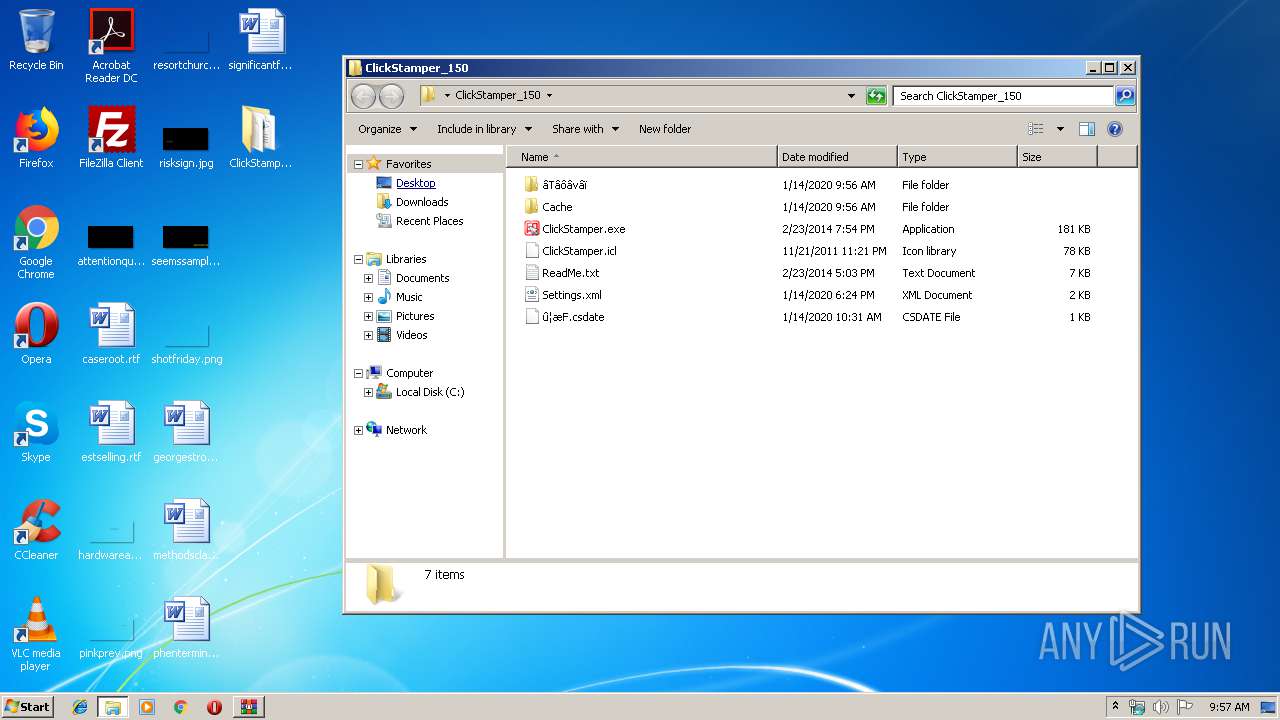
| File name: | ClickStamper_150.zip |
| Full analysis: | https://app.any.run/tasks/a628b155-f22f-4425-9acd-33b37ce39ec3 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2020, 09:56:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8CDC56A1878E84AF041FDD46AAB279FA |
| SHA1: | 3199DF169B47D728F92E46D0913FF97CDA9FBBFF |
| SHA256: | 28B53B0A08FFA136D586BAEB4BC8E36FEF55D70AE46BD4DBEDAED3F60D21C9EC |
| SSDEEP: | 3072:0UtFHBNnDuHRVzNvReZieZEQyUjXwR8QGo6pob4kY6+vVlbNmfvvoHJB0VXILj:0UlNnD4voWCARu7pyUvV/kvvoHOXg |
MALICIOUS
Application was dropped or rewritten from another process
- ClickStamper.exe (PID: 1908)
Starts Visual C# compiler
- ClickStamper.exe (PID: 1908)
SUSPICIOUS
Reads Internet Cache Settings
- ClickStamper.exe (PID: 1908)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4060)
INFO
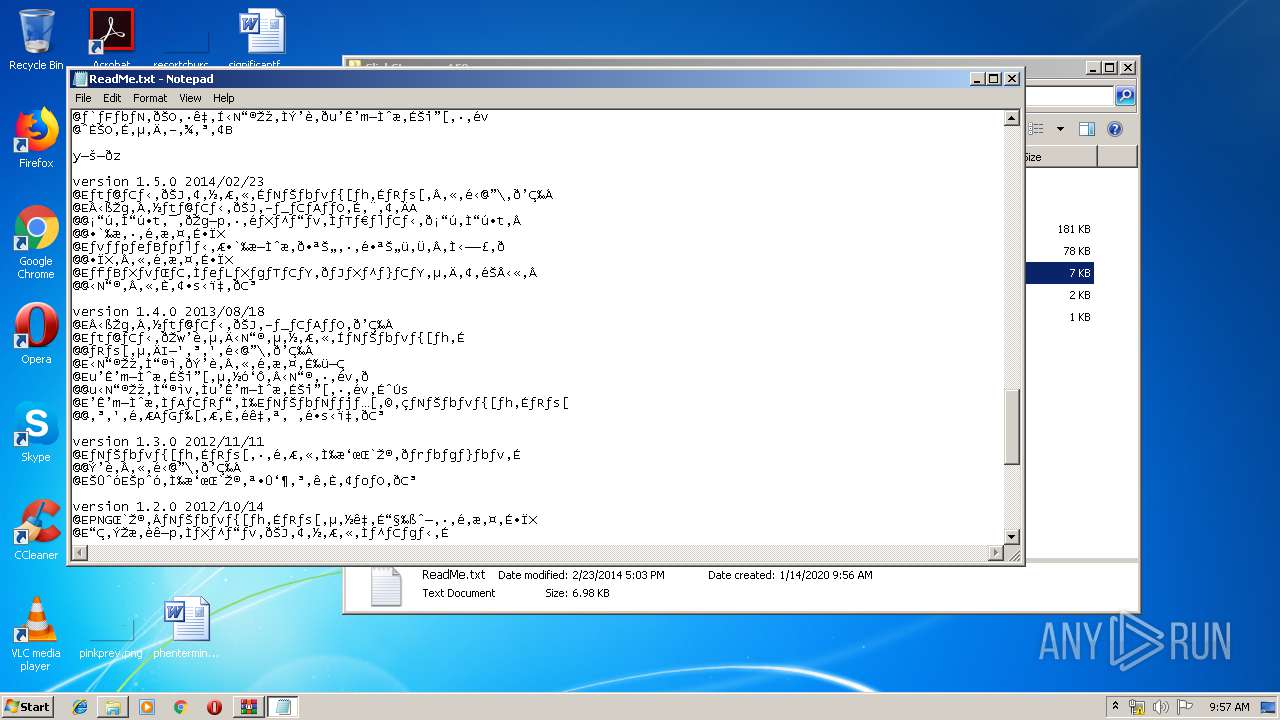
Manual execution by user
- NOTEPAD.EXE (PID: 1292)
- ClickStamper.exe (PID: 1908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:14 10:31:19 |
| ZipCRC: | 0x960da55d |
| ZipCompressedSize: | 452 |
| ZipUncompressedSize: | 816 |
| ZipFileName: | ClickStamper_150/Cache/EE887CB448EA08D7512AA710C8AD52761947709C |
Total processes
46
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES391C.tmp" "c:\Users\admin\AppData\Local\Temp\CSC391B.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
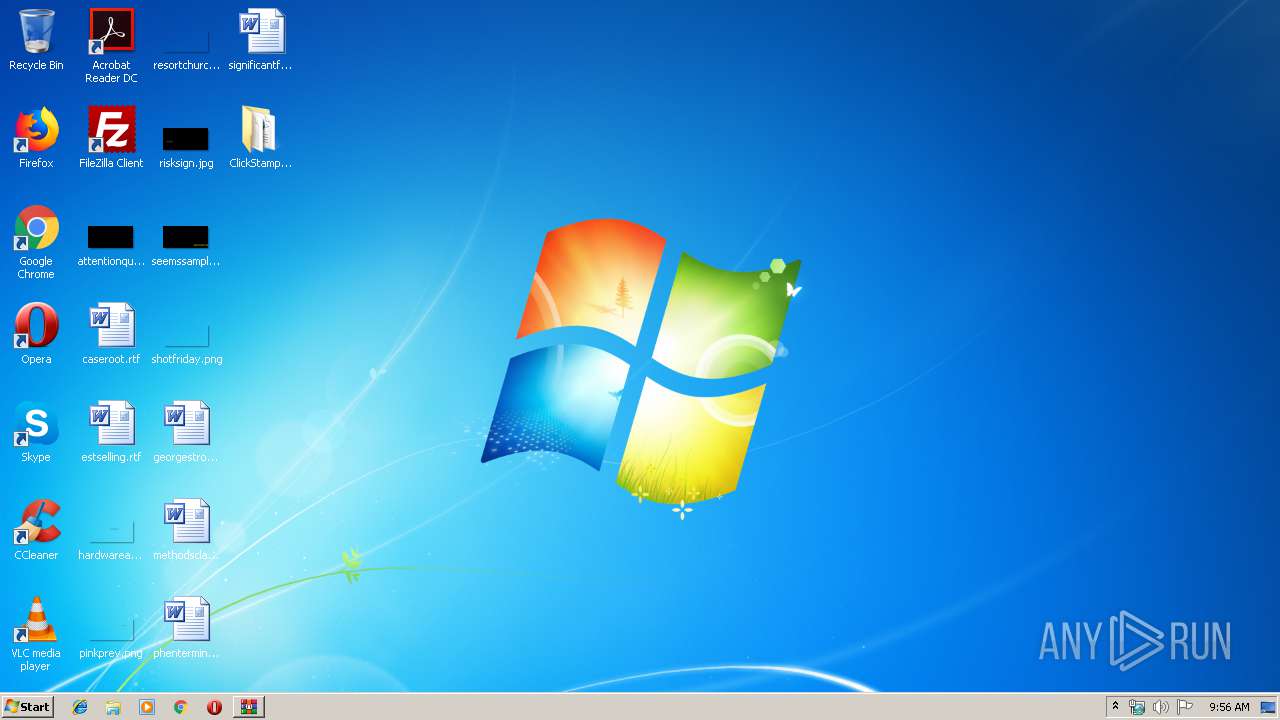
| 1292 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\ClickStamper_150\ReadMe.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
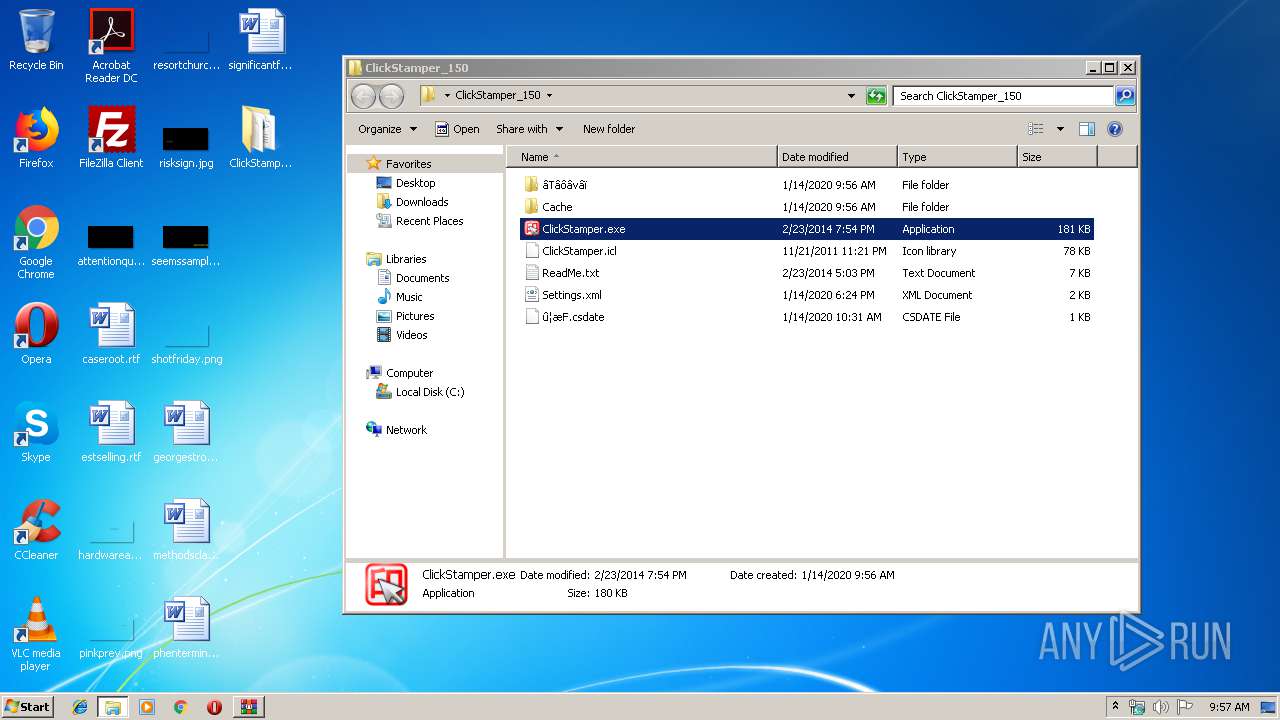
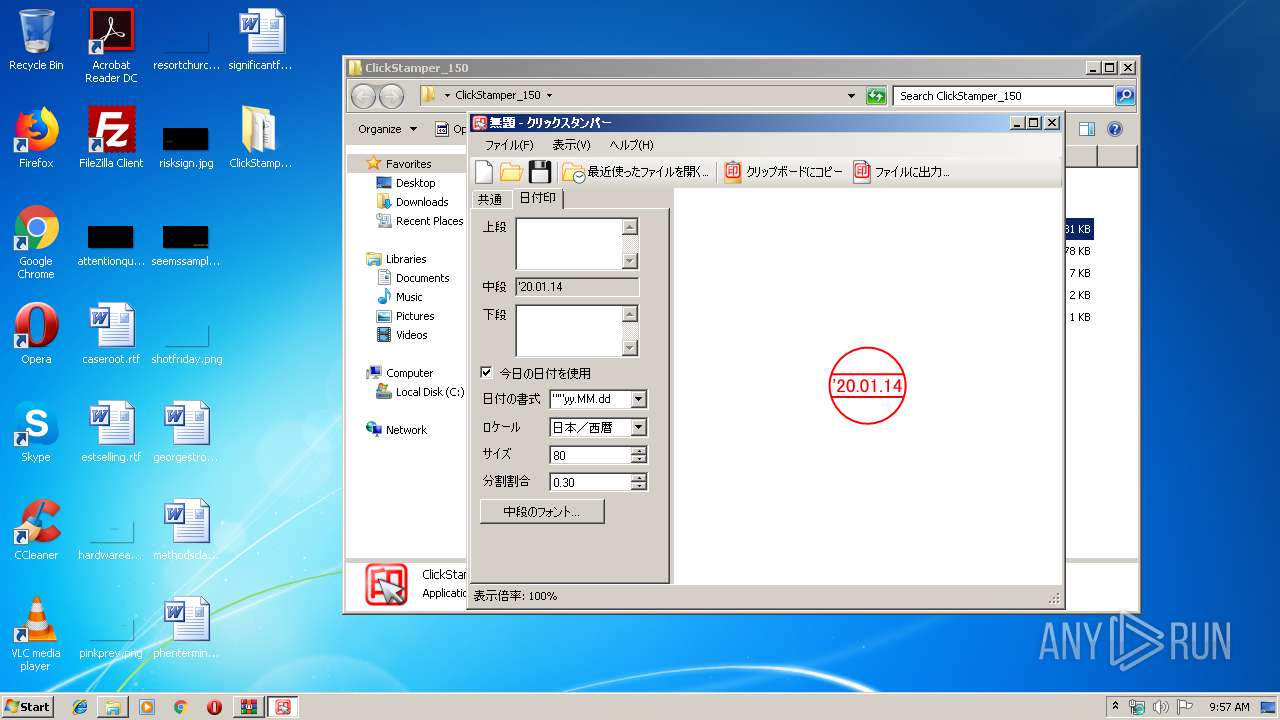
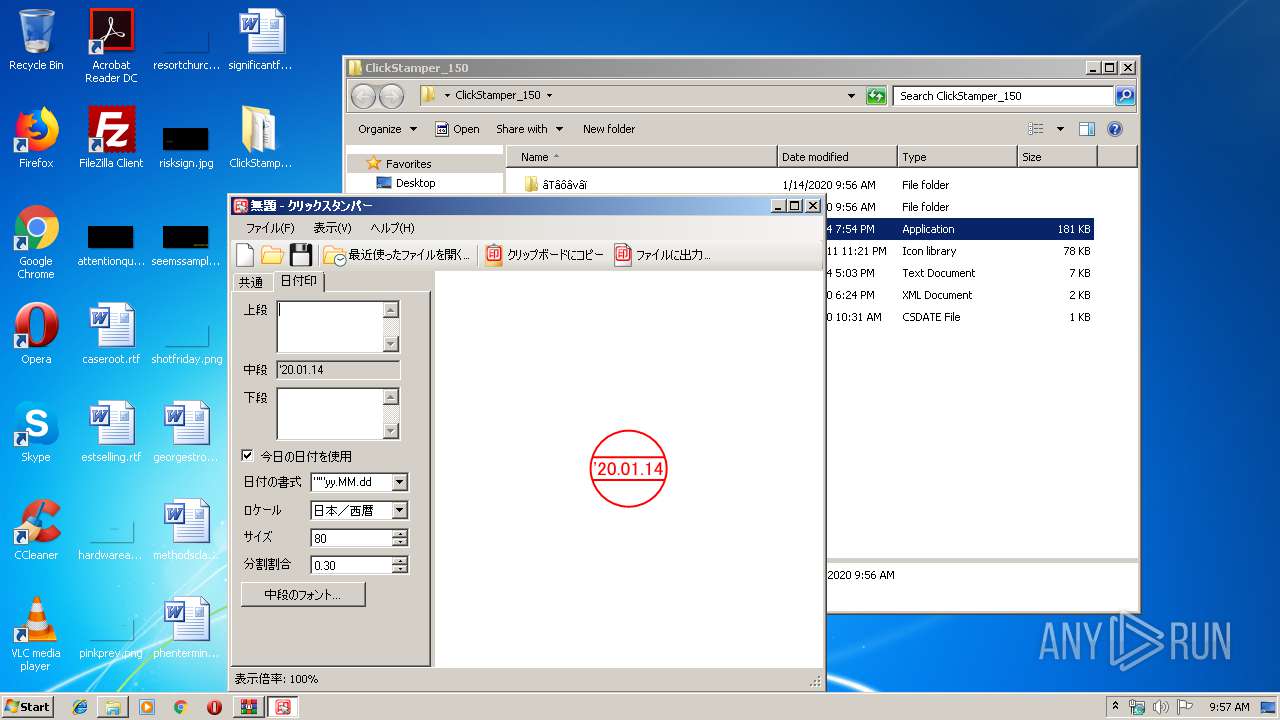
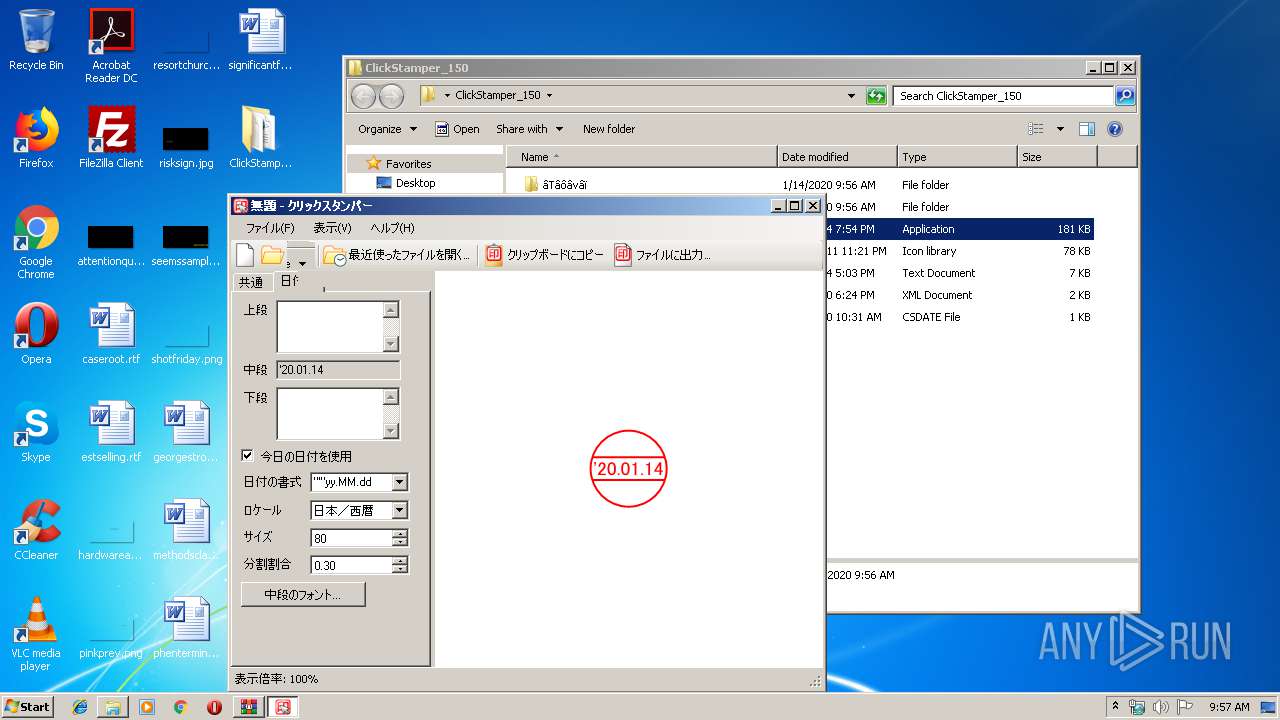
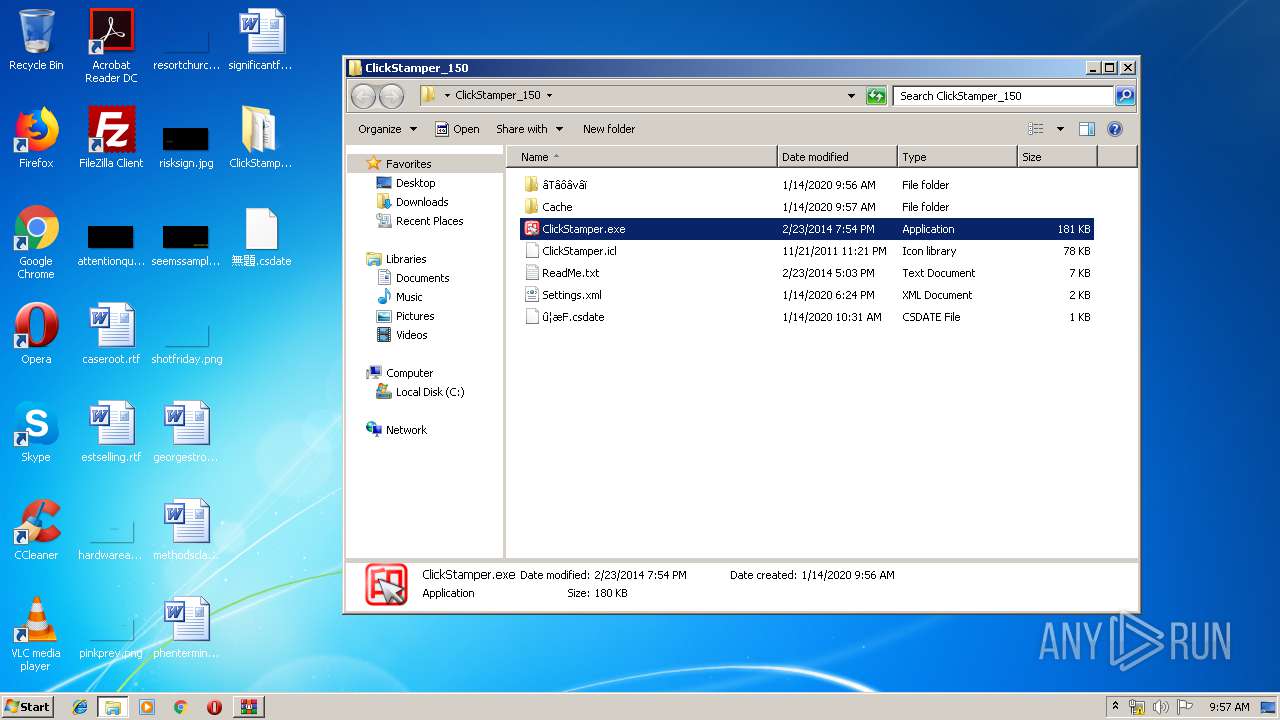
| 1908 | "C:\Users\admin\Desktop\ClickStamper_150\ClickStamper.exe" | C:\Users\admin\Desktop\ClickStamper_150\ClickStamper.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: クリックスタンパー Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 2748 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\s_kylk5z.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | ClickStamper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2944 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\uykfi_ef.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | ClickStamper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3180 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES9120.tmp" "c:\Users\admin\AppData\Local\Temp\CSC911F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
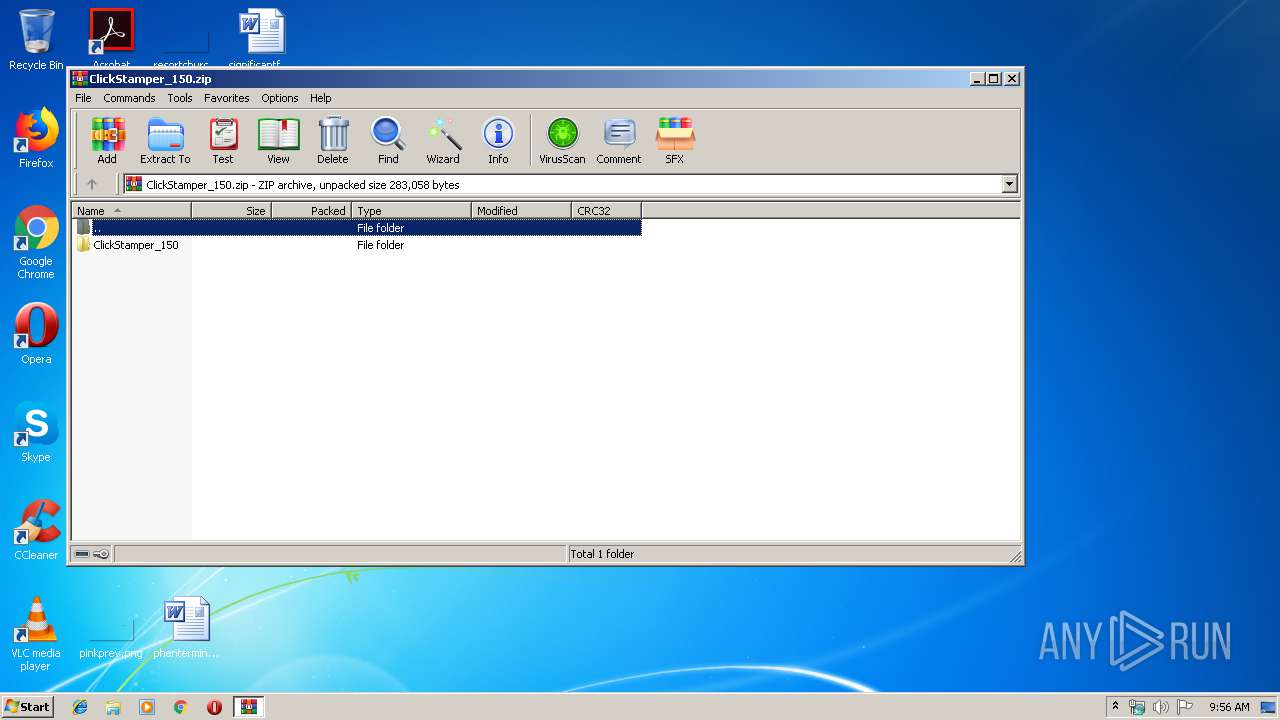
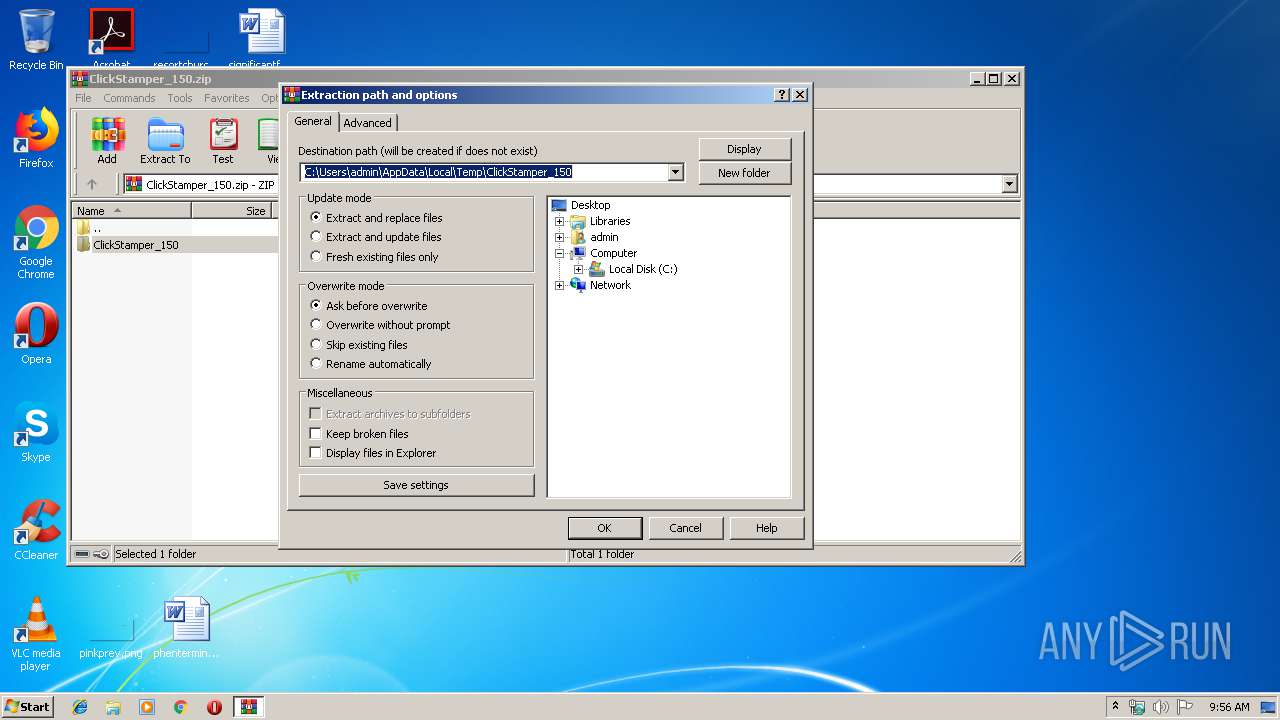
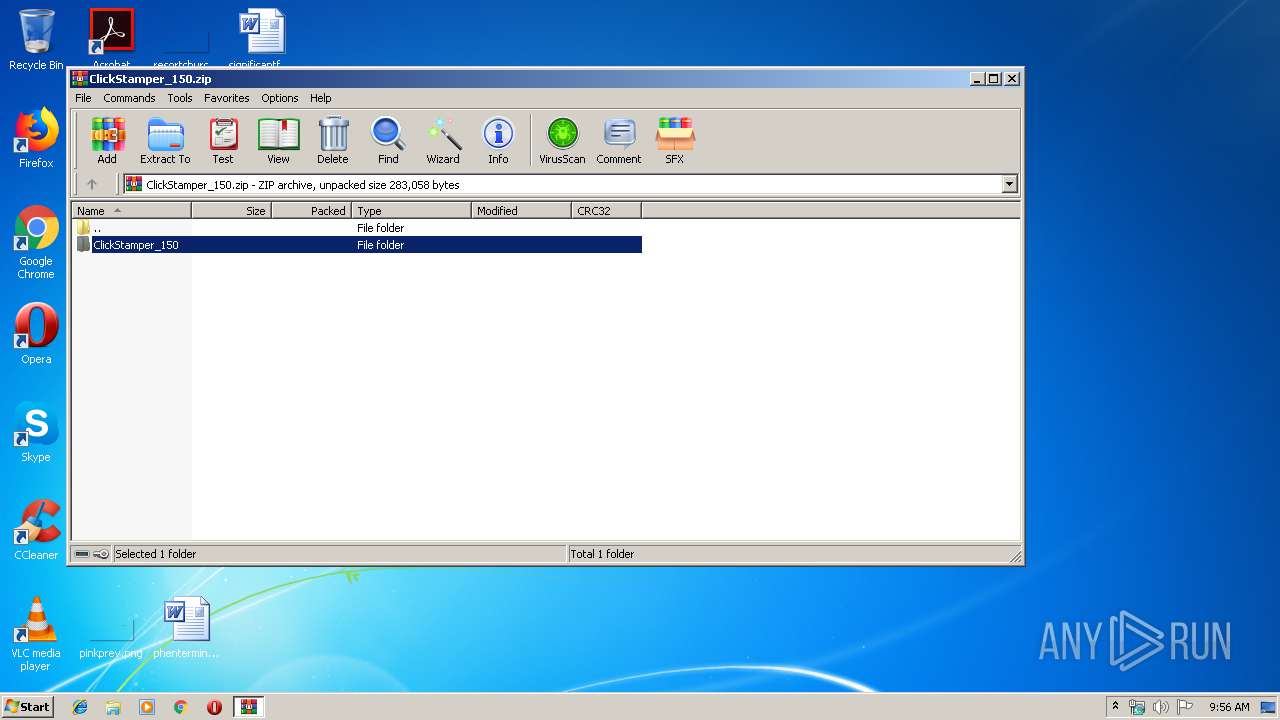
| 4060 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ClickStamper_150.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 035
Read events
952
Write events
80
Delete events
3
Modification events
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ClickStamper_150.zip | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
2
Suspicious files
0
Text files
21
Unknown types
0
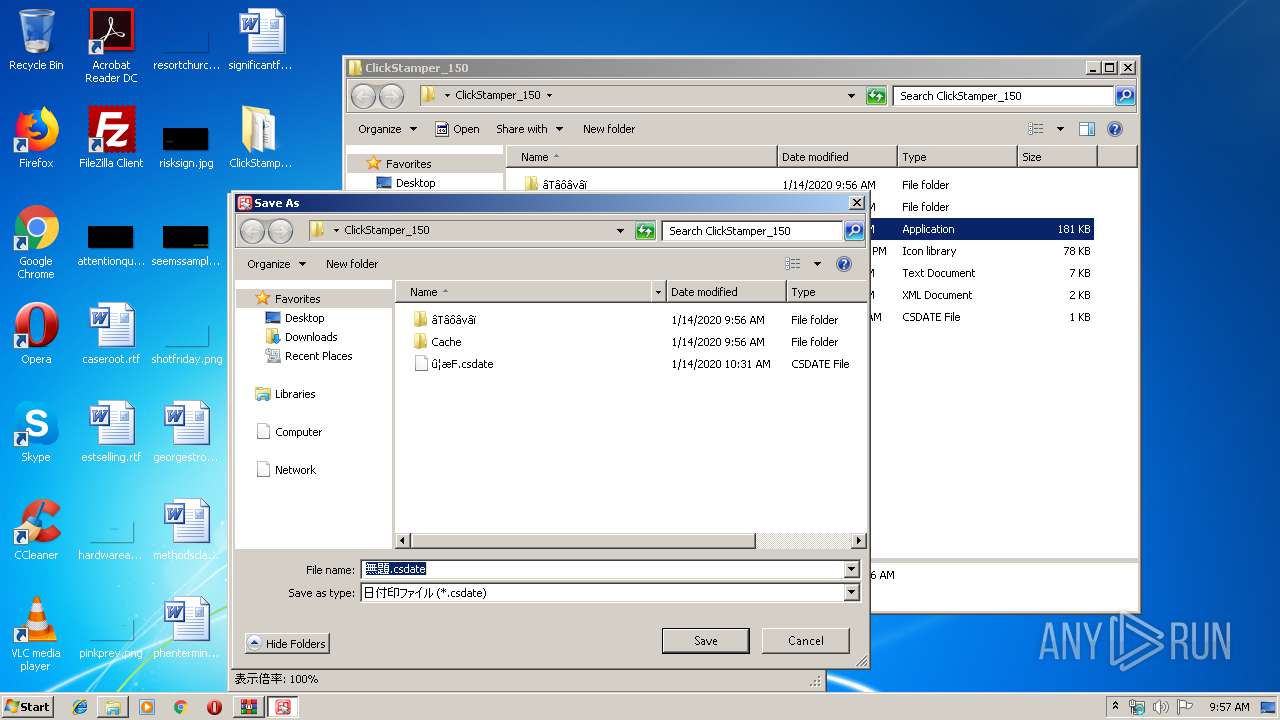
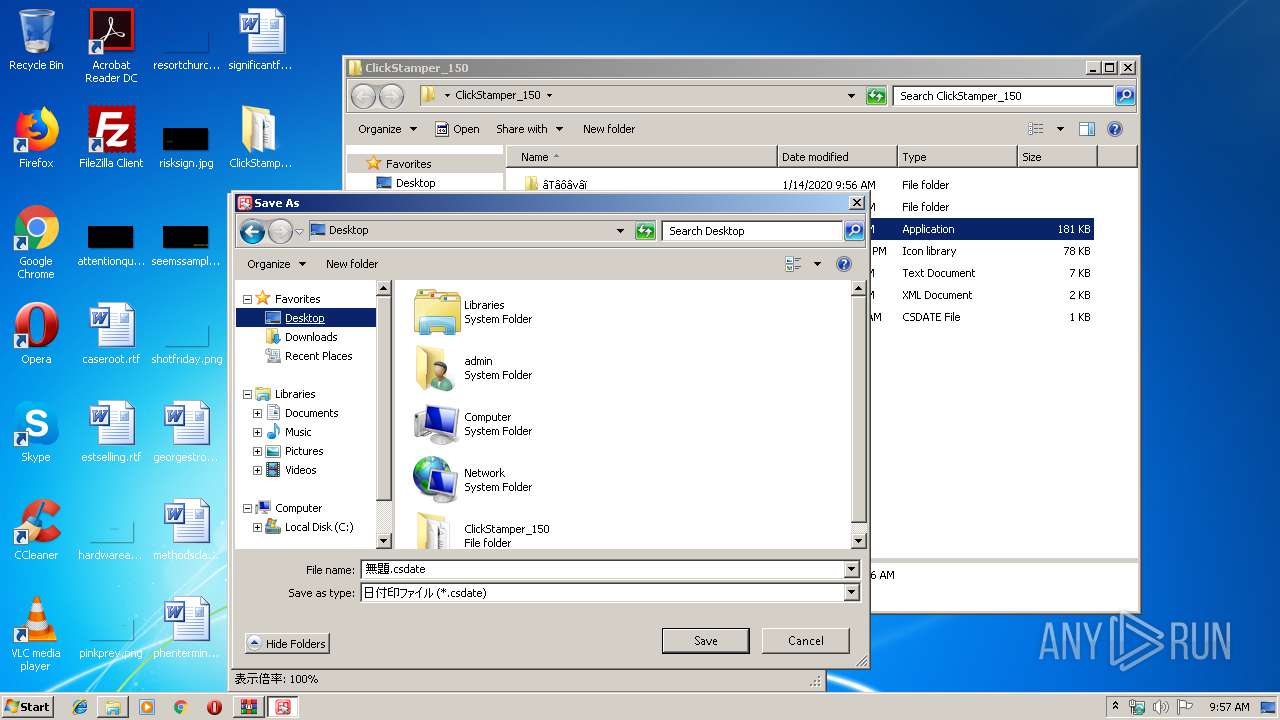
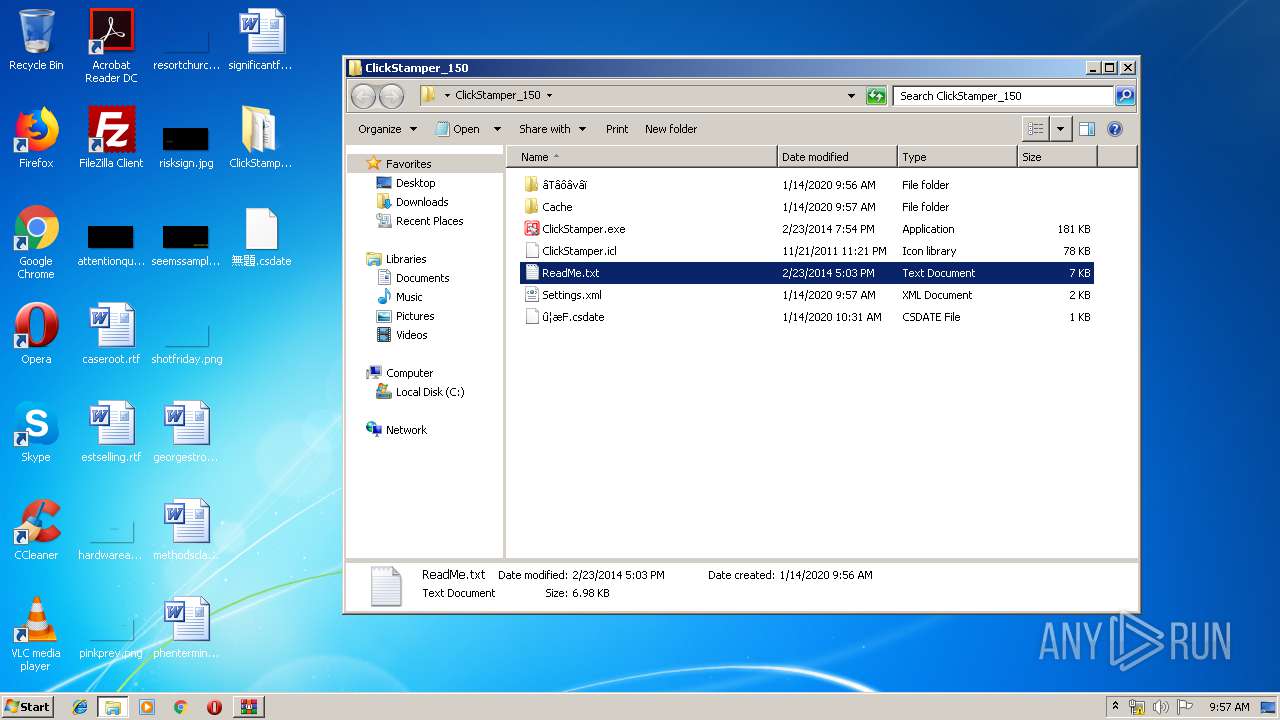
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | WinRAR.exe | C:\Users\admin\Desktop\ClickStamper_150\ClickStamper.icl | executable | |
MD5:— | SHA256:— | |||
| 2944 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC391B.tmp | — | |
MD5:— | SHA256:— | |||
| 656 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES391C.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | csc.exe | C:\Users\admin\AppData\Local\Temp\uykfi_ef.dll | — | |
MD5:— | SHA256:— | |||
| 2944 | csc.exe | C:\Users\admin\AppData\Local\Temp\uykfi_ef.out | — | |
MD5:— | SHA256:— | |||
| 1908 | ClickStamper.exe | C:\Users\admin\AppData\Local\Temp\s_kylk5z.0.cs | — | |
MD5:— | SHA256:— | |||
| 1908 | ClickStamper.exe | C:\Users\admin\AppData\Local\Temp\s_kylk5z.cmdline | — | |
MD5:— | SHA256:— | |||
| 2748 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC911F.tmp | — | |
MD5:— | SHA256:— | |||
| 3180 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES9120.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | csc.exe | C:\Users\admin\AppData\Local\Temp\s_kylk5z.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report