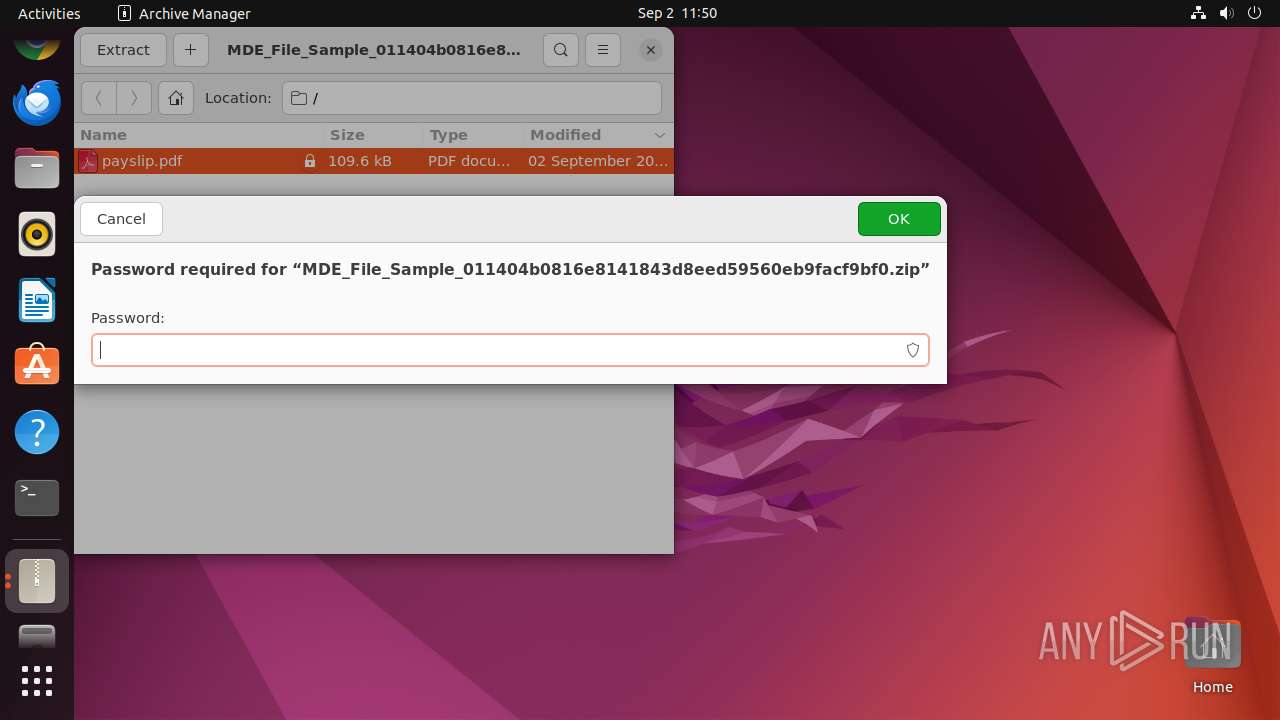
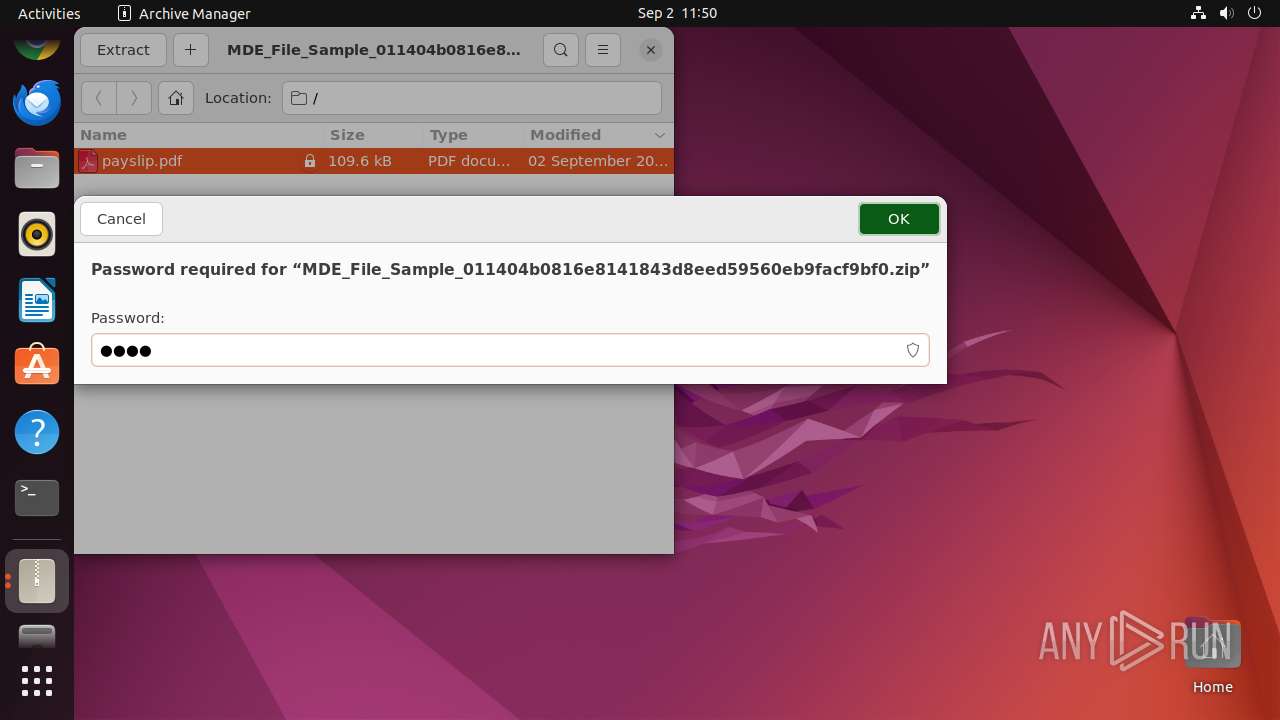
| File name: | MDE_File_Sample_011404b0816e8141843d8eed59560eb9facf9bf0.zip |
| Full analysis: | https://app.any.run/tasks/624a8013-d09d-48cb-82d5-83f6fab68651 |
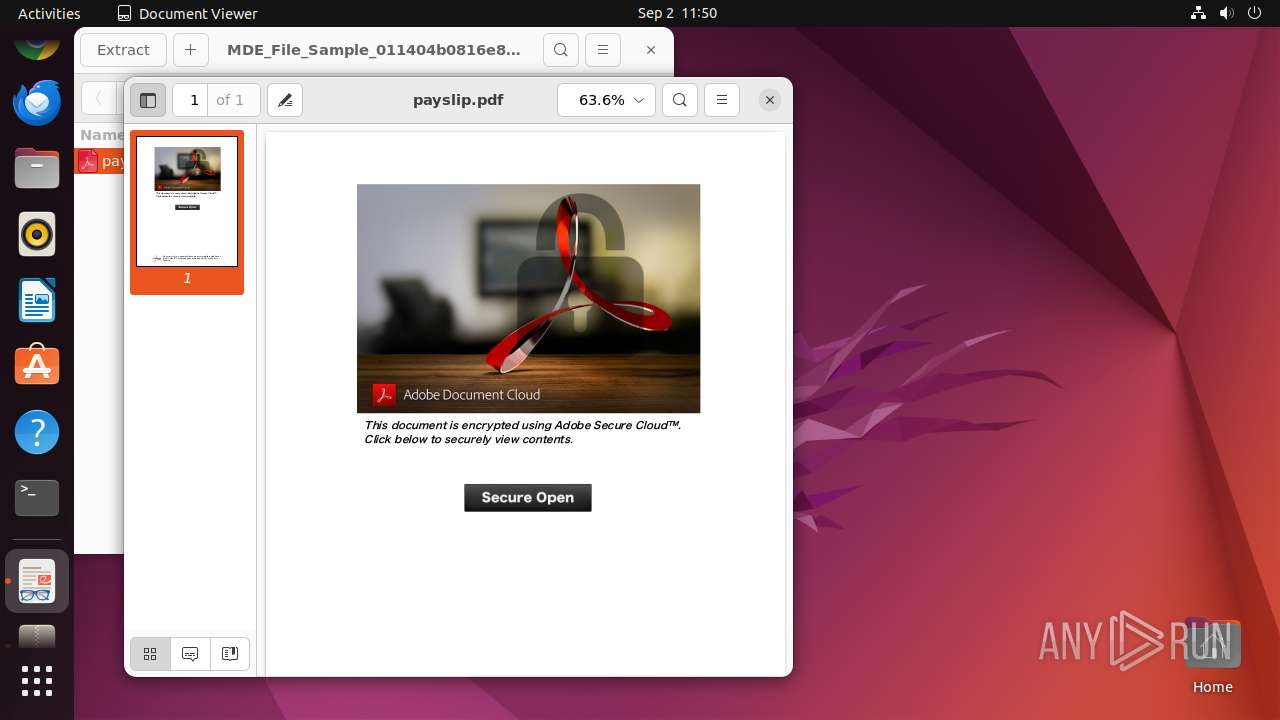
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2024, 10:50:40 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
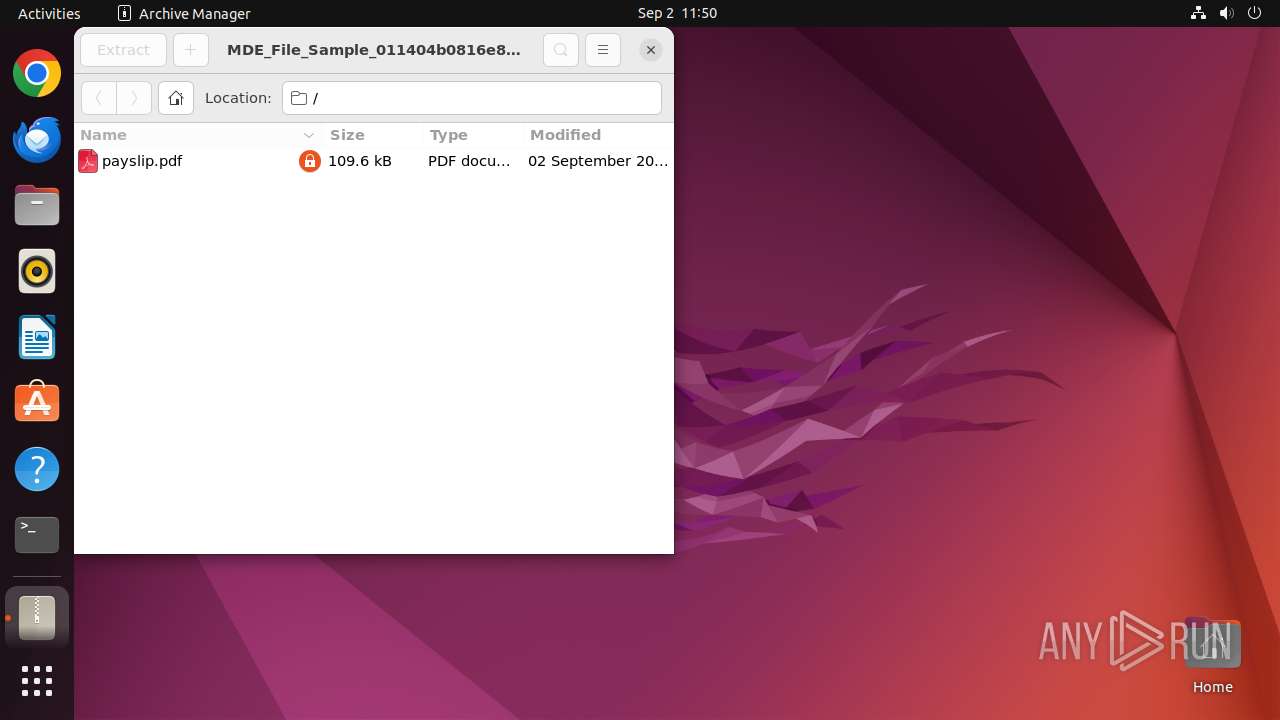
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 13AAA08A89D55D73E5E8B41C62CD92E3 |
| SHA1: | FD18A0773401FB8174FF168F90E188FA96DE1BFB |
| SHA256: | 28FCDFAB6F98C3638D59900C9A1FBCB36CA84F5A5BEA94E7AA1F5DDA8CD6FC05 |
| SSDEEP: | 1536:T6PMga8hQkFE3c/HxgG8LSDX7Le7Bau4SAnBGfpq+hGI7re9a8:T6kgRhQr6Hx/8+7Pe7Bau4Hwpq+Bsf |
MALICIOUS
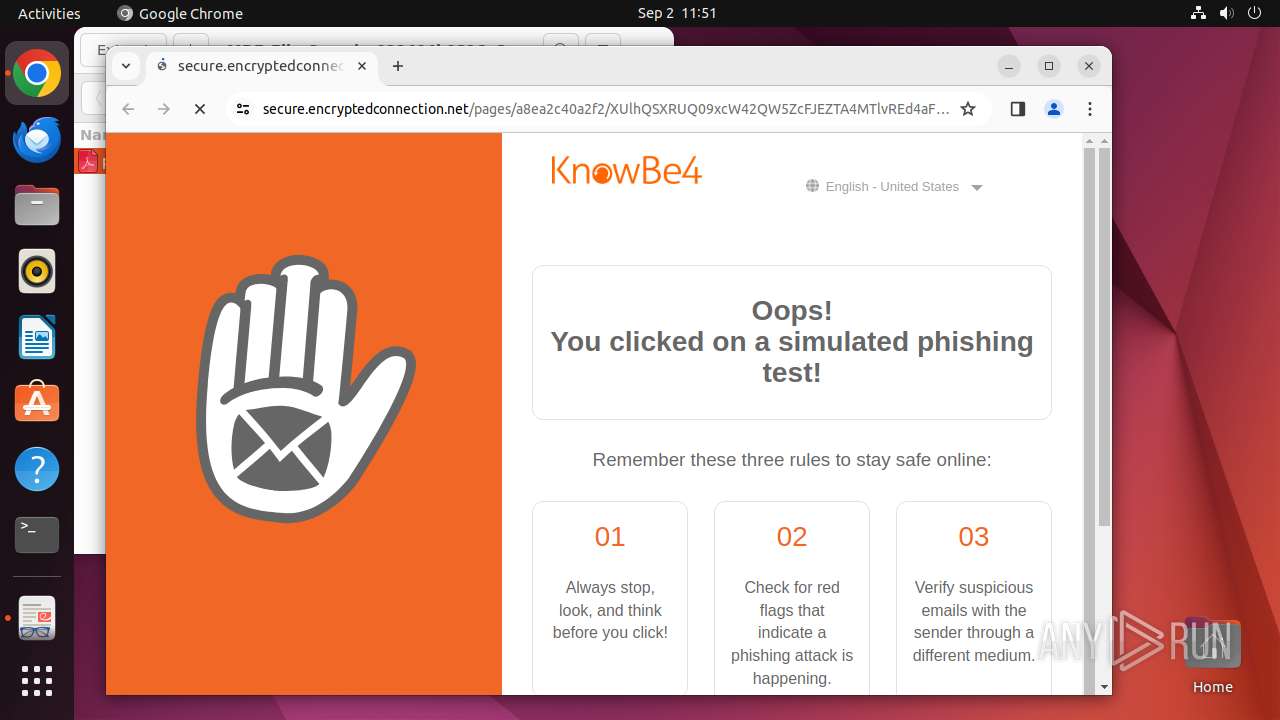
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 425)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:02 10:50:18 |
| ZipCRC: | 0x3d8a2d99 |
| ZipCompressedSize: | 78259 |
| ZipUncompressedSize: | 109643 |
| ZipFileName: | payslip.pdf |
Total processes
328
Monitored processes
113
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 425 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 13422 | /bin/sh -c "DISPLAY=:0 sudo -iu user file-roller /tmp/MDE_File_Sample_011404b0816e8141843d8eed59560eb9facf9bf0\.zip " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 13423 | sudo -iu user file-roller /tmp/MDE_File_Sample_011404b0816e8141843d8eed59560eb9facf9bf0.zip | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 13424 | file-roller /tmp/MDE_File_Sample_011404b0816e8141843d8eed59560eb9facf9bf0.zip | /usr/bin/file-roller | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 13425 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13439 | /usr/lib/p7zip/7z l -slt -bd -y -- /tmp/MDE_File_Sample_011404b0816e8141843d8eed59560eb9facf9bf0.zip | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13440 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13441 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13442 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 13443 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
Executable files
0
Suspicious files
68
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13499 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13499 | chrome | /home/user/.config/google-chrome/Default/History | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
31
DNS requests
47
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 195.181.175.40:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
13499 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
13549 | chrome | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
202.100.168.192.in-addr.arpa |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
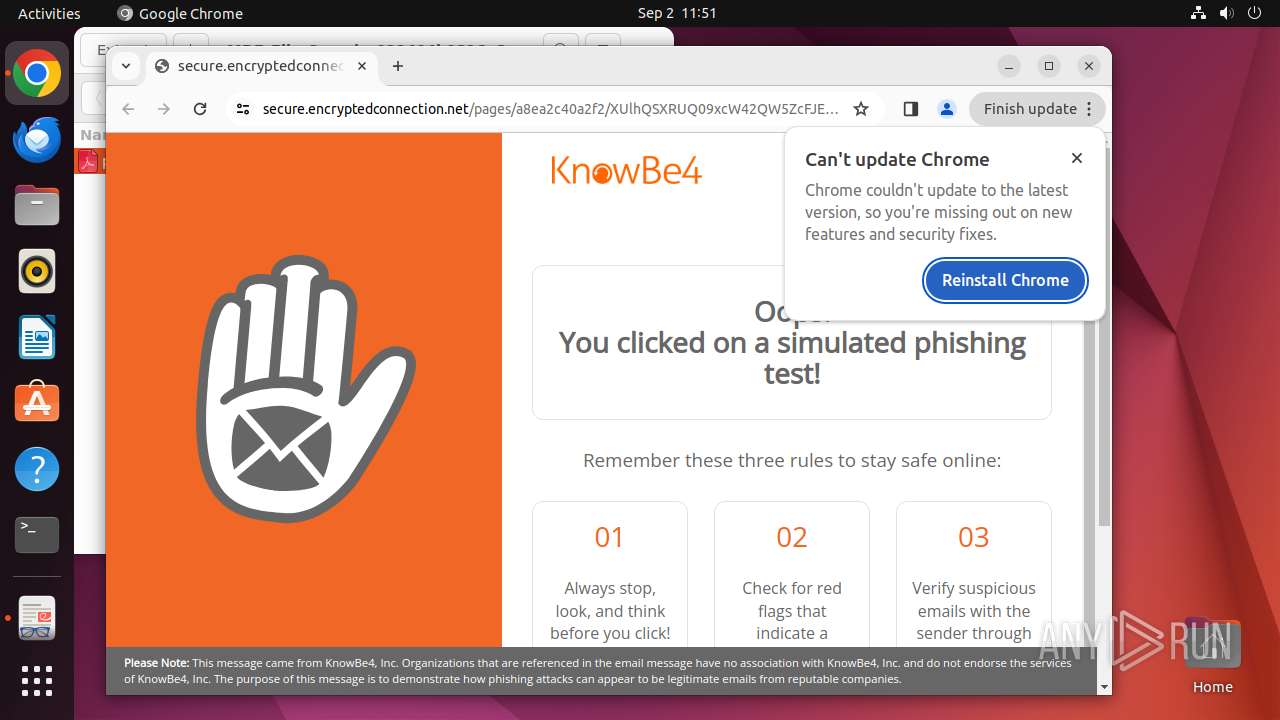
whoops.wishyoudidntclickthis.com |
| unknown |
landing.eu.knowbe4.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] KnowBe4: Security Awareness Training (knowbe4 .com) |
425 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] KnowBe4: Security Awareness Training (knowbe4 .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |