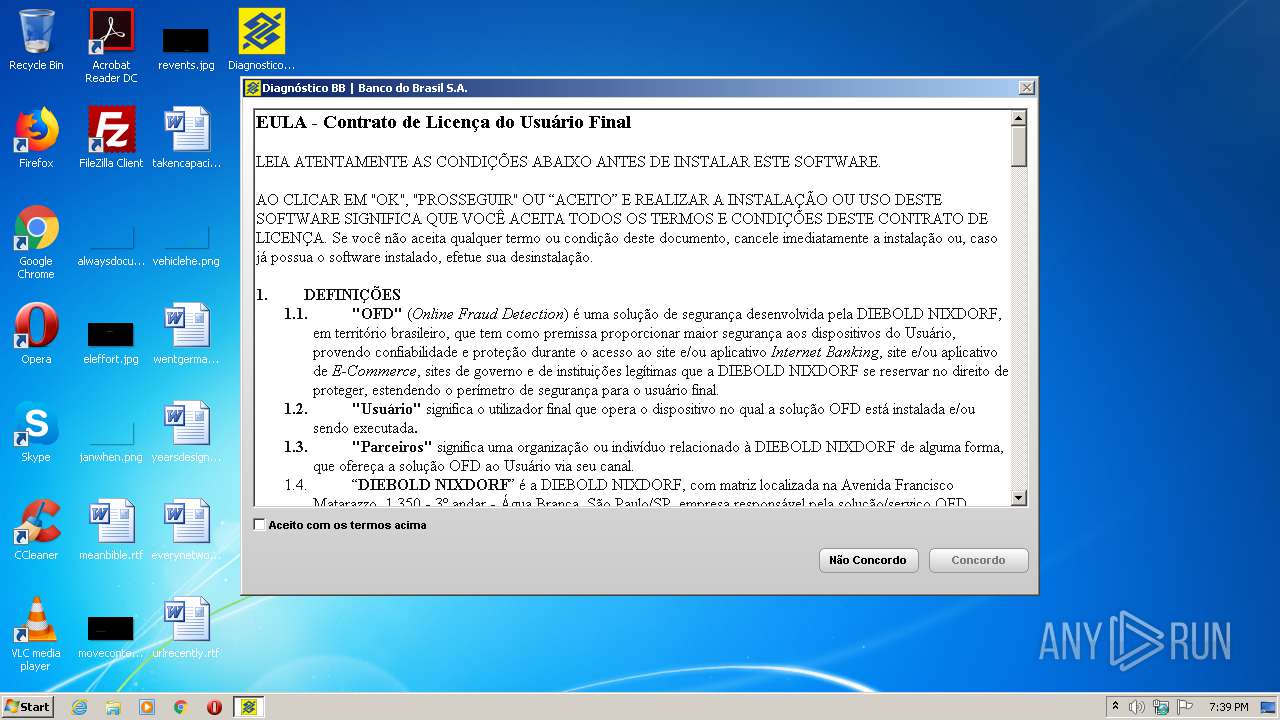
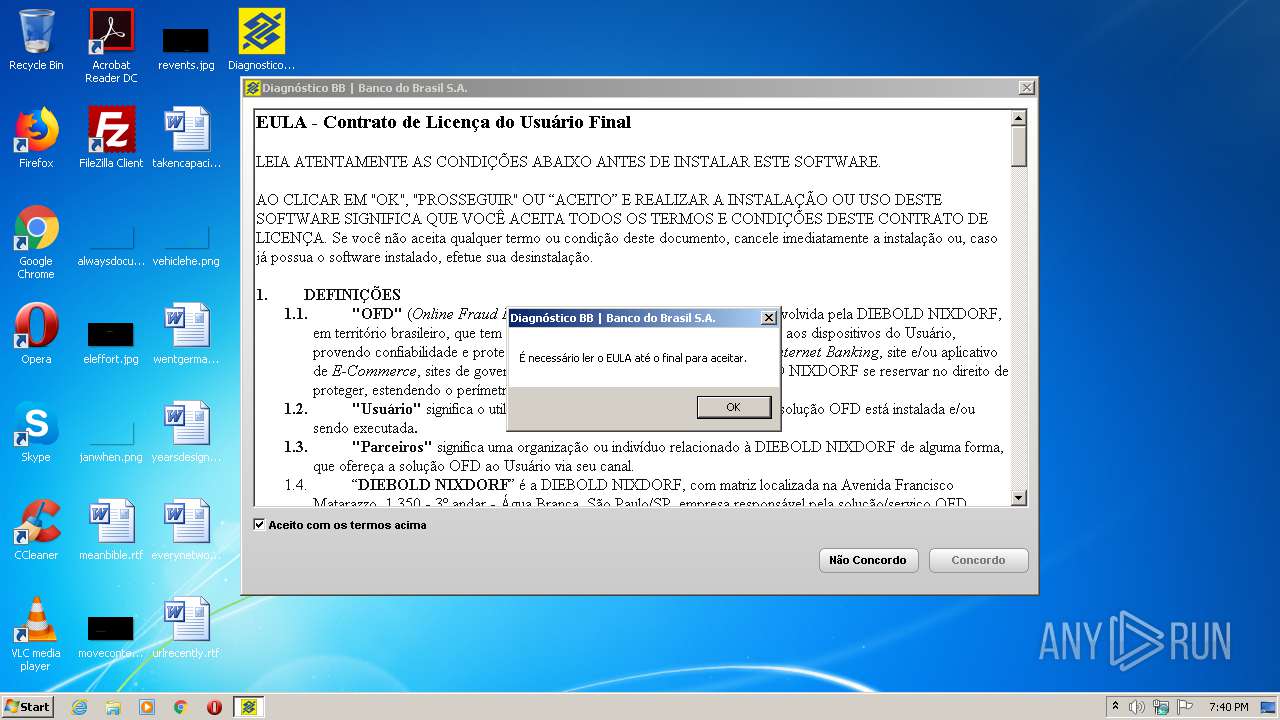
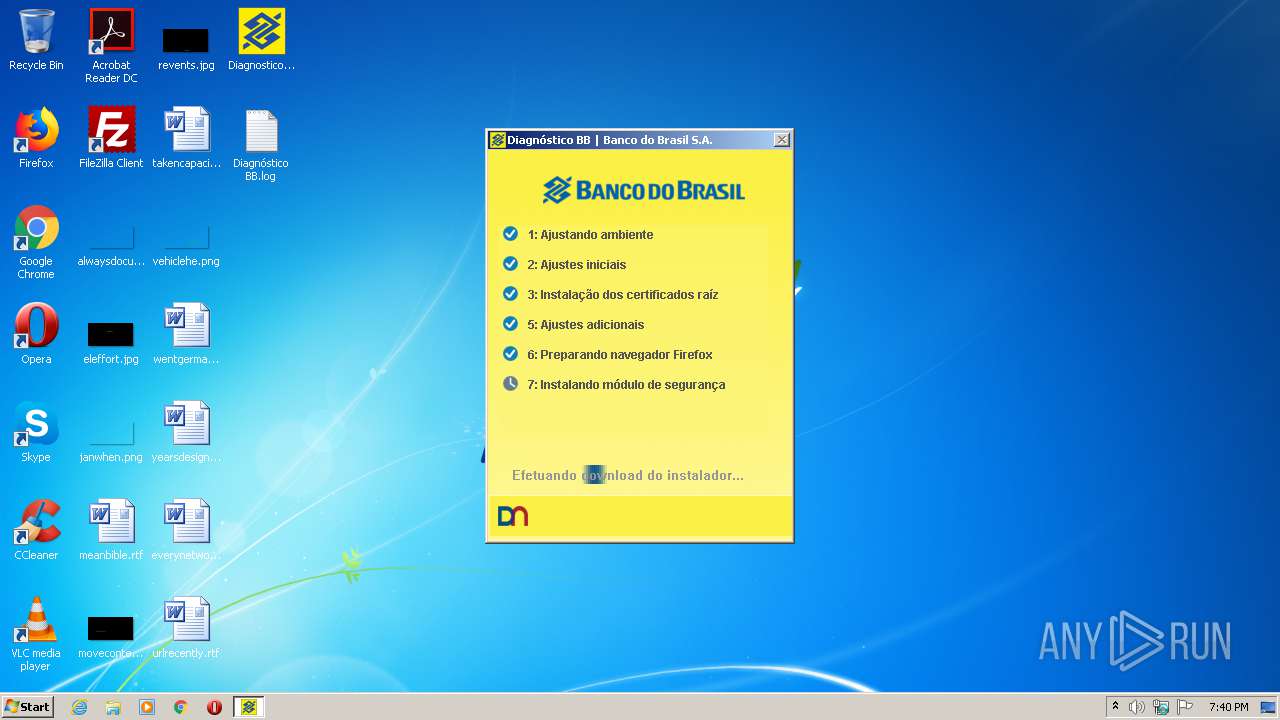
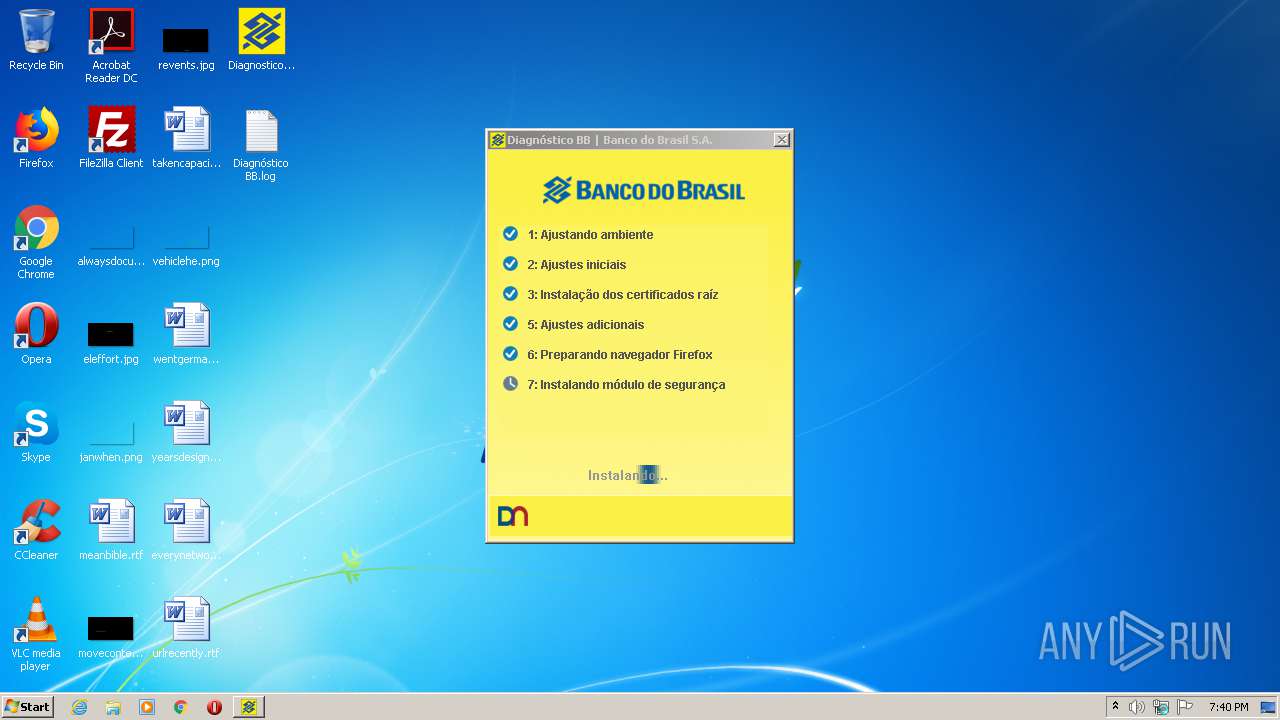
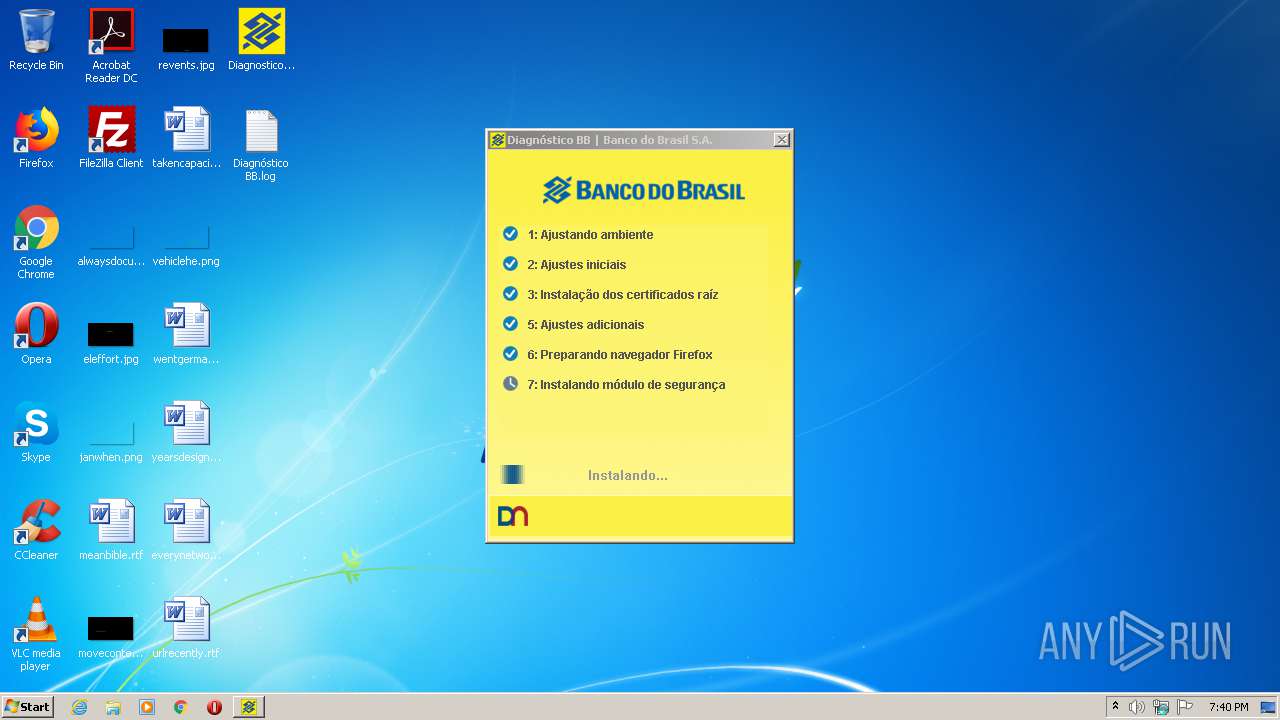
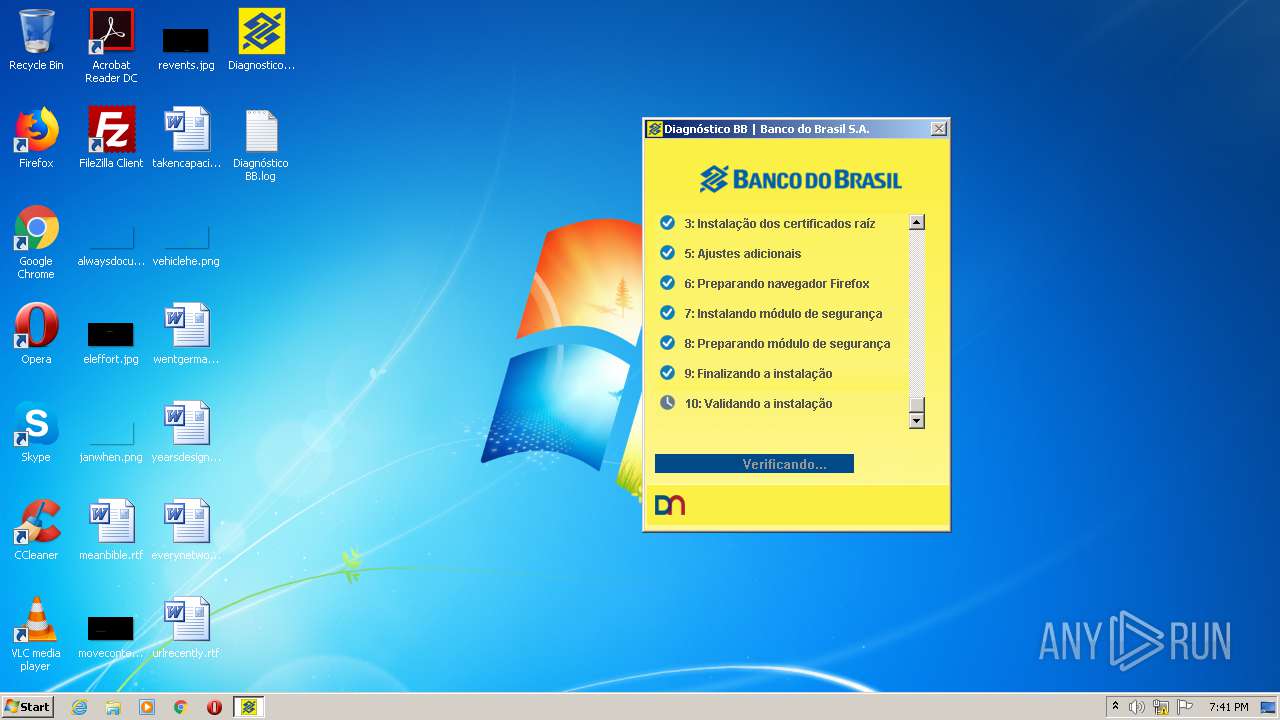
| File name: | DiagnosticoBB.exe |
| Full analysis: | https://app.any.run/tasks/00da2a5b-59d5-4742-b76f-1deca63af50c |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2020, 18:39:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AE2C02E869D3386633F96D8828DF6DFF |
| SHA1: | 238D634842505B77611A6F5FBE04A742BA69E854 |
| SHA256: | 28DEFFC419C1EAAFF4A5288D692026EE7CF350633E1484F07D5D70B8CA14A079 |
| SSDEEP: | 98304:OvzdpCuVCALwdebHSEgjaZZk8ymjcvnvXUU7uSmnhR0:eCuTJYaZulnvXtDOhR0 |
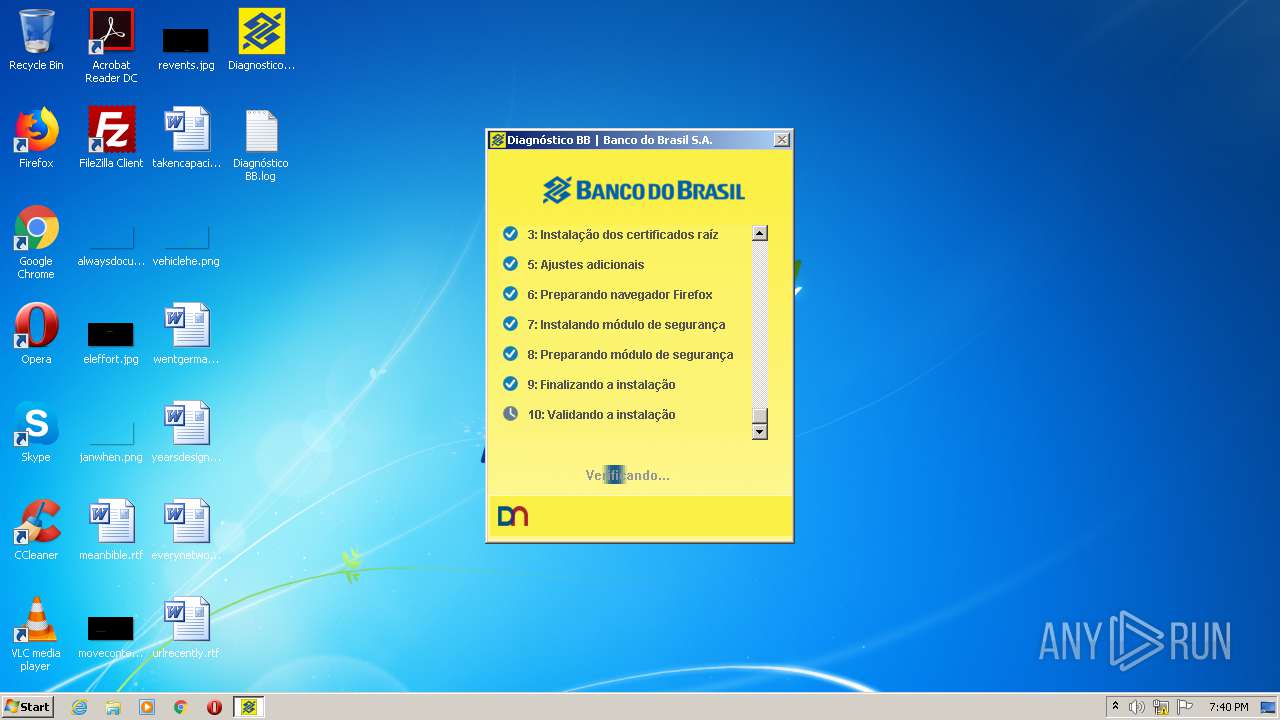
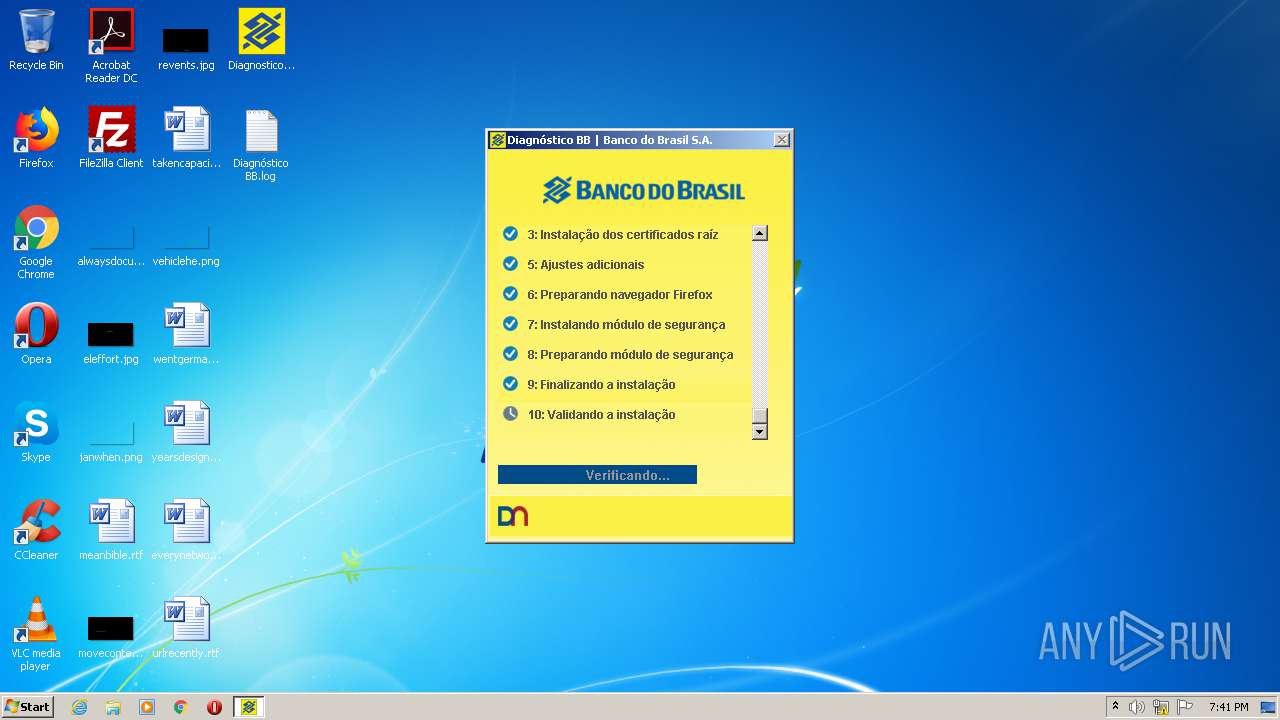
MALICIOUS
Actions looks like stealing of personal data
- DiagnosticoBB.exe (PID: 2872)
- wsffcmgr.exe (PID: 3284)
Changes settings of System certificates
- DiagnosticoBB.exe (PID: 2148)
- core.exe (PID: 1900)
Application was dropped or rewritten from another process
- warsaw_setup_32.exe (PID: 676)
- get_version.exe (PID: 3272)
- warsaw_setup_32.tmp (PID: 1296)
- get_version.exe (PID: 2804)
- core.exe (PID: 1900)
- core.exe (PID: 2292)
- core.exe (PID: 1912)
- corefixer.exe (PID: 1152)
- impersonate.exe (PID: 3392)
- wsffcmgr.exe (PID: 3284)
Loads dropped or rewritten executable
- rundll32.exe (PID: 980)
- core.exe (PID: 1912)
- rundll32.exe (PID: 3956)
- rundll32.exe (PID: 2056)
- core.exe (PID: 2292)
- core.exe (PID: 1900)
Loads the Task Scheduler COM API
- corefixer.exe (PID: 1152)
SUSPICIOUS
Application launched itself
- DiagnosticoBB.exe (PID: 2872)
Creates files in the program directory
- DiagnosticoBB.exe (PID: 2148)
- warsaw_setup_32.tmp (PID: 1296)
- DiagnosticoBB.exe (PID: 2872)
- core.exe (PID: 1900)
Executed as Windows Service
- DiagnosticoBB.exe (PID: 2148)
- core.exe (PID: 1900)
- vssvc.exe (PID: 2636)
Reads Internet Cache Settings
- DiagnosticoBB.exe (PID: 2872)
- core.exe (PID: 1912)
- DllHost.exe (PID: 1712)
Executable content was dropped or overwritten
- DiagnosticoBB.exe (PID: 2872)
- warsaw_setup_32.exe (PID: 676)
- warsaw_setup_32.tmp (PID: 1296)
- core.exe (PID: 1900)
- DrvInst.exe (PID: 968)
Adds / modifies Windows certificates
- DiagnosticoBB.exe (PID: 2148)
- core.exe (PID: 1900)
Creates files in the Windows directory
- warsaw_setup_32.exe (PID: 676)
- warsaw_setup_32.tmp (PID: 1296)
- get_version.exe (PID: 2804)
- cmd.exe (PID: 1564)
- core.exe (PID: 1900)
- DrvInst.exe (PID: 968)
Reads Windows owner or organization settings
- warsaw_setup_32.tmp (PID: 1296)
Reads the Windows organization settings
- warsaw_setup_32.tmp (PID: 1296)
Starts SC.EXE for service management
- warsaw_setup_32.tmp (PID: 1296)
Creates a software uninstall entry
- warsaw_setup_32.tmp (PID: 1296)
Uses RUNDLL32.EXE to load library
- warsaw_setup_32.tmp (PID: 1296)
- impersonate.exe (PID: 3392)
Reads the BIOS version
- core.exe (PID: 1900)
Creates or modifies windows services
- core.exe (PID: 1900)
Low-level read access rights to disk partition
- core.exe (PID: 1900)
Executed via COM
- DllHost.exe (PID: 1712)
- DrvInst.exe (PID: 968)
Creates files in the driver directory
- warsaw_setup_32.tmp (PID: 1296)
- core.exe (PID: 1900)
- DrvInst.exe (PID: 968)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1564)
- warsaw_setup_32.tmp (PID: 1296)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2968)
- cmd.exe (PID: 1564)
Removes files from Windows directory
- core.exe (PID: 1900)
- warsaw_setup_32.exe (PID: 676)
- DrvInst.exe (PID: 968)
- warsaw_setup_32.tmp (PID: 1296)
Loads DLL from Mozilla Firefox
- wsffcmgr.exe (PID: 3284)
Creates files in the user directory
- wsffcmgr.exe (PID: 3284)
INFO
Reads the hosts file
- DiagnosticoBB.exe (PID: 2148)
- core.exe (PID: 1900)
Dropped object may contain Bitcoin addresses
- warsaw_setup_32.tmp (PID: 1296)
Reads settings of System Certificates
- core.exe (PID: 1900)
- DiagnosticoBB.exe (PID: 2872)
Changes settings of System certificates
- DrvInst.exe (PID: 968)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2636)
Searches for installed software
- DrvInst.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:07 19:22:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 2447872 |
| InitializedDataSize: | 3520000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d145c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.6.0.12 |
| ProductVersionNumber: | 2.6.0.12 |
| FileFlagsMask: | 0x001f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (0016) |
| CharacterSet: | Unicode |
| CompanyName: | Banco do Brasil S.A. |
| FileDescription: | Diagnóstico BB |
| FileVersion: | 2,6,0,12 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2020, Diebold Nixdorf |
| OriginalFileName: | DiagnosticoBB_CLOUD_PT |
| PrivateBuild: | 2,6,0,12 |
| ProductName: | Diagnóstico BB |
| ProductVersion: | 2,6,0,12 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Feb-2020 18:22:54 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Banco do Brasil S.A. |
| FileDescription: | Diagnóstico BB |
| FileVersion: | 2,6,0,12 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2020, Diebold Nixdorf |
| OriginalFilename: | DiagnosticoBB_CLOUD_PT |
| PrivateBuild: | 2,6,0,12 |
| ProductName: | Diagnóstico BB |
| ProductVersion: | 2,6,0,12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 07-Feb-2020 18:22:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00234A4A | 0x00234C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66641 |
CODE | 0x00236000 | 0x00020DA0 | 0x00020E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58405 |
.rdata | 0x00257000 | 0x0004A952 | 0x0004AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44495 |
.data | 0x002A2000 | 0x000100E8 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17424 |
DATA | 0x002B3000 | 0x000014E0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98815 |
BSS | 0x002B5000 | 0x00000761 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x002B6000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x002B7000 | 0x002D9258 | 0x002D9400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.69366 |
.reloc | 0x00591000 | 0x0002C162 | 0x0002C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.14299 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87512 | 900 | Latin 1 / Western European | Portuguese - Brazil | RT_MANIFEST |
2 | 6.09242 | 7336 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
3 | 6.28267 | 3240 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
101 | 7.54665 | 1292 | Latin 1 / Western European | Portuguese - Brazil | FILE |
104 | 7.94318 | 57829 | Latin 1 / Western European | Portuguese - Brazil | IMG |
105 | 7.41396 | 557 | Latin 1 / Western European | Portuguese - Brazil | IMG |
106 | 7.36799 | 454 | Latin 1 / Western European | Portuguese - Brazil | IMG |
107 | 7.62796 | 563 | Latin 1 / Western European | Portuguese - Brazil | IMG |
108 | 7.30965 | 465 | Latin 1 / Western European | Portuguese - Brazil | IMG |
112 | 7.87518 | 3463 | Latin 1 / Western European | Portuguese - Brazil | FILE |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
NETAPI32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
76
Monitored processes
27
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | find /C "core.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | C:\ProgramData\Temp\warsaw_setup_32.exe /verysilent /sp- /norestart /suppressmsgboxes /restartexitcode=3010 /nocancel /accepteula /log="C:\ProgramData\Temp\wslog.dat" | C:\ProgramData\Temp\warsaw_setup_32.exe | DiagnosticoBB.exe | ||||||||||||
User: SYSTEM Company: Diebold Nixdorf Integrity Level: SYSTEM Description: Warsaw Exit code: 0 Version: 2.11.1.9 Modules
| |||||||||||||||
| 968 | DrvInst.exe "4" "8" "C:\Windows\TEMP\{61ad85d3-85e1-2262-bc90-1a4ec5a7f060}\wsddntf.inf" "0" "6a6586d23" "000003C4" "Service-0x0-3e7$\Default" "00000570" "208" "C:\Windows\system32\drivers" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | "C:\Windows\system32\rundll32.exe" "C:\Program Files\Diebold\Warsaw\wslbmid.dll", Function6 C:\Program Files\Diebold\Warsaw | C:\Windows\system32\rundll32.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | "C:\Windows\TEMP\is-TVFCR.tmp\corefixer.exe" /nocert | C:\Windows\TEMP\is-TVFCR.tmp\corefixer.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Warsaw Fixer Exit code: 0 Version: 1.7.2.127 Modules
| |||||||||||||||
| 1296 | "C:\Windows\TEMP\is-RV6SB.tmp\warsaw_setup_32.tmp" /SL5="$30144,19196216,121344,C:\ProgramData\Temp\warsaw_setup_32.exe" /verysilent /sp- /norestart /suppressmsgboxes /restartexitcode=3010 /nocancel /accepteula /log="C:\ProgramData\Temp\wslog.dat" | C:\Windows\TEMP\is-RV6SB.tmp\warsaw_setup_32.tmp | warsaw_setup_32.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1564 | "C:\Windows\system32\cmd.exe" /c C:\Windows\TEMP\is-TVFCR.tmp\check_core.bat | C:\Windows\system32\cmd.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1712 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Diebold\Warsaw\core.exe" | C:\Program Files\Diebold\Warsaw\core.exe | services.exe | ||||||||||||
User: SYSTEM Company: Diebold Nixdorf Integrity Level: SYSTEM Description: Diebold Nixdorf - Protection Module Exit code: 0 Version: 2.9.0.54 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Diebold\Warsaw\core.exe" | C:\Program Files\Diebold\Warsaw\core.exe | — | core.exe | |||||||||||
User: admin Company: Diebold Nixdorf Integrity Level: MEDIUM Description: Diebold Nixdorf - Protection Module Exit code: 0 Version: 2.9.0.54 Modules
| |||||||||||||||
Total events
813
Read events
469
Write events
340
Delete events
4
Modification events
| (PID) Process: | (2872) DiagnosticoBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2872) DiagnosticoBB.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\S-1-5-19\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\S-1-5-20\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 672 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2560 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\S-1-5-19\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2560 | |||
| (PID) Process: | (2148) DiagnosticoBB.exe | Key: | HKEY_USERS\S-1-5-20\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2560 | |||
Executable files
58
Suspicious files
53
Text files
133
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | DiagnosticoBB.exe | C:\Users\Administrator\NTUSER.DAT | — | |
MD5:— | SHA256:— | |||
| 2148 | DiagnosticoBB.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | — | |
MD5:— | SHA256:— | |||
| 2872 | DiagnosticoBB.exe | C:\ProgramData\Temp\cert1.cer | — | |
MD5:— | SHA256:— | |||
| 2148 | DiagnosticoBB.exe | C:\ProgramData\Temp\cert_temp\cert0.cer | — | |
MD5:— | SHA256:— | |||
| 2148 | DiagnosticoBB.exe | C:\ProgramData\Temp\cert_temp\cert1.cer | — | |
MD5:— | SHA256:— | |||
| 1296 | warsaw_setup_32.tmp | C:\Program Files\Diebold\Warsaw:z2fzaw5z | — | |
MD5:— | SHA256:— | |||
| 1296 | warsaw_setup_32.tmp | C:\Program Files\Diebold\Warsaw\is-U8AVS.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | warsaw_setup_32.tmp | C:\Program Files\Diebold\Warsaw\is-RO969.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | warsaw_setup_32.tmp | C:\Program Files\Diebold\Warsaw\is-B9DAH.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | warsaw_setup_32.tmp | C:\Program Files\Diebold\Warsaw\is-QIBL3.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
38
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2872 | DiagnosticoBB.exe | 52.222.149.151:443 | dn.gastecnologia.com.br | Amazon.com, Inc. | US | whitelisted |
2872 | DiagnosticoBB.exe | 52.222.156.186:443 | cloud.gastecnologia.com.br | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dn.gastecnologia.com.br |
| shared |
cloud.gastecnologia.com.br |
| suspicious |