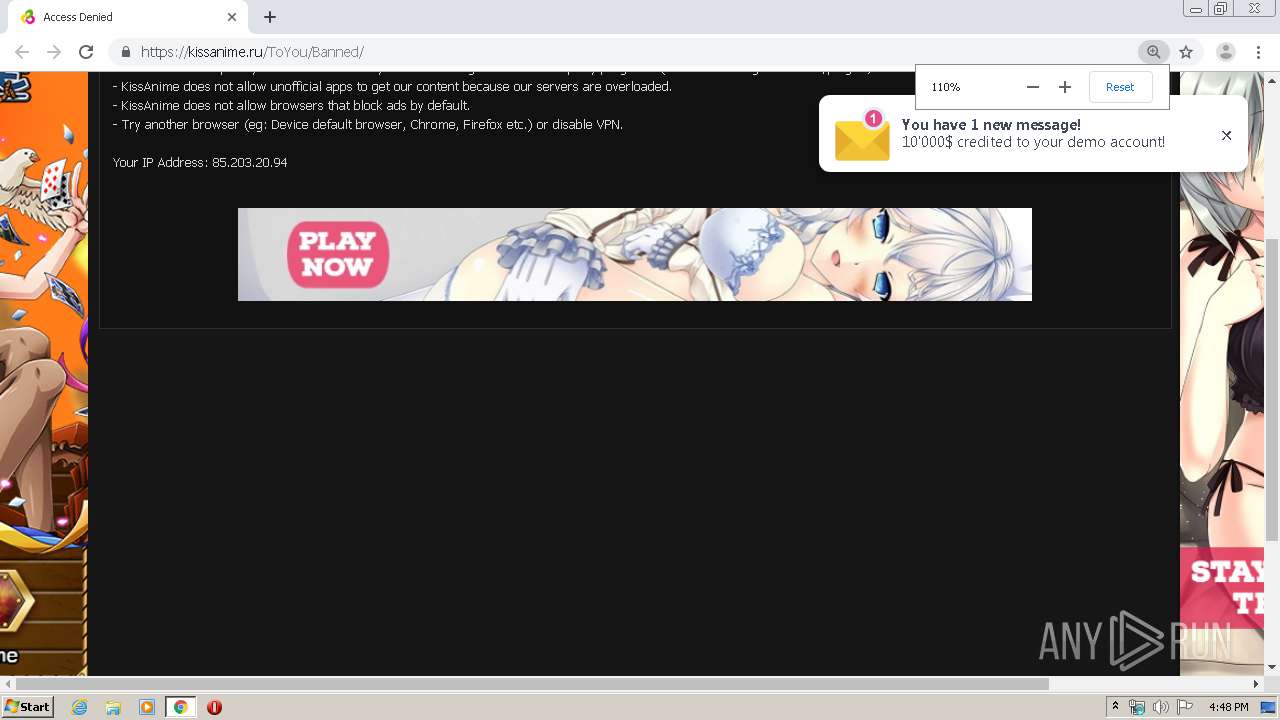
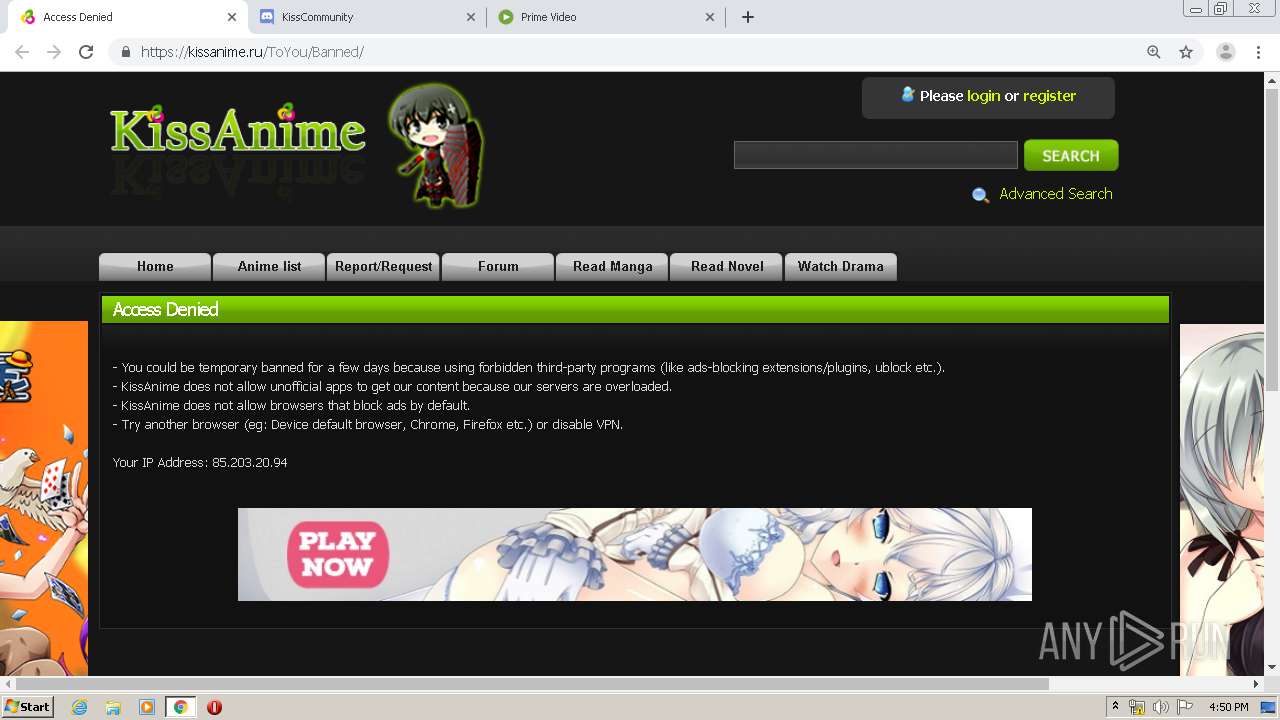
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 15:47:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8B25763B830E24D42A4D2232F3BAF07F |
| SHA1: | F4BCDC245A62D9054DEA589B564CF916D88D9513 |
| SHA256: | 29002D1817651E4142F74927FCE1EE6DF3F76307302584A7B5ACEC0D6B1CC609 |
| SSDEEP: | 3:N1KJS4tBfzGFaJ4l9kLMIANQDy68EIqMLIGY9sn:Cc4/fHJ4l9k6CDy6nMLue |
MALICIOUS
No malicious indicators.SUSPICIOUS
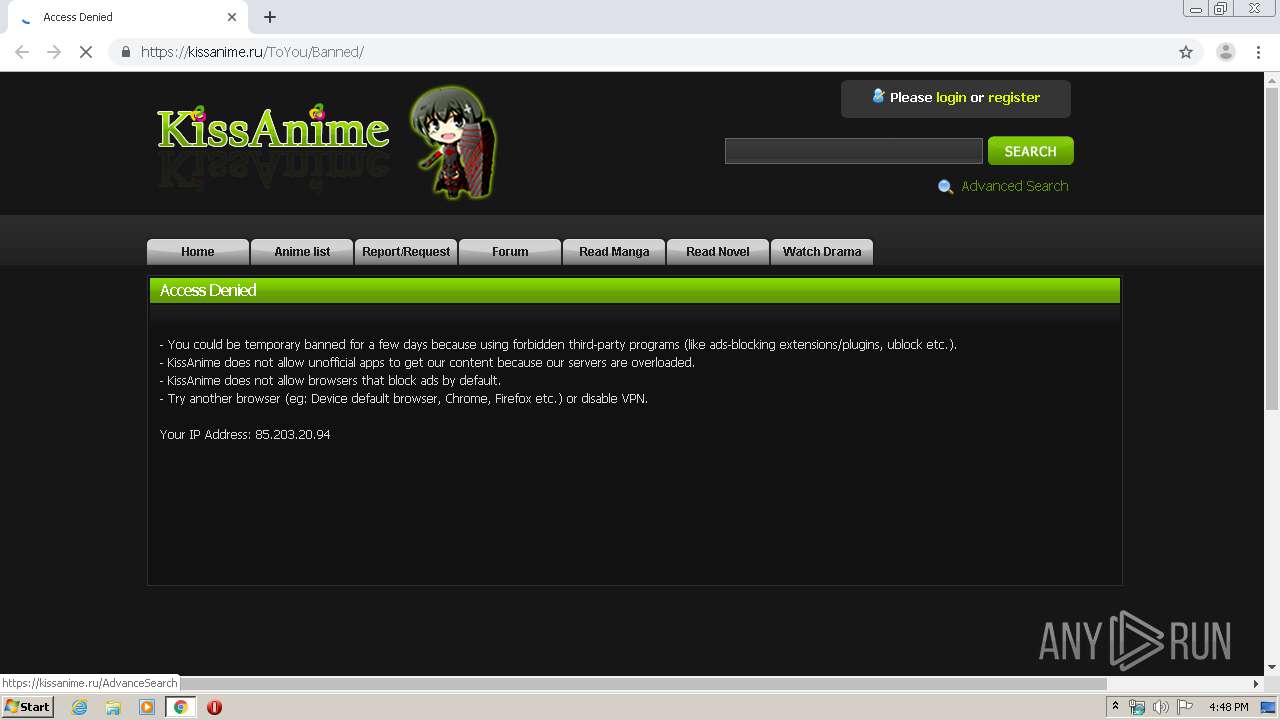
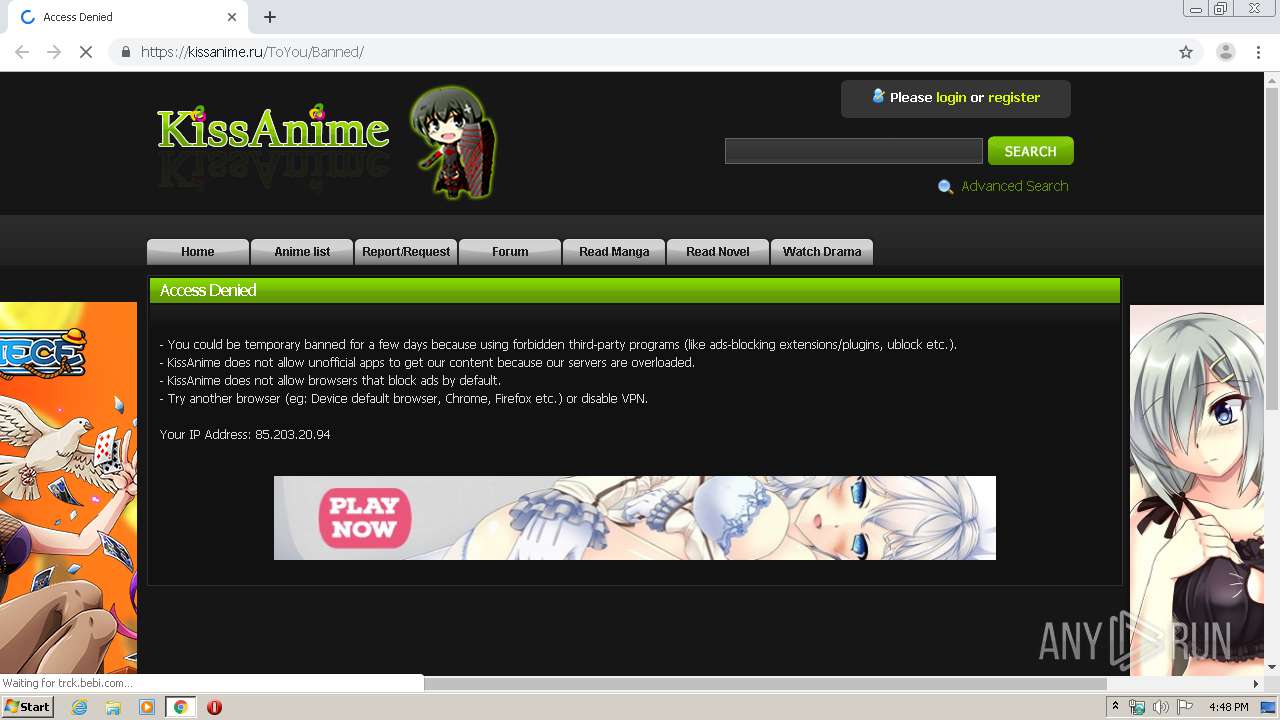
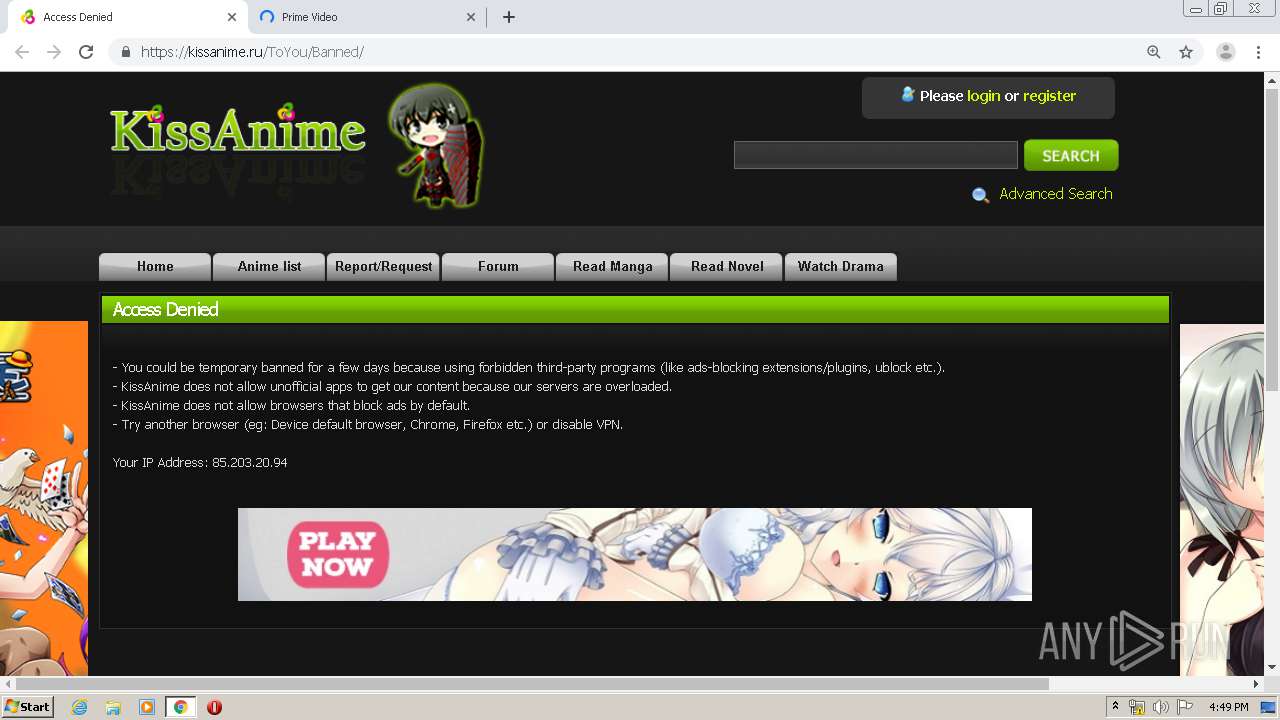
Modifies files in Chrome extension folder
- chrome.exe (PID: 3272)
INFO
Reads the hosts file
- chrome.exe (PID: 3272)
- chrome.exe (PID: 676)
Creates files in the user directory
- chrome.exe (PID: 3272)
Application launched itself
- chrome.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12741562616127051010 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8567267618644736320 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1635748295958230372 --mojo-platform-channel-handle=2764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11604690762269917447 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16178532565062715481 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1970623403265300790 --mojo-platform-channel-handle=1388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=761484318706377946 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11404605839510471664 --mojo-platform-channel-handle=4432 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5233322891106280193 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16871542577272668458,7407263148339869257,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6156331966641210099 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
679
Read events
563
Write events
110
Delete events
6
Modification events
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3272-13230143289388125 |
Value: 259 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
146
Text files
325
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E836639-CC8.pma | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c9632aa-33fa-43b2-b62f-969ccf26daf4.tmp | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66ea0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
146
DNS requests
74
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
676 | chrome.exe | GET | 301 | 104.22.0.150:80 | http://kissanime.ru/favicon.ico | US | — | — | whitelisted |
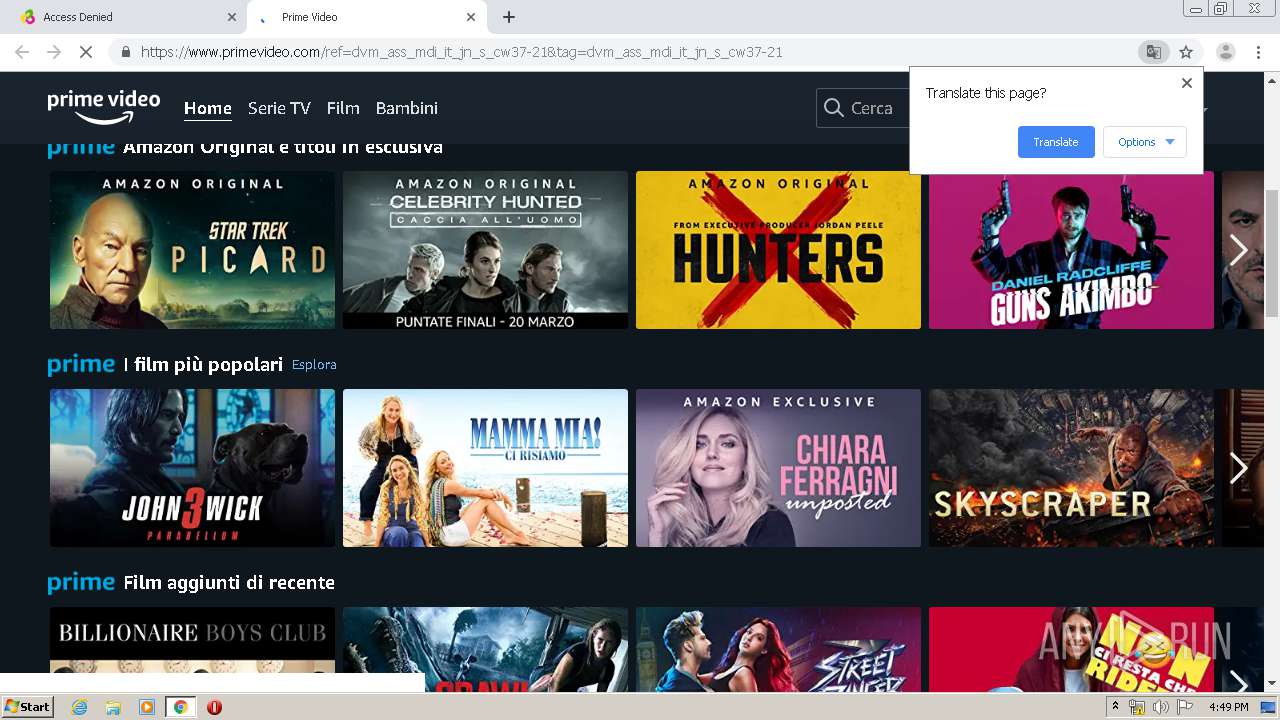
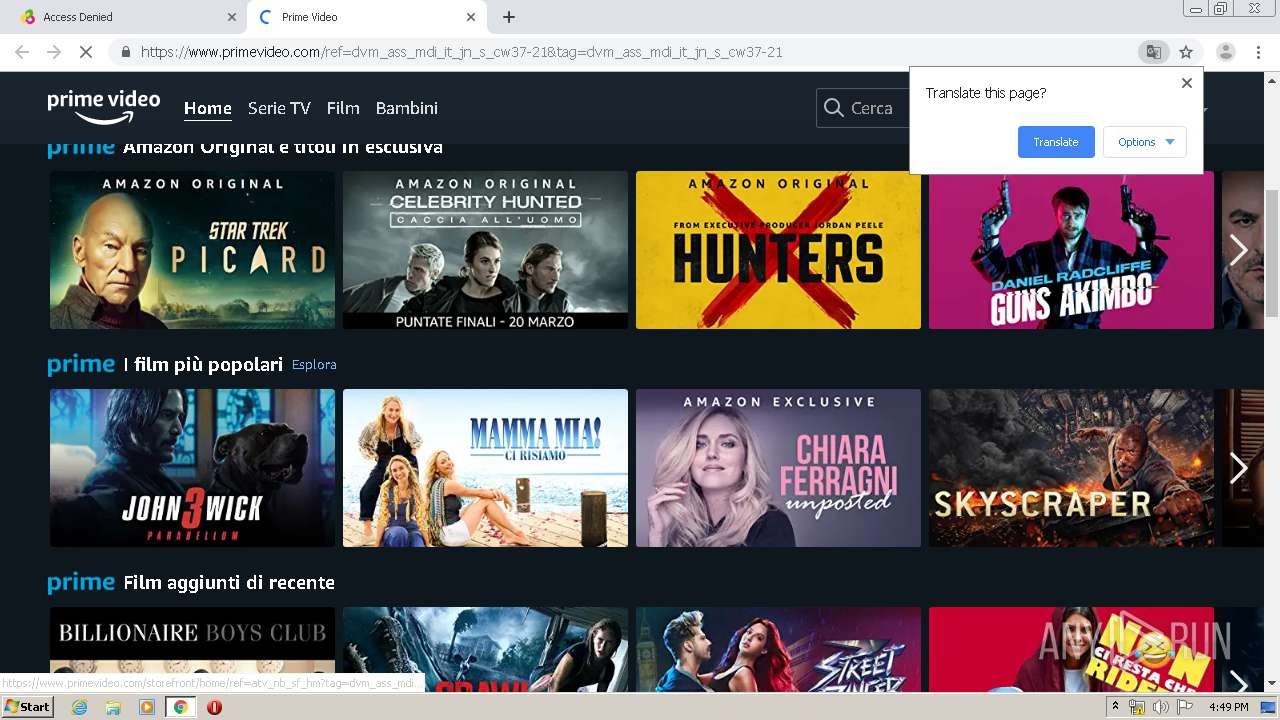
676 | chrome.exe | GET | — | 104.22.0.150:80 | http://kissanime.ru/special/areyouhuman2?reUrl=/Anime/Shokugeki-no-Souma-Shin-no-Sara/Episode-003?id=163326 | US | — | — | whitelisted |
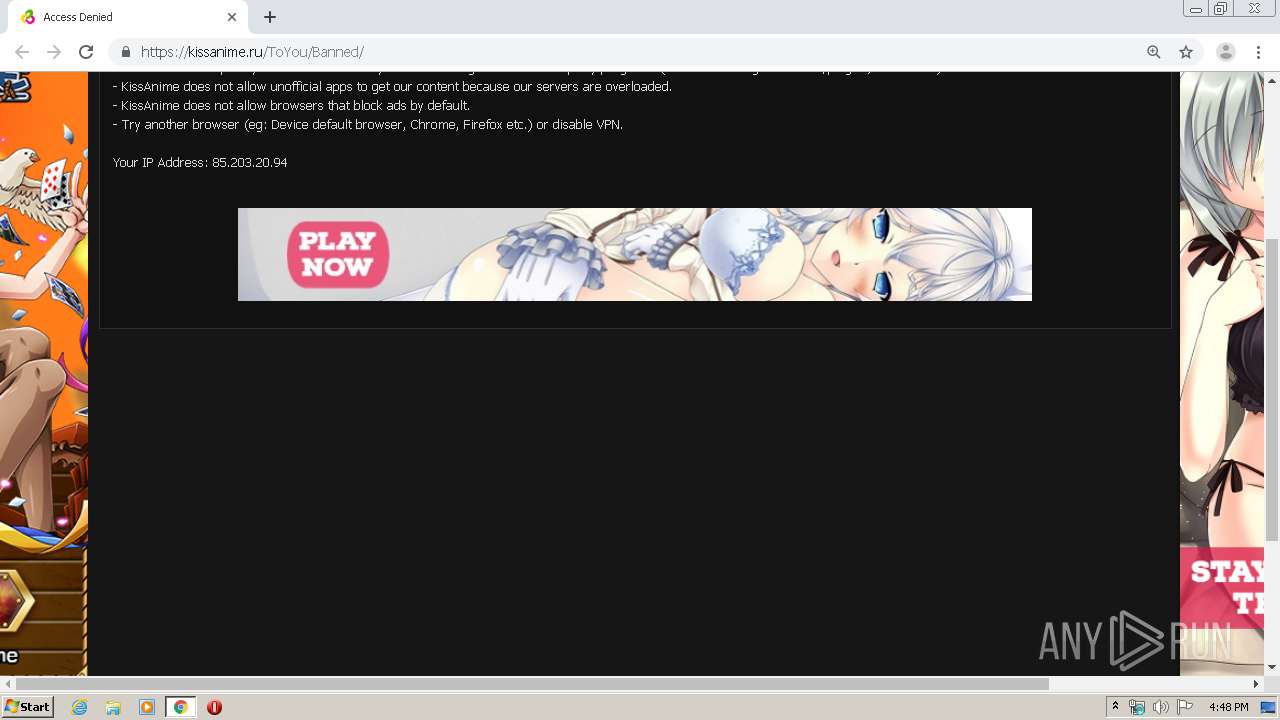
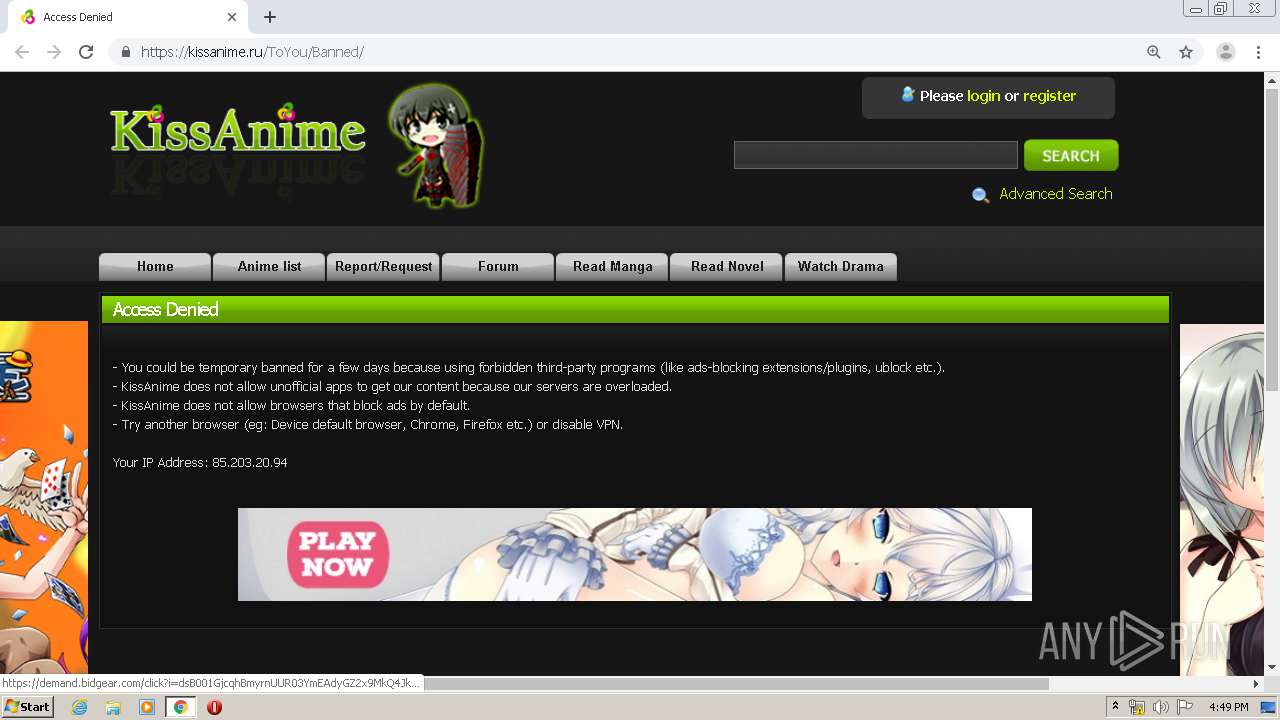
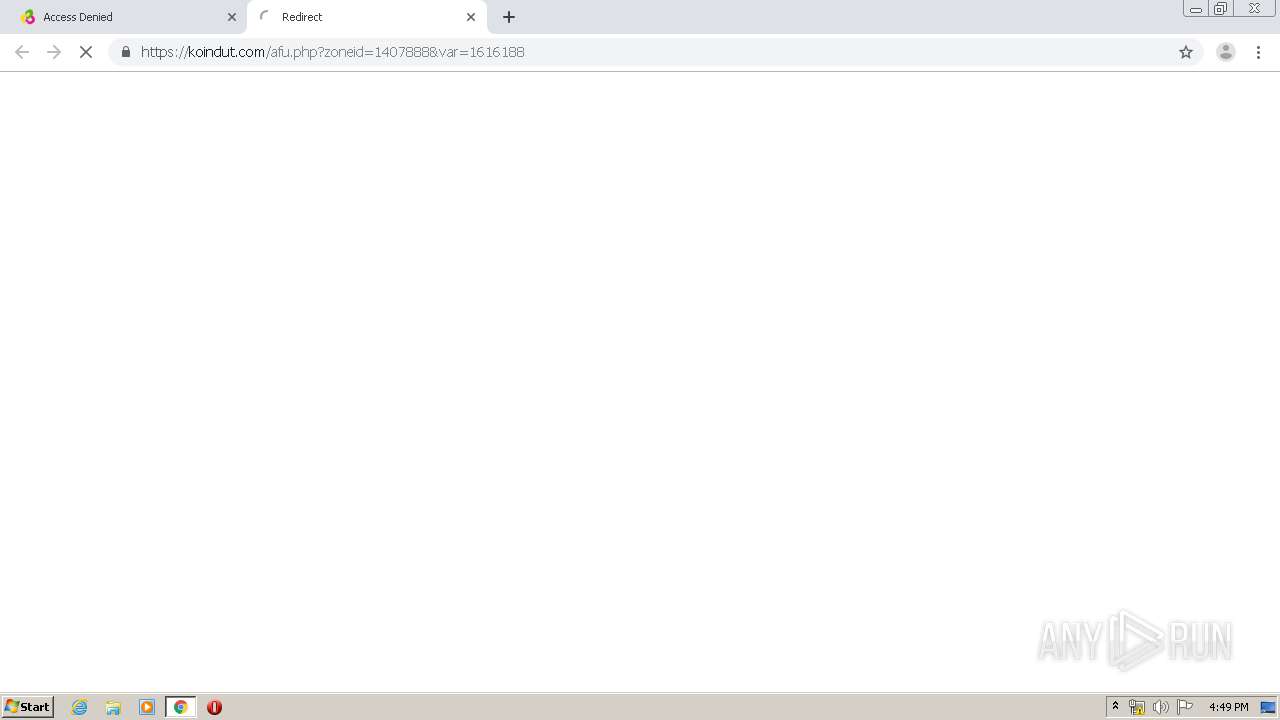
676 | chrome.exe | GET | — | 104.22.1.150:80 | http://www.kissanime.ru/special/areyouhuman2?reUrl=/Anime/Shokugeki-no-Souma-Shin-no-Sara/Episode-003?id=163326 | US | — | — | suspicious |
676 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
676 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
676 | chrome.exe | POST | 301 | 104.22.1.150:80 | http://www.kissanime.ru/special/areyouhuman2?reUrl=/Anime/Shokugeki-no-Souma-Shin-no-Sara/Episode-003?id=163326&__cf_chl_jschl_tk__=ef7d3ea7aeffd8e1939589aecfbd286148d9ec23-1585669691-0-AT1tIfuvIzzW8_6ciluIXQ4AcyBR43x2m0xu7ZkOem75t-YPmhGNi8srelg2Scb-BupKp15tkalLlkoRaHx-6u90cckmL-j0Te8zju7o1Fgg2Q9PcYnWerF3ZXq7BYelCgX-xDHdJ4xV5D-a06RduGsvvcLTthx_NhwrNwxaIcQPeBgY-u5lnHQC6yhsywrgzWzcMAygwp1e7hEnI8COXuNvOjpnH-rx4t5ZSuSbDCOJZSklr-PRnPZ_CCl7zP2fm_Gmd3YPMDcoghdQgJb40hVhOkVBfSufwaSGaqnoOcP8Aymnem0jU07Ggz69kgz8pBM7_yED3rTl21RuG7U9-PdrVBAEyUpnk21z-mDx-qExbHmpX4VaRRK-N24A2ntpWAzLzf0CniC_kTzwUVMummo | US | image | 42 b | suspicious |
676 | chrome.exe | GET | 200 | 104.22.0.150:80 | http://kissanime.ru/cdn-cgi/images/trace/jschal/nojs/transparent.gif?ray=57cb36affad2b799 | US | image | 42 b | whitelisted |
676 | chrome.exe | GET | 200 | 104.22.1.150:80 | http://www.kissanime.ru/cdn-cgi/images/trace/jschal/nojs/transparent.gif?ray=57cb3692ac95cde3 | US | image | 42 b | suspicious |
676 | chrome.exe | GET | 200 | 104.22.1.150:80 | http://www.kissanime.ru/cdn-cgi/images/trace/jschal/js/transparent.gif?ray=57cb3692ac95cde3 | US | image | 42 b | suspicious |
676 | chrome.exe | POST | 301 | 104.22.0.150:80 | http://kissanime.ru/special/areyouhuman2?reUrl=/Anime/Shokugeki-no-Souma-Shin-no-Sara/Episode-003?id=163326&__cf_chl_jschl_tk__=7af7679862ec68e59b66085fb9aad61d282525fc-1585669695-0-AZEAHfaYnntepfjWPsDRBZsxK_CxMW0RPMc1WIcuj_rfFJ5unyLFFY8RBVspOhVfeWhL_lOYdD7yjVjkhYK0mTyIWnRNOy0uTBOBfu5imAxOO30_00dKycgaSBU5cwvkCzJ711e6qYDkuN2rpRjahNorPeBql3gug8cjTaLNbnwD9f2wu-WyOf_d88Y6FNbjb2DUhw-O0K7ry6o0FcDXuZ3Z6A0iUC2TNHIw_2kMdXhSS_c_zMEfPHyCmCoxyW8tEC56qwpuTw6aNBnBV3azhZdqoJ3vf5ZV3qfyykZxkkpY8u6Q0PfUtfZcMpgP4zpylW1p32IXI0mW8lEm7u45bdB26exq02k09KCpj7f1q4j51A7Auz8i0_AS7v5b5fwhyRNvHNSIfnug11T4aKYy-2M | US | image | 42 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
676 | chrome.exe | 104.22.1.150:80 | www.kissanime.ru | Cloudflare Inc | US | suspicious |
676 | chrome.exe | 104.22.0.150:443 | www.kissanime.ru | Cloudflare Inc | US | suspicious |
676 | chrome.exe | 74.125.155.199:80 | r1---sn-p5qs7n7z.gvt1.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
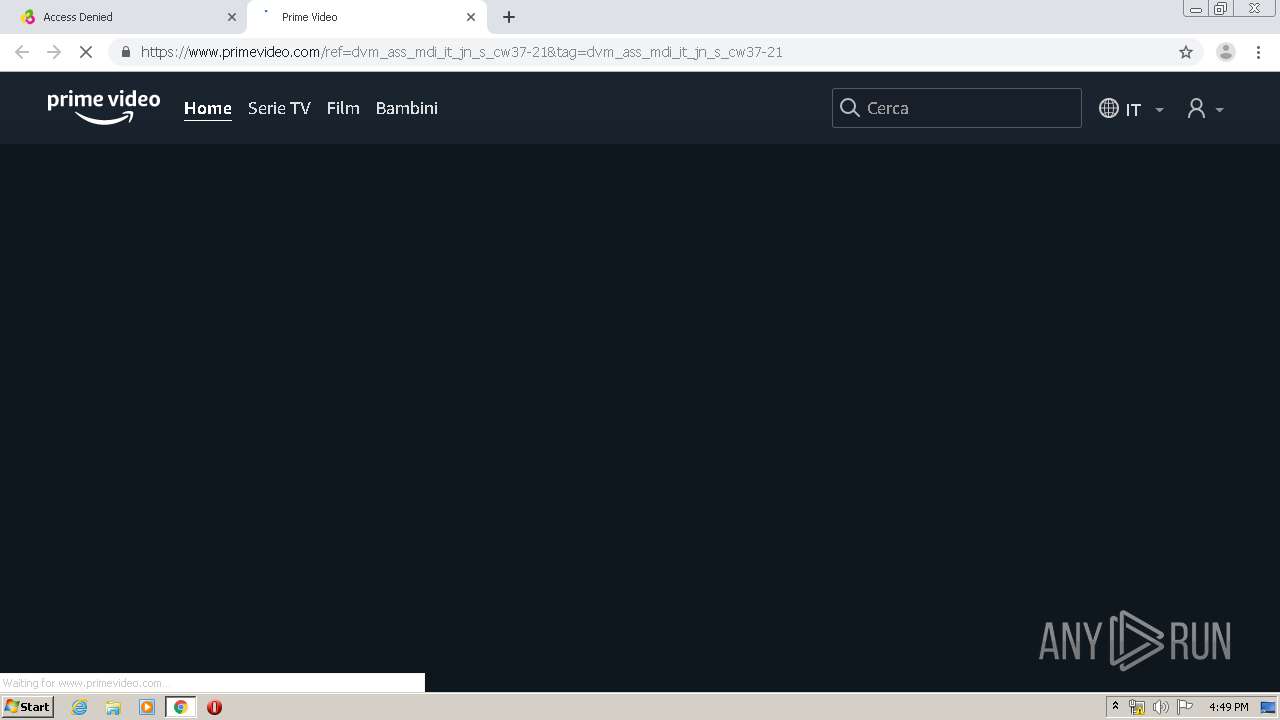
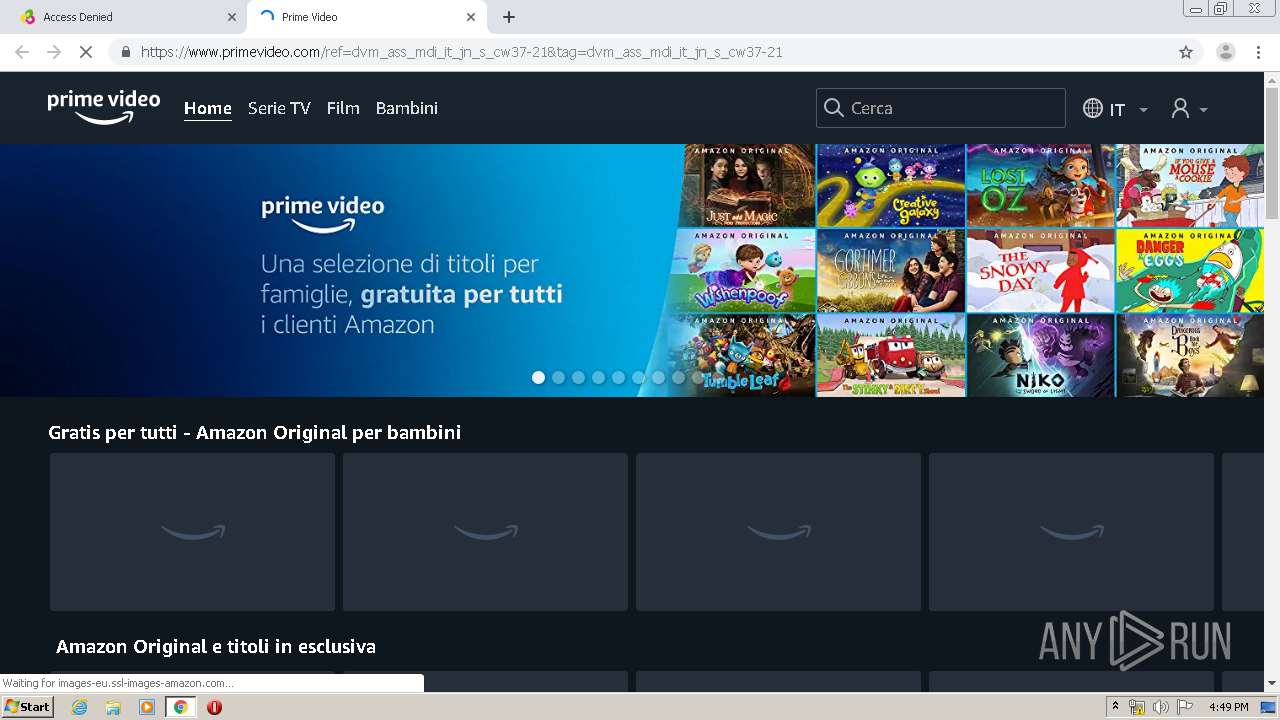
676 | chrome.exe | 88.85.66.147:443 | koindut.com | Webzilla B.V. | NL | unknown |
676 | chrome.exe | 78.140.191.103:443 | inpagepush.com | Webzilla B.V. | NL | unknown |
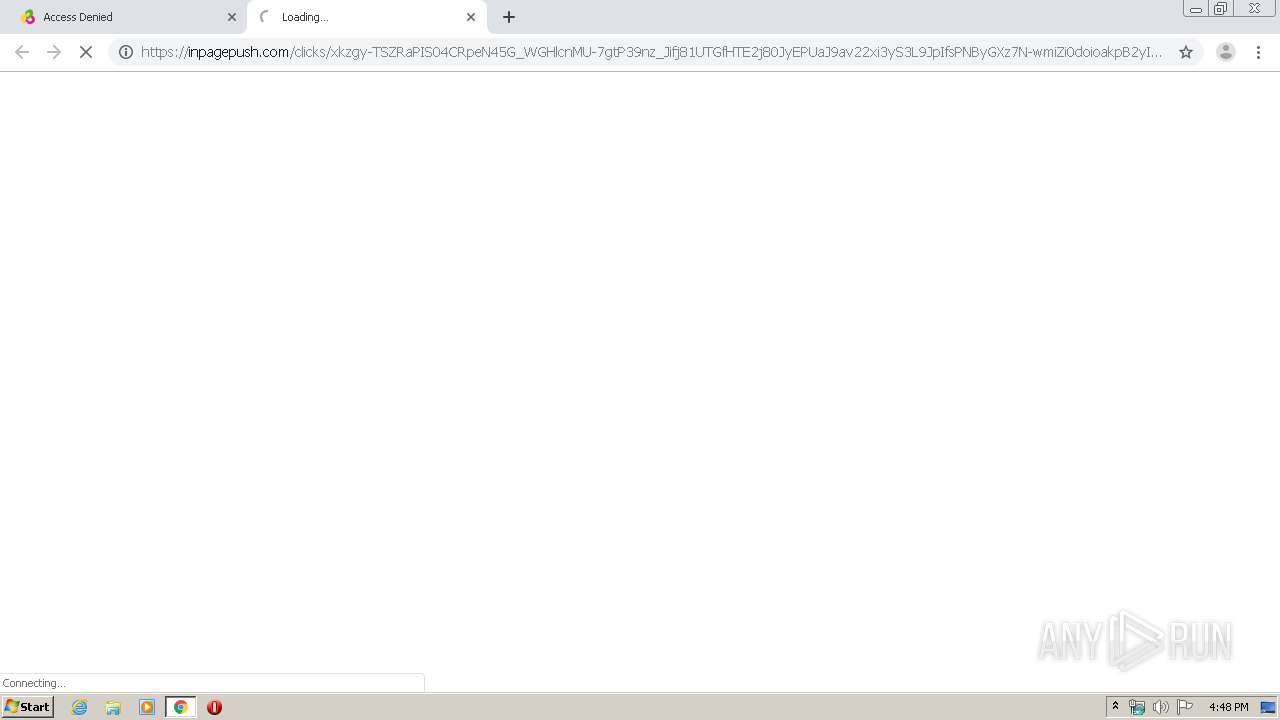
676 | chrome.exe | 104.27.189.119:443 | demand.bidgear.com | Cloudflare Inc | US | shared |
676 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
676 | chrome.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.kissanime.ru |
| suspicious |
accounts.google.com |
| shared |
www.cloudflare.com |
| whitelisted |
clients2.google.com |
| whitelisted |
kissanime.ru |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-p5qs7n7z.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
676 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
676 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |