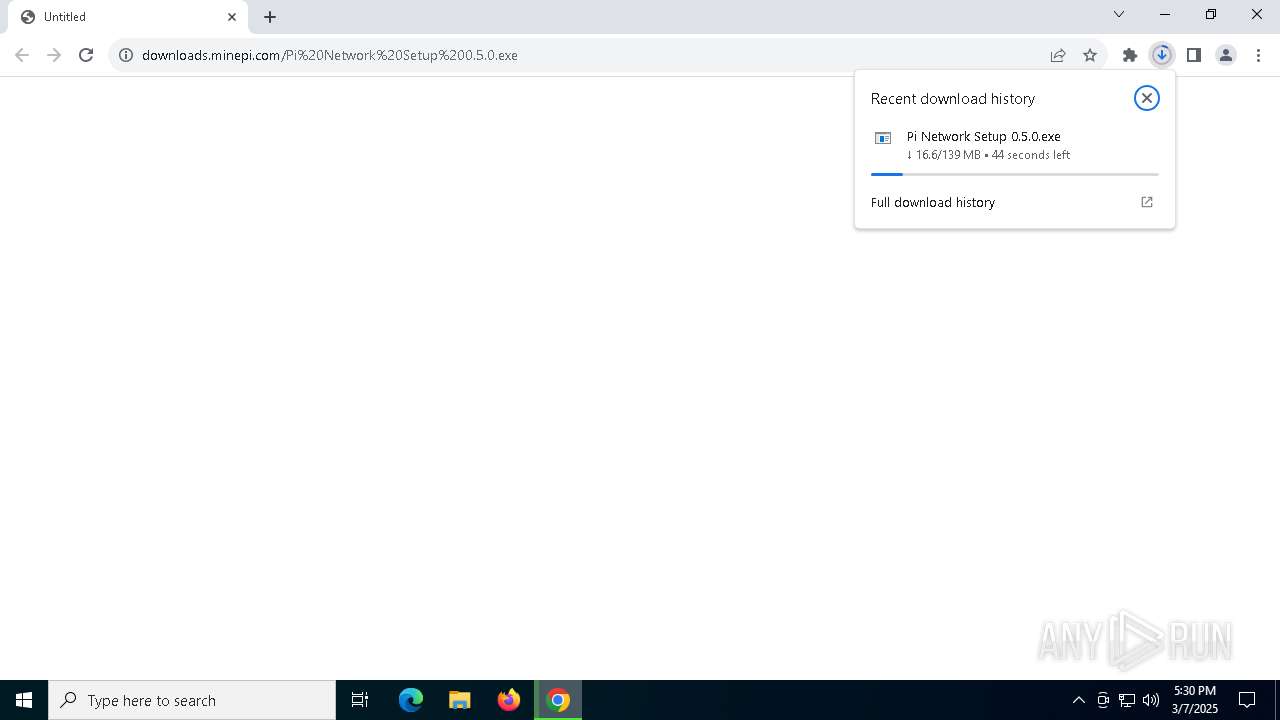
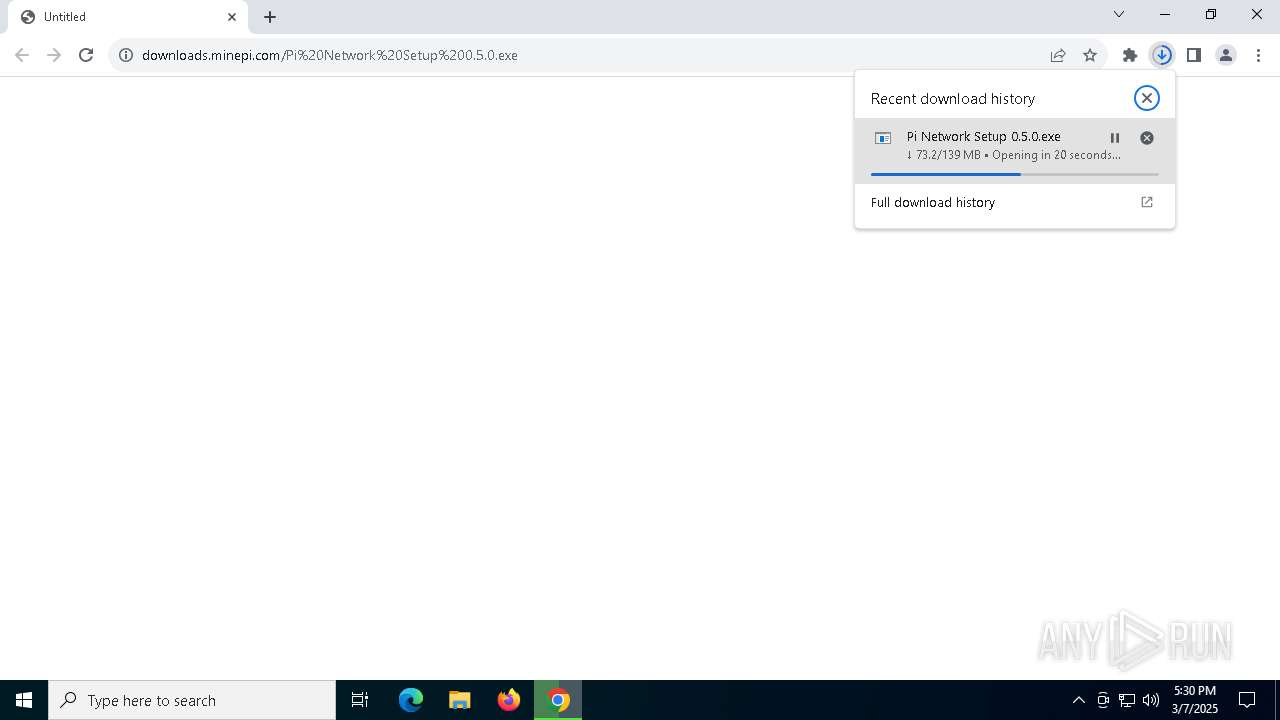
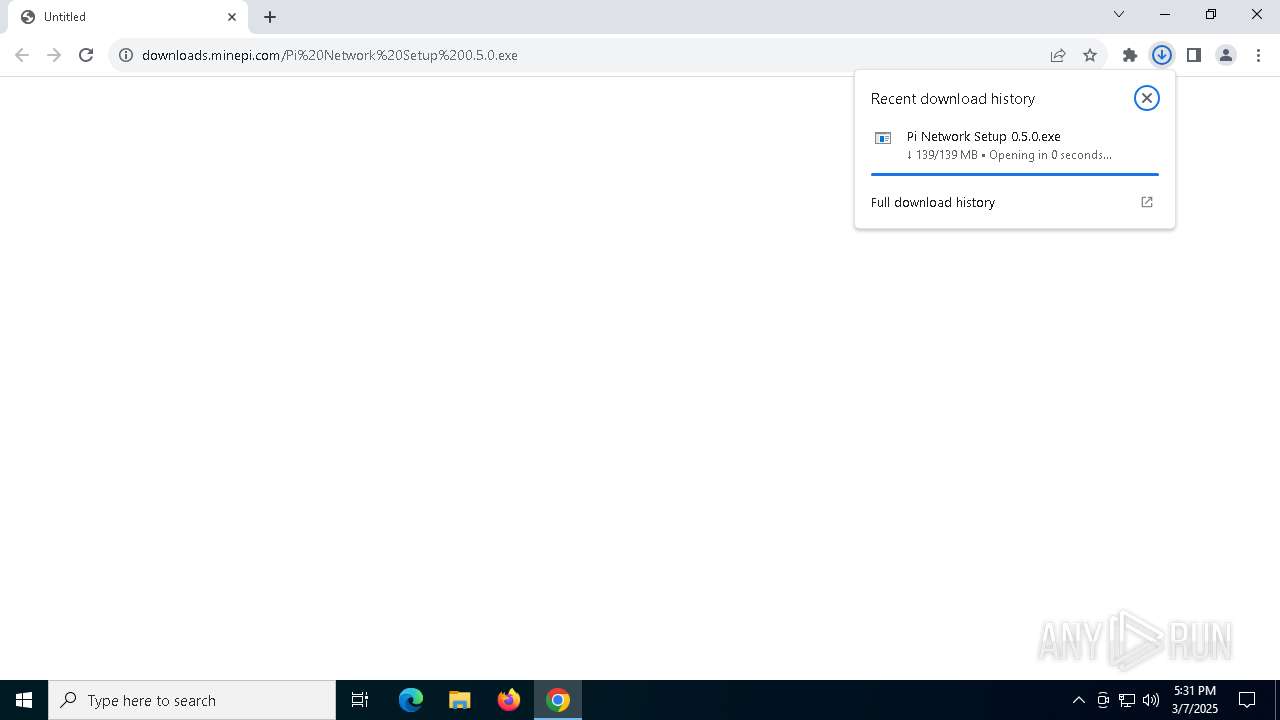
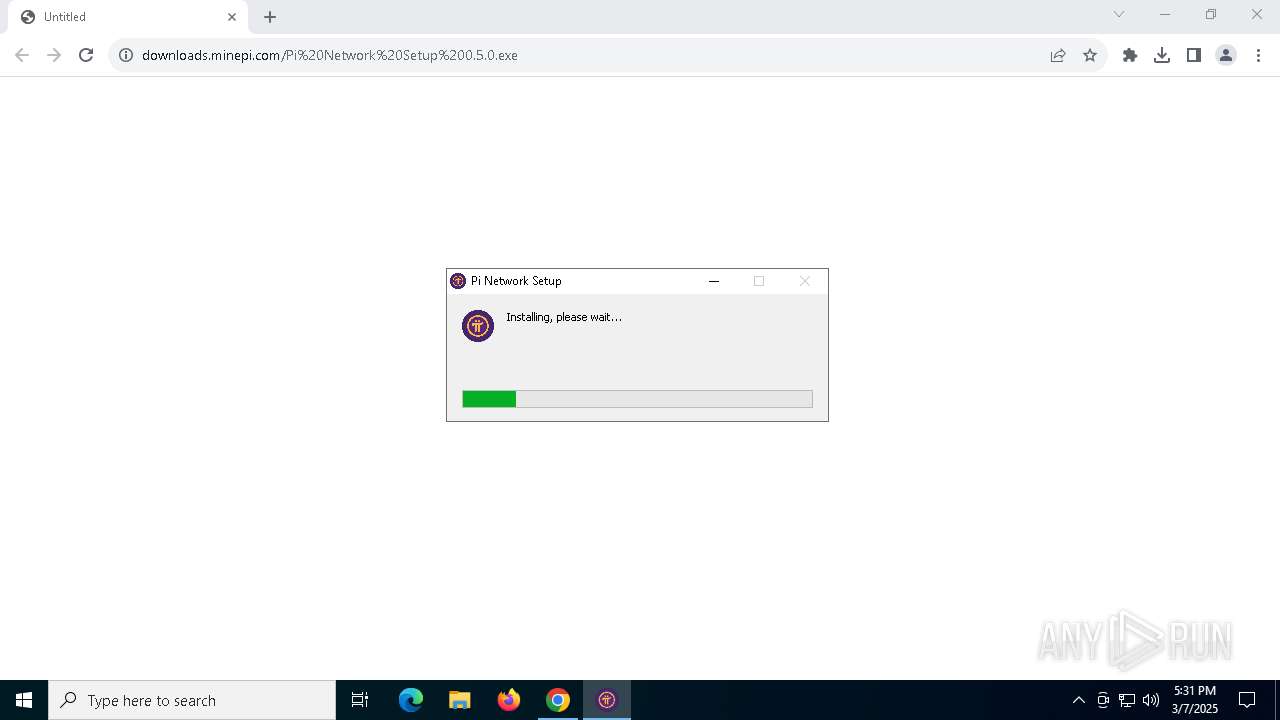
| URL: | https://downloads.minepi.com/Pi%20Network%20Setup%200.5.0.exe |
| Full analysis: | https://app.any.run/tasks/1807383f-04bd-419f-8b16-a8541b947bac |
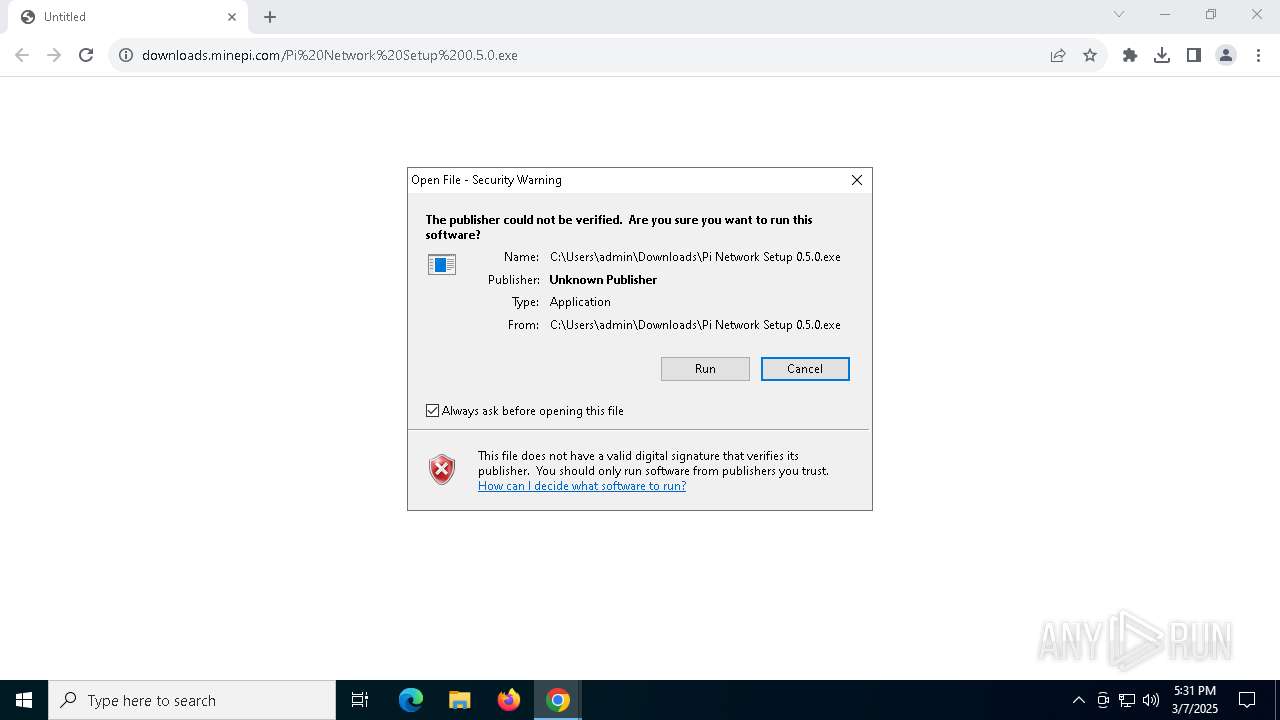
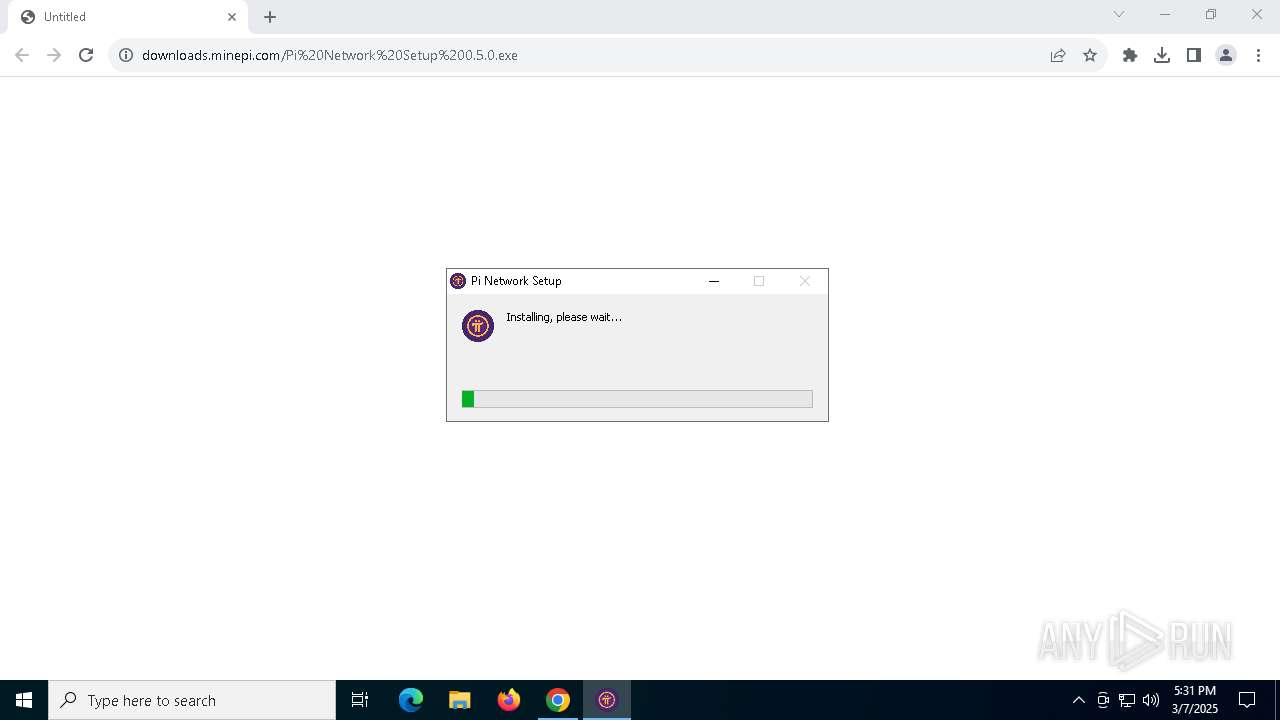
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 17:30:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | C3FEA9F33FE01F273E67D1B1902B48D0 |
| SHA1: | 17987E6975DE28F0F959A6D4A0CB7F84A10D1CAC |
| SHA256: | 28F27195A719F9165D4D7E6CCE863116A69836902D1E96554BDB9371C867A447 |
| SSDEEP: | 3:N8SE4LxsM2uDI5eyc0HcaA:2S+evL |
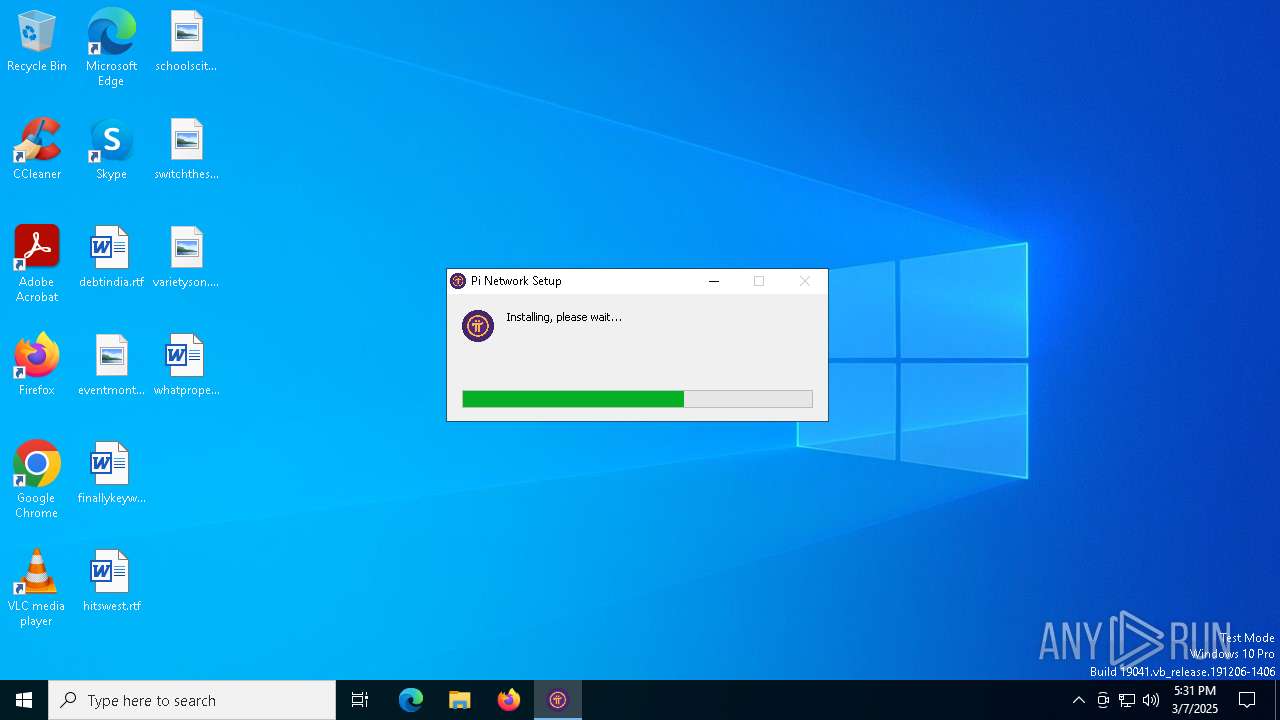
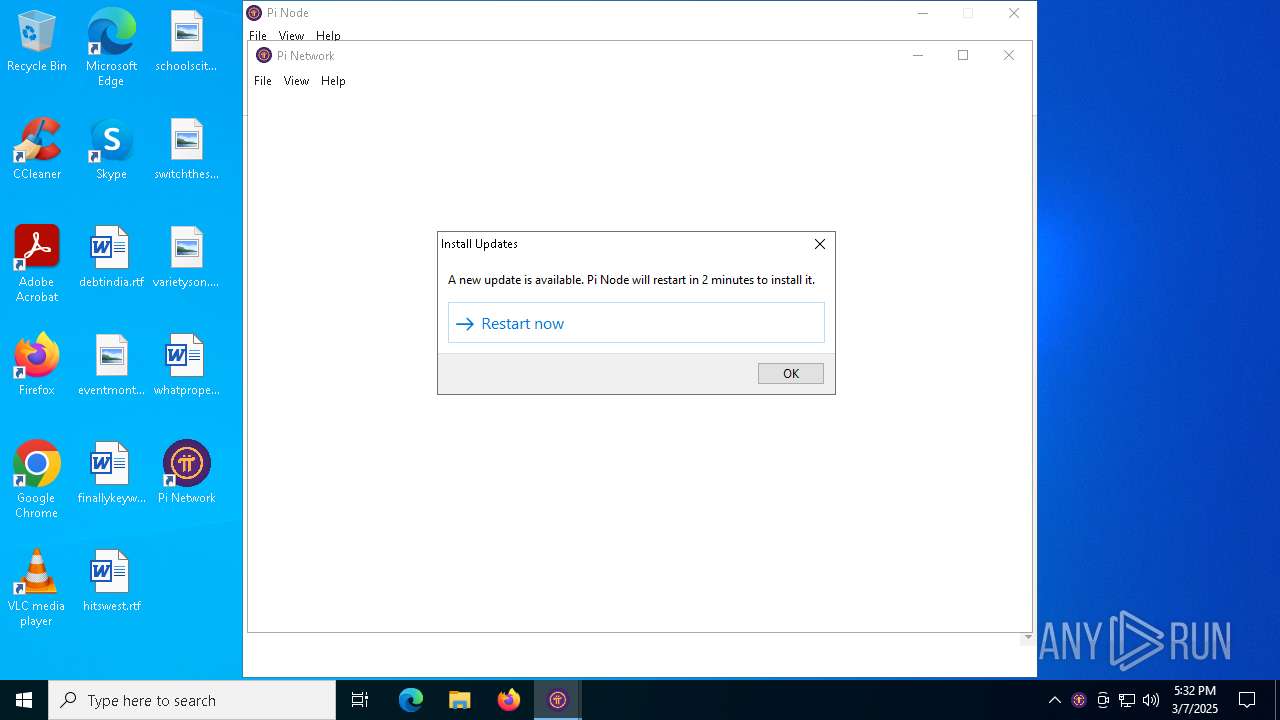
MALICIOUS
Executing a file with an untrusted certificate
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 8068)
- Pi Network.exe (PID: 7772)
- Pi Network.exe (PID: 7800)
- Pi Network.exe (PID: 2392)
- Pi Network.exe (PID: 7748)
- Pi Network.exe (PID: 7756)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
- Pi Network.exe (PID: 6456)
- Pi Network.exe (PID: 4244)
- Pi Network.exe (PID: 7504)
- Pi Network.exe (PID: 7556)
- Pi Network.exe (PID: 7312)
- Pi Network.exe (PID: 6384)
- Pi Network.exe (PID: 7832)
- Pi Network.exe (PID: 4756)
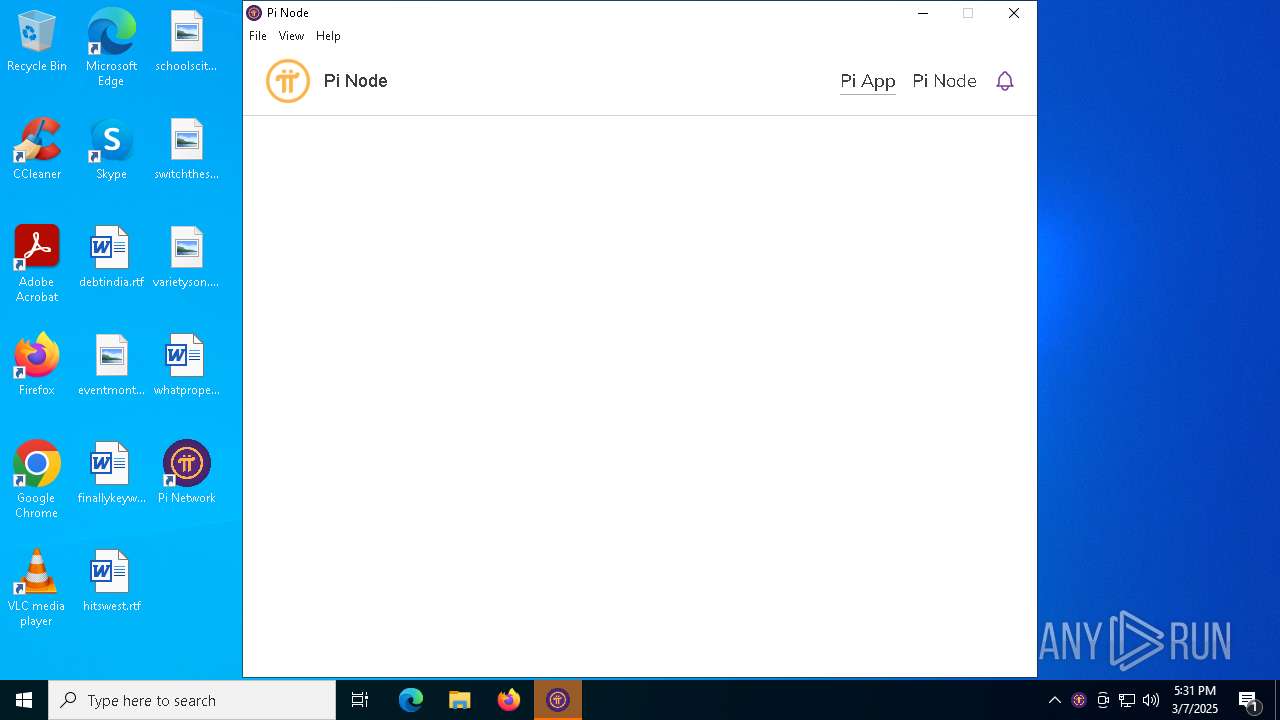
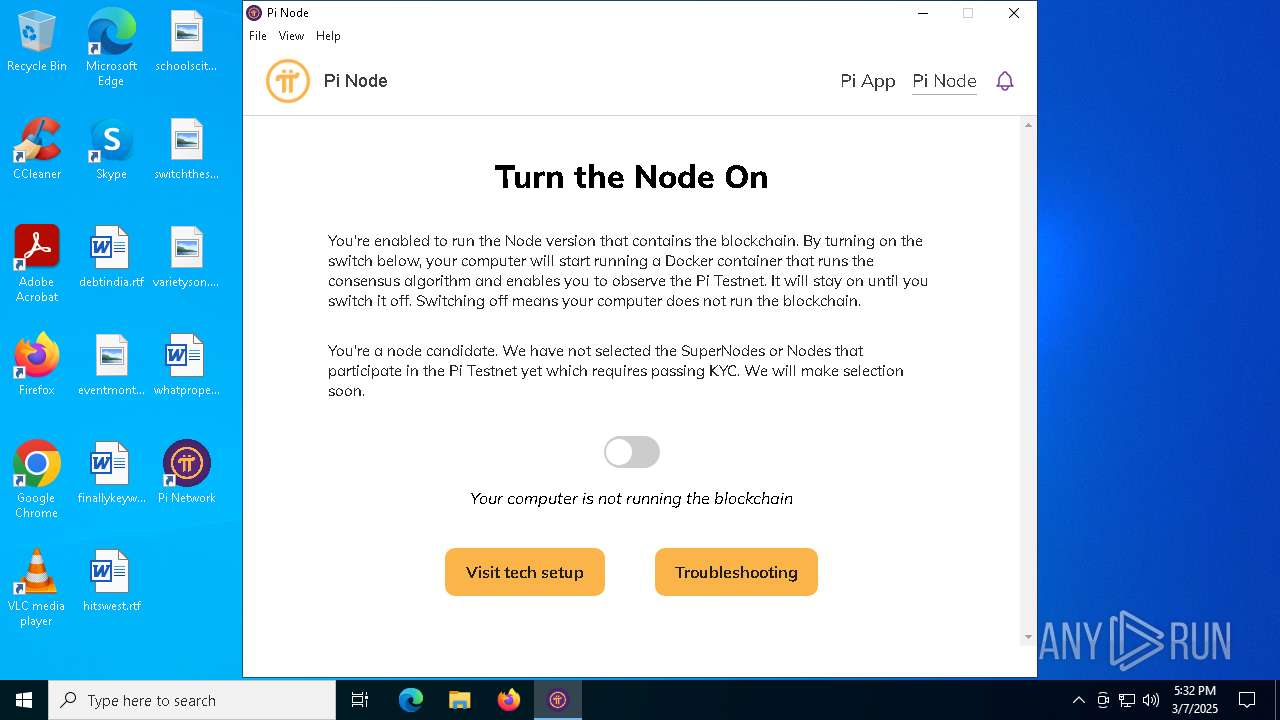
Changes the autorun value in the registry
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 6456)
Changes powershell execution policy (Unrestricted)
- Pi Network.exe (PID: 6456)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
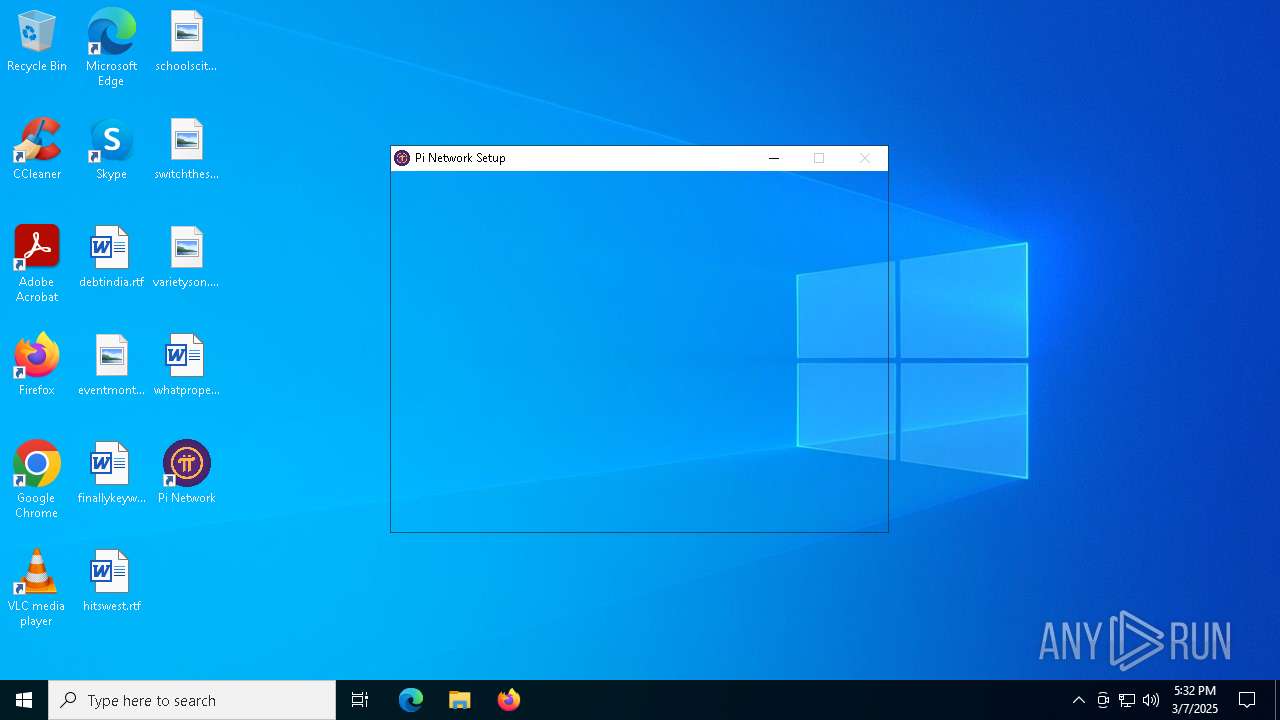
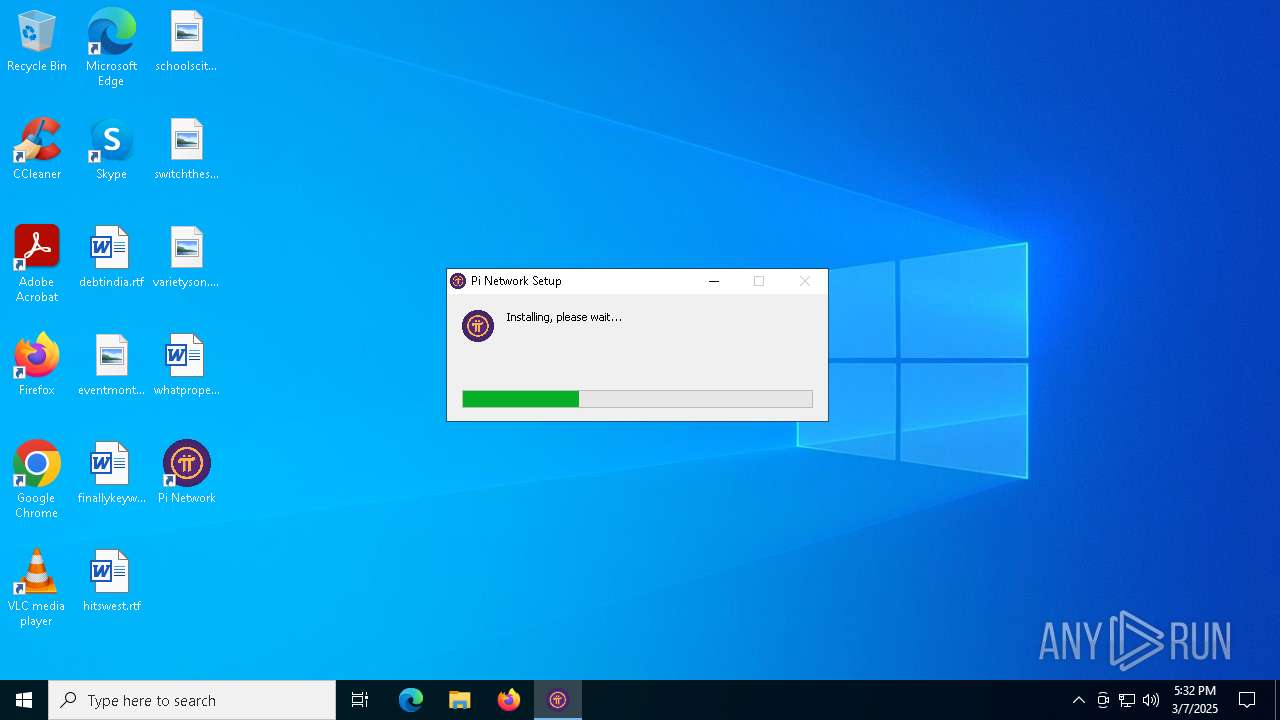
Executable content was dropped or overwritten
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
Starts CMD.EXE for commands execution
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi Network.exe (PID: 6516)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
- Pi Network.exe (PID: 6456)
Get information on the list of running processes
- Pi Network Setup 0.5.0.exe (PID: 1012)
- cmd.exe (PID: 3008)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- cmd.exe (PID: 8024)
- old-uninstaller.exe (PID: 4164)
- cmd.exe (PID: 2644)
Creates a software uninstall entry
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
Reads security settings of Internet Explorer
- Pi Network Setup 0.5.0.exe (PID: 1012)
- ShellExperienceHost.exe (PID: 4112)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
The process creates files with name similar to system file names
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
Application launched itself
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 6456)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6208)
- cmd.exe (PID: 2780)
Process drops legitimate windows executable
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 7788)
- WMIC.exe (PID: 2096)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7564)
Searches for installed software
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
Starts application with an unusual extension
- cmd.exe (PID: 7424)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 728)
The process bypasses the loading of PowerShell profile settings
- Pi Network.exe (PID: 6456)
The process hides Powershell's copyright startup banner
- Pi Network.exe (PID: 6456)
Starts POWERSHELL.EXE for commands execution
- Pi Network.exe (PID: 6456)
INFO
Application launched itself
- chrome.exe (PID: 6620)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8048)
- BackgroundTransferHost.exe (PID: 4560)
- BackgroundTransferHost.exe (PID: 4268)
- BackgroundTransferHost.exe (PID: 5736)
- BackgroundTransferHost.exe (PID: 7144)
- WMIC.exe (PID: 7788)
- WMIC.exe (PID: 2096)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5736)
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi Network.exe (PID: 8068)
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 7800)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- Pi Network.exe (PID: 4244)
- Pi Network.exe (PID: 6456)
- Pi Network.exe (PID: 7556)
- Pi Network.exe (PID: 4756)
Executable content was dropped or overwritten
- chrome.exe (PID: 6620)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5736)
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 6456)
- slui.exe (PID: 3888)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5736)
- slui.exe (PID: 7932)
The sample compiled with english language support
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
Create files in a temporary directory
- Pi Network Setup 0.5.0.exe (PID: 1012)
- Pi Network.exe (PID: 6516)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- old-uninstaller.exe (PID: 4164)
- Pi Network.exe (PID: 6456)
Reads the computer name
- Pi Network Setup 0.5.0.exe (PID: 1012)
- ShellExperienceHost.exe (PID: 4112)
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 7800)
- Pi Network.exe (PID: 7772)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- Pi Network.exe (PID: 6456)
- Pi Network.exe (PID: 7504)
- Pi Network.exe (PID: 7556)
Checks supported languages
- Pi Network Setup 0.5.0.exe (PID: 1012)
- ShellExperienceHost.exe (PID: 4112)
- Pi Network.exe (PID: 8068)
- Pi Network.exe (PID: 7772)
- Pi Network.exe (PID: 7800)
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 2392)
- Pi Network.exe (PID: 7756)
- Pi Network.exe (PID: 7748)
- Pi.Network.Setup.0.5.1.exe (PID: 7328)
- chcp.com (PID: 7508)
- Pi Network.exe (PID: 6456)
- Pi Network.exe (PID: 4244)
- Pi Network.exe (PID: 7504)
- Pi Network.exe (PID: 7312)
- chcp.com (PID: 2040)
- Pi Network.exe (PID: 7832)
- Pi Network.exe (PID: 6384)
Manual execution by a user
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 6456)
Reads Environment values
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 2392)
- Pi Network.exe (PID: 7312)
Reads product name
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 2392)
- Pi Network.exe (PID: 7312)
Process checks computer location settings
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 2392)
- Pi Network.exe (PID: 7756)
- Pi Network.exe (PID: 7748)
- Pi Network.exe (PID: 6456)
- Pi Network.exe (PID: 7312)
- Pi Network.exe (PID: 7832)
- Pi Network.exe (PID: 6384)
Reads the machine GUID from the registry
- Pi Network.exe (PID: 6516)
Reads CPU info
- Pi Network.exe (PID: 6516)
- Pi Network.exe (PID: 6456)
Changes the display of characters in the console
- cmd.exe (PID: 7424)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
702
Monitored processes
552
Malicious processes
8
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /d /s /c "docker compose -f "C:\Users\admin\AppData\Roaming\Pi Network\docker-compose.json" stop " | C:\Windows\System32\cmd.exe | — | Pi Network.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\system32\cmd.exe /d /s /c "docker compose -f "C:\Users\admin\AppData\Roaming\Pi Network\docker-compose.json" exec testnet2 supervisorctl status horizon" | C:\Windows\System32\cmd.exe | — | Pi Network.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
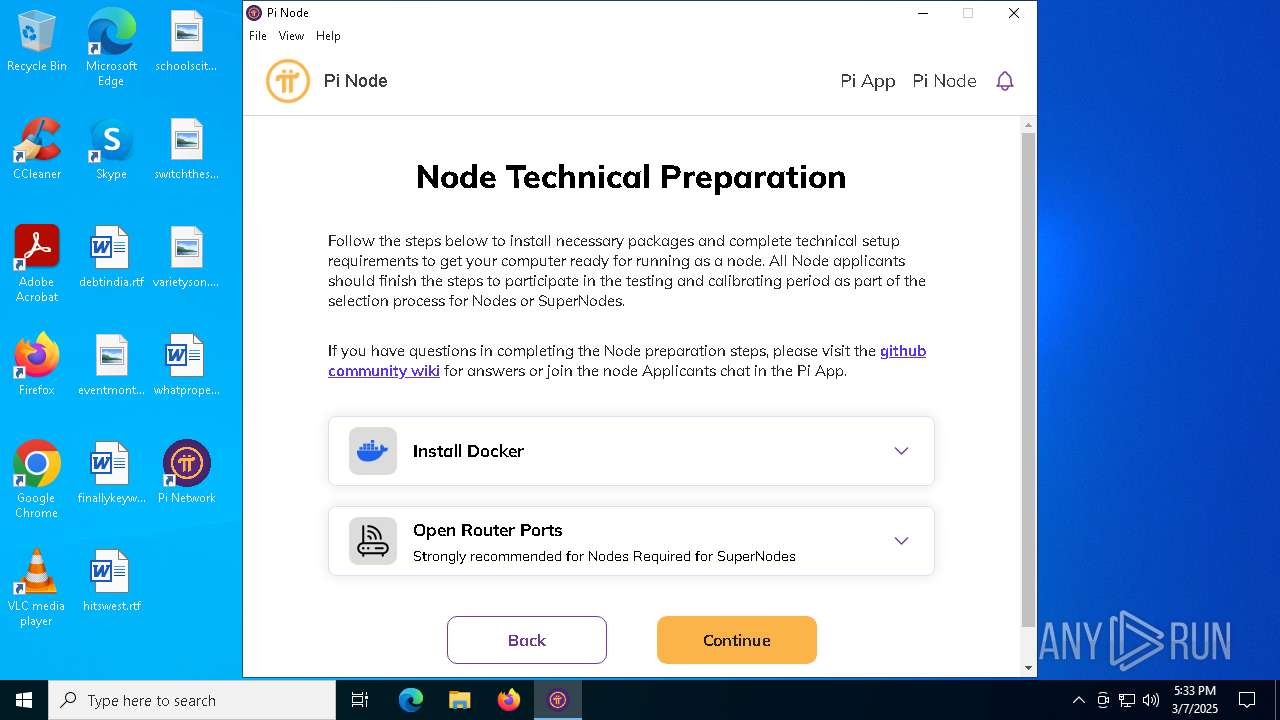
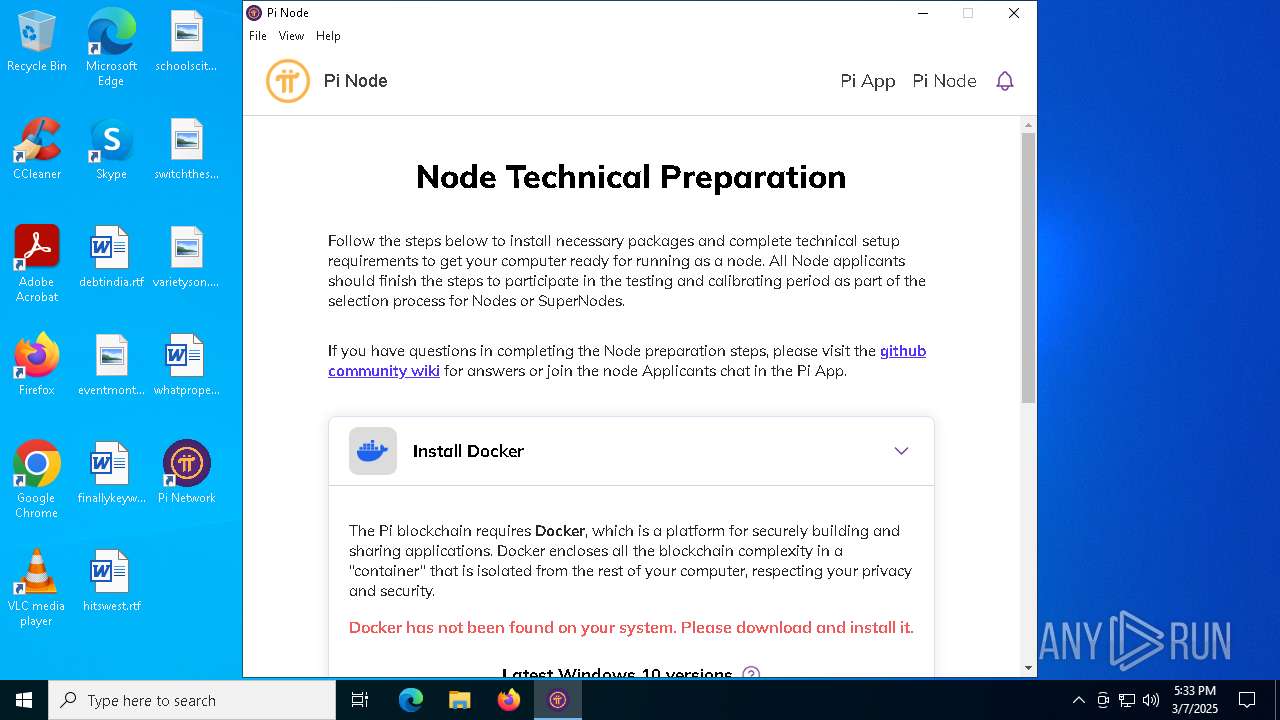
| 664 | C:\WINDOWS\system32\cmd.exe /d /s /c "docker --version" | C:\Windows\System32\cmd.exe | — | Pi Network.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\cmd.exe /d /s /c "docker stop pi-port-checker" | C:\Windows\System32\cmd.exe | — | Pi Network.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
84 289
Read events
84 194
Write events
54
Delete events
41
Modification events
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (8048) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8048) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8048) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5736) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5736) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
63
Suspicious files
561
Text files
358
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10bcd9.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10bcd9.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10bcd9.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10bce9.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10bce9.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10bcf9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
83
DNS requests
73
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7788 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7868 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5736 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4208 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
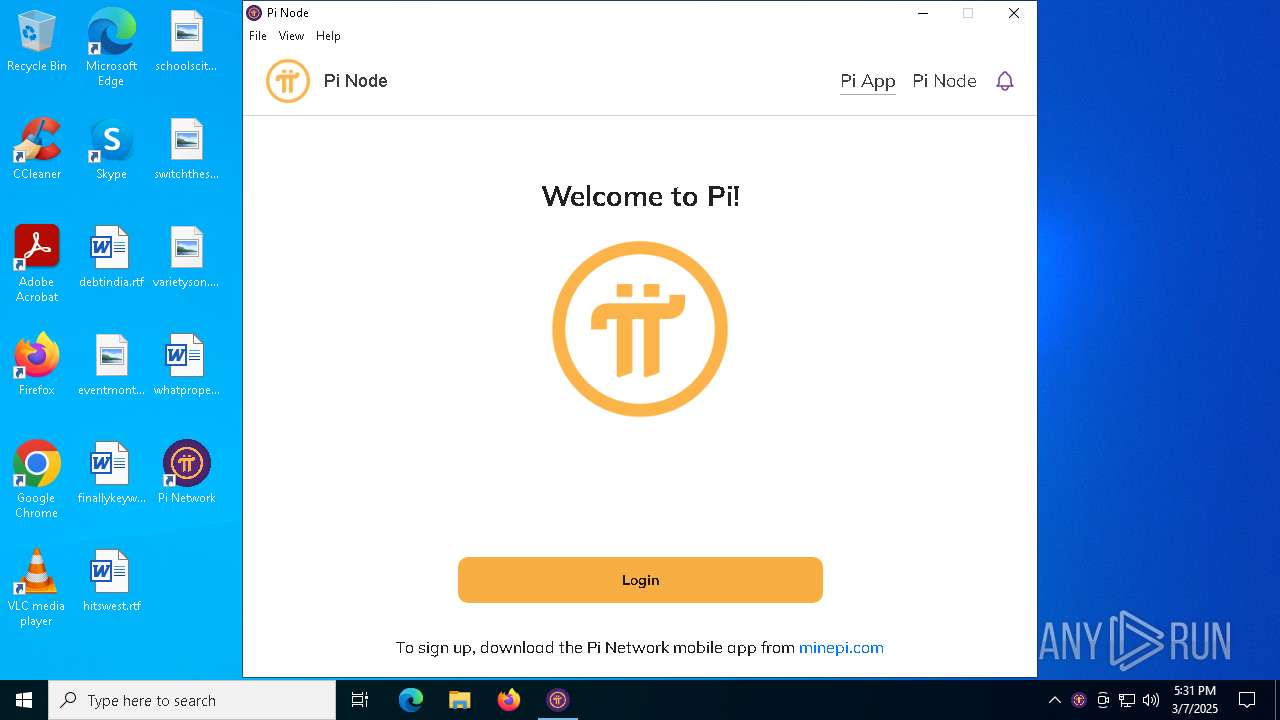
7328 | chrome.exe | 64.227.96.68:443 | downloads.minepi.com | DIGITALOCEAN-ASN | US | unknown |
6620 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7328 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
downloads.minepi.com |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7800 | Pi Network.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7800 | Pi Network.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7556 | Pi Network.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7556 | Pi Network.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |